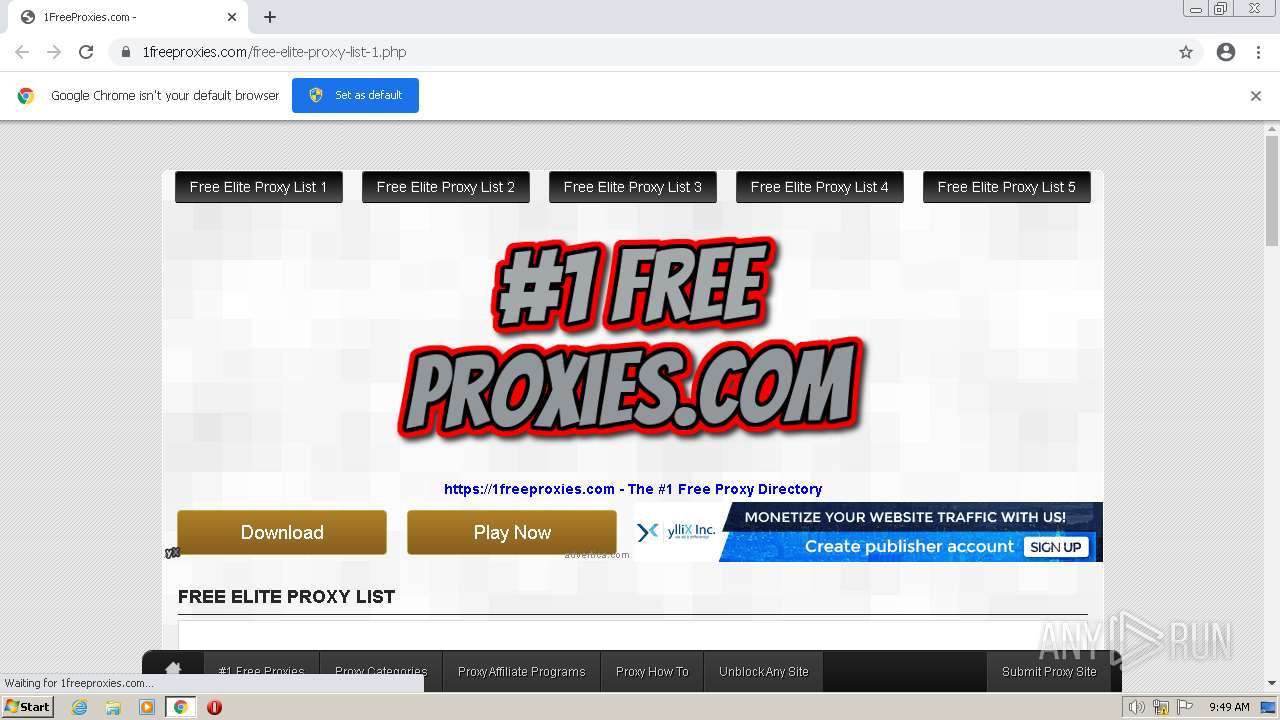
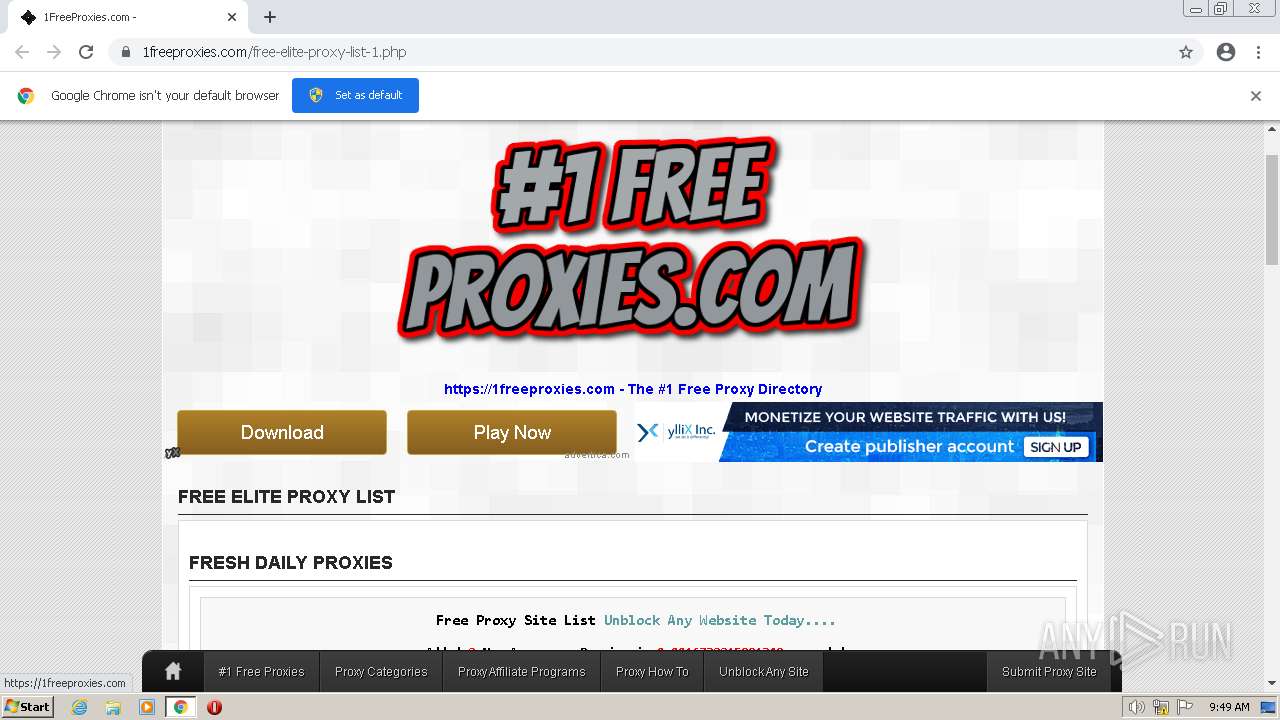
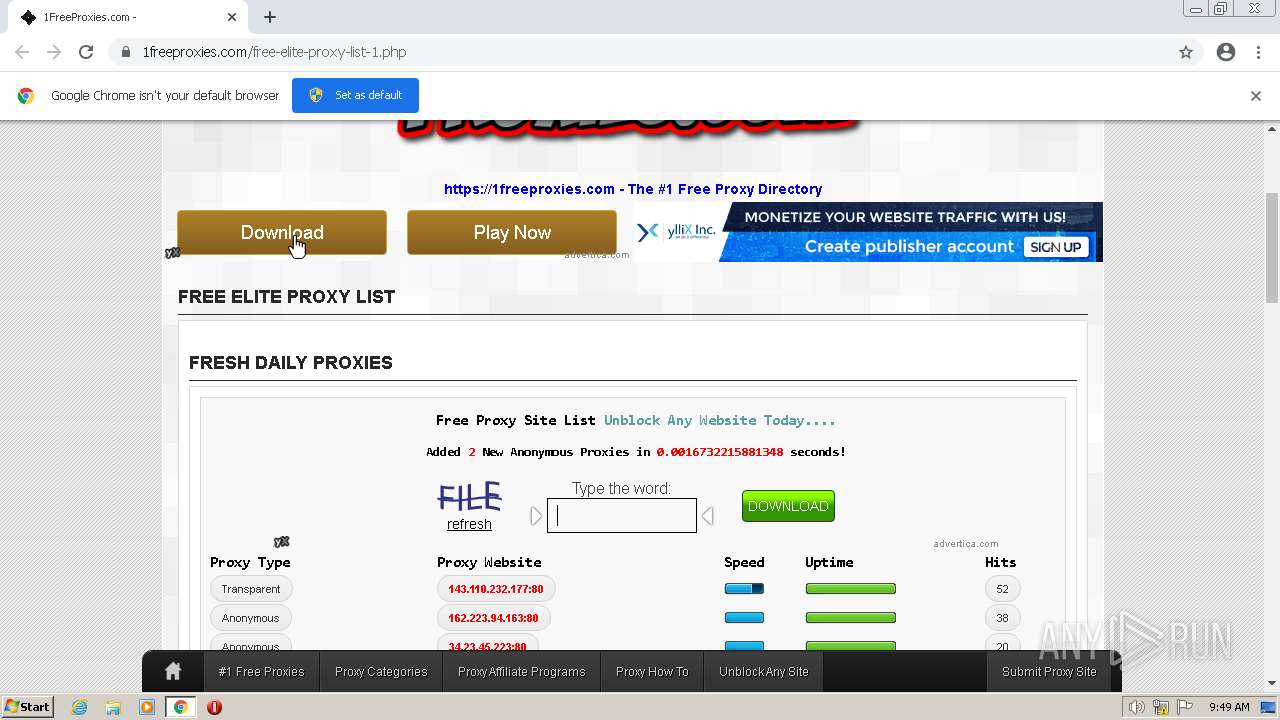
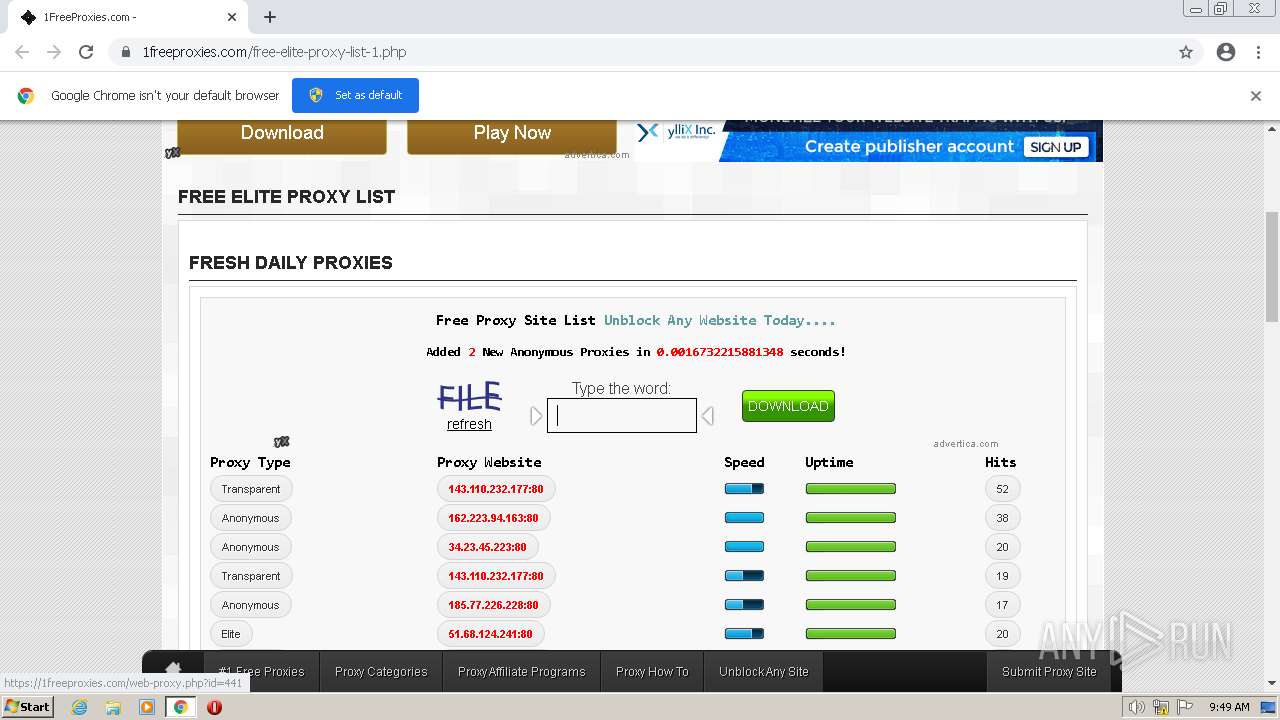
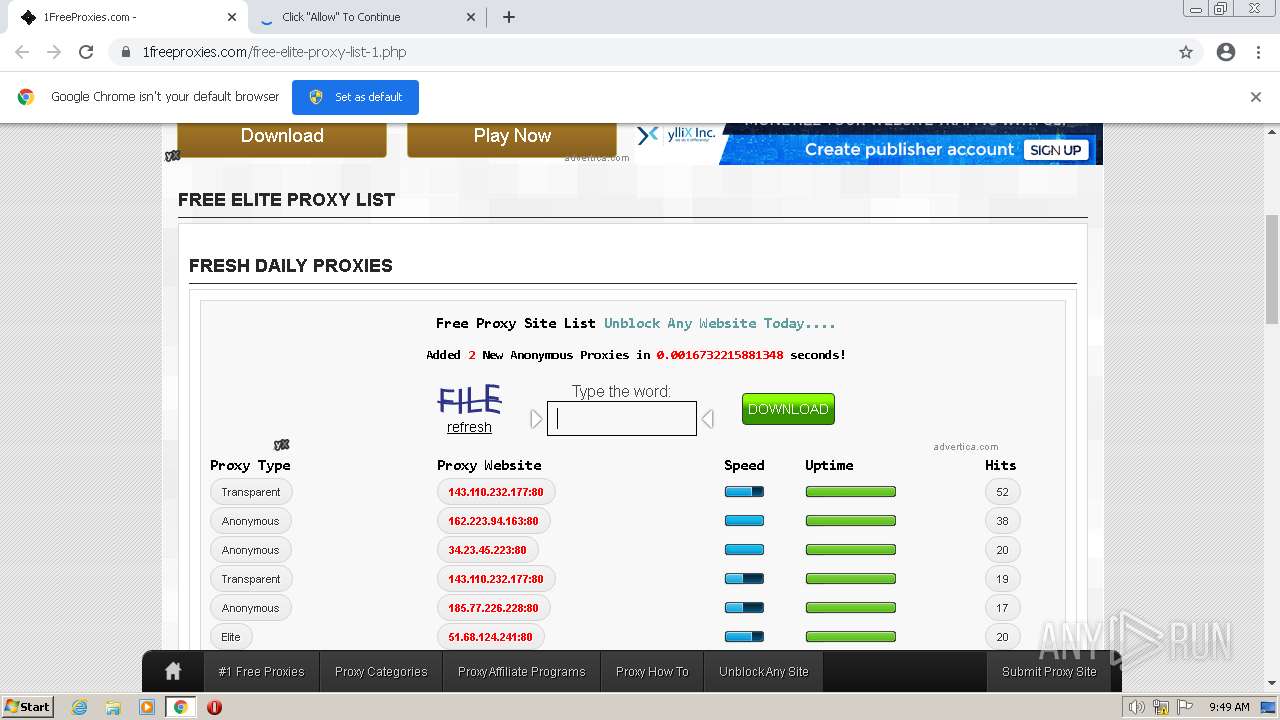
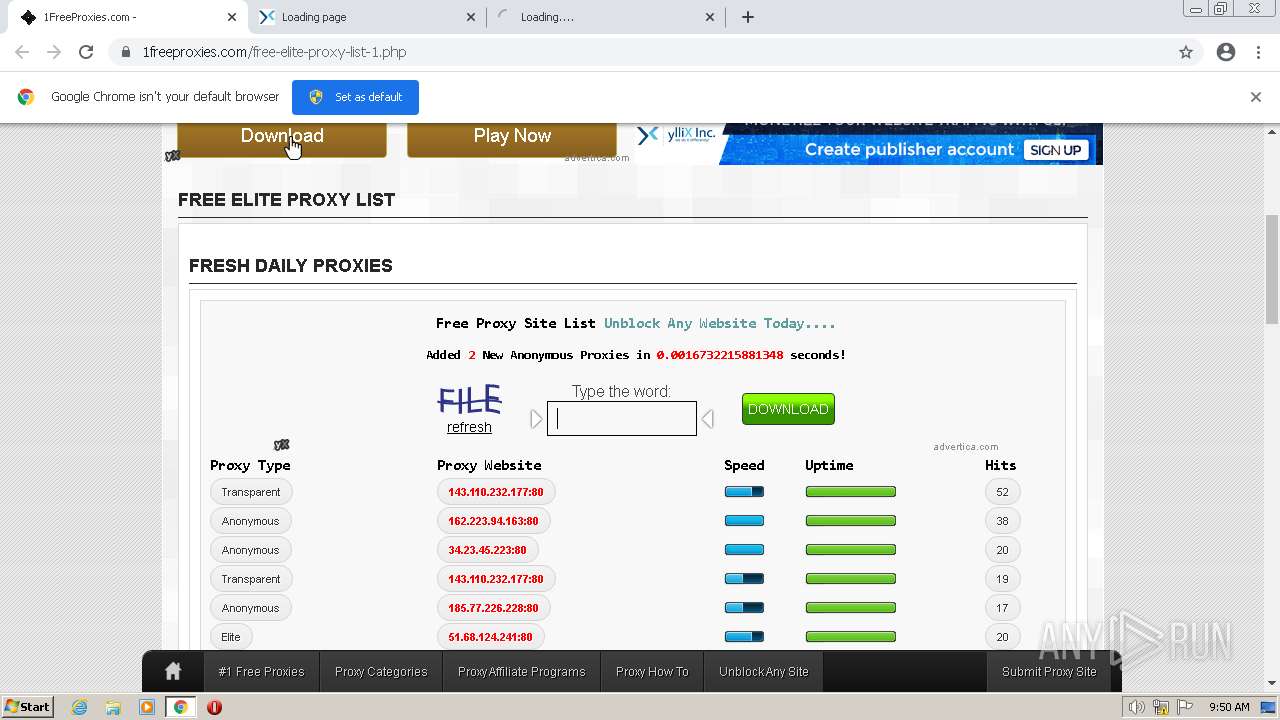
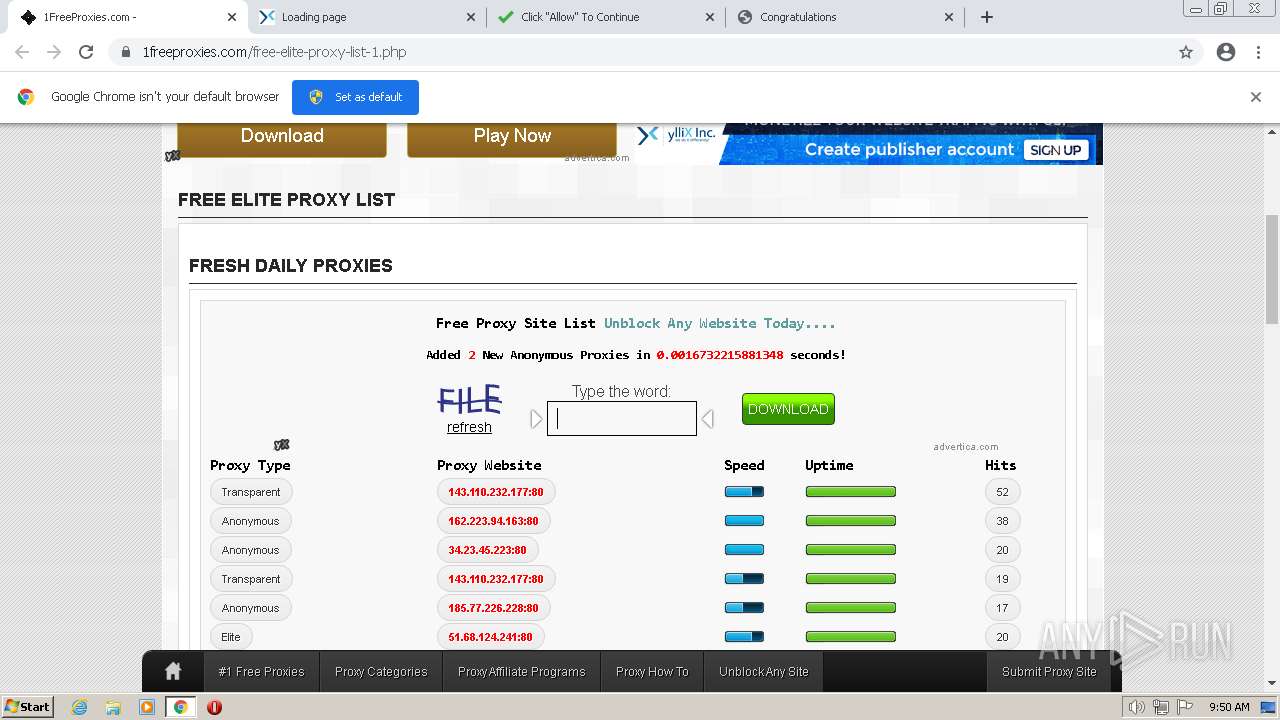
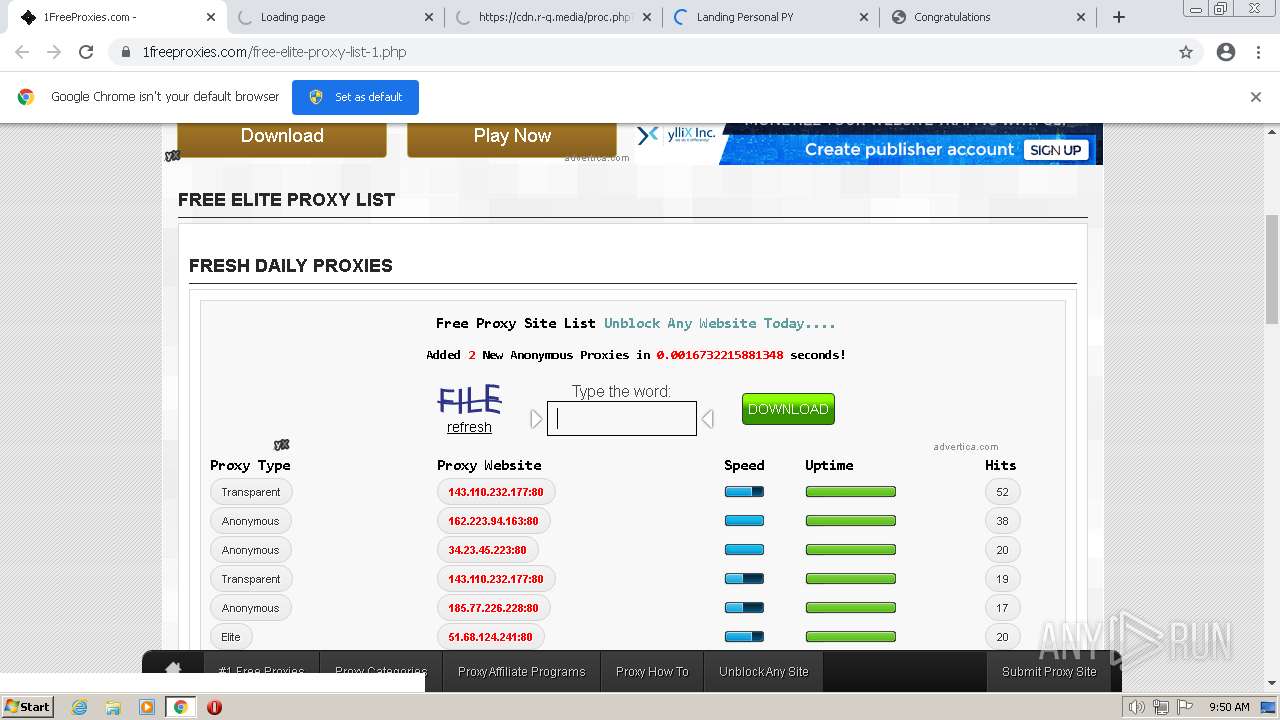
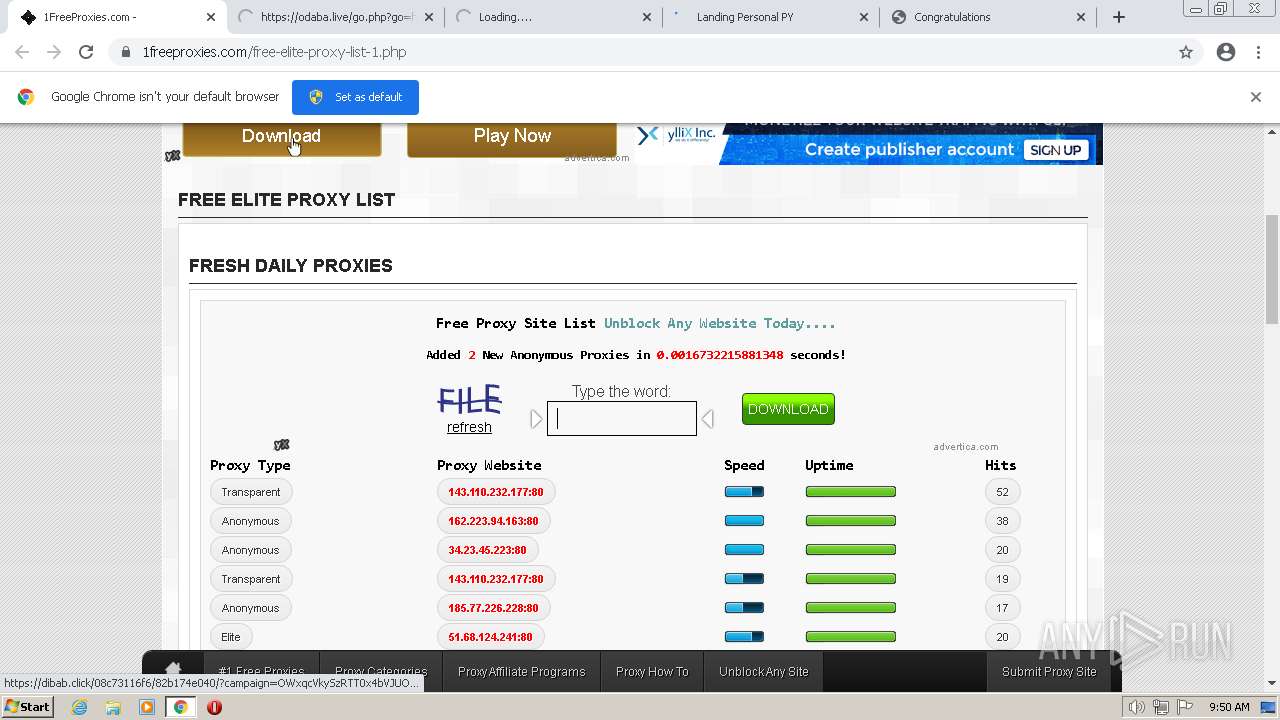
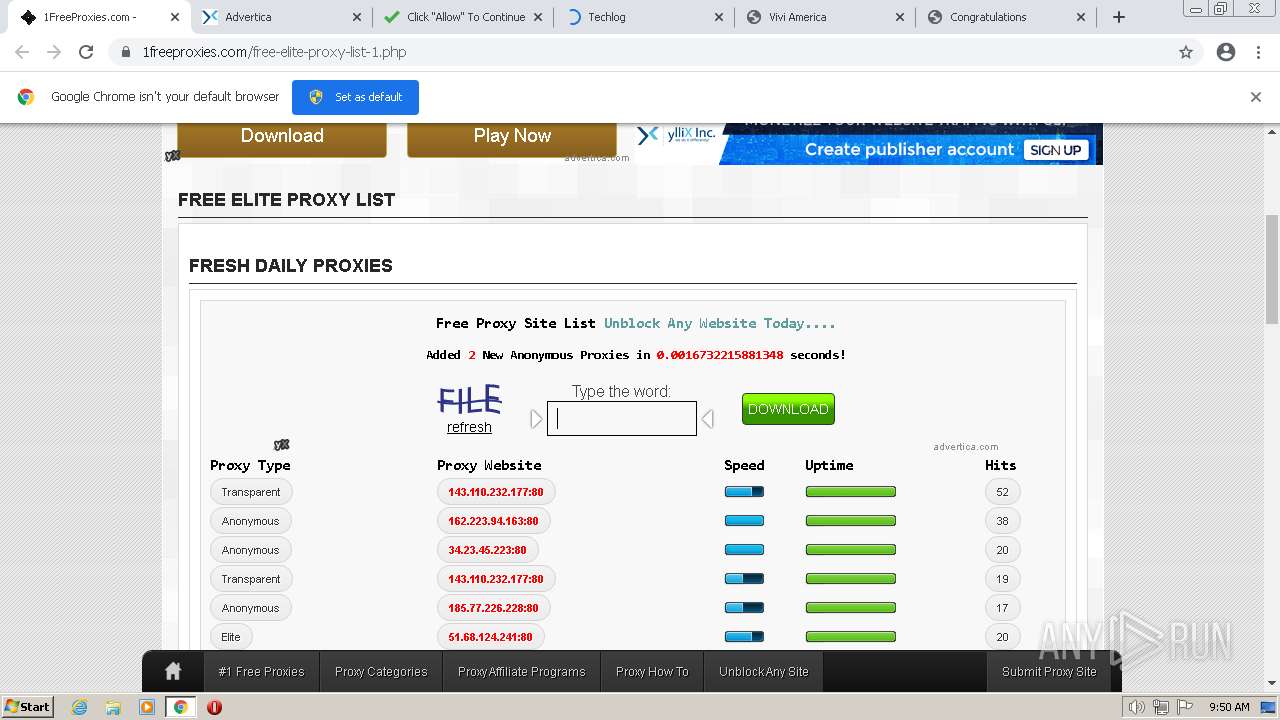
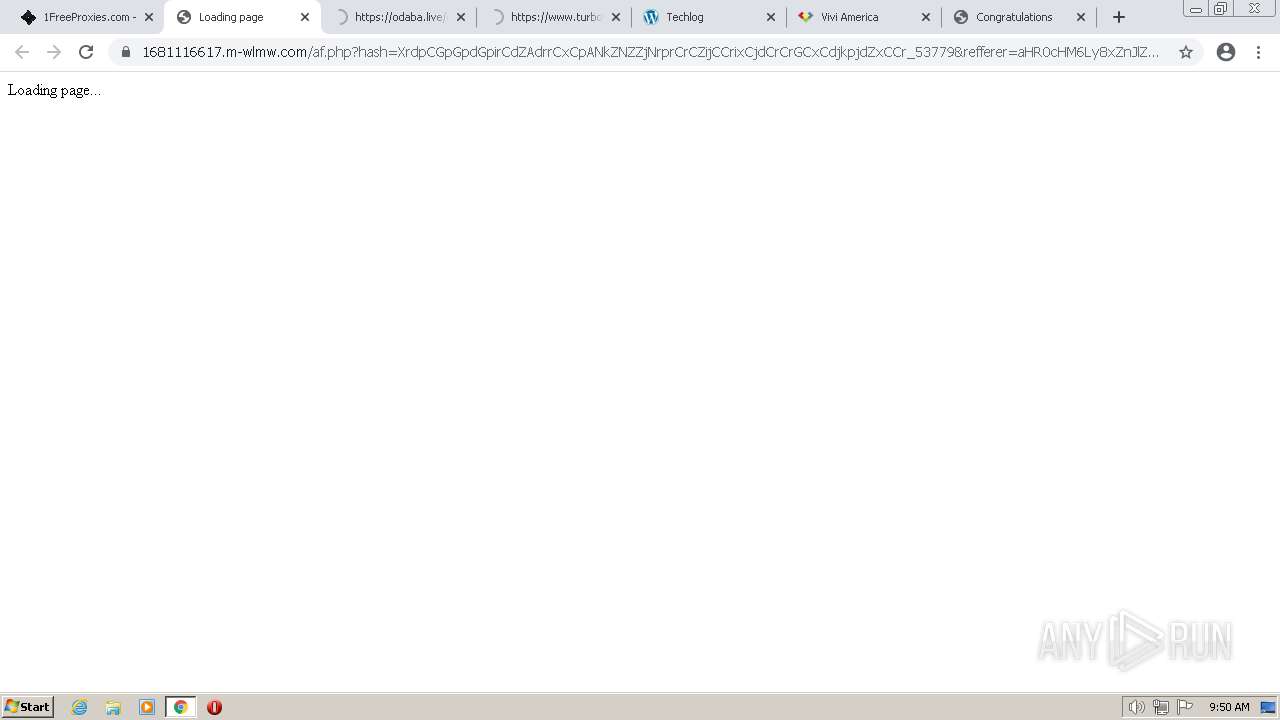
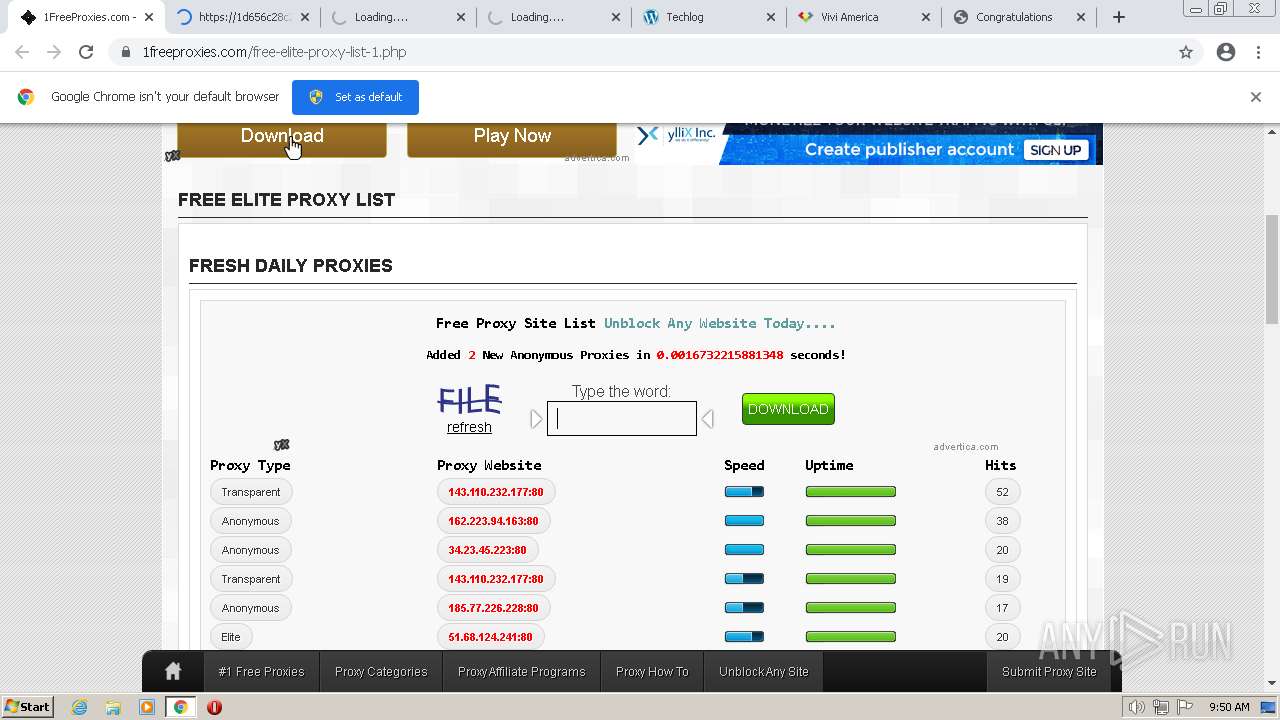
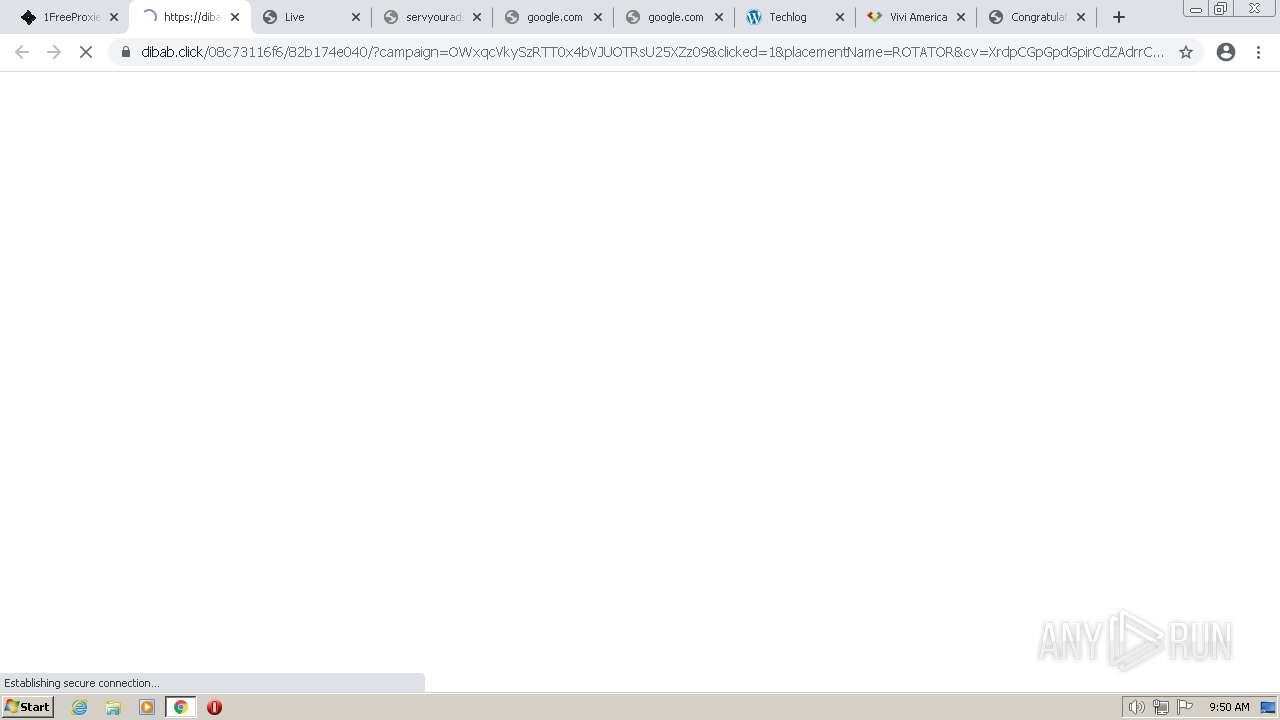
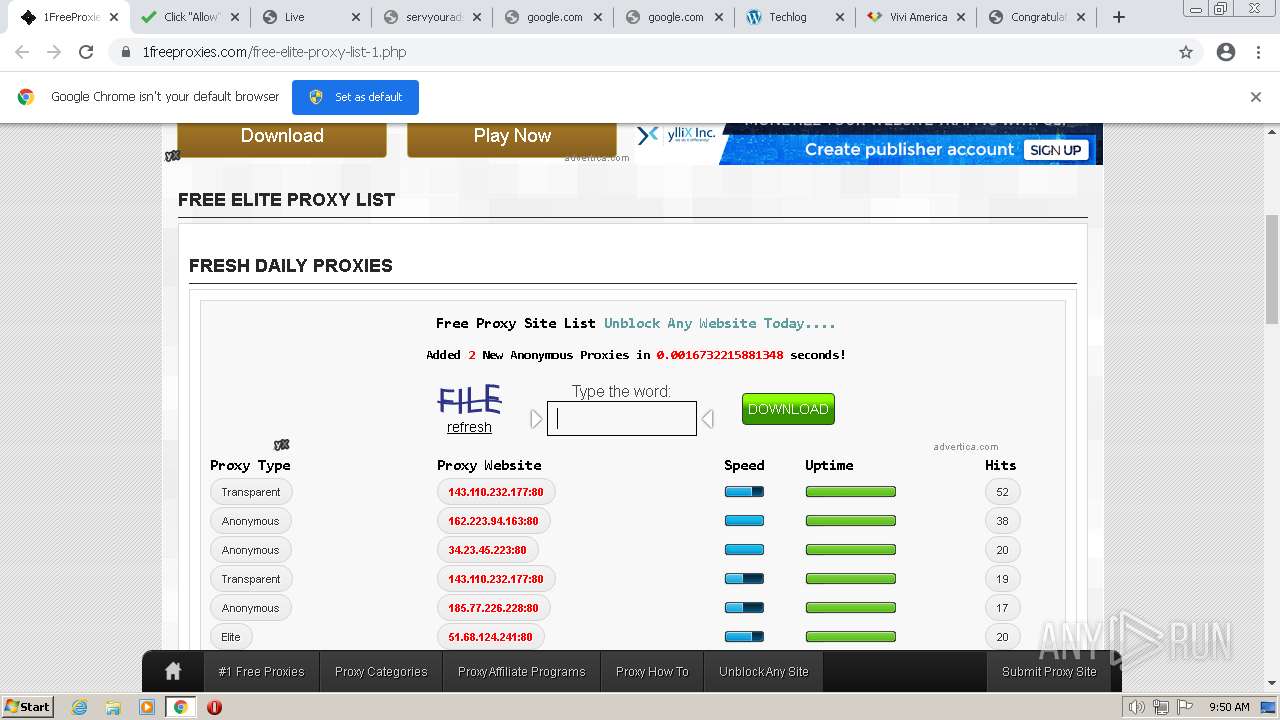
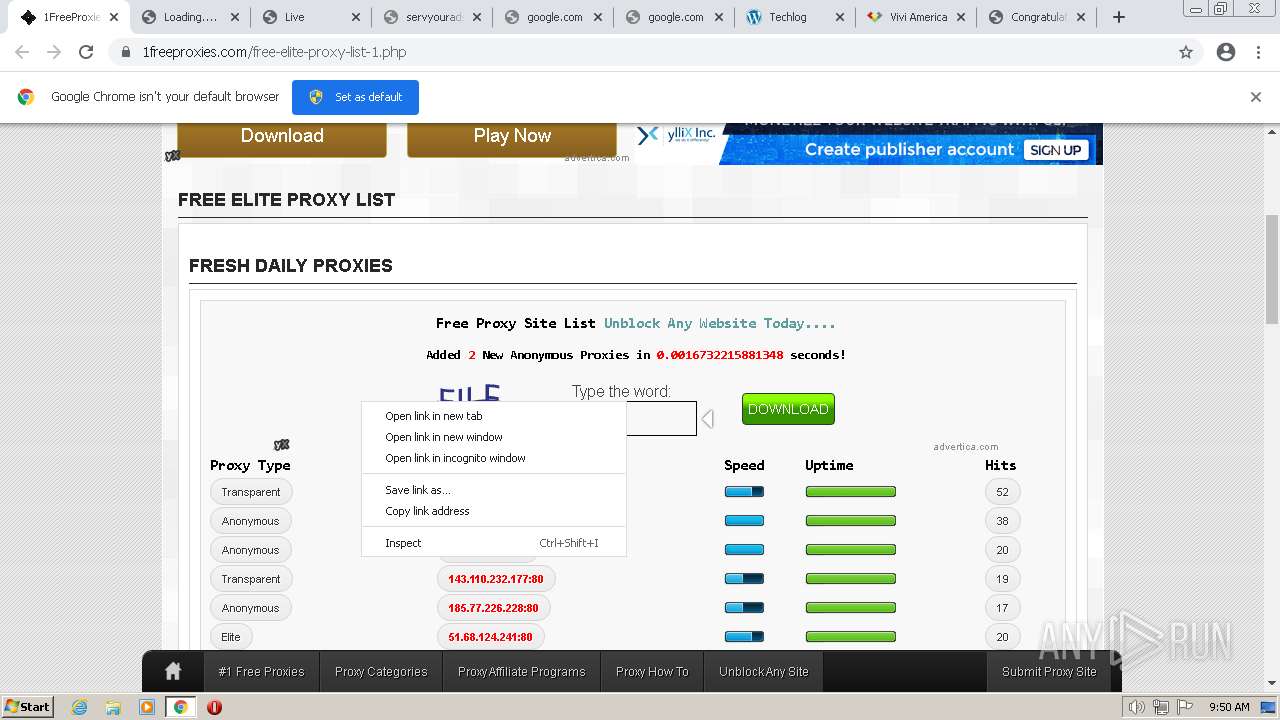
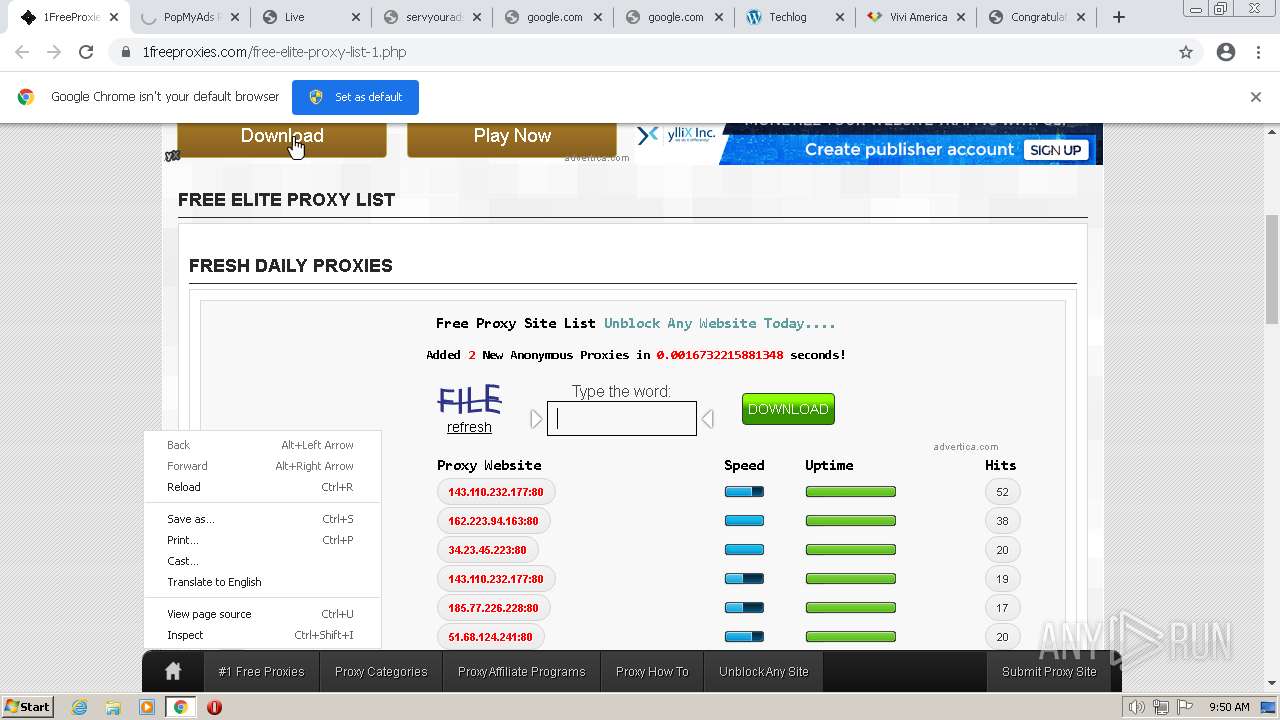
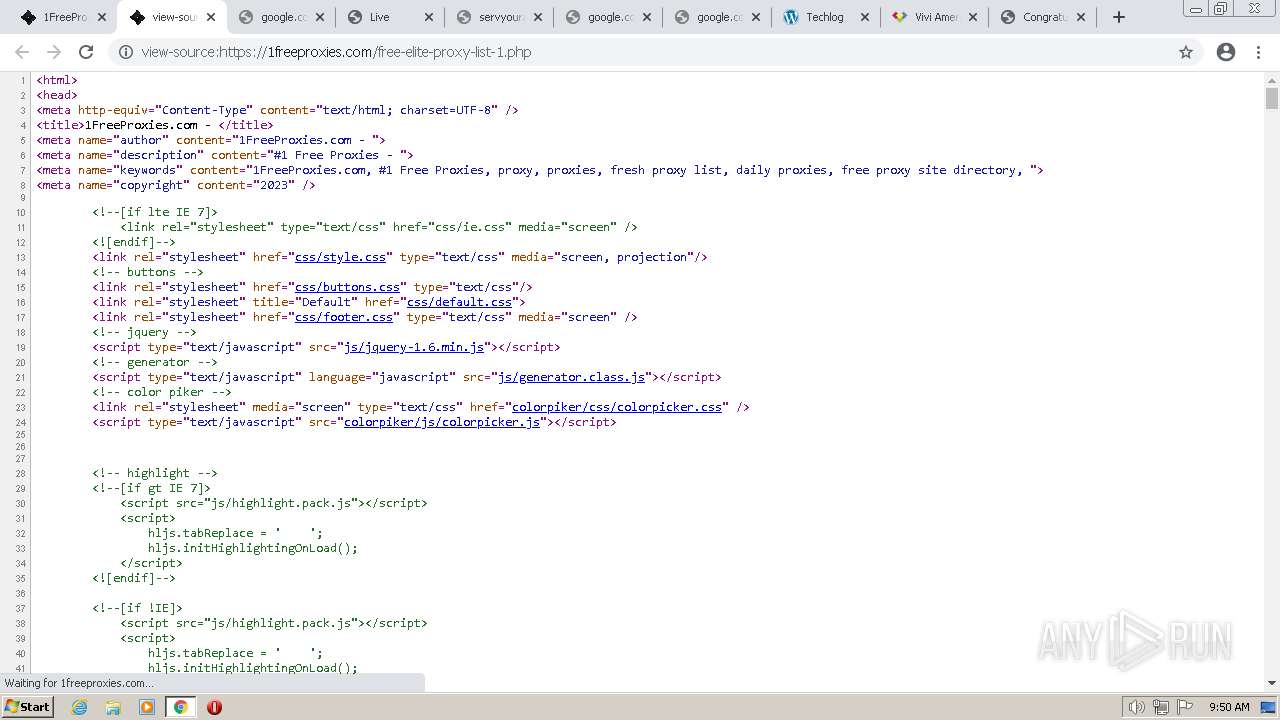
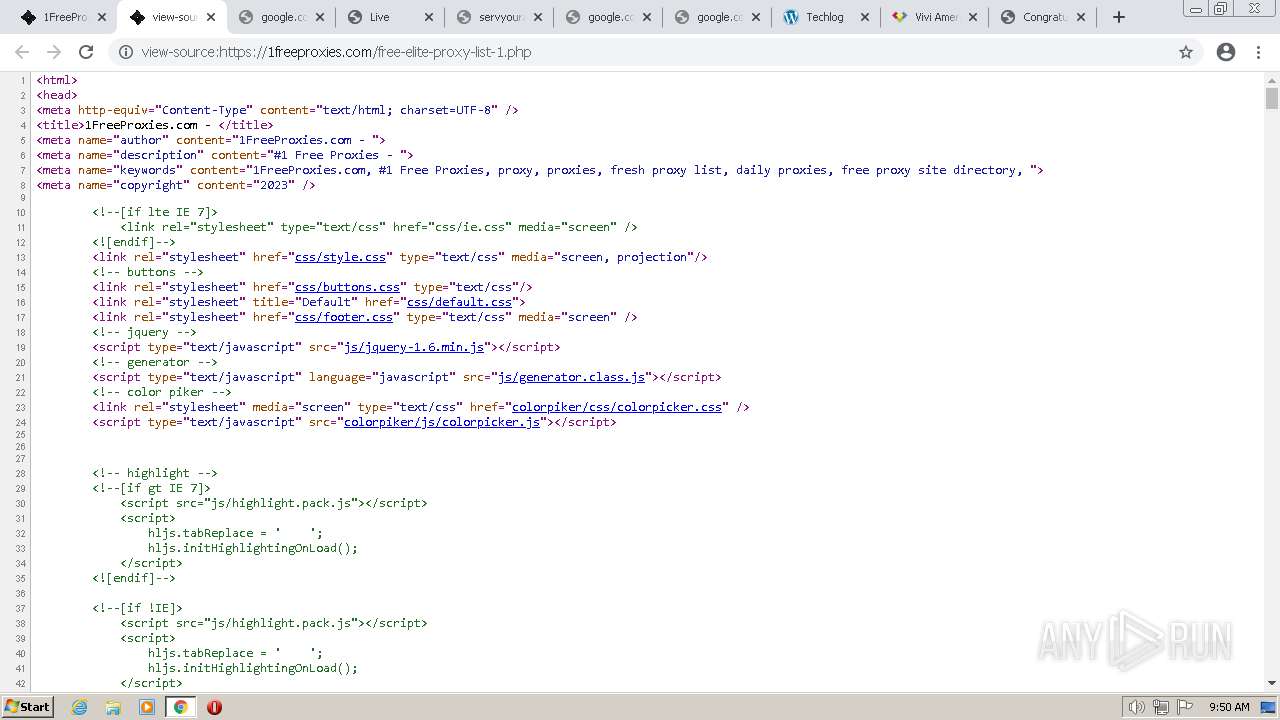
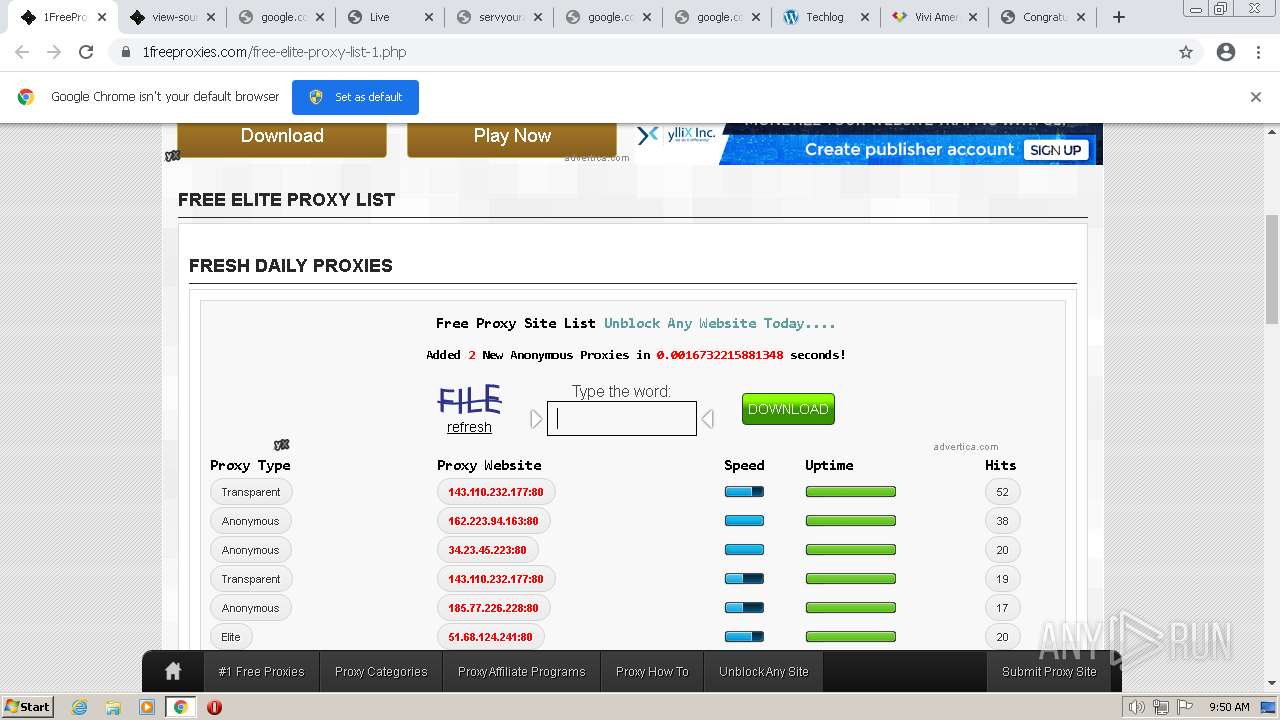
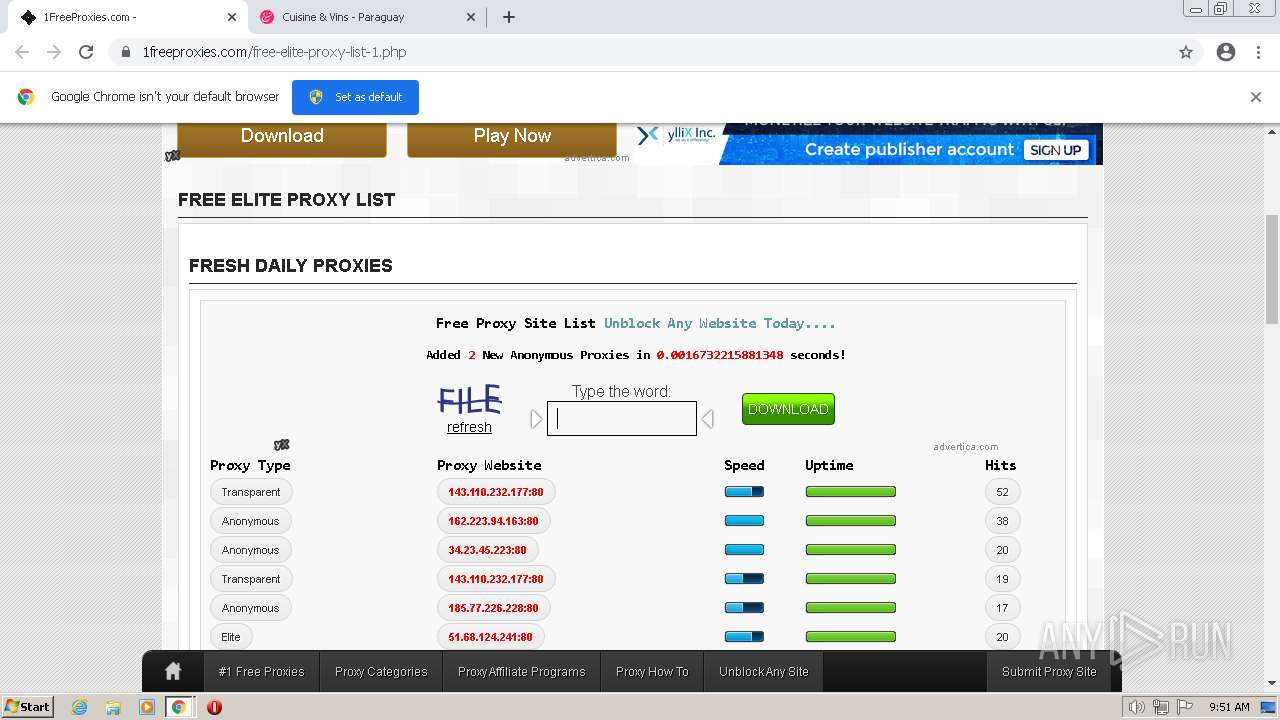
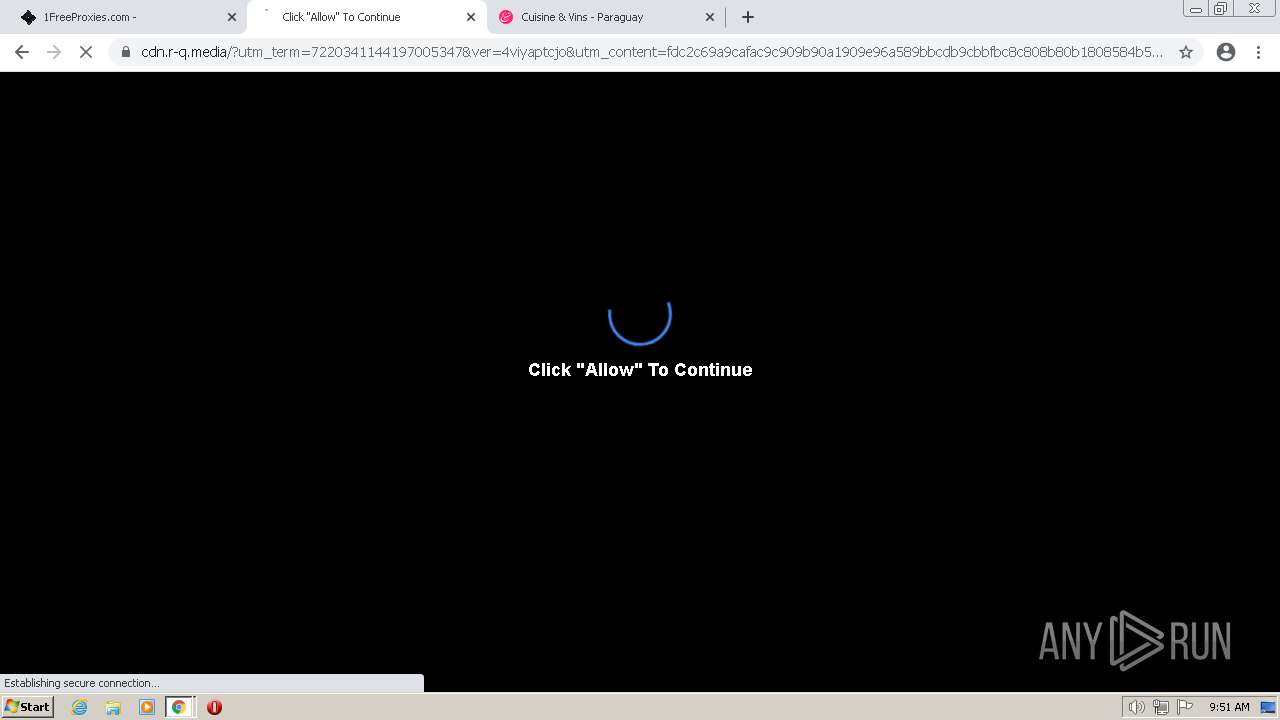
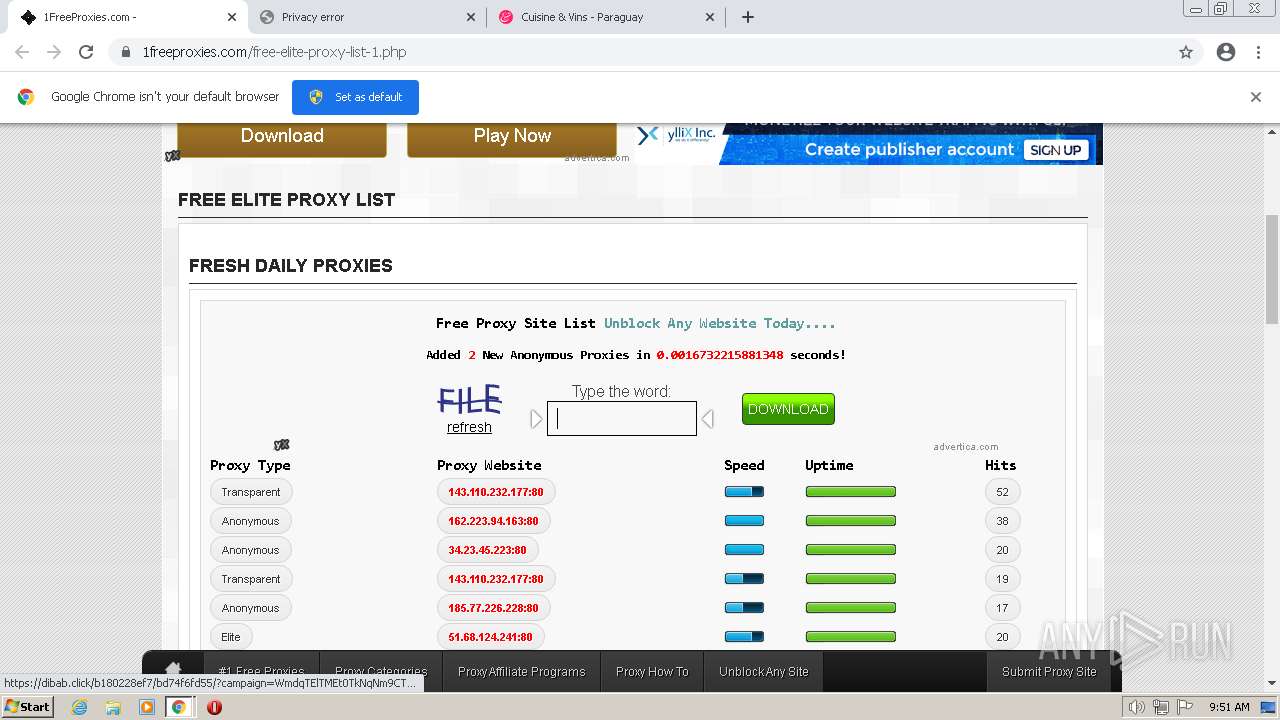
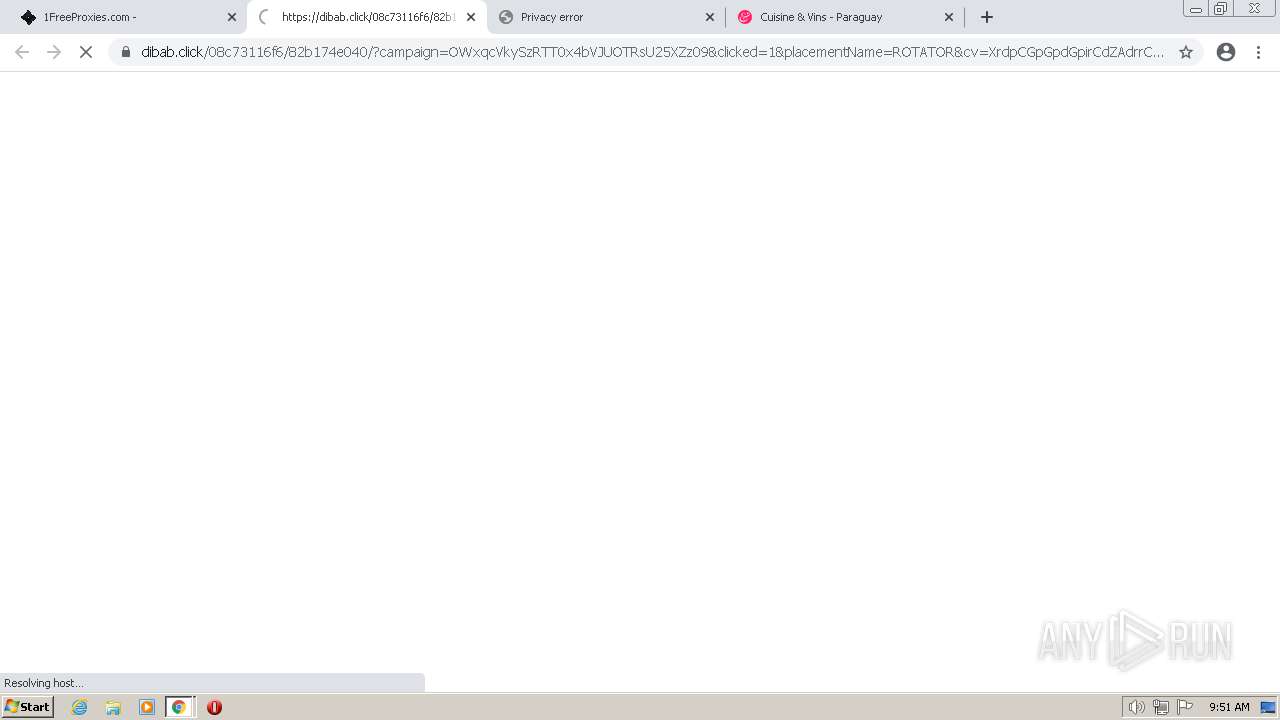
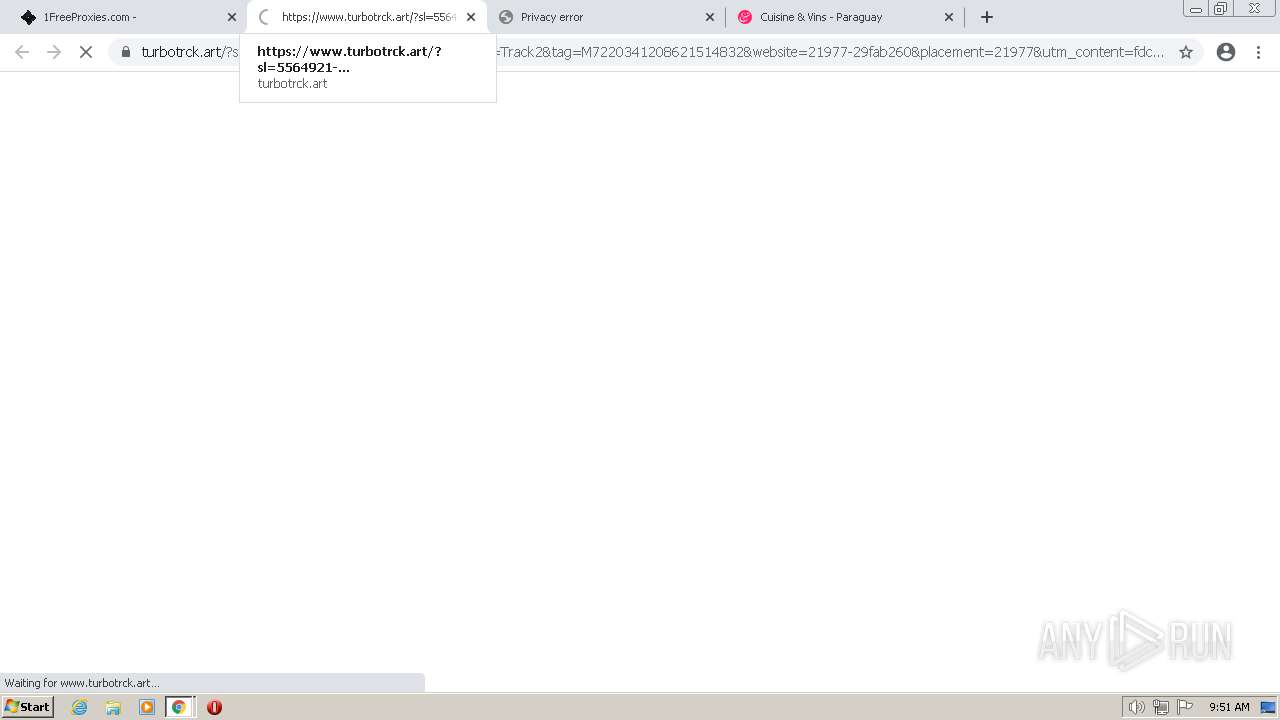
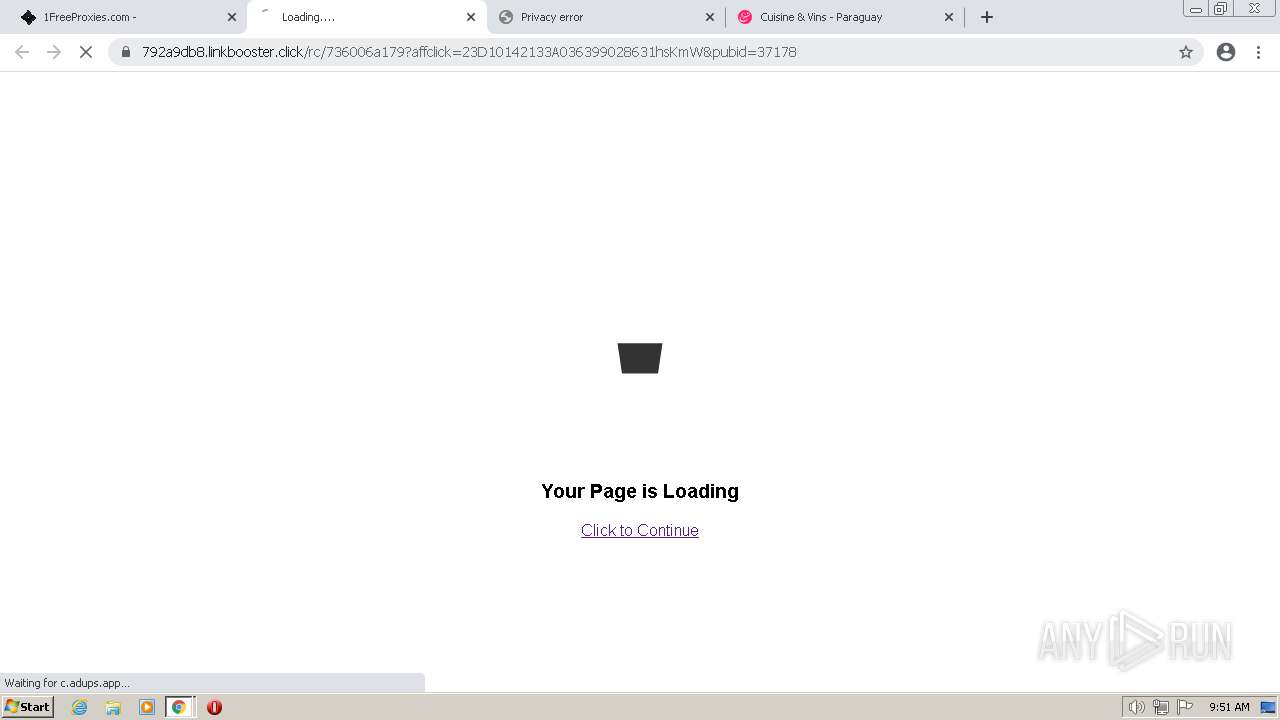
| URL: | https://1freeproxies.com/free-elite-proxy-list-1.php |
| Full analysis: | https://app.any.run/tasks/09b8c46e-5c6a-4a7f-bb6c-805373735b7e |
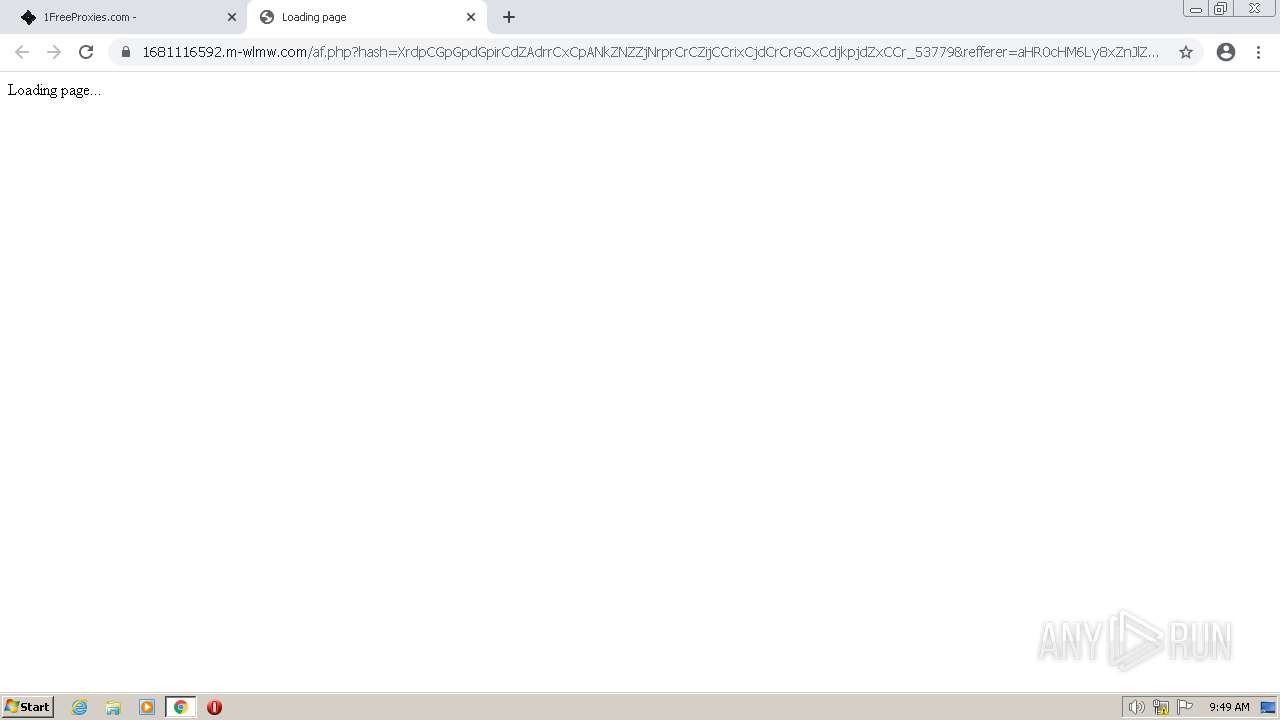
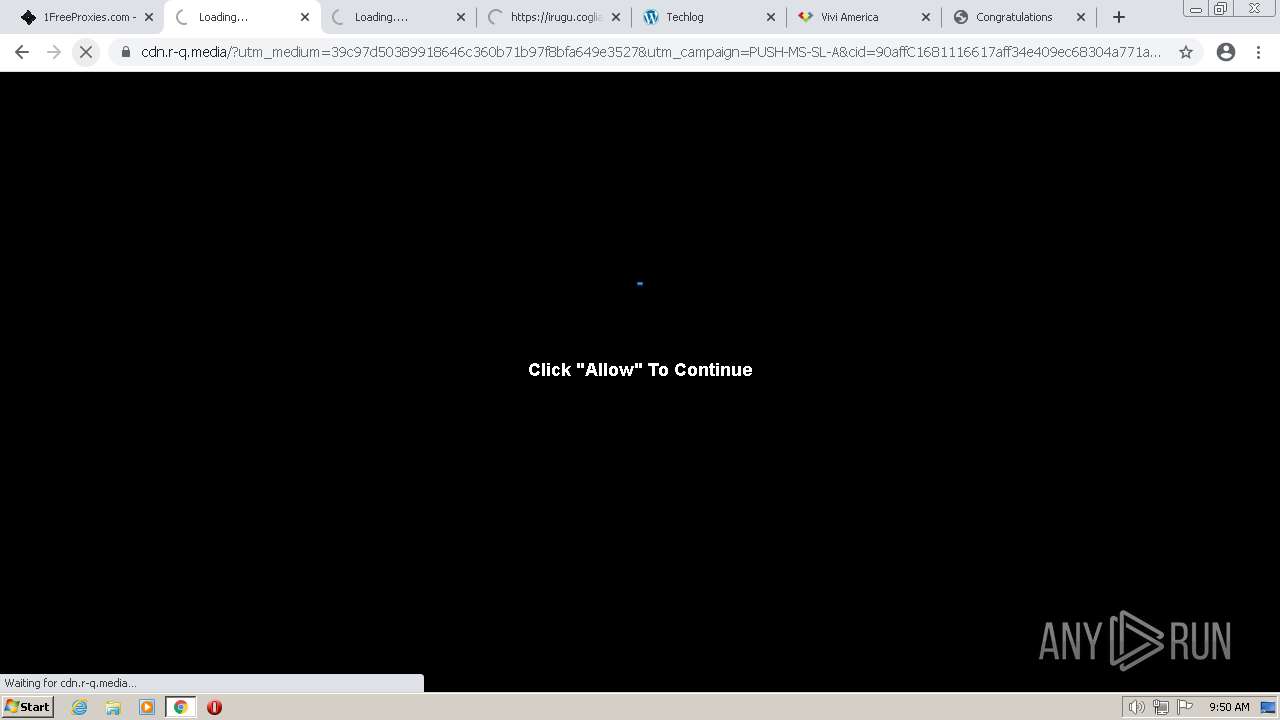
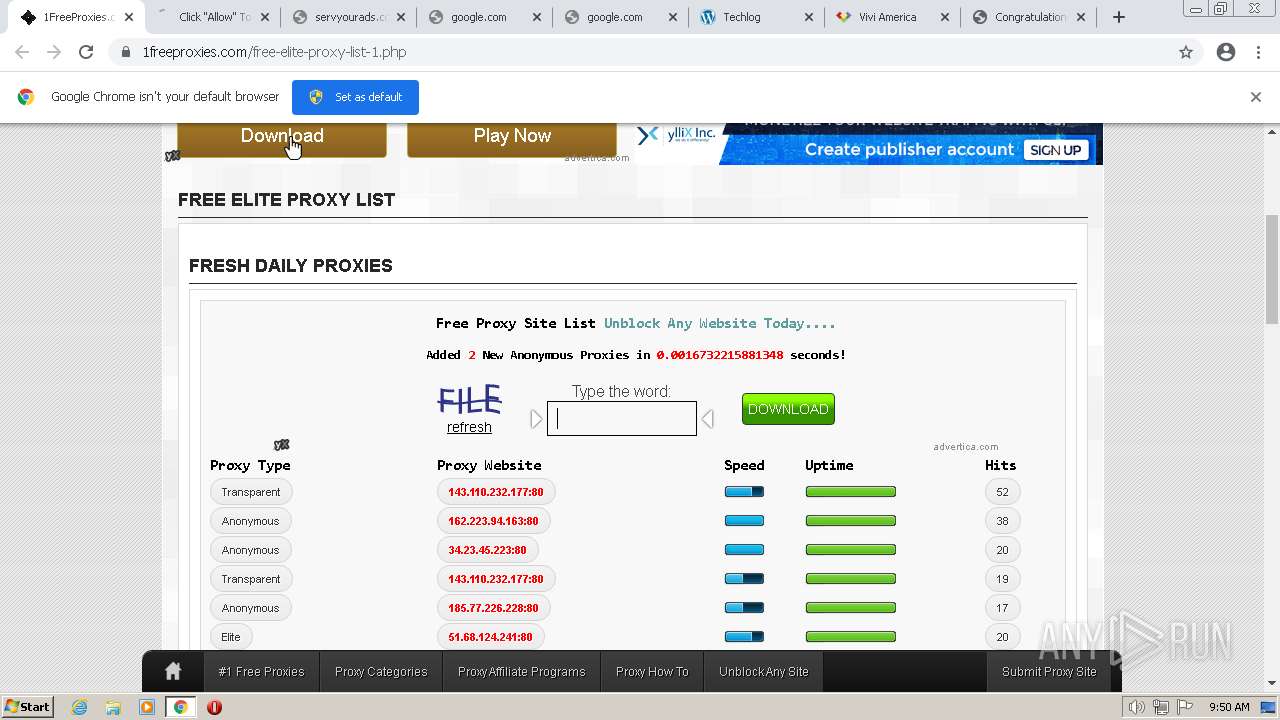
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2023, 08:49:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0951482A97094B48CBC718F7A0DF278A |
| SHA1: | C77CFC6F1285FE625BF3B85A5A4BABE7B41AB20C |
| SHA256: | 289610A507E60E925158497201980B4EAD127E37F0CE9903377FA4B08FEC8818 |
| SSDEEP: | 3:N8oXPXjGUQaMmIVXGcICsx:2oXvjSHdsCsx |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
The process checks LSA protection
- wmpnscfg.exe (PID: 4028)
Reads the computer name
- wmpnscfg.exe (PID: 4028)
Checks supported languages
- wmpnscfg.exe (PID: 4028)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 4028)
Manual execution by a user
- wmpnscfg.exe (PID: 4028)
Create files in a temporary directory
- chrome.exe (PID: 3616)
- chrome.exe (PID: 976)
Application launched itself
- chrome.exe (PID: 976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
120
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=91 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=69 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=82 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=77 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=84 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1096,16104225870693719205,17680682694820196061,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=102 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
36 348
Read events
35 892
Write events
440
Delete events
16
Modification events
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
0
Suspicious files
138
Text files
266
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6433CD82-3D0.pma | — | |
MD5:— | SHA256:— | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:A6EAFD0107D3448779F7B4767AB55570 | SHA256:2F85F20C3432B93F6002848F1C0D29D5FC0157F39C9E85621A697753F9877304 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e07a2fa1-a5e3-4a84-9b53-93a1cf6dc72c.tmp | text | |
MD5:A6EAFD0107D3448779F7B4767AB55570 | SHA256:2F85F20C3432B93F6002848F1C0D29D5FC0157F39C9E85621A697753F9877304 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf383d.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf380e.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
204
DNS requests
124
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3616 | chrome.exe | GET | 204 | 142.250.184.195:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
3616 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?29f538d6f3175e8e | US | compressed | 61.1 Kb | whitelisted |
3616 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e1fbb278befb029e | US | compressed | 61.1 Kb | whitelisted |
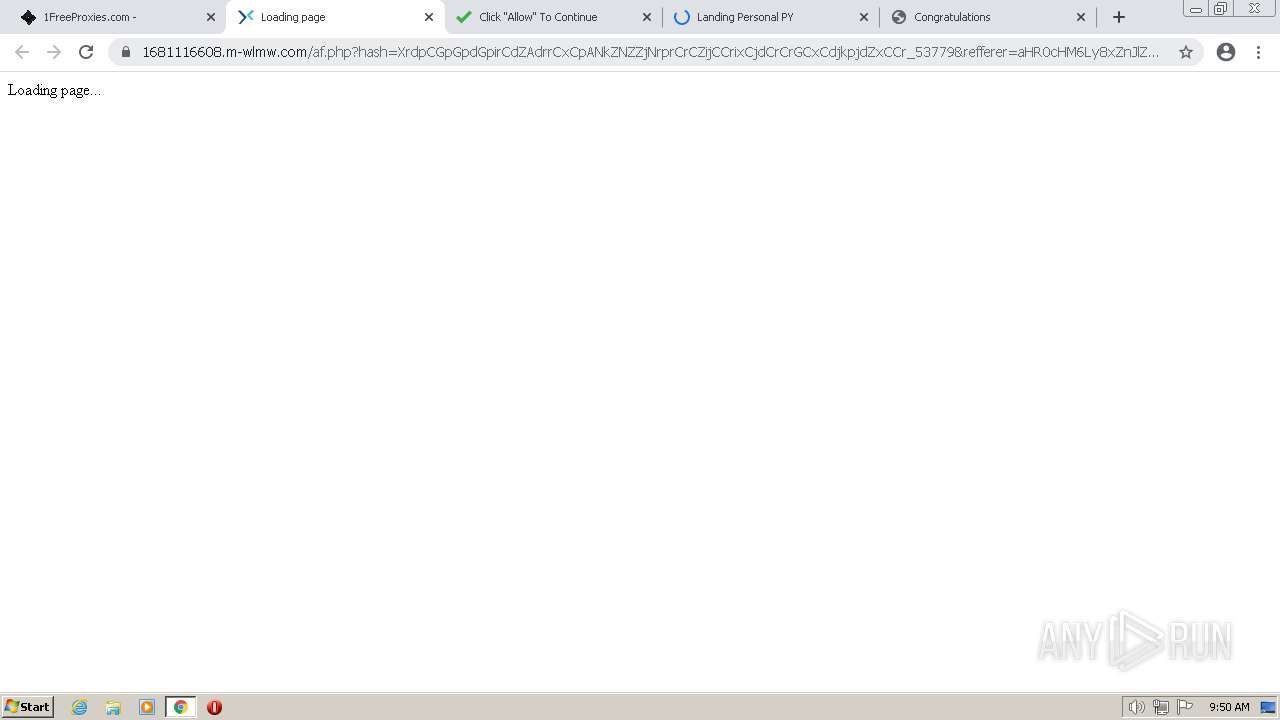
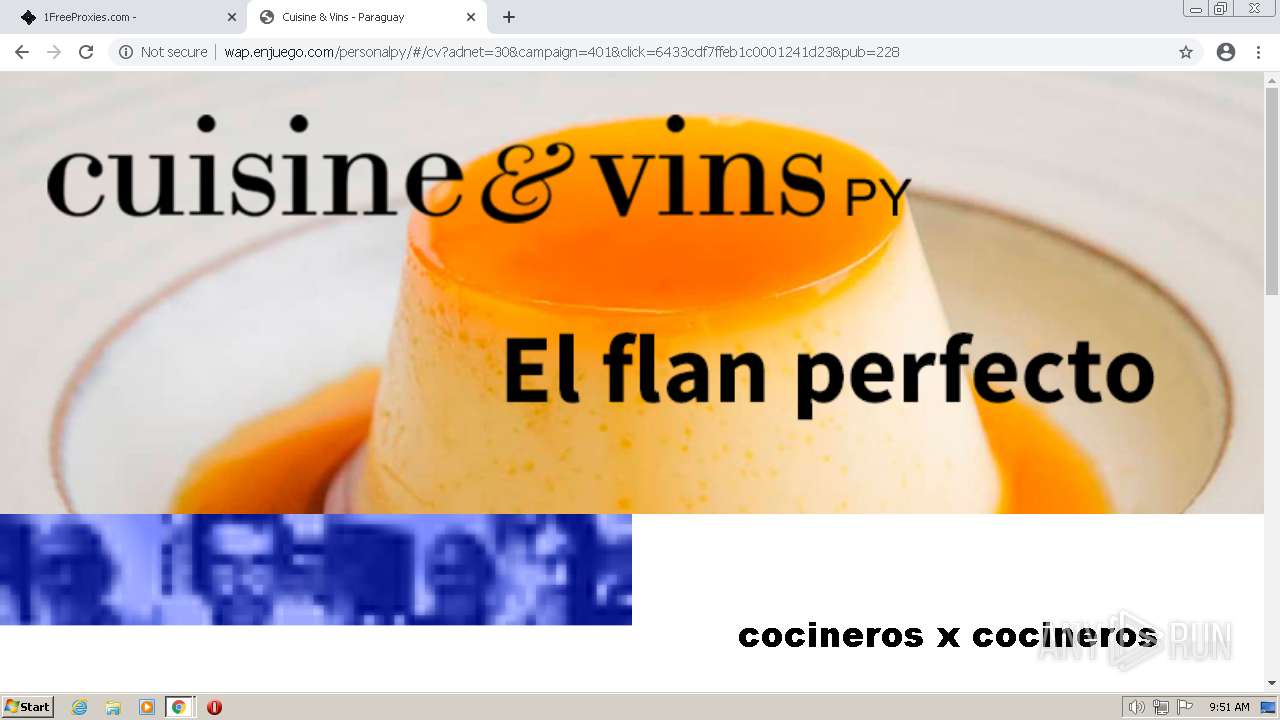
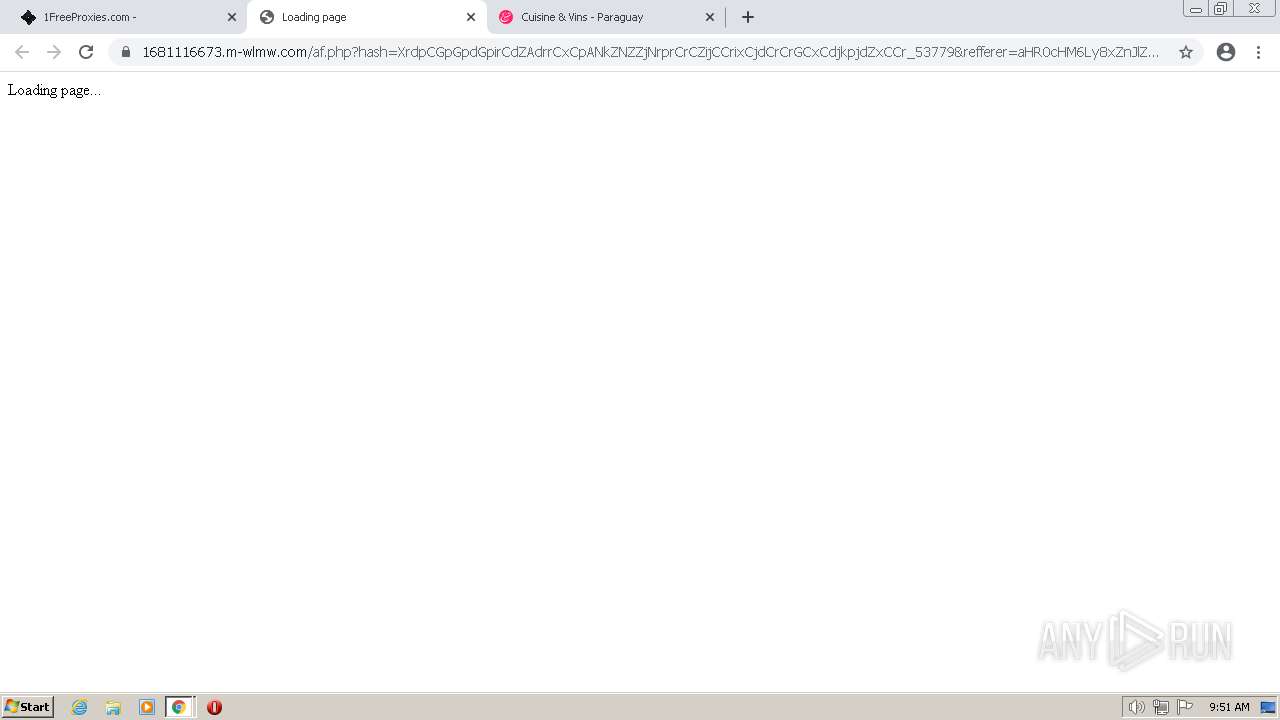
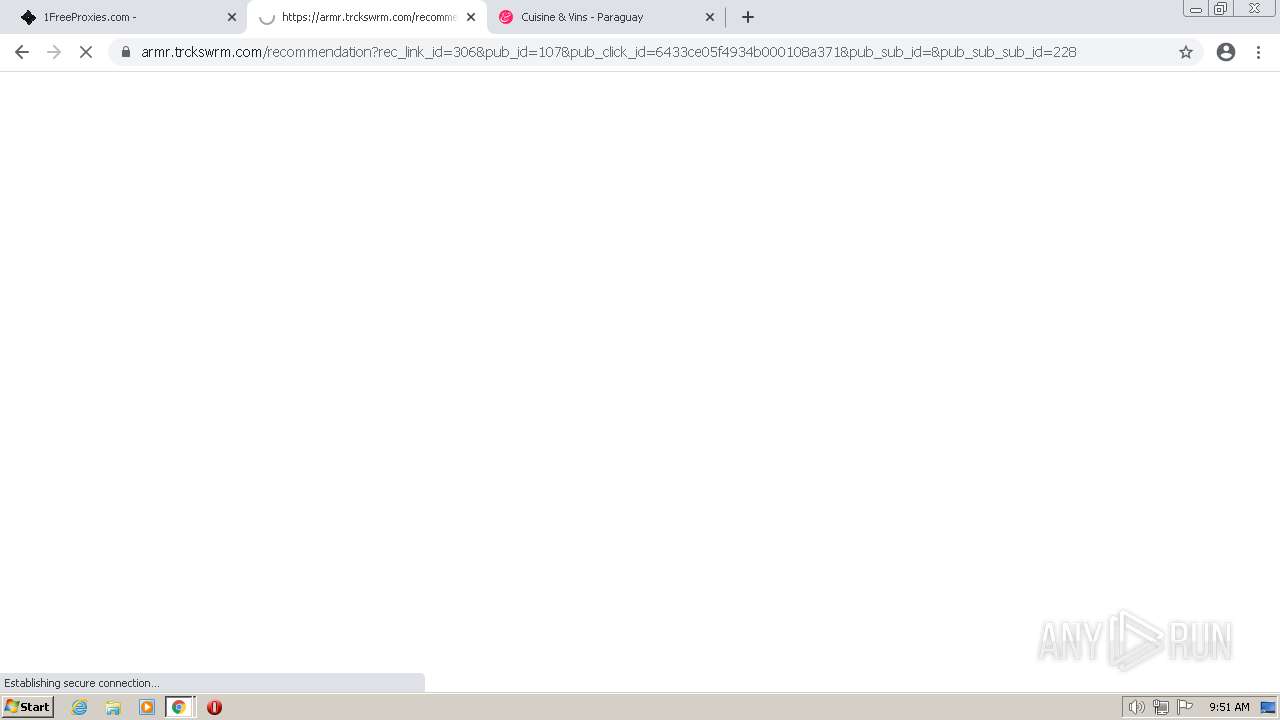
3616 | chrome.exe | GET | 302 | 200.49.90.26:80 | http://wap.enjuego.com/ContentManager/bridge/?AdNet=30&CampaignId=381&TelcoId=42&ClickID=6433cdbfa52ab600018b4aec&PublisherID=228 | AR | — | — | unknown |
3616 | chrome.exe | GET | 200 | 200.49.90.26:80 | http://wap.enjuego.com/personalpy/assets/js/sbcontrol-1.0.min.js | AR | text | 336 b | unknown |
3616 | chrome.exe | GET | 200 | 200.49.90.26:80 | http://wap.enjuego.com/personalpy/main-es2015.d07b4dfca224f29f6383.js | AR | text | 522 Kb | unknown |
3616 | chrome.exe | GET | 404 | 200.49.90.26:80 | http://wap.enjuego.com/personalpy/terminos.css | AR | html | 1.03 Kb | unknown |
3616 | chrome.exe | GET | 200 | 200.49.90.26:80 | http://wap.enjuego.com/personalpy/polyfills-es2015.ffa9bb4e015925544f91.js | AR | text | 36.2 Kb | unknown |
3616 | chrome.exe | GET | 200 | 200.49.90.26:80 | http://wap.enjuego.com/personalpy/ | AR | html | 2.37 Kb | unknown |
3616 | chrome.exe | GET | 200 | 200.49.90.26:80 | http://wap.enjuego.com/ContentManager/utilities/?Method=GET&Action=getHeader&adnetwork=30&campaign=381&Header=X-MSISDN&click=6433cdbfa52ab600018b4aec | AR | binary | 19 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3616 | chrome.exe | 142.250.184.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
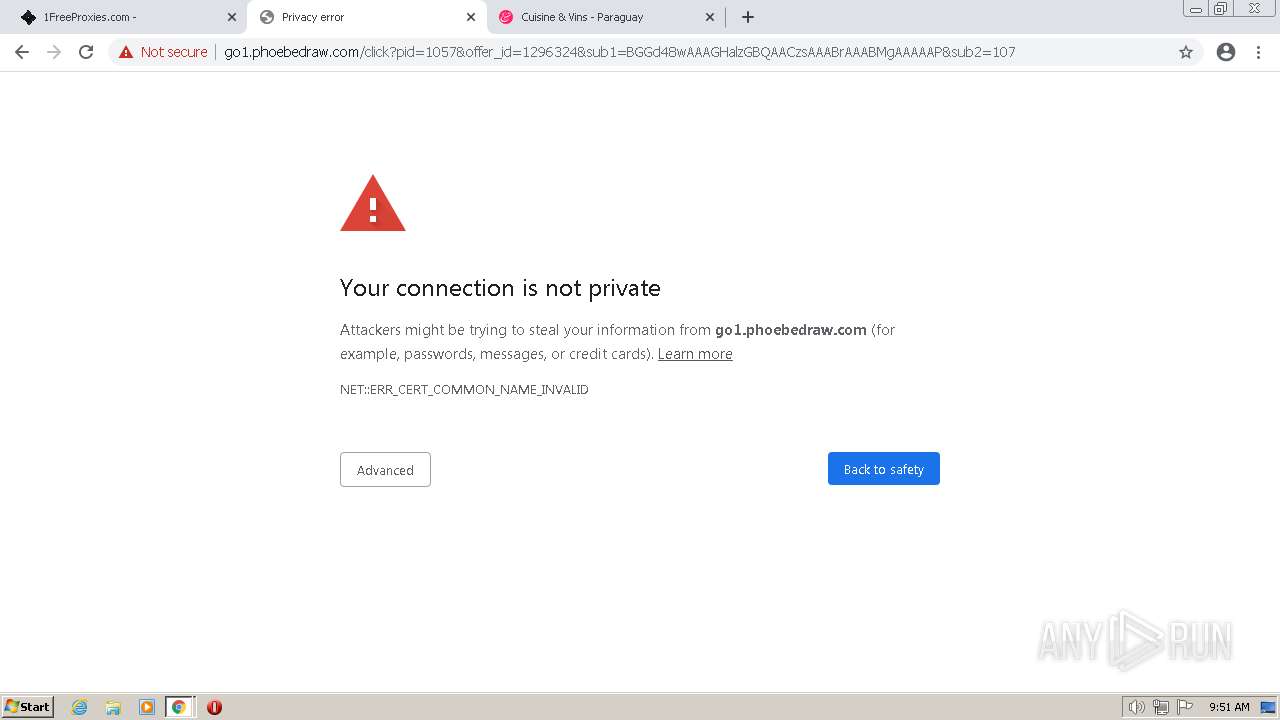
3616 | chrome.exe | 198.54.116.95:443 | 1freeproxies.com | NAMECHEAP-NET | US | malicious |
3616 | chrome.exe | 142.250.186.97:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3616 | chrome.exe | 142.250.184.195:80 | www.gstatic.com | GOOGLE | US | whitelisted |
3616 | chrome.exe | 142.250.185.131:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
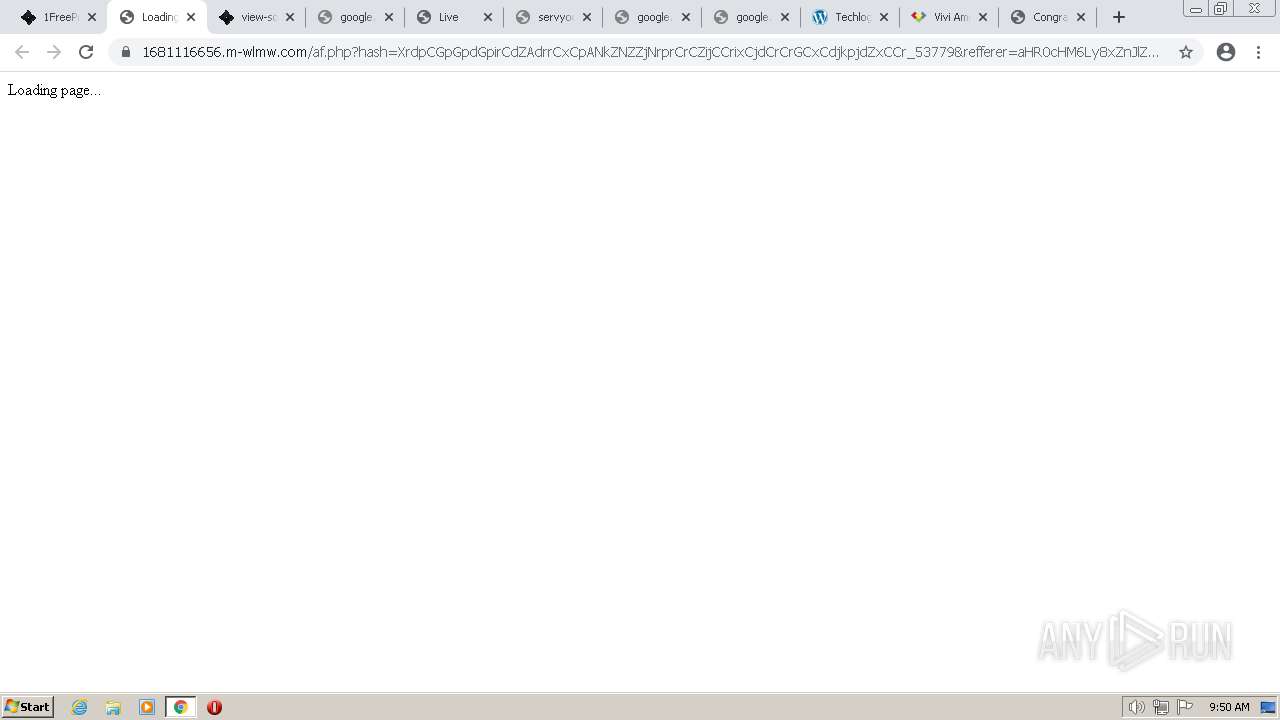
3616 | chrome.exe | 185.66.200.220:443 | udbaa.com | skHosting.eu s.r.o. | SK | unknown |
3616 | chrome.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
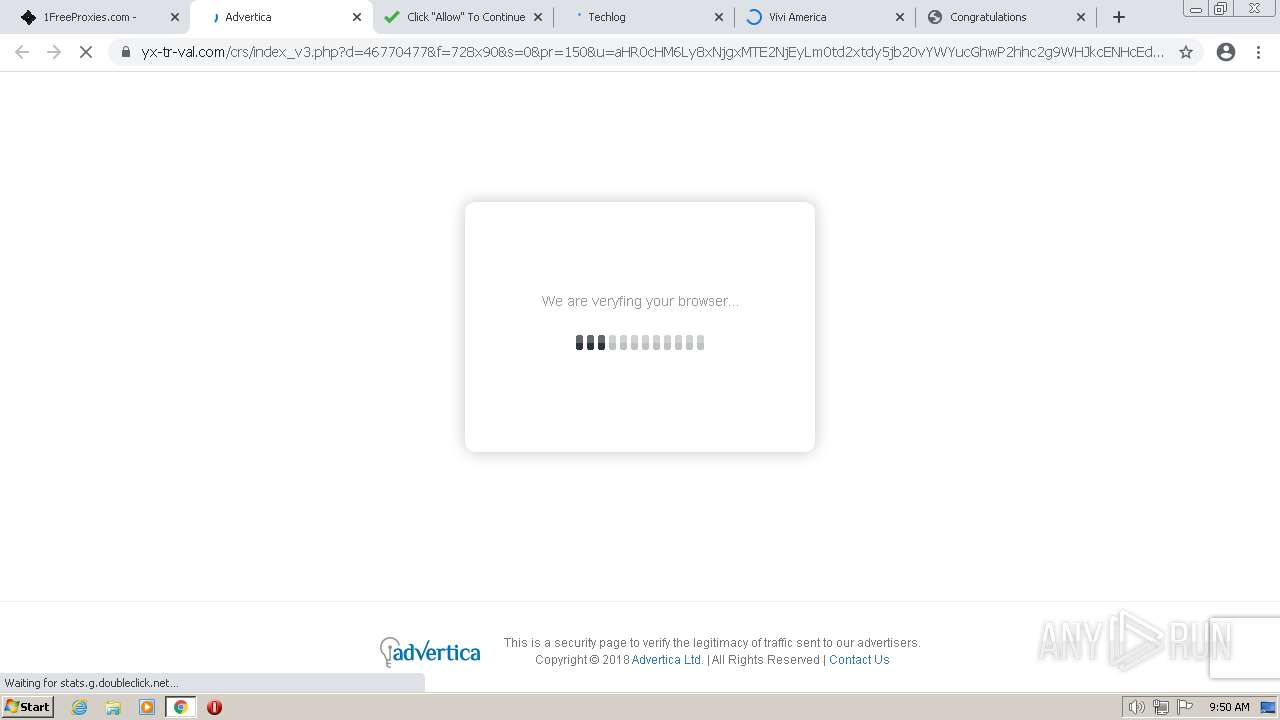
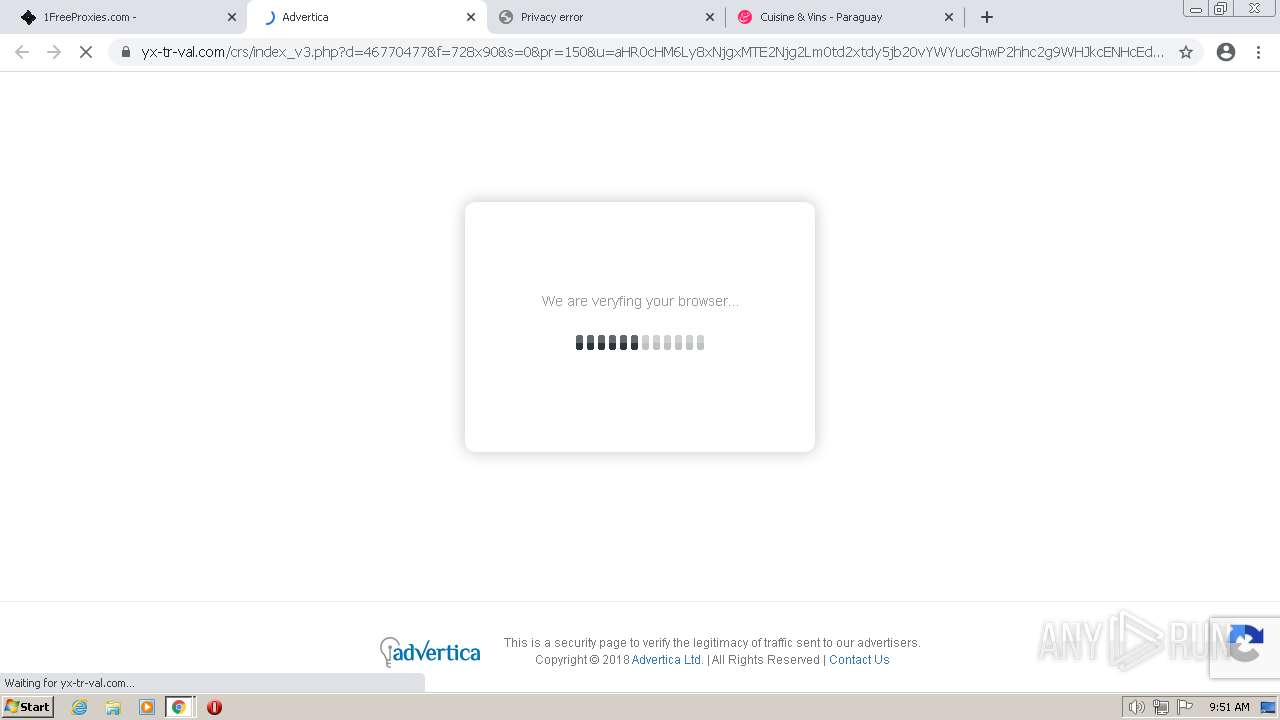
3616 | chrome.exe | 185.66.200.127:443 | ylx-aff.advertica-cdn.com | skHosting.eu s.r.o. | SK | suspicious |
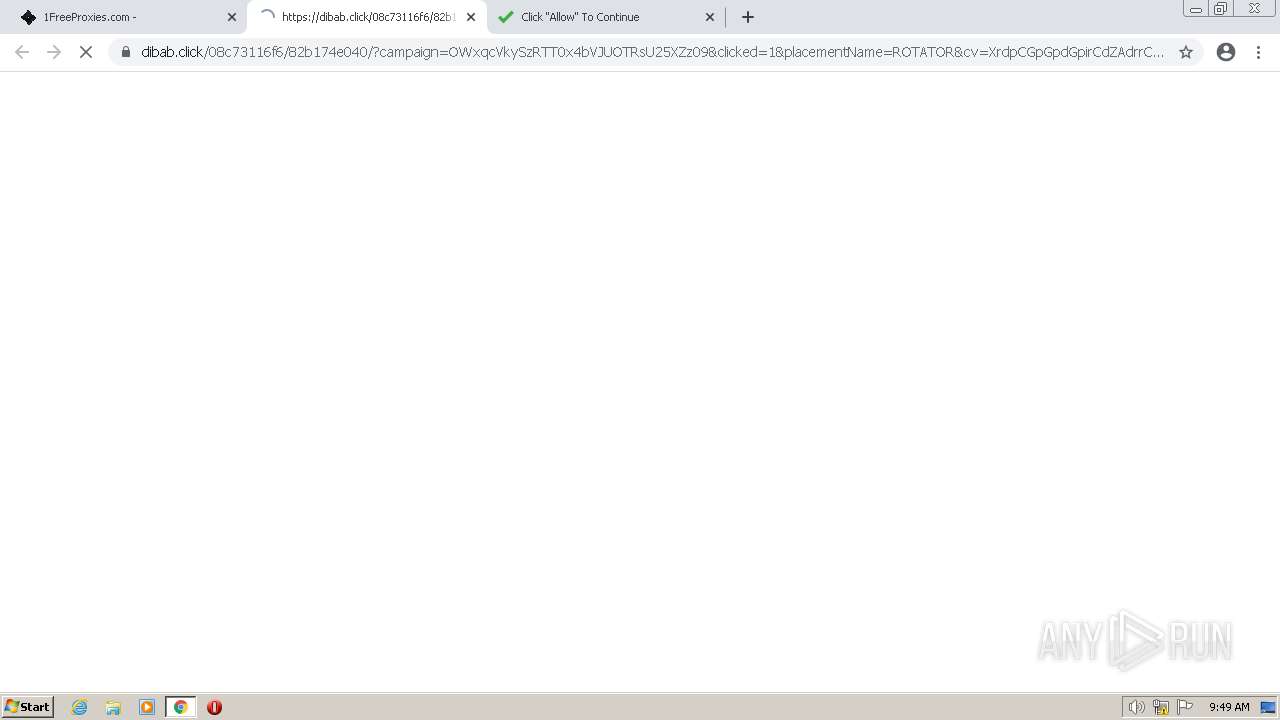
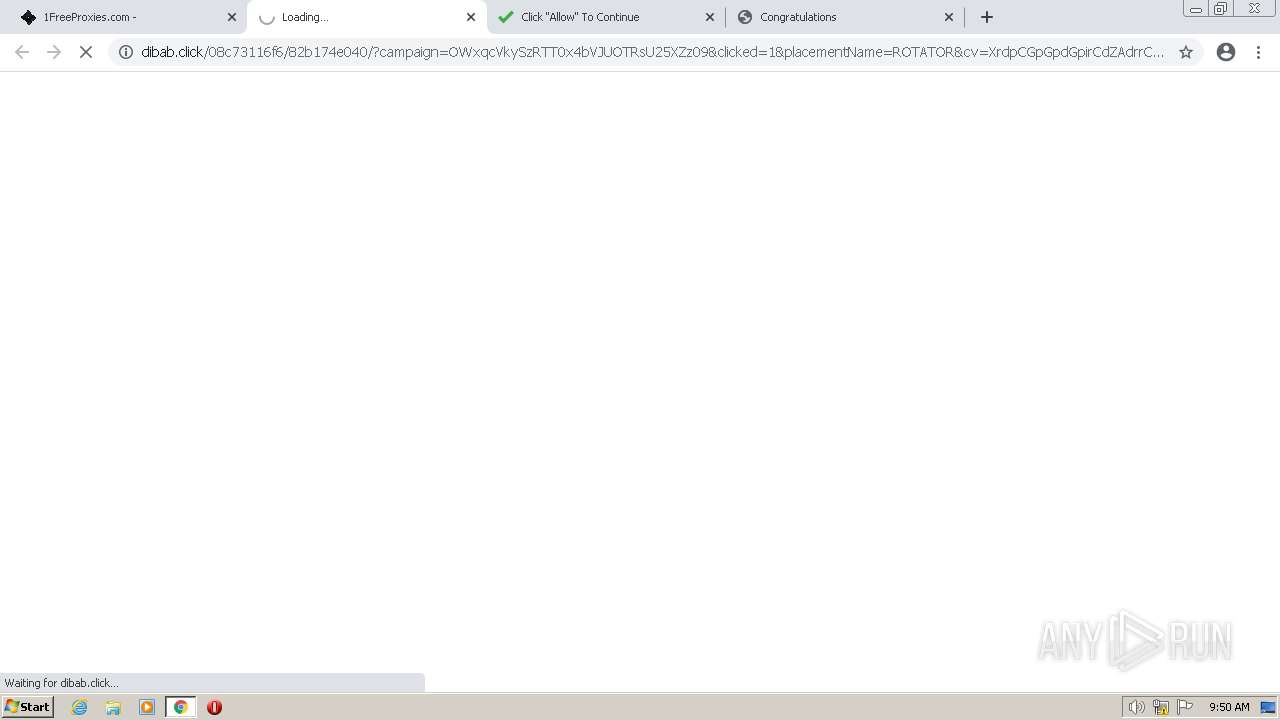
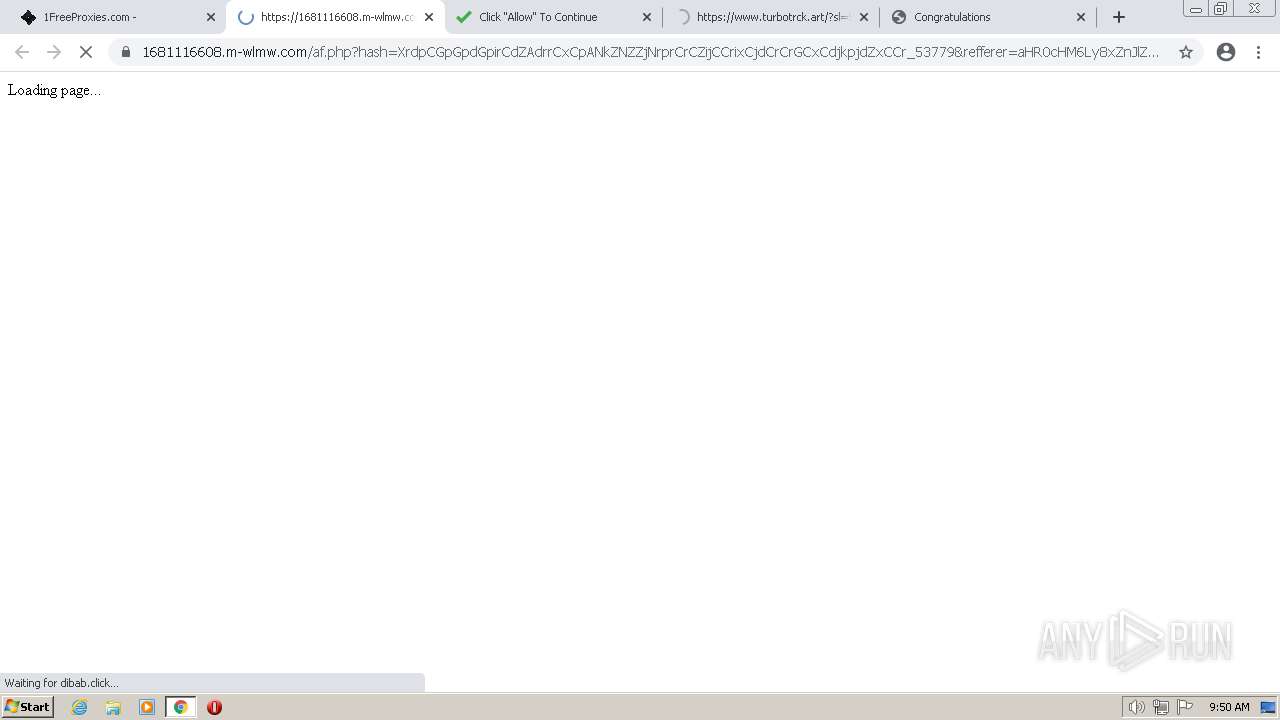
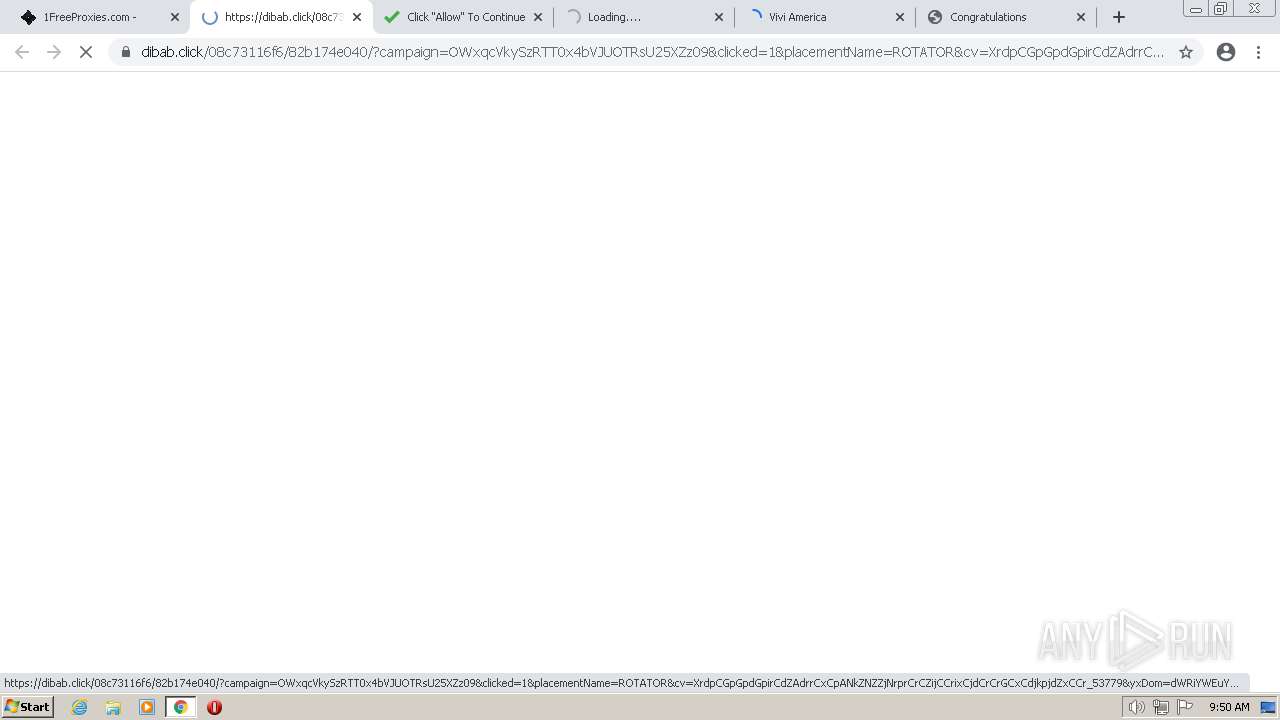
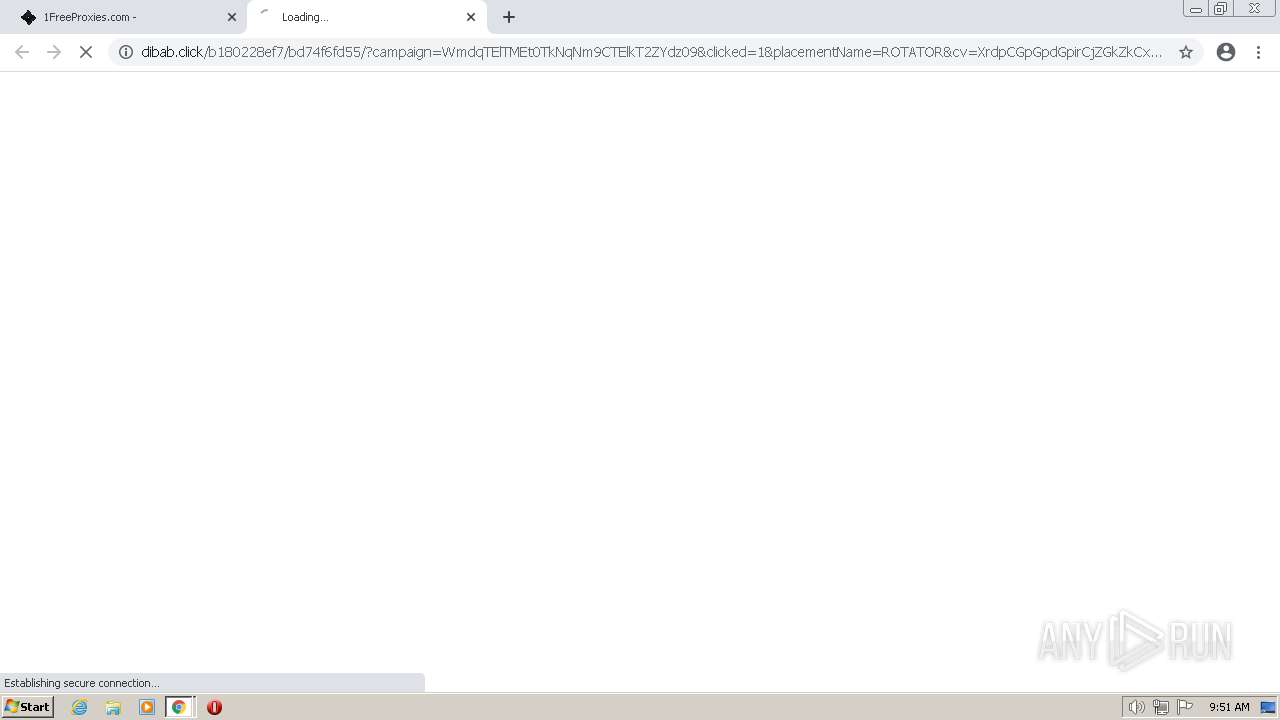
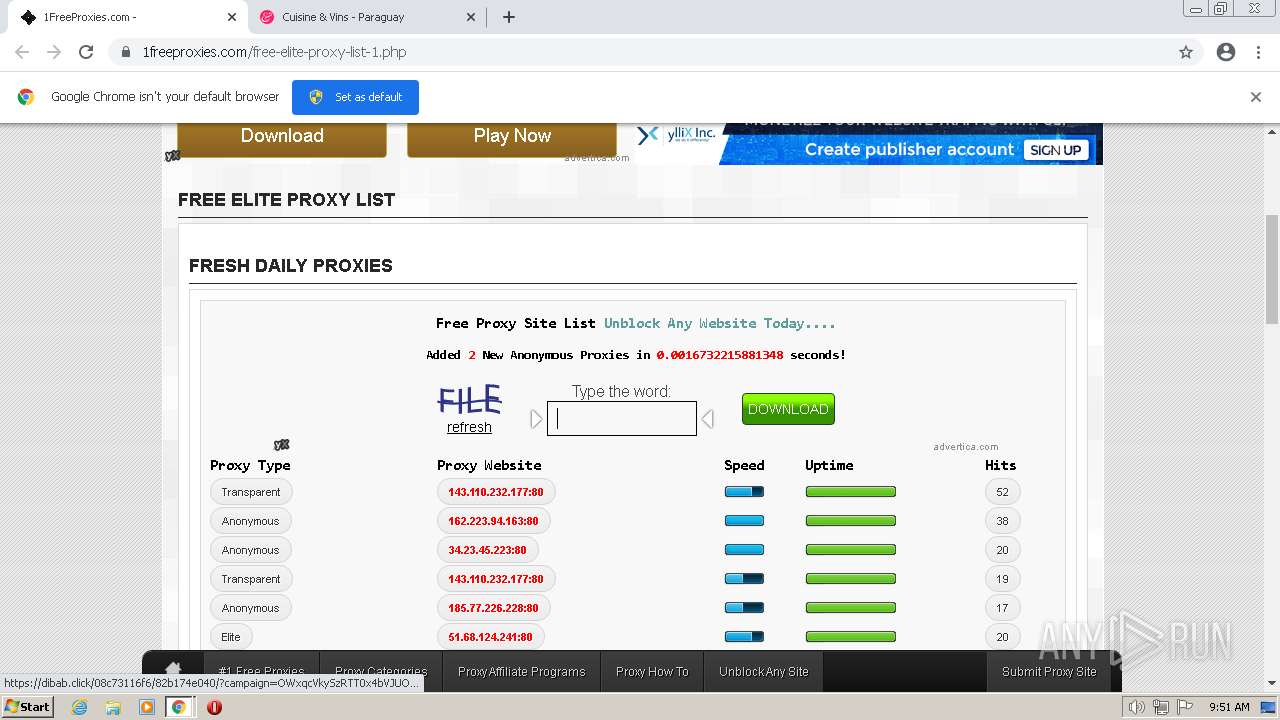
3616 | chrome.exe | 185.66.201.43:443 | dibab.click | skHosting.eu s.r.o. | SK | suspicious |
3616 | chrome.exe | 185.66.201.7:443 | 6784.world | skHosting.eu s.r.o. | SK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
1freeproxies.com |
| unknown |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
udbaa.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ylx-aff.advertica-cdn.com |
| suspicious |
dibab.click |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
3616 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3616 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3616 | chrome.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3616 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3616 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3616 | chrome.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M1 |
3616 | chrome.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M3 |