| File name: | BraveCrashHandler64.exe |
| Full analysis: | https://app.any.run/tasks/12b343be-c1a9-440b-90d2-b46e44218d10 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2024, 18:09:42 |
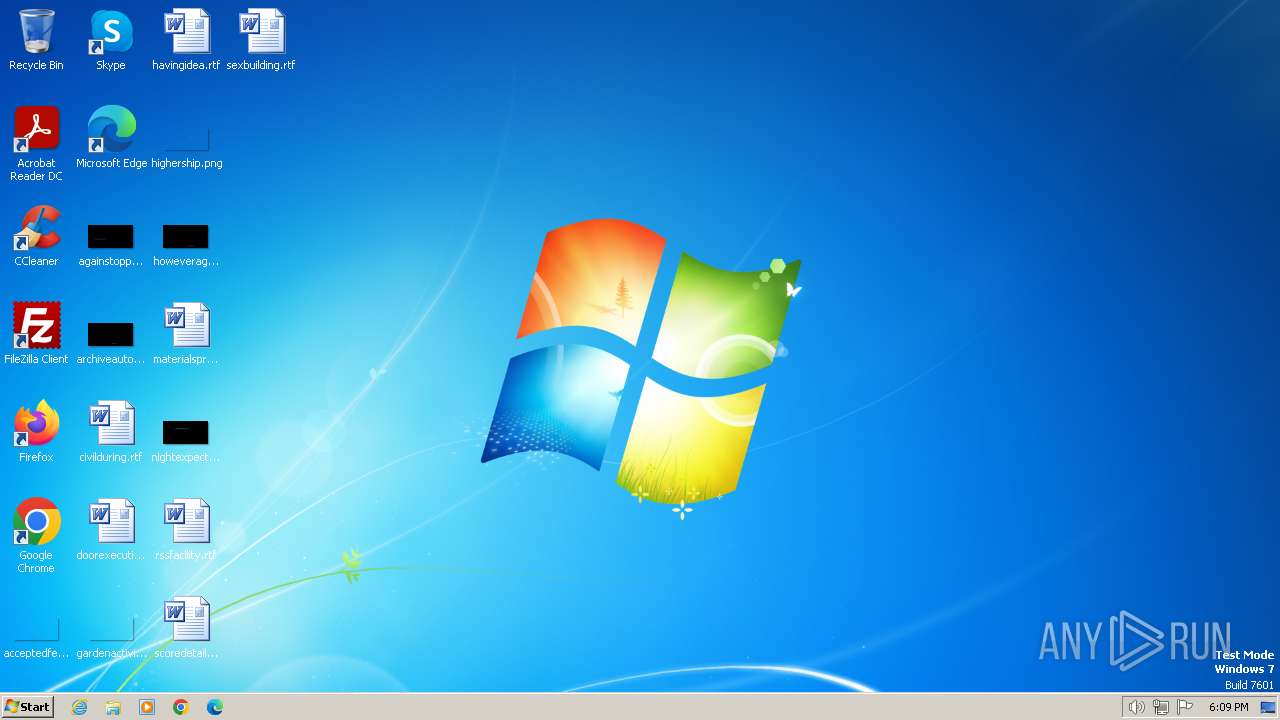
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A82CBFDC35B514DAF6C4CE754EB24FFB |
| SHA1: | 10F4808A3AAC2E77898A2F3471C12B21C783687A |
| SHA256: | 282E89AB3858800C8FBCE89EFFEBD7B9F7B1C280A5FF7639767A6C520F85B350 |
| SSDEEP: | 98304:JdHAznh9qazFcvk+1GkfPiFiTnRuEGNLfvz3nNoLBRdRPBR6LjOMTUw/kLOpb+yk:aTBY8XWmwbO6Sqwu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- BraveCrashHandler64.exe (PID: 2040)
Executing commands from a ".bat" file
- BraveCrashHandler64.exe (PID: 2040)
Starts application with an unusual extension
- cmd.exe (PID: 1776)
Get information on the list of running processes
- cmd.exe (PID: 1776)
Reads the Internet Settings
- powershell.exe (PID: 1316)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1776)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1776)
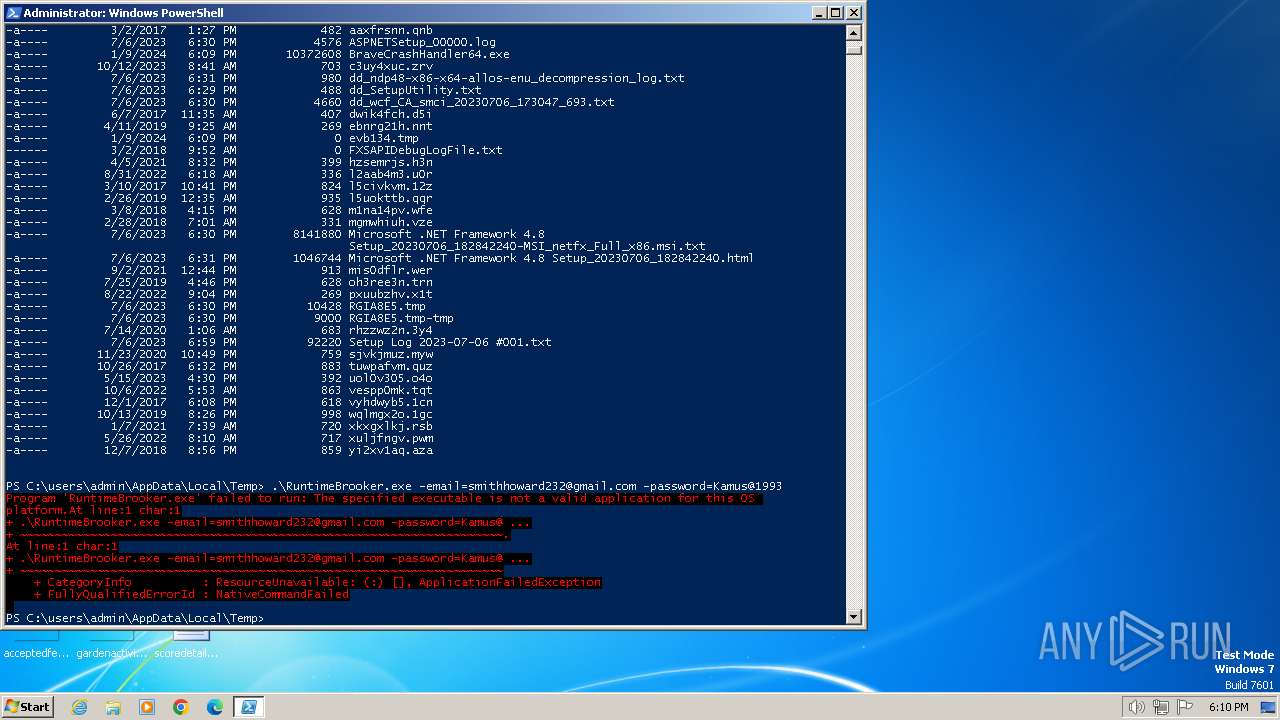
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1316)
INFO
Drops the executable file immediately after the start
- BraveCrashHandler64.exe (PID: 2040)
Reads the computer name
- BraveCrashHandler64.exe (PID: 2040)
Checks supported languages
- BraveCrashHandler64.exe (PID: 2040)
- chcp.com (PID: 1288)
Process drops legitimate windows executable
- BraveCrashHandler64.exe (PID: 2040)
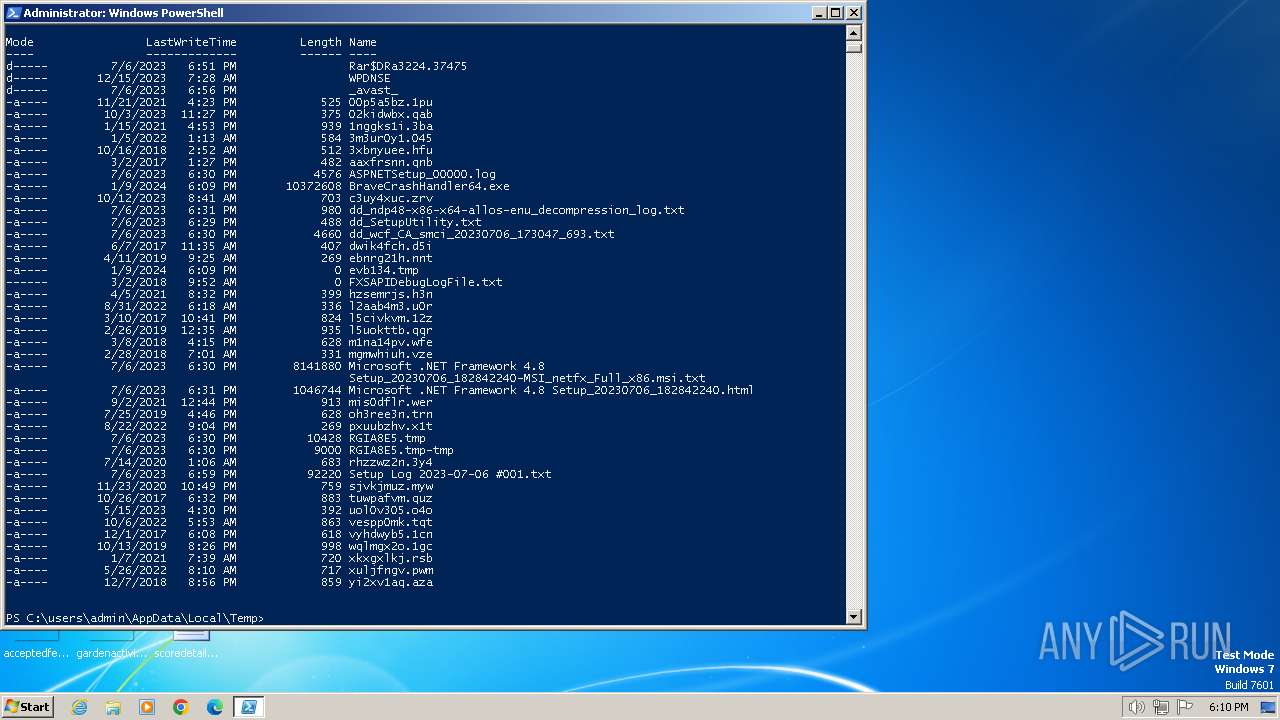
Create files in a temporary directory
- BraveCrashHandler64.exe (PID: 2040)
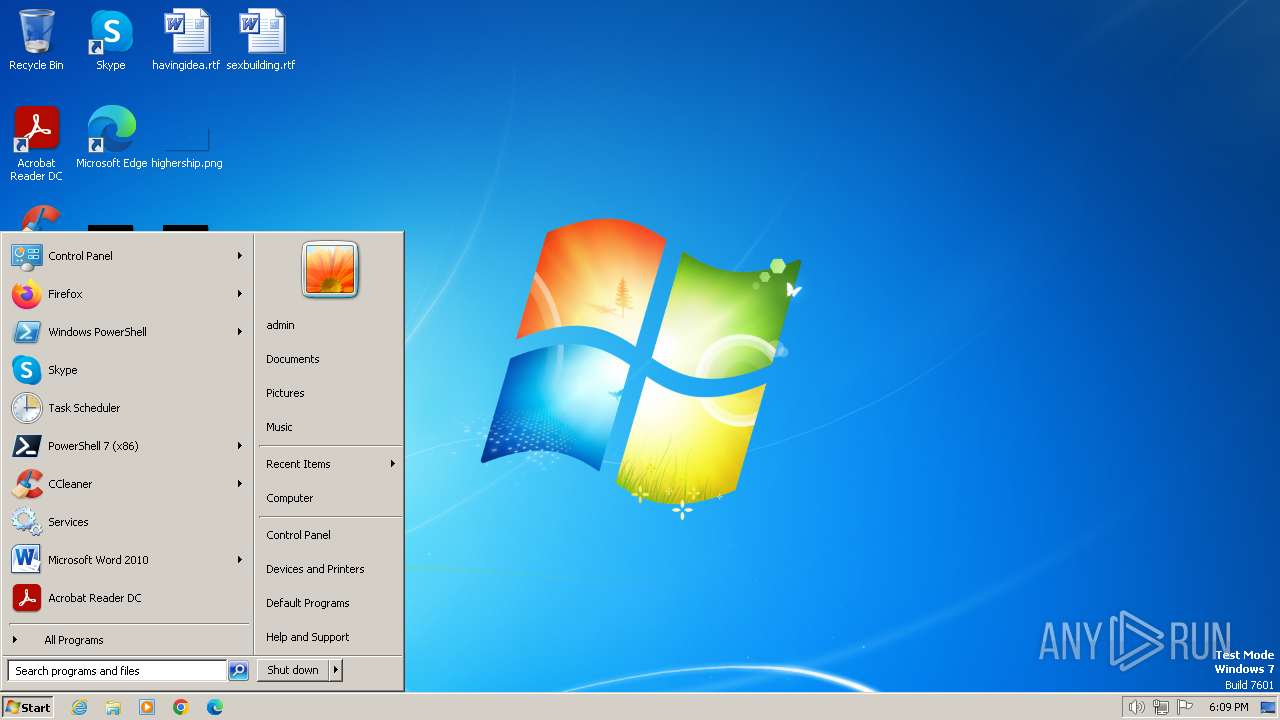
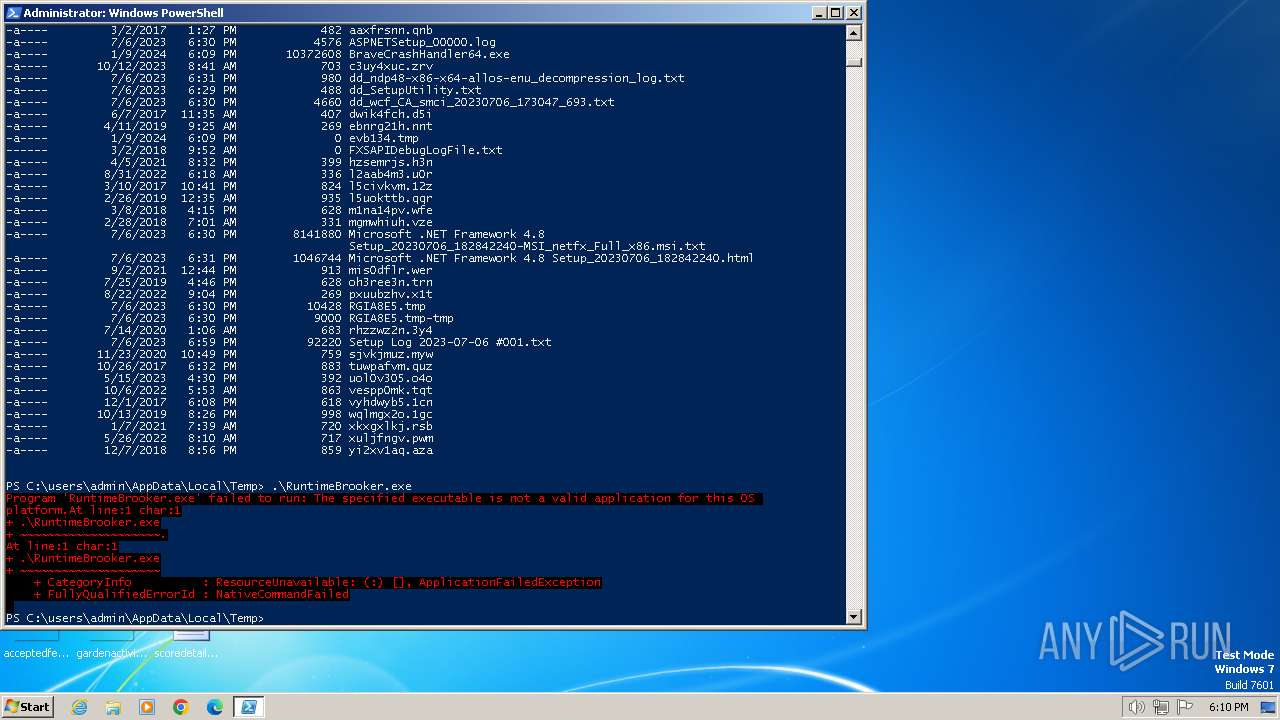
Manual execution by a user
- powershell.exe (PID: 1316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:11:16 23:57:03+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 35840 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3947bc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.361.141 |
| ProductVersionNumber: | 1.3.361.141 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | BraveSoftware Inc. |
| FileDescription: | BraveSoftware Update |
| FileVersion: | 1.3.361.141 |
| InternalName: | BraveSoftware Update |
| OriginalFileName: | BraveUpdate.exe |
| ProductName: | BraveSoftware Update |
| ProductVersion: | 1.3.361.141 |
| PrivateBuild: | - |
Total processes
62
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | FINDSTR /I "RuntimeBrooker.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | TASKLIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | FINDSTR /I "RuntimeBrooker.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | chcp 1252 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1380 | TIMEOUT /T 10 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | FINDSTR /I "RuntimeBrooker.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | TIMEOUT /T 10 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | FINDSTR /I "RuntimeBrooker.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\2040GRC2.bat" "C:\Users\admin\AppData\Local\Temp\BraveCrashHandler64.exe" " | C:\Windows\System32\cmd.exe | — | BraveCrashHandler64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 998
Read events
1 938
Write events
60
Delete events
0
Modification events
| (PID) Process: | (1316) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1316) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1316) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1316) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1316) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
6
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1316 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:FC7D37174171E1722F2DDE5758628A57 | SHA256:D11DCE78B444B42B01DC323CFF32F9B4B0ACDD8B733F3E4F10B9AD5231073267 | |||
| 1316 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe2314.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 2040 | BraveCrashHandler64.exe | C:\users\admin\appdata\local\temp\RuntimeBrooker.exe | executable | |
MD5:8417FF99EBE79A5911C32513E8C530C0 | SHA256:73E94205A2852B8A1A9E808D8D289571062307C7BCC7AB9D13835CE69554C9E6 | |||
| 1316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\i3kramop.sab.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2040 | BraveCrashHandler64.exe | C:\Users\admin\AppData\Local\Temp\2040GRC2.bat | text | |
MD5:D541D3874D09E1CC00B0450AECAA180C | SHA256:C0D8E7C585BF2A4C178F08908DA1958BBCD613554077B679E6EC87602F077507 | |||
| 1316 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YHSY9GN5GF5H51TQMPRX.temp | binary | |
MD5:FC7D37174171E1722F2DDE5758628A57 | SHA256:D11DCE78B444B42B01DC323CFF32F9B4B0ACDD8B733F3E4F10B9AD5231073267 | |||
| 1316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\uvyzvyvn.mql.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1316 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:DE3E389E155C6845D43C07185A11ACF1 | SHA256:6761E2D1F087BBAA8A8DB8B1294E66088FDBE0B9B7FC6E43476D8B2ABDB79E56 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |