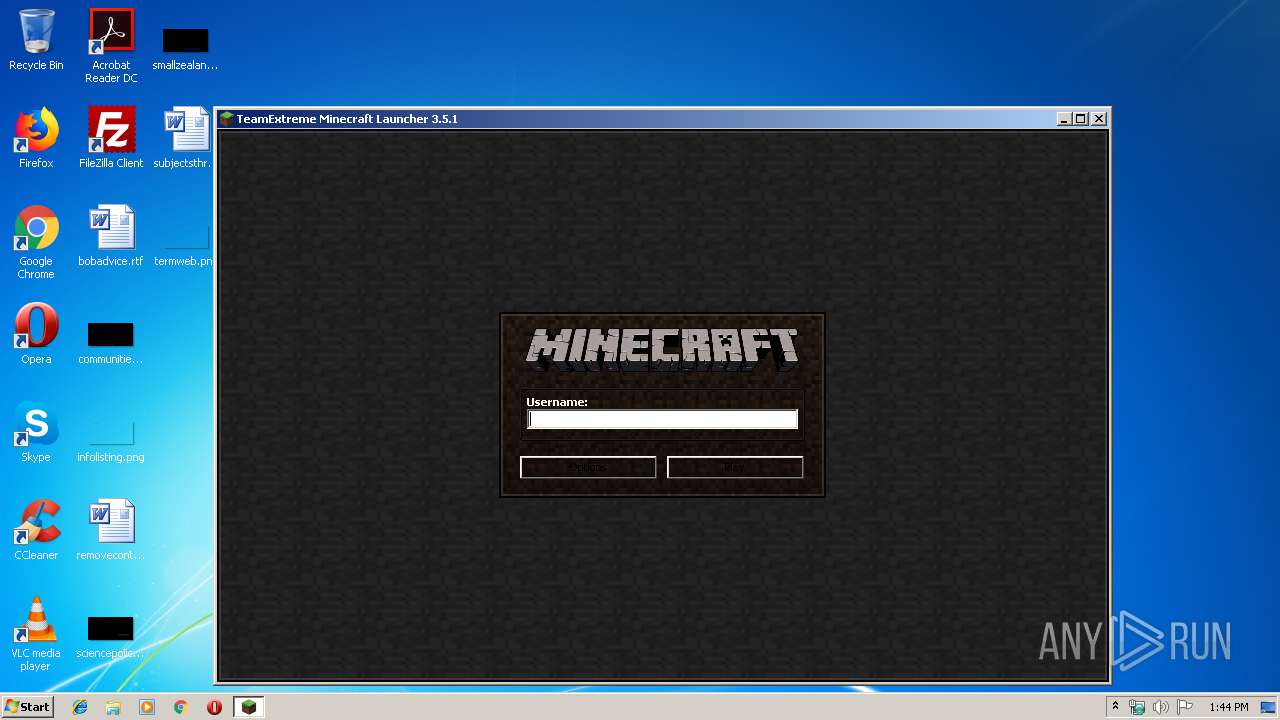
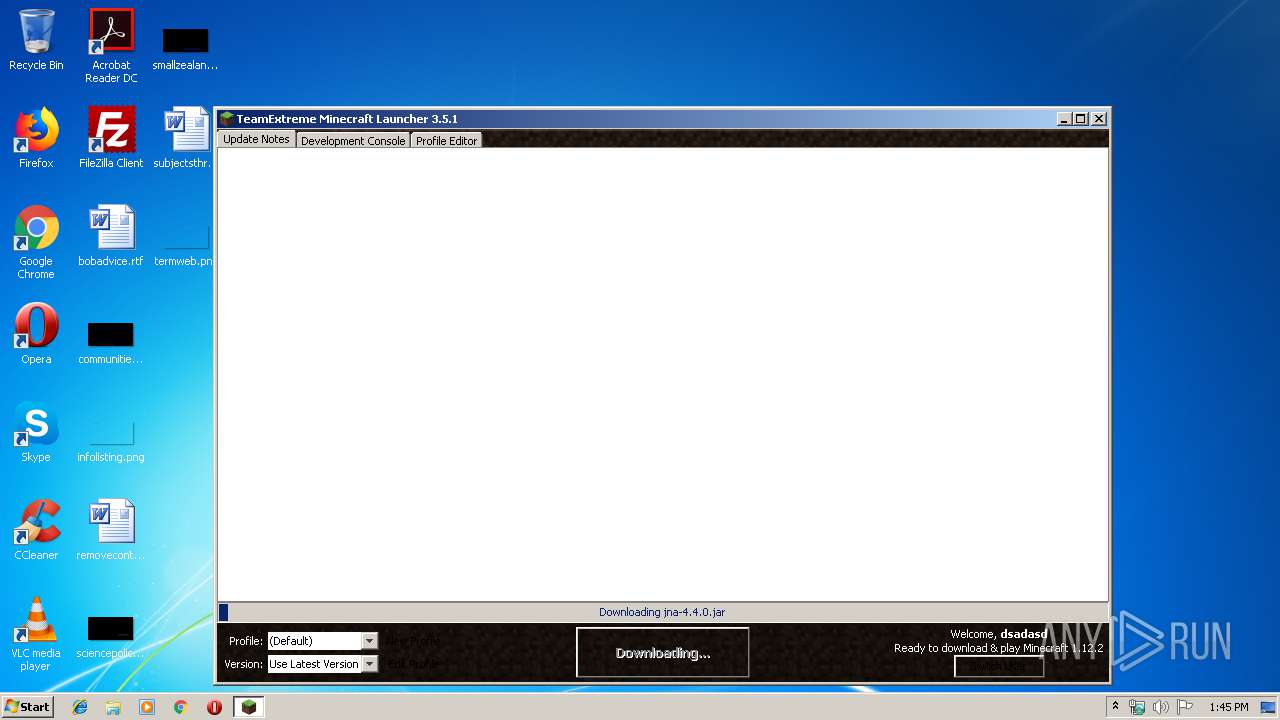
| File name: | Minecraft Cracked Launcher.exe |
| Full analysis: | https://app.any.run/tasks/006b801b-d1bb-499a-9ac9-6f74352023d5 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2020, 13:43:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C11F6674CCAE4E89F6970747C6E10E5F |
| SHA1: | 023D91D9ECD2222006F18CE7CCB07B4B66BE4E71 |
| SHA256: | 27CD248780400DB216FA6EA43E0DAD50A83BF00854C781601DE1F16468A0DCD0 |
| SSDEEP: | 49152:fjSeJnN0NdJu1UgHrnRAST8XrhaRY0T+nqO4P4S:Lcd4rn3T8hiVT+ne4S |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- Minecraft Cracked Launcher.exe (PID: 2620)
Creates files in the user directory
- javaw.exe (PID: 4088)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:12 17:47:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 18432 |
| InitializedDataSize: | 18432 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.1.0 |
| ProductVersionNumber: | 1.8.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TeamExtreme |
| FileDescription: | 1.8.1 Minecraft Launcher |
| FileVersion: | 3.5.1 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | TeamExtreme |
| OriginalFileName: | Minecraft Launcher.exe |
| ProductName: | TeamExtreme Minecraft Launcher |
| ProductVersion: | 1.8.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2015 16:47:59 |
| Detected languages: |
|
| CompanyName: | TeamExtreme |
| FileDescription: | 1.8.1 Minecraft Launcher |
| FileVersion: | 3.5.1 |
| InternalName: | Minecraft Launcher |
| LegalCopyright: | TeamExtreme |
| OriginalFilename: | Minecraft Launcher.exe |
| ProductName: | TeamExtreme Minecraft Launcher |
| ProductVersion: | 1.8.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 12-Feb-2015 16:47:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004728 | 0x00004800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.05951 |
.data | 0x00006000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.346693 |
.rdata | 0x00007000 | 0x00000500 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99808 |
.bss | 0x00008000 | 0x00008EF0 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000A94 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.61998 |
.rsrc | 0x00012000 | 0x00003248 | 0x00003400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.6483 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86519 | 1138 | UNKNOWN | Process Default Language | RT_MANIFEST |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 3.91327 | 25 | UNKNOWN | Process Default Language | RT_RCDATA |
25 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
27 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
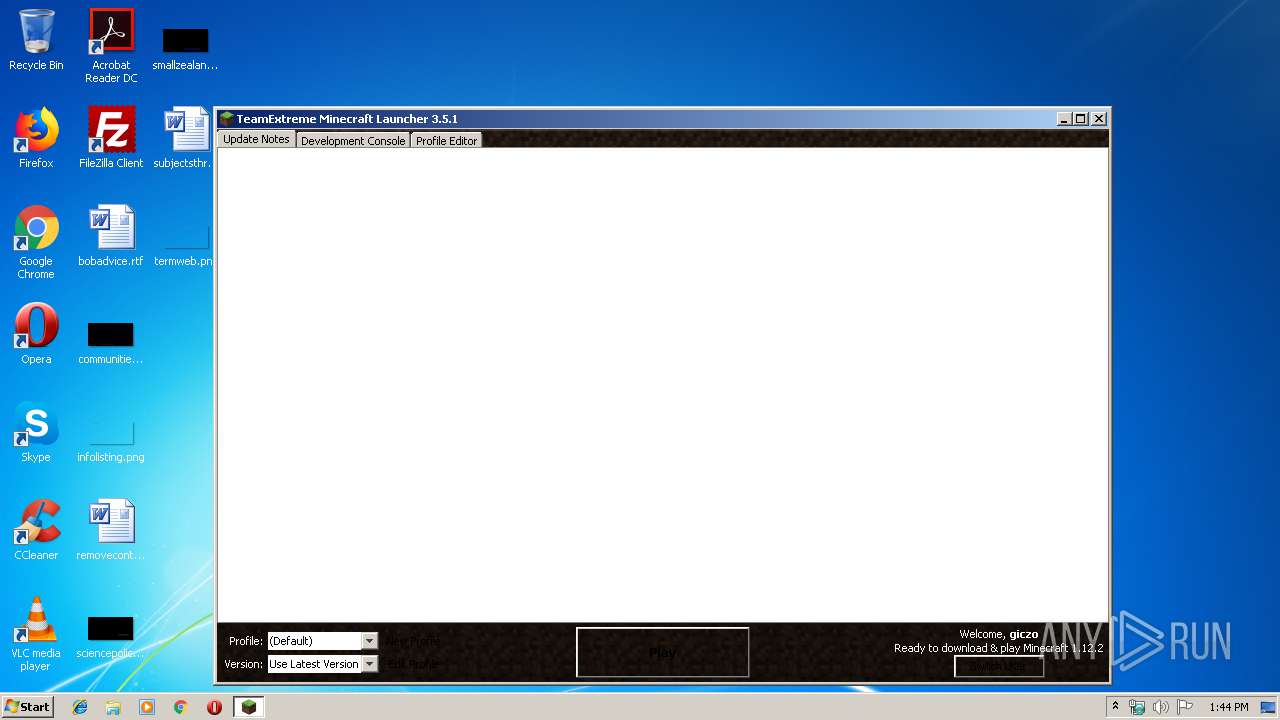
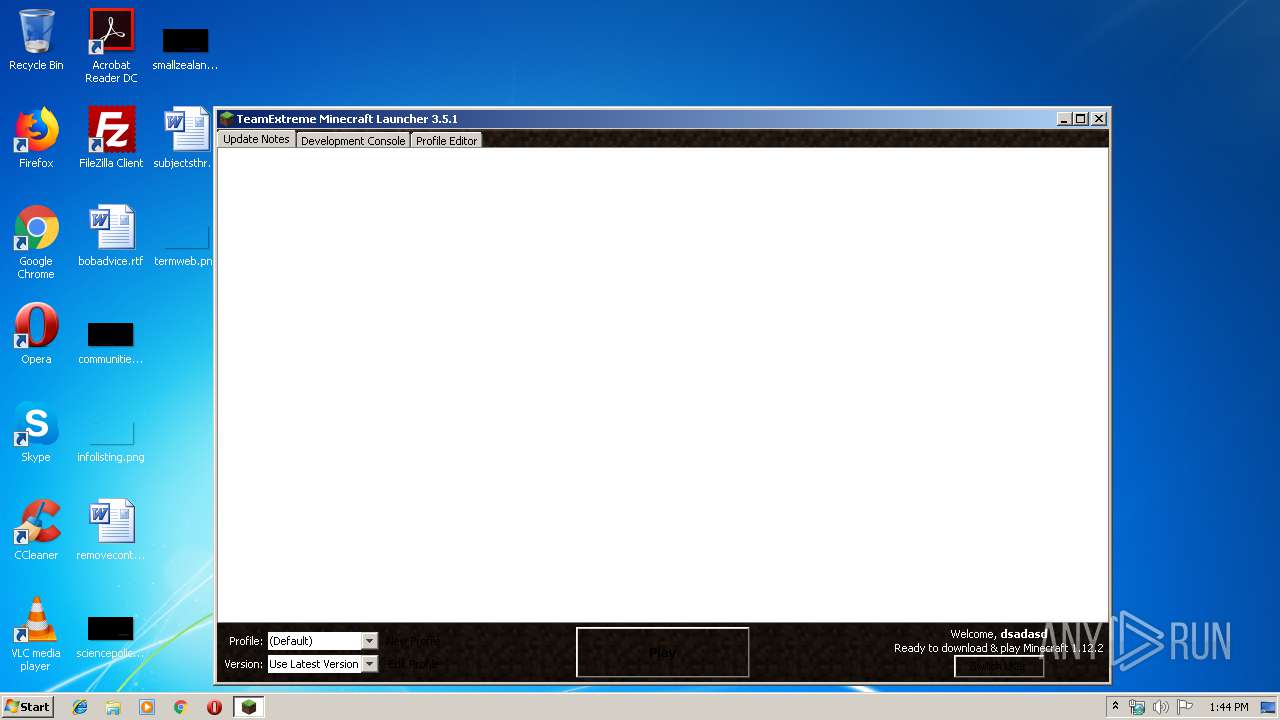
| 2620 | "C:\Users\admin\AppData\Local\Temp\Minecraft Cracked Launcher.exe" | C:\Users\admin\AppData\Local\Temp\Minecraft Cracked Launcher.exe | — | explorer.exe | |||||||||||
User: admin Company: TeamExtreme Integrity Level: MEDIUM Description: 1.8.1 Minecraft Launcher Exit code: 0 Version: 3.5.1 Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xms256m -Xmx512m -jar "C:\Users\admin\AppData\Local\Temp\Minecraft Cracked Launcher.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | Minecraft Cracked Launcher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
26
Read events
24
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4088) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
4
Suspicious files
16
Text files
45
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3211034832159806124.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio206842734146667801.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio7567851914460465367.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5901741970249696176.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio6760565288205614485.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4815234454217826071.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4834425565863949636.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3753684359825819859.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | text | |
MD5:— | SHA256:— | |||
| 4088 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl\lwjgl_util\2.9.4-nightly-20150209\lwjgl_util-2.9.4-nightly-20150209.jar.sha | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4088 | javaw.exe | GET | — | 54.240.168.67:80 | http://resources.download.minecraft.net/2c/2c4f3f8f259dc782867727311fea30875ecc3917 | US | — | — | shared |
— | — | GET | — | 54.240.168.67:80 | http://resources.download.minecraft.net/8f/8f81627af3836988935abc58a29362b2bcb13598 | US | — | — | shared |
— | — | GET | — | 54.240.168.67:80 | http://resources.download.minecraft.net/51/514185914aceffef29a78d7c4aabacd12e1a6cd1 | US | — | — | shared |
4088 | javaw.exe | GET | 404 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/launcherversion.txt | US | html | 315 b | malicious |
4088 | javaw.exe | GET | 200 | 198.54.115.64:80 | http://teamextrememc.com/failsafe/url.txt | US | text | 36 b | malicious |
4088 | javaw.exe | GET | 200 | 54.240.168.67:80 | http://resources.download.minecraft.net/22/2211e494688ba04b0c4658ed74d7e48c2d391c33 | US | ogg | 4.61 Kb | shared |
— | — | GET | 200 | 54.240.168.67:80 | http://resources.download.minecraft.net/5c/5c5c046607c1694ef1af630729921e3551e4b5e8 | US | ogg | 10.9 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4088 | javaw.exe | 162.125.65.6:443 | dl.dropboxusercontent.com | Dropbox, Inc. | NL | shared |
4088 | javaw.exe | 198.54.115.64:80 | teamextrememc.com | Namecheap, Inc. | US | malicious |
4088 | javaw.exe | 13.227.161.148:443 | libraries.minecraft.net | — | US | unknown |
4088 | javaw.exe | 54.240.168.67:80 | resources.download.minecraft.net | Amazon.com, Inc. | US | unknown |
— | — | 54.240.168.67:80 | resources.download.minecraft.net | Amazon.com, Inc. | US | unknown |
4088 | javaw.exe | 52.216.130.189:443 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.dropboxusercontent.com |
| shared |
teamextrememc.com |
| malicious |
dl.dropbox.com |
| shared |
s3.amazonaws.com |
| shared |
libraries.minecraft.net |
| shared |
resources.download.minecraft.net |
| shared |