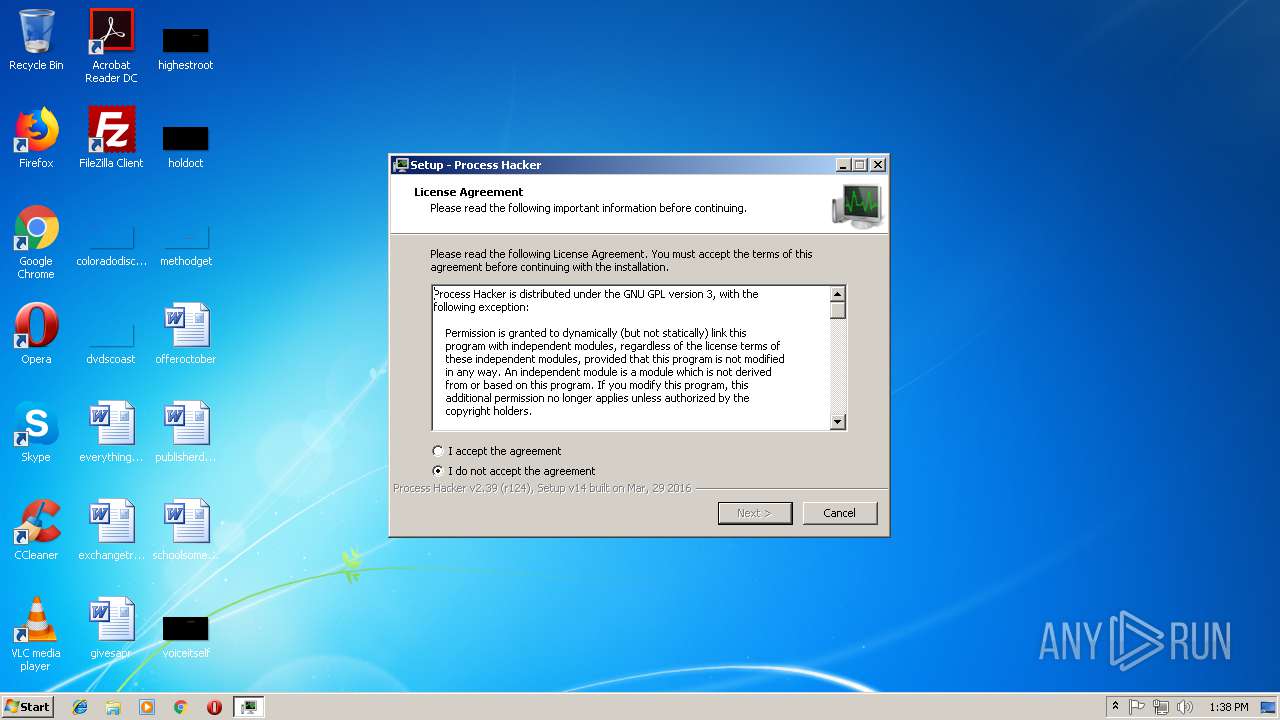
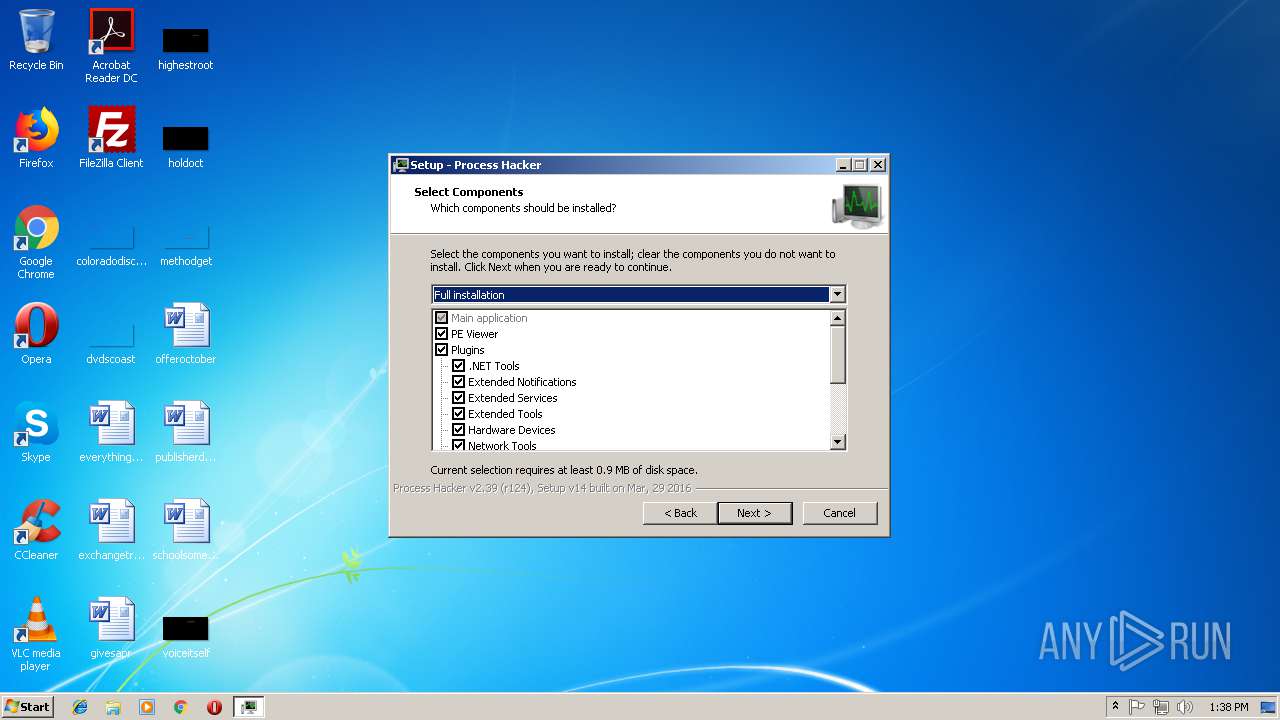
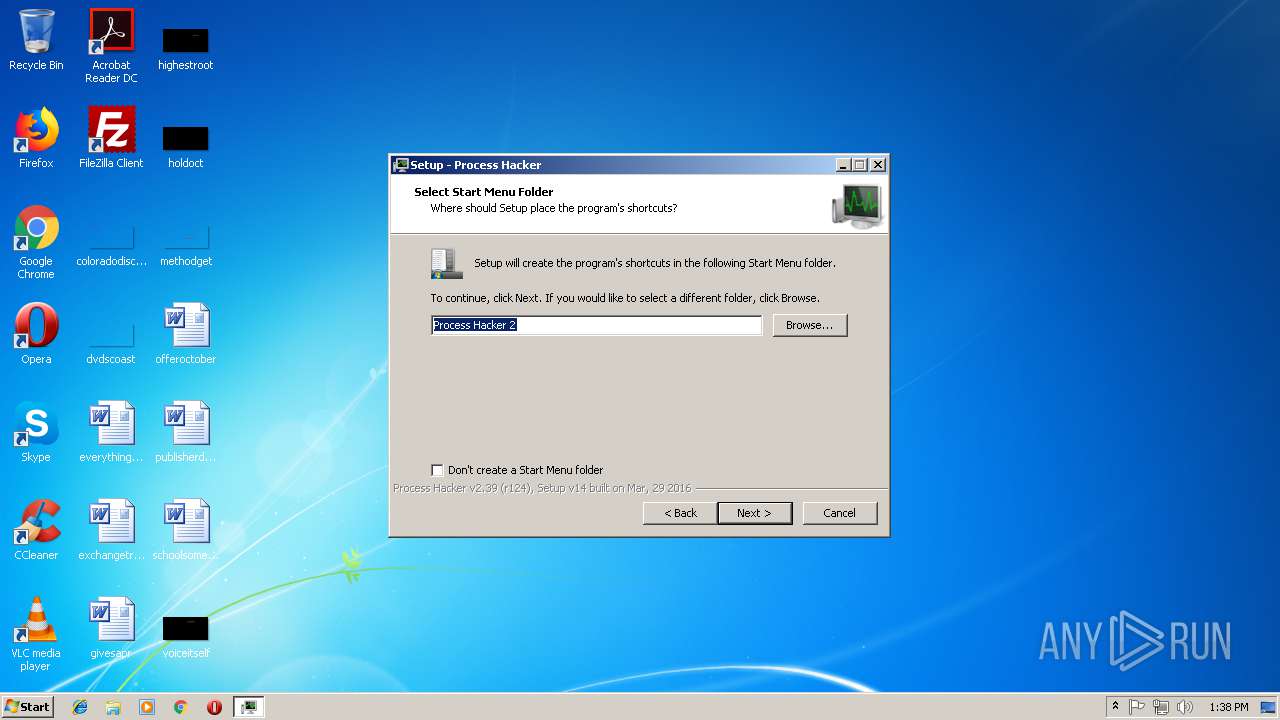
| File name: | processhacker-2.39-setup.exe |
| Full analysis: | https://app.any.run/tasks/8300766a-45da-4b2f-8150-775fe85bc4b4 |
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2018, 12:38:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 54DAAD58CCE5003BEE58B28A4F465F49 |
| SHA1: | 162B08B0B11827CC024E6B2EED5887EC86339BAA |
| SHA256: | 28042DD4A92A0033B8F1D419B9E989C5B8E32D1D2D881F5C8251D58CE35B9063 |
| SSDEEP: | 49152:l9hfV/U5NkLXXzGZjt6kFTCVP6hWE0wvmk/eE+FrAl+NGsOSE6IX8pq:Dh9/ULkjKxtTGP6VZd2rAcvOSE6Nq |
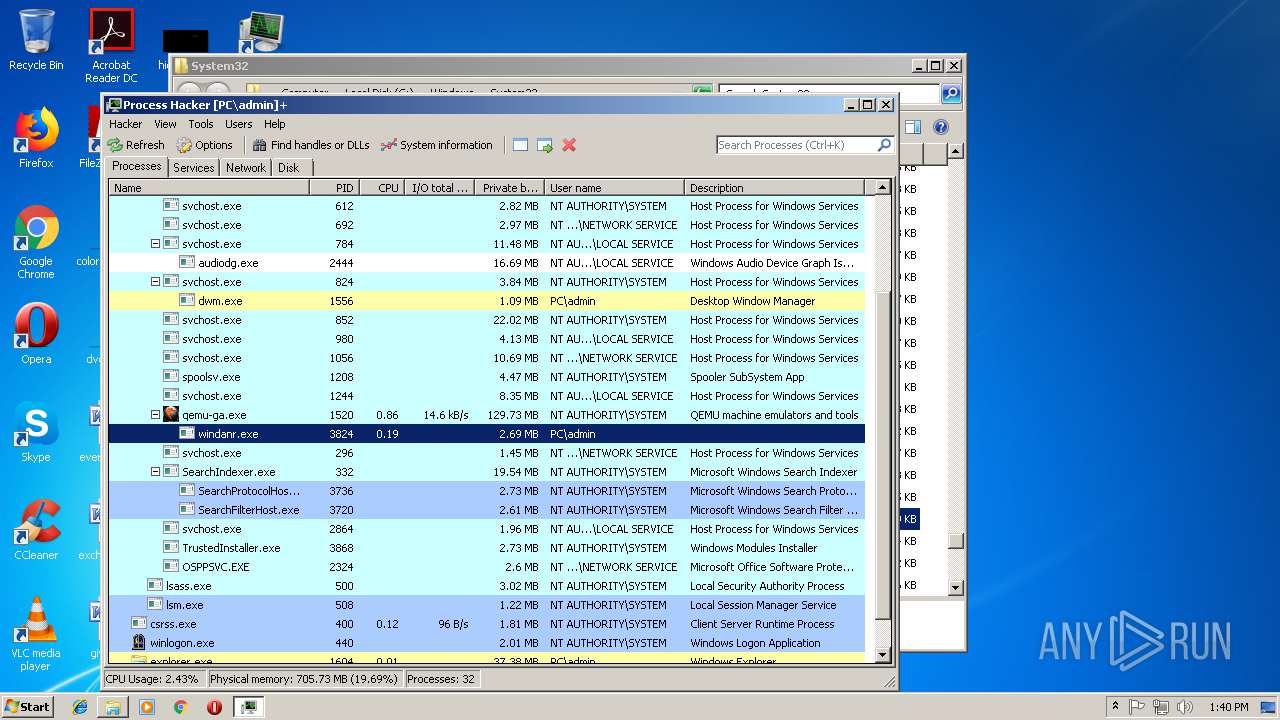
MALICIOUS
Changes the autorun value in the registry
- processhacker-2.39-setup.tmp (PID: 3304)
Changes Image File Execution Options
- processhacker-2.39-setup.tmp (PID: 3304)
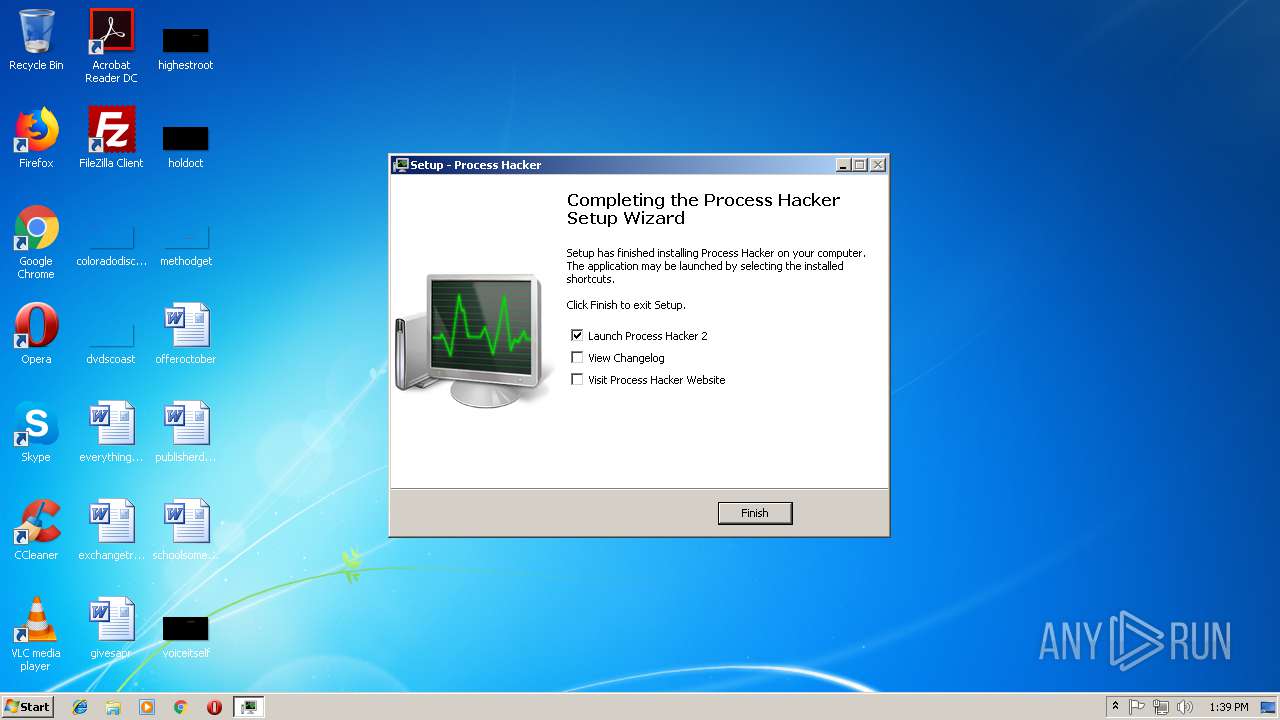
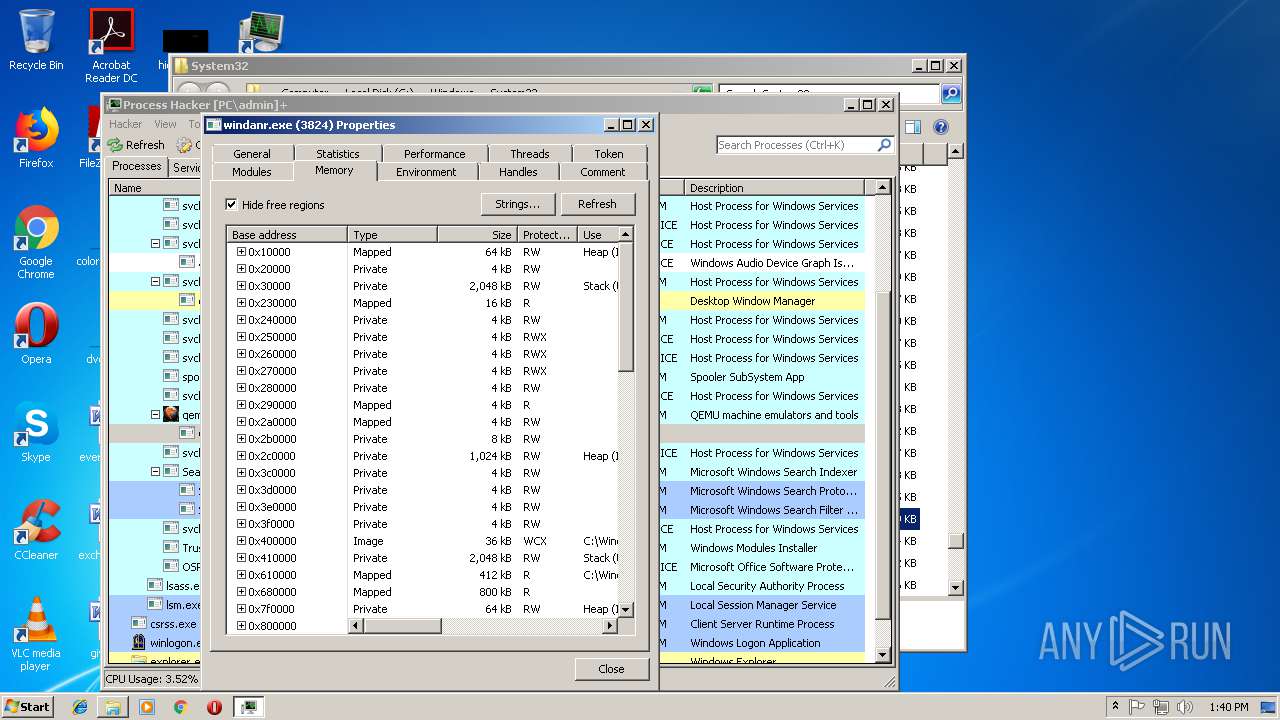
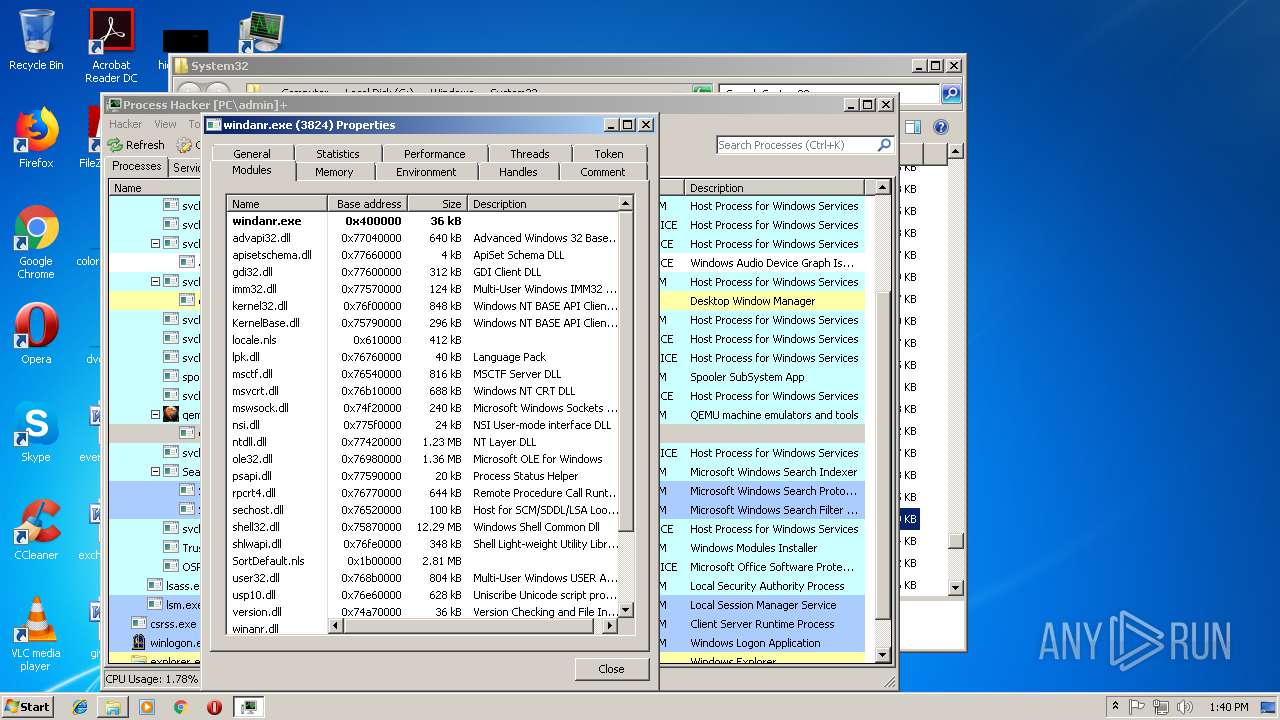
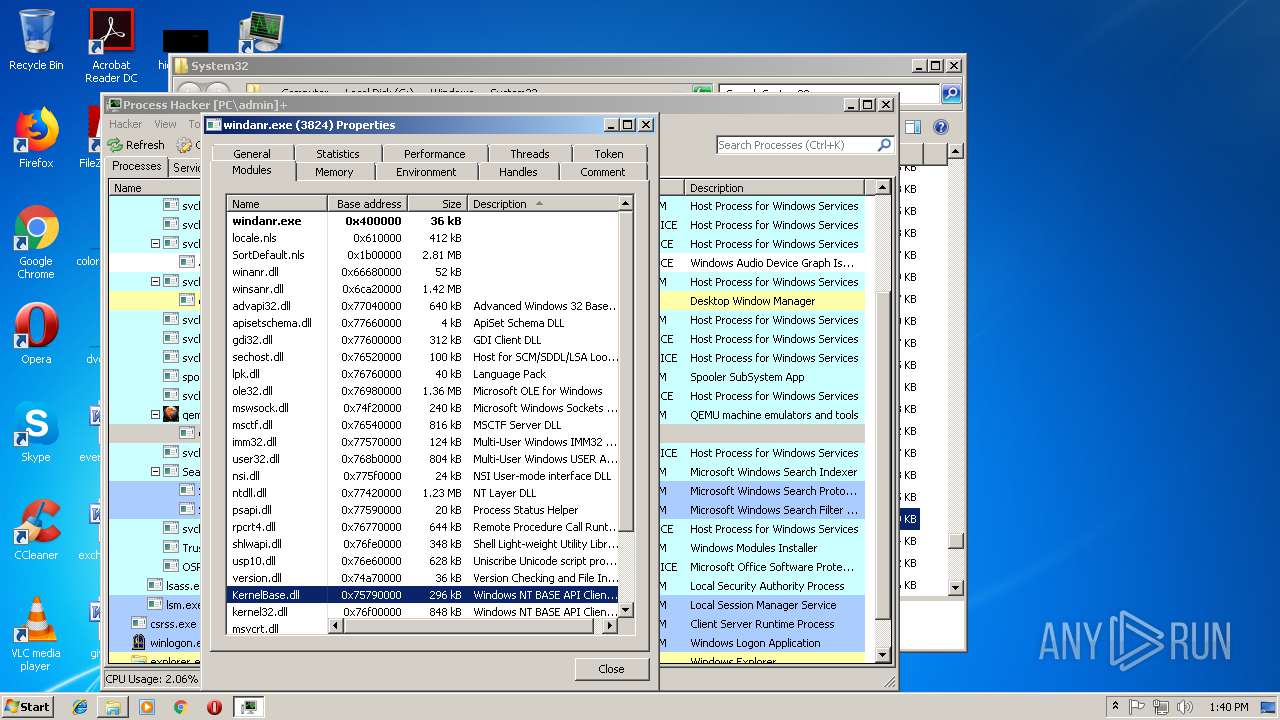
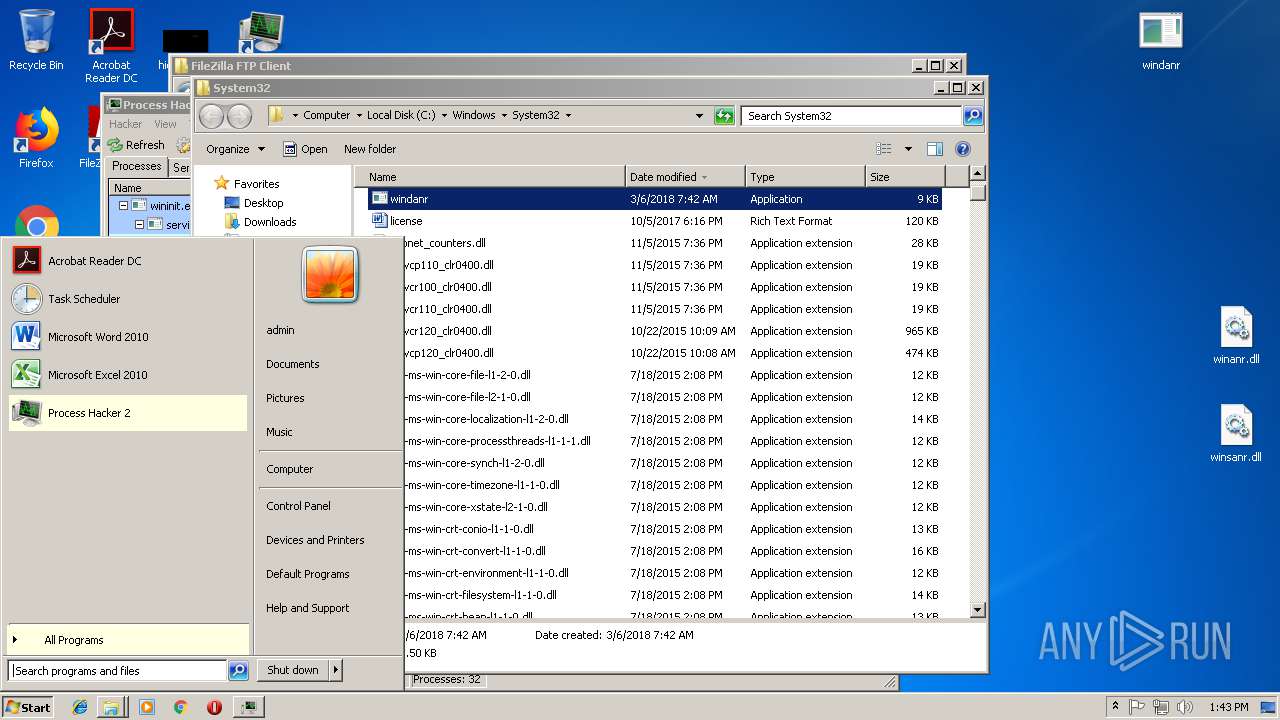
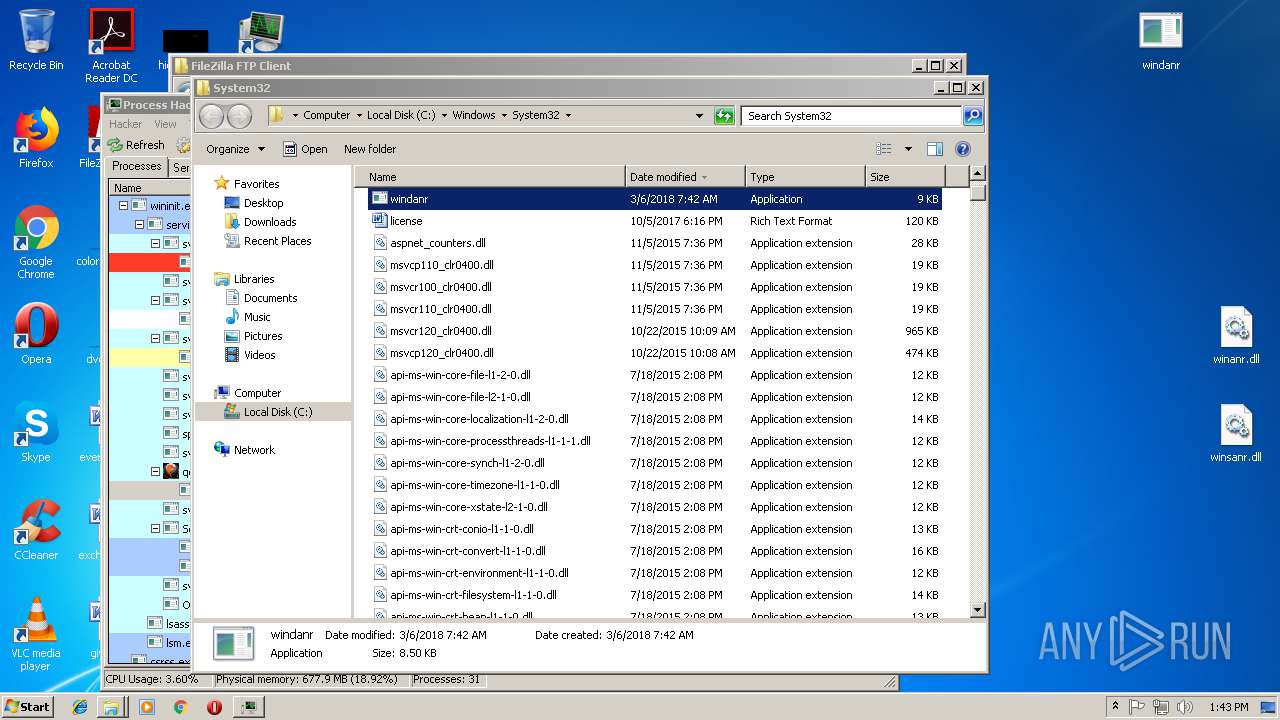
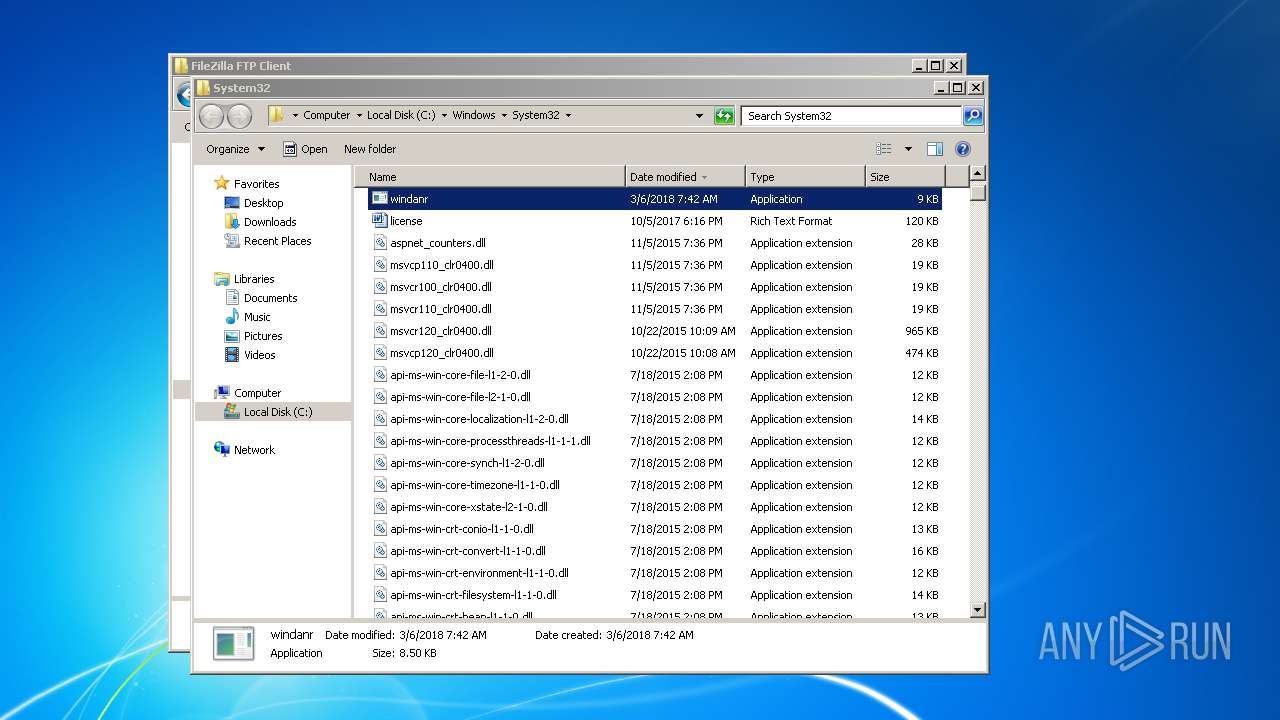
Application was dropped or rewritten from another process
- ProcessHacker.exe (PID: 3952)
- ProcessHacker.exe (PID: 4084)
- peview.exe (PID: 3588)
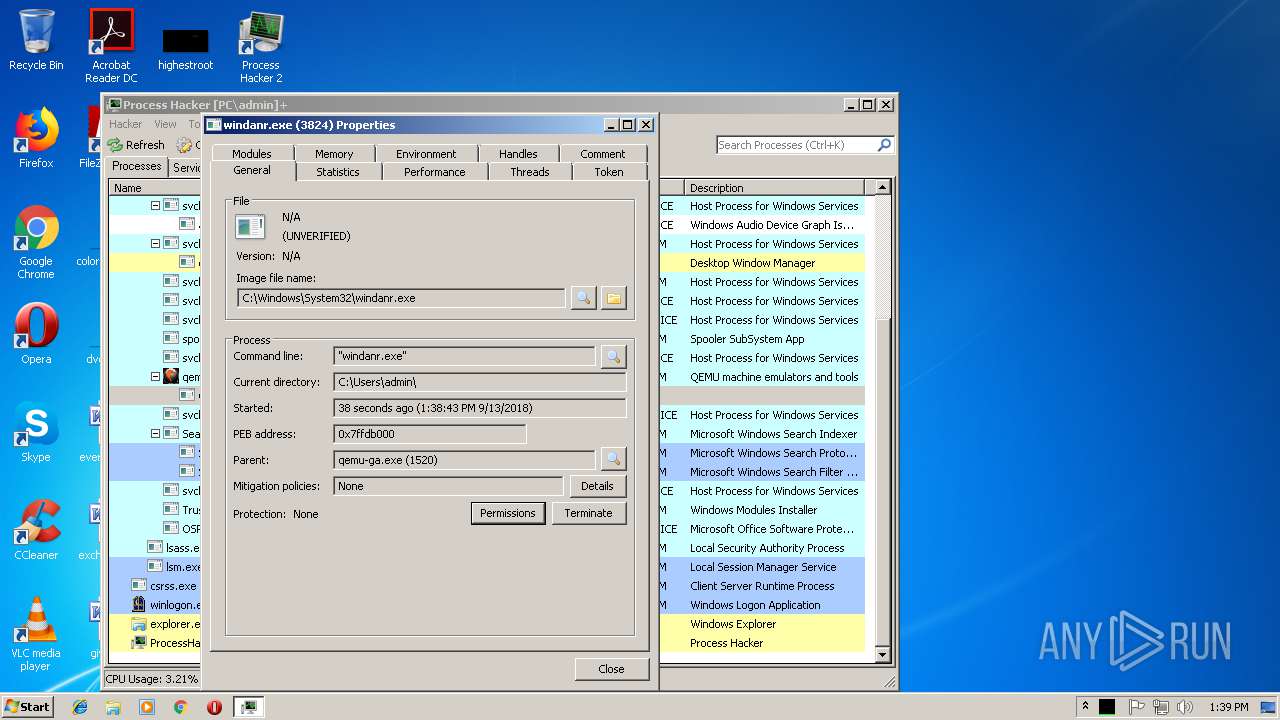
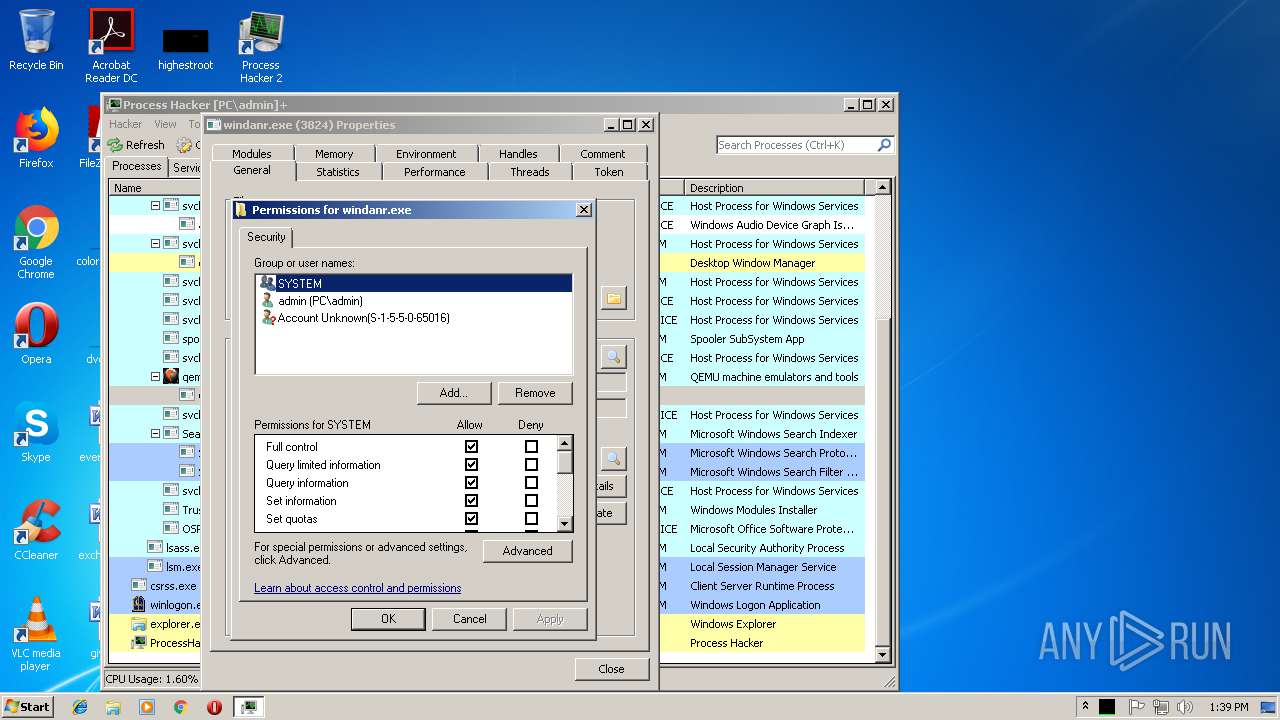
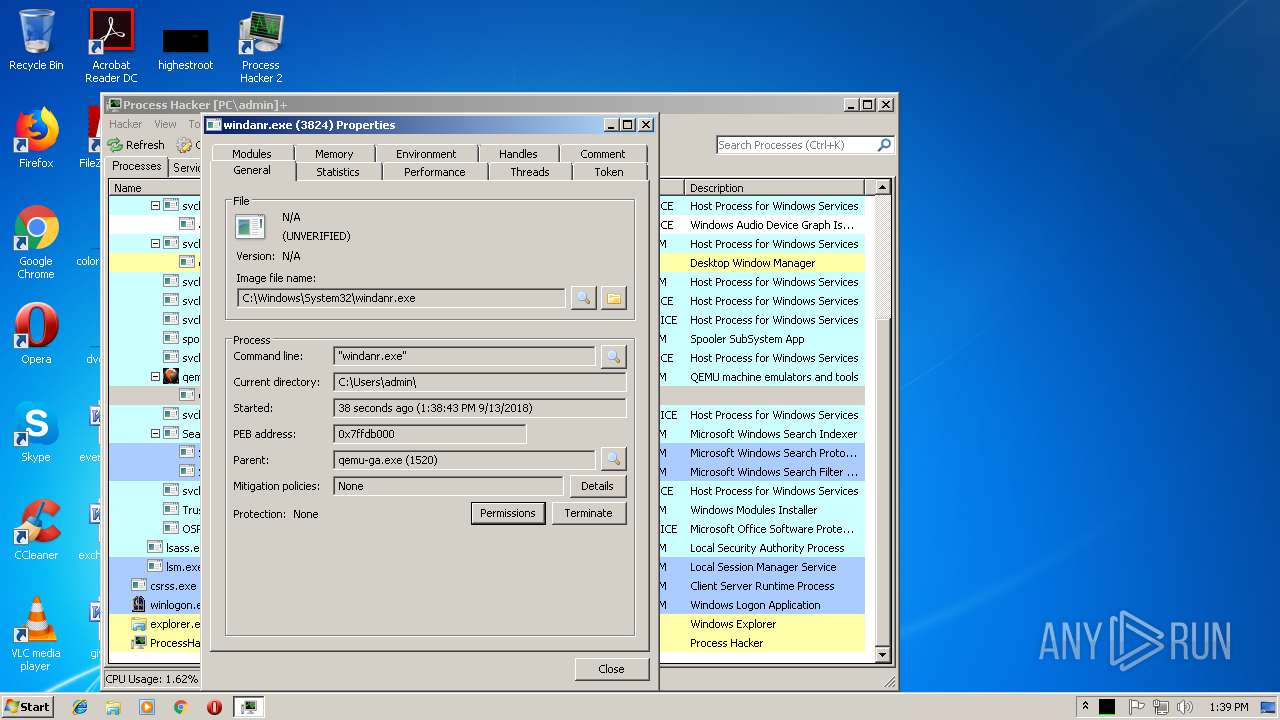
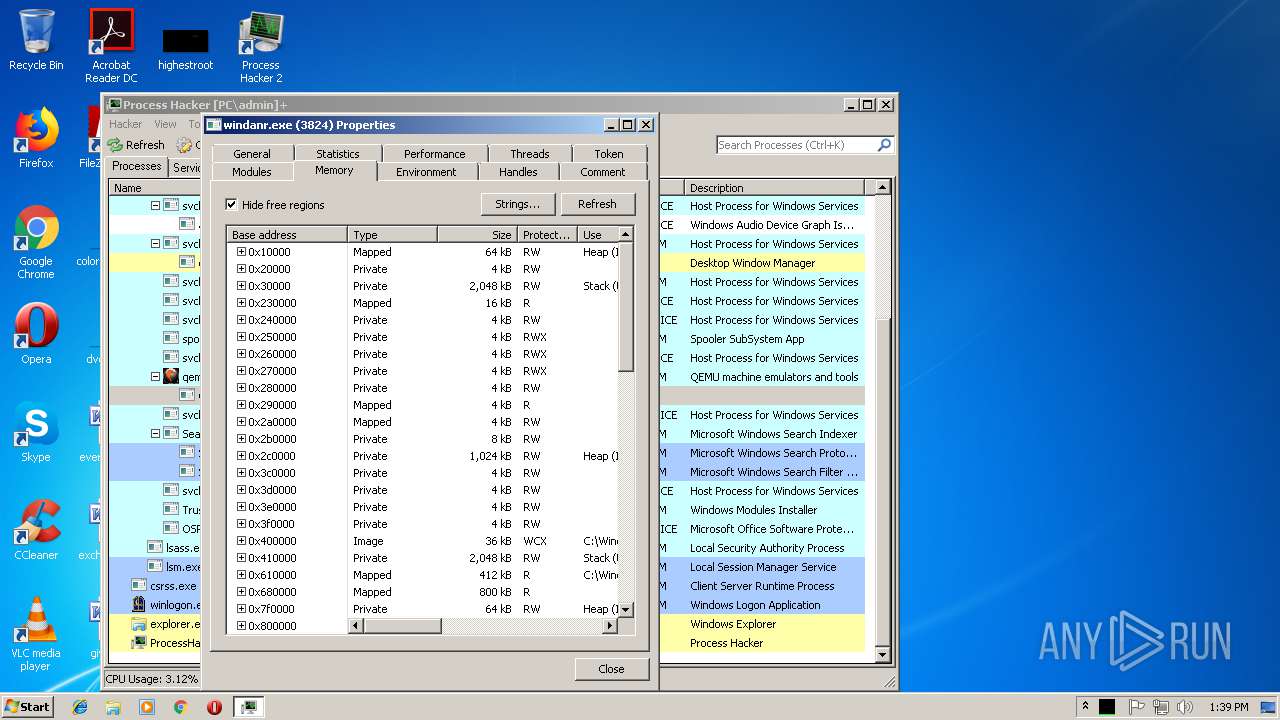
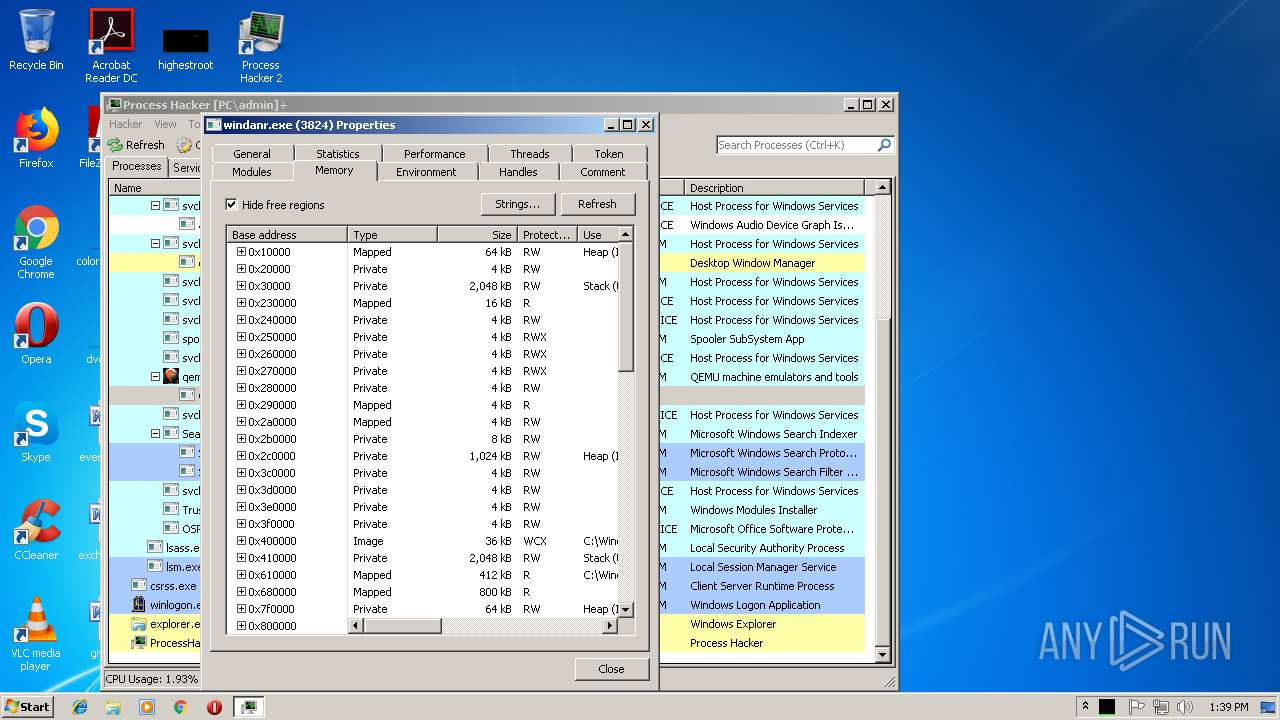
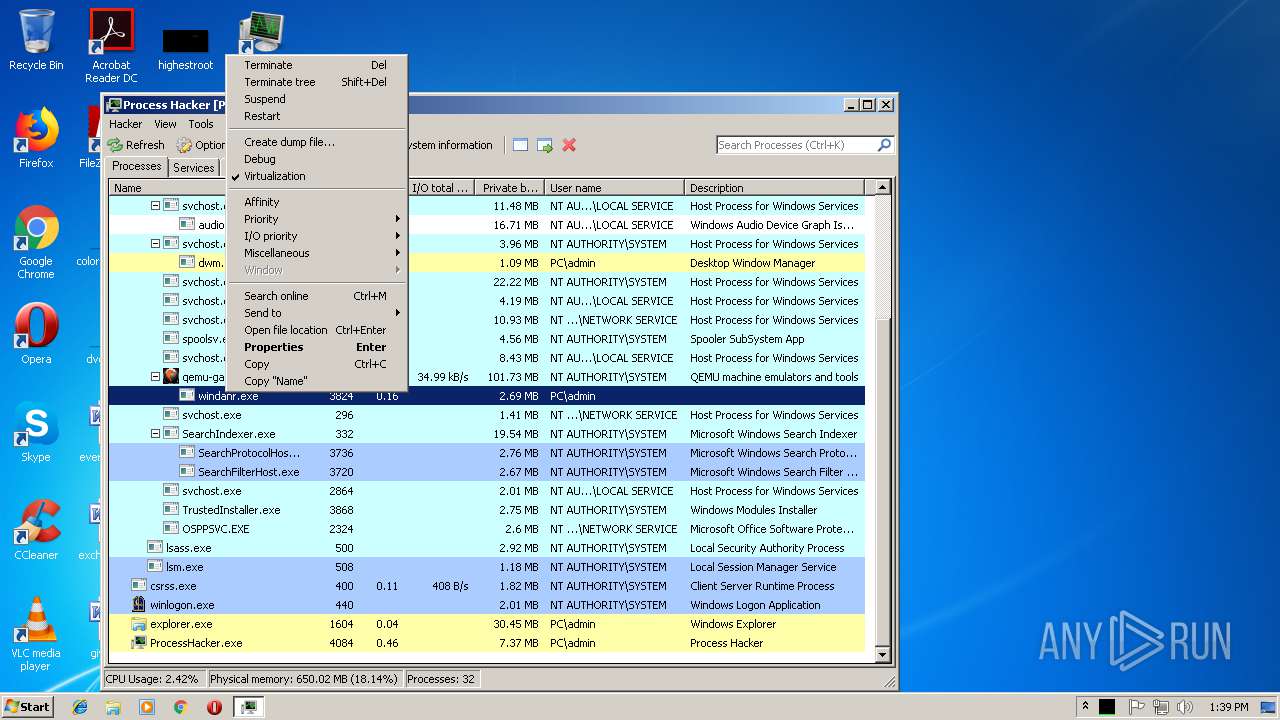
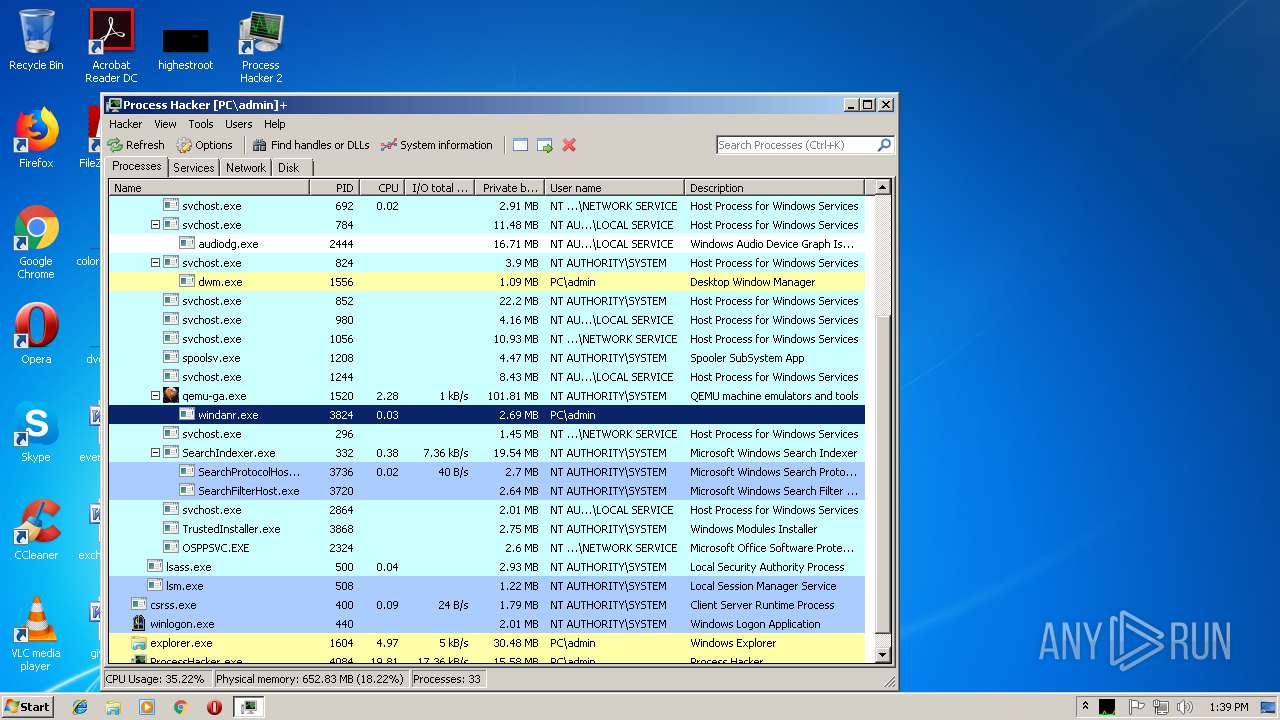
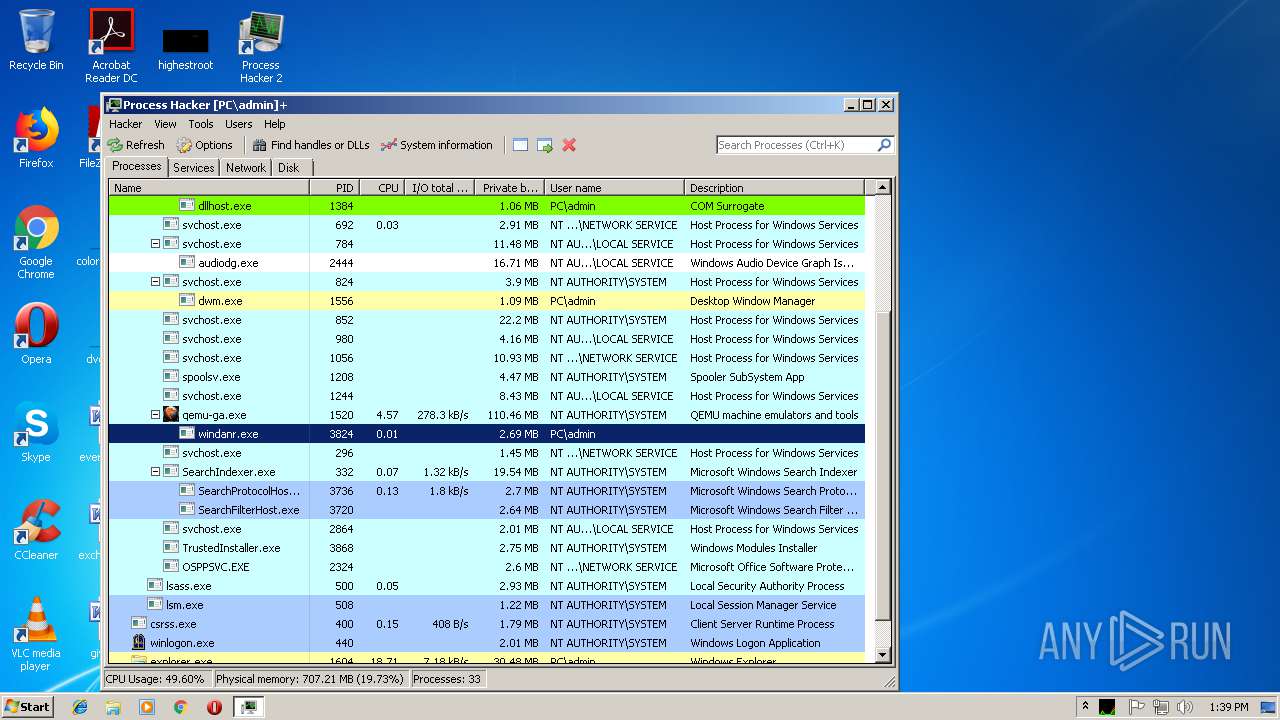
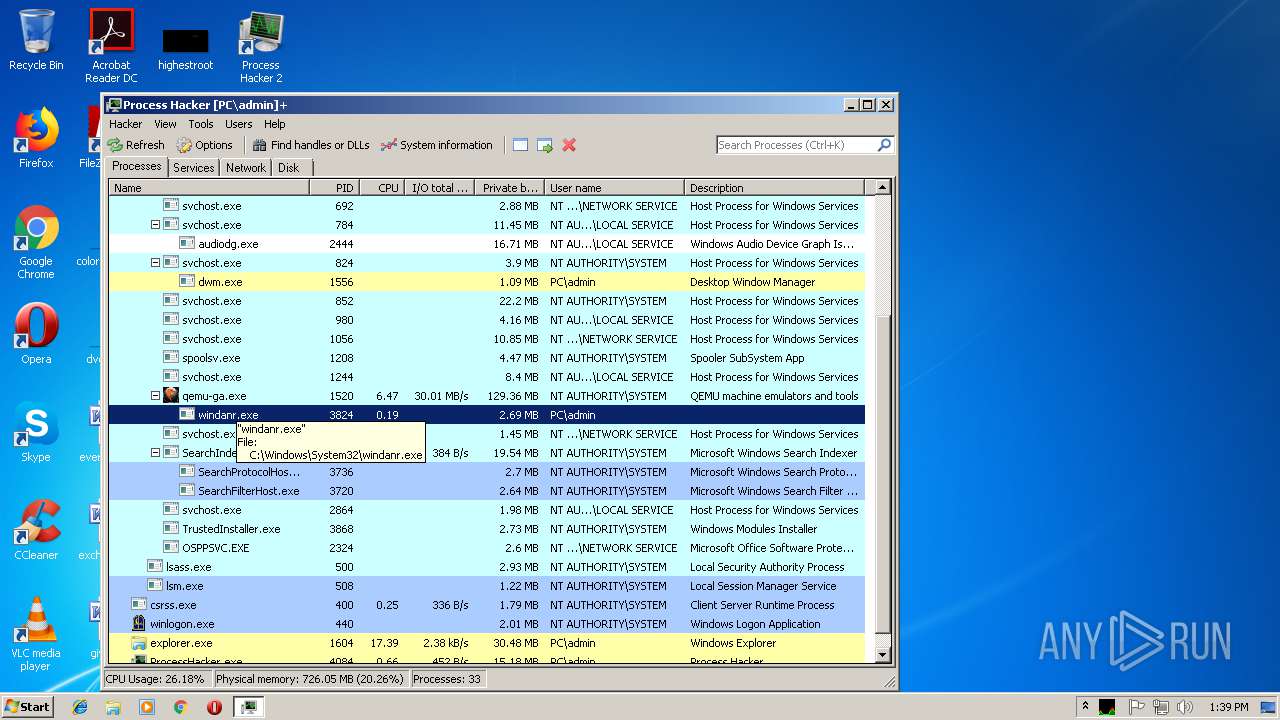
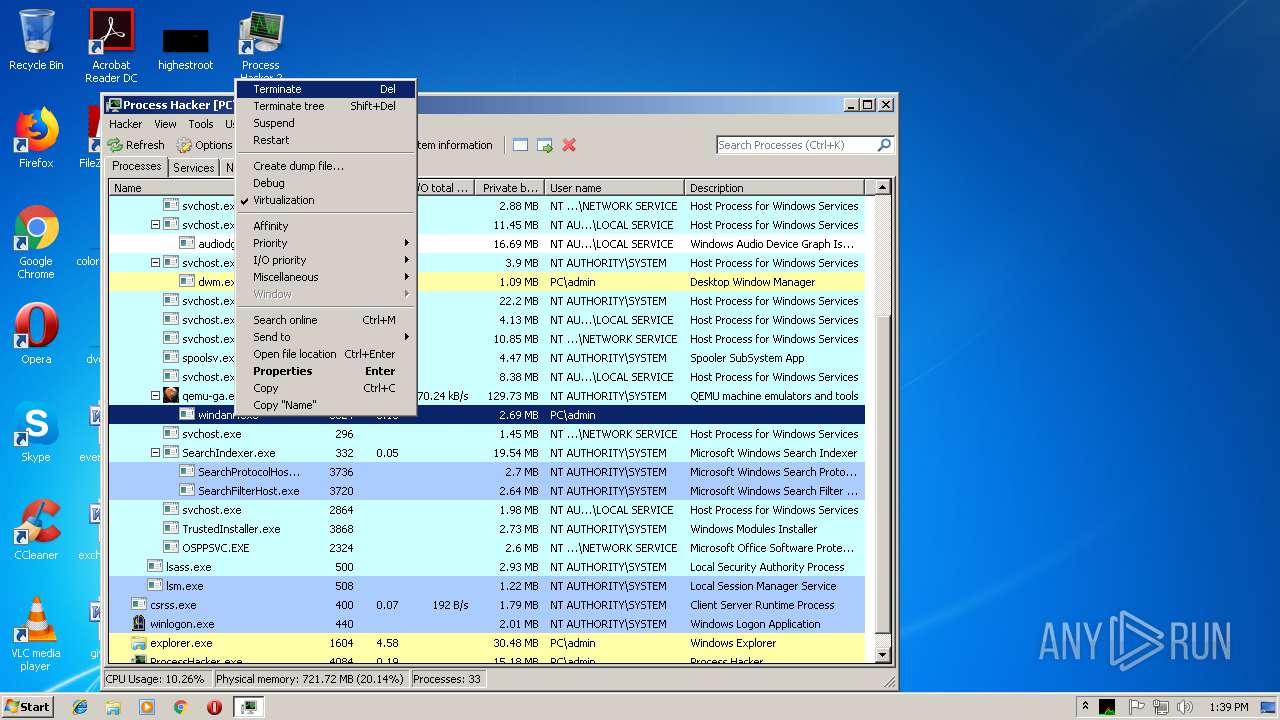
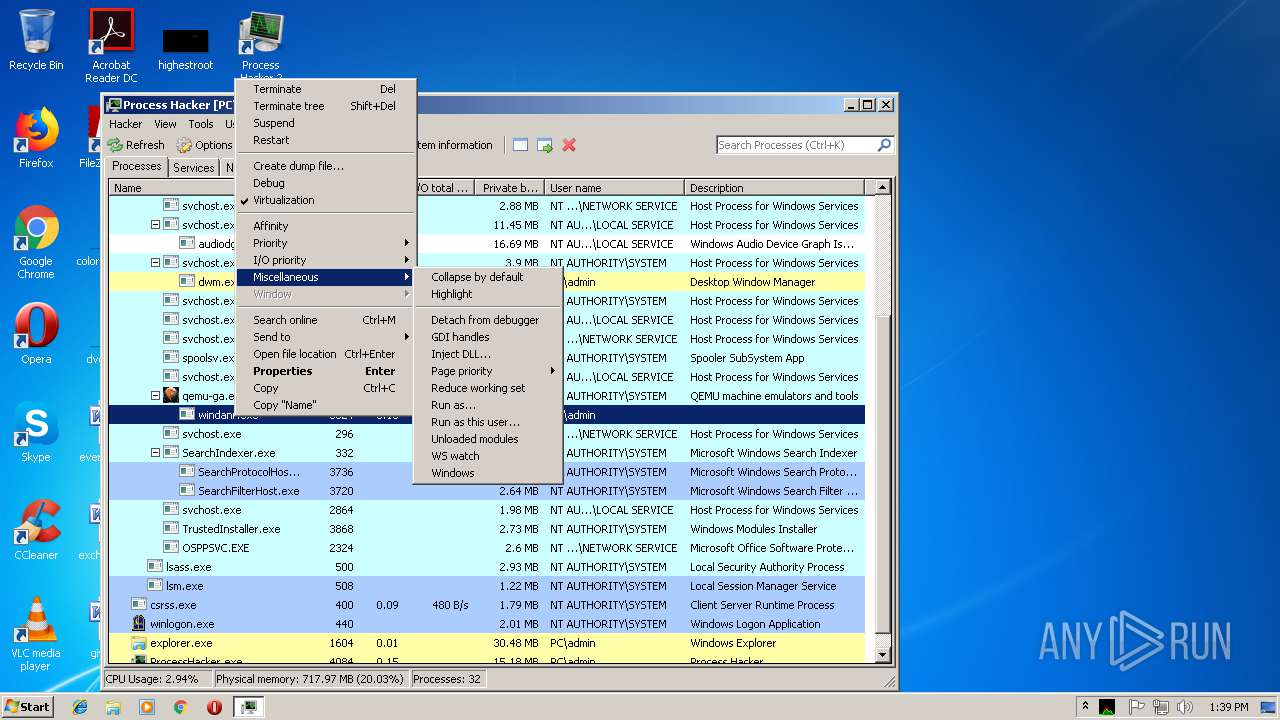
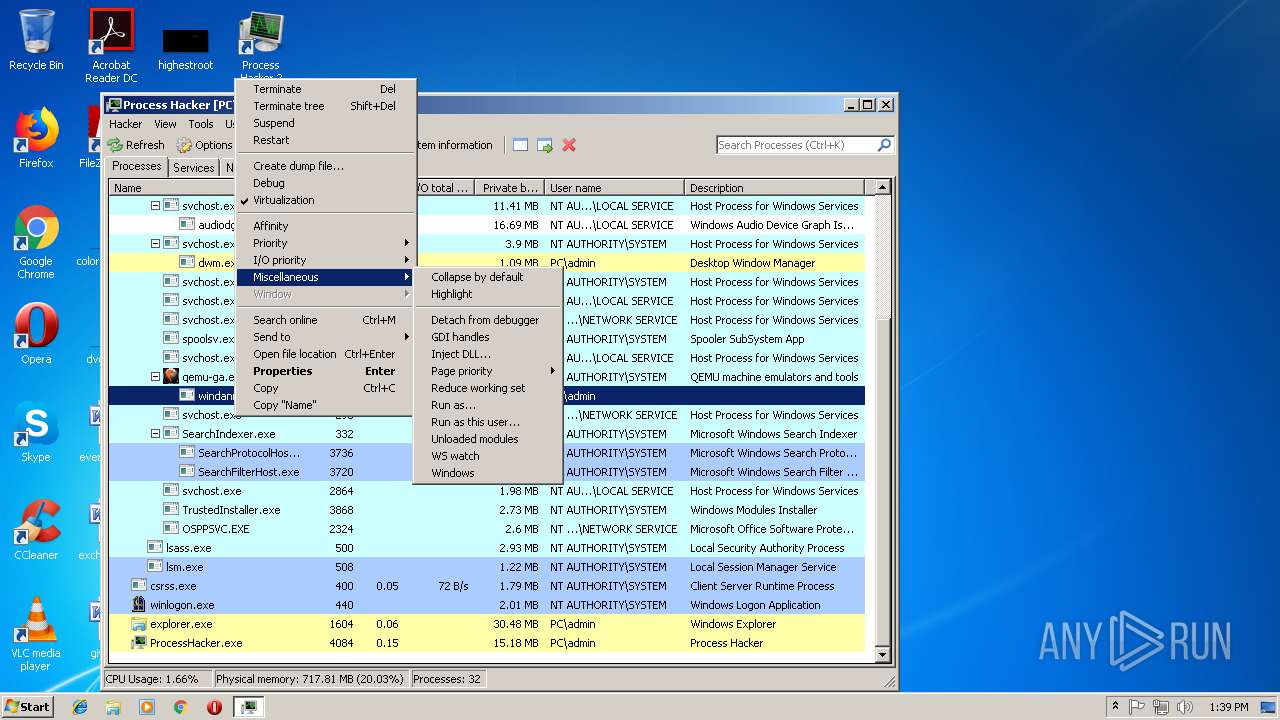
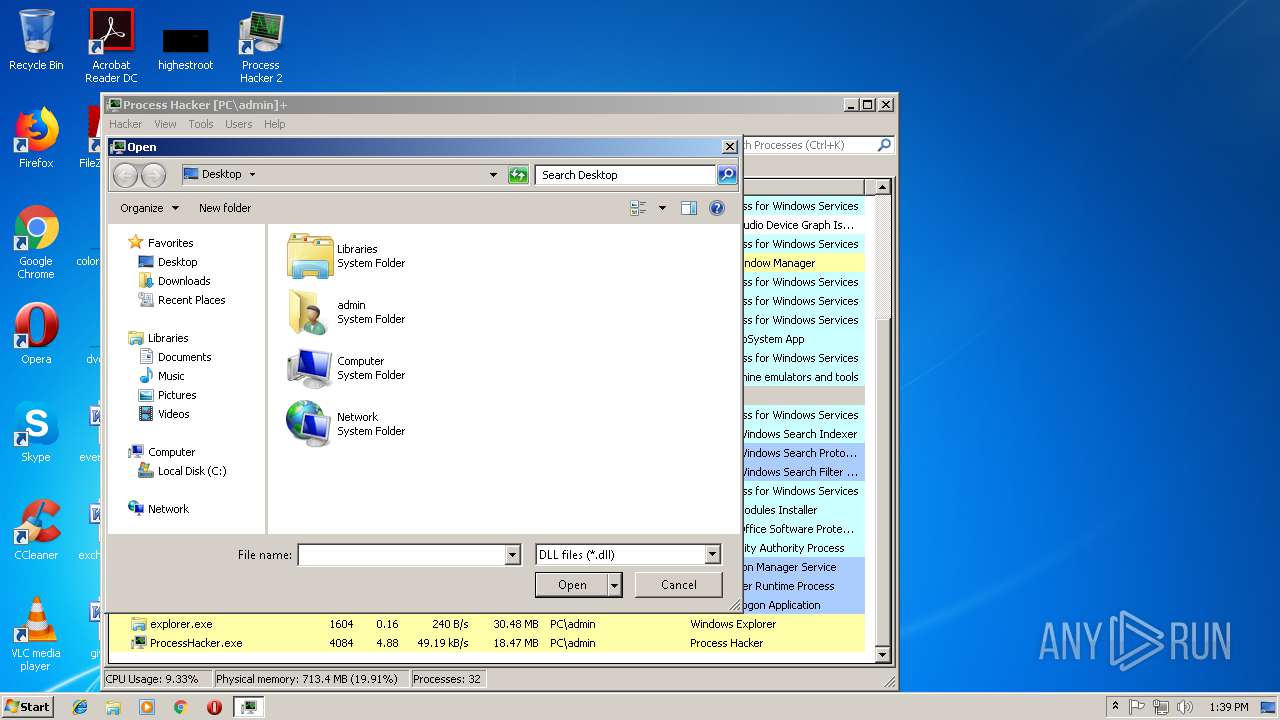
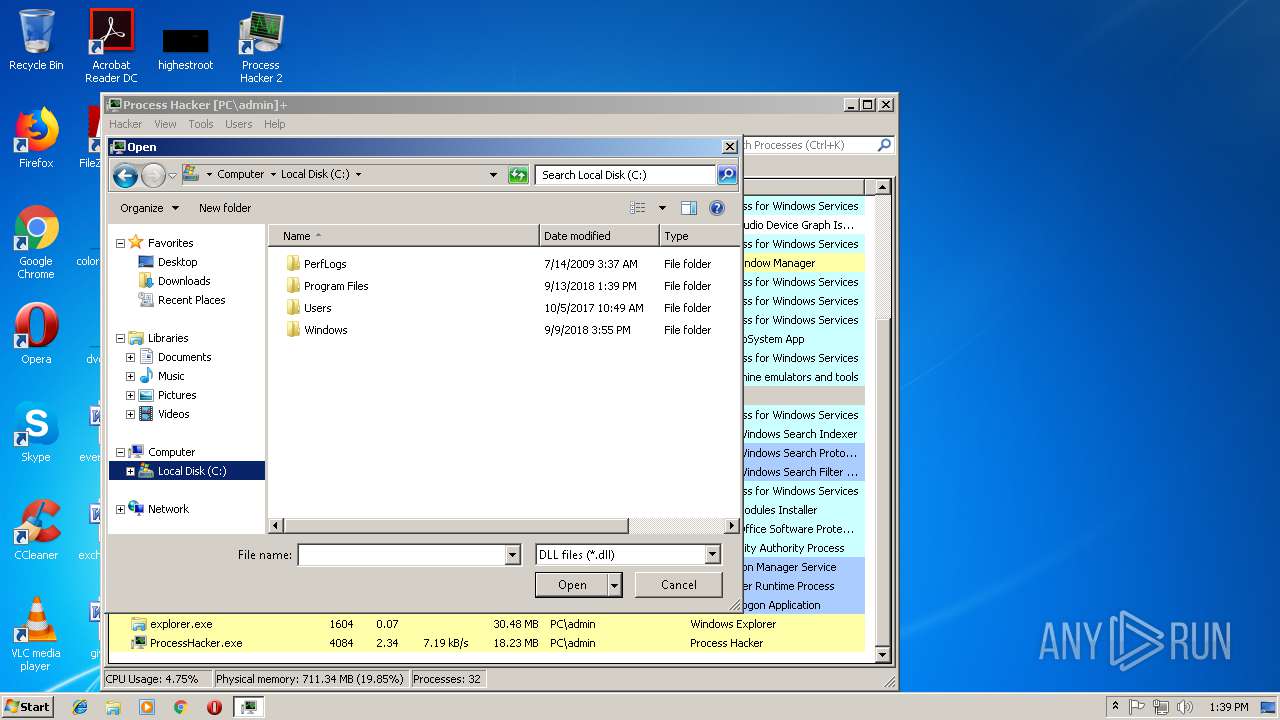
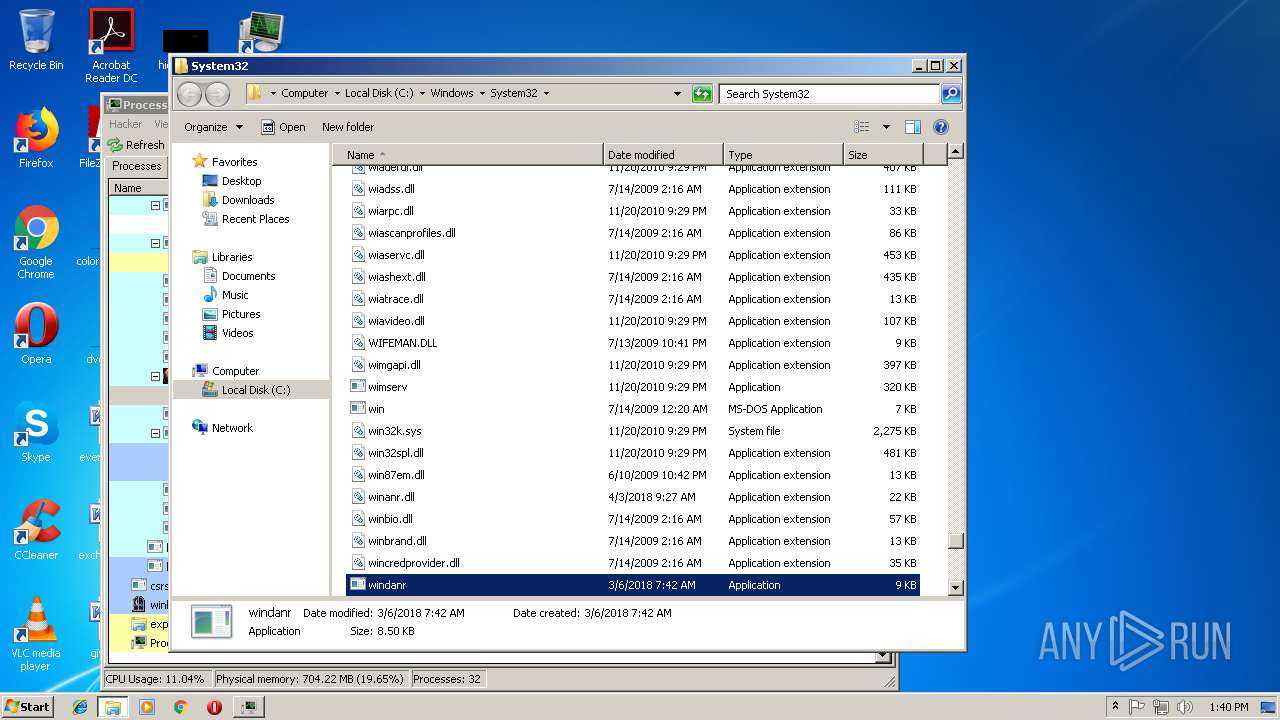
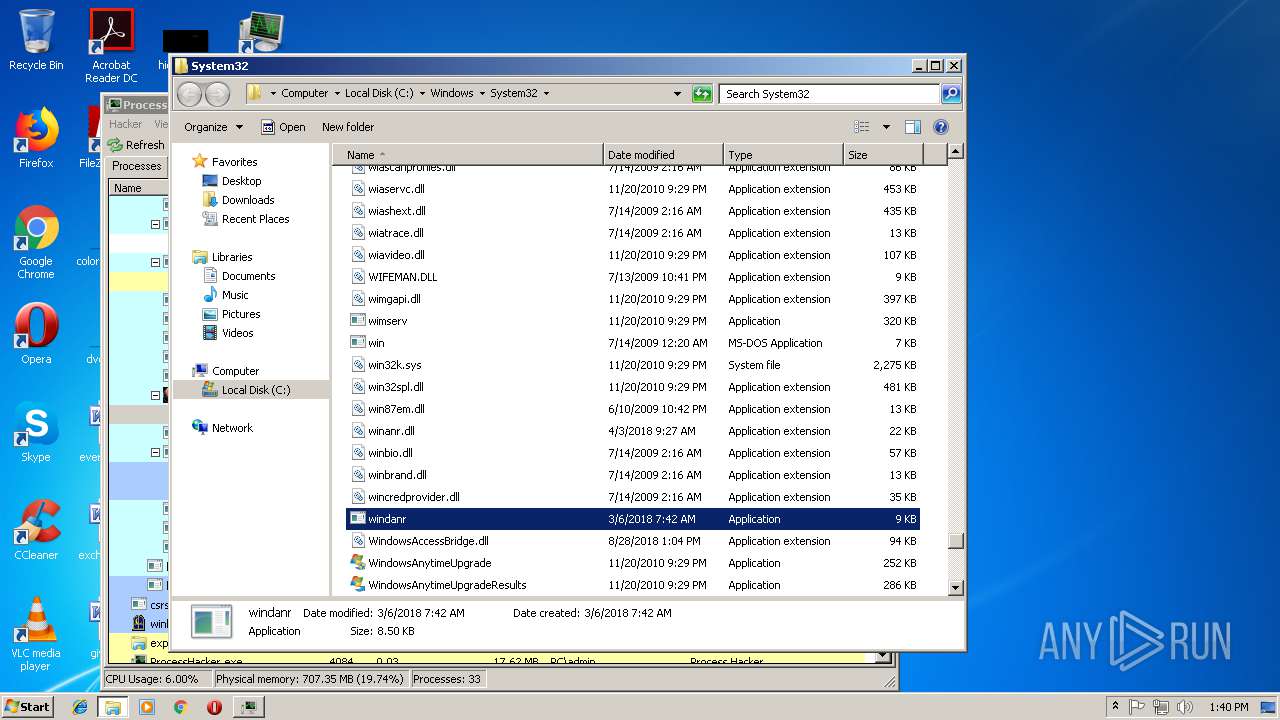
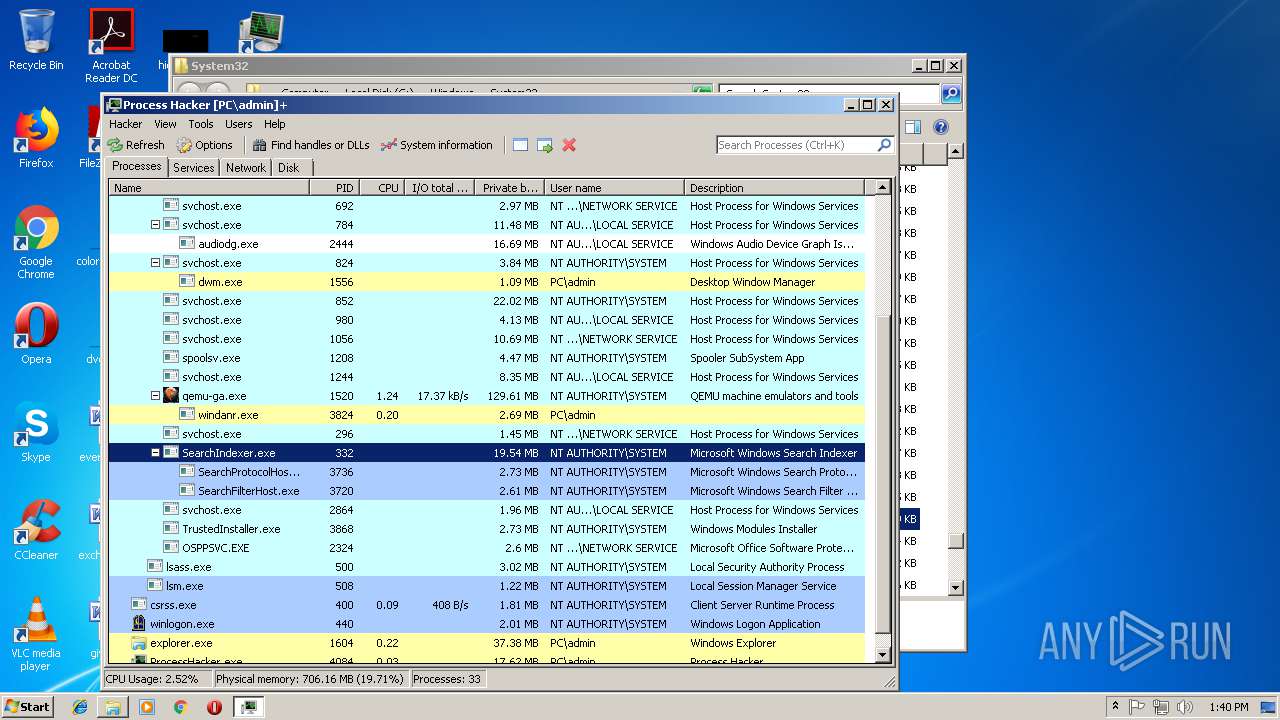
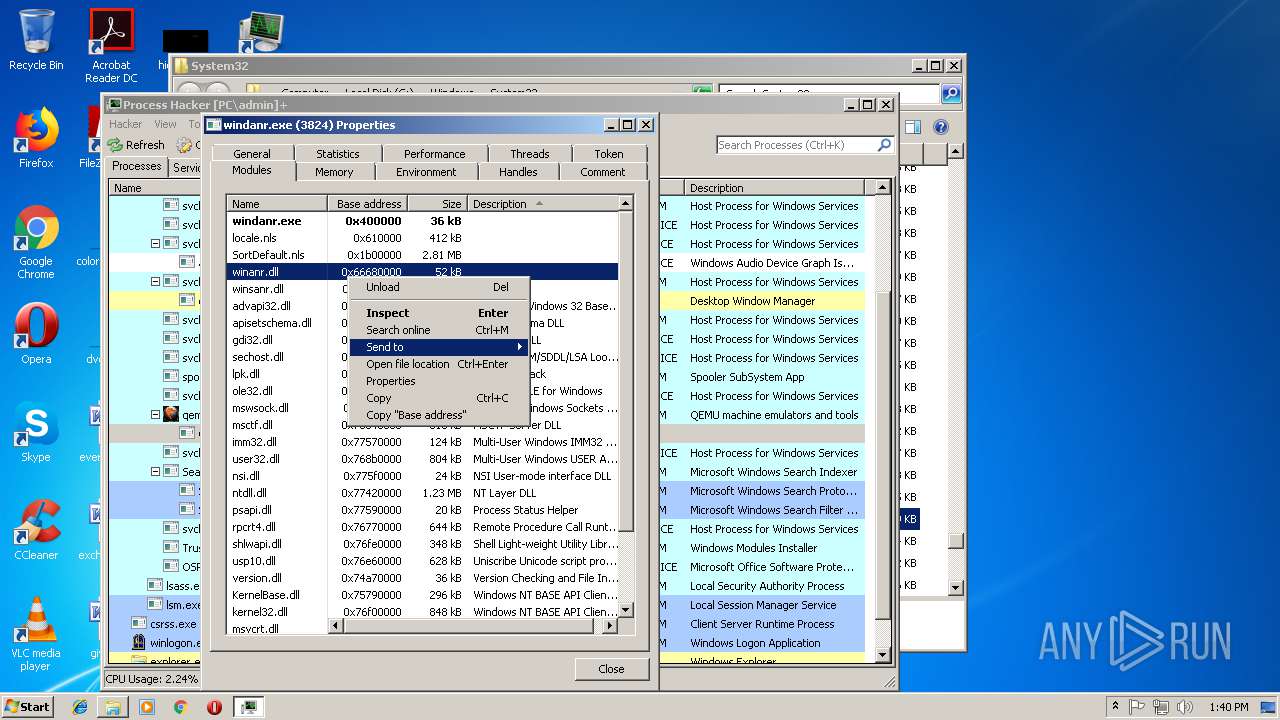
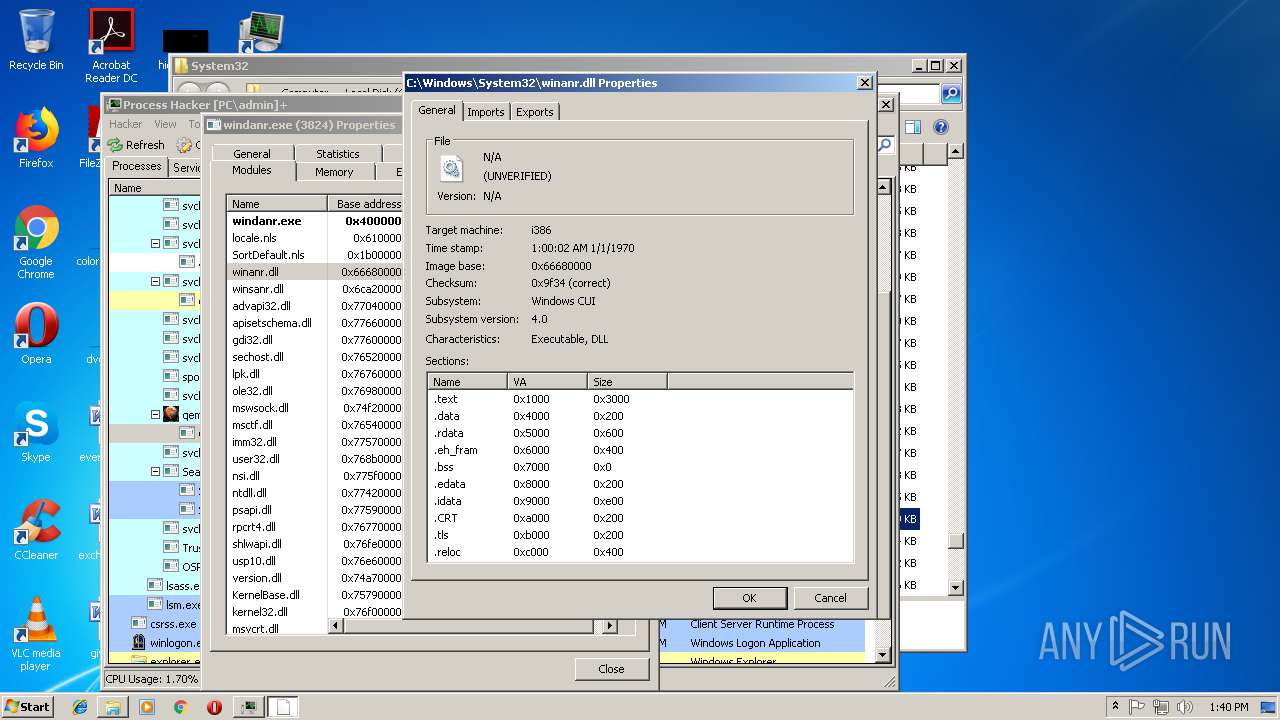
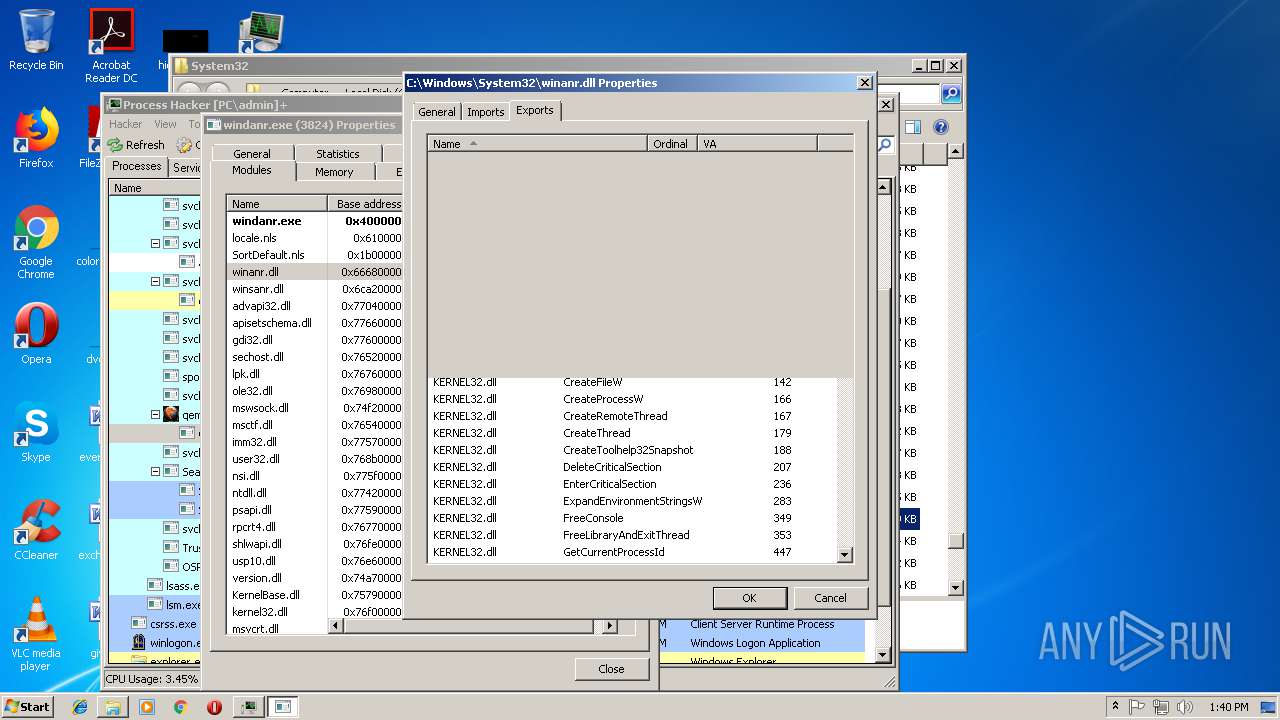
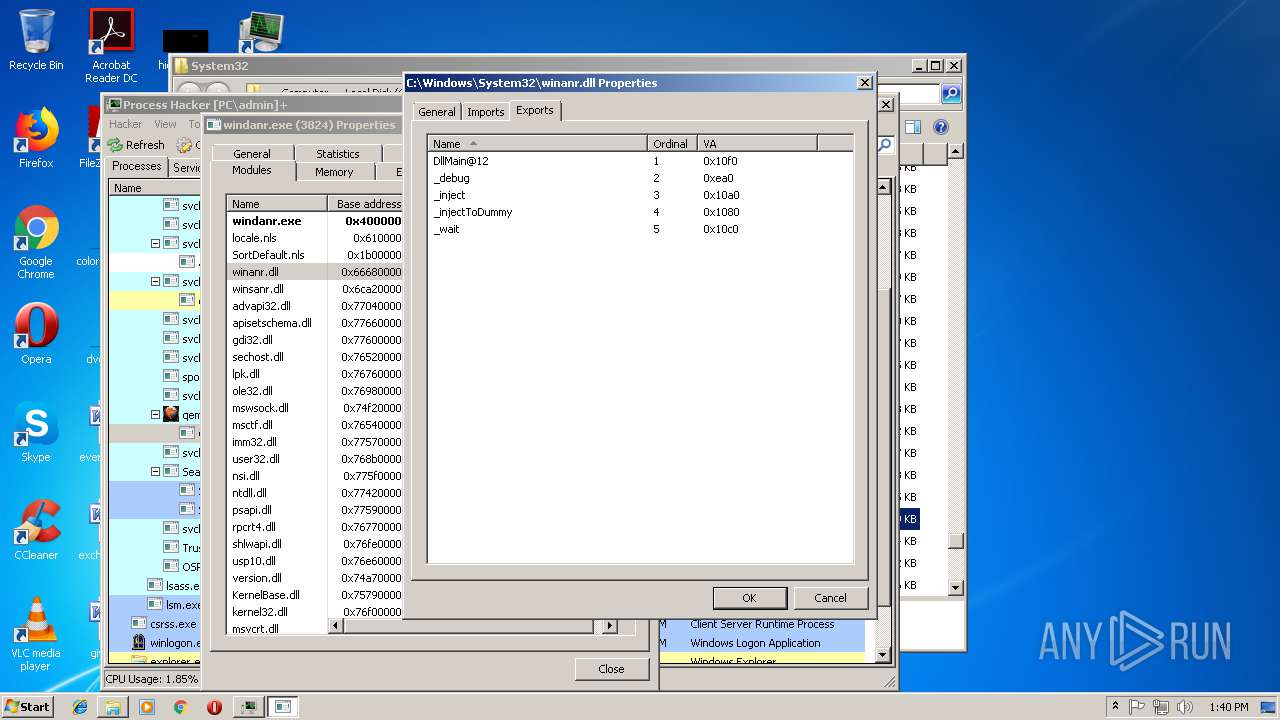
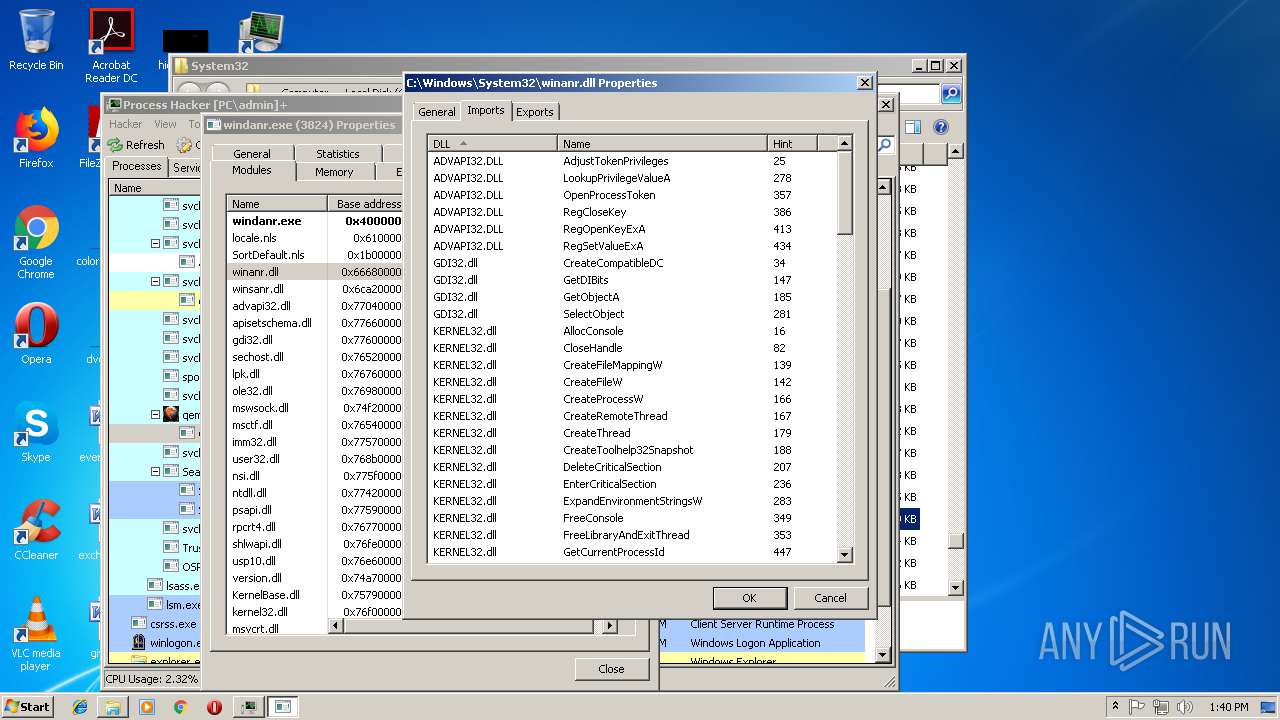
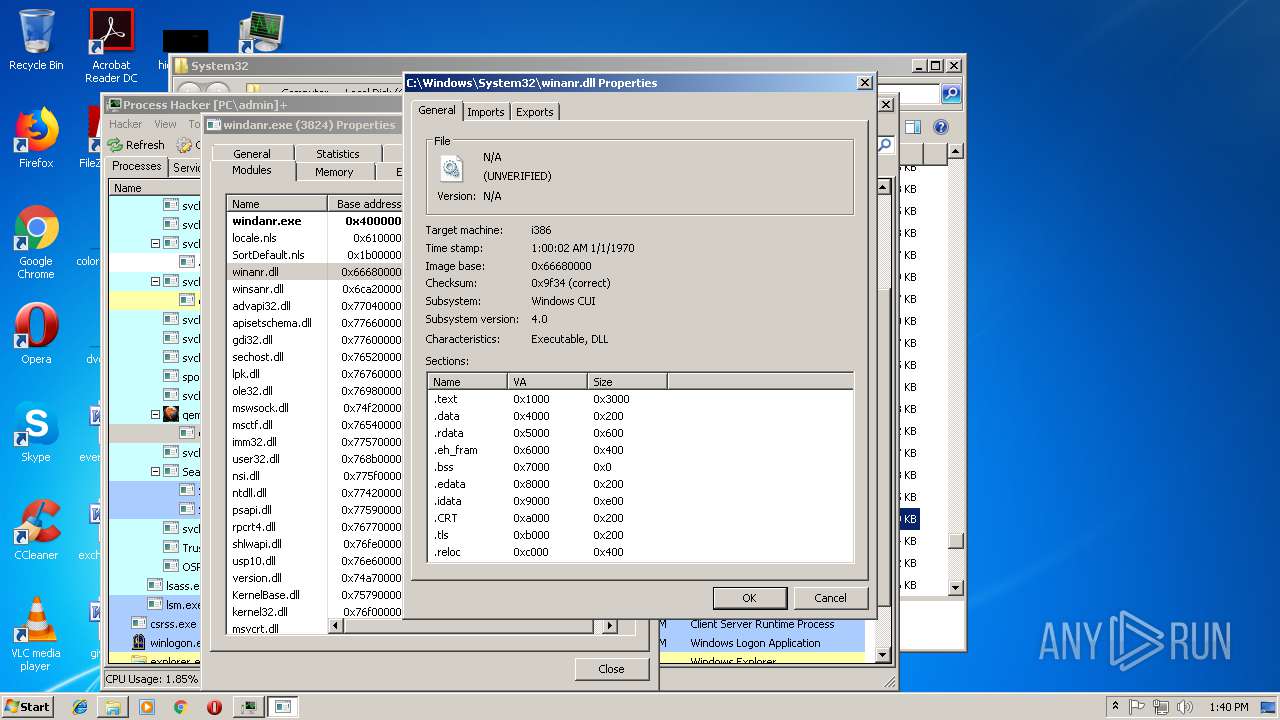
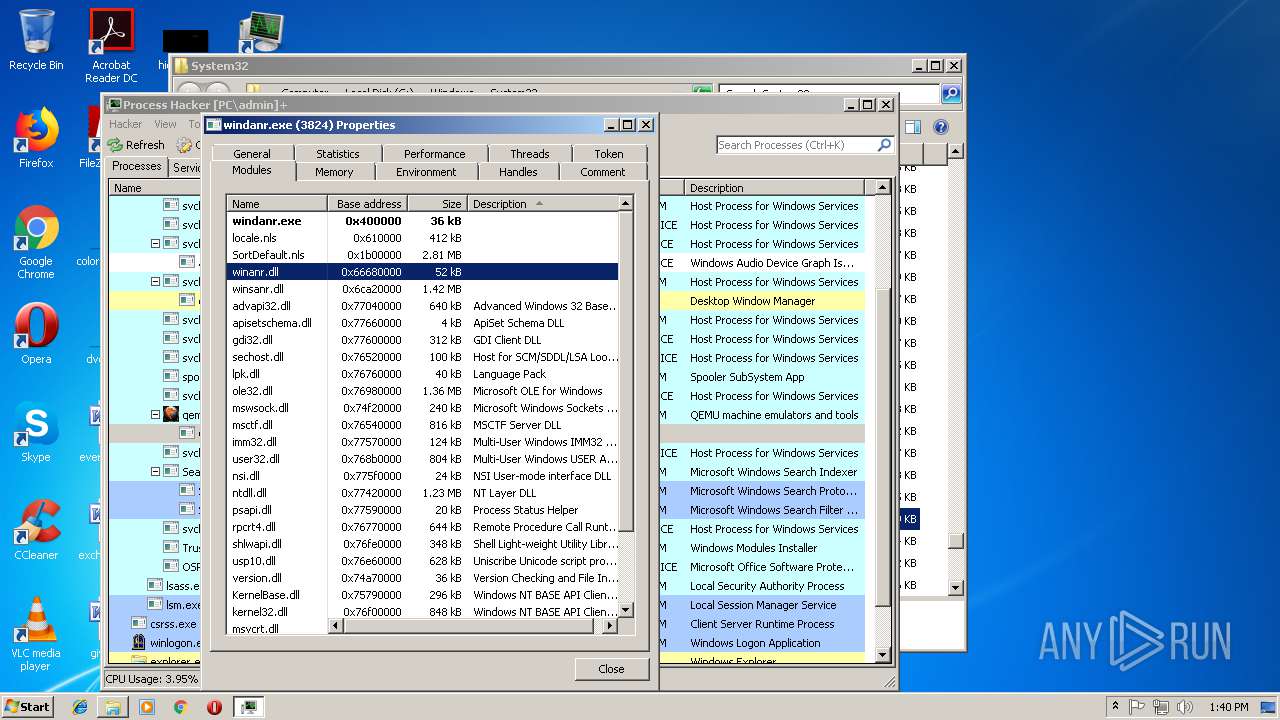
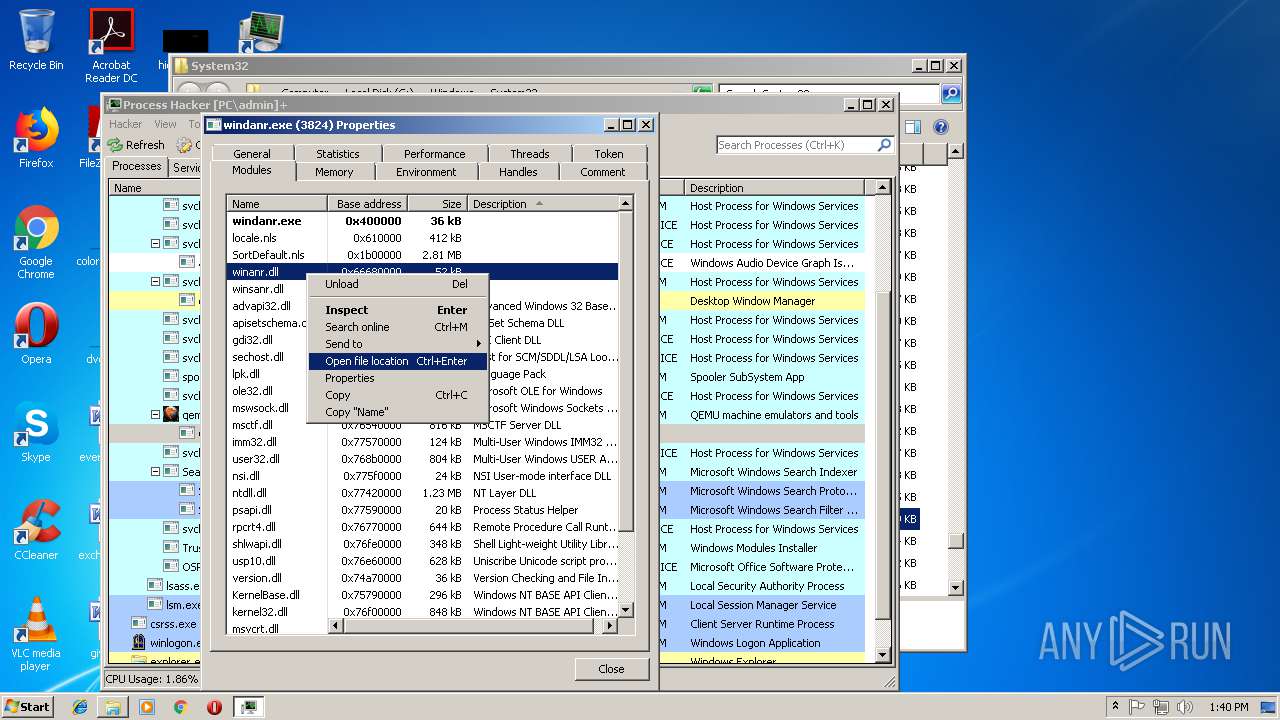
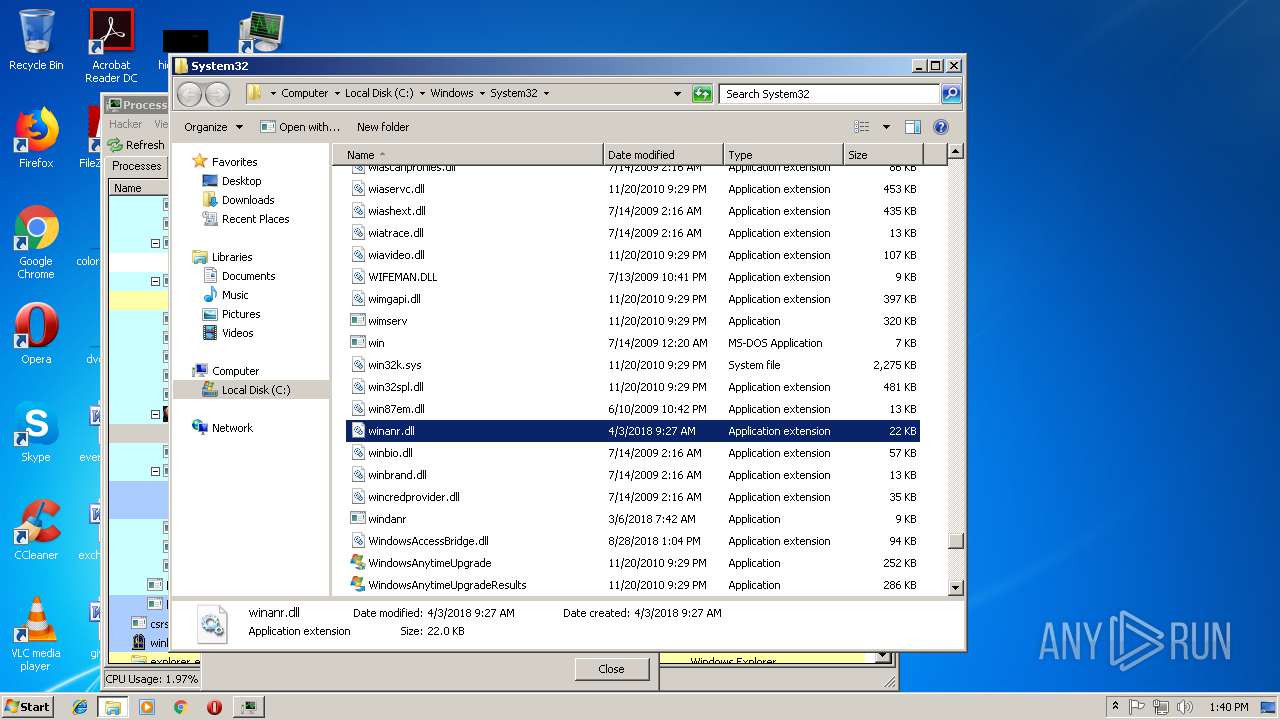
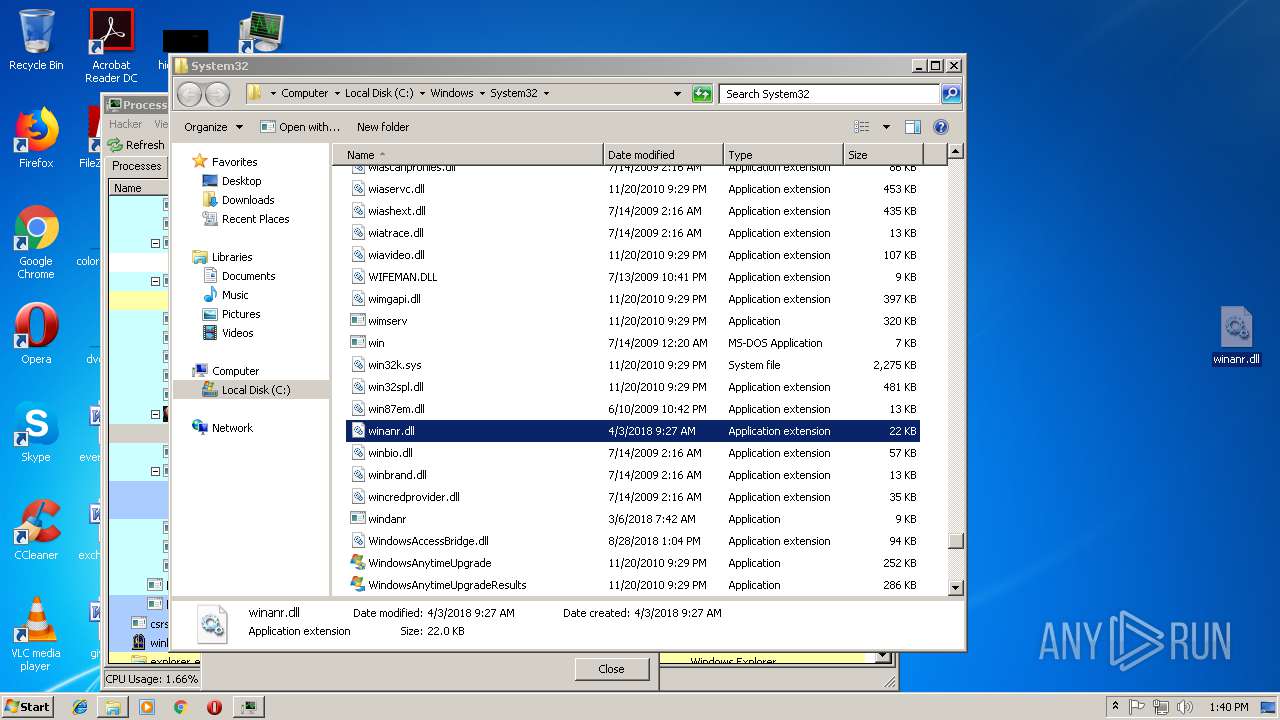
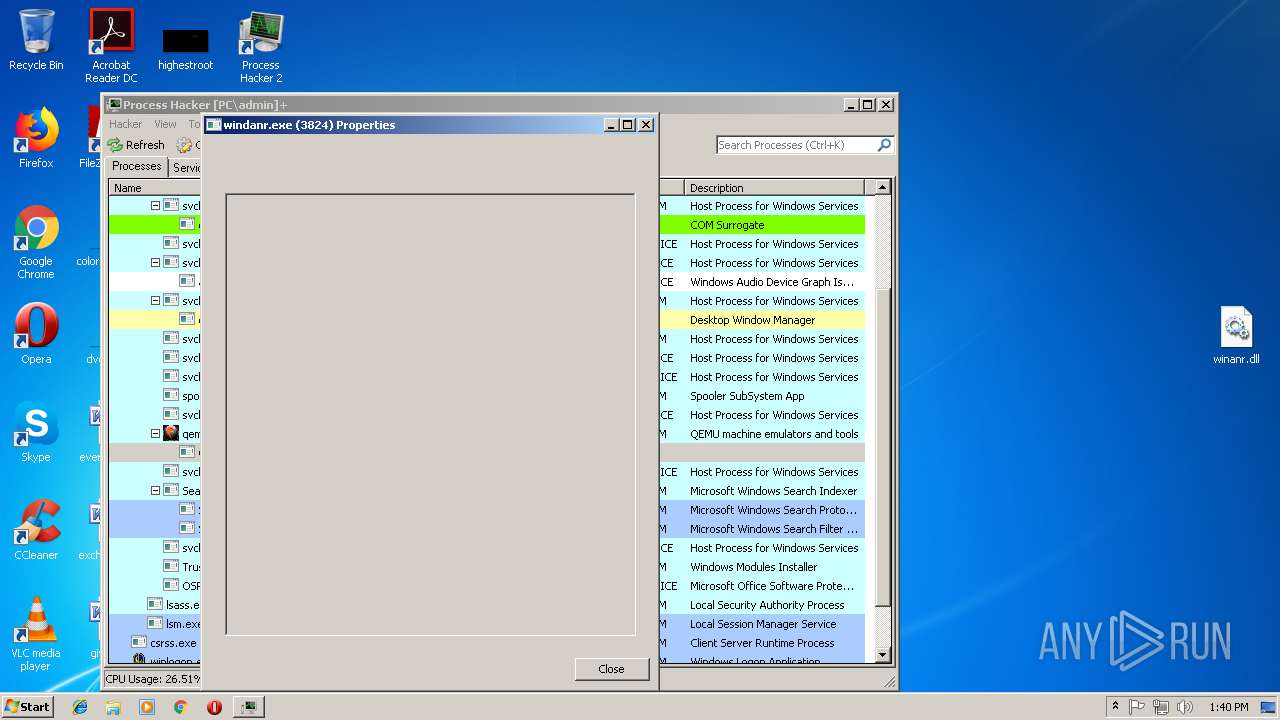
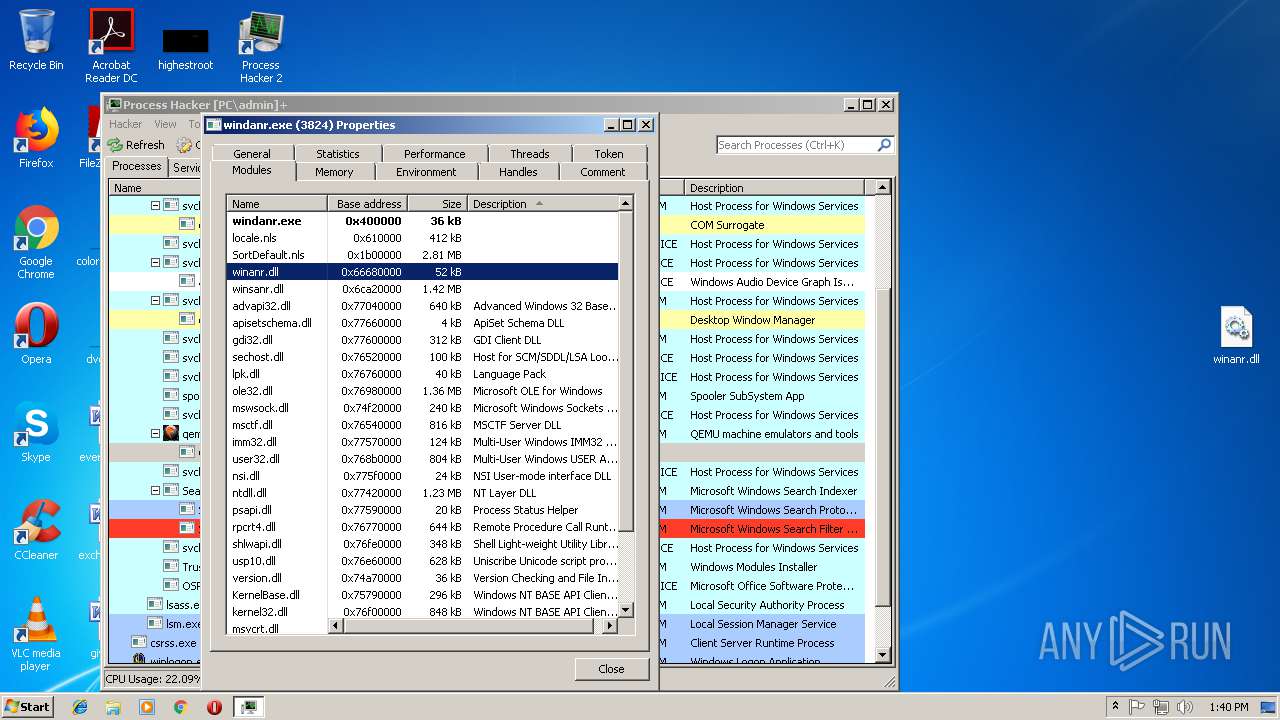
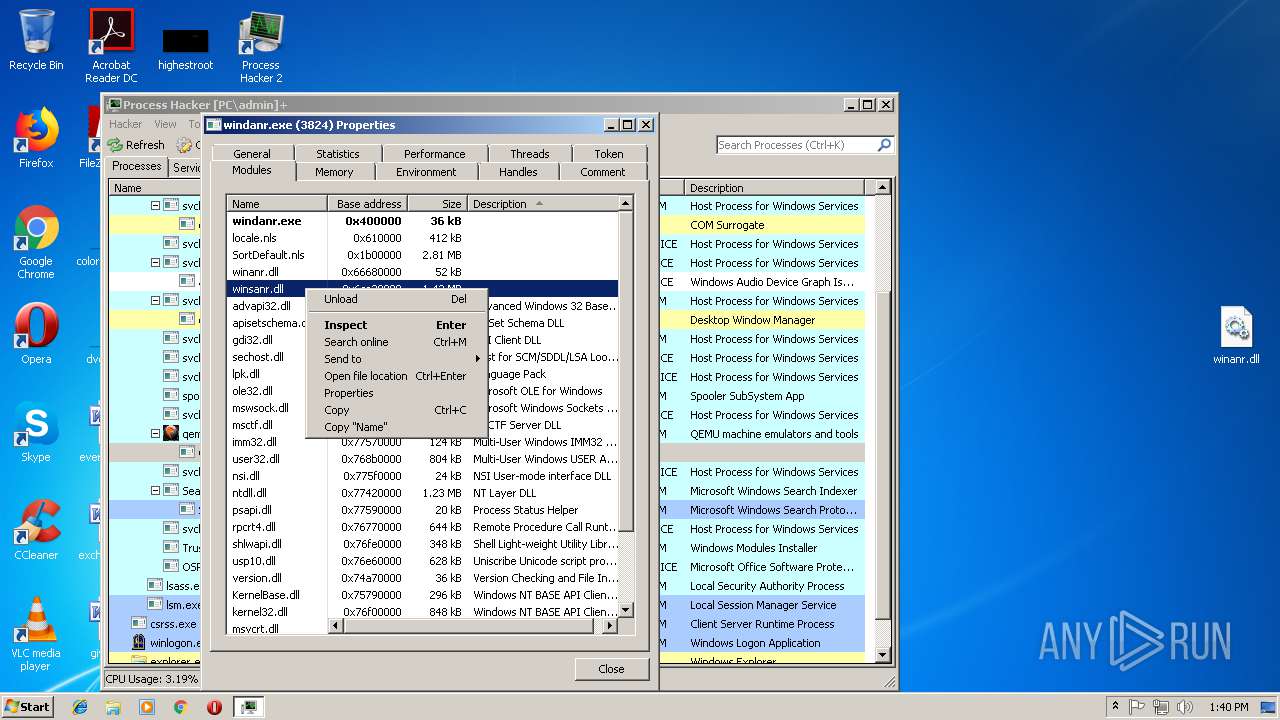
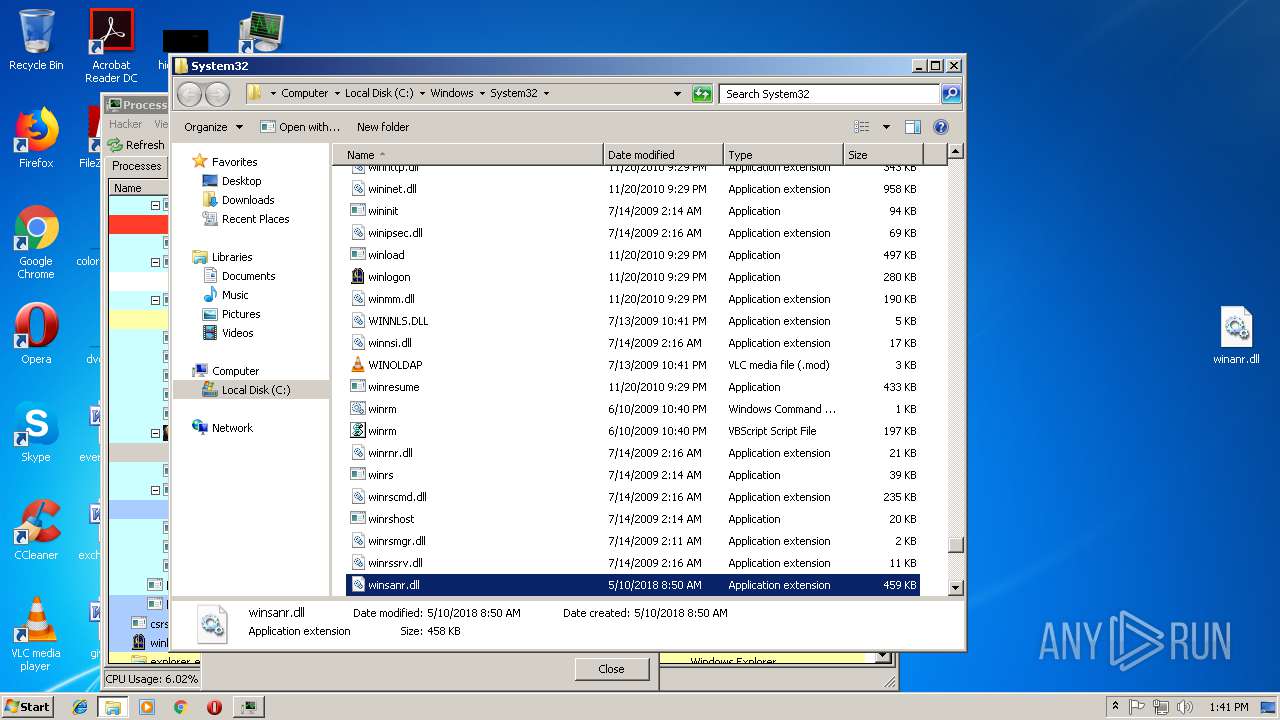
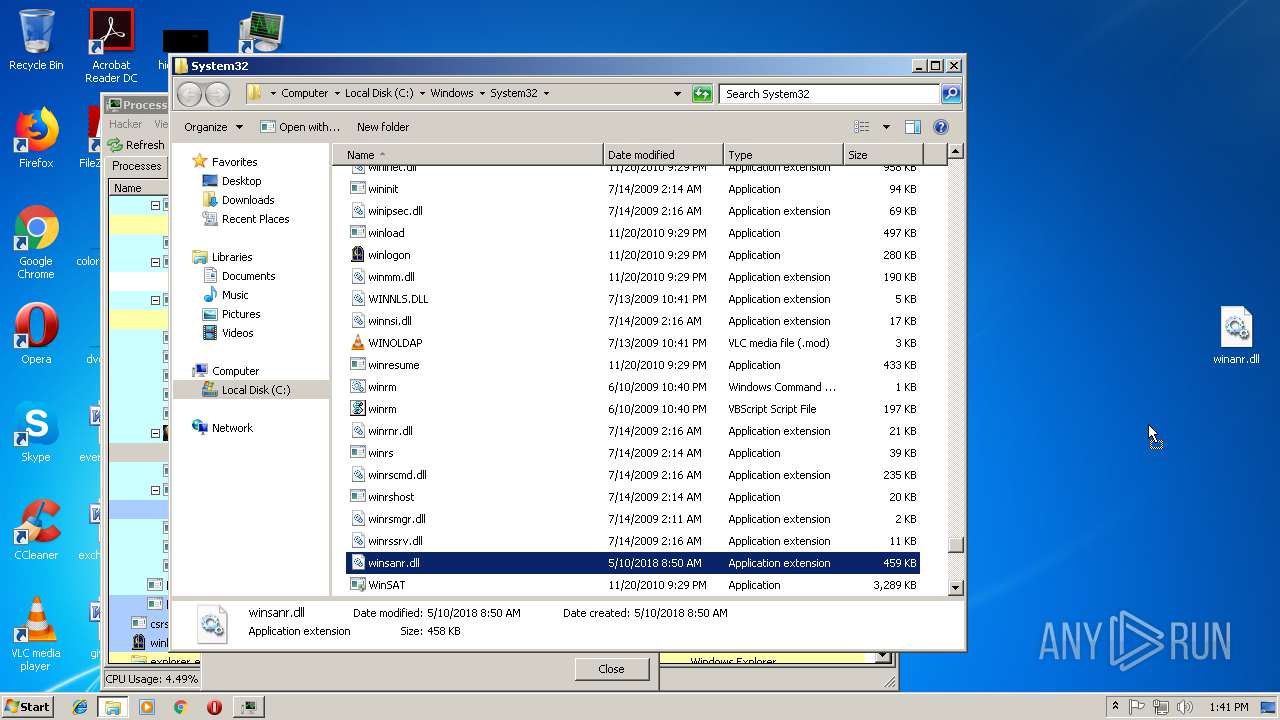
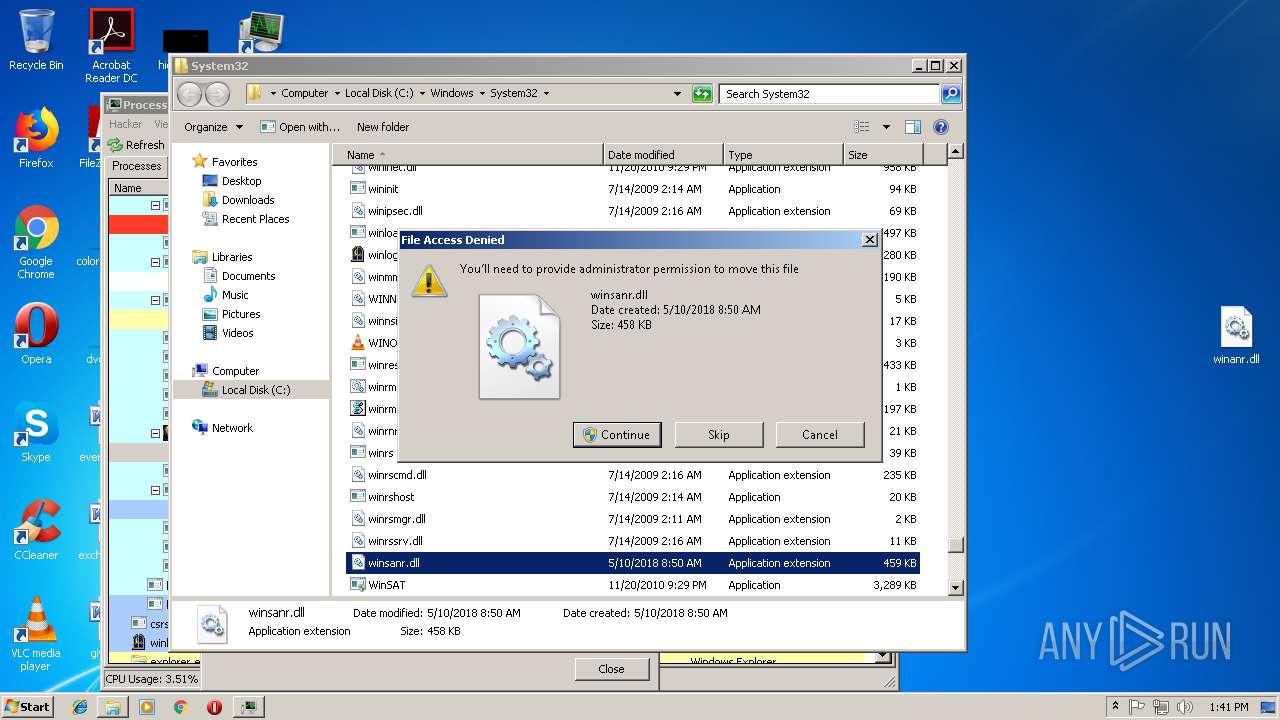
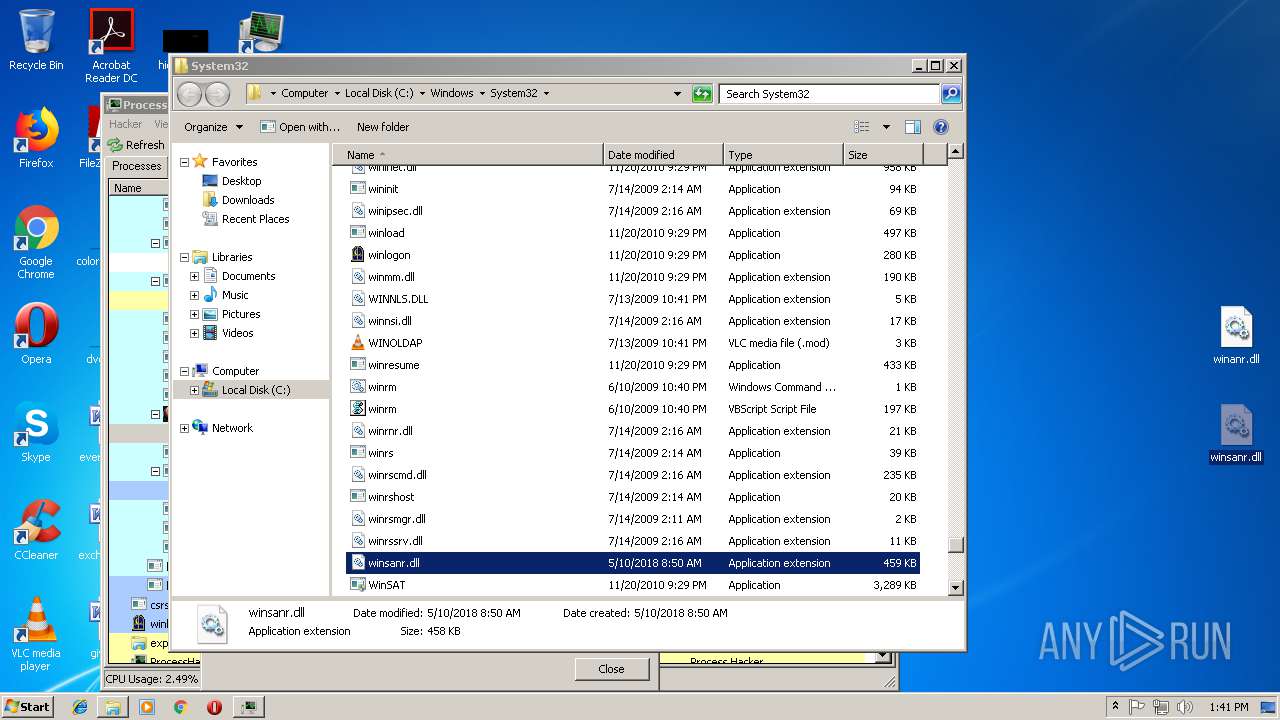
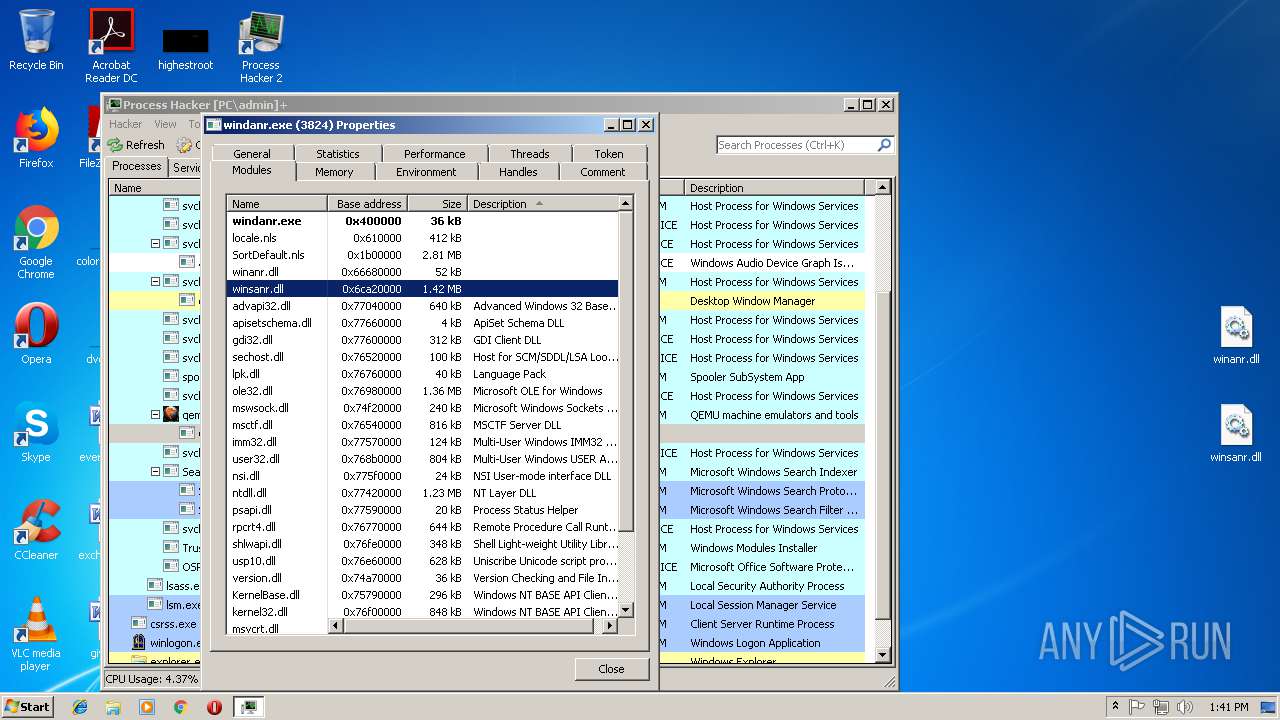
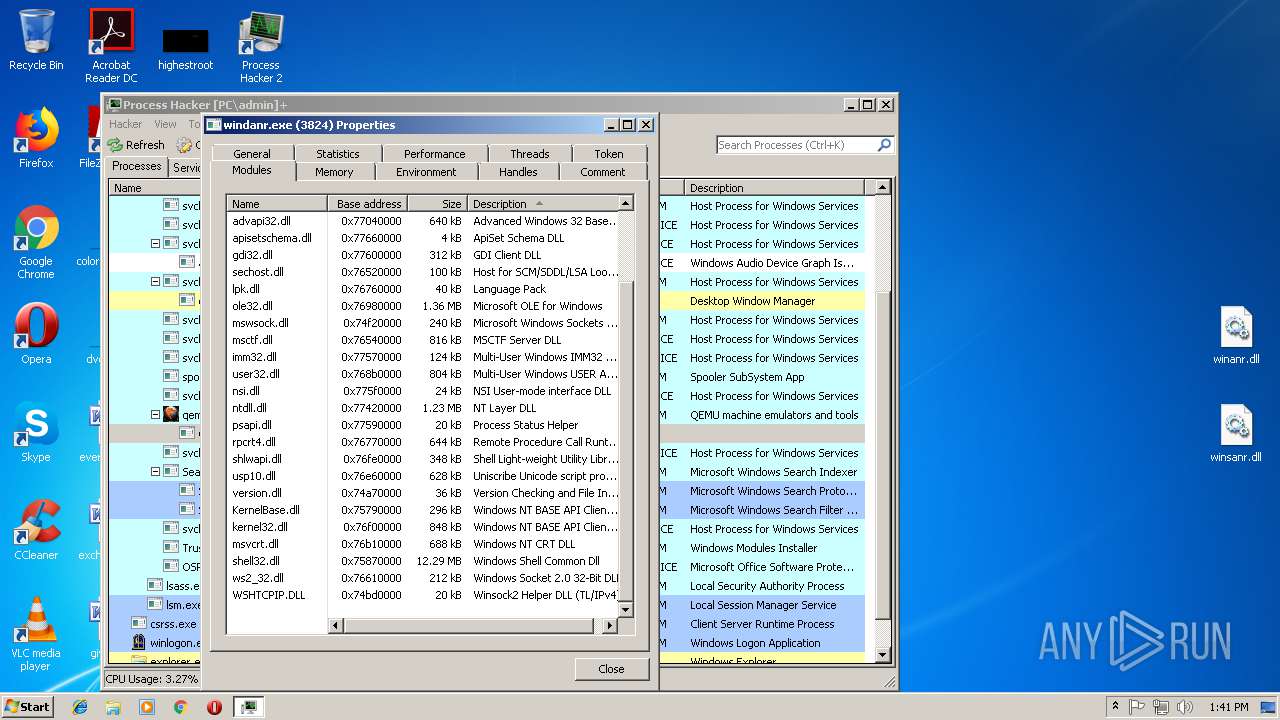
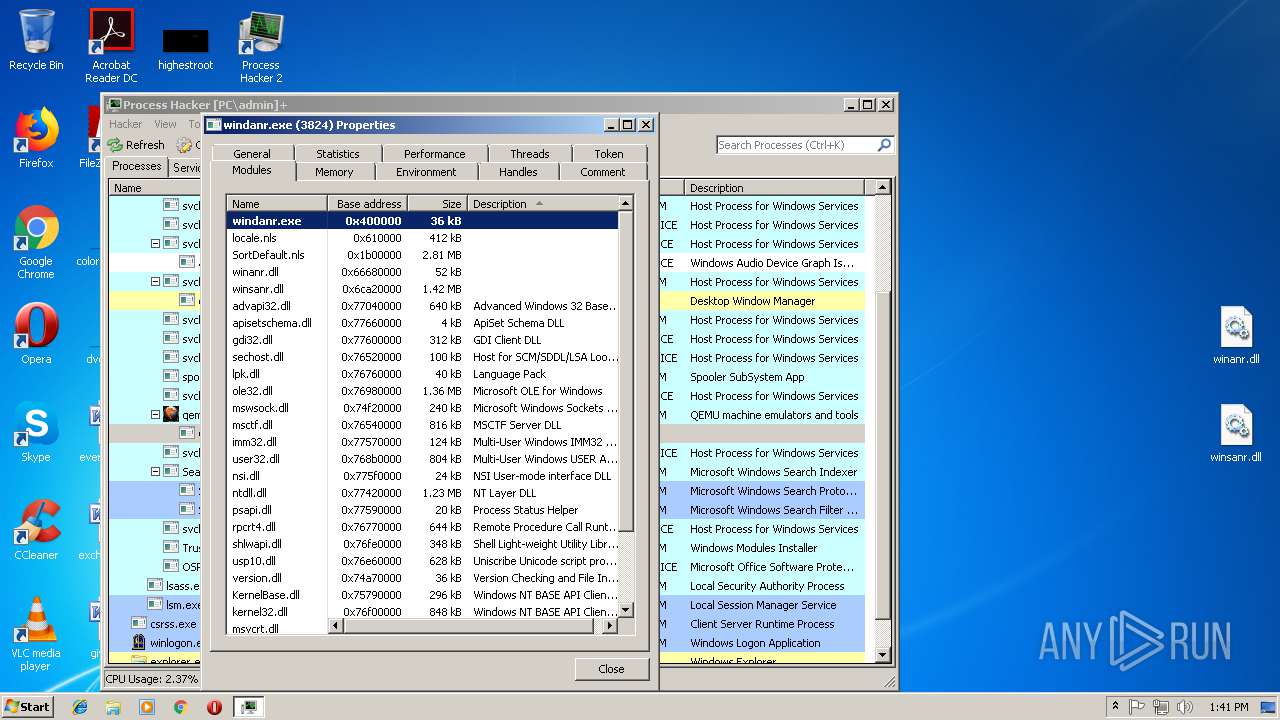
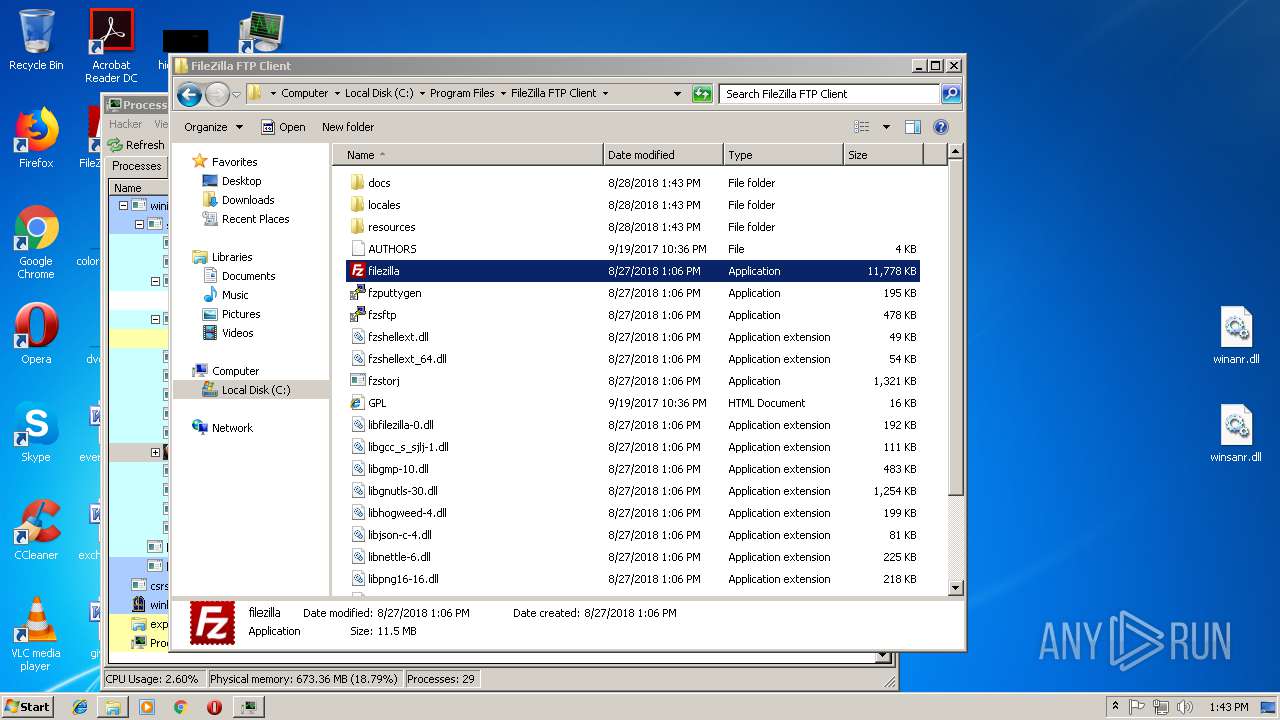
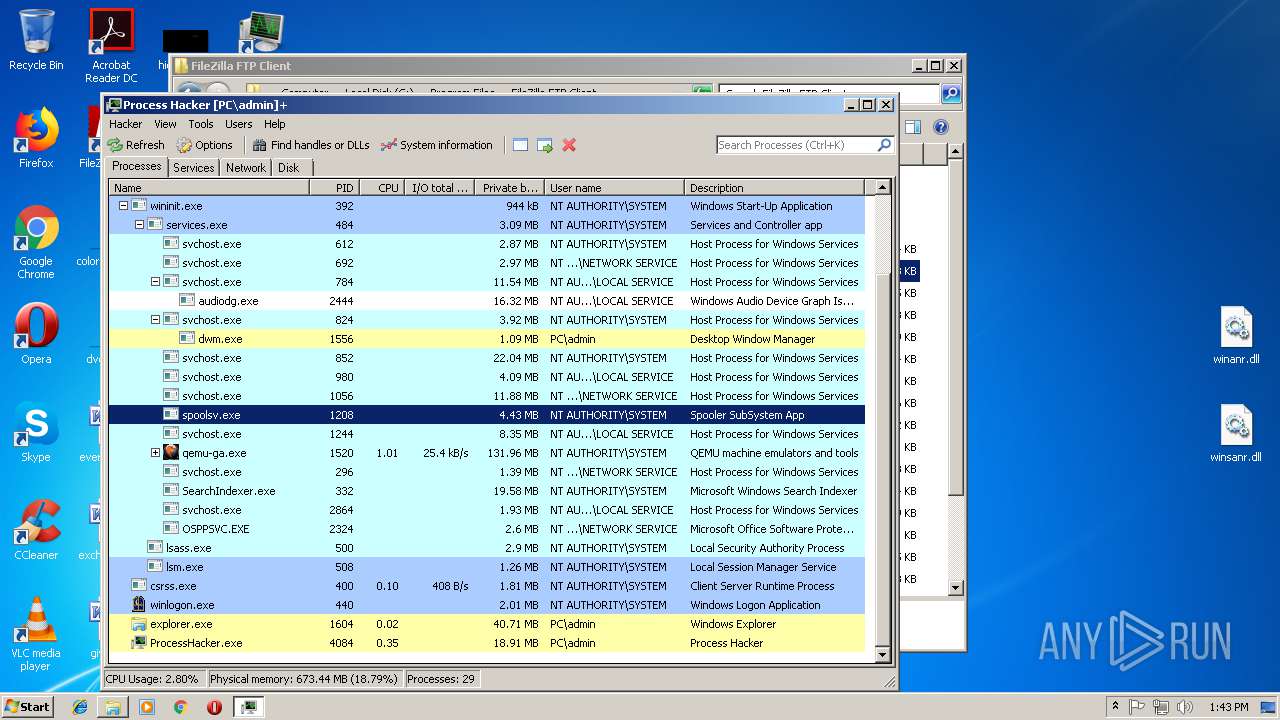
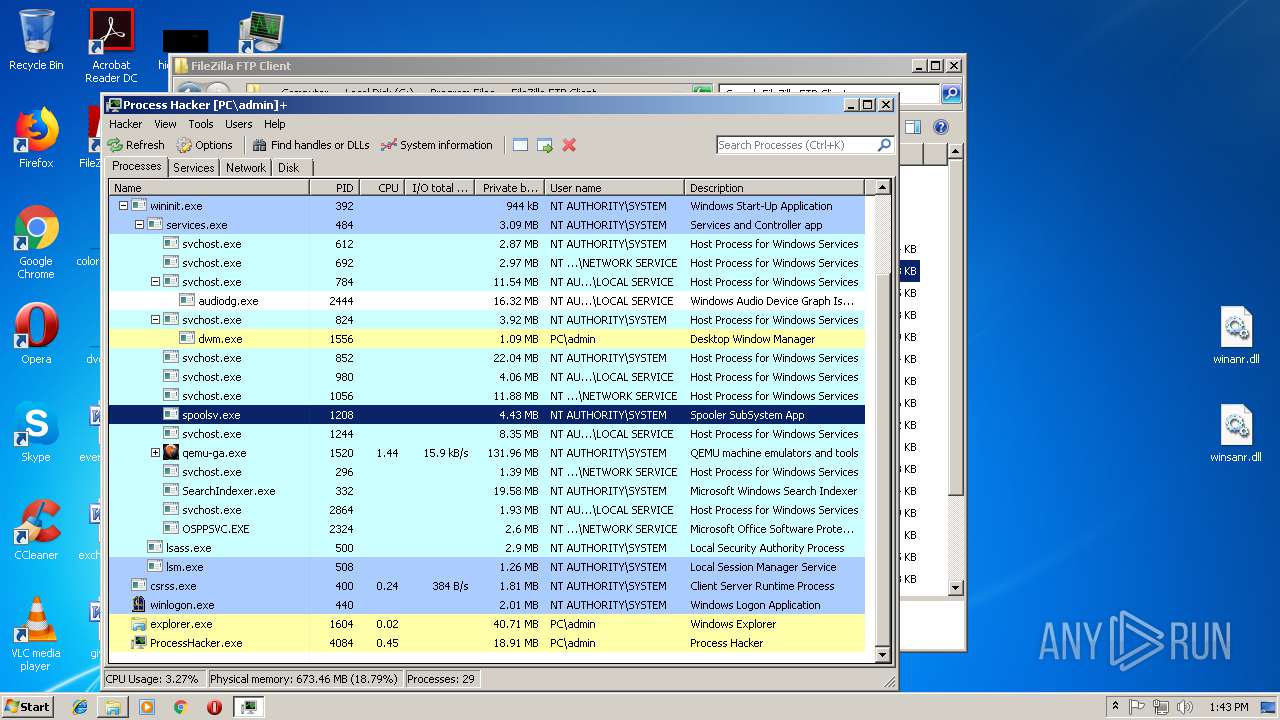
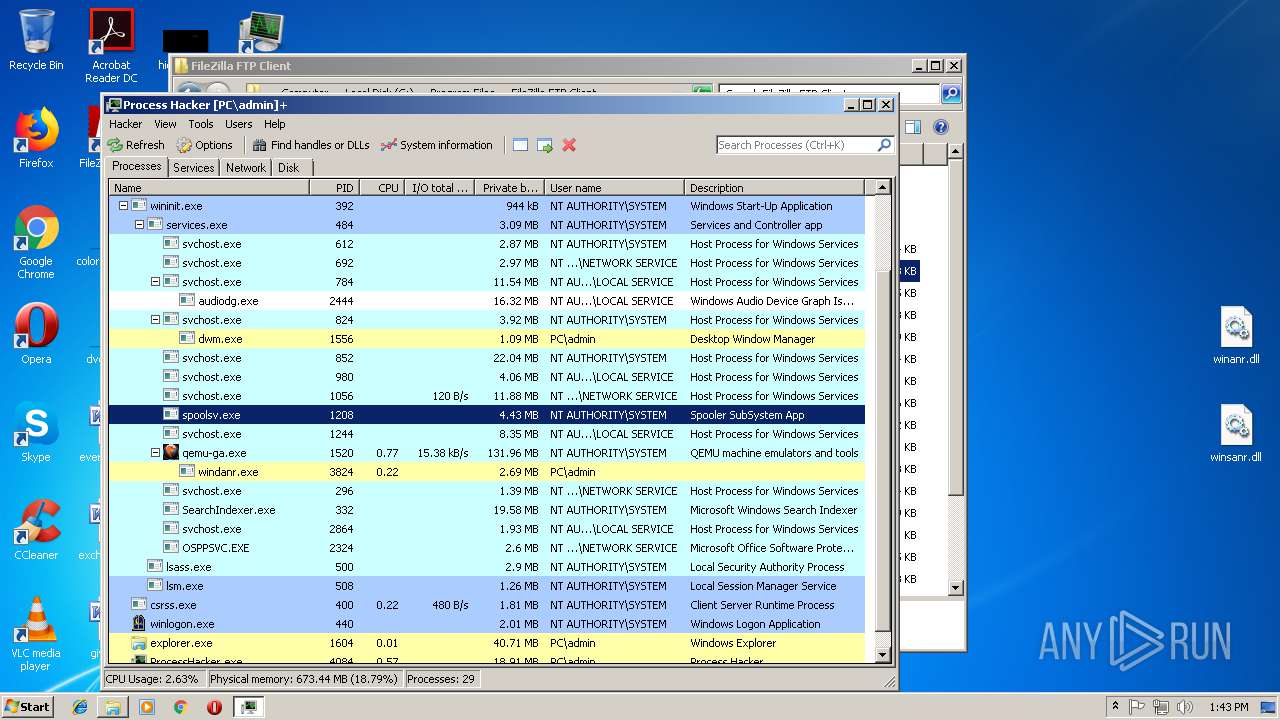
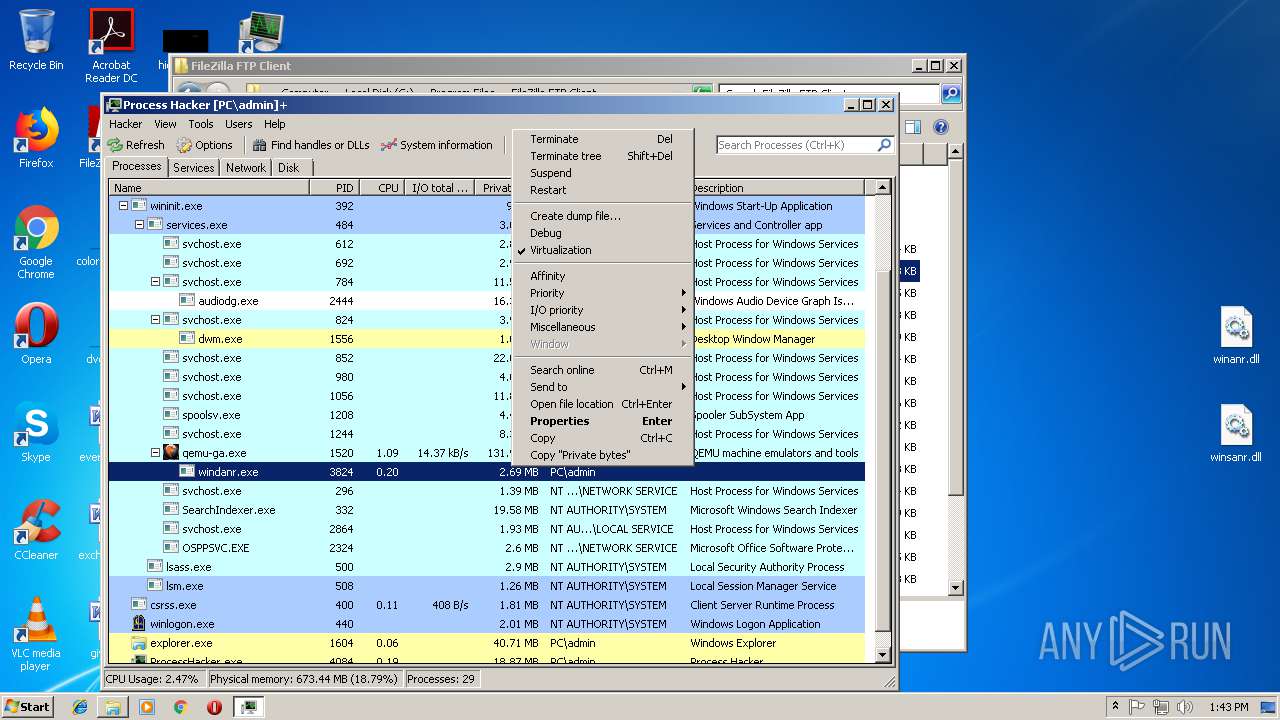
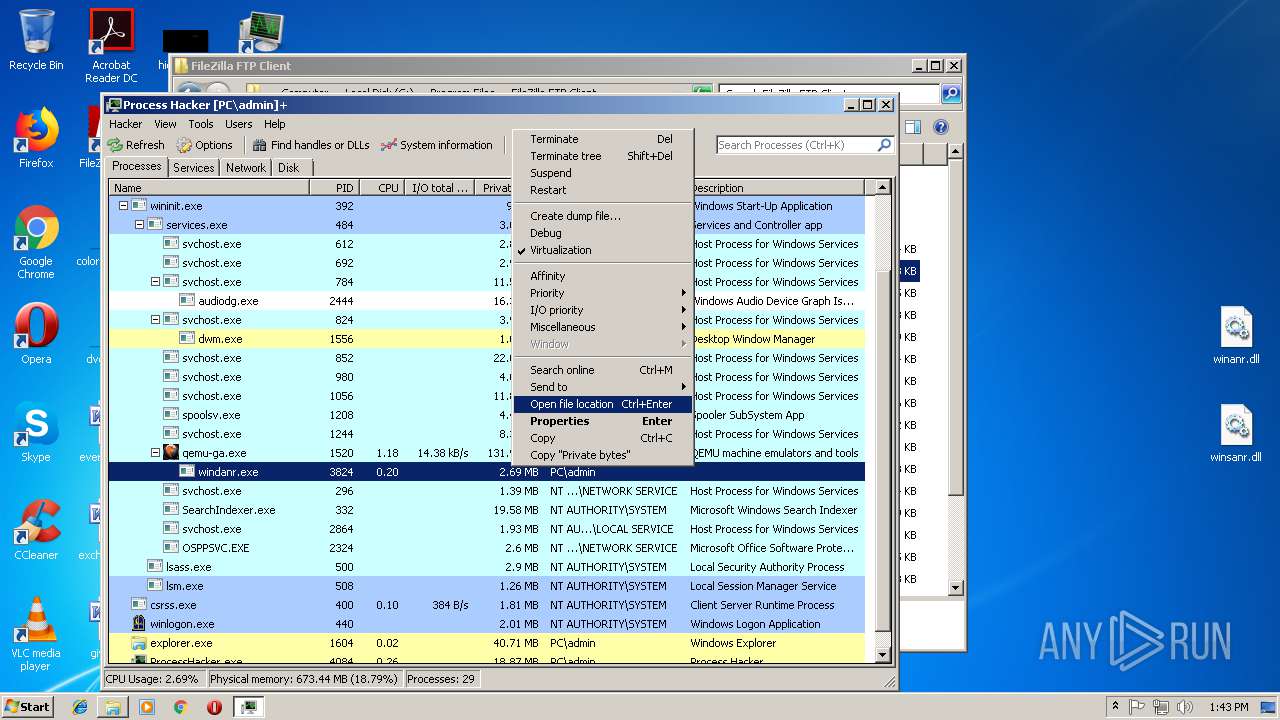
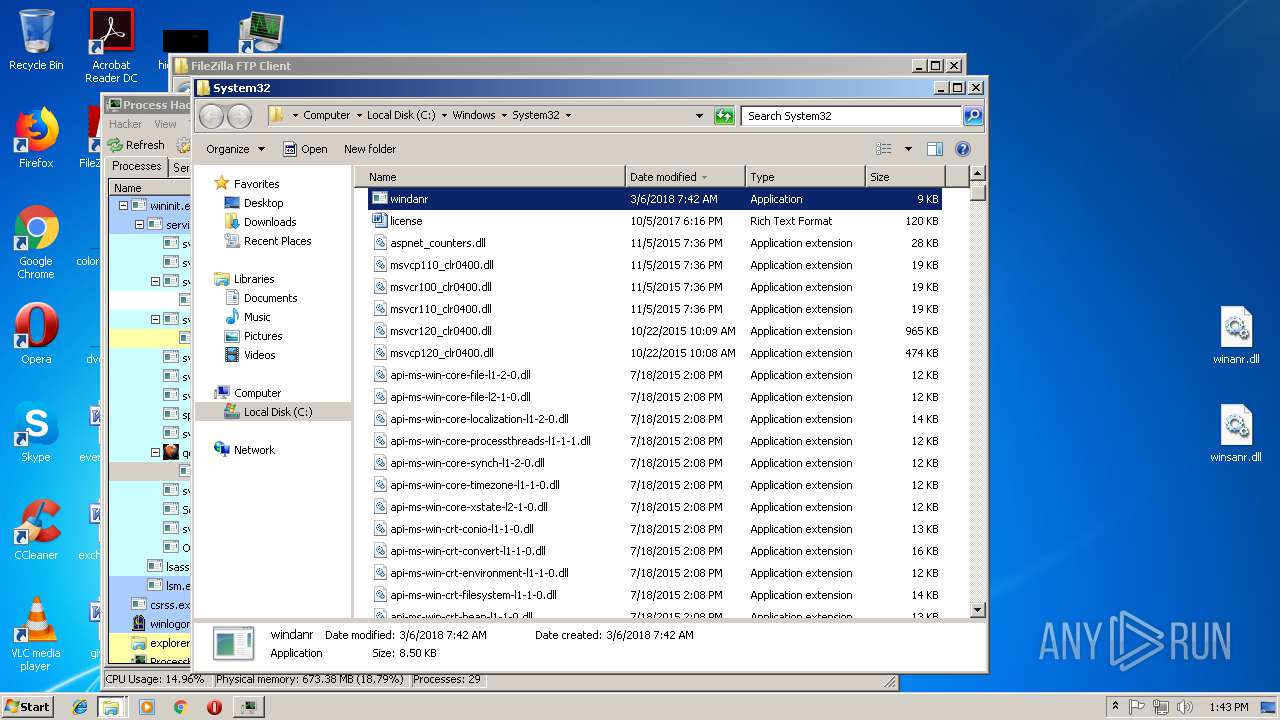
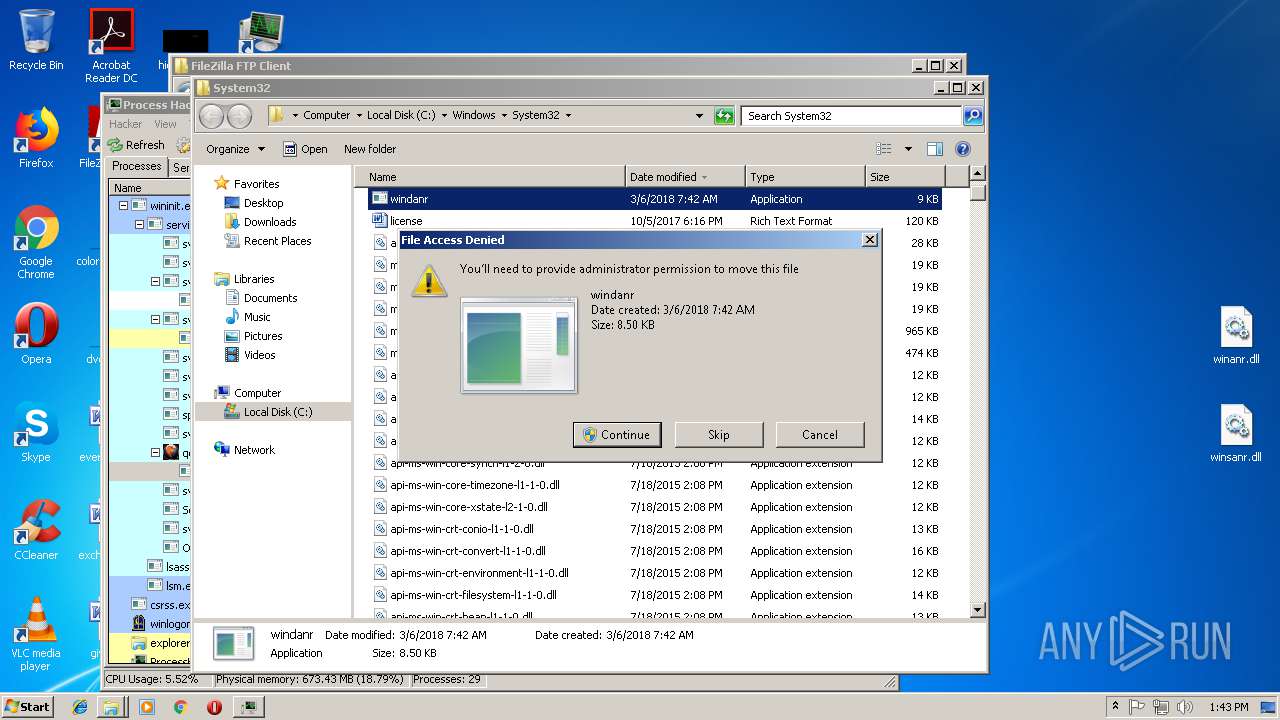
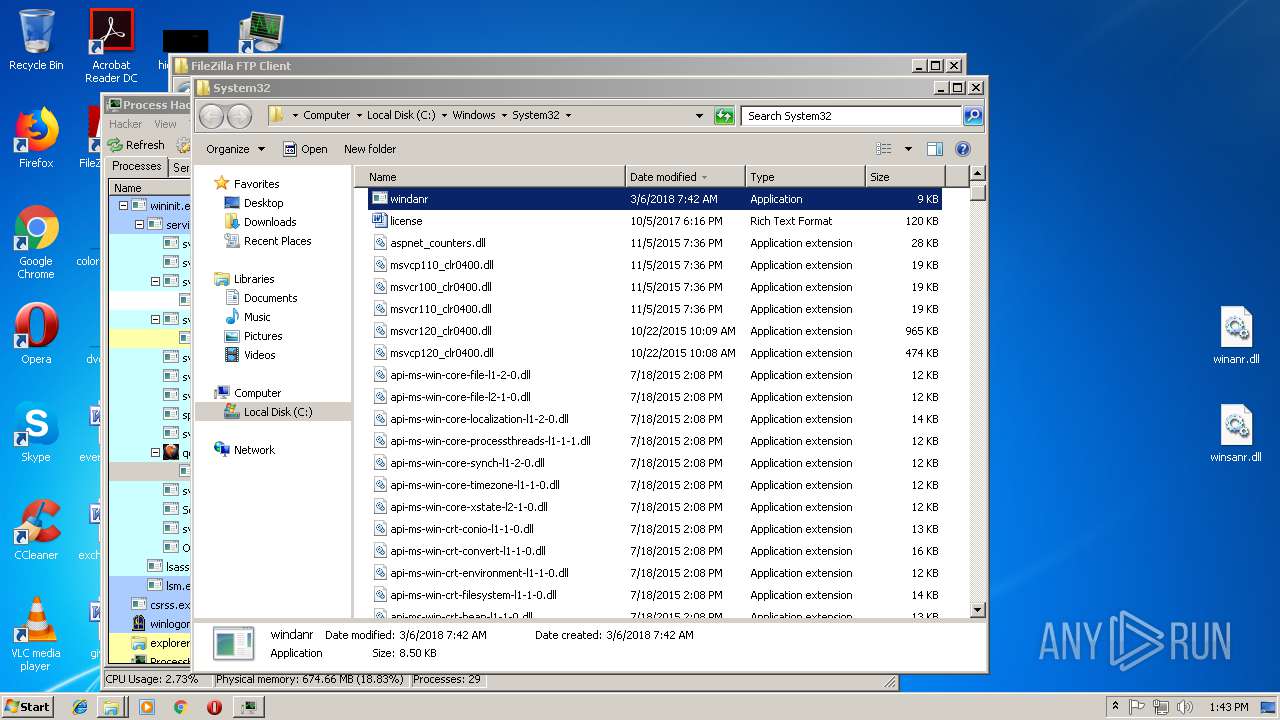
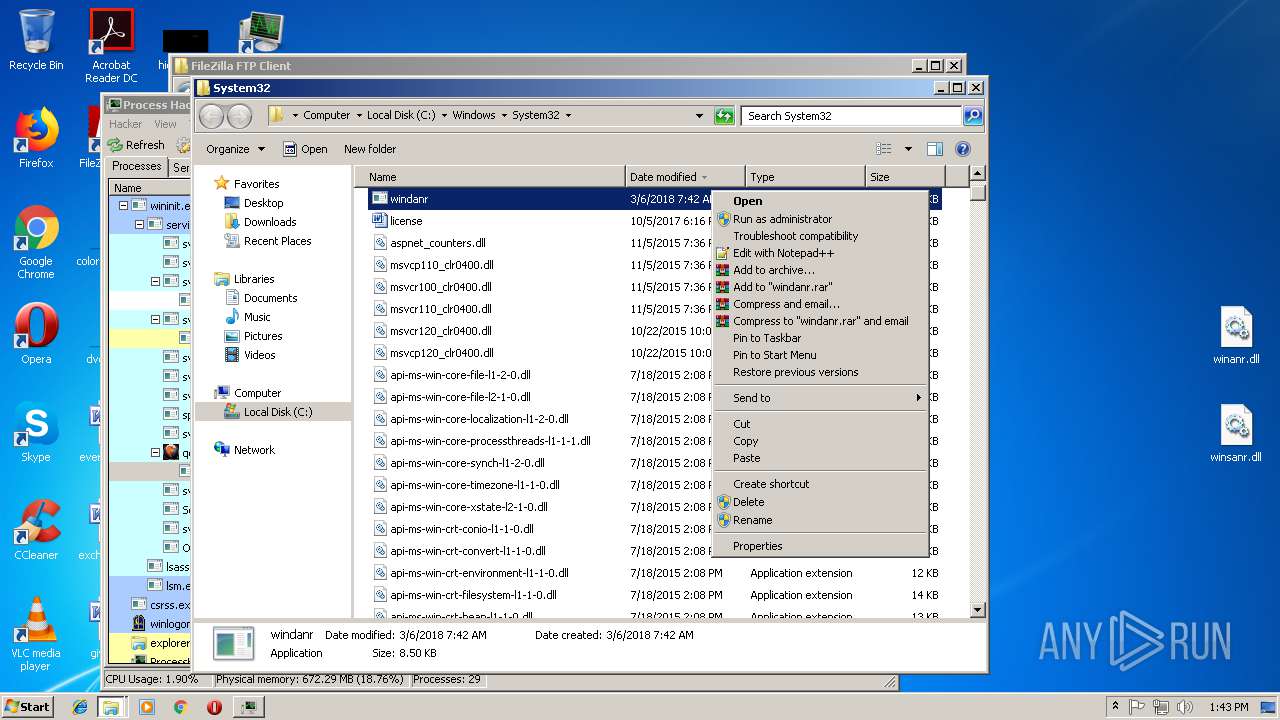
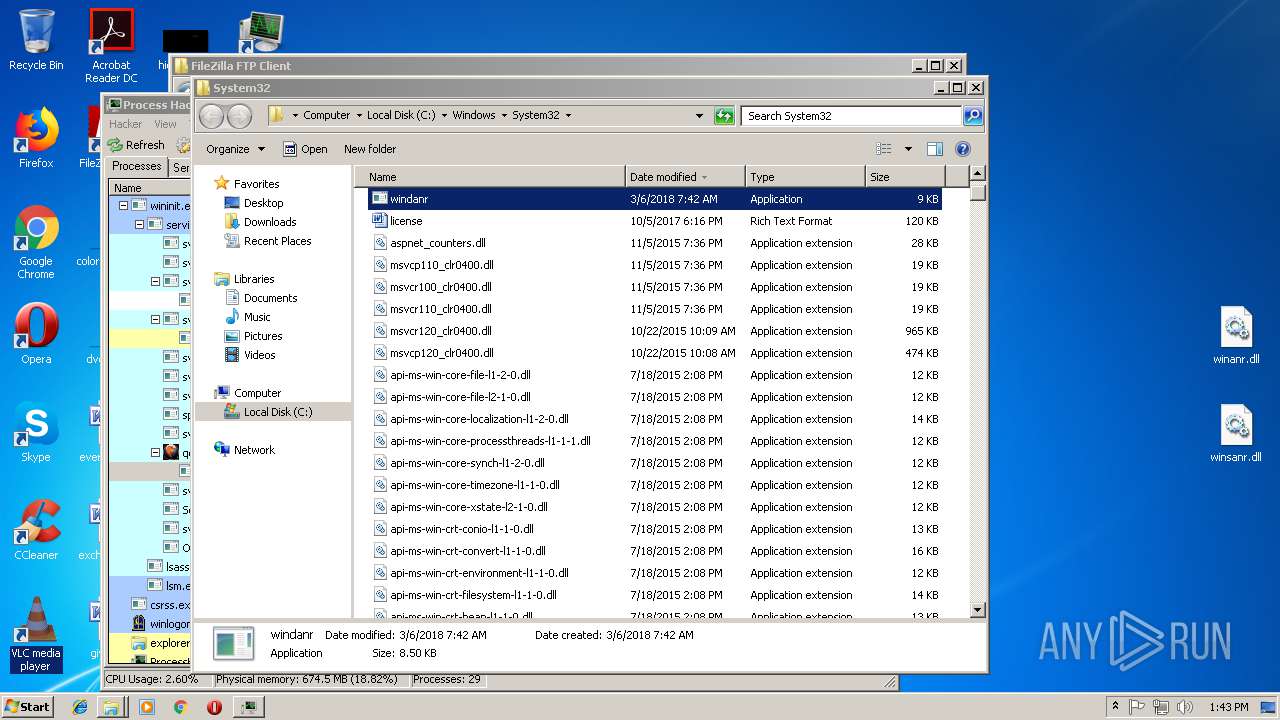
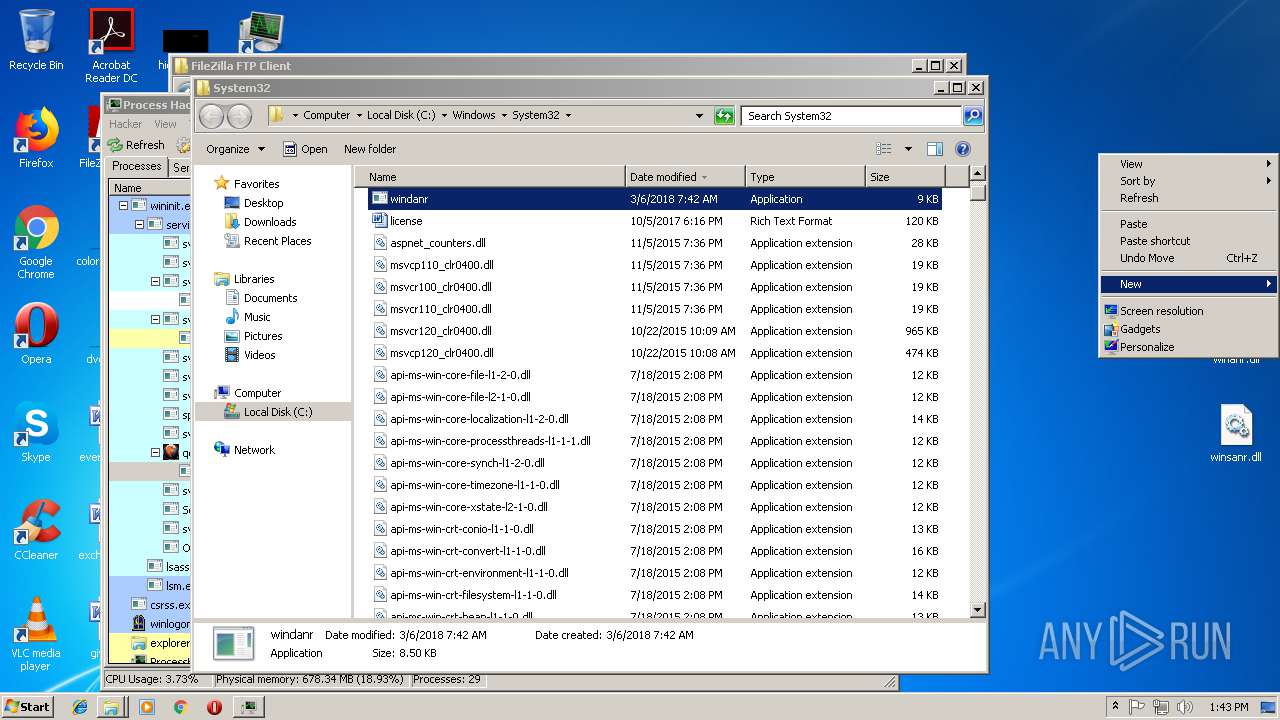
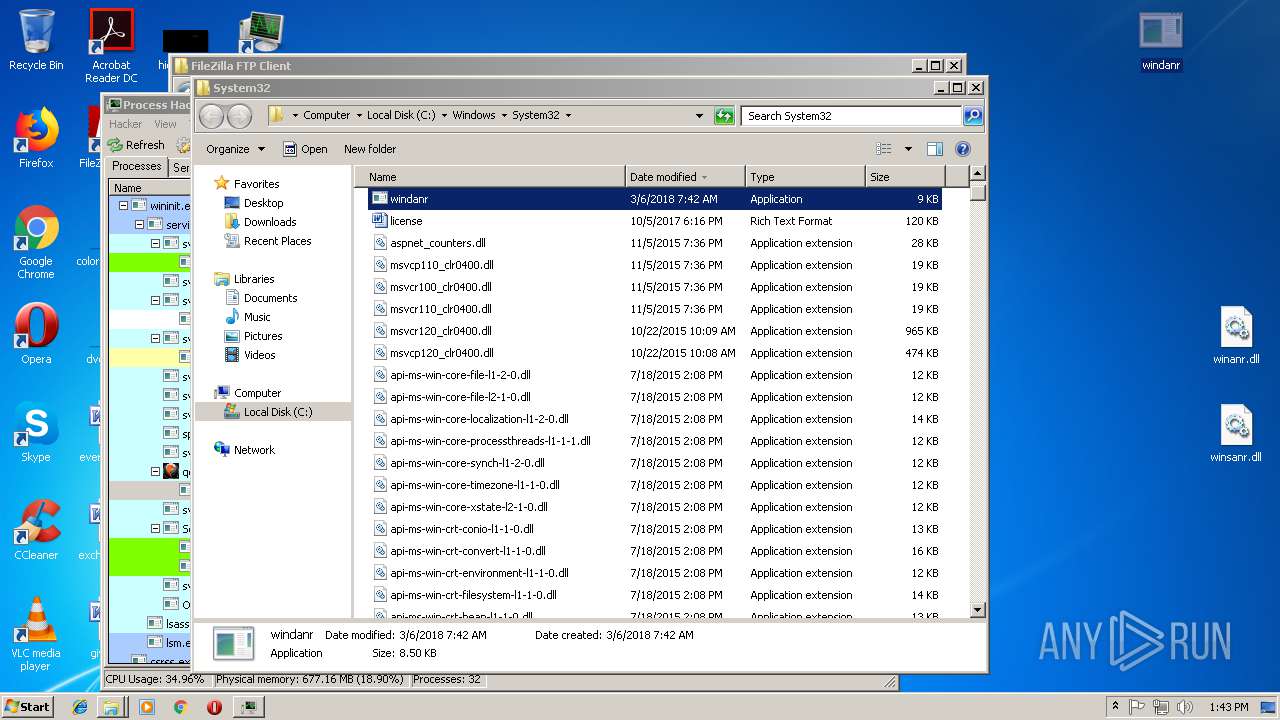
- windanr.exe (PID: 3824)
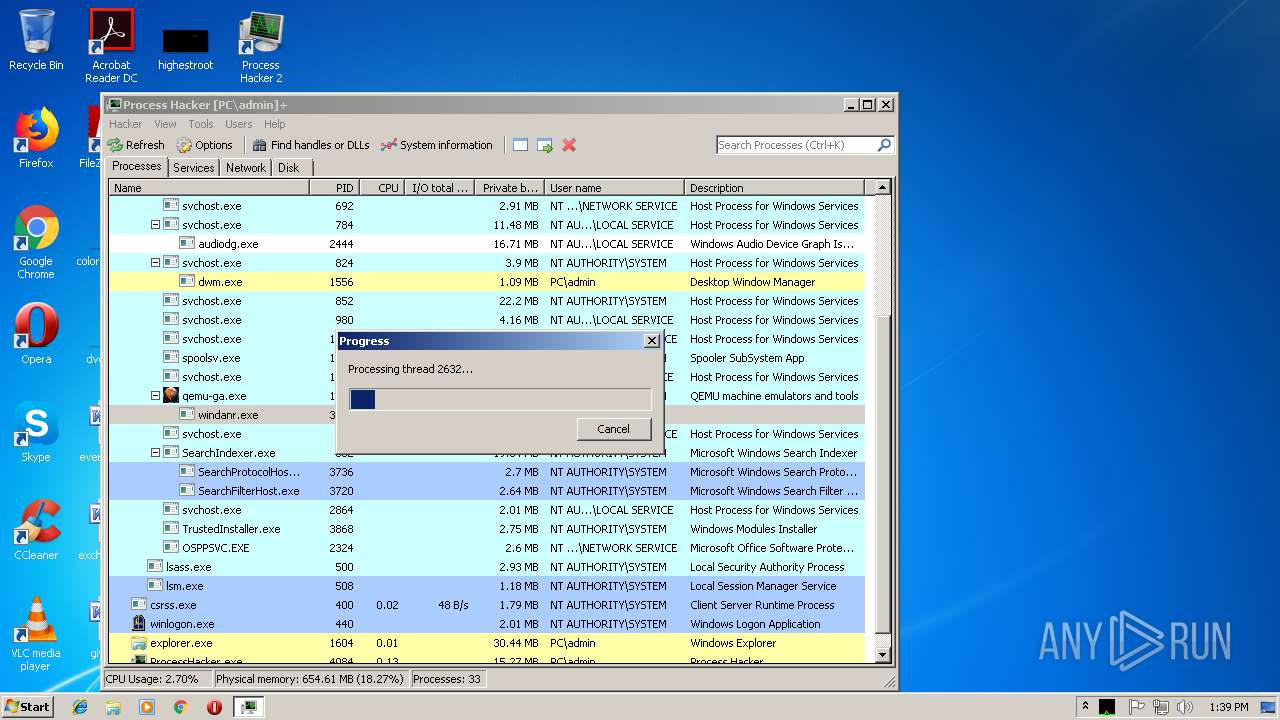
- windanr.exe (PID: 2632)
Loads dropped or rewritten executable
- ProcessHacker.exe (PID: 4084)
- windanr.exe (PID: 3824)
- explorer.exe (PID: 1604)
- peview.exe (PID: 3588)
- SearchProtocolHost.exe (PID: 3736)
- windanr.exe (PID: 2632)
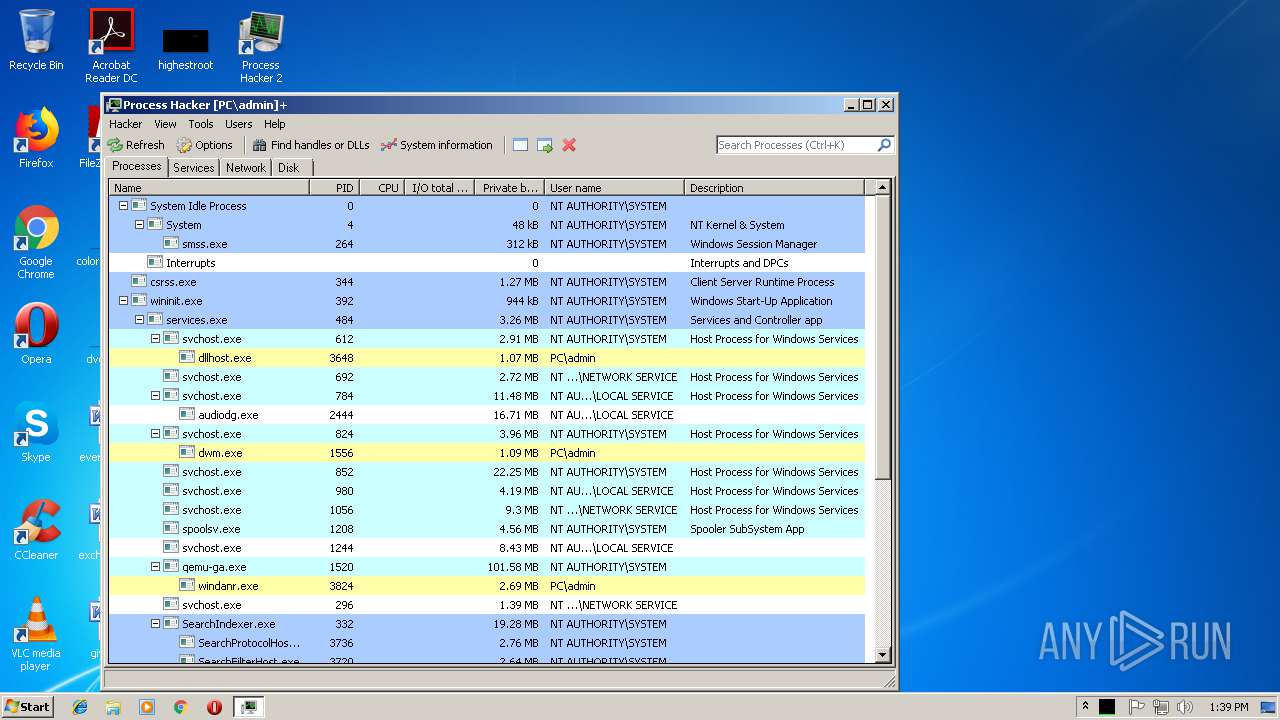
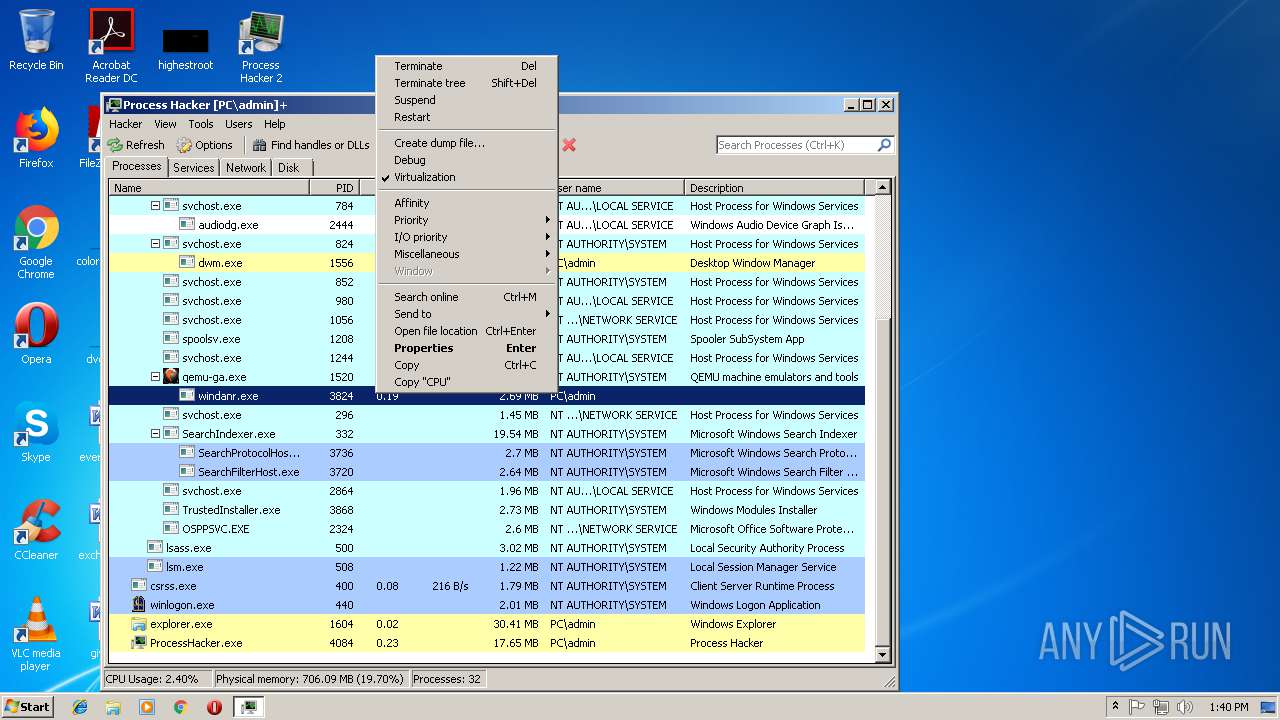
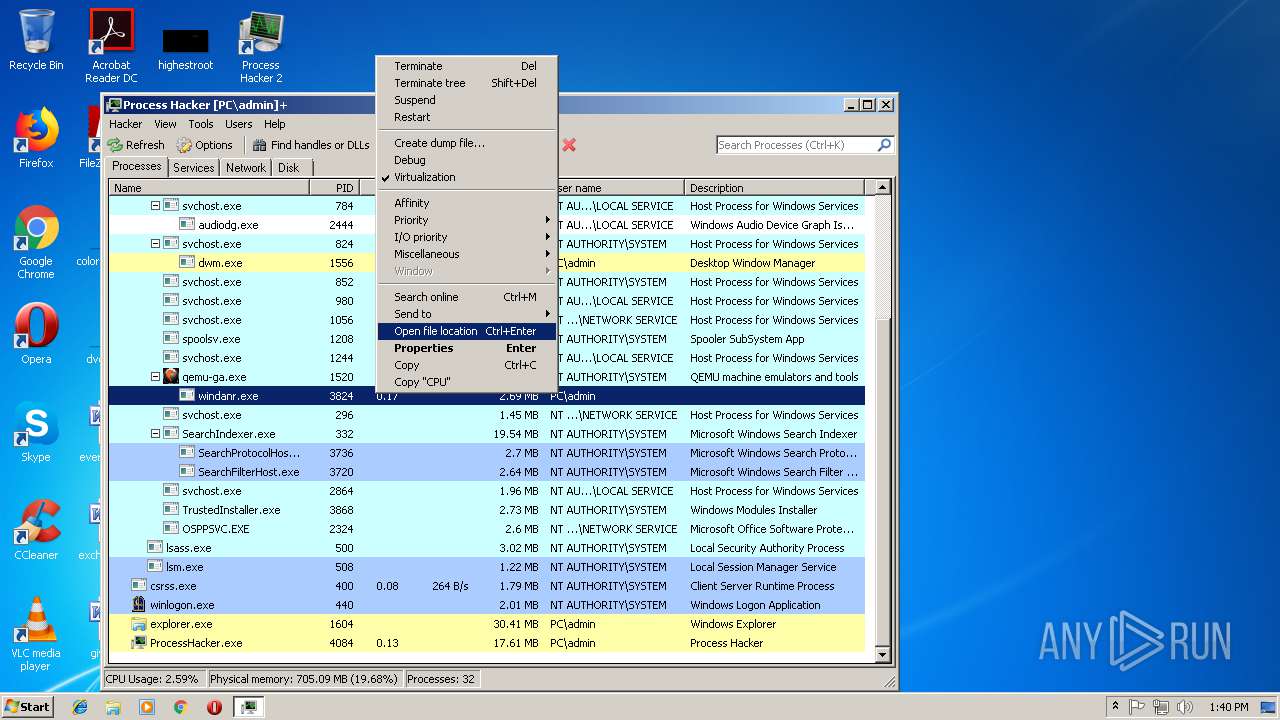
Runs injected code in another process
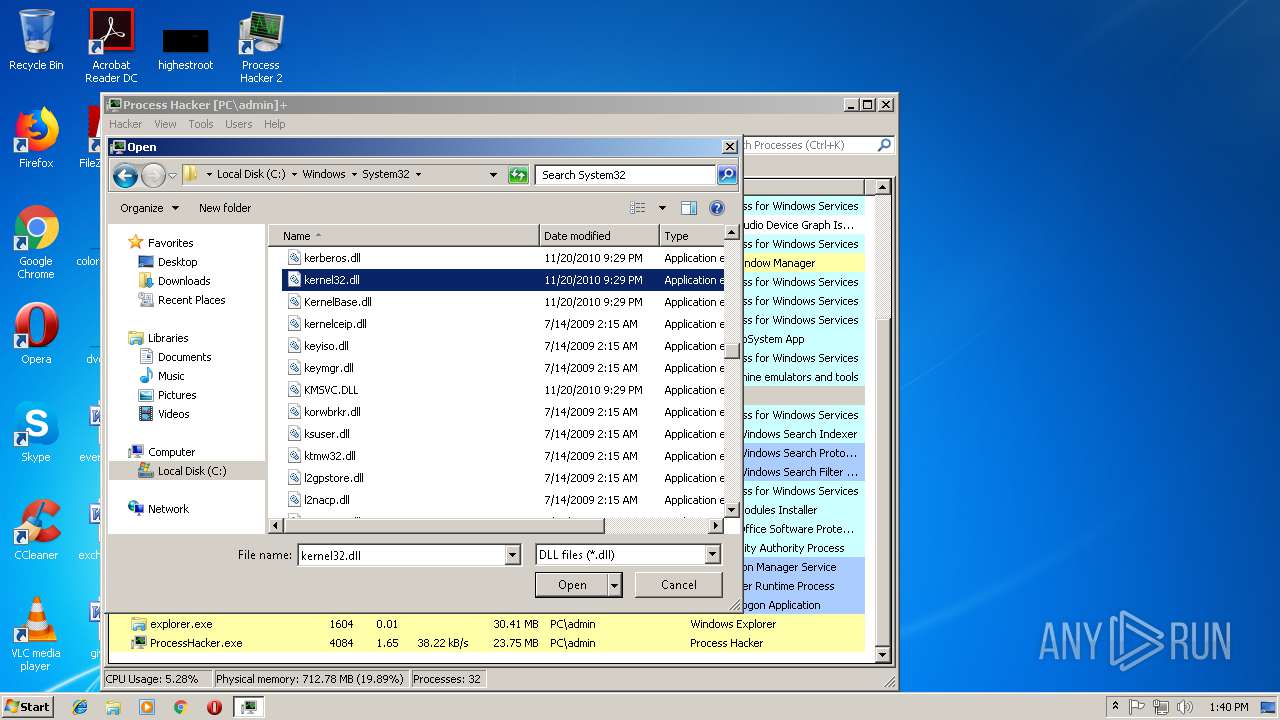
- ProcessHacker.exe (PID: 4084)
Application was injected by another process
- windanr.exe (PID: 3824)
SUSPICIOUS
Executable content was dropped or overwritten
- processhacker-2.39-setup.exe (PID: 2904)
- processhacker-2.39-setup.tmp (PID: 3304)
- processhacker-2.39-setup.exe (PID: 3232)
- explorer.exe (PID: 1604)
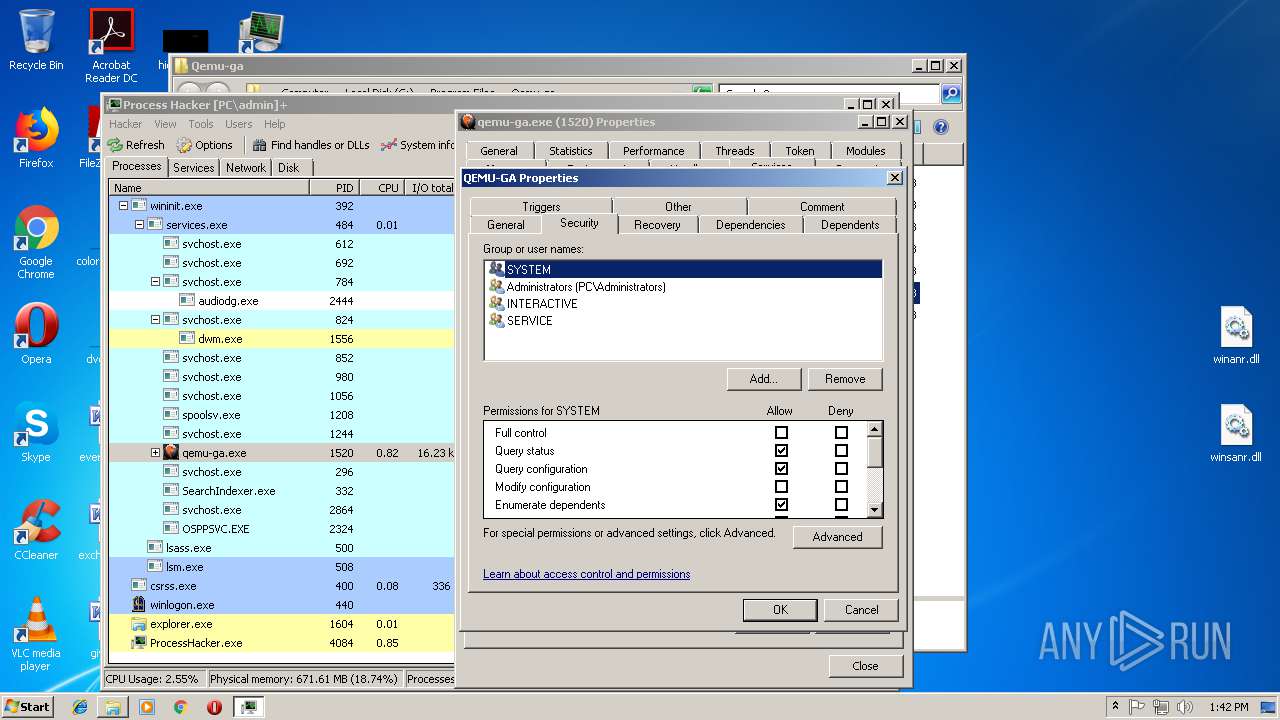
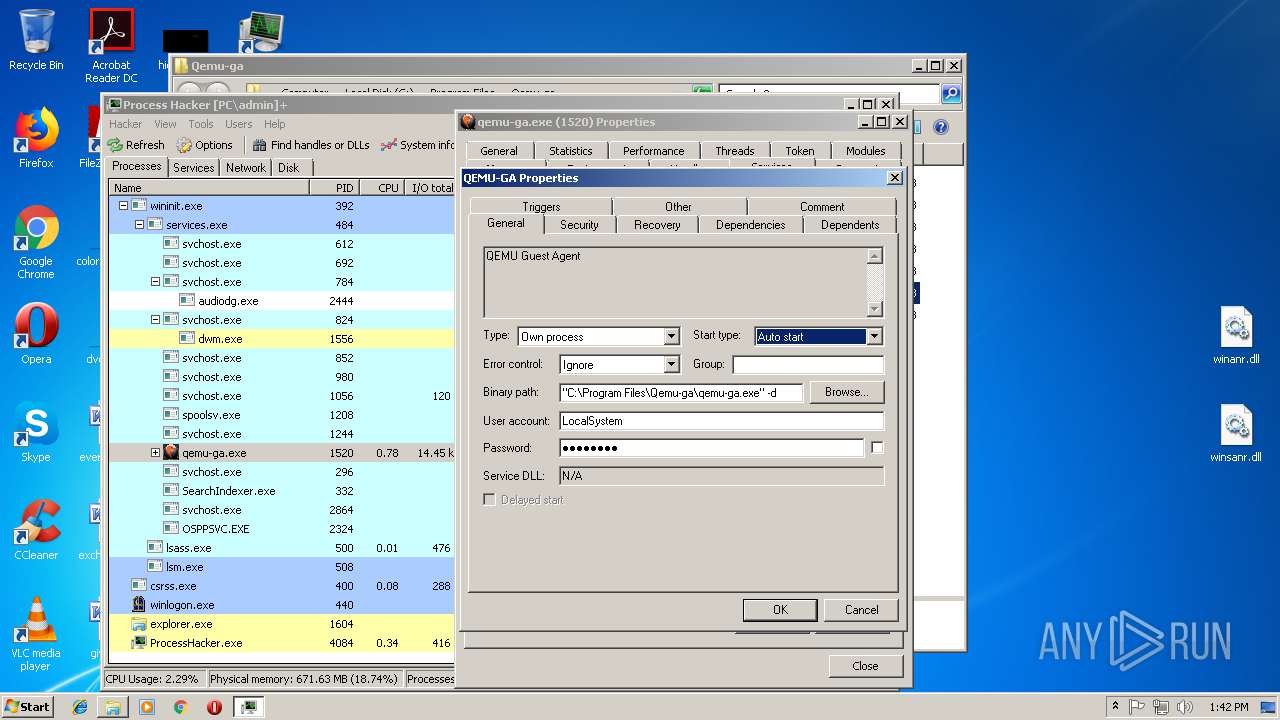
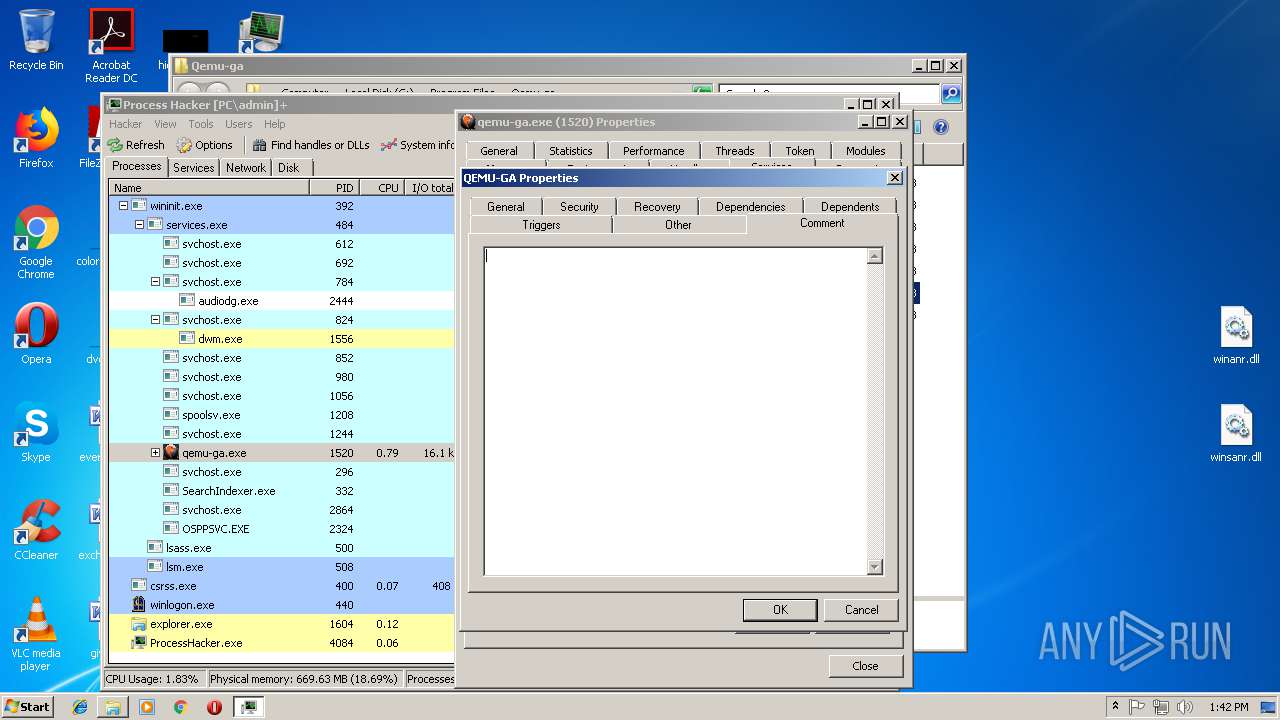
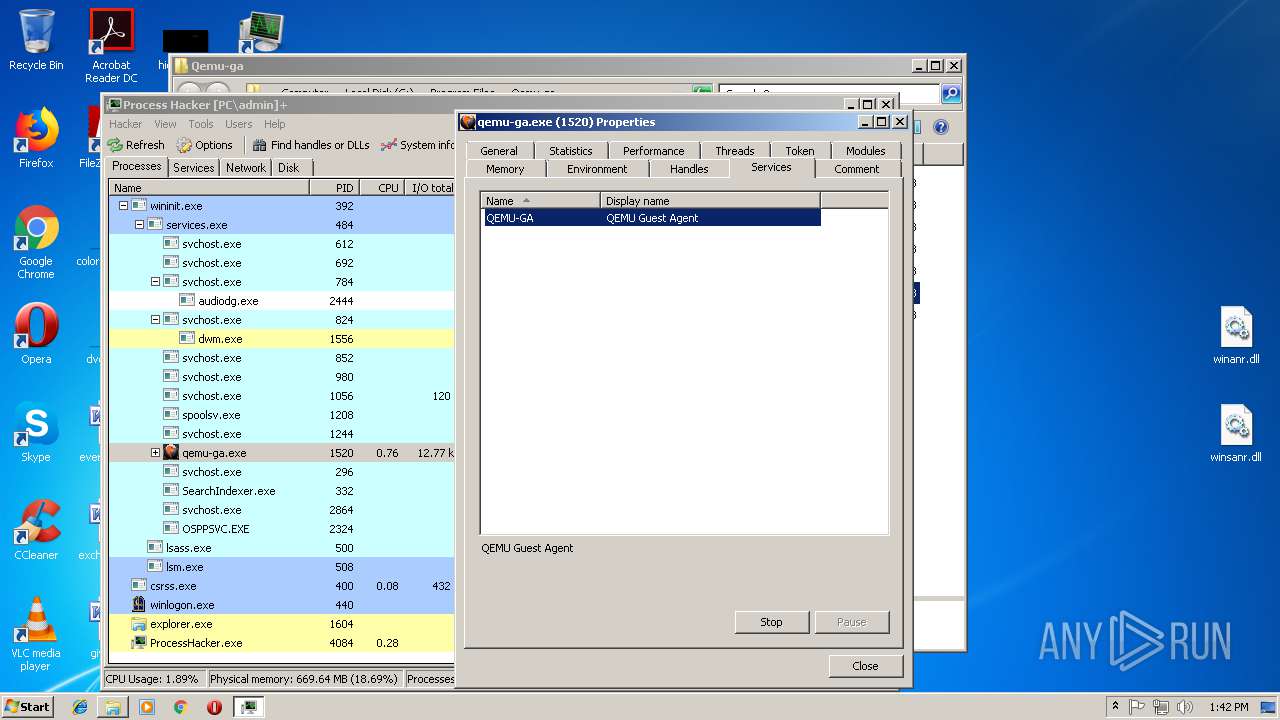
Creates or modifies windows services
- ProcessHacker.exe (PID: 3952)
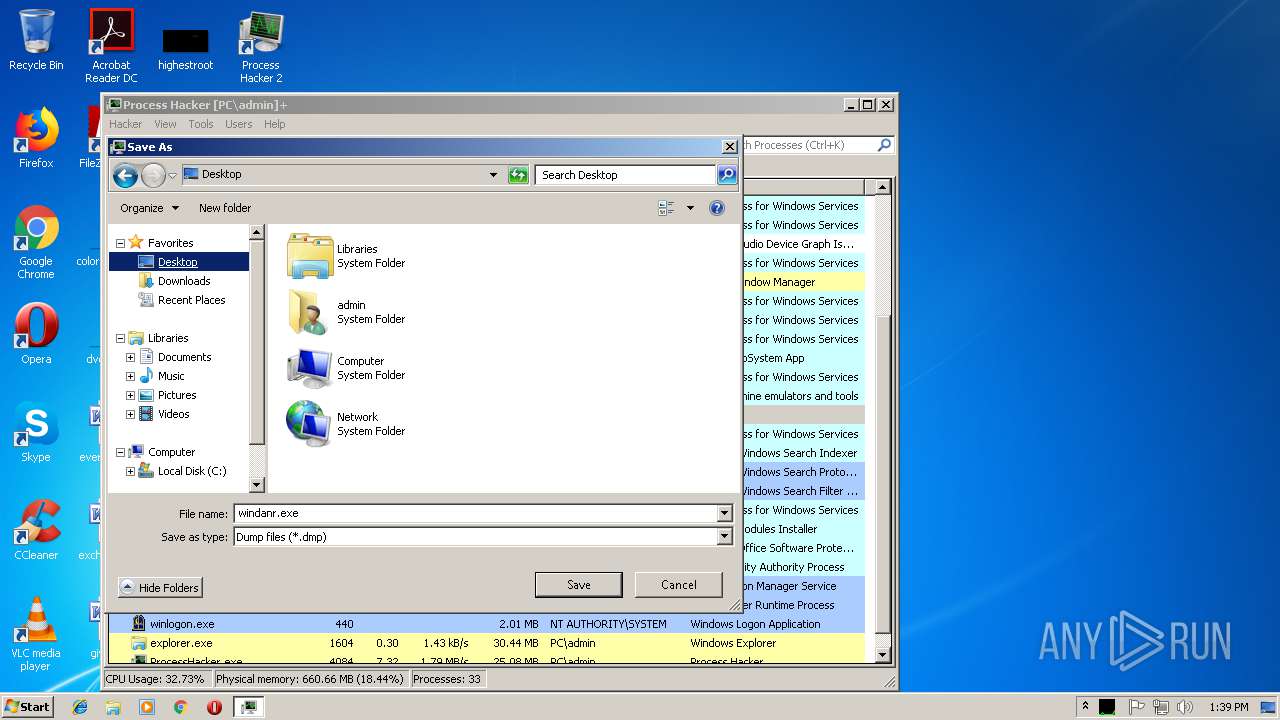
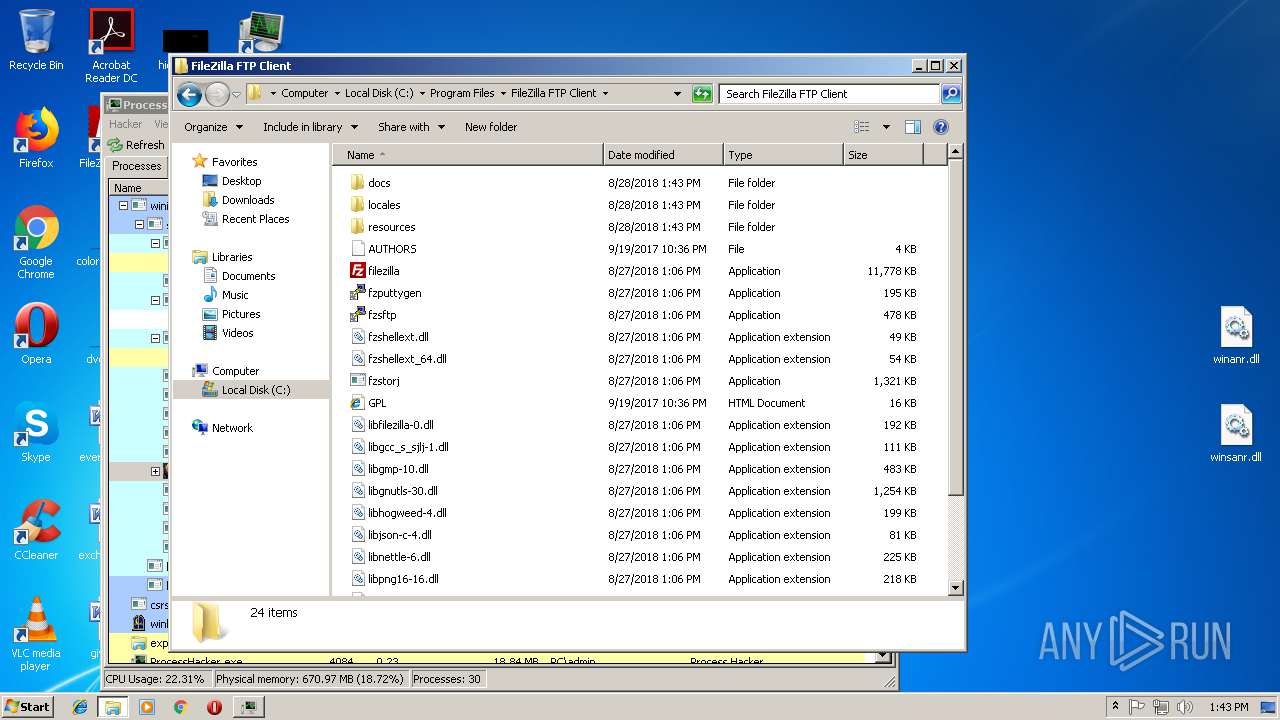
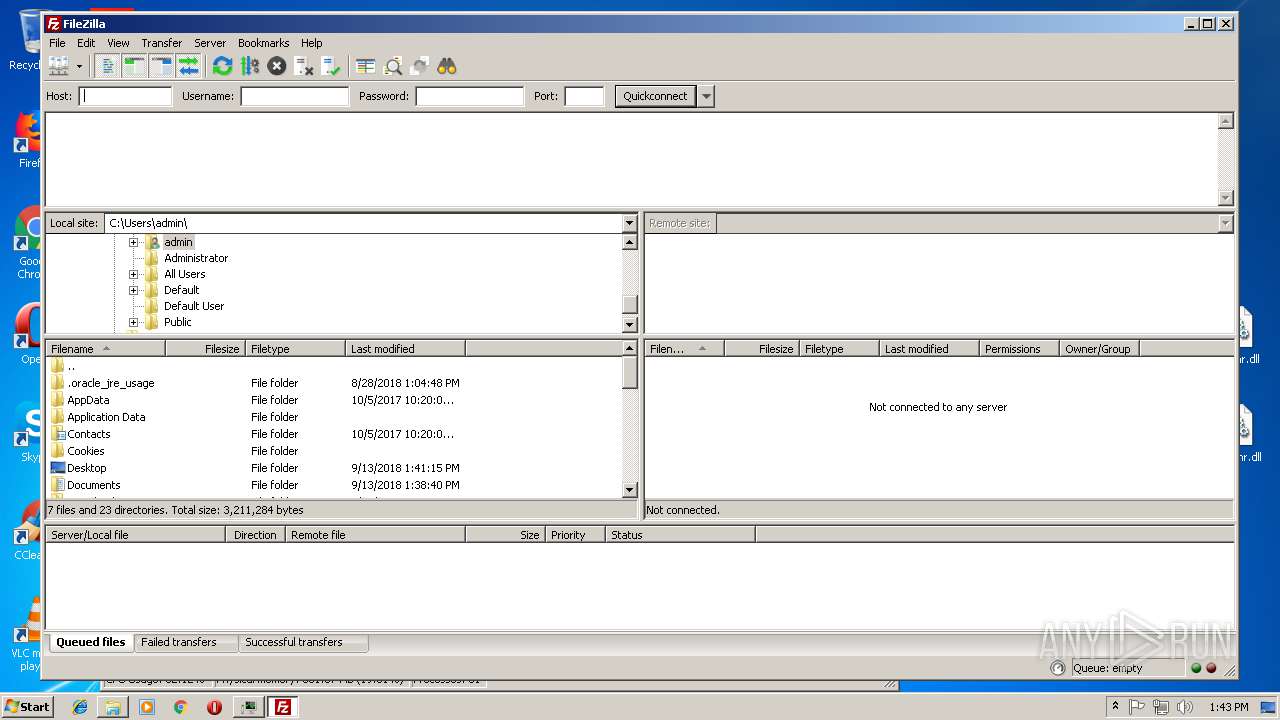
Creates files in the user directory
- explorer.exe (PID: 1604)
- ProcessHacker.exe (PID: 4084)
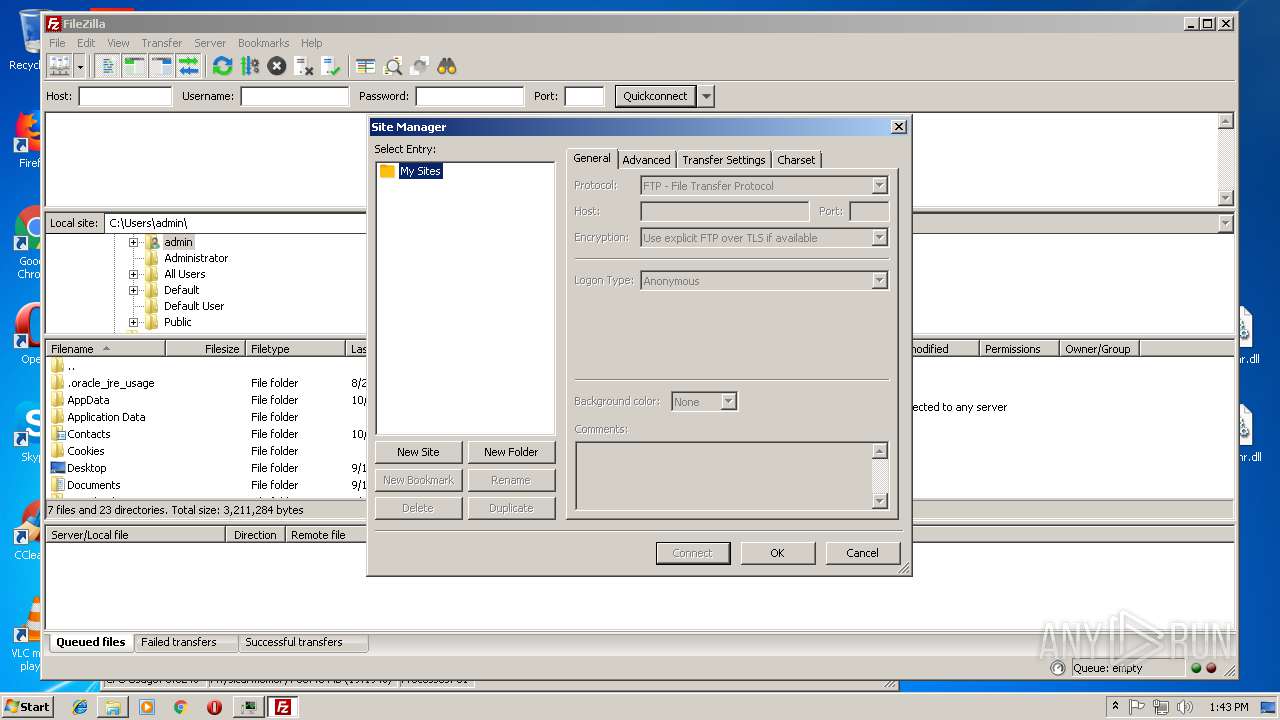
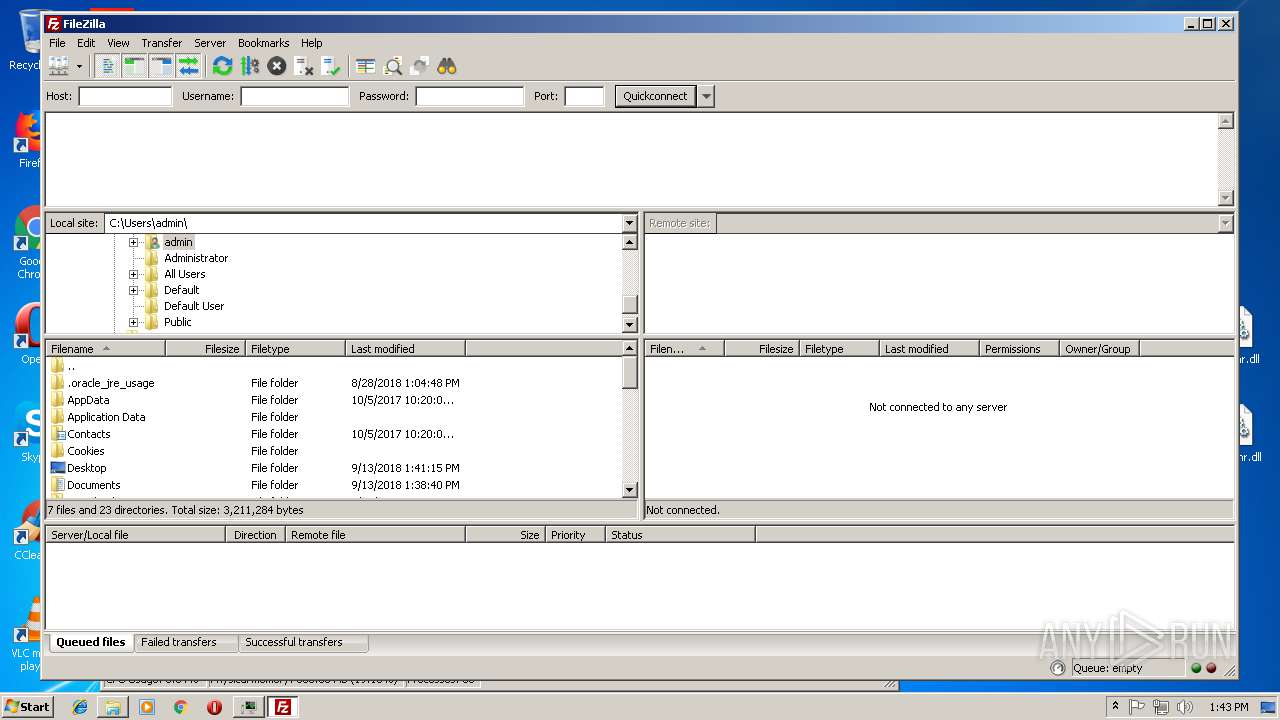
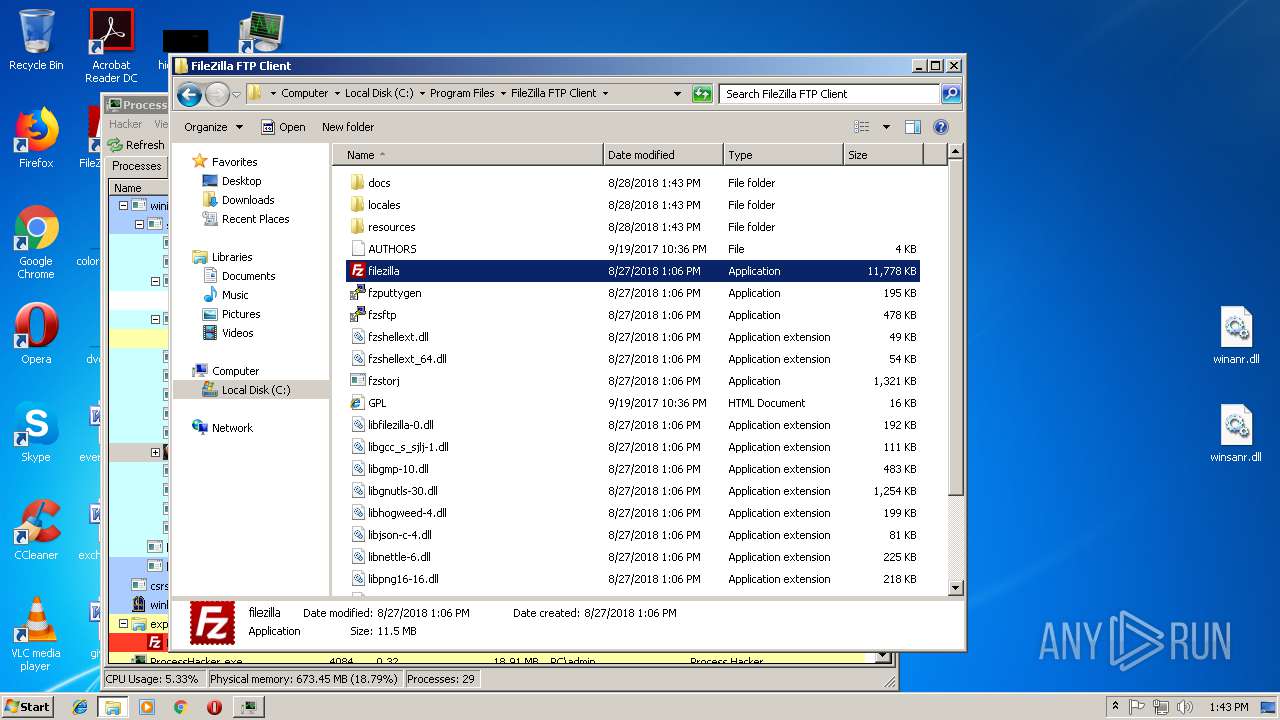
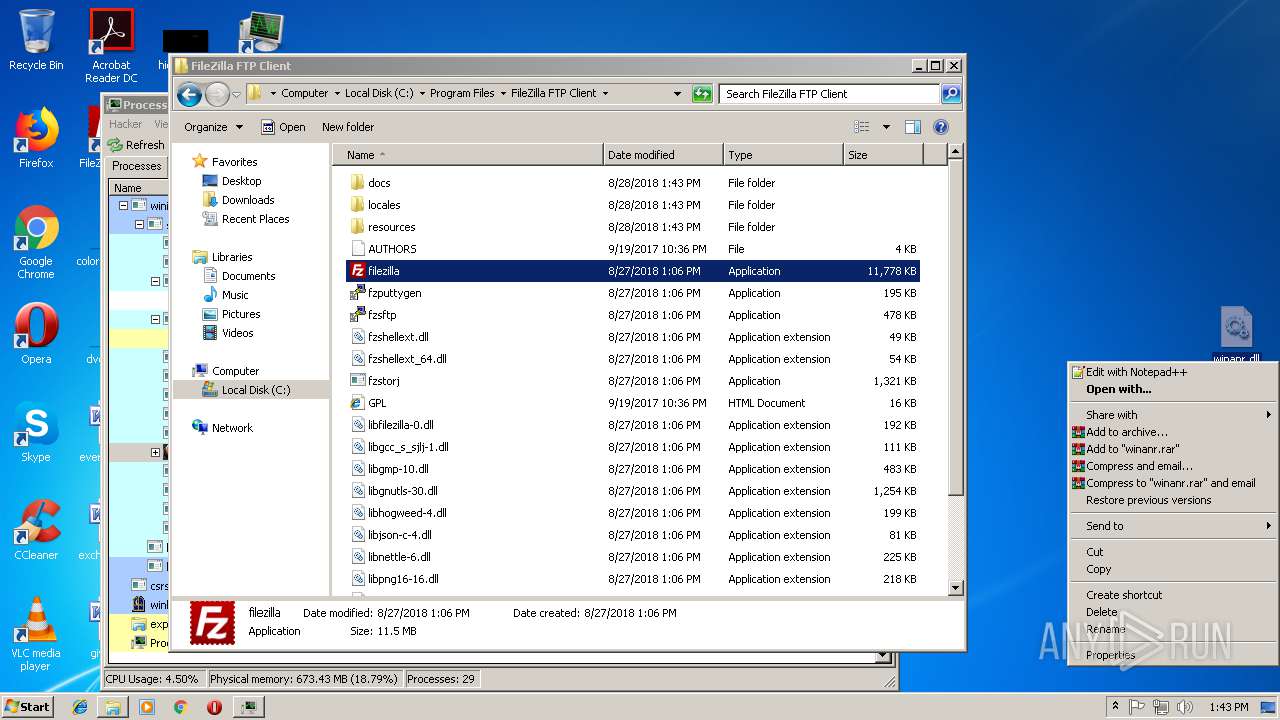
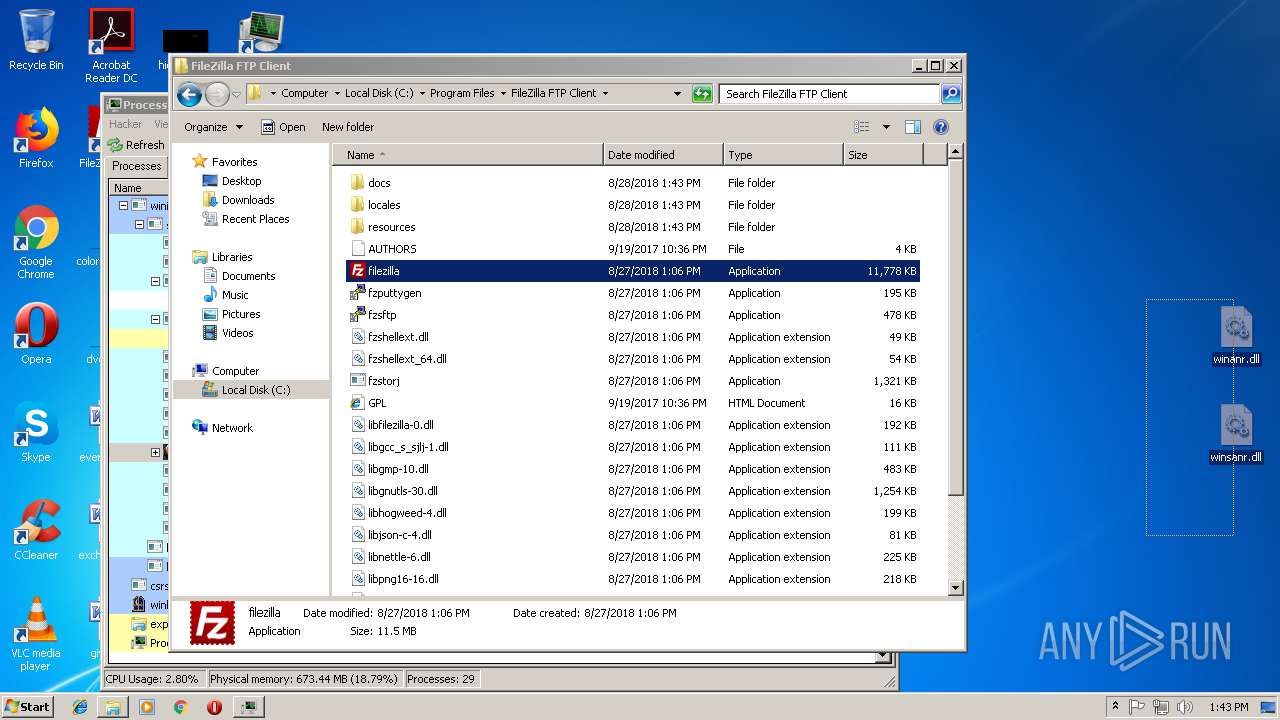
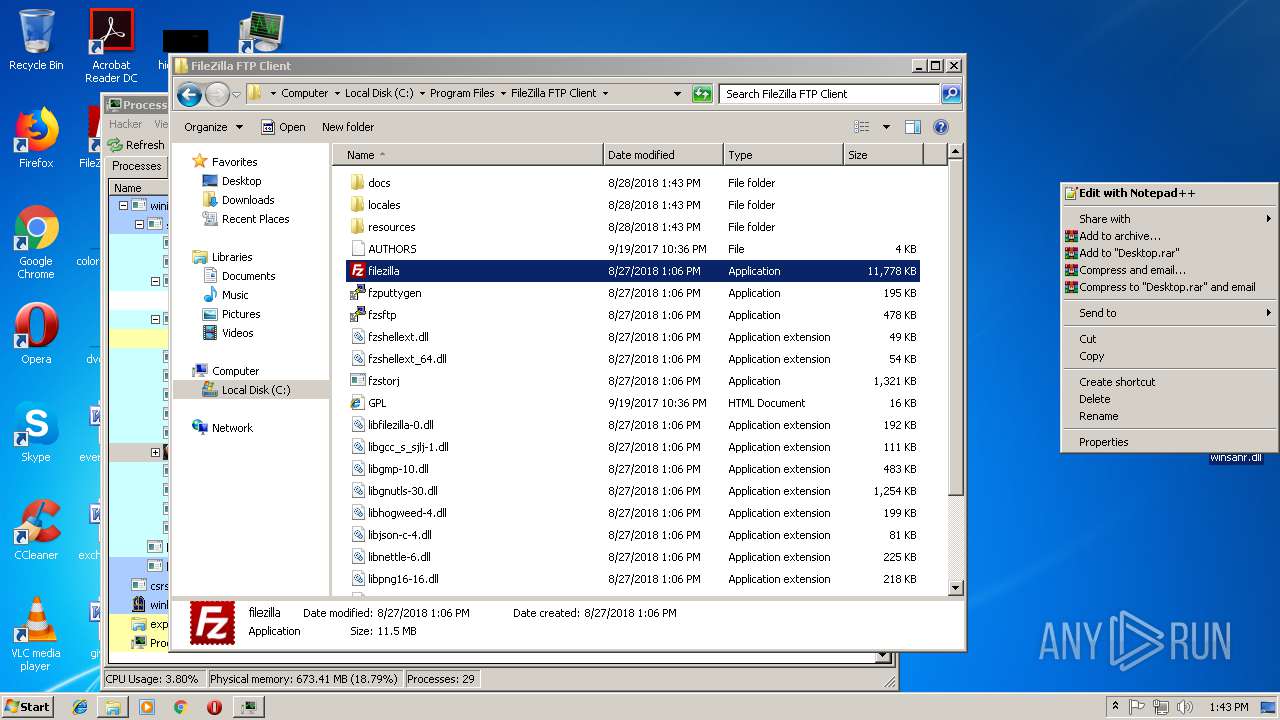
- filezilla.exe (PID: 3956)
Reads Internet Cache Settings
- explorer.exe (PID: 1604)
- ProcessHacker.exe (PID: 4084)
INFO
Application was dropped or rewritten from another process
- processhacker-2.39-setup.tmp (PID: 3304)
- processhacker-2.39-setup.tmp (PID: 3024)
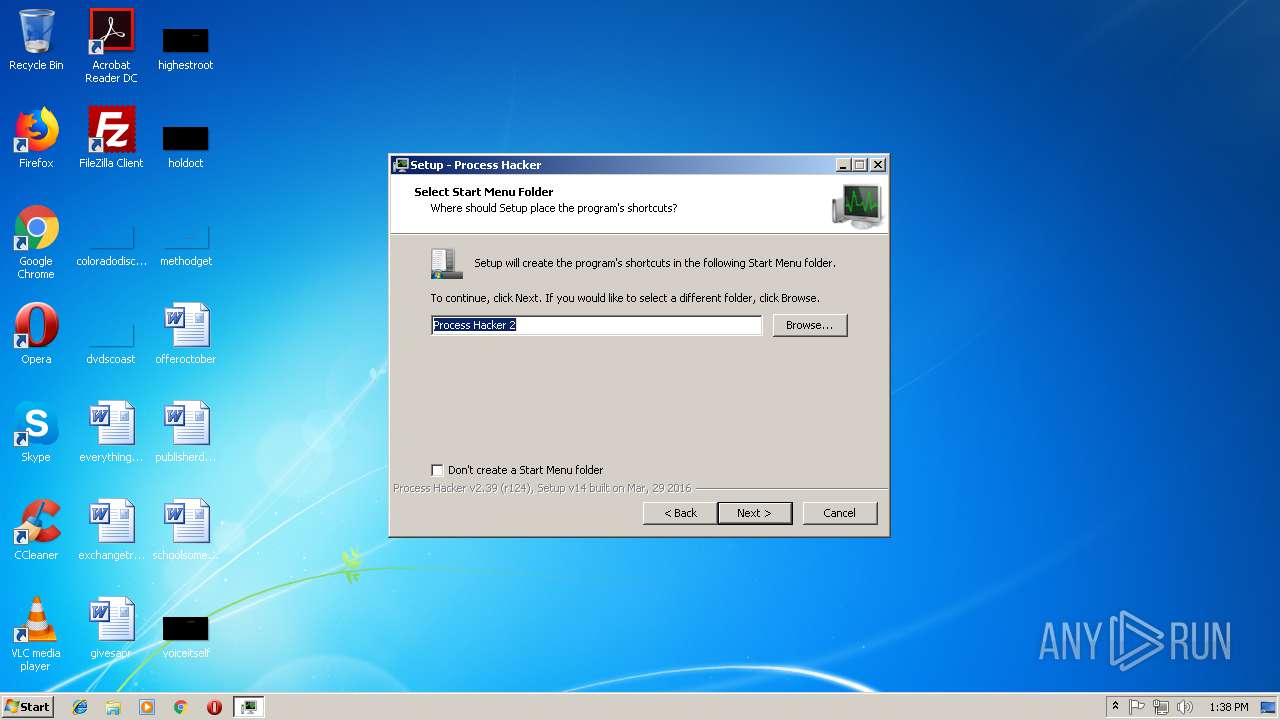
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 3304)
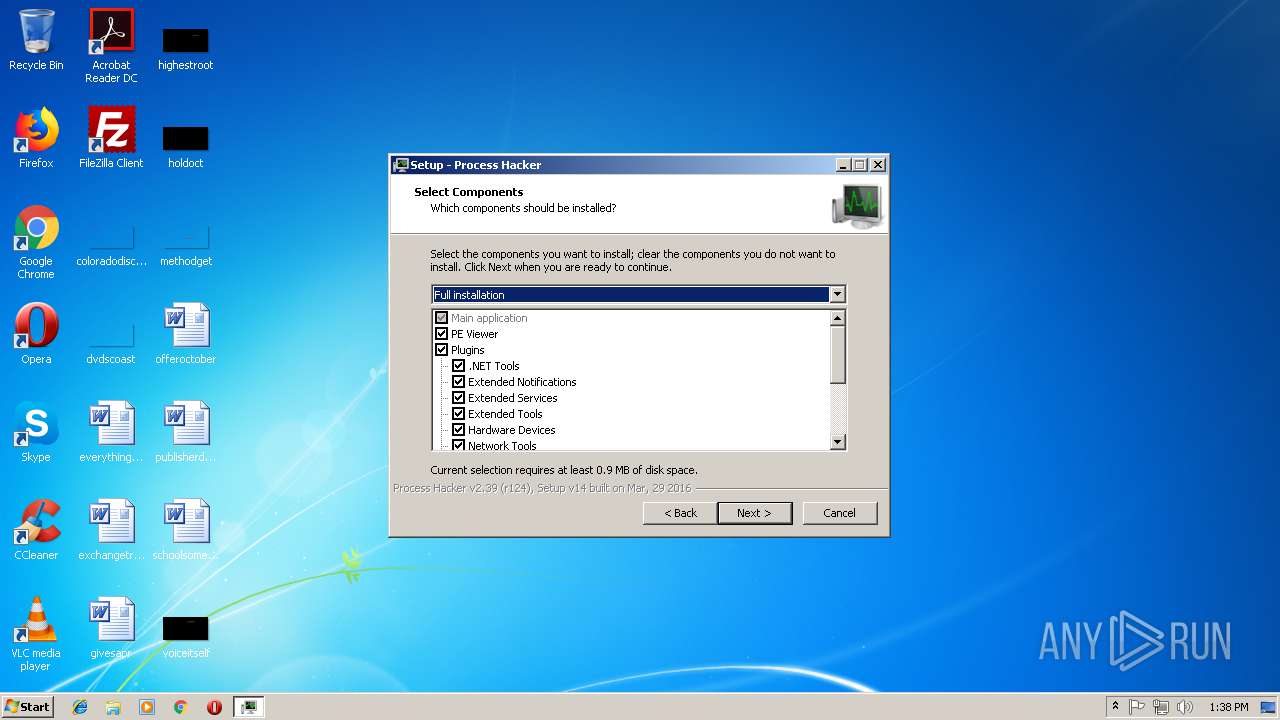
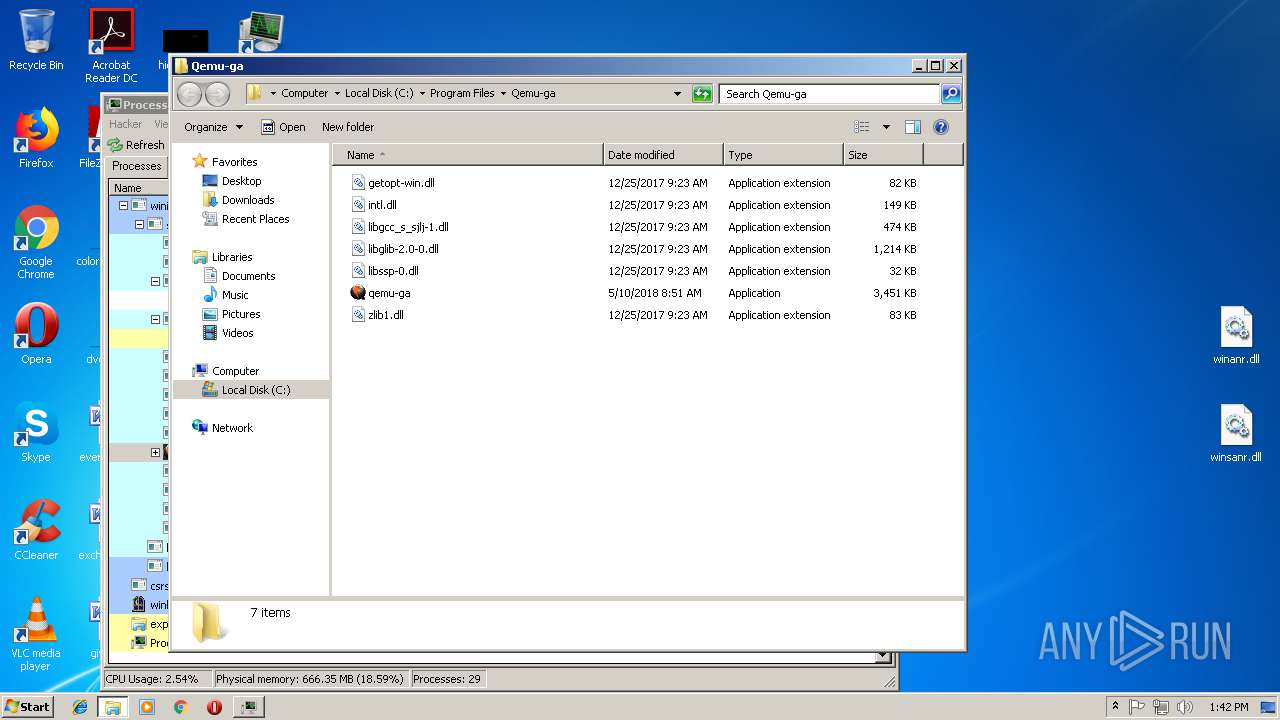
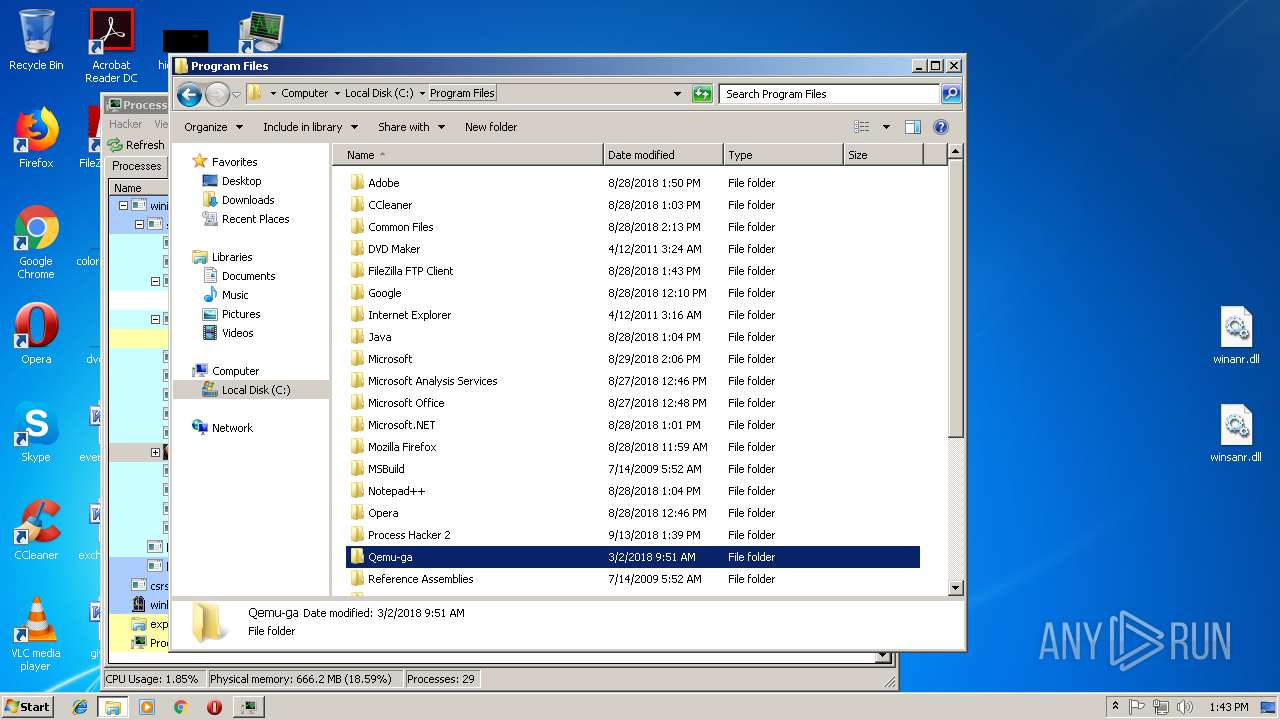
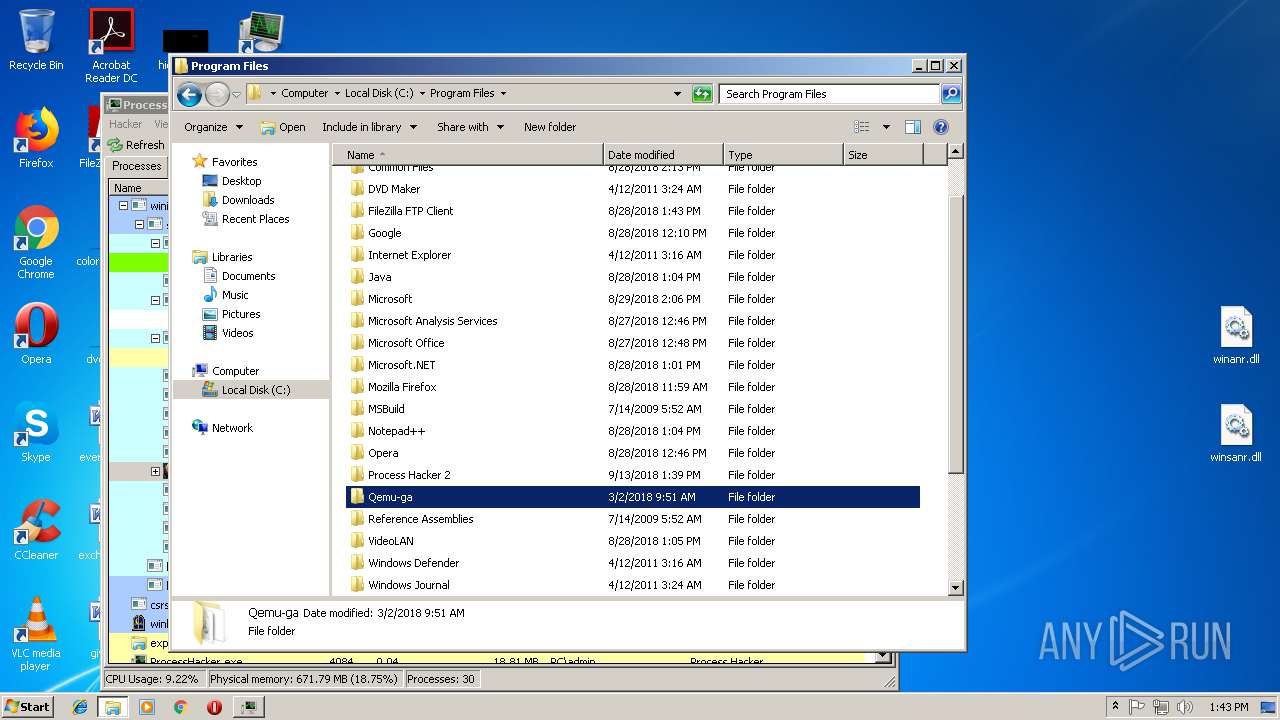
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 3304)
Loads dropped or rewritten executable
- processhacker-2.39-setup.tmp (PID: 3304)
Reads settings of System Certificates
- ProcessHacker.exe (PID: 4084)
Reads Microsoft Office registry keys
- explorer.exe (PID: 1604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 108544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.39.0.124 |
| ProductVersionNumber: | 2.39.0.124 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | wj32 |
| FileDescription: | Process Hacker Setup |
| FileVersion: | 2.39 (r124) |
| LegalCopyright: | Copyright © 2010-2016, Process Hacker Team. Licensed under the GNU GPL, v3. |
| ProductName: | Process Hacker |
| ProductVersion: | 2.39 (r124) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | wj32 |
| FileDescription: | Process Hacker Setup |
| FileVersion: | 2.39 (r124) |
| LegalCopyright: | Copyright © 2010-2016, Process Hacker Team. Licensed under the GNU GPL, v3. |
| ProductName: | Process Hacker |
| ProductVersion: | 2.39 (r124) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63175 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75472 |
BSS | 0x0000C000 | 0x00000E90 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0001977C | 0x00019800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.29544 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.80858 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.29425 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.1653 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.5254 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.002 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.2012 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 2.89511 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.94638 | 67507 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.27113 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
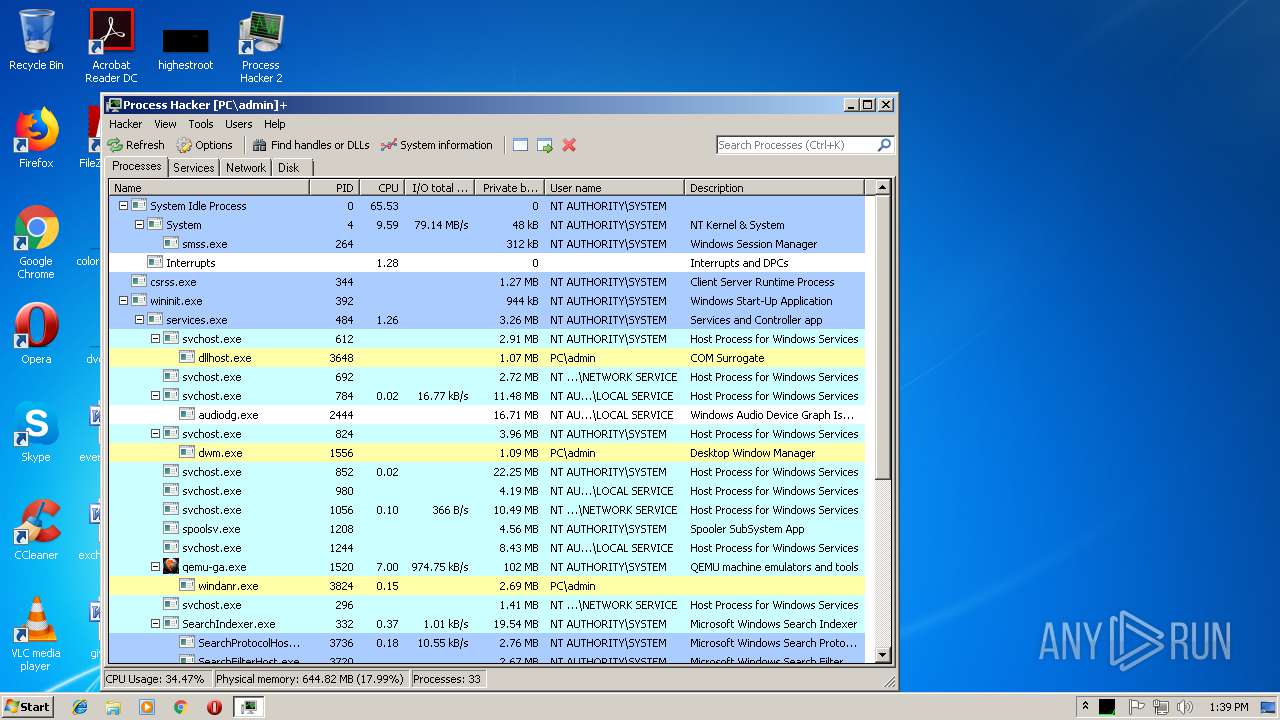
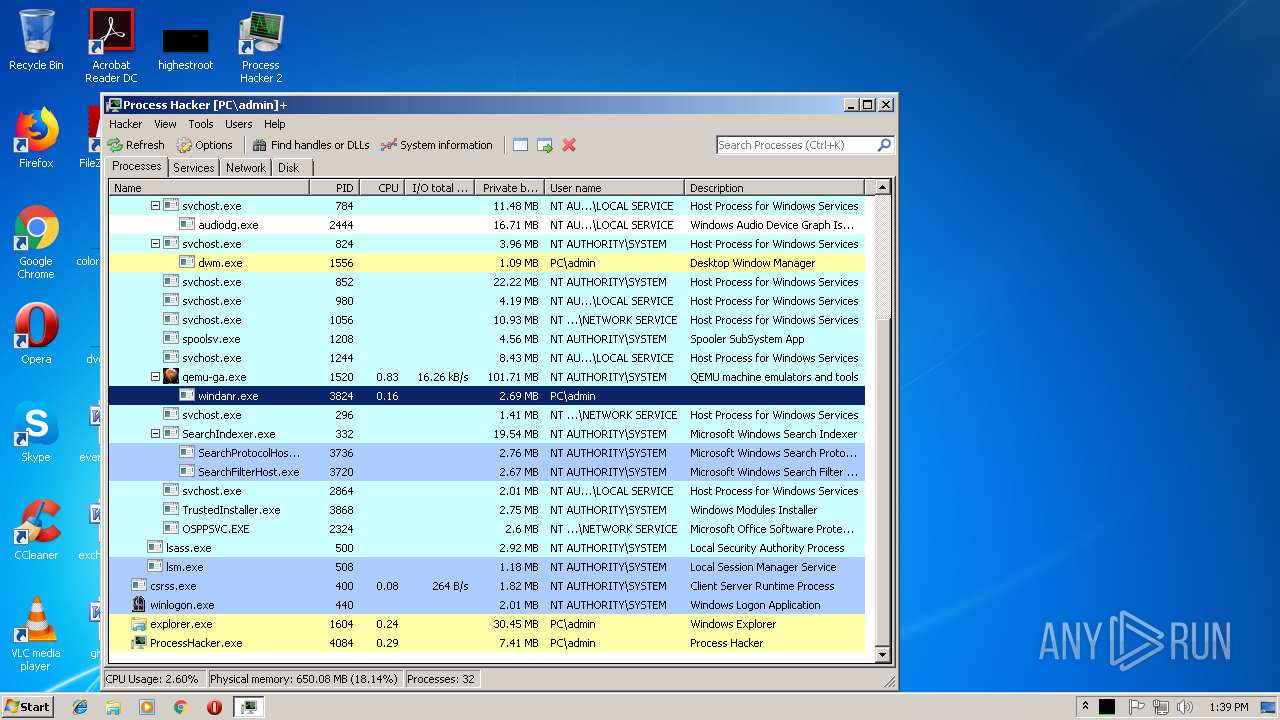
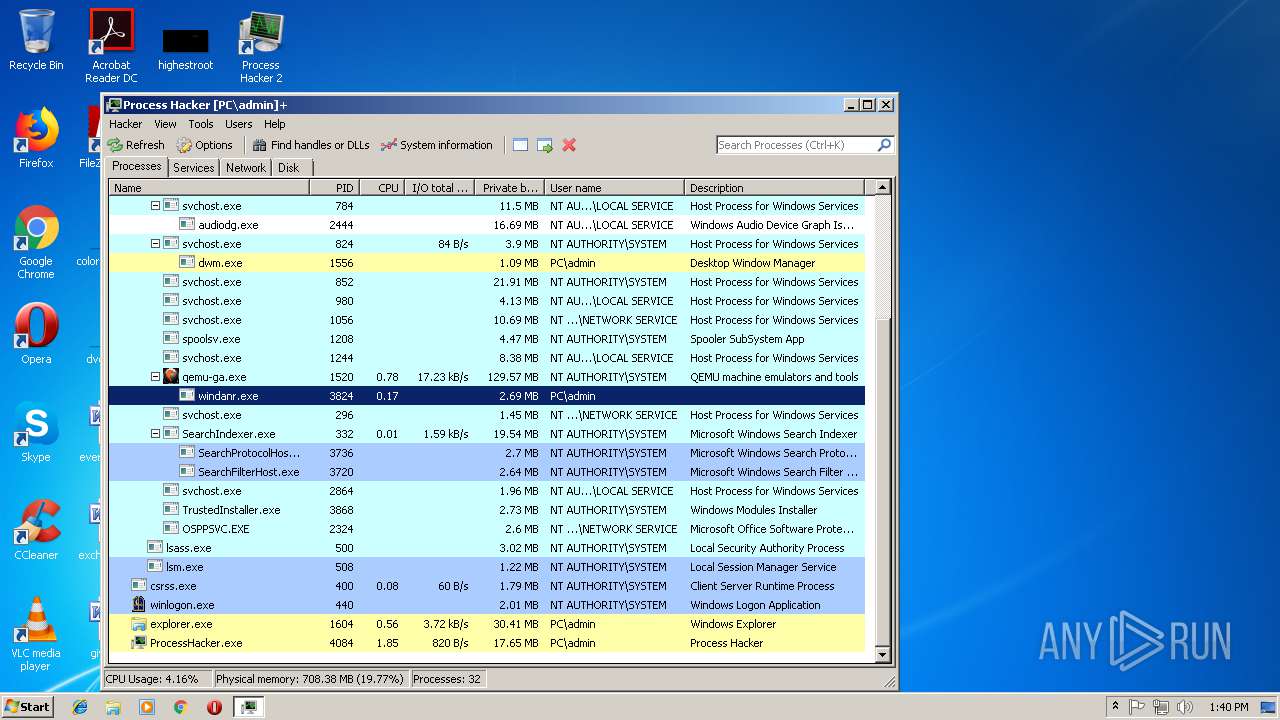
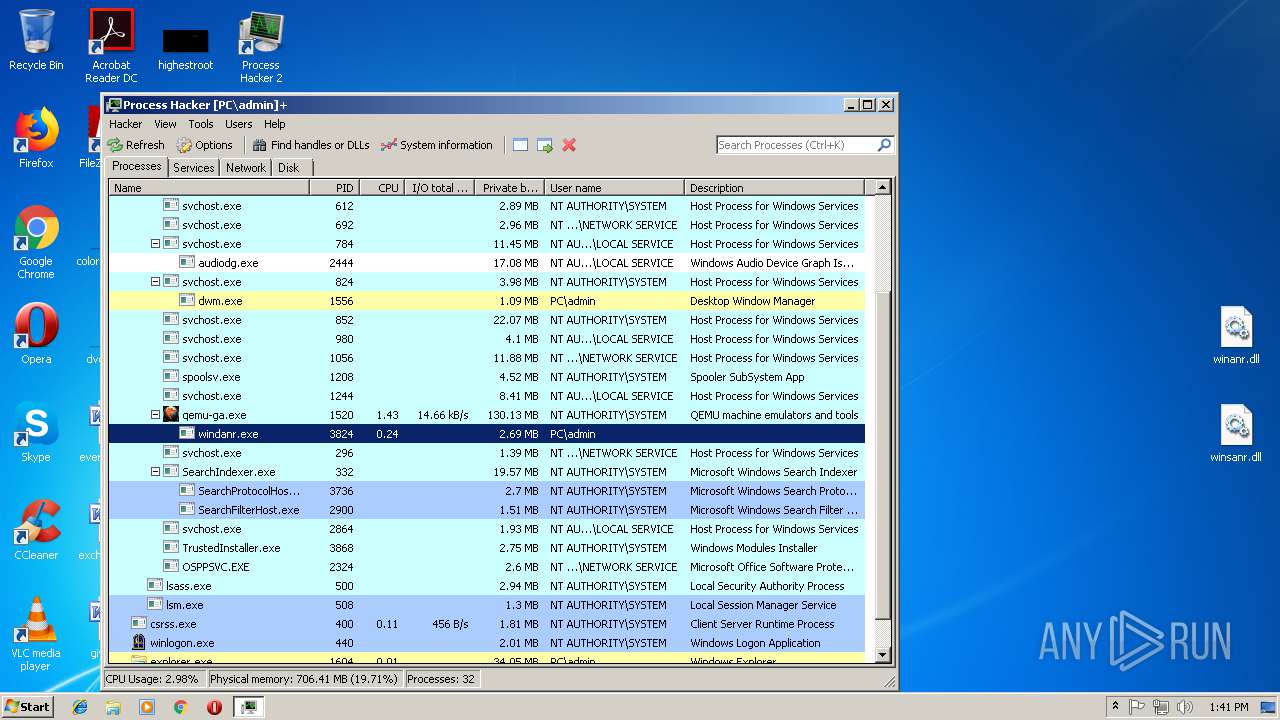
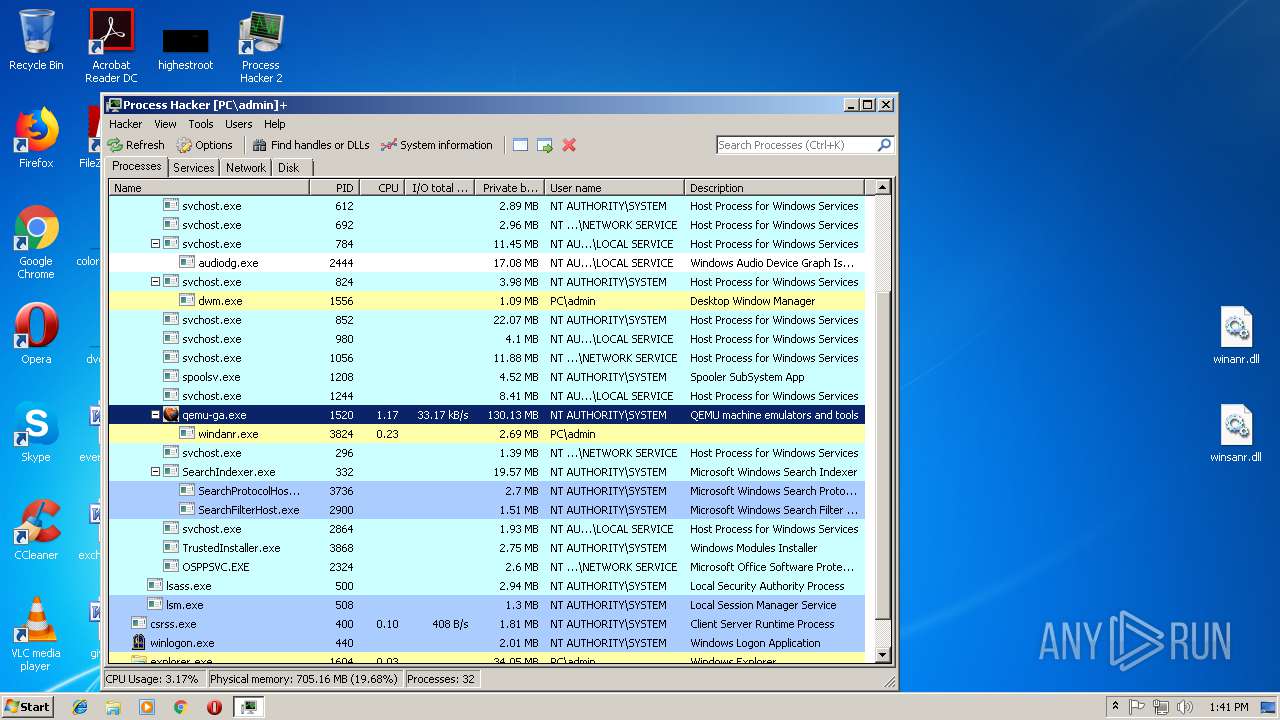
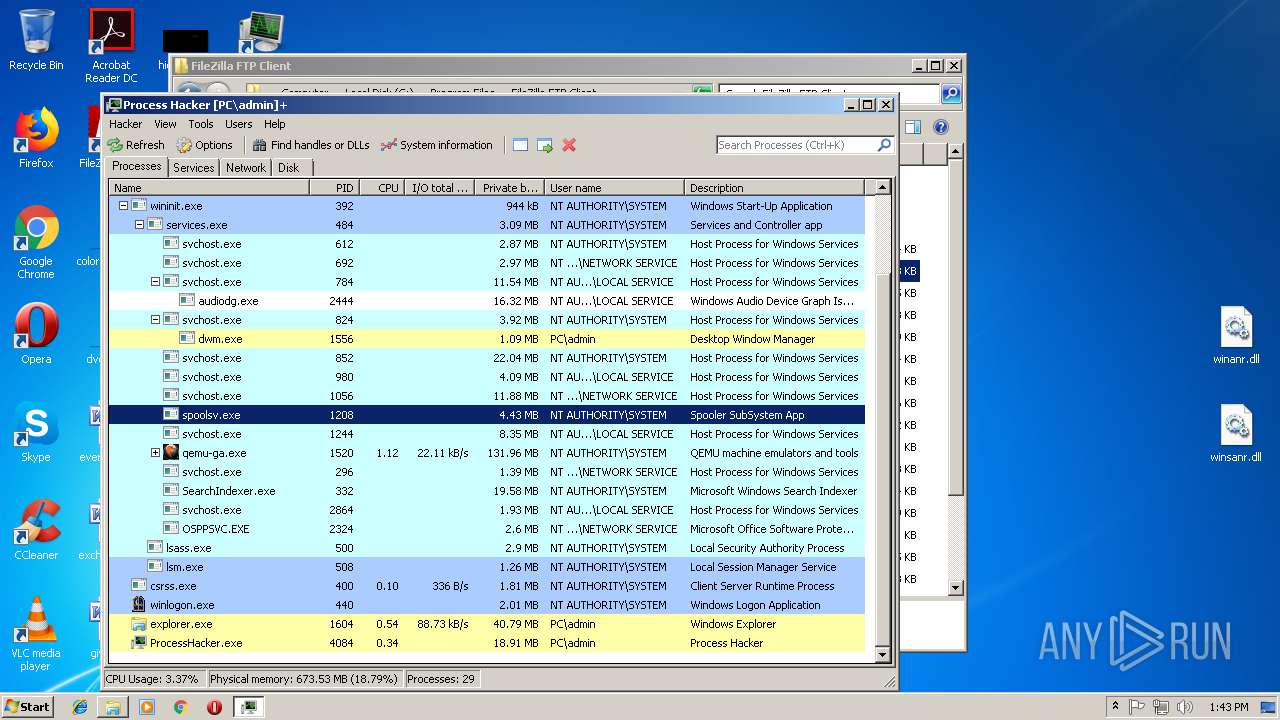
Total processes
59
Monitored processes
12
Malicious processes
6
Suspicious processes
3
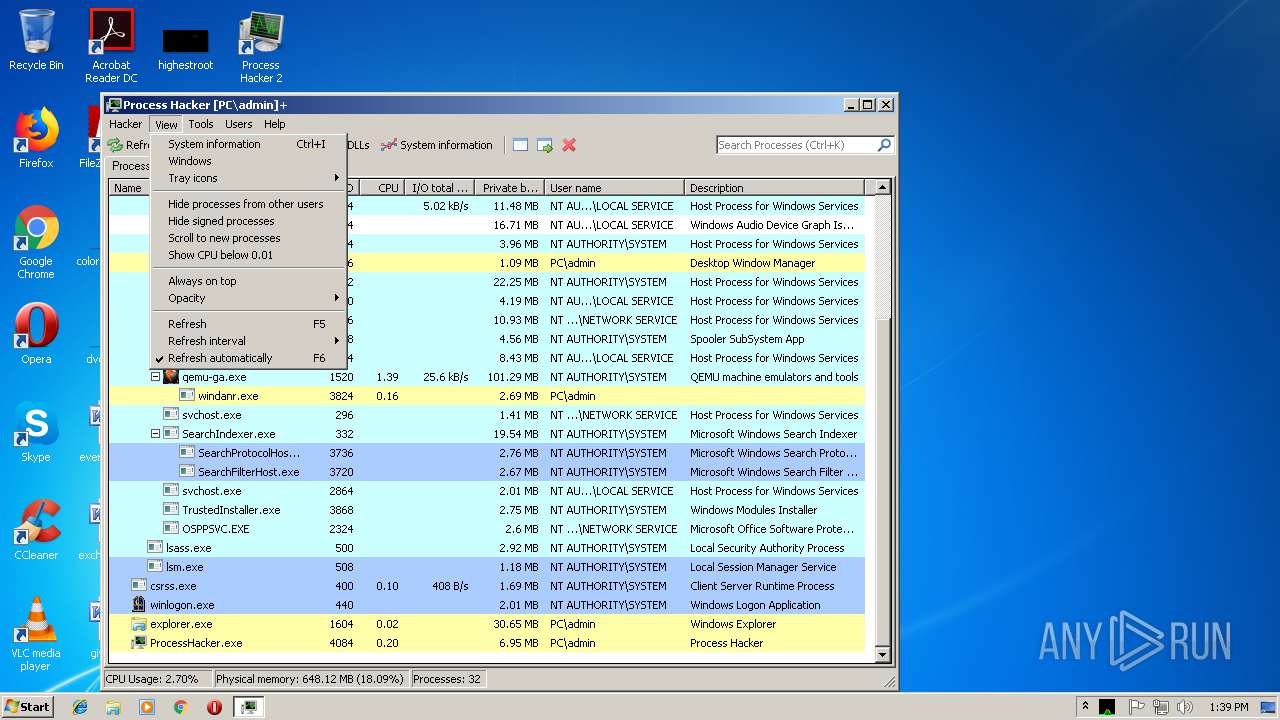
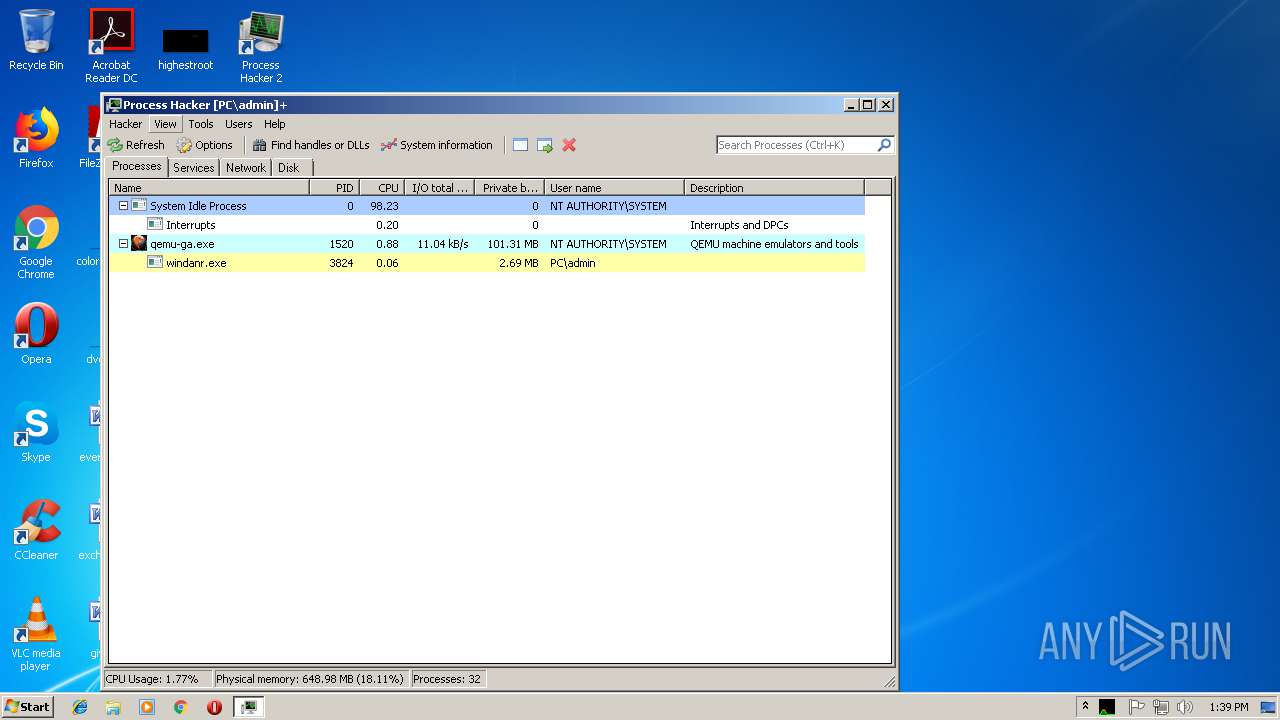
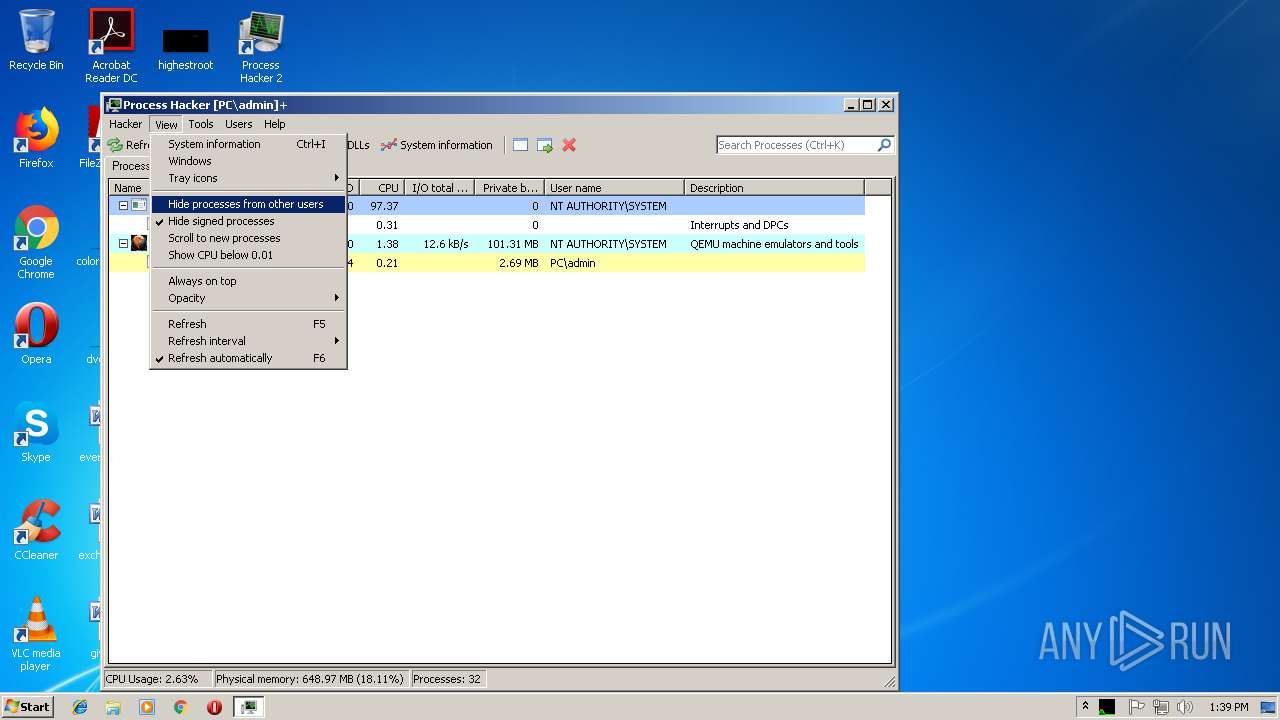
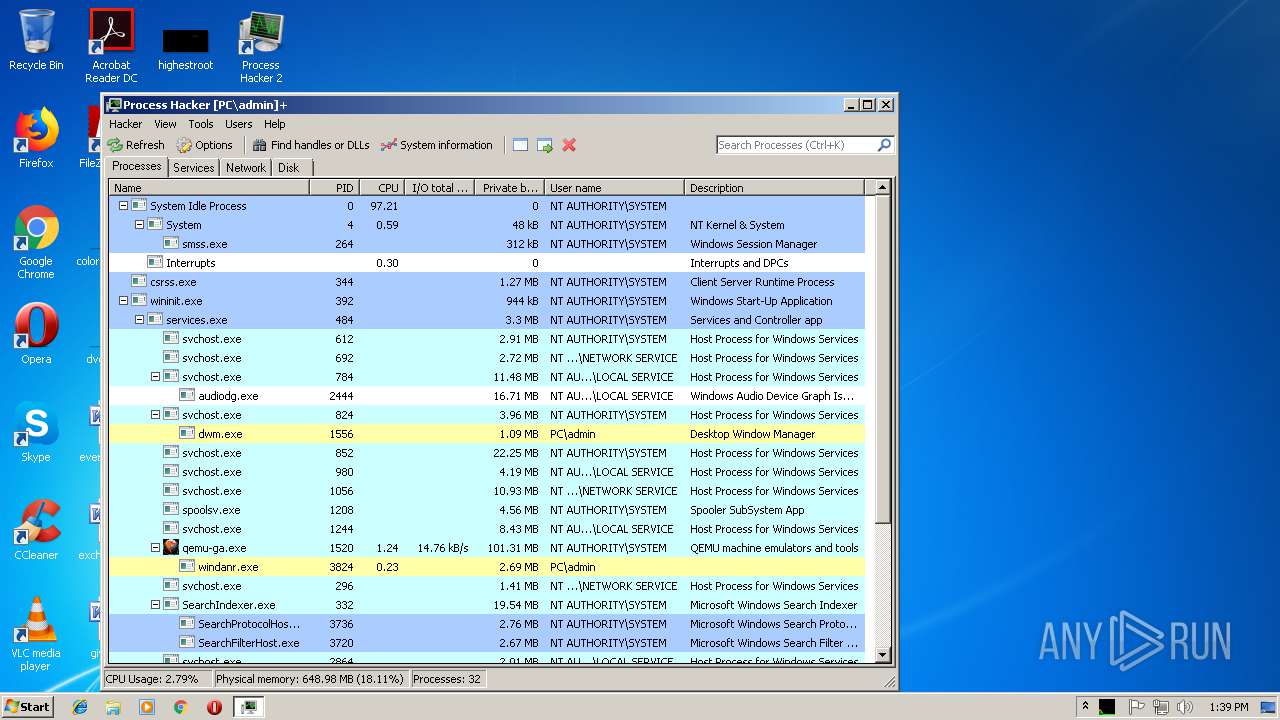
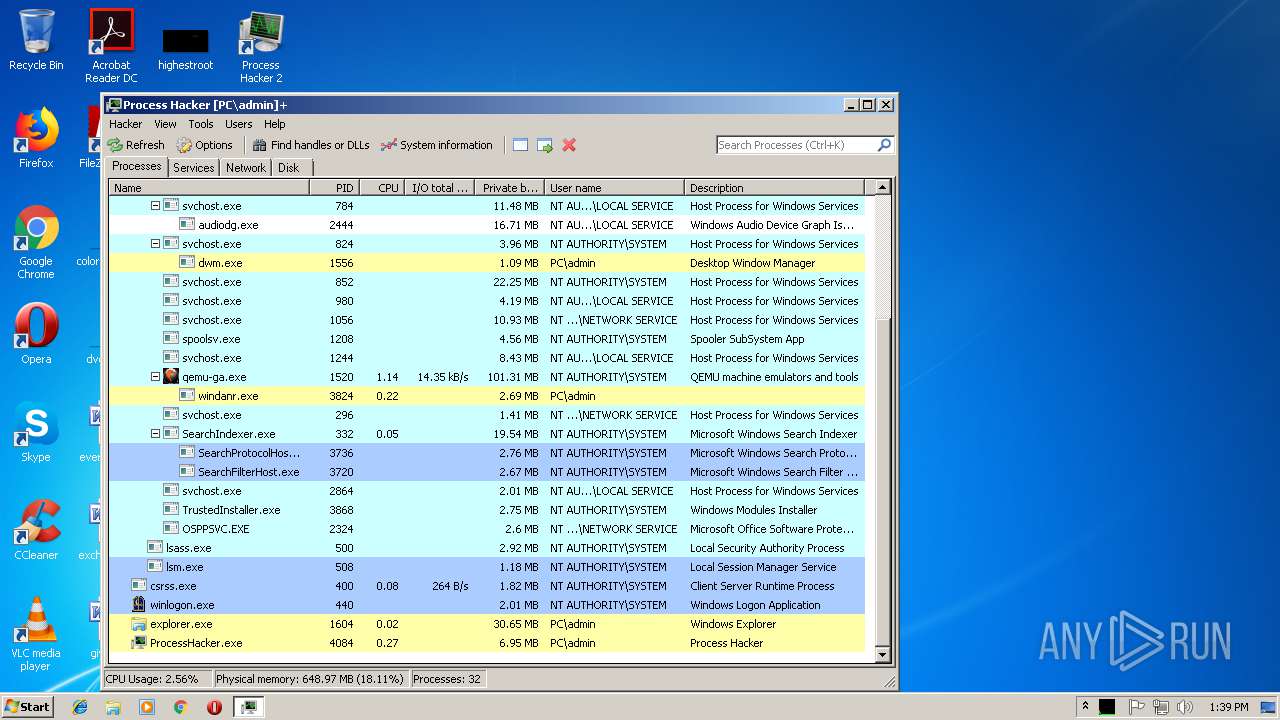
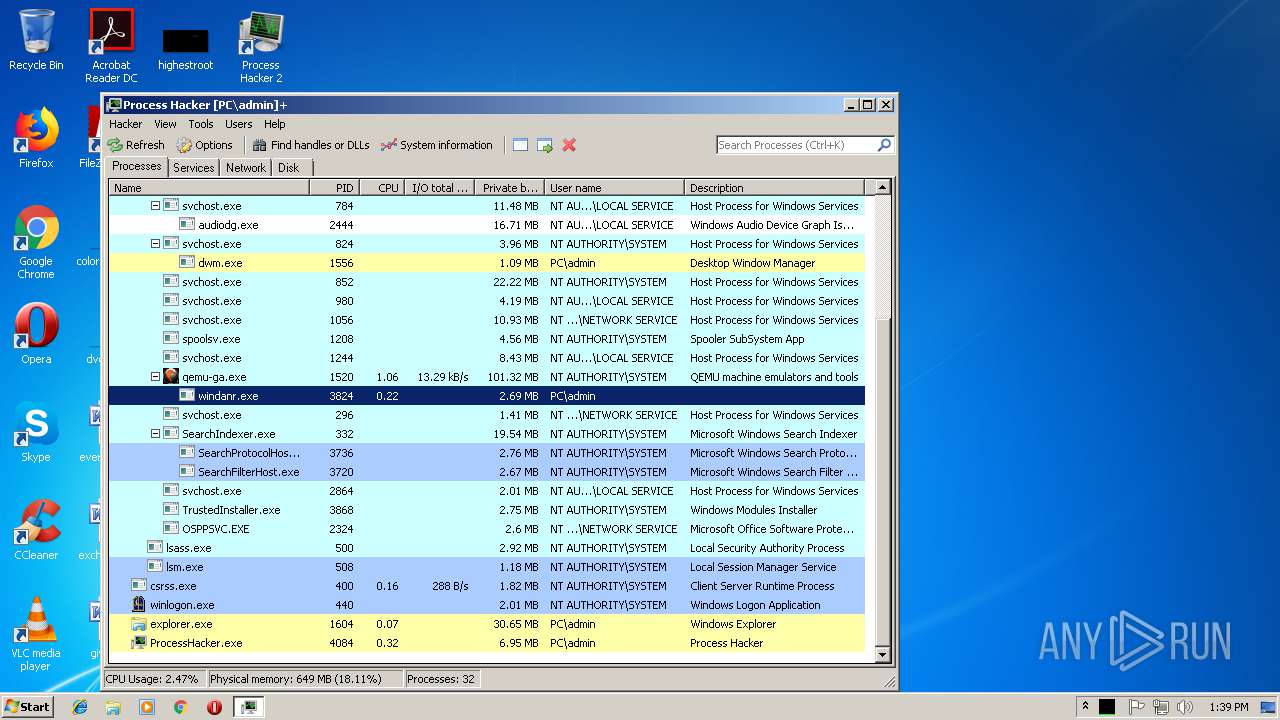
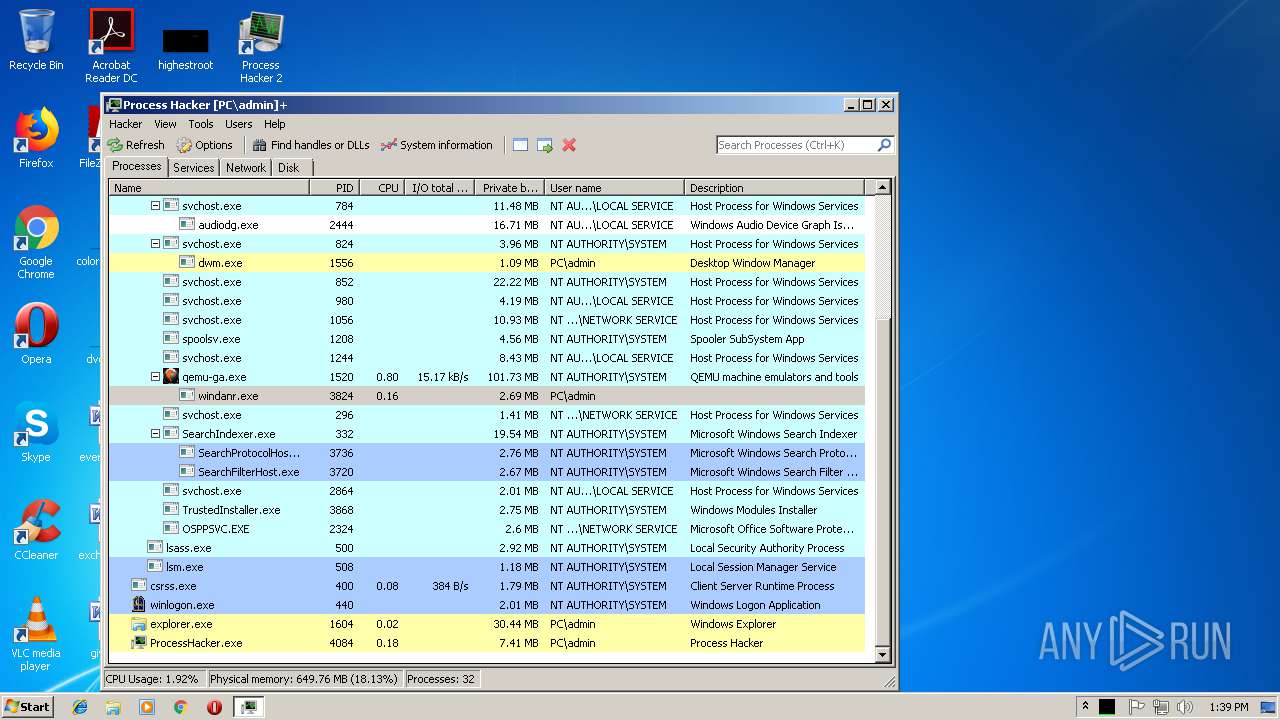
Behavior graph
Click at the process to see the details
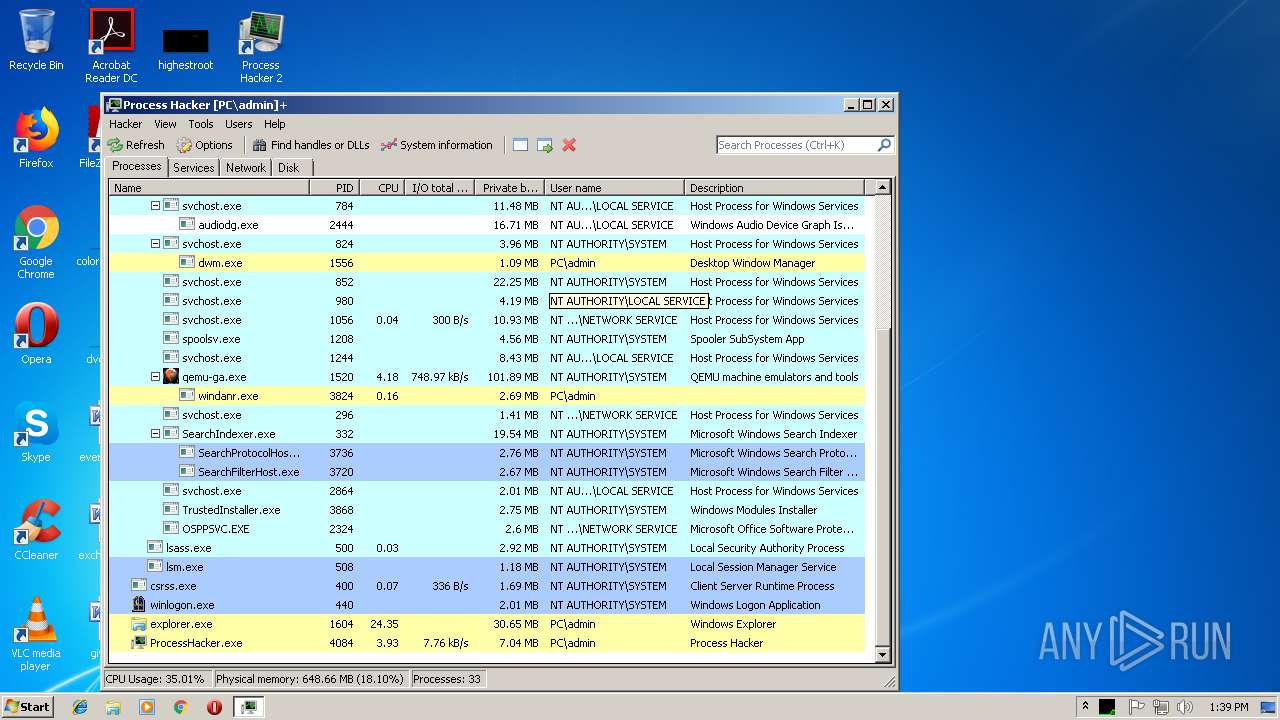
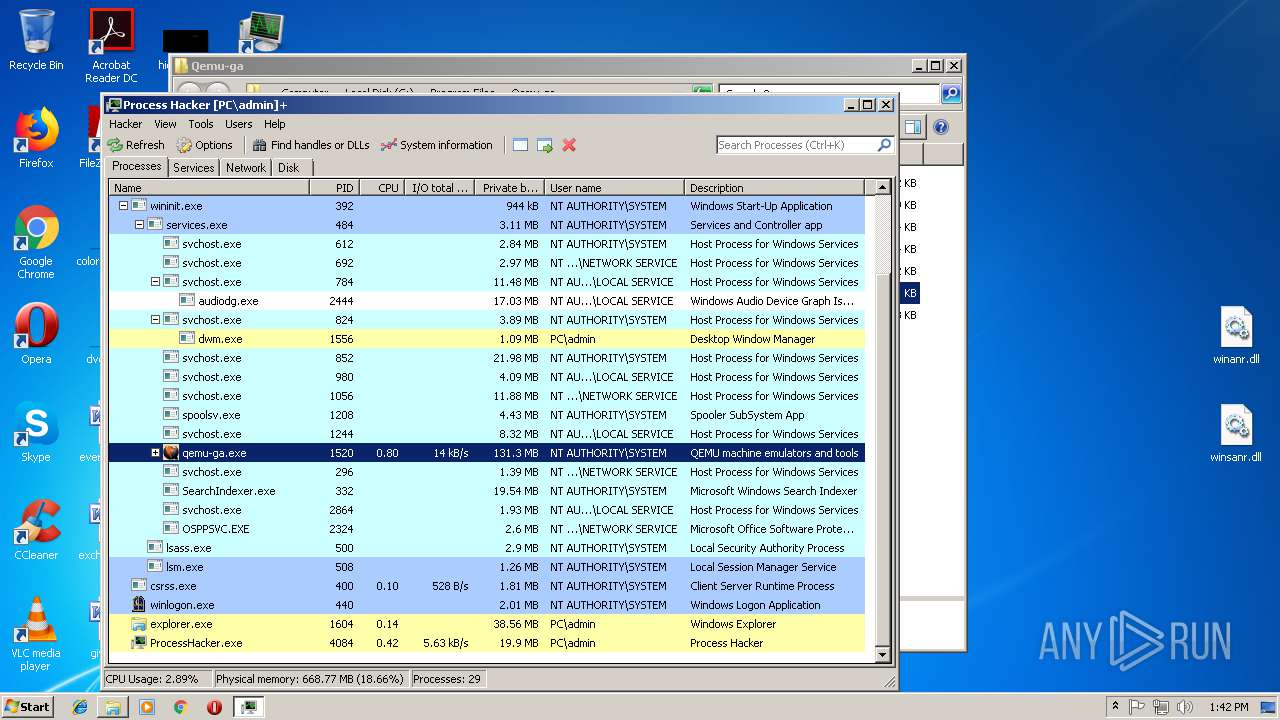
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
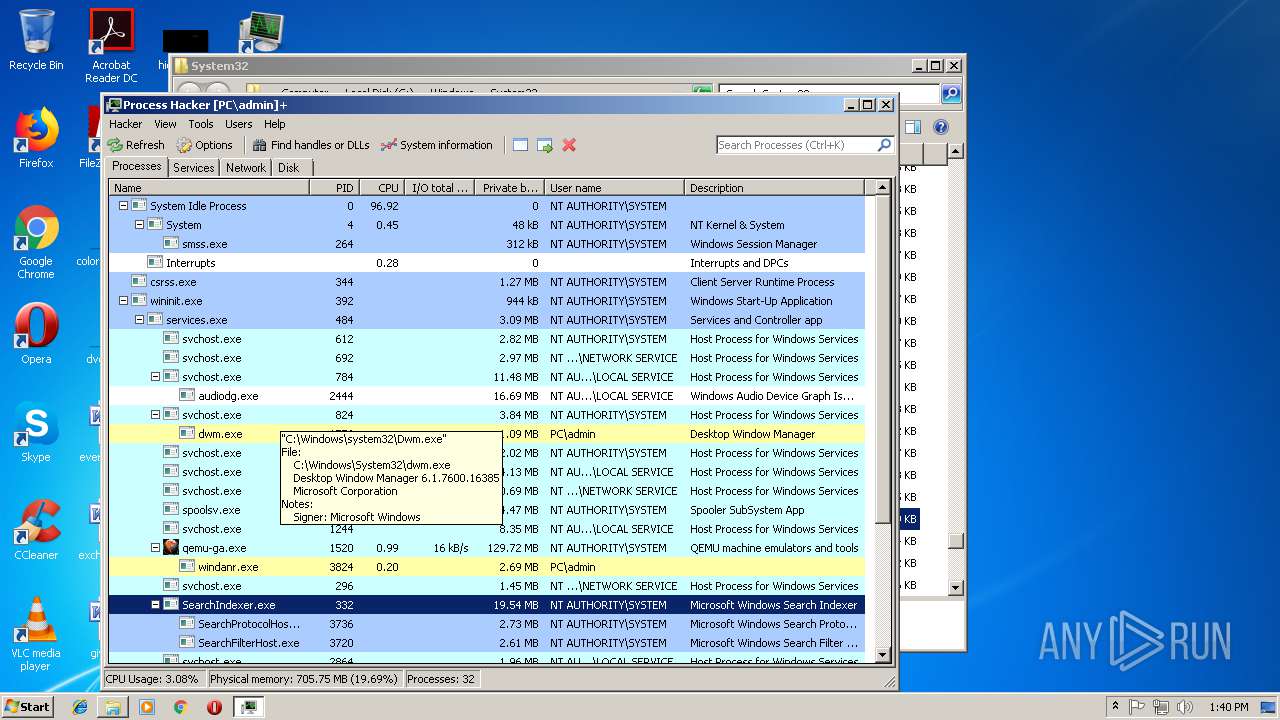
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
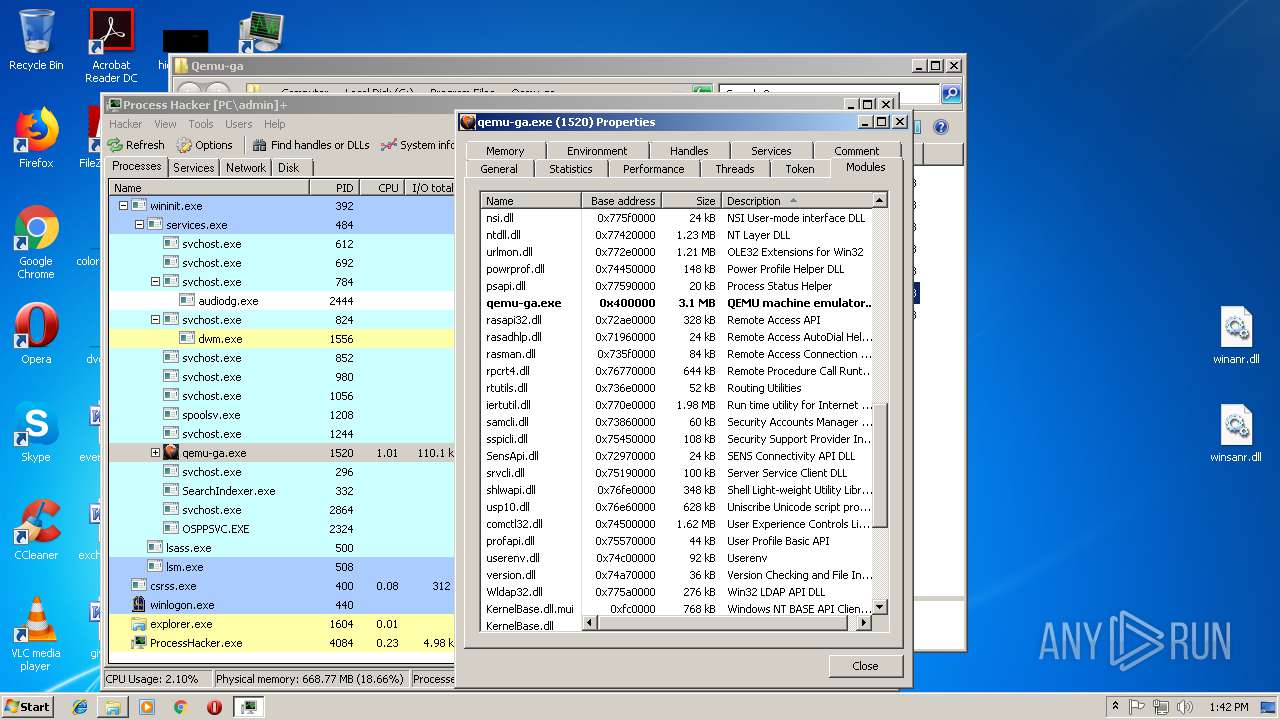
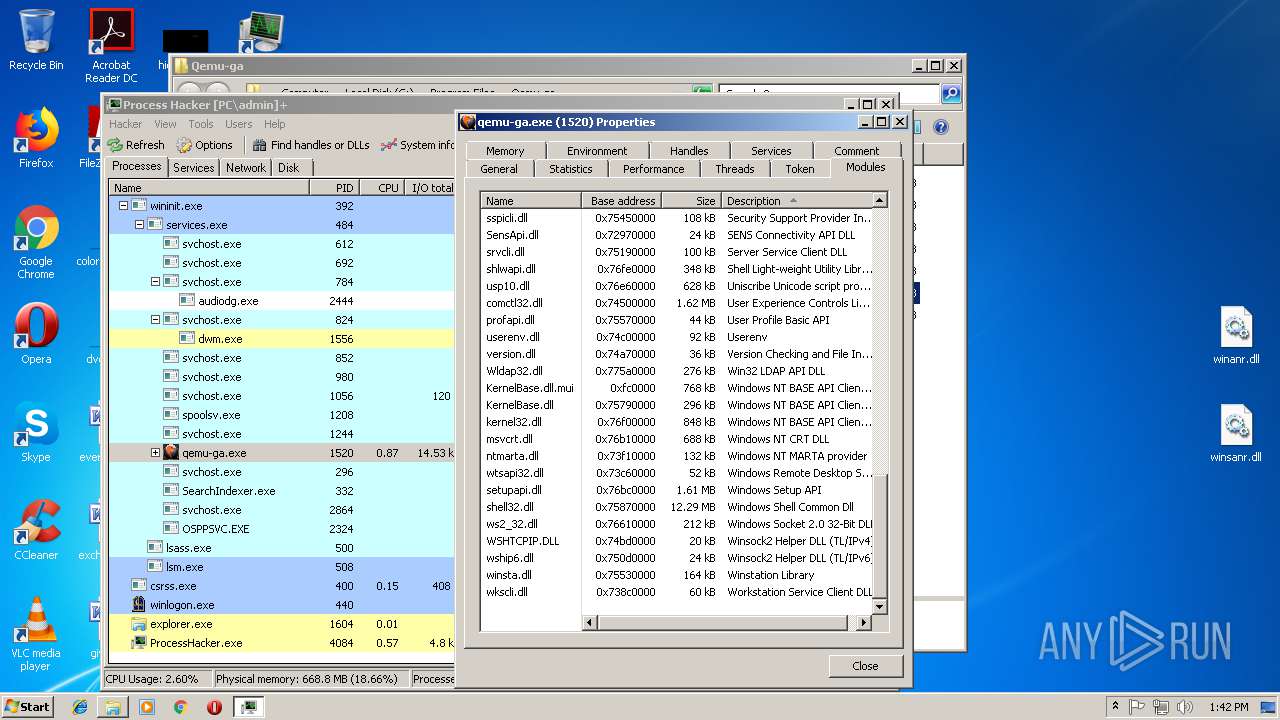
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
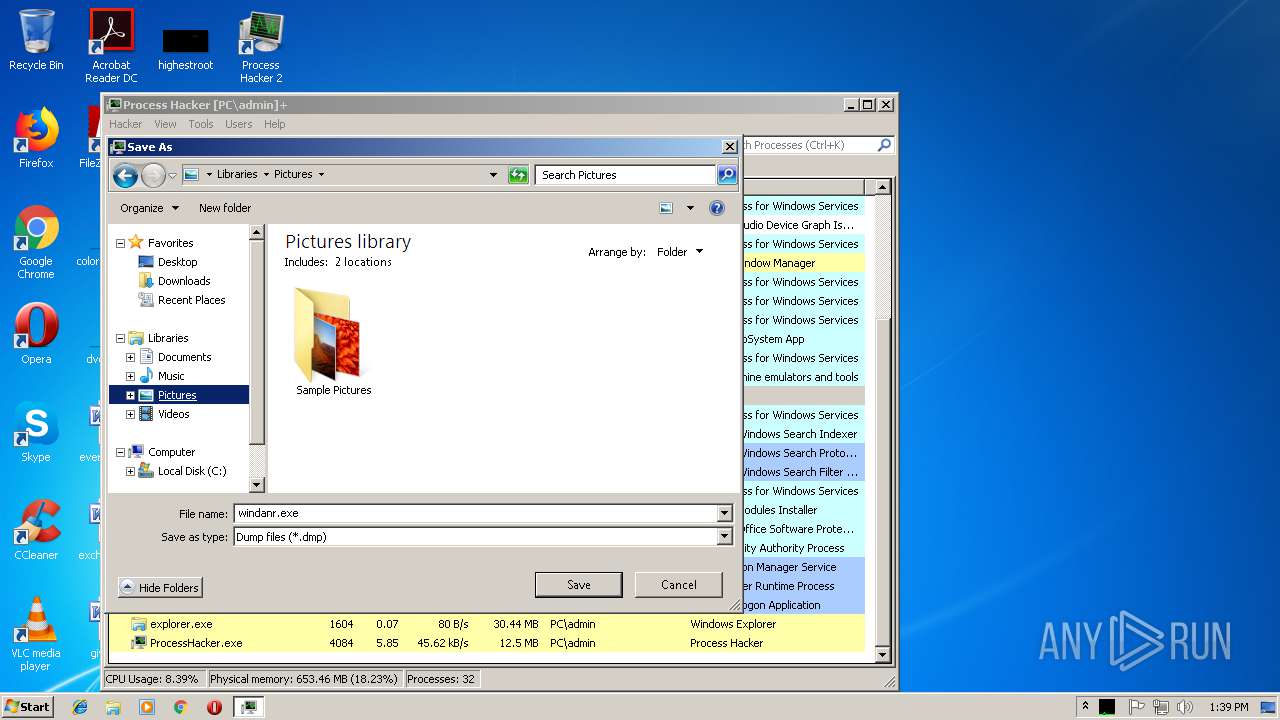
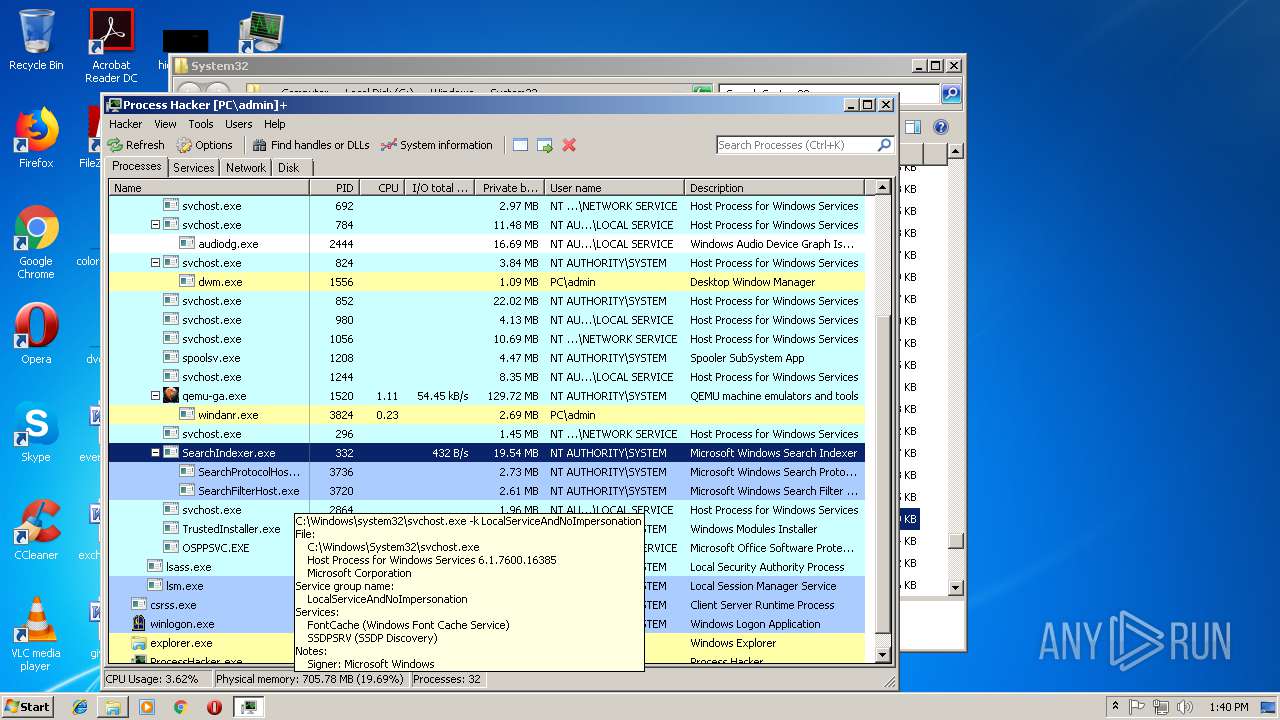
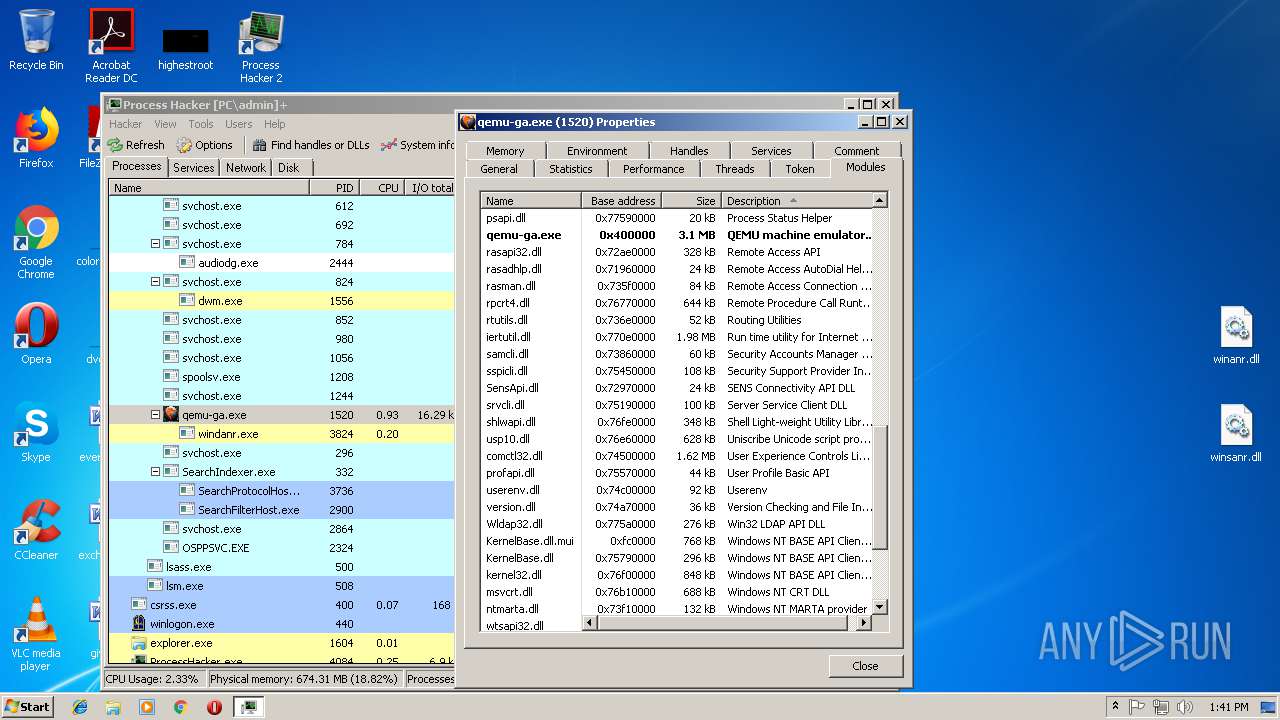
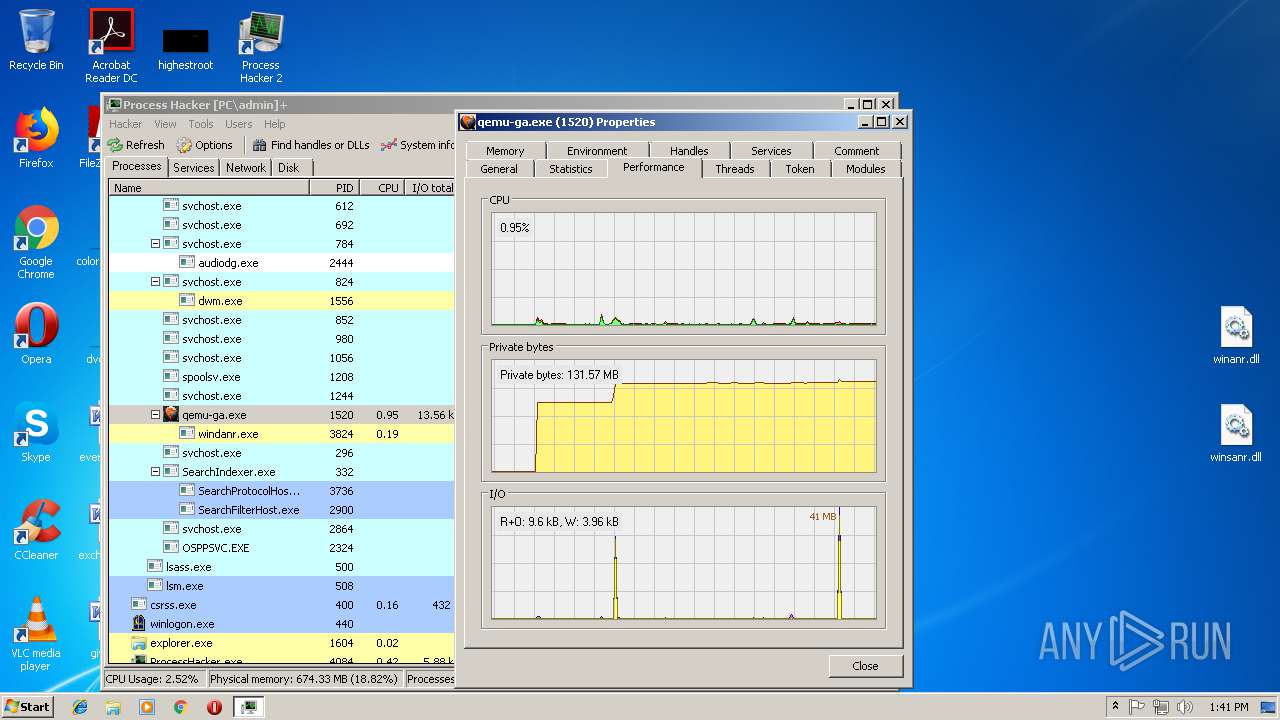
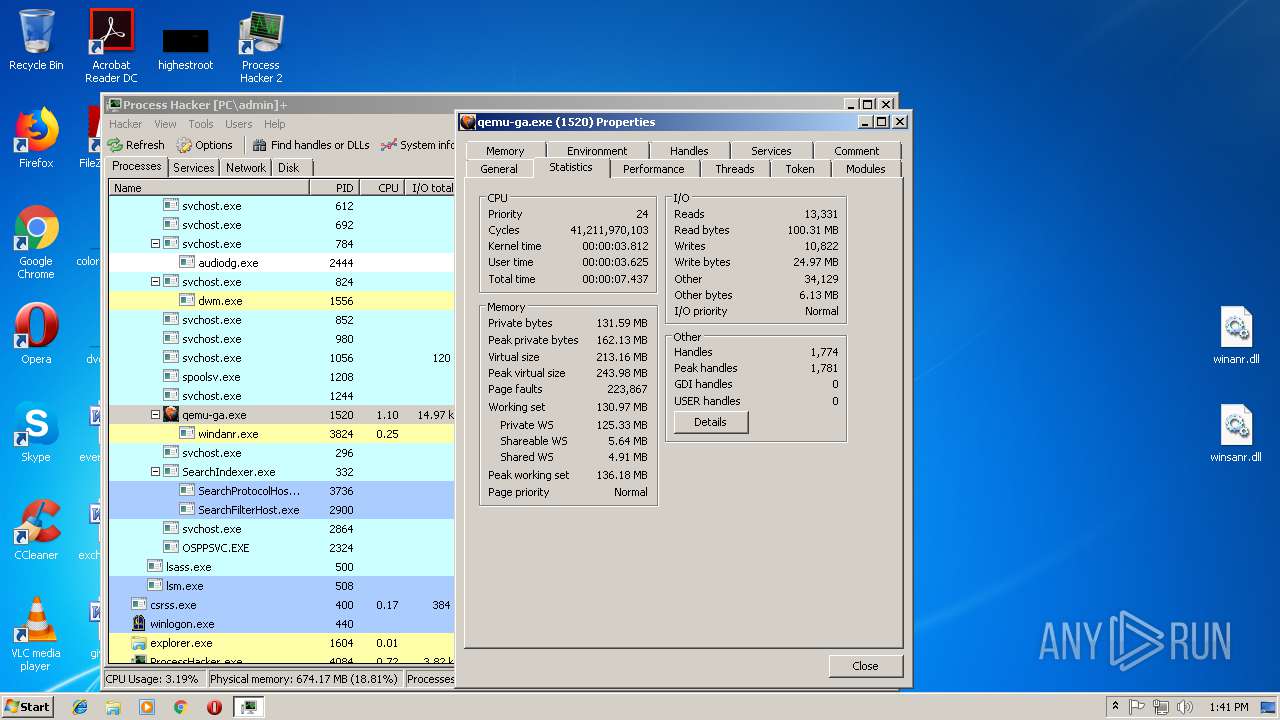
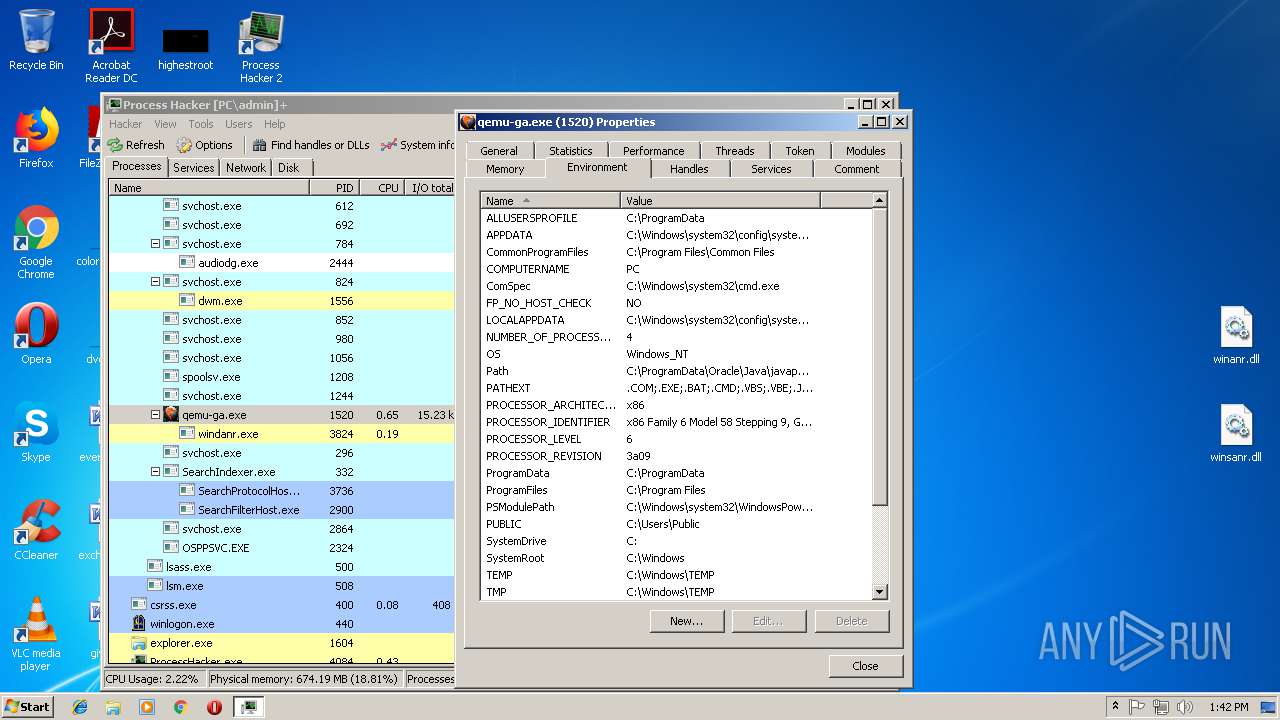
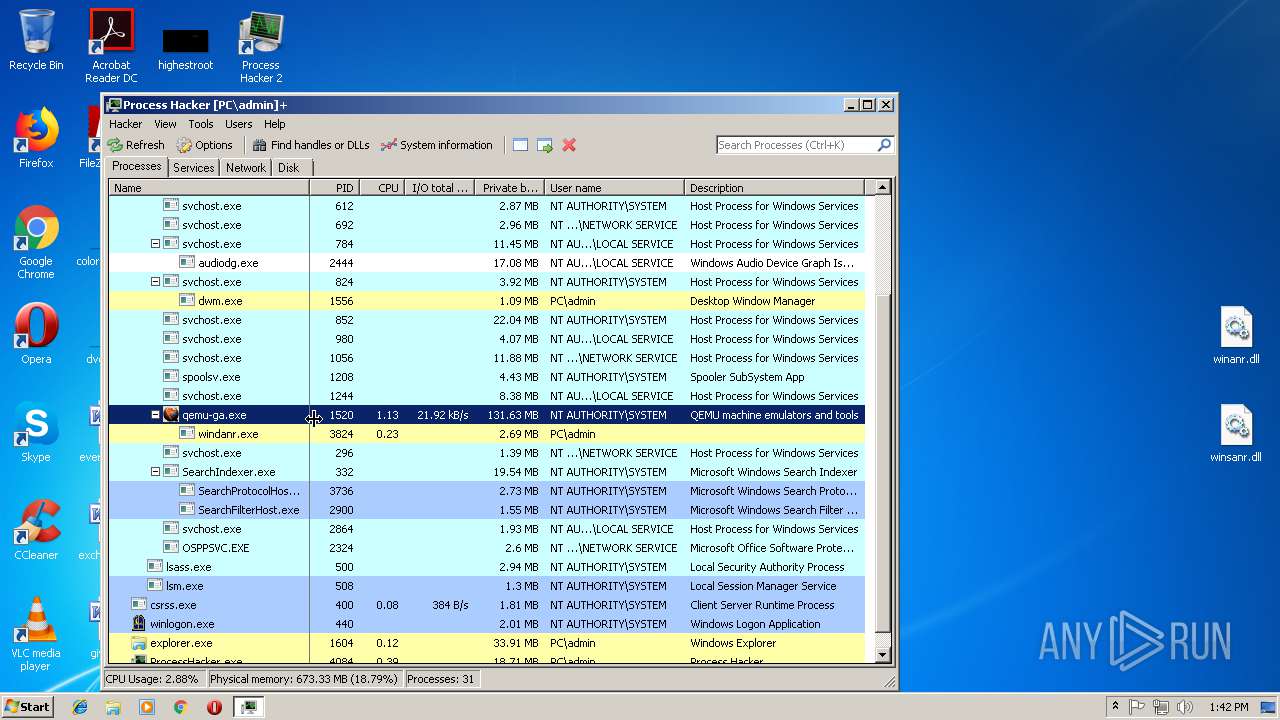
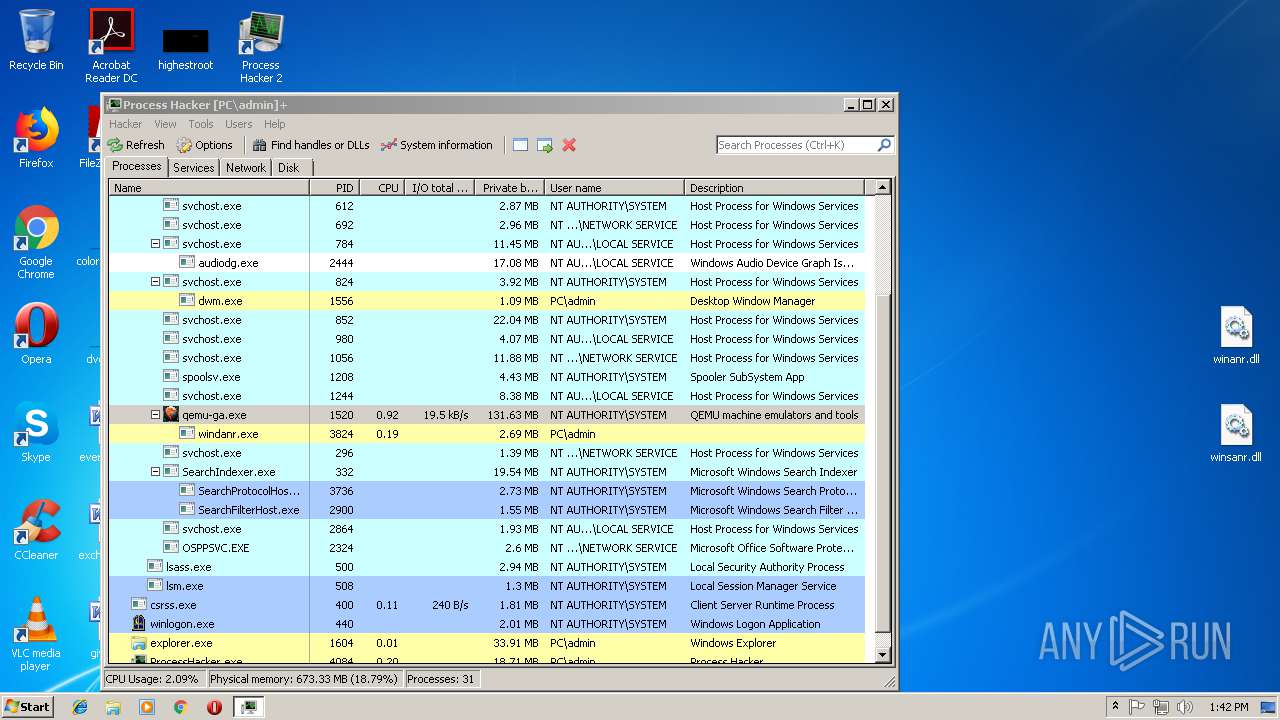
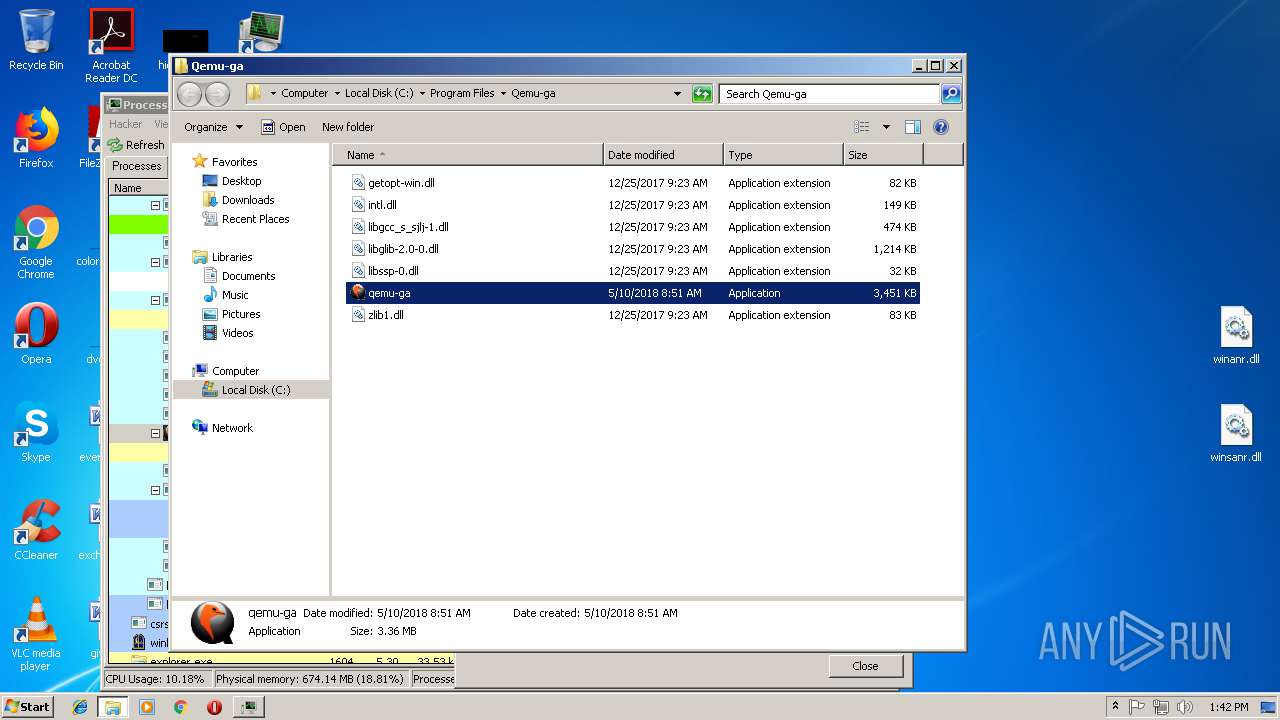
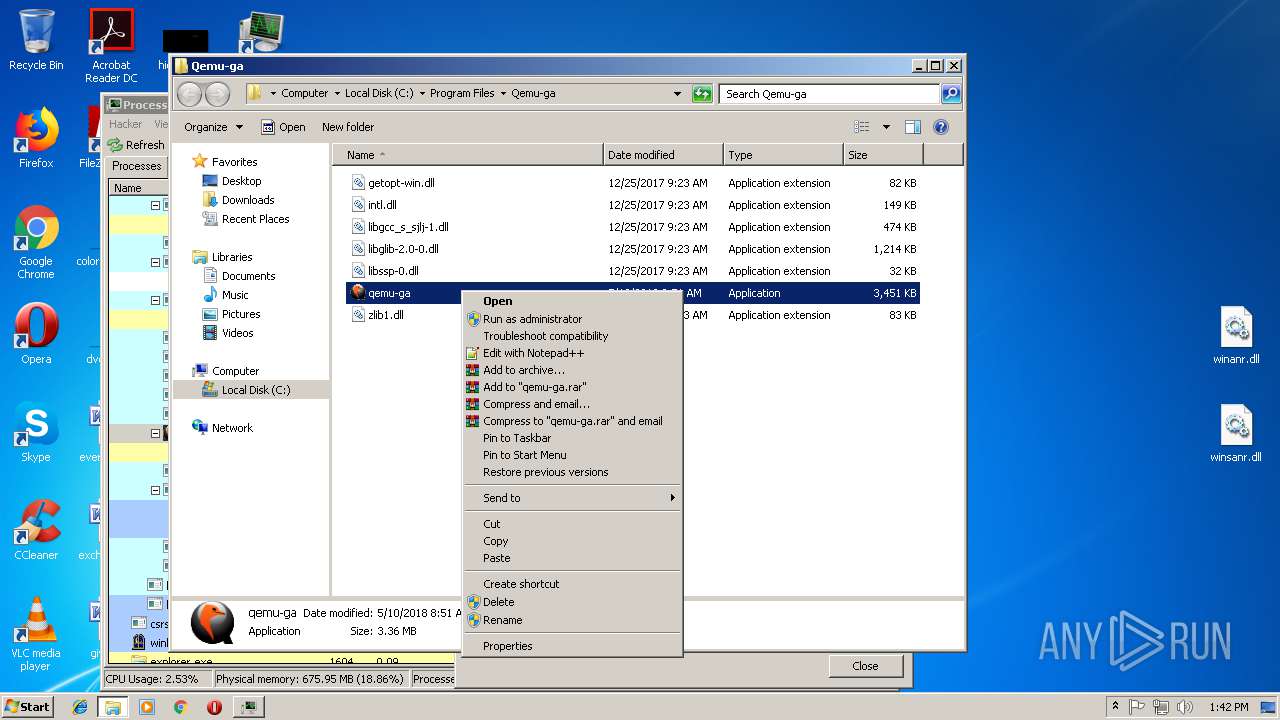
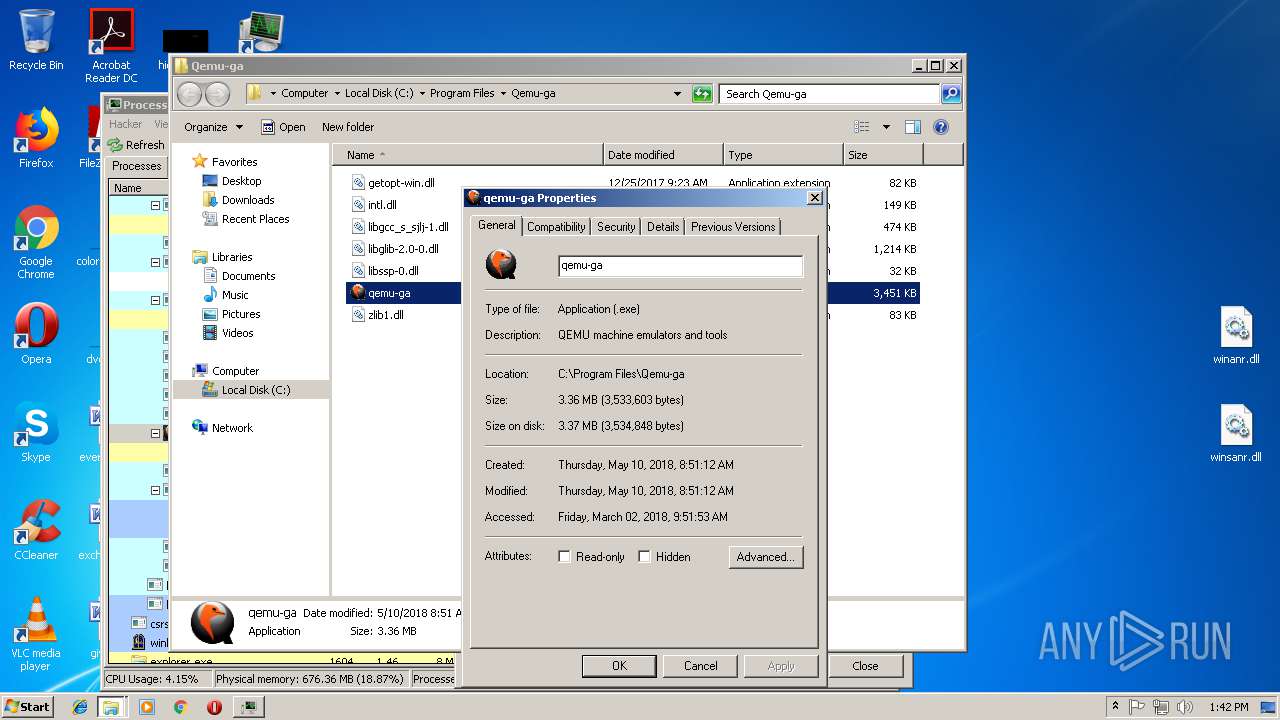
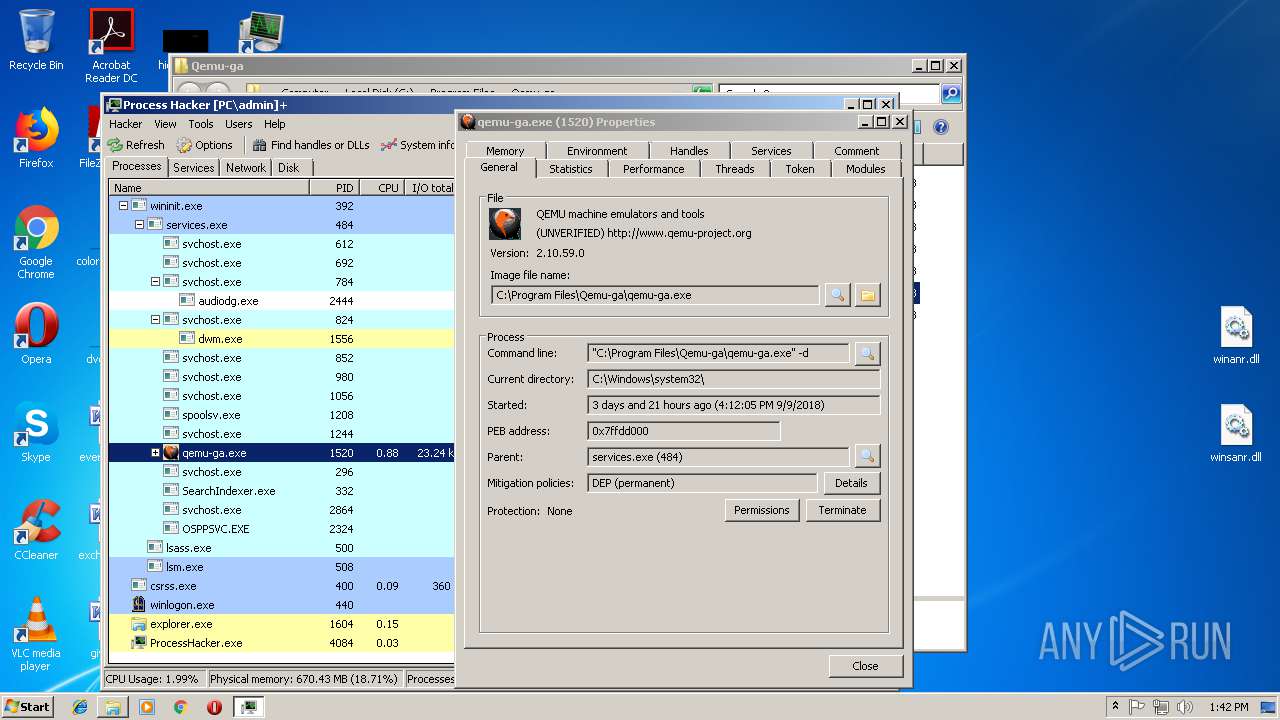
| 2632 | "windanr.exe" | C:\Windows\system32\windanr.exe | — | qemu-ga.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225794 Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe" | C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe | explorer.exe | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\AppData\Local\Temp\is-64AI9.tmp\processhacker-2.39-setup.tmp" /SL5="$B014E,1874675,150016,C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-64AI9.tmp\processhacker-2.39-setup.tmp | — | processhacker-2.39-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe" /SPAWNWND=$C01A4 /NOTIFYWND=$B014E | C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 3304 | "C:\Users\admin\AppData\Local\Temp\is-O3VUT.tmp\processhacker-2.39-setup.tmp" /SL5="$D015E,1874675,150016,C:\Users\admin\AppData\Local\Temp\processhacker-2.39-setup.exe" /SPAWNWND=$C01A4 /NOTIFYWND=$B014E | C:\Users\admin\AppData\Local\Temp\is-O3VUT.tmp\processhacker-2.39-setup.tmp | processhacker-2.39-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
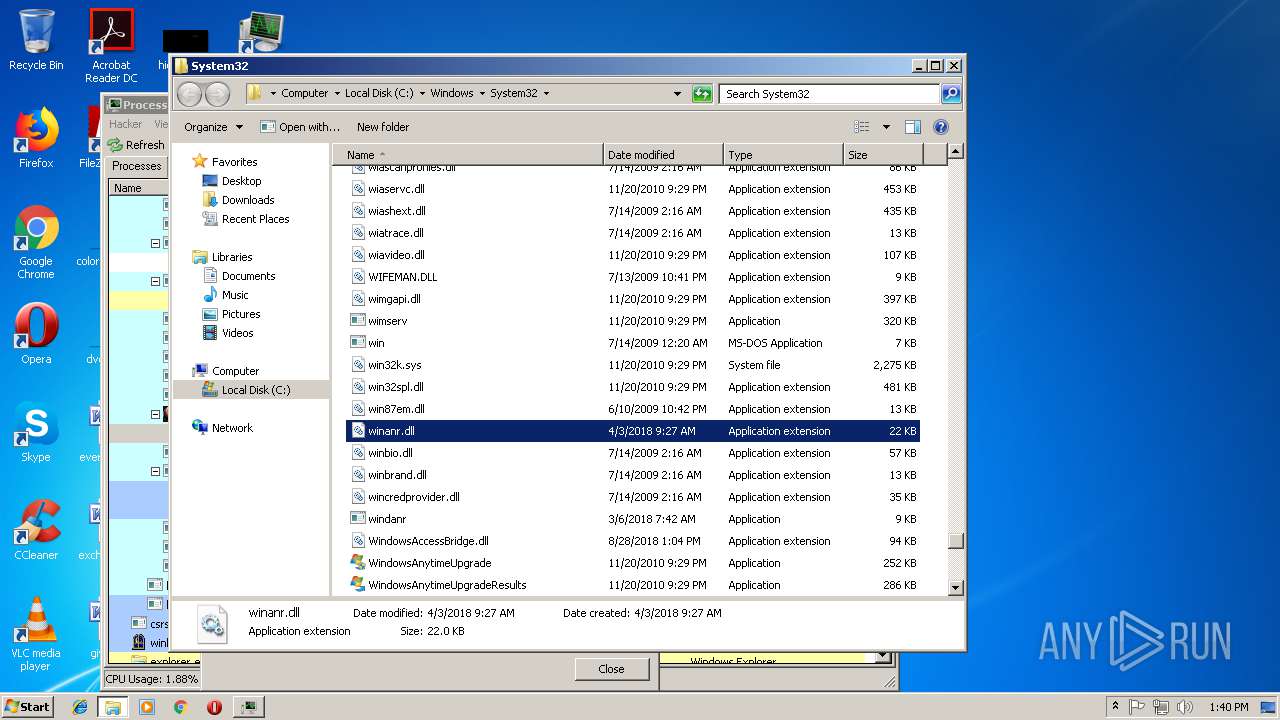
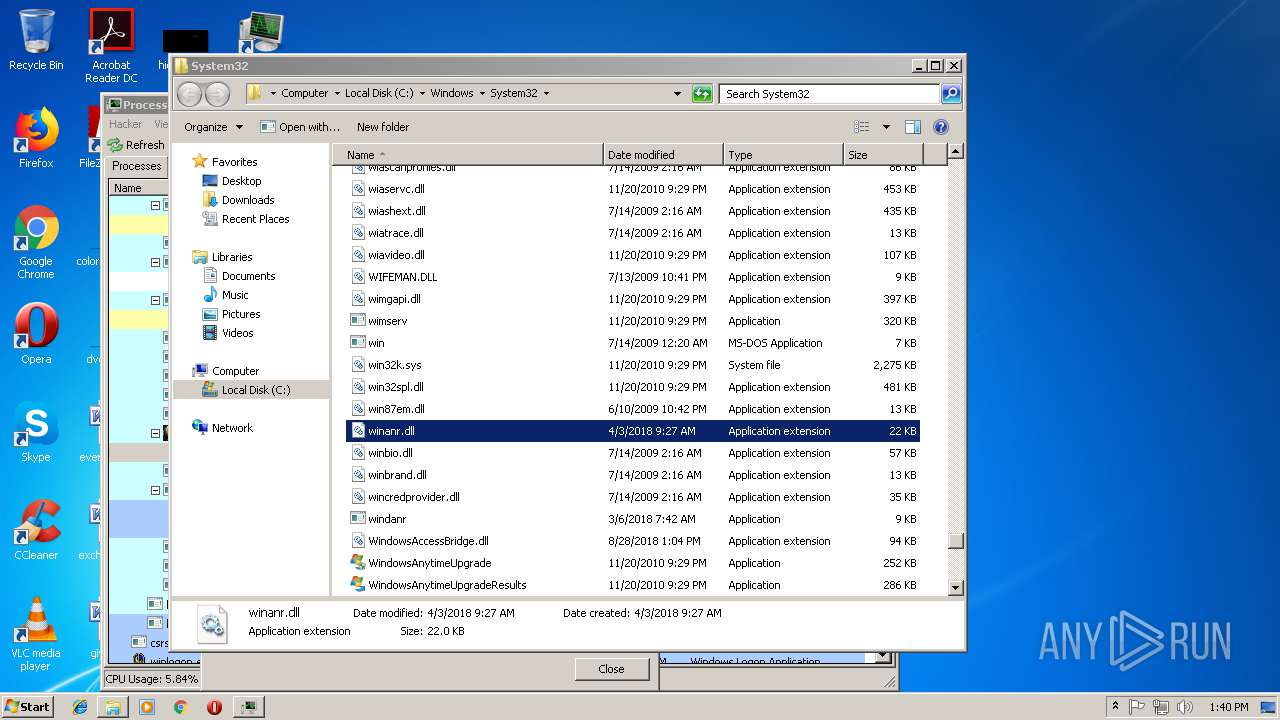
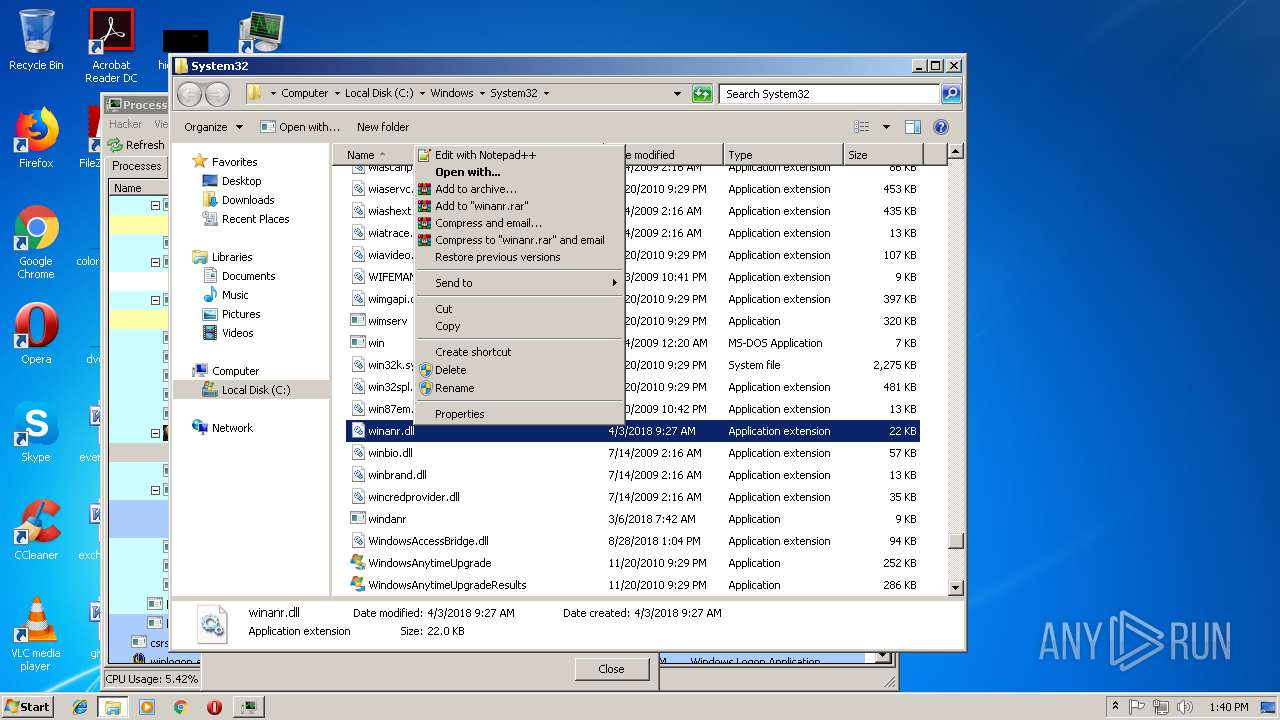
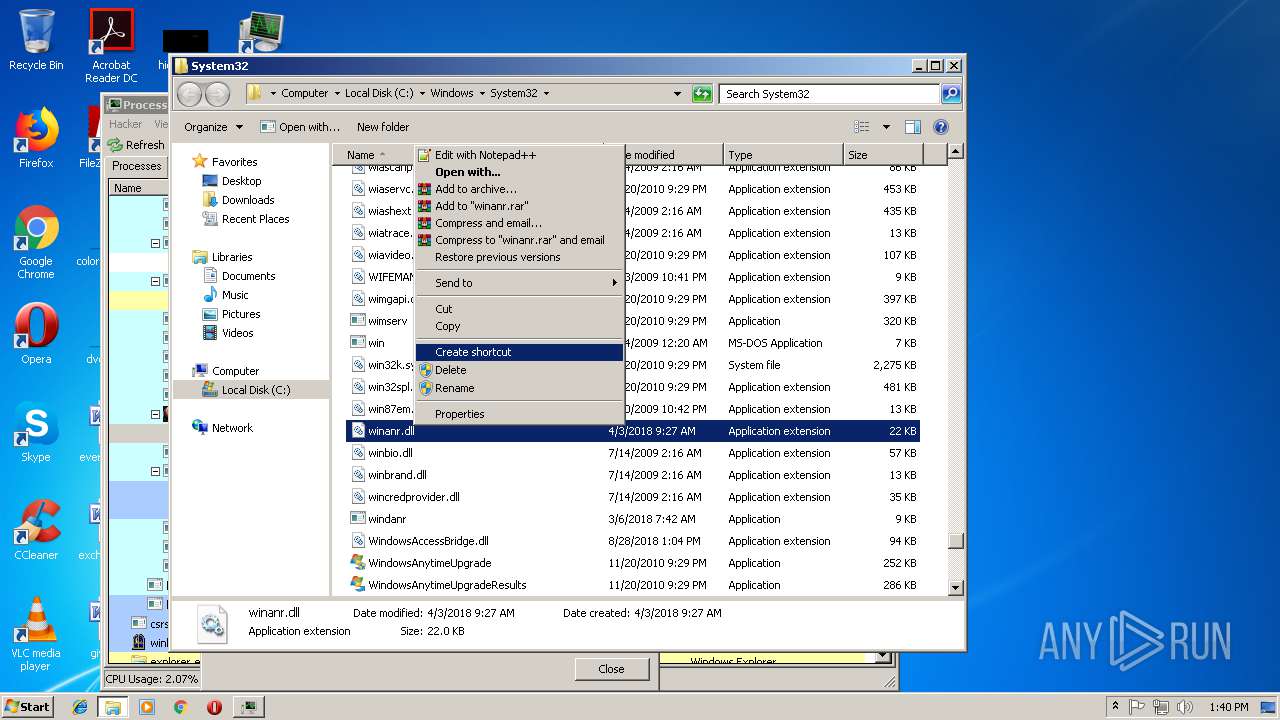
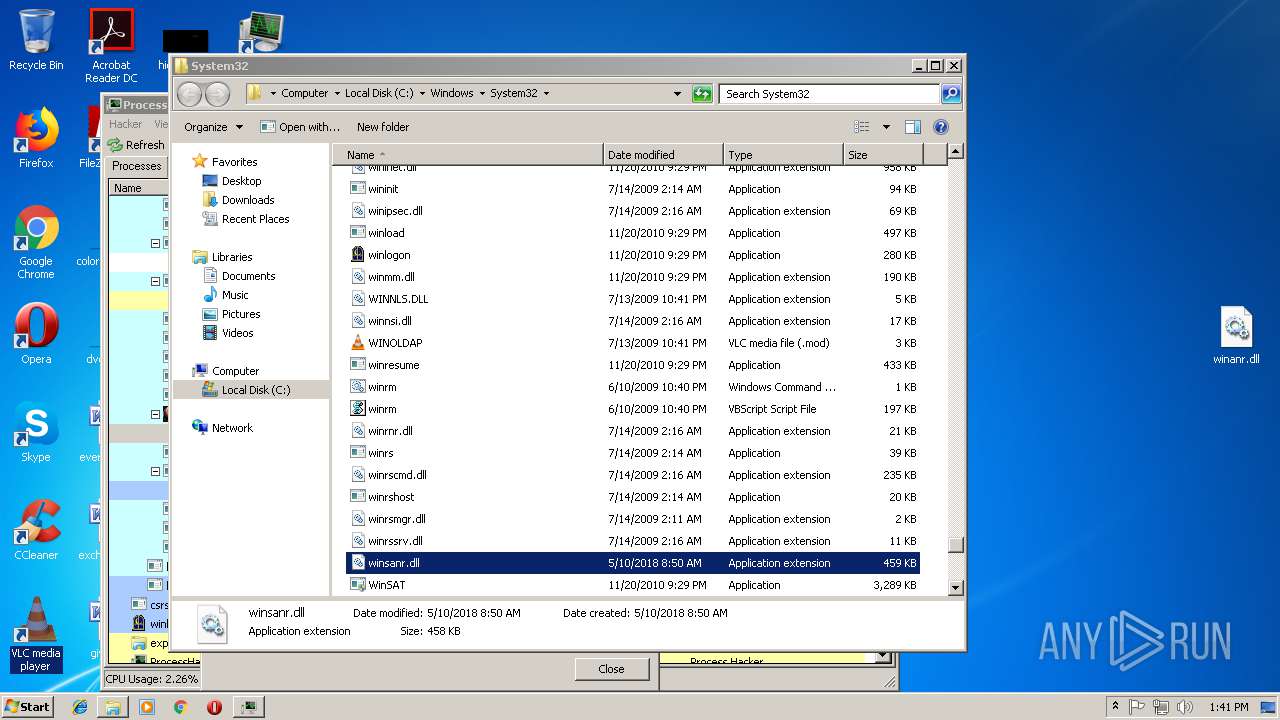
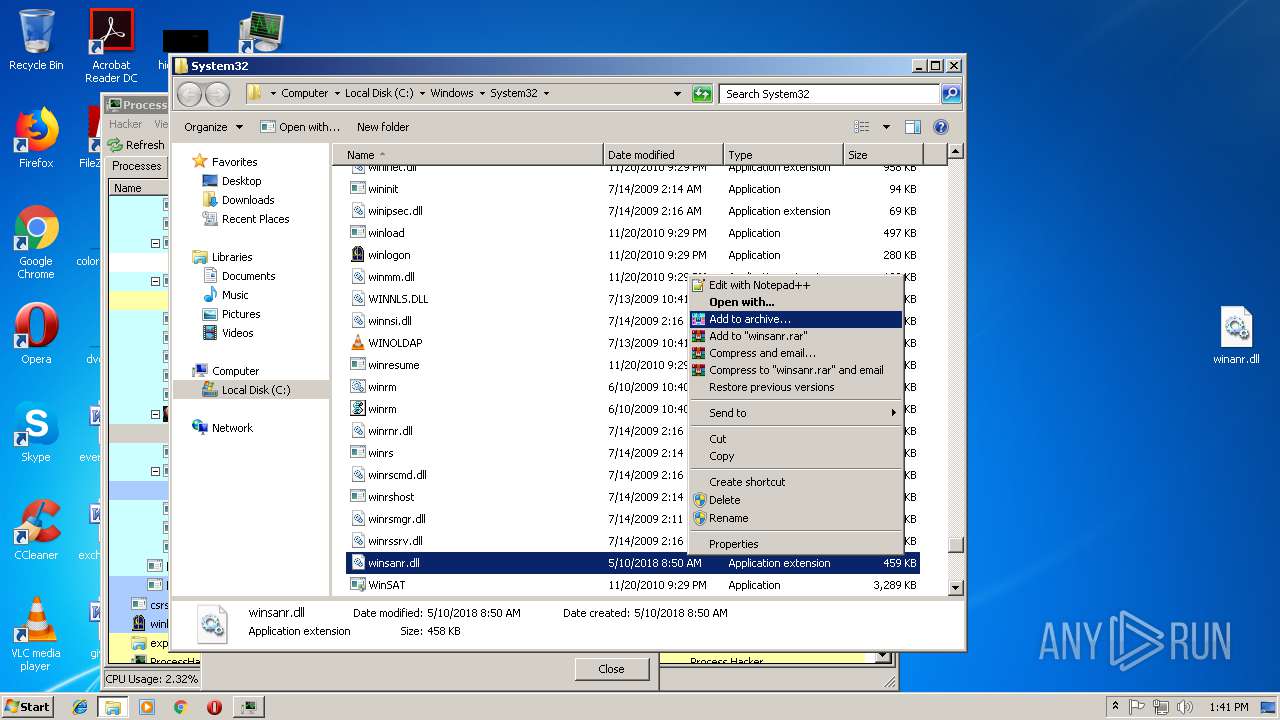
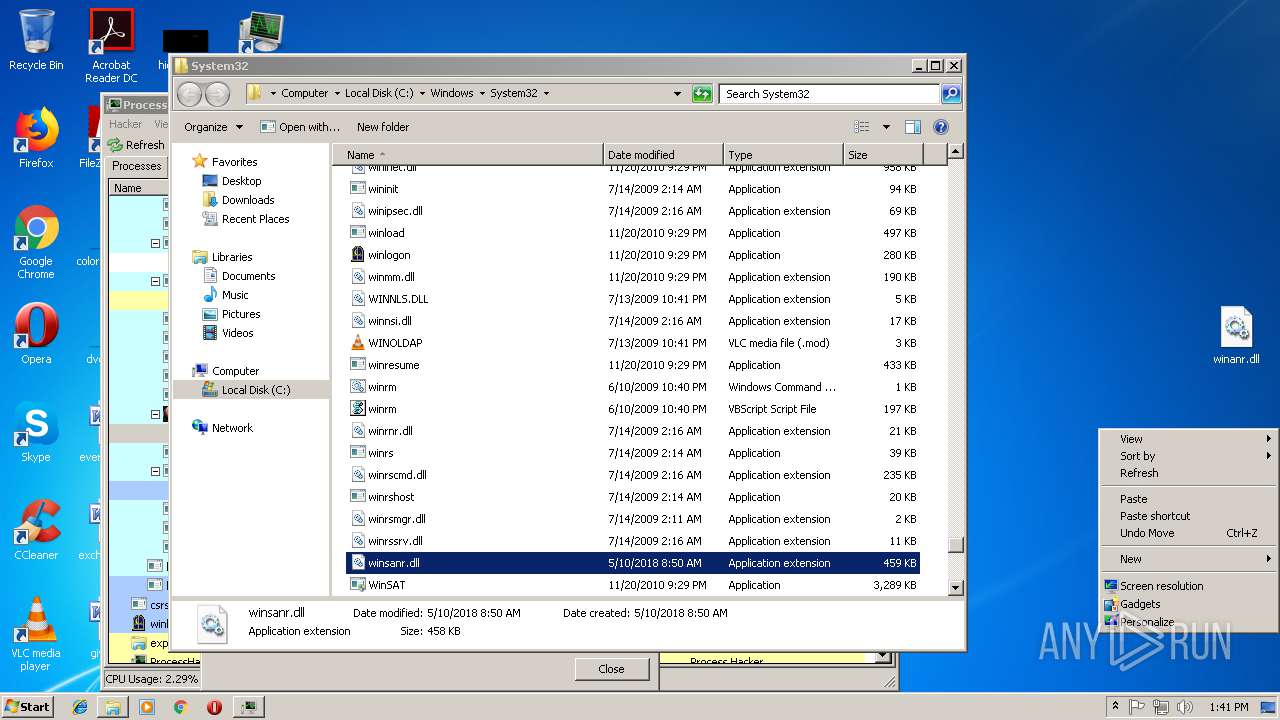
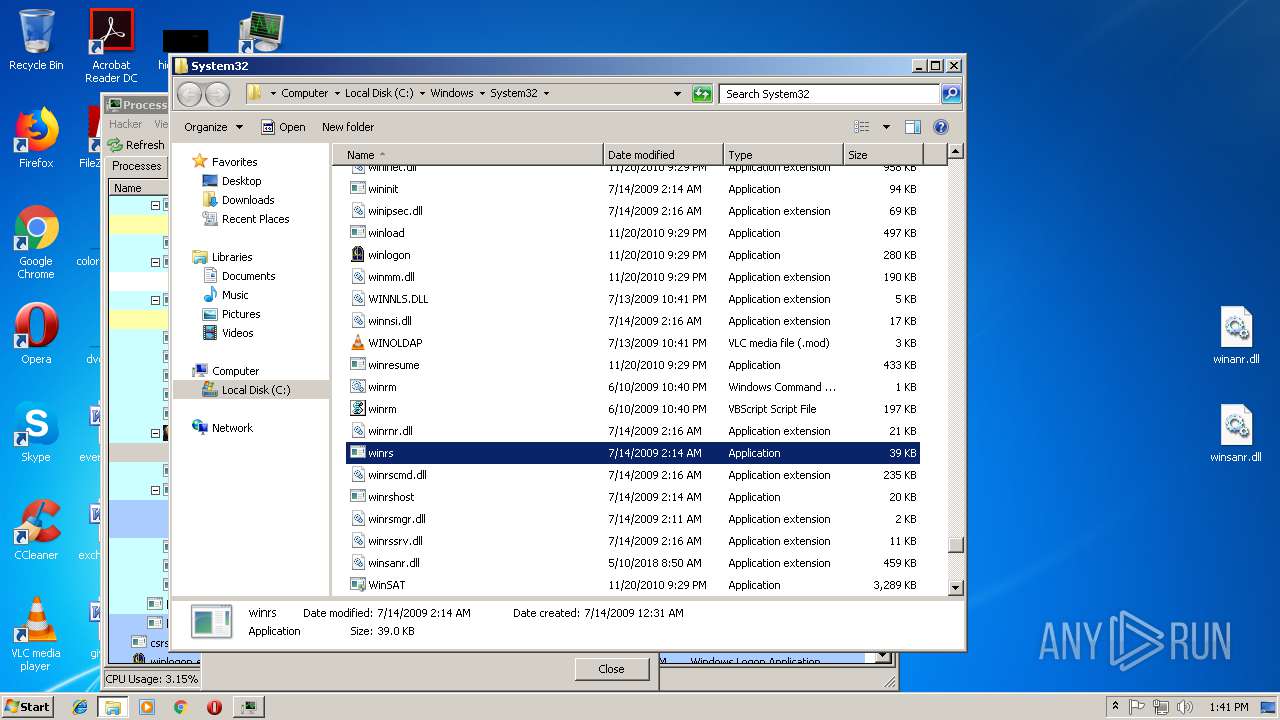
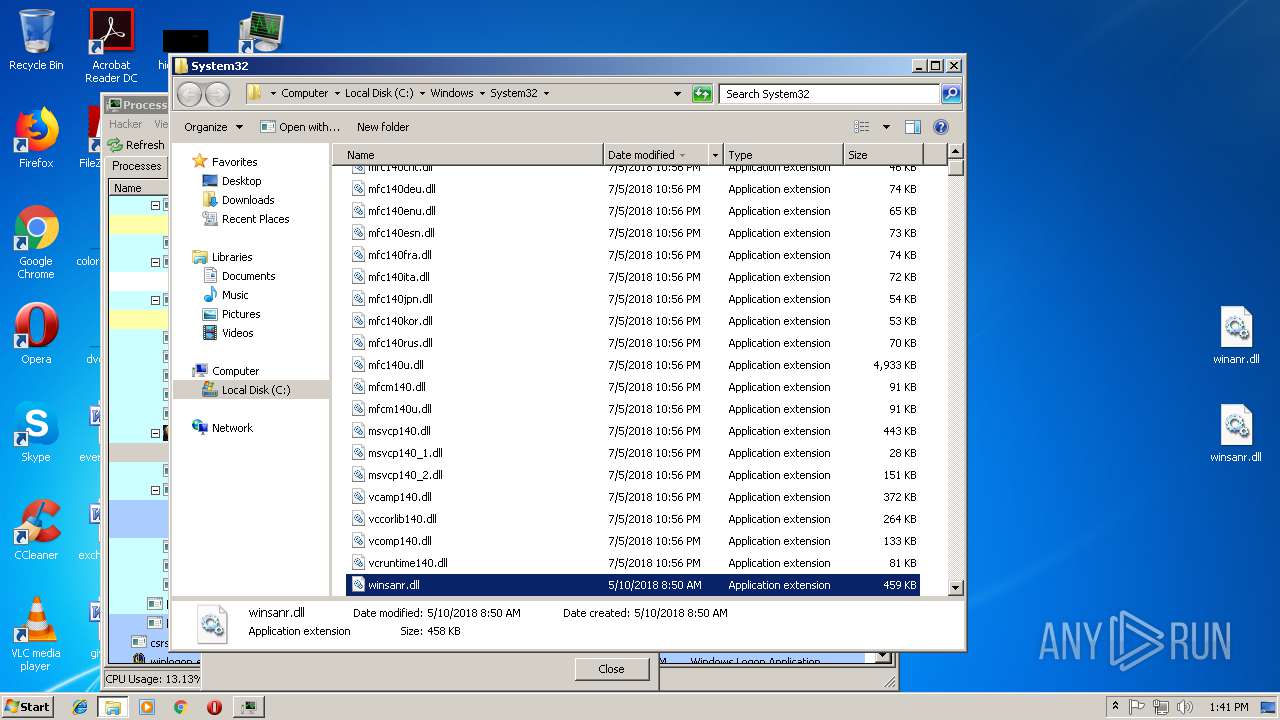
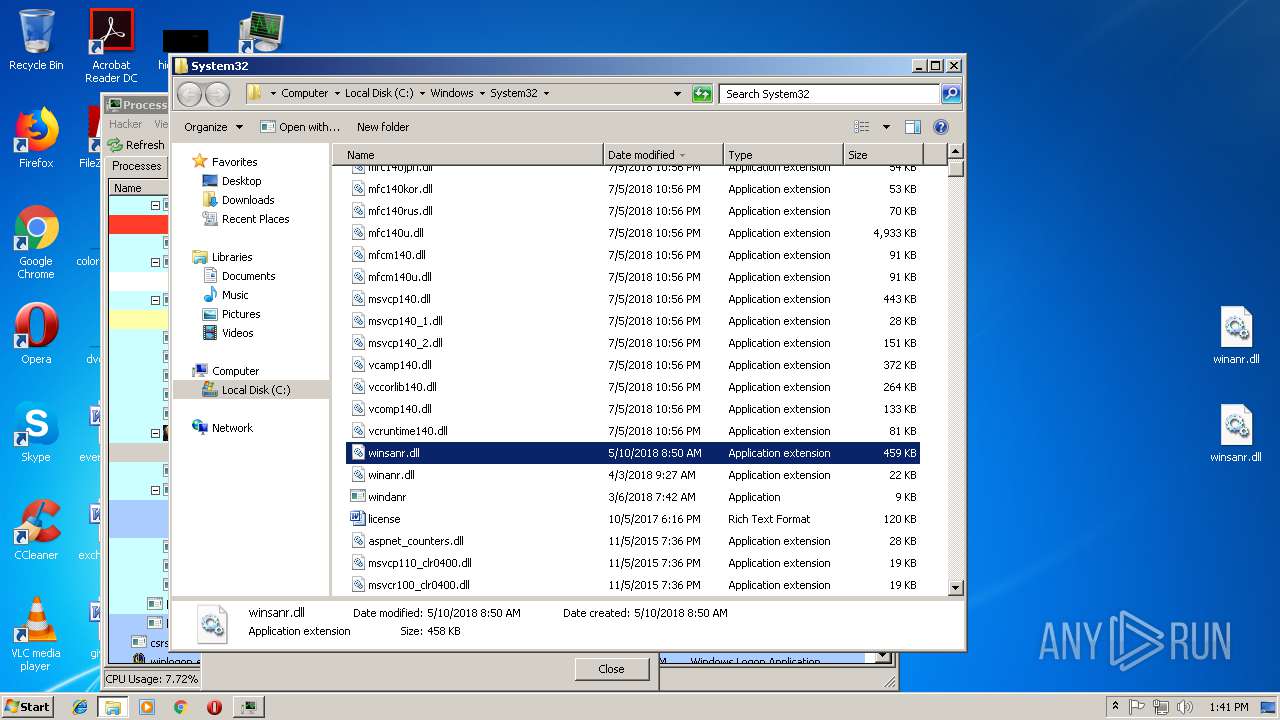
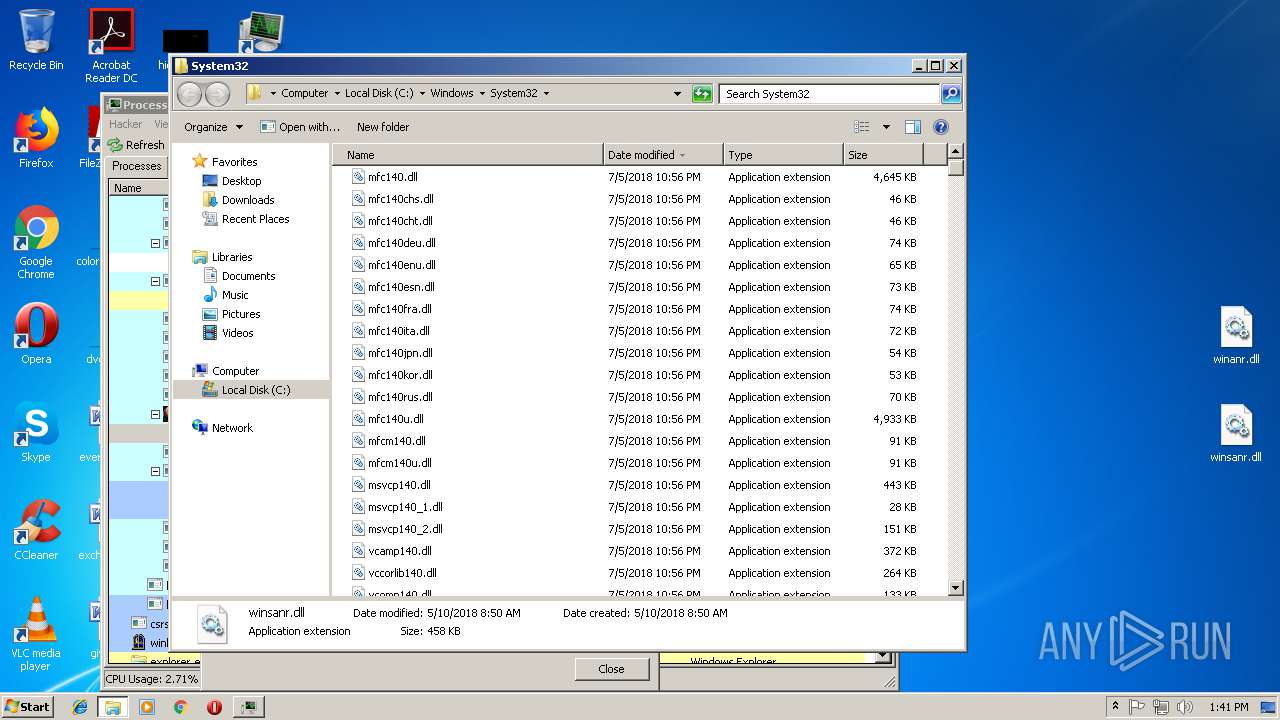
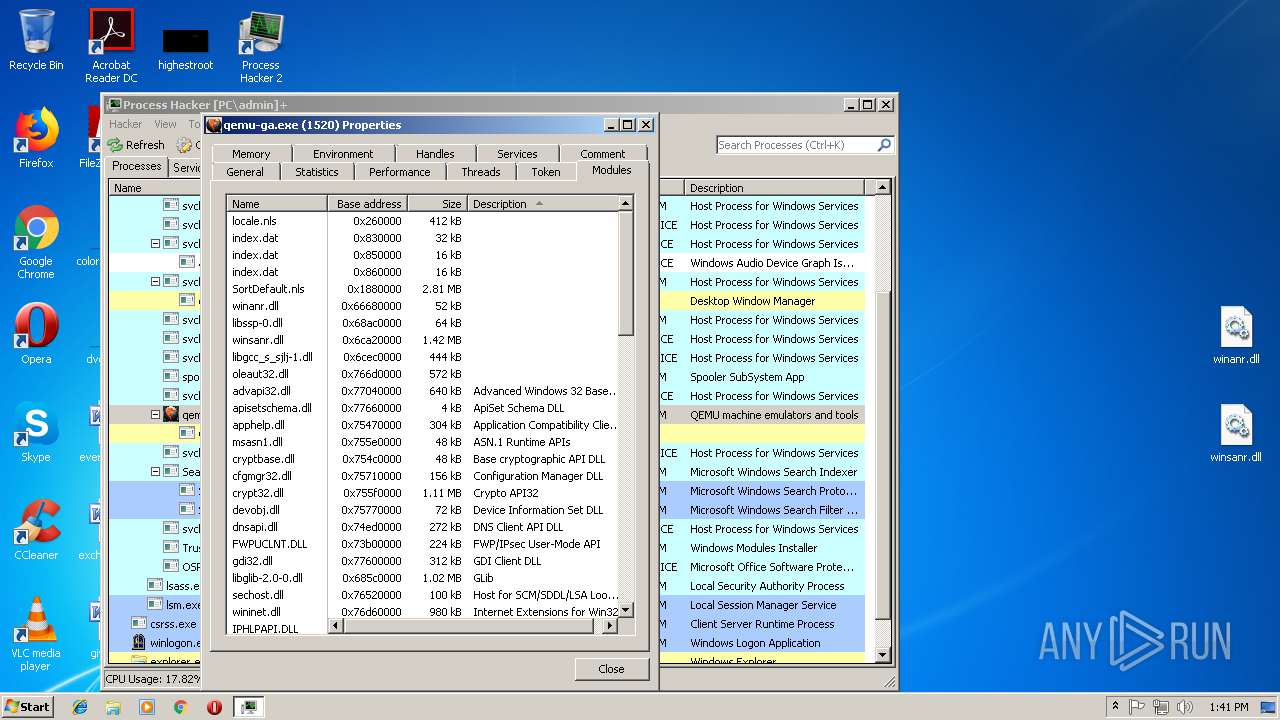
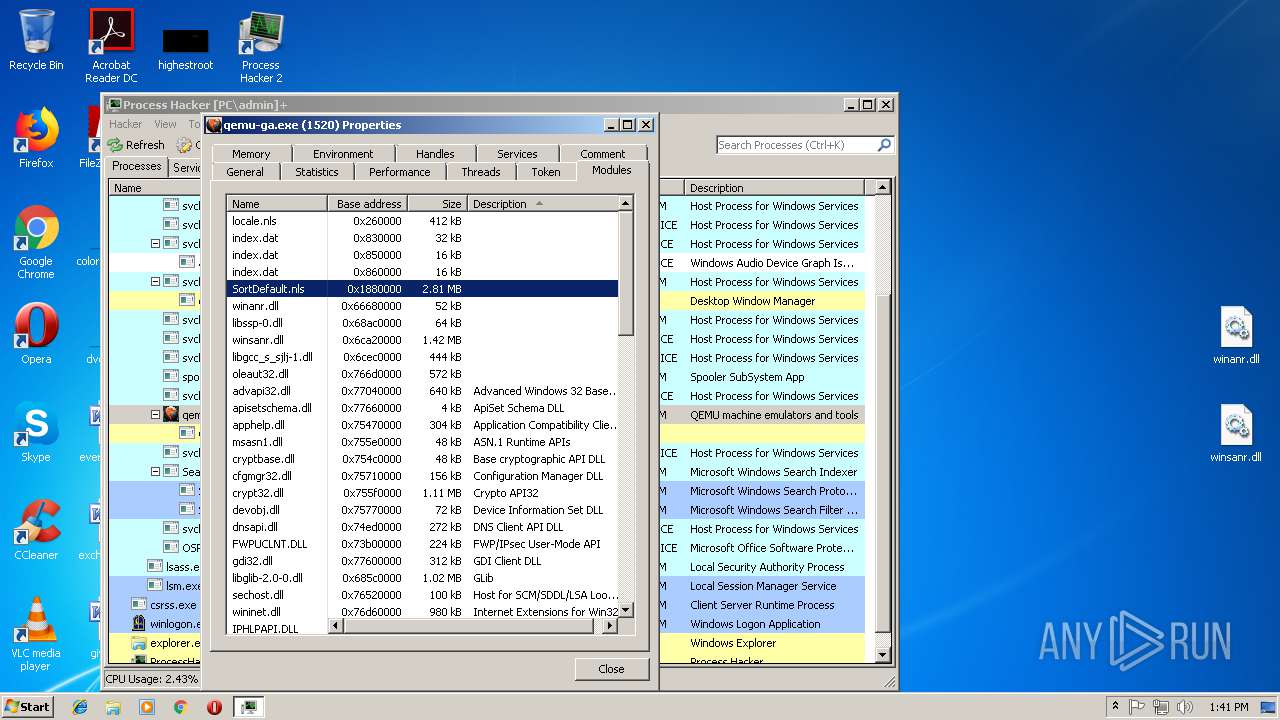
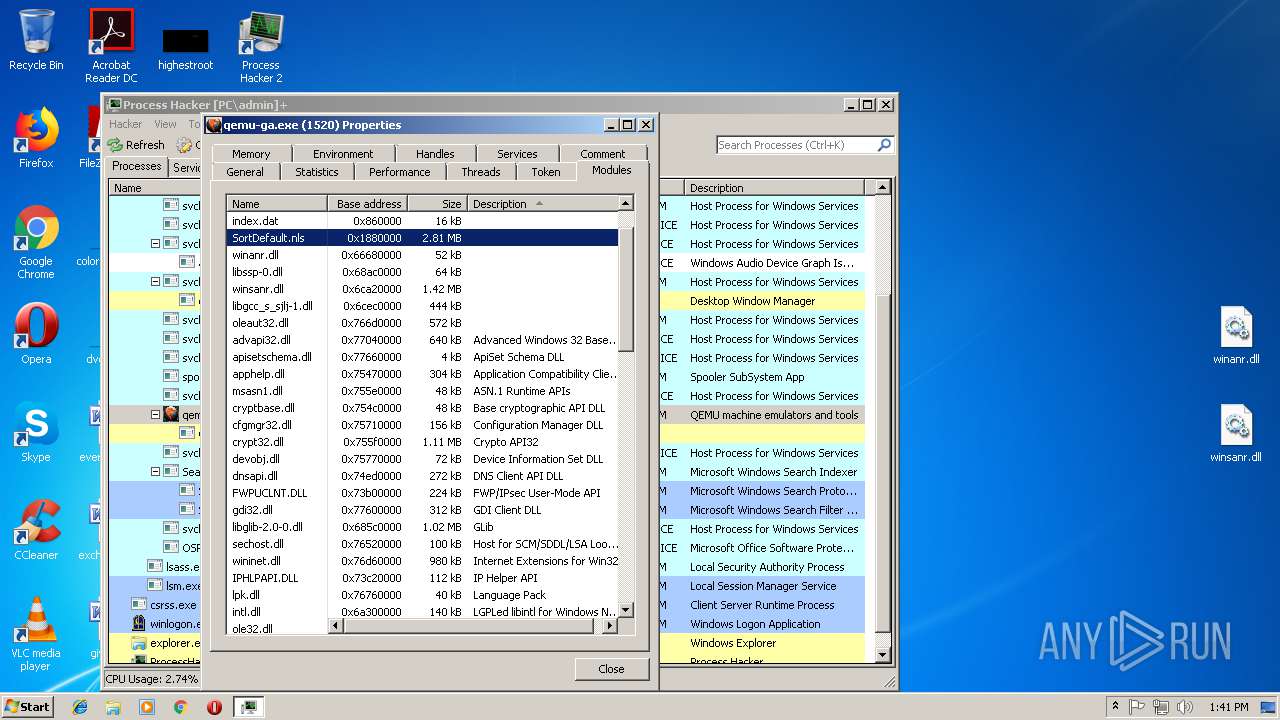
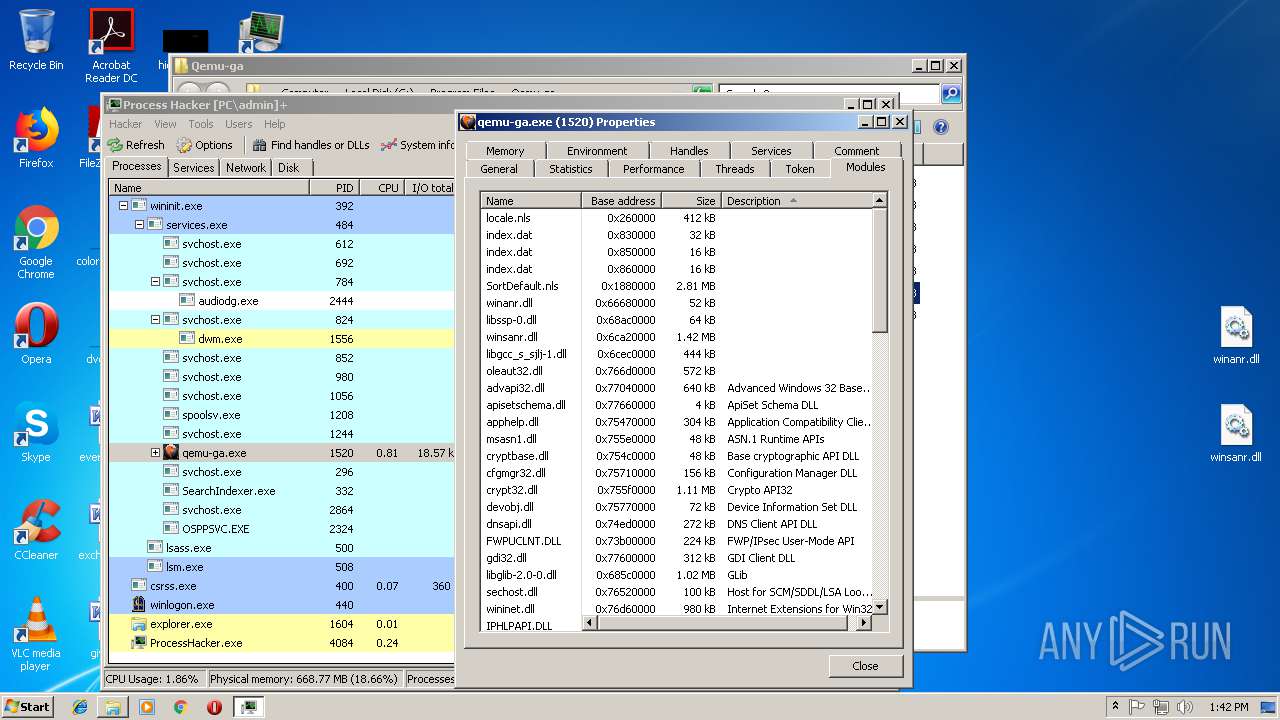
| 3588 | "C:\Program Files\Process Hacker 2\peview.exe" "C:\Windows\System32\winanr.dll" | C:\Program Files\Process Hacker 2\peview.exe | — | ProcessHacker.exe | |||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: PE Viewer Exit code: 0 Version: 2.39.0.123 Modules
| |||||||||||||||
| 3736 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
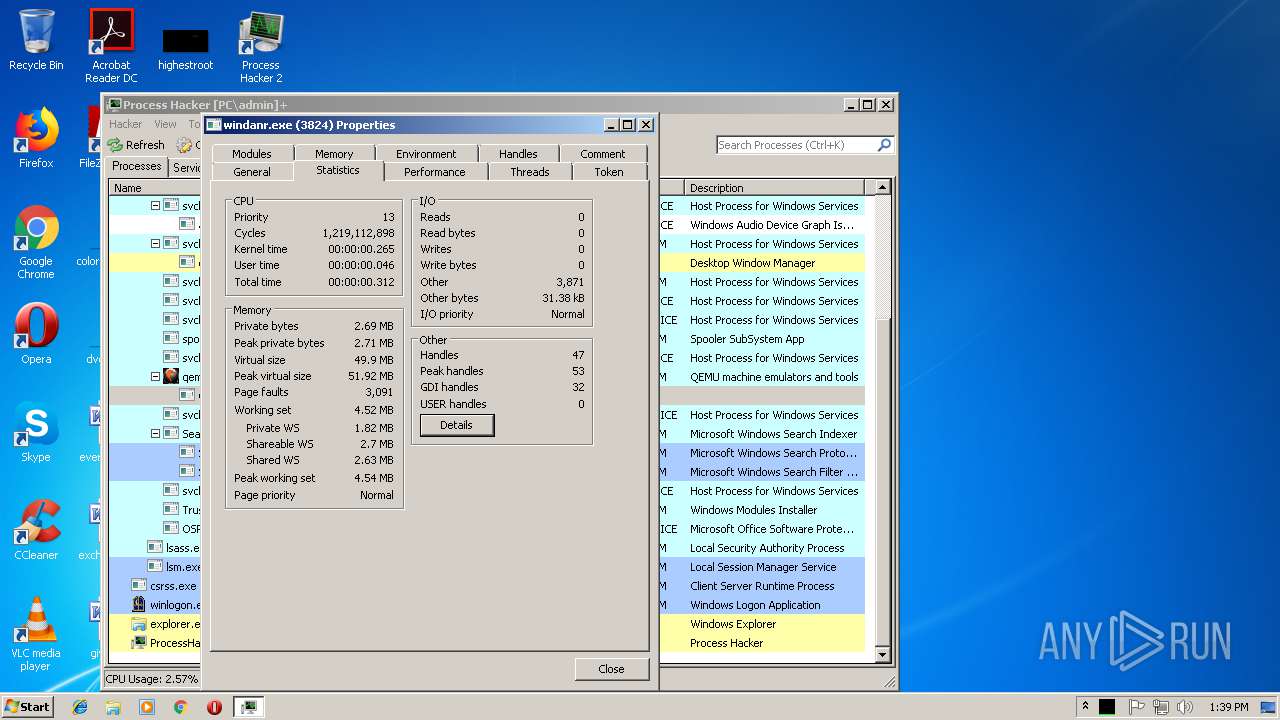
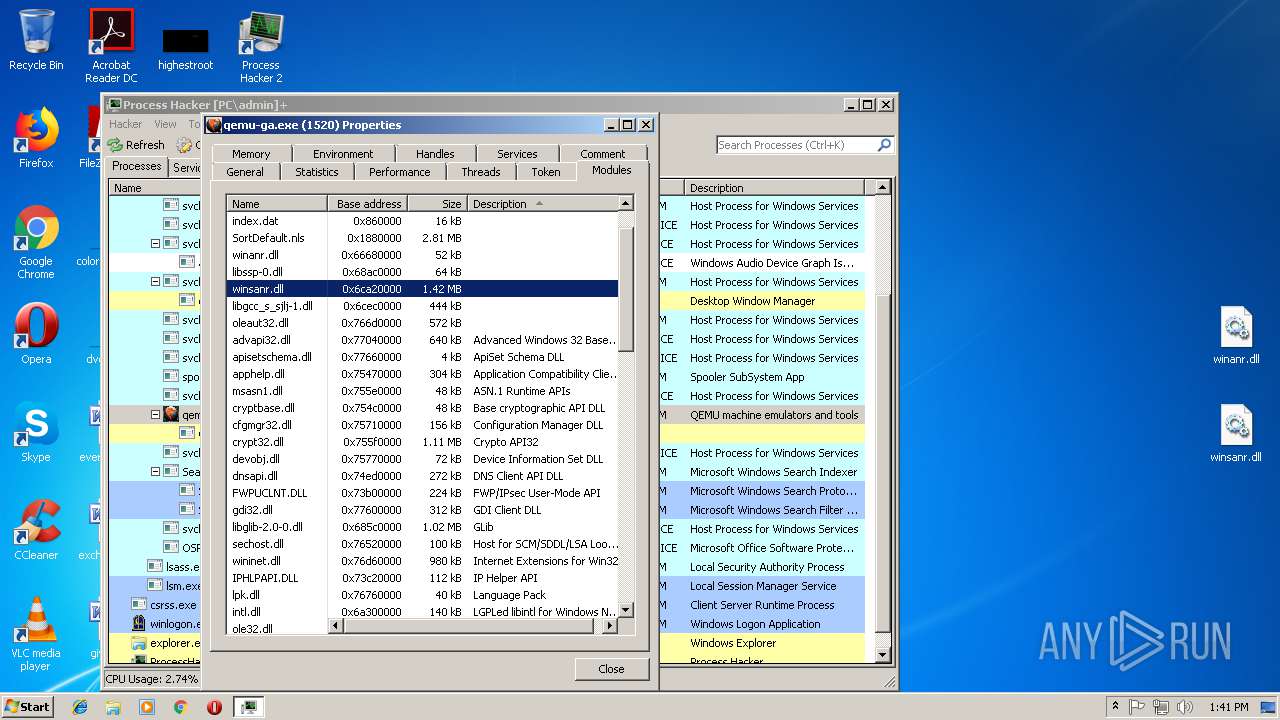
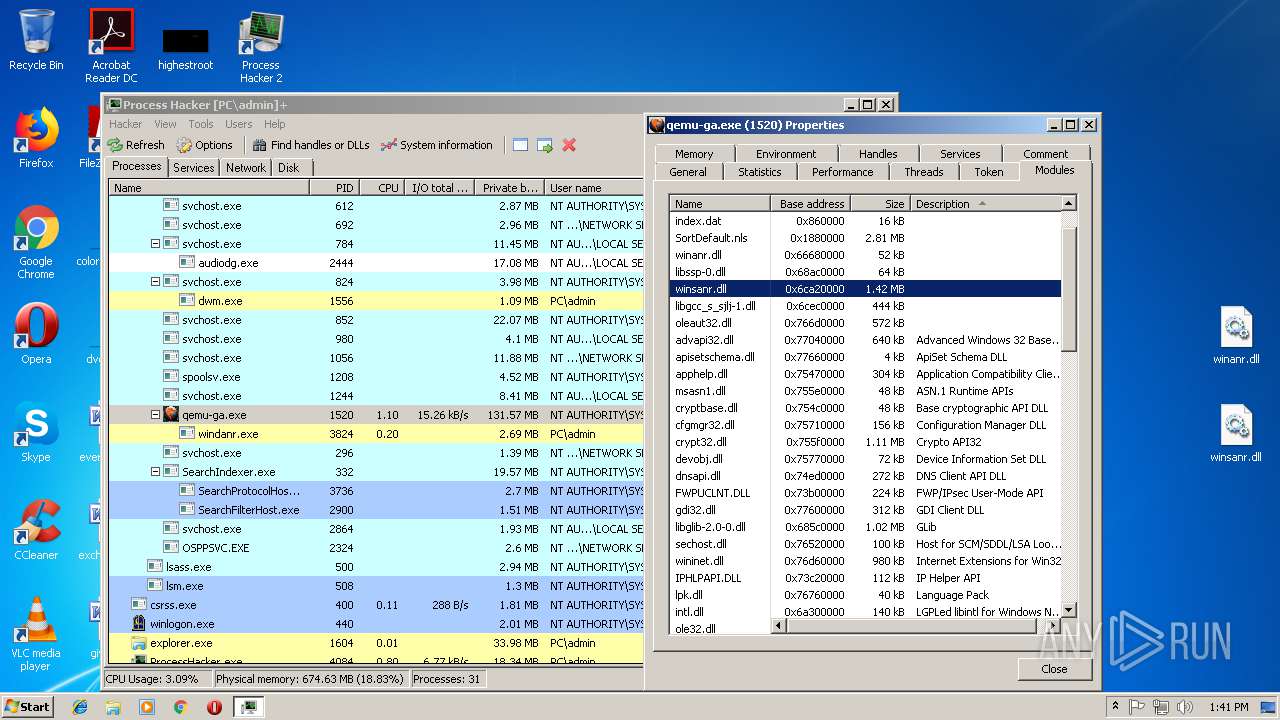
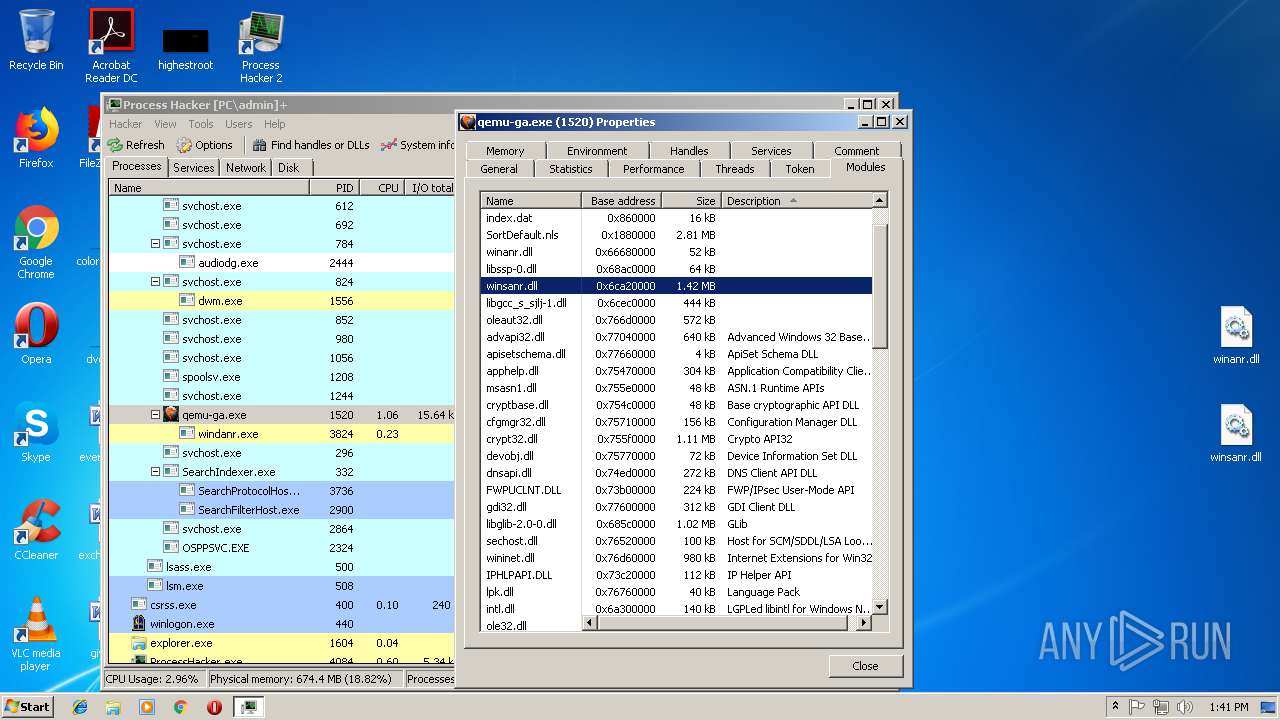
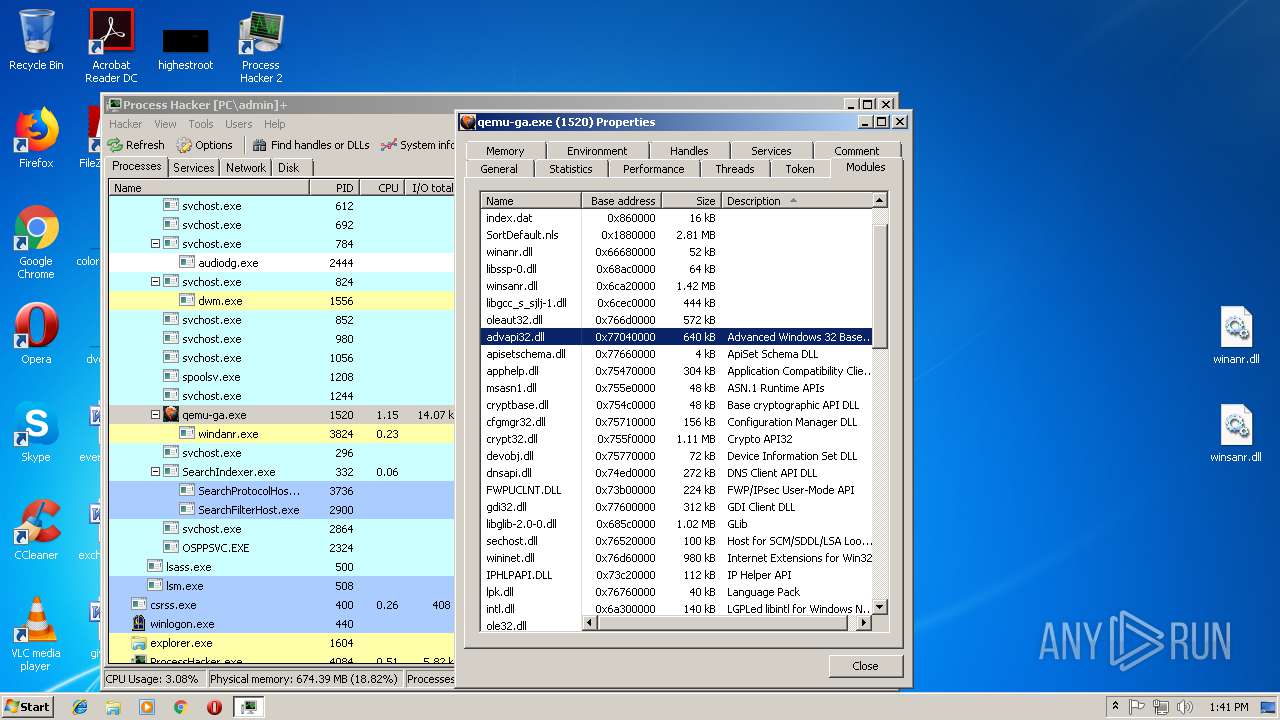
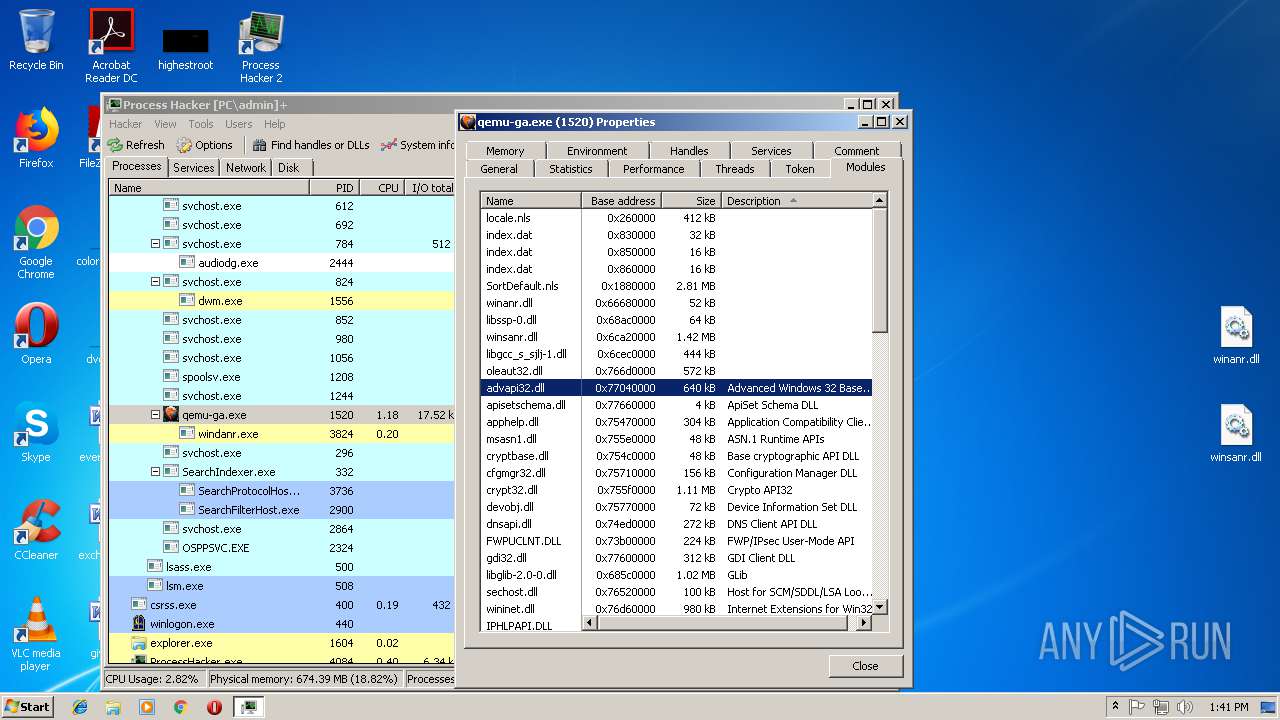
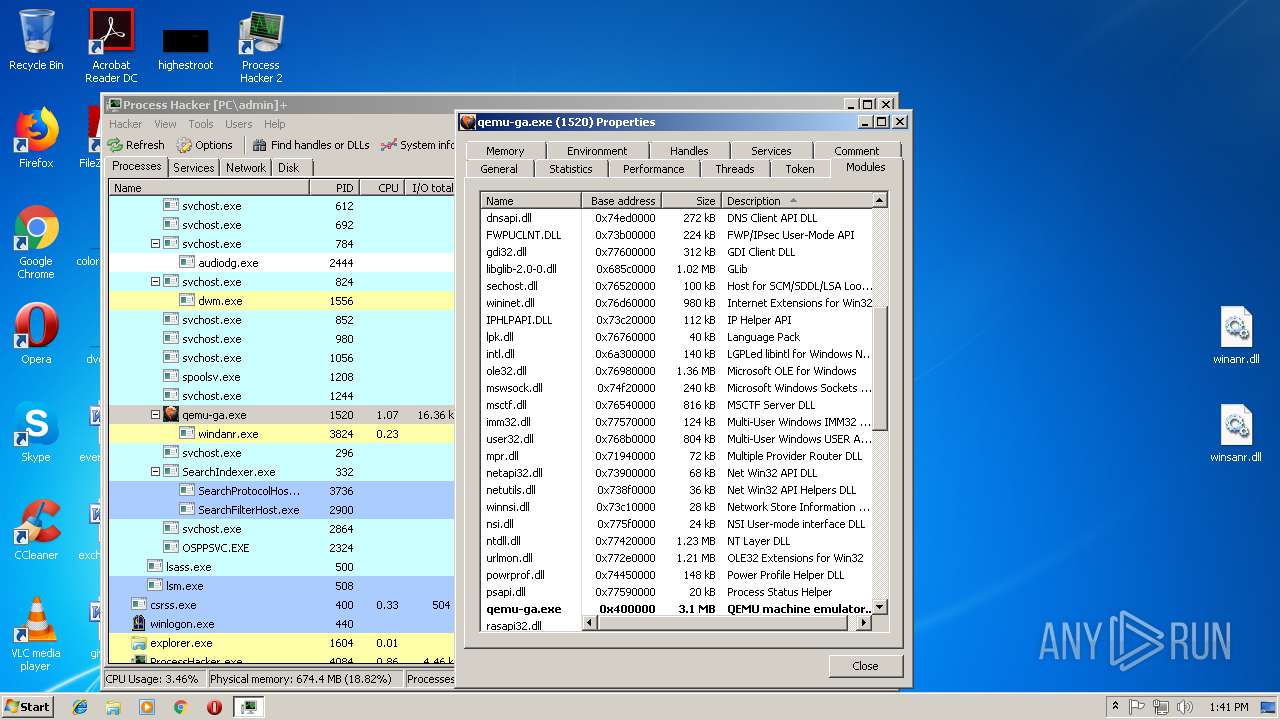
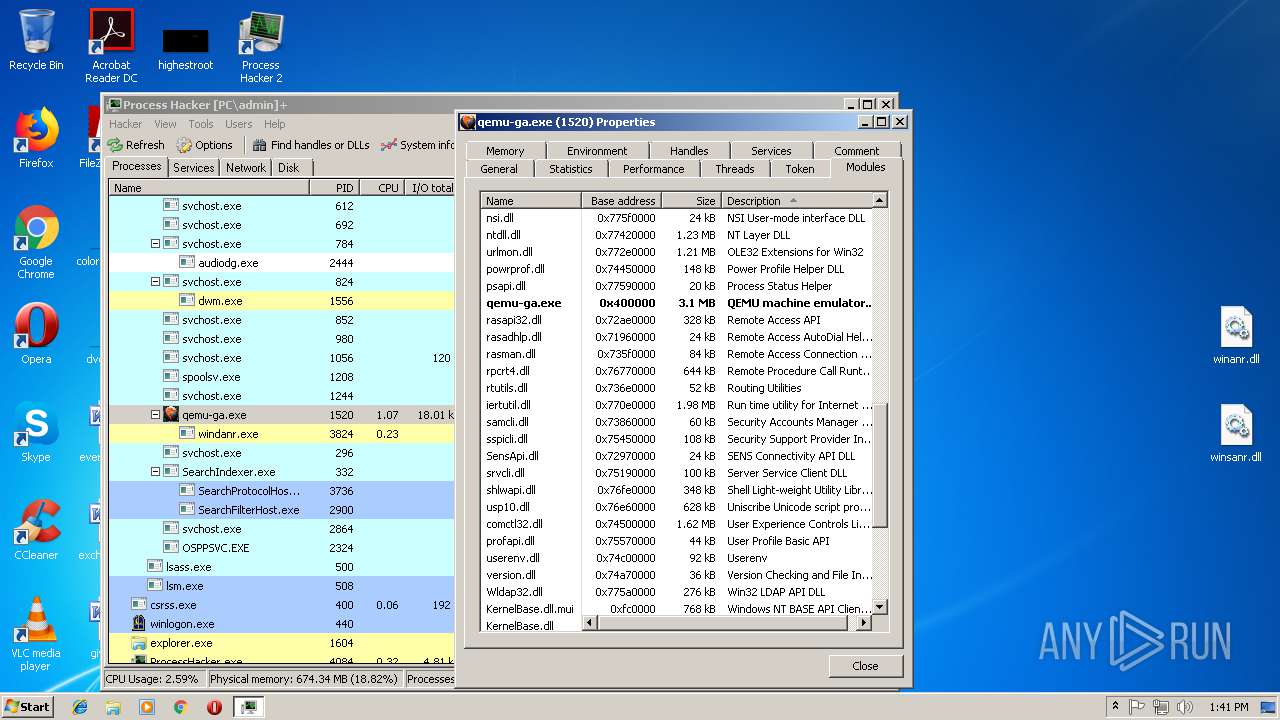
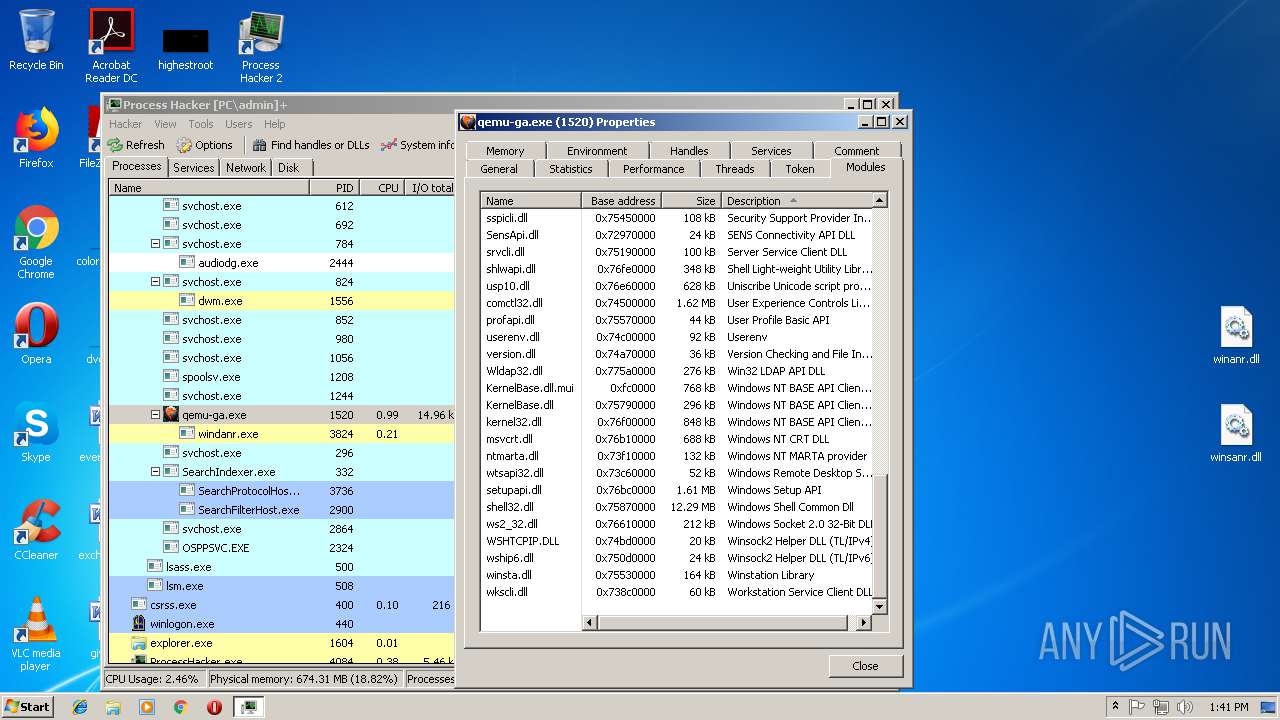
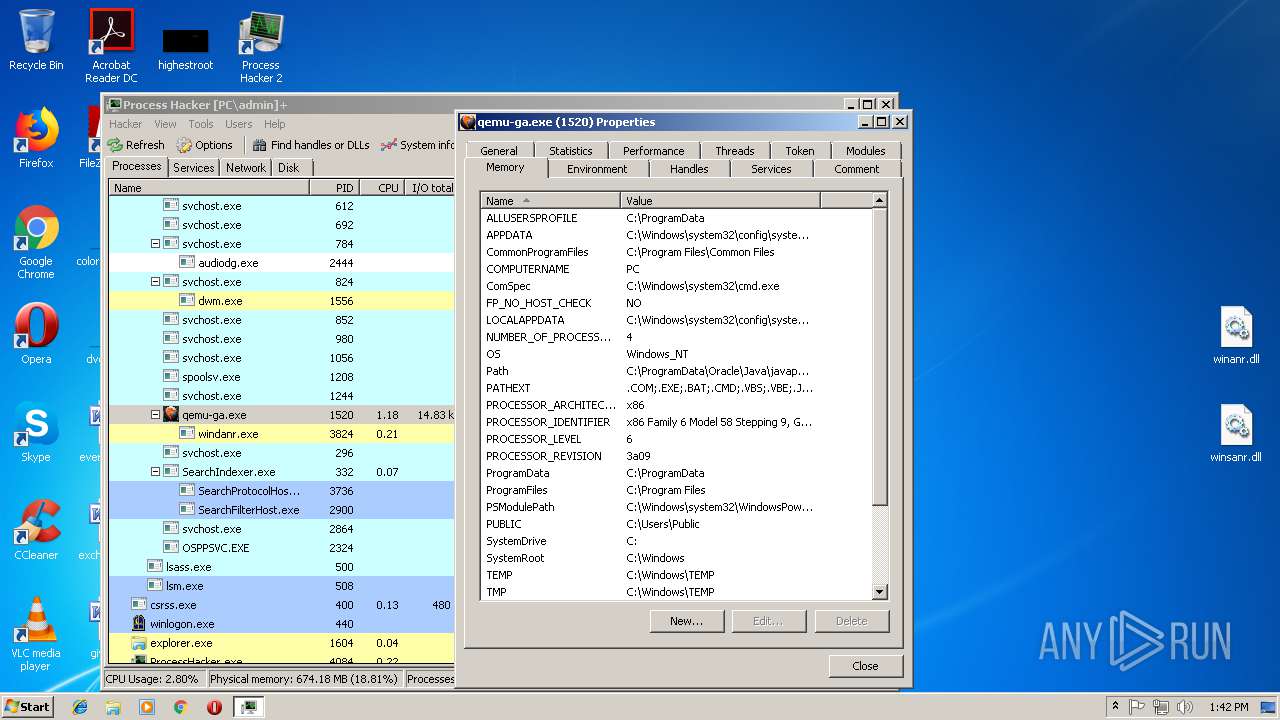
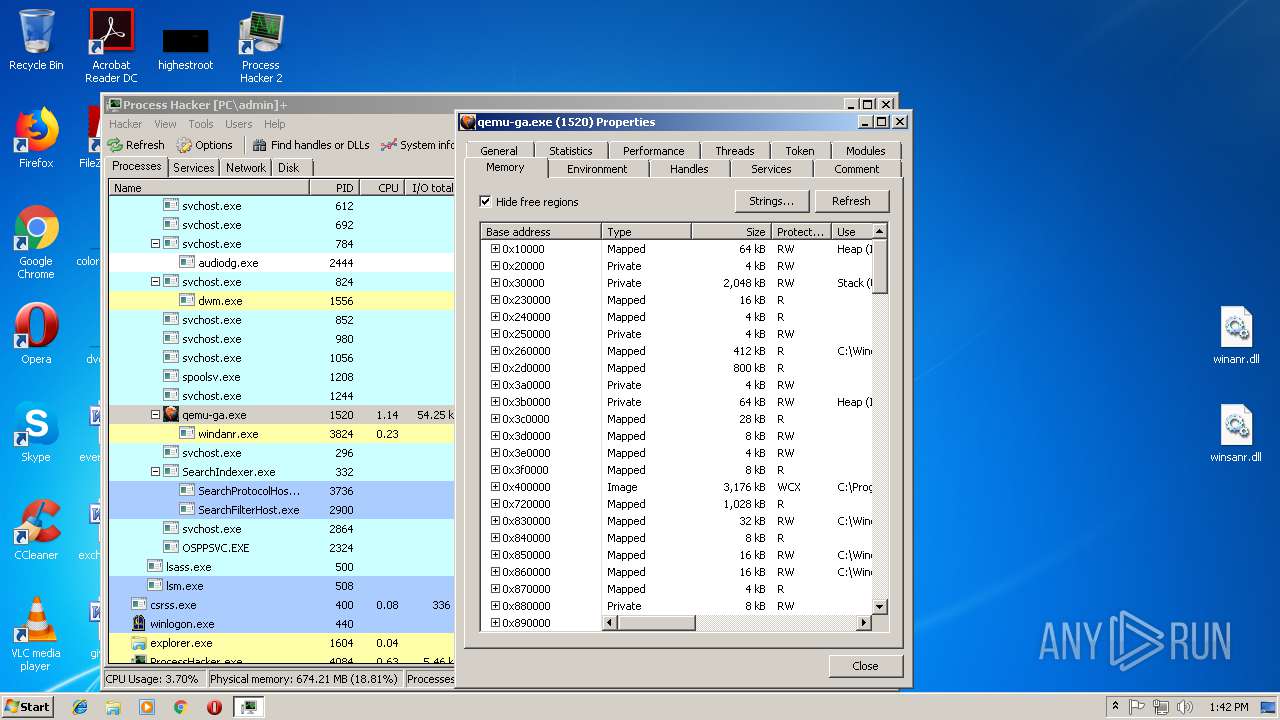
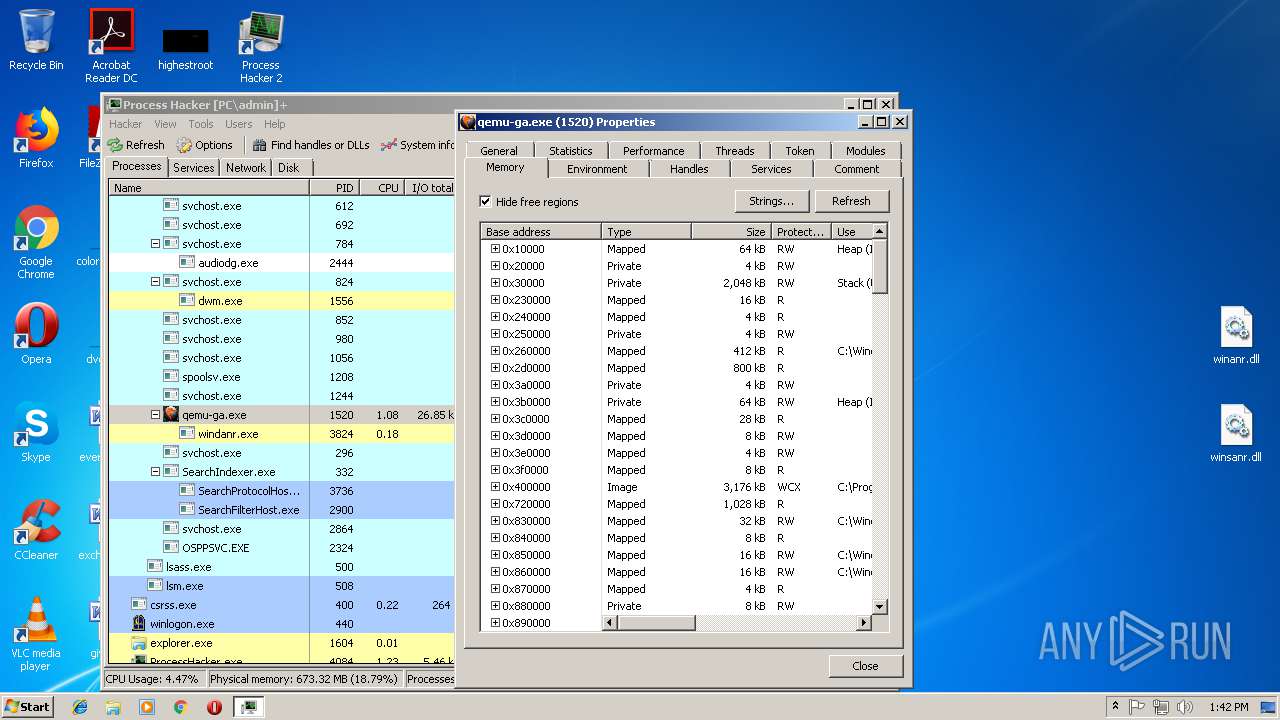
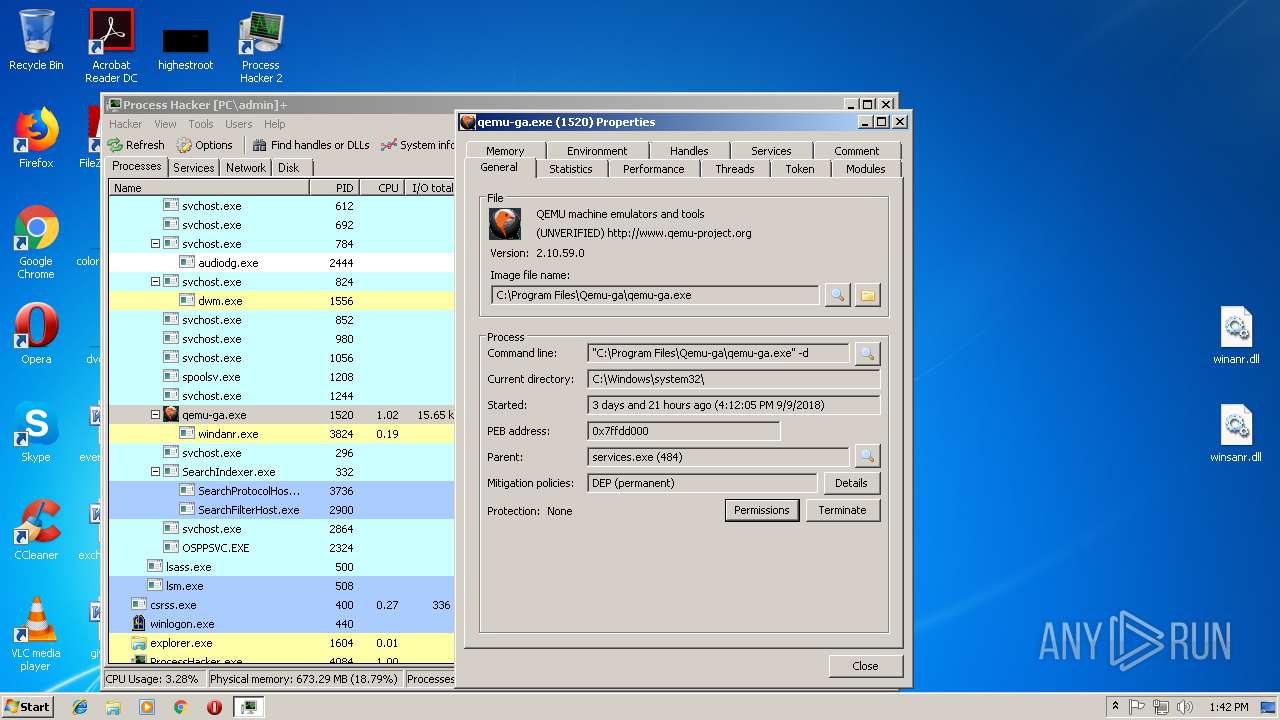
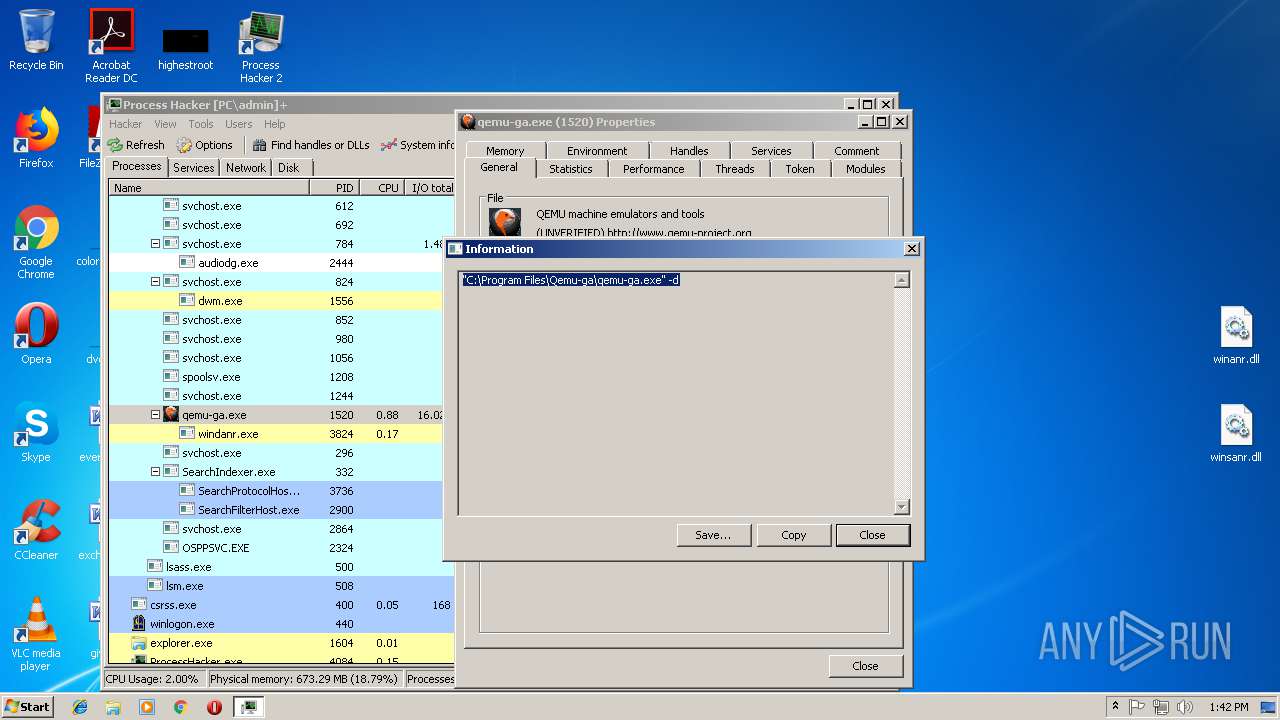
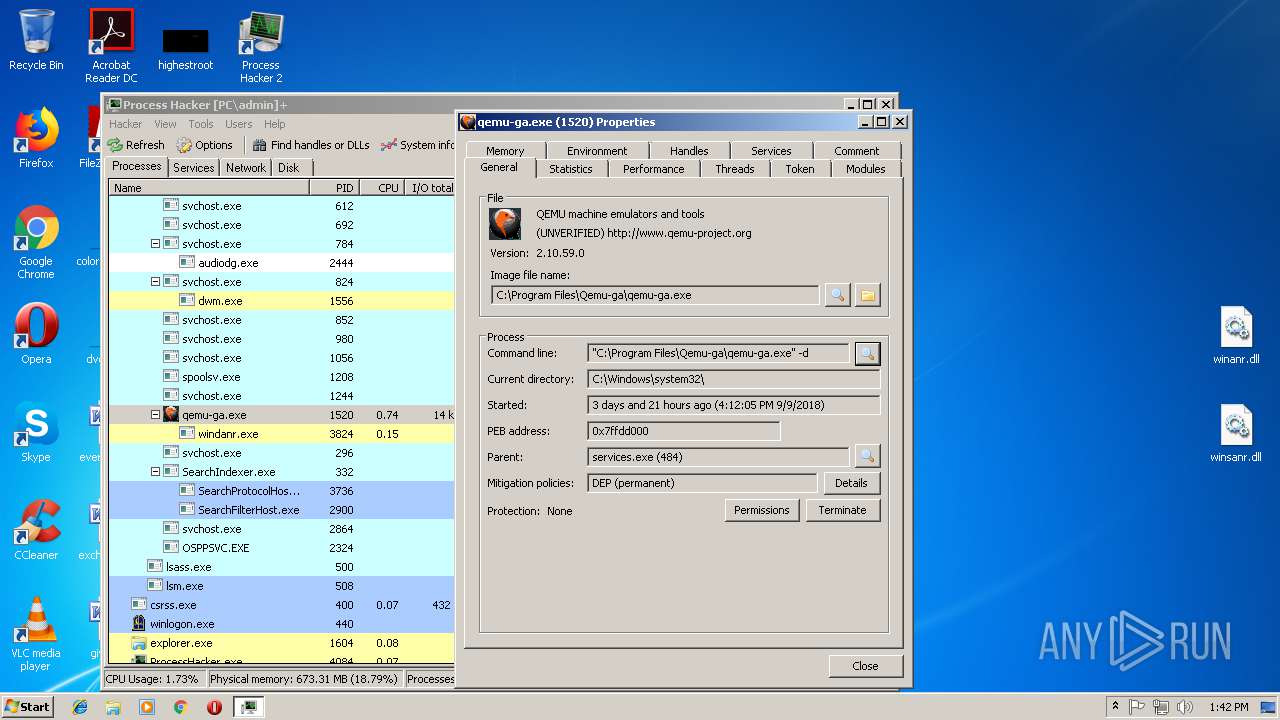
| 3824 | "windanr.exe" | C:\Windows\system32\windanr.exe | qemu-ga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Process Hacker 2\ProcessHacker.exe" -installkph -s | C:\Program Files\Process Hacker 2\ProcessHacker.exe | — | processhacker-2.39-setup.tmp | |||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Exit code: 0 Version: 2.39.0.124 Modules
| |||||||||||||||
Total events
9 683
Read events
8 733
Write events
930
Delete events
20
Modification events
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3824) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
22
Suspicious files
1
Text files
12
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-3LPFL.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-BNPBN.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-9QKM7.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-BBH21.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-9C9HD.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-IA13H.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-JDGOB.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-NB83K.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-38ICA.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\plugins\is-1UP92.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | ProcessHacker.exe | 162.243.25.33:443 | wj32.org | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wj32.org |
| whitelisted |