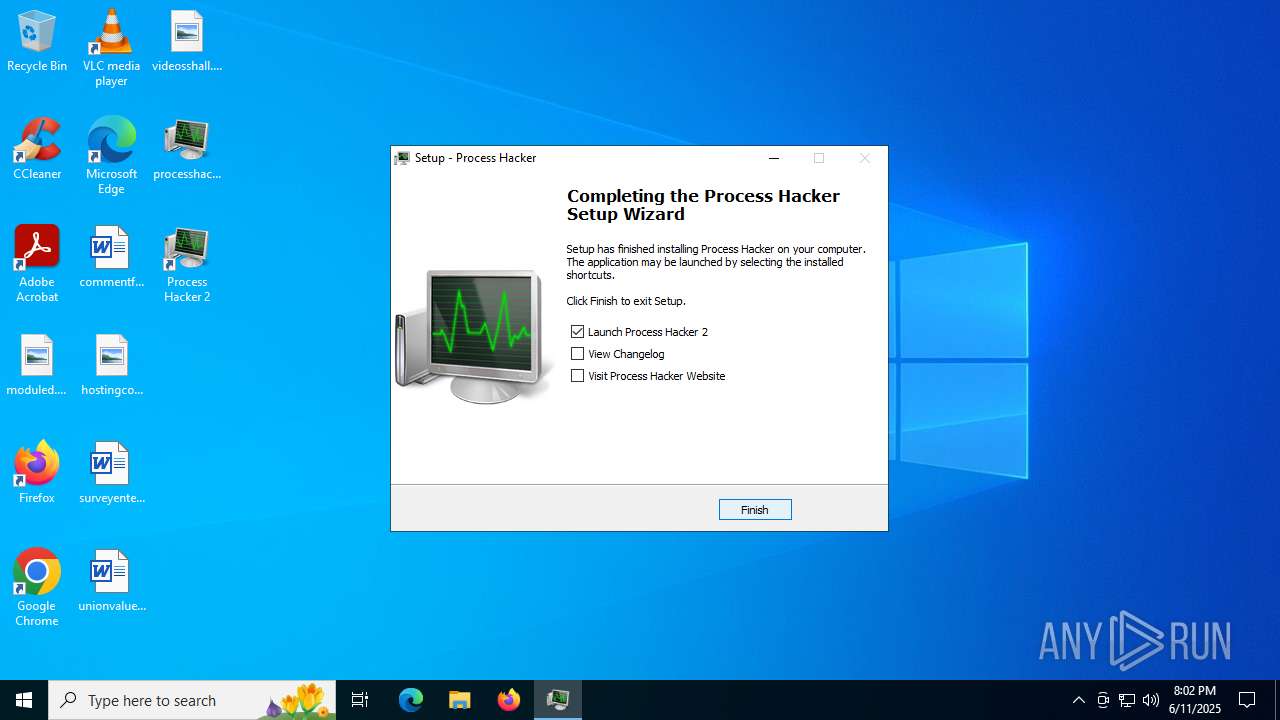
| File name: | processhacker-2.39-setup.exe |
| Full analysis: | https://app.any.run/tasks/2a2a01b3-6f5f-47c1-a1cb-6622f9a67364 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2025, 20:02:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 54DAAD58CCE5003BEE58B28A4F465F49 |
| SHA1: | 162B08B0B11827CC024E6B2EED5887EC86339BAA |
| SHA256: | 28042DD4A92A0033B8F1D419B9E989C5B8E32D1D2D881F5C8251D58CE35B9063 |
| SSDEEP: | 49152:l9hfV/U5NkLXXzGZjt6kFTCVP6hWE0wvmk/eE+FrAl+NGsOSE6IX8pqI:Dh9/ULkjKxtTGP6VZd2rAcvOSE6NqI |
MALICIOUS
Vulnerable driver has been detected
- processhacker-2.39-setup.tmp (PID: 1328)
SUSPICIOUS
Process drops legitimate windows executable
- processhacker-2.39-setup.tmp (PID: 1328)
Executable content was dropped or overwritten
- processhacker-2.39-setup.tmp (PID: 1328)
- processhacker-2.39-setup.exe (PID: 6620)
- processhacker-2.39-setup.exe (PID: 1496)
Reads the Windows owner or organization settings
- processhacker-2.39-setup.tmp (PID: 1328)
Drops a system driver (possible attempt to evade defenses)
- processhacker-2.39-setup.tmp (PID: 1328)
Reads security settings of Internet Explorer
- ProcessHacker.exe (PID: 4684)
- processhacker-2.39-setup.tmp (PID: 6208)
There is functionality for taking screenshot (YARA)
- ProcessHacker.exe (PID: 4684)
INFO
Checks supported languages
- processhacker-2.39-setup.exe (PID: 6620)
- processhacker-2.39-setup.tmp (PID: 1328)
- ProcessHacker.exe (PID: 4684)
- processhacker-2.39-setup.tmp (PID: 6208)
- processhacker-2.39-setup.exe (PID: 1496)
Create files in a temporary directory
- processhacker-2.39-setup.exe (PID: 6620)
- processhacker-2.39-setup.exe (PID: 1496)
- processhacker-2.39-setup.tmp (PID: 1328)
- ProcessHacker.exe (PID: 4684)
Reads the computer name
- processhacker-2.39-setup.tmp (PID: 1328)
- ProcessHacker.exe (PID: 4684)
- processhacker-2.39-setup.tmp (PID: 6208)
The sample compiled with english language support
- processhacker-2.39-setup.tmp (PID: 1328)
PROCESSHACKER mutex has been found
- processhacker-2.39-setup.tmp (PID: 1328)
Detects InnoSetup installer (YARA)
- processhacker-2.39-setup.tmp (PID: 6208)
- processhacker-2.39-setup.exe (PID: 6620)
- processhacker-2.39-setup.exe (PID: 1496)
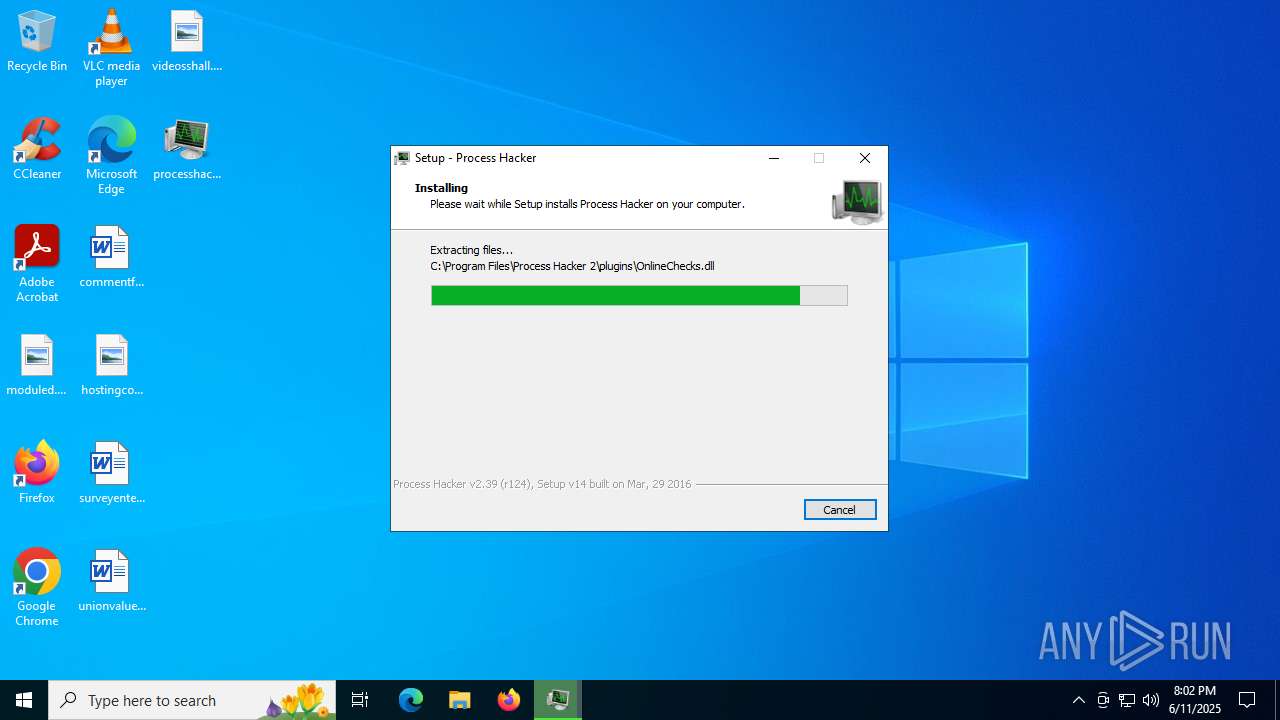
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 1328)
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 1328)
Compiled with Borland Delphi (YARA)
- processhacker-2.39-setup.tmp (PID: 6208)
Checks proxy server information
- ProcessHacker.exe (PID: 4684)
- slui.exe (PID: 1520)
Reads the machine GUID from the registry
- ProcessHacker.exe (PID: 4684)
Reads Environment values
- ProcessHacker.exe (PID: 4684)
Reads the software policy settings
- ProcessHacker.exe (PID: 4684)
- slui.exe (PID: 1520)
Process checks computer location settings
- processhacker-2.39-setup.tmp (PID: 6208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 108544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.39.0.124 |
| ProductVersionNumber: | 2.39.0.124 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | wj32 |
| FileDescription: | Process Hacker Setup |
| FileVersion: | 2.39 (r124) |
| LegalCopyright: | Copyright © 2010-2016, Process Hacker Team. Licensed under the GNU GPL, v3. |
| ProductName: | Process Hacker |
| ProductVersion: | 2.39 (r124) |
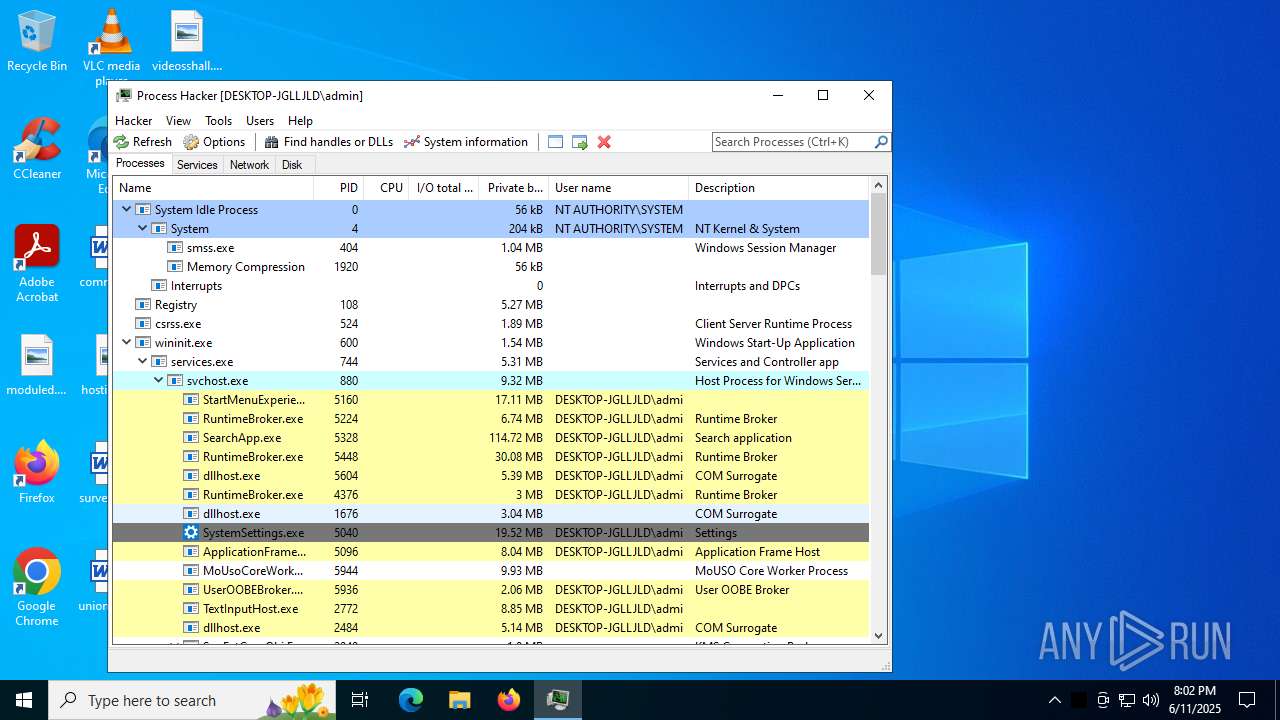
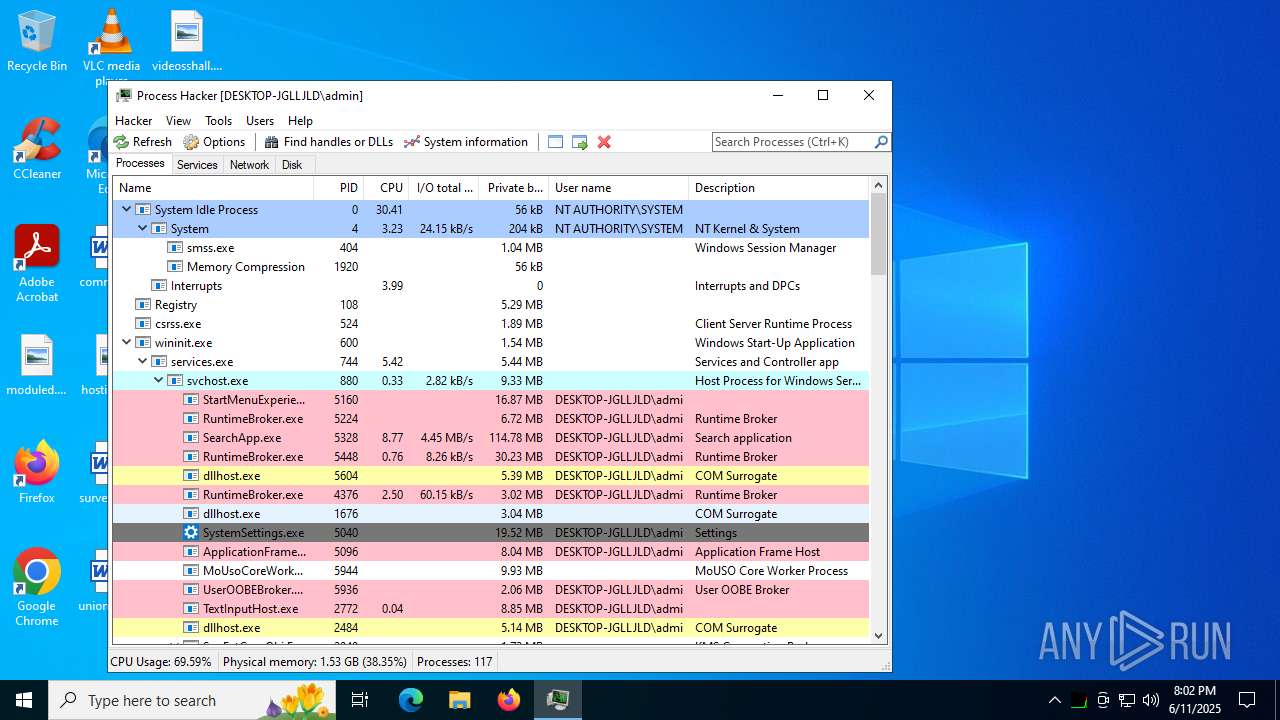
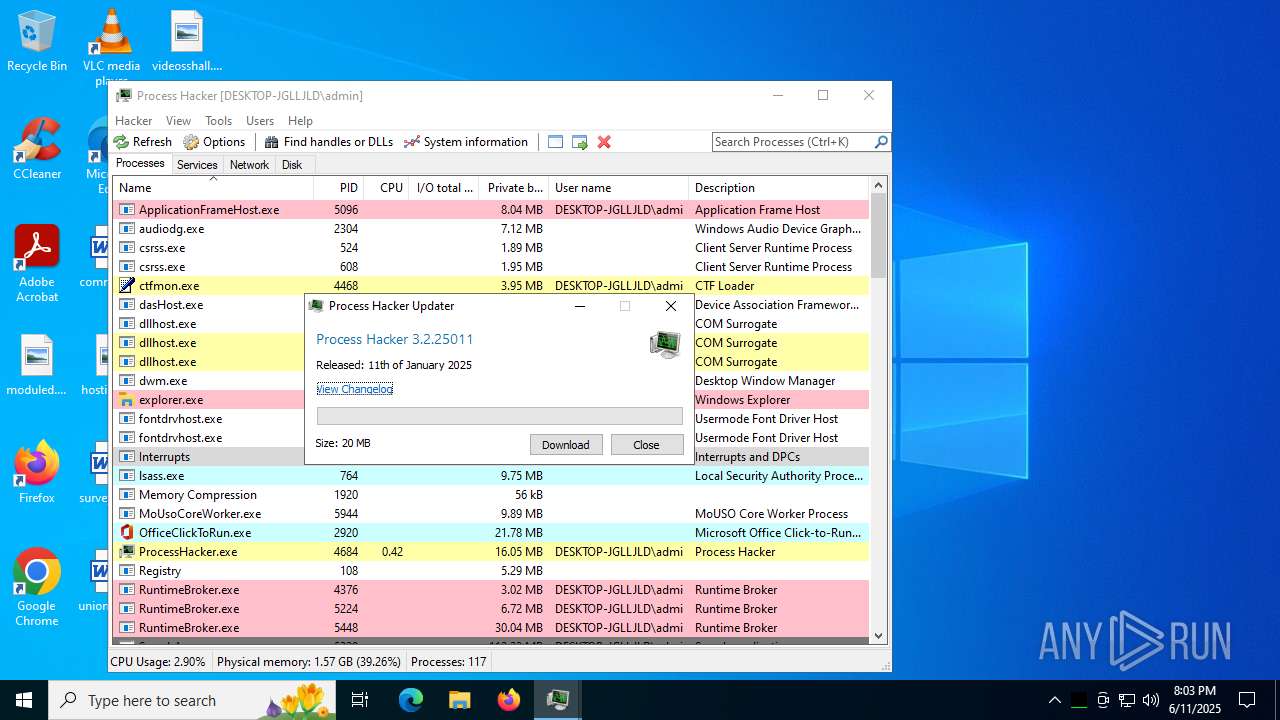
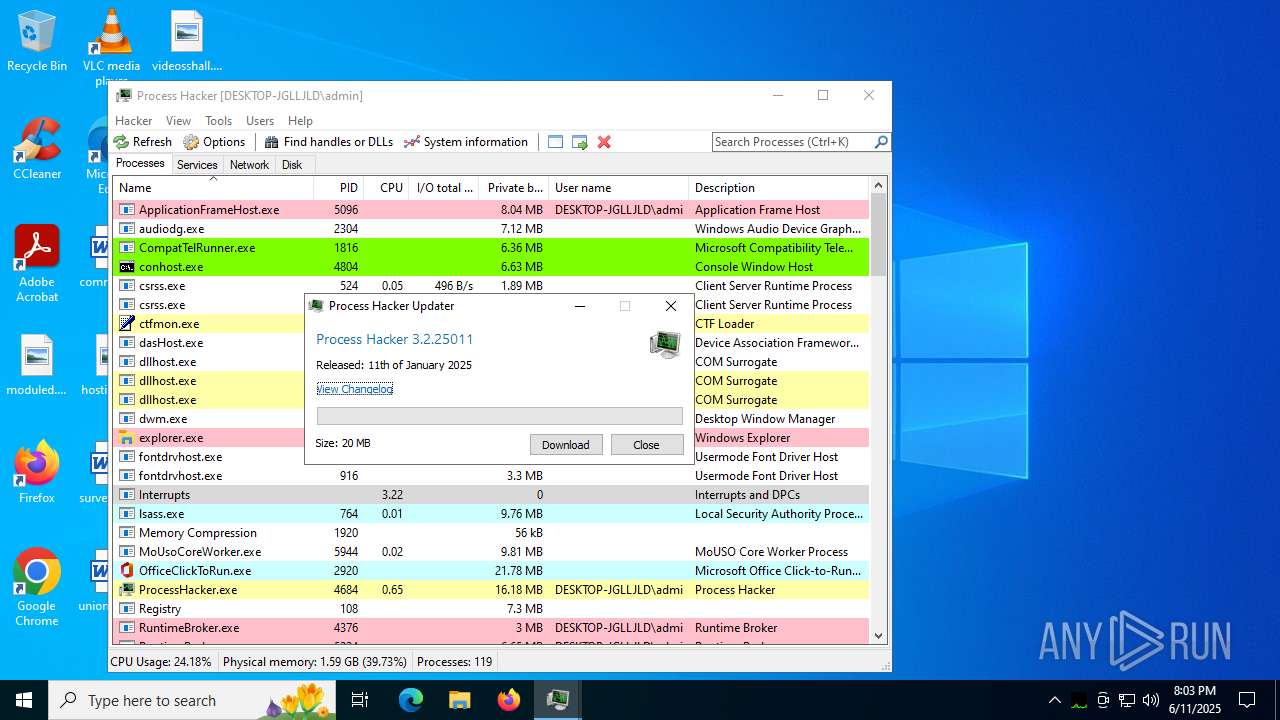
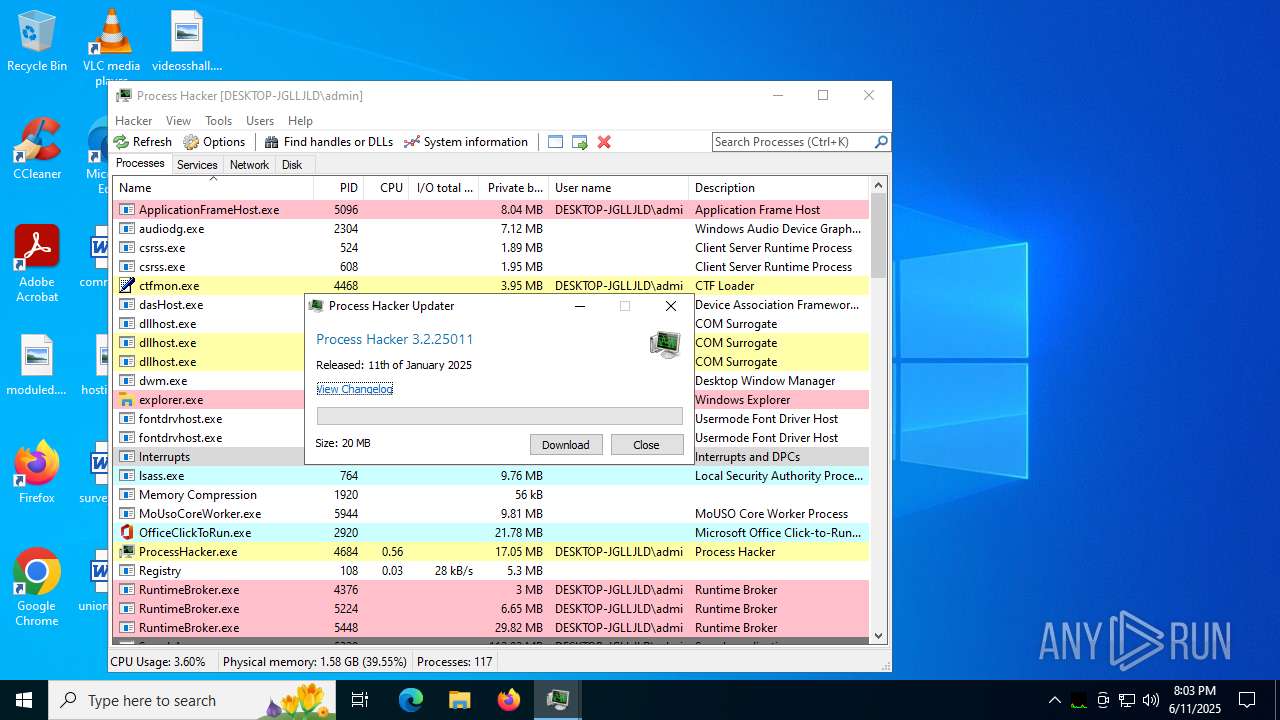
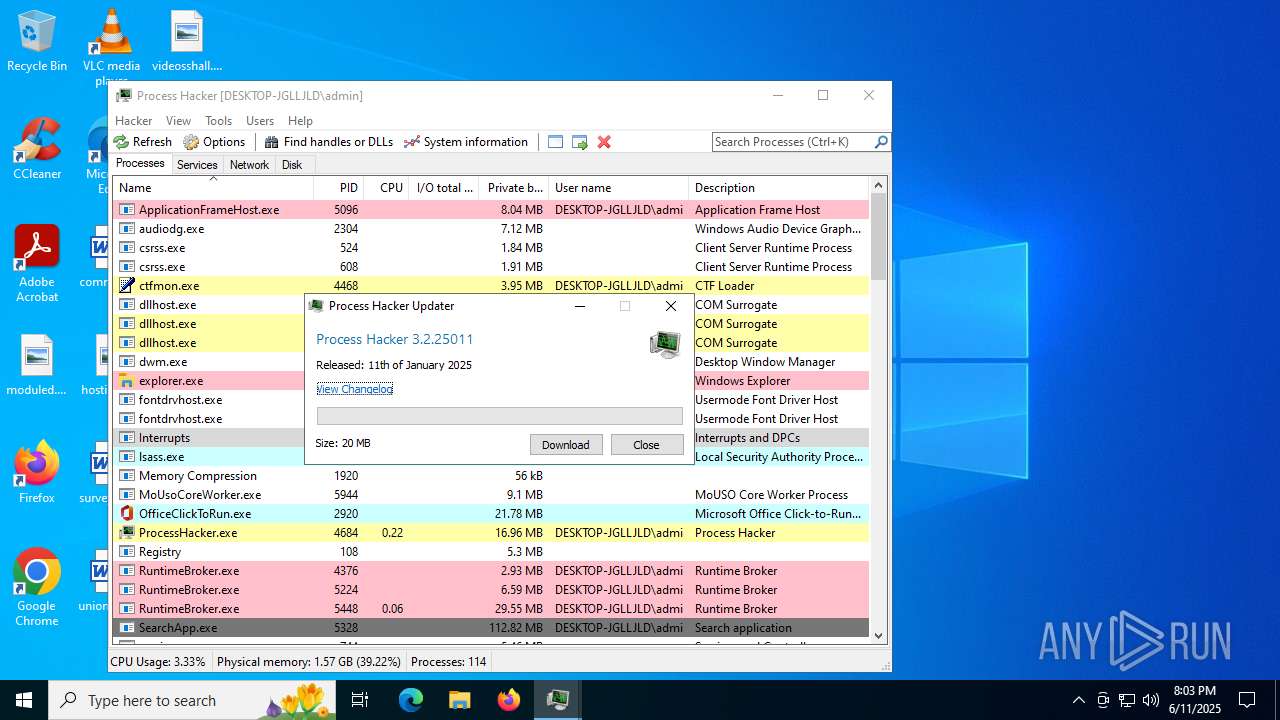
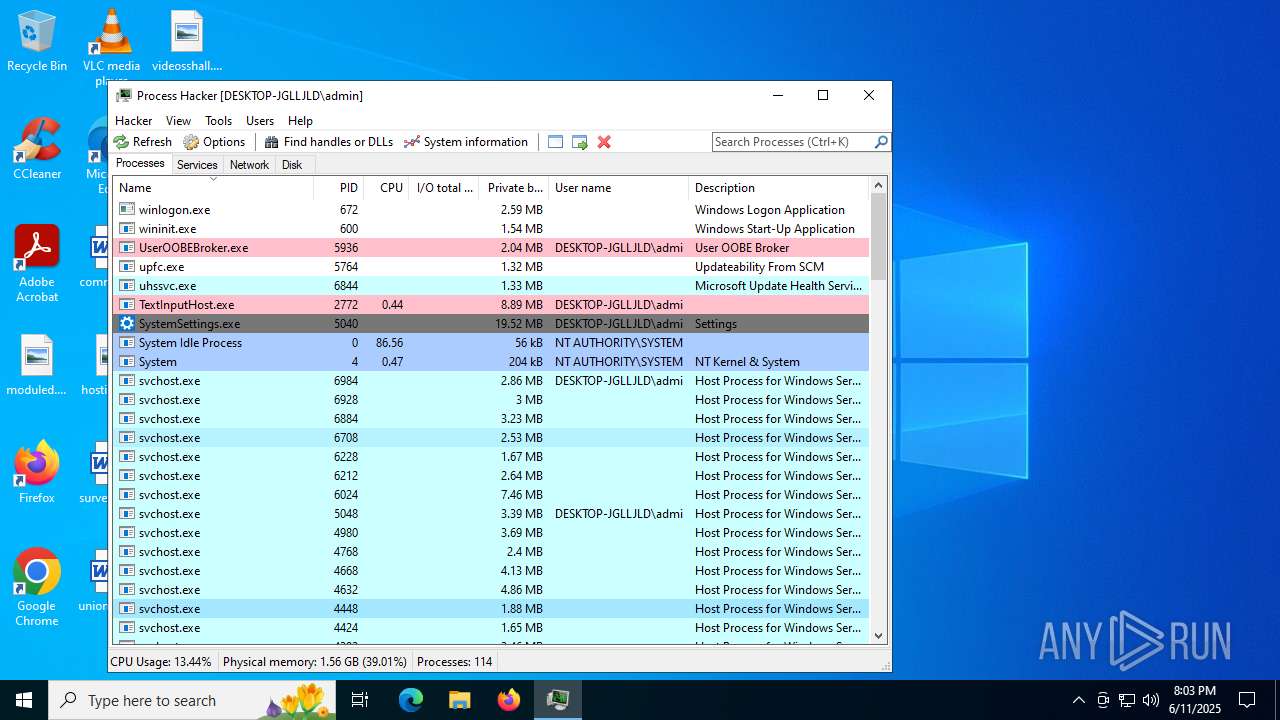
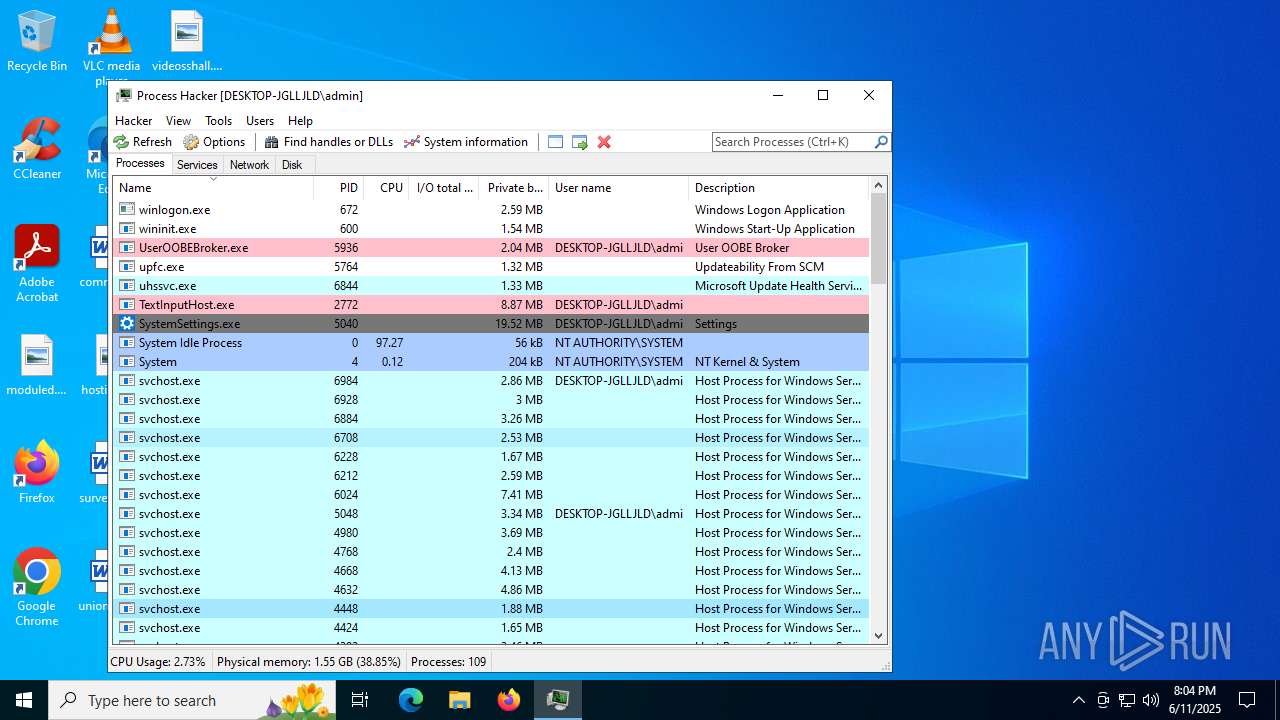
Total processes
140
Monitored processes
6
Malicious processes
3
Suspicious processes
1
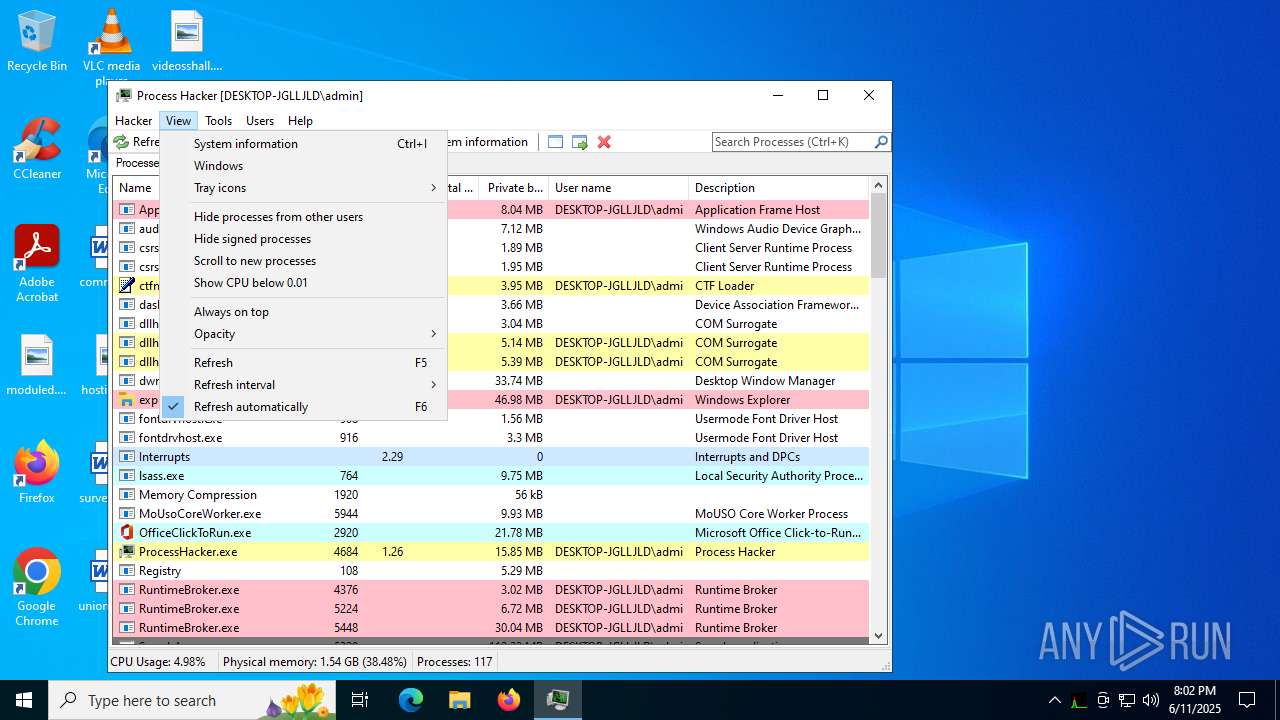
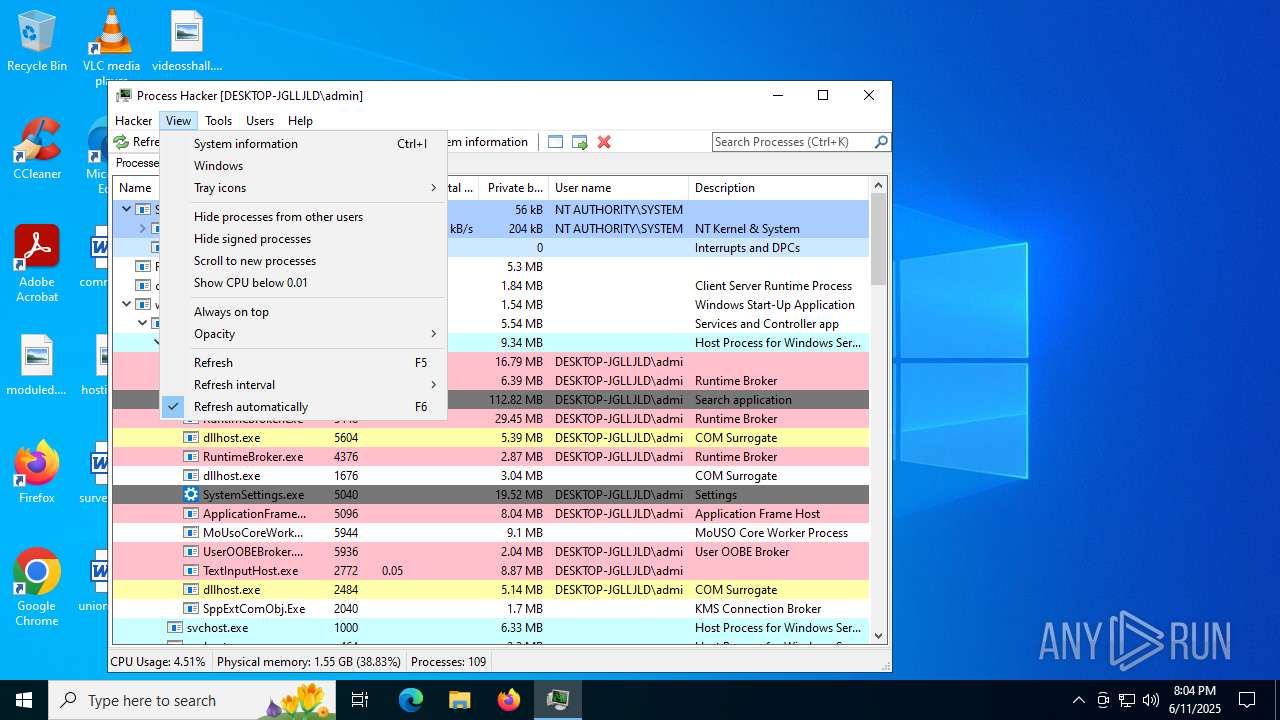
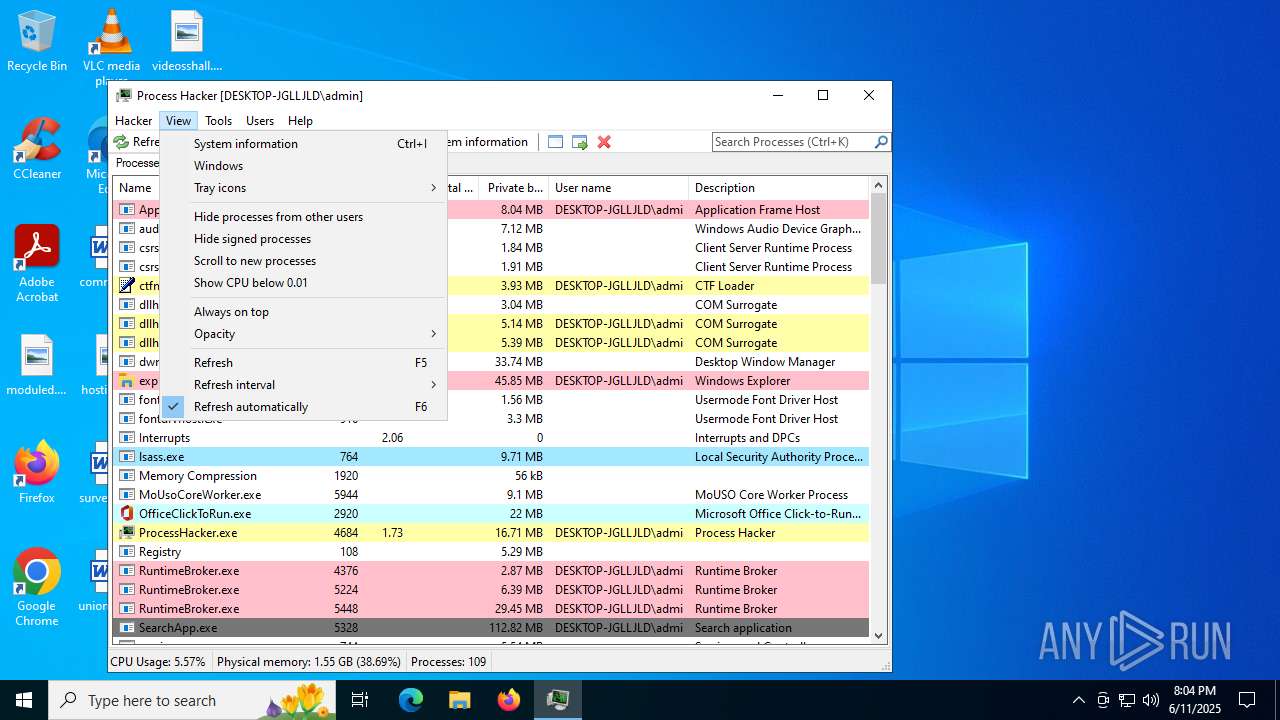
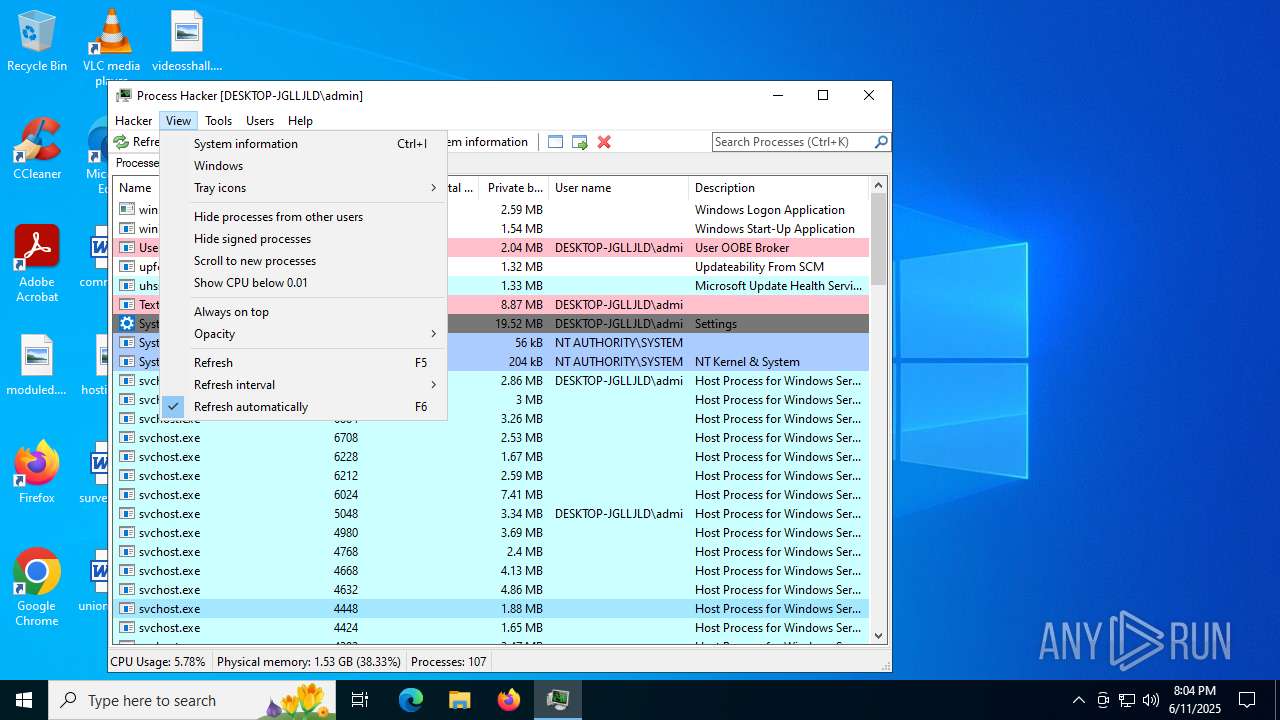
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Users\admin\AppData\Local\Temp\is-S546N.tmp\processhacker-2.39-setup.tmp" /SL5="$70374,1874675,150016,C:\Users\admin\Desktop\processhacker-2.39-setup.exe" /SPAWNWND=$1102BA /NOTIFYWND=$90230 | C:\Users\admin\AppData\Local\Temp\is-S546N.tmp\processhacker-2.39-setup.tmp | processhacker-2.39-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\Desktop\processhacker-2.39-setup.exe" /SPAWNWND=$1102BA /NOTIFYWND=$90230 | C:\Users\admin\Desktop\processhacker-2.39-setup.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | "C:\Program Files\Process Hacker 2\ProcessHacker.exe" | C:\Program Files\Process Hacker 2\ProcessHacker.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Version: 2.39.0.124 Modules
| |||||||||||||||
| 6208 | "C:\Users\admin\AppData\Local\Temp\is-NSFDH.tmp\processhacker-2.39-setup.tmp" /SL5="$90230,1874675,150016,C:\Users\admin\Desktop\processhacker-2.39-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-NSFDH.tmp\processhacker-2.39-setup.tmp | — | processhacker-2.39-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 6620 | "C:\Users\admin\Desktop\processhacker-2.39-setup.exe" | C:\Users\admin\Desktop\processhacker-2.39-setup.exe | explorer.exe | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
Total events
9 671
Read events
9 644
Write events
27
Delete events
0
Modification events
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.8 (a) | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Process Hacker 2 | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Process Hacker 2\ | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Process Hacker 2 | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: main,peview,plugins,plugins\dotnettools,plugins\extendednotifications,plugins\extendedservices,plugins\extendedtools,plugins\hardwaredevices,plugins\networktools,plugins\onlinechecks,plugins\sbiesupport,plugins\toolstatus,plugins\updater,plugins\usernotes,plugins\windowexplorer | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon,desktopicon\user | |||
| (PID) Process: | (1328) processhacker-2.39-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Process_Hacker2_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: desktopicon\common,startup,startup\minimized,set_default_taskmgr,create_kph_service | |||
Executable files
40
Suspicious files
2
Text files
10
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | processhacker-2.39-setup.exe | C:\Users\admin\AppData\Local\Temp\is-NSFDH.tmp\processhacker-2.39-setup.tmp | executable | |
MD5:1C96ED29E0136825E06F037BF10B2419 | SHA256:B10CF8CDF541CA0DD6DF79E66FB4B0854DCAC717ABA034BA0C4961BFF92FD021 | |||
| 1496 | processhacker-2.39-setup.exe | C:\Users\admin\AppData\Local\Temp\is-S546N.tmp\processhacker-2.39-setup.tmp | executable | |
MD5:1C96ED29E0136825E06F037BF10B2419 | SHA256:B10CF8CDF541CA0DD6DF79E66FB4B0854DCAC717ABA034BA0C4961BFF92FD021 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\unins000.exe | executable | |
MD5:43EA49877A2A1508BA733E41C874E16E | SHA256:E7C1D4C07728671C3B28295C863BBE681F962196C8A974EB4B3003540338AA04 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-F12S0.tmp | executable | |
MD5:43EA49877A2A1508BA733E41C874E16E | SHA256:E7C1D4C07728671C3B28295C863BBE681F962196C8A974EB4B3003540338AA04 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-QLSMC.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-QLSMC.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\ProcessHacker.exe | executable | |
MD5:B365AF317AE730A67C936F21432B9C71 | SHA256:BD2C2CF0631D881ED382817AFCCE2B093F4E412FFB170A719E2762F250ABFEA4 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\ProcessHacker.sig | binary | |
MD5:2CCB4420D40893846E1F88A2E82834DA | SHA256:519C2C2CA0CAF00DB5B3EB2B79DFE42E6128161C13AEB4B4D8B86FBFFC67E3D4 | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\x86\ProcessHacker.exe | executable | |
MD5:68F9B52895F4D34E74112F3129B3B00D | SHA256:D4A0FE56316A2C45B9BA9AC1005363309A3EDC7ACF9E4DF64D326A0FF273E80F | |||
| 1328 | processhacker-2.39-setup.tmp | C:\Program Files\Process Hacker 2\is-QKGI5.tmp | executable | |
MD5:B365AF317AE730A67C936F21432B9C71 | SHA256:BD2C2CF0631D881ED382817AFCCE2B093F4E412FFB170A719E2762F250ABFEA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6936 | RUXIMICS.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4684 | ProcessHacker.exe | GET | 301 | 104.18.13.149:80 | http://processhacker.sourceforge.net/update.php | unknown | — | — | whitelisted |
6936 | RUXIMICS.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 301 | 104.18.11.31:443 | https://processhacker.sourceforge.net/update.php | unknown | html | 255 b | whitelisted |
— | — | GET | 200 | 104.18.10.31:443 | https://processhacker.sourceforge.io/update.php | unknown | text | 450 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6936 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
6936 | RUXIMICS.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
1268 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
wj32.org |
| whitelisted |
processhacker.sourceforge.net |
| whitelisted |
processhacker.sourceforge.io |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
sourceforge.net |
| whitelisted |
downloads.sourceforge.net |
| whitelisted |