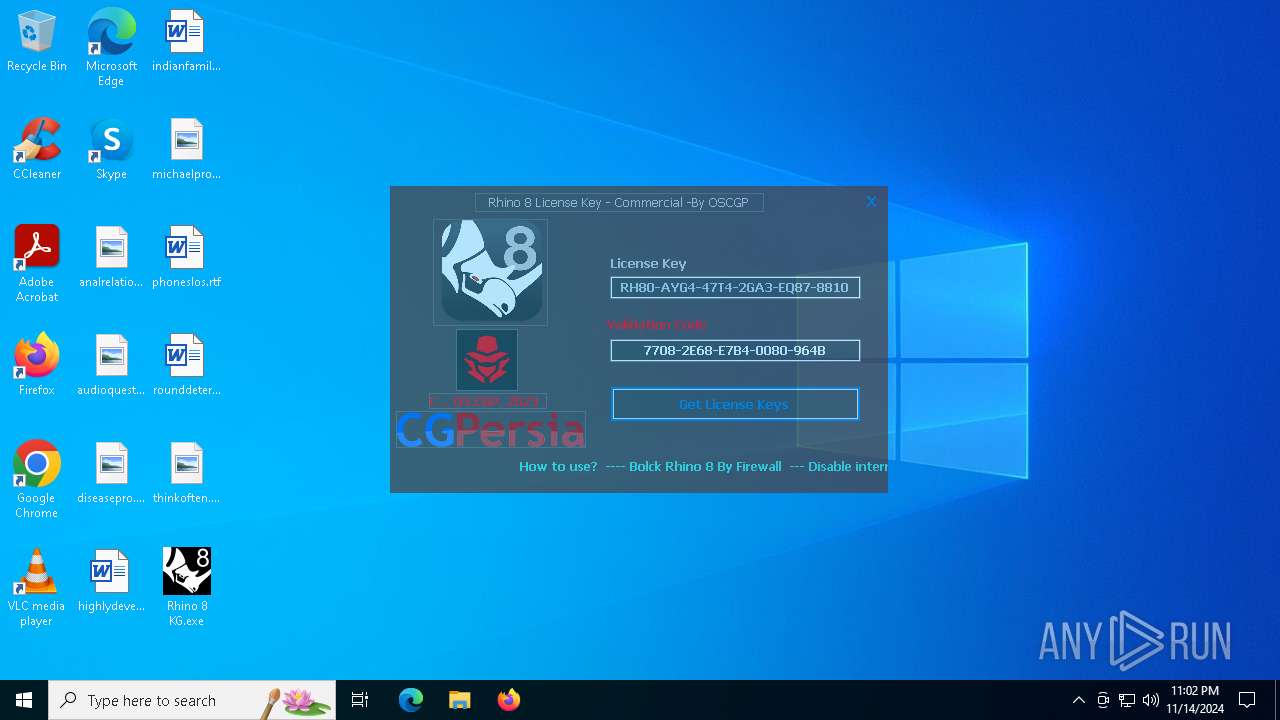
| File name: | Rhinoceros Universal License Patch.exe |
| Full analysis: | https://app.any.run/tasks/1a445695-7856-4684-a033-881e629261c0 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2024, 23:00:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | A0797366897CAAD2F6915F821F390997 |
| SHA1: | 146D95D5ADFE6A0601A89AAC3489636B3ED7EE29 |
| SHA256: | 285B0961CEEE6ADBA7780E9FBD78F2EACEB1C3821112A45E19E8F3DA21EACF15 |
| SSDEEP: | 98304:MH8iylH+6ez3fElXYD8xfvNReZZ1Gc6ez3fElXYD8xfvNReZC++alXez3fElXYDk:+4ad |
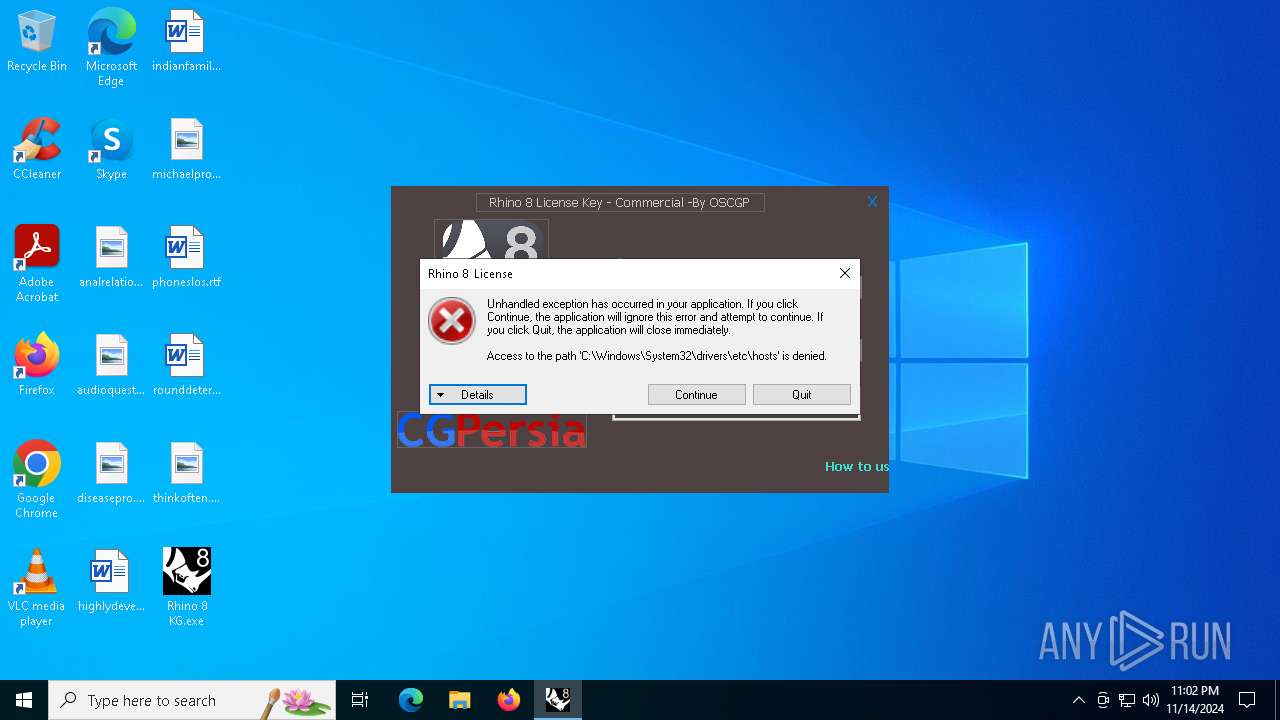
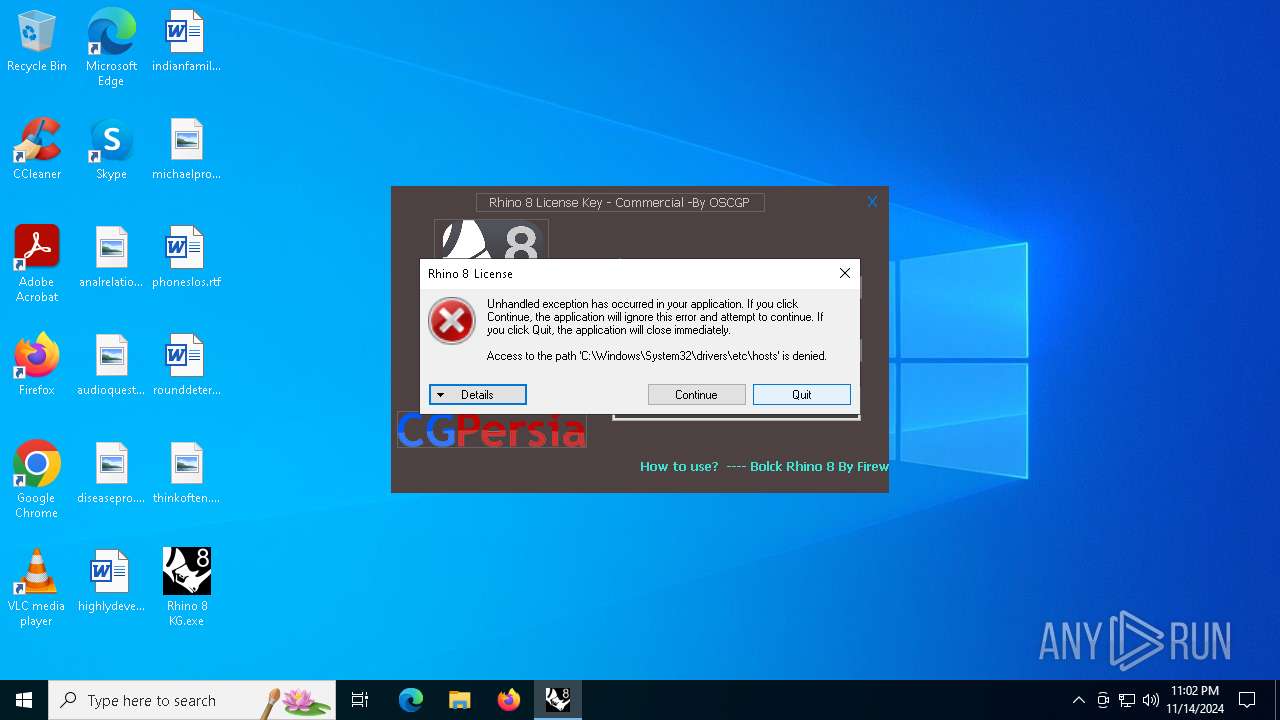
MALICIOUS
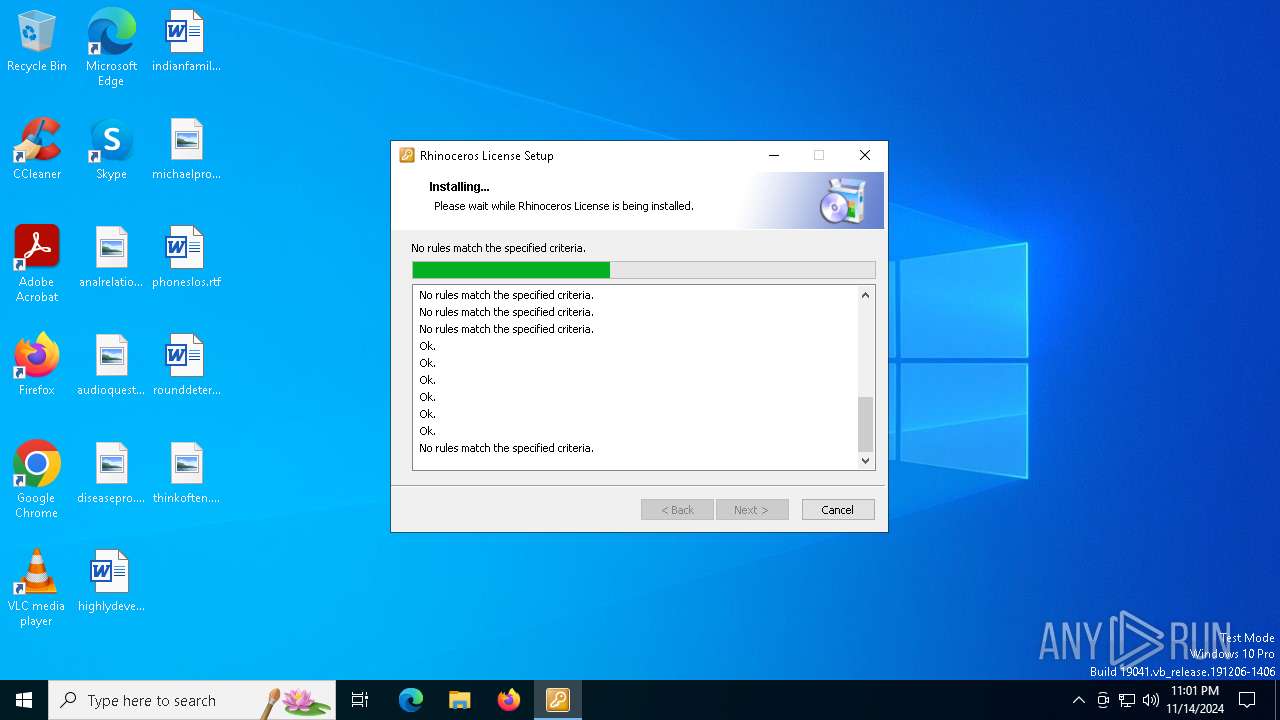
Bypass execution policy to execute commands
- powershell.exe (PID: 7268)
- powershell.exe (PID: 2980)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 6988)
Changes powershell execution policy (Bypass)
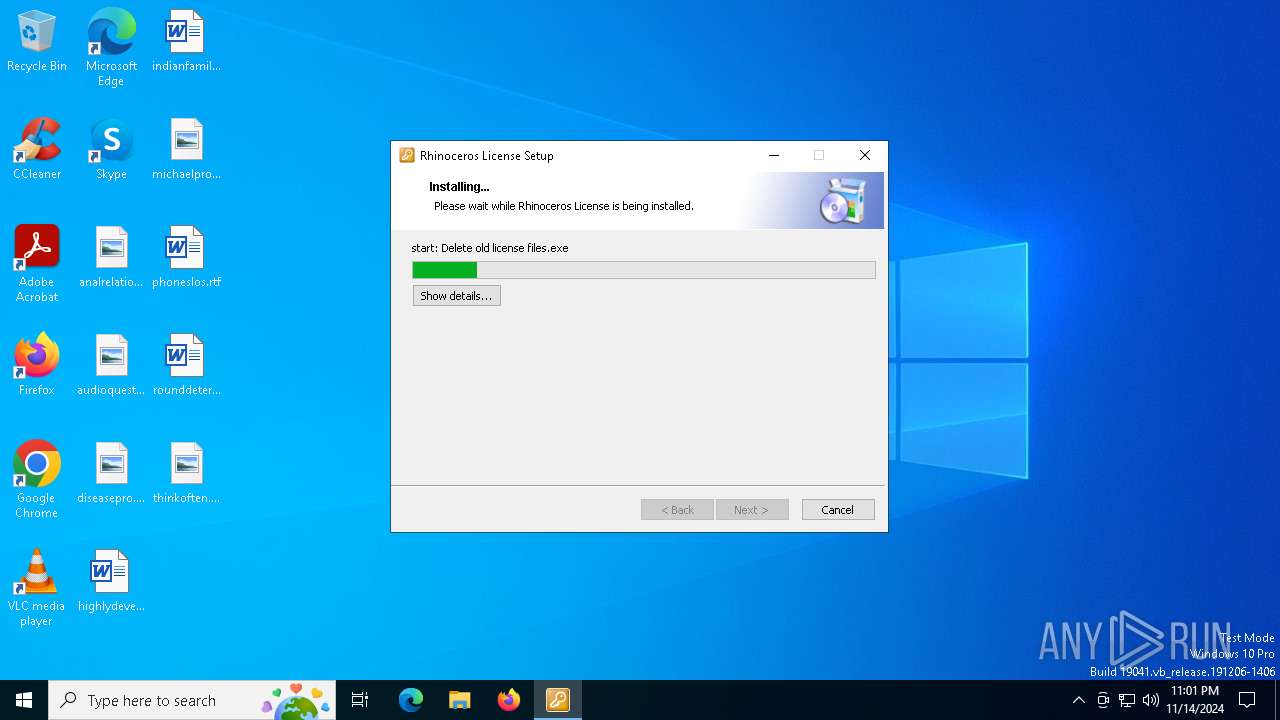
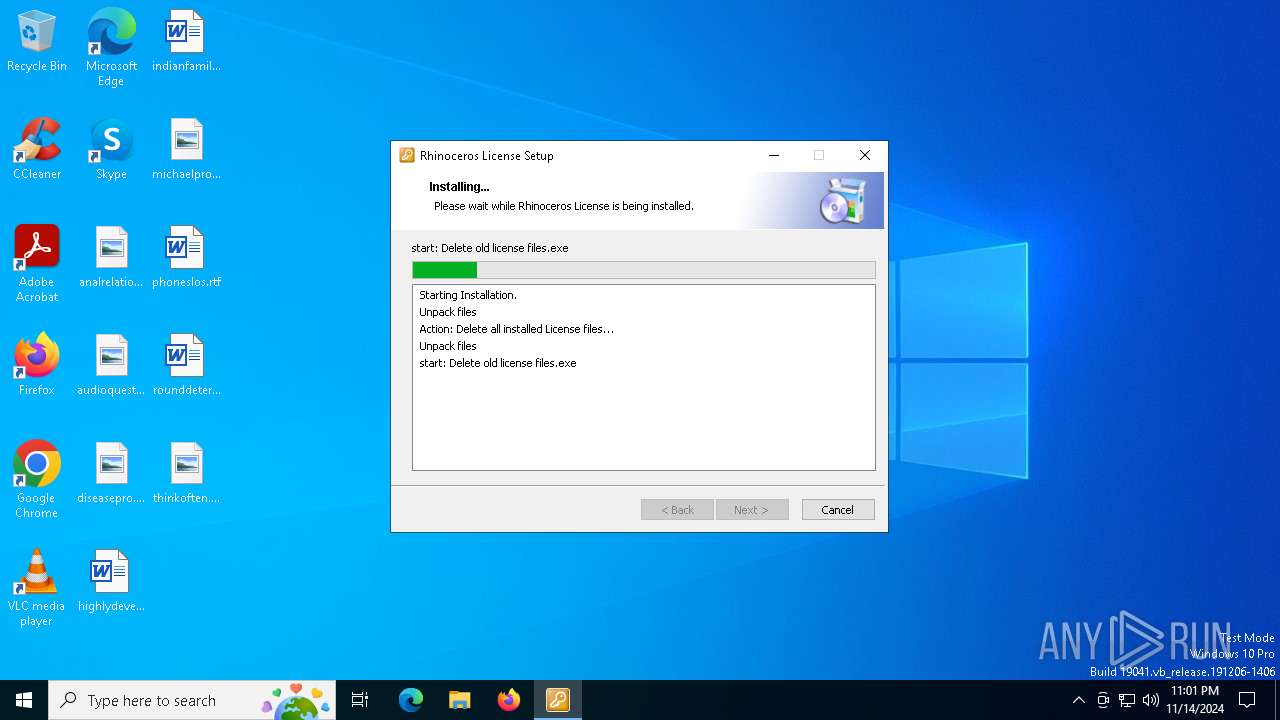
- Delete old license files.exe (PID: 5756)
- Adding entries to hosts file.exe (PID: 7220)
- Adding entries to hosts file.exe (PID: 7252)
- Adding entries to hosts file.exe (PID: 7892)
- Adding entries to hosts file.exe (PID: 7176)
SUSPICIOUS
The process executes Powershell scripts
- Delete old license files.exe (PID: 5756)
- Adding entries to hosts file.exe (PID: 7220)
- Adding entries to hosts file.exe (PID: 7252)
- Adding entries to hosts file.exe (PID: 7892)
- Adding entries to hosts file.exe (PID: 7176)
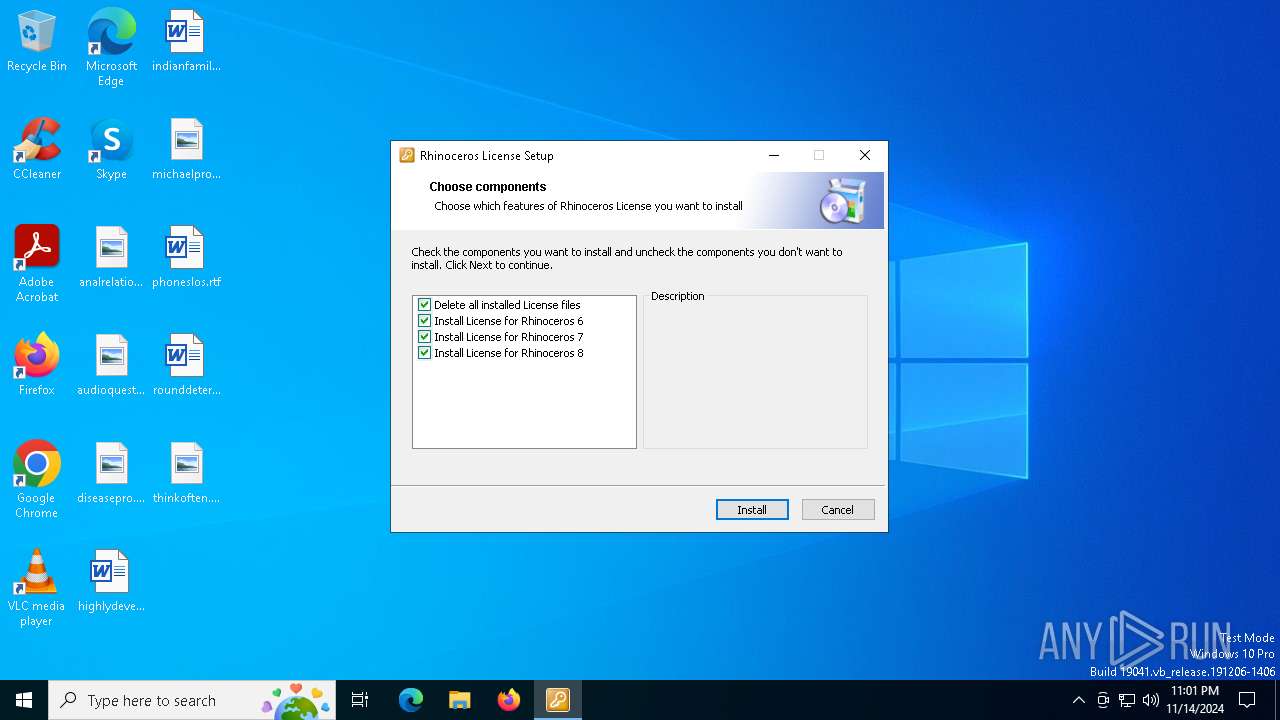
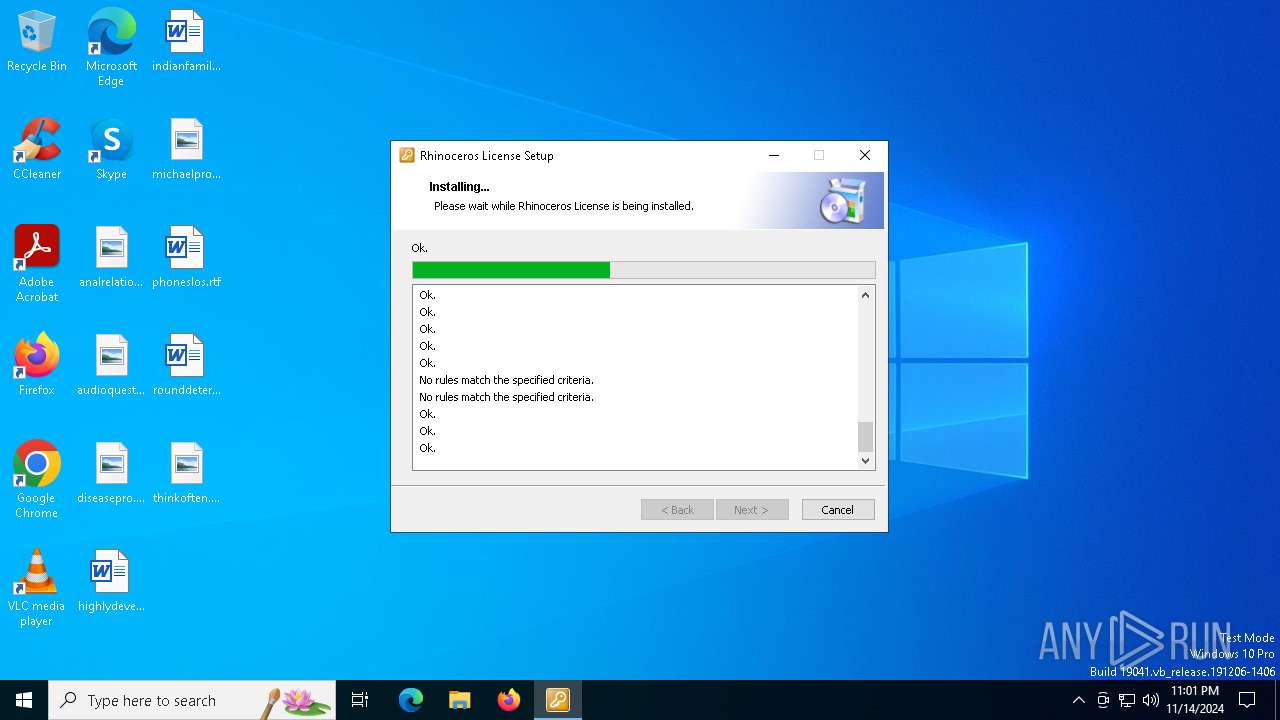
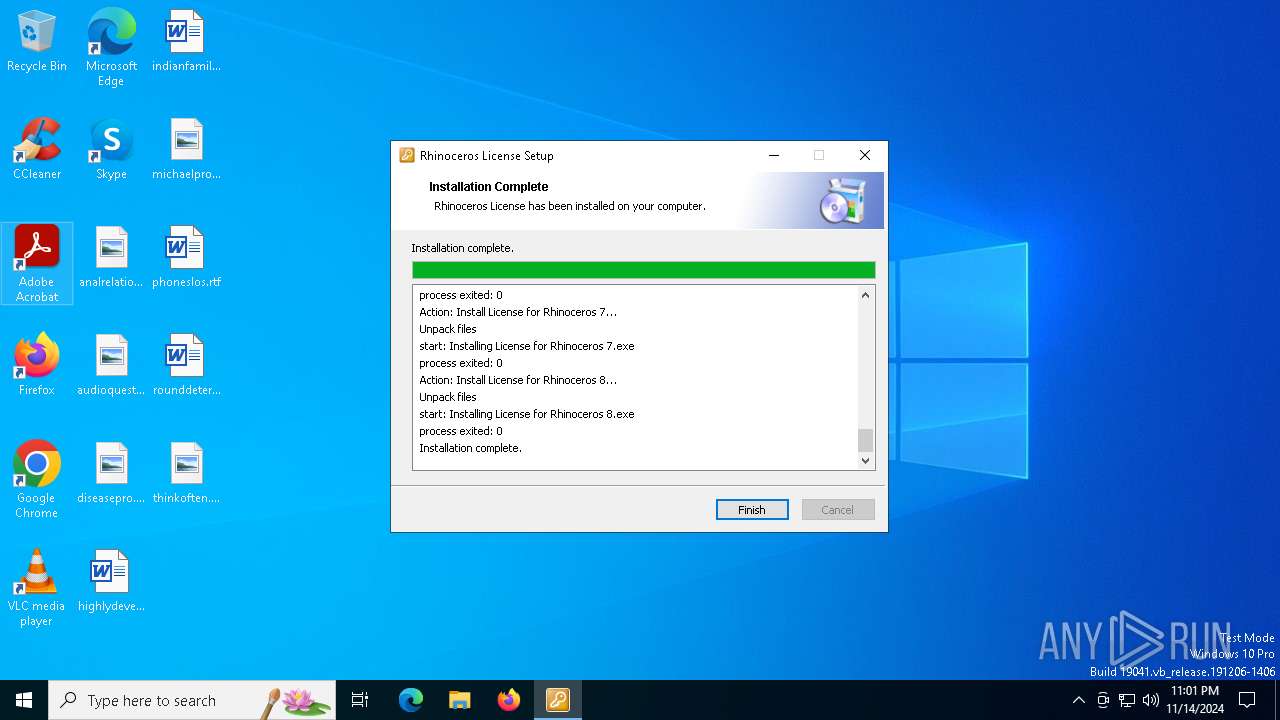
Executable content was dropped or overwritten
- Rhinoceros Universal License Patch.exe (PID: 3852)
- Installing License for Rhinoceros 6.exe (PID: 7380)
- Installing License for Rhinoceros 7.exe (PID: 7788)
- Installing License for Rhinoceros 8.exe (PID: 7156)
Starts POWERSHELL.EXE for commands execution
- Delete old license files.exe (PID: 5756)
- Adding entries to hosts file.exe (PID: 7220)
- Adding entries to hosts file.exe (PID: 7252)
- Adding entries to hosts file.exe (PID: 7892)
- Adding entries to hosts file.exe (PID: 7176)
Executing commands from ".cmd" file
- Rhinoceros Universal License Patch.exe (PID: 3852)
- Installing License for Rhinoceros 6.exe (PID: 7380)
- Installing License for Rhinoceros 7.exe (PID: 7788)
- Installing License for Rhinoceros 8.exe (PID: 7156)
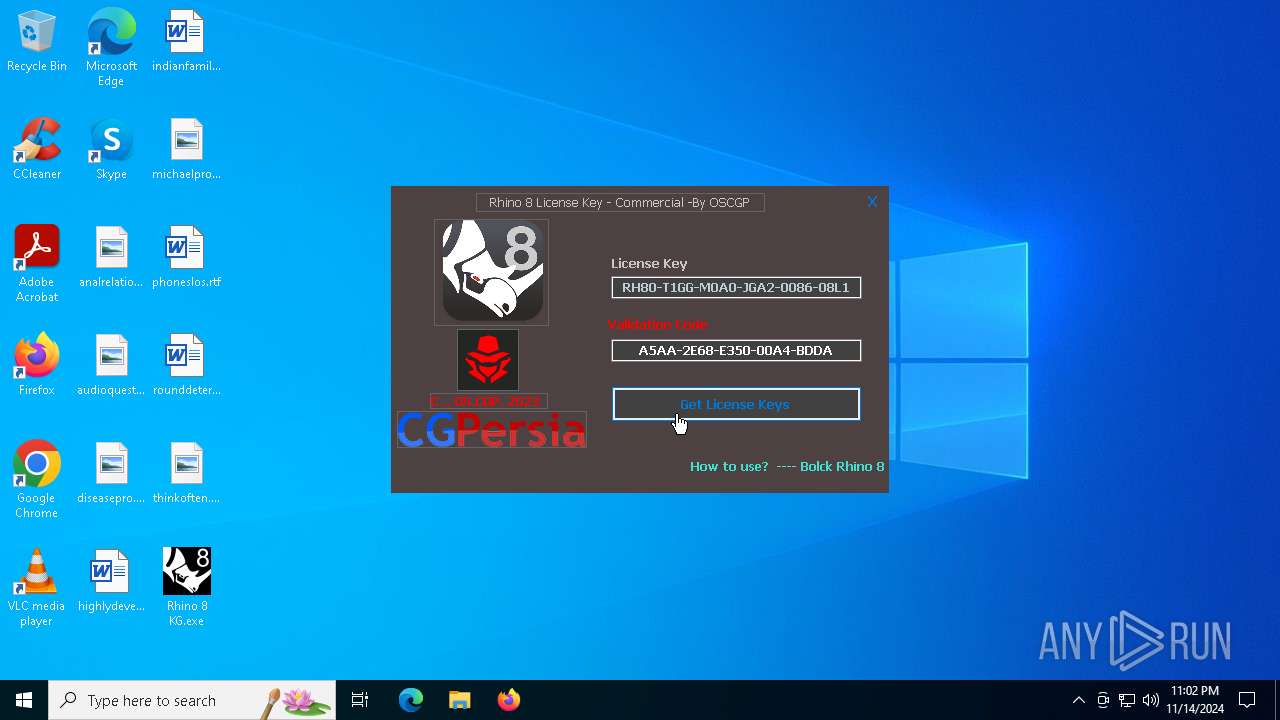
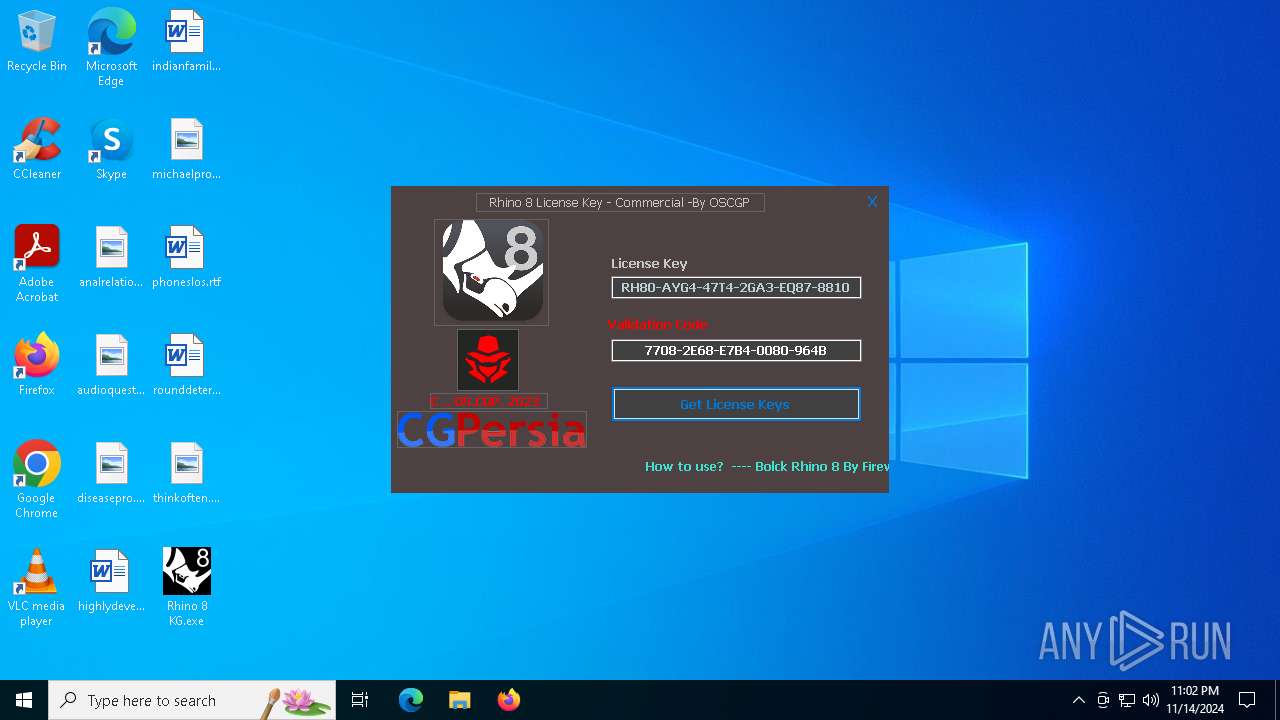
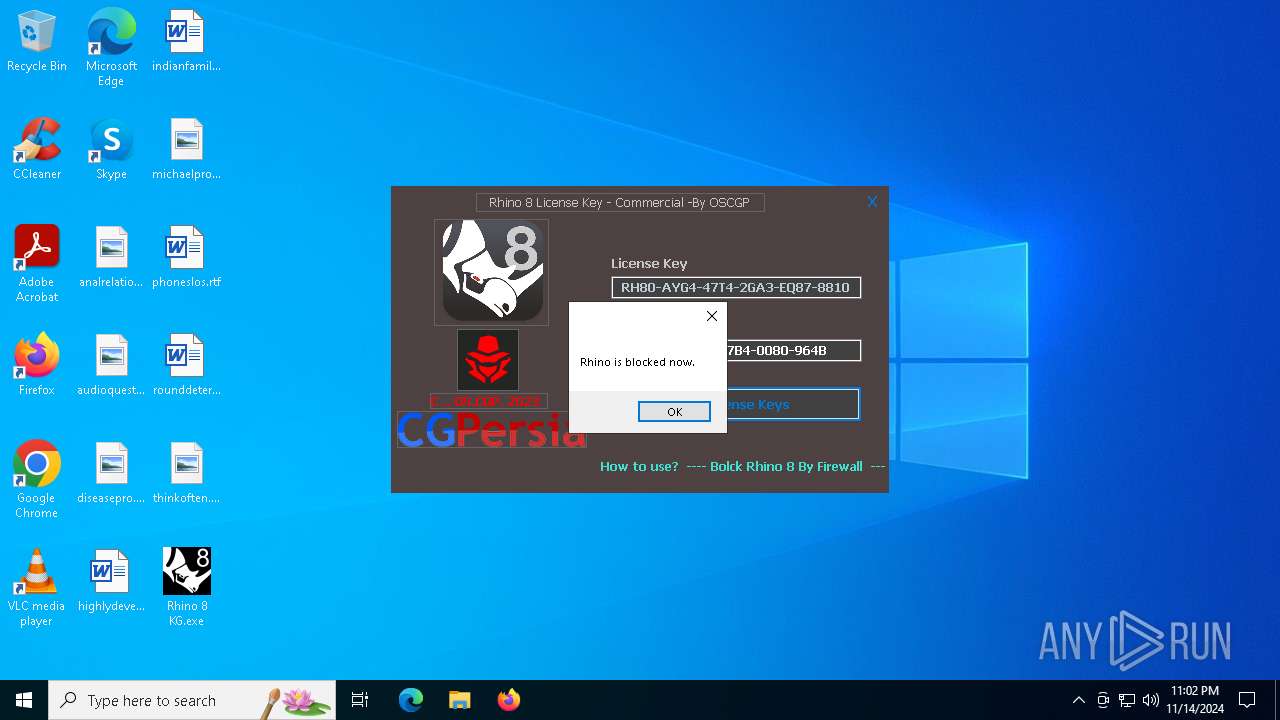
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 6560)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 6560)
Starts CMD.EXE for commands execution
- Rhinoceros Universal License Patch.exe (PID: 3852)
- Installing License for Rhinoceros 7.exe (PID: 7788)
- Installing License for Rhinoceros 6.exe (PID: 7380)
- Installing License for Rhinoceros 8.exe (PID: 7156)
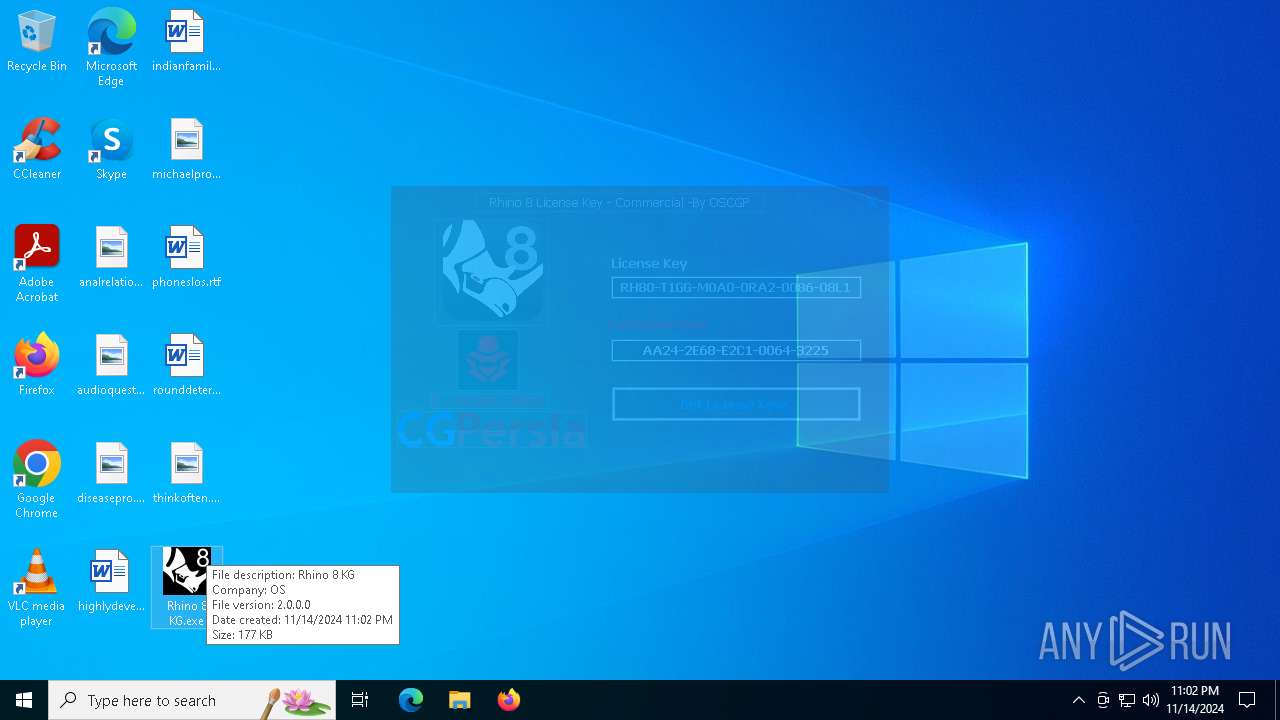
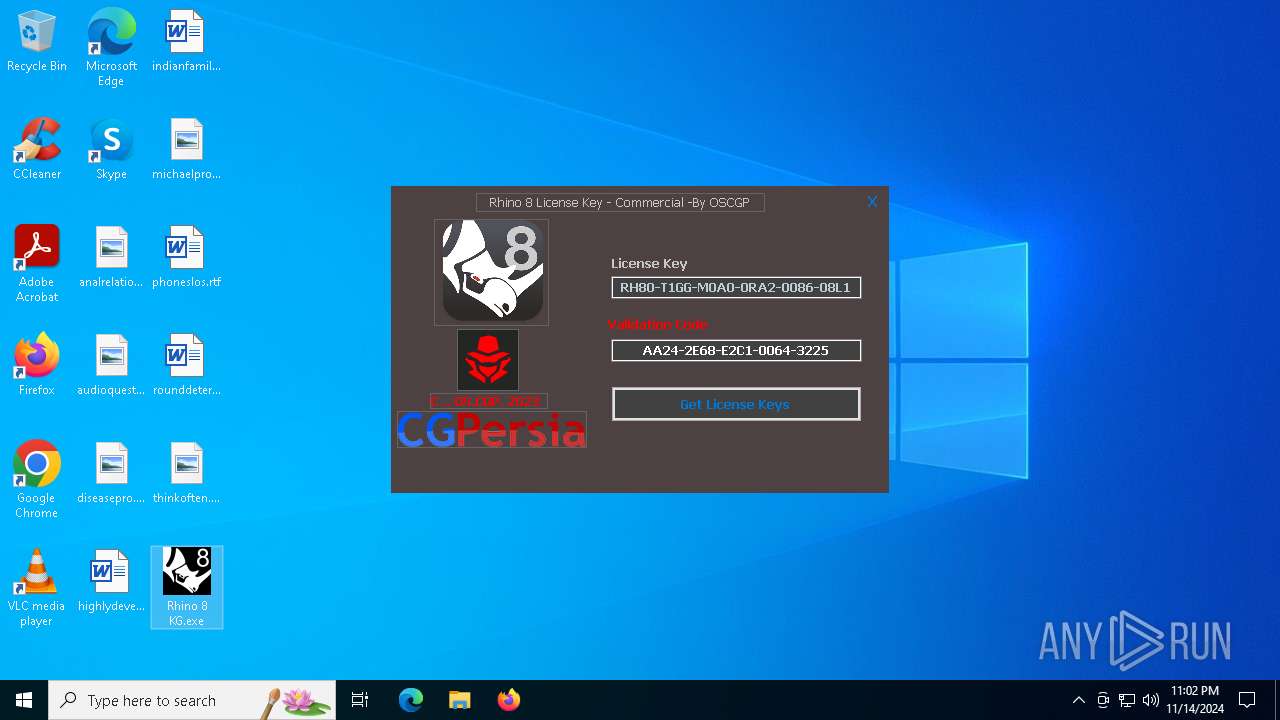
Starts itself from another location
- Rhinoceros Universal License Patch.exe (PID: 3852)
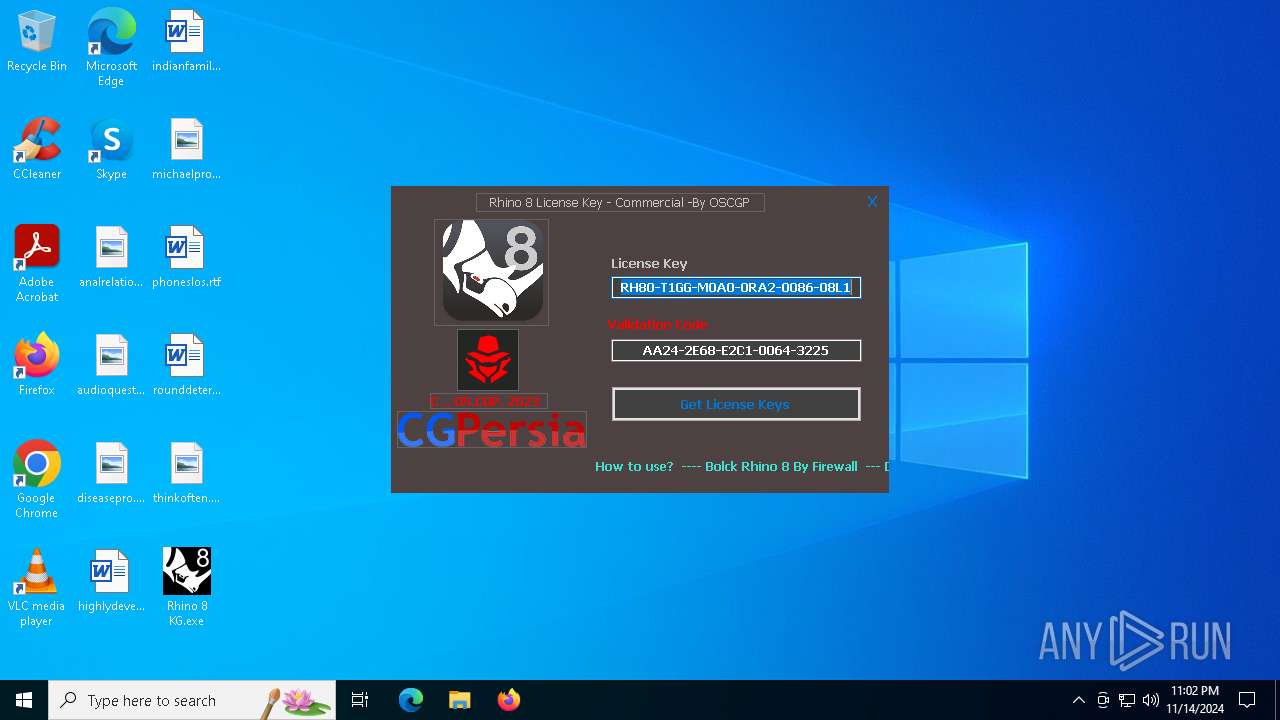
INFO
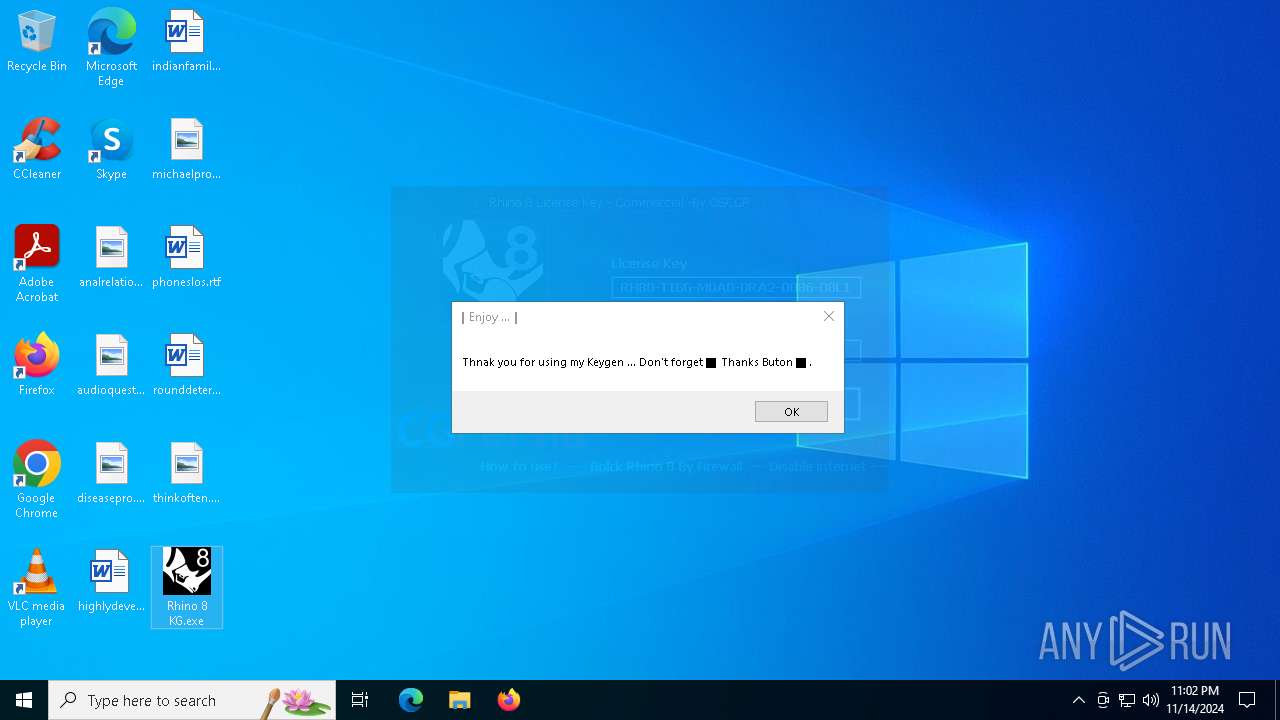
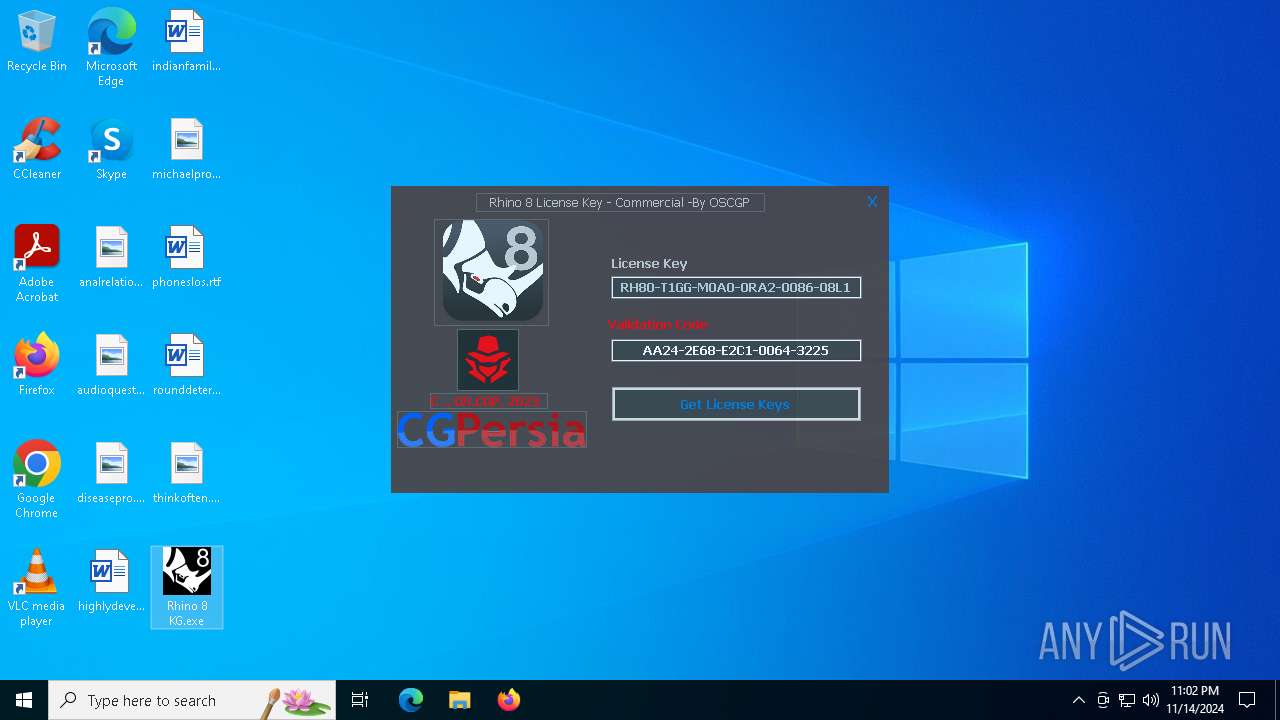
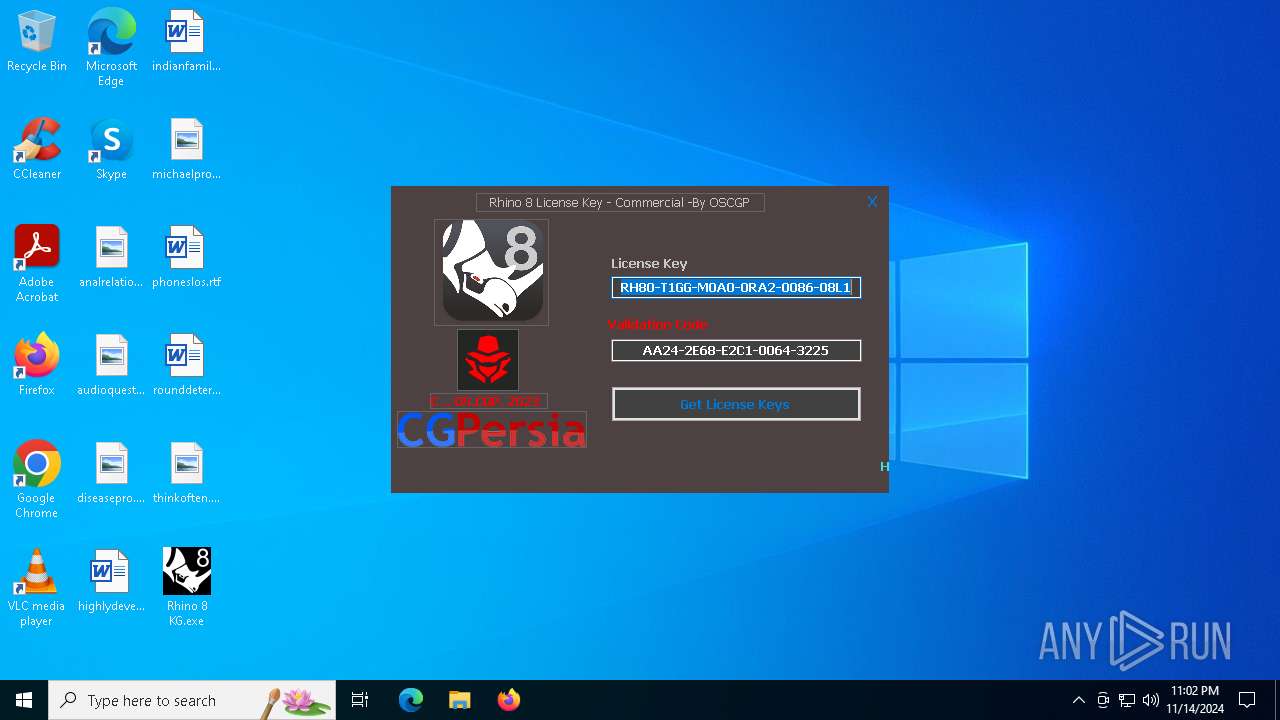
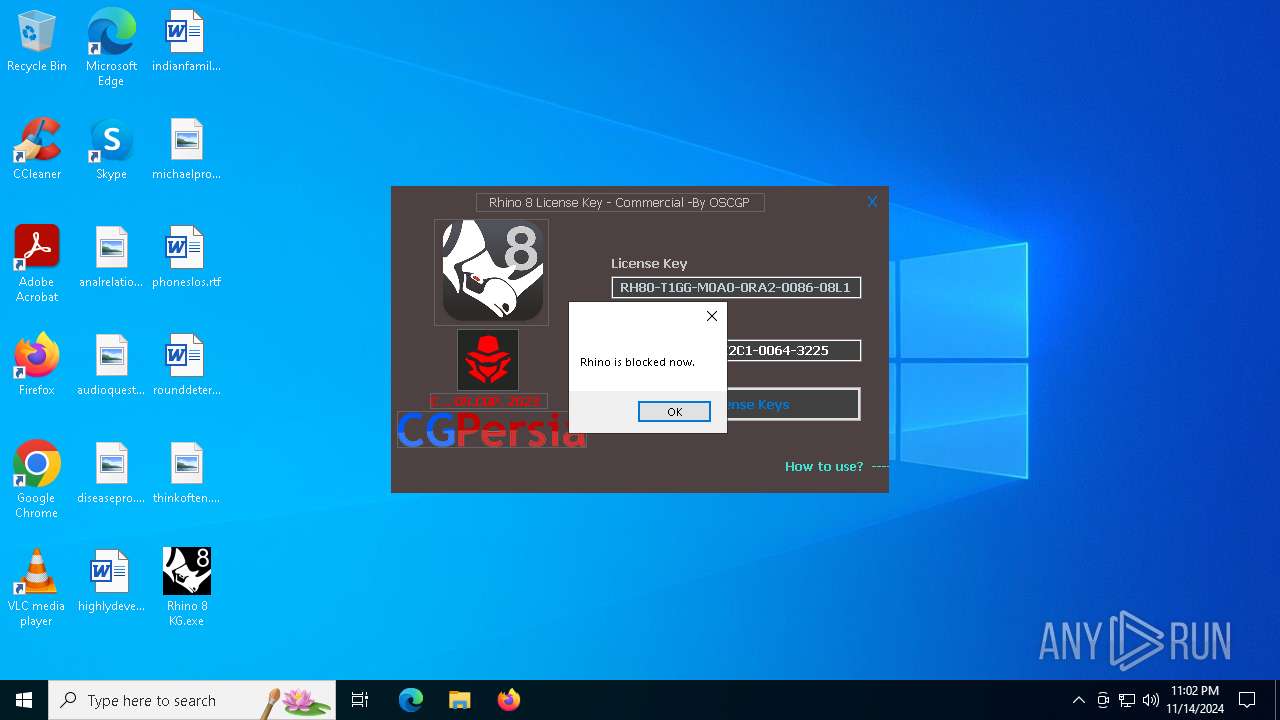
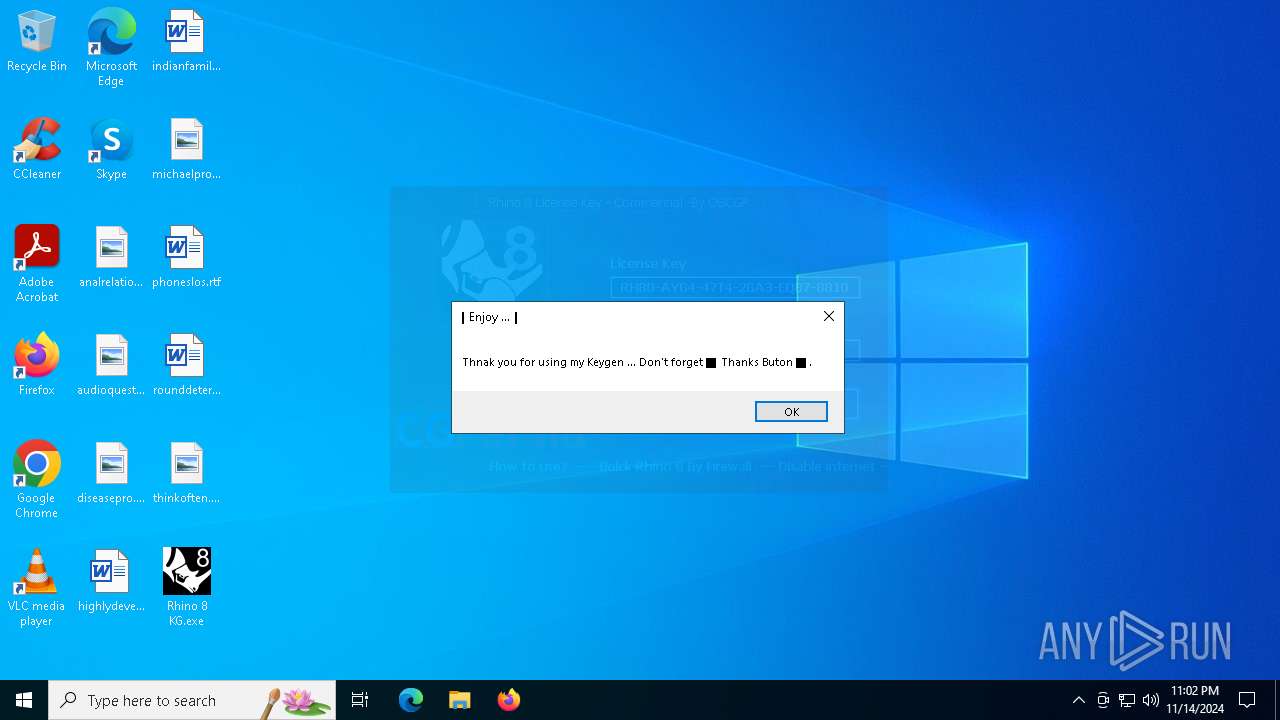
Manual execution by a user
- Rhino 8 KG.exe (PID: 7220)
- Rhino 8 KG.exe (PID: 6272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:24 10:55:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 453120 |
| InitializedDataSize: | 327680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49ef7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Robert McNeel & Associates |
| FileDescription: | - |
| FileVersion: | 1.0.0 |
| InternalName: | SibInstaller.exe |
| LegalCopyright: | Robert McNeel & Associates |
| OriginalFileName: | SibInstaller.exe |
| ProductName: | Rhinoceros License |
| ProductVersion: | 1.0.0 |
Total processes
301
Monitored processes
173
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Users\admin\AppData\Local\Temp\Rhinoceros Universal License Patch.exe" | C:\Users\admin\AppData\Local\Temp\Rhinoceros Universal License Patch.exe | — | explorer.exe | |||||||||||
User: admin Company: Robert McNeel & Associates Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 624 | netsh advfirewall firewall delete rule name=all program="C:\Program Files\Rhino 6\System\Rhino.exe" | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | netsh advfirewall firewall add rule name="Rhino 7" dir=out program="C:\Program Files\Rhino 7\System\Rhino.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1252 | netsh advfirewall firewall add rule name="Rhino 6 RmaErrorReporting" dir=out program="C:\Program Files\Rhino 6\System\RmaErrorReporting.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1500 | netsh advfirewall firewall add rule name="Rhino 8" dir=in program="C:\Program Files\Rhino 8\System\Rhino.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1748 | netsh advfirewall firewall add rule name="Rhino 7 Yak" dir=out program="C:\Program Files\Rhino 7\System\Yak.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | netsh advfirewall firewall add rule name="Rhino 6 RmaErrorReporting" dir=out program="C:\Program Files\Rhino 6\System\RmaErrorReporting.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1788 | netsh advfirewall firewall add rule name="Rhino 7 Yak" dir=out program="C:\Program Files\Rhino 7\System\Yak.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | sc stop "McNeelUpdate" | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2272 | netsh advfirewall firewall add rule name="Rhino 8" dir=out program="C:\Program Files\Rhino 8\System\Rhino.exe" profile=any action=block | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
48 407
Read events
48 407
Write events
0
Delete events
0
Modification events
Executable files
19
Suspicious files
4
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5tkrxi4f.gyn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_npnq0vn2.5kg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3852 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibB985.tmp\SibClr.dll | executable | |
MD5:D60C5FCECD3E597BB7F4ABFE32C06EE6 | SHA256:BDBDA94913063E3BE952E09151EB8DB8A5A1749B7D0512C11AA3C93677E9FF8F | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cojgjua5.s3p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5756 | Delete old license files.exe | C:\Users\admin\AppData\Local\Temp\CBA5.tmp\CBA6.tmp\CBA7.ps1 | text | |
MD5:ECAA358B8C58F2D4D17991C029EB4709 | SHA256:2C6438C415068CED6443A5B297859011C338132CF32A67E6E1B8496BA9E1CAE3 | |||
| 3852 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibB985.tmp\0\Delete old license files.exe | executable | |
MD5:8C991843B5D89D091321226A922D7851 | SHA256:A5C4A1C1E602CF5967C955AF812BE38604D01461AFE59C1971B920565E391FC7 | |||
| 7432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hu30xl2q.q2u.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3852 | Rhinoceros Universal License Patch.exe | C:\Users\admin\AppData\Local\Temp\sibB985.tmp\1\Adding entries to hosts file.exe | executable | |
MD5:C0F59103215D483CC4E2593C4E1AA62E | SHA256:0EEA5DEA08CBC022D84AA34436C98B95B383F687F1E87C673F56A03957B0B274 | |||
| 7268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zdxfrlsf.nvm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7220 | Adding entries to hosts file.exe | C:\Users\admin\AppData\Local\Temp\DCDC.tmp\DCDD.tmp\DCDE.ps1 | text | |
MD5:0B9CBE5F1C815F45C8756FADDDA3D760 | SHA256:BC2F04AEECD85919442F7AAE90E6851F036925CB6CFCDA92DFE005A0BDD6CF85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
42
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.107:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.209.176:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |