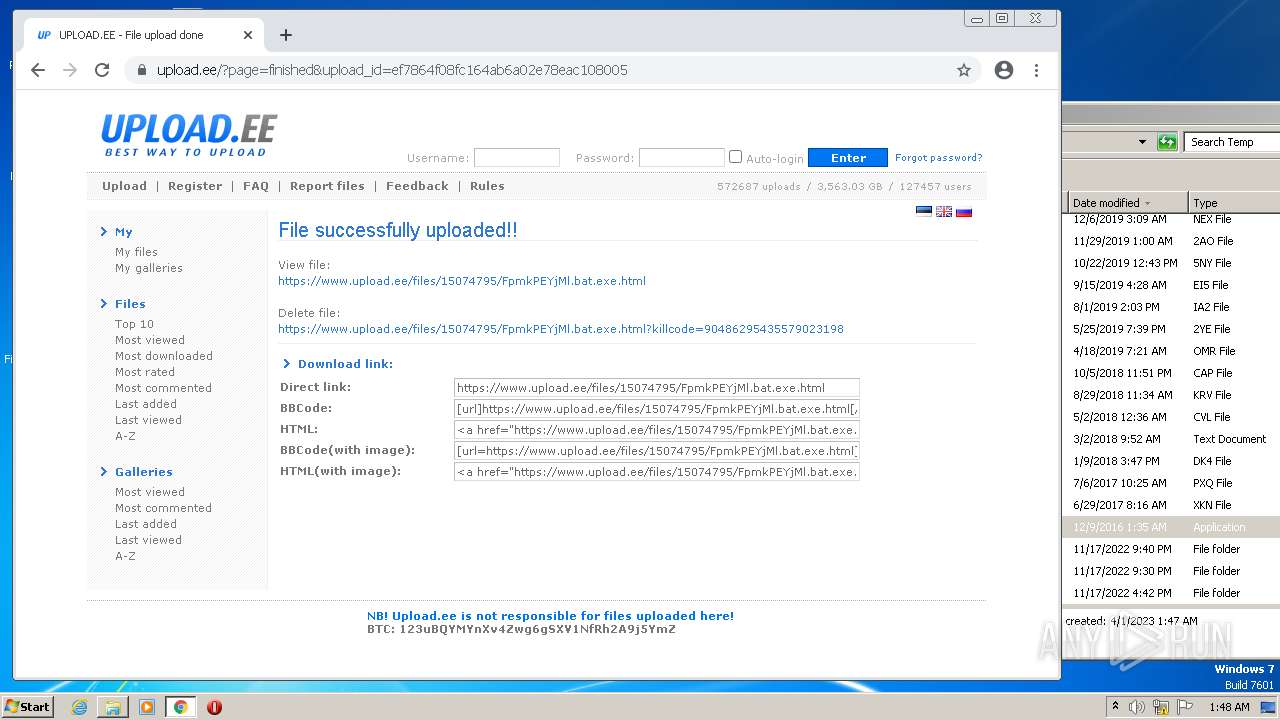
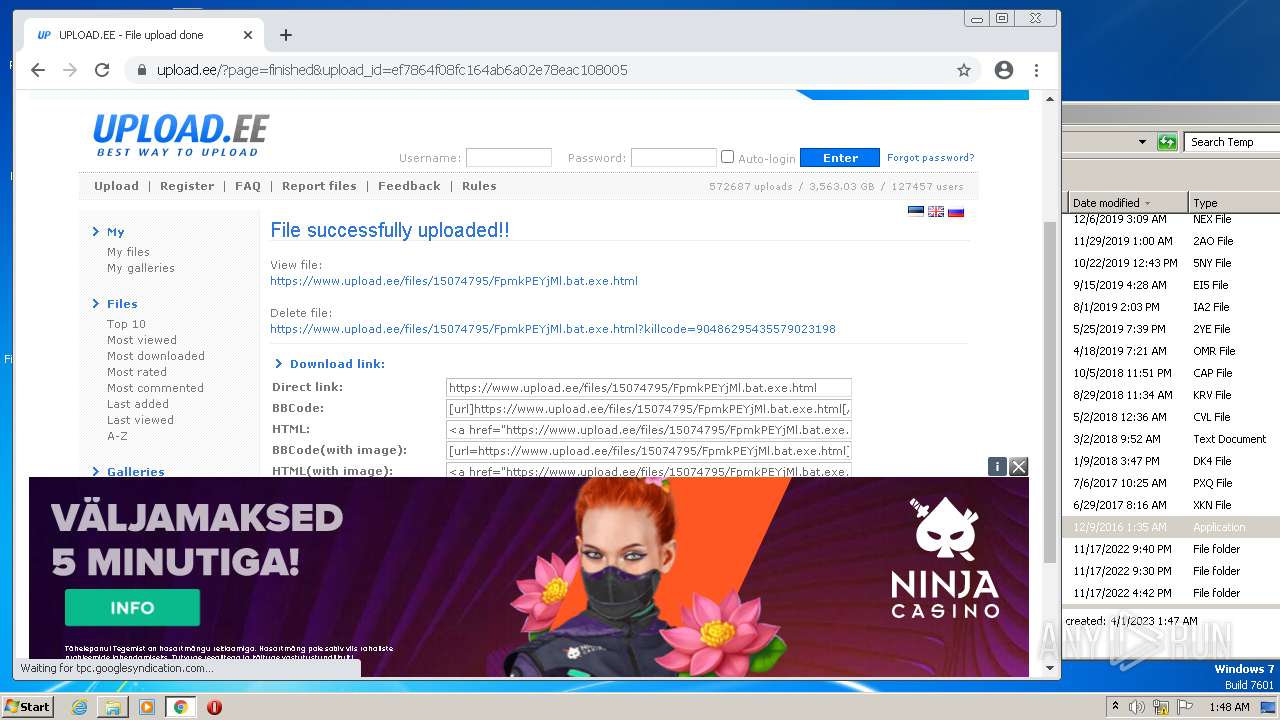
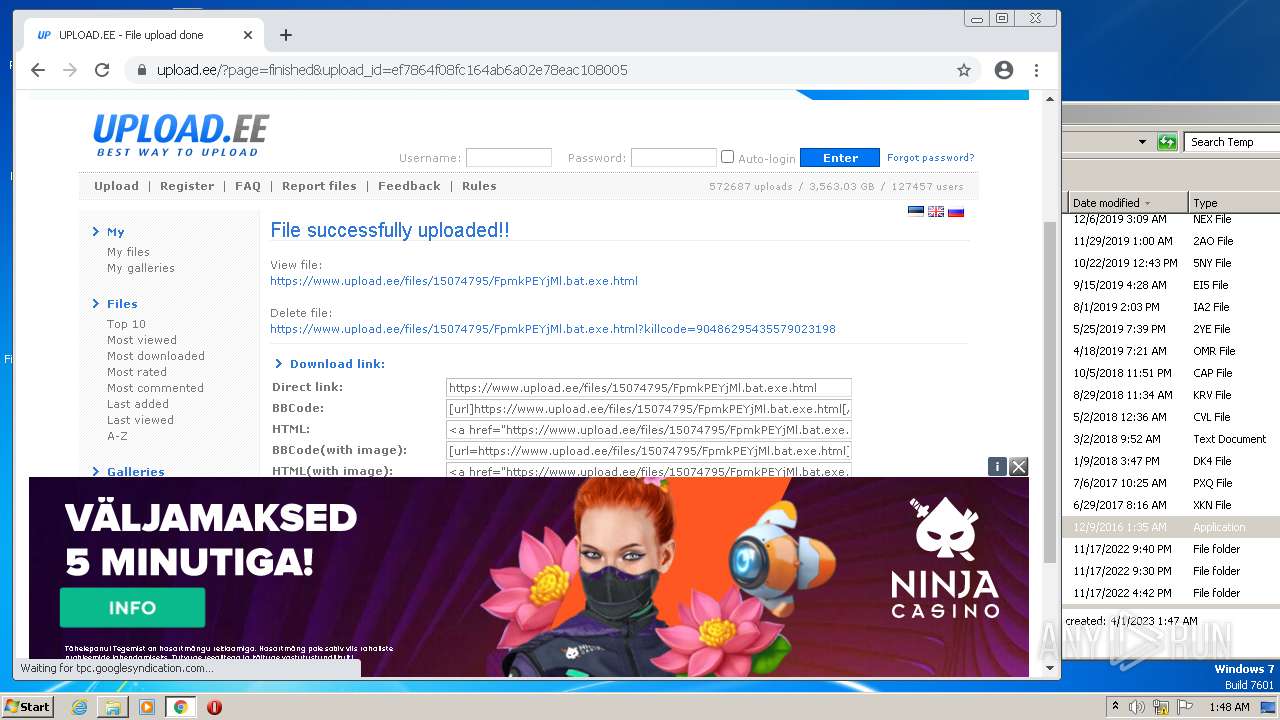
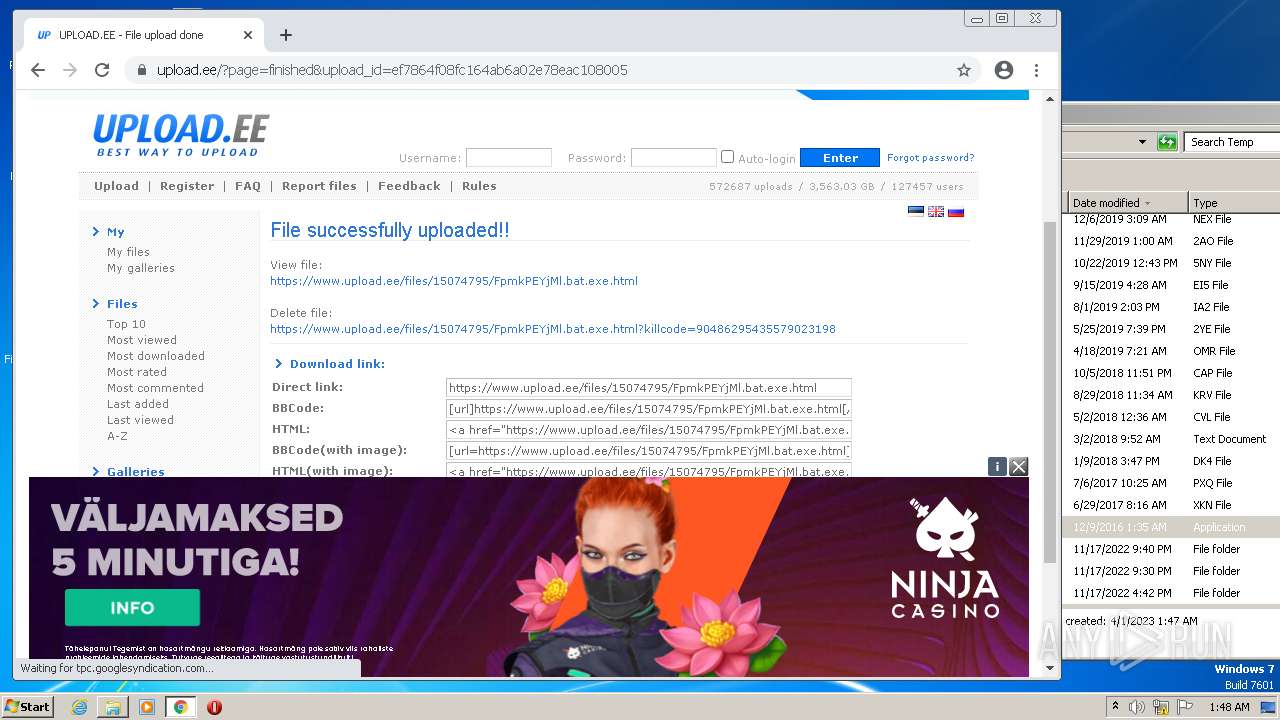
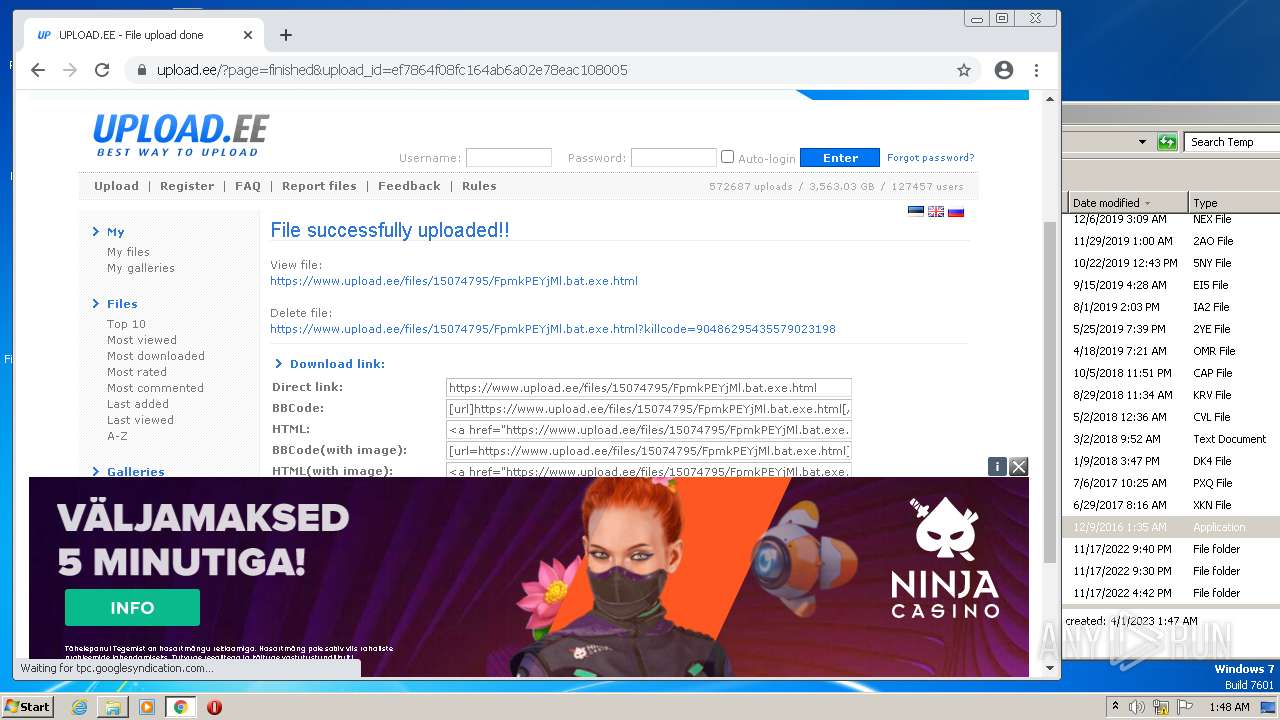
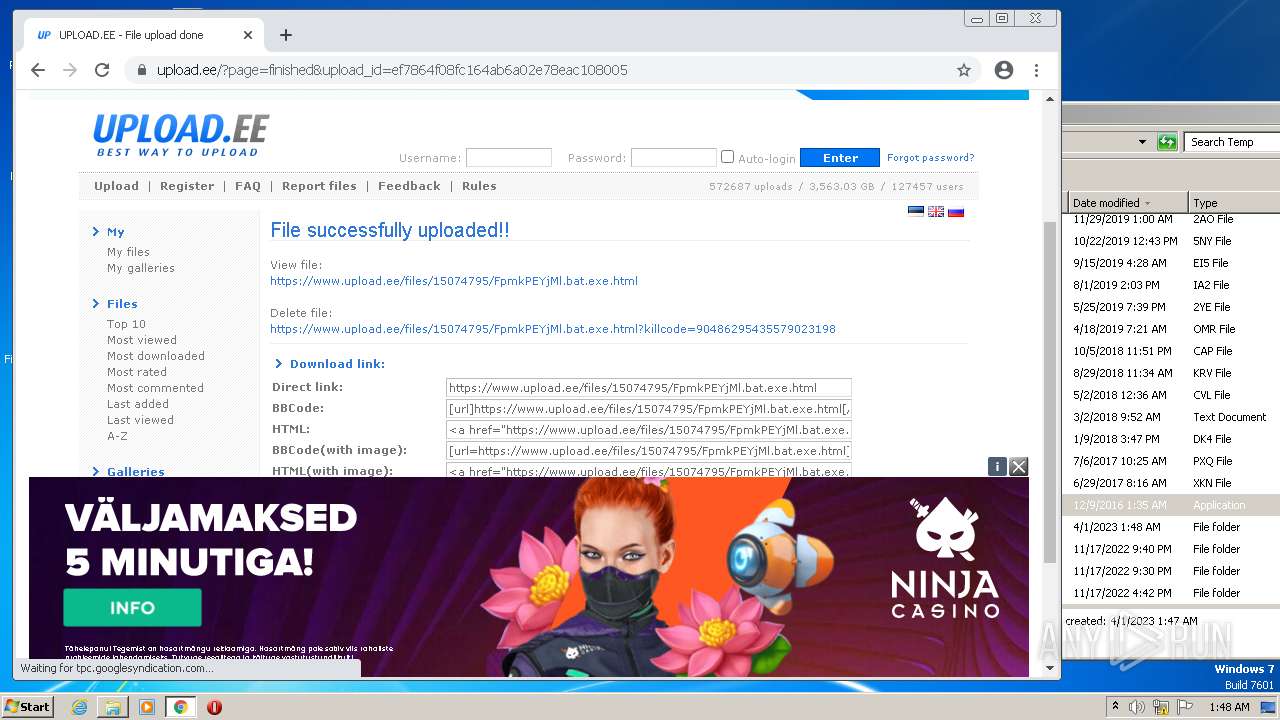
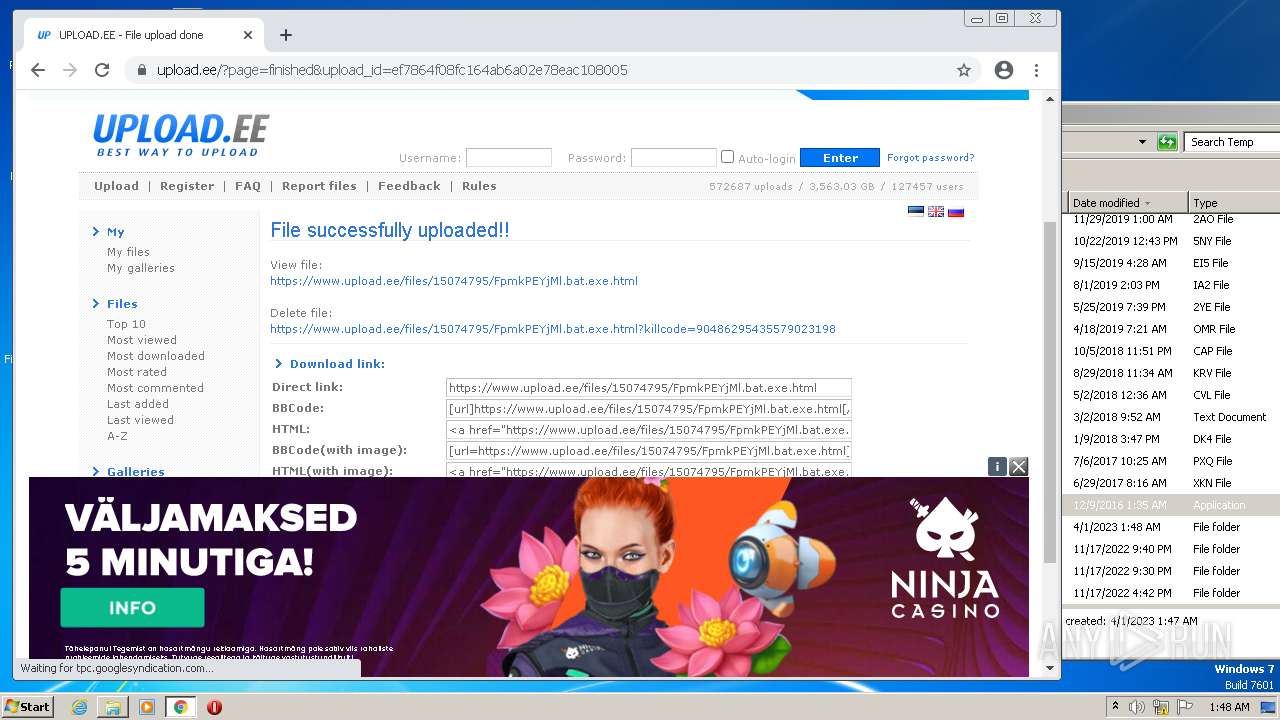
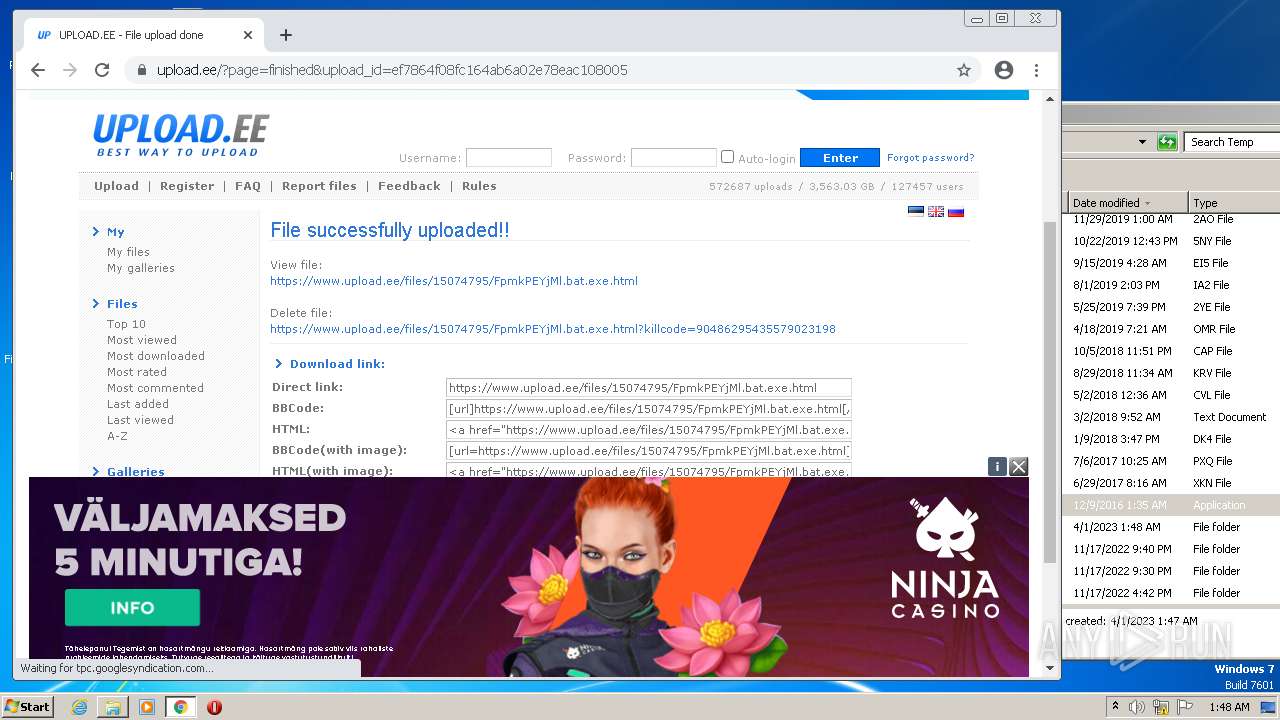
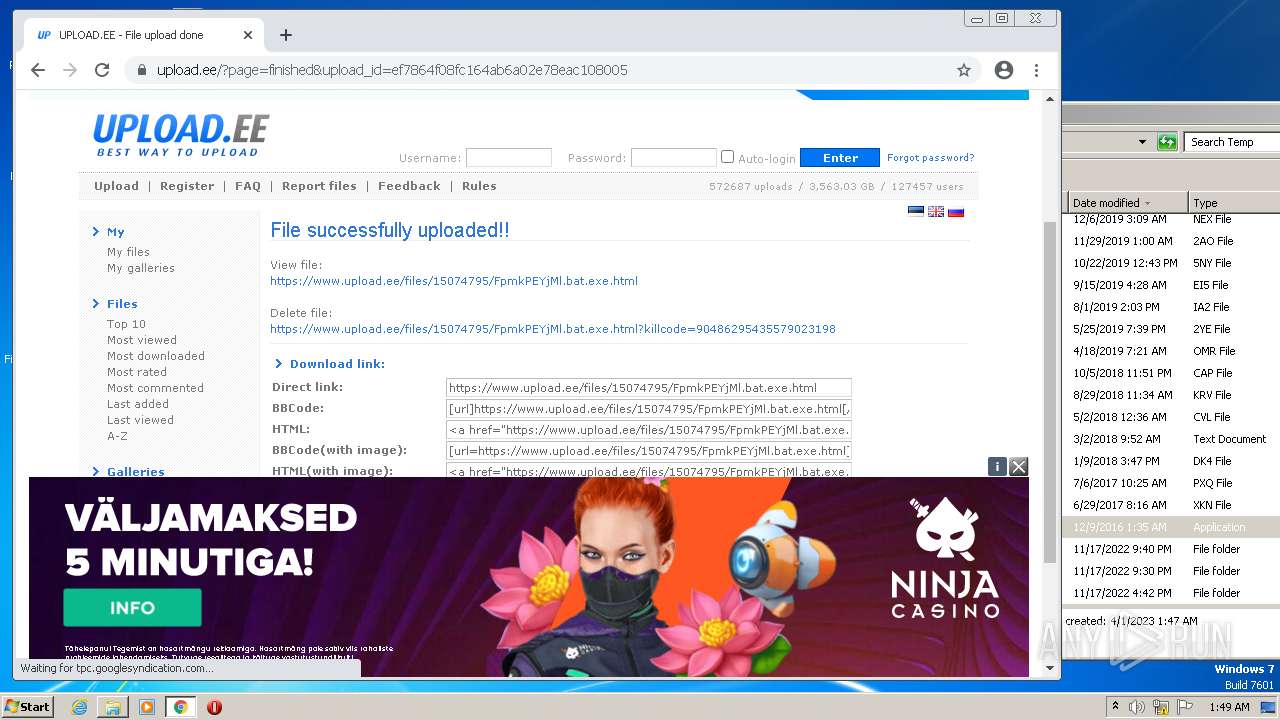
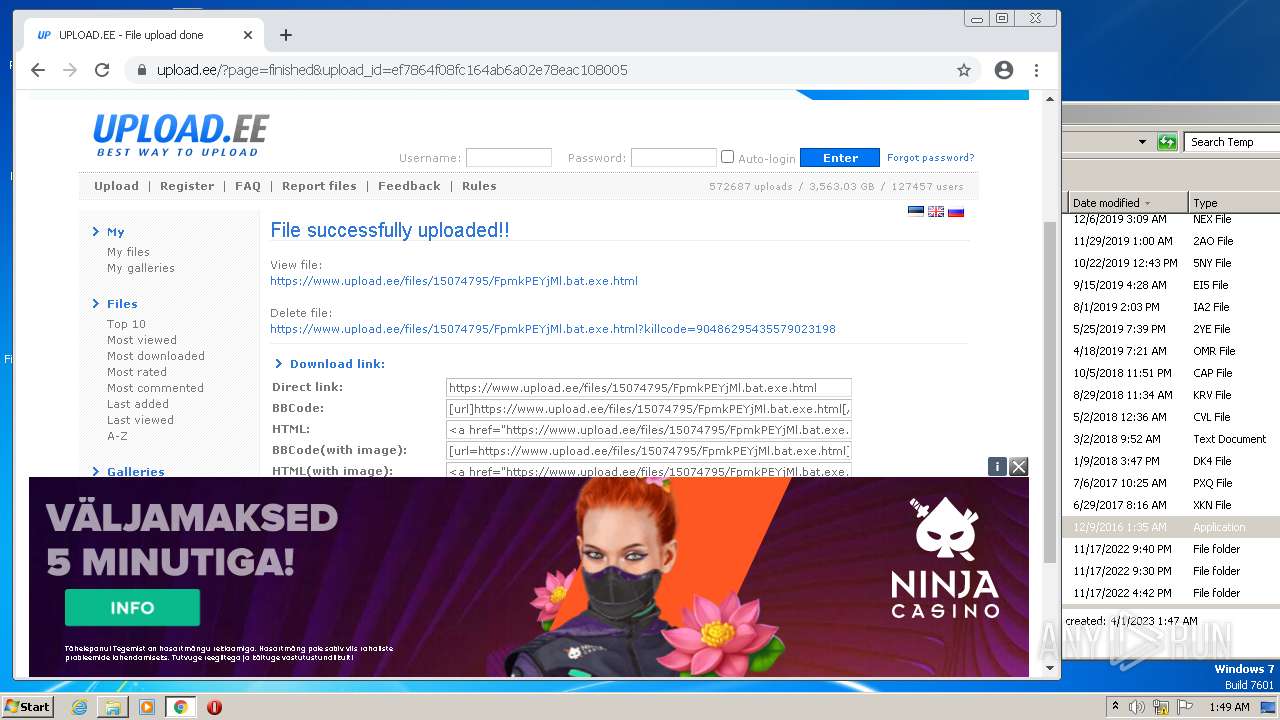
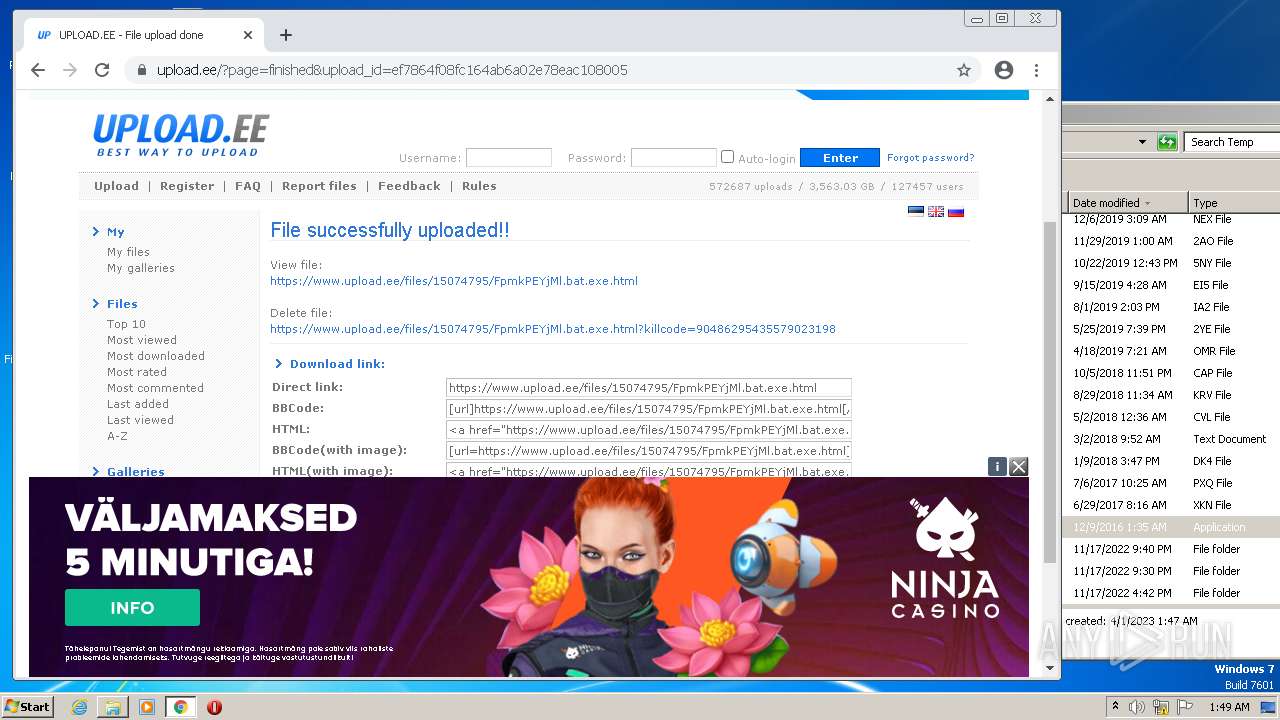
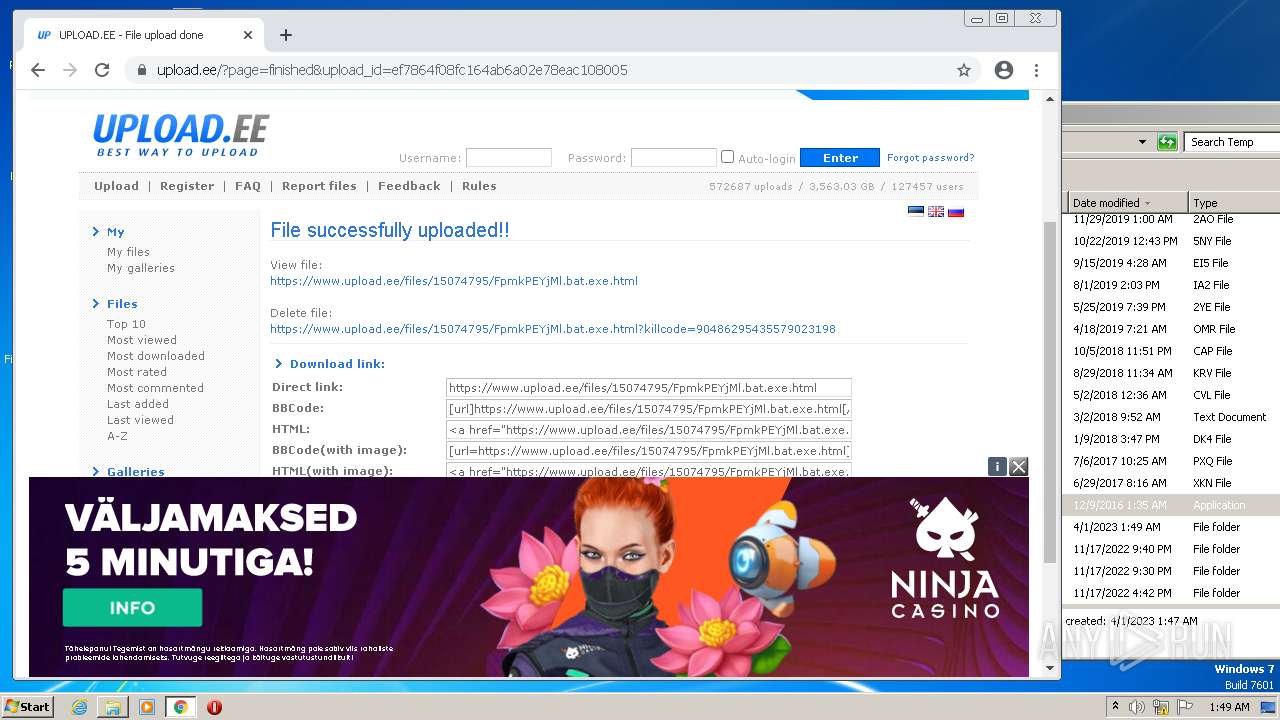
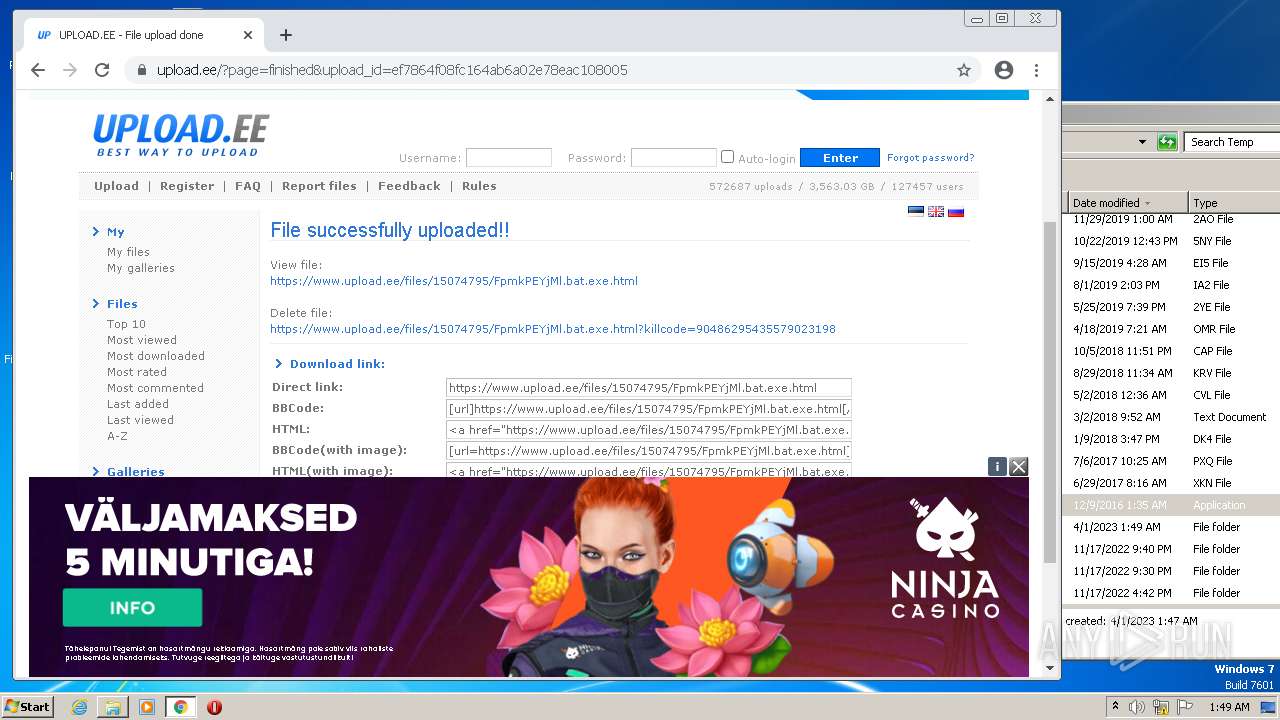
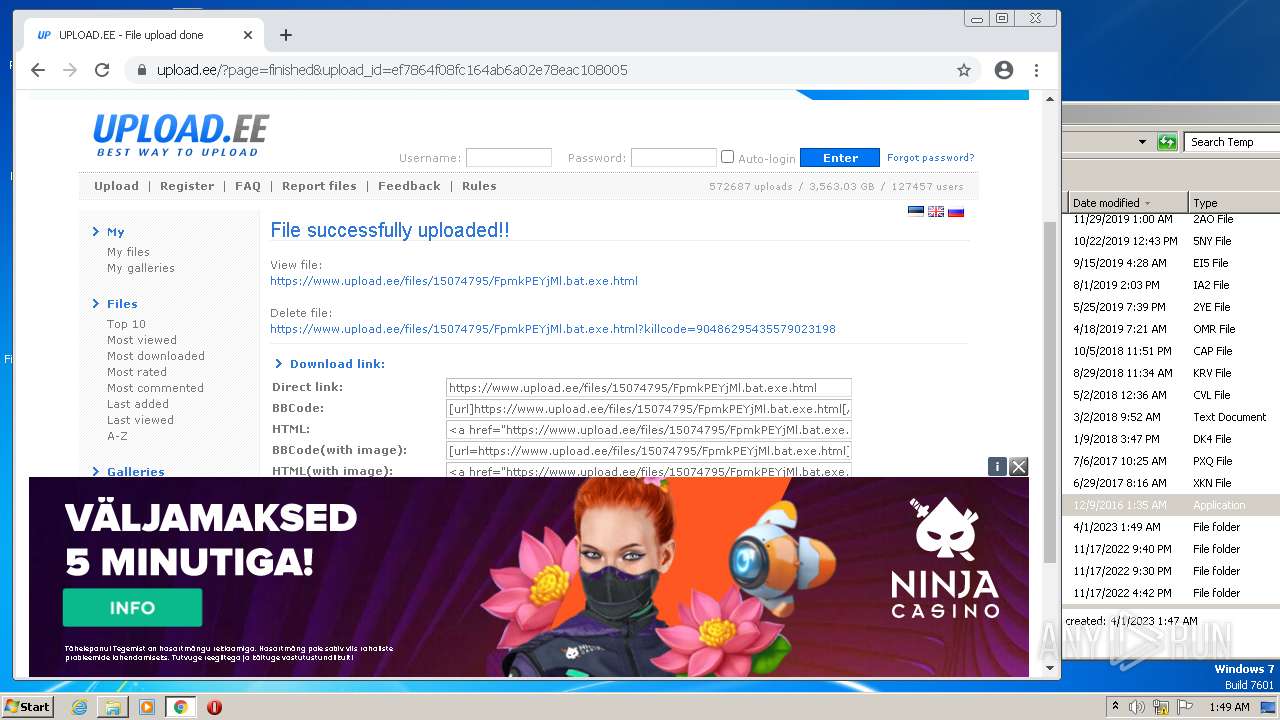
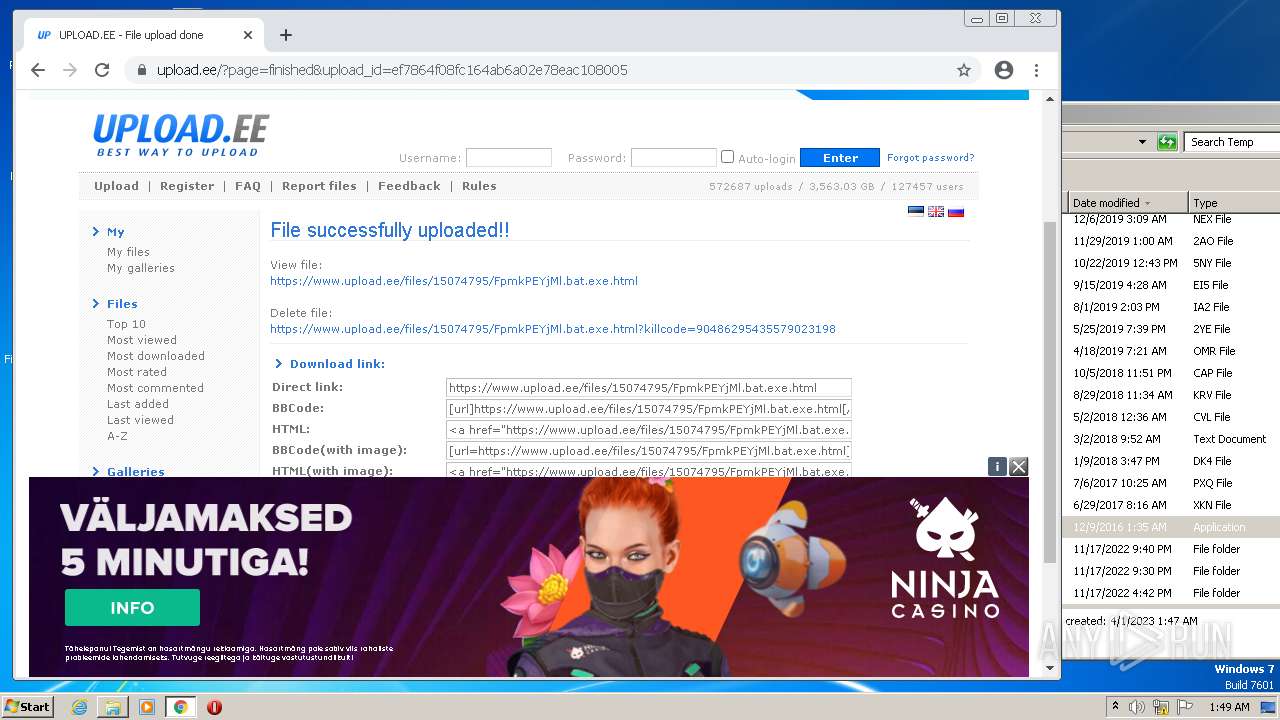
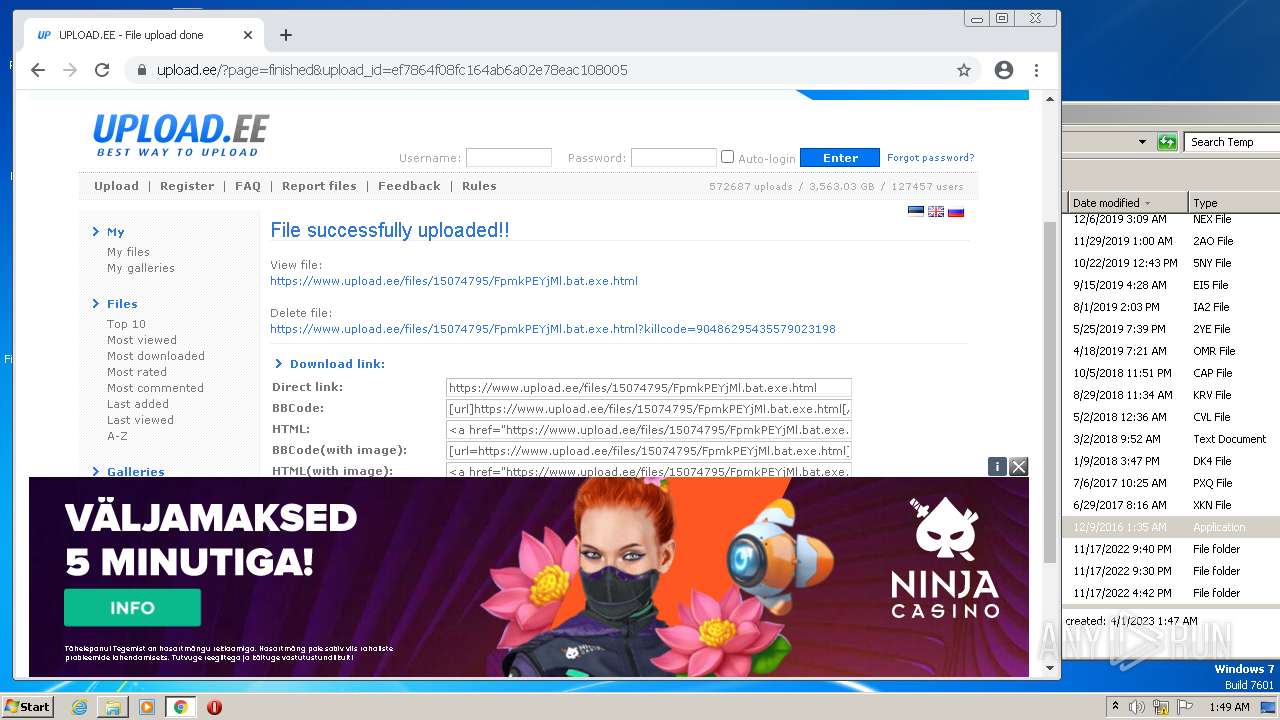
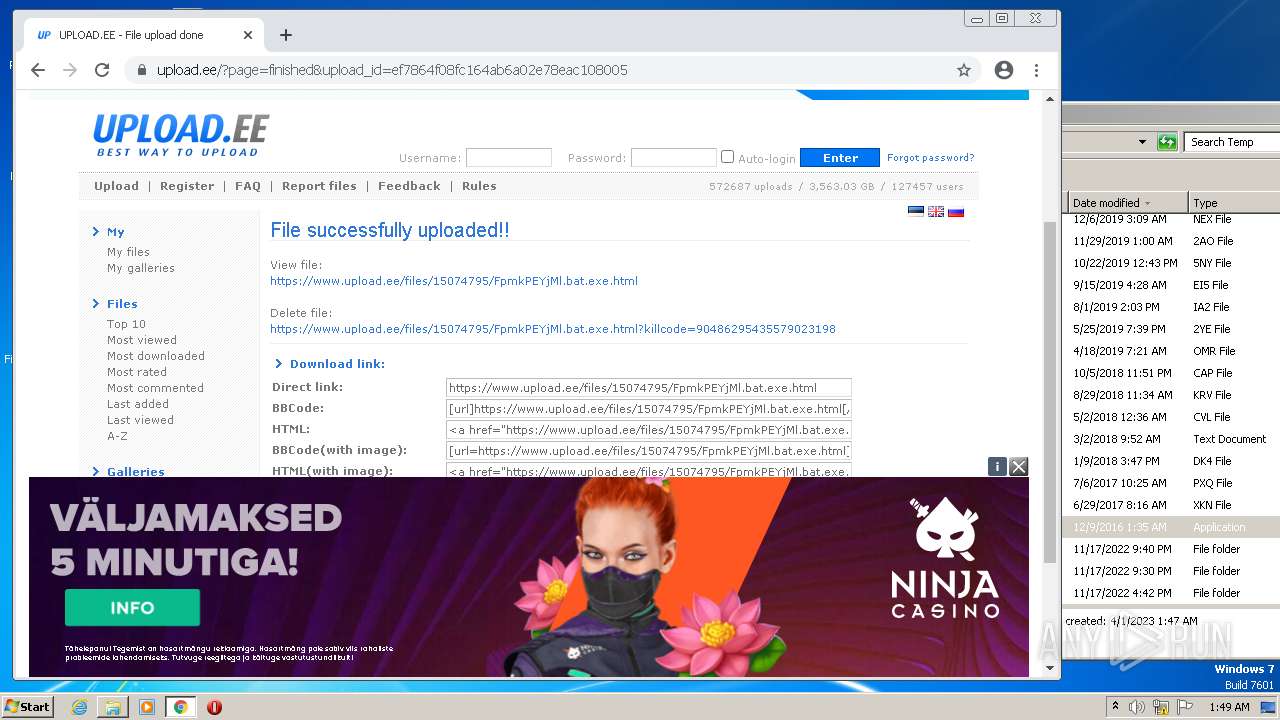
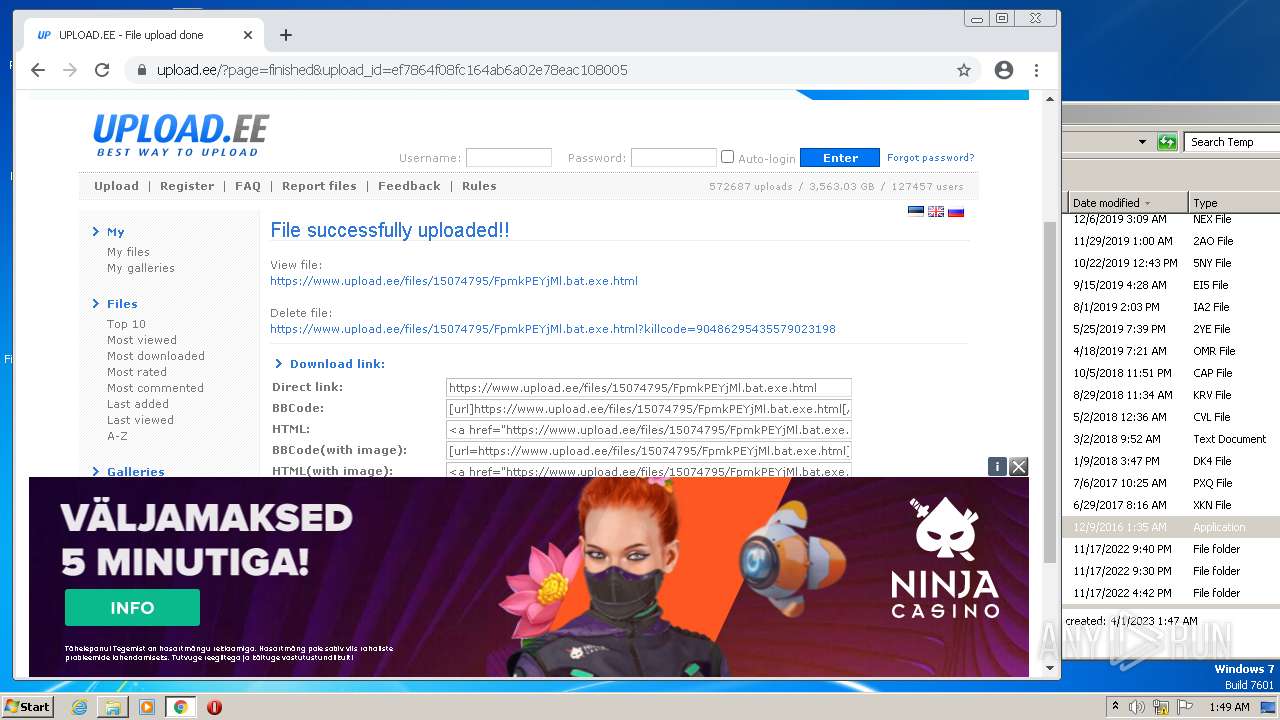
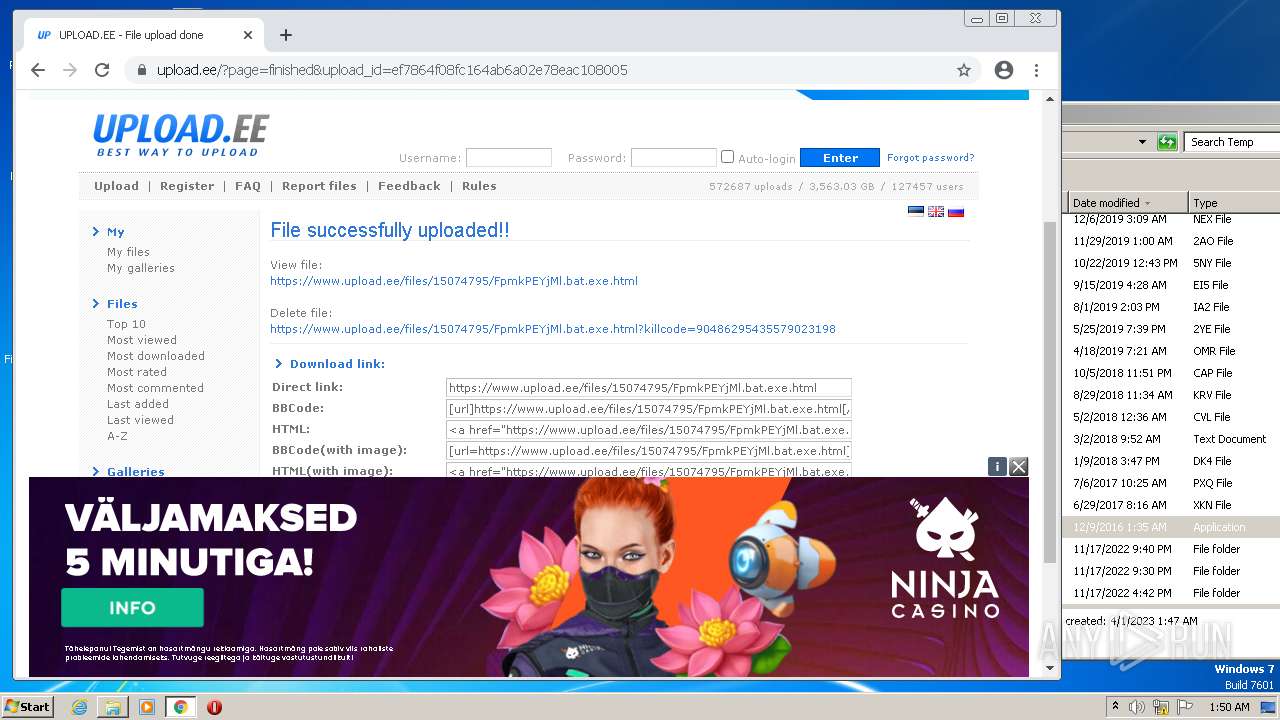
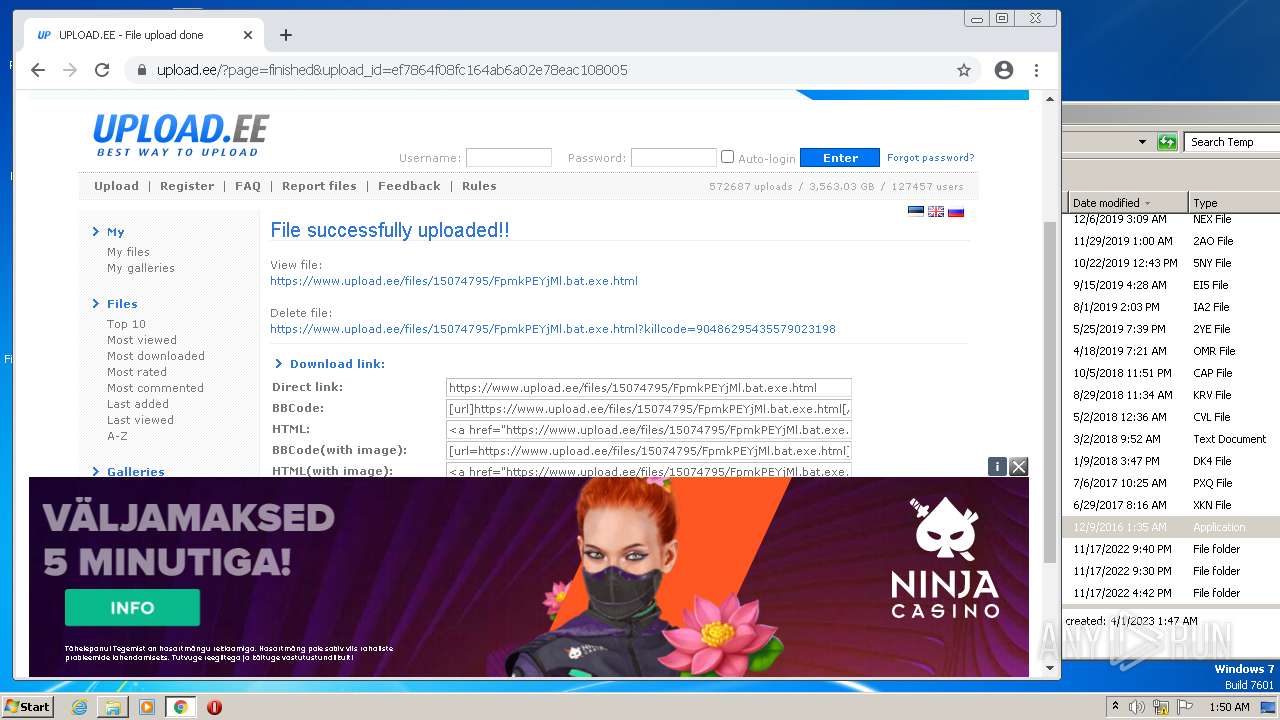
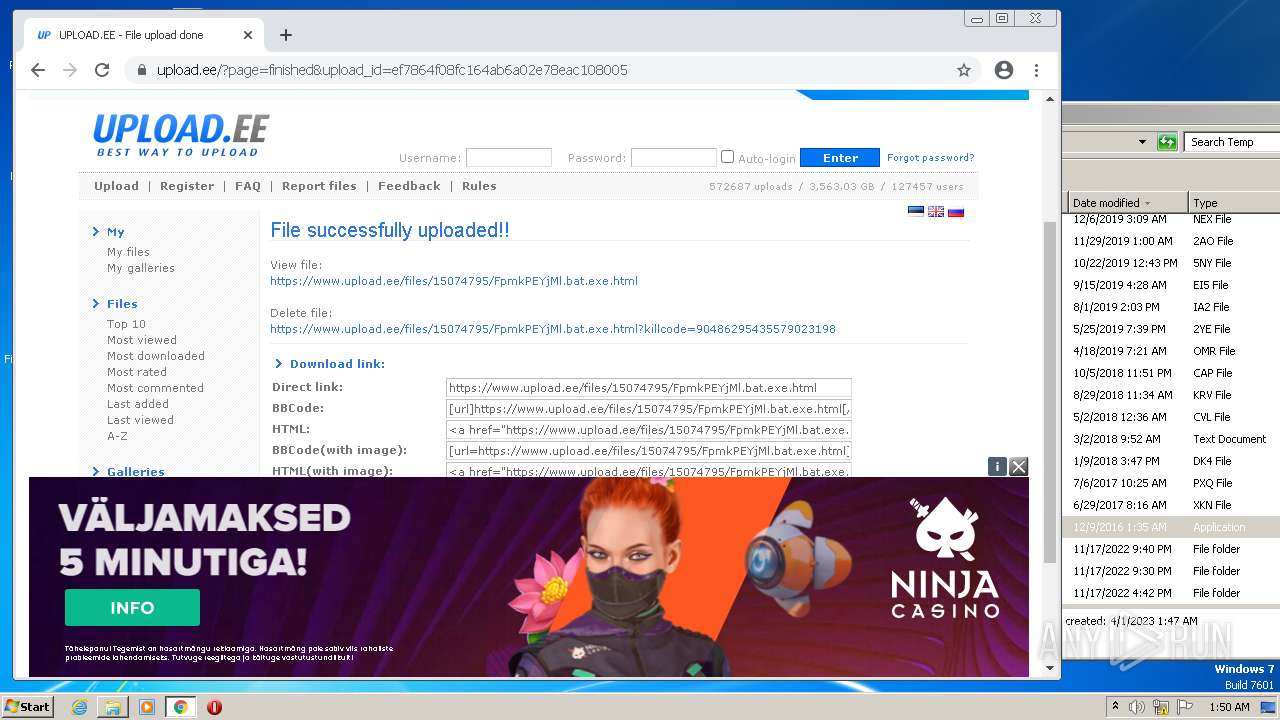
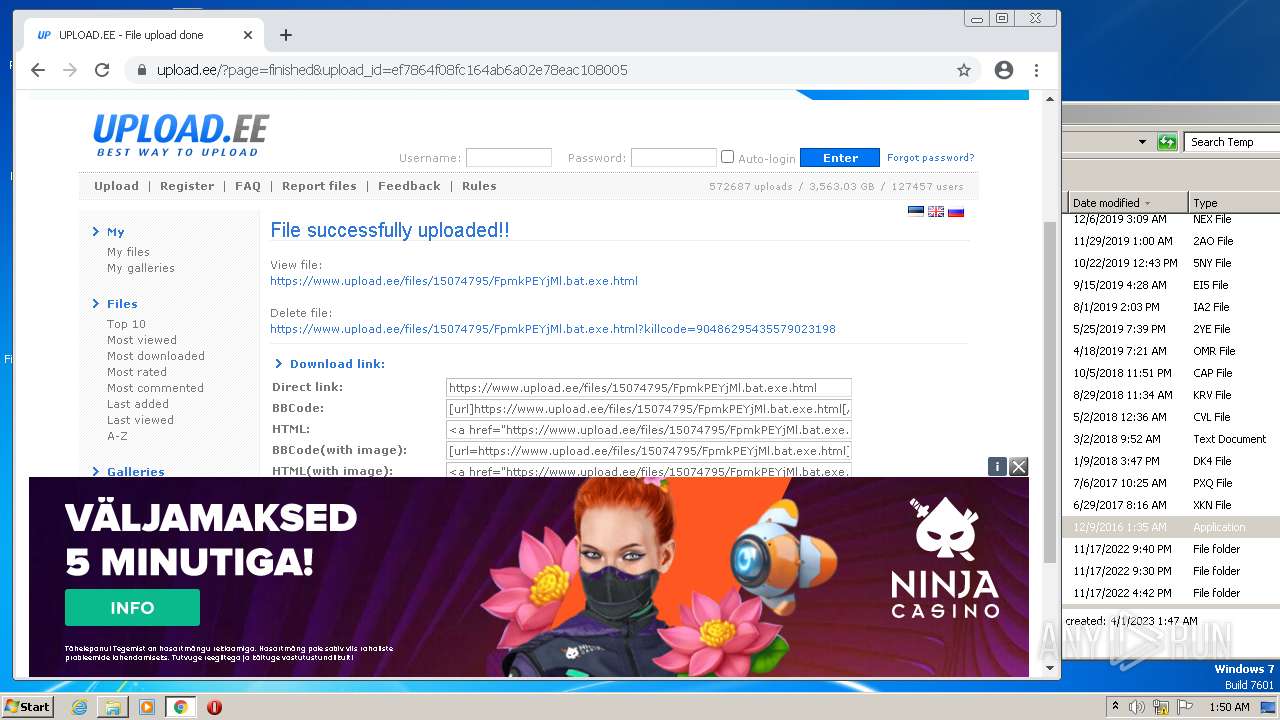
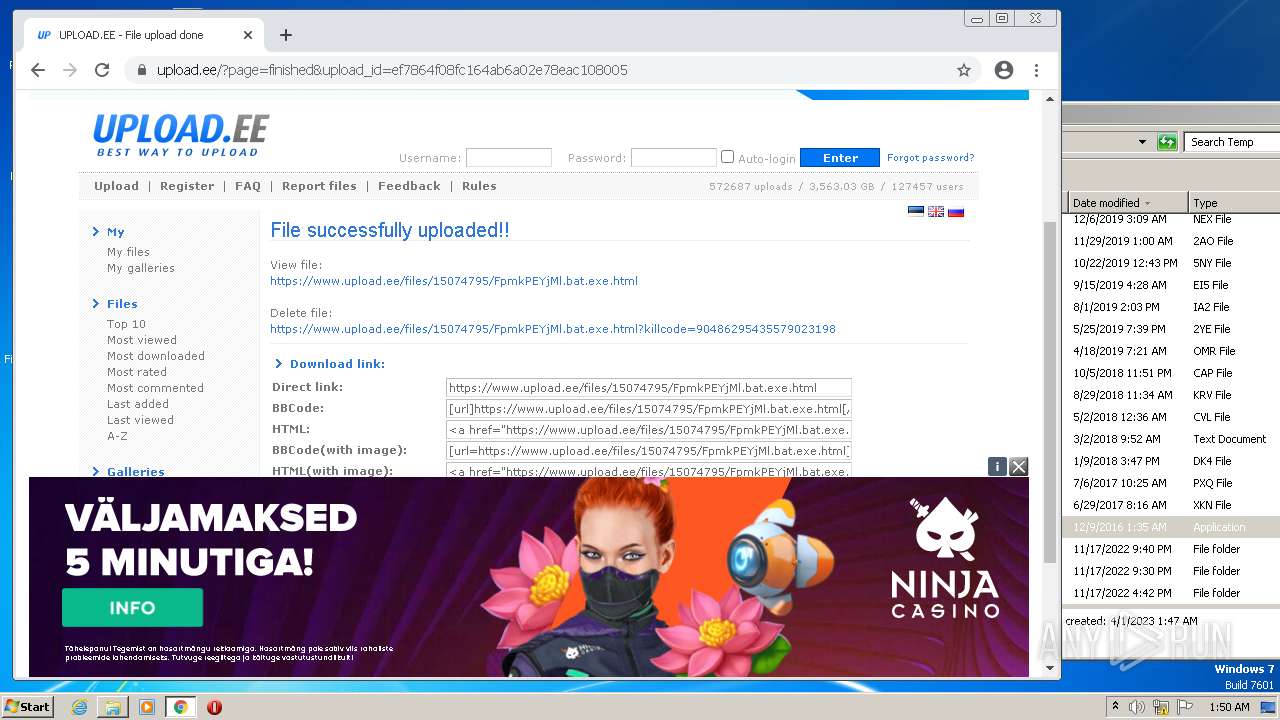
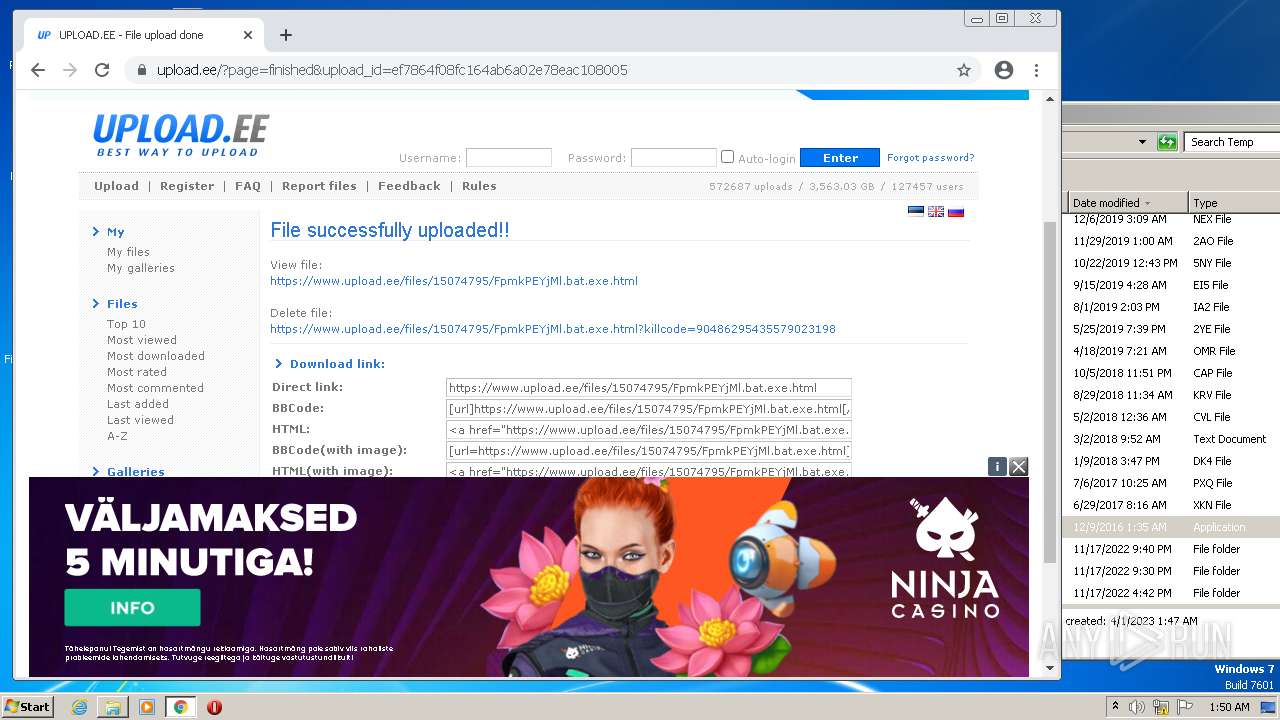
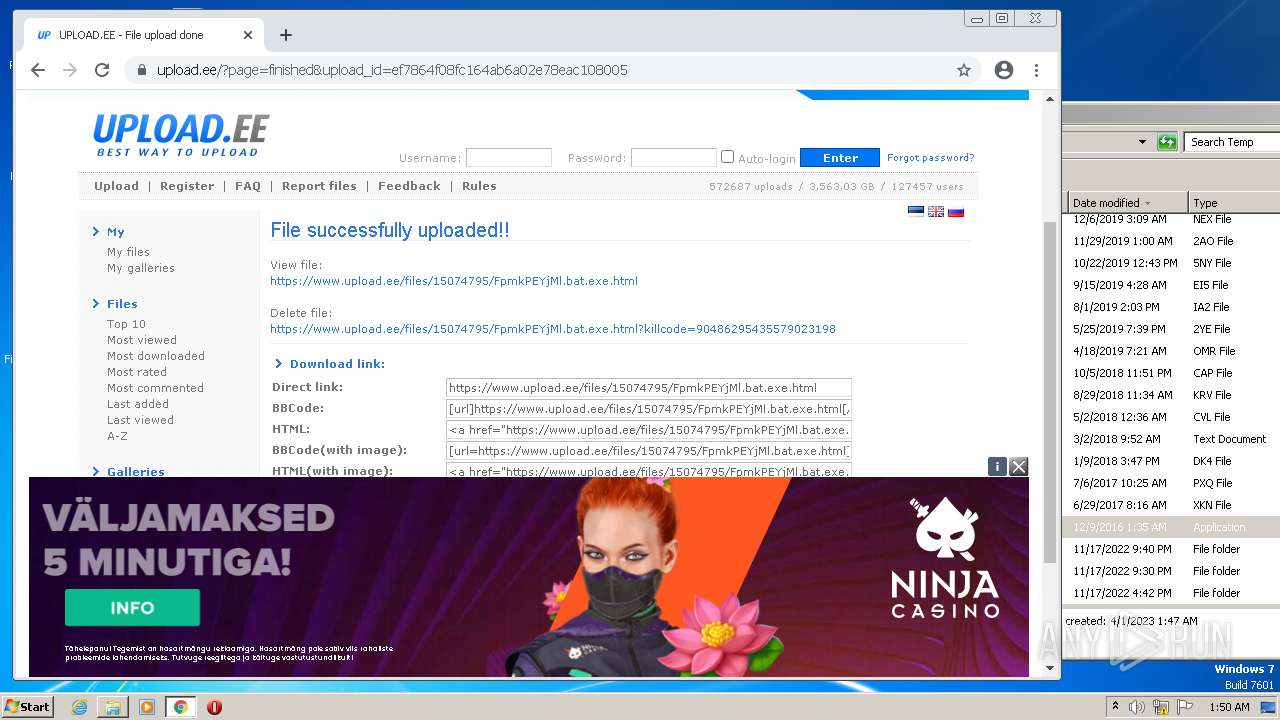
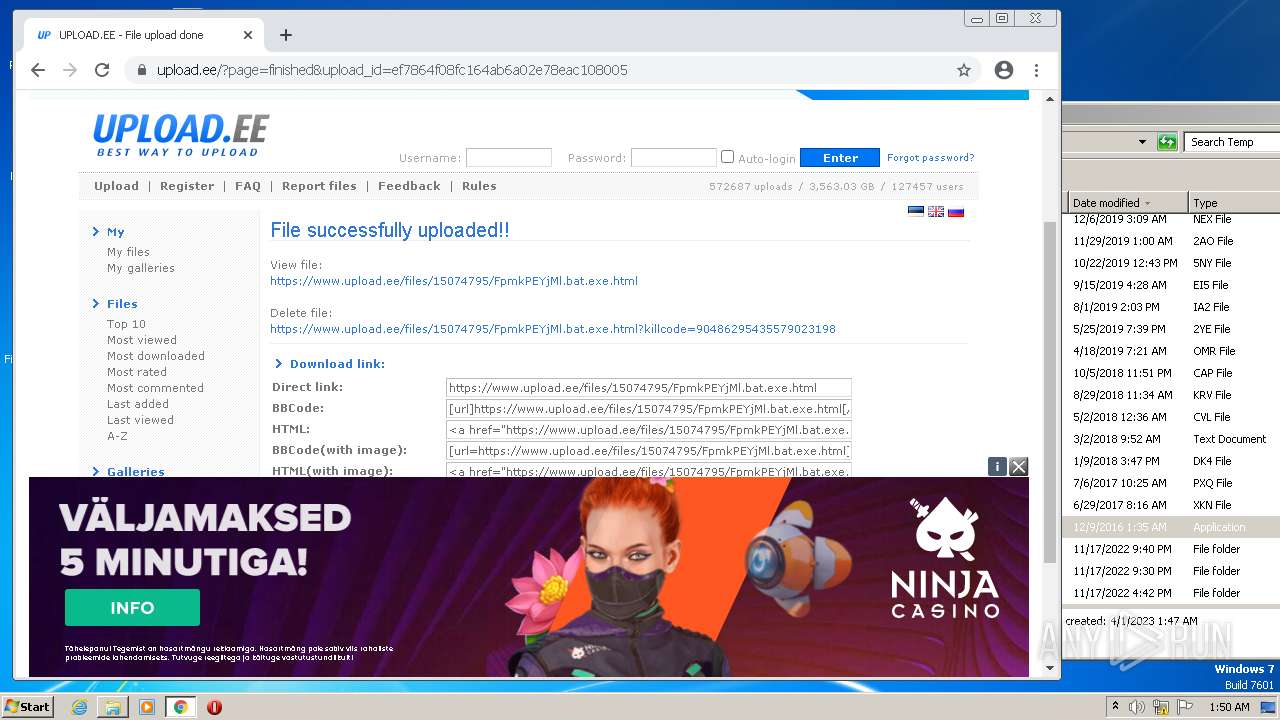
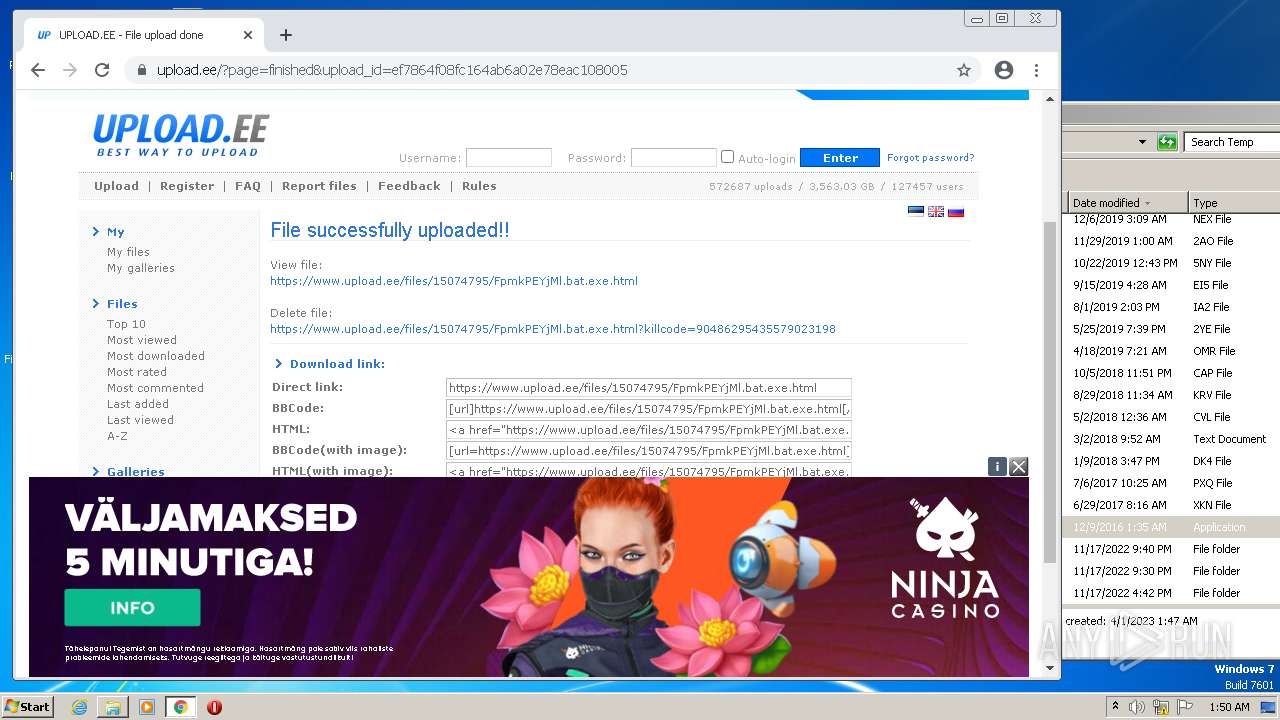
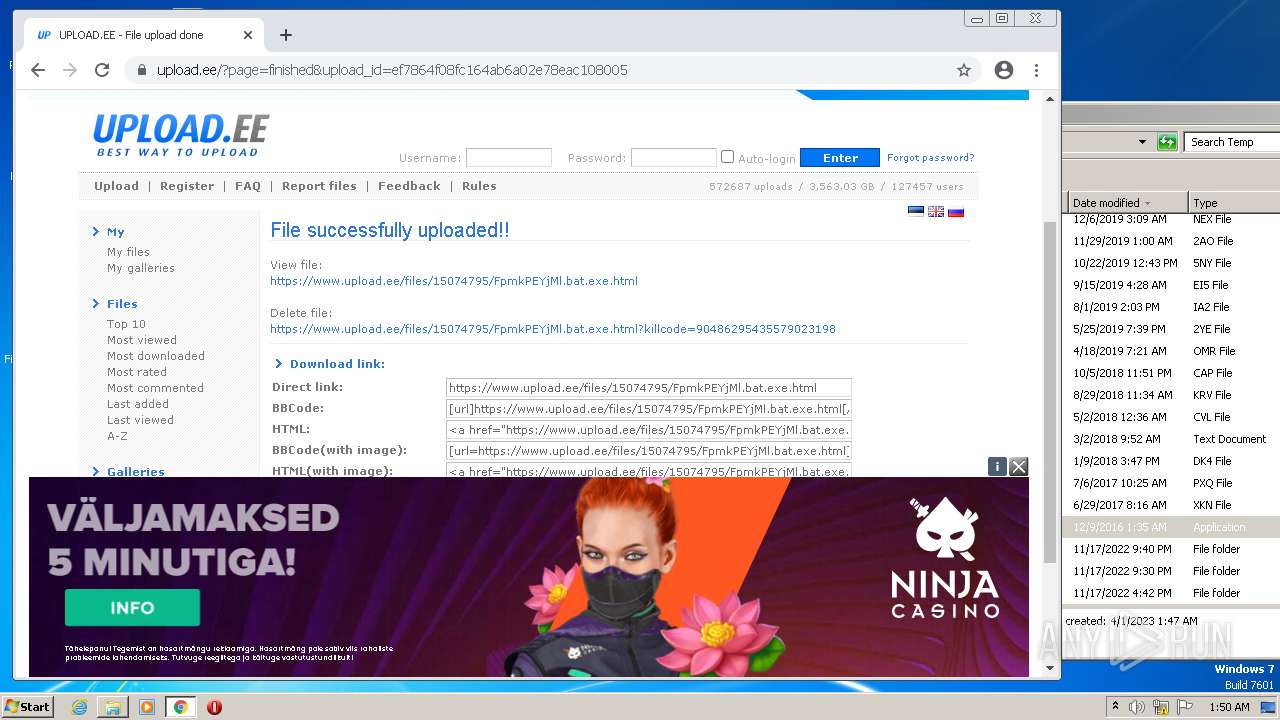
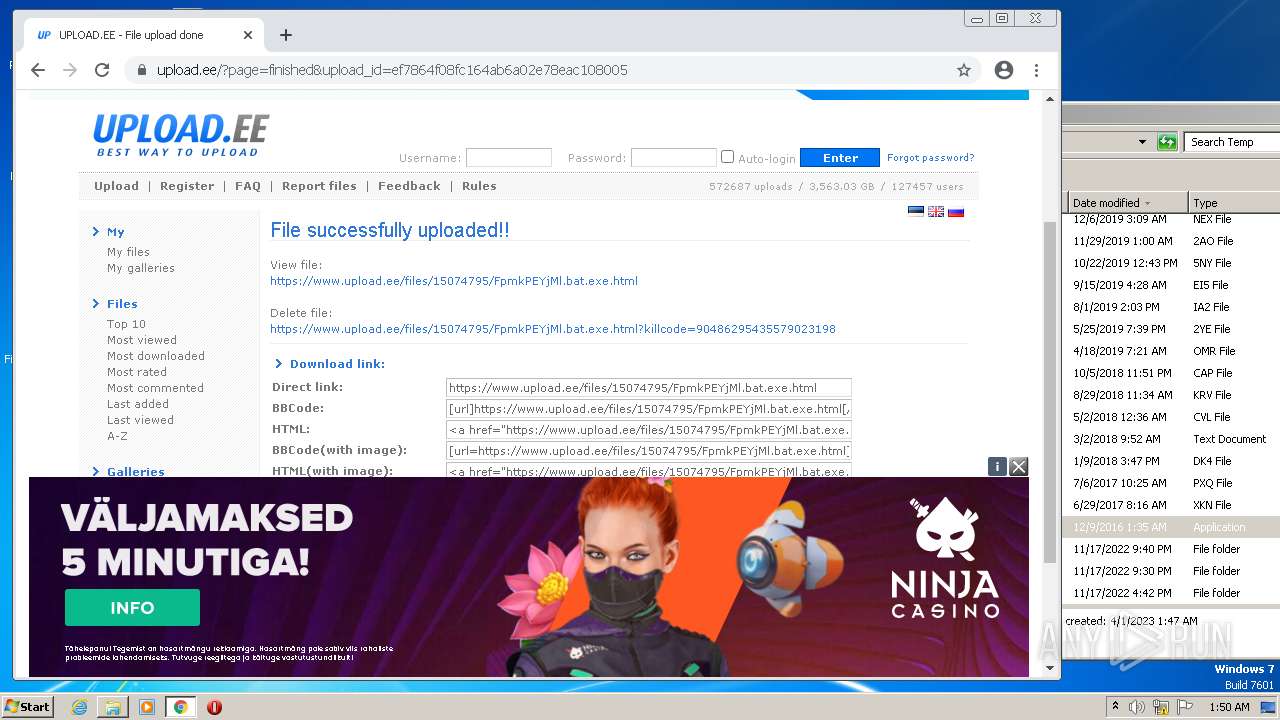
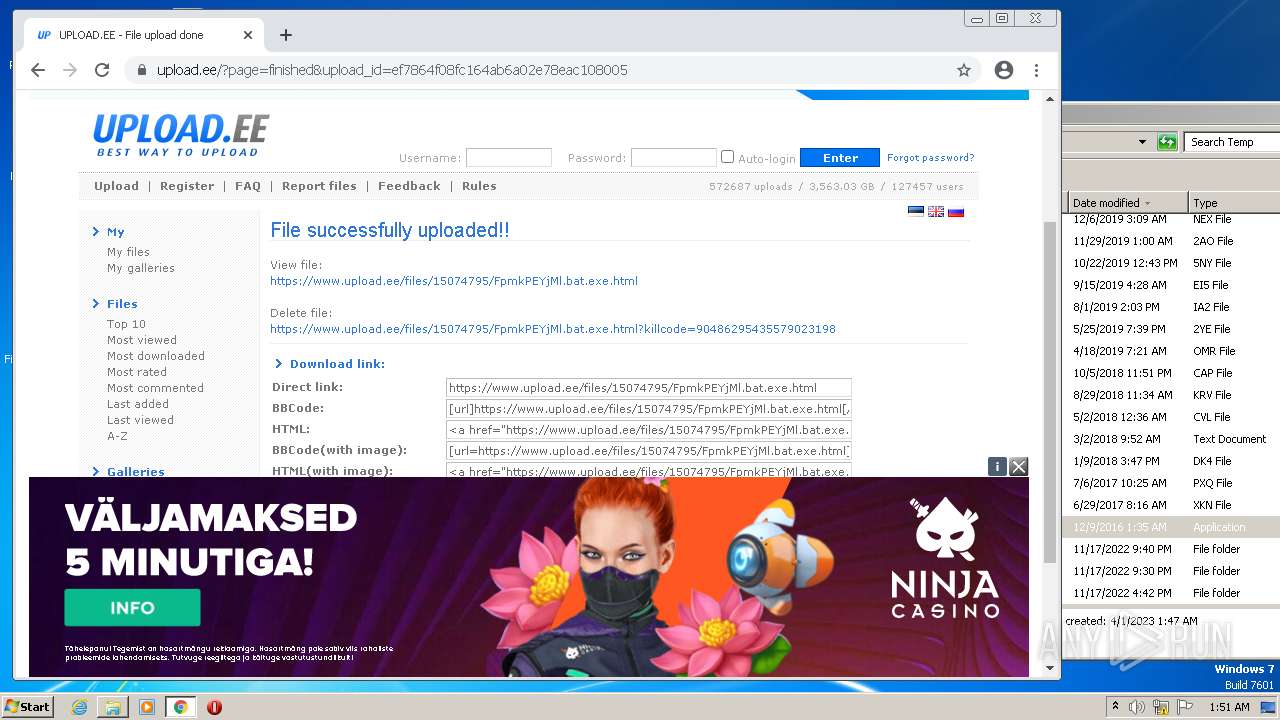
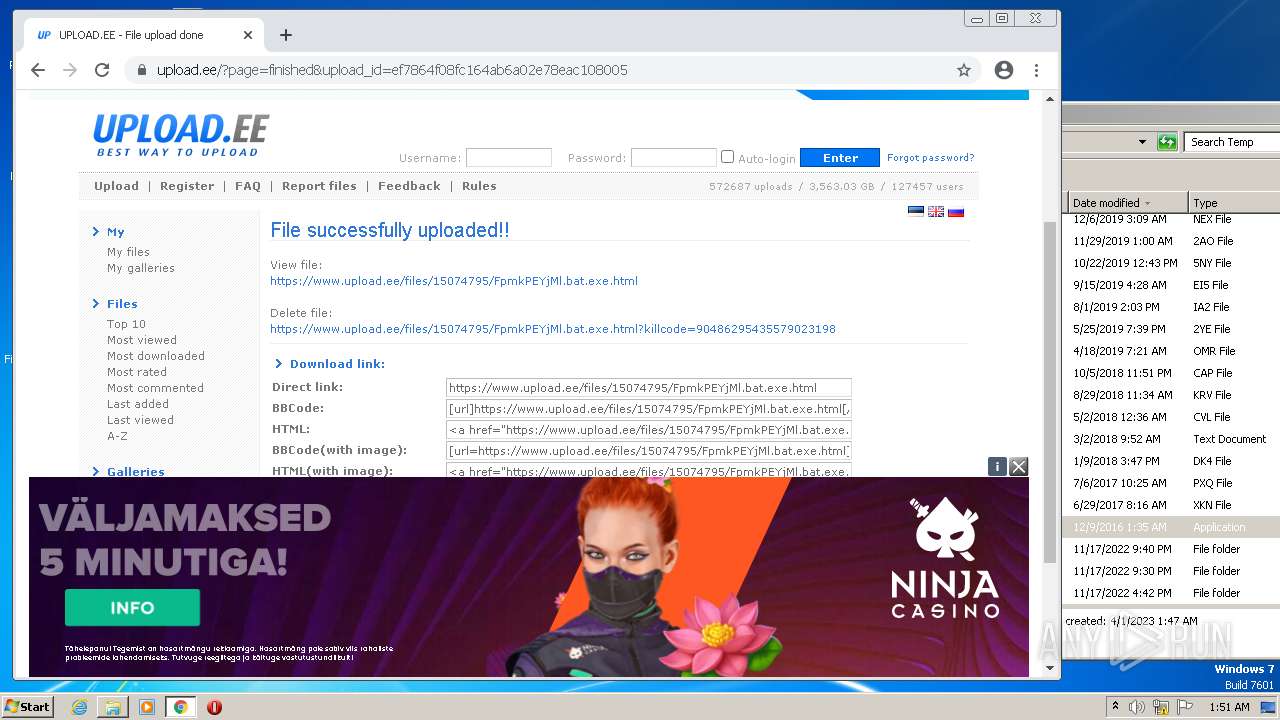
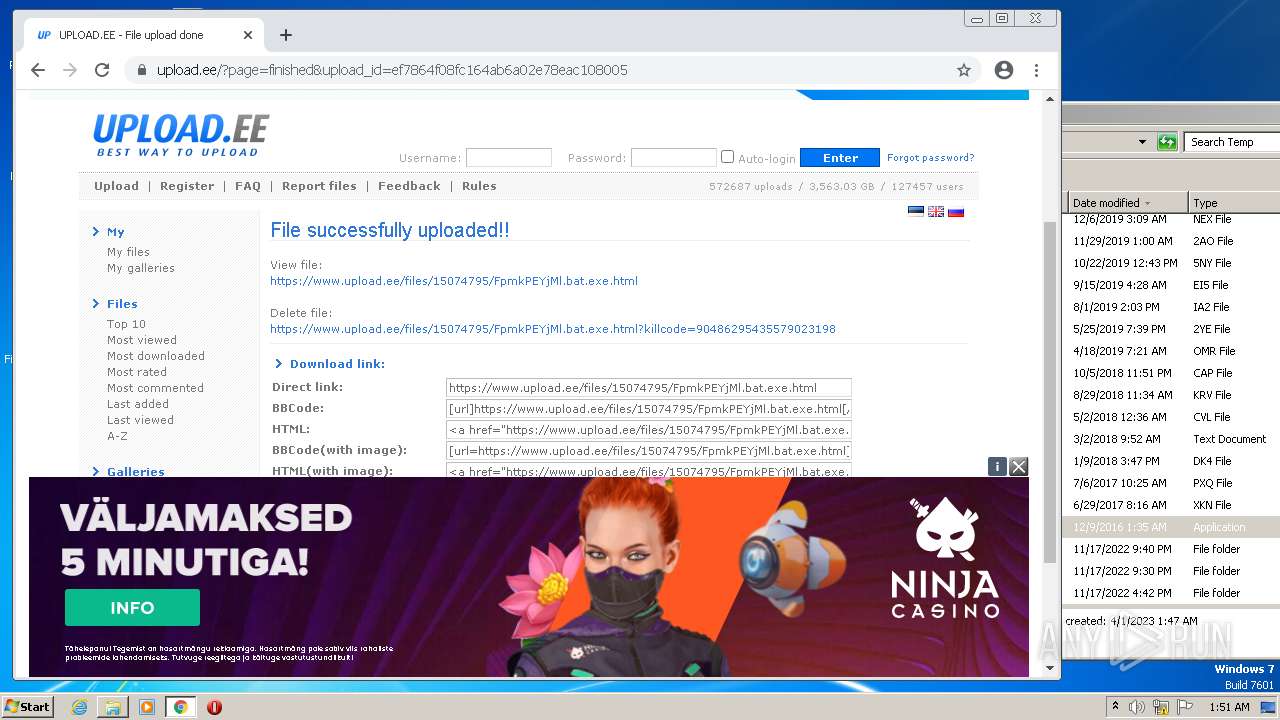
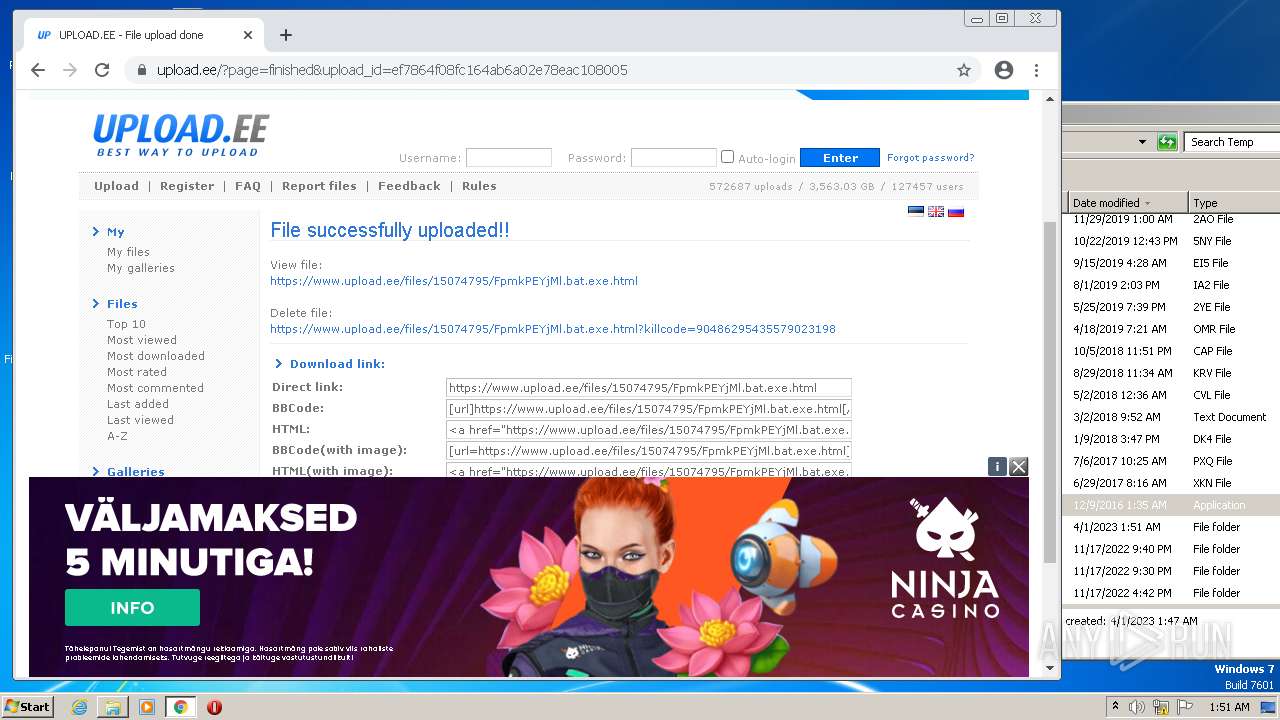
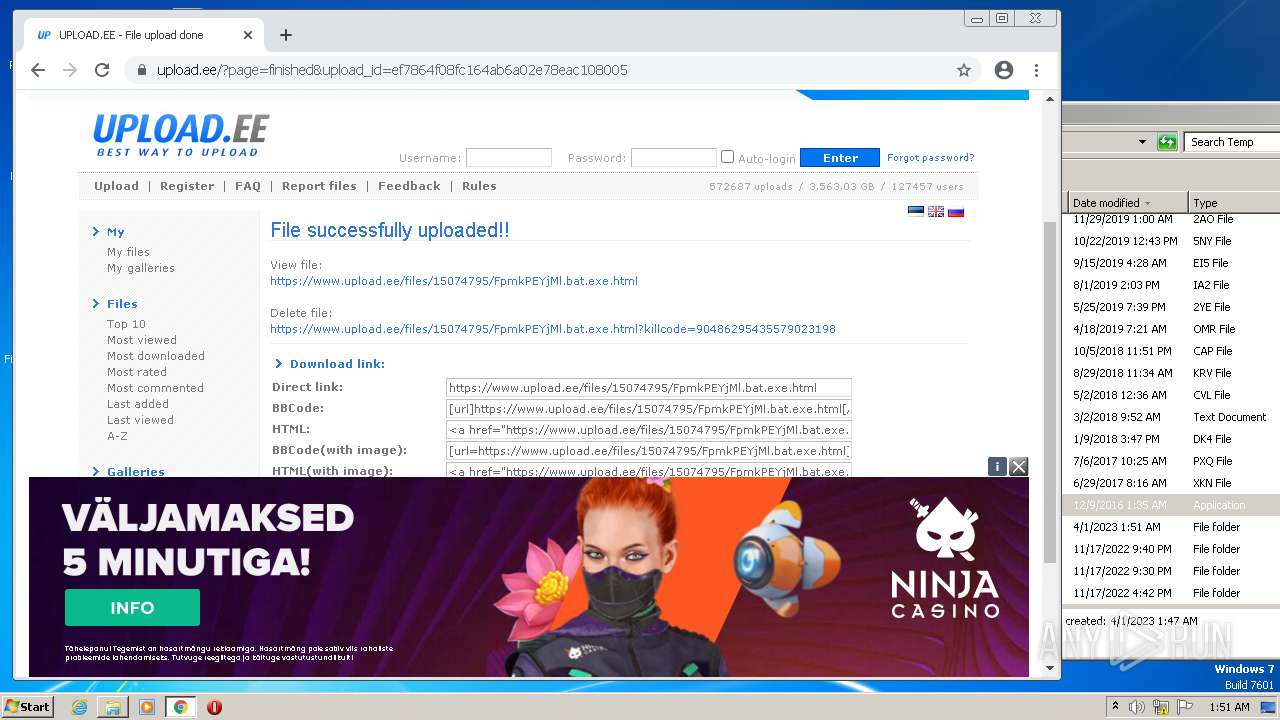
| File name: | FpmkPEYjMl.bat |
| Full analysis: | https://app.any.run/tasks/91064ac0-cc35-4f37-bbf6-078f236bcac3 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 00:47:14 |
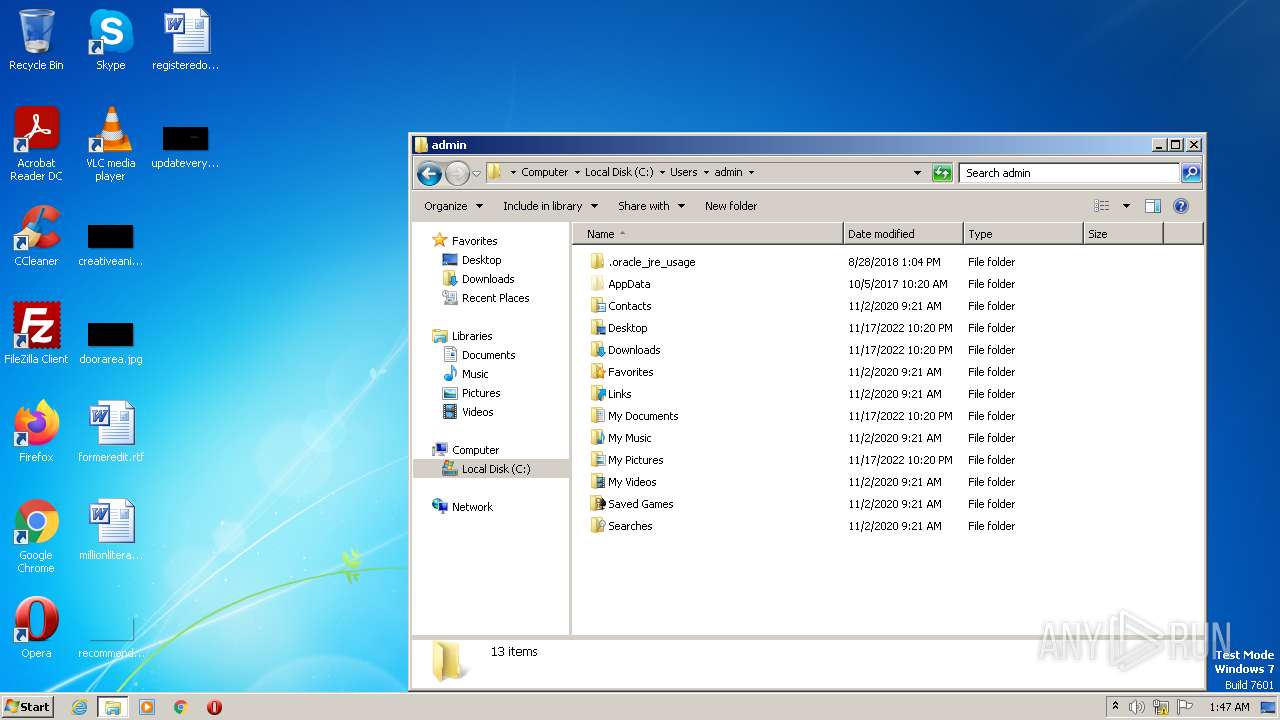
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | D3FFEC6D27A5BA1335569FC9ED788055 |
| SHA1: | 61B981A4A6FAB441DCA82BFCEB6507FB221CA479 |
| SHA256: | 2810B0060FA7F2A125C713DCD8960DB4B5626C962AD4F05DBD5E2D38206CB64E |
| SSDEEP: | 6144:AIFV1lNrGJR7mcnN9eWXRiLQcJ7kXt/7+n5+fwC:TFzlNqzN9ZIV7k9/nfwC |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 964)
Starts PowerShell from an unusual location
- cmd.exe (PID: 2672)
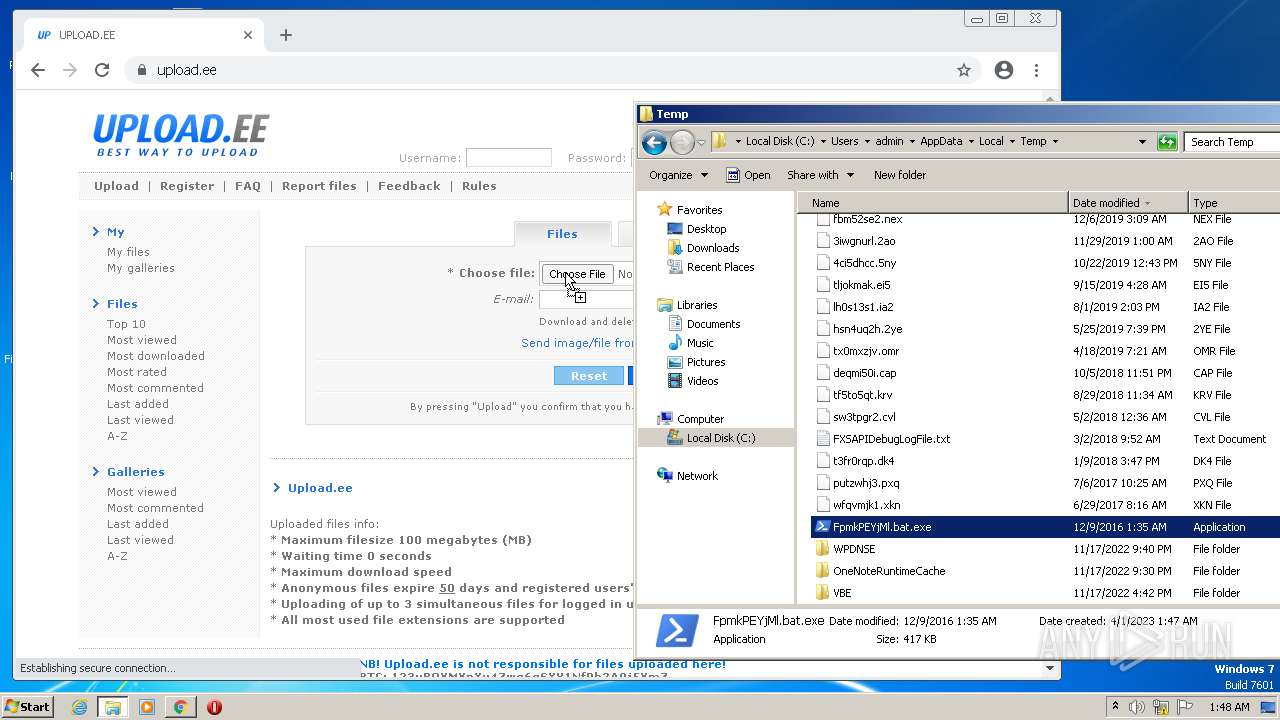
Application was dropped or rewritten from another process
- powershell.exe (PID: 964)
- FpmkPEYjMl.bat.exe (PID: 3128)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2672)
Executable content was dropped or overwritten
- cmd.exe (PID: 2672)
Checks Windows Trust Settings
- FpmkPEYjMl.bat.exe (PID: 3128)
Reads security settings of Internet Explorer
- FpmkPEYjMl.bat.exe (PID: 3128)
INFO
The process checks LSA protection
- powershell.exe (PID: 964)
- FpmkPEYjMl.bat.exe (PID: 3128)
- explorer.exe (PID: 3740)
Reads security settings of Internet Explorer
- powershell.exe (PID: 964)
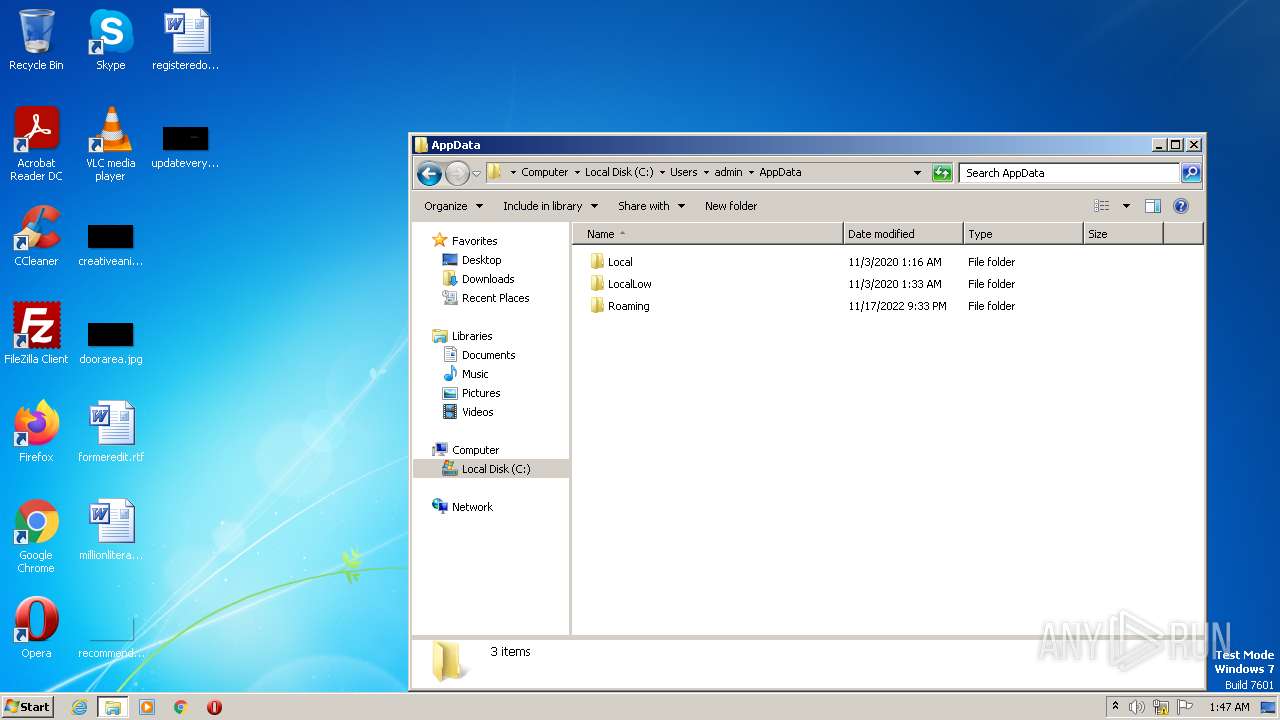
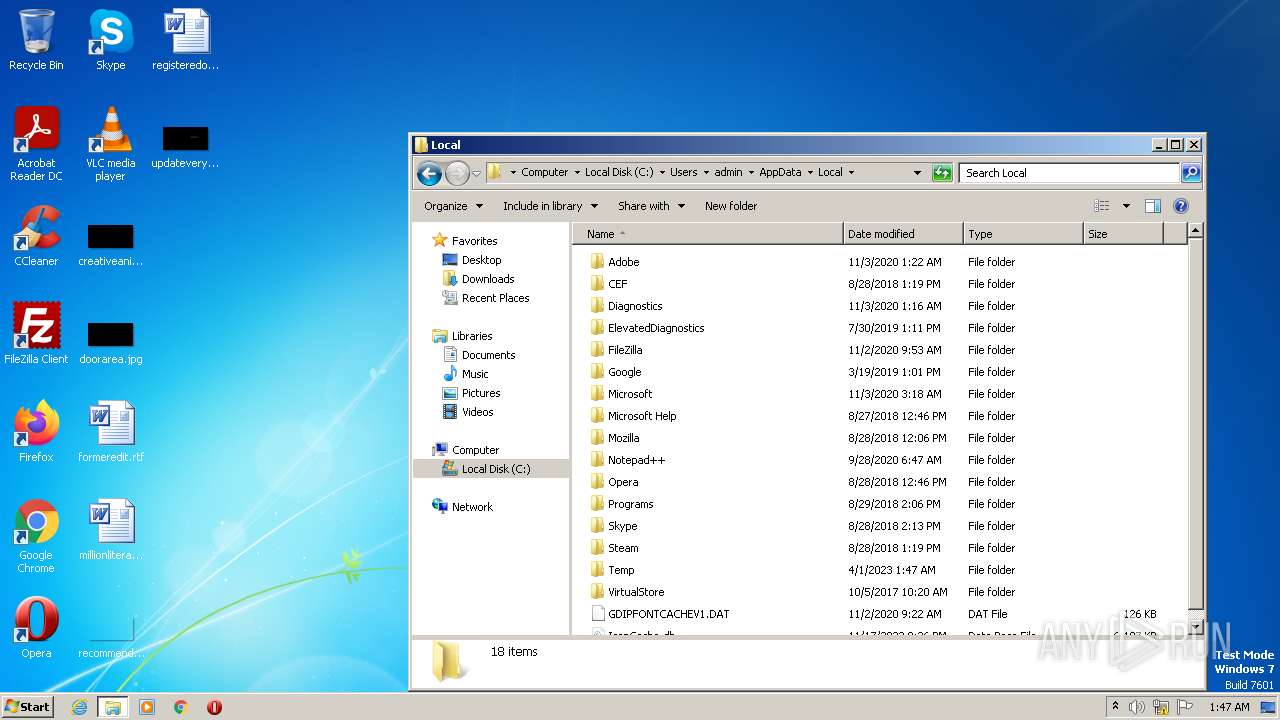
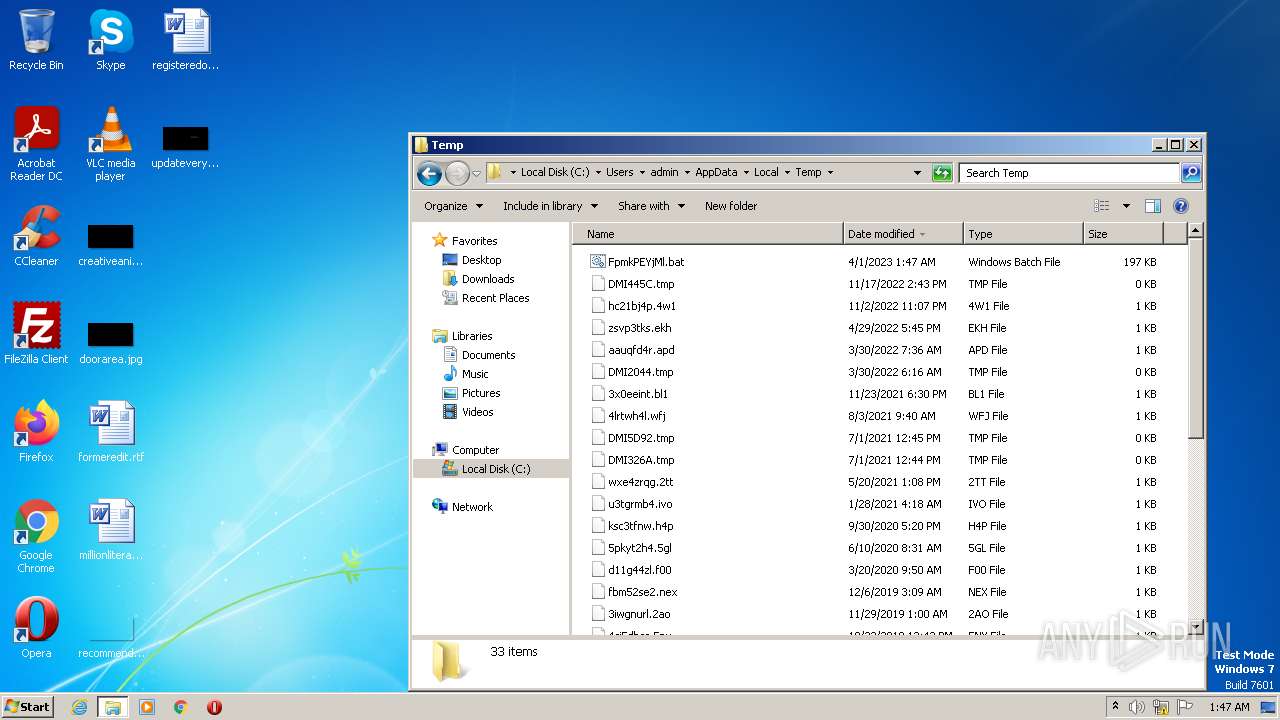
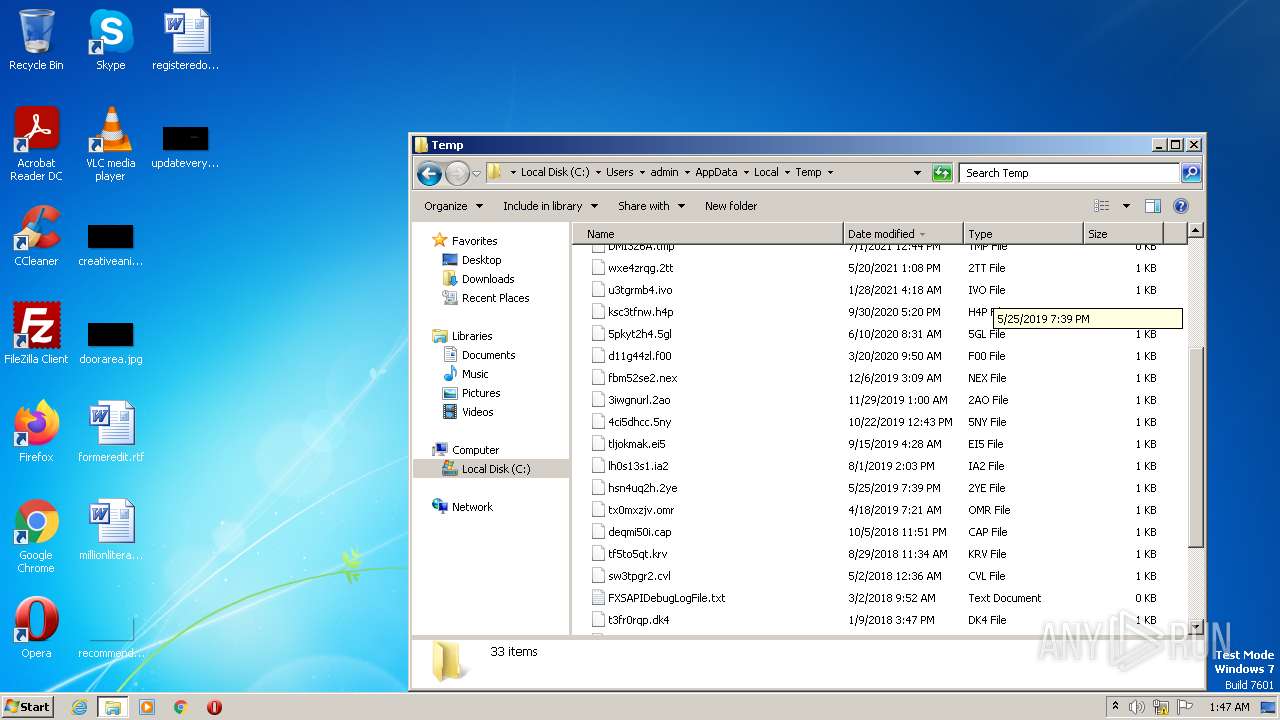
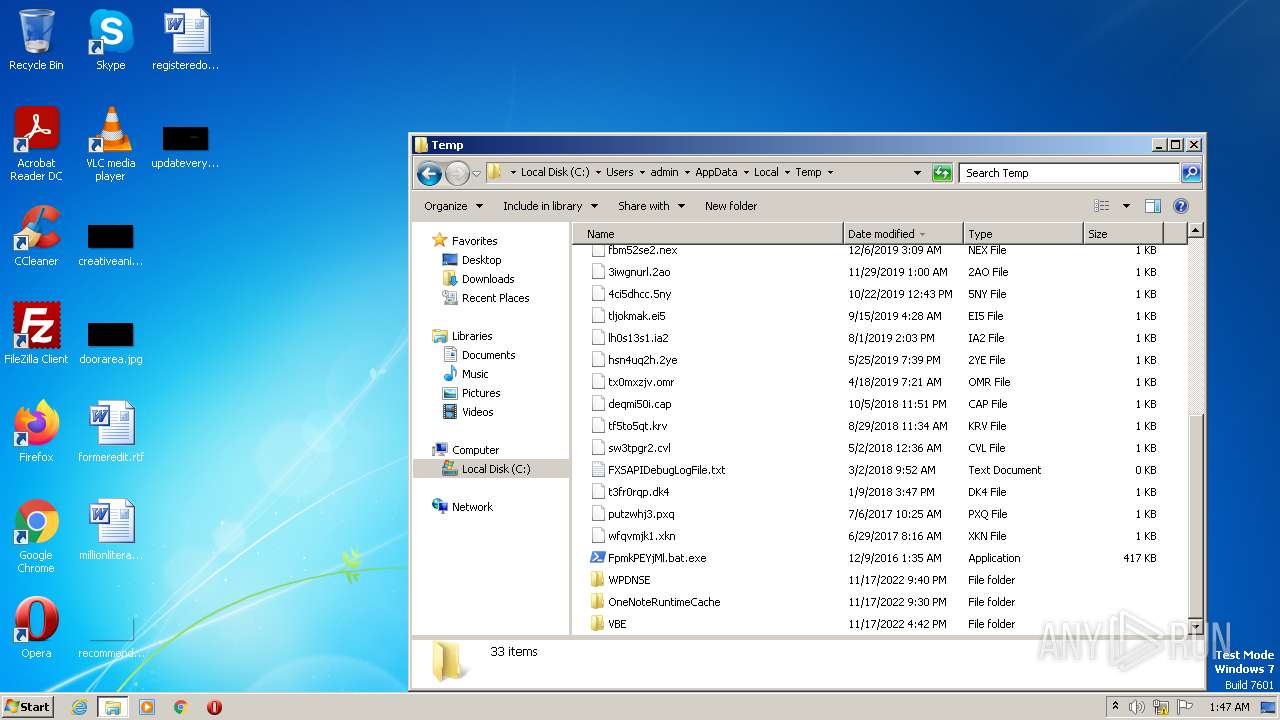
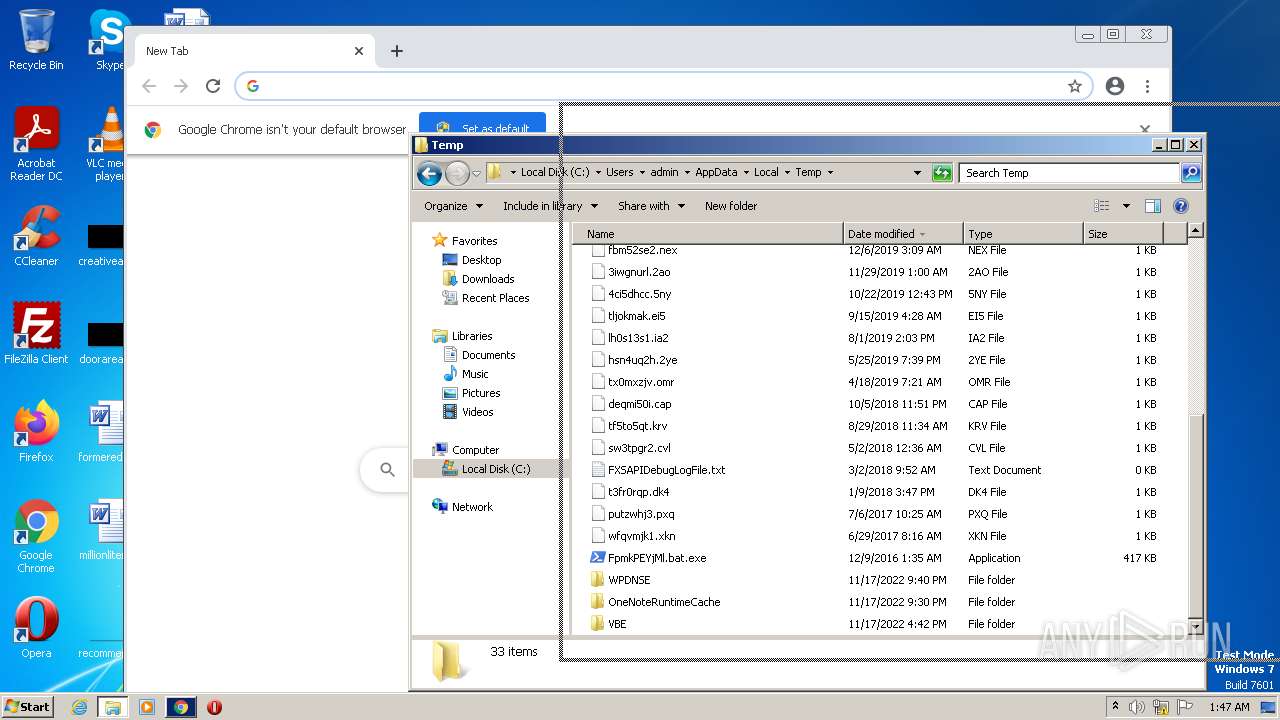
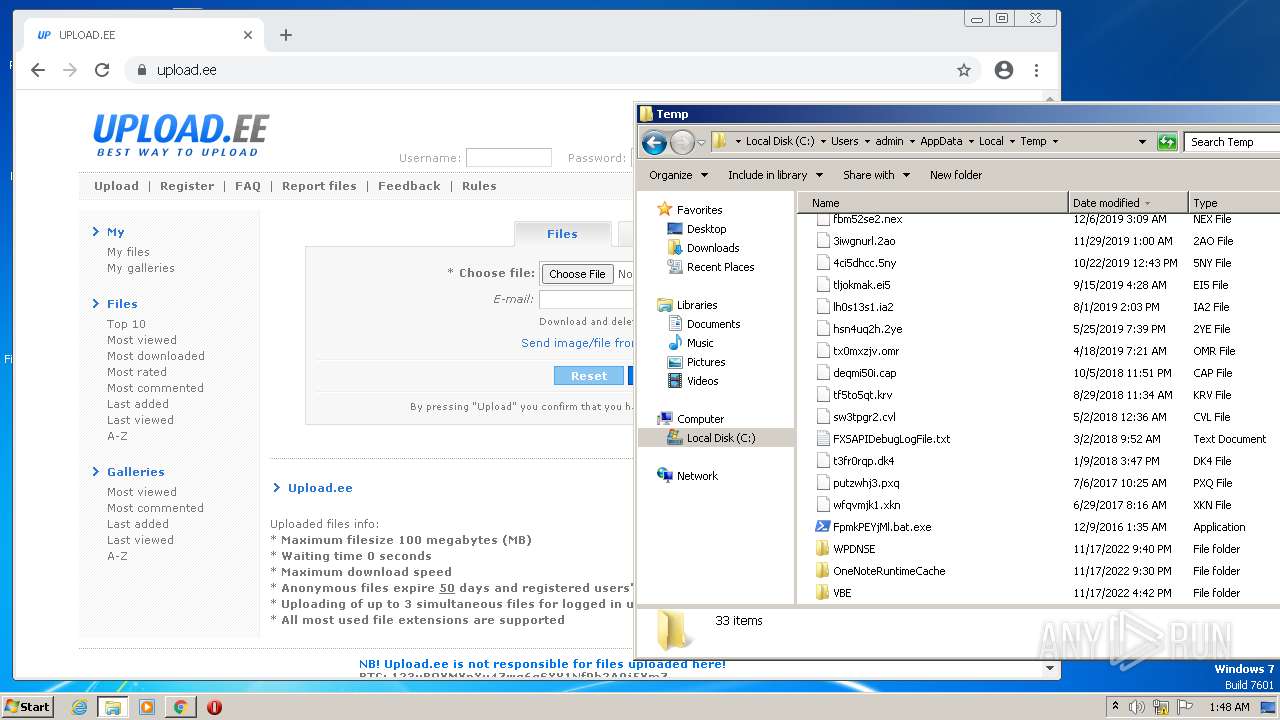
Create files in a temporary directory
- powershell.exe (PID: 964)
- cmd.exe (PID: 2672)
- FpmkPEYjMl.bat.exe (PID: 3128)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 3464)
Checks supported languages
- FpmkPEYjMl.bat.exe (PID: 3128)
Process checks Powershell version
- FpmkPEYjMl.bat.exe (PID: 3128)
Reads the machine GUID from the registry
- FpmkPEYjMl.bat.exe (PID: 3128)
Reads the computer name
- FpmkPEYjMl.bat.exe (PID: 3128)
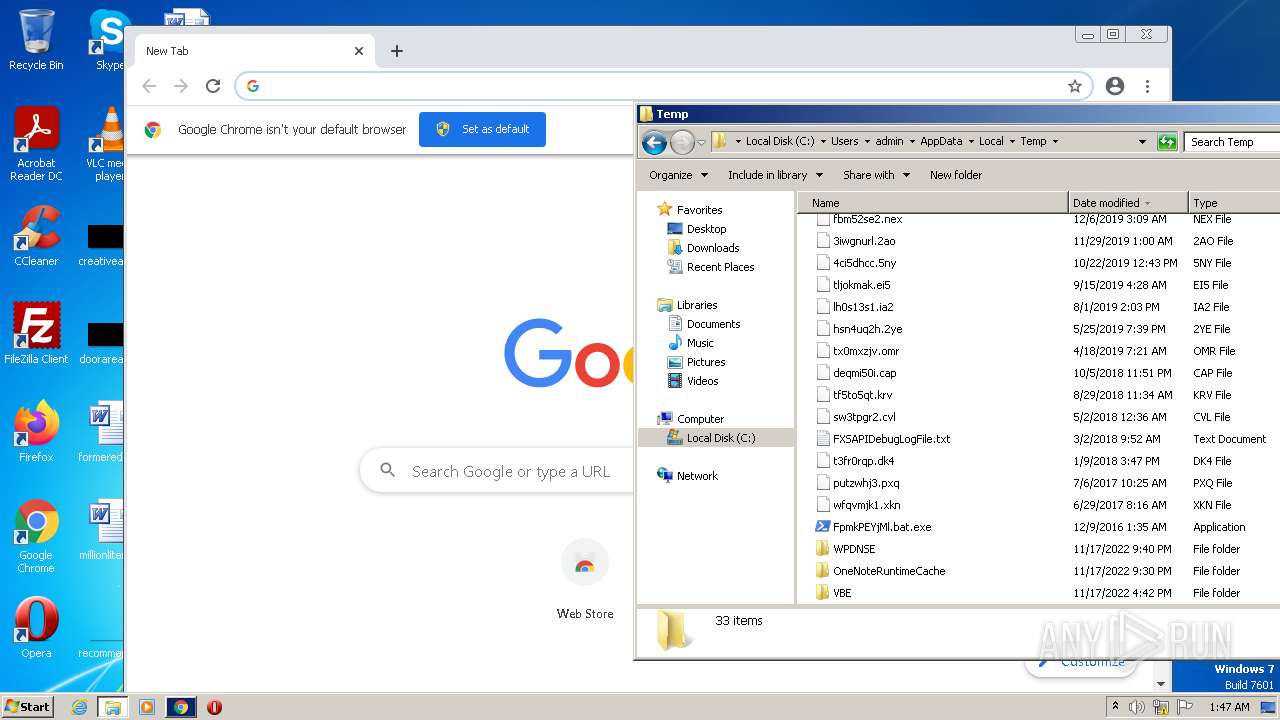
Manual execution by a user
- explorer.exe (PID: 3740)
- chrome.exe (PID: 3464)
Application launched itself
- chrome.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
46
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1004 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | powershell -w hidden -c # | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2808 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
28 998
Read events
28 732
Write events
250
Delete events
16
Modification events
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
2
Suspicious files
330
Text files
320
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64277F28-D88.pma | — | |
MD5:— | SHA256:— | |||
| 964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\obfv2slw.2ej.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 964 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5ufna1b2.xi4.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3128 | FpmkPEYjMl.bat.exe | C:\Users\admin\AppData\Local\Temp\0th0ms2l.o3i.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
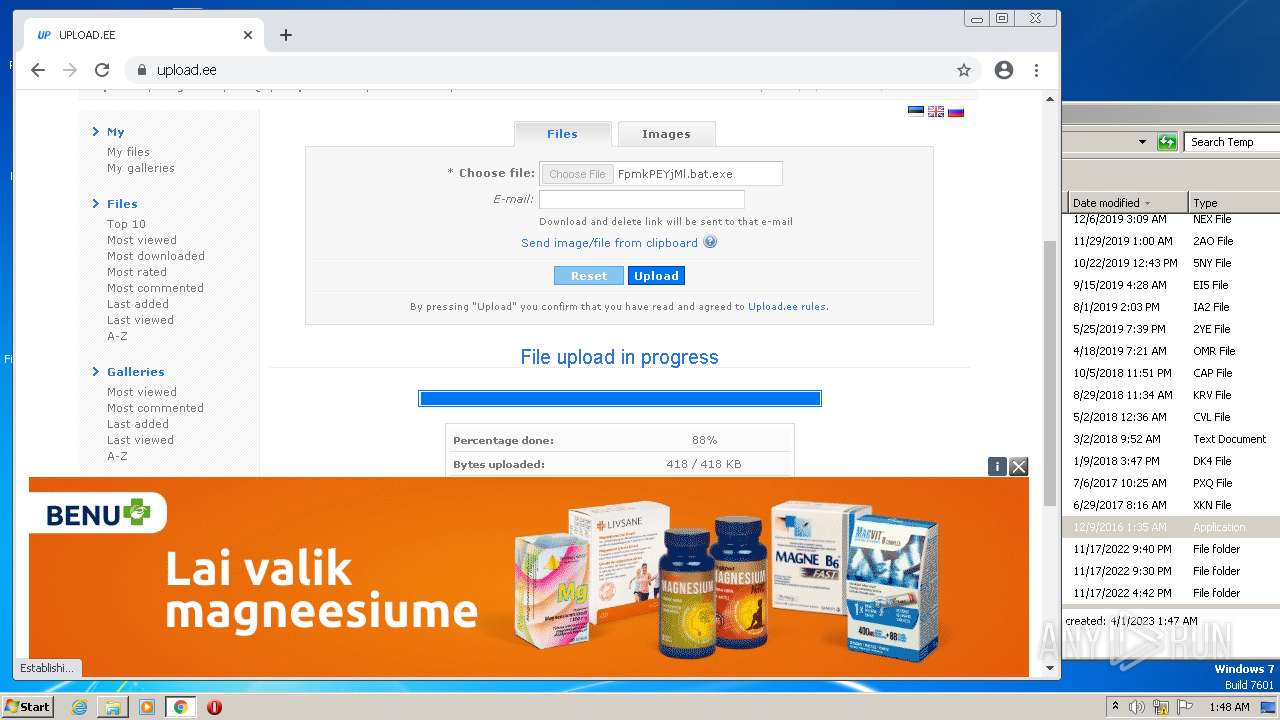
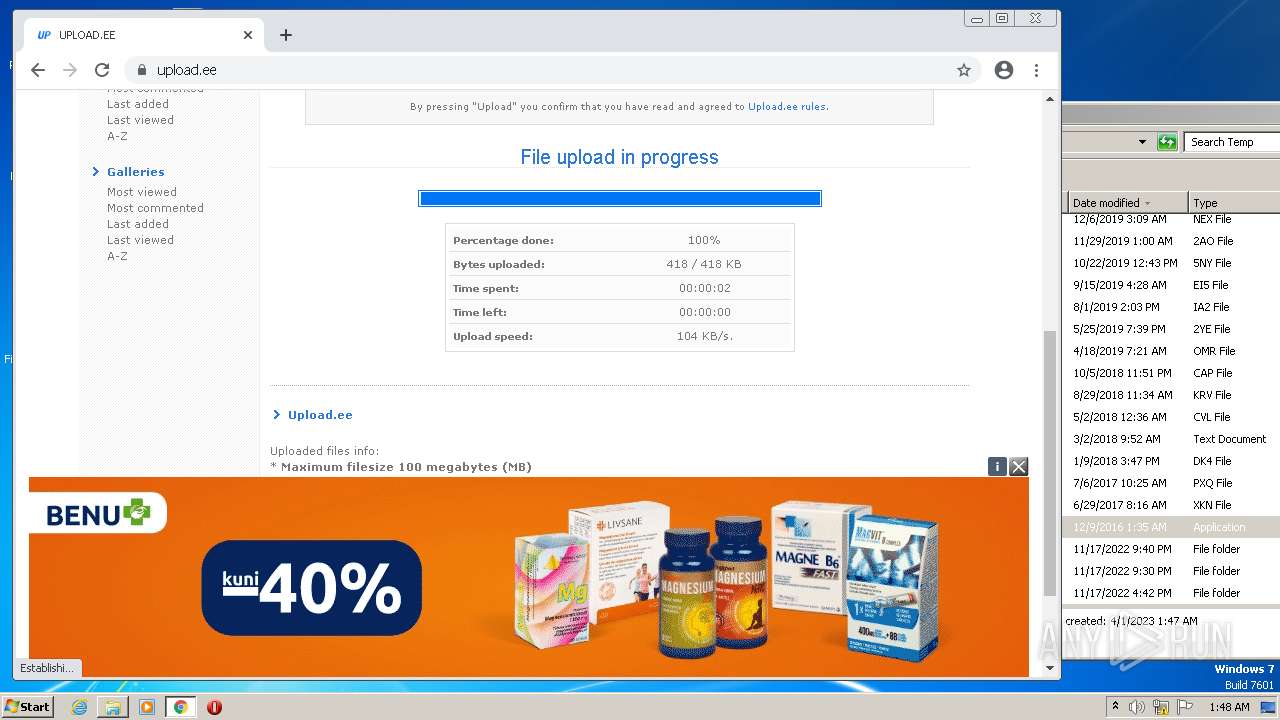
| 2672 | cmd.exe | C:\Users\admin\AppData\Local\Temp\FpmkPEYjMl.bat.exe | executable | |
MD5:EB32C070E658937AA9FA9F3AE629B2B8 | SHA256:70BA57FB0BF2F34B86426D21559F5F6D05C1268193904DE8E959D7B06CE964CE | |||
| 3464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF25340c.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
61
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
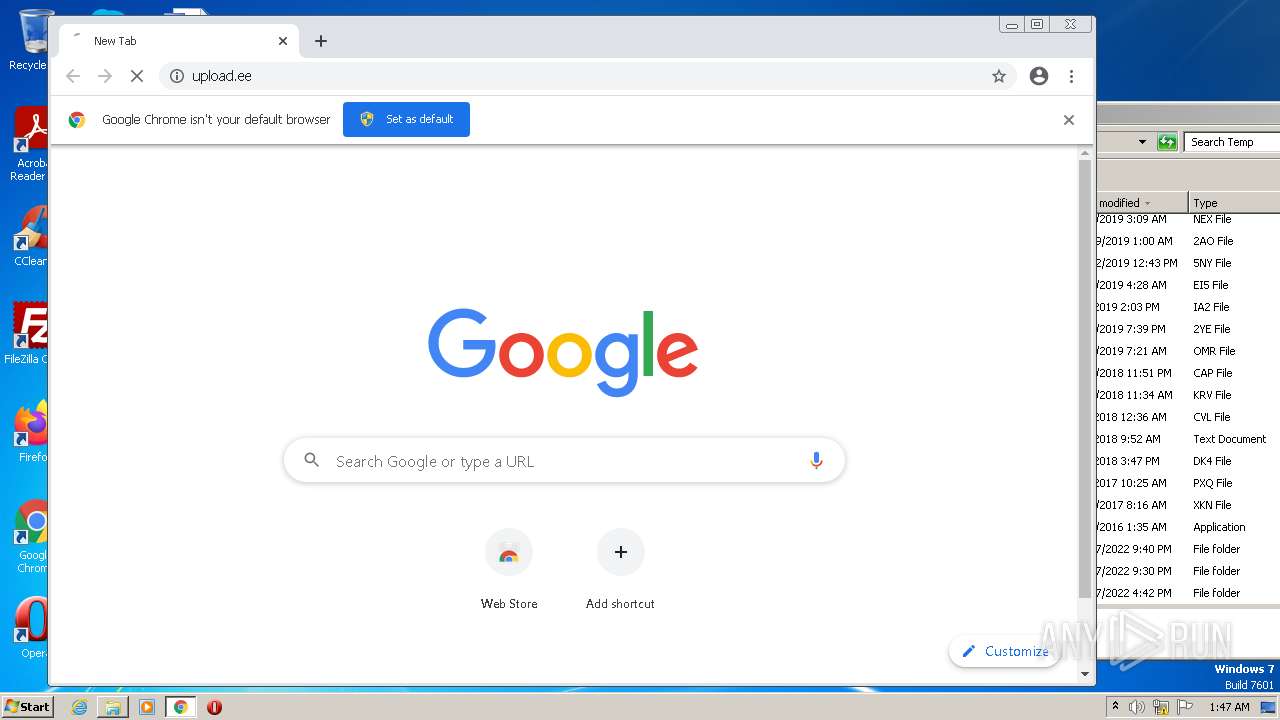
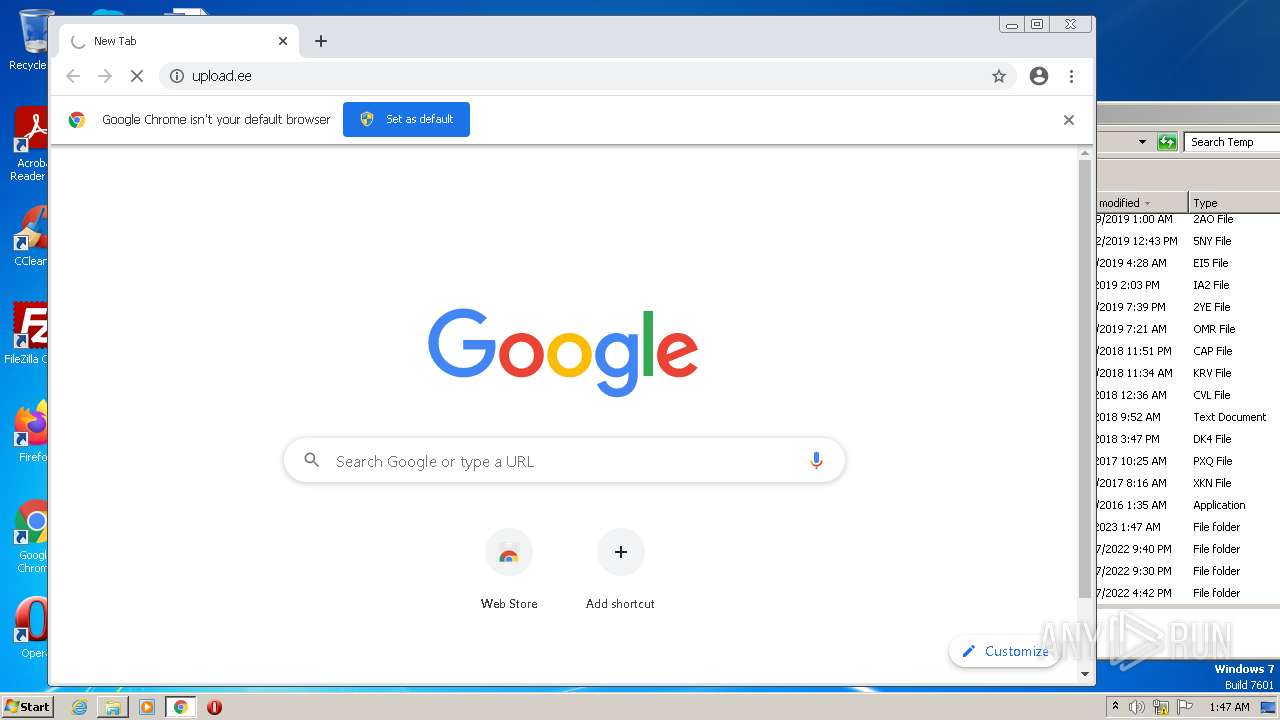
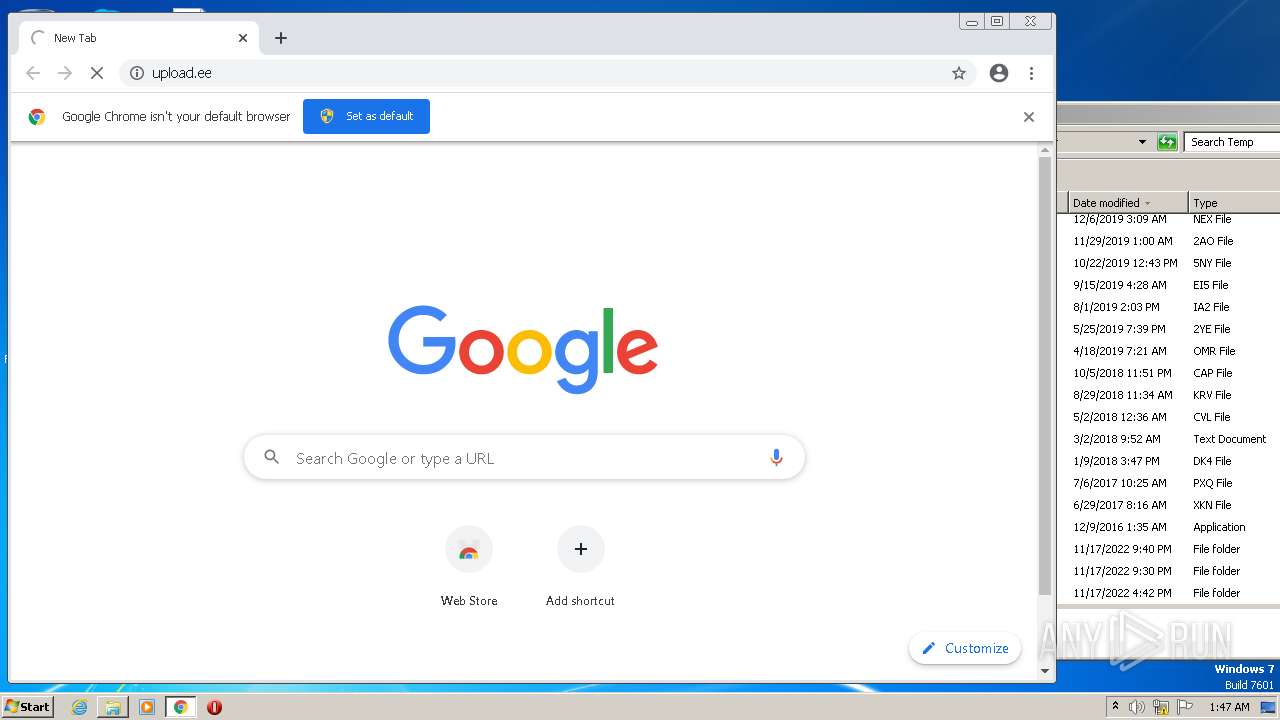
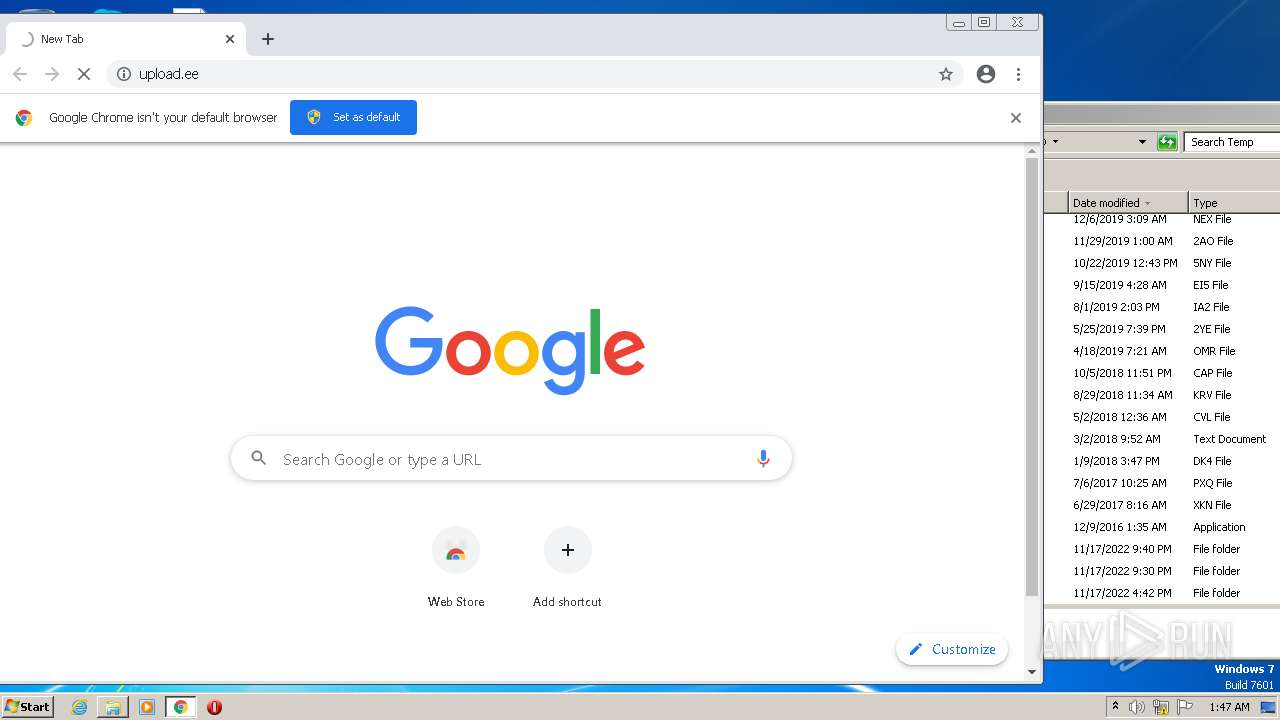
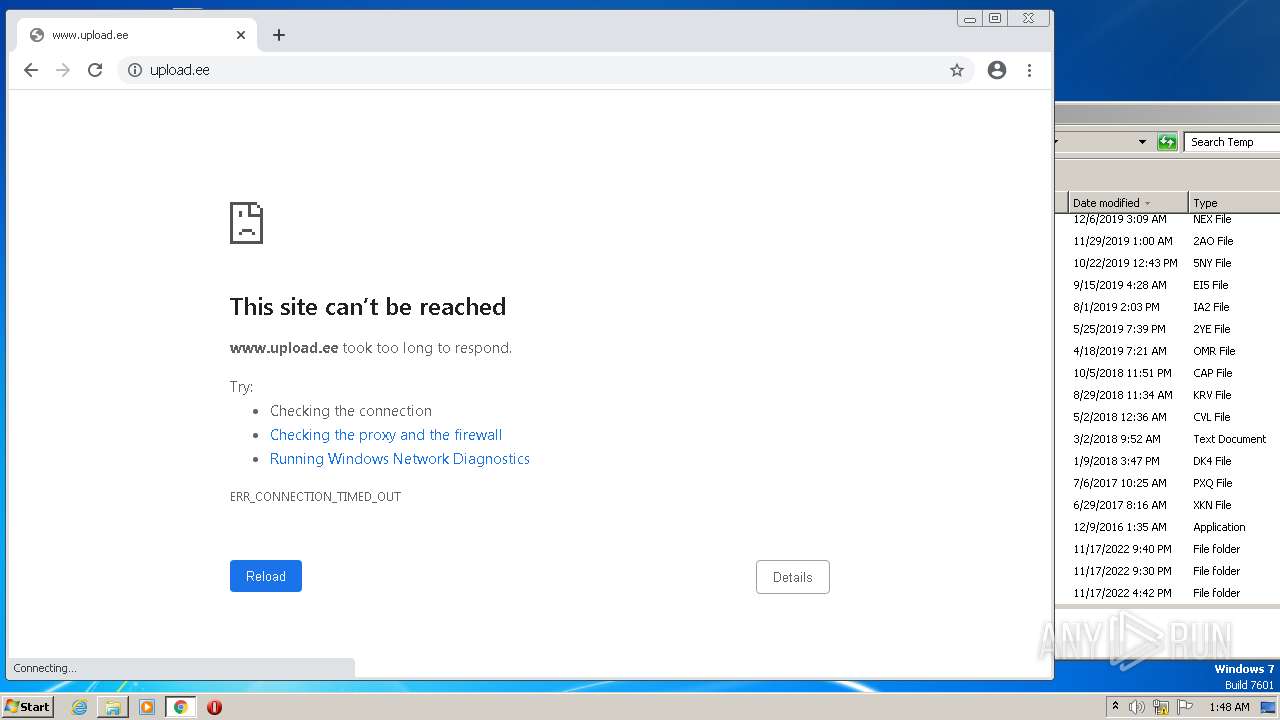
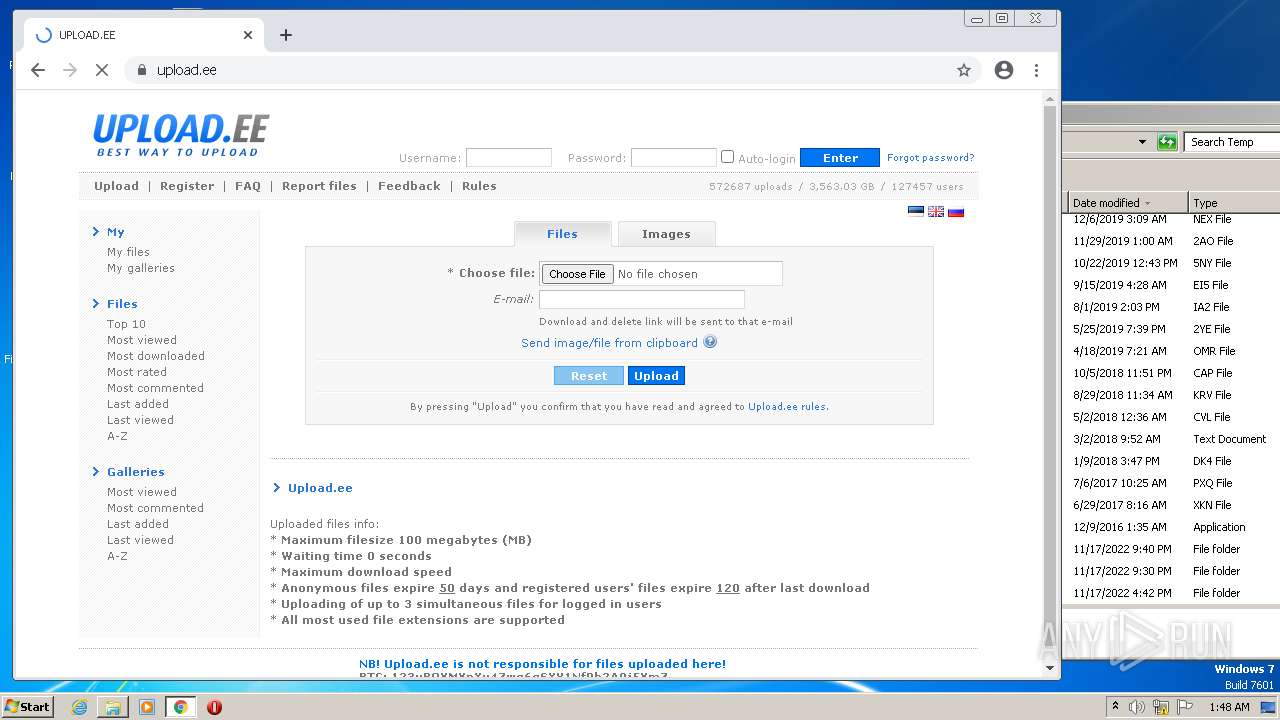
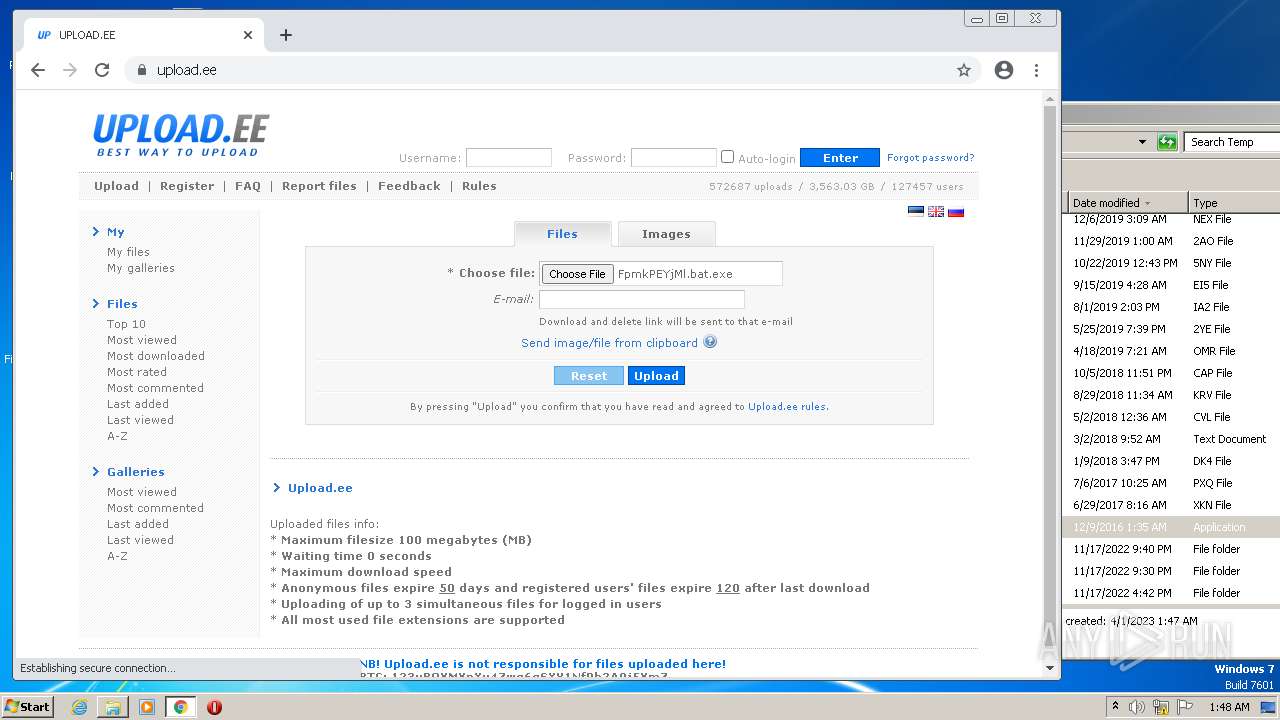
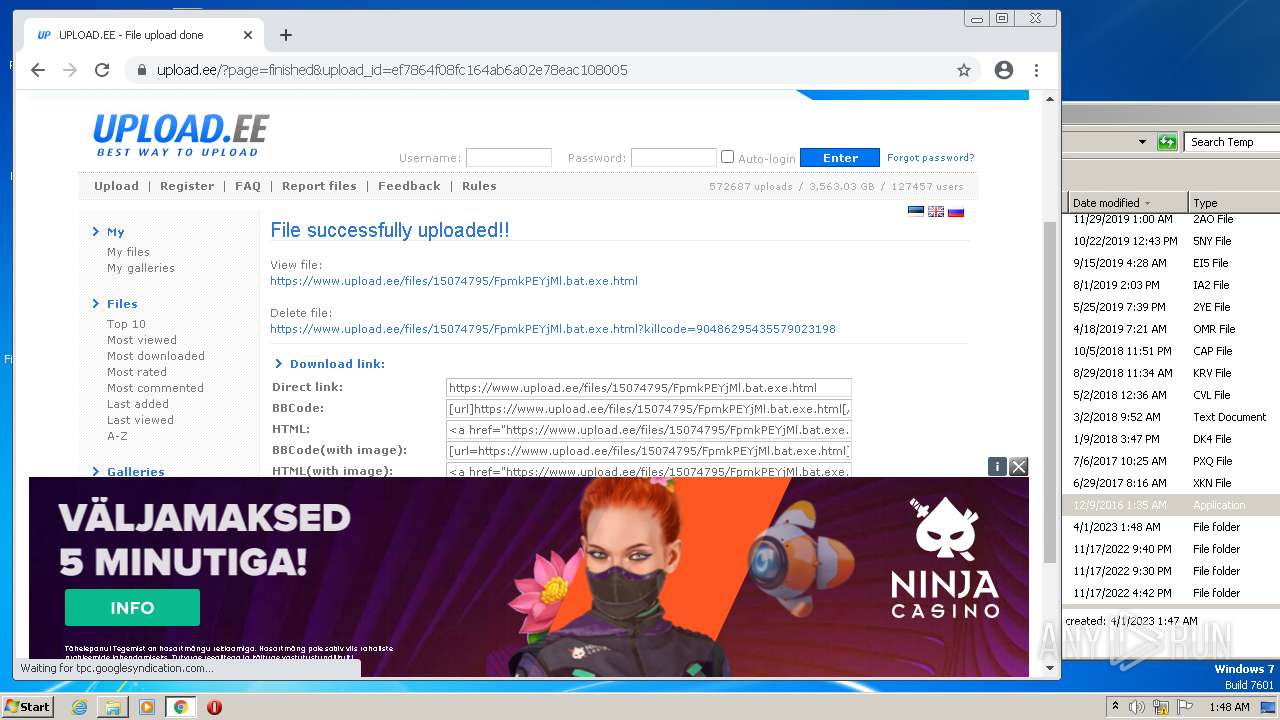
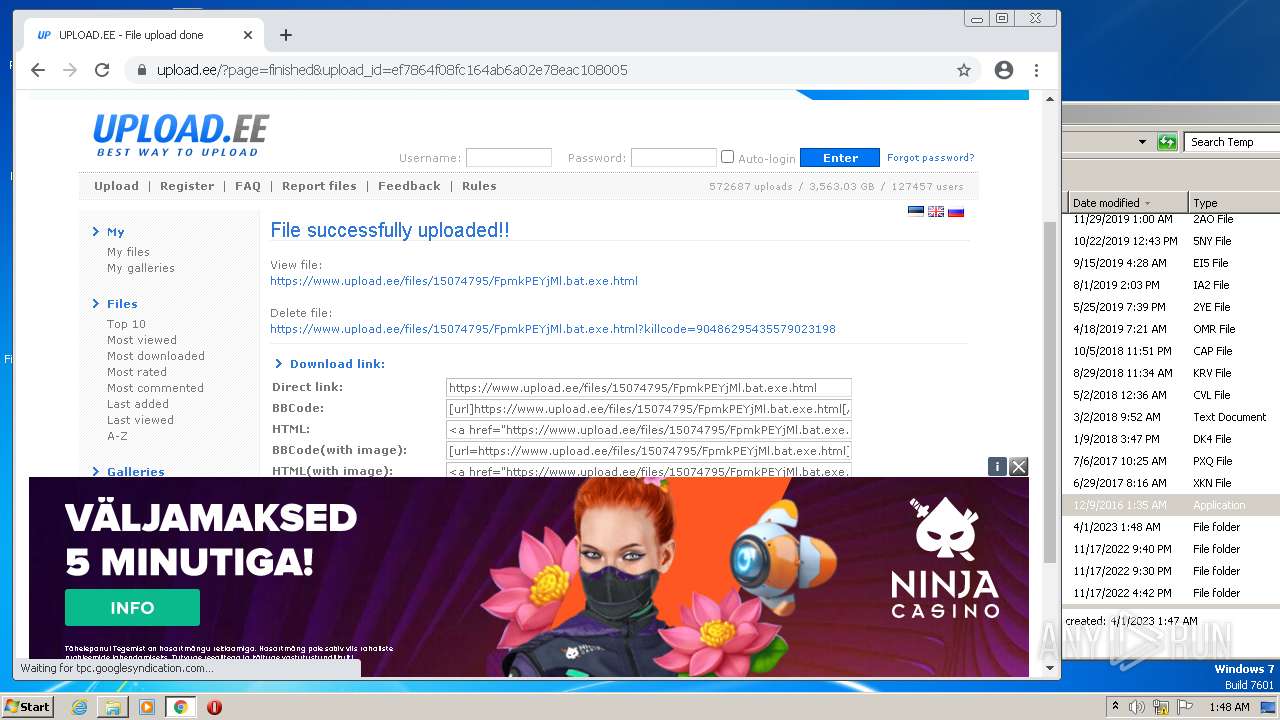
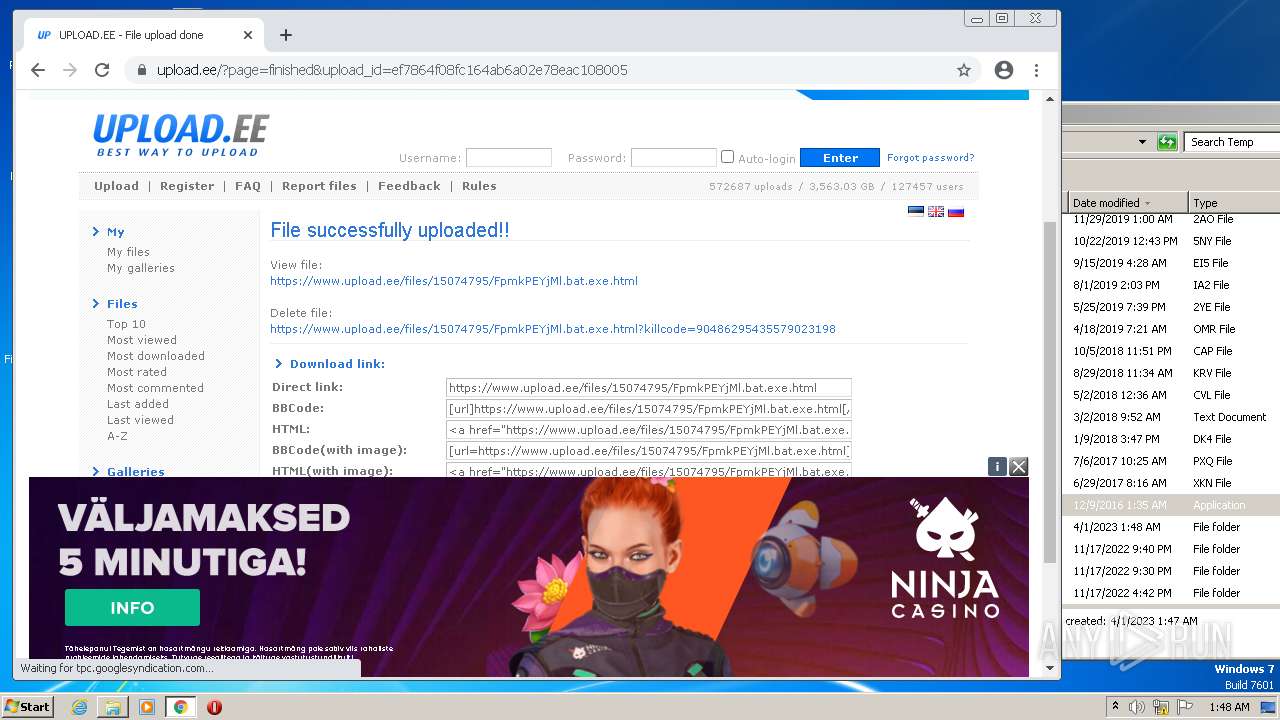
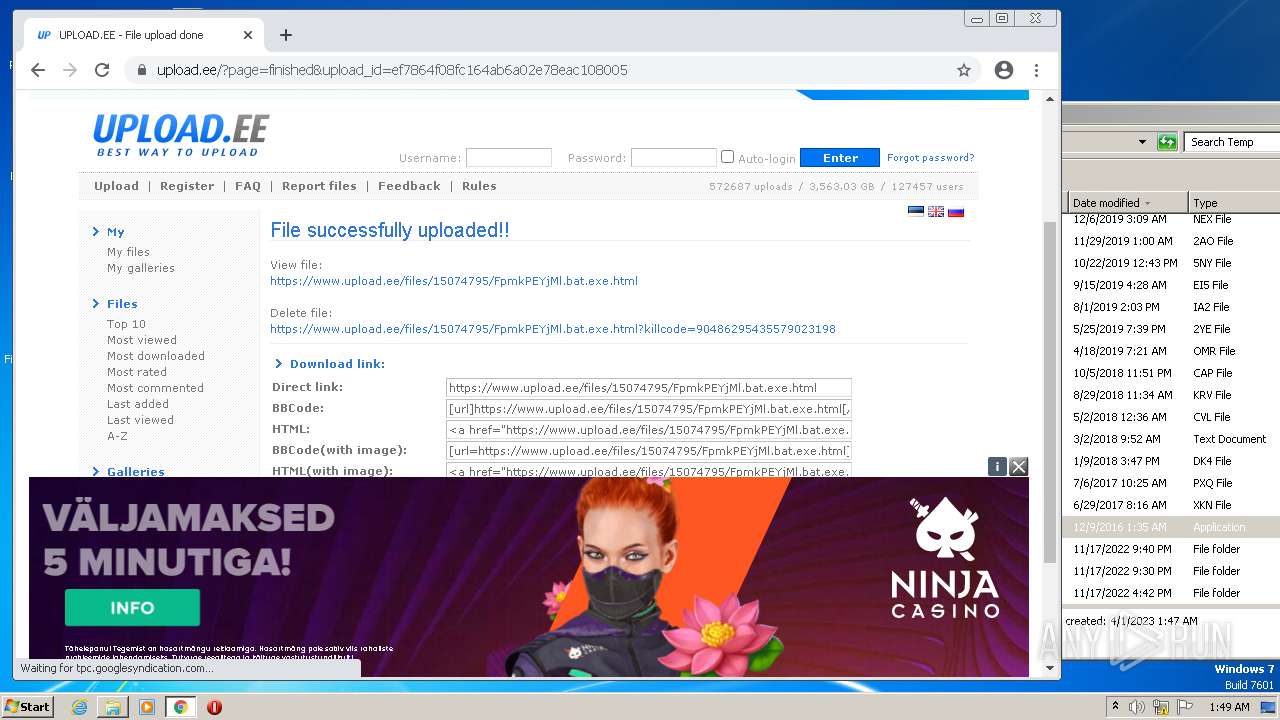
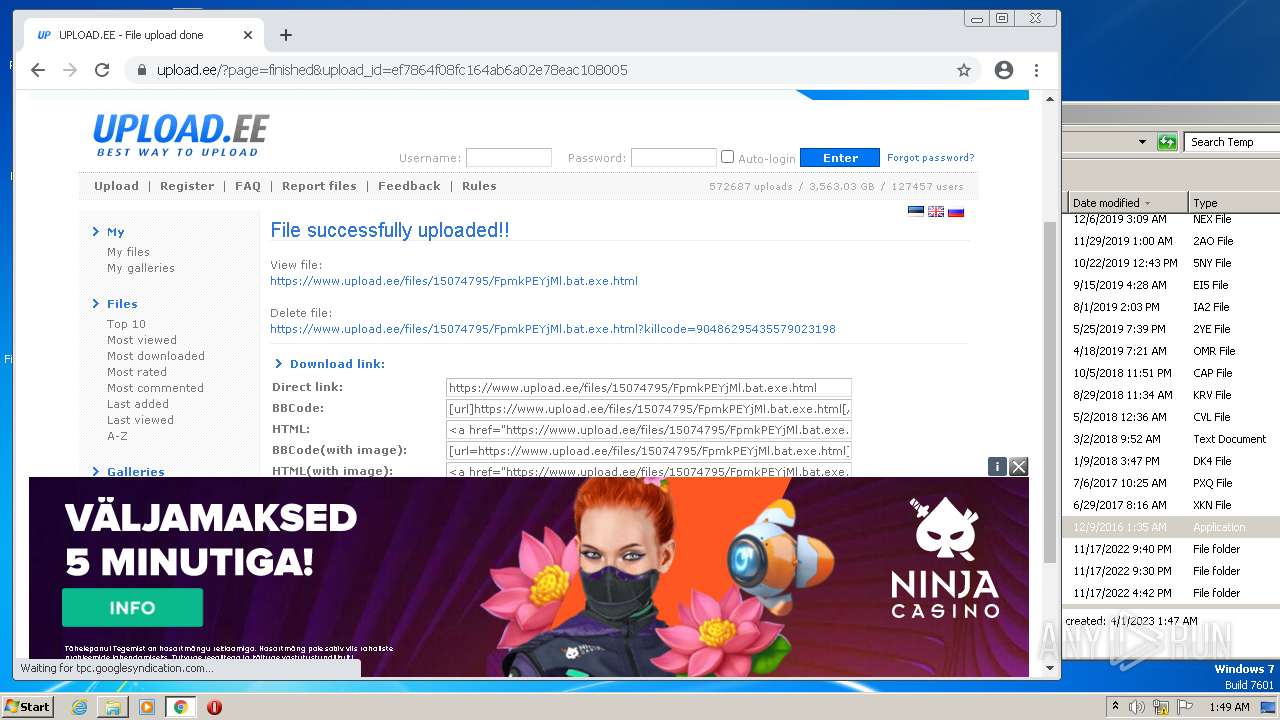
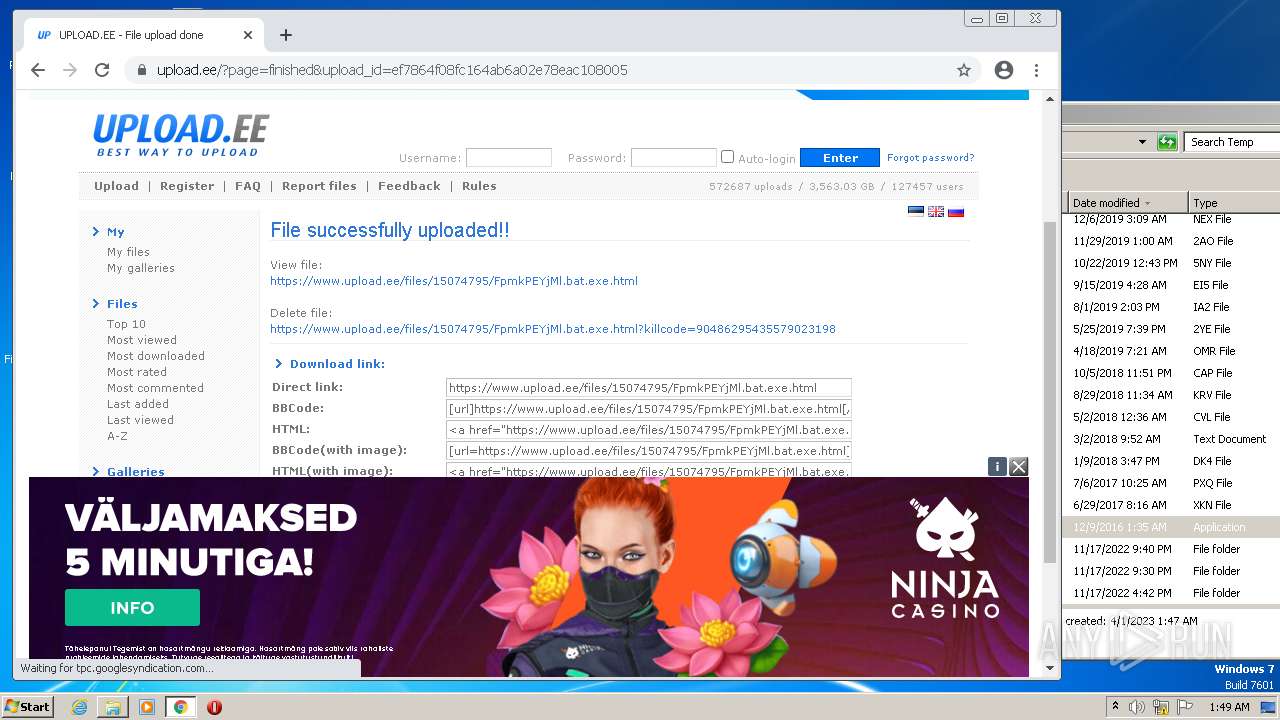
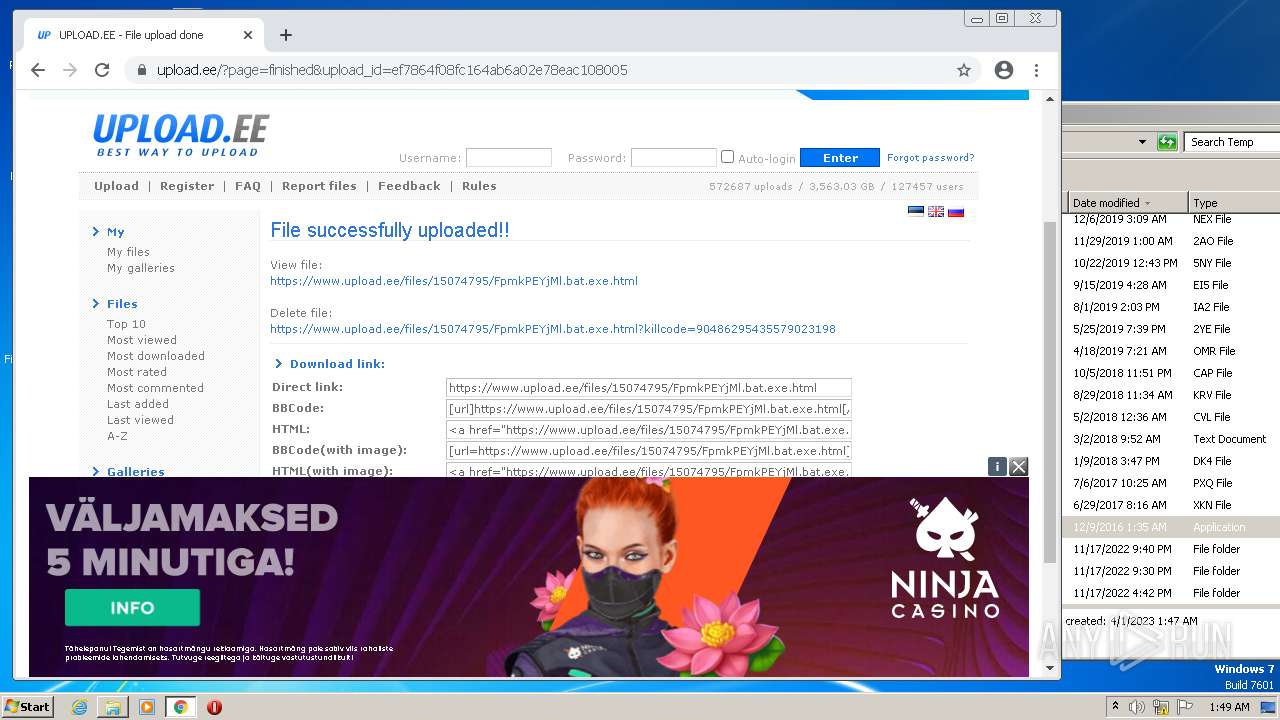
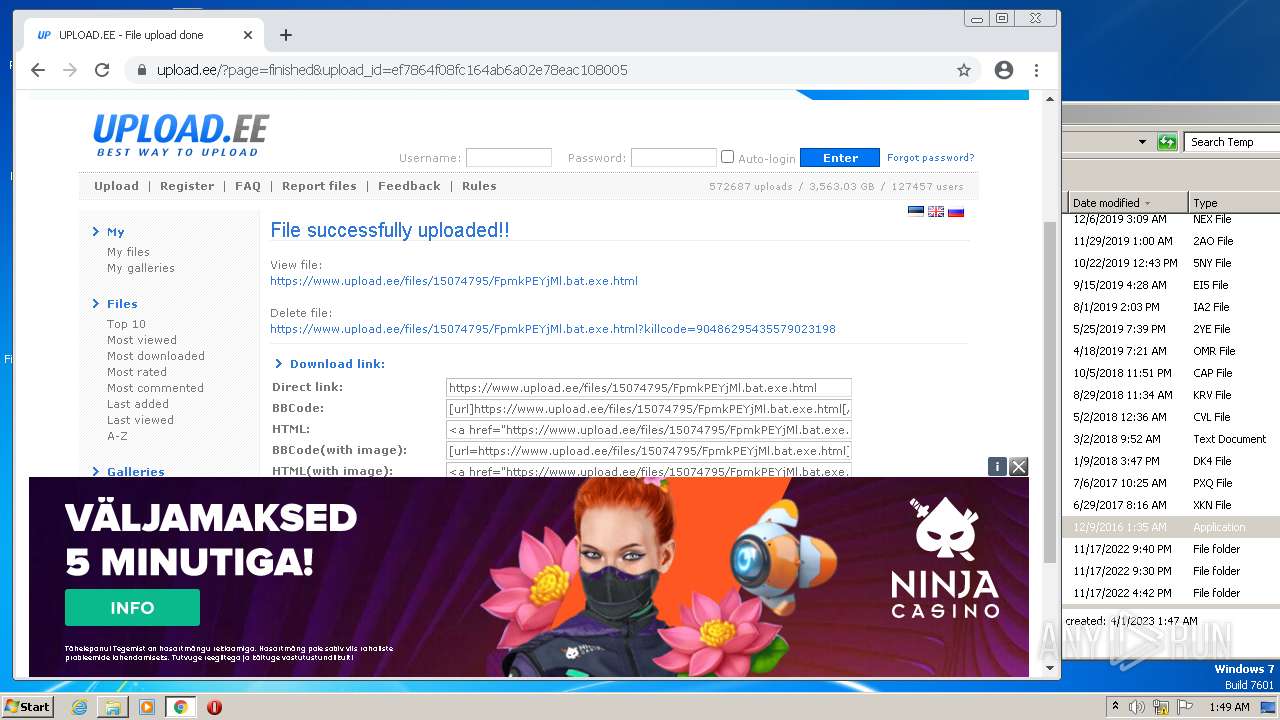
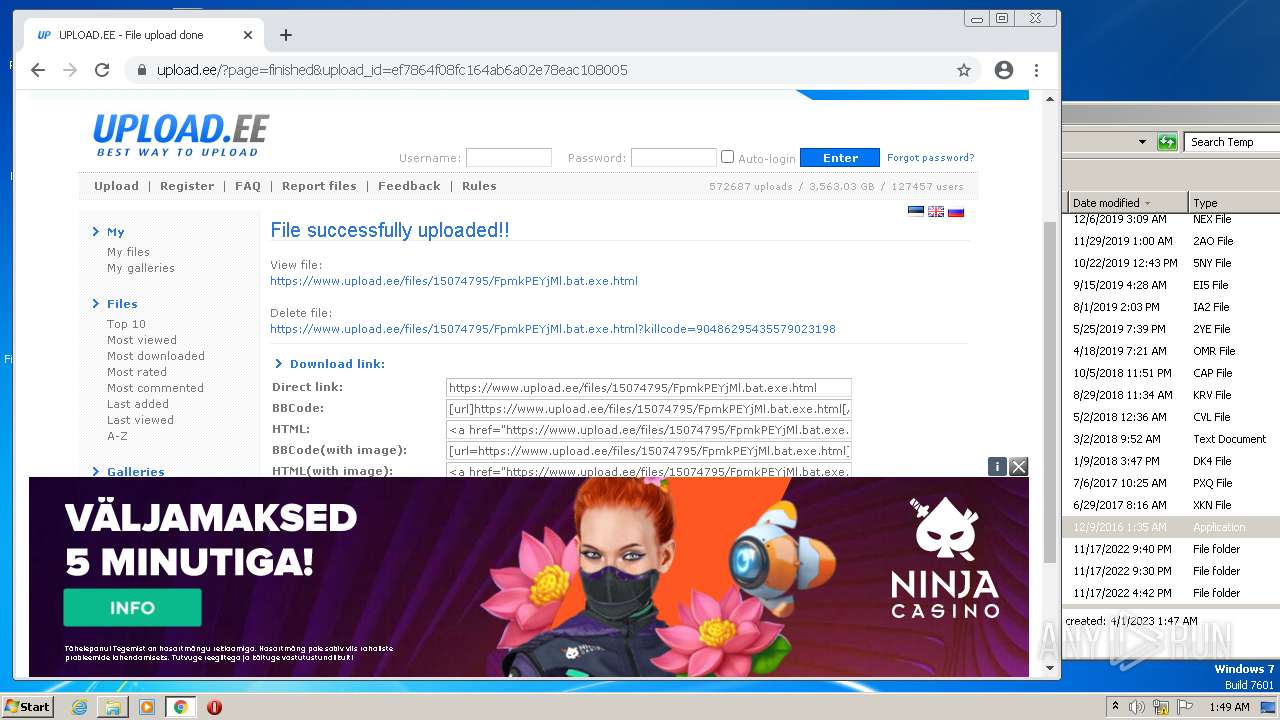
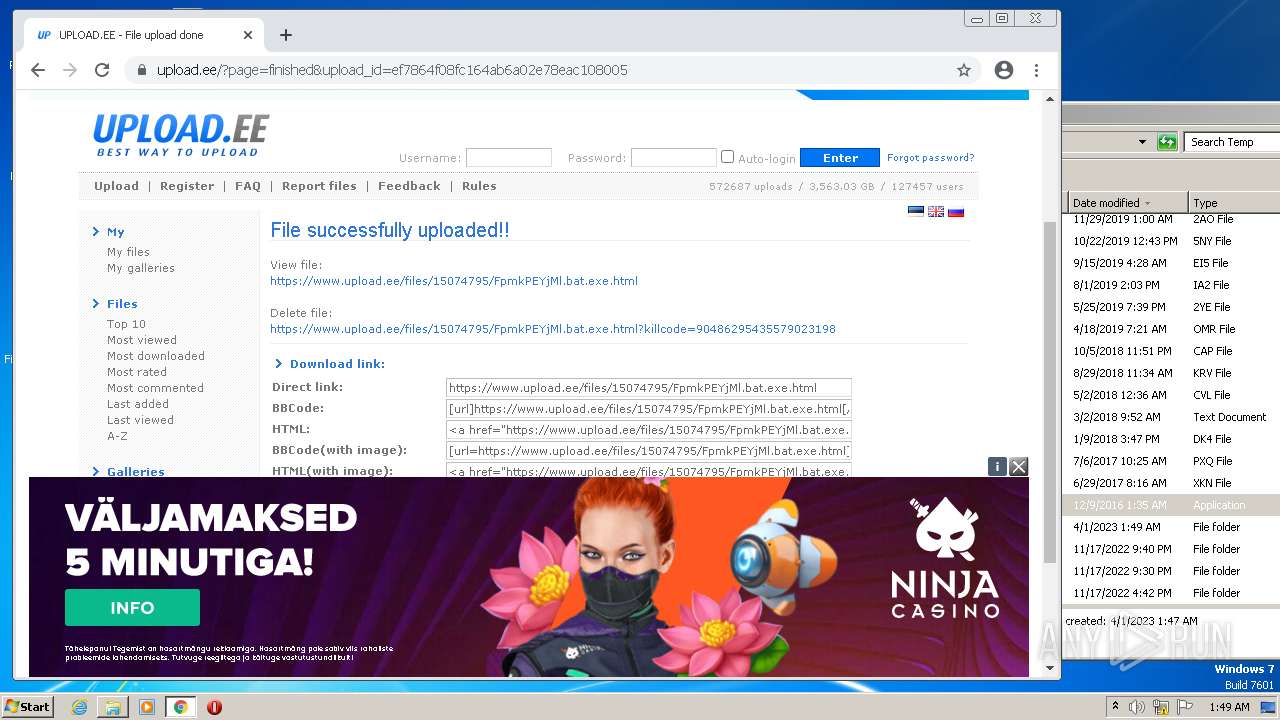
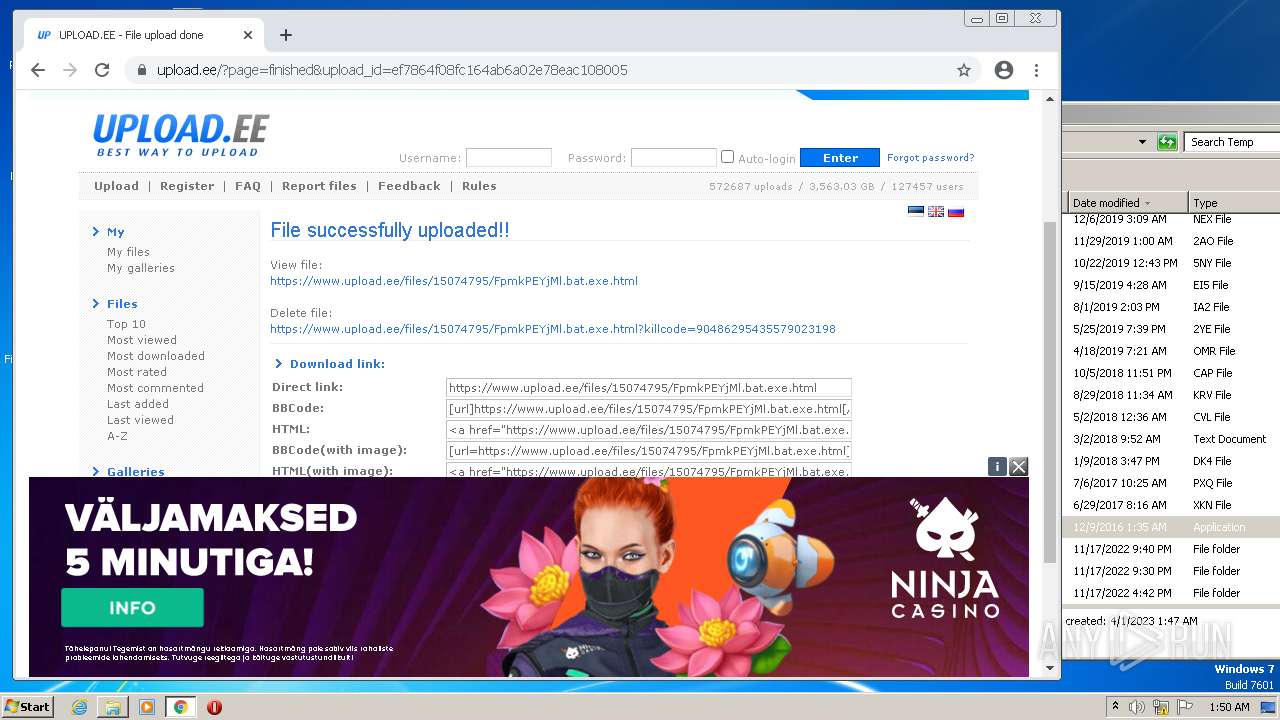
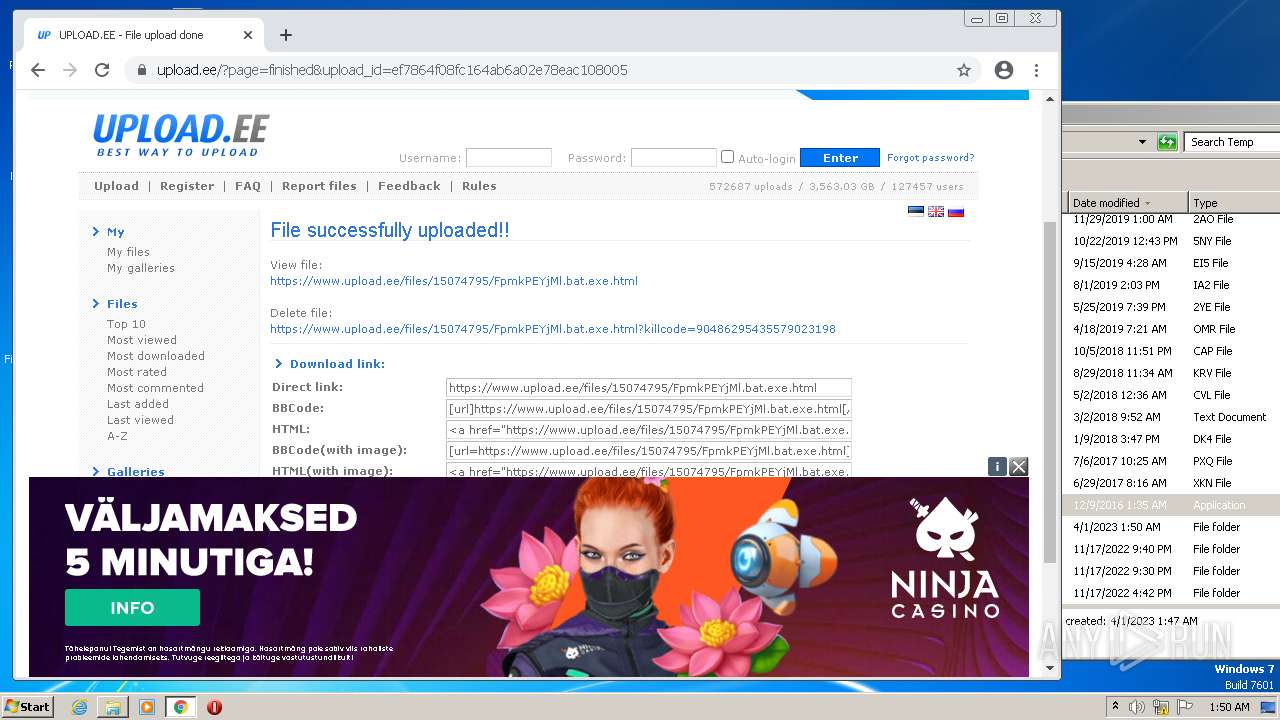
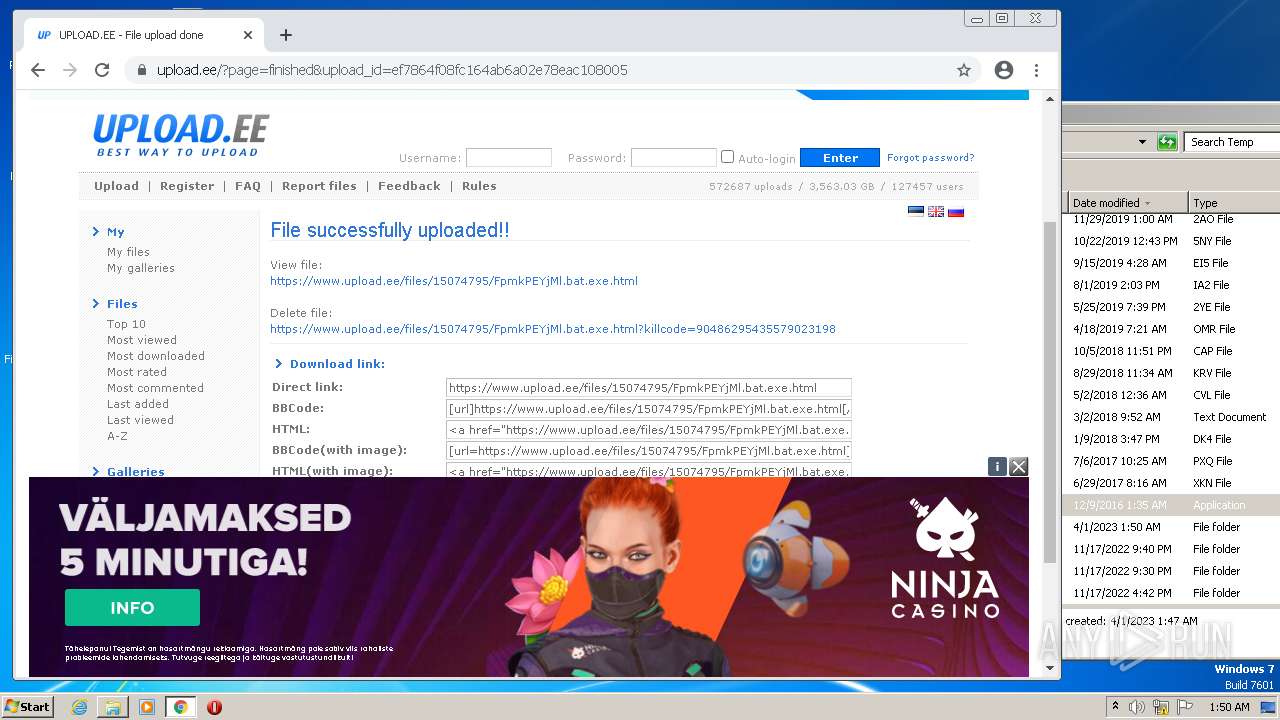
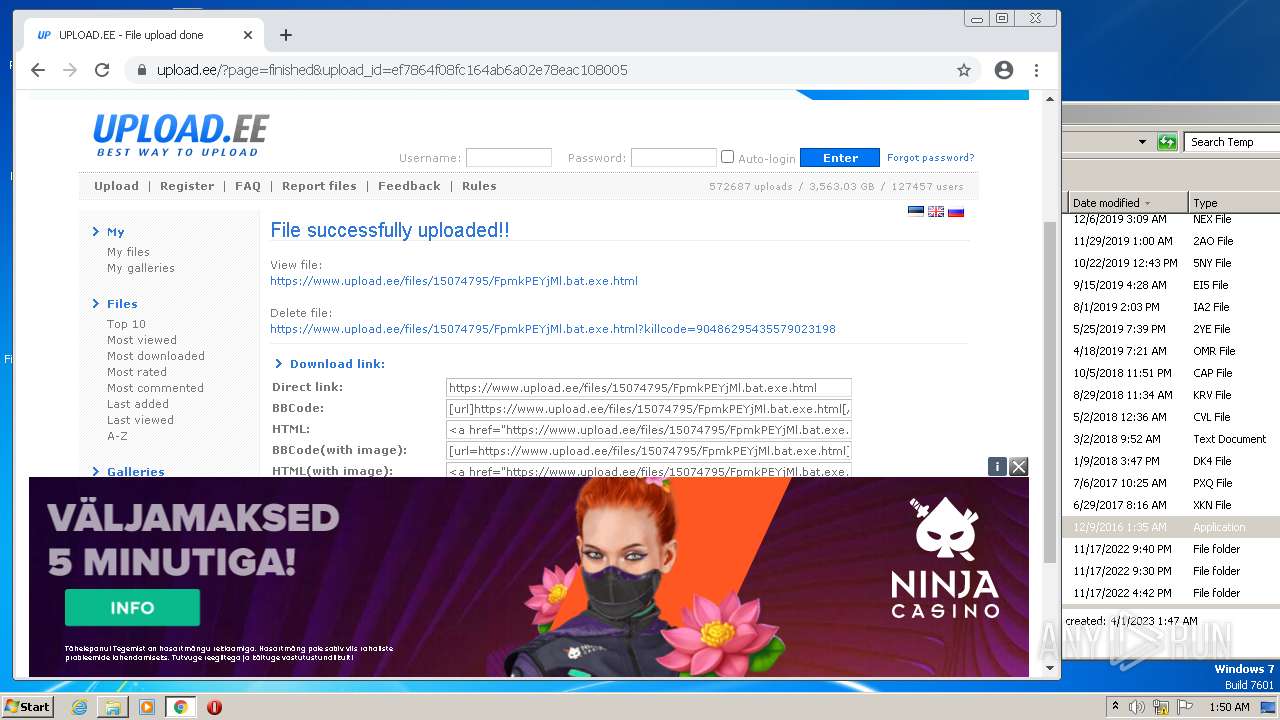
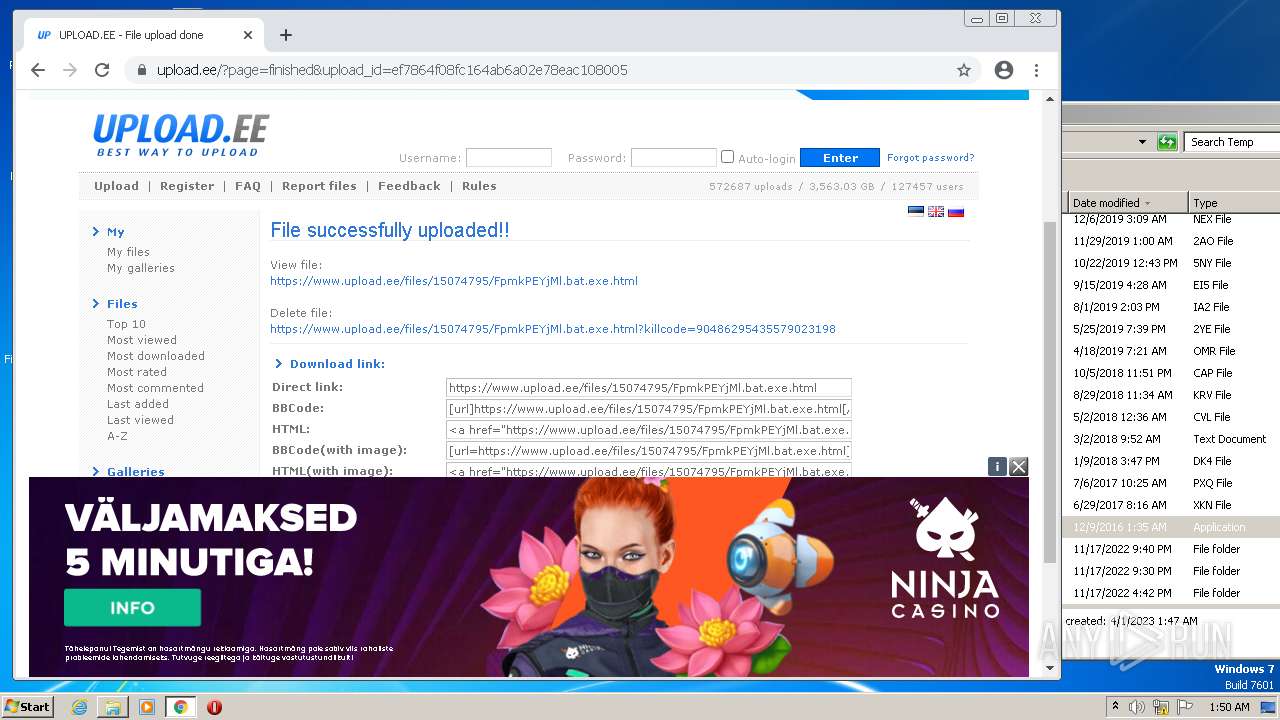
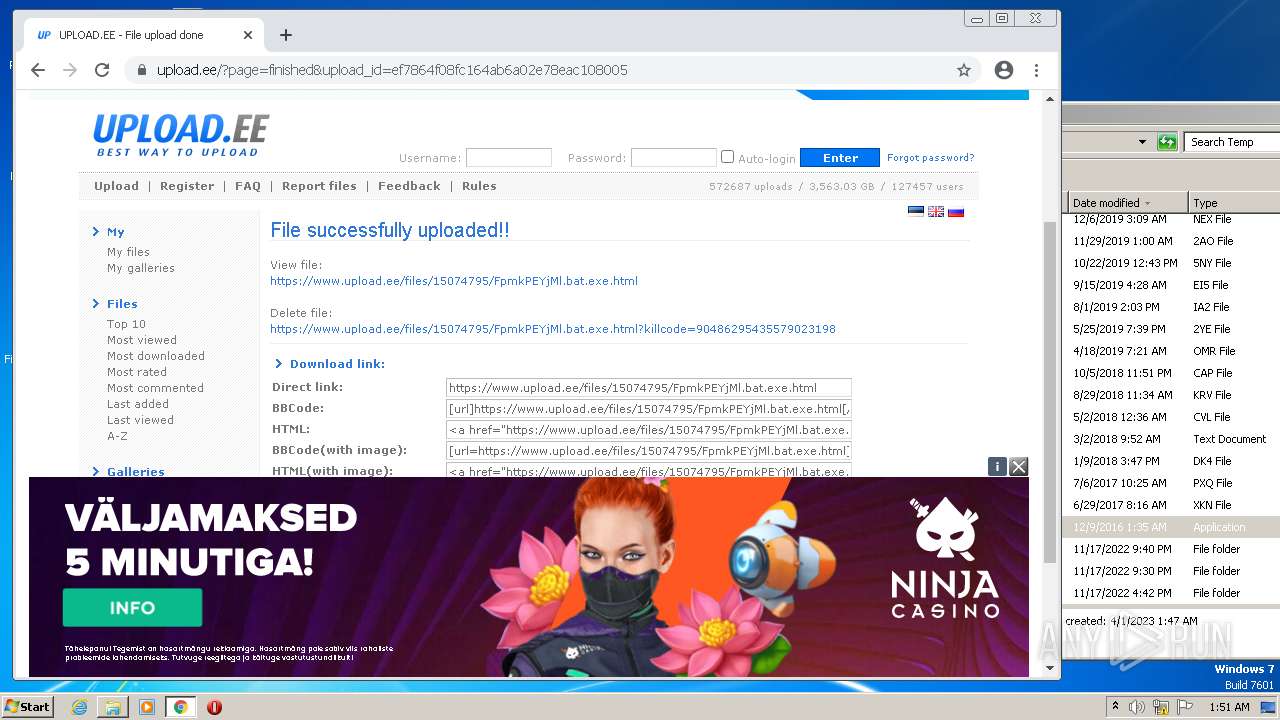
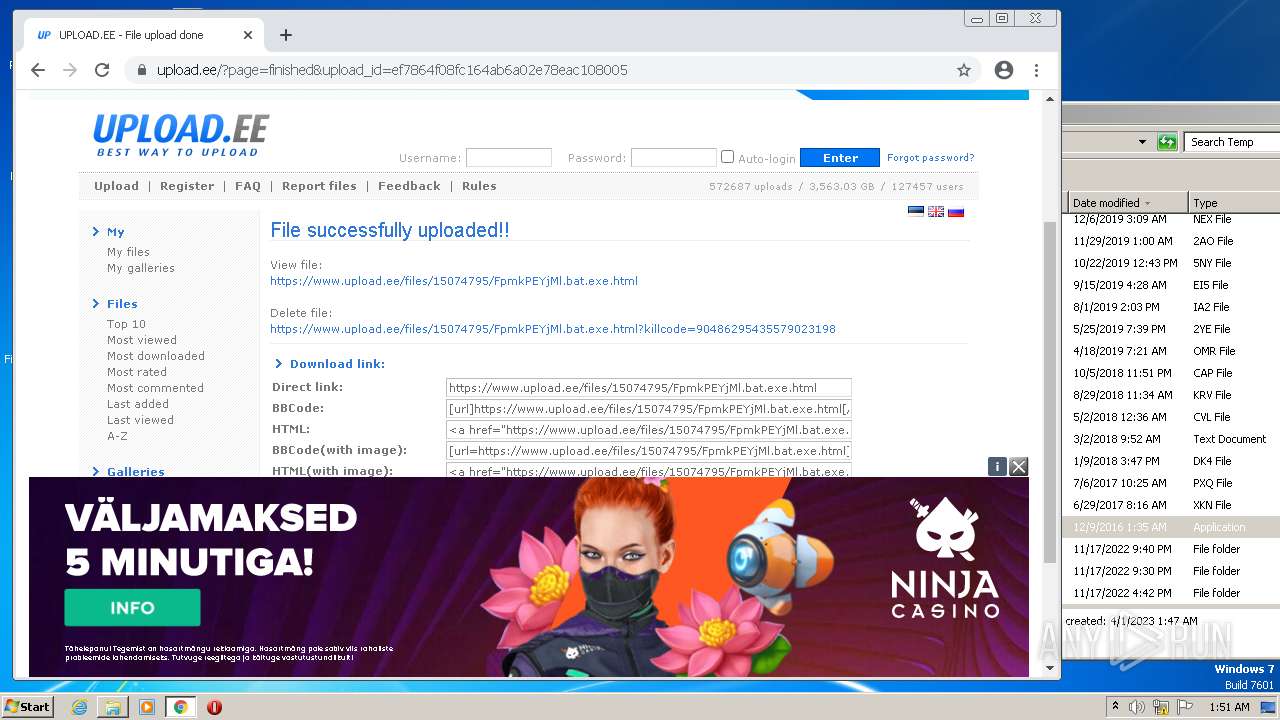
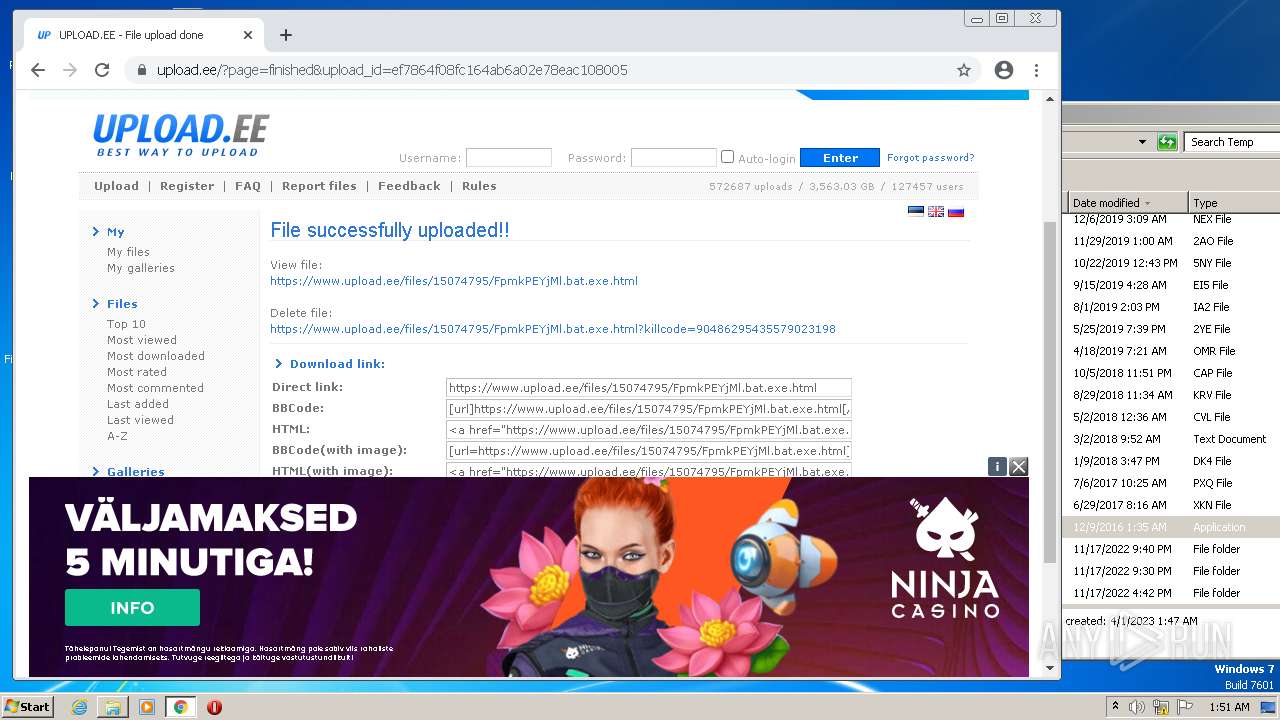
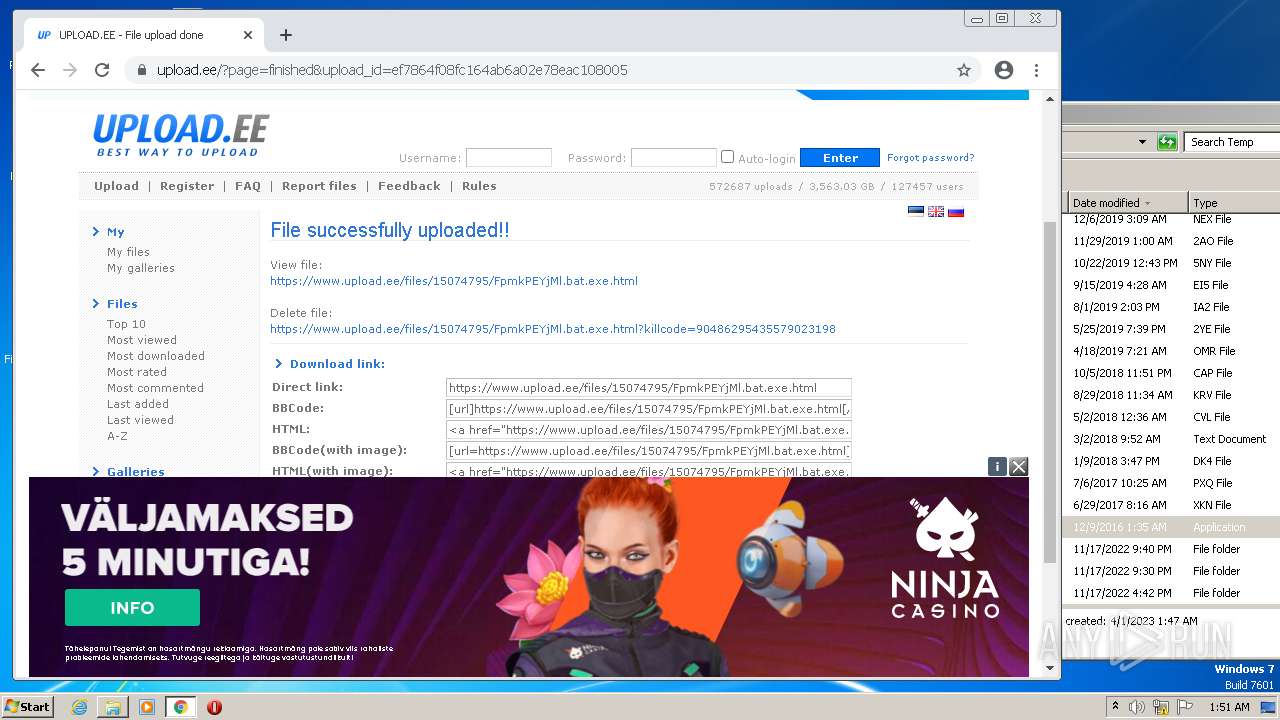
1744 | chrome.exe | GET | 302 | 51.91.30.159:80 | http://www.upload.ee/ | GB | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | — | — | whitelisted |
1744 | chrome.exe | GET | 204 | 142.250.186.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | binary | 10.3 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jewvegtcs2qdew3nlzz4kvsjqm_9.44.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.44.0_all_pywouuhjzu3khiqqvvfs2jt53q.crx3 | US | binary | 6.10 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | binary | 11.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | binary | 26.6 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | binary | 6.10 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jewvegtcs2qdew3nlzz4kvsjqm_9.44.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.44.0_all_pywouuhjzu3khiqqvvfs2jt53q.crx3 | US | binary | 567 b | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 567 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
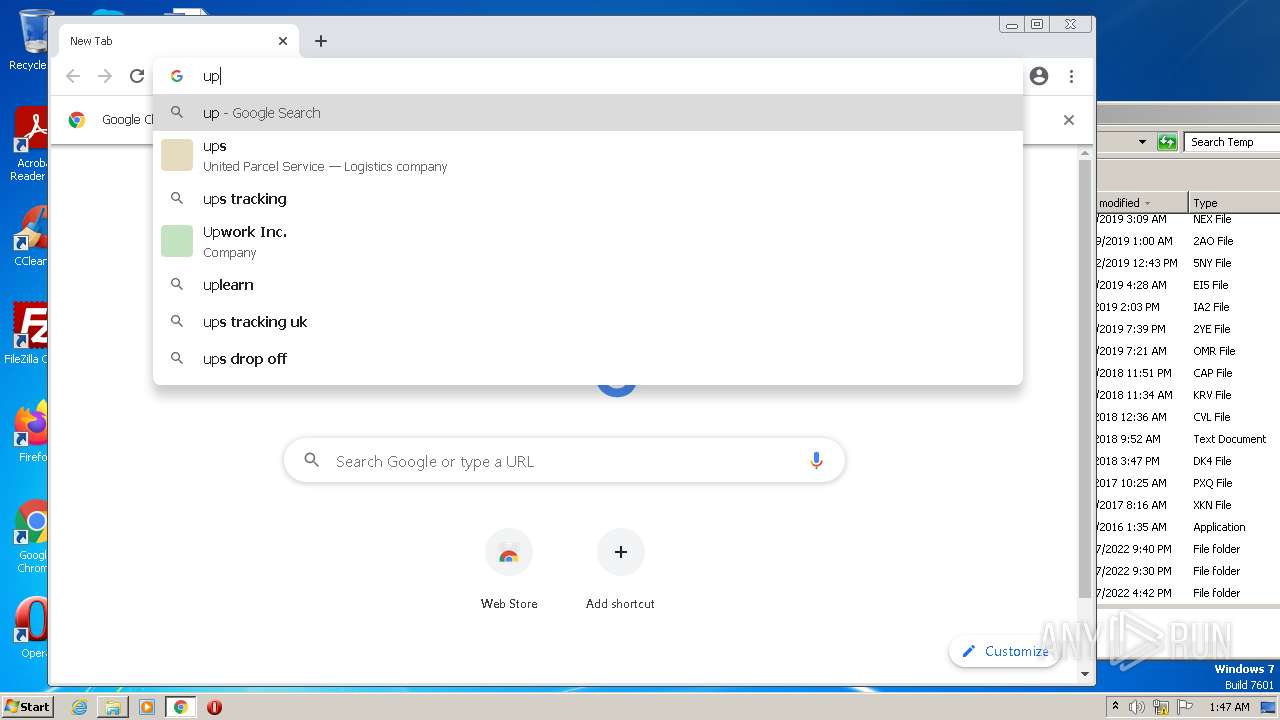
1744 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 172.217.16.206:443 | clients2.google.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.74.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.184.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 51.91.30.159:80 | upload.ee | OVH SAS | FR | suspicious |
1744 | chrome.exe | 51.91.30.159:443 | upload.ee | OVH SAS | FR | suspicious |
1744 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.186.99:80 | www.gstatic.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
1744 | chrome.exe | 142.250.184.194:443 | pagead2.googlesyndication.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
upload.ee |
| suspicious |
www.upload.ee |
| whitelisted |
ssl.gstatic.com |
| whitelisted |