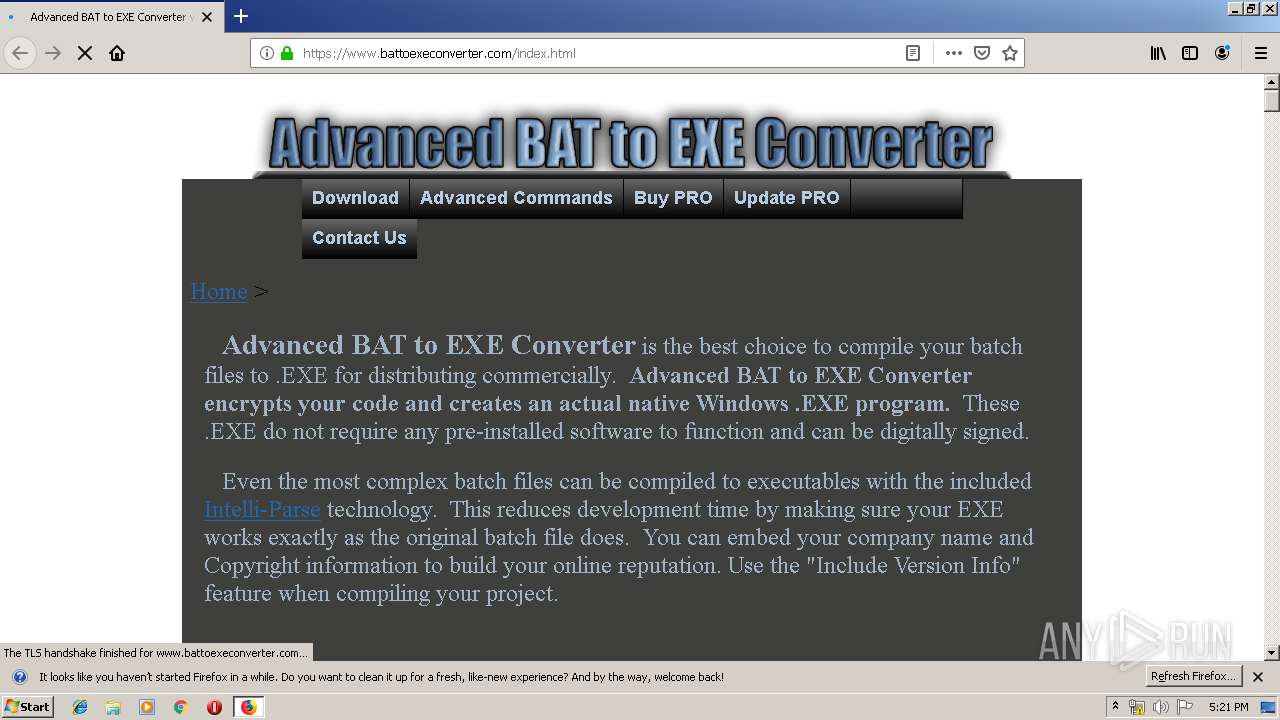
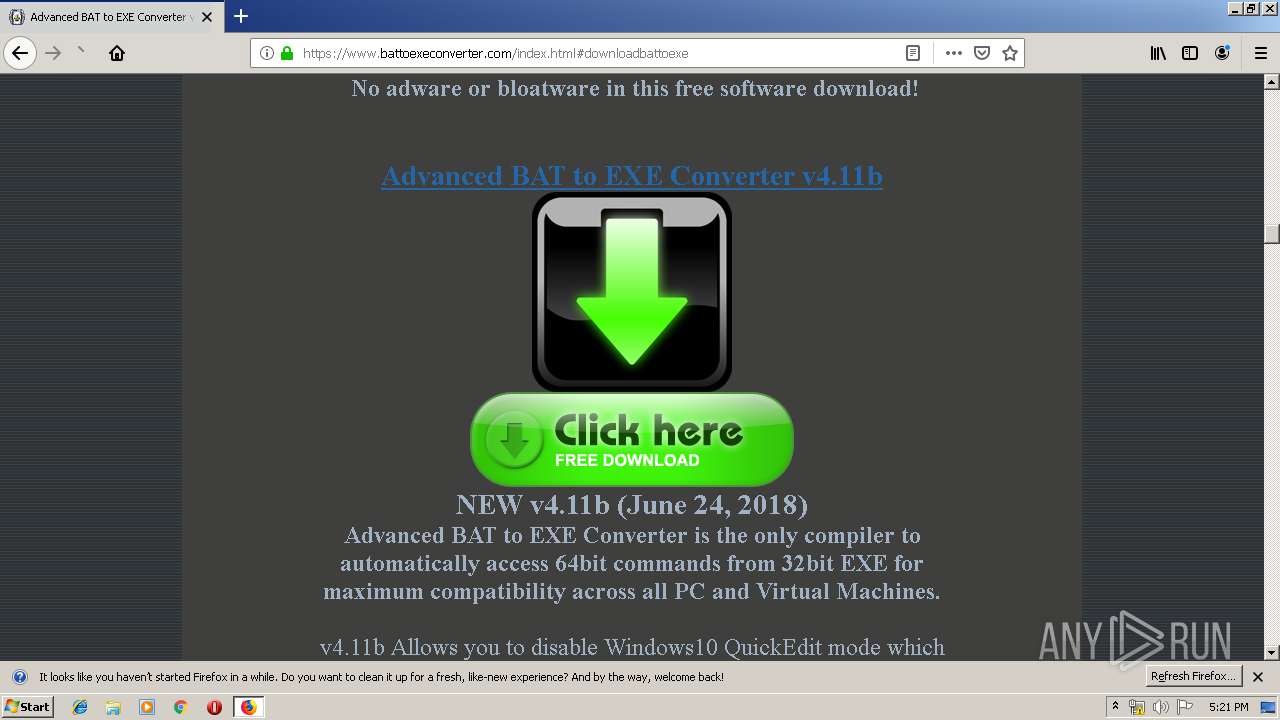
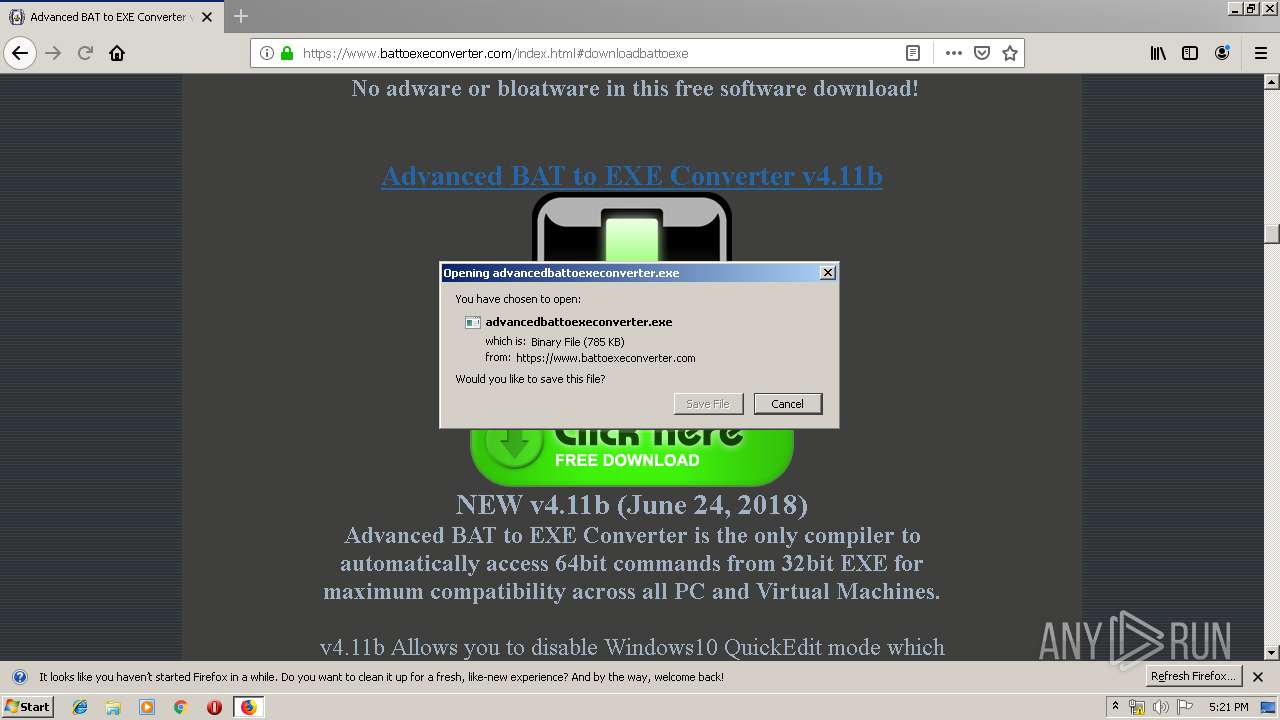
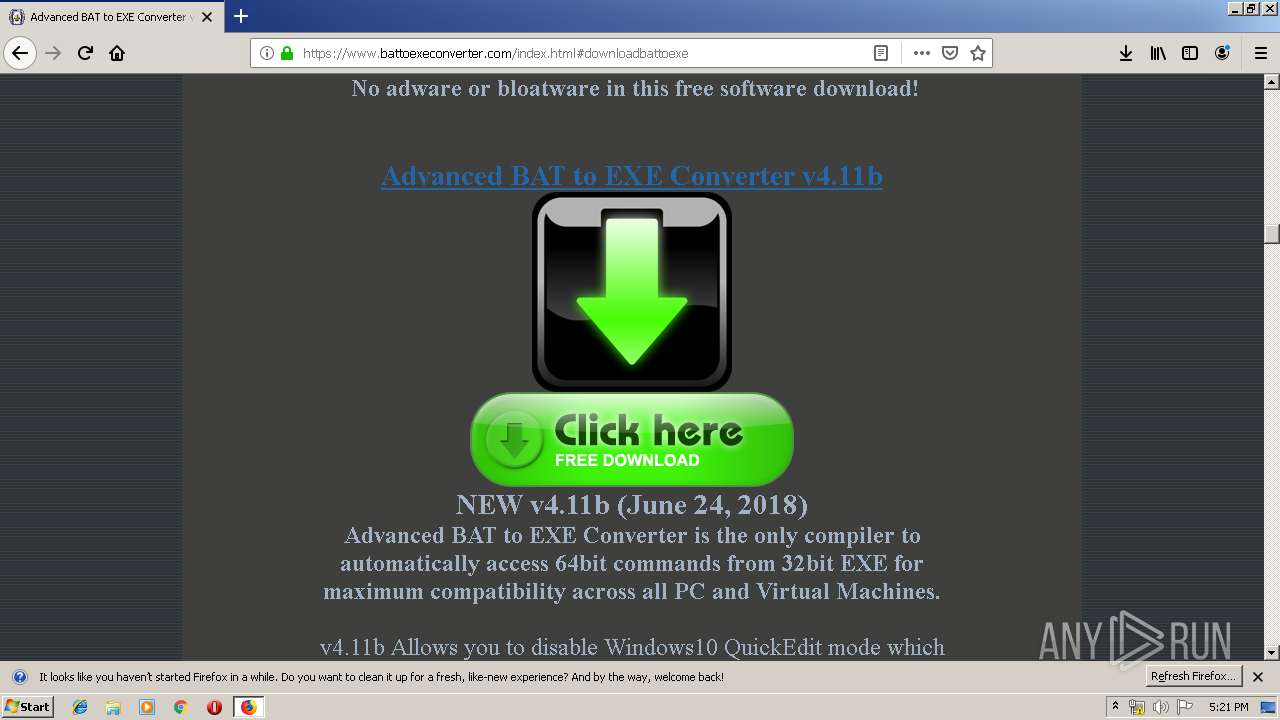
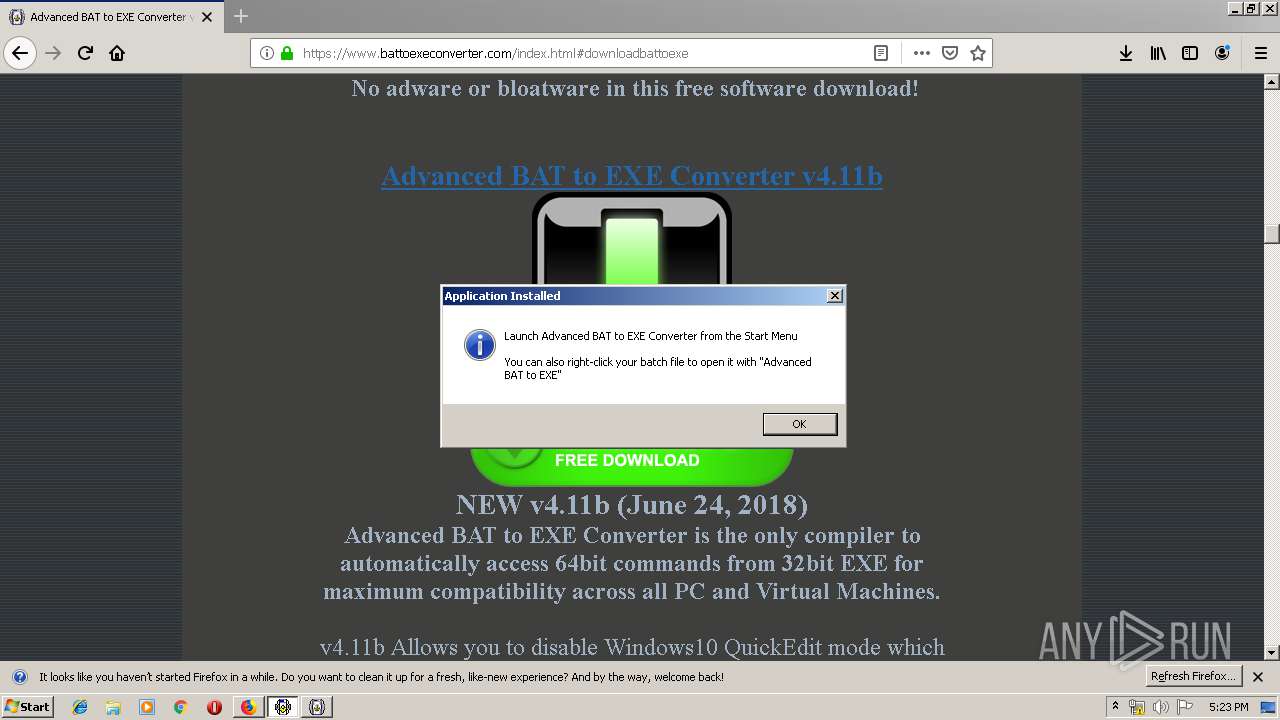
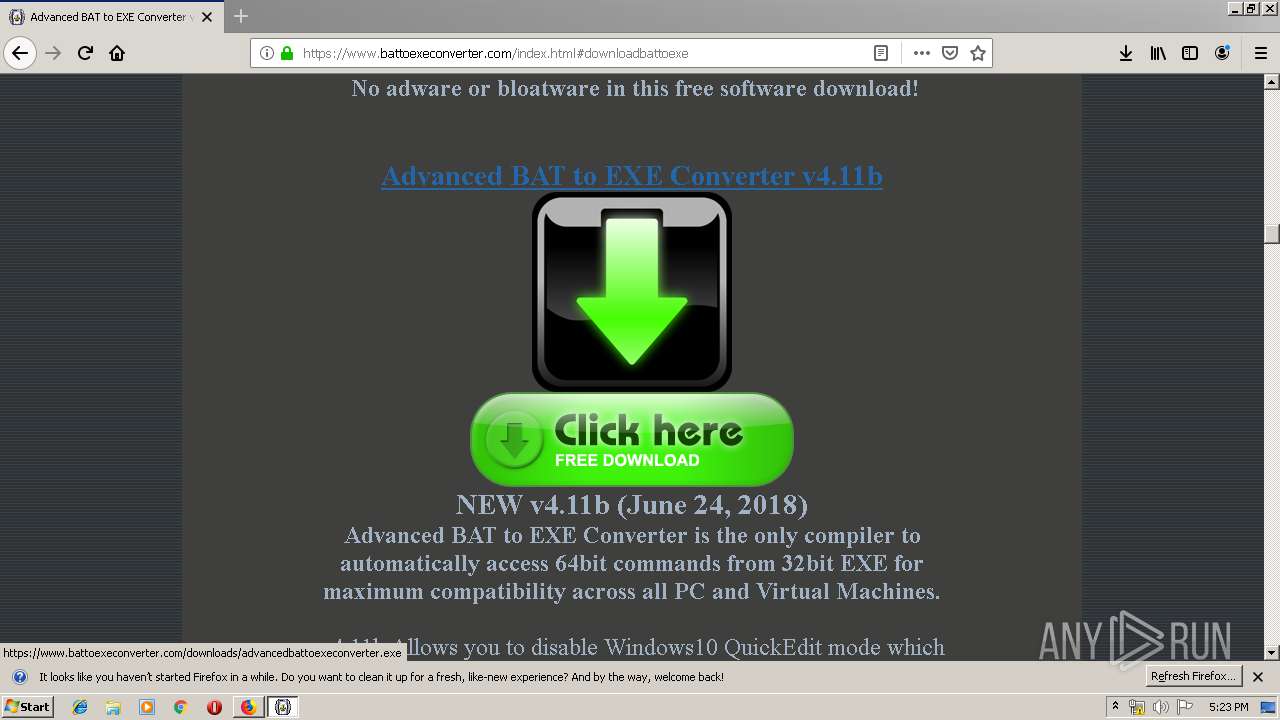
| URL: | https://www.battoexeconverter.com/index.html |
| Full analysis: | https://app.any.run/tasks/49251767-4f50-4075-96d2-2348b6bd3bef |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 16:20:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 941468DAA4B228C92F5790B3E5B5CD7A |
| SHA1: | 62910B9CD466133124B5B306E78F45F2B5DAEC74 |
| SHA256: | 27CC7E482BD722513FFA2A2186B43B13BD271EC57A1ED2E05A17D4E382C9E4DD |
| SSDEEP: | 3:N8DSLkJjXX4DG:2OLkpXoDG |
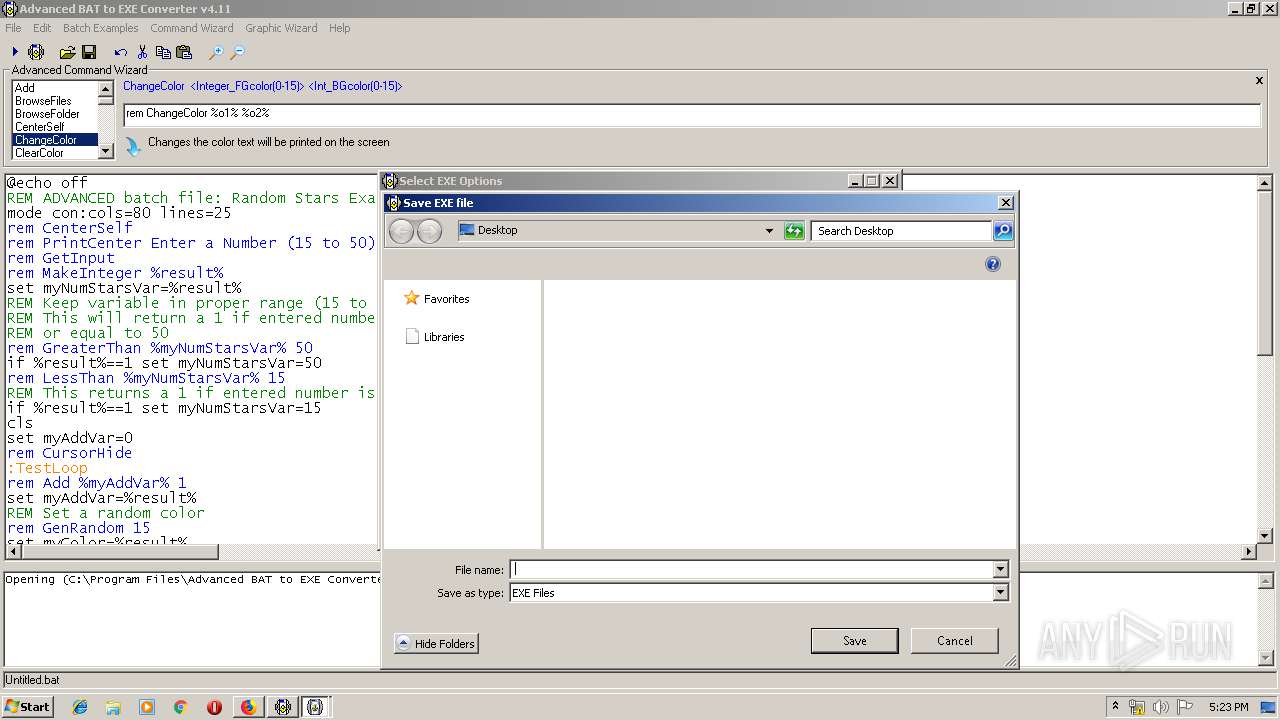
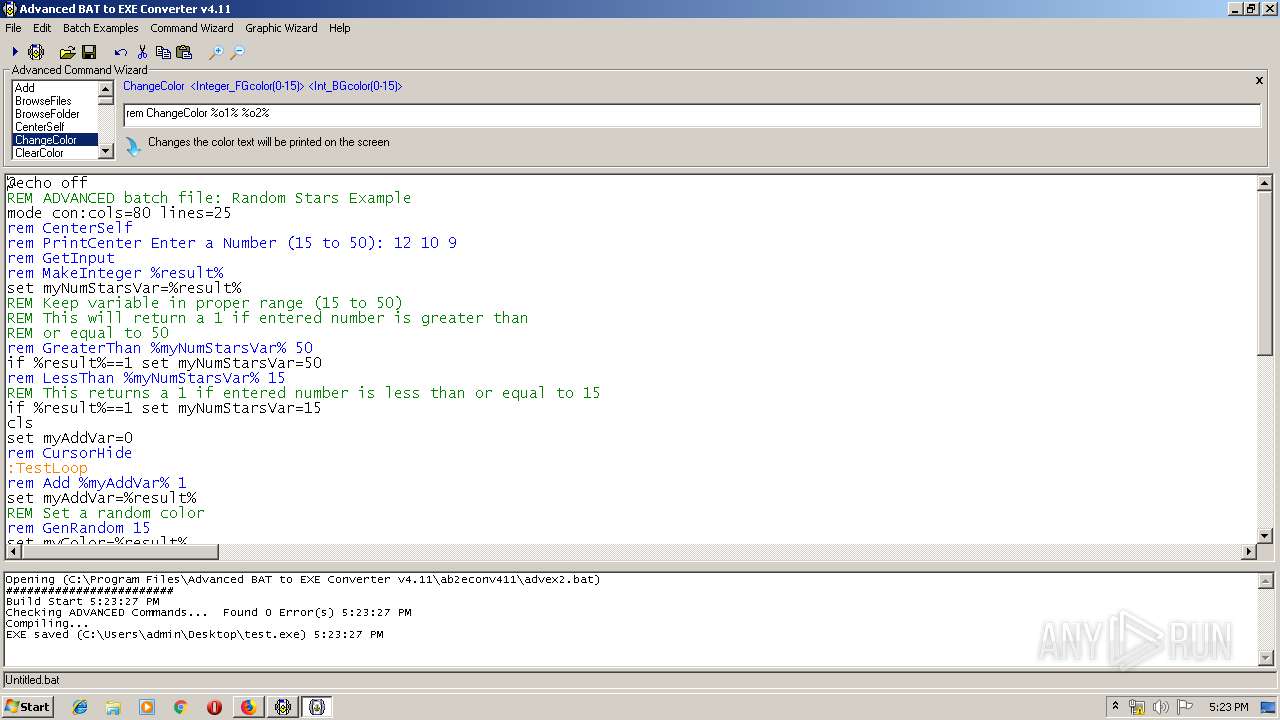
MALICIOUS
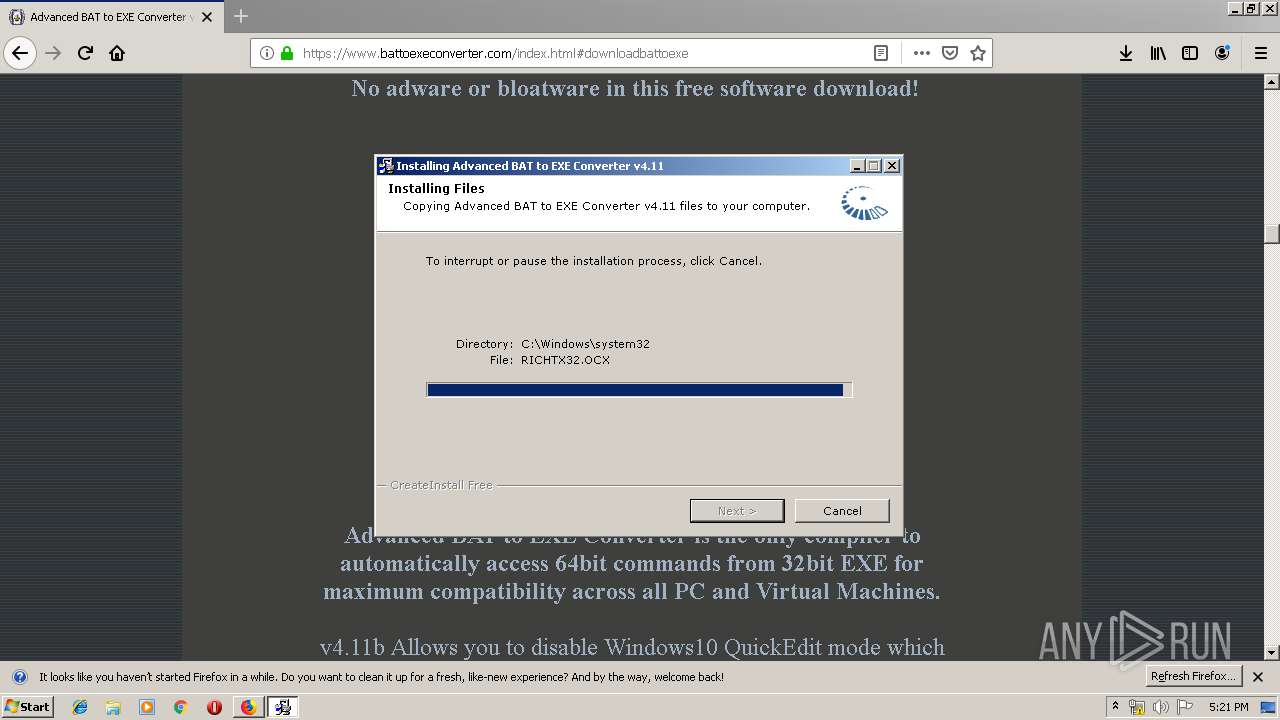
Application was dropped or rewritten from another process
- advancedbattoexeconverter.exe (PID: 1484)
- setupinf.exe (PID: 3316)
- test.exe (PID: 1632)
- advancedbattoexeconverter.exe (PID: 2092)
- ab2econv.exe (PID: 1312)
- tmp64389.exe (PID: 3304)
- tmp64389.exe (PID: 1680)
- tmp64389.exe (PID: 1784)
- tmp64389.exe (PID: 2288)
- tmp64389.exe (PID: 3216)
- tmp64389.exe (PID: 1440)
- tmp64389.exe (PID: 3816)
- tmp64389.exe (PID: 1512)
- tmp64389.exe (PID: 3824)
- tmp64389.exe (PID: 1752)
- tmp64389.exe (PID: 3892)
- tmp64389.exe (PID: 2416)
- tmp64389.exe (PID: 836)
- tmp64389.exe (PID: 3636)
- tmp64389.exe (PID: 2396)
- tmp64389.exe (PID: 3700)
- tmp64389.exe (PID: 3100)
- tmp64389.exe (PID: 3500)
- tmp64389.exe (PID: 2996)
- tmp64389.exe (PID: 2944)
- tmp64389.exe (PID: 3848)
- tmp64389.exe (PID: 3216)
- tmp64389.exe (PID: 2996)
- tmp64389.exe (PID: 1732)
- tmp64389.exe (PID: 932)
- tmp64389.exe (PID: 2072)
- tmp64389.exe (PID: 356)
- tmp64389.exe (PID: 2328)
- tmp64389.exe (PID: 2736)
- tmp64389.exe (PID: 1688)
- tmp64389.exe (PID: 3536)
- tmp64389.exe (PID: 1992)
- tmp64389.exe (PID: 1332)
- tmp64389.exe (PID: 548)
- tmp64389.exe (PID: 1720)
- tmp64389.exe (PID: 3572)
- tmp64389.exe (PID: 2784)
- tmp64389.exe (PID: 3944)
- tmp64389.exe (PID: 1200)
- tmp64389.exe (PID: 3620)
- tmp64389.exe (PID: 3812)
- tmp64389.exe (PID: 3712)
- tmp64389.exe (PID: 1568)
- tmp64389.exe (PID: 3004)
- tmp64389.exe (PID: 876)
- tmp64389.exe (PID: 3940)
- tmp64389.exe (PID: 2992)
- tmp64389.exe (PID: 3684)
- tmp64389.exe (PID: 3604)
- tmp64389.exe (PID: 3356)
- tmp64389.exe (PID: 2032)
- tmp64389.exe (PID: 2320)
- tmp64389.exe (PID: 3768)
- tmp64389.exe (PID: 340)
- tmp64389.exe (PID: 1852)
- tmp64389.exe (PID: 2444)
- tmp64389.exe (PID: 3056)
- tmp64389.exe (PID: 4056)
- tmp64389.exe (PID: 3484)
- tmp64389.exe (PID: 2416)
- tmp64389.exe (PID: 1852)
- tmp64389.exe (PID: 3100)
- tmp64389.exe (PID: 608)
- tmp64389.exe (PID: 2408)
- tmp64389.exe (PID: 3620)
- tmp64389.exe (PID: 884)
- tmp64389.exe (PID: 2660)
- tmp64389.exe (PID: 860)
- tmp64389.exe (PID: 2484)
- tmp64389.exe (PID: 1892)
- tmp64389.exe (PID: 2788)
- tmp64389.exe (PID: 3364)
- tmp64389.exe (PID: 3940)
- tmp64389.exe (PID: 3720)
- tmp64389.exe (PID: 3080)
- tmp64389.exe (PID: 1000)
- tmp64389.exe (PID: 2724)
- tmp64389.exe (PID: 3180)
- tmp64389.exe (PID: 3784)
- tmp64389.exe (PID: 1512)
- tmp64389.exe (PID: 3632)
- tmp64389.exe (PID: 3368)
- tmp64389.exe (PID: 1492)
- tmp64389.exe (PID: 3304)
- tmp64389.exe (PID: 1808)
- tmp64389.exe (PID: 1892)
- tmp64389.exe (PID: 2320)
- tmp64389.exe (PID: 1708)
- tmp64389.exe (PID: 3860)
- tmp64389.exe (PID: 1956)
- tmp64389.exe (PID: 3068)
- tmp64389.exe (PID: 3572)
- tmp64389.exe (PID: 3164)
- tmp64389.exe (PID: 3024)
- tmp64389.exe (PID: 1472)
- tmp64389.exe (PID: 1692)
- tmp64389.exe (PID: 1252)
- tmp64389.exe (PID: 1672)
- tmp64389.exe (PID: 3340)
- tmp64389.exe (PID: 2488)
- tmp64389.exe (PID: 3224)
