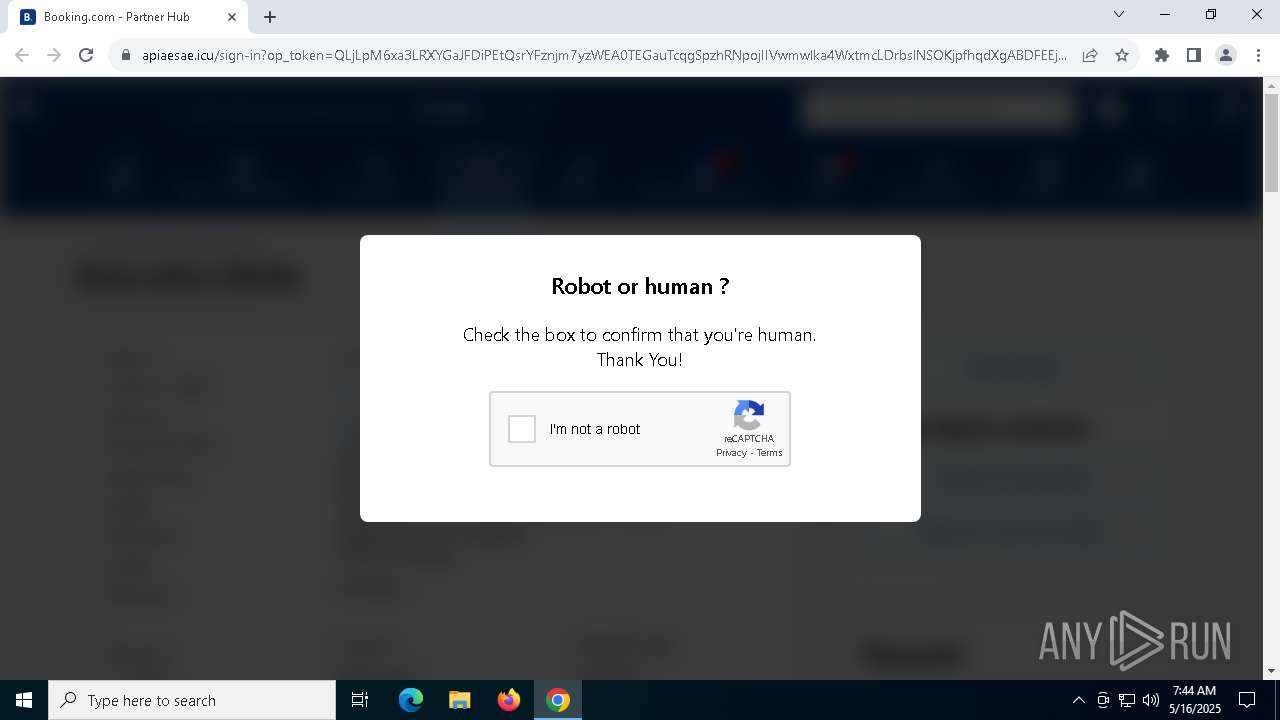
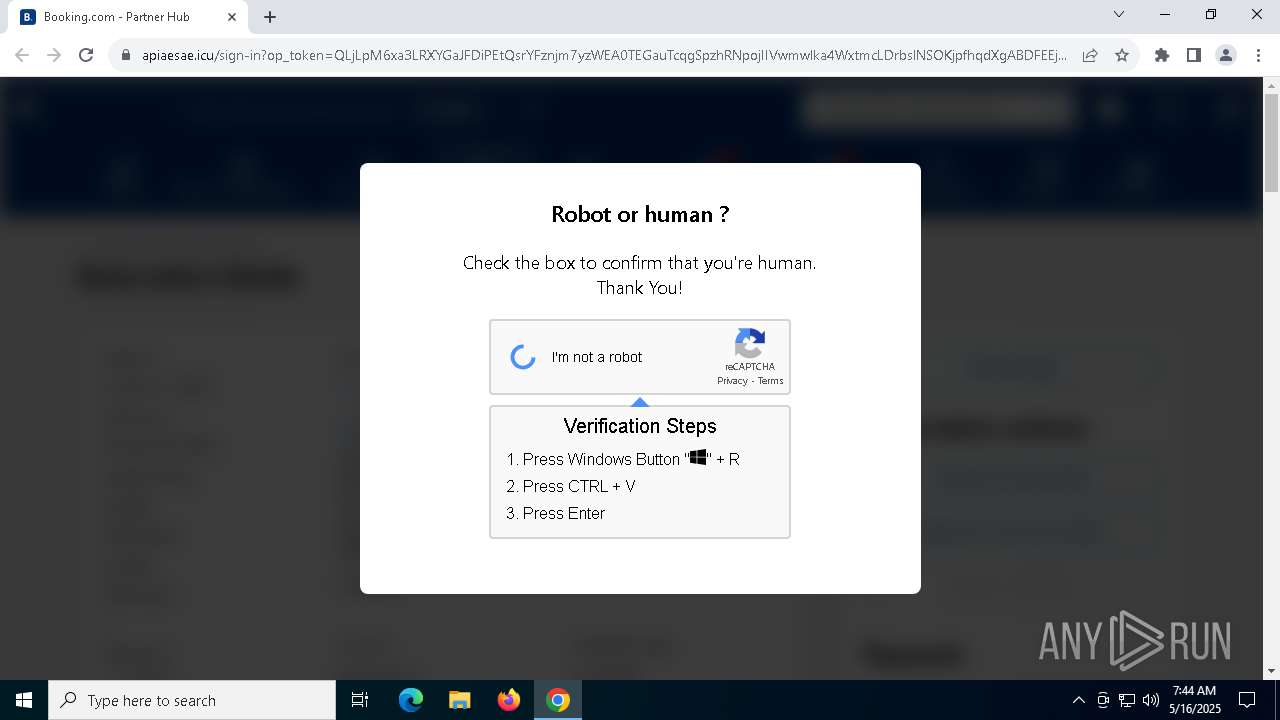
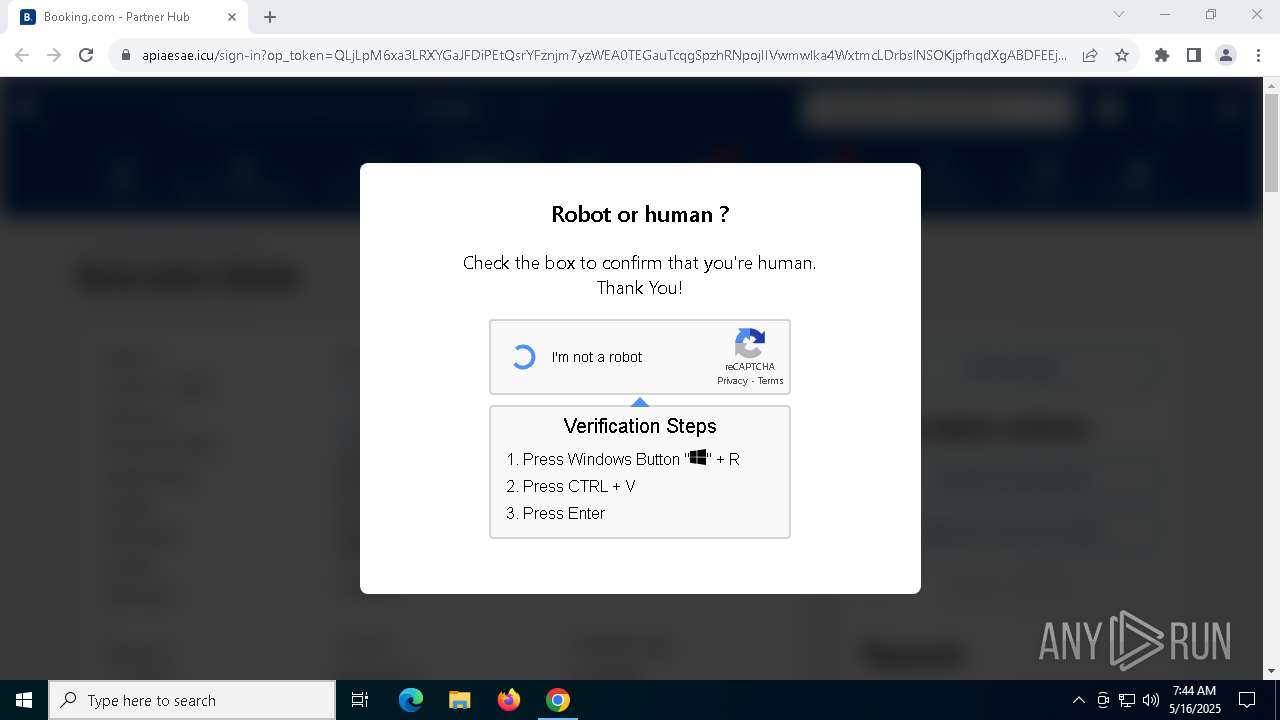
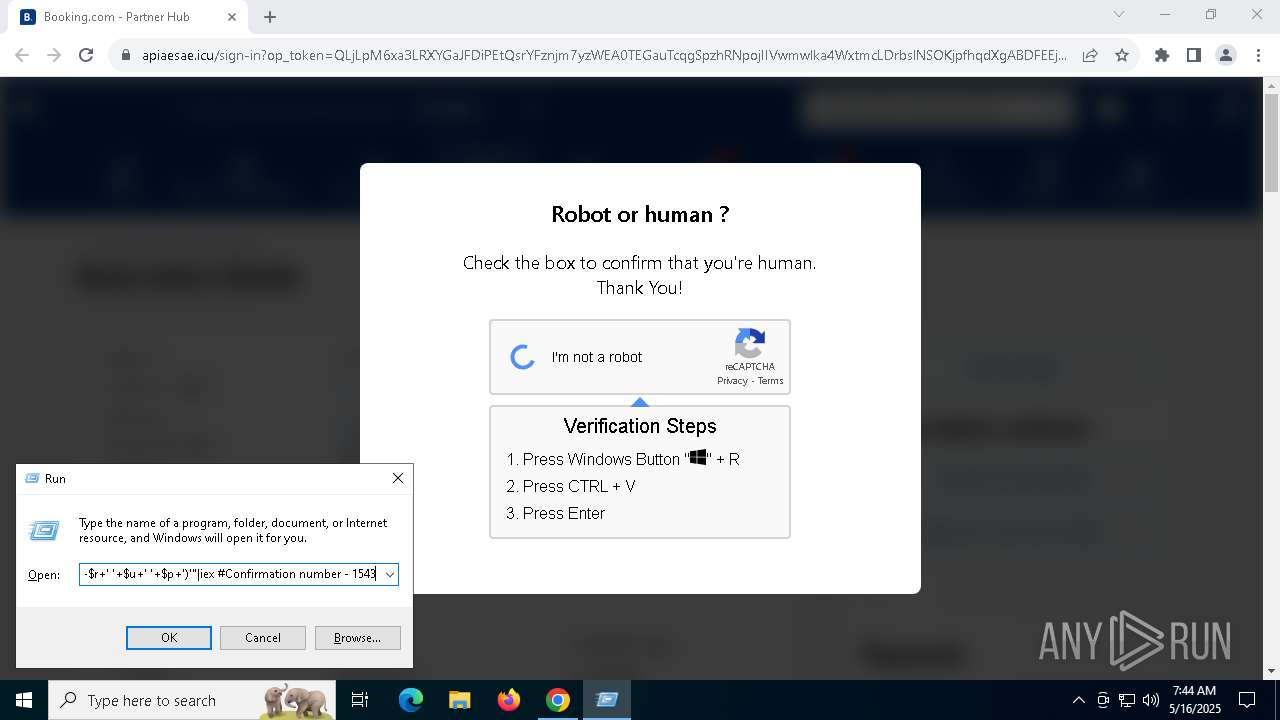
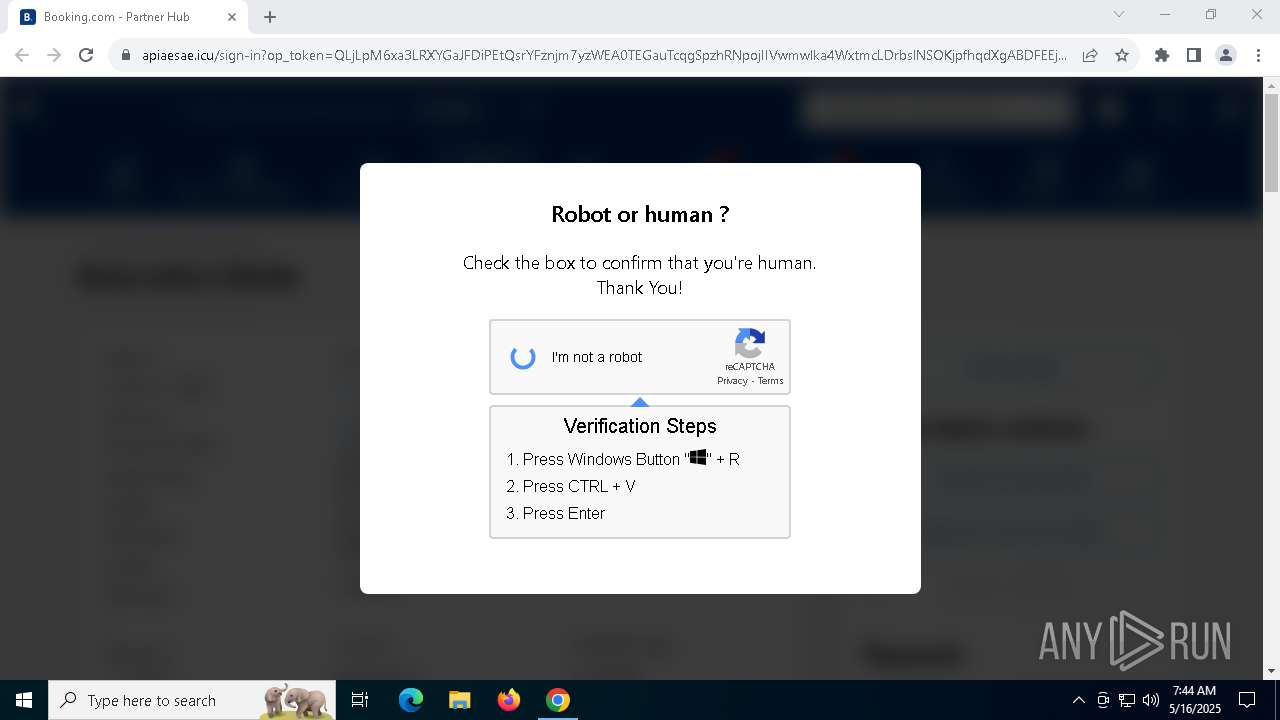
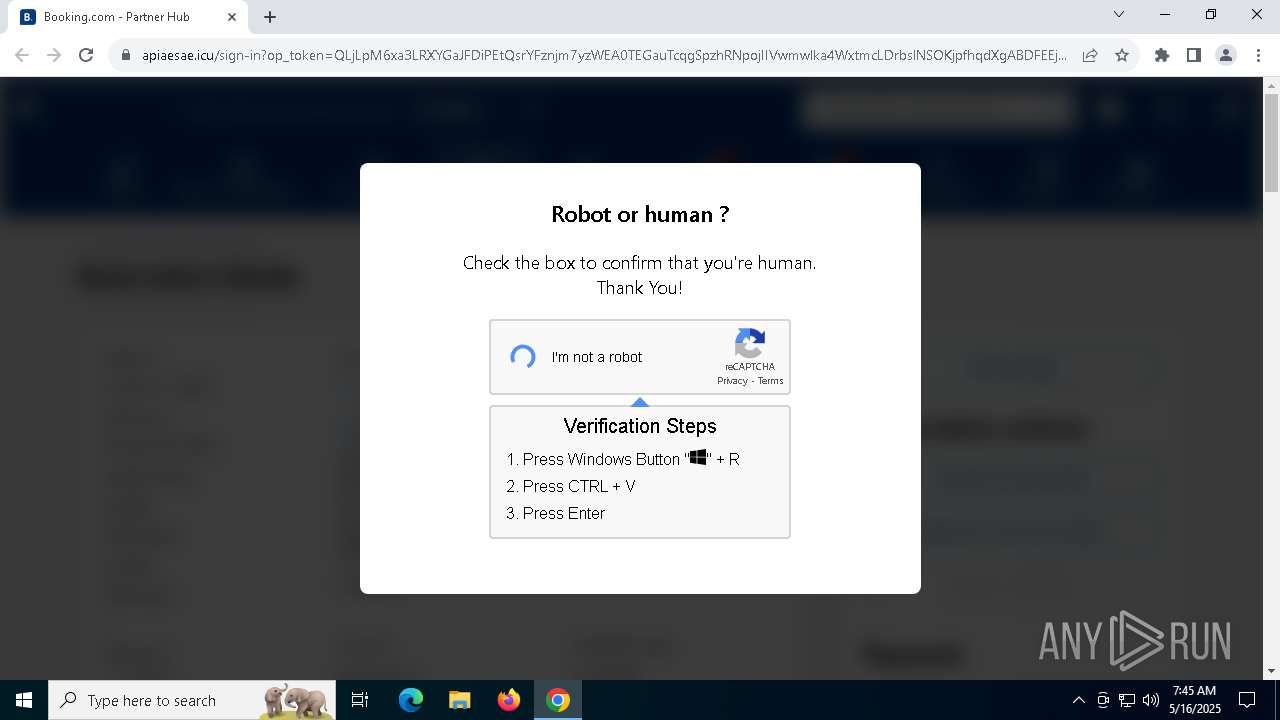
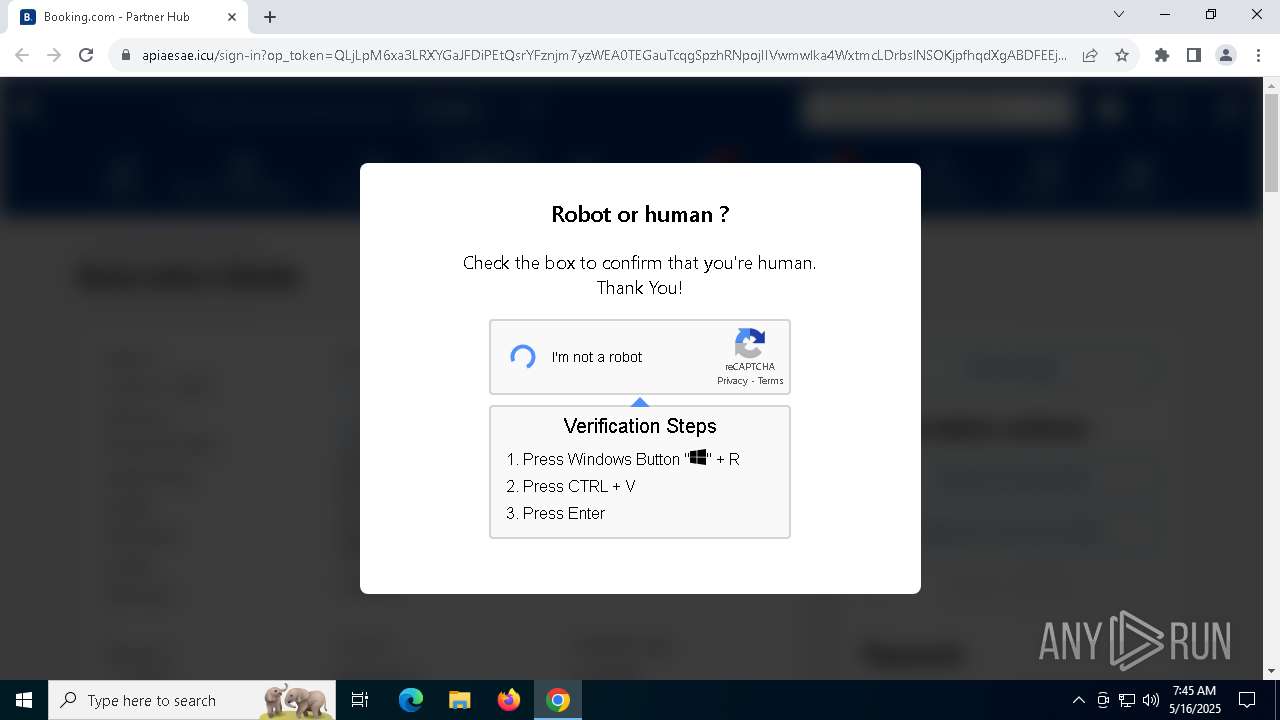
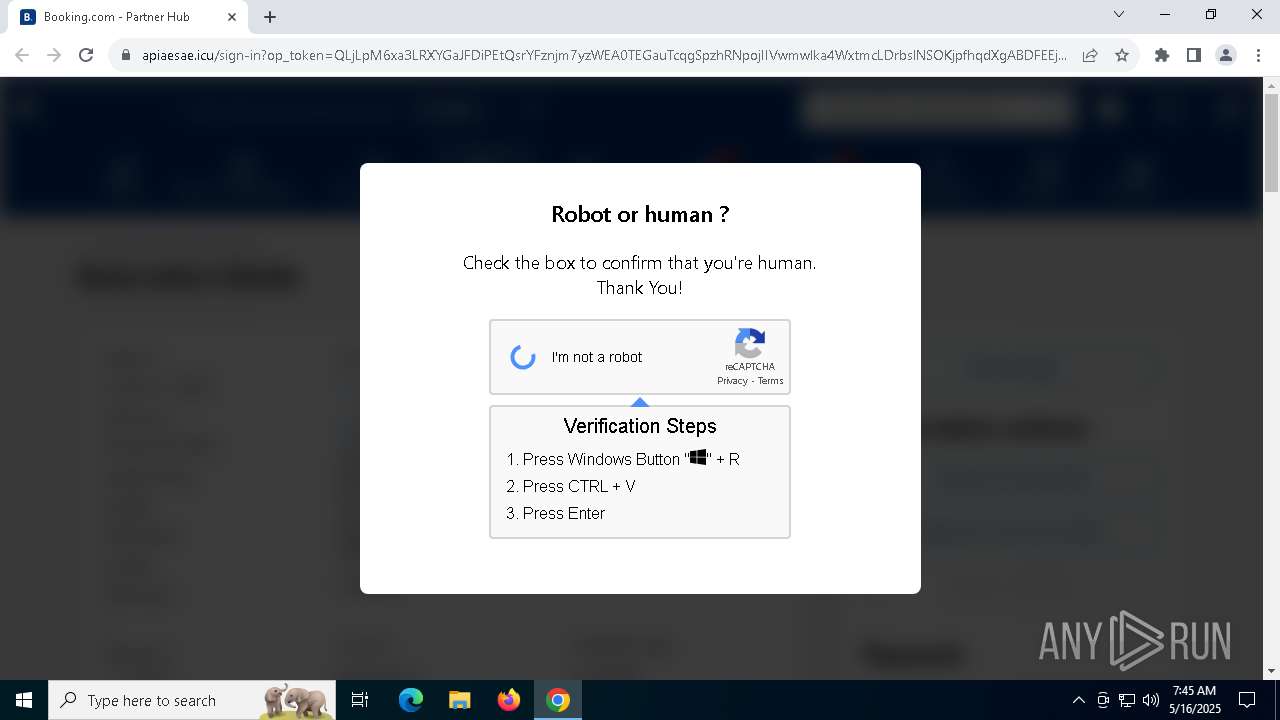
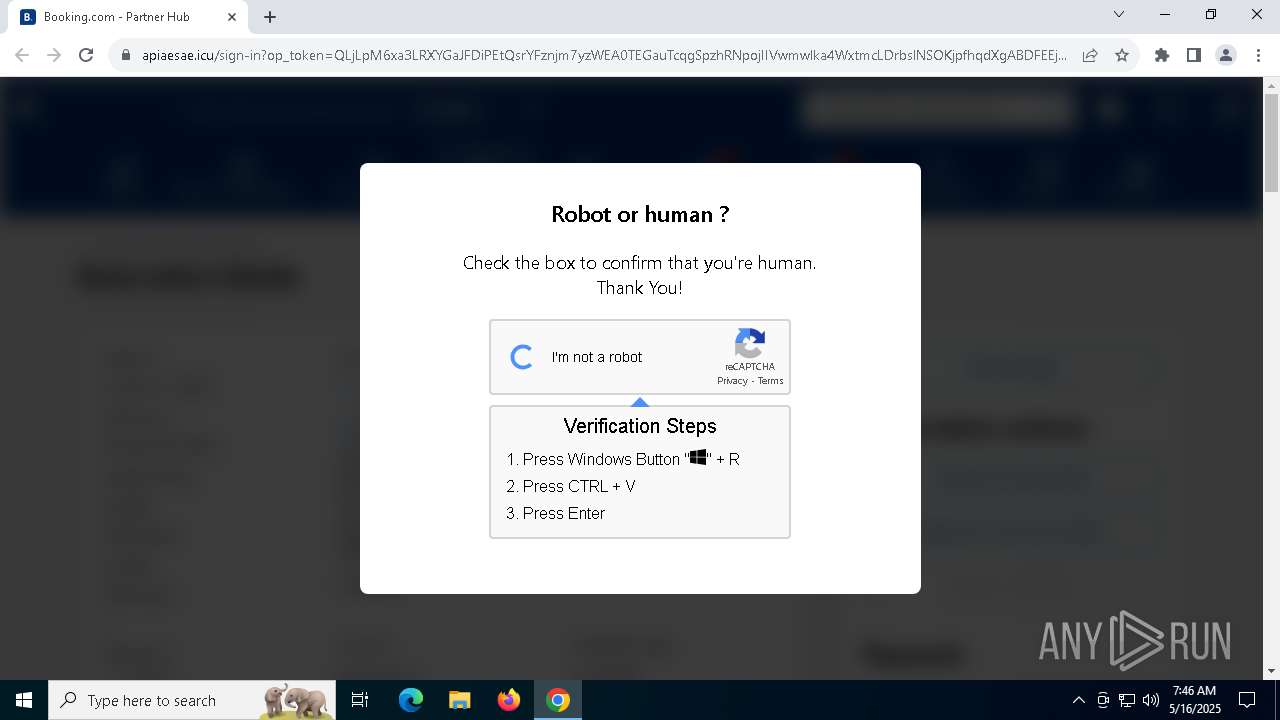
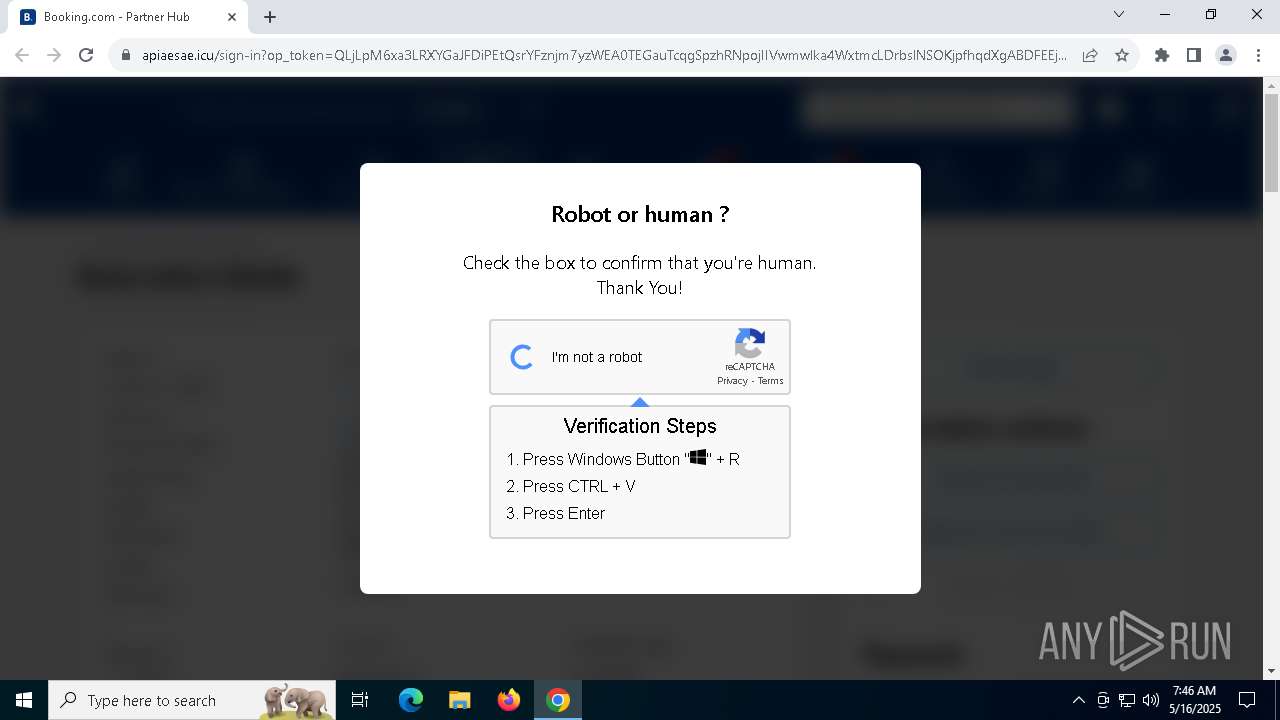
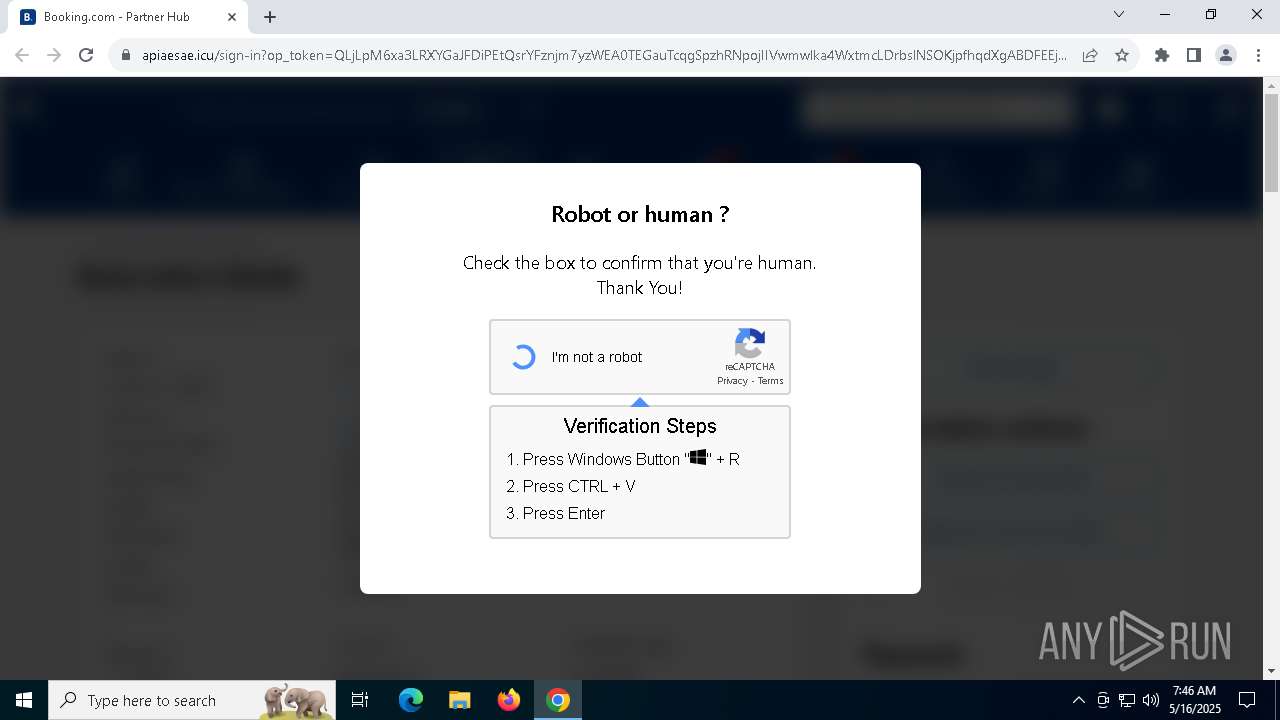
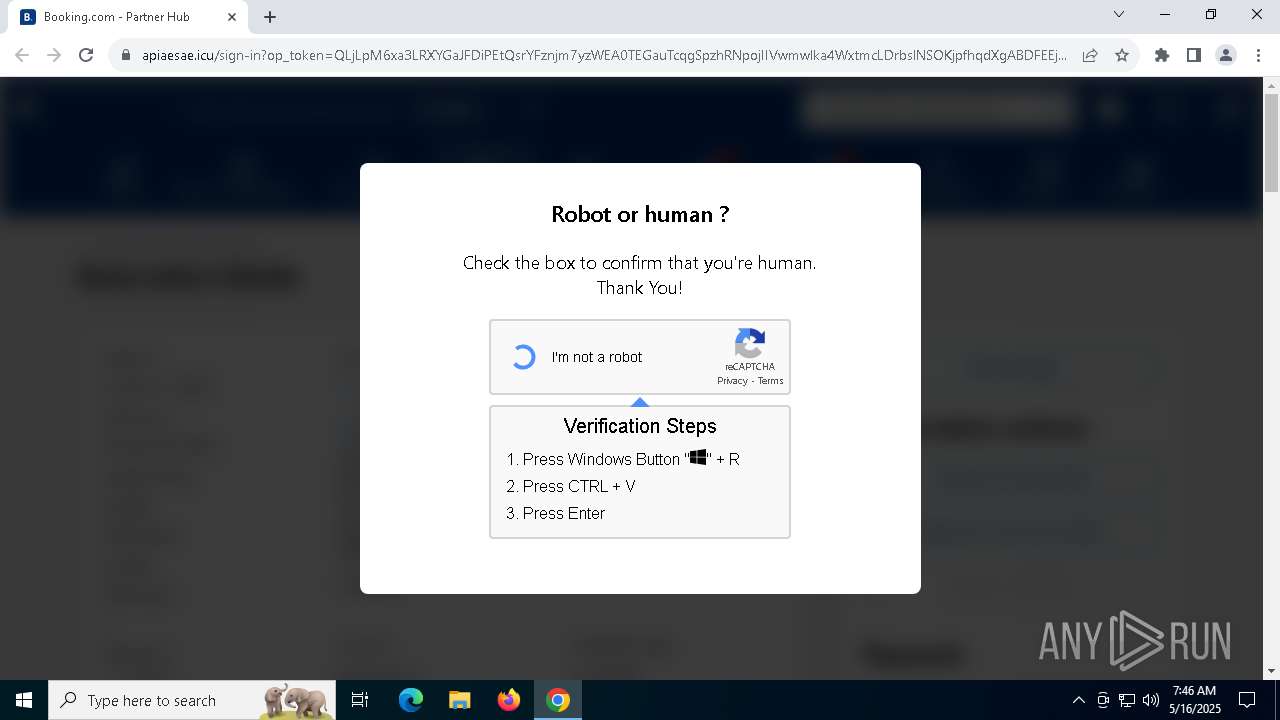
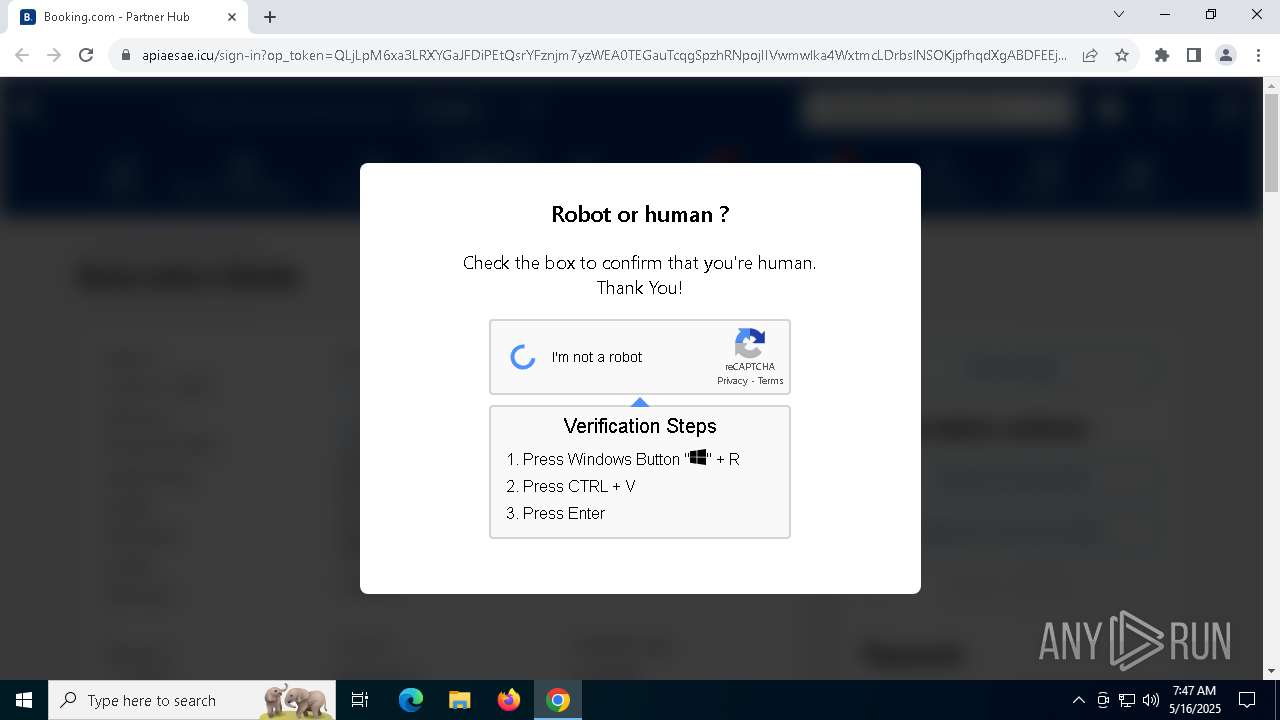
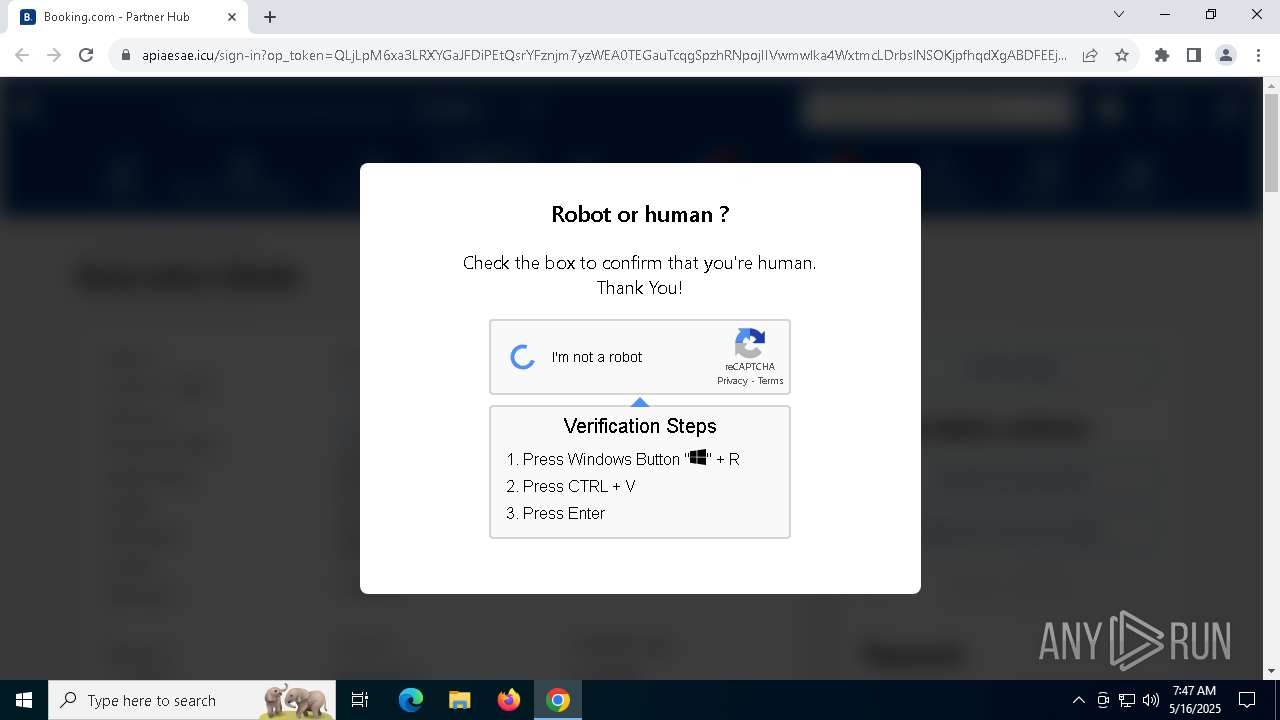
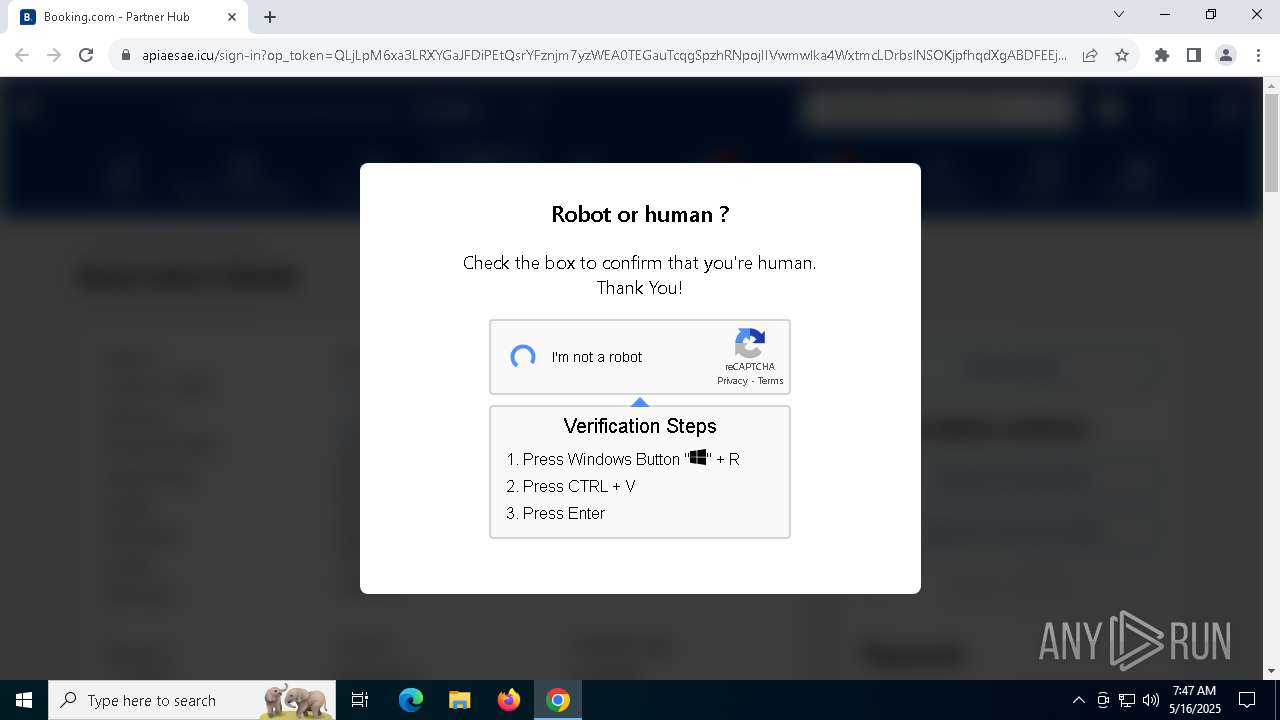
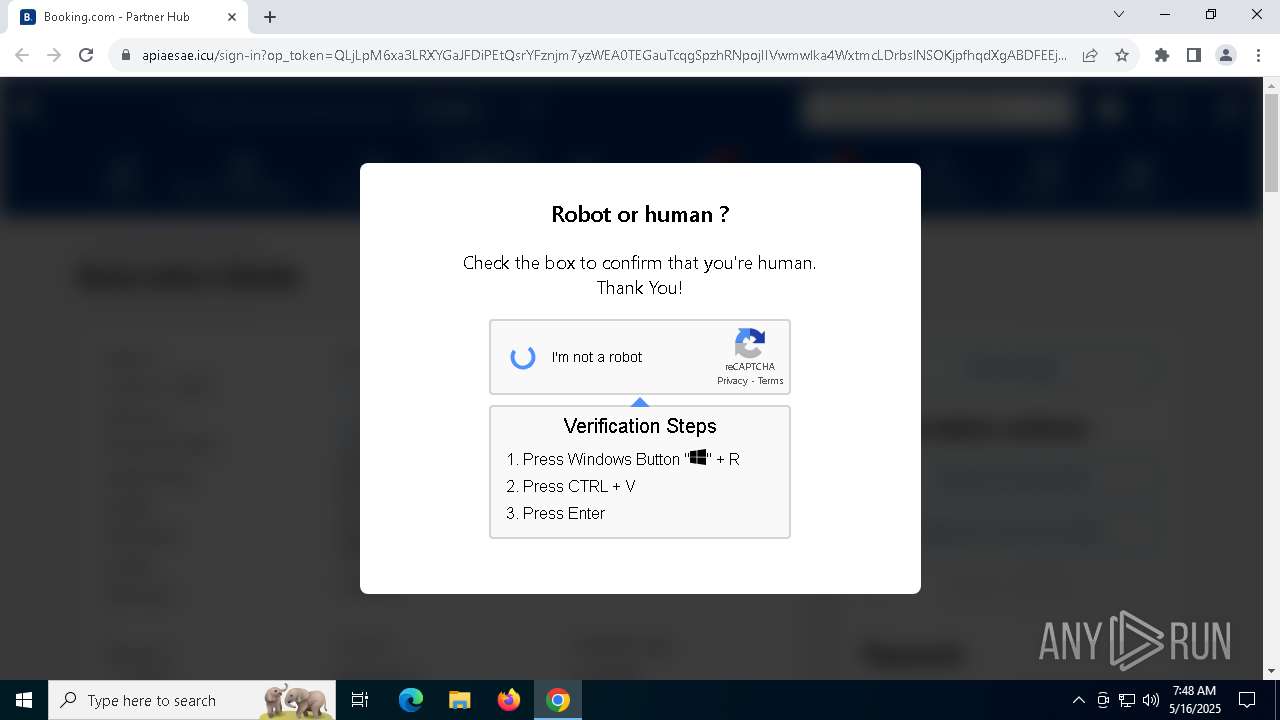
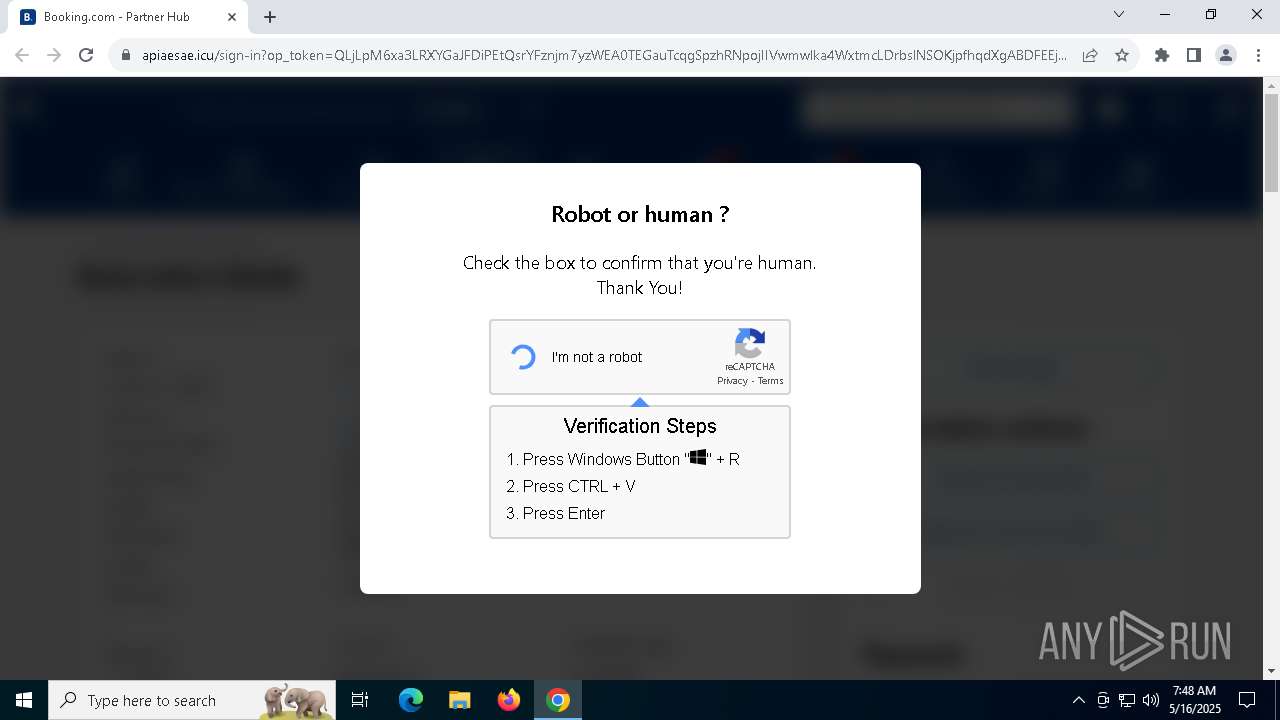
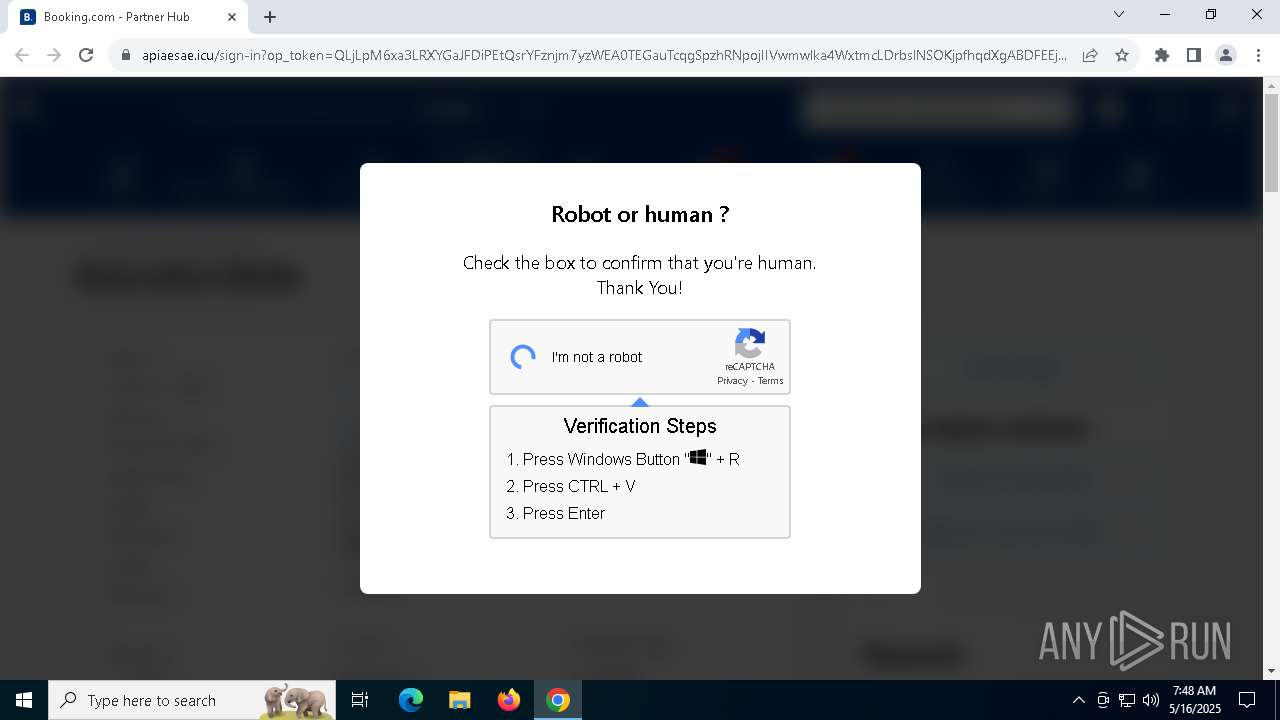
| URL: | apiaesae.icu |
| Full analysis: | https://app.any.run/tasks/f2a6d355-06c9-4743-8881-beac25683bf7 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 07:44:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EC2B50B7378CB3FE5D28A521DF3BF6D8 |
| SHA1: | 03C839F513C37890252269C6A9CE96649AD5AED9 |
| SHA256: | 28A253A8EC206AB56D0AFA4304D3606136B5EF531ADF6497912C61B286D978AD |
| SSDEEP: | 3:8MOLQn:8MBn |
MALICIOUS
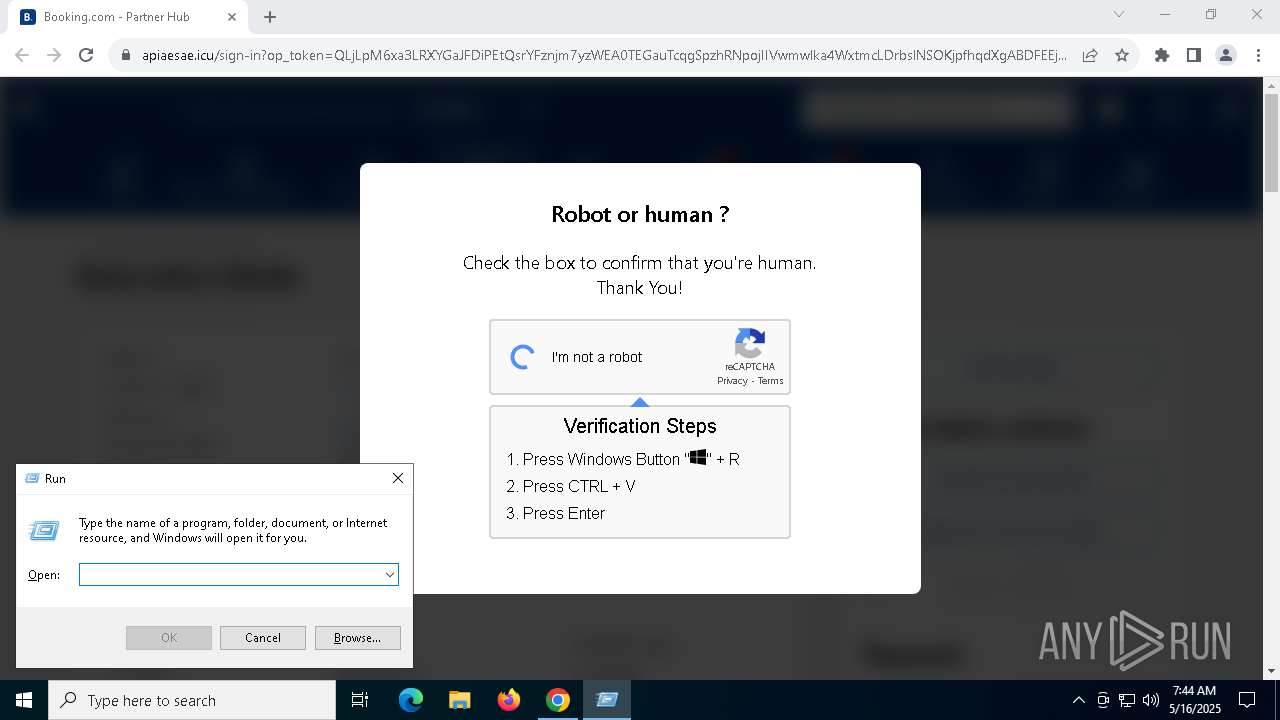
Bypass execution policy to execute commands
- powershell.exe (PID: 6632)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8104)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 8104)
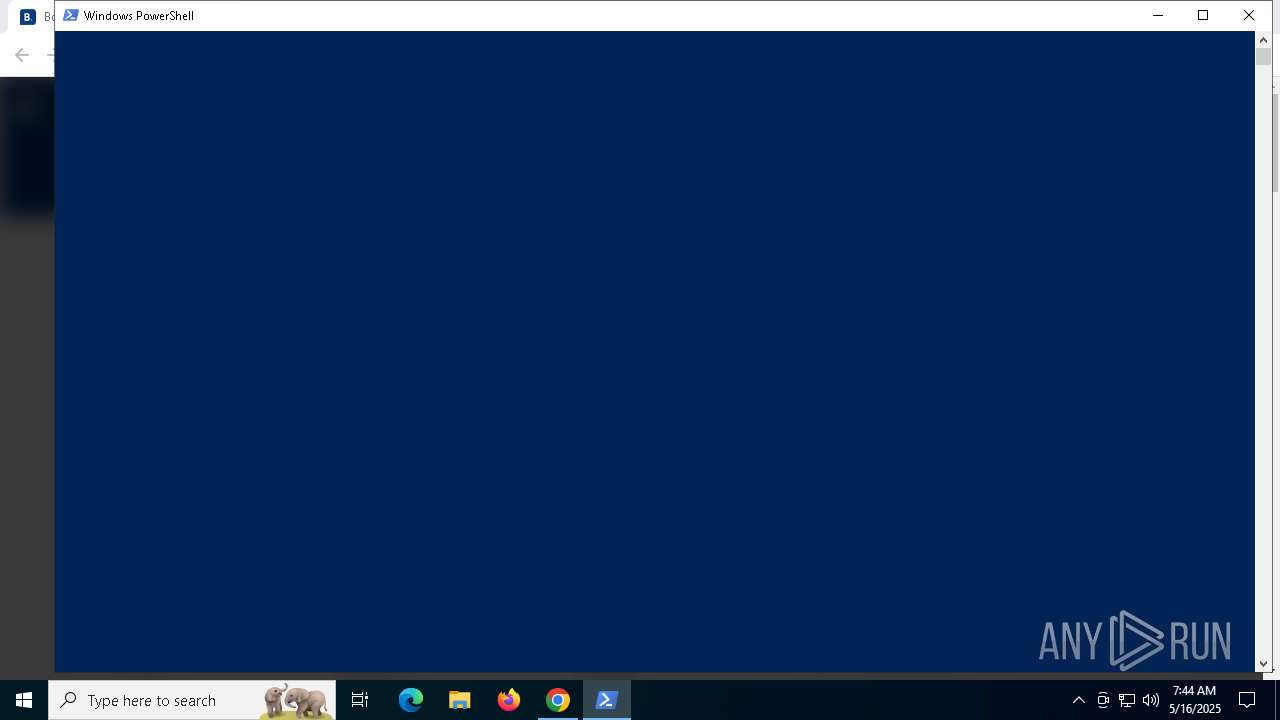
Run PowerShell with an invisible window
- powershell.exe (PID: 6632)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6632)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 6068)
SUSPICIOUS
Executes script without checking the security policy
- powershell.exe (PID: 8104)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8104)
Application launched itself
- powershell.exe (PID: 8104)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 8104)
Base64-obfuscated command line is found
- powershell.exe (PID: 8104)
Executable content was dropped or overwritten
- powershell.exe (PID: 6632)
Executes application which crashes
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 900)
INFO
Application launched itself
- chrome.exe (PID: 5408)
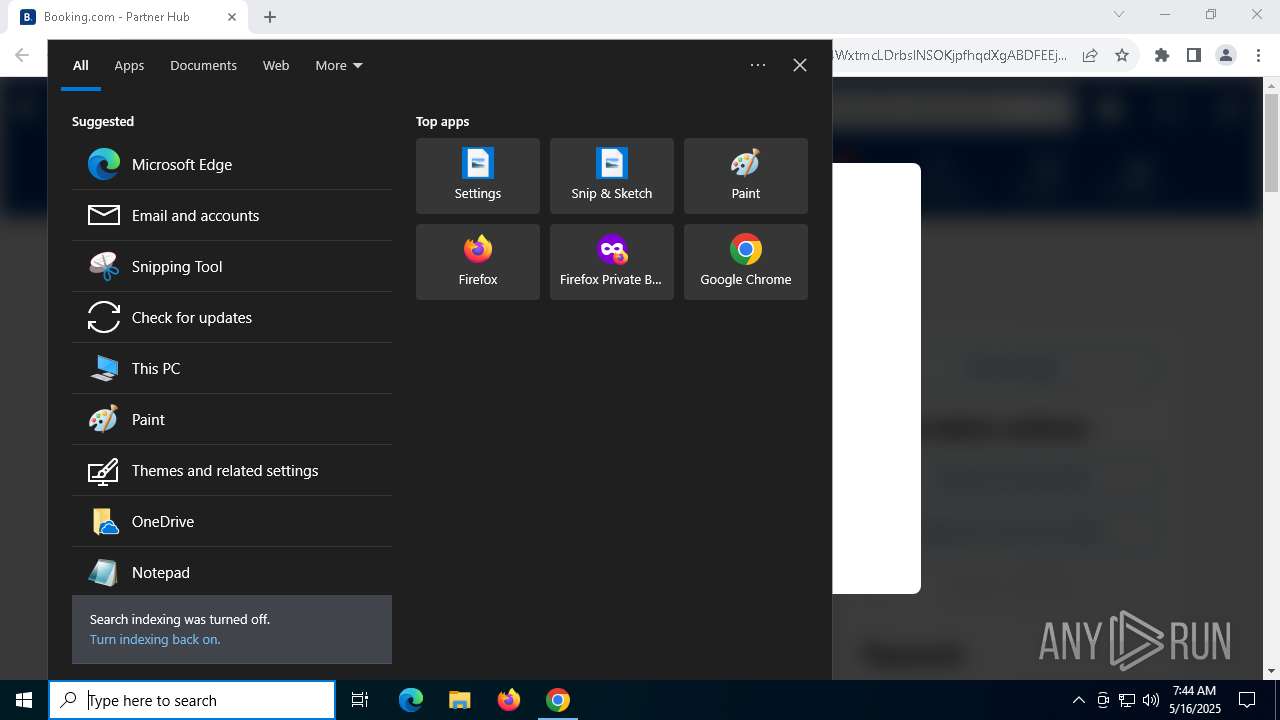
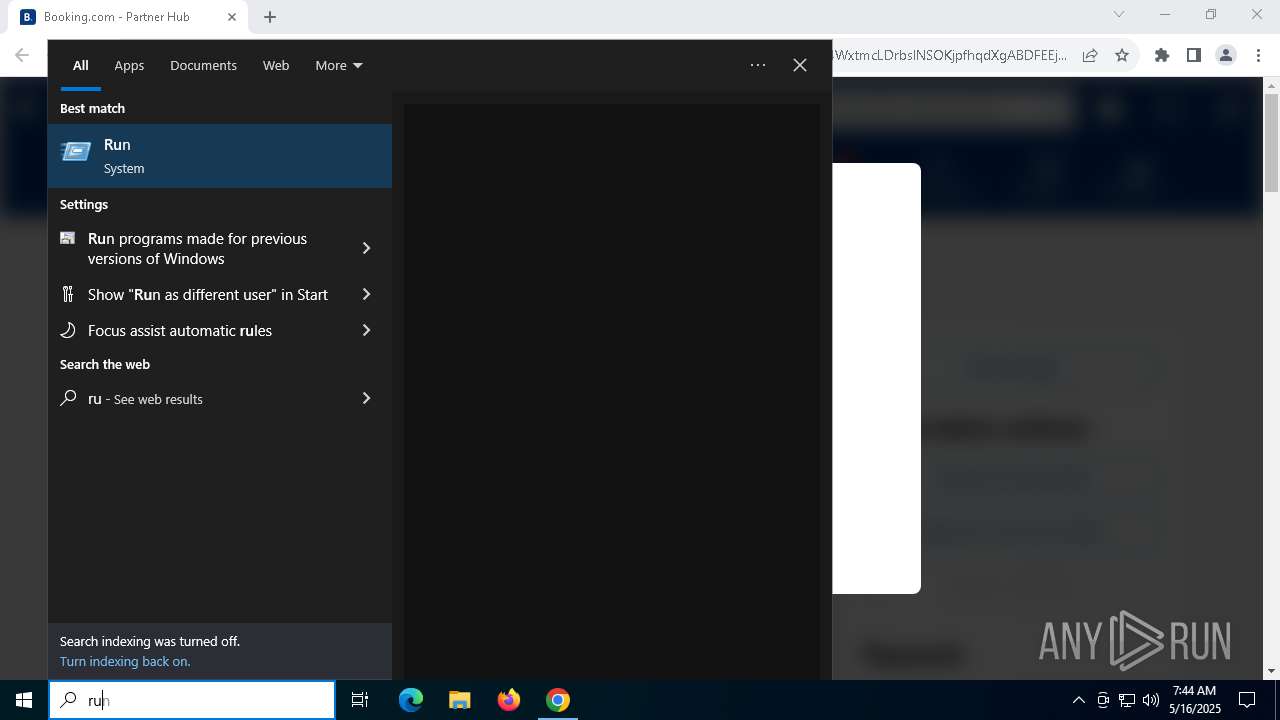
Manual execution by a user
- powershell.exe (PID: 8104)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8104)
Disables trace logs
- powershell.exe (PID: 8104)
- powershell.exe (PID: 6632)
Checks proxy server information
- powershell.exe (PID: 8104)
- powershell.exe (PID: 6632)
- slui.exe (PID: 920)
Found Base64 encoded network access via PowerShell (YARA)
- powershell.exe (PID: 8104)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 8104)
The executable file from the user directory is run by the Powershell process
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 6512)
Checks supported languages
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 6512)
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 900)
Reads the computer name
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 6512)
- 037ac97a-700b-4469-ab10-ba9541b8213f.exe (PID: 900)
Creates files or folders in the user directory
- WerFault.exe (PID: 6004)
Reads the software policy settings
- slui.exe (PID: 920)
- slui.exe (PID: 7772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
171
Monitored processes
30
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Users\admin\AppData\Local\Temp\037ac97a-700b-4469-ab10-ba9541b8213f.exe" | C:\Users\admin\AppData\Local\Temp\037ac97a-700b-4469-ab10-ba9541b8213f.exe | ComputerDefaults.exe | ||||||||||||
User: admin Company: Underarms frig Integrity Level: HIGH Description: Modernness boscage kaolines Exit code: 2147483652 Version: 7.224.111.5 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5088 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4848 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=868 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4648 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4804 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5088 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5132 --field-trial-handle=1824,i,18353372193487620382,8022295896525902567,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "apiaesae.icu" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
19 356
Read events
19 307
Write events
40
Delete events
9
Modification events
| (PID) Process: | (5408) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5408) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5408) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5408) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5408) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6004) WerFault.exe | Key: | \REGISTRY\A\{dc803d6e-14cf-366e-8ef1-42afaeb76a71}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (6004) WerFault.exe | Key: | \REGISTRY\A\{dc803d6e-14cf-366e-8ef1-42afaeb76a71}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6004) WerFault.exe | Key: | \REGISTRY\A\{dc803d6e-14cf-366e-8ef1-42afaeb76a71}\Root\InventoryApplicationFile\037ac97a-700b-44|ef604ea716b337cd |
| Operation: | write | Name: | LinkDate |
Value: 11/16/2023 20:21:30 | |||
| (PID) Process: | (6004) WerFault.exe | Key: | \REGISTRY\A\{dc803d6e-14cf-366e-8ef1-42afaeb76a71}\Root\InventoryApplicationFile\037ac97a-700b-44|ef604ea716b337cd |
| Operation: | write | Name: | BinProductVersion |
Value: 7.224.111.5 | |||
| (PID) Process: | (6004) WerFault.exe | Key: | \REGISTRY\A\{dc803d6e-14cf-366e-8ef1-42afaeb76a71}\Root\InventoryApplicationFile\037ac97a-700b-44|ef604ea716b337cd |
| Operation: | write | Name: | AppxPackageFullName |
Value: | |||
Executable files
9
Suspicious files
438
Text files
40
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10d89f.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10d89f.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10d89f.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10d8ae.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10d8ae.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
71
DNS requests
63
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8028 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5780 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
5780 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
5780 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
5780 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7204 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5408 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7204 | chrome.exe | 172.67.186.110:443 | apiaesae.icu | CLOUDFLARENET | US | unknown |
7204 | chrome.exe | 172.67.186.110:80 | apiaesae.icu | CLOUDFLARENET | US | unknown |
7204 | chrome.exe | 18.66.147.79:443 | partner.booking.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
apiaesae.icu |
| unknown |
accounts.google.com |
| whitelisted |
partner.booking.com |
| whitelisted |
bstatic.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7204 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
7204 | chrome.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7204 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |