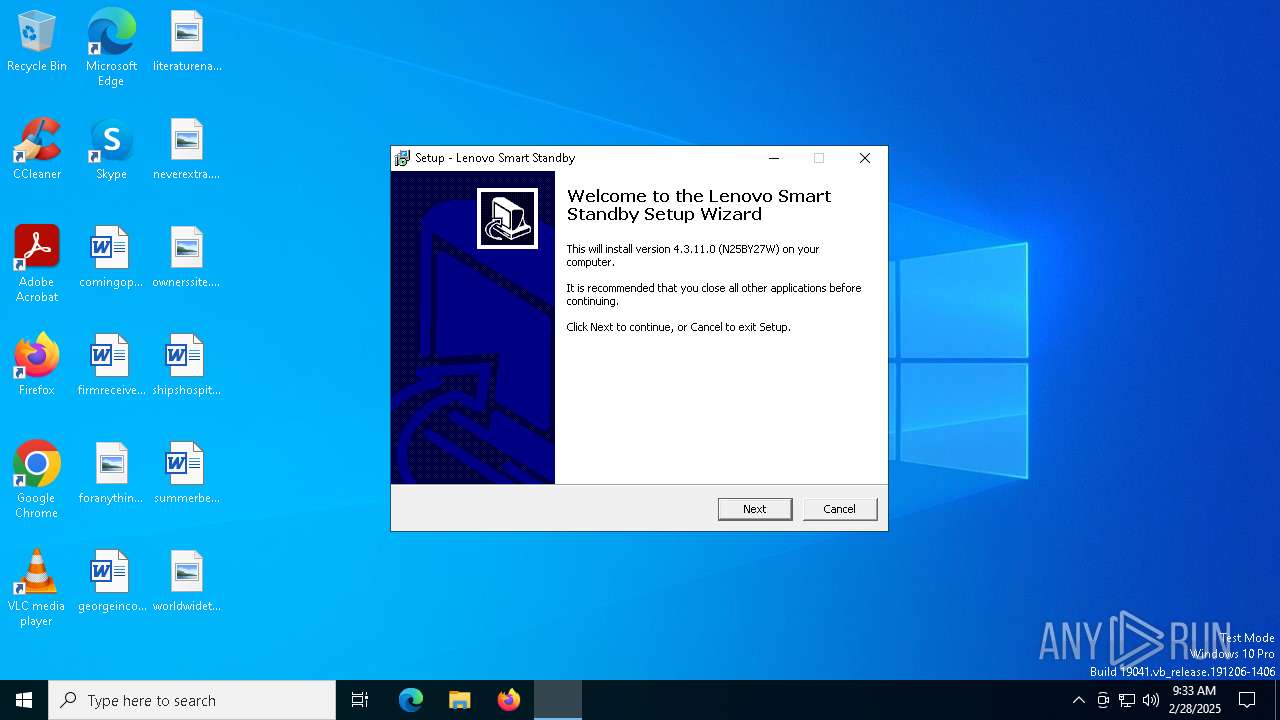
| File name: | n25by27w.exe |
| Full analysis: | https://app.any.run/tasks/22cc690d-e96c-44ee-8545-498bd2f9ede3 |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2025, 09:32:50 |
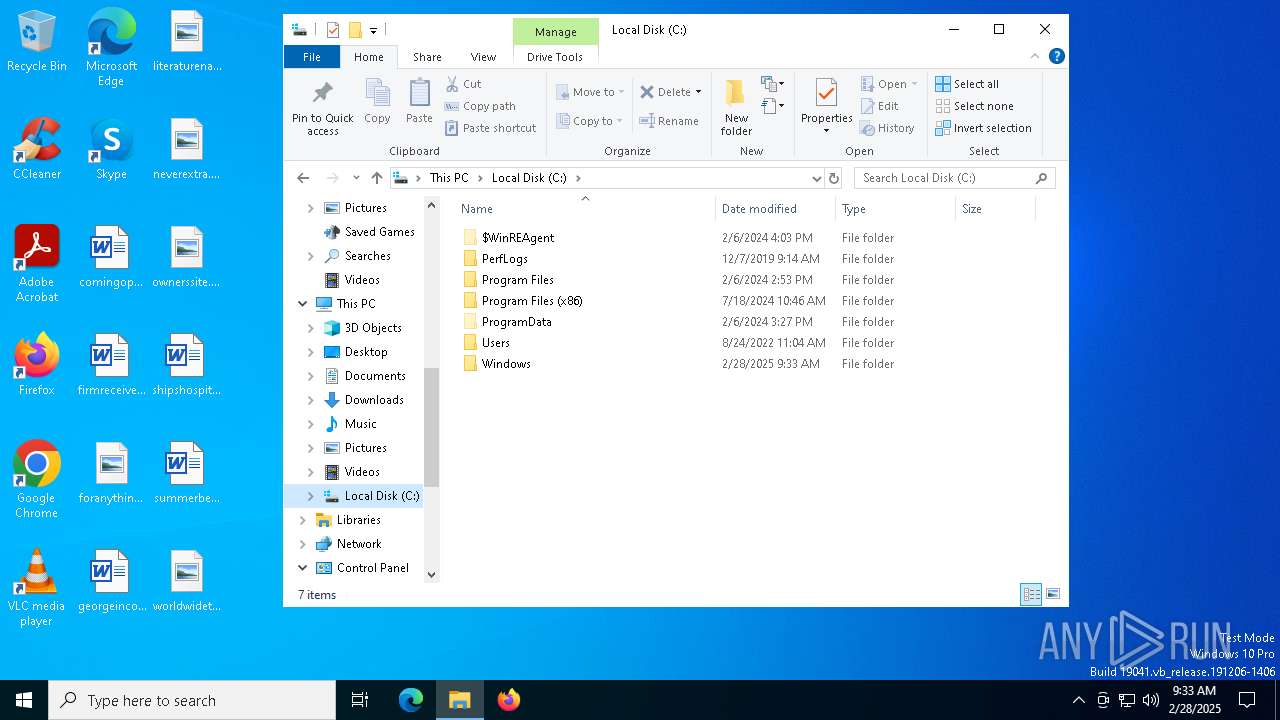
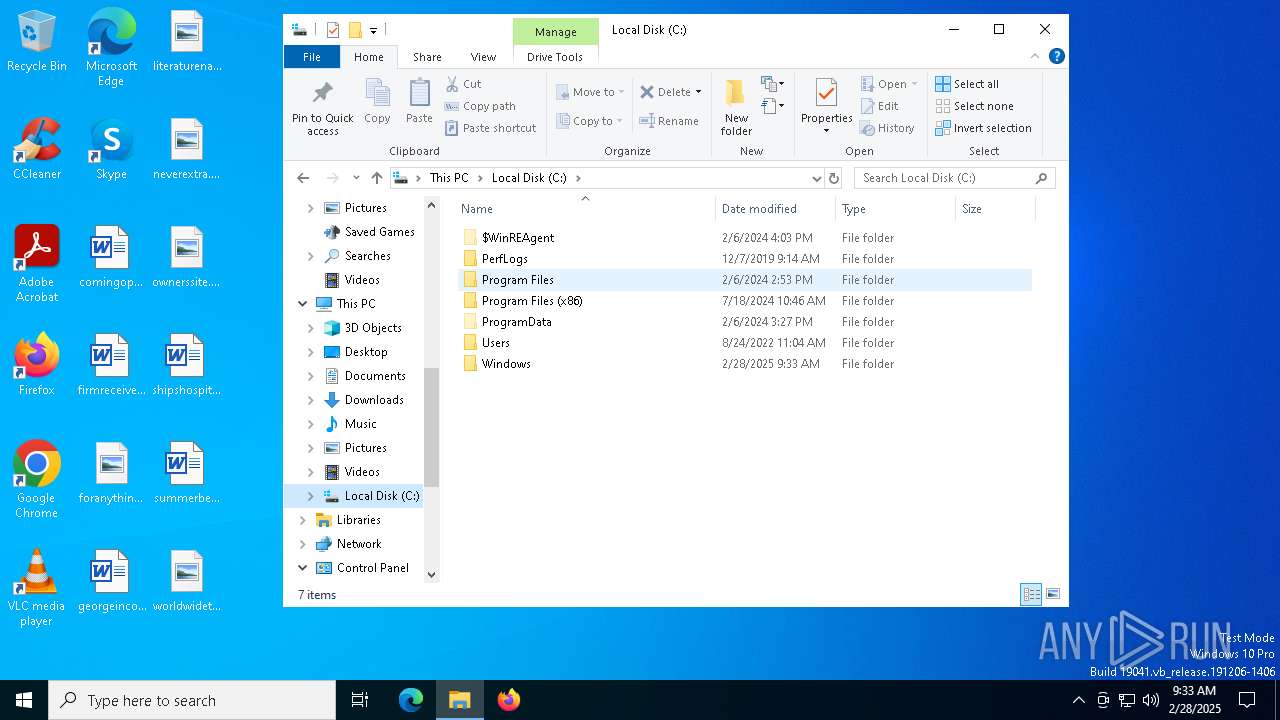
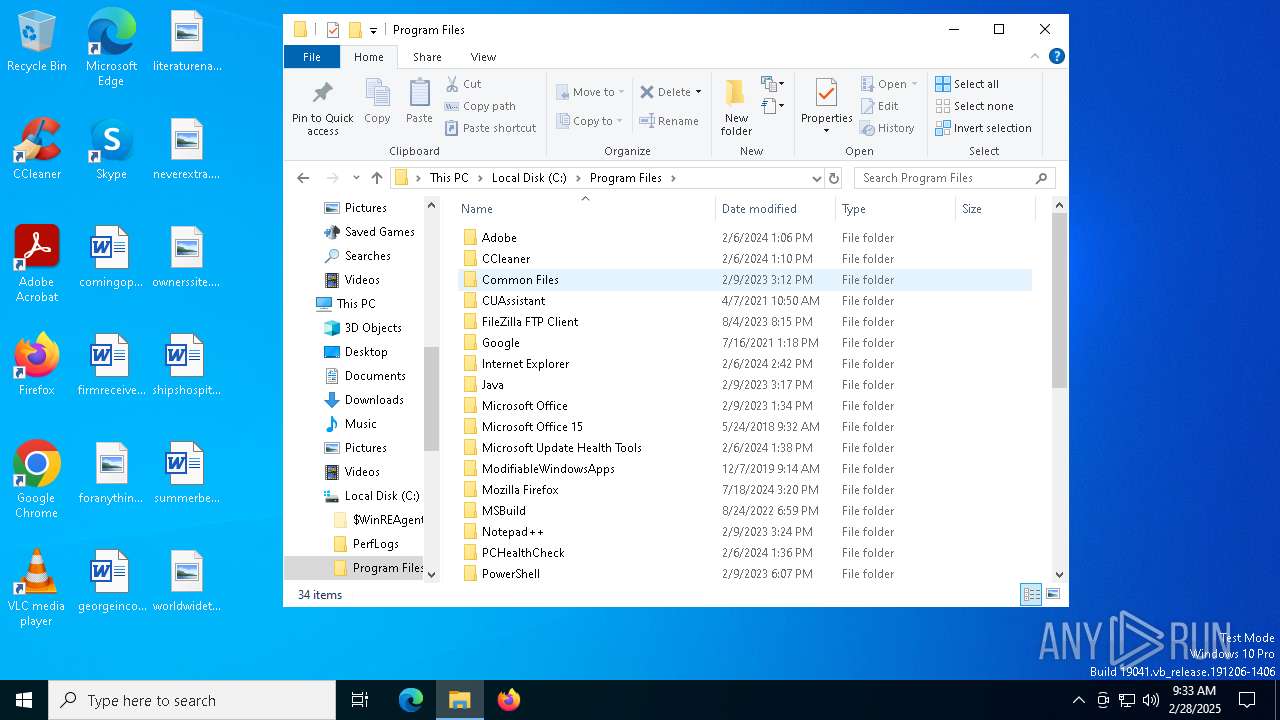
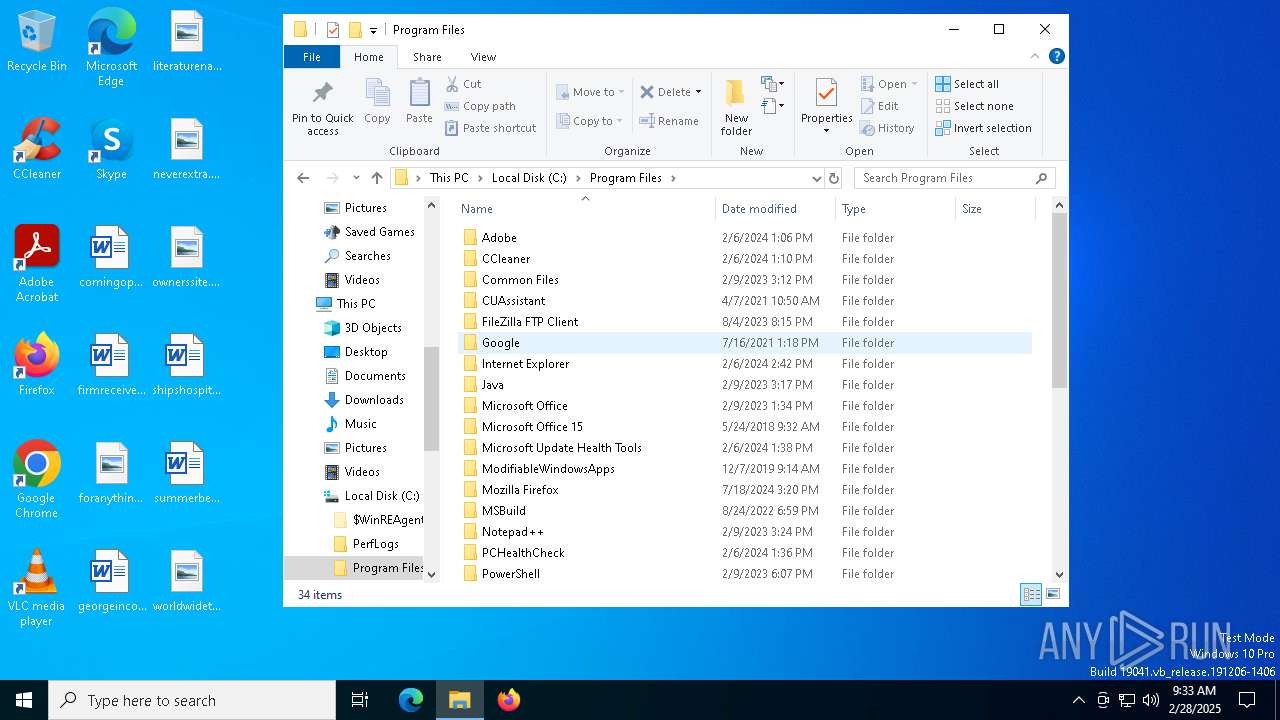
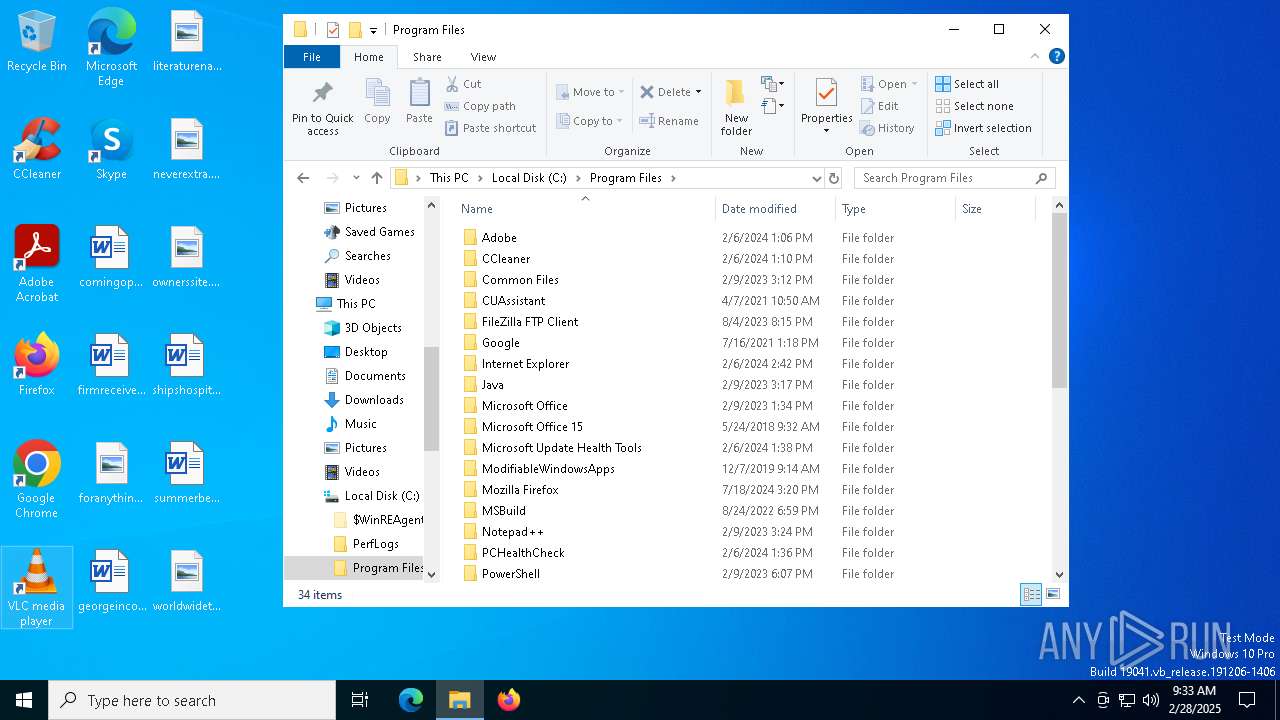
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | 5E644A3B9ABB99B38C66FDA1982189AC |
| SHA1: | DB028DB188734117D29C4A6B5F10851973FFA8EA |
| SHA256: | 283BF3304563C0B2FC1B74AE4404E2402916A9ED4B15D42FE8963CBAC3068C4E |
| SSDEEP: | 49152:ubZPlhu8PICCEmRlIZpgdnE2Zrvwc4yg63C8Dhi8gtv5h8uFrqgu2ucU8u6u4q/H:8988PIfZRWDgdbrvA6JDhzgV5XQ2uWuj |
MALICIOUS
No malicious indicators.SUSPICIOUS
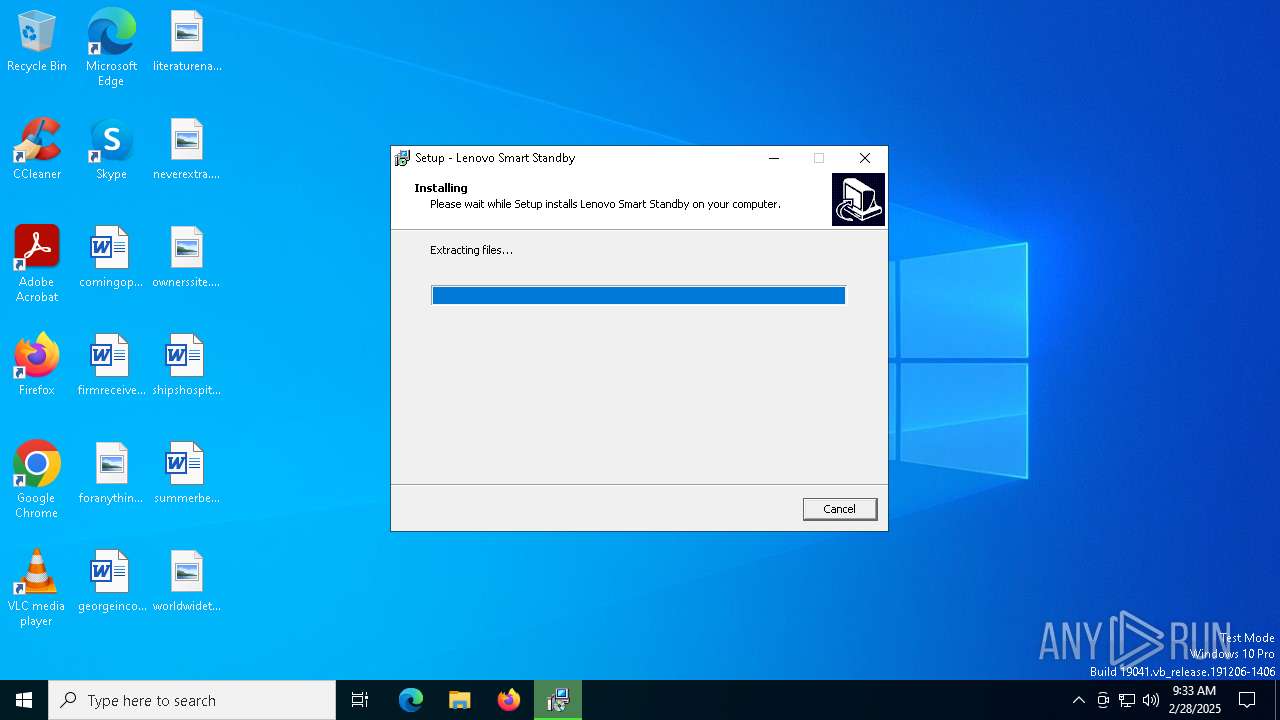
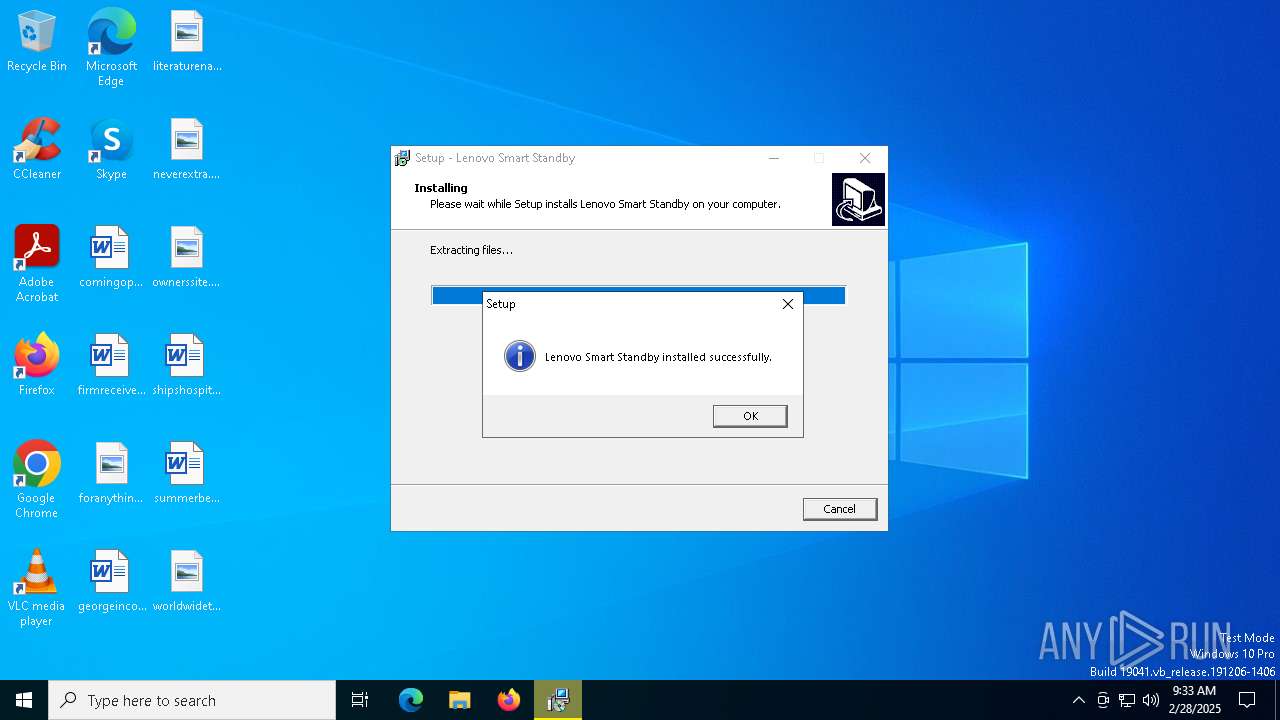
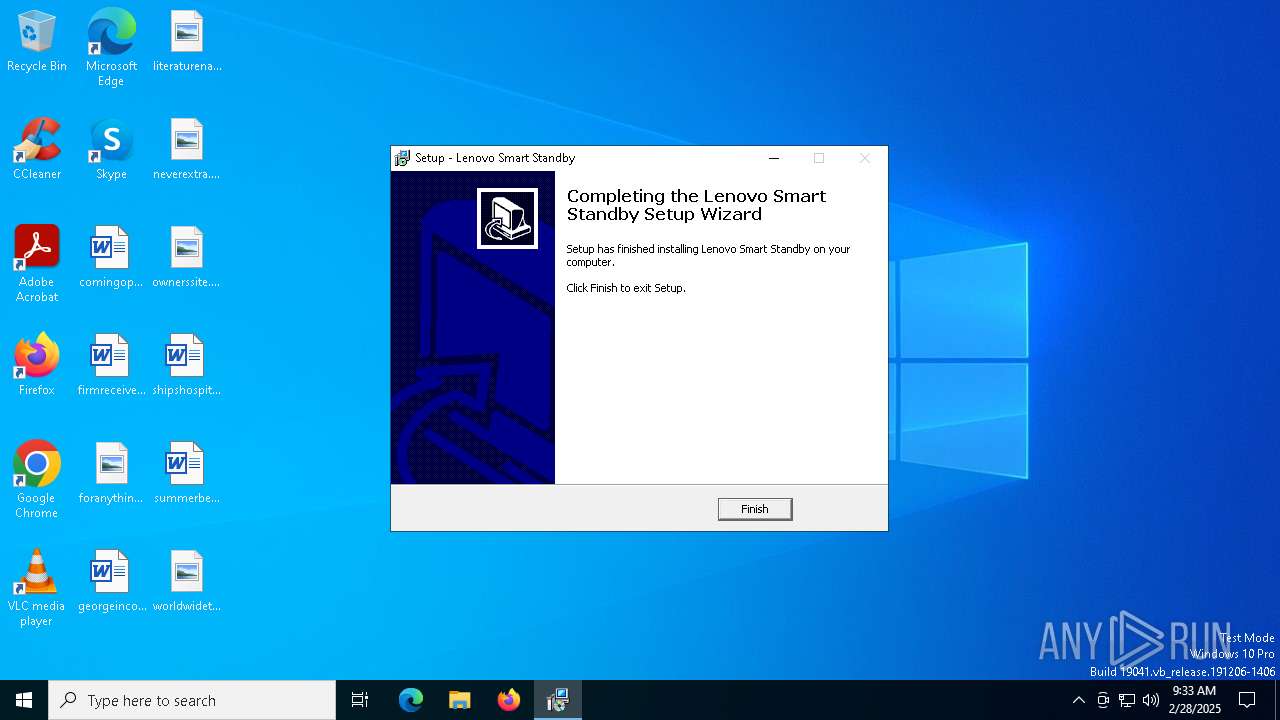
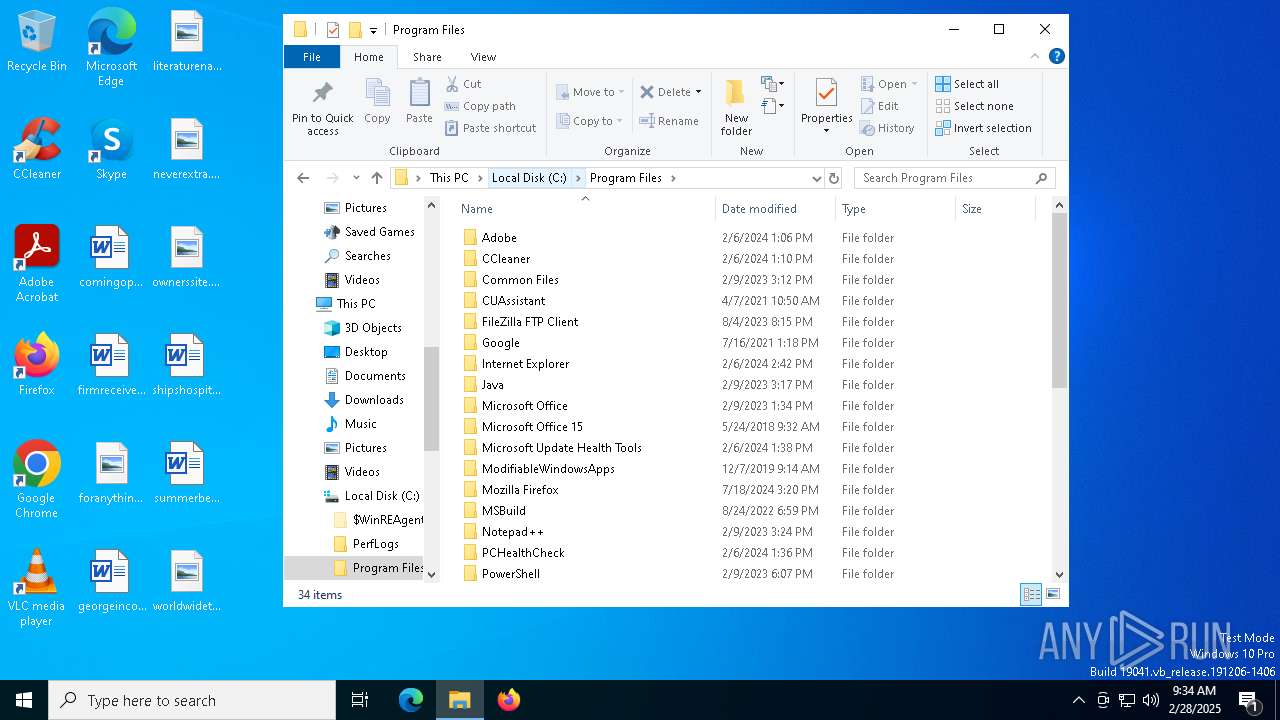
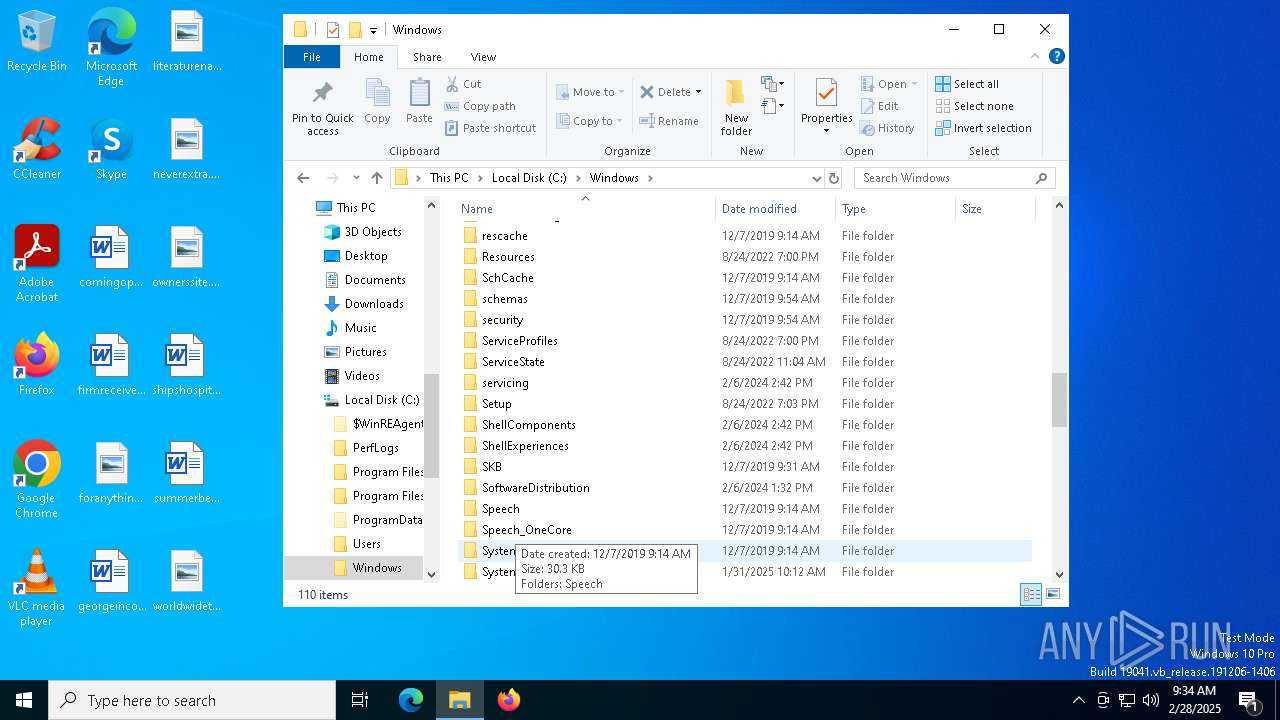
Executable content was dropped or overwritten
- n25by27w.exe (PID: 3332)
- n25by27w.exe (PID: 7212)
- n25by27w.tmp (PID: 7236)
- pnputil.exe (PID: 904)
- drvinst.exe (PID: 6972)
Reads security settings of Internet Explorer
- n25by27w.tmp (PID: 4040)
- ShellExperienceHost.exe (PID: 2504)
Starts application with an unusual extension
- n25by27w.exe (PID: 7212)
Reads the Windows owner or organization settings
- n25by27w.tmp (PID: 7236)
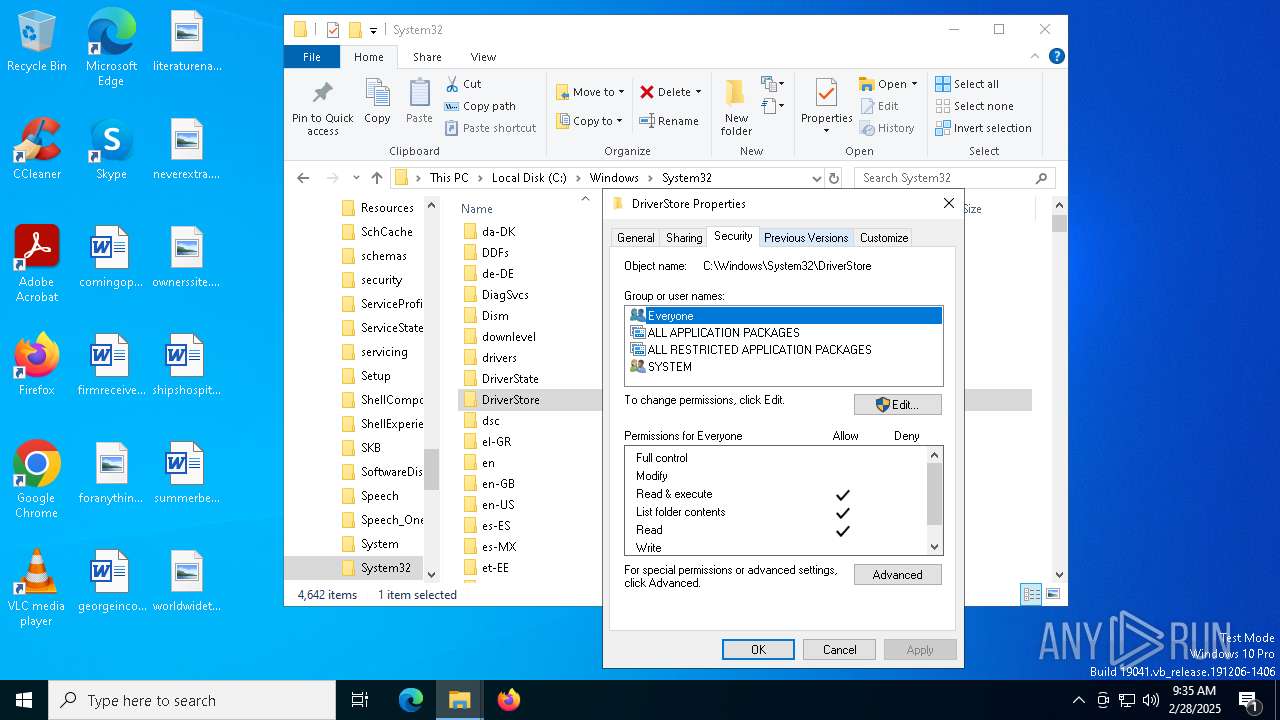
Checks Windows Trust Settings
- drvinst.exe (PID: 6972)
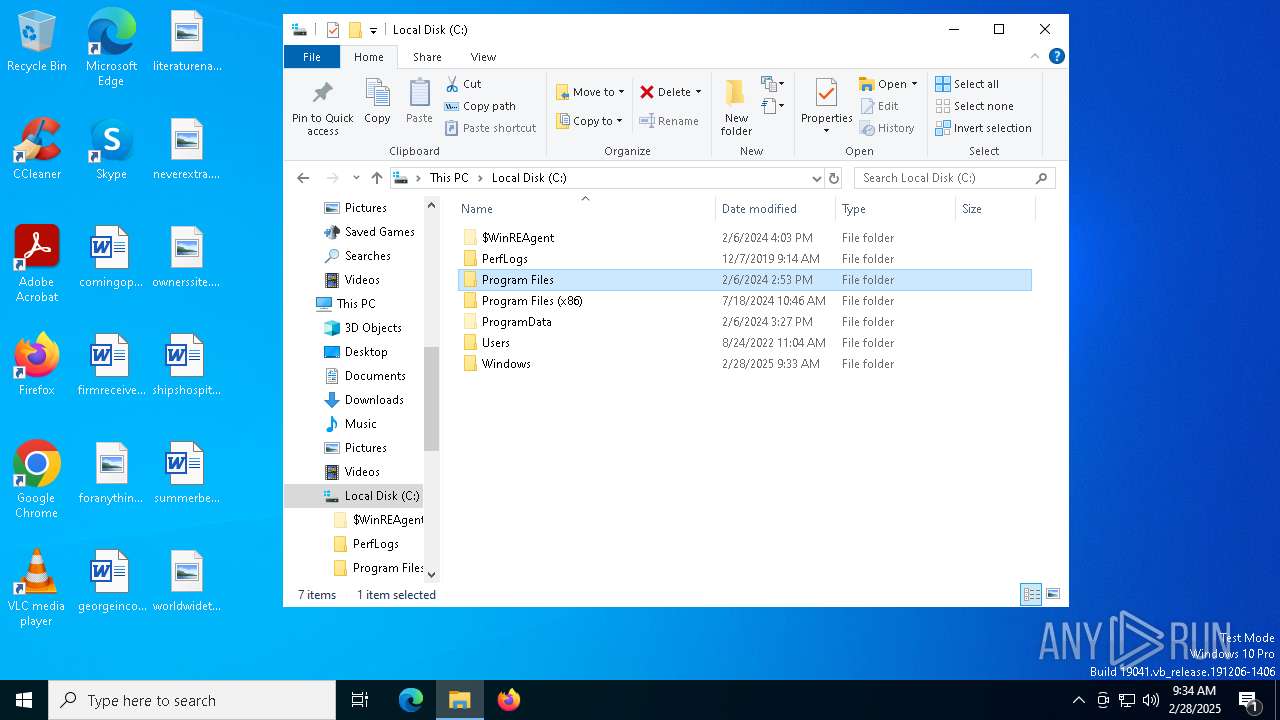
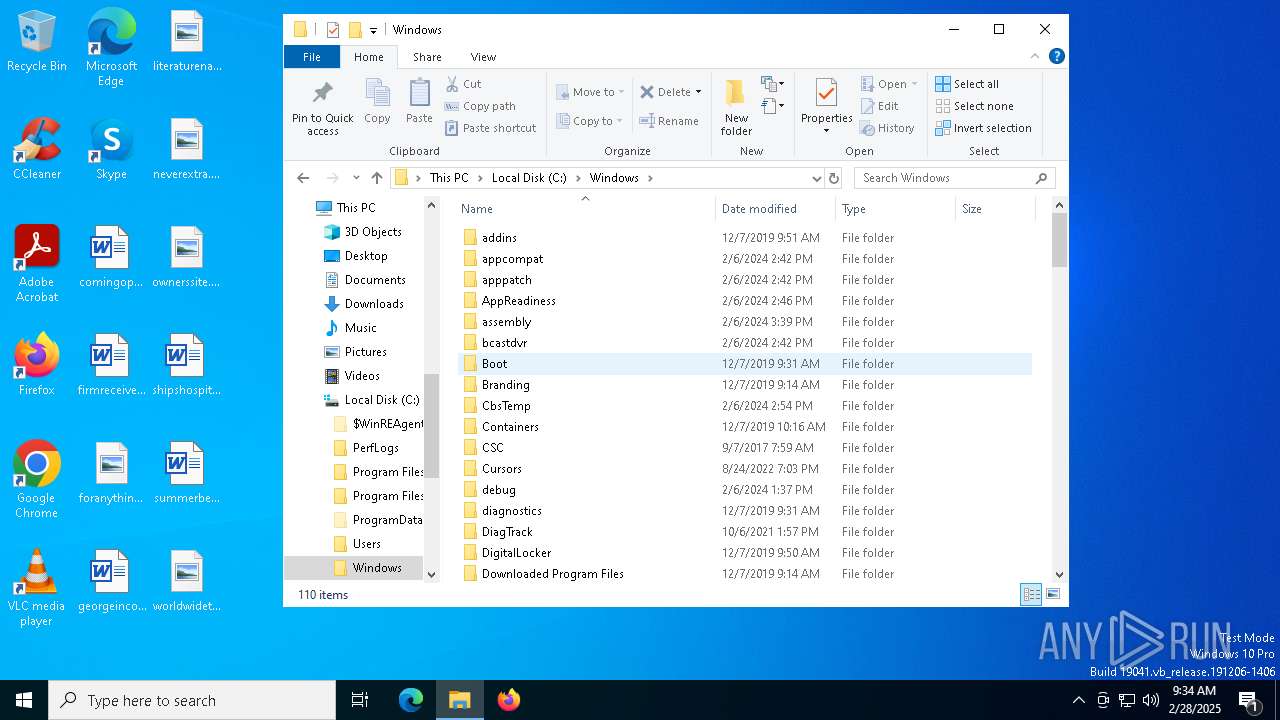
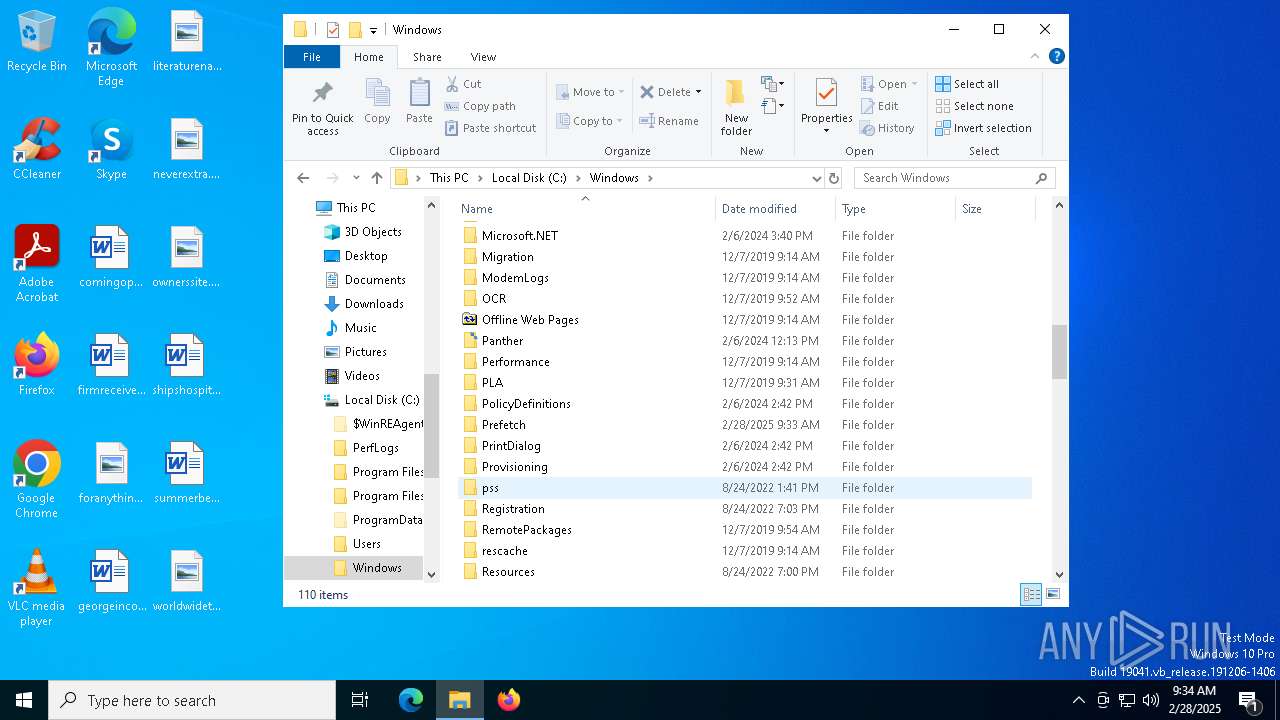
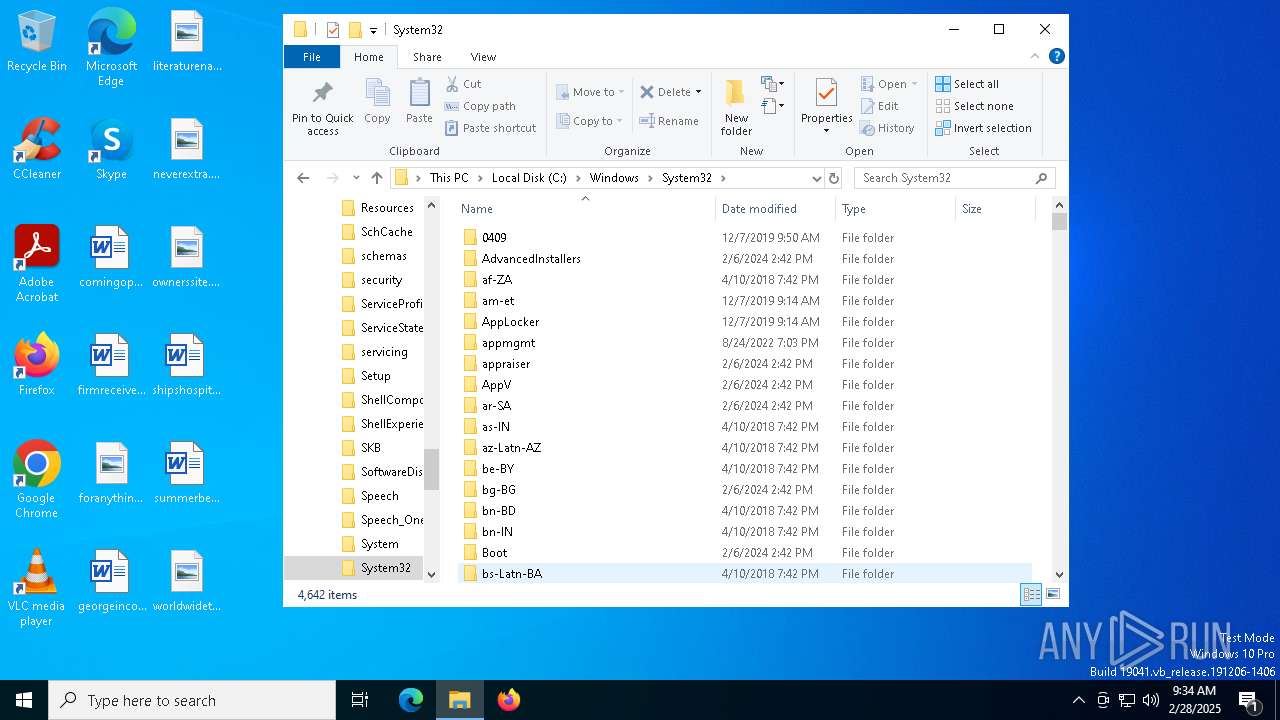
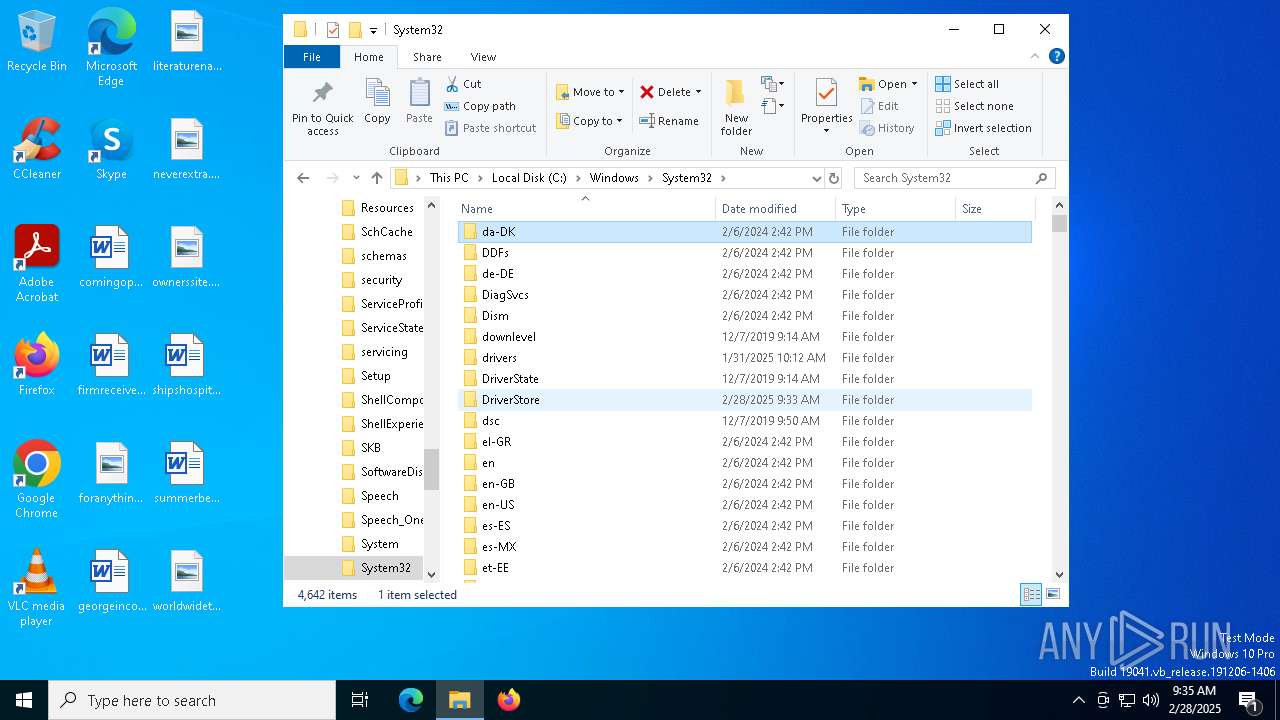
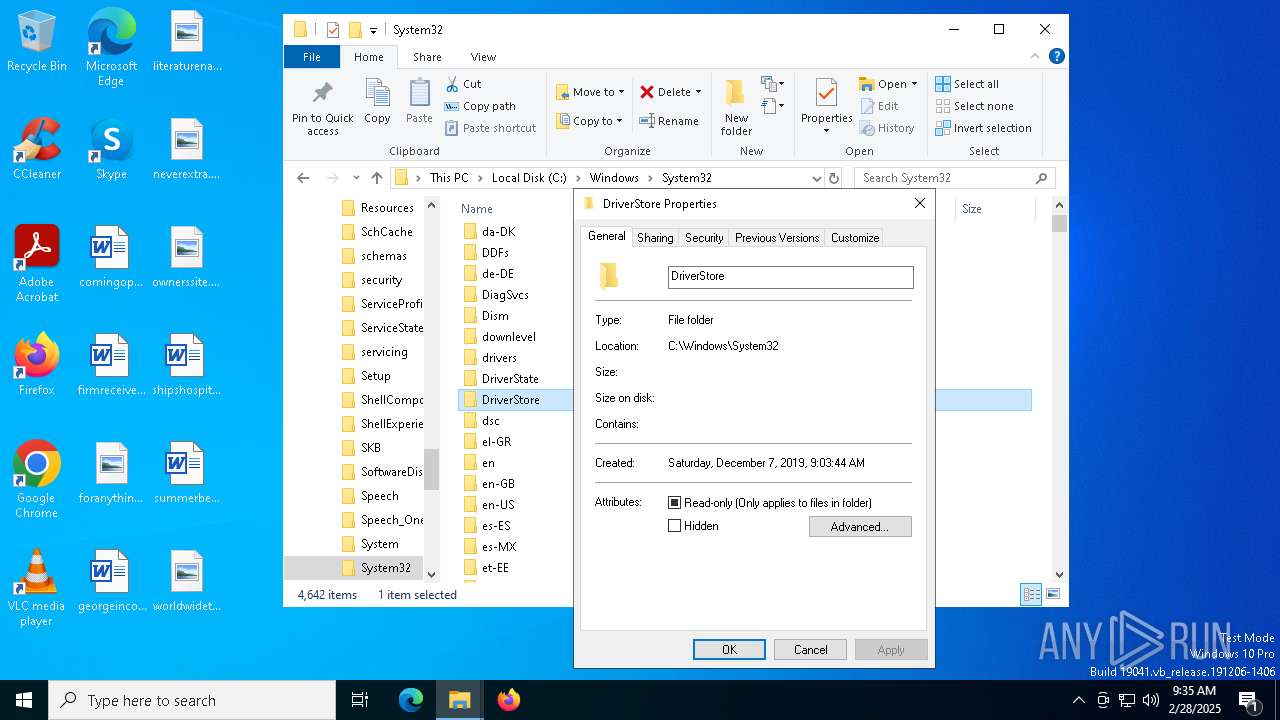
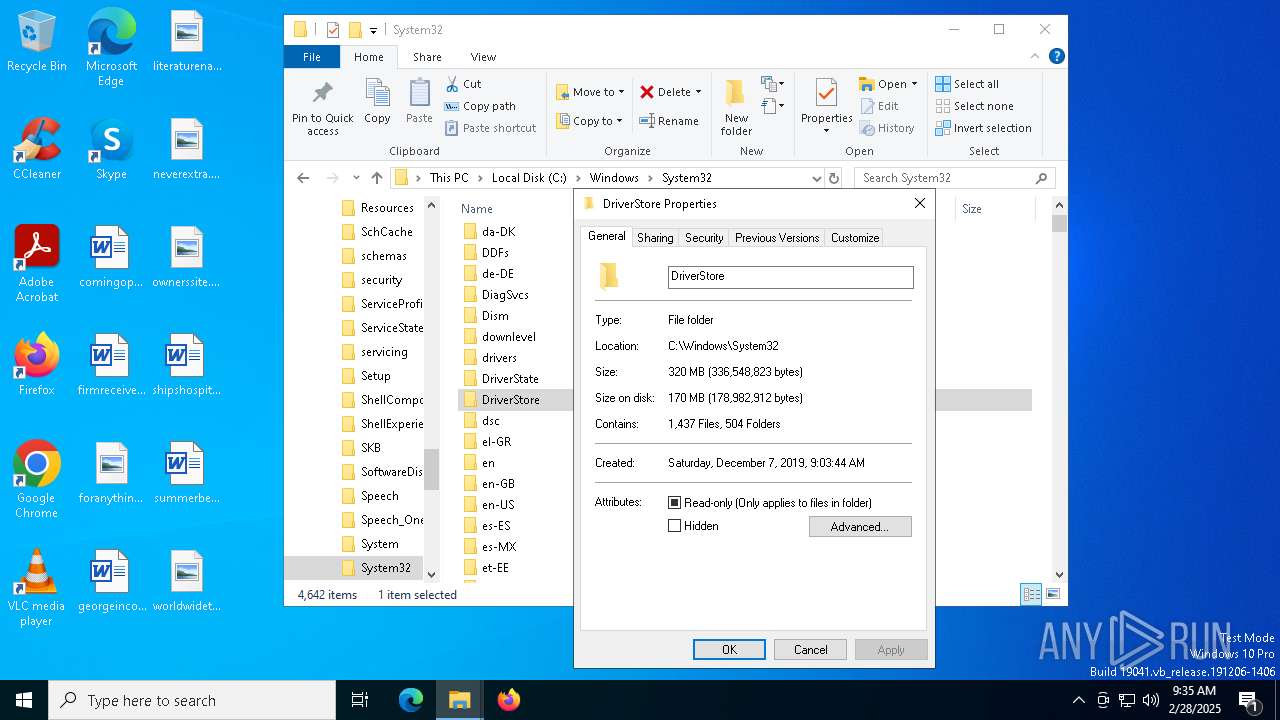
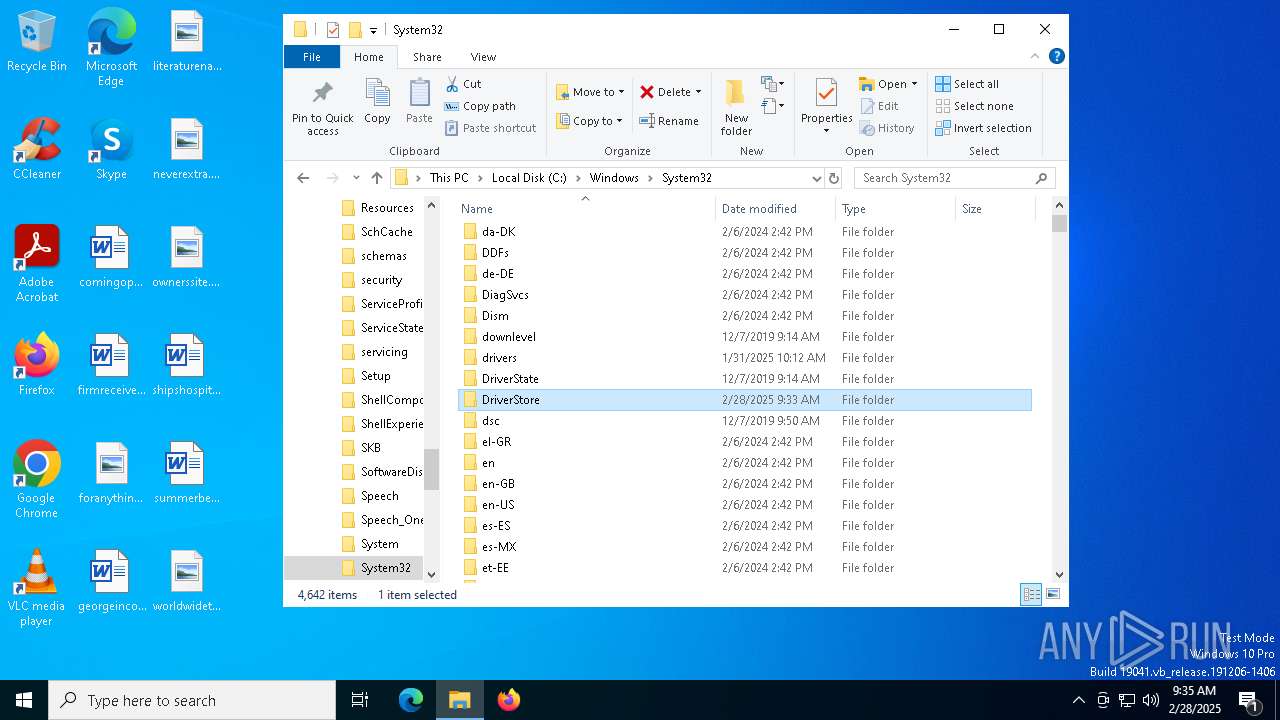
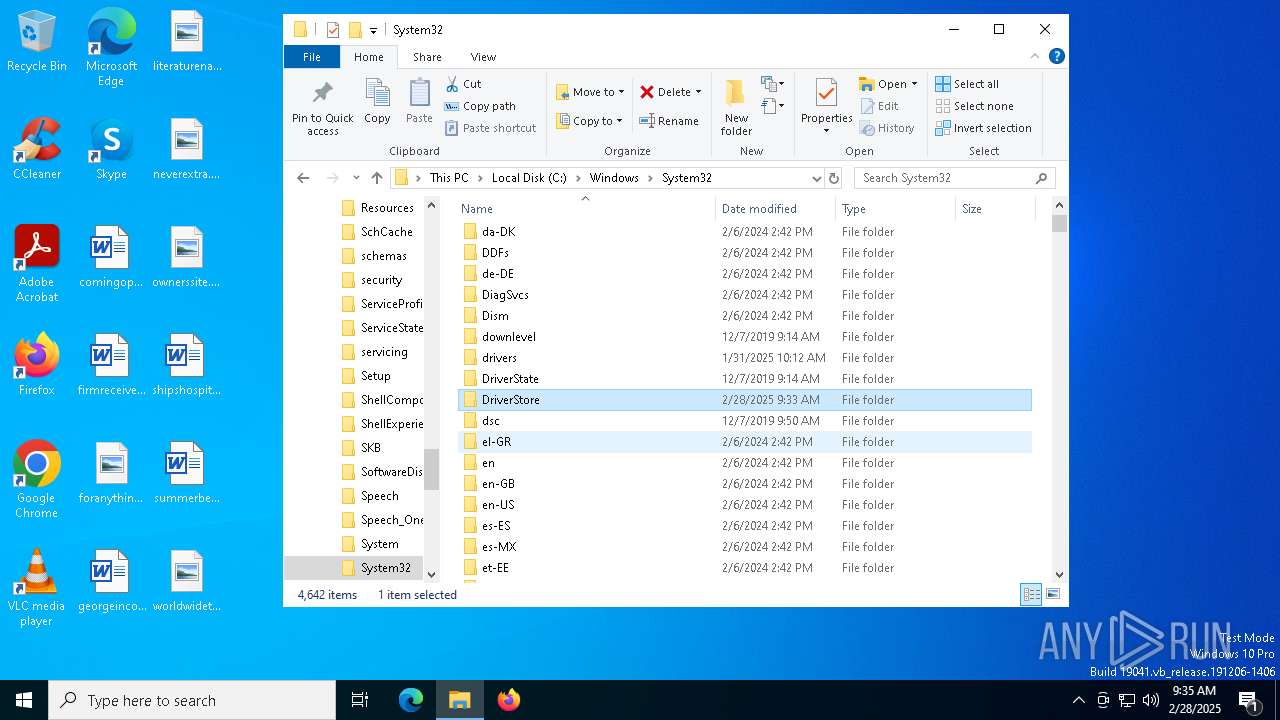
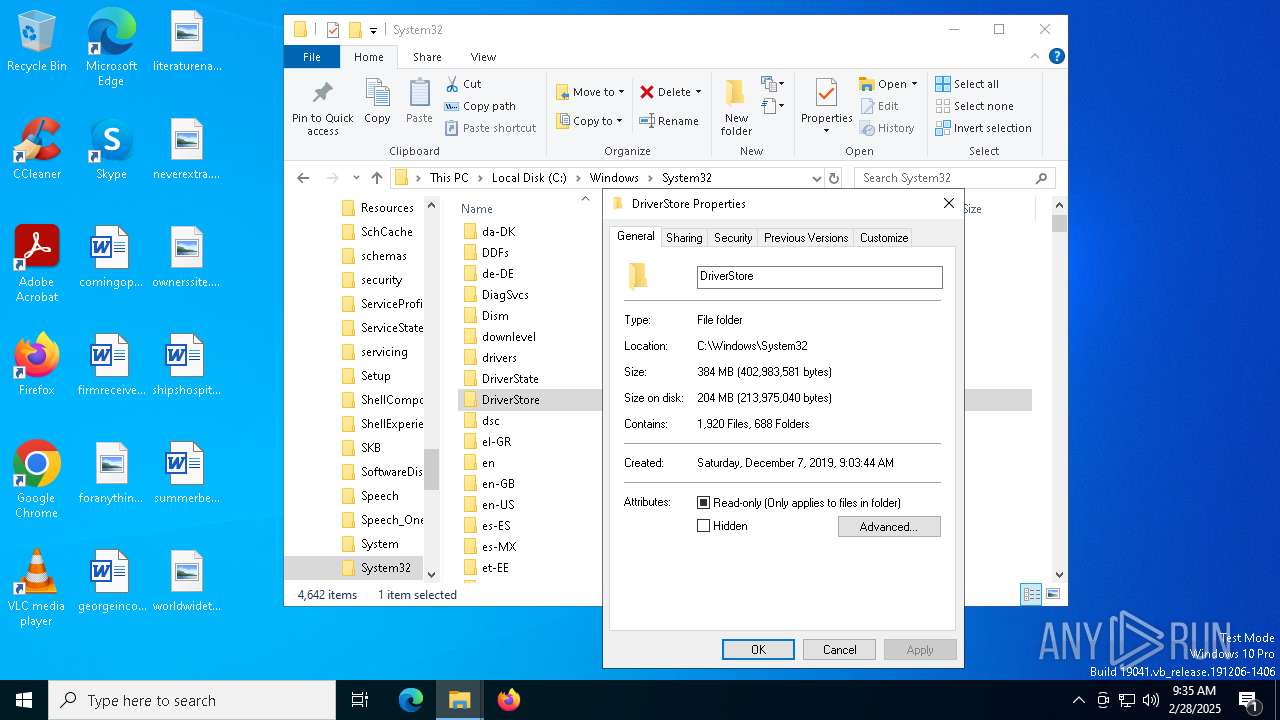
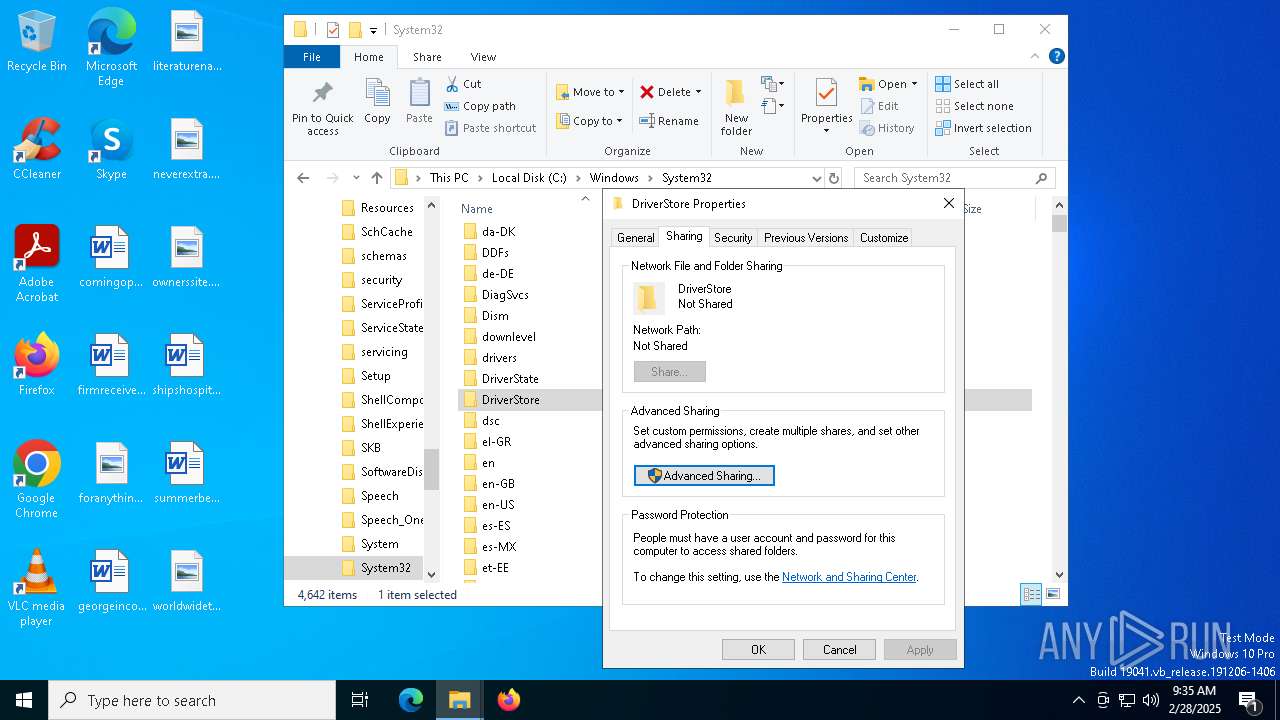
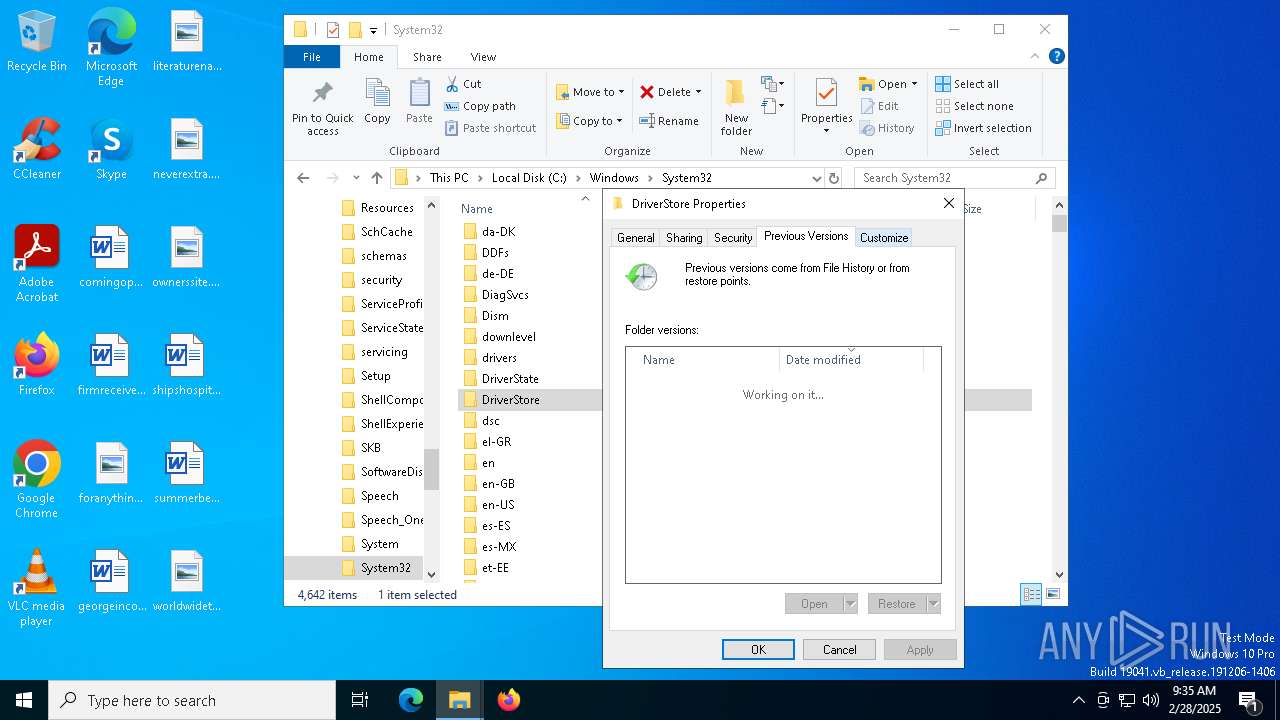
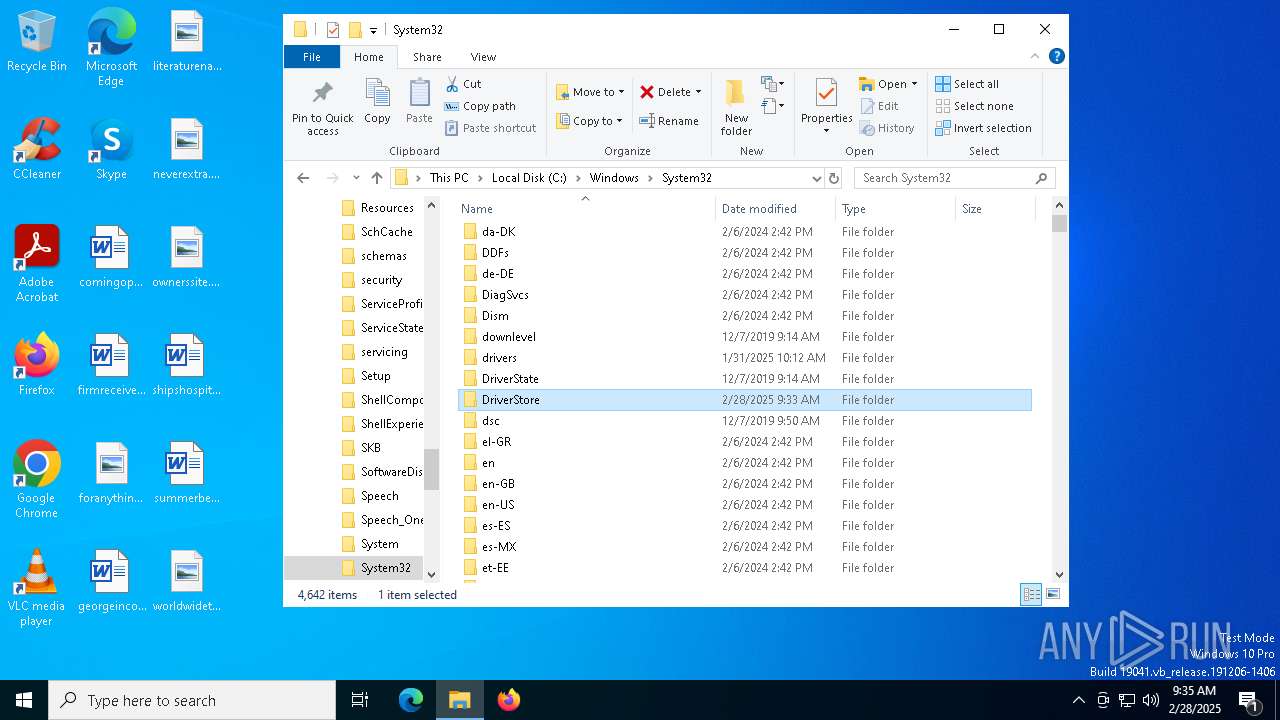
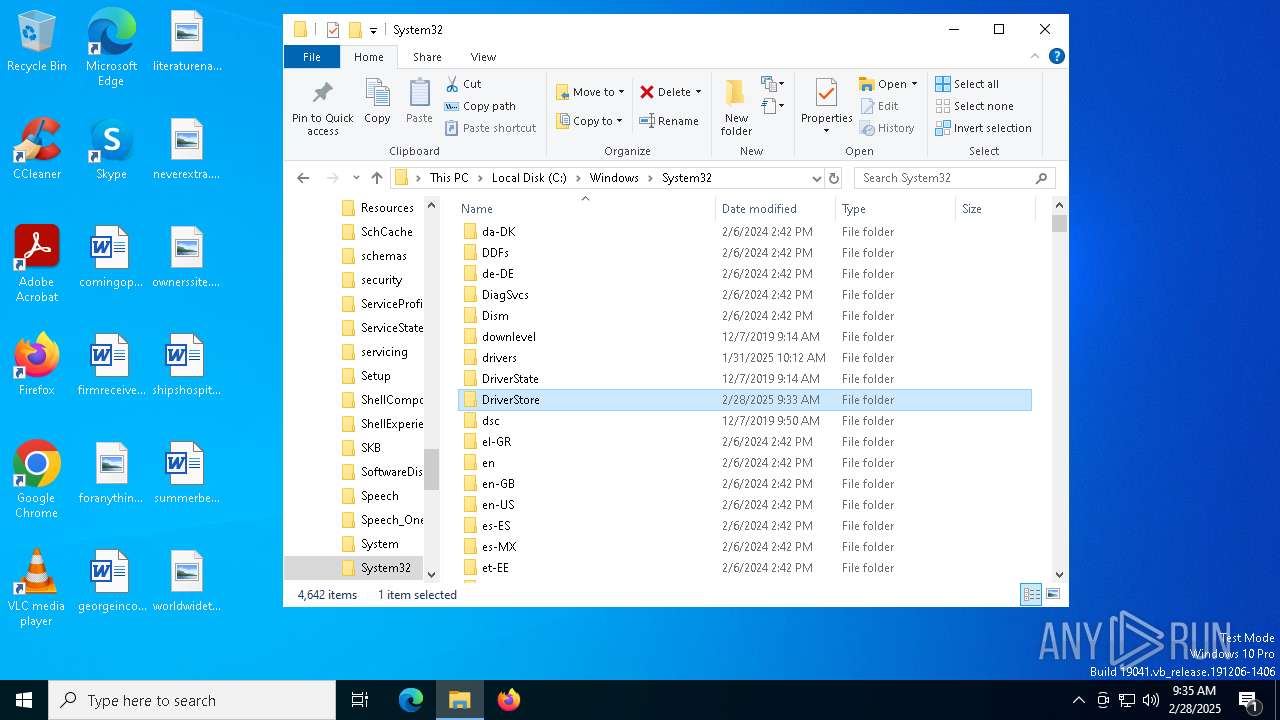
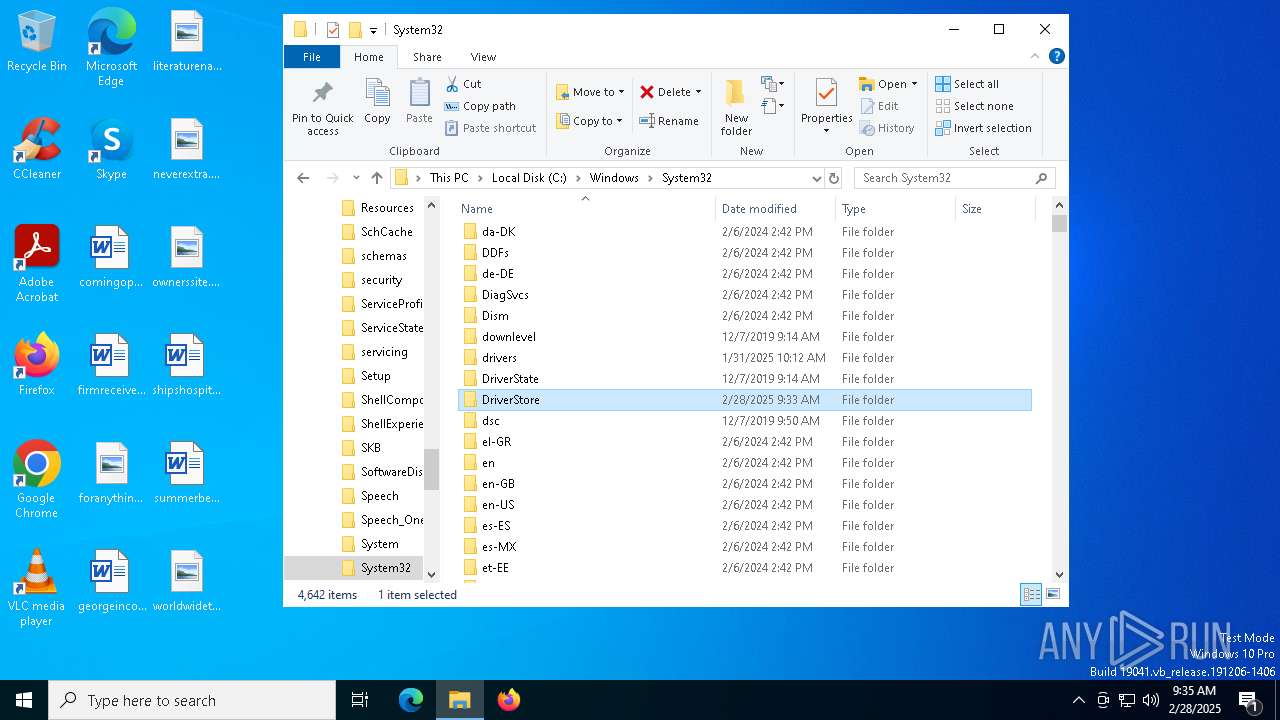
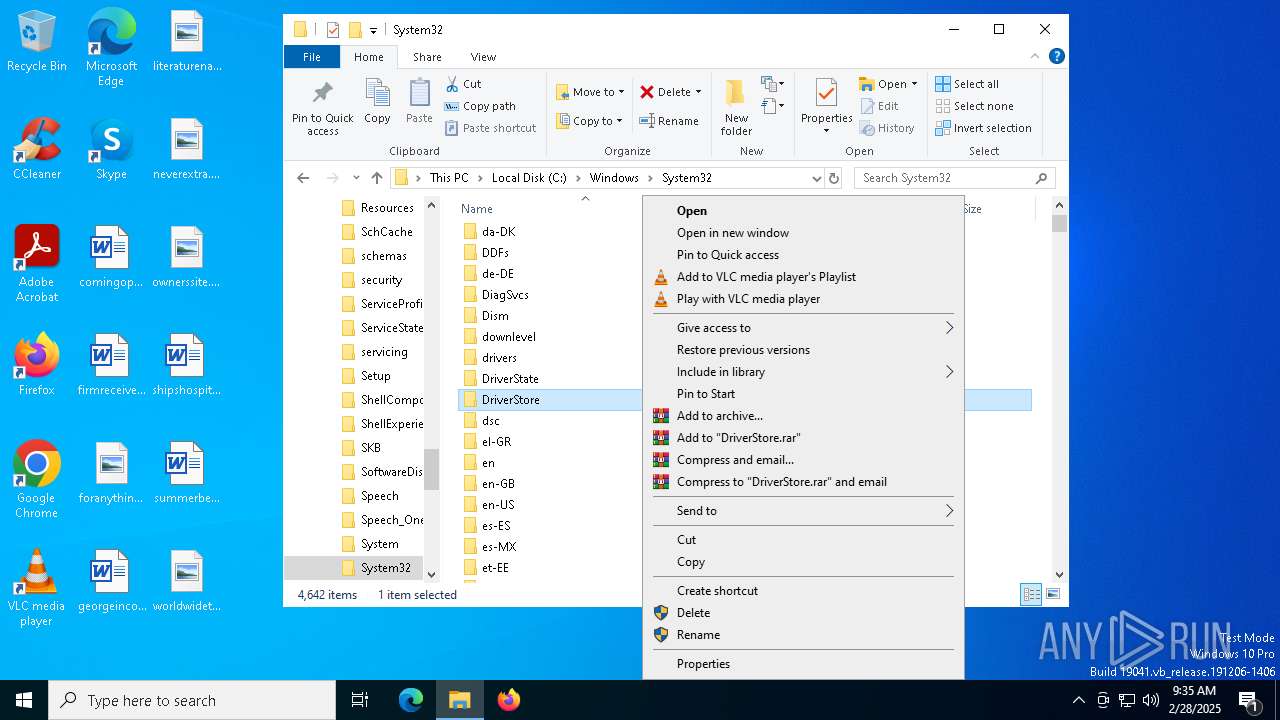
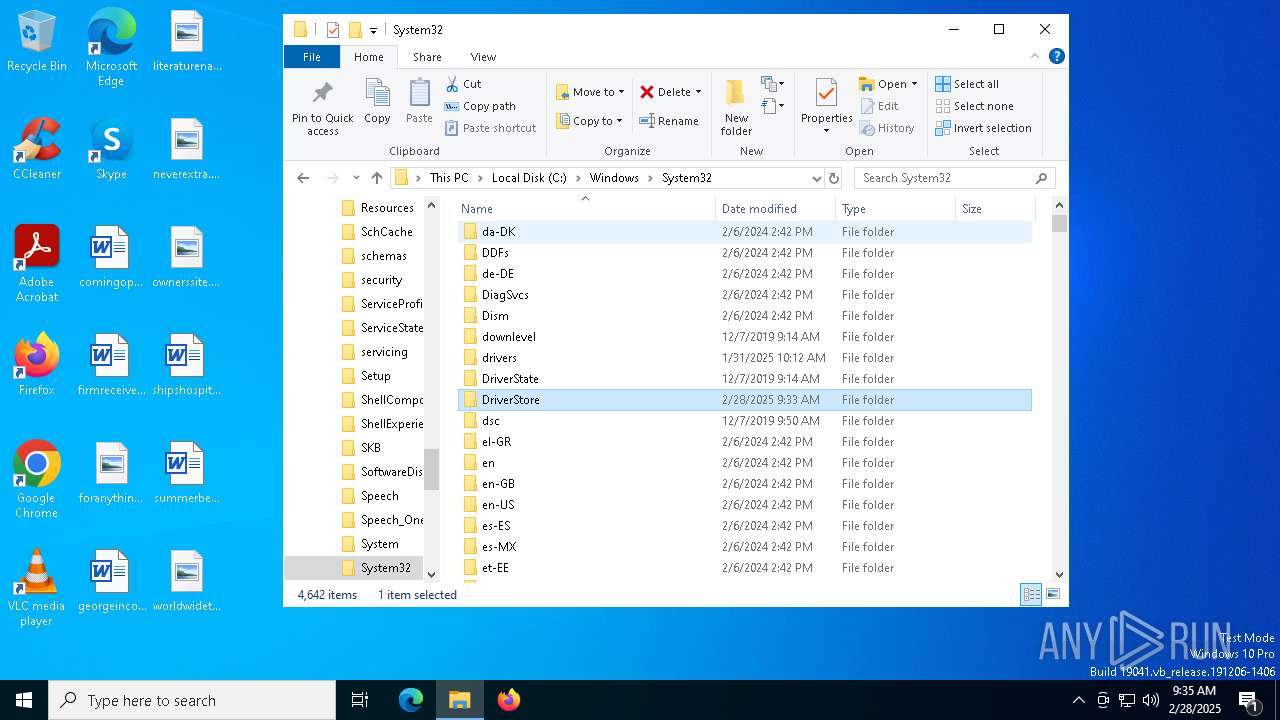
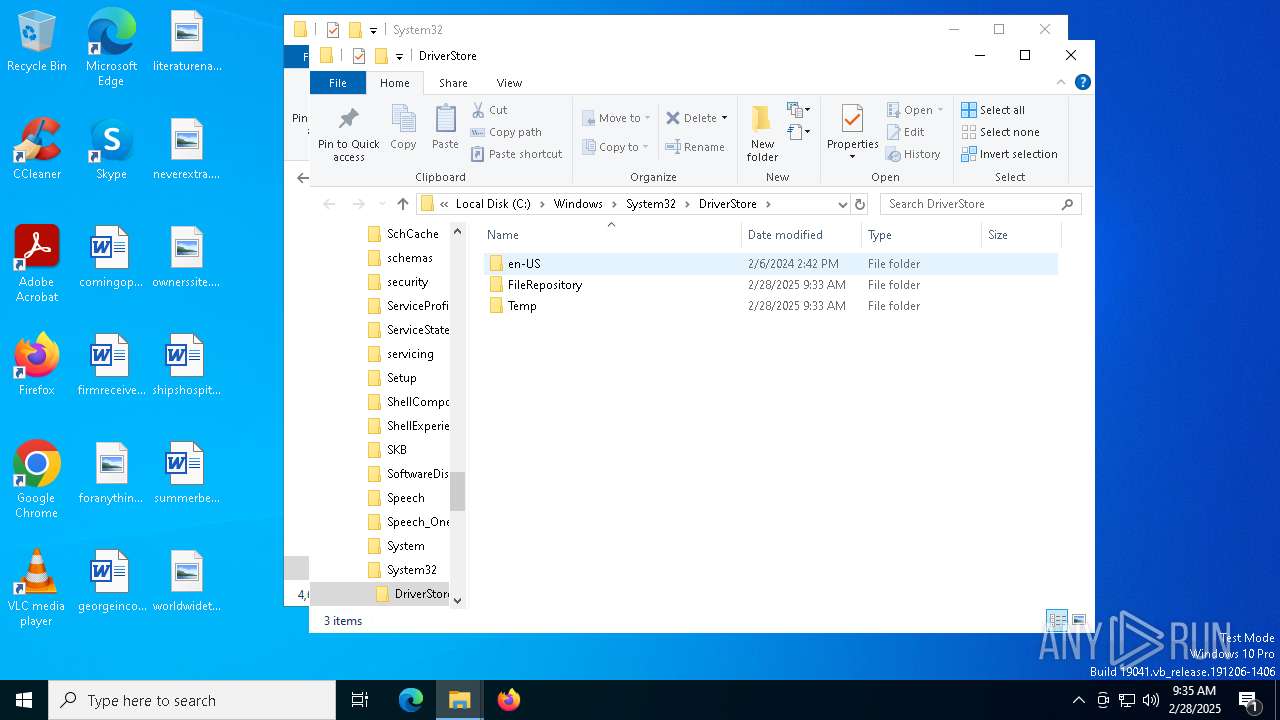
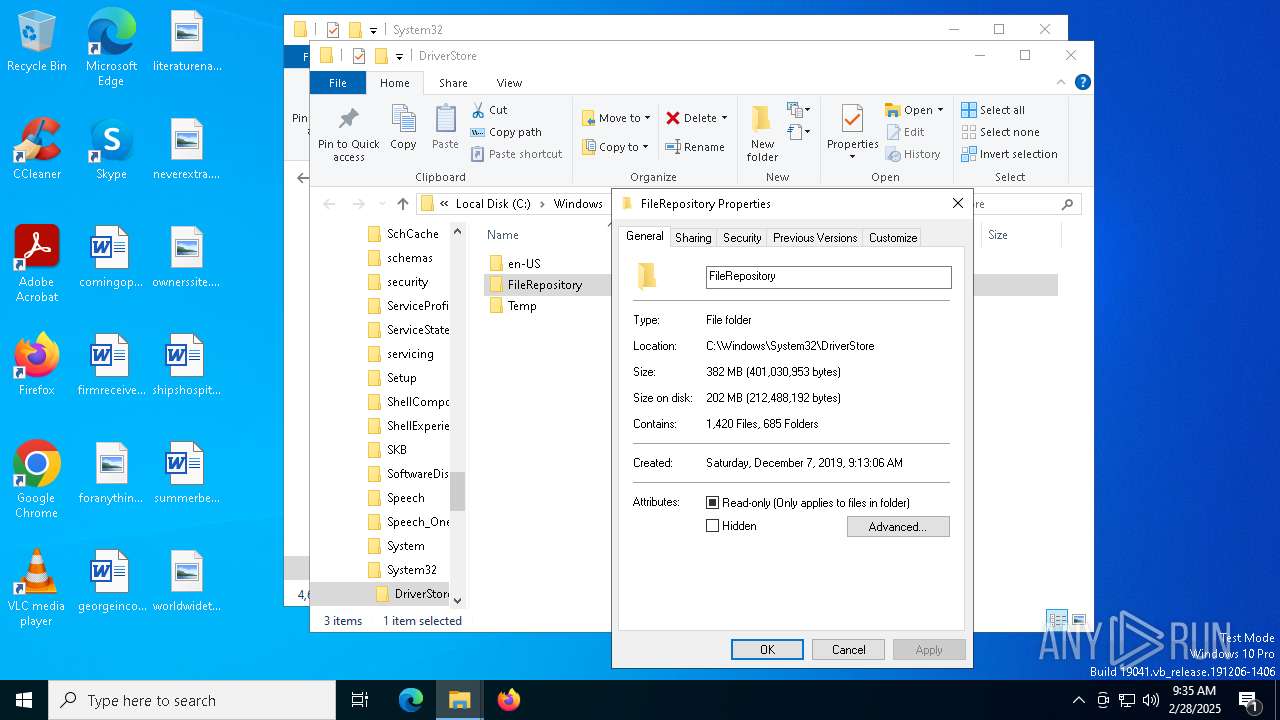
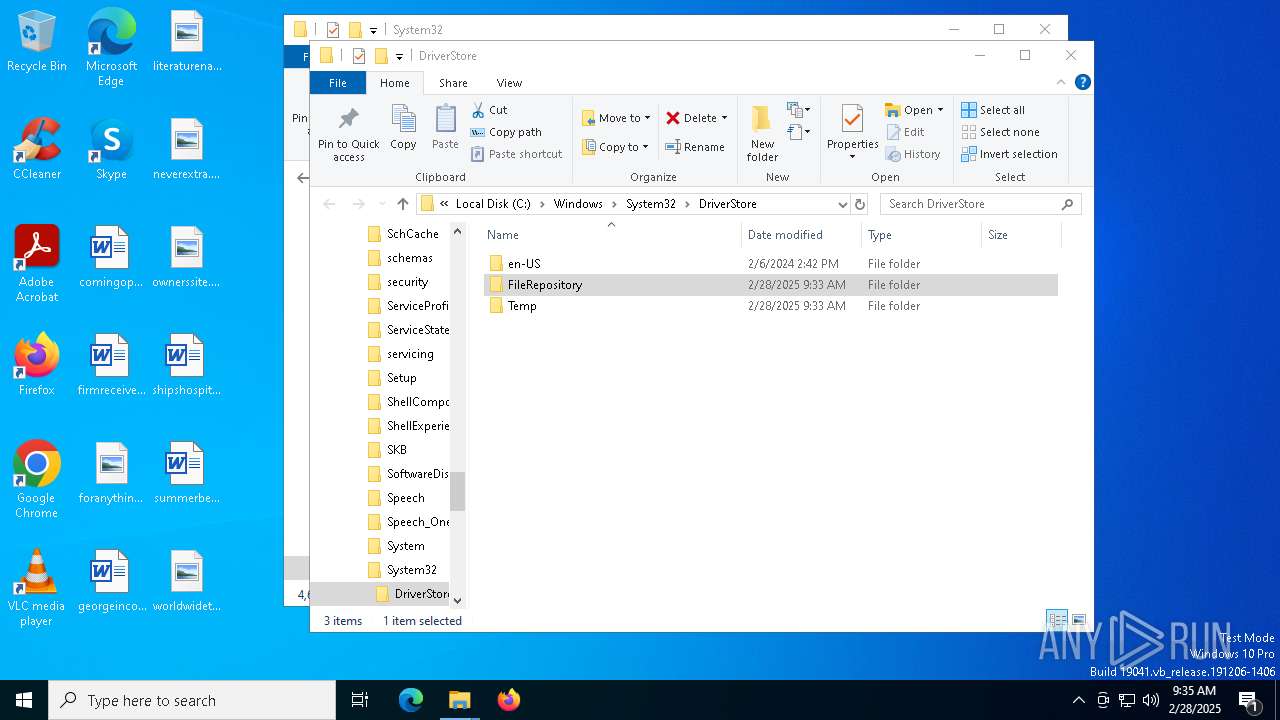
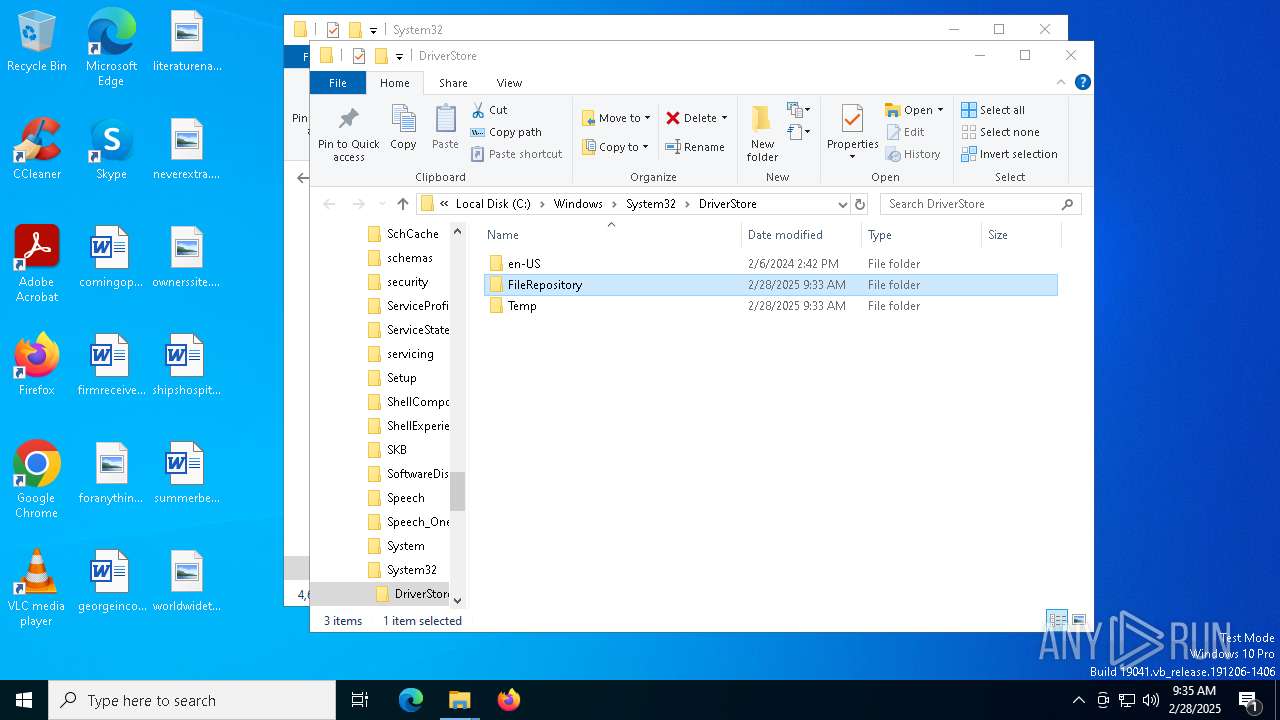
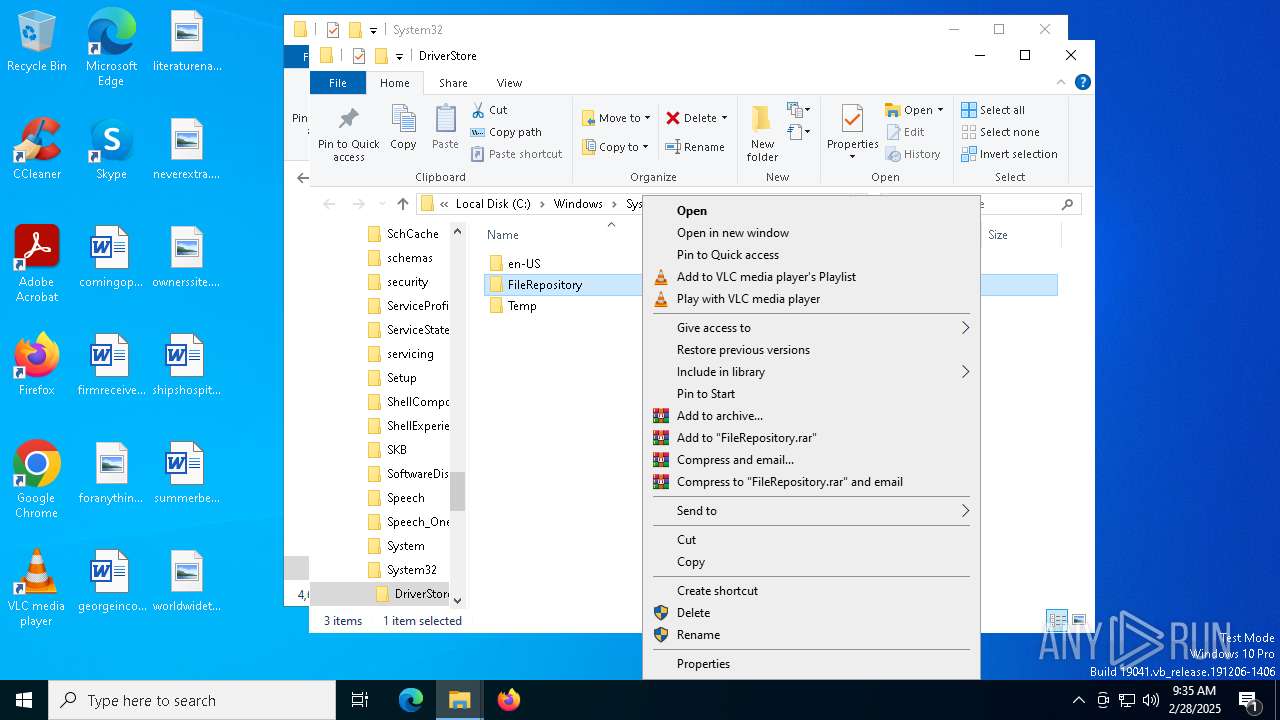
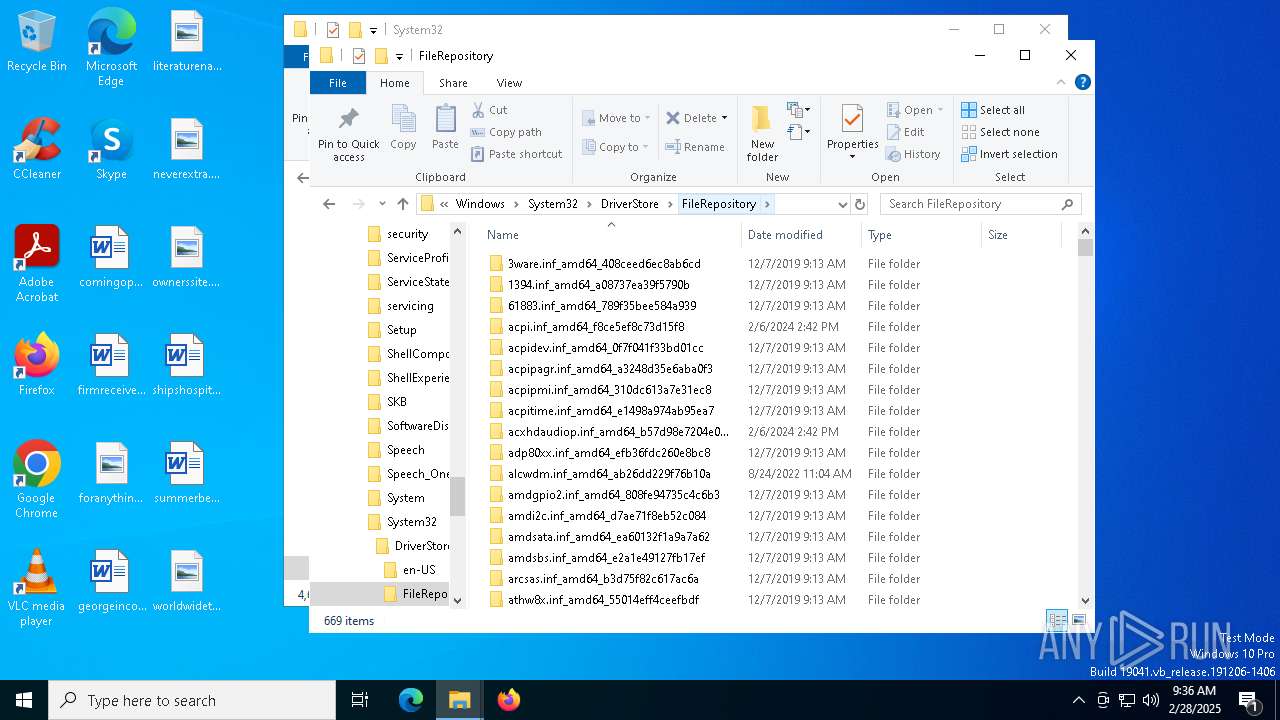
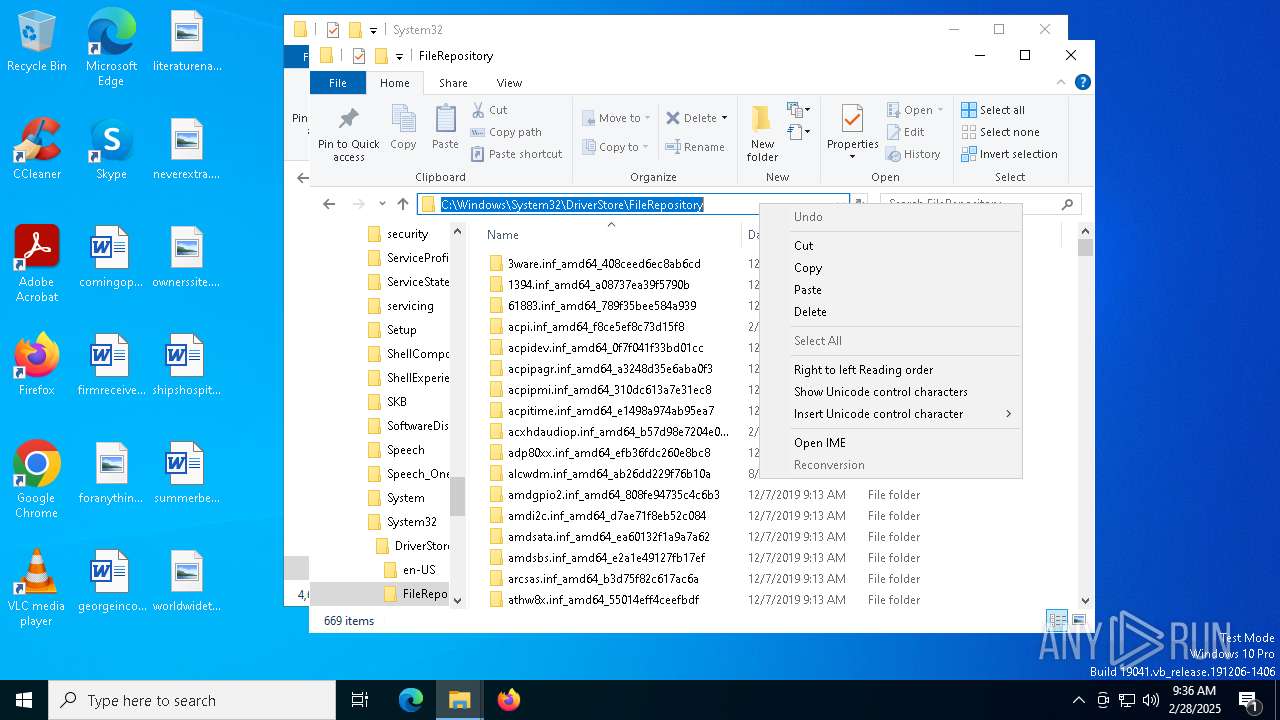
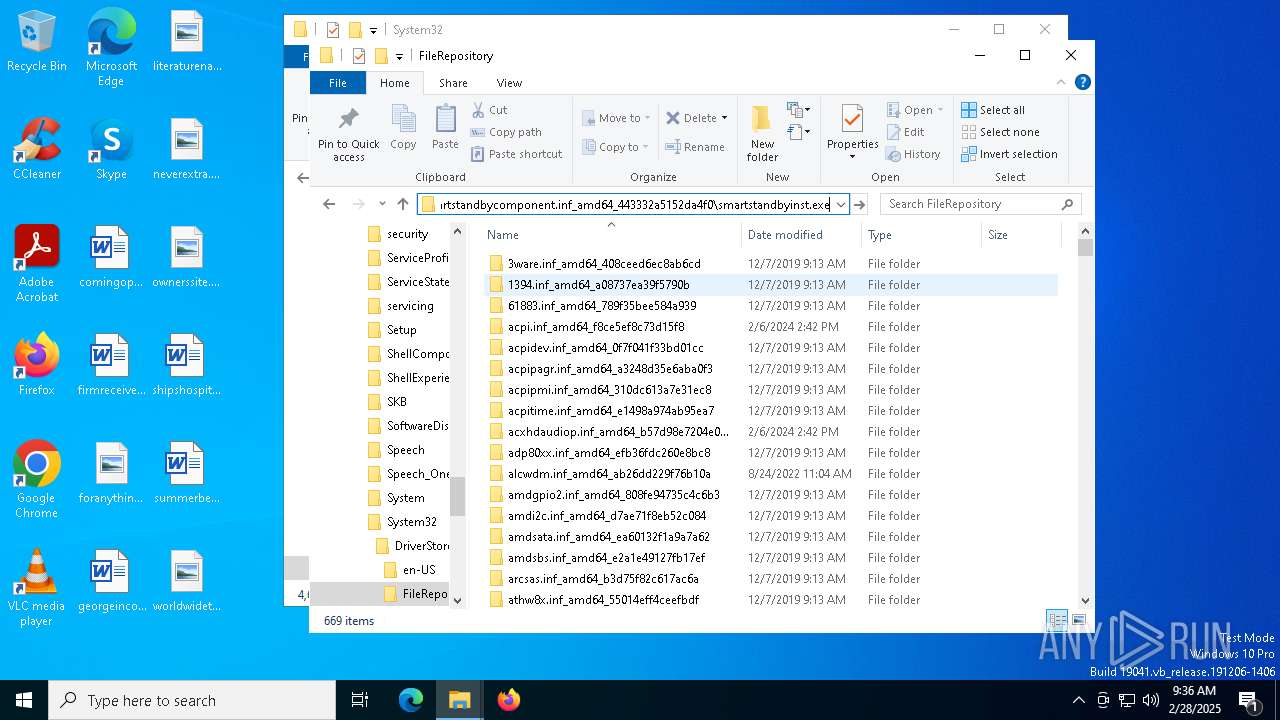
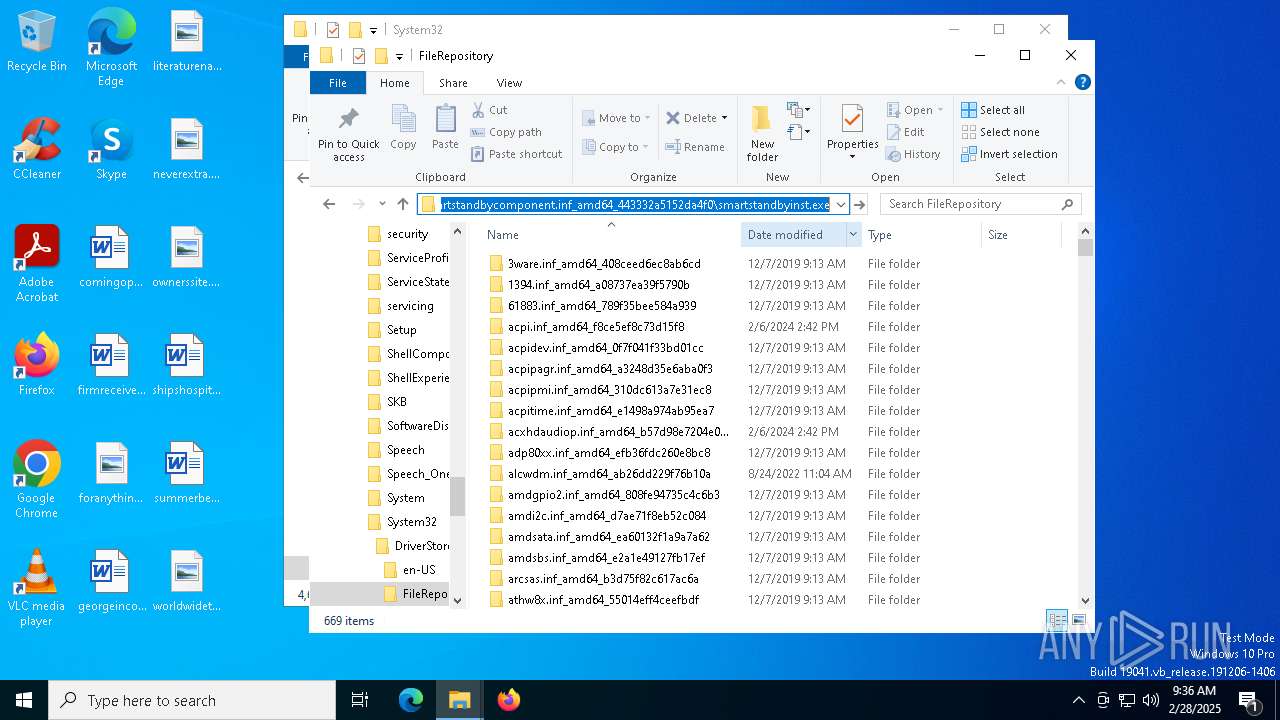
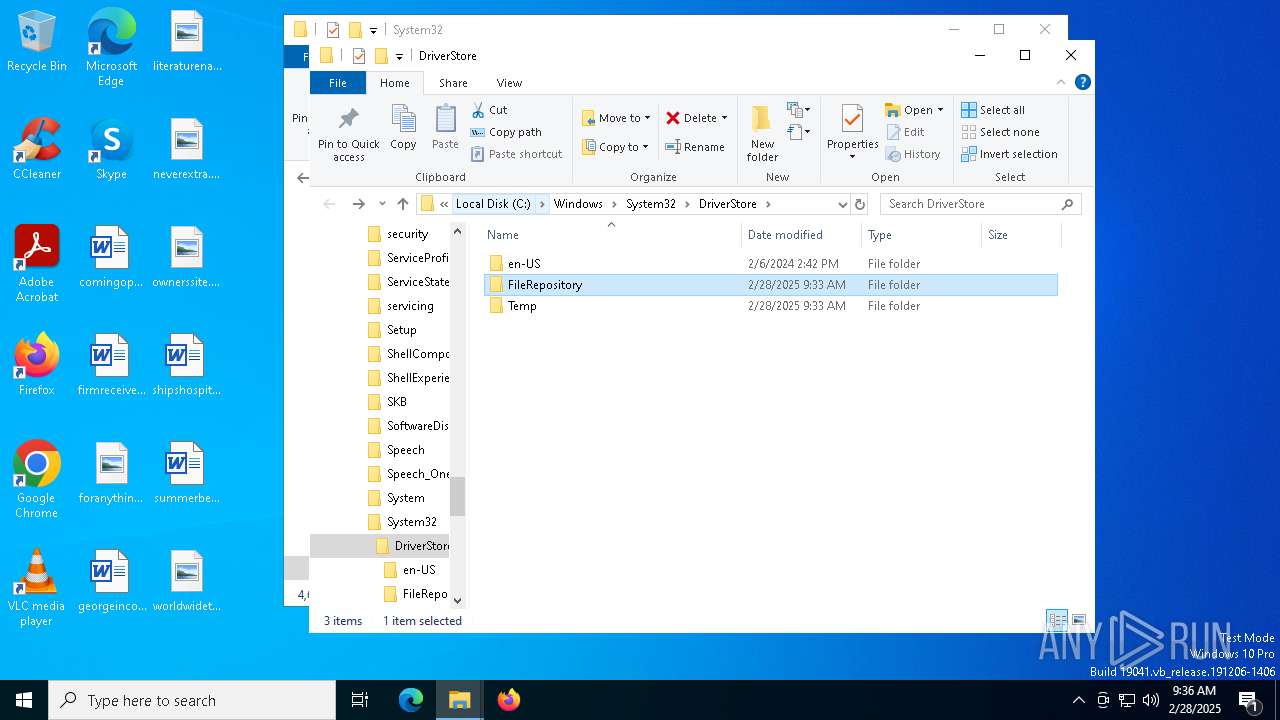
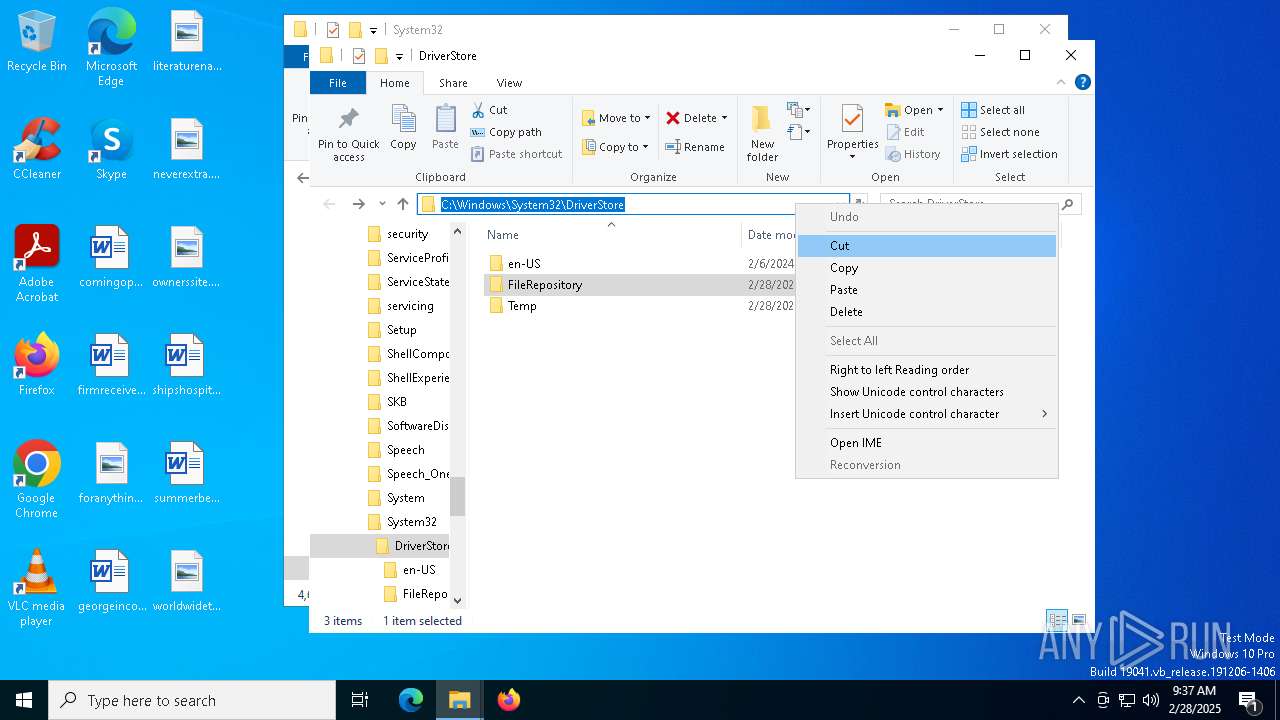
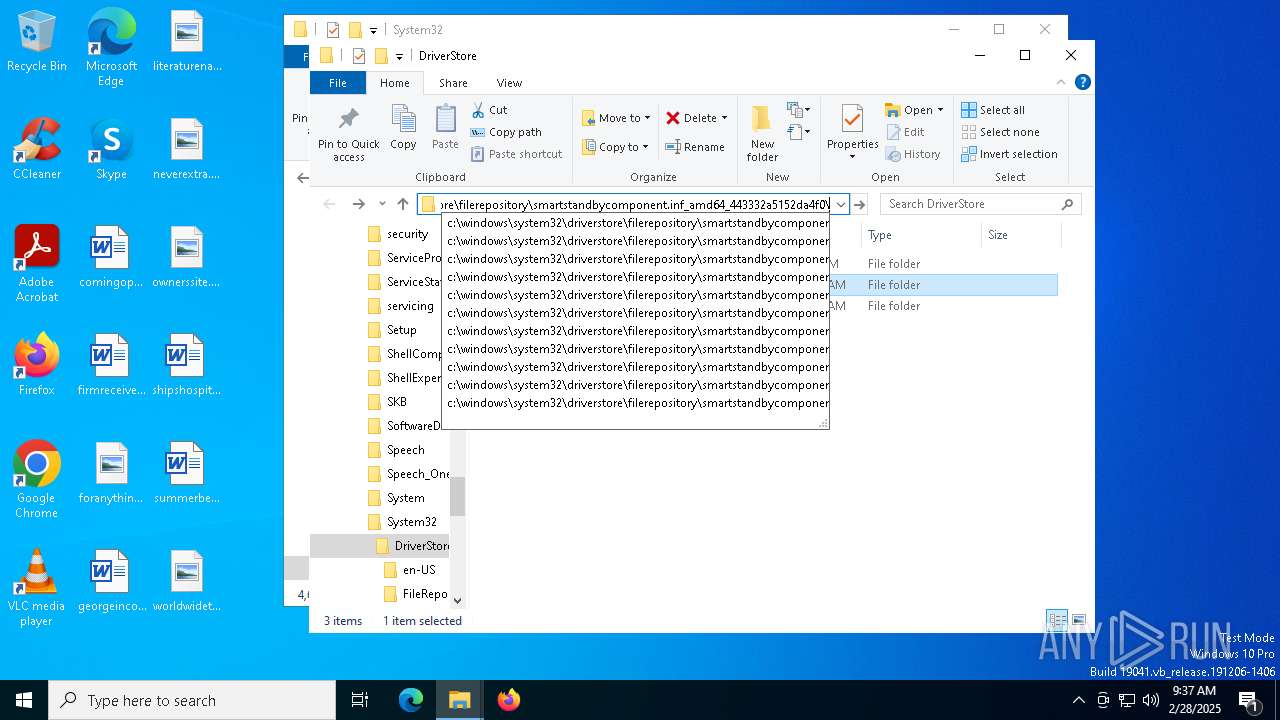
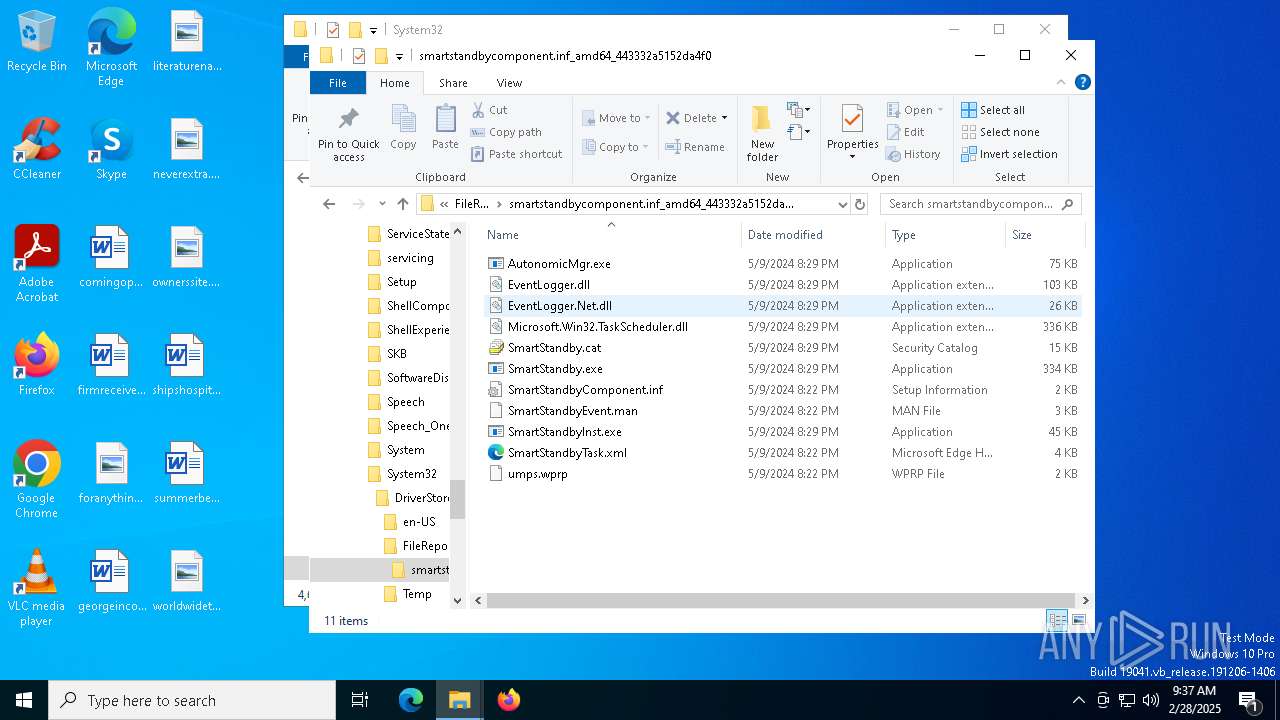
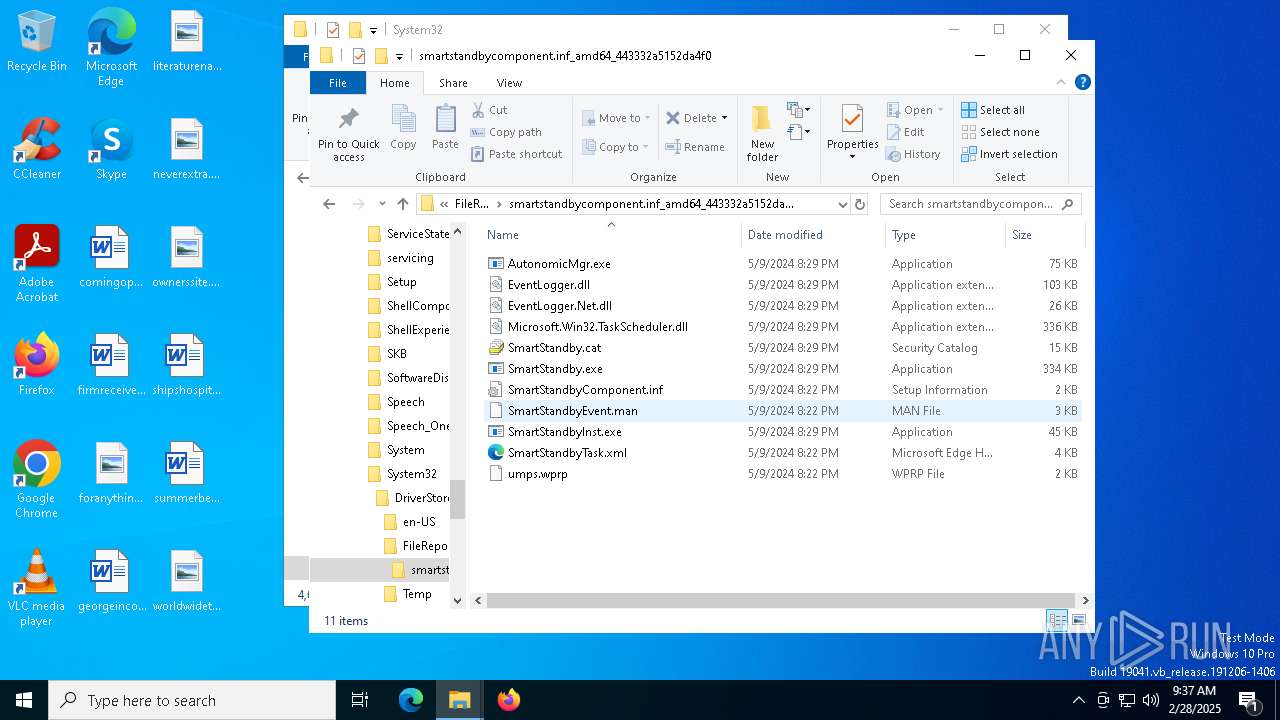
Creates files in the driver directory
- drvinst.exe (PID: 6972)
INFO
Create files in a temporary directory
- n25by27w.exe (PID: 3332)
- pnputil.exe (PID: 904)
Checks supported languages
- n25by27w.tmp (PID: 4040)
- n25by27w.exe (PID: 3332)
- n25by27w.tmp (PID: 7236)
- n25by27w.exe (PID: 7212)
- drvinst.exe (PID: 6972)
- ShellExperienceHost.exe (PID: 2504)
Reads the computer name
- n25by27w.tmp (PID: 7236)
- n25by27w.tmp (PID: 4040)
- drvinst.exe (PID: 6972)
- ShellExperienceHost.exe (PID: 2504)
Process checks computer location settings
- n25by27w.tmp (PID: 4040)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7892)
- BackgroundTransferHost.exe (PID: 6668)
- BackgroundTransferHost.exe (PID: 5720)
- BackgroundTransferHost.exe (PID: 7020)
- BackgroundTransferHost.exe (PID: 1272)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6668)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 6668)
- slui.exe (PID: 7836)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 6668)
- SIHClient.exe (PID: 5112)
- drvinst.exe (PID: 6972)
- slui.exe (PID: 7368)
- slui.exe (PID: 7836)
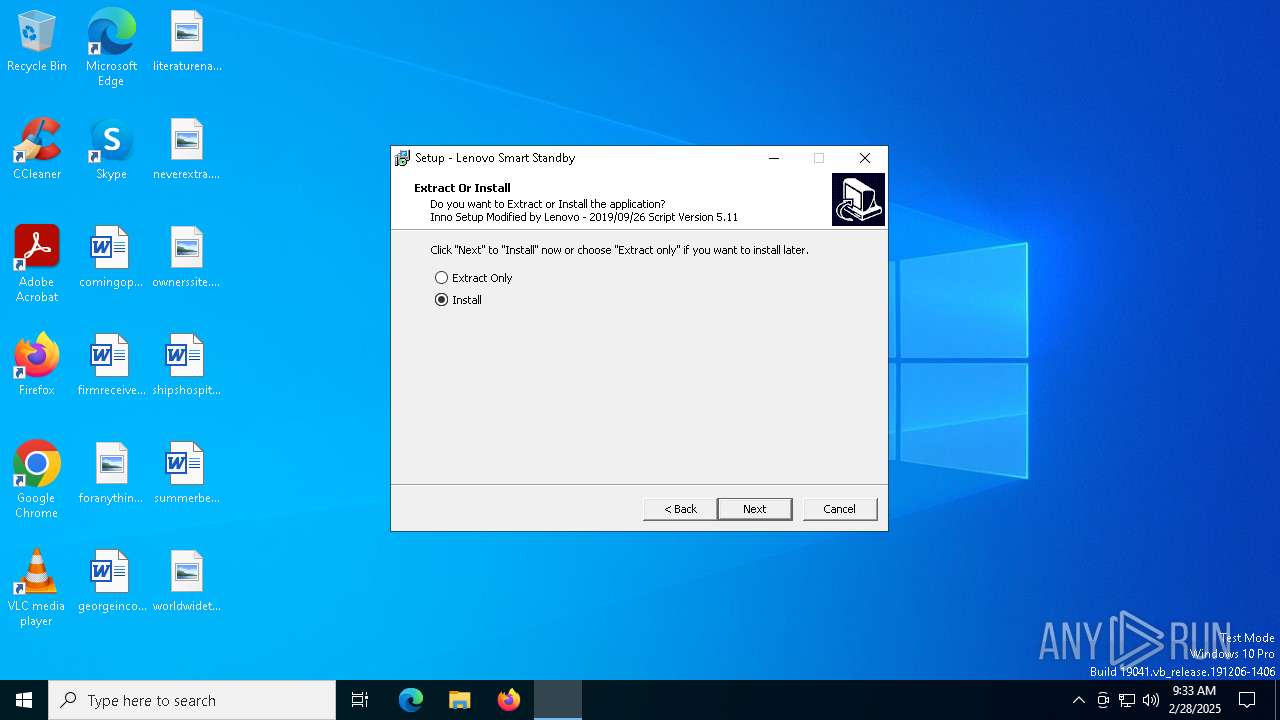
Detects InnoSetup installer (YARA)
- n25by27w.exe (PID: 3332)
- n25by27w.tmp (PID: 4040)
- n25by27w.exe (PID: 7212)
- n25by27w.tmp (PID: 7236)
Compiled with Borland Delphi (YARA)
- n25by27w.tmp (PID: 4040)
- n25by27w.tmp (PID: 7236)
Reads the machine GUID from the registry
- drvinst.exe (PID: 6972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (42.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (40.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Win16/32 Executable Delphi generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:06 06:31:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 151552 |
| InitializedDataSize: | 27648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25be0 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.3.11.0 |
| ProductVersionNumber: | 4.3.11.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Lenovo Group Limited |
| FileDescription: | For Lenovo Updates Catalog |
| FileVersion: | 4.3.11.0 (N25BY27W) |
| LegalCopyright: | Copyright © Lenovo 2024. |
| ProductName: | Lenovo Smart Standby -Package 1.5.11.5 |
| ProductVersion: | 4.3.11.0 (N25BY27W) |
Total processes
162
Monitored processes
21
Malicious processes
1
Suspicious processes
2
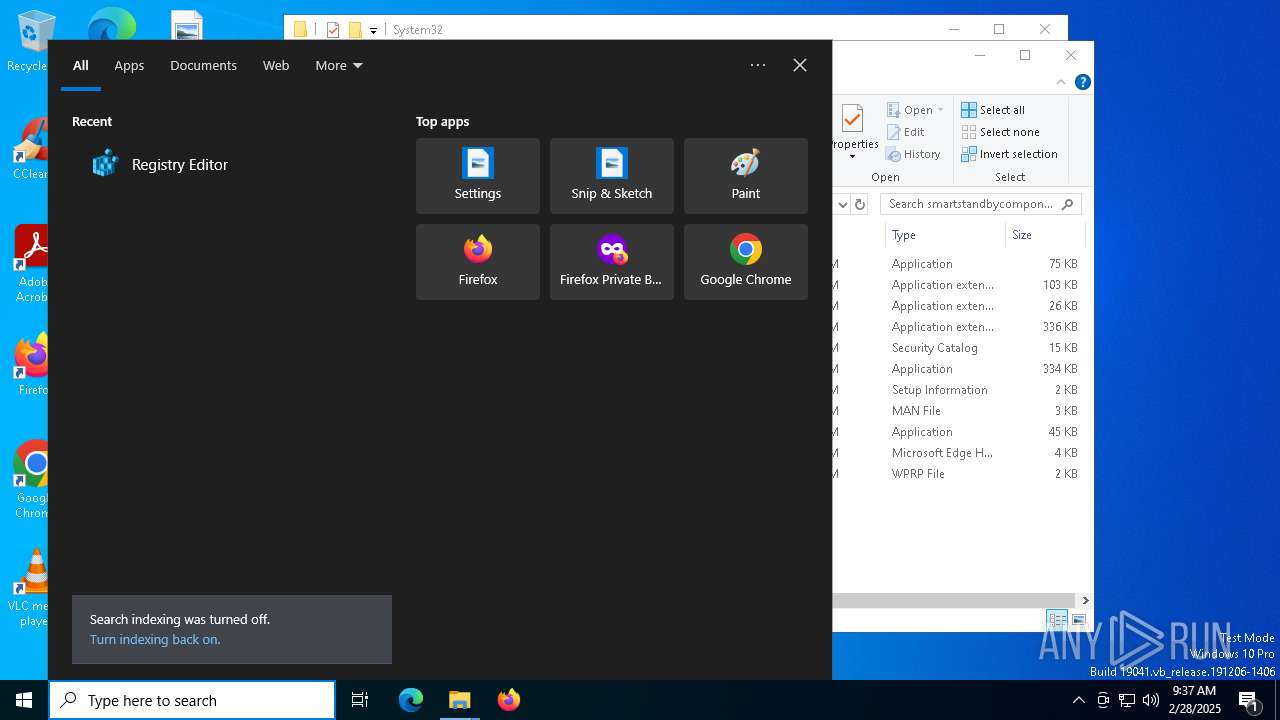
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\WINDOWS\system32\pnputil.exe" /add-driver "C:\WINDOWS\TempInst\is-IC8D4.tmp\Comp\SmartStandbyComponent.inf" /install | C:\Windows\System32\pnputil.exe | n25by27w.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s wuauserv | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\Temp\n25by27w.exe" | C:\Users\admin\AppData\Local\Temp\n25by27w.exe | explorer.exe | ||||||||||||
User: admin Company: Lenovo Group Limited Integrity Level: MEDIUM Description: For Lenovo Updates Catalog Exit code: 0 Version: 4.3.11.0 (N25BY27W) Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\is-OLAV5.tmp\n25by27w.tmp" /SL5="$50352,501968,180224,C:\Users\admin\AppData\Local\Temp\n25by27w.exe" | C:\Users\admin\AppData\Local\Temp\is-OLAV5.tmp\n25by27w.tmp | — | n25by27w.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5112 | C:\WINDOWS\System32\sihclient.exe /cv G8rd//FYTUGMCdwLHn8tmA.0.2 | C:\Windows\System32\SIHClient.exe | upfc.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: SIH Client Exit code: 2379777 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | C:\WINDOWS\System32\Upfc.exe /launchtype periodic /cv G8rd//FYTUGMCdwLHn8tmA.0 | C:\Windows\System32\upfc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Updateability From SCM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pnputil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 942
Read events
10 911
Write events
31
Delete events
0
Modification events
| (PID) Process: | (7892) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7892) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7892) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6668) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6668) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6668) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5720) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5720) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5720) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5244) upfc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\WaaS\Upfc |
| Operation: | write | Name: | LastSihPeriodicLaunchAttempt |
Value: 2025-02-28T09:33:23Z | |||
Executable files
40
Suspicious files
58
Text files
16
Unknown types
0
Dropped files
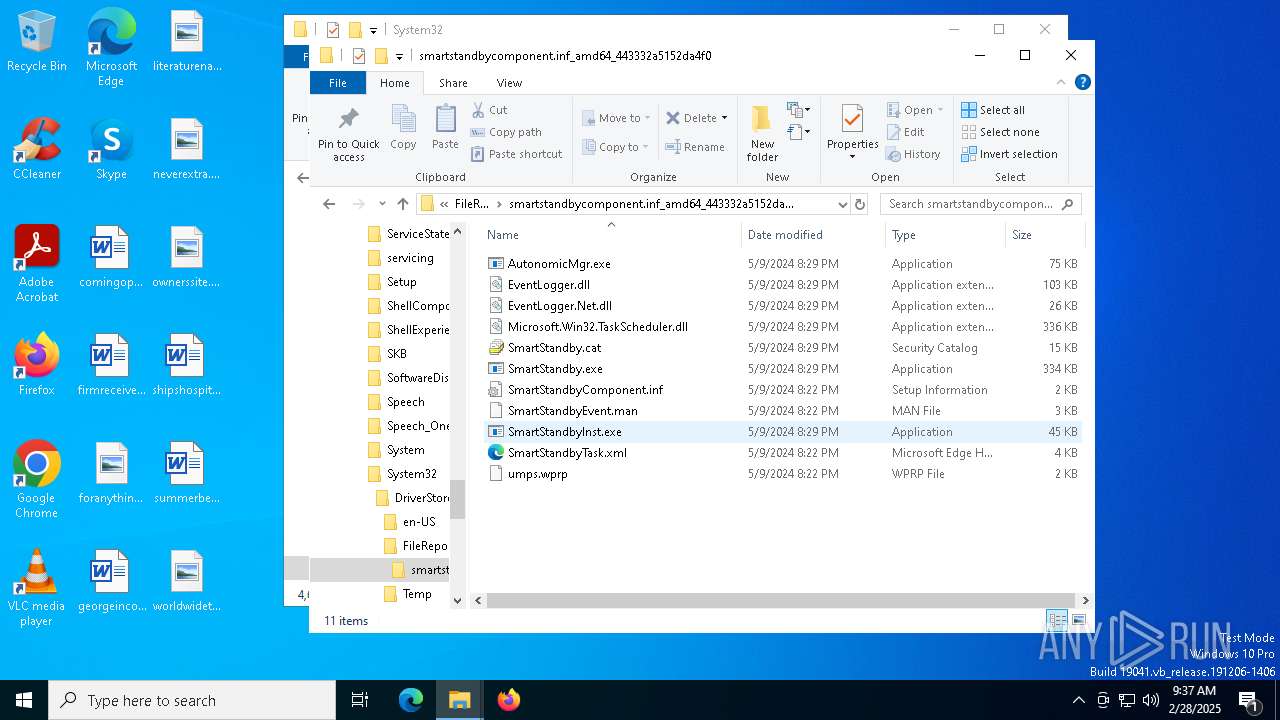
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\e9820db7-8a8c-4cf9-8eae-bdf25340d897.down_data | — | |
MD5:— | SHA256:— | |||
| 3332 | n25by27w.exe | C:\Users\admin\AppData\Local\Temp\is-OLAV5.tmp\n25by27w.tmp | executable | |
MD5:E8E2DA1D38D869444F8AAA51EB2C0B05 | SHA256:D39DBB28861180959CE5A2858DAF5094FCAD2D0E92BBC5C012FBD3BF2C301633 | |||
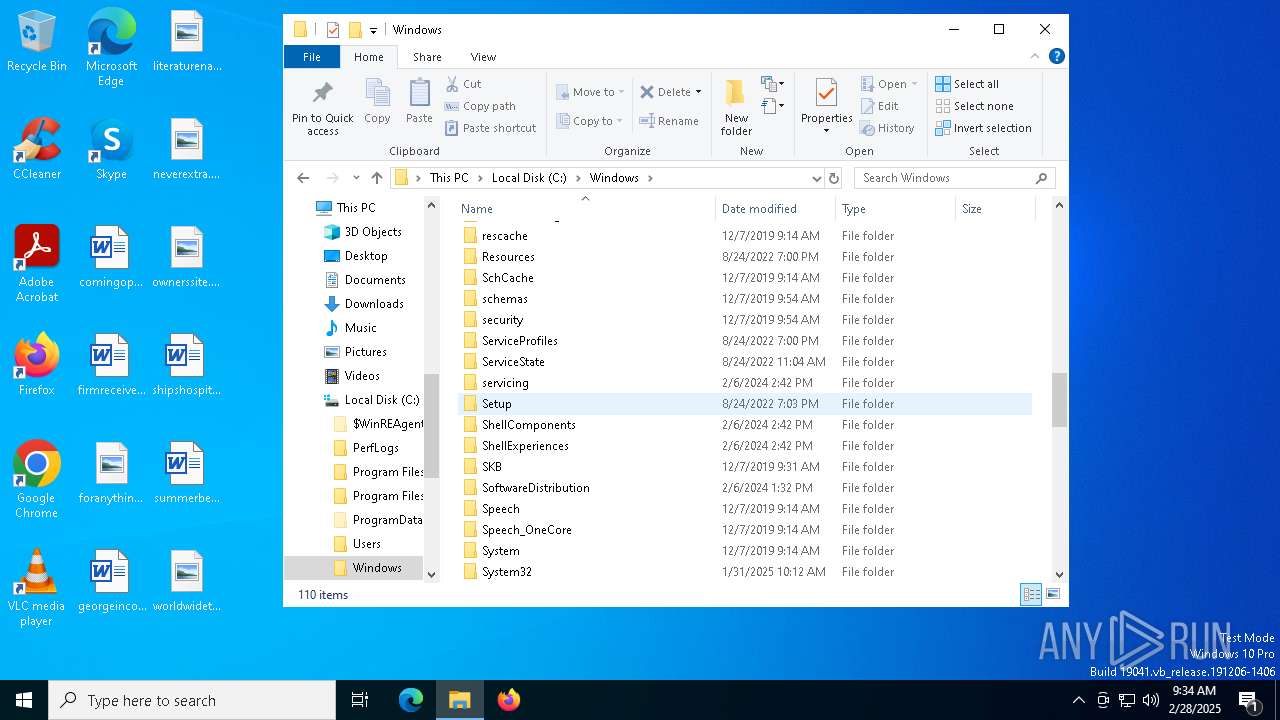
| 7212 | n25by27w.exe | C:\Windows\TempInst\is-T29QV.tmp\n25by27w.tmp | executable | |
MD5:E8E2DA1D38D869444F8AAA51EB2C0B05 | SHA256:D39DBB28861180959CE5A2858DAF5094FCAD2D0E92BBC5C012FBD3BF2C301633 | |||
| 6572 | sppsvc.exe | C:\Windows\System32\spp\store\2.0\cache\cache.dat | binary | |
MD5:8648AA8CC0475F3D04DA1EFB805F1E22 | SHA256:A5BC4C14FA84D4A8A6B817E5E4E87AA26517C4E398AE07471F59732FDEB9AF9F | |||
| 7236 | n25by27w.tmp | C:\Windows\TempInst\is-IC8D4.tmp\is-1I2O3.tmp | text | |
MD5:02116E7809844CDED937FDC0043D5628 | SHA256:5E86200643A9359366F0E77C962B9A569B559CEB2D1B5680477FB89EA4D8011E | |||
| 7236 | n25by27w.tmp | C:\Windows\TempInst\is-IC8D4.tmp\Comp\is-BGQPB.tmp | executable | |
MD5:D04996B80CA4C10902B4E0FA85C648CE | SHA256:79FCECB6CC95C2CD827C2747AE69345769E310450E922E7F82D2EAA9D4D992A1 | |||
| 6668 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f4a3aa4e-15b4-4adc-b84a-80232a78957c.up_meta_secure | binary | |
MD5:DF4F52652C0D14B52476FF74496CCA5D | SHA256:50EA24E50F7984B45CF38F4E7D114339DAC02FD034FE87E4C9FF9135E98E8C24 | |||
| 7236 | n25by27w.tmp | C:\Windows\TempInst\is-IC8D4.tmp\Comp\EventLogger.Net.dll | executable | |
MD5:34CA320027495721CF092F915CE6A2E1 | SHA256:57BCF8C9BC773ECB9FAD2DEDFF4376E44C6CA3FD892FF7344D0747D88259418E | |||
| 7236 | n25by27w.tmp | C:\Windows\TempInst\is-IC8D4.tmp\setup.bat | text | |
MD5:02116E7809844CDED937FDC0043D5628 | SHA256:5E86200643A9359366F0E77C962B9A569B559CEB2D1B5680477FB89EA4D8011E | |||
| 7236 | n25by27w.tmp | C:\Windows\TempInst\is-IC8D4.tmp\Comp\EventLogger.dll | executable | |
MD5:D04996B80CA4C10902B4E0FA85C648CE | SHA256:79FCECB6CC95C2CD827C2747AE69345769E310450E922E7F82D2EAA9D4D992A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
32
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6668 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5112 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5112 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2040 | backgroundTaskHost.exe | 20.199.58.43:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3008 | backgroundTaskHost.exe | 2.23.227.202:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |