| download: | valvoline-oil-change-prices-2221.php |
| Full analysis: | https://app.any.run/tasks/6b5e5447-da0f-4165-bf57-3b72251c9b10 |
| Verdict: | No threats detected |
| Analysis date: | June 20, 2019, 13:18:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | B79965DA3F5458E982FA1BDBC5DC03B0 |
| SHA1: | C998F7997595F6DDFFAD8A5554C137A7F2DFF2B1 |
| SHA256: | 2885A98338C9929D9897E52FF52439AFC3E51420AB1E6901898EE59CB28C5C2C |
| SSDEEP: | 192:/iWoGosO6jl3zWUanFlL6dqjzne5NsgwsUERw88w:zorp6jljWFqsjy/zBB/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
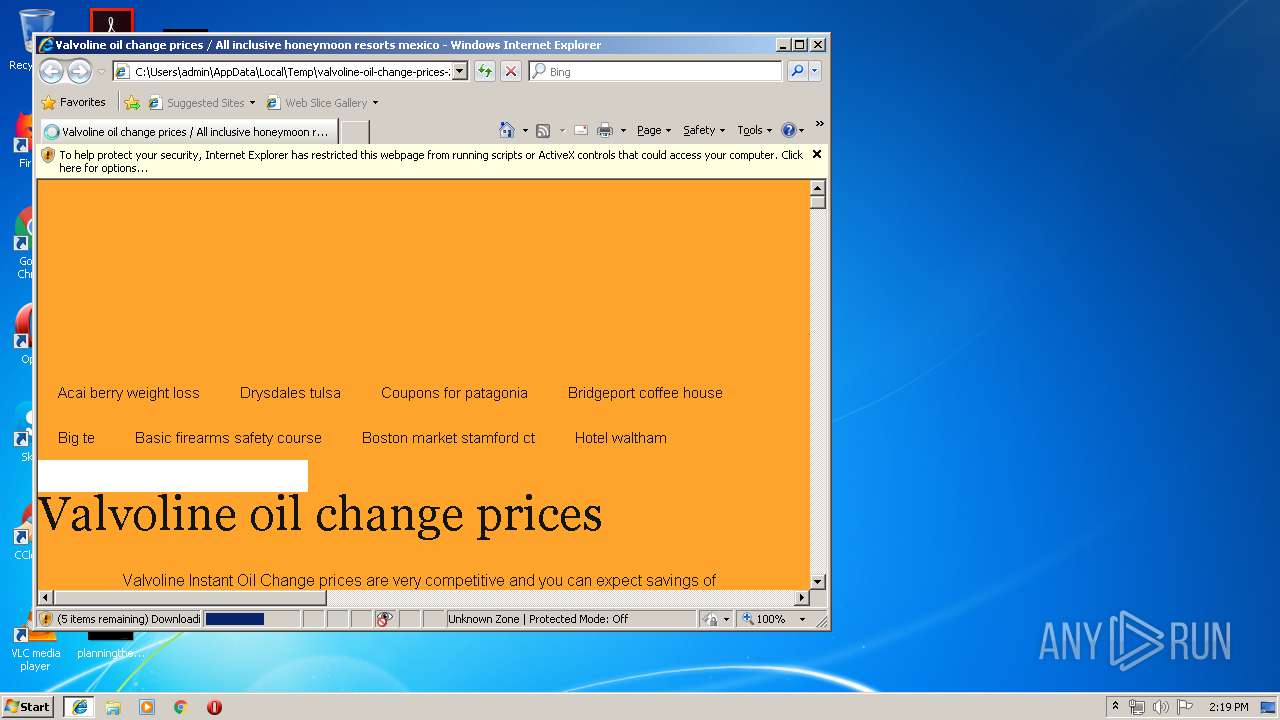
Changes internet zones settings
- iexplore.exe (PID: 3604)
Reads internet explorer settings
- iexplore.exe (PID: 644)
Application launched itself
- iexplore.exe (PID: 3604)
Reads settings of System Certificates
- iexplore.exe (PID: 644)
Creates files in the user directory
- iexplore.exe (PID: 644)
Changes settings of System certificates
- iexplore.exe (PID: 644)
Adds / modifies Windows certificates
- iexplore.exe (PID: 644)
Reads Internet Cache Settings
- iexplore.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | width=device-width |
|---|---|
| Title: | Valvoline oil change prices / All inclusive honeymoon resorts mexico |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3604 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\valvoline-oil-change-prices-2221.php.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
487
Read events
394
Write events
86
Delete events
7
Modification events
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F79255FB-935D-11E9-A370-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3604) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070600040014000D0013000200C200 | |||
Executable files
0
Suspicious files
0
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3604 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3604 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
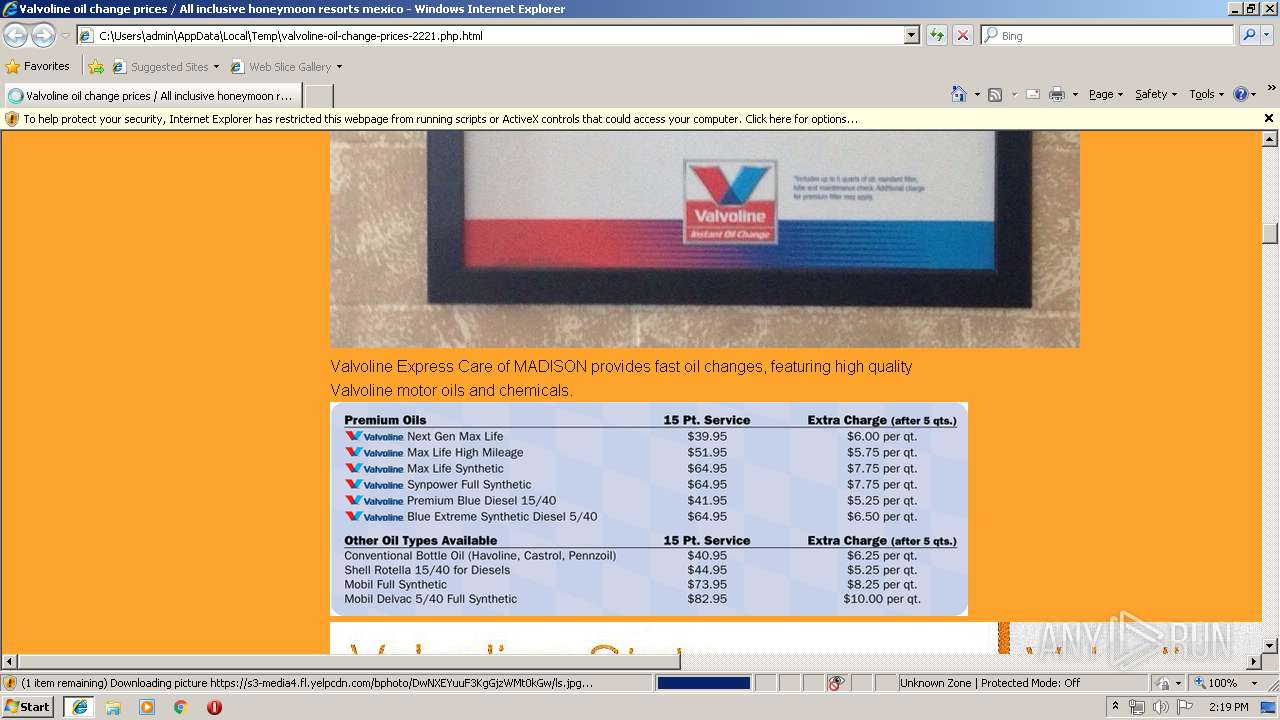
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\valvoline-premium-oil-cost[1].png | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\damoxof[1].css | text | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\header[1].jpg | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ls[1].jpg | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\americas-tire-company-printable-coupon-apple-store-student-deals-for-valvoline-instant-oil-change-coupons-printable[1].jpg | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\797978-c[1].jpg | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\valvoline-oil-change[1].jpg | image | |
MD5:— | SHA256:— | |||
| 644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\valvoline-oil-180x180[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
28
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
644 | iexplore.exe | GET | 404 | 104.28.10.14:80 | http://www.cewevks.ga/genericons.eot)%20format(%22embedded-opentype%22 | US | html | 271 b | suspicious |
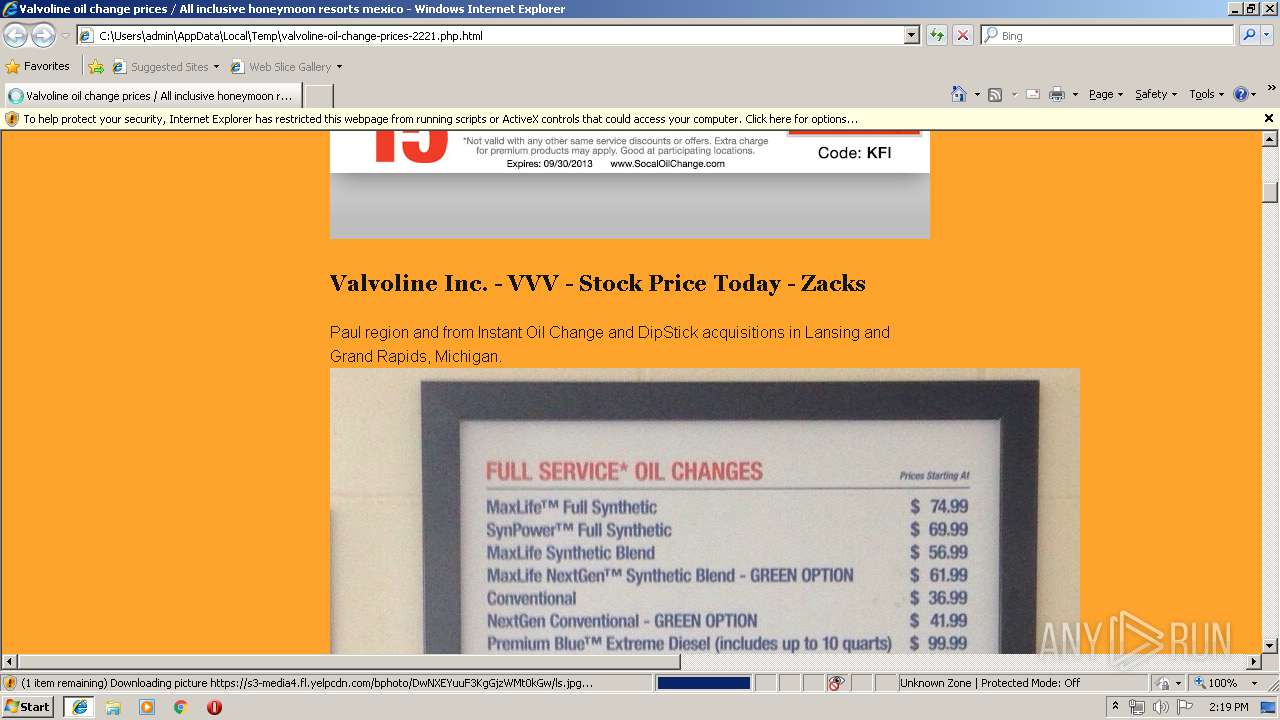
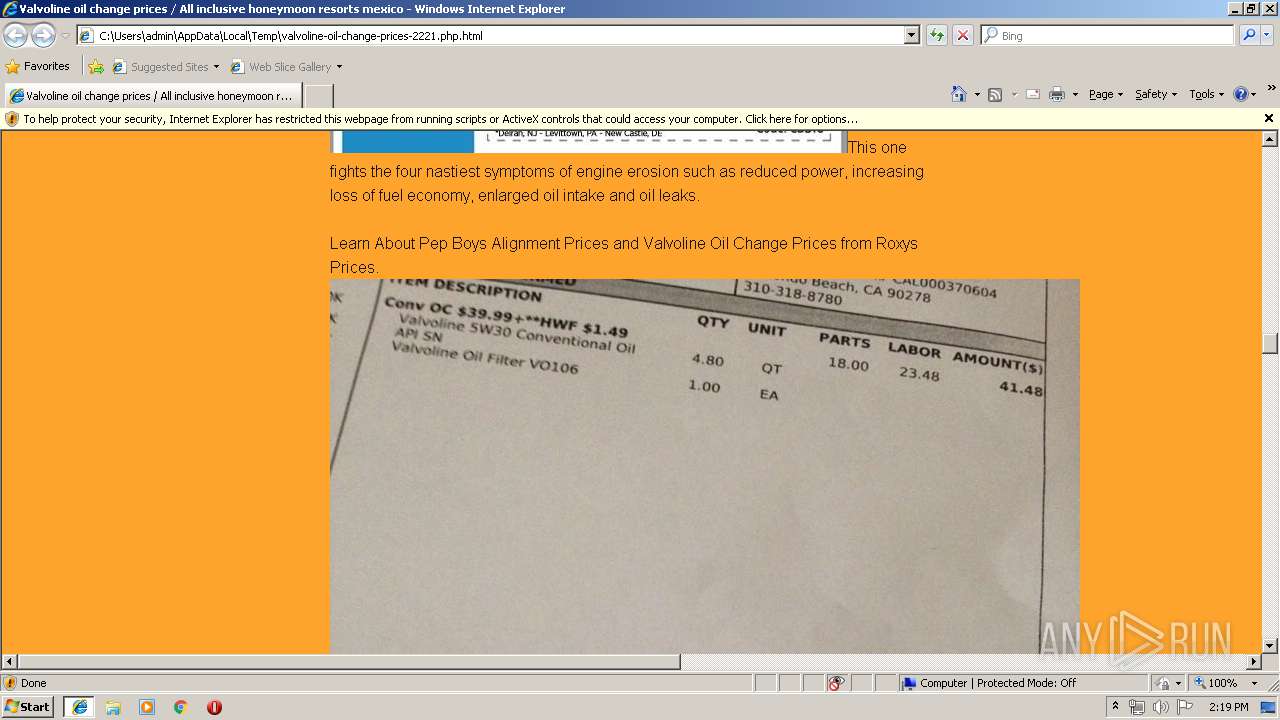
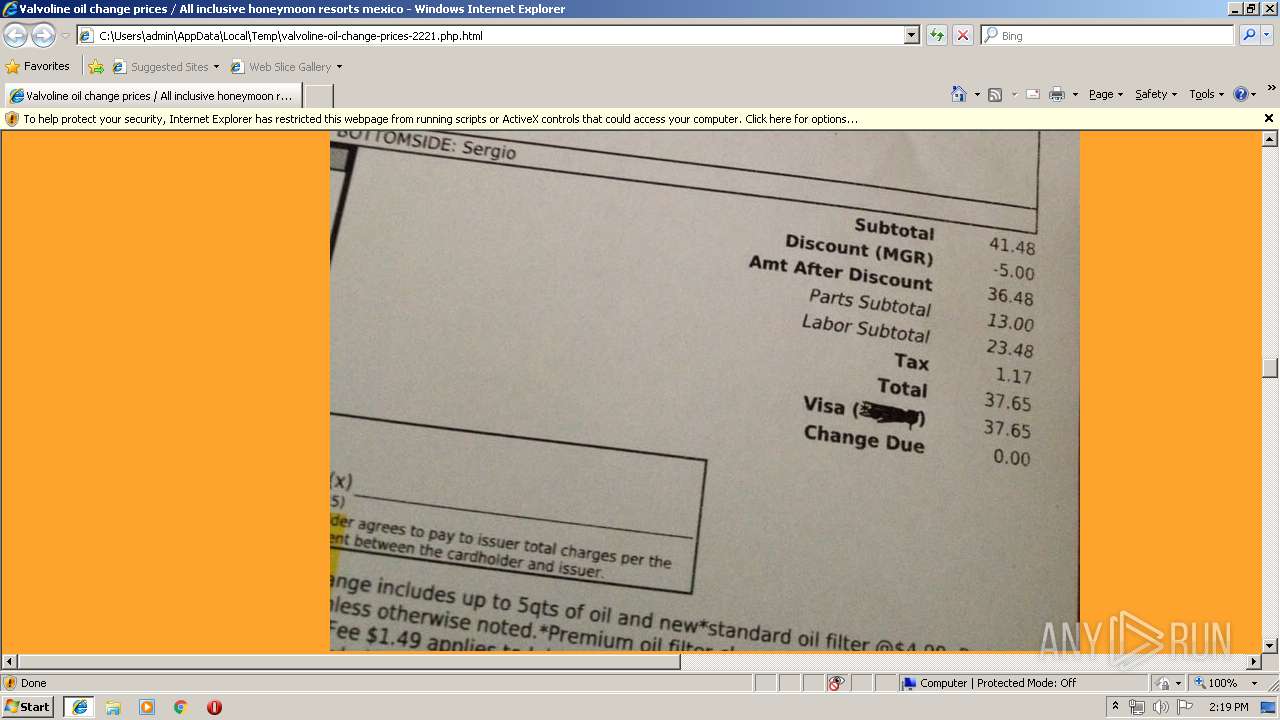
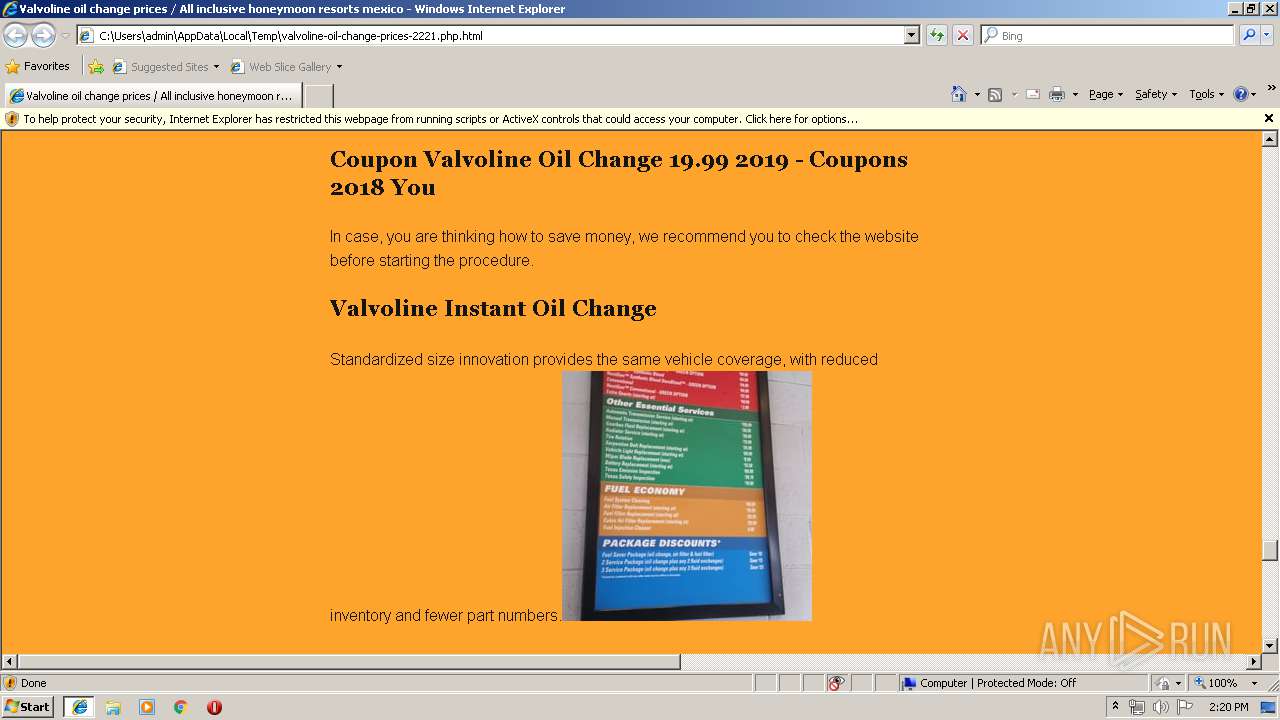
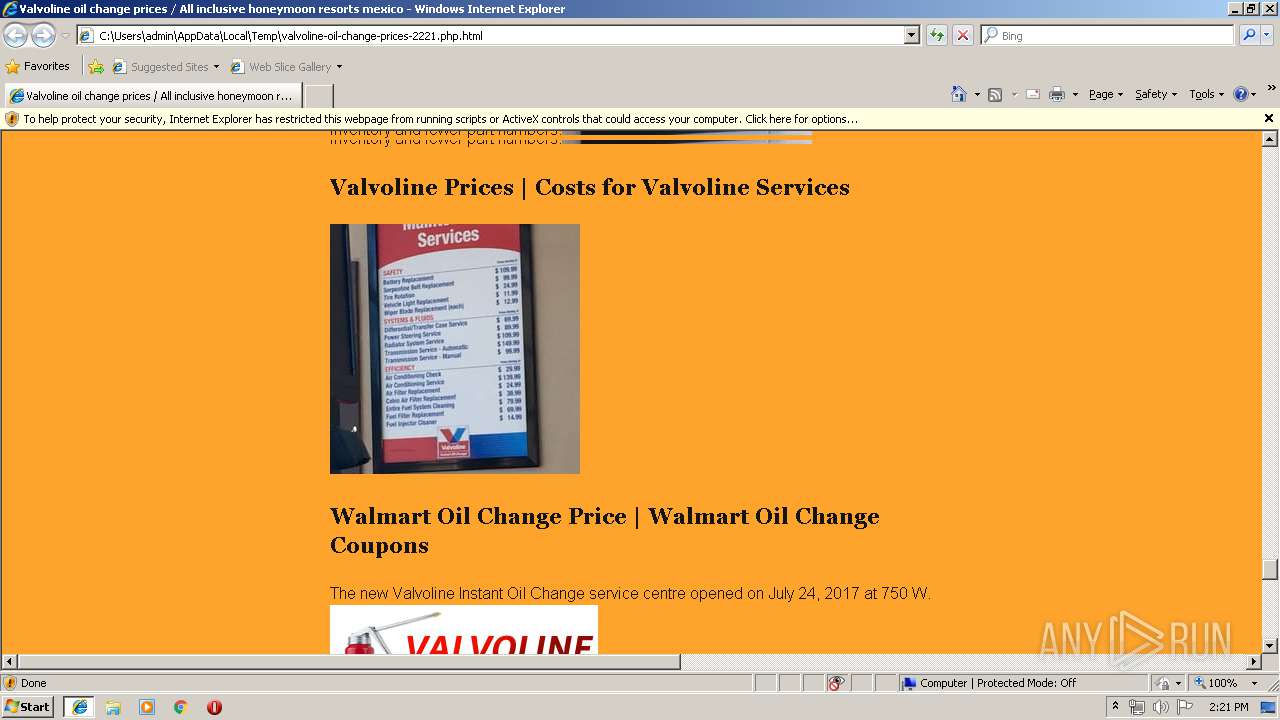
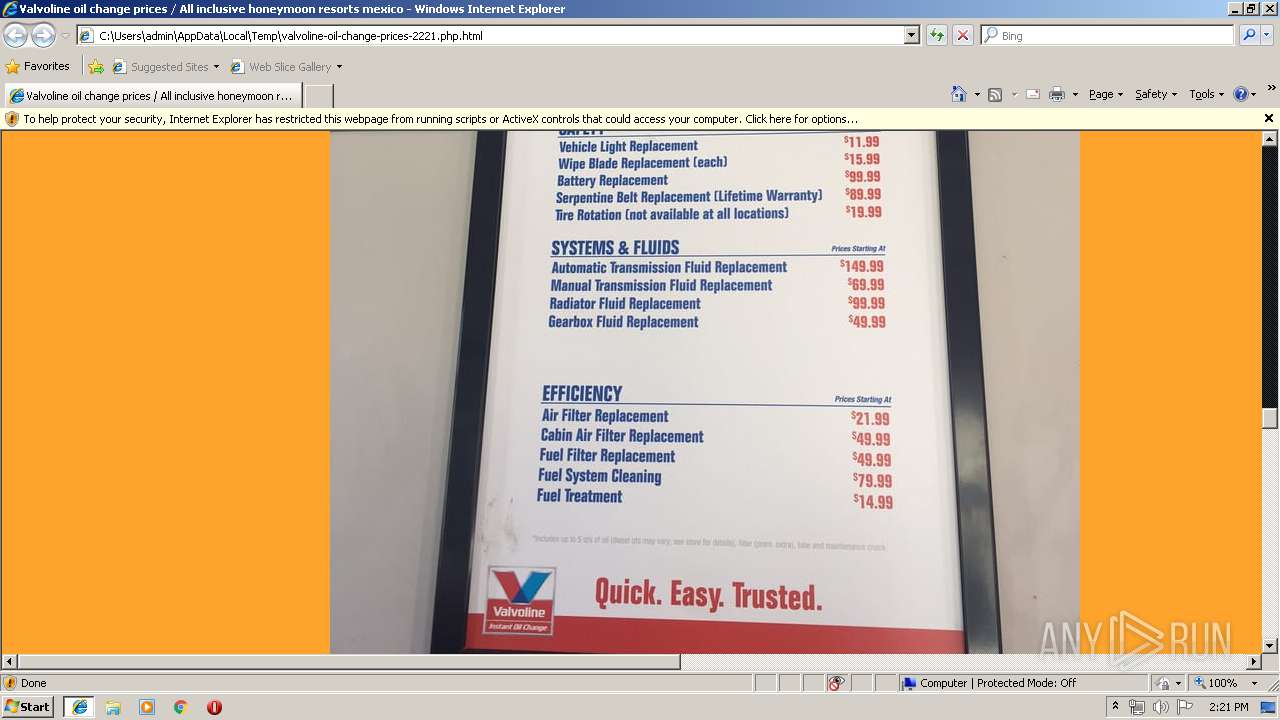
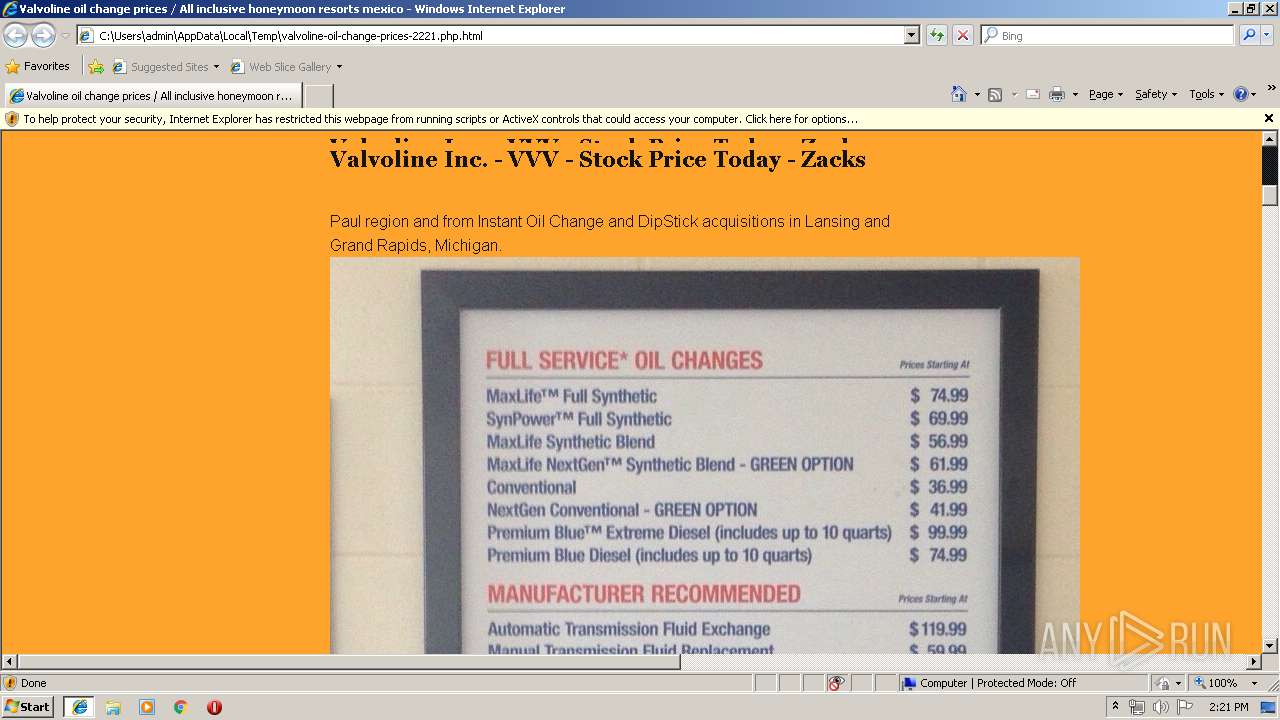
644 | iexplore.exe | GET | 200 | 192.186.235.198:80 | http://oilchangecouponspro.com/wp-content/gallery/valvoline-prices/valvoline-instant-oil-change-prices.jpg | US | image | 136 Kb | unknown |
644 | iexplore.exe | GET | 200 | 104.28.10.14:80 | http://www.cewevks.ga/damoxof.css | US | text | 11.7 Kb | suspicious |
644 | iexplore.exe | GET | 200 | 192.186.235.198:80 | http://oilchangecouponspro.com/wp-content/gallery/valvoline-prices/valvoline-premium-oil-cost.png | US | image | 49.4 Kb | unknown |
644 | iexplore.exe | GET | 200 | 66.254.66.41:80 | http://triplenetzerodebt.com/wp-content/uploads/Valvoline-Stats1.jpg | US | image | 2.22 Mb | unknown |
644 | iexplore.exe | GET | 200 | 151.101.2.2:80 | http://s3-media2.fl.yelpcdn.com/bphoto/qXHi-mZIEkrMlG4oxPty0Q/ls.jpg | US | image | 7.29 Kb | whitelisted |
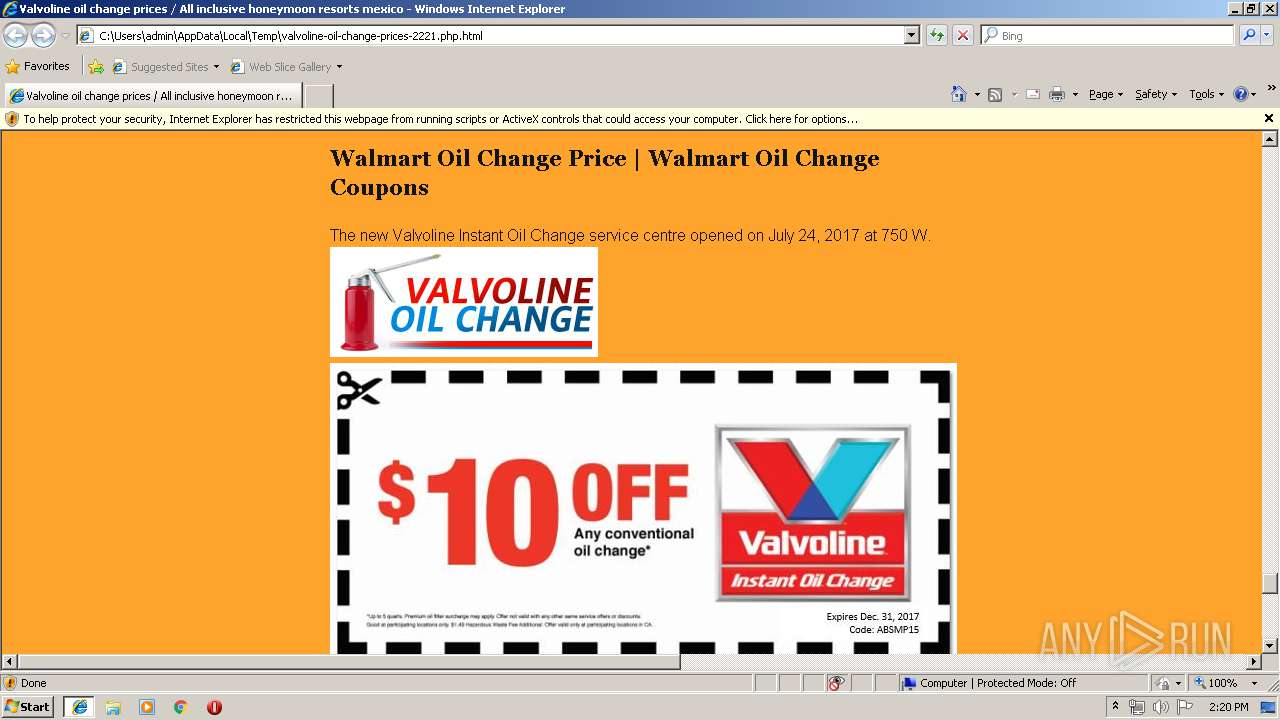
644 | iexplore.exe | GET | 200 | 167.86.114.70:80 | http://www.freepsychiclovereadings.com/wp-content/uploads/2018/01/americas-tire-company-printable-coupon-apple-store-student-deals-for-valvoline-instant-oil-change-coupons-printable.jpg | US | image | 144 Kb | unknown |
644 | iexplore.exe | GET | 301 | 199.188.205.55:80 | http://cheapoilchangecoupons.com/wp-content/uploads/2012/02/valvoline-oil-change-coupon-296x300.jpg | US | html | 308 b | unknown |
644 | iexplore.exe | GET | 404 | 104.28.10.14:80 | http://www.cewevks.ga/1e.png | US | html | 236 b | suspicious |
644 | iexplore.exe | GET | 404 | 104.28.10.14:80 | http://www.cewevks.ga/undefined)%20format(%22woff%22),%20url(genericons.ttf)%20format(%22truetype%22),%20url(genericons.svg)%20format(%22svg%22 | US | html | 297 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
644 | iexplore.exe | 104.28.10.14:80 | www.cewevks.ga | Cloudflare Inc | US | shared |
4 | System | 205.185.208.52:445 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
644 | iexplore.exe | 66.254.66.41:80 | triplenetzerodebt.com | PixelGate | US | unknown |
644 | iexplore.exe | 192.186.235.198:80 | oilchangecouponspro.com | GoDaddy.com, LLC | US | unknown |
— | — | 205.185.208.52:137 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
644 | iexplore.exe | 70.32.90.50:80 | valvoilchange.com | Media Temple, Inc. | US | unknown |
644 | iexplore.exe | 151.101.2.2:443 | s3-media2.fl.yelpcdn.com | Fastly | US | shared |
644 | iexplore.exe | 151.101.2.2:80 | s3-media2.fl.yelpcdn.com | Fastly | US | shared |
644 | iexplore.exe | 167.86.114.70:80 | www.freepsychiclovereadings.com | Arapahoe School District #6 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
code.jquery.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.cewevks.ga |
| suspicious |
couponscodesblog.com |
| unknown |
oilchangecouponspro.com |
| unknown |
triplenetzerodebt.com |
| unknown |
www.autoserviceprices.com |
| unknown |
www.freepsychiclovereadings.com |
| unknown |
cheapoilchangecoupons.com |
| unknown |
s3-media2.fl.yelpcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |