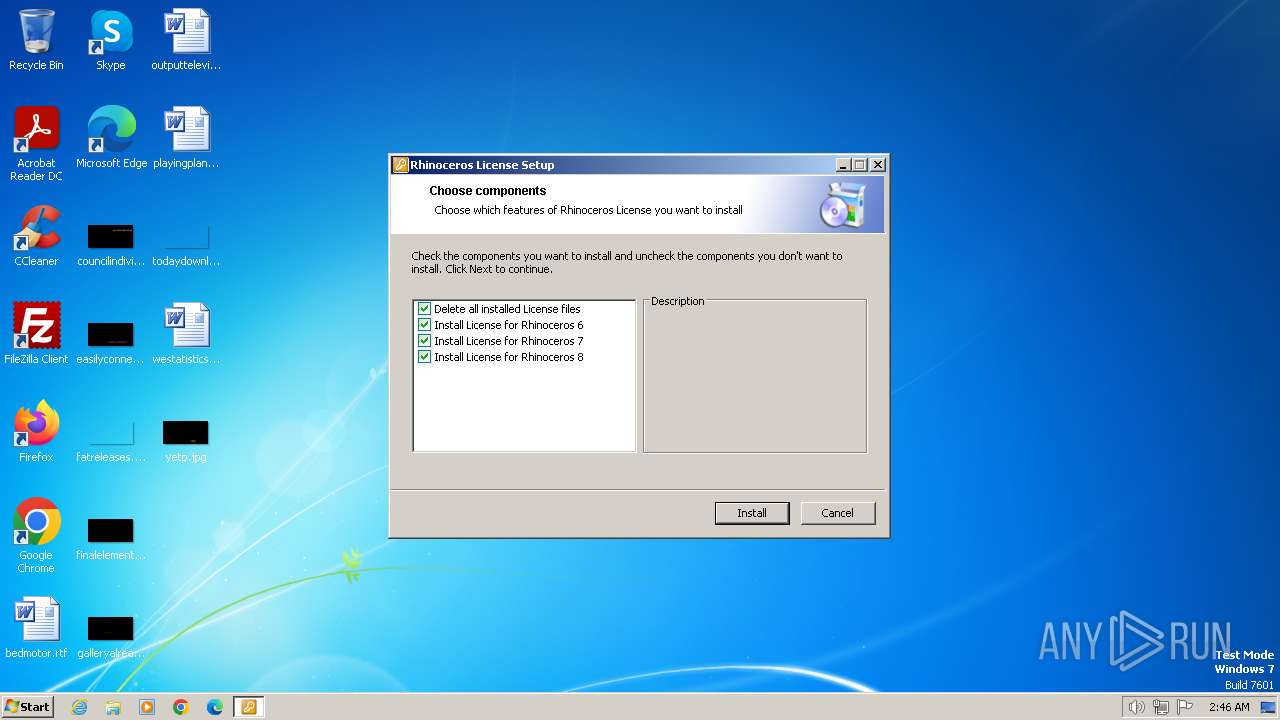
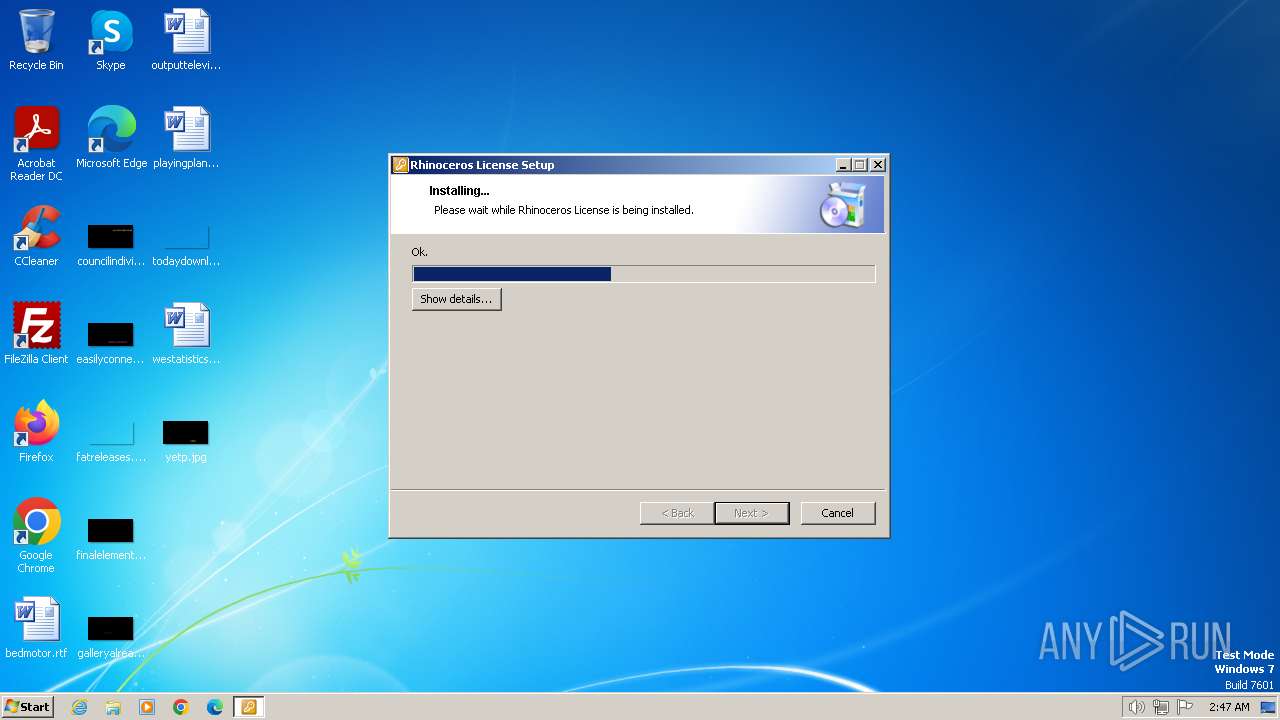
| File name: | Rhinoceros Universal License Patch.exe |
| Full analysis: | https://app.any.run/tasks/4f8a8202-b0c6-48e4-a787-9f270dbc6db1 |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2024, 02:46:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A0797366897CAAD2F6915F821F390997 |
| SHA1: | 146D95D5ADFE6A0601A89AAC3489636B3ED7EE29 |
| SHA256: | 285B0961CEEE6ADBA7780E9FBD78F2EACEB1C3821112A45E19E8F3DA21EACF15 |
| SSDEEP: | 98304:MH8iylH+6ez3fElXYD8xfvNReZZ1Gc6ez3fElXYD8xfvNReZC++alXez3fElXYDk:+4ad |
MALICIOUS
Drops the executable file immediately after the start
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
SUSPICIOUS
Reads the Internet Settings
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
Reads security settings of Internet Explorer
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
Executing commands from ".cmd" file
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
Starts SC.EXE for service management
- cmd.exe (PID: 3304)
- cmd.exe (PID: 2104)
Executable content was dropped or overwritten
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 3304)
- cmd.exe (PID: 2104)
Starts itself from another location
- Rhinoceros Universal License Patch.exe (PID: 3660)
Starts CMD.EXE for commands execution
- Installing License for Rhinoceros 6.exe (PID: 3492)
- Rhinoceros Universal License Patch.exe (PID: 3660)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3304)
- cmd.exe (PID: 2104)
INFO
Reads the computer name
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
- Installing Rhinoceros 6 License.exe (PID: 1540)
Create files in a temporary directory
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
Checks supported languages
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing License for Rhinoceros 6.exe (PID: 3492)
- Installing Rhinoceros 6 License.exe (PID: 1540)
Reads the machine GUID from the registry
- Installing License for Rhinoceros 6.exe (PID: 3492)
- Rhinoceros Universal License Patch.exe (PID: 3660)
- Installing Rhinoceros 6 License.exe (PID: 1540)
Creates files in the program directory
- Installing Rhinoceros 6 License.exe (PID: 1540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:24 10:55:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 453120 |
| InitializedDataSize: | 327680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49ef7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Robert McNeel & Associates |
| FileDescription: | - |
| FileVersion: | 1.0.0 |
| InternalName: | SibInstaller.exe |
| LegalCopyright: | Robert McNeel & Associates |
| OriginalFileName: | SibInstaller.exe |
| ProductName: | Rhinoceros License |
| ProductVersion: | 1.0.0 |
Total processes
116
Monitored processes
76
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | netsh advfirewall firewall add rule name="Rhino 5" dir=in program="C:\Program Files\Rhinoceros 5 (64-bit)\System\Rhino.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | sc config "McNeelUpdate" start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | netsh advfirewall firewall delete rule name=all program="C:\Program Files\Rhino 6\System\Yak.exe" | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | sc config "McNeelUpdate" start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | netsh advfirewall firewall delete rule name=all program="C:\Program Files\Rhinoceros 5 (64-bit)\System\RmaErrorReporting.exe" | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | netsh advfirewall firewall add rule name="Rhino 6" dir=in program="C:\Program Files\Rhino 6\System\Rhino.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | netsh advfirewall firewall add rule name="Rhino 5" dir=in program="C:\Program Files\Rhinoceros 5 (64-bit)\System\Rhino.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | netsh advfirewall firewall add rule name="Rhino 7" dir=out program="C:\Program Files\Rhino 7\System\Rhino.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | netsh advfirewall firewall add rule name="Rhino 6 RmaErrorReporting" dir=out program="C:\Program Files\Rhino 6\System\RmaErrorReporting.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1112 | netsh advfirewall firewall add rule name="Rhino 6 RmaErrorReporting" dir=in program="C:\Program Files\Rhino 6\System\RmaErrorReporting.exe" profile=any action=block | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
44 064
Read events
40 996
Write events
3 068
Delete events
0
Modification events
| (PID) Process: | (3660) Rhinoceros Universal License Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3660) Rhinoceros Universal License Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3660) Rhinoceros Universal License Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3660) Rhinoceros Universal License Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (4008) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
Executable files
9
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | Installing License for Rhinoceros 6.exe | C:\Users\admin\AppData\Local\Temp\sibAA16.tmp\SibCa.dll | executable | |
MD5:D6E5AB47E04CDE333586F6374E9FE12B | SHA256:A897064E82AC7D6FDAEF0C2B06089EDB6BA9FBF955B2B2F483AB938EBE081921 | |||
| 3660 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibF3F5.tmp\SibCa.dll | executable | |
MD5:ADA59857C772C7D0C30E514BC090C9AF | SHA256:DE7827598A92D996B24AA1E104DA544ECC55EB6BE947736B8E194C48AD6B3D33 | |||
| 3660 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibF3F5.tmp\3\Installing License for Rhinoceros 6.exe | executable | |
MD5:D78D0319AEFEBA532C3015EF759E43E4 | SHA256:81BE37B1910873AB524D3245F57C1BC0BC199DE0B2ECAEA3AE1C1A2FAE91B1E3 | |||
| 3660 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibF3F5.tmp\1\Adding entries to hosts file.exe | executable | |
MD5:C0F59103215D483CC4E2593C4E1AA62E | SHA256:0EEA5DEA08CBC022D84AA34436C98B95B383F687F1E87C673F56A03957B0B274 | |||
| 3492 | Installing License for Rhinoceros 6.exe | C:\Users\admin\AppData\Local\Temp\sibAA16.tmp\0\Adding entries to hosts file.exe | executable | |
MD5:C0F59103215D483CC4E2593C4E1AA62E | SHA256:0EEA5DEA08CBC022D84AA34436C98B95B383F687F1E87C673F56A03957B0B274 | |||
| 3660 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibF3F5.tmp\2\Adding rules in firewall.cmd | text | |
MD5:BCB70EA84C80E65ED3466B7768B66F3E | SHA256:F0A87B24772CB59F6D9D4238486BCF6AFE57469E56C760E8B8A67BE73AE295F7 | |||
| 3492 | Installing License for Rhinoceros 6.exe | C:\Users\admin\AppData\Local\Temp\sibAA16.tmp\SibClr.dll | executable | |
MD5:D60C5FCECD3E597BB7F4ABFE32C06EE6 | SHA256:BDBDA94913063E3BE952E09151EB8DB8A5A1749B7D0512C11AA3C93677E9FF8F | |||
| 3660 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibF3F5.tmp\SibClr.dll | executable | |
MD5:D60C5FCECD3E597BB7F4ABFE32C06EE6 | SHA256:BDBDA94913063E3BE952E09151EB8DB8A5A1749B7D0512C11AA3C93677E9FF8F | |||
| 1540 | Installing Rhinoceros 6 License.exe | C:\ProgramData\McNeel\Rhinoceros\6.0\License Manager\Licenses\55500d41-3a41-4474-99b3-684032a4f4df.lic | binary | |
MD5:B1F81128FB43D865EDFE42D9D461EE1B | SHA256:F017D1E73D9AF5B5E722164EE27E39269976BB3CDC243D0685BD01A182602C9B | |||
| 3492 | Installing License for Rhinoceros 6.exe | C:\Users\admin\AppData\Local\Temp\sibAA16.tmp\1\Adding rules in firewall.cmd | text | |
MD5:BCB70EA84C80E65ED3466B7768B66F3E | SHA256:F0A87B24772CB59F6D9D4238486BCF6AFE57469E56C760E8B8A67BE73AE295F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |