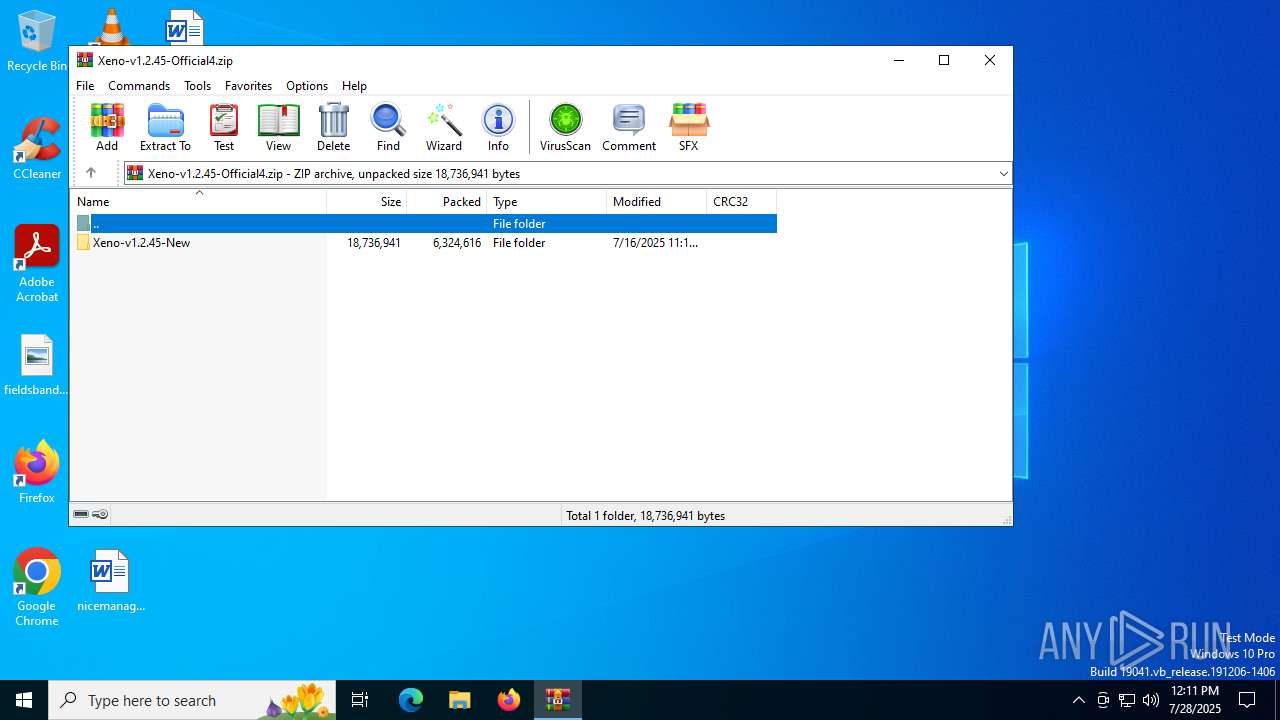
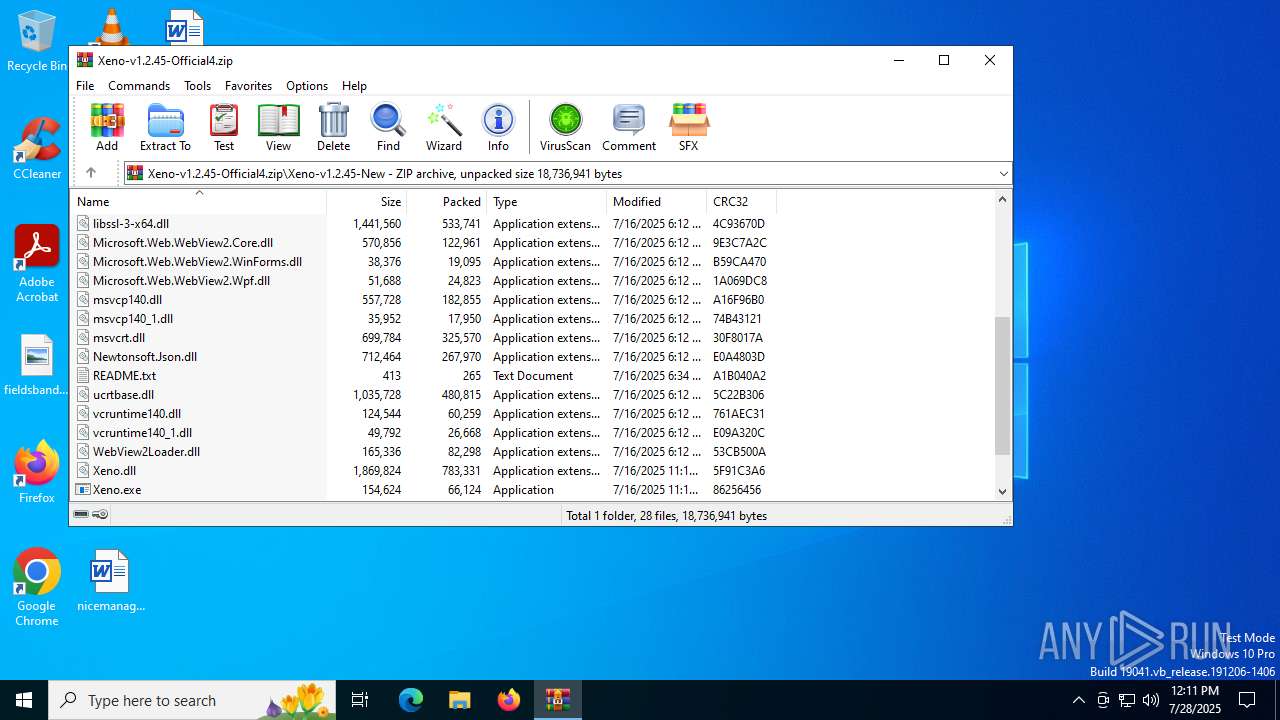
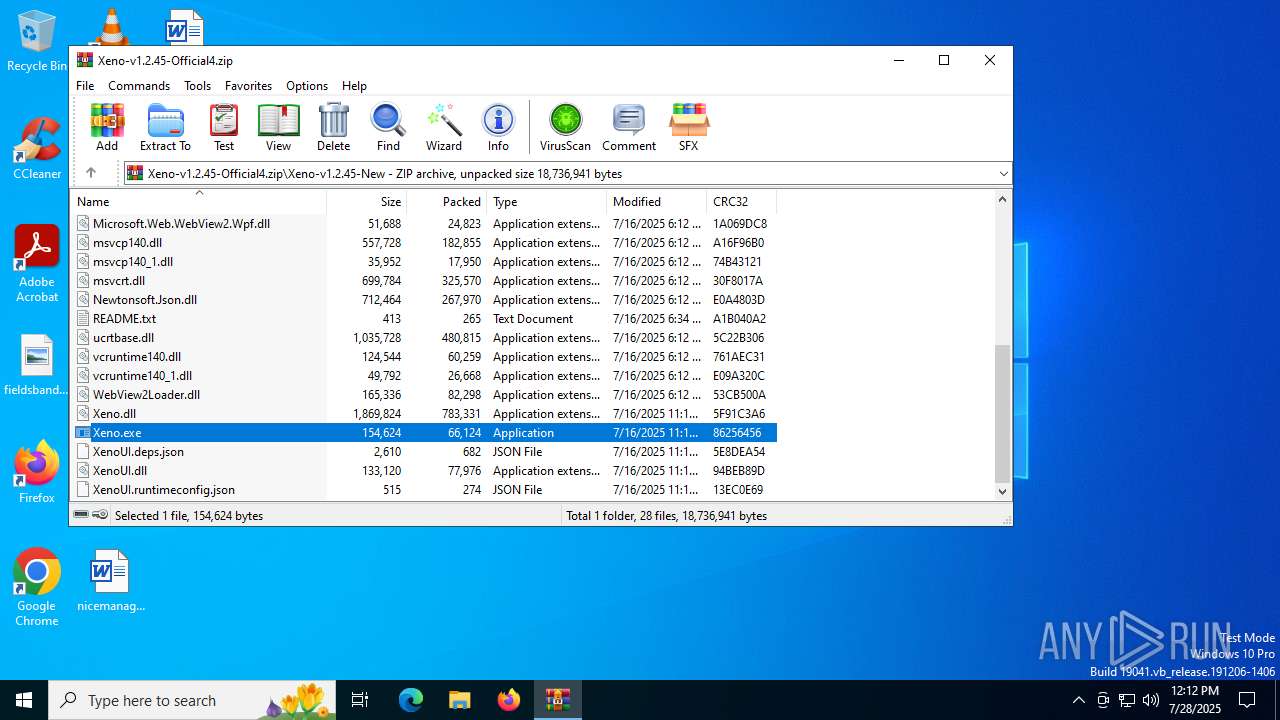
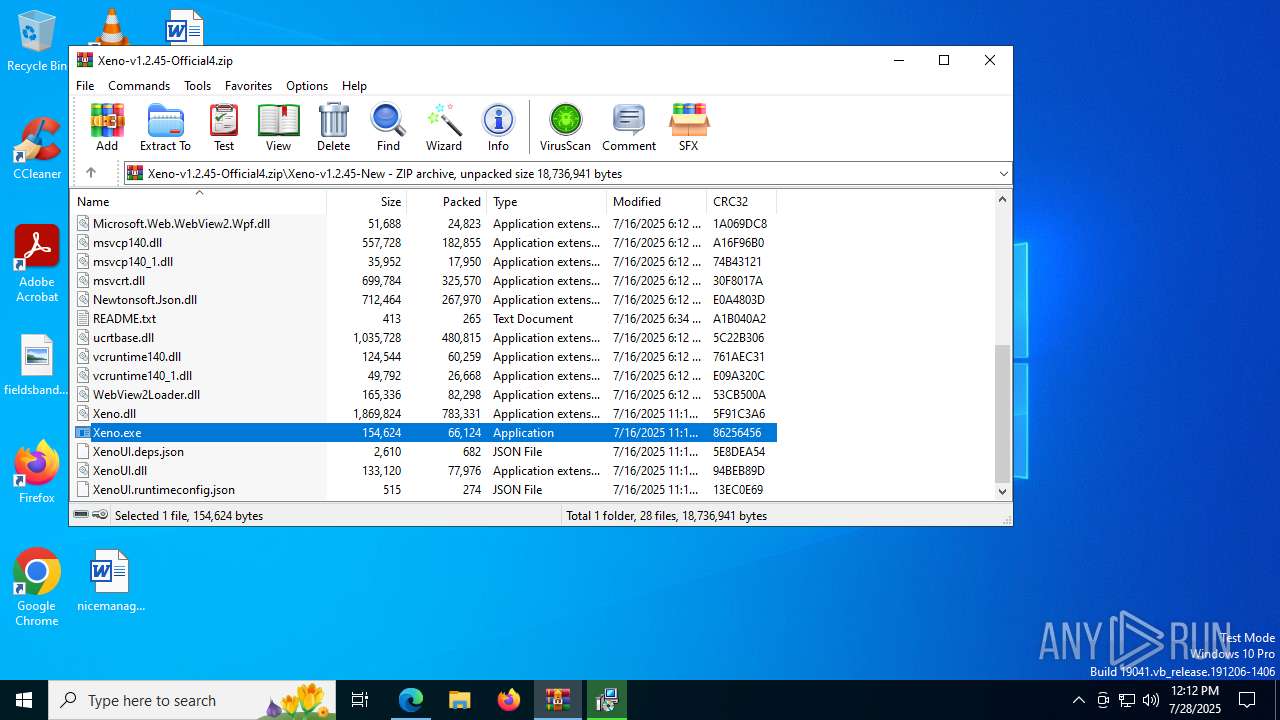
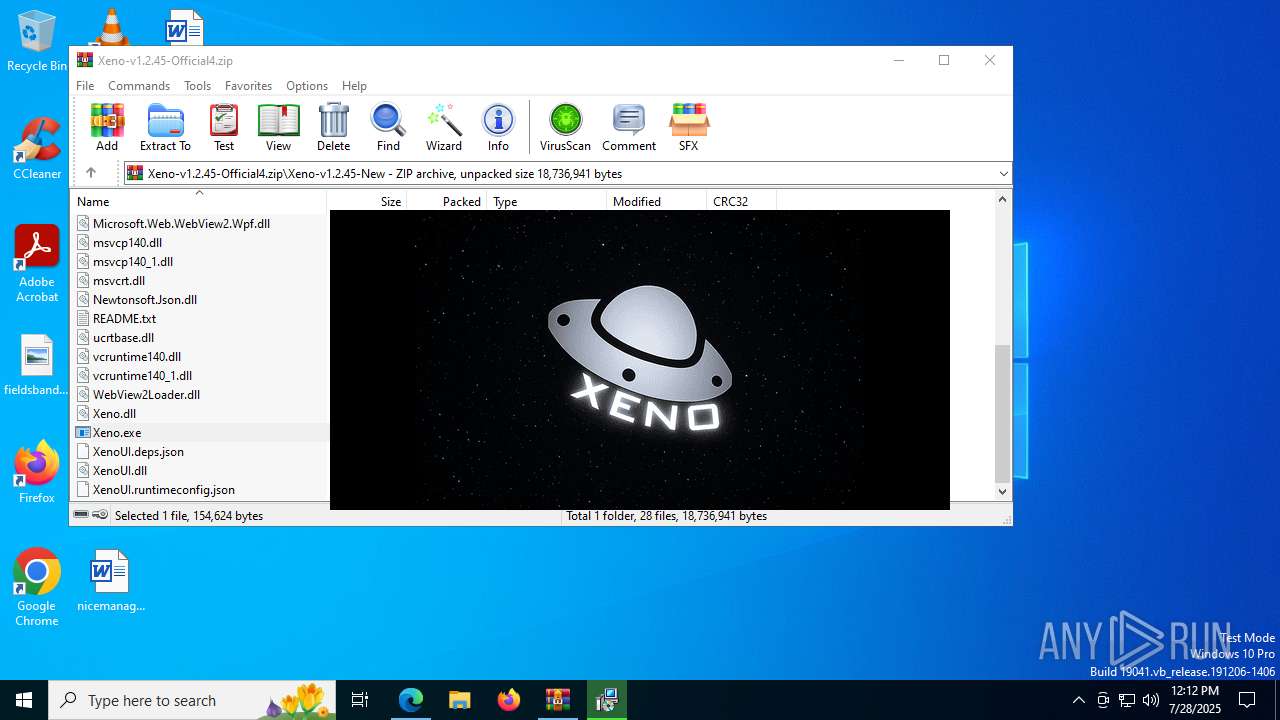
| File name: | Xeno-v1.2.45-Official4.zip |
| Full analysis: | https://app.any.run/tasks/ad5b999b-4e4b-4be0-b763-e609ba8ddc9a |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2025, 12:11:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 33176A071711E1594BAD11FE30FBD58C |
| SHA1: | 1DA0D0F13282E0B0FF48E29E61576441066C77DF |
| SHA256: | 284C342A0D3F64C6E06CAE76A6D89FCAF4A501D8121AA48DEF39C14C026659E2 |
| SSDEEP: | 98304:nrDve352liLnX4eK0lJBSJc0uULOP3uatn283FMZwyivrzga4RqNQccmTgaJonsS:qQYSReS5K3kYJNU |
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 5456)
Changes the autorun value in the registry
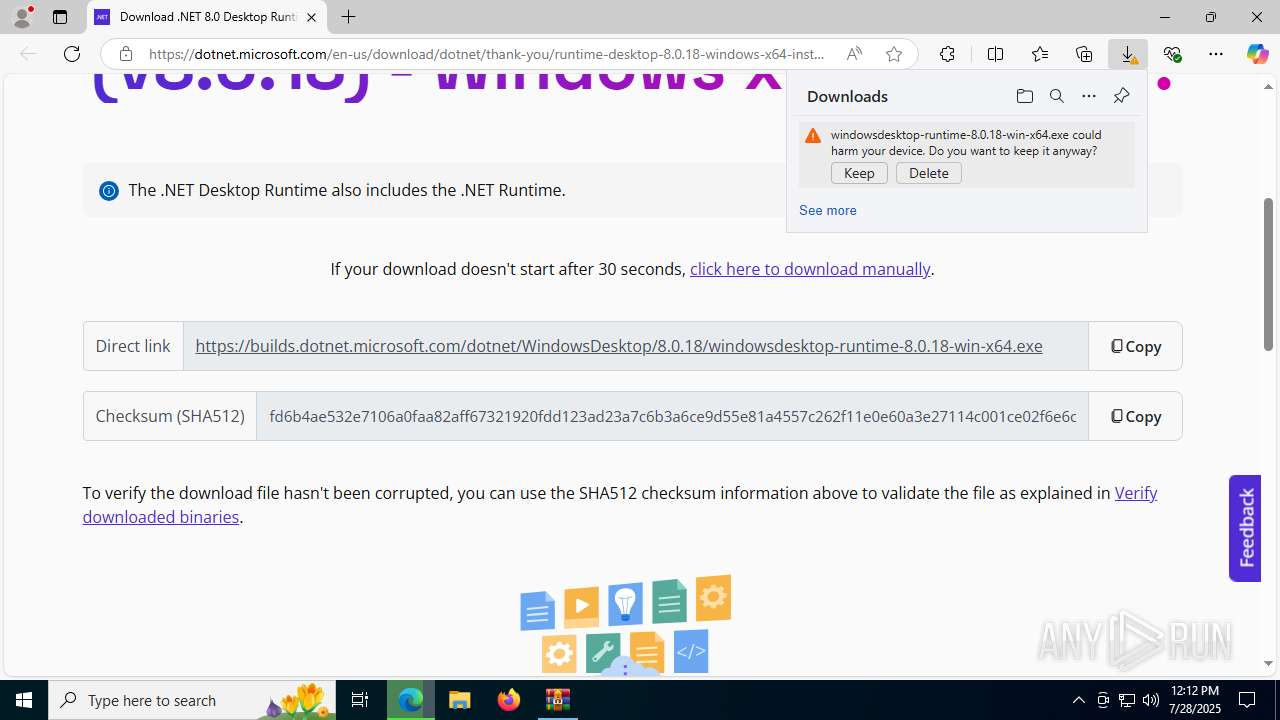
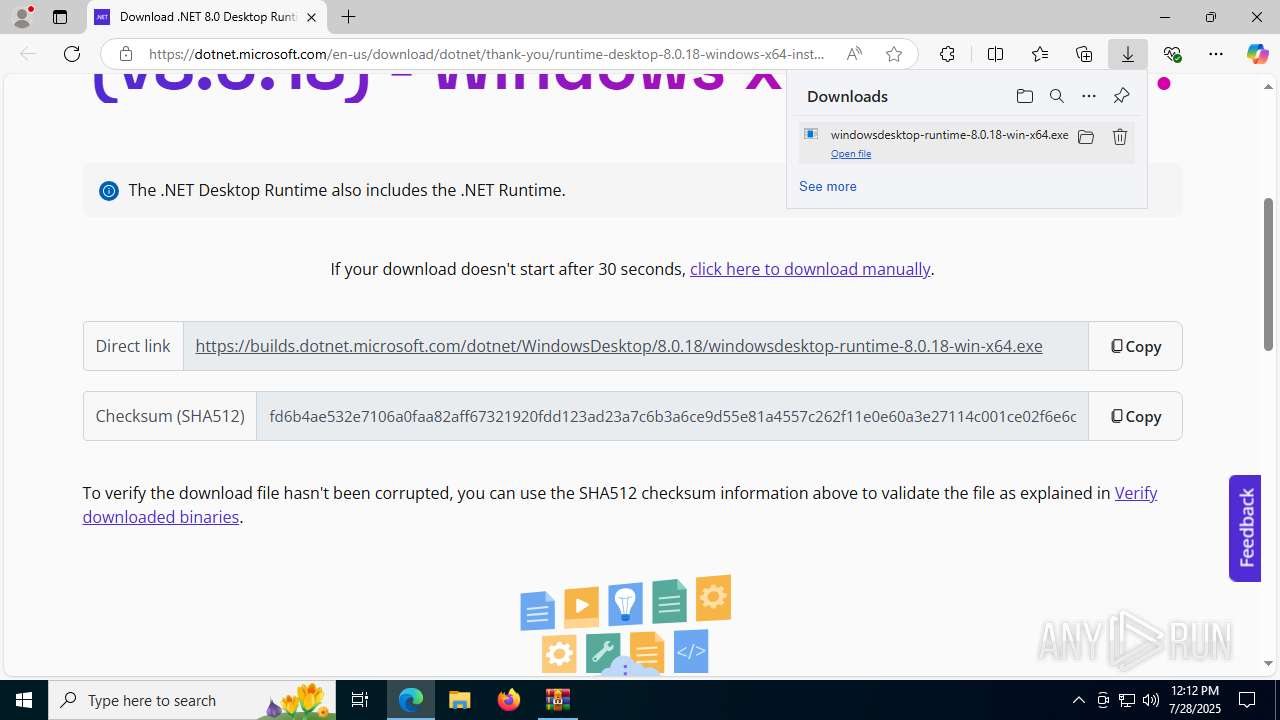
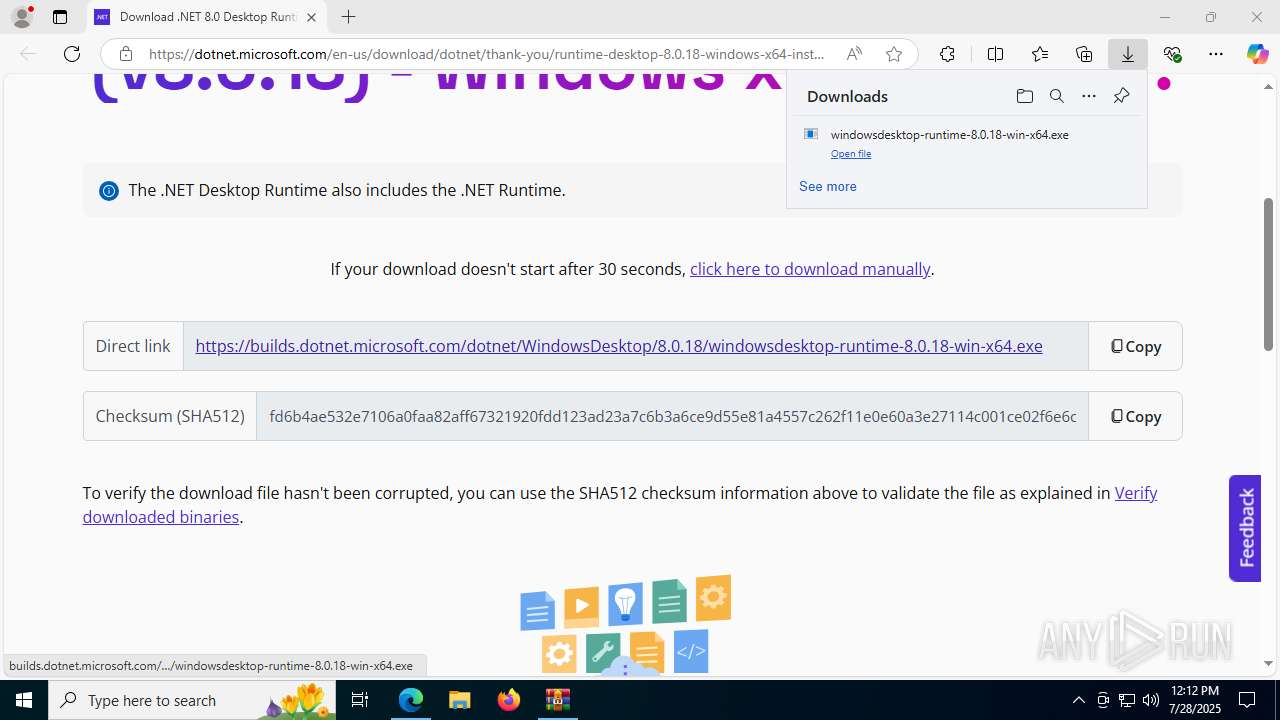
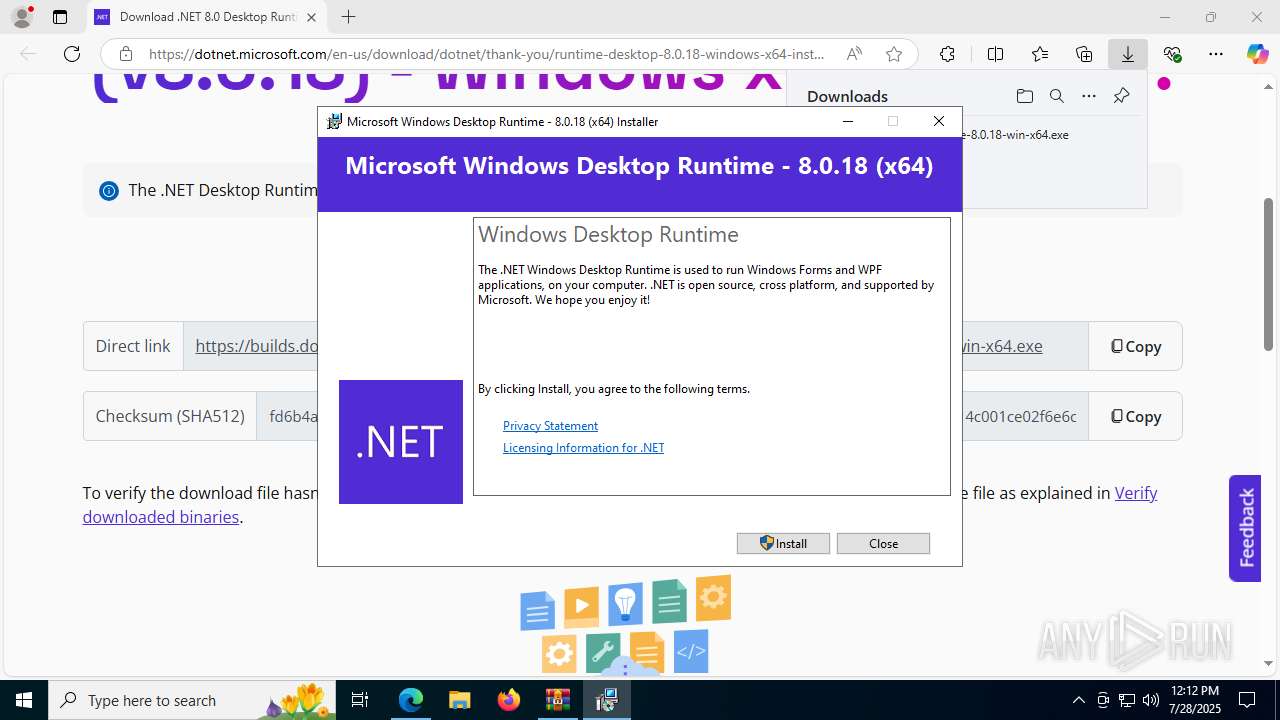
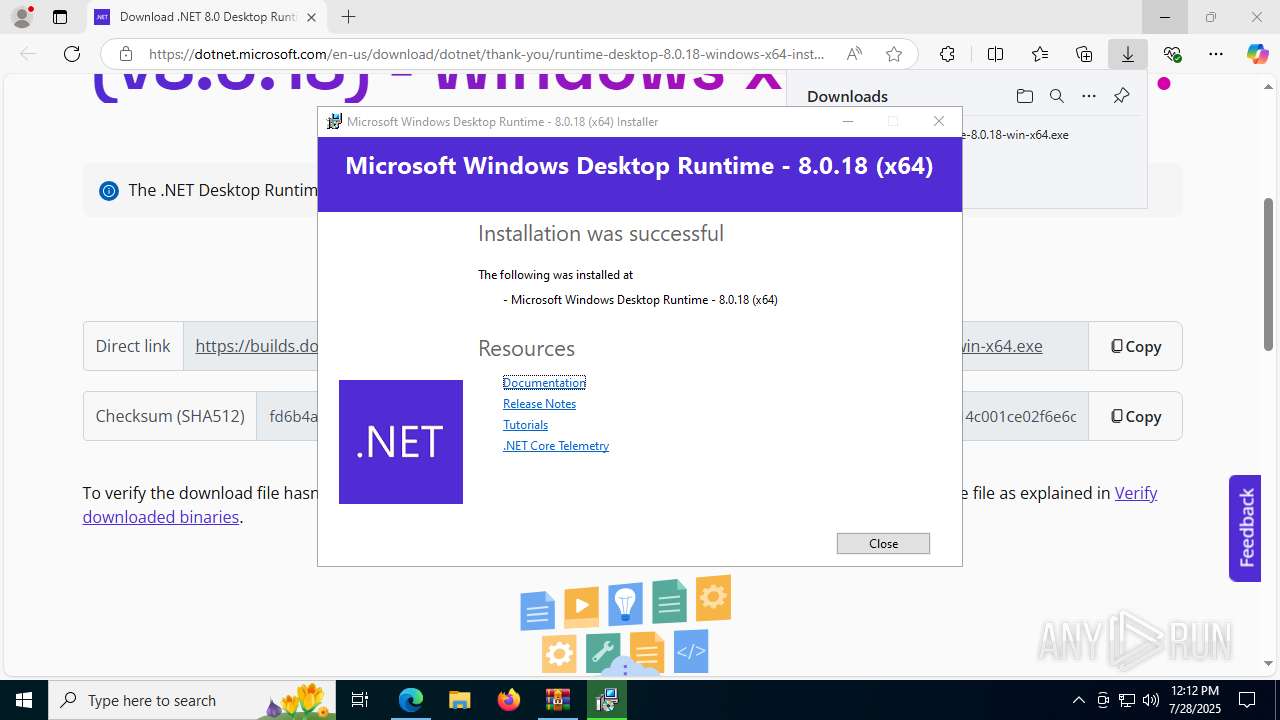
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
SUSPICIOUS
Reads security settings of Internet Explorer
- Xeno.exe (PID: 3760)
- WinRAR.exe (PID: 5456)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- Xeno.exe (PID: 8064)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5456)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 8180)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- msiexec.exe (PID: 6408)
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 8180)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
Searches for installed software
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6408)
Starts itself from another location
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
The process drops C-runtime libraries
- msiexec.exe (PID: 6408)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6408)
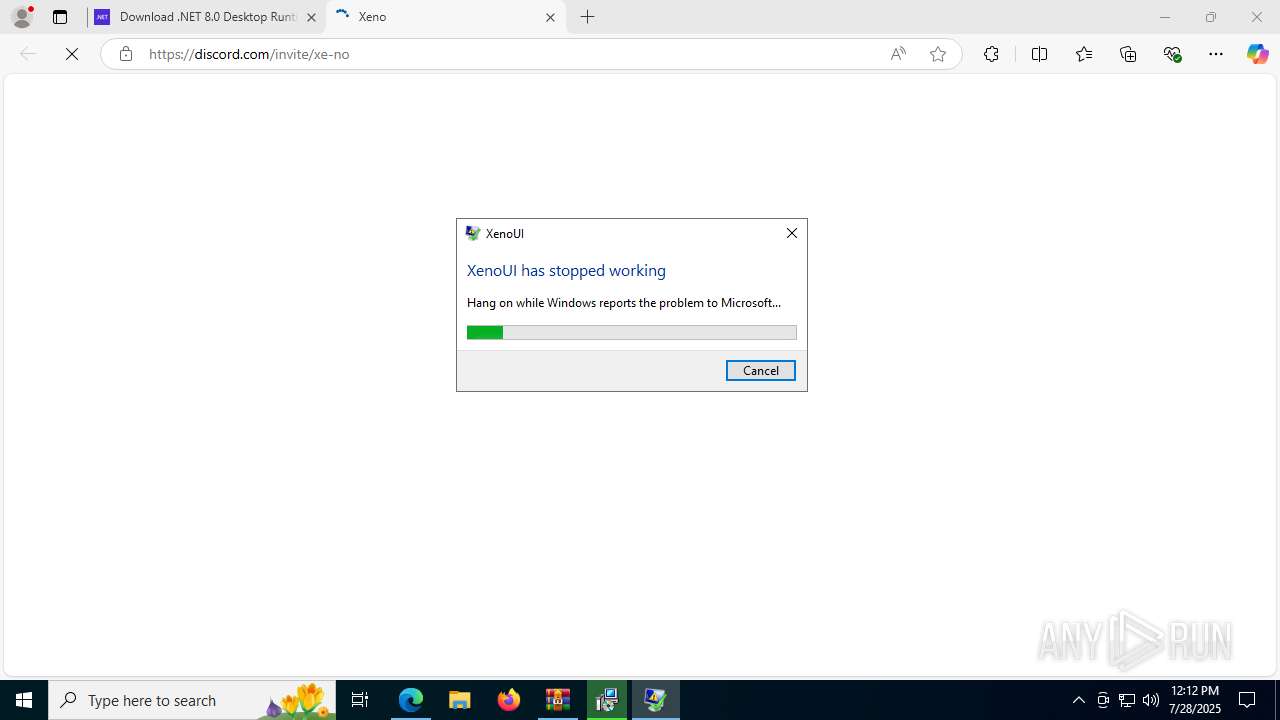
Executes application which crashes
- Xeno.exe (PID: 8064)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5456)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 8180)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- msiexec.exe (PID: 6408)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5456)
- msedge.exe (PID: 3480)
- msiexec.exe (PID: 6408)
Checks supported languages
- Xeno.exe (PID: 3760)
- identity_helper.exe (PID: 7856)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 8180)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- msiexec.exe (PID: 6408)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- msiexec.exe (PID: 7664)
- msiexec.exe (PID: 7956)
- Xeno.exe (PID: 8064)
- msiexec.exe (PID: 7932)
- msiexec.exe (PID: 8048)
Reads the computer name
- Xeno.exe (PID: 3760)
- identity_helper.exe (PID: 7856)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- msiexec.exe (PID: 6408)
- msiexec.exe (PID: 7664)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- Xeno.exe (PID: 8064)
- msiexec.exe (PID: 7932)
- msiexec.exe (PID: 7956)
- msiexec.exe (PID: 8048)
Application launched itself
- msedge.exe (PID: 3480)
Reads Environment values
- identity_helper.exe (PID: 7856)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 8180)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- Xeno.exe (PID: 8064)
Process checks computer location settings
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 4160)
Creates files in the program directory
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
- Xeno.exe (PID: 8064)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6408)
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
Reads the software policy settings
- msiexec.exe (PID: 6408)
- Xeno.exe (PID: 8064)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.18-win-x64.exe (PID: 6876)
Checks proxy server information
- Xeno.exe (PID: 8064)
Creates a software uninstall entry
- msiexec.exe (PID: 6408)
Creates files or folders in the user directory
- Xeno.exe (PID: 8064)
Attempting to use instant messaging service
- msedge.exe (PID: 1204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:07:16 19:14:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Xeno-v1.2.45-New/ |
Total processes
180
Monitored processes
42
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2360,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2412,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=2408 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2216,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=2536 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1880 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3624,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --always-read-main-dll --field-trial-handle=4968,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=6472 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4528f208,0x7ffc4528f214,0x7ffc4528f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
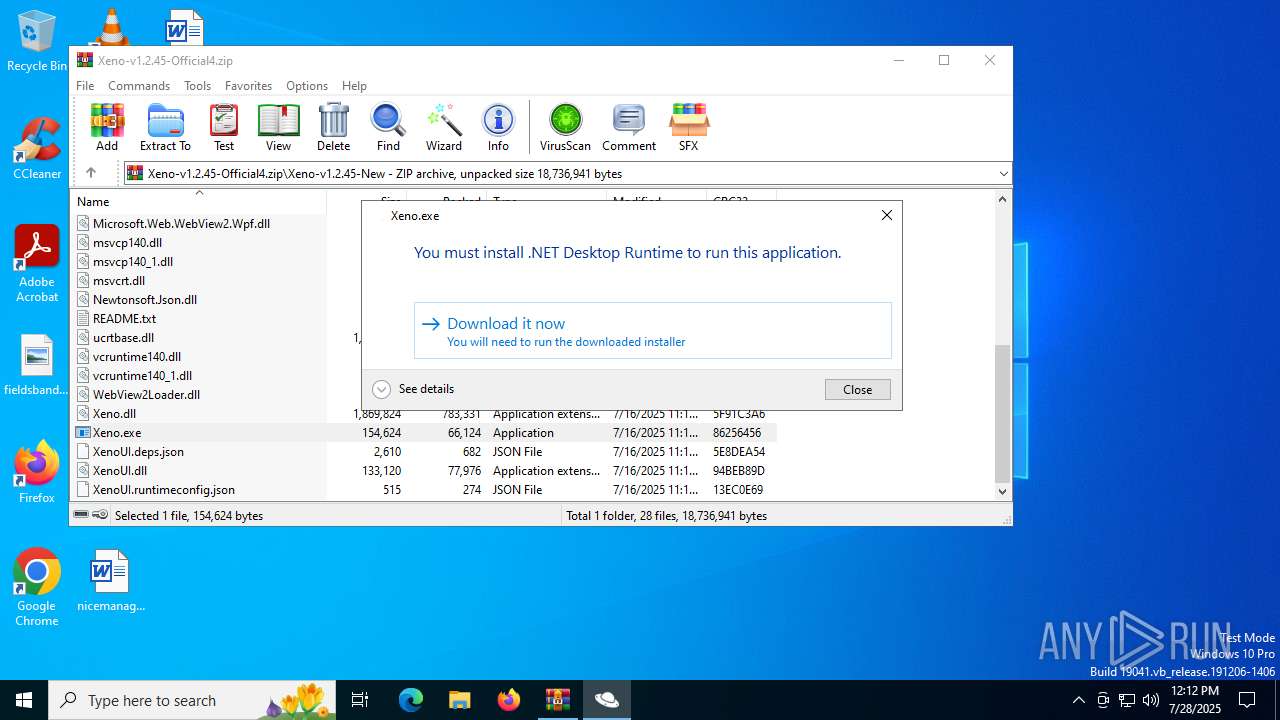
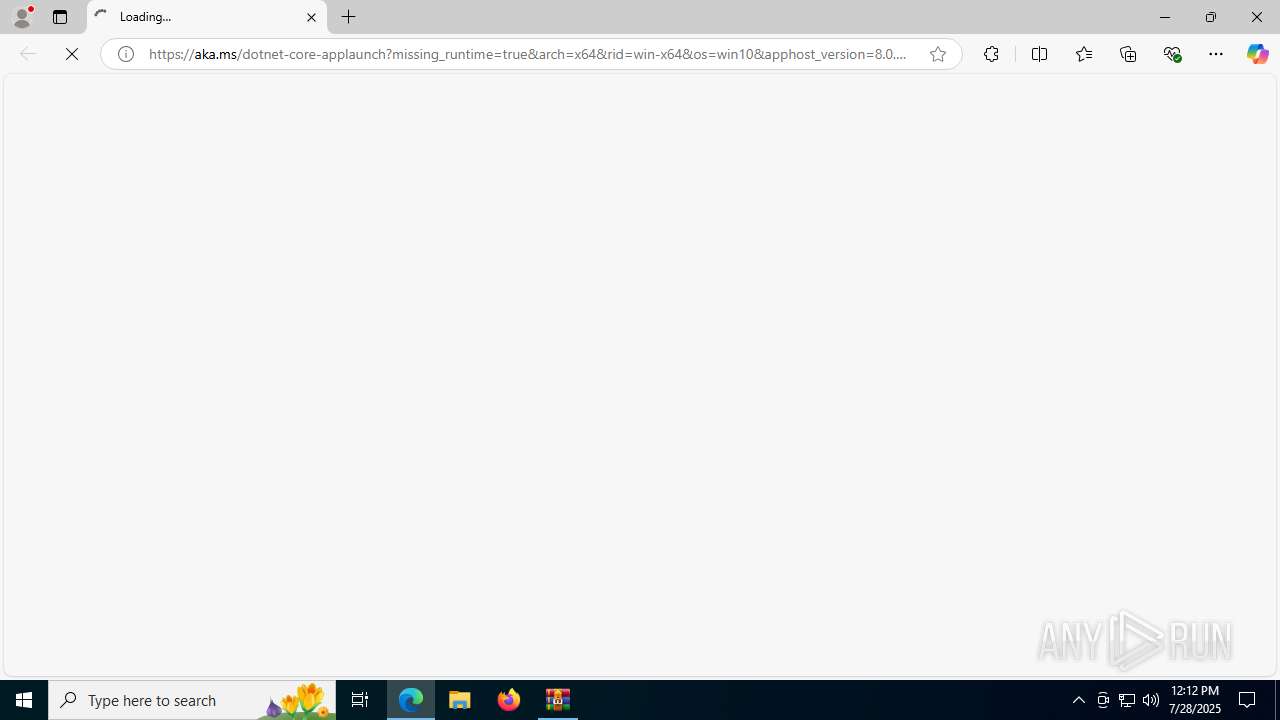
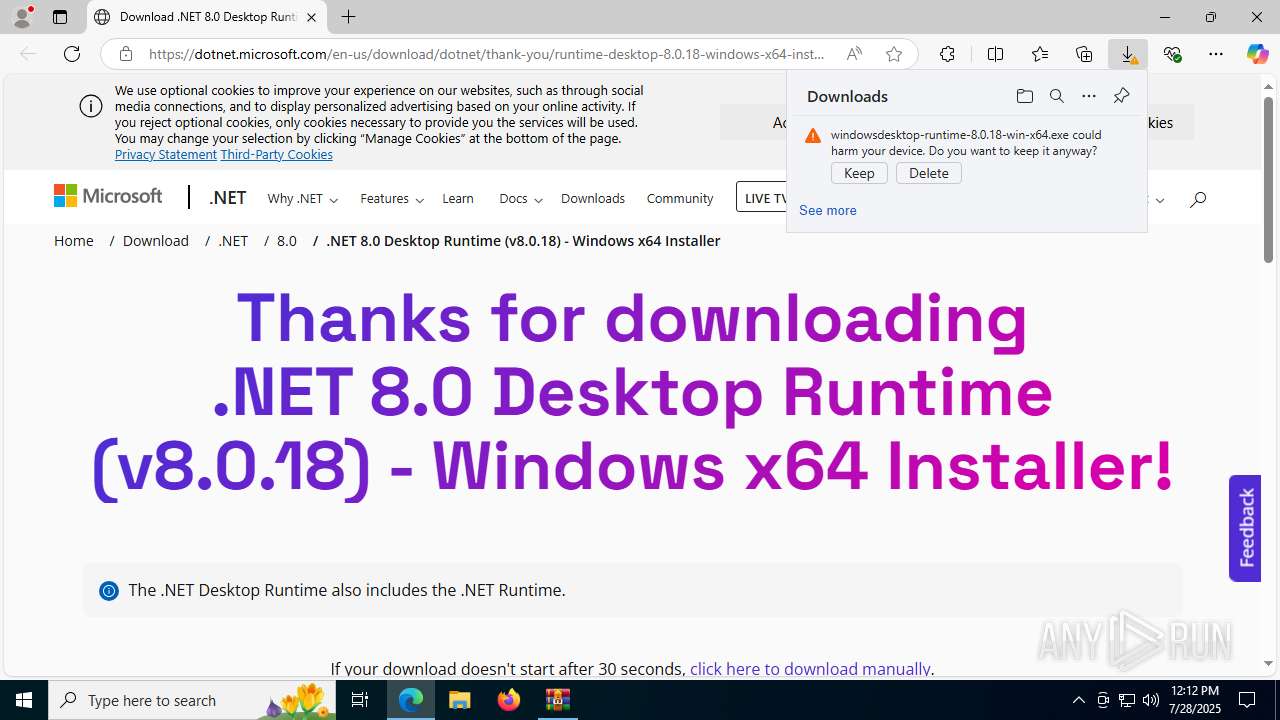
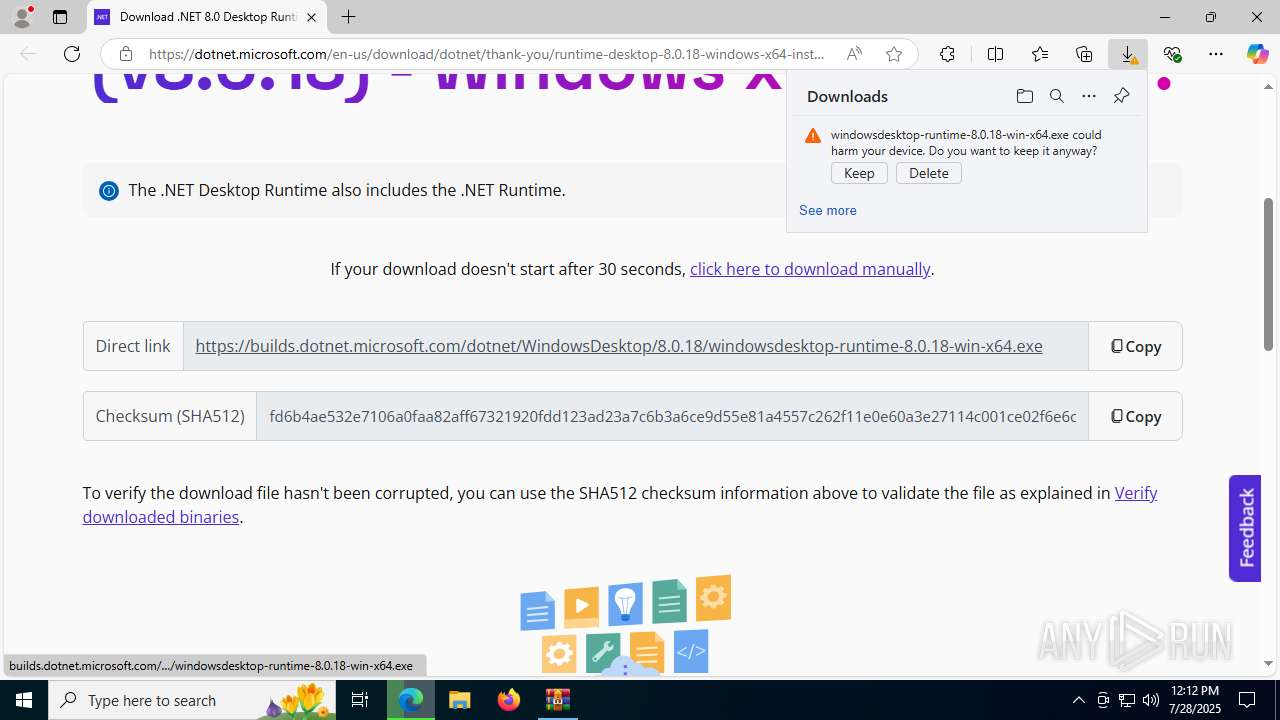
| 3480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.18&gui=true | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | Xeno.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
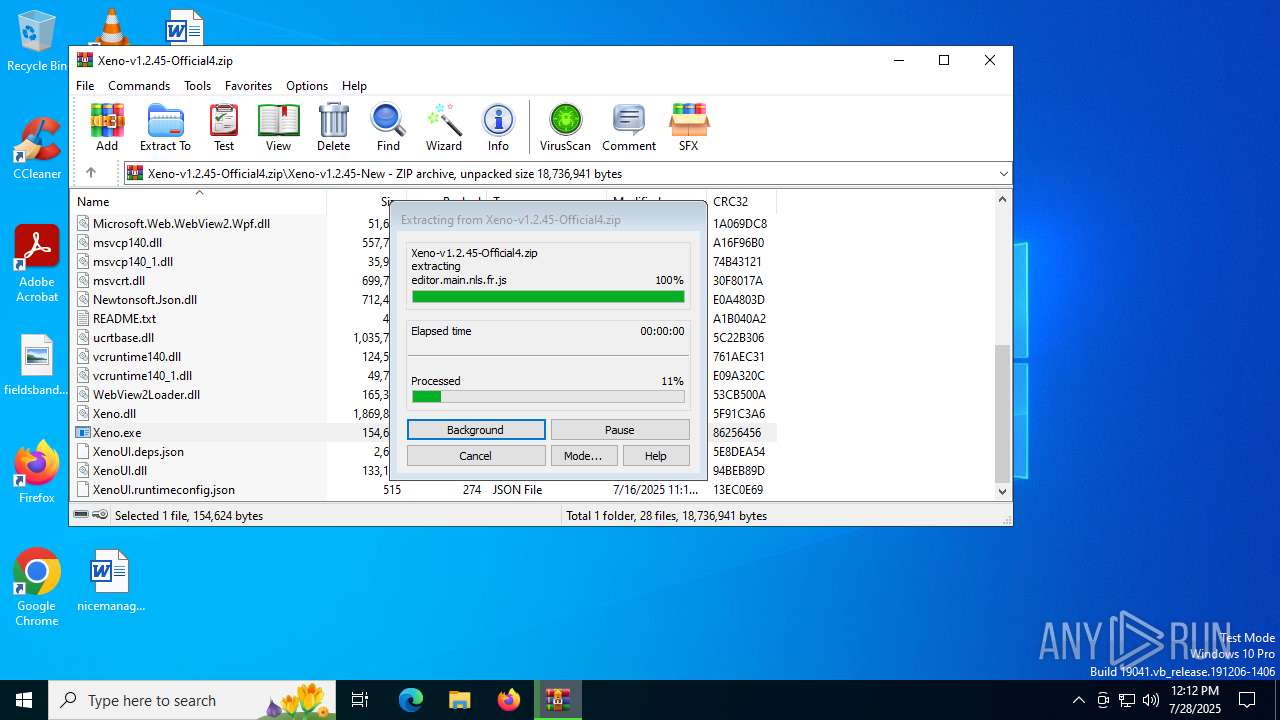
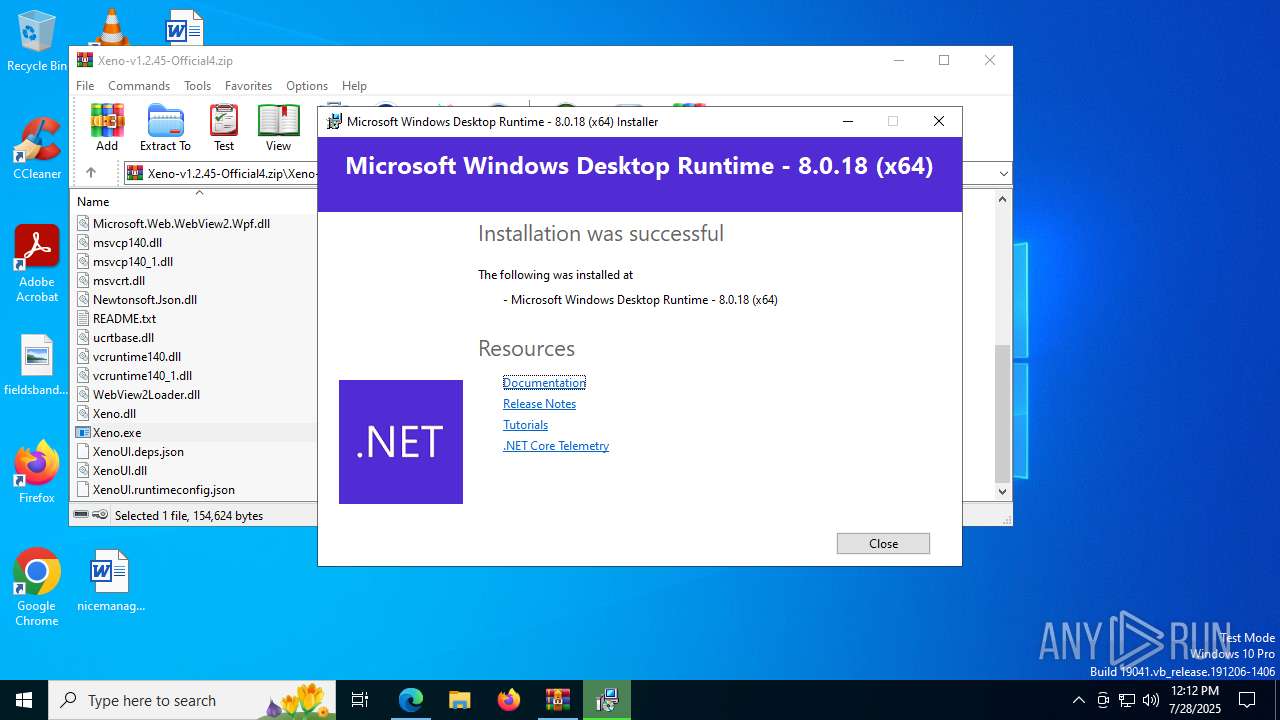
| 3760 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\Xeno.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\Xeno.exe | WinRAR.exe | ||||||||||||
User: admin Company: XenoUI Integrity Level: MEDIUM Description: XenoUI Exit code: 2147516547 Version: 1.2.45 Modules
| |||||||||||||||
| 4032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4192,i,13726387147145651471,16820370378690636917,262144 --variations-seed-version --mojo-platform-channel-handle=4304 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
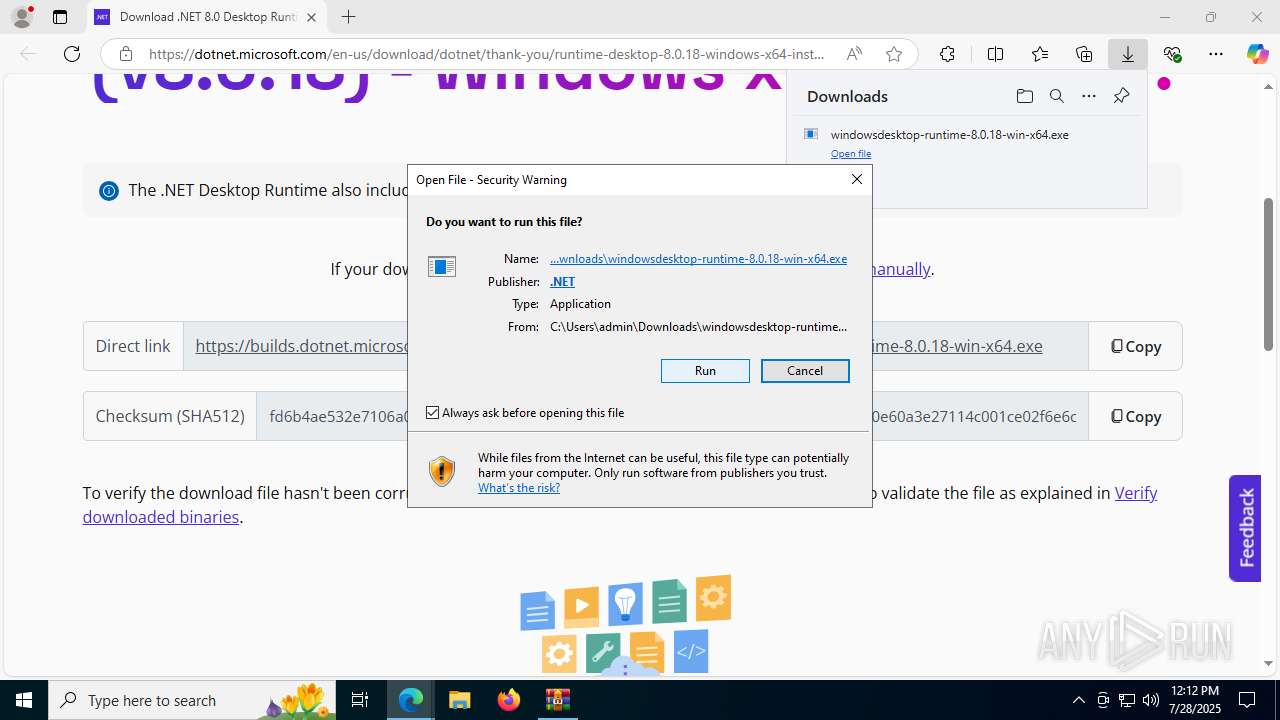
| 4160 | "C:\Users\admin\AppData\Local\Temp\{8D5BF348-45EA-4200-81C6-ABA306B218ED}\.cr\windowsdesktop-runtime-8.0.18-win-x64.exe" -burn.clean.room="C:\Users\admin\Downloads\windowsdesktop-runtime-8.0.18-win-x64.exe" -burn.filehandle.attached=560 -burn.filehandle.self=556 | C:\Users\admin\AppData\Local\Temp\{8D5BF348-45EA-4200-81C6-ABA306B218ED}\.cr\windowsdesktop-runtime-8.0.18-win-x64.exe | windowsdesktop-runtime-8.0.18-win-x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 8.0.18 (x64) Version: 8.0.18.35017 Modules
| |||||||||||||||
Total events
24 585
Read events
23 630
Write events
908
Delete events
47
Modification events
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xeno-v1.2.45-Official4.zip | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3760) Xeno.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3760) Xeno.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
537
Suspicious files
360
Text files
111
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:C8DBF0CA88FACFE87899168A7F7DB52C | SHA256:94B6E91B93C2202DABD659BFF294BEE87C22897A30A6B4930B49051C2FB502DC | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\editor\vs\editor\editor.main.nls.ja.js | text | |
MD5:3BF851CC70F515CBBE1D39DA93E4F041 | SHA256:1F3556EA7233843B9E08B3C97B6727C533D702563E195C2090A438070DC85F0F | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\editor\vs\basic-languages\lua\lua.js | s | |
MD5:EEBDA1FDD970433750C115EAE2F03865 | SHA256:AC729EFB3164F48D6B08F74D4B15060C126A30D40FB4CD4FC9CC94F2E19BD7C7 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-heap-l1-1-0.dll | executable | |
MD5:98DA186FD7D7873C164A51C5D7B77F1A | SHA256:80139E4CAA379D87B1D1DAFC23ACE71D2B330368115F6314140D4AE59C2A78E8 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-runtime-l1-1-0.dll | executable | |
MD5:F91E1FF896B5616919AC97C7095C513E | SHA256:07382C0D91DAD2BB6BA8BD06EA02F12C57ABF7C4E5A70672E9F2954D09A4FFD4 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\editor\vs\editor\editor.main.css | text | |
MD5:23C7DB6E12F6454EF6E7FB98D17924D8 | SHA256:615824C59ED1E07F5924286E9F02F3120B9064D59E115D3F668A914E07839451 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-math-l1-1-0.dll | executable | |
MD5:E10E077BB06209AEDD0D0D378C758F73 | SHA256:8A7BFF1C918539A75C25568DB25933D653C003E016FD7791A37186B42BBB7C20 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-string-l1-1-0.dll | executable | |
MD5:0F593E50BE4715AA8E1F6EB39434EDD5 | SHA256:BF4EA10BE1B64C442AC0CCF4BDF69F6703467176A27E9E14A488D26448A6E179 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\api-ms-win-crt-stdio-l1-1-0.dll | executable | |
MD5:429C26ED27A026442F89C95FF16CE8C2 | SHA256:2A466648AFFD3D51B944F563BB65046A3DA91006A0D90FB2C0B123487A1FC1B3 | |||
| 5456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\concrt140.dll | executable | |
MD5:5FE9A647921DED8A2FAD92DEB9EC4AB2 | SHA256:2405355F0A58067B258F8DF33C327E3A3D716EAAC5A3A5AEBB757842D85BD376 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
82
DNS requests
83
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1204 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:9XclYI2cugVVZiGS2t_esH_5uSOh-NN5_abC-ZMRjFY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6936 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3480 | msedge.exe | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3480 | msedge.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
7296 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7296 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5460 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1204 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1204 | msedge.exe | 2.20.153.252:443 | aka.ms | Telkom-Internet | ZA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aka.ms |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
2200 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
8064 | Xeno.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
1204 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1204 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1204 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1204 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
1204 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
Process | Message |
|---|---|
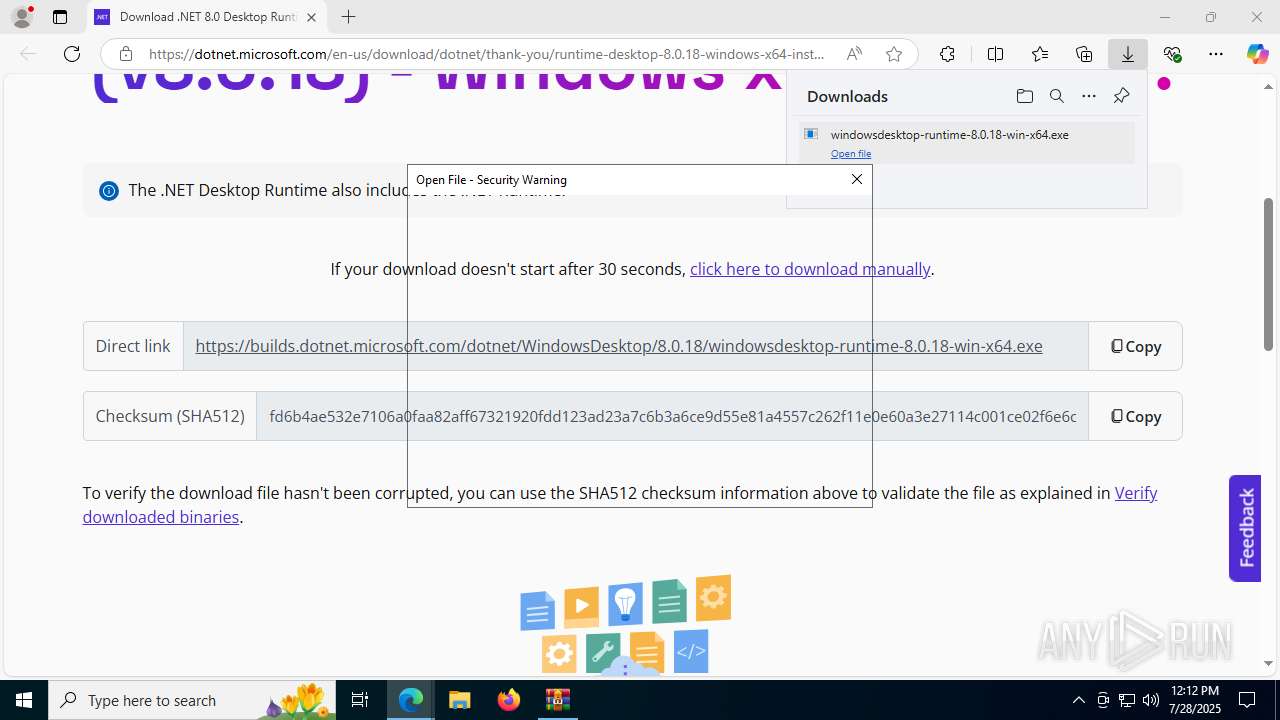
Xeno.exe | You must install .NET to run this application.
App: C:\Users\admin\AppData\Local\Temp\Rar$EXa5456.3082\Xeno-v1.2.45-New\Xeno.exe
Architecture: x64
App host version: 8.0.18
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.18 |
Xeno.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Xeno.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|