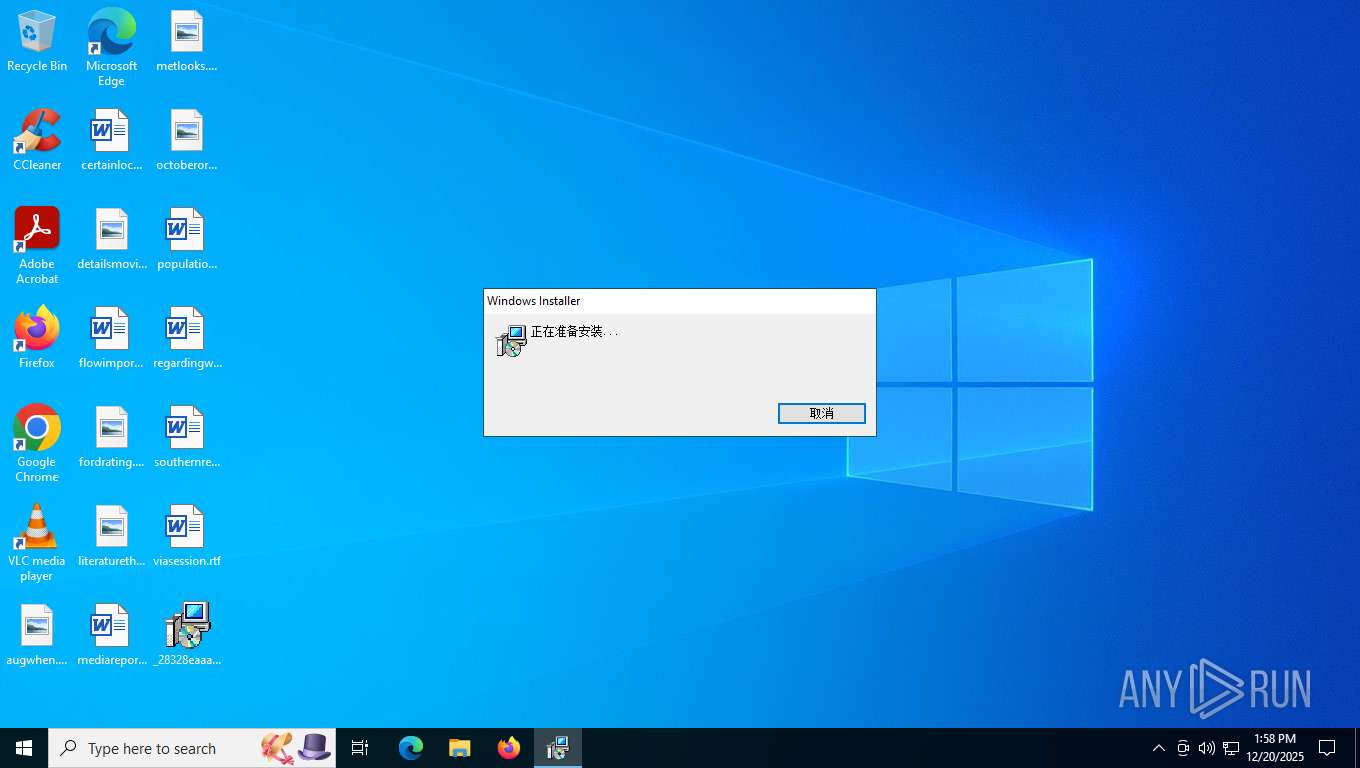
| File name: | _28328eaaa8995f20f7160ba23e29a14d7e60f2614e4f27f889123f754d7626ab.fpx |
| Full analysis: | https://app.any.run/tasks/c50341cd-ad76-4cd5-99e4-a4c4261125aa |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2025, 18:58:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 14:06:51 2020, Security: 0, Code page: 936, Revision Number: {4452925F-301D-4F87-8038-8BDFA4E52DD0}, Number of Words: 2, Subject: in, Author: MonKeyDu, Name of Creating Application: in, Template: ;2052, Comments: Installer in , Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Fri Dec 19 14:07:29 2025, Number of Pages: 200 |
| MD5: | EDAE83CA4F25A901CBC08D5805B9025E |
| SHA1: | A656D020B5123B5870B7FF4DB8316DF5050F9B6D |
| SHA256: | 28328EAAA8995F20F7160BA23E29A14D7E60F2614E4F27F889123F754D7626AB |
| SSDEEP: | 98304:h9IDogorhThPaxcUGWL2E6Gbvpx44SyzNUPnUVB7q74lfJBFIjzcDK5CLWoFg4Q2:Ope7caRsJ2zC36D |
MALICIOUS
Creates a new scheduled task via Registry
- msiexec.exe (PID: 7476)
WINOS has been detected (YARA)
- weicha.exe (PID: 7580)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1772)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 7856)
Likely accesses (executes) a file from the Public directory
- weicha.exe (PID: 7580)
There is functionality for taking screenshot (YARA)
- weicha.exe (PID: 7580)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7856)
Checks supported languages
- msiexec.exe (PID: 8076)
- msiexec.exe (PID: 7276)
- msiexec.exe (PID: 7476)
- weicha.exe (PID: 7580)
Checks proxy server information
- msiexec.exe (PID: 7856)
- slui.exe (PID: 7648)
Creates files or folders in the user directory
- msiexec.exe (PID: 7856)
Manages system restore points
- SrTasks.exe (PID: 7252)
Reads the computer name
- msiexec.exe (PID: 7276)
- msiexec.exe (PID: 8076)
- msiexec.exe (PID: 7476)
- weicha.exe (PID: 7580)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8076)
Reads Environment values
- msiexec.exe (PID: 7276)
The sample compiled with english language support
- msiexec.exe (PID: 8076)
VMProtect protector has been detected
- weicha.exe (PID: 7580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
| RevisionNumber: | {4452925F-301D-4F87-8038-8BDFA4E52DD0} |
| Words: | 2 |
| Subject: | in |
| Author: | MonKeyDu |
| LastModifiedBy: | - |
| Software: | in |
| Template: | ;2052 |
| Comments: | ?? Installer ???ݿ??????˰?װ in ?????????????ݡ? |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2025:12:19 14:07:29 |
| Pages: | 200 |
Total processes
147
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7276 | C:\Windows\syswow64\MsiExec.exe -Embedding 242E214F1638339ABF2908CD930536E3 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7476 | C:\Windows\syswow64\MsiExec.exe -Embedding C5DBC3E5B35E2DCABA6342225224856D E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7580 | "C:\Users\Public\weicha.exe" | C:\Users\Public\weicha.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7648 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7856 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\_28328eaaa8995f20f7160ba23e29a14d7e60f2614e4f27f889123f754d7626ab.fpx.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8076 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 757
Read events
9 587
Write events
160
Delete events
10
Modification events
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000032693BAEE271DC018C1F0000C81F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000032693BAEE271DC018C1F0000C81F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008850A4AEE271DC018C1F0000C81F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000001FEDC0AEE271DC018C1F0000FC1B0000E803000001000000000000000000000062D364660519AD4F8744A1B778E5E95500000000000000000000000000000000 | |||
| (PID) Process: | (1772) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000058C4D8AEE271DC01EC060000681D0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000358C9FAEE271DC018C1F0000C81F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000358C9FAEE271DC018C1F0000C81F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000358C9FAEE271DC018C1F0000C81F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (8076) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000C98ABEAEE271DC018C1F0000C81F0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
22
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8076 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 8076 | msiexec.exe | C:\Windows\Installer\1029a2.msi | — | |
MD5:— | SHA256:— | |||
| 8076 | msiexec.exe | C:\Config.Msi\1029a4.rbs | binary | |
MD5:FA9CFC85768301C1D6CE0E2890BAA3A7 | SHA256:9A15CAFA74A9EEFEE6FC4E03CE6F54D16559CC8C5F197FDB915140F9713F7992 | |||
| 7856 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B03113490075047F519A3F760F0FF379_B4FFE8820923C5F5C915DC5E625A569C | binary | |
MD5:9D850A464763F787DD5423796207F6F8 | SHA256:16C38960F2F2416BF9FDA70561C149420E7D6748FB888BADD4B804121F399BDB | |||
| 8076 | msiexec.exe | C:\Windows\Installer\MSI2D7C.tmp | executable | |
MD5:89F70B588A48793450DD603B6CD4096F | SHA256:066C52ED8EBF63A33AB8290B7C58D0C13F79C14FAA8BF12B1B41F643D3EBE281 | |||
| 7856 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\30069012ED3CF5DB92F9F4FC78D55E2D_16AA5B9B040CB195ADDB70661F18F3C5 | binary | |
MD5:20CE6836CB113C7A045989B8198FA5A5 | SHA256:4DA832CEAB48EF08EFE40D00B5F336C3DC9F3FD7A5FCEBE663D888D08F13FE78 | |||
| 8076 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:DB9F7BFD0012A0A62B2EB316116C45A8 | SHA256:2E1A9D0FB48357DC88AB0B56528DC3B36554A4F9691FA8E2875B00BD6C96F4E3 | |||
| 8076 | msiexec.exe | C:\Windows\Installer\MSI2DBC.tmp | executable | |
MD5:89F70B588A48793450DD603B6CD4096F | SHA256:066C52ED8EBF63A33AB8290B7C58D0C13F79C14FAA8BF12B1B41F643D3EBE281 | |||
| 8076 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6664d362-1905-4fad-8744-a1b778e5e955}_OnDiskSnapshotProp | binary | |
MD5:DB9F7BFD0012A0A62B2EB316116C45A8 | SHA256:2E1A9D0FB48357DC88AB0B56528DC3B36554A4F9691FA8E2875B00BD6C96F4E3 | |||
| 8076 | msiexec.exe | C:\Windows\Installer\MSI2C80.tmp | executable | |
MD5:89F70B588A48793450DD603B6CD4096F | SHA256:066C52ED8EBF63A33AB8290B7C58D0C13F79C14FAA8BF12B1B41F643D3EBE281 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
32
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1156 | svchost.exe | GET | 200 | 2.19.198.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.19.198.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.198.104:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1156 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7856 | msiexec.exe | GET | 200 | 23.53.42.243:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQC78My1t7gx%2FSGuMneK5AyJ | unknown | — | — | unknown |
7856 | msiexec.exe | GET | 200 | 23.53.43.50:80 | http://cevcsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR2rKuShFxBxX%2BVZ%2F8jiOwbsyptXQQUrFfKCBbcP8UxHApN2%2Fvx3pknLTQCEHNo45ni7XV5SvqHy5M993g%3D | unknown | — | — | unknown |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
3500 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1156 | svchost.exe | 2.19.198.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.19.198.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.19.198.104:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
1156 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
7856 | msiexec.exe | 23.53.42.243:80 | subca.ocsp-certum.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
cevcsca2021.ocsp-certum.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
yandi1188.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |