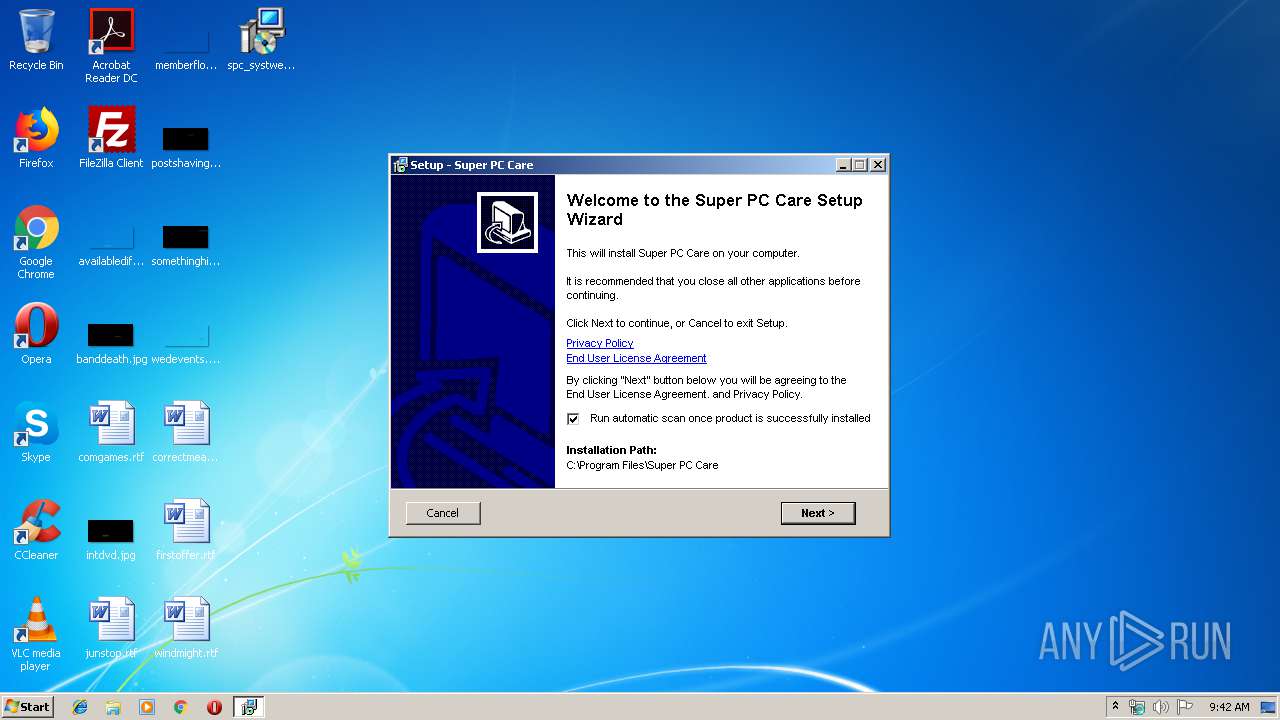
| download: | spc_systweak-default.exe |
| Full analysis: | https://app.any.run/tasks/857f86a5-aab8-4518-a4d6-569303a35ee8 |
| Verdict: | Malicious activity |
| Analysis date: | November 07, 2019, 09:41:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 58B830C6D223E31087FDDF80D7BCB3B7 |
| SHA1: | 9E302851E6E16A836485B7CBE114C9A3E6E3C11D |
| SHA256: | 28889A5C340424B7E5381041D2B44A7C40AC33EB3537262E28EE277947A34AEF |
| SSDEEP: | 98304:19Kbx9syK5ZAxm95BM0FoosMY2qnXy5yklC+abJySOSV0/WUoDA+oidNi:19Kbx25aA3smqnXMygUU20/WhDAGdg |
MALICIOUS
Application was dropped or rewritten from another process
- SuperPCCare.exe (PID: 584)
Loads the Task Scheduler COM API
- SuperPCCare.exe (PID: 584)
Loads dropped or rewritten executable
- SuperPCCare.exe (PID: 584)
Starts Visual C# compiler
- SuperPCCare.exe (PID: 584)
Actions looks like stealing of personal data
- SuperPCCare.exe (PID: 584)
Changes settings of System certificates
- spc_systweak-default.tmp (PID: 3308)
SUSPICIOUS
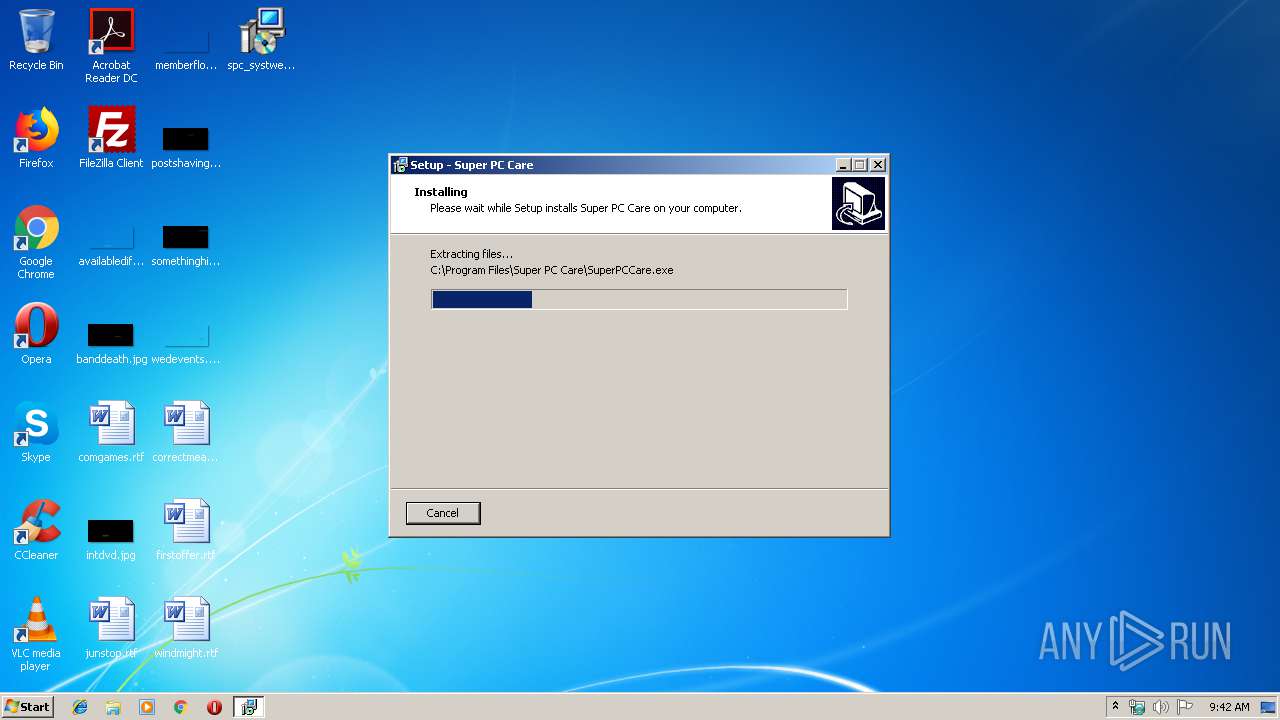
Executable content was dropped or overwritten
- spc_systweak-default.exe (PID: 1044)
- spc_systweak-default.exe (PID: 460)
- spc_systweak-default.tmp (PID: 3308)
- SuperPCCare.exe (PID: 584)
Uses TASKKILL.EXE to kill process
- spc_systweak-default.tmp (PID: 3308)
Reads Windows owner or organization settings
- spc_systweak-default.tmp (PID: 3308)
Creates files in the user directory
- SuperPCCare.exe (PID: 584)
- spc_systweak-default.tmp (PID: 3308)
- regedit.exe (PID: 3400)
Reads the Windows organization settings
- spc_systweak-default.tmp (PID: 3308)
Creates files in the Windows directory
- spc_systweak-default.tmp (PID: 3308)
Uses TASKKILL.EXE to kill Browsers
- spc_systweak-default.tmp (PID: 3308)
Reads Internet Cache Settings
- SuperPCCare.exe (PID: 584)
- regedit.exe (PID: 3400)
Executed as Windows Service
- PresentationFontCache.exe (PID: 520)
- vssvc.exe (PID: 2256)
Creates files in the program directory
- SuperPCCare.exe (PID: 584)
- dw20.exe (PID: 492)
Reads internet explorer settings
- SuperPCCare.exe (PID: 584)
Searches for installed software
- SuperPCCare.exe (PID: 584)
Executed via COM
- DllHost.exe (PID: 3360)
Reads default file associations for system extensions
- regedit.exe (PID: 3400)
Removes files from Windows directory
- SuperPCCare.exe (PID: 584)
INFO
Application was dropped or rewritten from another process
- spc_systweak-default.tmp (PID: 3600)
- spc_systweak-default.tmp (PID: 3308)
Creates files in the program directory
- spc_systweak-default.tmp (PID: 3308)
Loads dropped or rewritten executable
- spc_systweak-default.tmp (PID: 3308)
Creates a software uninstall entry
- spc_systweak-default.tmp (PID: 3308)
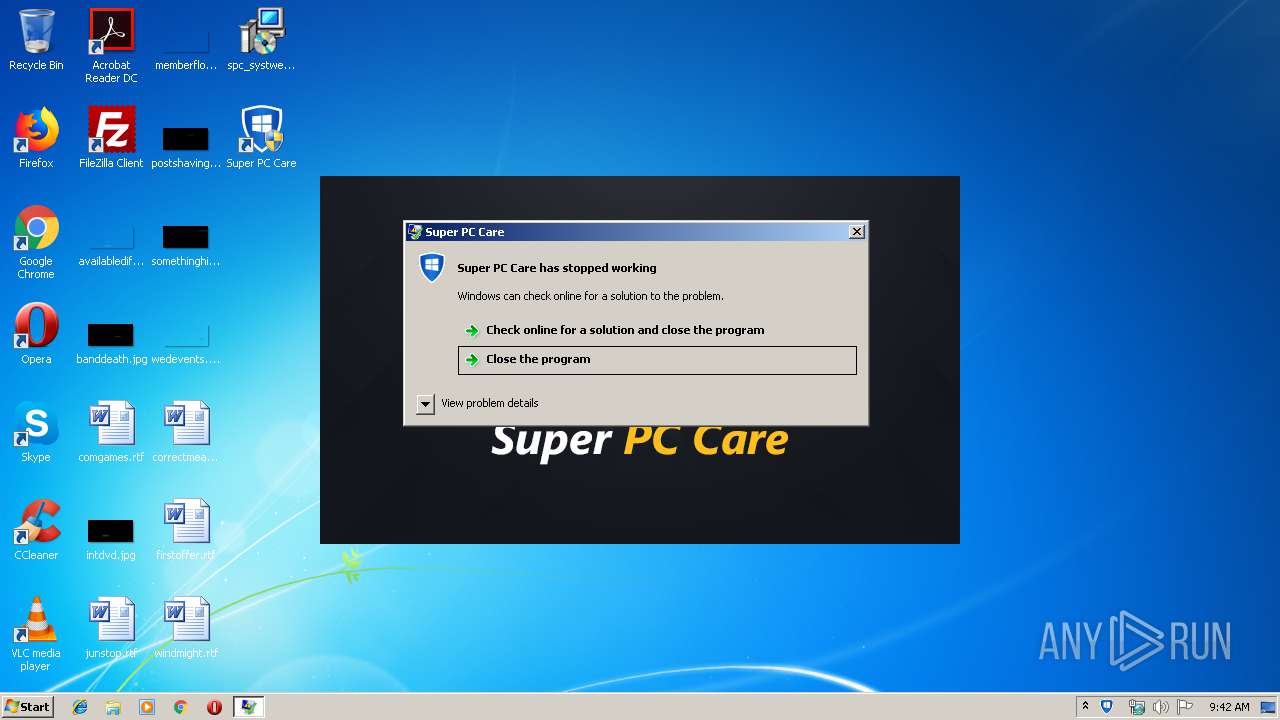
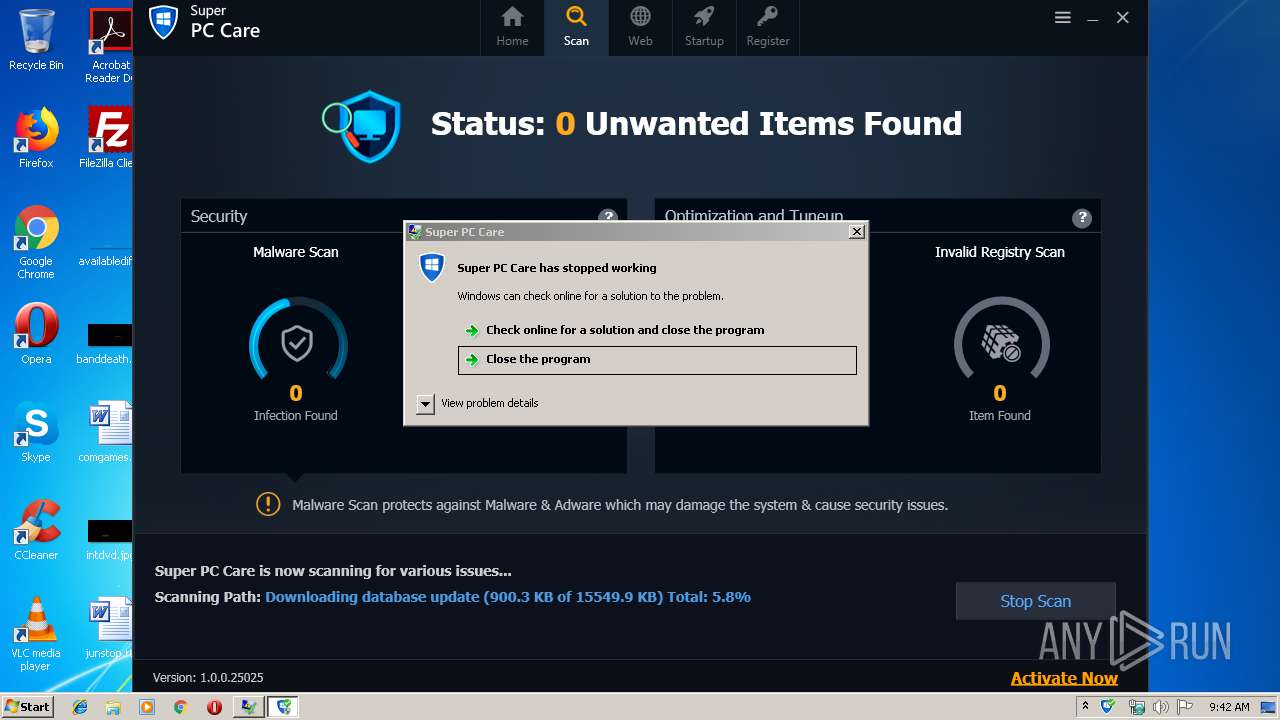
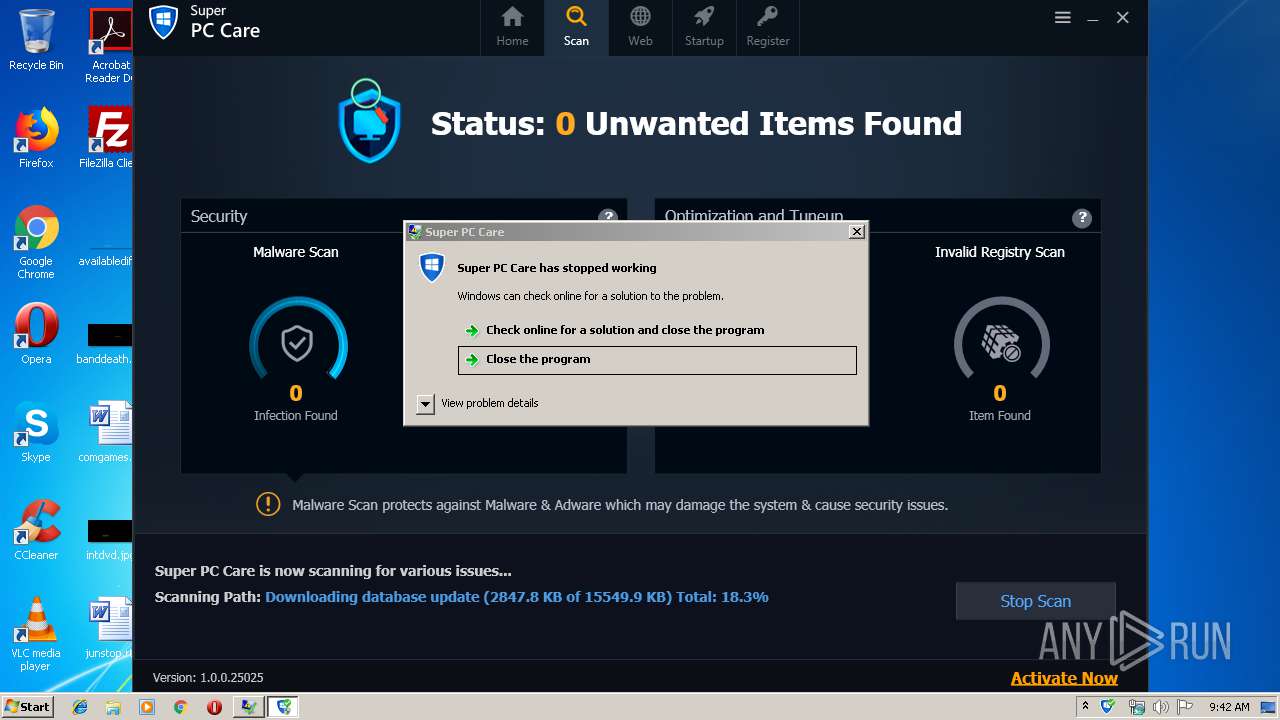
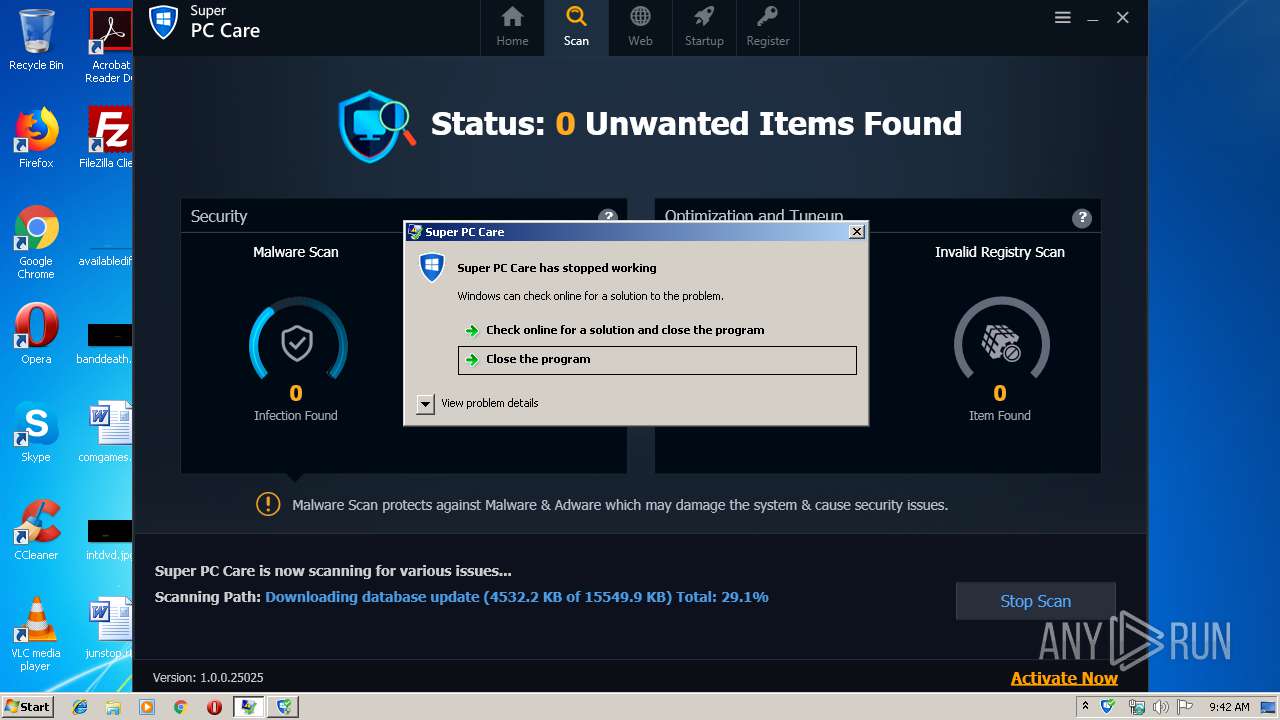
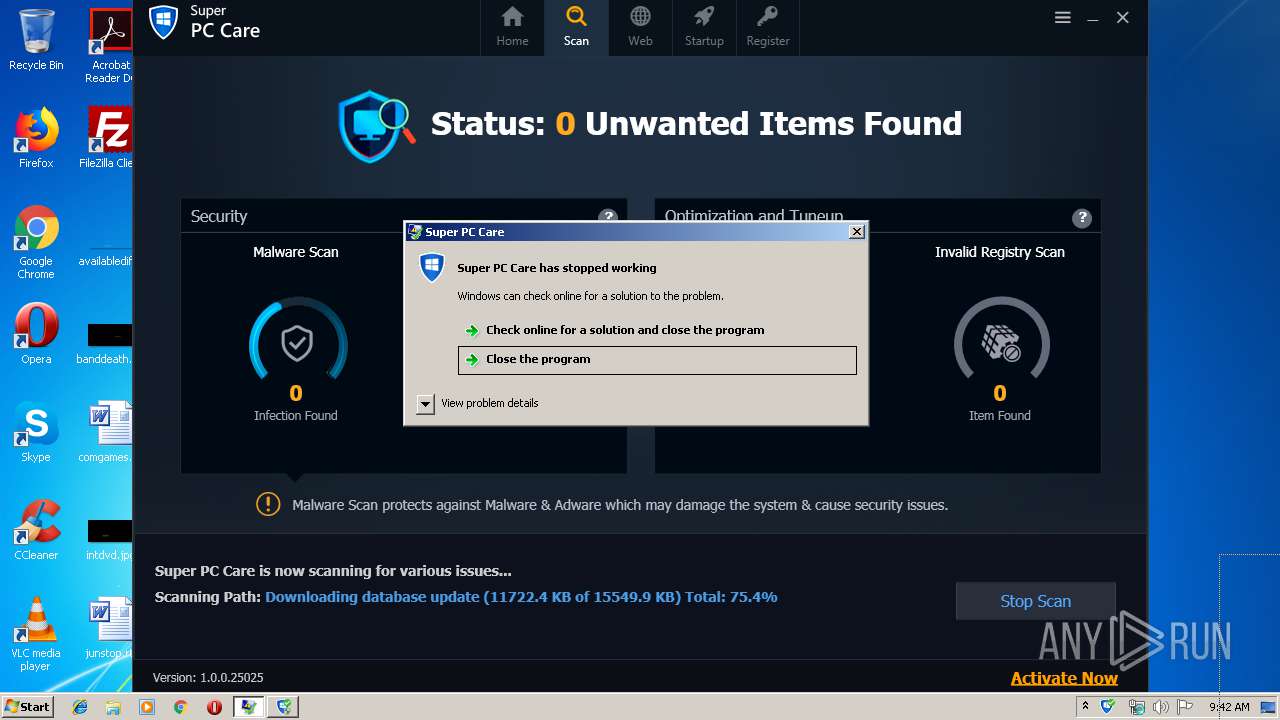
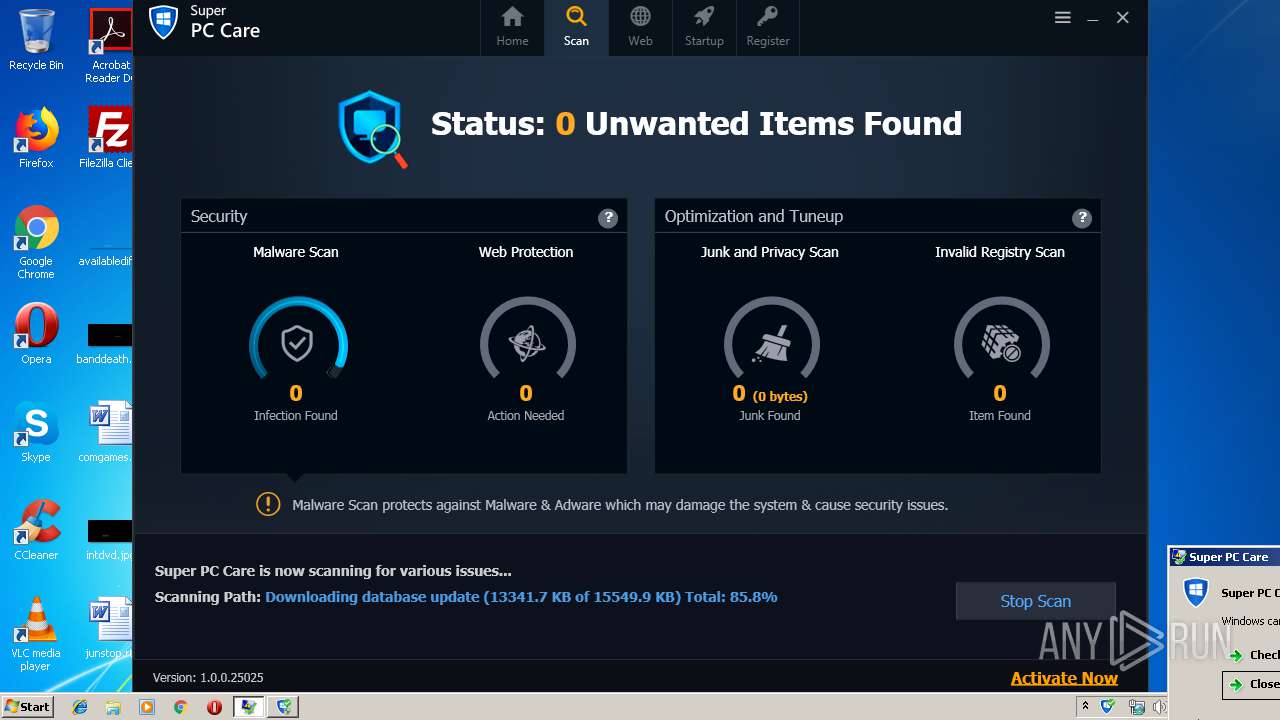
Application was crashed
- SuperPCCare.exe (PID: 584)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2256)
Dropped object may contain Bitcoin addresses
- SuperPCCare.exe (PID: 584)
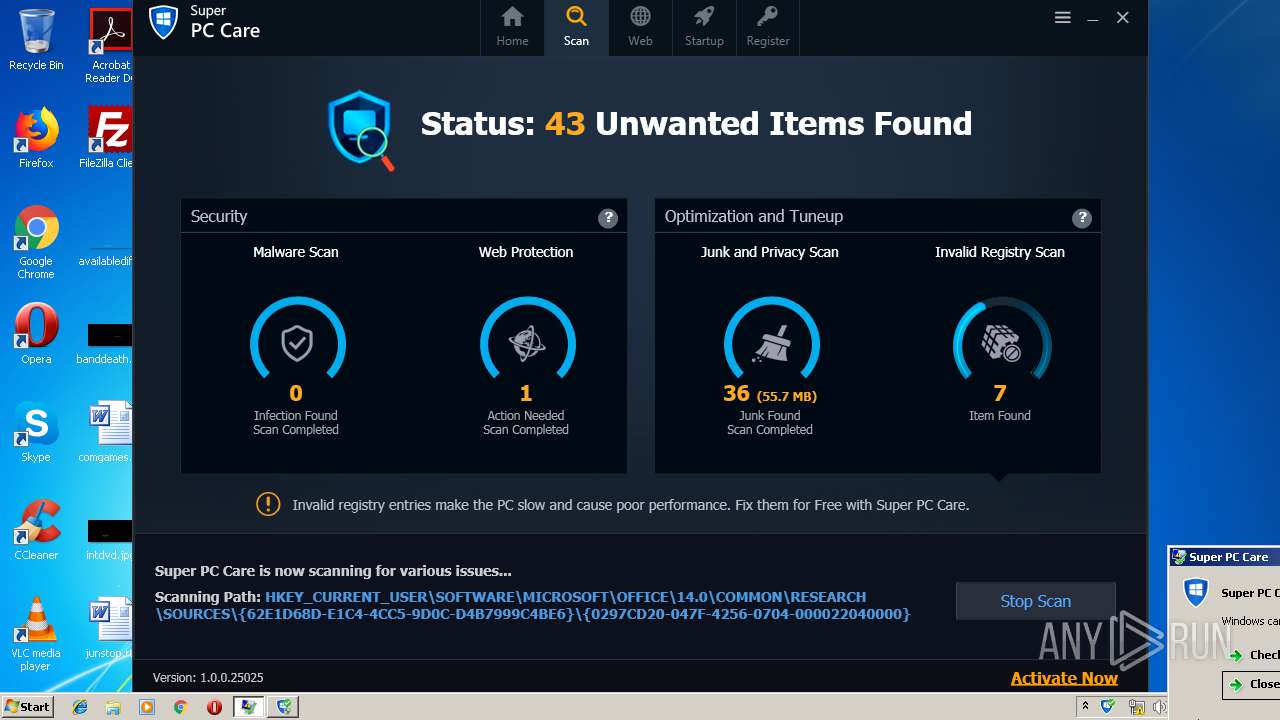
Reads Microsoft Office registry keys
- regedit.exe (PID: 3400)
- SuperPCCare.exe (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
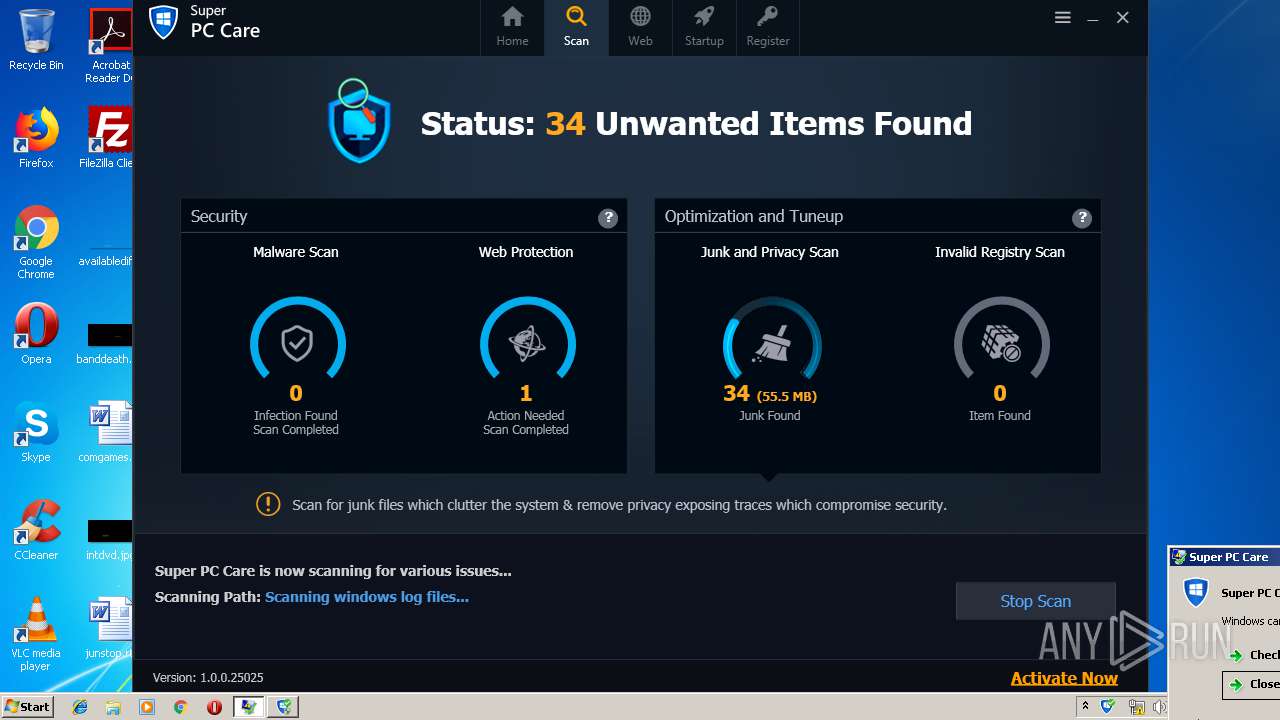
| FileVersionNumber: | 1.0.0.25025 |
| ProductVersionNumber: | 1.0.0.25025 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Systweak |
| FileDescription: | Super PC Care |
| FileVersion: | Super PC Care 2.2 |
| LegalCopyright: | Systweak Software 2019 |
| ProductName: | Super PC Care |
| ProductVersion: | 1.0.0.25025 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Systweak |
| FileDescription: | Super PC Care |
| FileVersion: | Super PC Care 2.2 |
| LegalCopyright: | Systweak Software 2019 |
| ProductName: | Super PC Care |
| ProductVersion: | 1.0.0.25025 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14493 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
67
Monitored processes
18
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Windows\system32\taskkill.exe" /f /im SmartPCCare.exe | C:\Windows\system32\taskkill.exe | — | spc_systweak-default.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | "C:\Users\admin\Desktop\spc_systweak-default.exe" | C:\Users\admin\Desktop\spc_systweak-default.exe | explorer.exe | ||||||||||||
User: admin Company: Systweak Integrity Level: MEDIUM Description: Super PC Care Exit code: 0 Version: Super PC Care 2.2 Modules
| |||||||||||||||
| 492 | dw20.exe -x -s 2272 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | SuperPCCare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 496 | "C:\Windows\System32\taskkill.exe" /f /im "iexplore.exe" | C:\Windows\System32\taskkill.exe | — | spc_systweak-default.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 520 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Super PC Care\SuperPCCare.exe" /firstinstall /autoscan | C:\Program Files\Super PC Care\SuperPCCare.exe | spc_systweak-default.tmp | ||||||||||||
User: admin Company: Systweak Software Integrity Level: HIGH Description: Super PC Care Exit code: 3221225477 Version: 1.0.0.25025 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\Desktop\spc_systweak-default.exe" /SPAWNWND=$30128 /NOTIFYWND=$40138 | C:\Users\admin\Desktop\spc_systweak-default.exe | spc_systweak-default.tmp | ||||||||||||
User: admin Company: Systweak Integrity Level: HIGH Description: Super PC Care Exit code: 0 Version: Super PC Care 2.2 Modules
| |||||||||||||||
| 1328 | "C:\Windows\system32\taskkill.exe" /f /im iexplore.exe /t | C:\Windows\system32\taskkill.exe | — | spc_systweak-default.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9292.tmp" "c:\Users\admin\AppData\Local\Temp\CSC9291.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1528 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7754.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7753.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
5 235
Read events
4 677
Write events
455
Delete events
103
Modification events
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: EC0C000078E27BA44F95D501 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: EF5647A6846547DE416B5AD7EA30A8C710B8D8ED5DCF553469DFF262592B7BB8 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Systweak\Super PC Care |
| Operation: | write | Name: | bldtyp |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_CURRENT_USER\Software\Systweak\Super PC Care |
| Operation: | write | Name: | bldtyp |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Systweak\Super PC Care |
| Operation: | write | Name: | AFTINSTS |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_CURRENT_USER\Software\Systweak\Super PC Care |
| Operation: | write | Name: | AFTINSTS |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spc_systweak-default_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spc_systweak-default_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3308) spc_systweak-default.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\spc_systweak-default_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
39
Suspicious files
60
Text files
89
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-A06Q2.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-PH4RN.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-QFQI9.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-HHCAB.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-0H76S.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-0L0AR.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-6S38V.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-LMKIN.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-OA03R.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | spc_systweak-default.tmp | C:\Program Files\Super PC Care\is-OSAQM.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
9
DNS requests
8
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
584 | SuperPCCare.exe | GET | 200 | 212.32.229.107:80 | http://updates.superpccare.com/update.asp?productname=superpccare¤tapplicationid=1.0.0.25025¤tdbversionid=0&firstinstall=1&utm_source=systweak&utm_campaign=default&utm_medium=newbuild&affiliateid=&x-at=&utm_content=&utm_days=0&langcode=en&productversion=1.0.0.25025&isreg=&isexpired=&macid=7268116778660445783&lip=1382422120&instdatetime=637087165624491250&productid=10895&os=Microsoft%20Windows%207%20Professional%20&ram=4.00%20GB&model=DELL&procr=Intel(R)%20Core(TM)%20i5-6400%20CPU%20@%202.70GHz&ibv=&pid=10895&iev=8&utm_updt=&utm_updatedate= | NL | text | 735 b | malicious |
584 | SuperPCCare.exe | GET | 200 | 178.79.242.0:80 | http://y31uv4ra1.vo.llnwd.net/superpccare/dbupdates/3830completedatabase.zip | DE | compressed | 15.1 Mb | malicious |
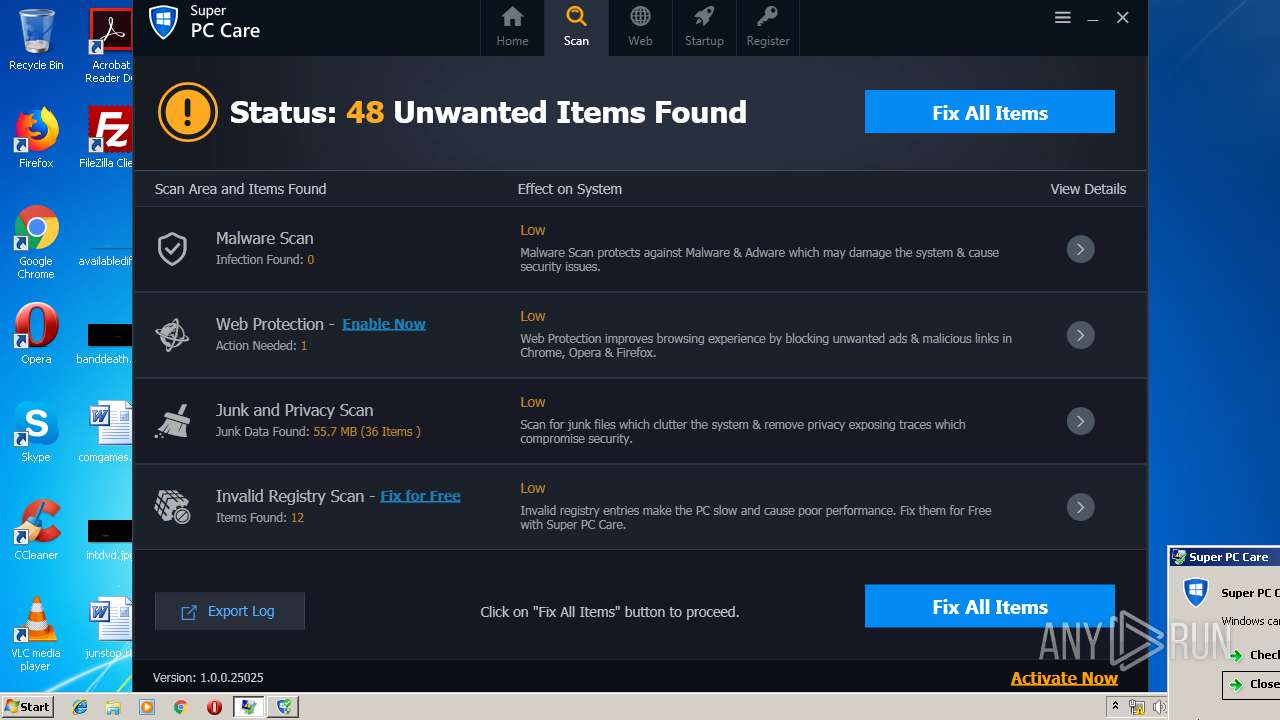
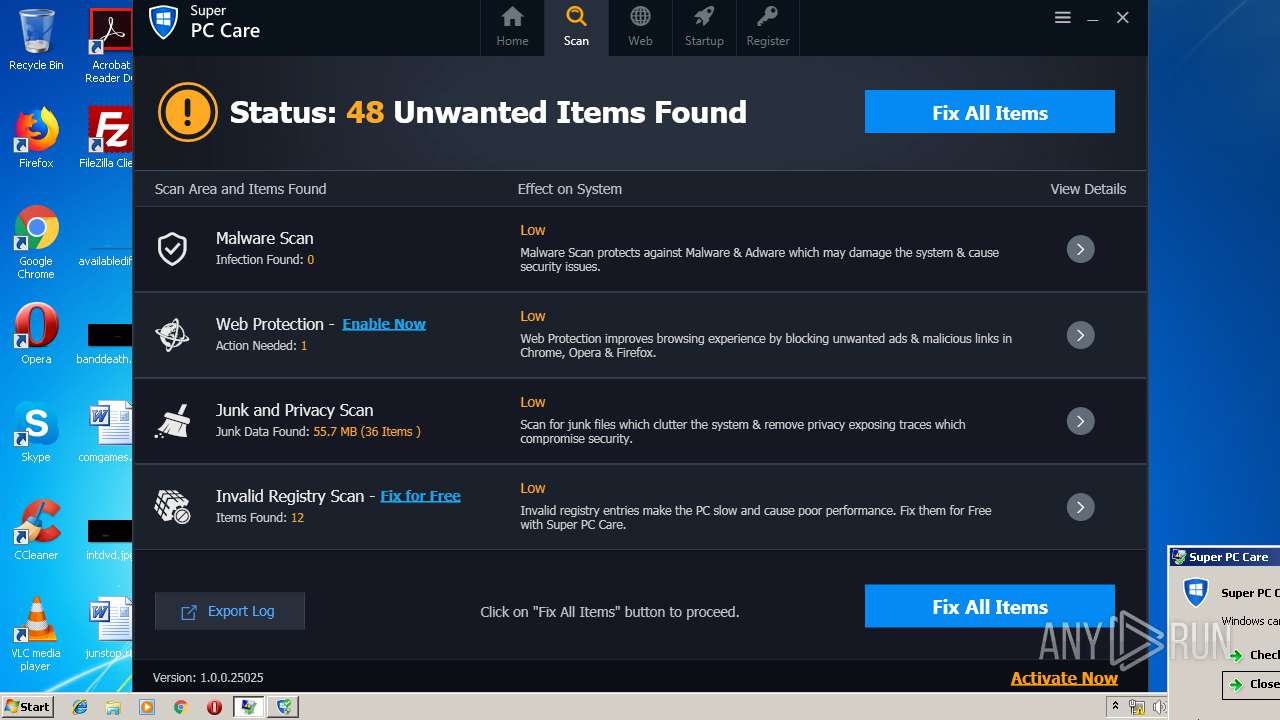
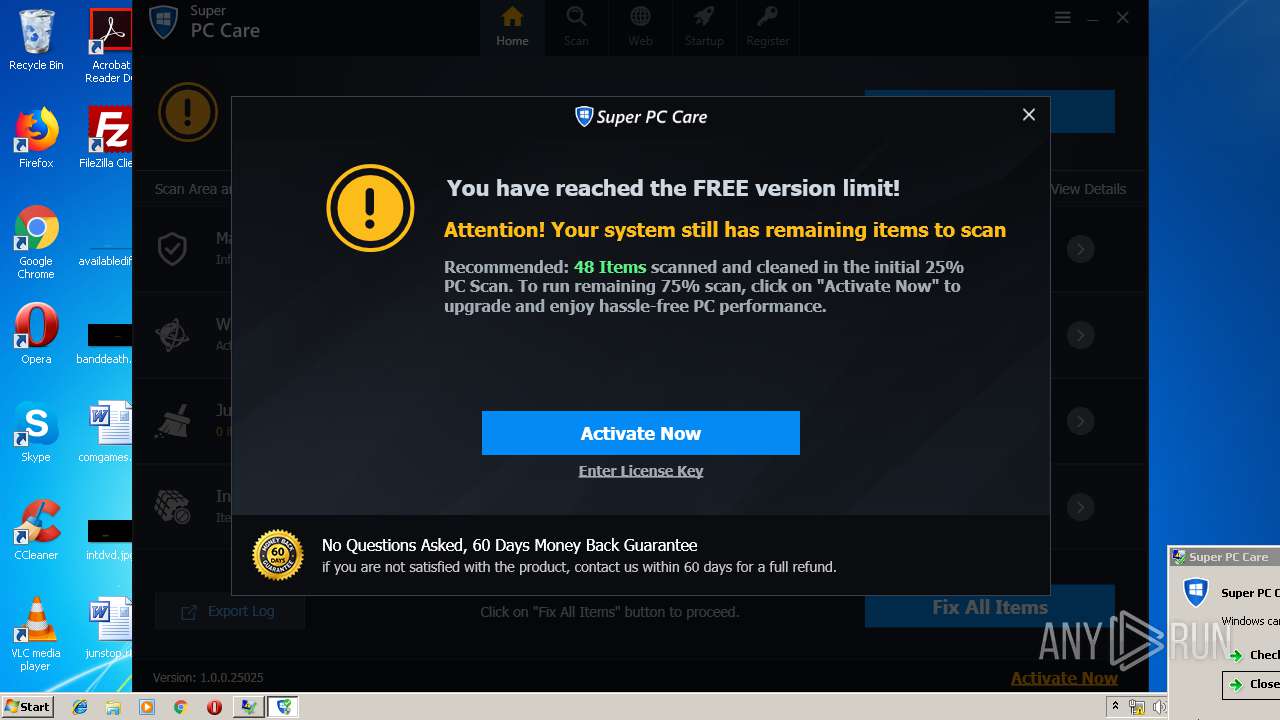
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=BtnFixAllItemsFromScannerTabTop-BTN_Click&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
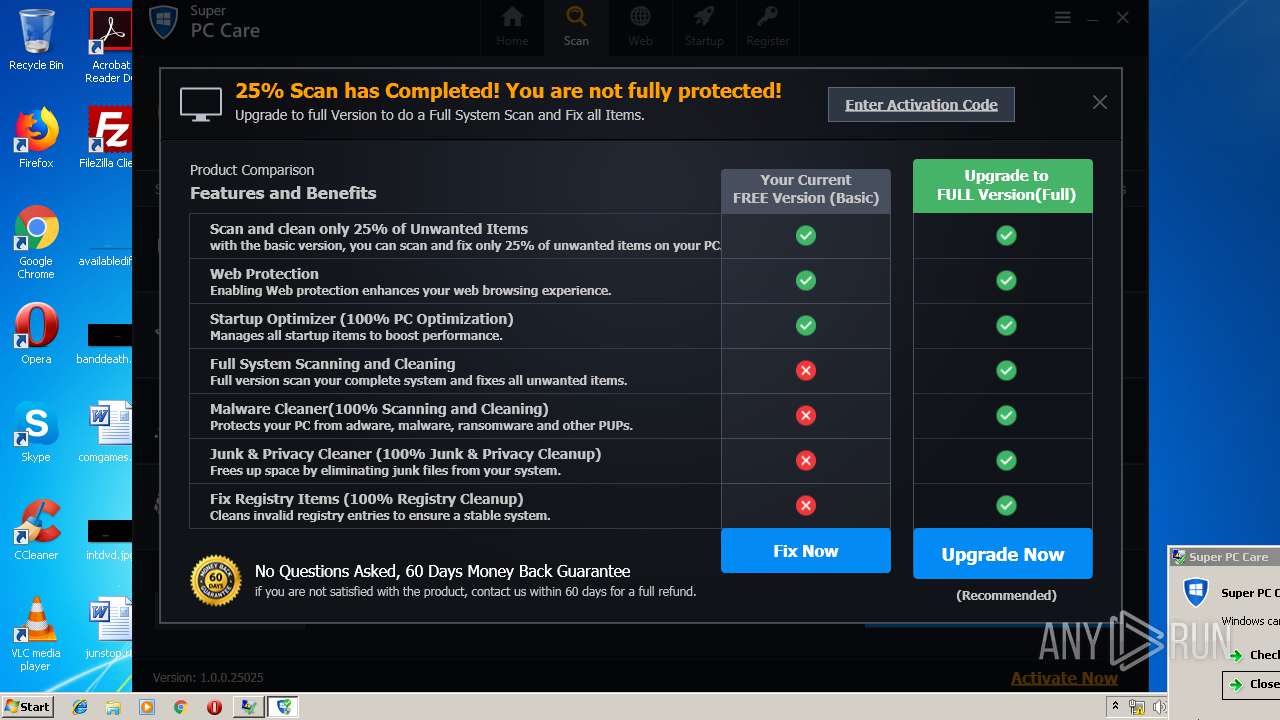
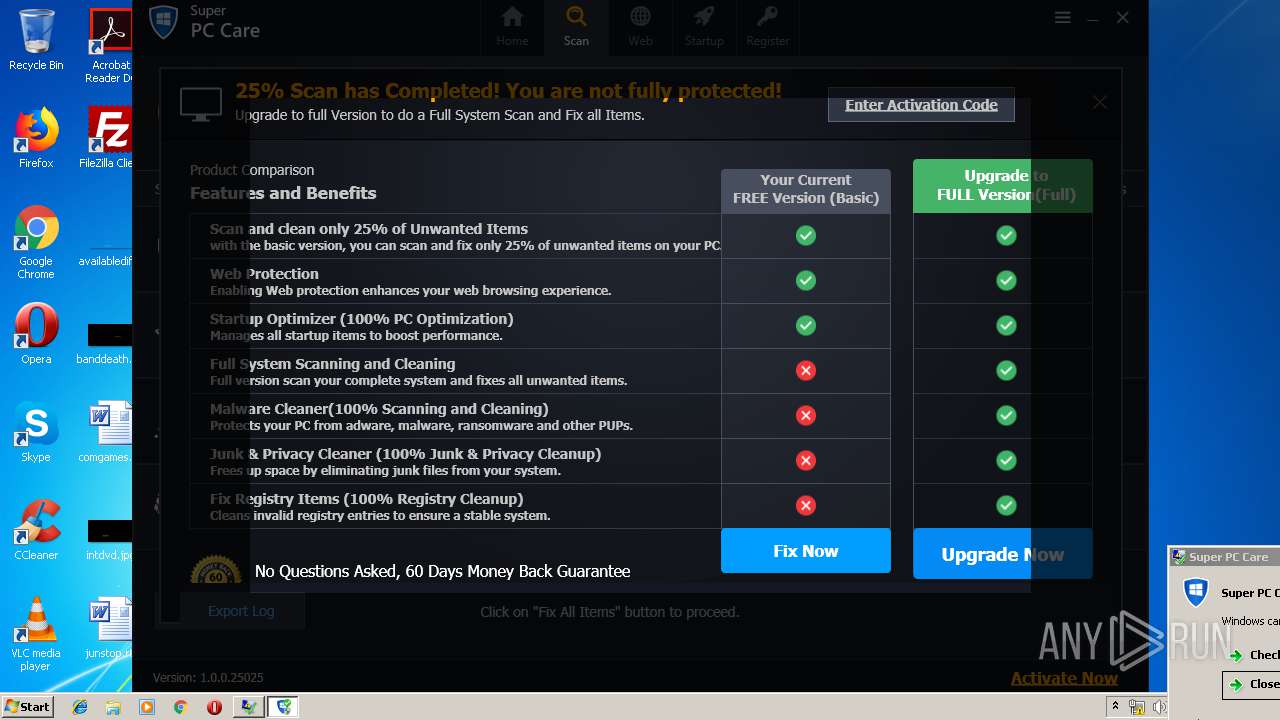
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagUpgradeNow-BTN_FixNowItems&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagCleaningProcess-Show&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagReachFreeCleanLimit-BTN_Close&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagUpgradeNow-Show&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagUpgradeNow-Show&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagReachFreeCleanLimit-Show&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
584 | SuperPCCare.exe | GET | 200 | 172.217.21.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-122429992-1&cid=52-54-00-4A-04-AF&t=event&ec=spc_winapp&ea=btnclick&el=NagUpgradeNow-BTN_Close&ev=1&cs=systweak&cm=newbuild&cn=default | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | spc_systweak-default.tmp | 212.32.229.107:443 | www.superpccare.com | LeaseWeb Netherlands B.V. | NL | malicious |
3308 | spc_systweak-default.tmp | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3308 | spc_systweak-default.tmp | 212.32.229.107:80 | www.superpccare.com | LeaseWeb Netherlands B.V. | NL | malicious |
584 | SuperPCCare.exe | 178.79.242.0:80 | y31uv4ra1.vo.llnwd.net | Limelight Networks, Inc. | DE | whitelisted |
584 | SuperPCCare.exe | 212.32.229.107:80 | www.superpccare.com | LeaseWeb Netherlands B.V. | NL | malicious |
584 | SuperPCCare.exe | 212.32.229.107:443 | www.superpccare.com | LeaseWeb Netherlands B.V. | NL | malicious |
584 | SuperPCCare.exe | 172.217.21.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.superpccare.com |
| malicious |
www.systweak.com |
| unknown |
crt.comodoca.com |
| whitelisted |
updates.superpccare.com |
| malicious |
y31uv4ra1.vo.llnwd.net |
| malicious |
www.google-analytics.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
584 | SuperPCCare.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
Process | Message |
|---|---|
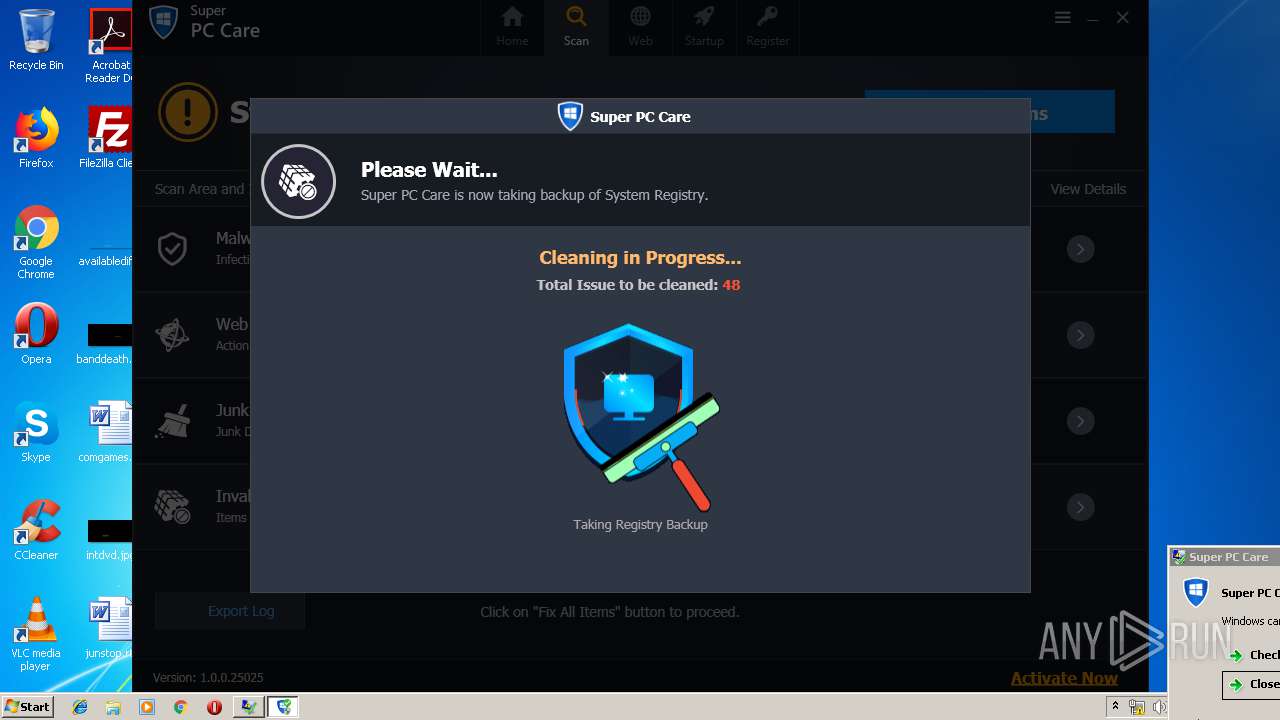
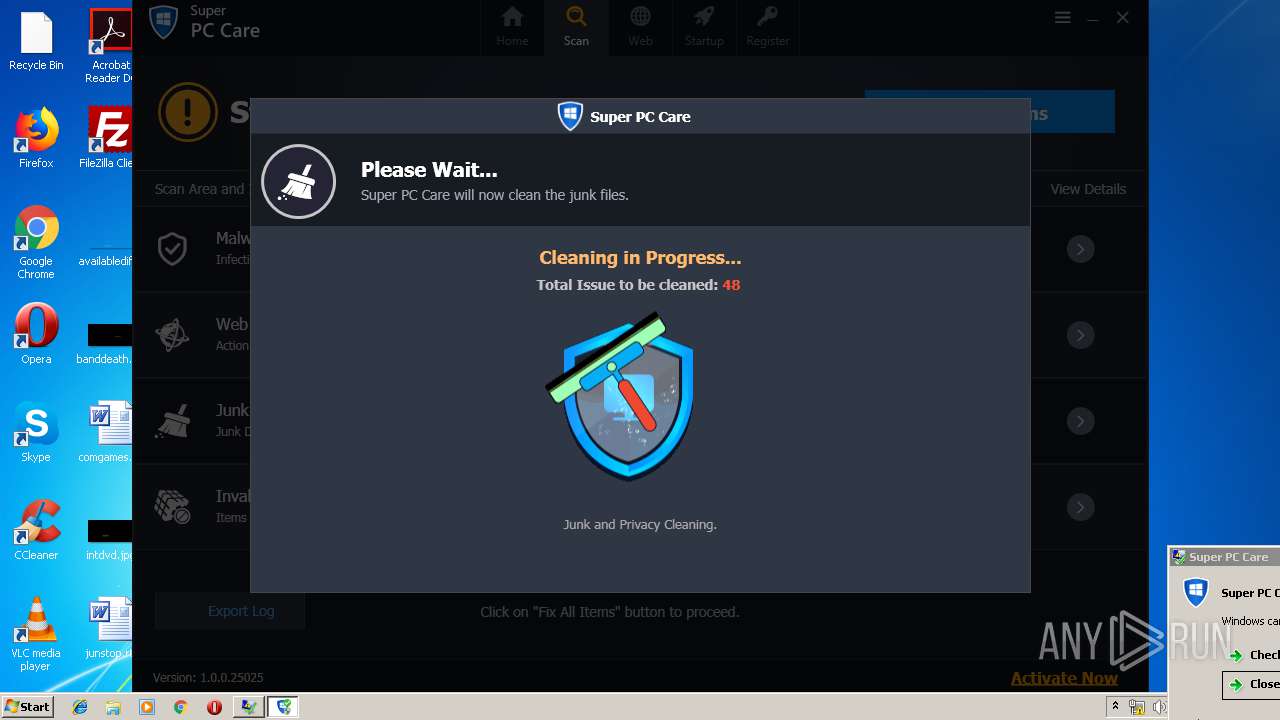
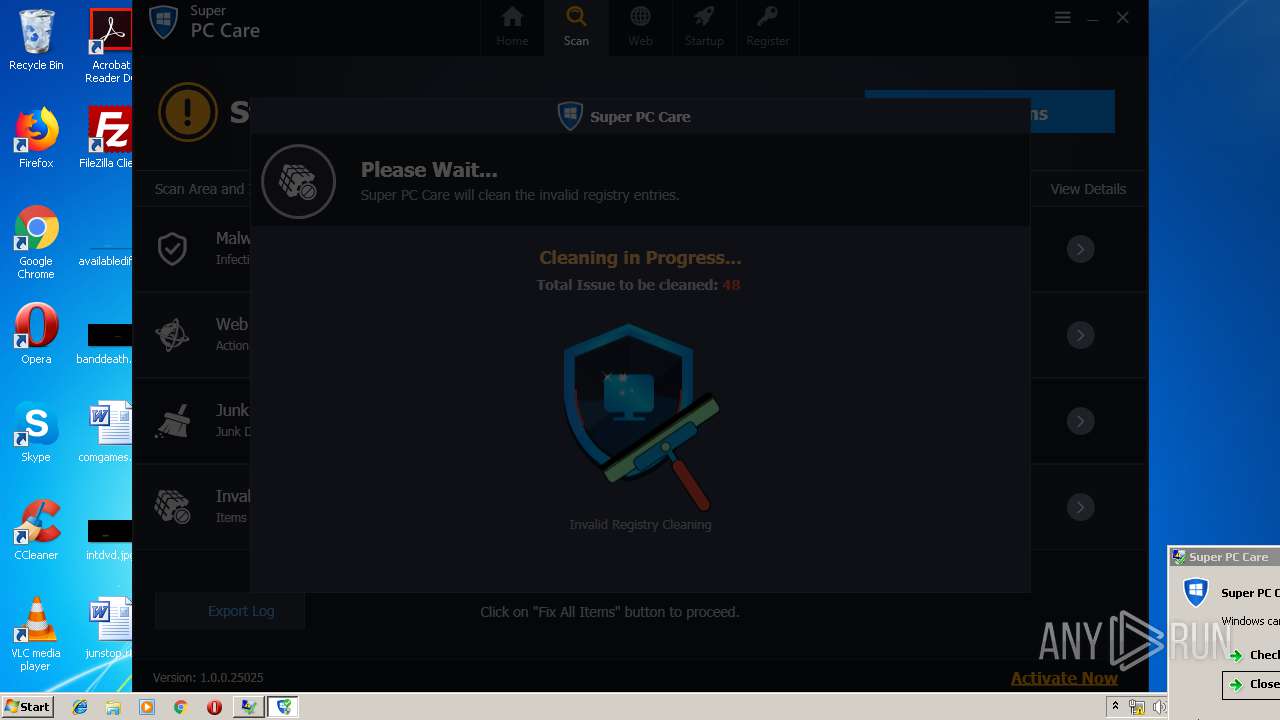
SuperPCCare.exe | STR_MSG_CLEANING_PLEASEWAIT
|
SuperPCCare.exe | STR_MSG_CLEANING_PLEASEWAIT
|
SuperPCCare.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
SuperPCCare.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
SuperPCCare.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
SuperPCCare.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
SuperPCCare.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
SuperPCCare.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
SuperPCCare.exe | System.Transactions Critical: 0 : |
SuperPCCare.exe | <TraceRecord xmlns="http://schemas.microsoft.com/2004/10/E2ETraceEvent/TraceRecord" Severity="Critical"><TraceIdentifier>http://msdn.microsoft.com/TraceCodes/System/ActivityTracing/2004/07/Reliability/Exception/Unhandled</TraceIdentifier><Description>Unhandled exception</Description><AppDomain>SuperPCCare.exe</AppDomain><Exception><ExceptionType>System.NullReferenceException, mscorlib, Version=2.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089</ExceptionType><Message>Object reference not set to an instance of an object.</Message><StackTrace> at Ge.Xg.Rq45(bL )
at gw.P9.mq4Q(bL , eN , IEnumerable`1 , IEnumerable`1 , IEnumerable`1 , IEnumerable`1 )
at Hd.cU.&lt;&gt;c__DisplayClass9_0.&lt;IsVirtualMachine&gt;b__2(DO c)
at System.Linq.Enumerable.FirstOrDefault[TSource](IEnumerable`1 source, Func`2 predicate)
at Hd.cU.JM(String&amp; )
at yH3.kHn.e1l()
at yH3.kHn.y19(Boolean )
at MWS.yWT.&lt;&gt;c.&lt;.ctor&gt;b__100_1()
at System.Threading.ThreadHelper.ThreadStart_Context(Object state)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at System.Threading.ThreadHelper.ThreadStart()</StackTrace><ExceptionString>System.NullReferenceException: Object reference not set to an instance of an object.
at Ge.Xg.Rq45(bL )
at gw.P9.mq4Q(bL , eN , IEnumerable`1 , IEnumerable`1 , IEnumerable`1 , IEnumerable`1 )
at Hd.cU.&lt;&gt;c__DisplayClass9_0.&lt;IsVirtualMachine&gt;b__2(DO c)
at System.Linq.Enumerable.FirstOrDefault[TSource](IEnumerable`1 source, Func`2 predicate)
at Hd.cU.JM(String&amp; )
at yH3.kHn.e1l()
at yH3.kHn.y19(Boolean )
at MWS.yWT.&lt;&gt;c.&lt;.ctor&gt;b__100_1()
at System.Threading.ThreadHelper.ThreadStart_Context(Object state)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at System.Threading.ThreadHelper.ThreadStart()</ExceptionString></Exception></TraceRecord>
|