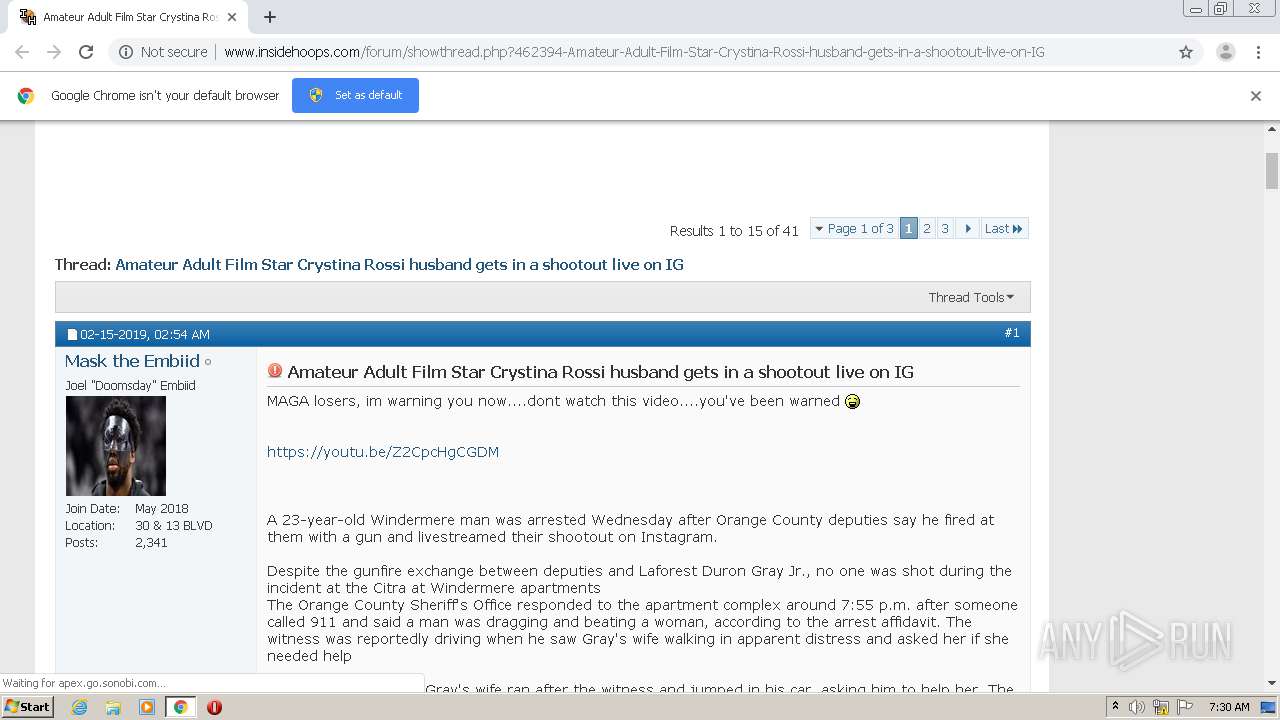
| URL: | http://www.insidehoops.com/forum/showthread.php?462394-Amateur-Adult-Film-Star-Crystina-Rossi-husband-gets-in-a-shootout-live-on-IG |
| Full analysis: | https://app.any.run/tasks/0544207e-97cc-49c3-b239-993007d96ac9 |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2020, 07:29:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C890E5CD355BFBDEF09043E31C11DE25 |
| SHA1: | 33438965B2E5E694CBD1C4A6836CAB6C6C425667 |
| SHA256: | 286E858E52B5D53F411DBC469BAC0397C5813C635FB8DE432BE03561D34CC26B |
| SSDEEP: | 3:N1KJS4NMqzHKzu/9aXWgDXItgjIAQwEjJVHiBID91WNKRQRICiE:Cc49d9cWg8tgjbQRJgID7RRQulE |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2796)
Reads settings of System Certificates
- chrome.exe (PID: 988)
Changes settings of System certificates
- chrome.exe (PID: 988)
Reads the hosts file
- chrome.exe (PID: 2796)
- chrome.exe (PID: 988)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
58
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3747635760617054584 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17583052375047025926 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2616 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=313778531726360176 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10090450722008376352 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17069245067295746765 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9795235036324968988 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17803729214436658591 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9247645767758577286 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2232741960730429025,6986497162080659407,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5921542724191280539 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
633
Read events
535
Write events
95
Delete events
3
Modification events
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2796-13251454189613250 |
Value: 259 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2796-13251454189613250 |
Value: 259 | |||
Executable files
0
Suspicious files
114
Text files
70
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC893EE-AEC.pma | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dec62ea1-b45d-442b-802f-4f82a140bbb8.tmp | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF18d3a6.TMP | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18d358.TMP | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d5aa.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
511
DNS requests
231
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
988 | chrome.exe | GET | 301 | 13.224.194.69:80 | http://i65.tinypic.com/281hgrr.png | US | — | — | malicious |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/image.php?s=488730e5a069998f890f1a9e886c1bdd&u=461060&dateline=1576756686 | US | image | 3.70 Kb | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/showthread.php?462394-Amateur-Adult-Film-Star-Crystina-Rossi-husband-gets-in-a-shootout-live-on-IG | US | html | 17.6 Kb | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/css.php?styleid=49&langid=1&d=1606290227&td=ltr&sheet=additional.css | US | text | 43.9 Kb | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/insidehoops_april2007b.jpg | US | image | 19.6 Kb | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/css.php?styleid=49&langid=1&d=1606290227&td=ltr&sheet=bbcode.css,editor.css,popupmenu.css,reset-fonts.css,vbulletin.css,vbulletin-chrome.css,vbulletin-formcontrols.css, | US | text | 82.7 Kb | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/css.php?styleid=49&langid=1&d=1606290227&td=ltr&sheet=toolsmenu.css,postlist.css,showthread.css,postbit.css,options.css,attachment.css,poll.css,lightbox.css | US | text | 43.9 Kb | unknown |
988 | chrome.exe | GET | 200 | 104.18.5.23:80 | http://tags.expo9.exponential.com/tags/InsideHoopscom/ROS/tags.js | US | text | 13.6 Kb | whitelisted |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/images/icons/icon4.png | US | image | 752 b | unknown |
988 | chrome.exe | GET | 200 | 207.244.125.227:80 | http://www.insidehoops.com/forum/clientscript/vbulletin-core.js?v=425 | US | text | 50.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
988 | chrome.exe | 207.244.125.227:80 | www.insidehoops.com | Leaseweb USA, Inc. | US | unknown |
988 | chrome.exe | 104.18.5.23:80 | tags.expo9.exponential.com | Cloudflare Inc | US | unknown |
988 | chrome.exe | 151.101.14.2:443 | media.giphy.com | Fastly | US | unknown |
988 | chrome.exe | 104.26.14.238:80 | services.vlitag.com | Cloudflare Inc | US | suspicious |
988 | chrome.exe | 68.232.35.237:443 | ih1.redbubble.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
988 | chrome.exe | 172.217.22.66:80 | www.googletagservices.com | Google Inc. | US | whitelisted |
988 | chrome.exe | 216.58.212.162:443 | — | Google Inc. | US | whitelisted |
988 | chrome.exe | 13.224.194.69:80 | i65.tinypic.com | — | US | suspicious |
988 | chrome.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
988 | chrome.exe | 64.233.165.155:443 | adservice.google.ie | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.insidehoops.com |
| unknown |
accounts.google.com |
| shared |
tags.expo9.exponential.com |
| whitelisted |
services.vlitag.com |
| shared |
media.giphy.com |
| whitelisted |
ih1.redbubble.net |
| unknown |
i65.tinypic.com |
| malicious |
www.googletagservices.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
tinypic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
988 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |