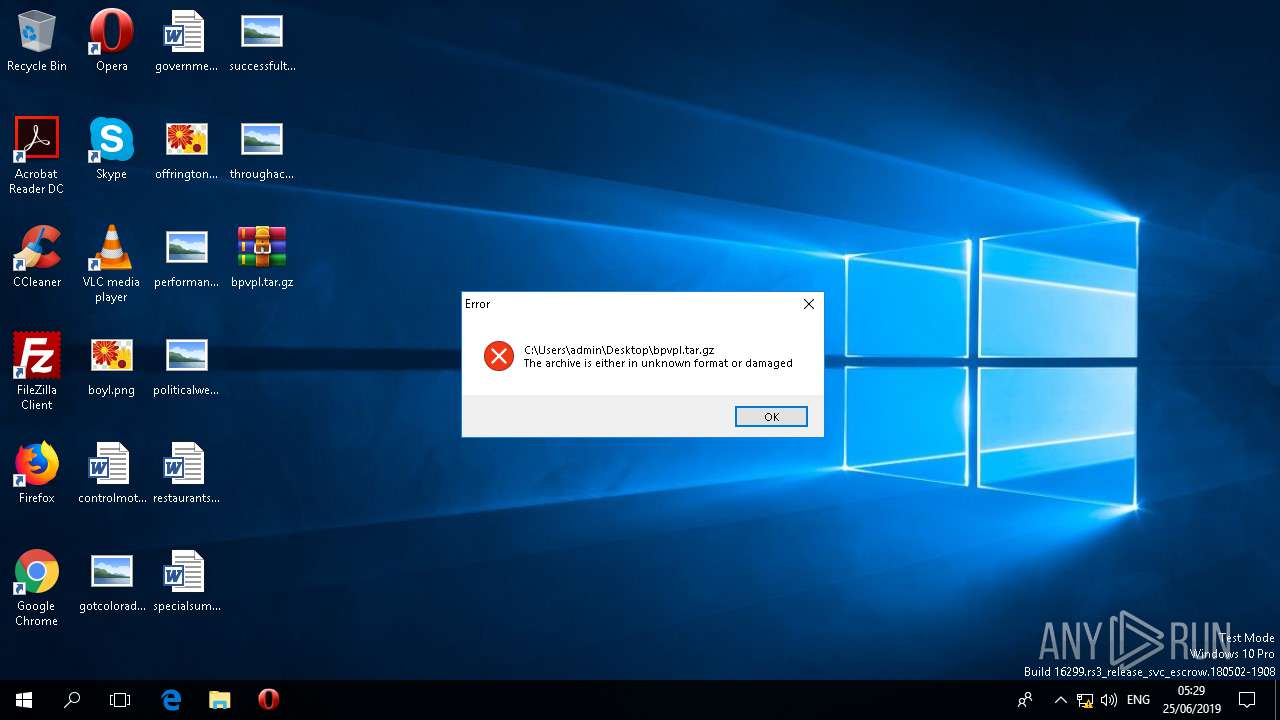
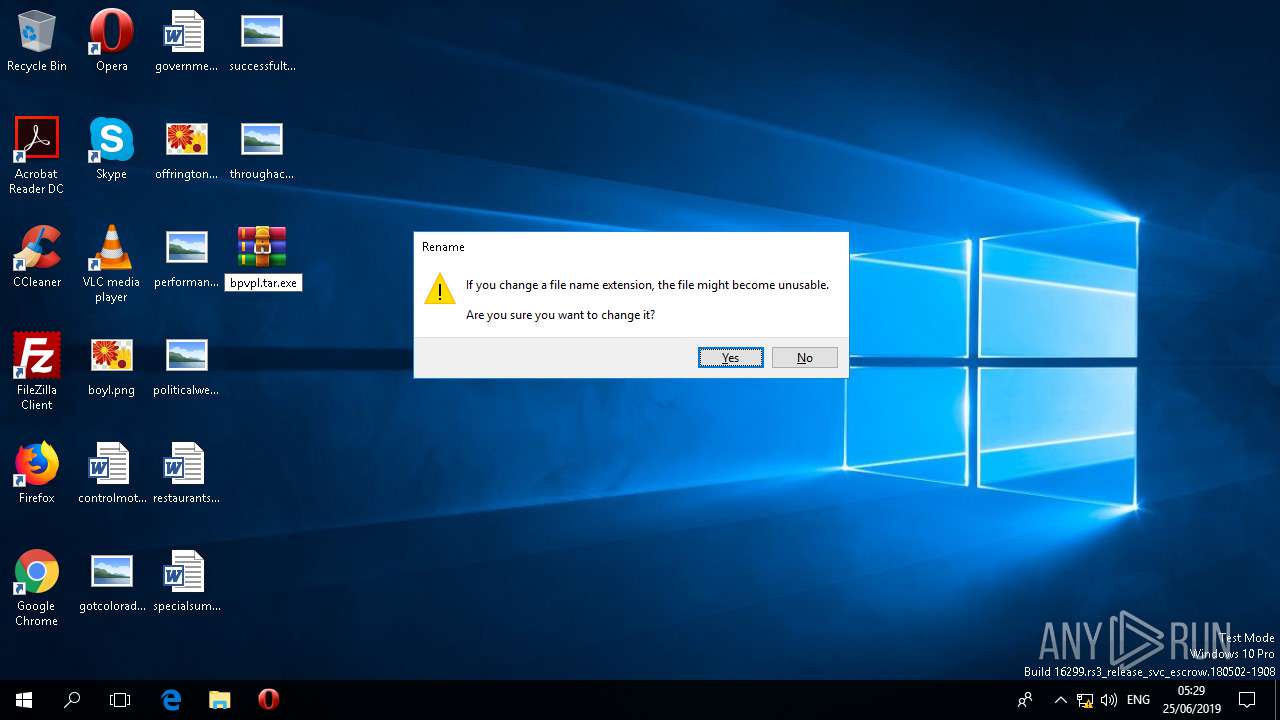
| File name: | bpvpl.tar.gz |
| Full analysis: | https://app.any.run/tasks/80aed1de-6cb6-4955-b466-b8e7ad6bc115 |
| Verdict: | Suspicious activity |
| Analysis date: | June 25, 2019, 04:28:38 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5A2B62B657782F37EB0F7C27064CFFA9 |
| SHA1: | 8B1C131F6B9DC1F020A18AB8F4FA3095224ADCC9 |
| SHA256: | 27BD6DB946DD85DE546F6FB9B80658E46ECD327136773C949CD212DDFD52AA4E |
| SSDEEP: | 12288:zpYxqKVa+P7lX2CgHsMaXE6AEAeapS6drlx/1Ea5AAPhsoeNkM3Z4GPtHB57kXMz:z7/HgEfZXuCEVm969VC |
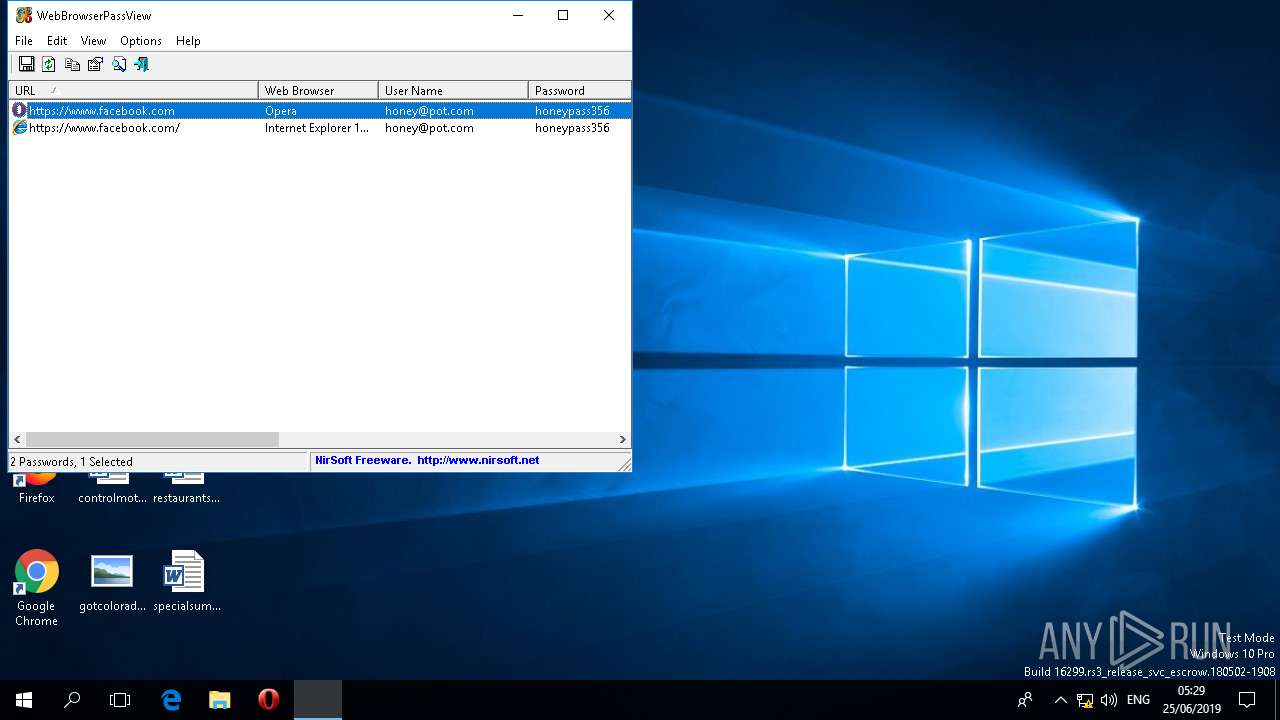
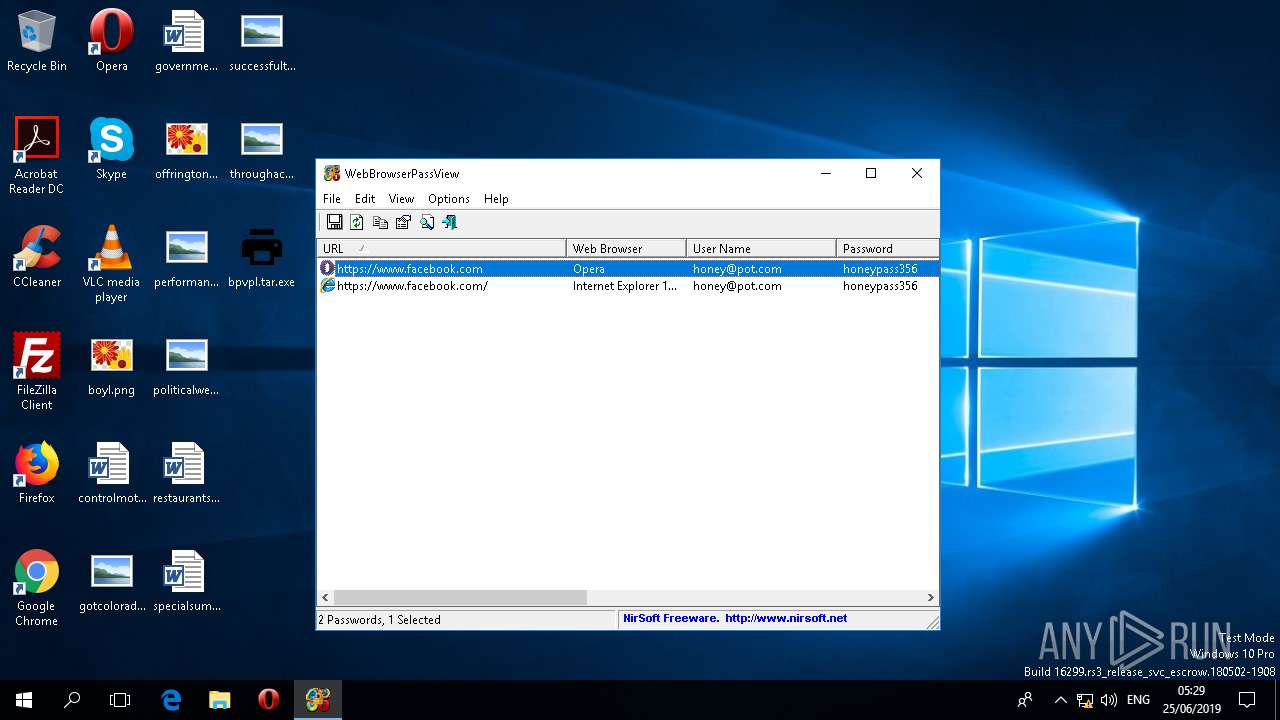
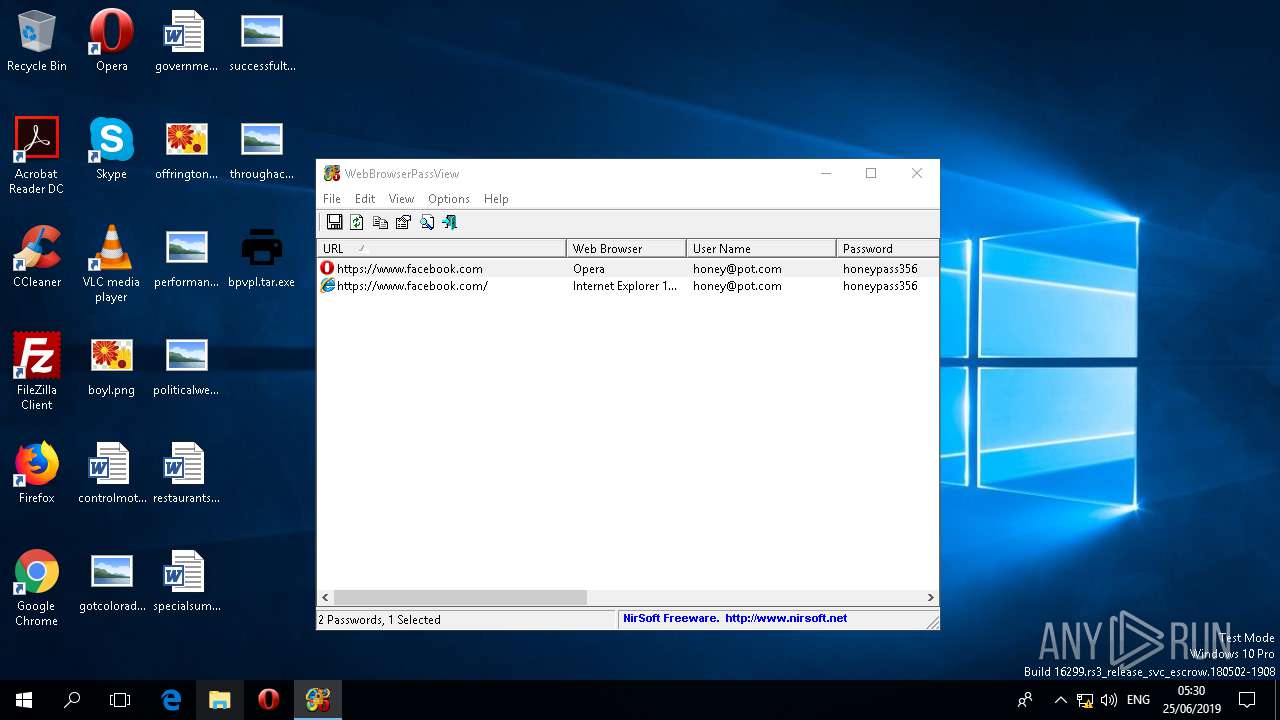
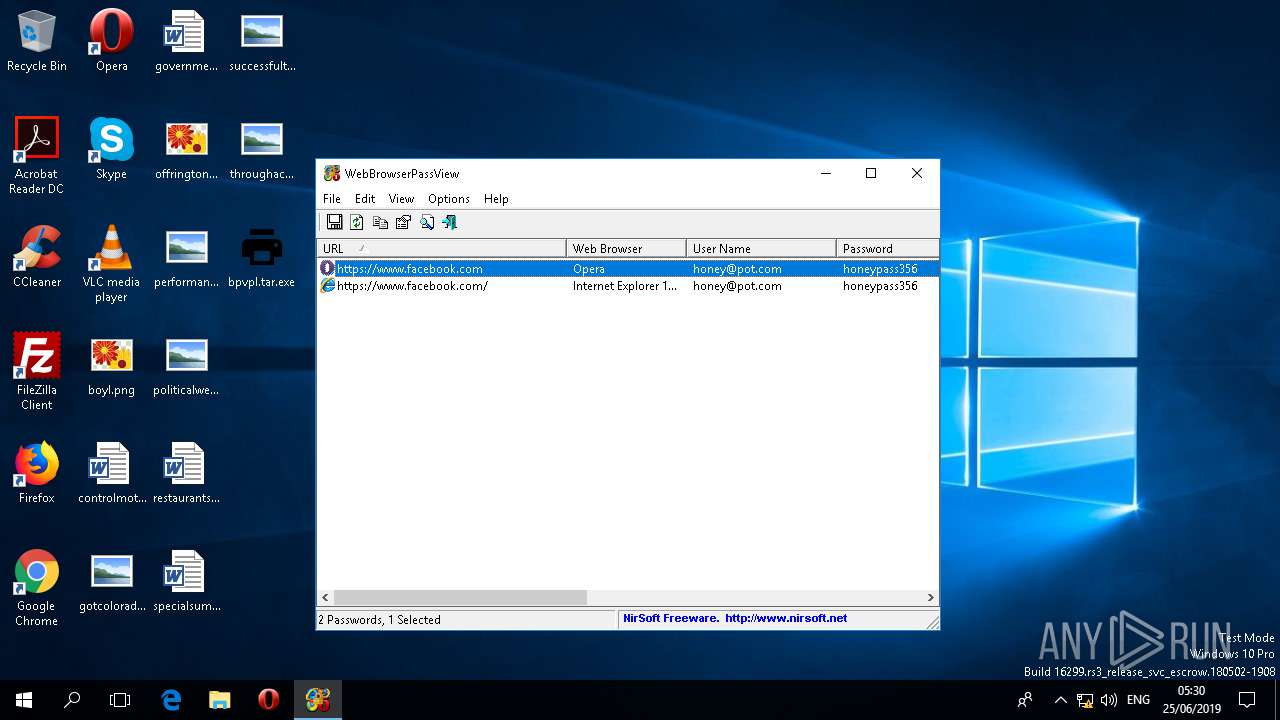
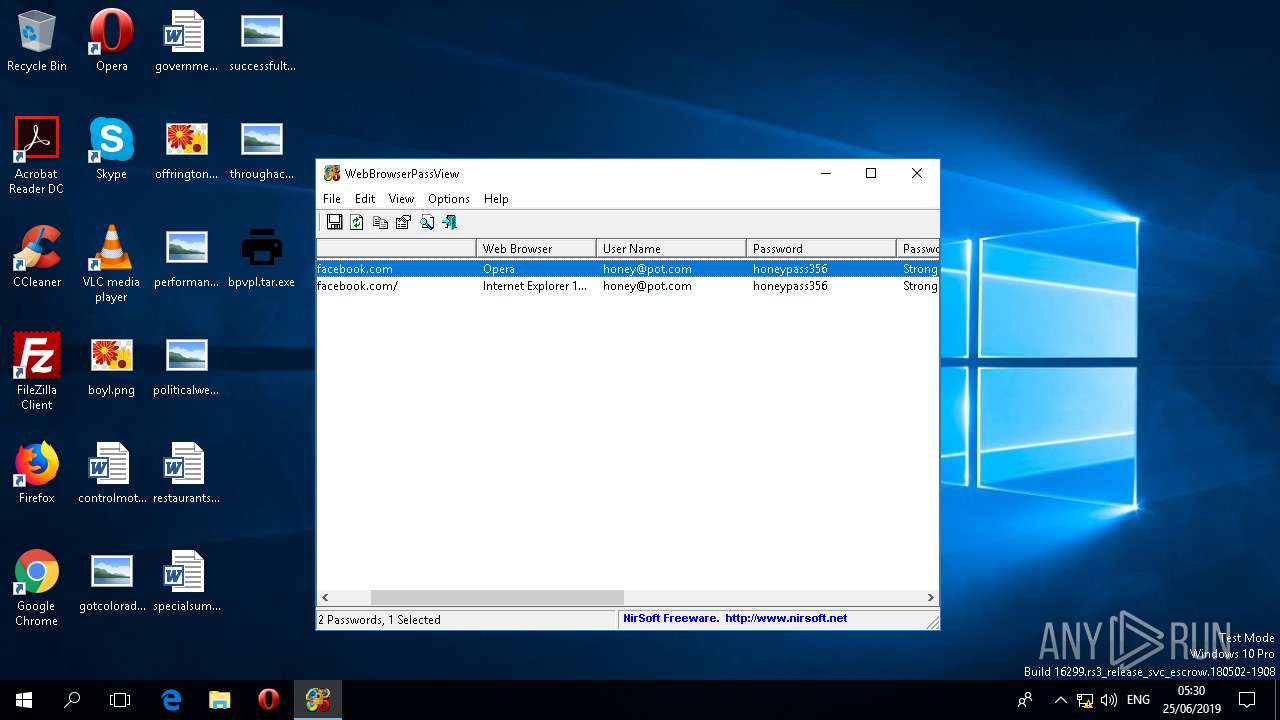
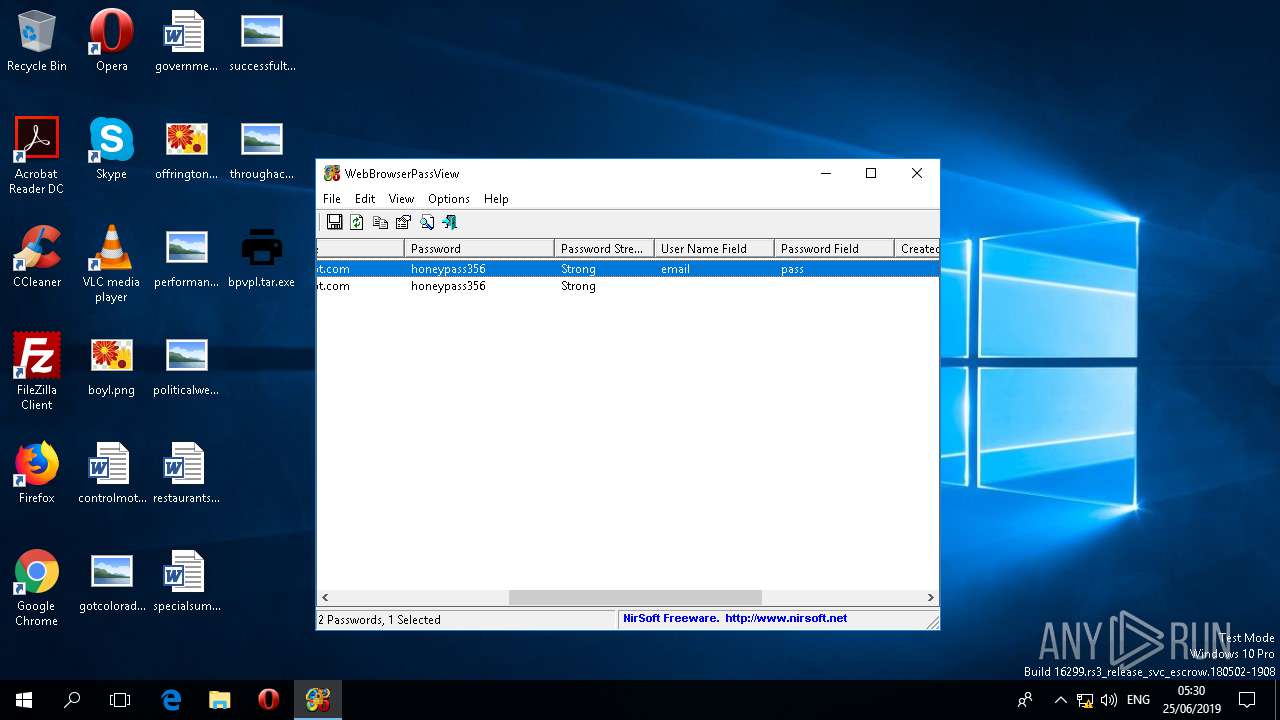
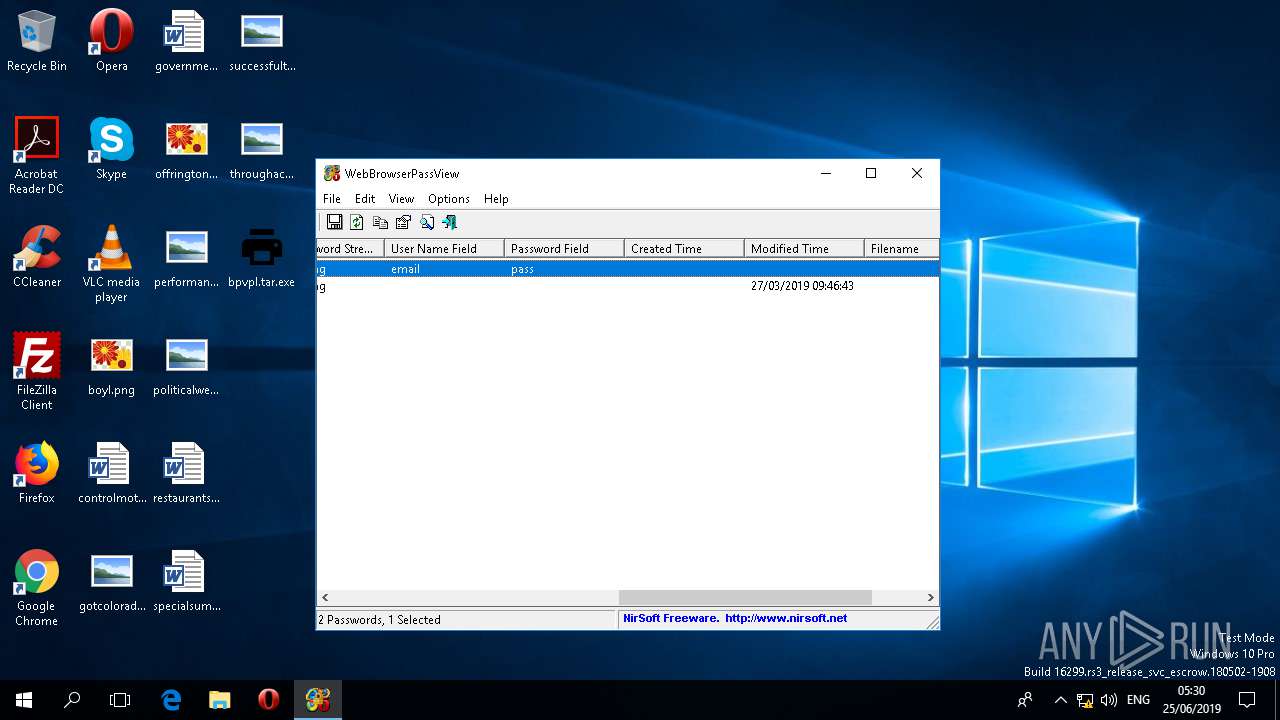
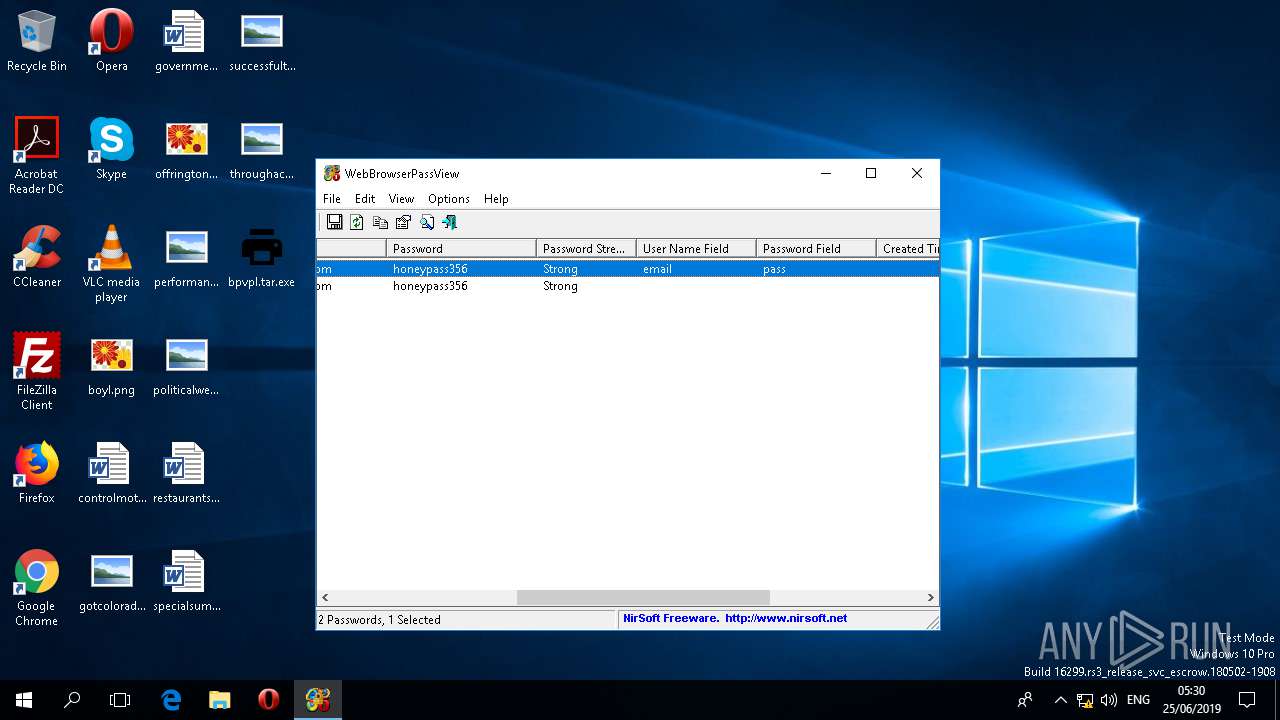
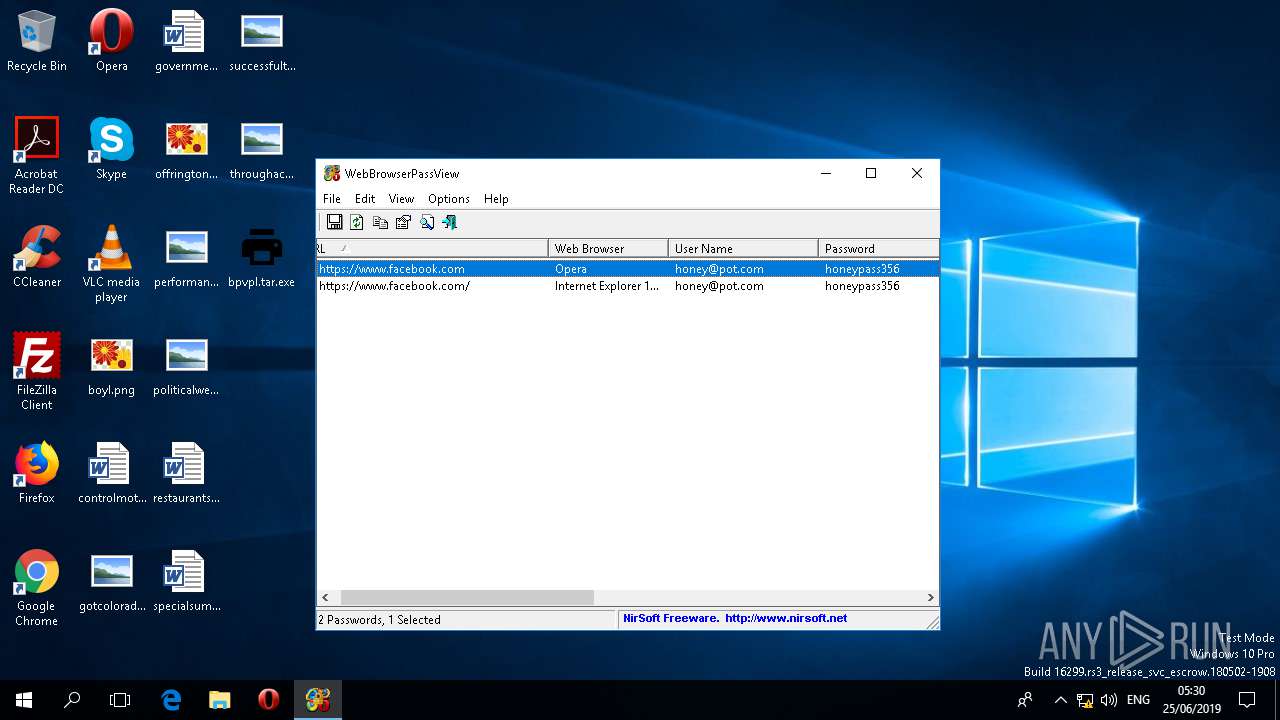
MALICIOUS
Actions looks like stealing of personal data
- bpvpl.tar.exe (PID: 5748)
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 3692)
SUSPICIOUS
Reads the machine GUID from the registry
- WinRAR.exe (PID: 3972)
- bpvpl.tar.exe (PID: 3644)
Application launched itself
- bpvpl.tar.exe (PID: 3644)
Reads Environment values
- WINWORD.EXE (PID: 3692)
INFO
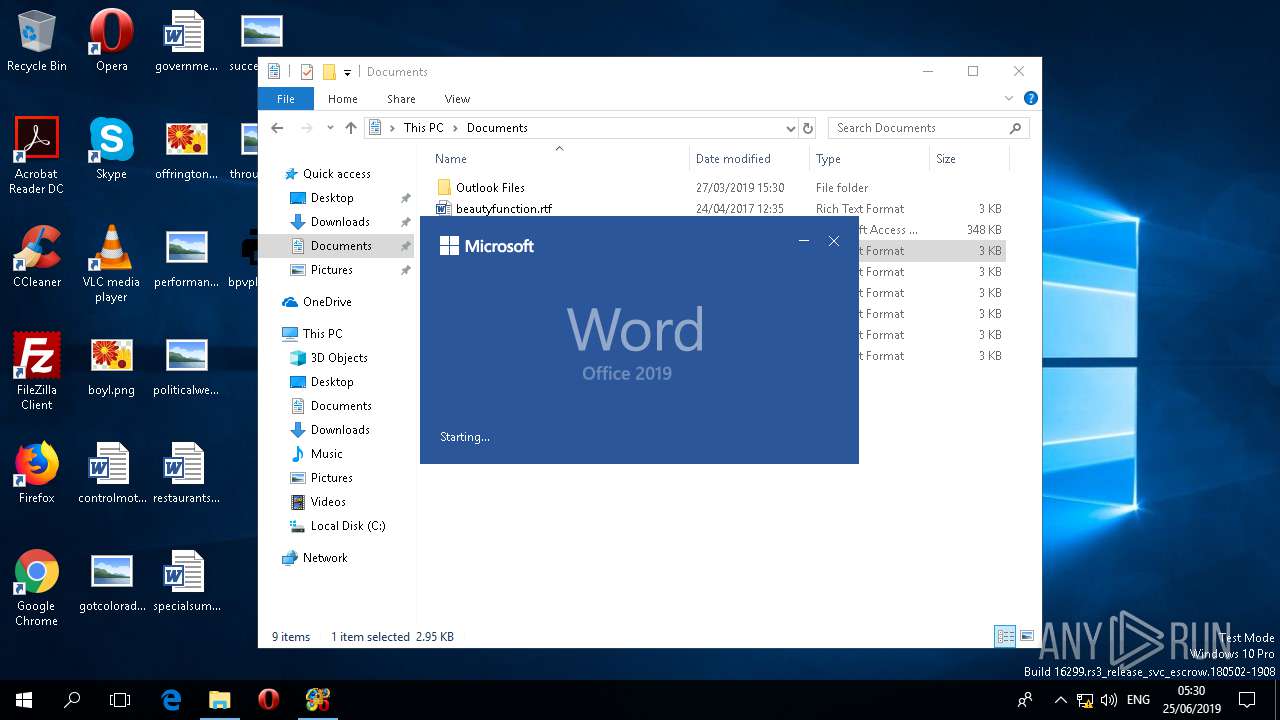
Manual execution by user
- WINWORD.EXE (PID: 3692)
- bpvpl.tar.exe (PID: 3644)
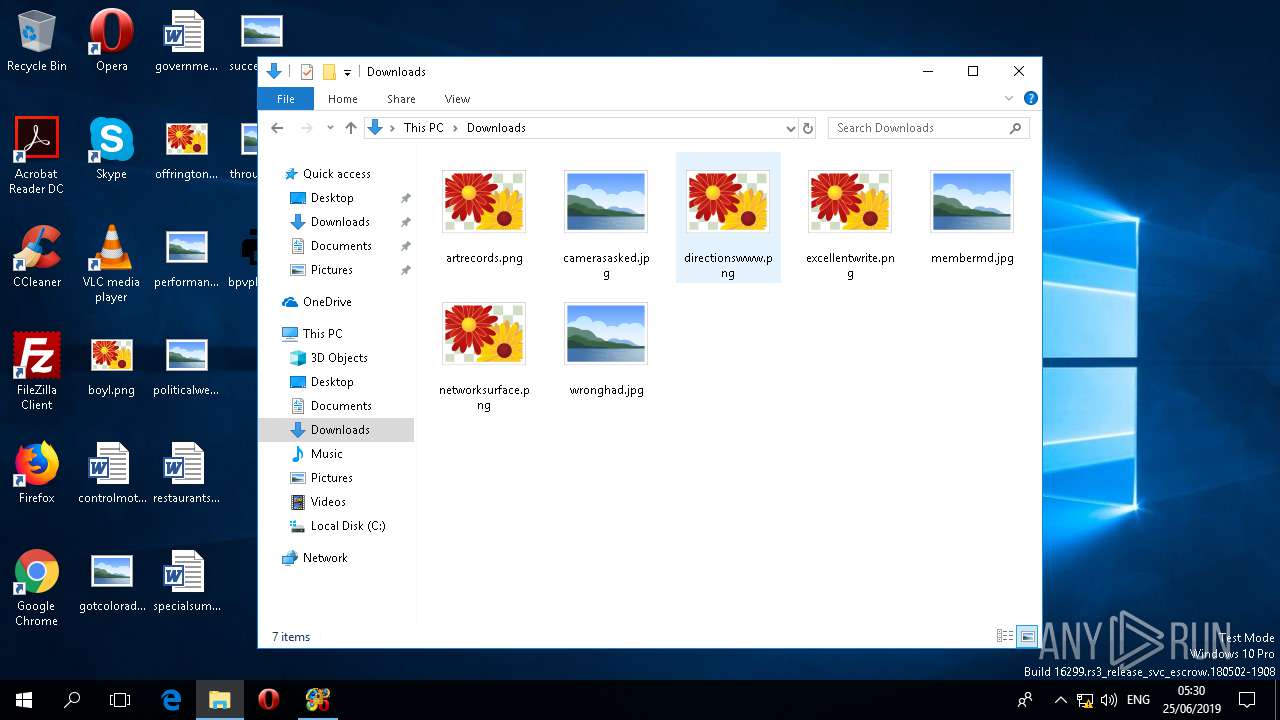
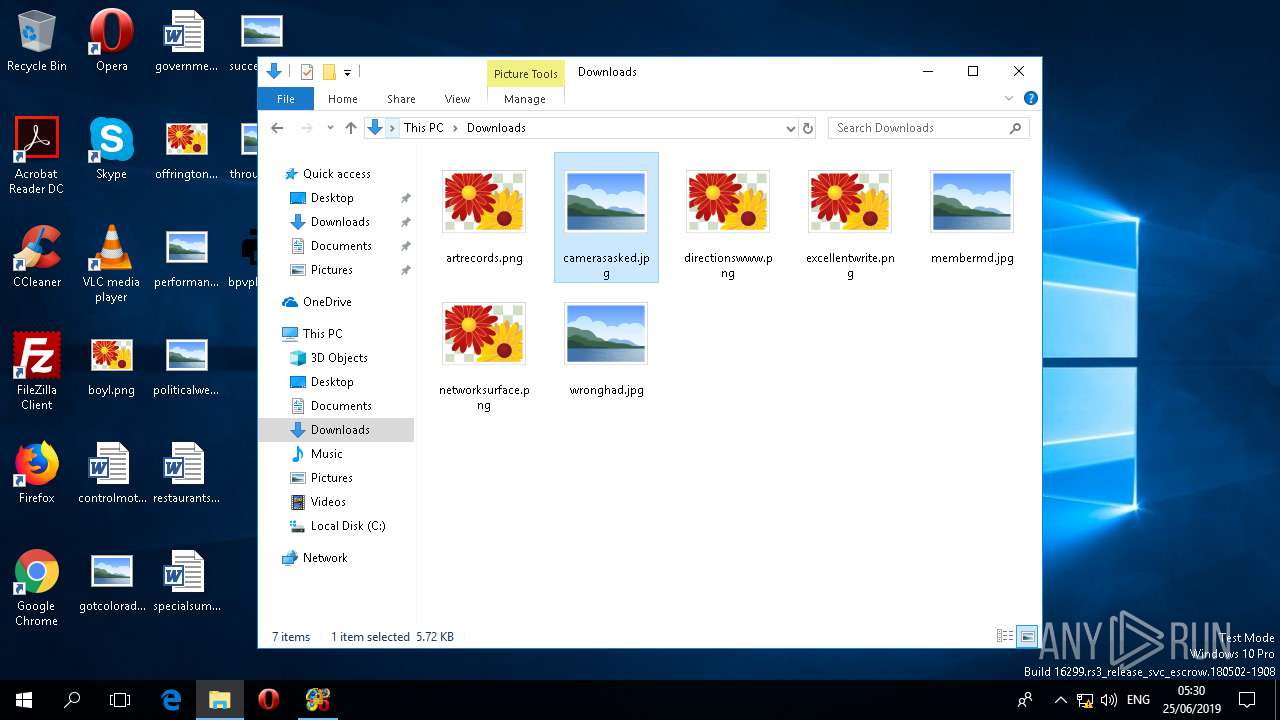
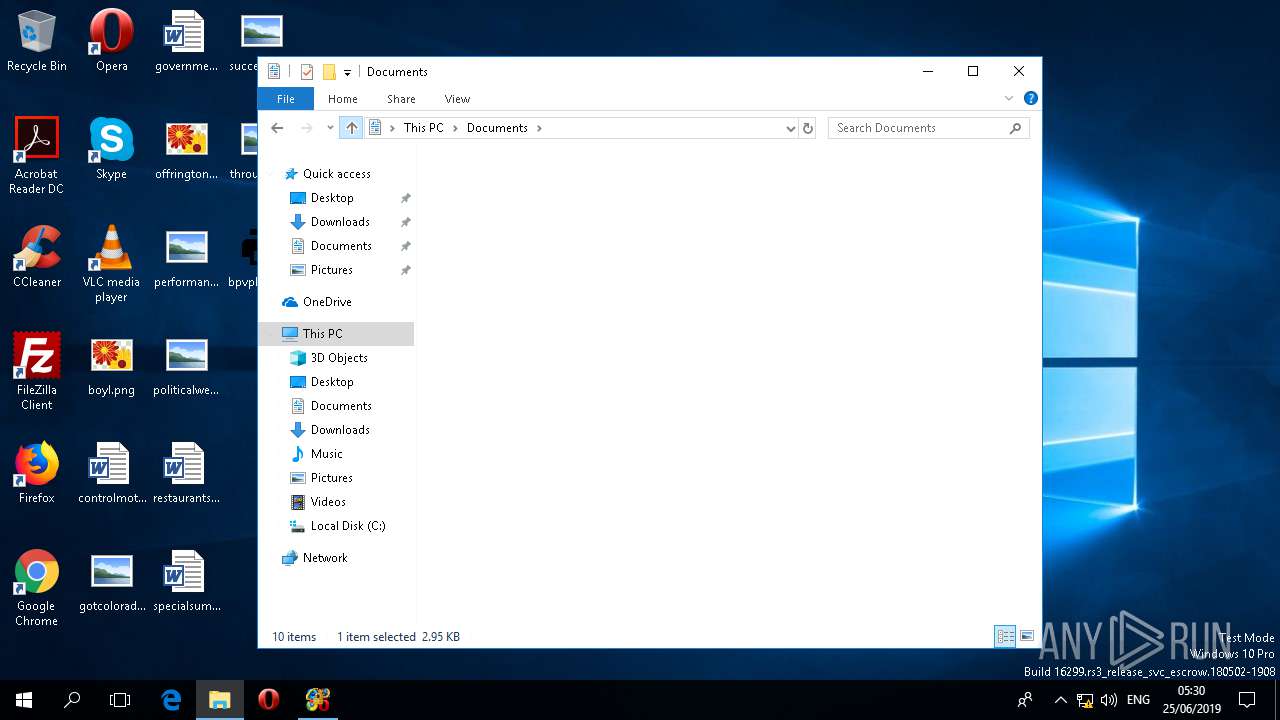
Creates files in the user directory
- WINWORD.EXE (PID: 3692)
Reads the software policy settings
- WINWORD.EXE (PID: 3692)
Reads settings of System Certificates
- WINWORD.EXE (PID: 3692)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 3692)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:08 12:36:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1054208 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10352e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.3.3.4 |
| ProductVersionNumber: | 8.3.3.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | WSH Plugin |
| CompanyName: | WSH Inc |
| FileDescription: | bpvpl |
| FileVersion: | 8.3.3.4 |
| InternalName: | Doctorpol.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFileName: | Doctorpol.exe |
| ProductName: | bpvpl |
| ProductVersion: | 8.3.3.4 |
| AssemblyVersion: | 8.3.3.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-May-2019 10:36:03 |
| Debug artifacts: |
|
| Comments: | WSH Plugin |
| CompanyName: | WSH Inc |
| FileDescription: | bpvpl |
| FileVersion: | 8.3.3.4 |
| InternalName: | Doctorpol.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFilename: | Doctorpol.exe |
| ProductName: | bpvpl |
| ProductVersion: | 8.3.3.4 |
| Assembly Version: | 8.3.3.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-May-2019 10:36:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00101534 | 0x00101600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.19151 |
.sdata | 0x00104000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.02607 |
.rsrc | 0x00106000 | 0x000190C0 | 0x00019200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.930343 |
.reloc | 0x00120000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.89261 | 1092 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 0.631414 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 0.697419 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 0.819653 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 0.826137 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 1.039 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.81879 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
92
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3644 | "C:\Users\admin\Desktop\bpvpl.tar.exe" | C:\Users\admin\Desktop\bpvpl.tar.exe | — | explorer.exe | |||||||||||
User: admin Company: WSH Inc Integrity Level: MEDIUM Description: bpvpl Exit code: 0 Version: 8.3.3.4 Modules
| |||||||||||||||
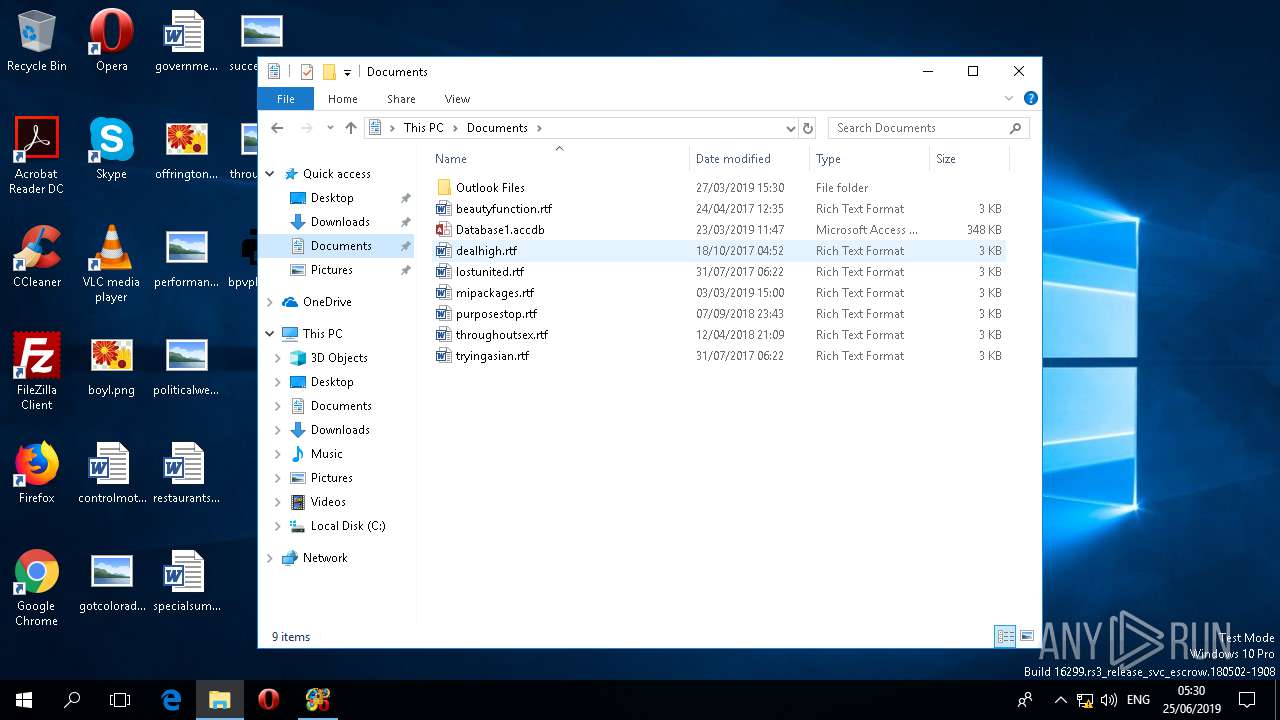
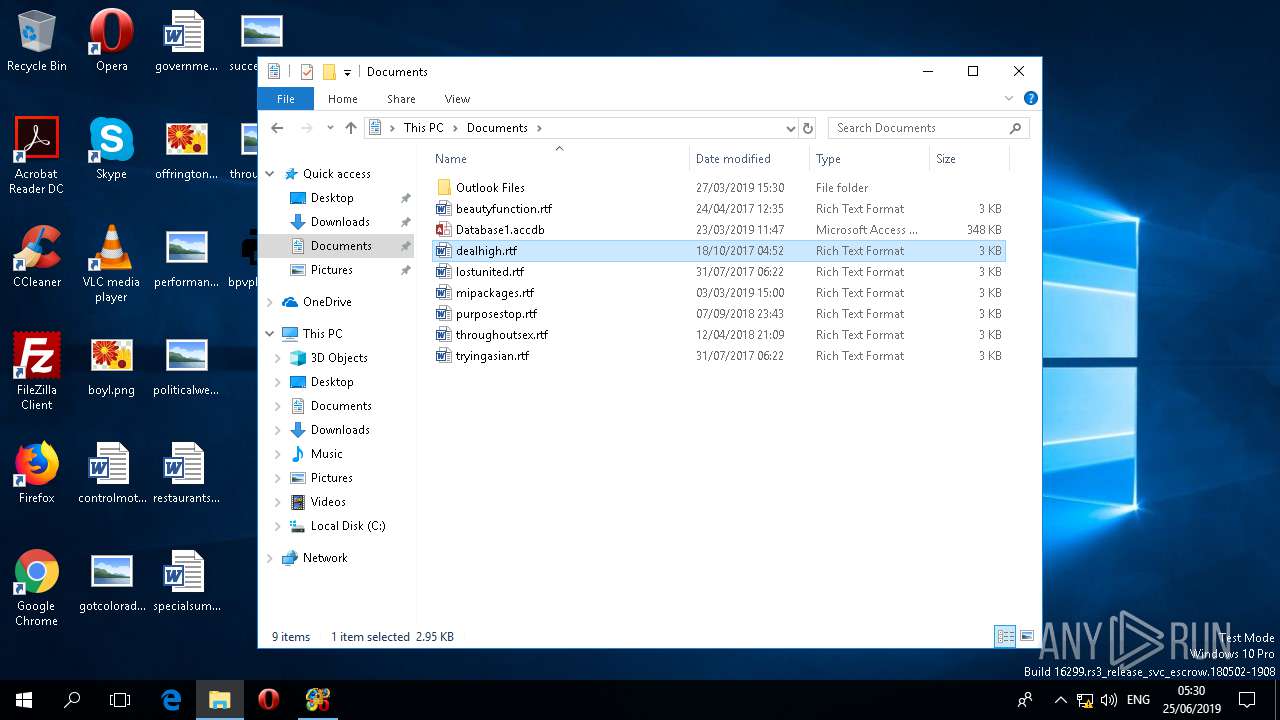
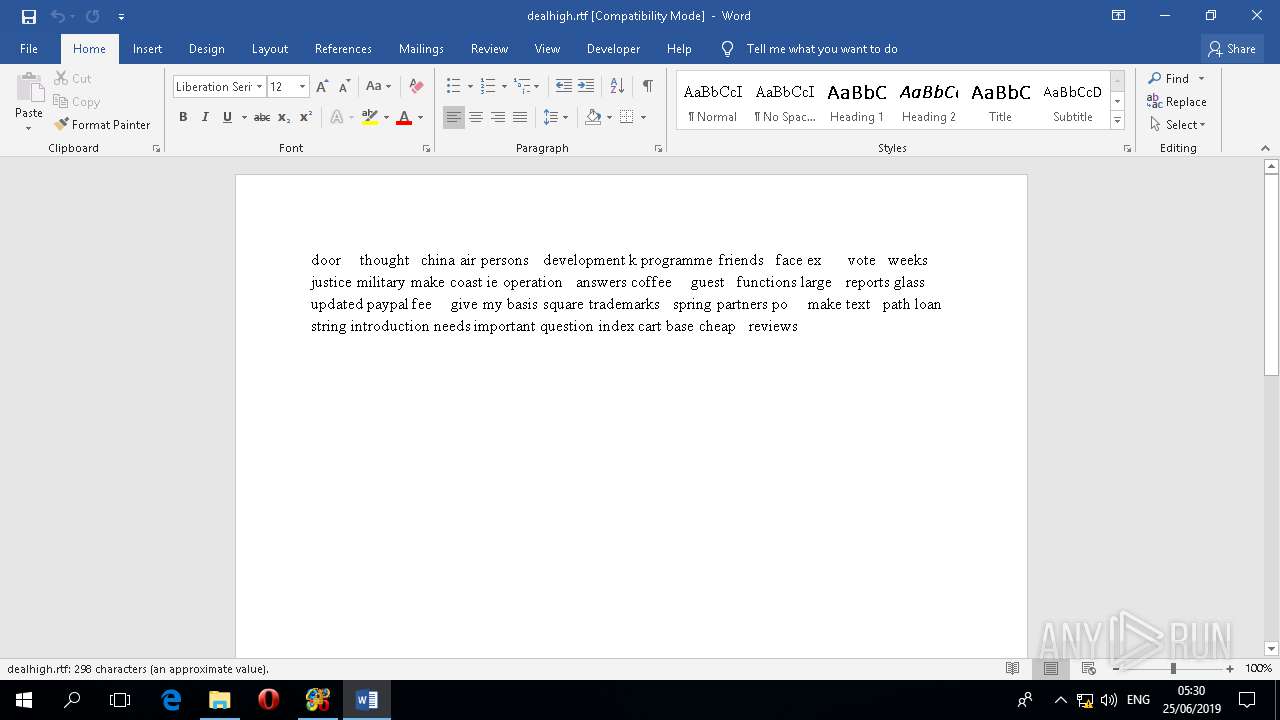
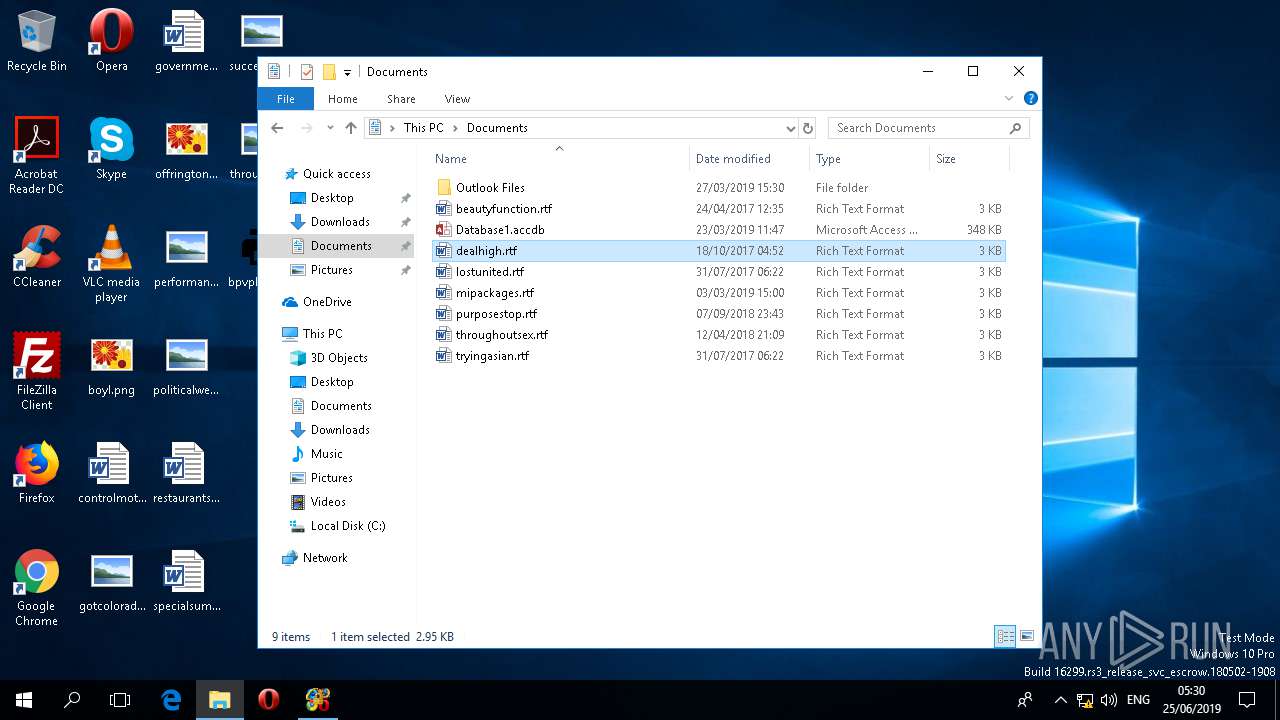
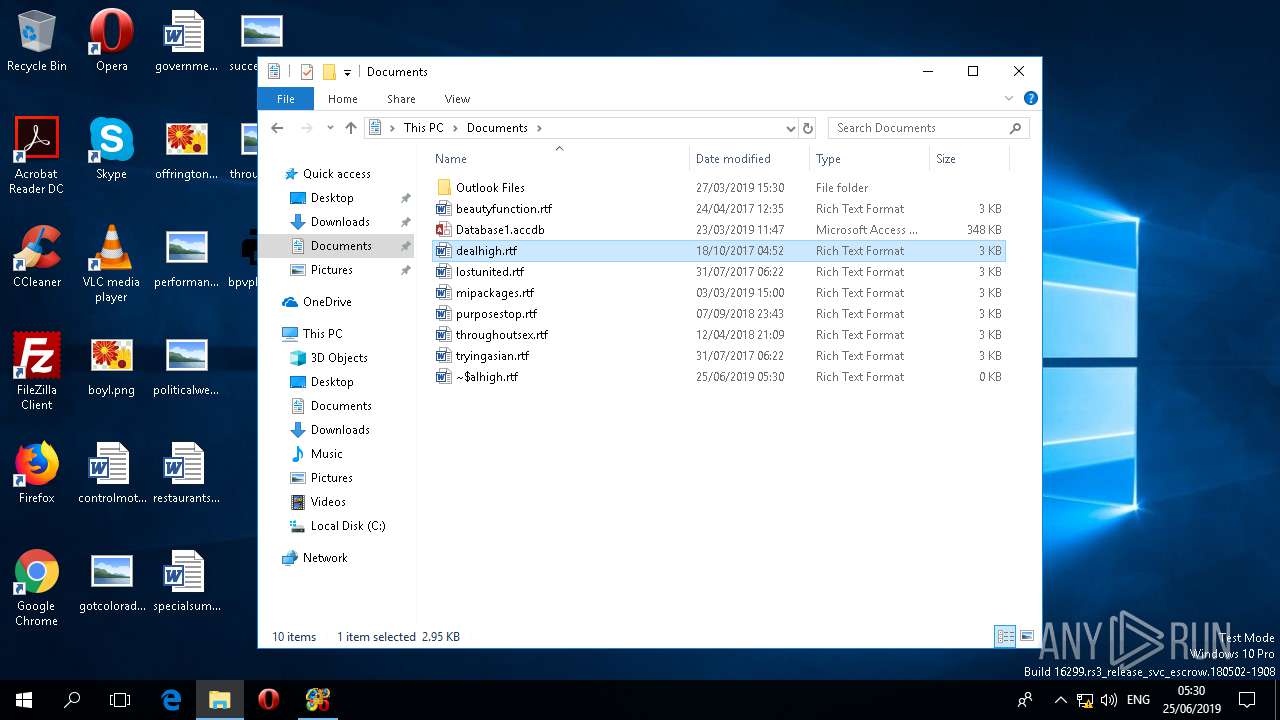
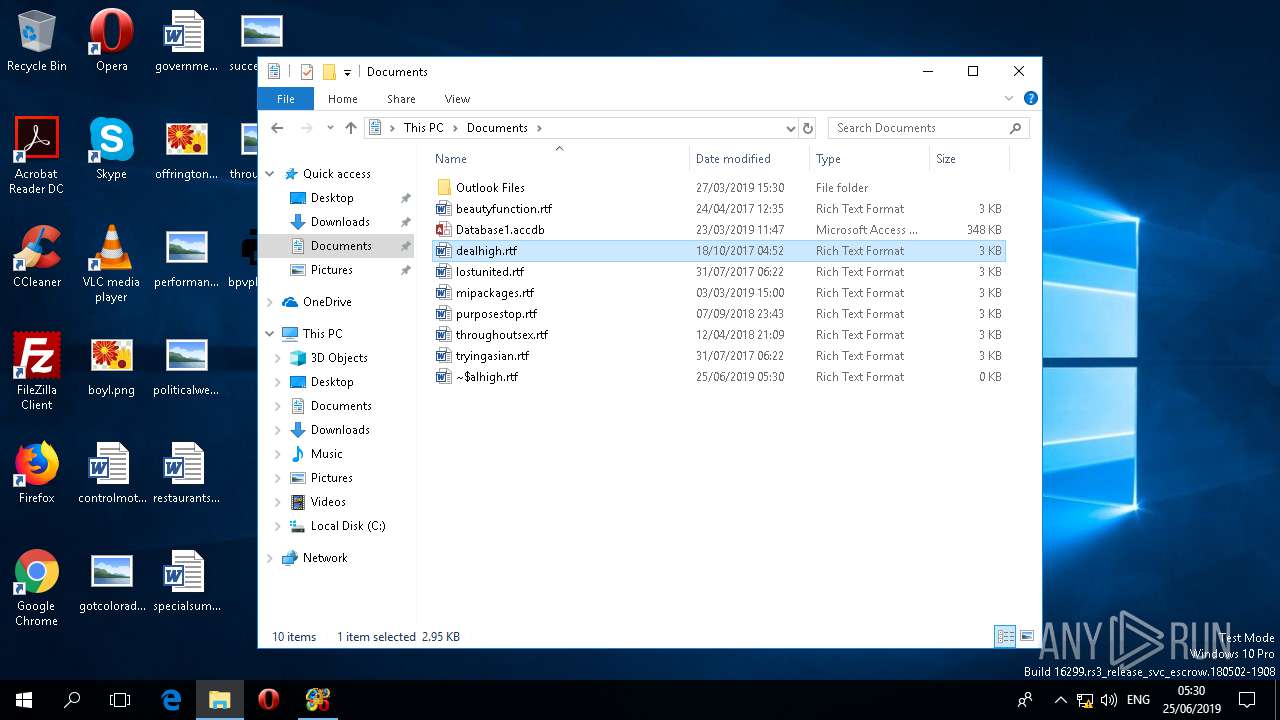
| 3692 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Documents\dealhigh.rtf" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.11328.20158 Modules
| |||||||||||||||
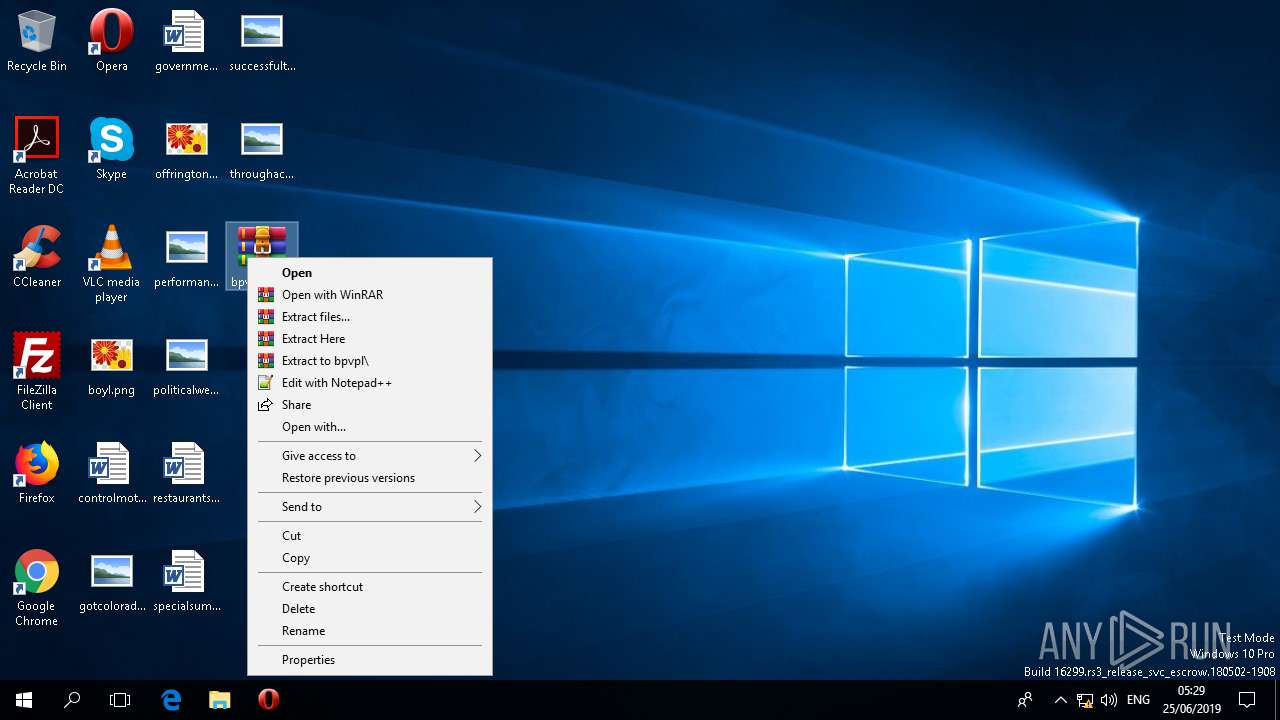
| 3972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\bpvpl.tar.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
| 5748 | C:\Users\admin\Desktop\bpvpl.tar.exe | C:\Users\admin\Desktop\bpvpl.tar.exe | bpvpl.tar.exe | ||||||||||||
User: admin Company: WSH Inc Integrity Level: MEDIUM Description: bpvpl Exit code: 0 Version: 8.3.3.4 Modules
| |||||||||||||||
Total events
1 529
Read events
1 399
Write events
107
Delete events
23
Modification events
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\22\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000003802100000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F00000000000000000000000000000000000000000007E000A000000000000000000180000002A00000000000000000000000000000002000000 | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5748 | bpvpl.tar.exe | C:\Users\admin\AppData\Local\Temp\bhvD4A5.tmp | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{7CF346E8-4A25-419D-9F46-19651C279713}.tmp | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{5FE5945F-A48A-4CB7-BE2A-1A87B70DC84A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db-shm | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db-wal | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3644 | bpvpl.tar.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v2.0_32\UsageLogs\bpvpl.tar.exe.log | text | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\dealhigh.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\winword.exe.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3692 | WINWORD.EXE | GET | 200 | 13.107.3.128:443 | https://config.edge.skype.com/config/v1/Office/16.0.11328.20158?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=word&Platform=win32&Version=16.0.11328.20158&MsoVersion=16.0.11328.20156&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&Channel=CC&InstallType=C2R&SessionId=%7bDE4A3DC1-9453-4F18-AAD7-A4058F074CDD%7d&LabMachine=false | US | text | 61.8 Kb | malicious |
3692 | WINWORD.EXE | POST | 200 | 52.114.76.34:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | IE | text | 10 b | whitelisted |
3692 | WINWORD.EXE | POST | 200 | 52.114.76.34:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | IE | text | 9 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3692 | WINWORD.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3692 | WINWORD.EXE | 52.114.76.34:443 | self.events.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | 2019-06-25 04:30:25.285 T#1680 <E> [AriaSDK.PAL] PAL is already shutdown!
|