| File name: | Activator.exe |
| Full analysis: | https://app.any.run/tasks/9c5186b9-409e-4290-817f-db972cd1bfbd |
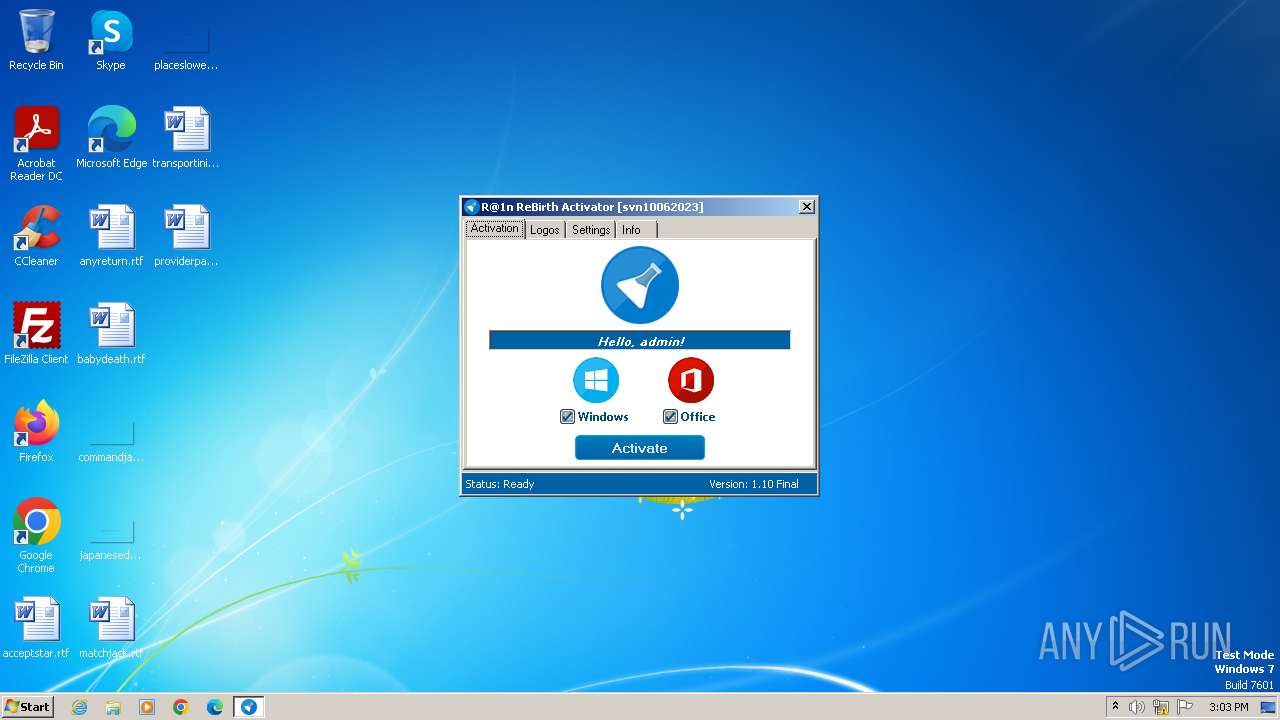
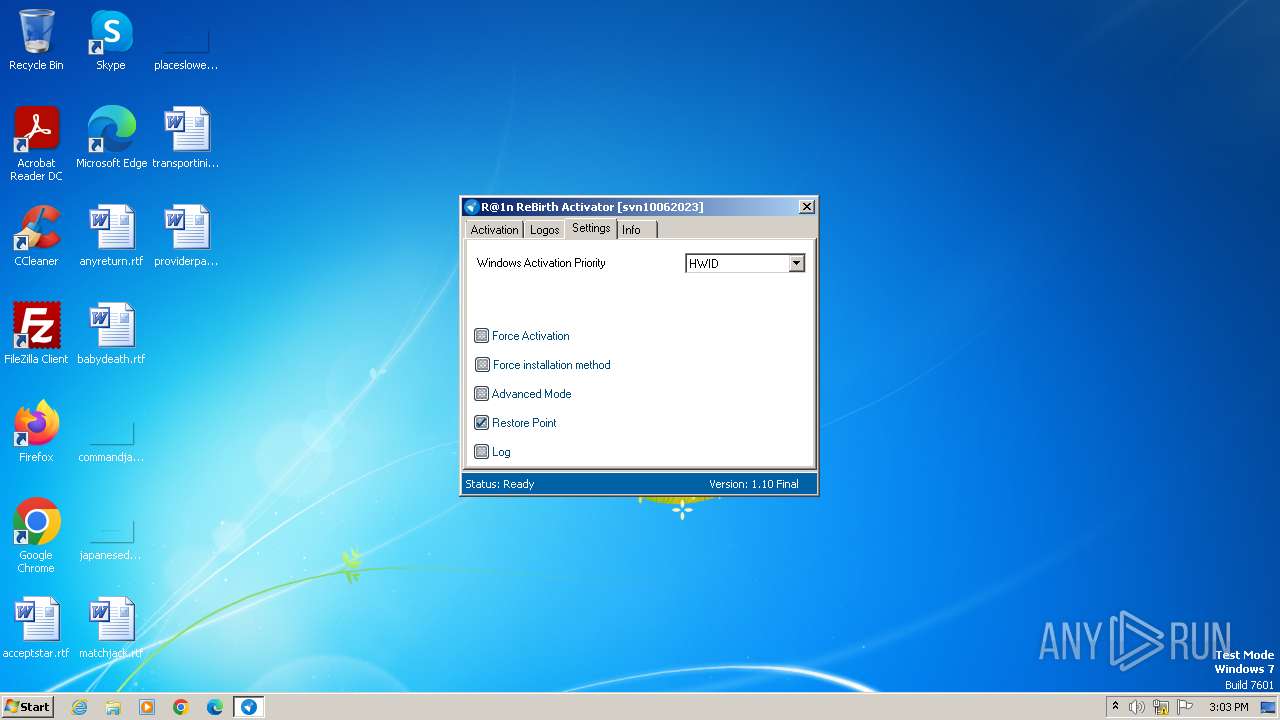
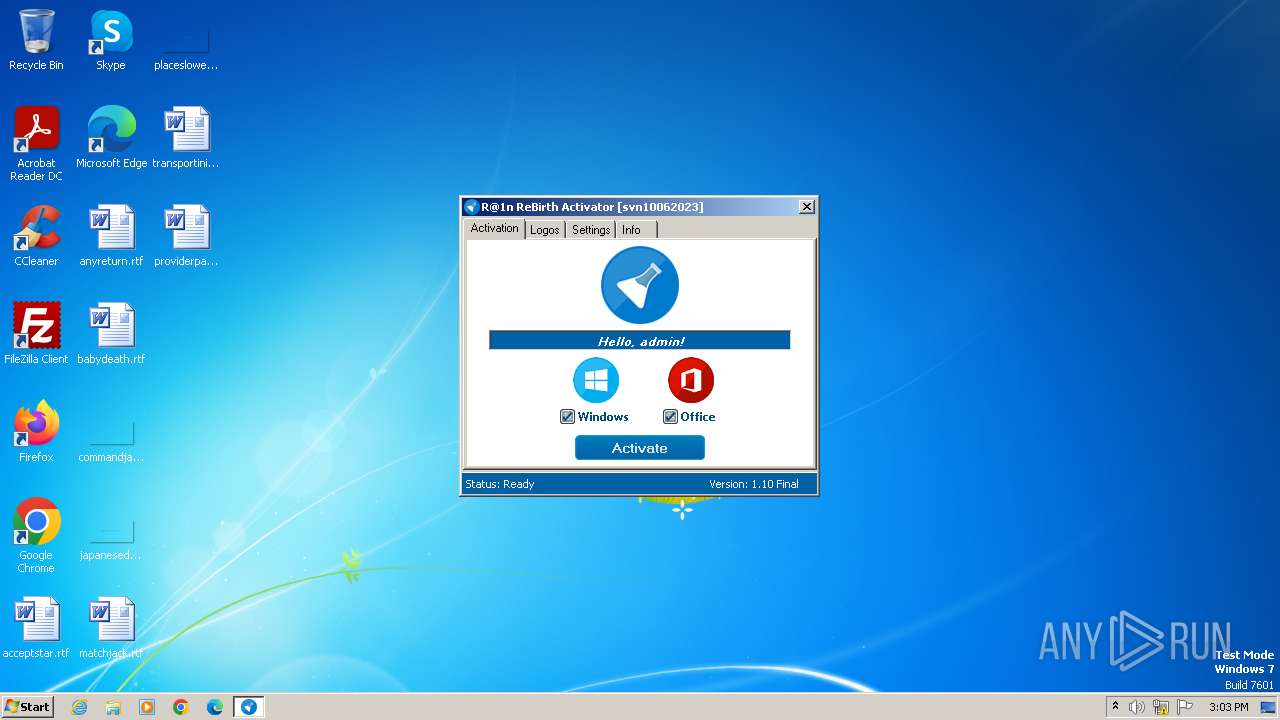
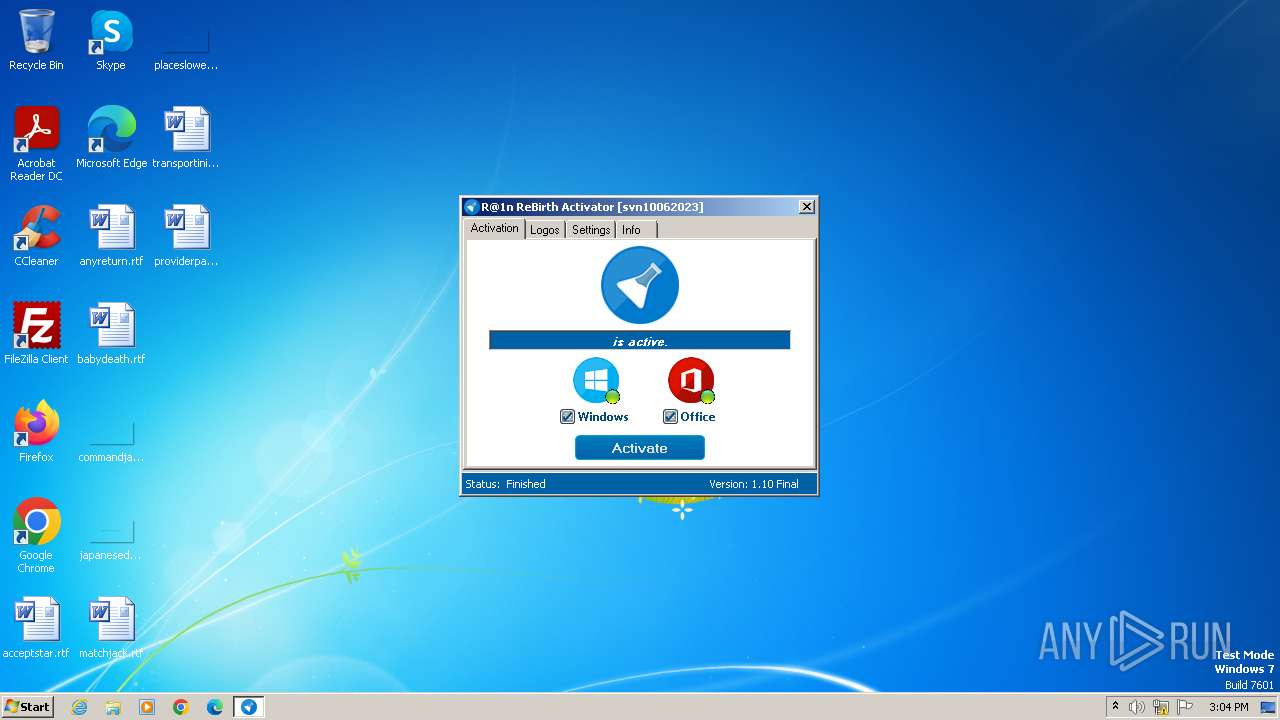
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 15:03:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, MZ for MS-DOS |
| MD5: | 12FA08CBC727A7C704692631D6024B0C |
| SHA1: | 1DF1E27DBAB8213F0154E17020CA8C8F78CC22B2 |
| SHA256: | 28A16A5B6D61075A13F66F049B63C87A5C44B5E88927C0A29ED09E95717FFB62 |
| SSDEEP: | 49152:MgPzOSVeX0QMbBS+NOZAA4hotIab5LF6wQ:MgLOSmKw/4T9 |
MALICIOUS
Uses Task Scheduler to autorun other applications
- Activator.exe (PID: 2904)
Creates a writable file in the system directory
- Activator.exe (PID: 2904)
Drops the executable file immediately after the start
- Activator.exe (PID: 2904)
SUSPICIOUS
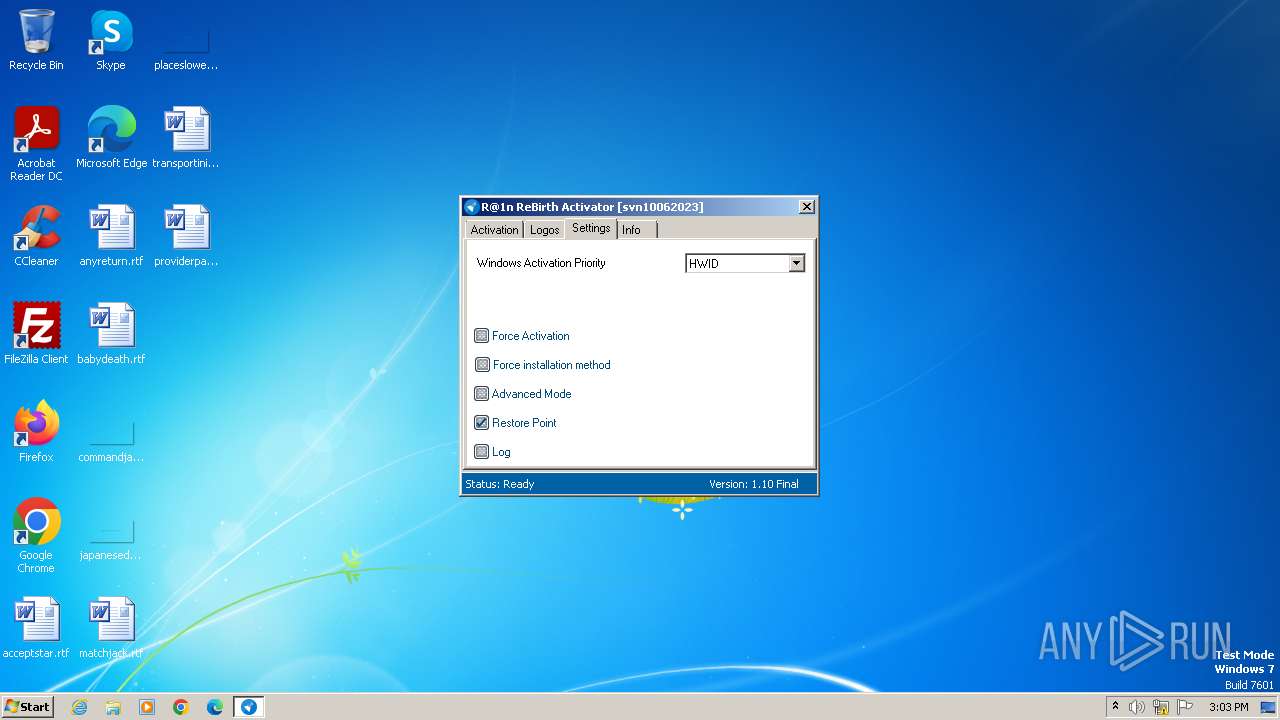
Reads the Internet Settings
- Activator.exe (PID: 2904)
Executes as Windows Service
- VSSVC.exe (PID: 3652)
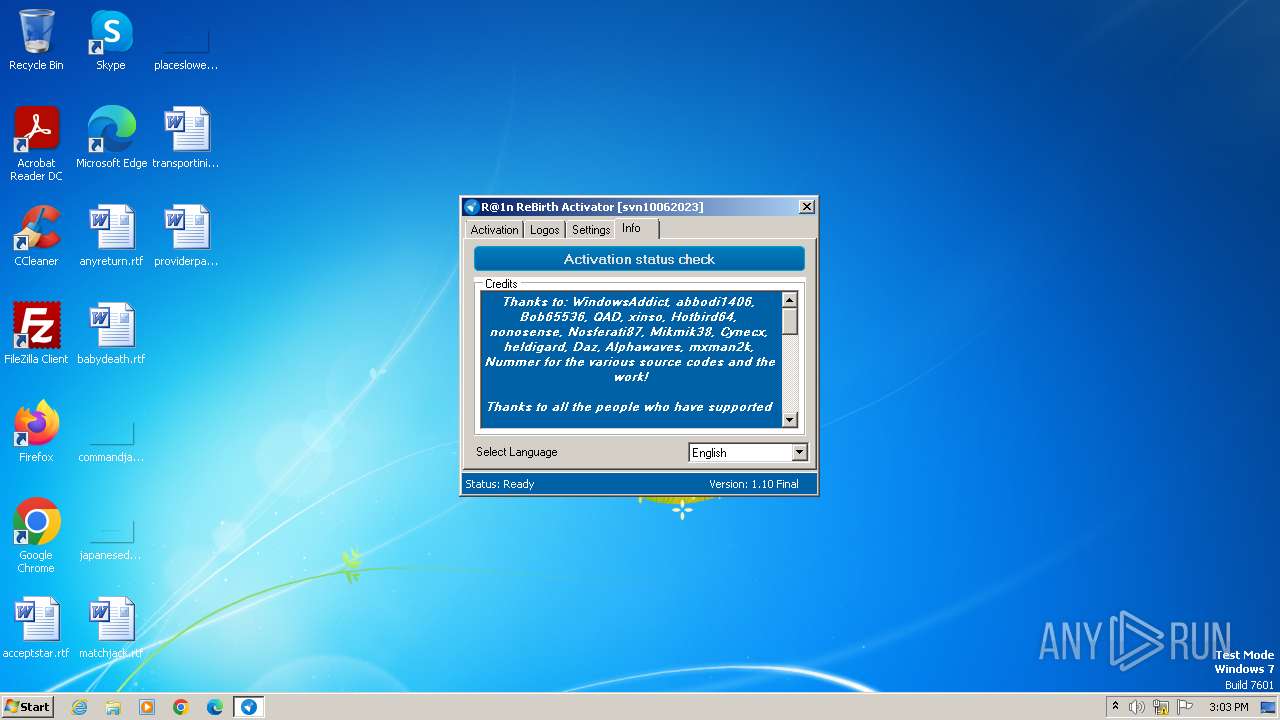
Searches for installed software
- dllhost.exe (PID: 3380)
INFO
Checks supported languages
- Activator.exe (PID: 2904)
- wmpnscfg.exe (PID: 2432)
Reads the computer name
- Activator.exe (PID: 2904)
- wmpnscfg.exe (PID: 2432)
Reads the machine GUID from the registry
- Activator.exe (PID: 2904)
- wmpnscfg.exe (PID: 2432)
Reads Microsoft Office registry keys
- Activator.exe (PID: 2904)
Reads Environment values
- Activator.exe (PID: 2904)
Manual execution by a user
- wmpnscfg.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 19:58:13+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.10.3.0 |
| ProductVersionNumber: | 1.10.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
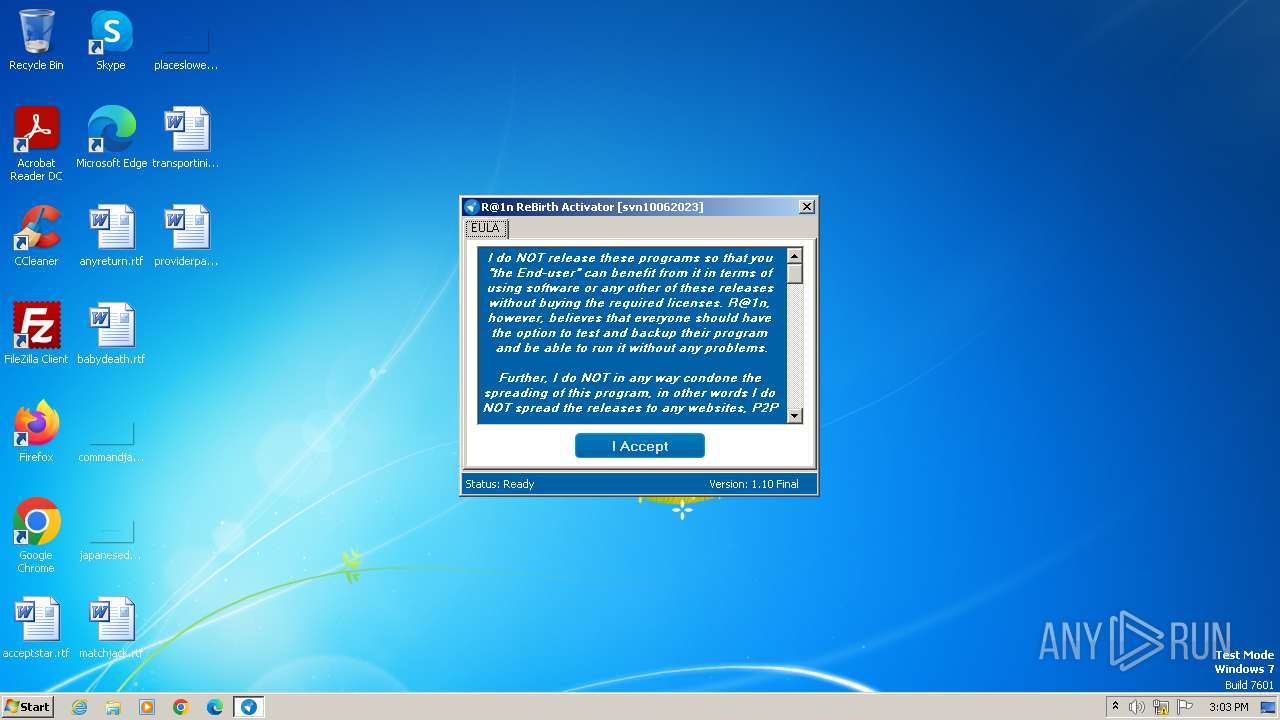
| FileDescription: | R@1n Activator |
| FileVersion: | 1.10.3.0 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | R@1n Activator |
| ProductVersion: | 1.10.3.0 |
| AssemblyVersion: | 1.10.3.0 |
Total processes
52
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1460 | "C:\Windows\System32\schtasks.exe" /Create /TN "\R@1n\Office 14 Word" /SC ONLOGON /TR "wmic path OfficeSoftwareProtectionProduct where (ID='2d0882e7-a4e7-423b-8ccc-70d91e0158b1') call Activate" /ru "SYSTEM" /RL "HIGHEST" | C:\Windows\System32\schtasks.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Windows\System32\schtasks.exe" /Create /TN "\R@1n\Office 14 OneNote" /SC ONLOGON /TR "wmic path OfficeSoftwareProtectionProduct where (ID='ab586f5c-5256-4632-962f-fefd8b49e6f4') call Activate" /ru "SYSTEM" /RL "HIGHEST" | C:\Windows\System32\schtasks.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\Temp\Activator.exe" | C:\Users\admin\AppData\Local\Temp\Activator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: R@1n Activator Exit code: 0 Version: 1.10.3.0 Modules
| |||||||||||||||
| 3376 | "C:\Users\admin\AppData\Local\Temp\Activator.exe" | C:\Users\admin\AppData\Local\Temp\Activator.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: R@1n Activator Exit code: 3221226540 Version: 1.10.3.0 Modules
| |||||||||||||||
| 3380 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 629
Read events
1 610
Write events
16
Delete events
3
Modification events
| (PID) Process: | (2904) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2904) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2904) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2904) Activator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 72 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008C62D6BA16B0D901C80700002C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3380) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 400000000000000034645DBC16B0D901C80700002C0A0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2904 | Activator.exe | C:\Windows\System32\SppExtComObjHook.dll | executable | |
MD5:2A2BBC30D8E715C3C29E728989498469 | SHA256:81F8FC4AEF686DBC4E2B1F6B08FBAC33BF877610C268564E9ECFBAE1425D5E5C | |||
| 3380 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{601453a2-cc86-4a93-b283-75ced3ca164f}_OnDiskSnapshotProp | binary | |
MD5:8E6F00556E69B8C23EED4B7AD37E7FDC | SHA256:A2500988670F414508D0C19BE00EC19F83DBFCC24F833F1F506D8C3699CC6FFC | |||
| 3380 | dllhost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:8E6F00556E69B8C23EED4B7AD37E7FDC | SHA256:A2500988670F414508D0C19BE00EC19F83DBFCC24F833F1F506D8C3699CC6FFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |