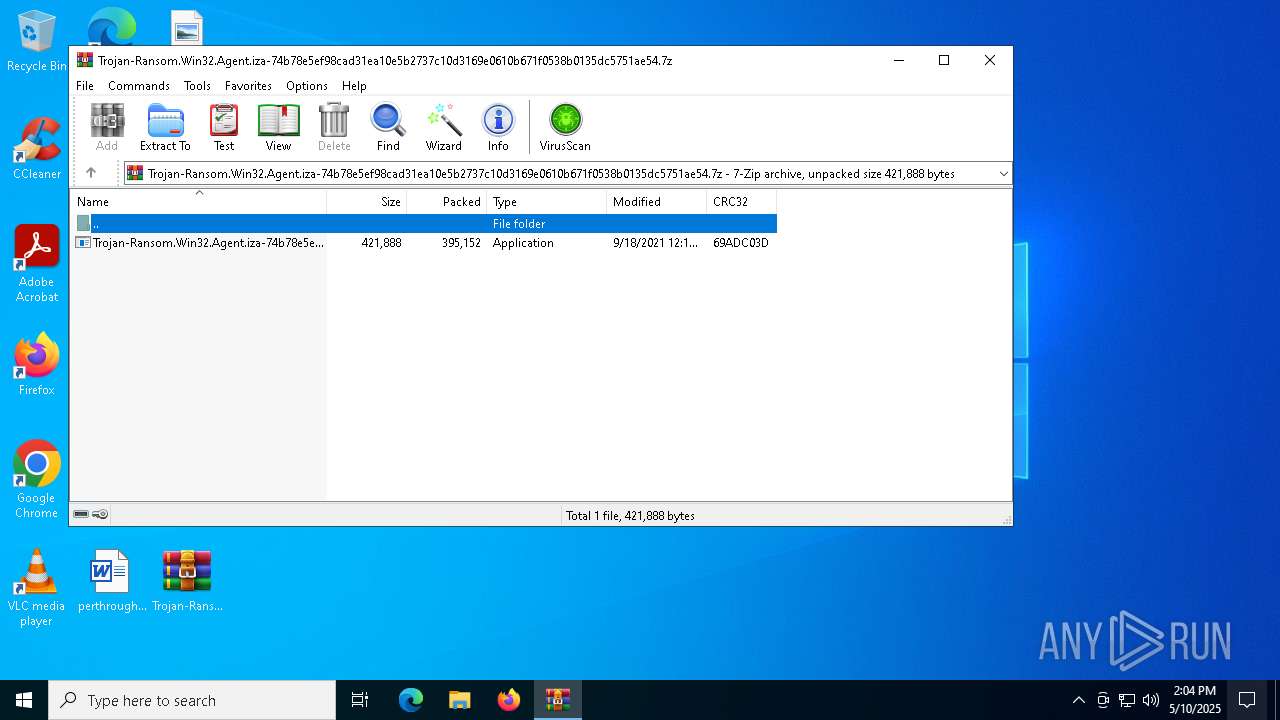
| File name: | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.7z |
| Full analysis: | https://app.any.run/tasks/f36fa118-a547-4a8b-b3ba-e03420cbfd2e |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 14:04:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 0009ACC82D4F30814112C143C3735383 |
| SHA1: | BF87E562DEA7AA793FBD362269C6C75F3EA0E51E |
| SHA256: | 289A205089199C09188D44527BDF925EDC59E074DC921C4C0C03F4A9C4326080 |
| SSDEEP: | 12288:CIxBqiSstFUZlDug+BiSZlYJ24j+UlT2dm/jAJMLFBTRS1:CIxBqlstFUZlDug+BiAYJhj+UlT2dsjg |
MALICIOUS
Changes the autorun value in the registry
- Isass.exe (PID: 5936)
SUSPICIOUS
Application launched itself
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
- Isass.exe (PID: 7260)
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
Starts CMD.EXE for commands execution
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
Potential Corporate Privacy Violation
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
Starts itself from another location
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
Detected use of alternative data streams (AltDS)
- Isass.exe (PID: 5936)
There is functionality for taking screenshot (YARA)
- Isass.exe (PID: 7260)
Connects to unusual port
- Isass.exe (PID: 5936)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7392)
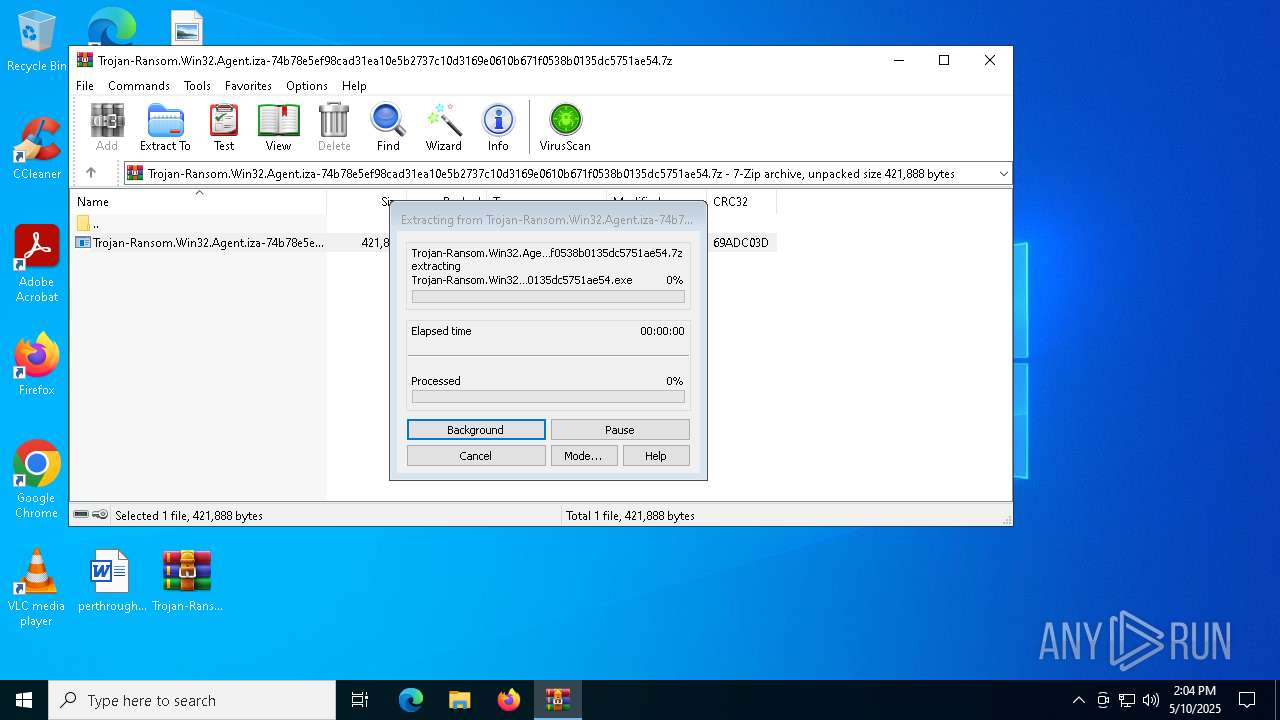
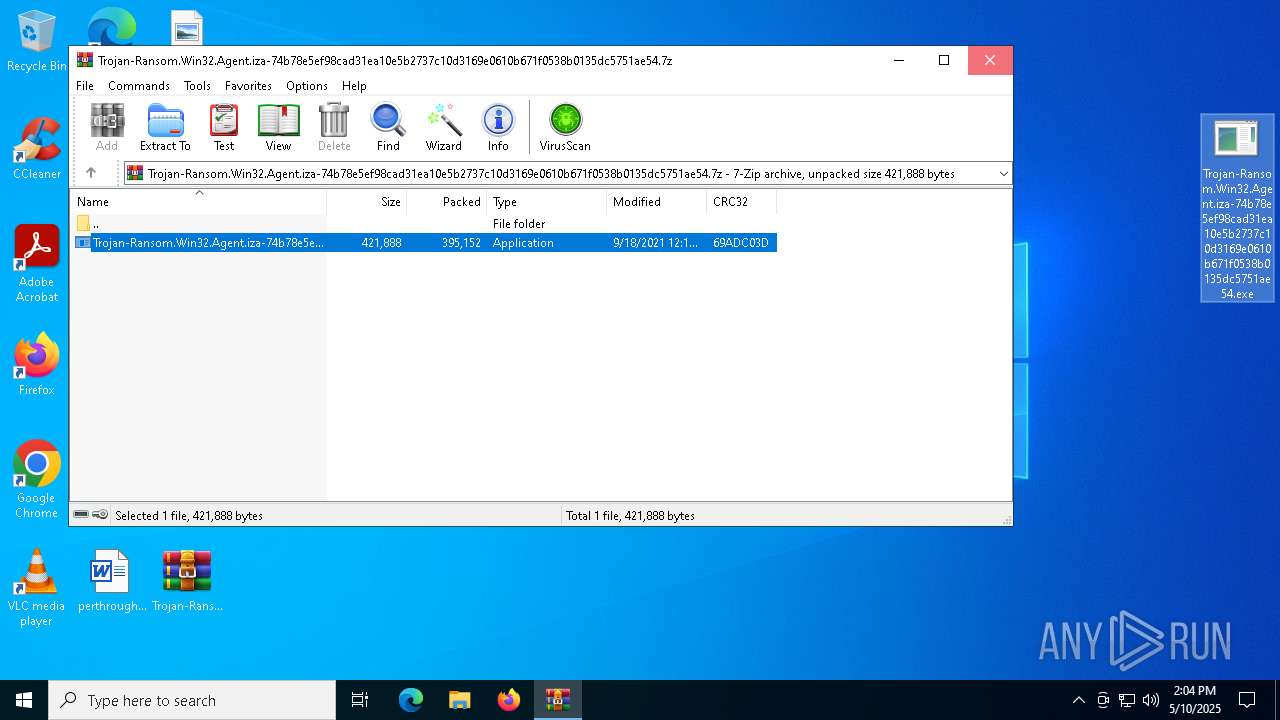
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7392)
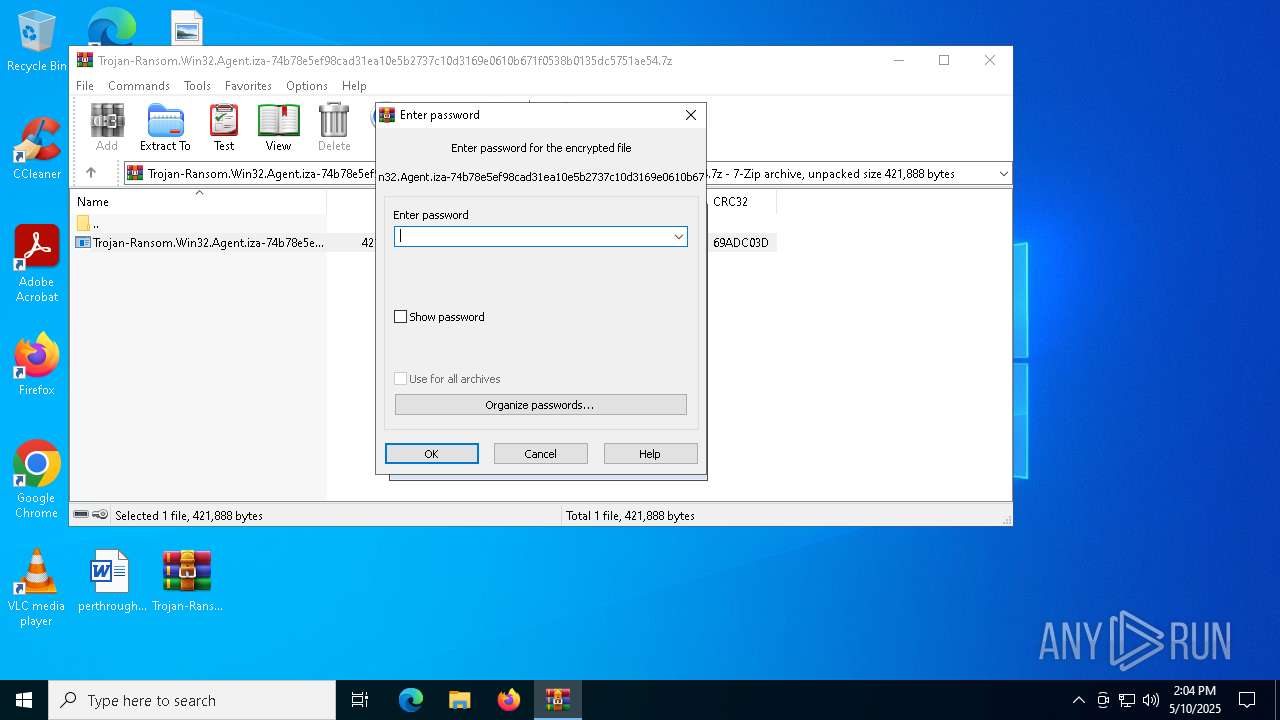
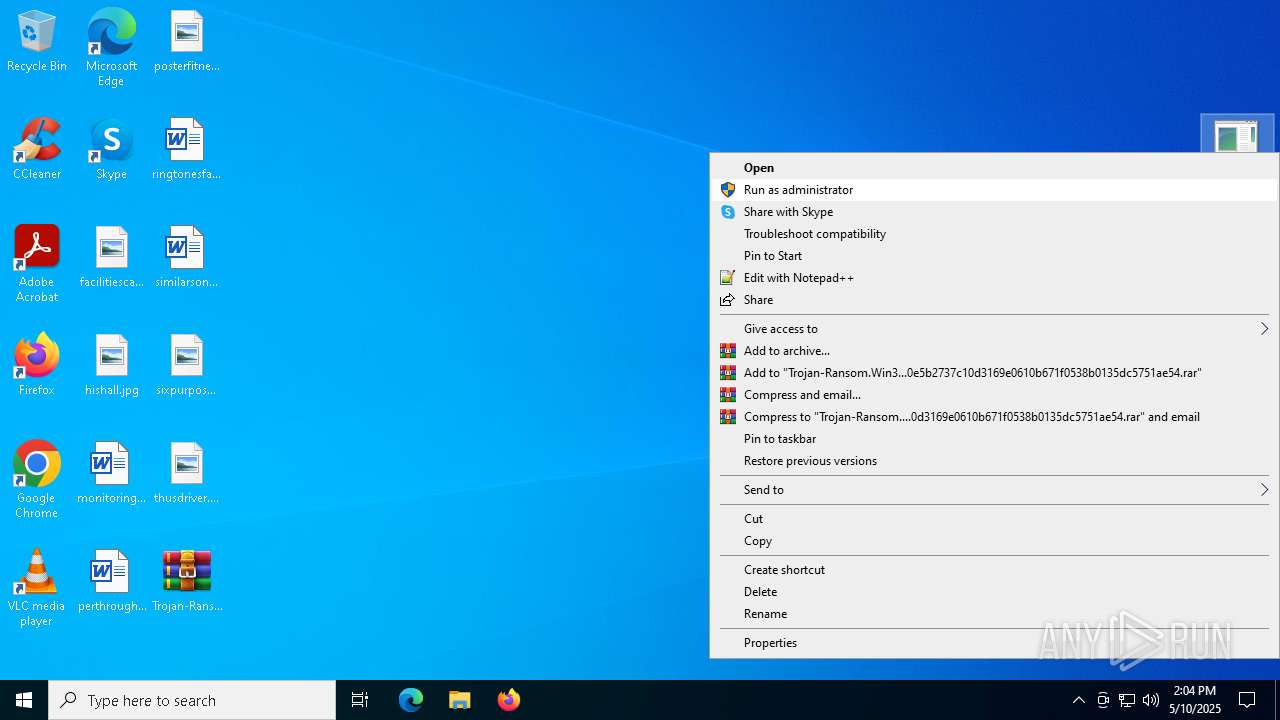
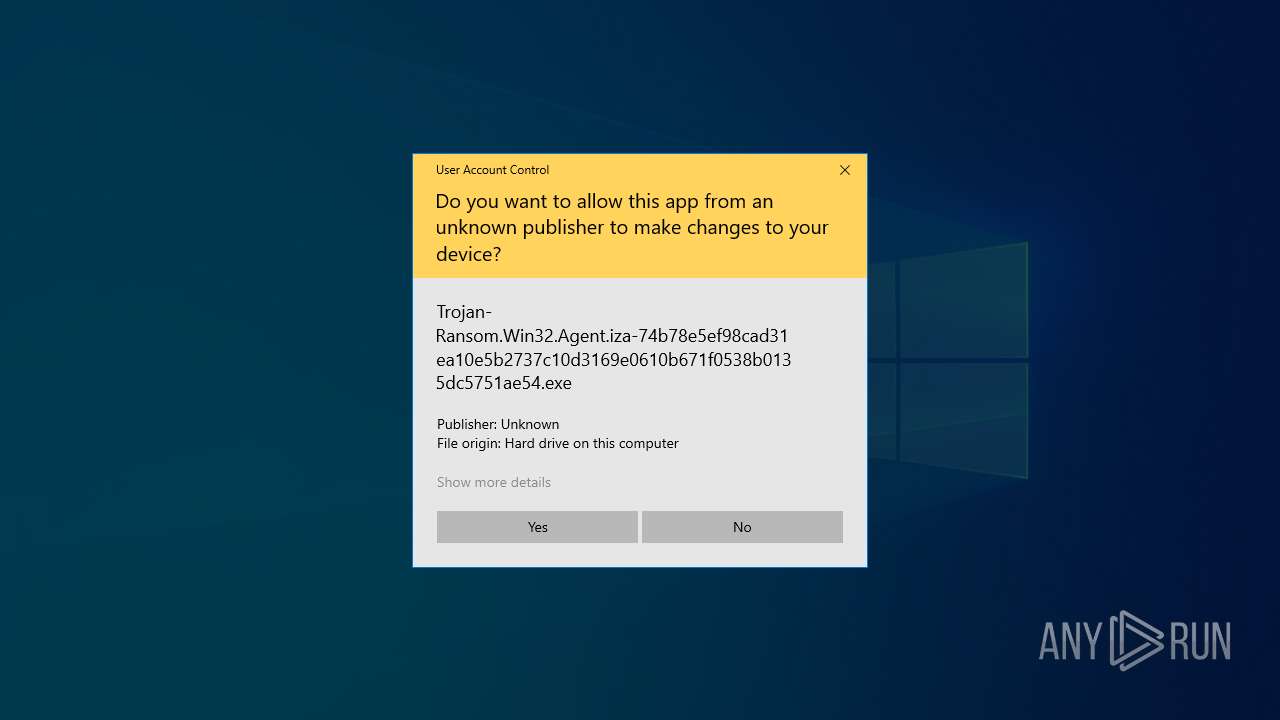
Manual execution by a user
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
Reads mouse settings
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 7260)
- Isass.exe (PID: 5936)
Checks supported languages
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 7260)
- Isass.exe (PID: 5936)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
Create files in a temporary directory
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8156)
Reads the computer name
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
Checks proxy server information
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe (PID: 8180)
- Isass.exe (PID: 5936)
The process uses AutoIt
- Isass.exe (PID: 7260)
UPX packer has been detected
- Isass.exe (PID: 7260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:09:18 12:11:10+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe |
Total processes
138
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5936 | C:\Users\admin\AppData\Roaming\Isass.exe /AutoIt3ExecuteScript "C:\Users\admin\AppData\Local\Temp\delph1.dat" | C:\Users\admin\AppData\Roaming\Isass.exe | Isass.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7208 | C:\WINDOWS\system32\cmd.exe /C echo. > "C:\Users\admin\AppData\Roaming\Isass.exe":Zone.Identifier | C:\Windows\SysWOW64\cmd.exe | — | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7260 | C:\Users\admin\AppData\Roaming\Isass.exe | C:\Users\admin\AppData\Roaming\Isass.exe | — | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7392 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7528 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7560 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8156 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8180 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe /AutoIt3ExecuteScript "C:\Users\admin\AppData\Local\Temp\delph1.dat" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 603
Read events
2 577
Write events
26
Delete events
0
Modification events
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.7z | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
2
Suspicious files
4
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Roaming\Isass.exe | — | |
MD5:— | SHA256:— | |||
| 7392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7392.17305\Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | executable | |
MD5:0E2B58CDD2C89FF96DA664D3EA3F2C9B | SHA256:74B78E5EF98CAD31EA10E5B2737C10D3169E0610B671F0538B0135DC5751AE54 | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\delph1.bin | binary | |
MD5:07F22BD673671E43F7C14003EC840246 | SHA256:E35FF9970ACF2A5BDAFDA03676164AF6F86AE1D987F198E5D4776583CF92116A | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\autD88F.tmp | binary | |
MD5:07F22BD673671E43F7C14003EC840246 | SHA256:E35FF9970ACF2A5BDAFDA03676164AF6F86AE1D987F198E5D4776583CF92116A | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\pd4ta.bin | binary | |
MD5:F07FD78340FE8DC4D94120BAAC82E126 | SHA256:34E2B9B4CB23C157C178AA780C6BB4D4772D7FA768E201CE45316DBC6B88EBF1 | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\pd4ta.dat | text | |
MD5:460E8A8EF9ABEA0AE3A5BA47CB76031A | SHA256:BE2187915B830017CD0DDE177B18F5D029F37981C544447EB56C966A9E42C3F0 | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\autD8A0.tmp | binary | |
MD5:F07FD78340FE8DC4D94120BAAC82E126 | SHA256:34E2B9B4CB23C157C178AA780C6BB4D4772D7FA768E201CE45316DBC6B88EBF1 | |||
| 8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\PZXNCWC0.htm | html | |
MD5:8F0A5178A0E76C976A9A0080C8FDE134 | SHA256:80798350440E98402F628CA0D22C1C01E8D6D8074FDC0BF98930F5E934473D54 | |||
| 8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\9X1T46V8.htm | html | |
MD5:D4B691CD9D99117B2EA34586D3E7EEB8 | SHA256:2178EEDD5723A6AC22E94EC59BDCD99229C87F3623753F5E199678242F0E90DE | |||
| 8156 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | C:\Users\admin\AppData\Local\Temp\delph1.dat | a3x | |
MD5:04979DB956D28F674929FCB76CAD8D00 | SHA256:12587BA985F95D58ACD65039709A5820B1608B33866D023370AFA9B46DAED6E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
15
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | GET | 301 | 172.217.16.206:80 | http://google.com/ | unknown | — | — | whitelisted |
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | GET | 200 | 142.250.185.100:80 | http://www.google.com/ | unknown | — | — | whitelisted |
5936 | Isass.exe | GET | 301 | 172.217.16.206:80 | http://google.com/ | unknown | — | — | whitelisted |
5936 | Isass.exe | GET | 200 | 142.250.185.100:80 | http://www.google.com/ | unknown | — | — | whitelisted |
5156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | 172.217.16.206:80 | google.com | GOOGLE | US | whitelisted |
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | 142.250.185.100:80 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
8180 | Trojan-Ransom.Win32.Agent.iza-74b78e5ef98cad31ea10e5b2737c10d3169e0610b671f0538b0135dc5751ae54.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
5936 | Isass.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
5936 | Isass.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |