| URL: | https://cld.pt/dl/download/e30c7587-c1e1-4911-ab27-d6d061fa9074/Fact.Endesa-Ref-27-06-2022.zip |
| Full analysis: | https://app.any.run/tasks/1d837ab5-7129-4c1b-afc3-6c590387ab85 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 09:24:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7E9C0CE027C9E23556215CFA5AD6130C |
| SHA1: | D5314E9BA943284F1380215841505A8589BD3B3F |
| SHA256: | 27C3E1317ED09BC3D10601AA2E6C01540E953F007C38B232EEA8B220AF86ECC0 |
| SSDEEP: | 3:N8U9VRK/a4z8dS36a/CVIpjEGtO2WWUXC5U:2U3RKCE8dT6CVINEGO7 |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 1980)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4020)
Reads the computer name
- WinRAR.exe (PID: 3696)
- msiexec.exe (PID: 1980)
- MsiExec.exe (PID: 3436)
Checks supported languages
- WinRAR.exe (PID: 3696)
- MsiExec.exe (PID: 3436)
- msiexec.exe (PID: 1980)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2392)
- msiexec.exe (PID: 1980)
Reads the Windows organization settings
- msiexec.exe (PID: 2392)
- msiexec.exe (PID: 1980)
Drops a file with a compile date too recent
- msiexec.exe (PID: 1980)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1980)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2504)
Checks supported languages
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 4020)
- msiexec.exe (PID: 2392)
Reads the computer name
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 4020)
- msiexec.exe (PID: 2392)
Application launched itself
- iexplore.exe (PID: 2504)
- msiexec.exe (PID: 1980)
Checks Windows Trust Settings
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 2504)
Reads settings of System Certificates
- iexplore.exe (PID: 4020)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2504)
Reads the date of Windows installation
- iexplore.exe (PID: 2504)
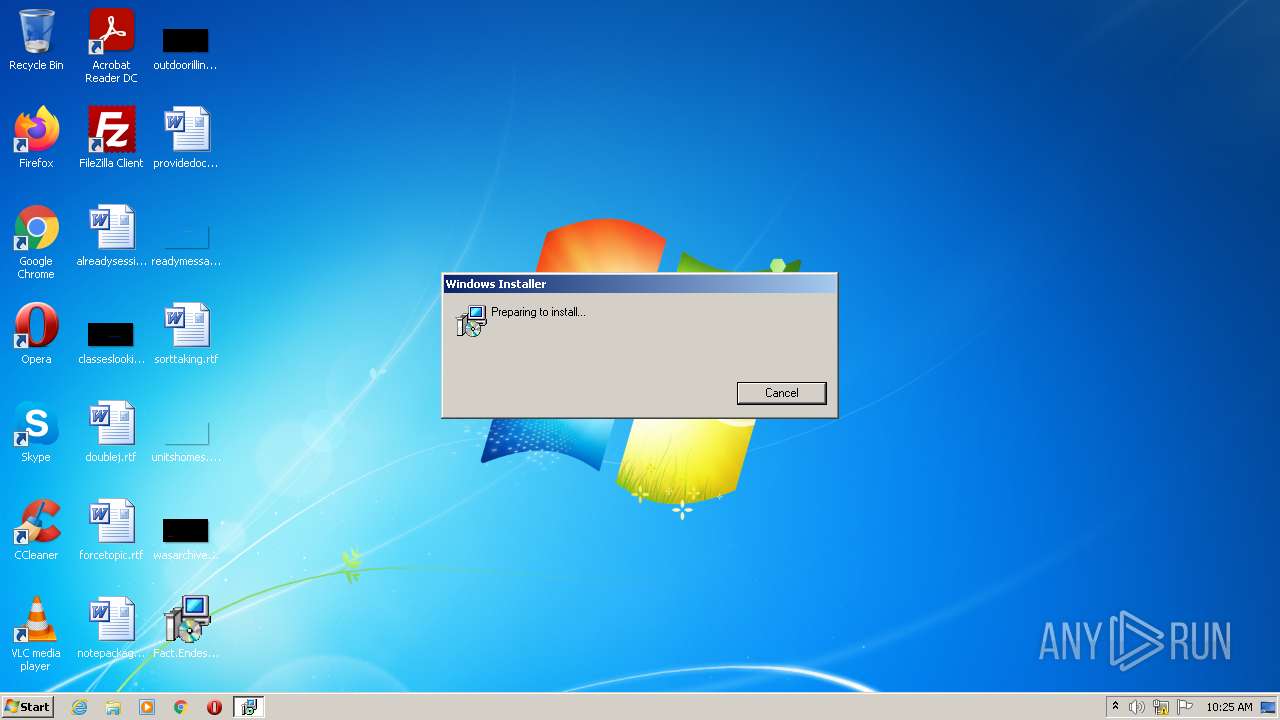
Manual execution by user
- msiexec.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
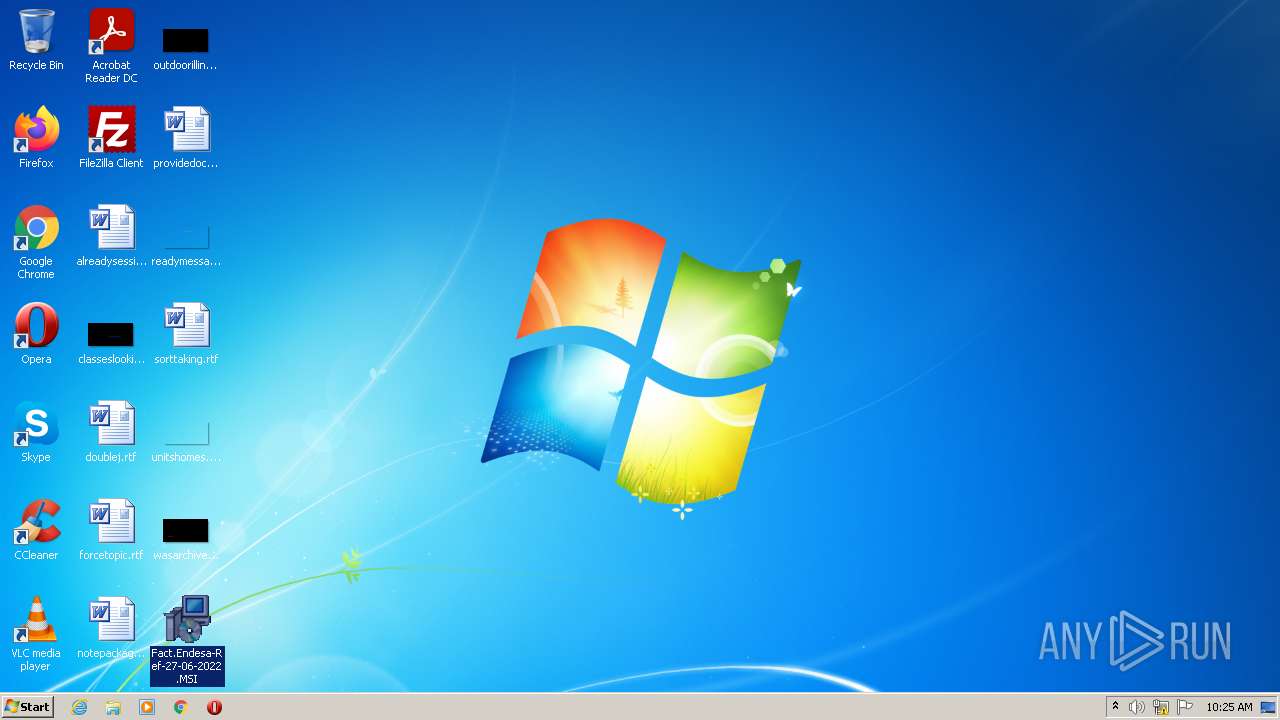
| 2392 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\Fact.Endesa-Ref-27-06-2022.MSI" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
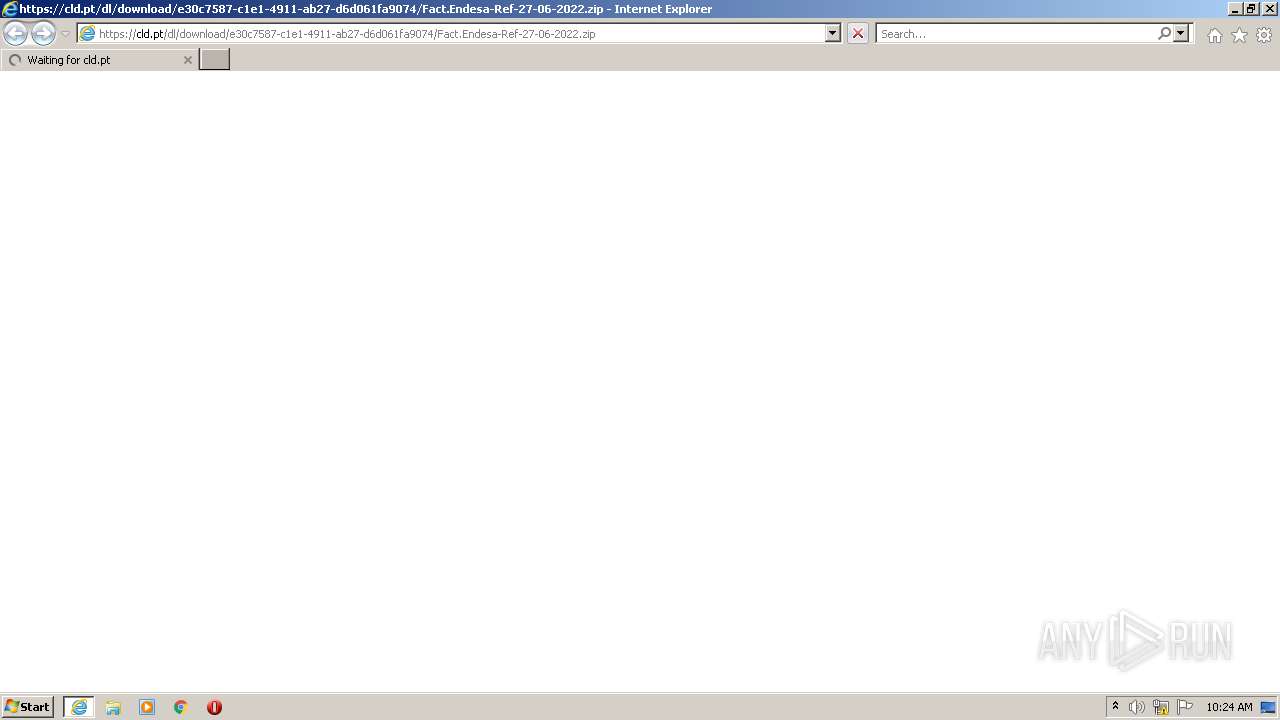
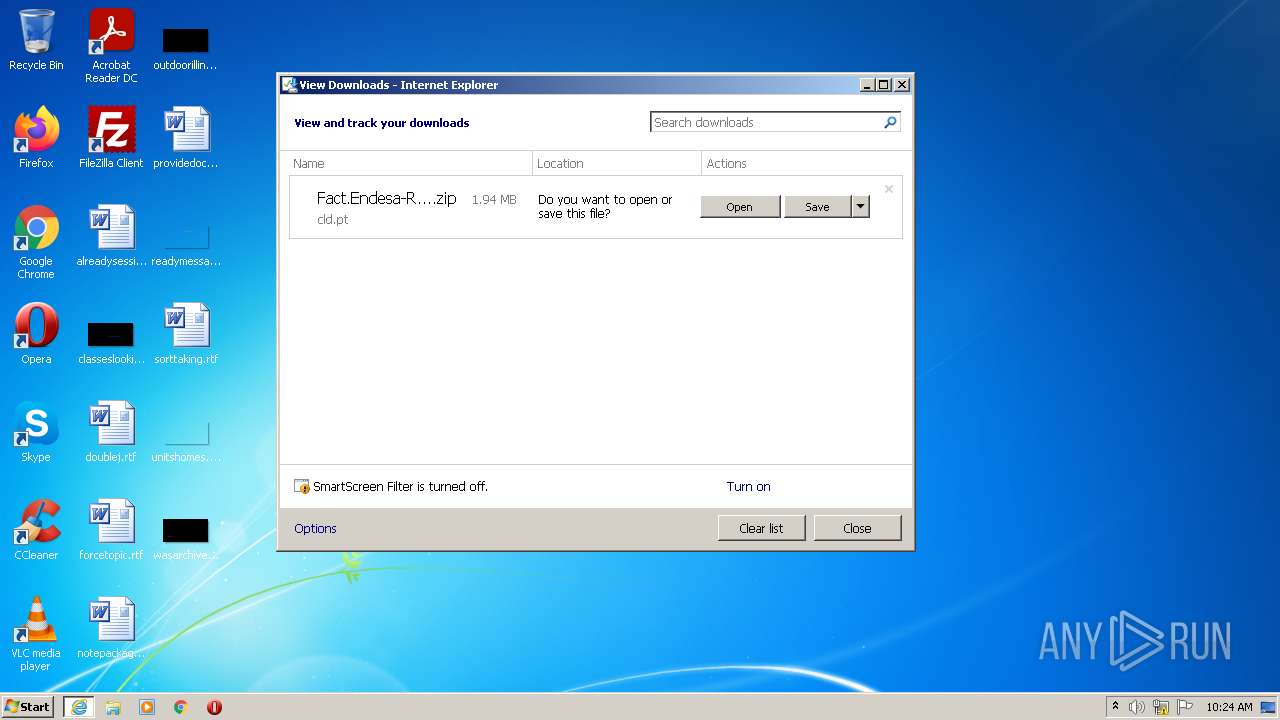
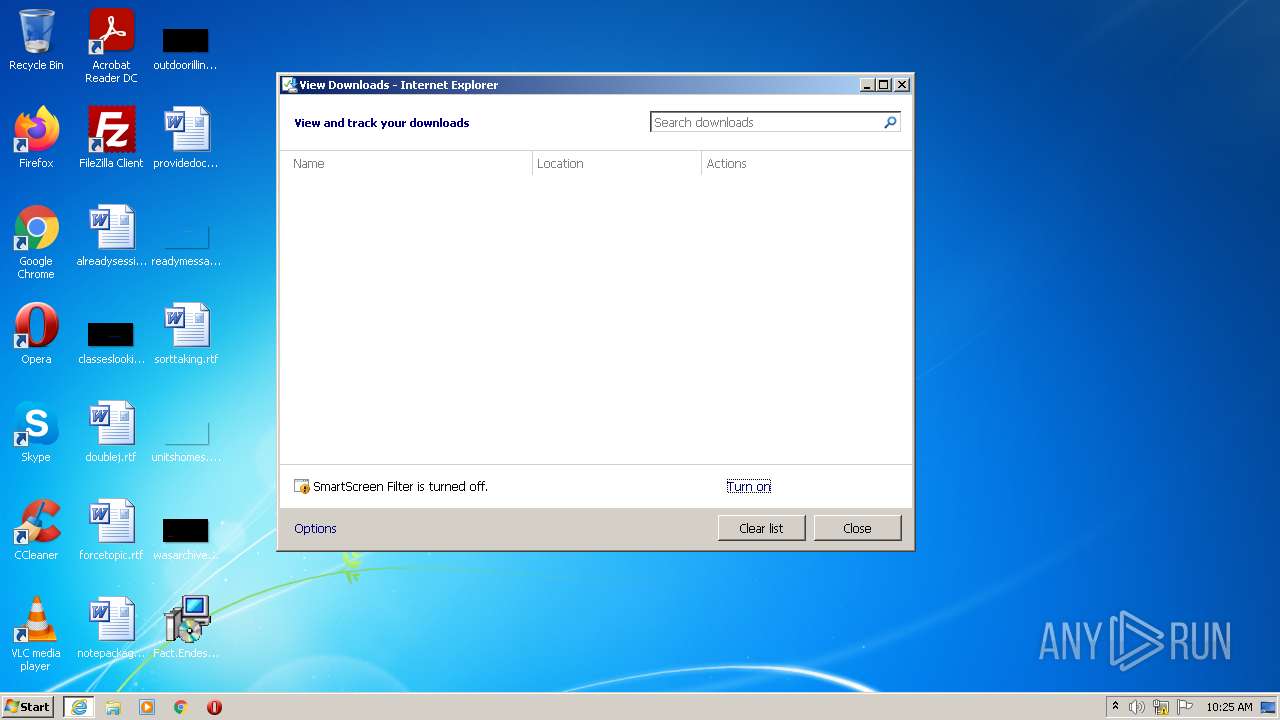
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cld.pt/dl/download/e30c7587-c1e1-4911-ab27-d6d061fa9074/Fact.Endesa-Ref-27-06-2022.zip" | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3436 | C:\Windows\system32\MsiExec.exe -Embedding D0BB0E29A0DE568EFC20917DE809CFF1 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
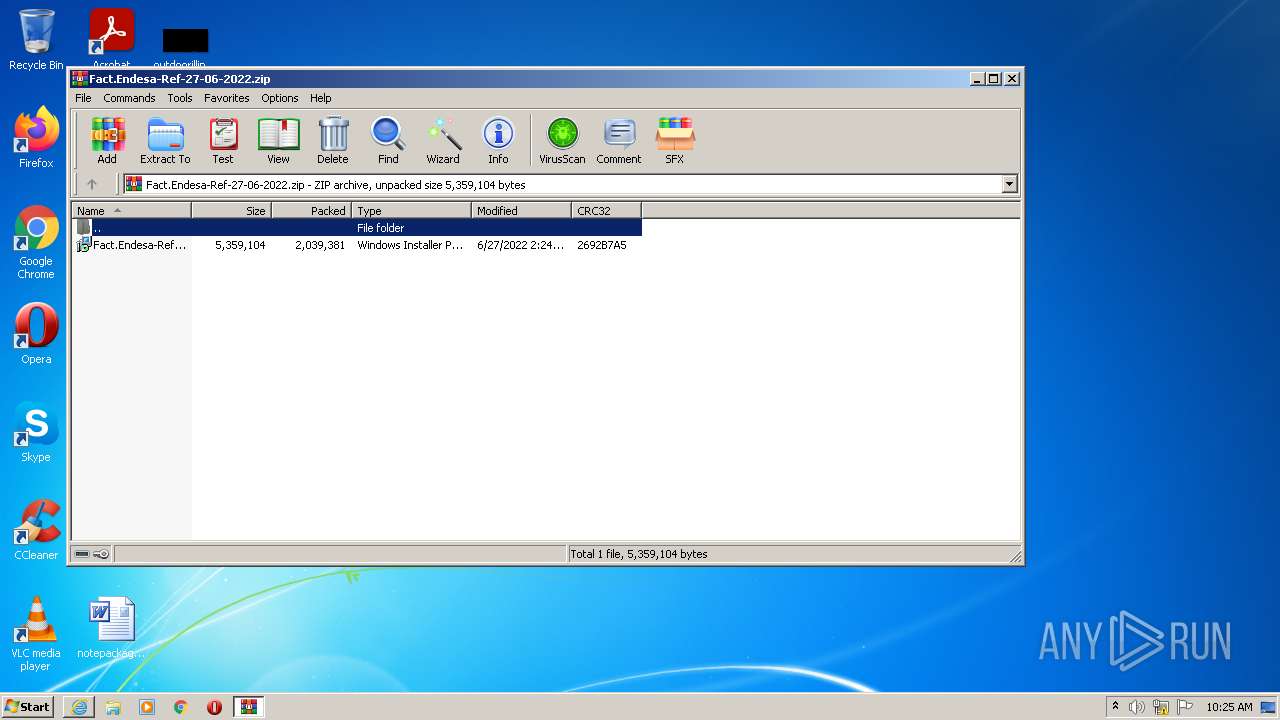
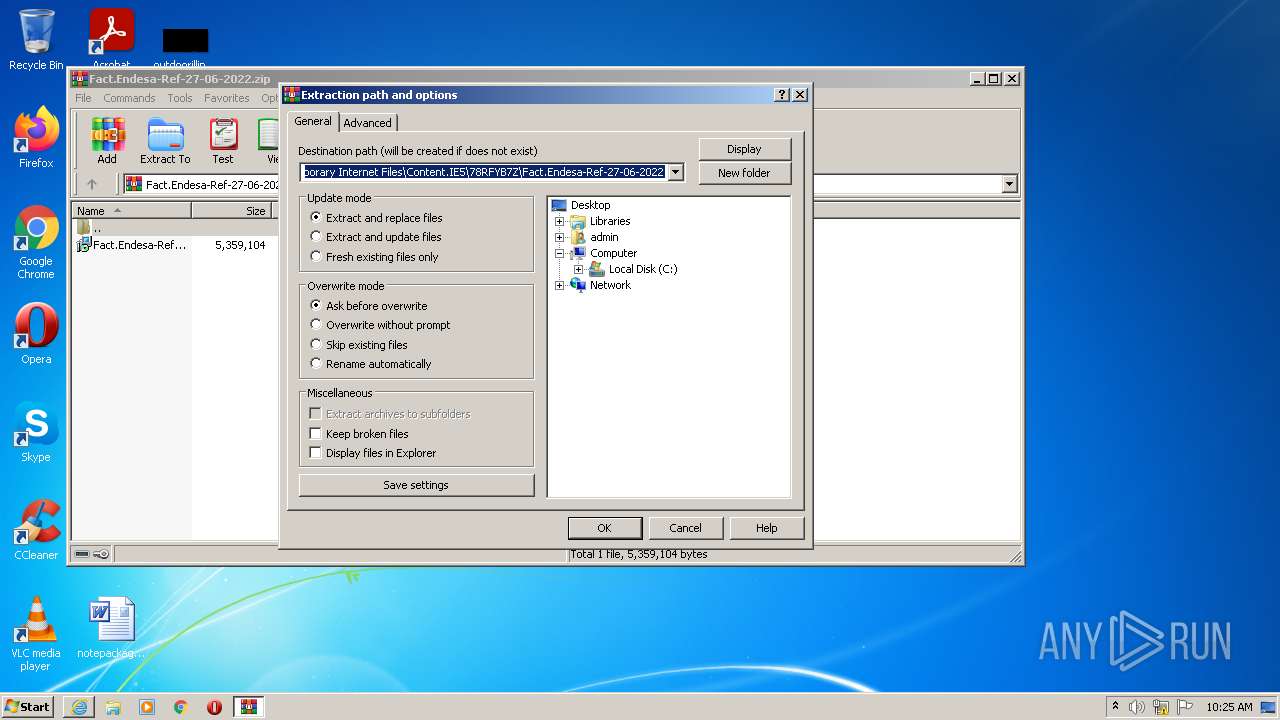
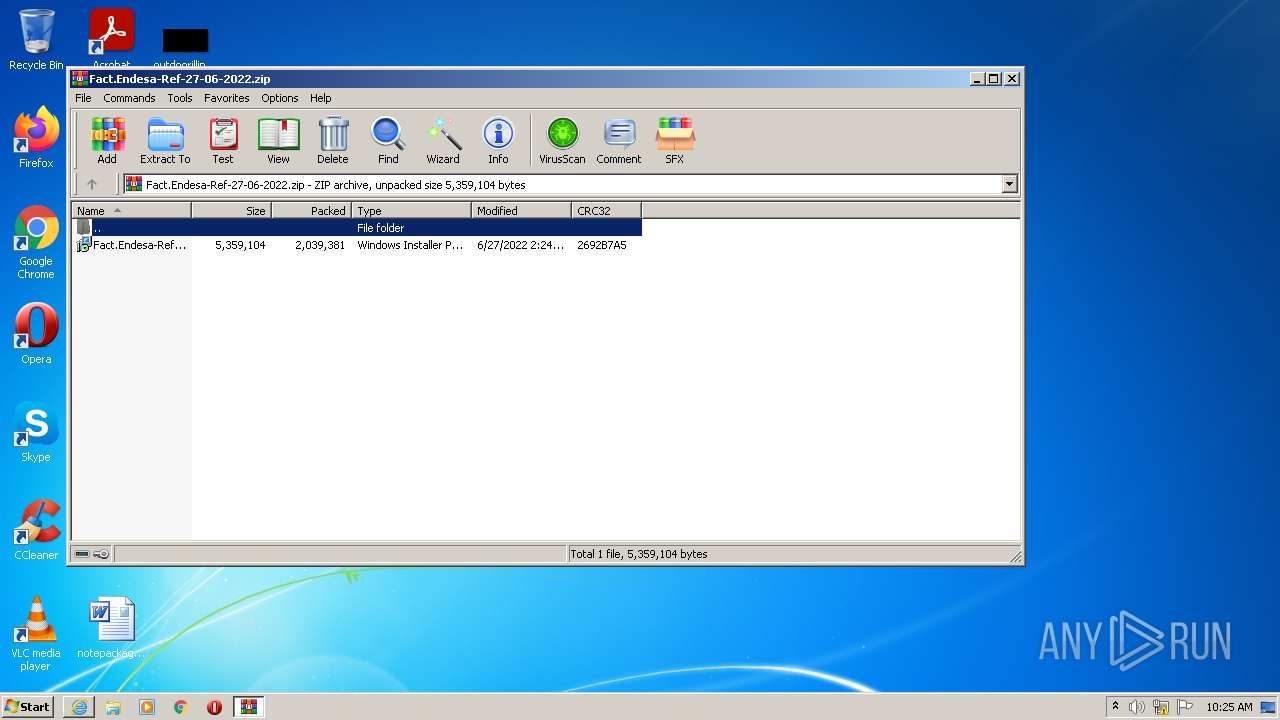
| 3696 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Fact.Endesa-Ref-27-06-2022.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4020 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2504 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 757
Read events
9 641
Write events
103
Delete events
13
Modification events
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30968327 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30968327 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
13
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | WinRAR.exe | C:\Users\admin\Desktop\Fact.Endesa-Ref-27-06-2022.MSI | — | |
MD5:— | SHA256:— | |||
| 1980 | msiexec.exe | C:\Windows\Installer\fd151.msi | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Fact.Endesa-Ref-27-06-2022[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_DA58D95BD38CF7D8DB4249810F70B0D9 | der | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_DA58D95BD38CF7D8DB4249810F70B0D9 | binary | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Fact.Endesa-Ref-27-06-2022.zip.lb9o67y.partial | compressed | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF436DEC430DFEE790.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA5q8Sc%2FJmSklHRWiYBeK%2FY%3D | US | der | 471 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f443ad68667e6b58 | US | compressed | 4.70 Kb | whitelisted |
4020 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?684e7b3ad5972330 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4020 | iexplore.exe | 213.13.26.152:443 | cld.pt | Servicos De Comunicacoes E Multimedia S.A. | PT | suspicious |
4020 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4020 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cld.pt |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Public Cloud Domain in DNS Lookup (cld .pt) |
— | — | Potentially Bad Traffic | ET INFO Public Cloud Domain in DNS Lookup (cld .pt) |
4020 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Public Cloud Domain (cld .pt in TLS SNI) |
4020 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Public Cloud Domain (cld .pt in TLS SNI) |