- tmp64389.exe (PID: 2456)
- tmp64389.exe (PID: 1356)
- tmp64389.exe (PID: 352)
- tmp64389.exe (PID: 2544)
- tmp64389.exe (PID: 4056)
- tmp64389.exe (PID: 3220)
- tmp64389.exe (PID: 1700)
- tmp64389.exe (PID: 884)
- tmp64389.exe (PID: 2912)
- tmp64389.exe (PID: 3716)
- tmp64389.exe (PID: 3076)
- tmp64389.exe (PID: 2124)
- tmp64389.exe (PID: 2796)
- tmp64389.exe (PID: 4036)
- tmp64389.exe (PID: 3824)
- tmp64389.exe (PID: 3996)
- tmp64389.exe (PID: 3684)
- tmp64389.exe (PID: 1036)
- tmp64389.exe (PID: 1412)
- tmp64389.exe (PID: 2372)
- tmp64389.exe (PID: 1200)
- tmp64389.exe (PID: 3652)
- tmp64389.exe (PID: 3308)
- tmp64389.exe (PID: 3028)
- tmp64389.exe (PID: 3040)
- tmp64389.exe (PID: 1752)
- tmp64389.exe (PID: 2844)
- tmp64389.exe (PID: 3672)
- tmp64389.exe (PID: 3868)
- tmp64389.exe (PID: 2516)
- tmp64389.exe (PID: 1700)
- tmp64389.exe (PID: 760)
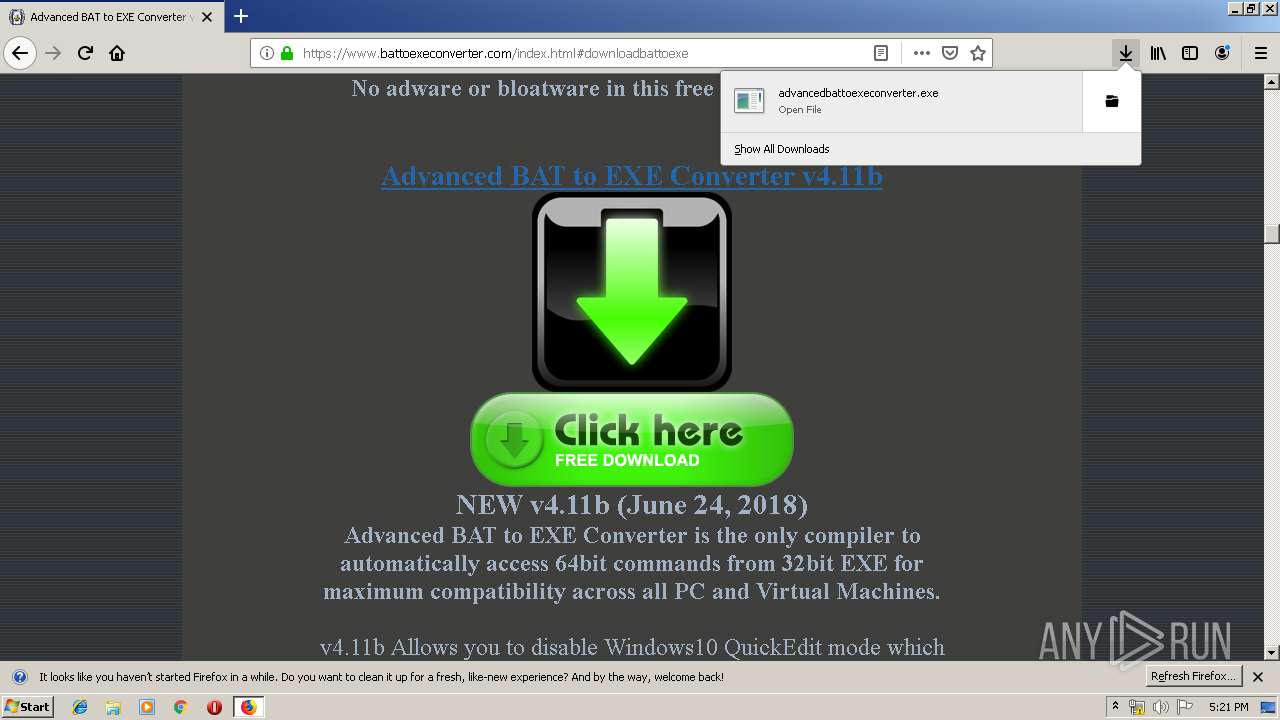
Loads dropped or rewritten executable
- advancedbattoexeconverter.exe (PID: 2092)
SUSPICIOUS
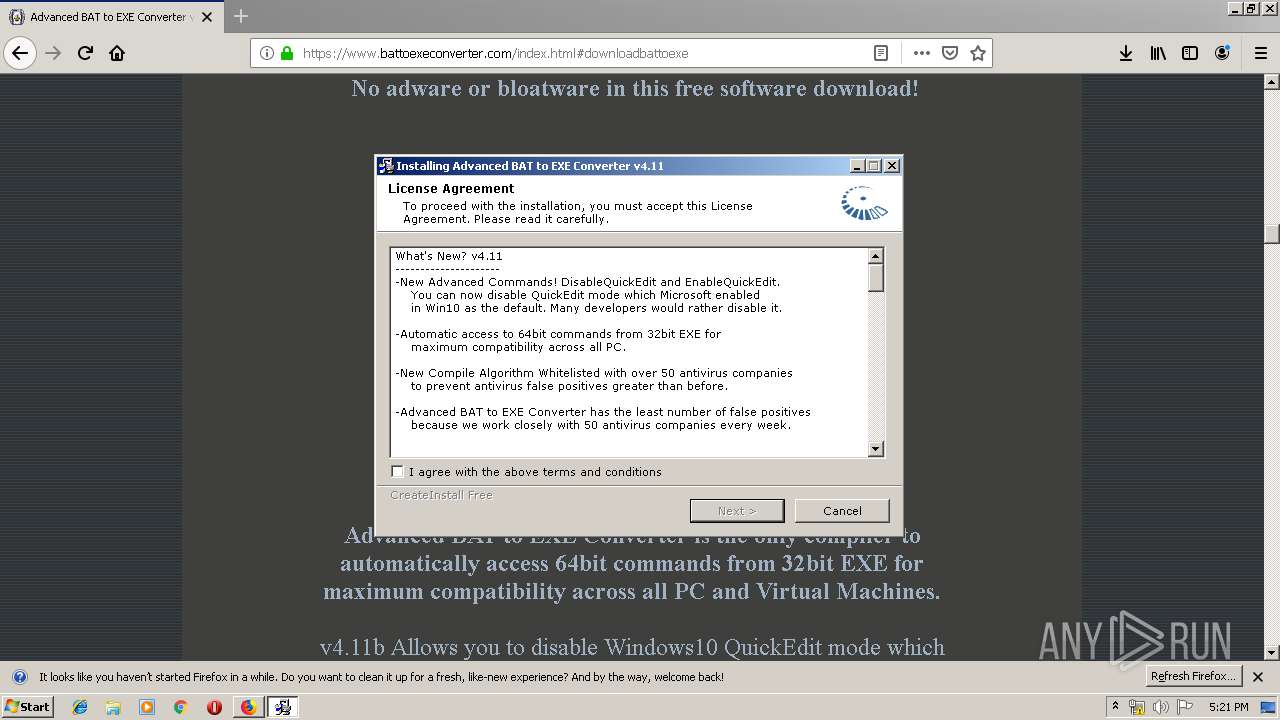
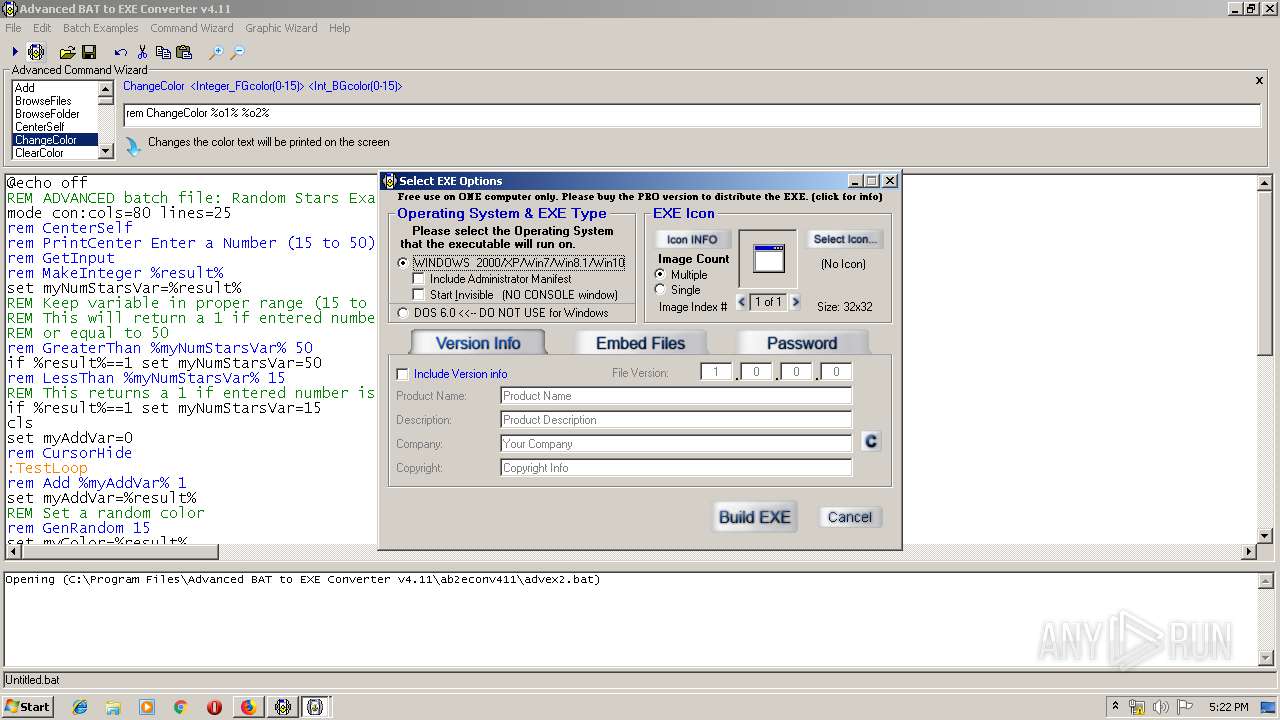
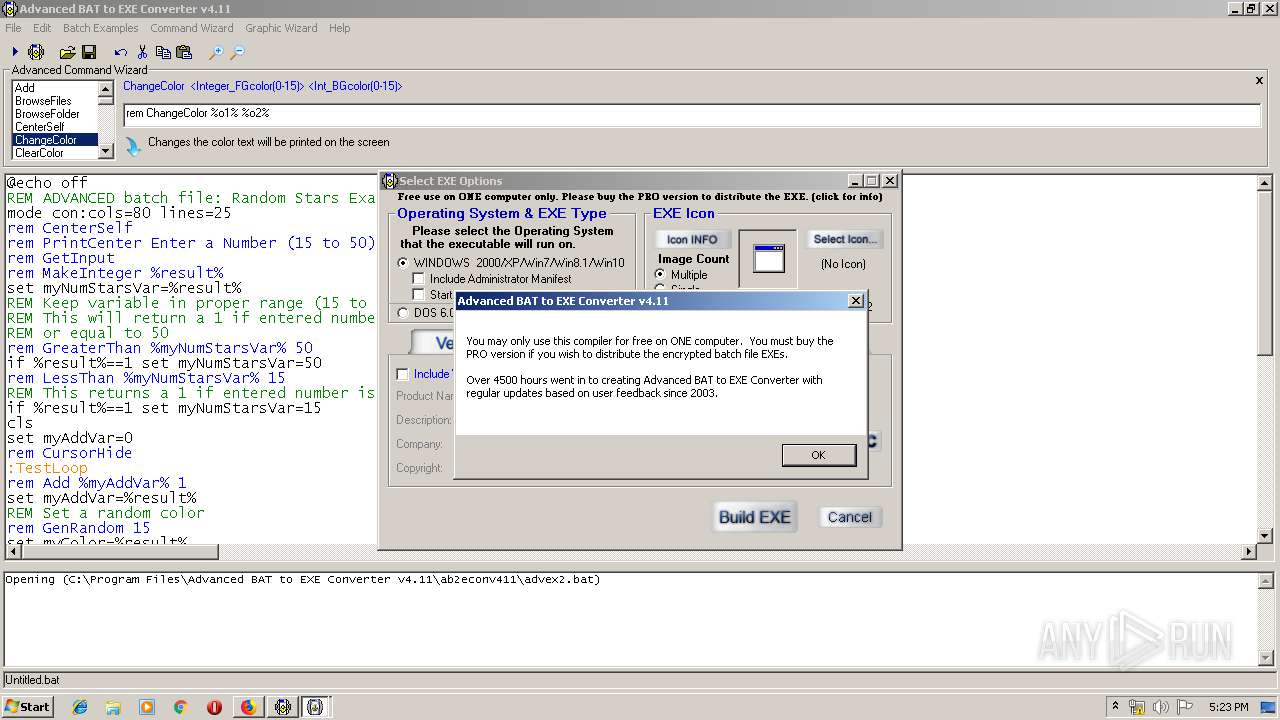
Creates a software uninstall entry
- advancedbattoexeconverter.exe (PID: 2092)
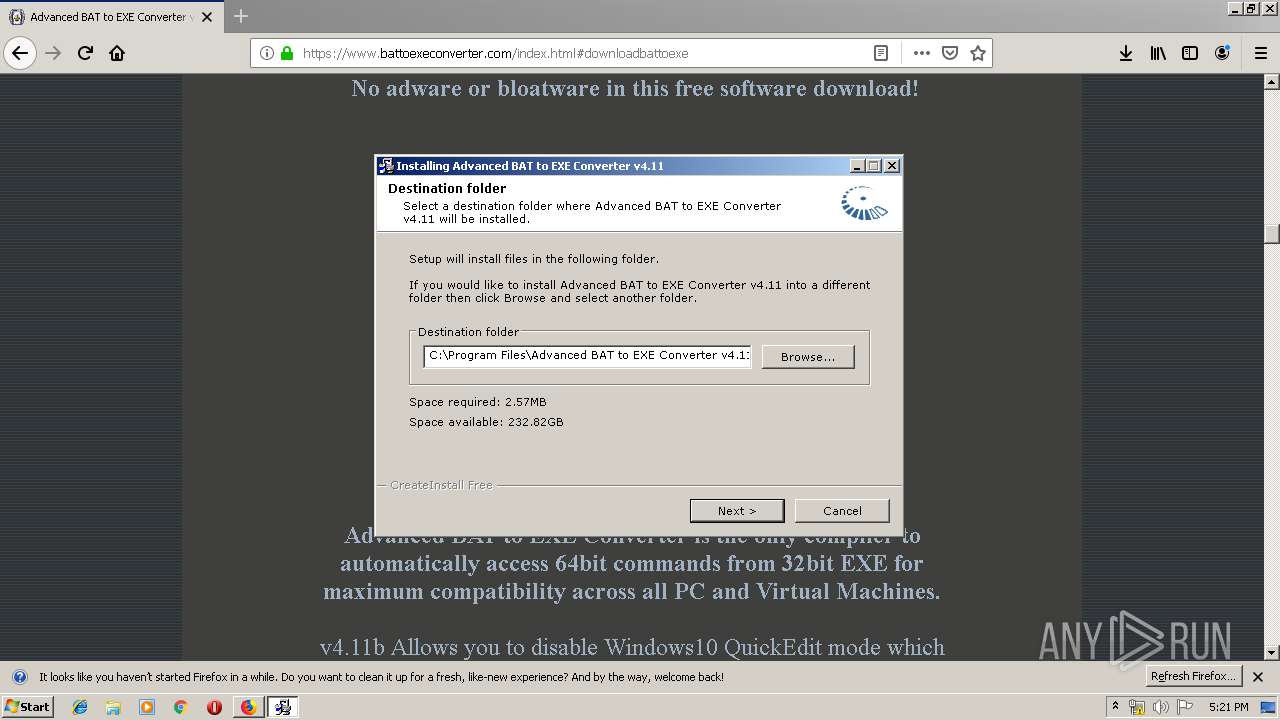
Creates files in the program directory
- advancedbattoexeconverter.exe (PID: 2092)
Creates files in the Windows directory
- advancedbattoexeconverter.exe (PID: 2092)
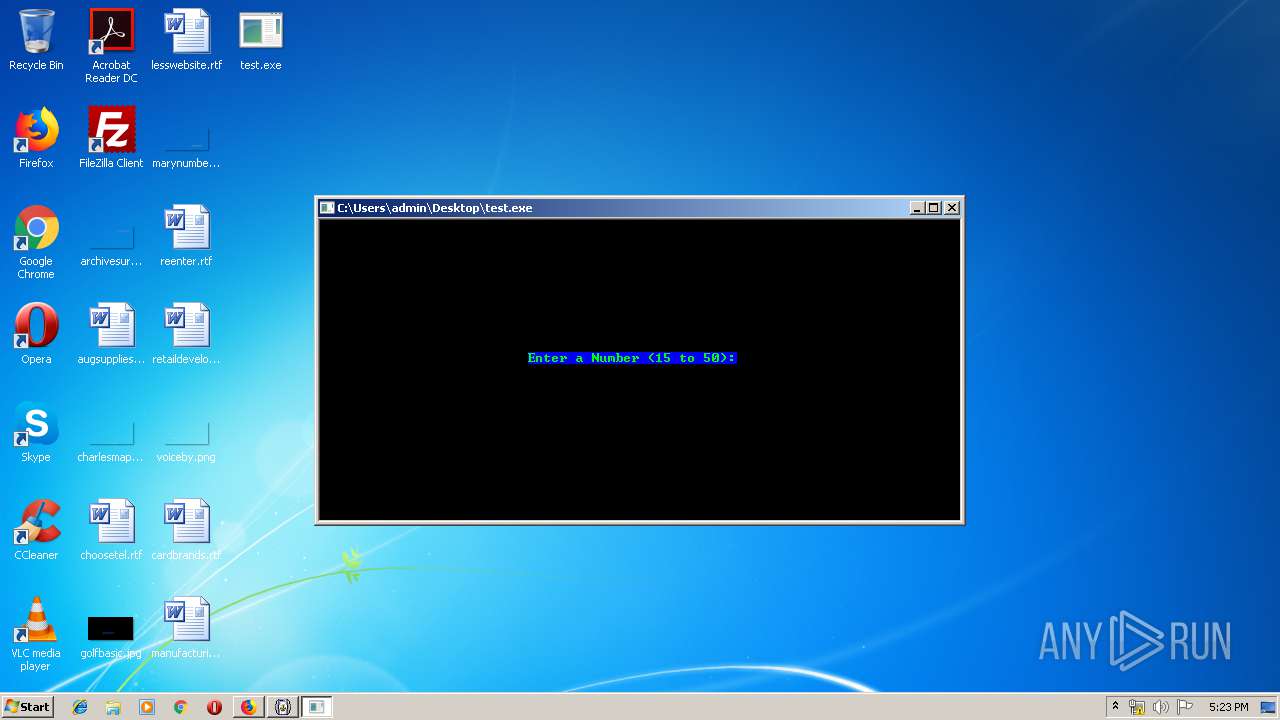
Starts CMD.EXE for commands execution
- test.exe (PID: 1632)
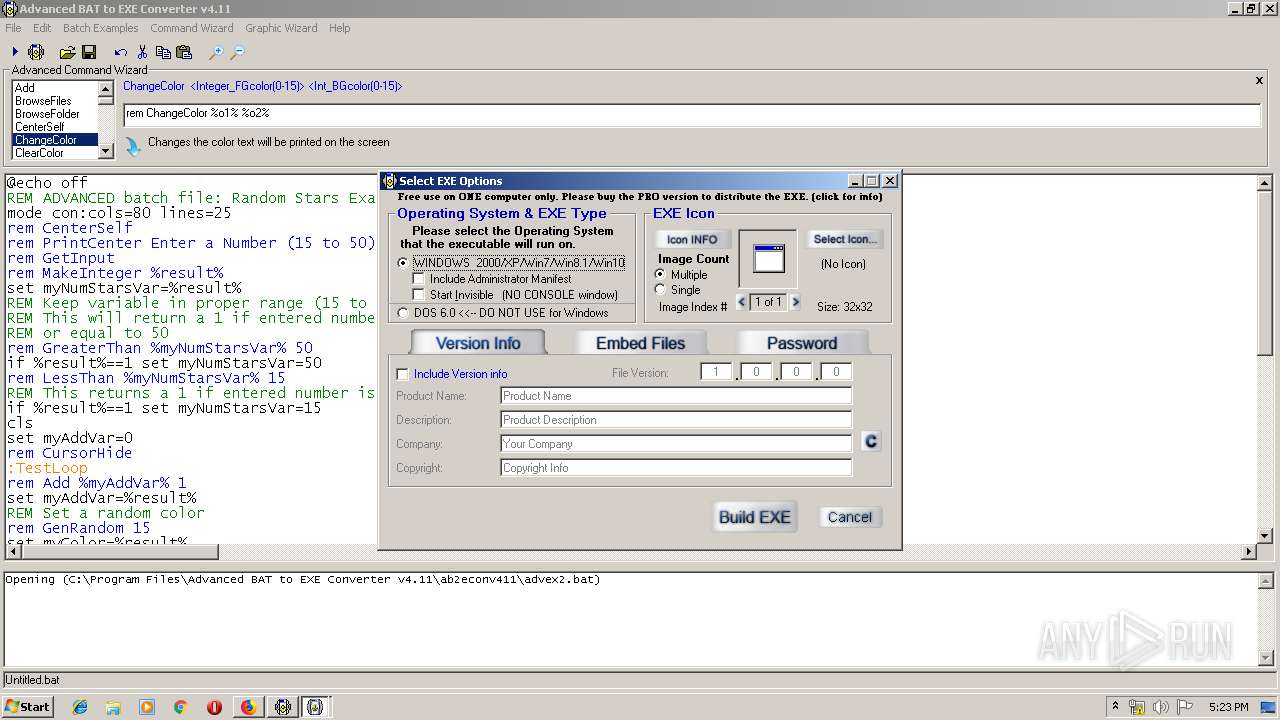
Executable content was dropped or overwritten
- advancedbattoexeconverter.exe (PID: 2092)
- ab2econv.exe (PID: 1312)
- test.exe (PID: 1632)
- firefox.exe (PID: 2720)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2540)
Creates files in the user directory
- advancedbattoexeconverter.exe (PID: 2092)
INFO
Application launched itself
- firefox.exe (PID: 2720)
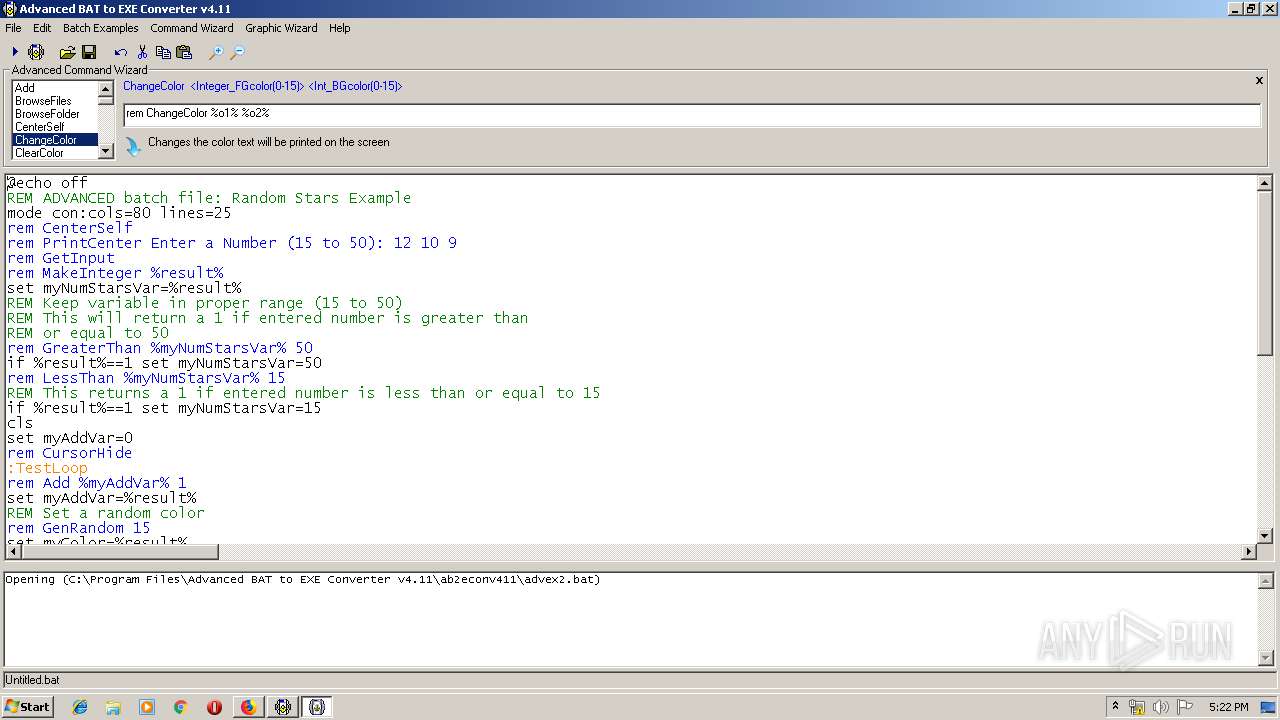
Manual execution by user
- test.exe (PID: 1632)
Reads CPU info
- firefox.exe (PID: 2720)
Reads settings of System Certificates
- firefox.exe (PID: 2720)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2720)
Creates files in the user directory
- firefox.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
153
Malicious processes
32
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe" del "C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe" | C:\Windows\system32\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 340 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe h4XZpeGaQv 15 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 352 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe x6jH08uIp2 13 38 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 356 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli X 21 80 6 0 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 548 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe h4XZpeGaQv 80 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 608 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli X 22 8 8 0 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 760 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli x 5 64 4 15 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 836 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli x 14 53 15 15 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 860 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli x 22 8 8 15 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 876 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe Y53moFxWli x 12 41 11 15 | C:\Users\admin\AppData\Local\Temp\xtmp\tmp64389.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 654
Read events
1 532
Write events
116
Delete events
6
Modification events
| (PID) Process: | (2720) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (2720) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2720) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2720) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2720) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2092) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.11 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.11\uninstall.exe | |||
| (PID) Process: | (2092) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.11 |
| Operation: | write | Name: | DisplayName |
Value: Advanced BAT to EXE Converter v4.11 | |||
| (PID) Process: | (2092) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter v4.11 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Advanced BAT to EXE Converter v4.11\uninstall.exe | |||
| (PID) Process: | (2092) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2092) advancedbattoexeconverter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | write | Name: | |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
Executable files
27
Suspicious files
71
Text files
111
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\pluginreg.dat.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2720 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
52
DNS requests
76
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2720 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2720 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2720 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
— | — | 172.217.16.174:80 | — | Google Inc. | US | whitelisted |
2720 | firefox.exe | 52.18.148.152:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
2720 | firefox.exe | 50.63.124.28:443 | www.battoexeconverter.com | GoDaddy.com, LLC | US | unknown |
2720 | firefox.exe | 34.208.138.0:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | malicious |
2720 | firefox.exe | 13.224.192.58:443 | snippets.cdn.mozilla.net | — | US | unknown |
2720 | firefox.exe | 188.121.36.239:80 | ocsp.godaddy.com | GoDaddy.com, LLC | NL | unknown |
2720 | firefox.exe | 35.160.187.49:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2720 | firefox.exe | 172.217.23.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2720 | firefox.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod1-elb-eu-west-1.prod.mozaws.net |
| whitelisted |
www.battoexeconverter.com |
| malicious |
battoexeconverter.com |
| malicious |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |