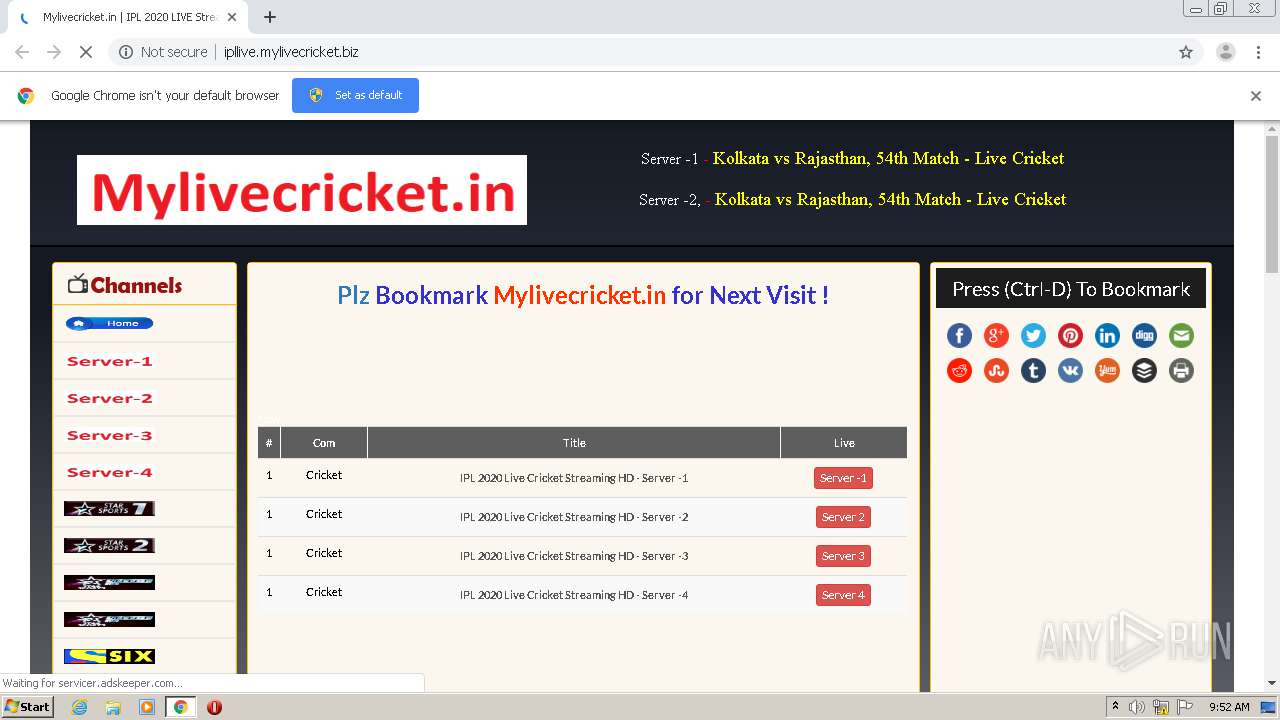
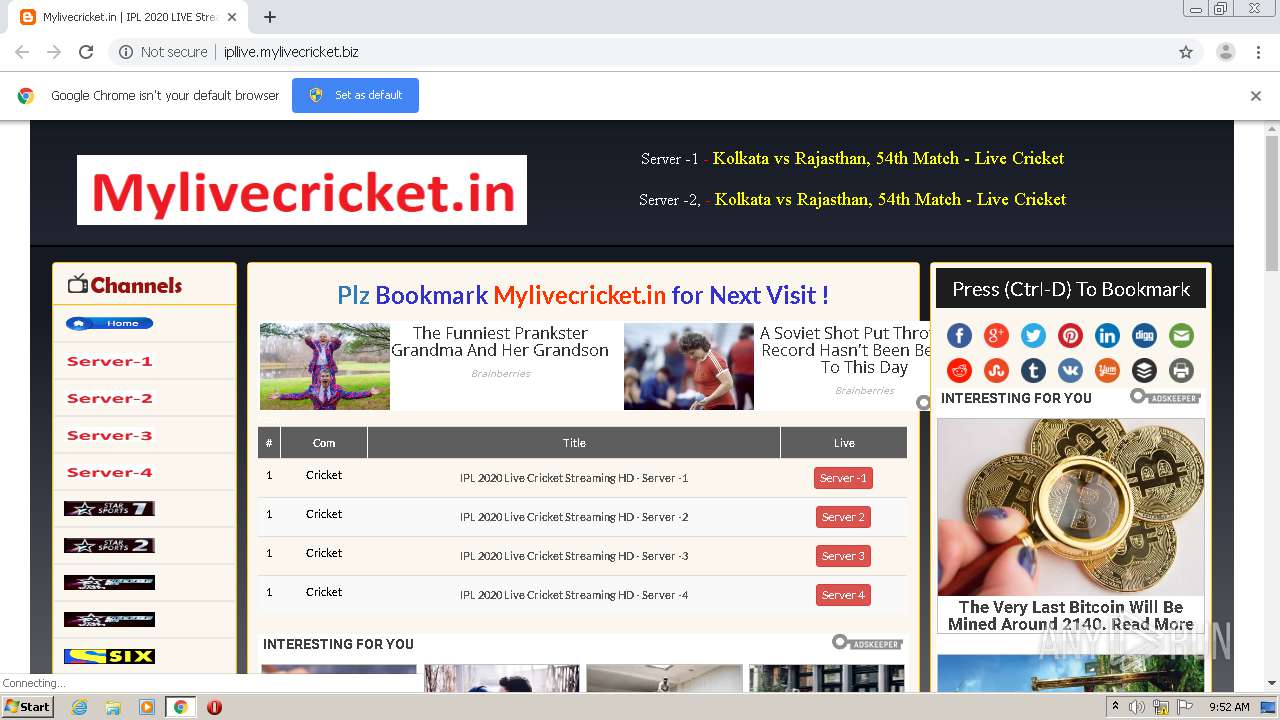
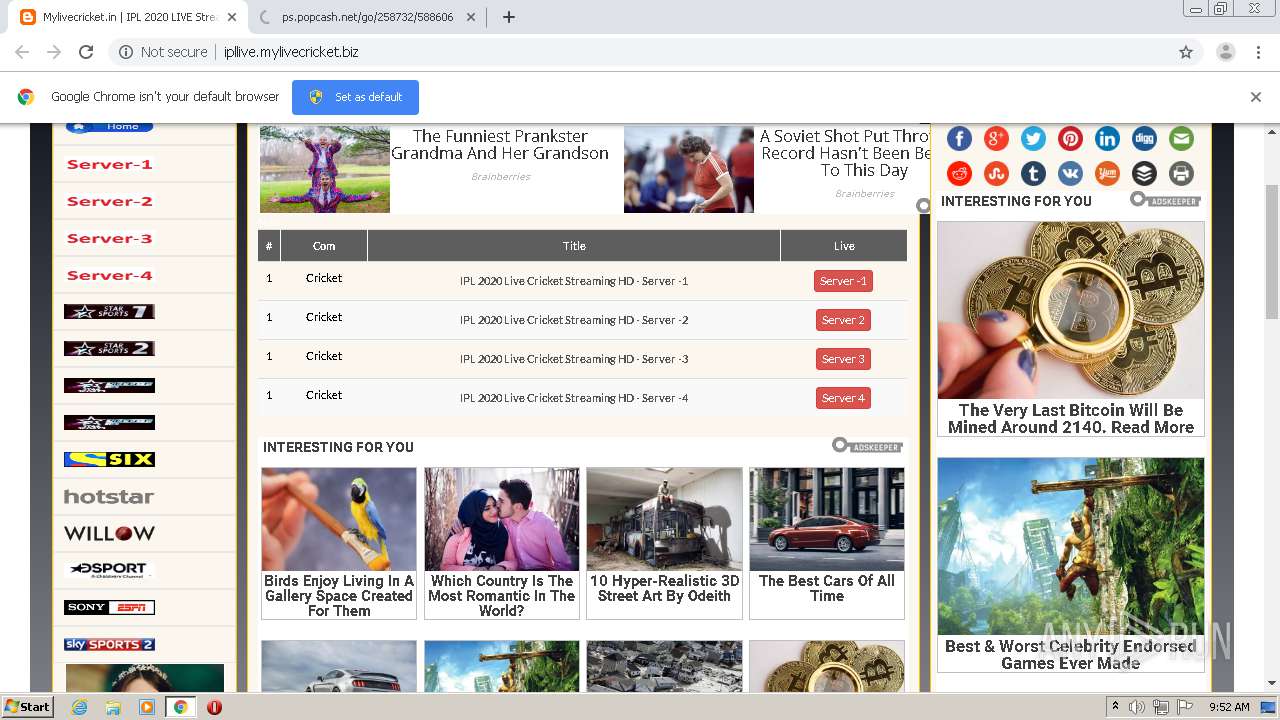
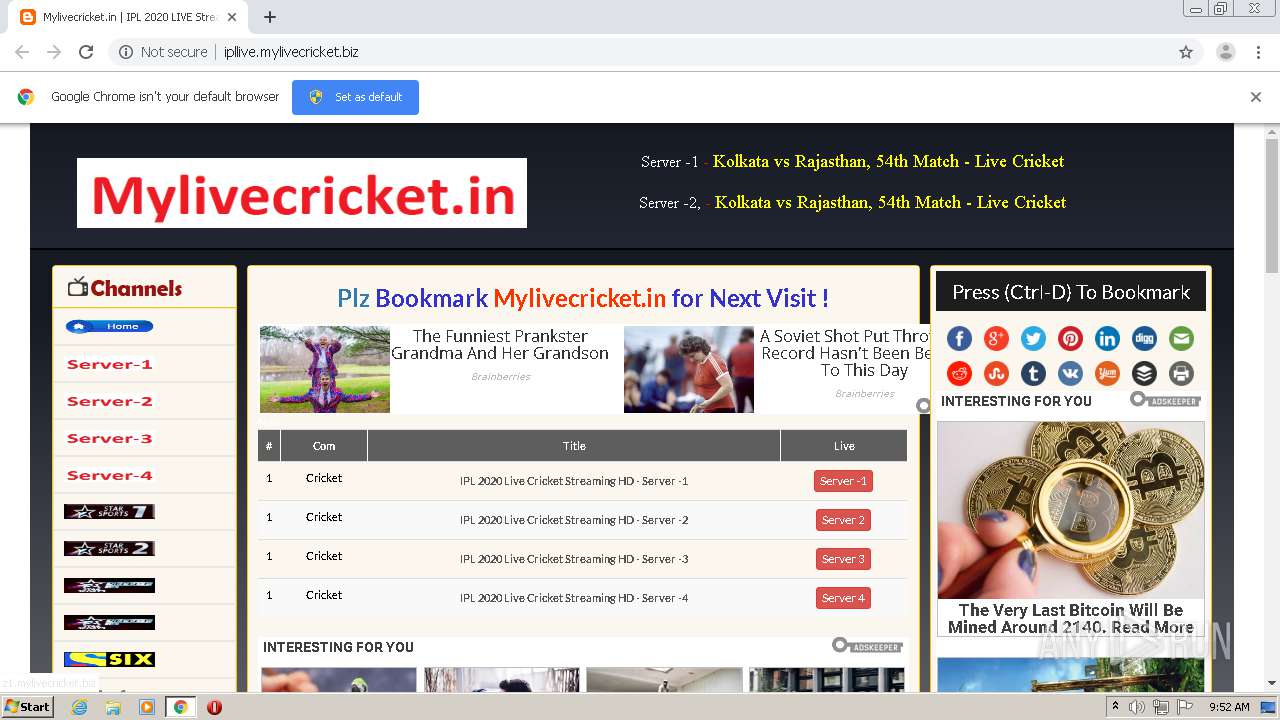
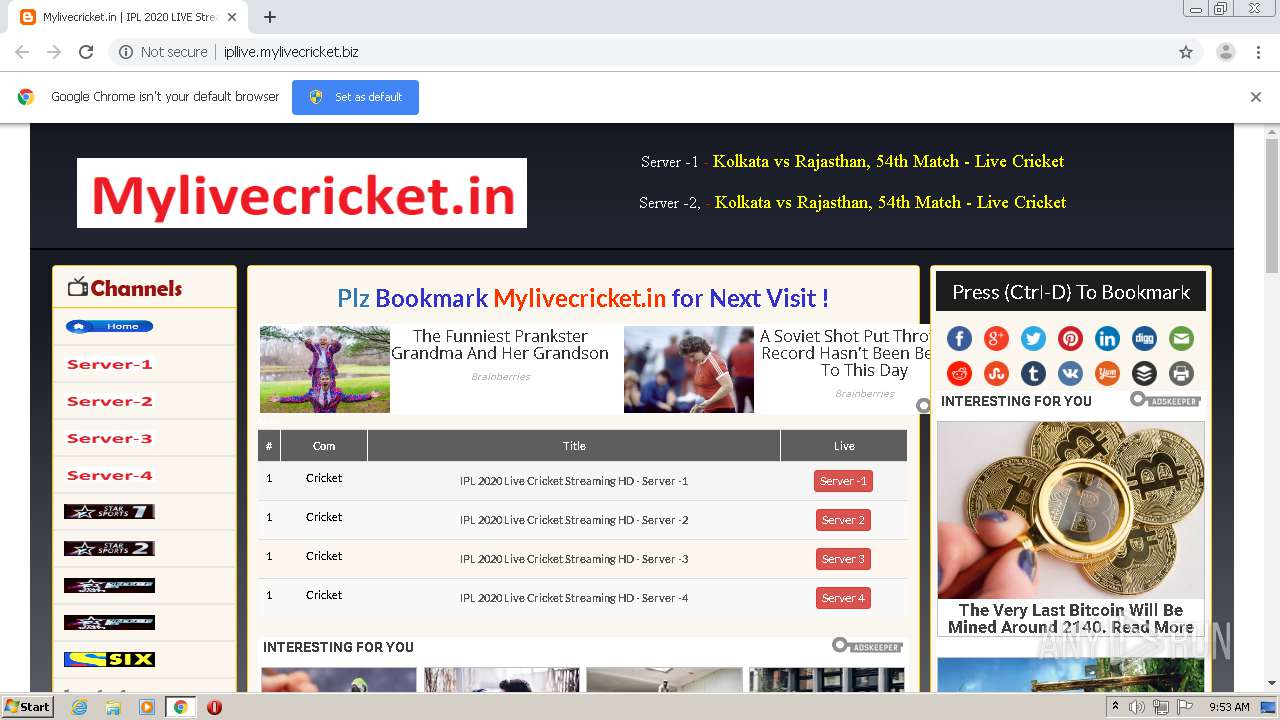
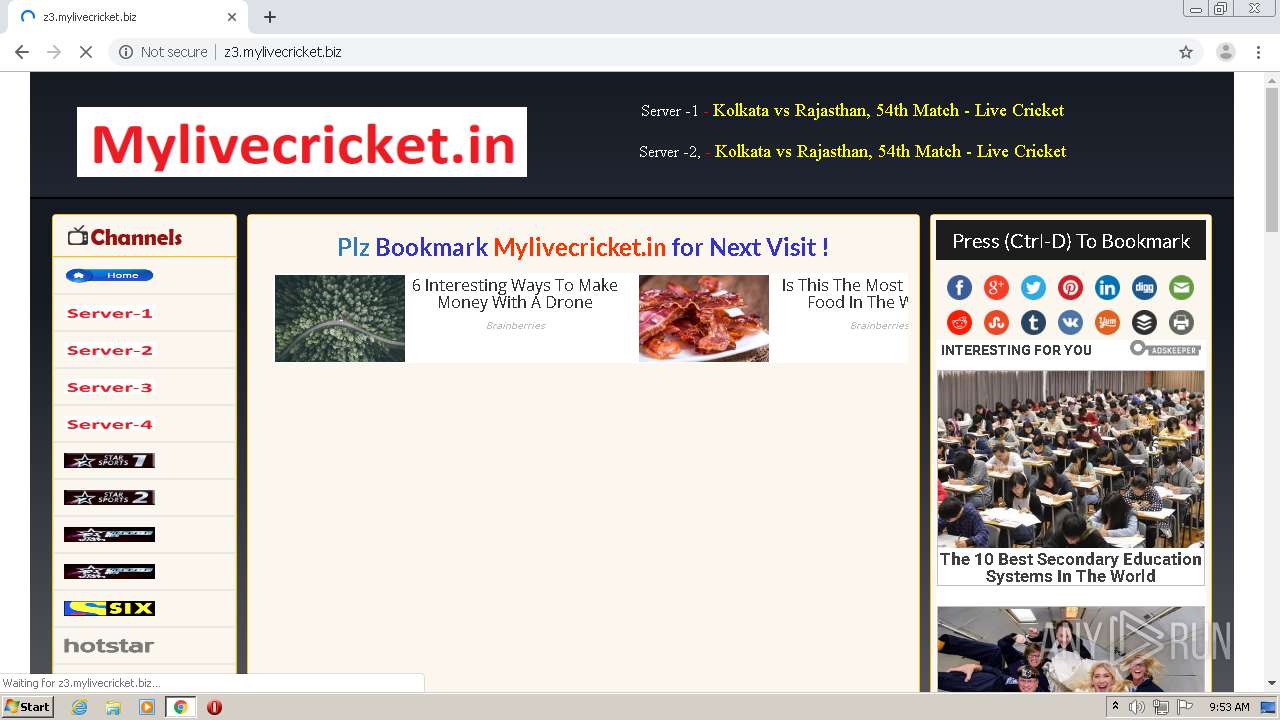
| URL: | http://ipllive.mylivecricket.biz/ |
| Full analysis: | https://app.any.run/tasks/5b0b8167-cc38-43be-b6bf-898a359f228c |
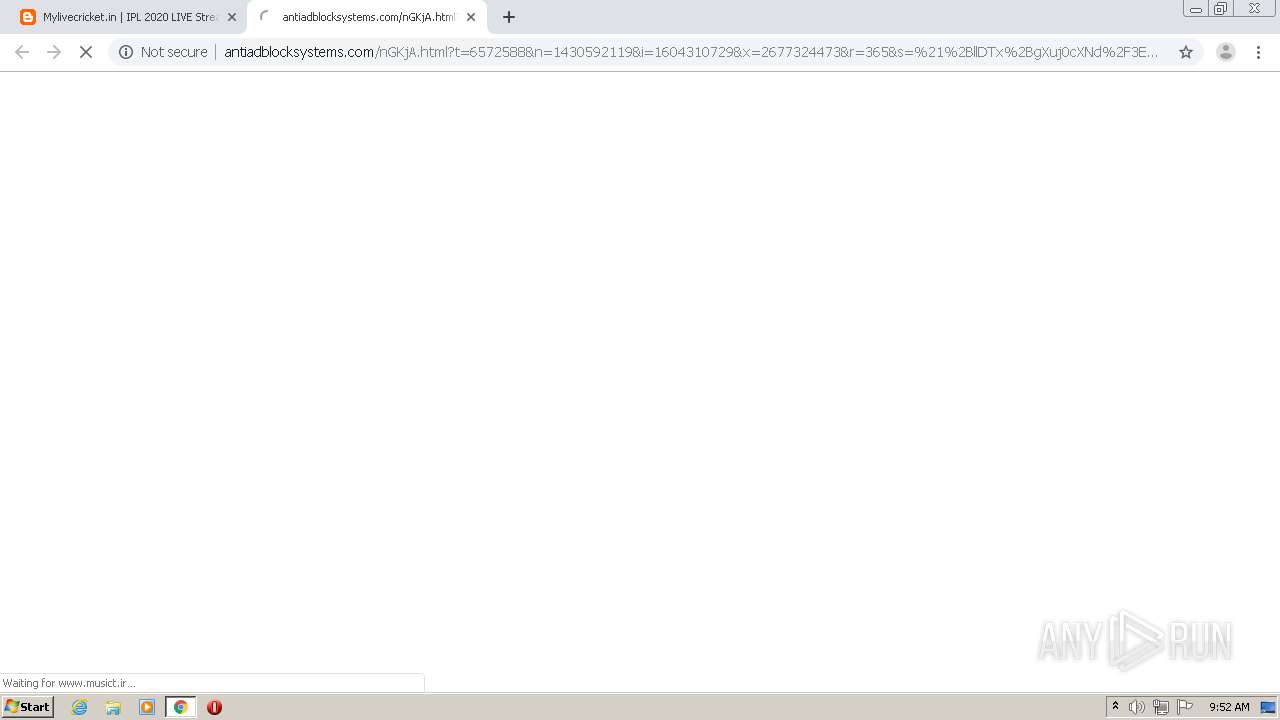
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2020, 09:51:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 18AA1AA778C6DB22EAF0071ACABF26CA |
| SHA1: | CC0F69CECC39AC04A836A1F07937150CCCB1C122 |
| SHA256: | 282B2EBCEC669A37B32D4CBC9F3AFAAC5E665EA93B9AD0676BBF23CD13D67512 |
| SSDEEP: | 3:N1KX1MxYGOy1:CDGOA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2572)
INFO
Reads the hosts file
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2572)
Application launched itself
- chrome.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=237757284331669523 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3838905861145201015 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6371204258642563806 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10682171746789919000 --mojo-platform-channel-handle=3476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12613240579348929370 --mojo-platform-channel-handle=3484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1535492654392521840 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4426196231586578901 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12817325413275052591 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=108685321839084525 --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1433287311594720590,6704654820066144588,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11201074191330457461 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
642
Read events
544
Write events
93
Delete events
5
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2572-13248784320515500 |
Value: 259 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
106
Text files
239
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F9FD6C1-A0C.pma | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d85e7bf3-4e7c-4677-a2e3-cceb86eb4540.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1899ba.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF189a47.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF189a57.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF189b9f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
209
DNS requests
108
Threats
228
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2112 | chrome.exe | GET | 403 | 192.243.59.20:80 | http://radiancethedevice.com/e2/ec/c8/e2ecc80492ec53289cdff91eef6b0e88.js | US | — | — | malicious |
2112 | chrome.exe | GET | 403 | 192.243.59.20:80 | http://radiancethedevice.com/e2/ec/c8/e2ecc80492ec53289cdff91eef6b0e88.js | US | — | — | malicious |
2112 | chrome.exe | GET | 403 | 192.243.59.20:80 | http://radiancethedevice.com/29/bf/f3/29bff3c1cc40893cc60afa31ac01fca2.js | US | — | — | malicious |
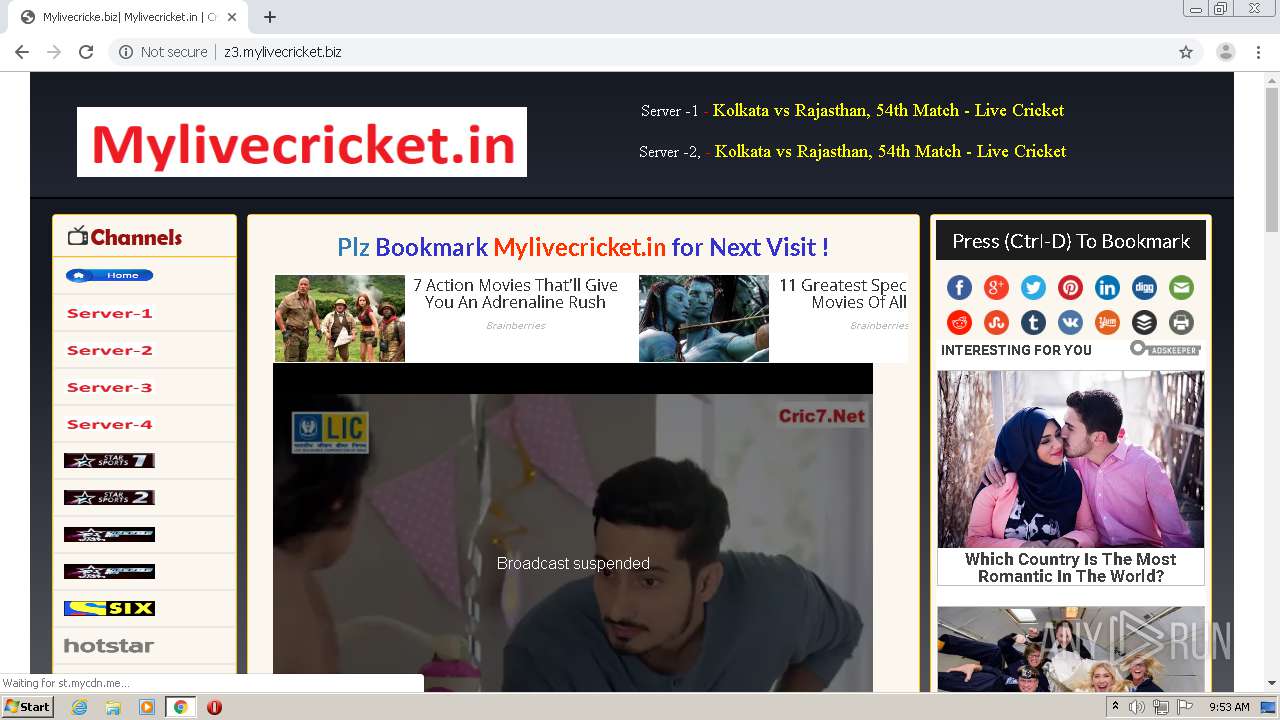
2112 | chrome.exe | GET | — | 208.93.230.16:80 | http://st.chatango.com/js/gz/emb.js | US | — | — | whitelisted |
2112 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://4.bp.blogspot.com/-4HFPIDzMzzM/WR7efCF8gPI/AAAAAAAAAD0/BoFXeKBnVlkY3CNiRktPZnf9zHy06kL4wCLcB/s320/star2.png | US | image | 20.2 Kb | whitelisted |
2112 | chrome.exe | GET | 200 | 142.250.74.193:80 | http://2.bp.blogspot.com/-kwAER8qXGWY/WSa_nS-di8I/AAAAAAAAAGE/aIT-HL5SHi4gHdjoGGkVfilQdOiMAc78QCLcB/s320/home_button.png | US | image | 23.8 Kb | whitelisted |
2112 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://1.bp.blogspot.com/-KX5lvpQ_f7c/WUT-g5qilcI/AAAAAAAAAJY/Cc9pZ1k2iy8nump40syJ5QZQczYlq7d1ACLcBGAs/s1600/mylive.png | US | image | 7.36 Kb | whitelisted |
2112 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://4.bp.blogspot.com/-RAMUYBnzwUM/WR7mC-SUX5I/AAAAAAAAAEk/Aa8MQqM15XUqd71lNIT_6PNvcwW75Lx9ACLcB/s1600/23.png | US | image | 4.68 Kb | whitelisted |
2112 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://3.bp.blogspot.com/-x3R--bo1dnI/WR7ecyVlJgI/AAAAAAAAADM/AHWLYNZb4LUDjb5i9qPdCbgMB9SSTW24QCLcB/s1600/schedule.png | US | image | 1.96 Kb | whitelisted |
2112 | chrome.exe | GET | 200 | 172.217.22.115:80 | http://a.cric7.biz/ | US | html | 3.37 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2112 | chrome.exe | 172.217.16.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 216.58.206.1:80 | 1.bp.blogspot.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 185.199.108.153:80 | — | GitHub, Inc. | NL | shared |
2112 | chrome.exe | 142.250.74.193:80 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 142.250.74.193:443 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 172.217.18.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 185.199.108.153:443 | — | GitHub, Inc. | NL | shared |
2112 | chrome.exe | 172.217.22.1:443 | lh4.googleusercontent.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 104.18.17.65:443 | jsc.adskeeper.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipllive.mylivecricket.biz |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.blogger.com |
| shared |
1.bp.blogspot.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
mylivecricket.github.io |
| malicious |
fonts.googleapis.com |
| whitelisted |
2.bp.blogspot.com |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2112 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |