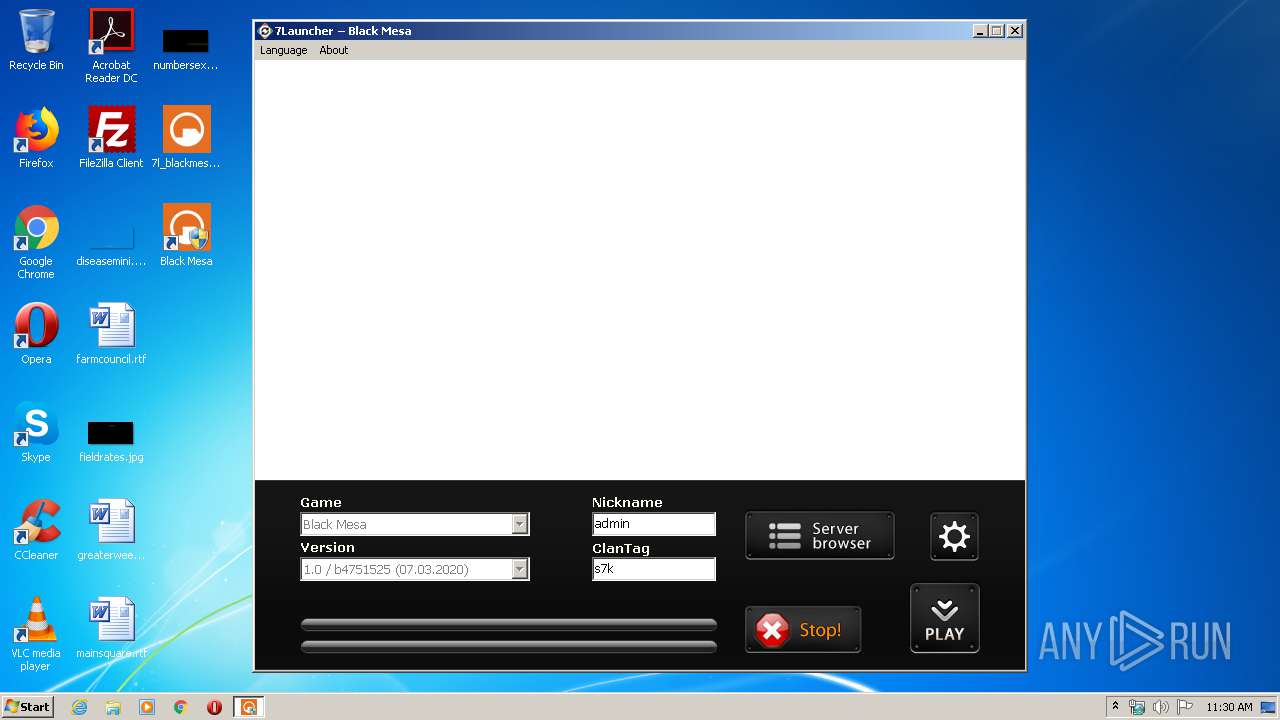
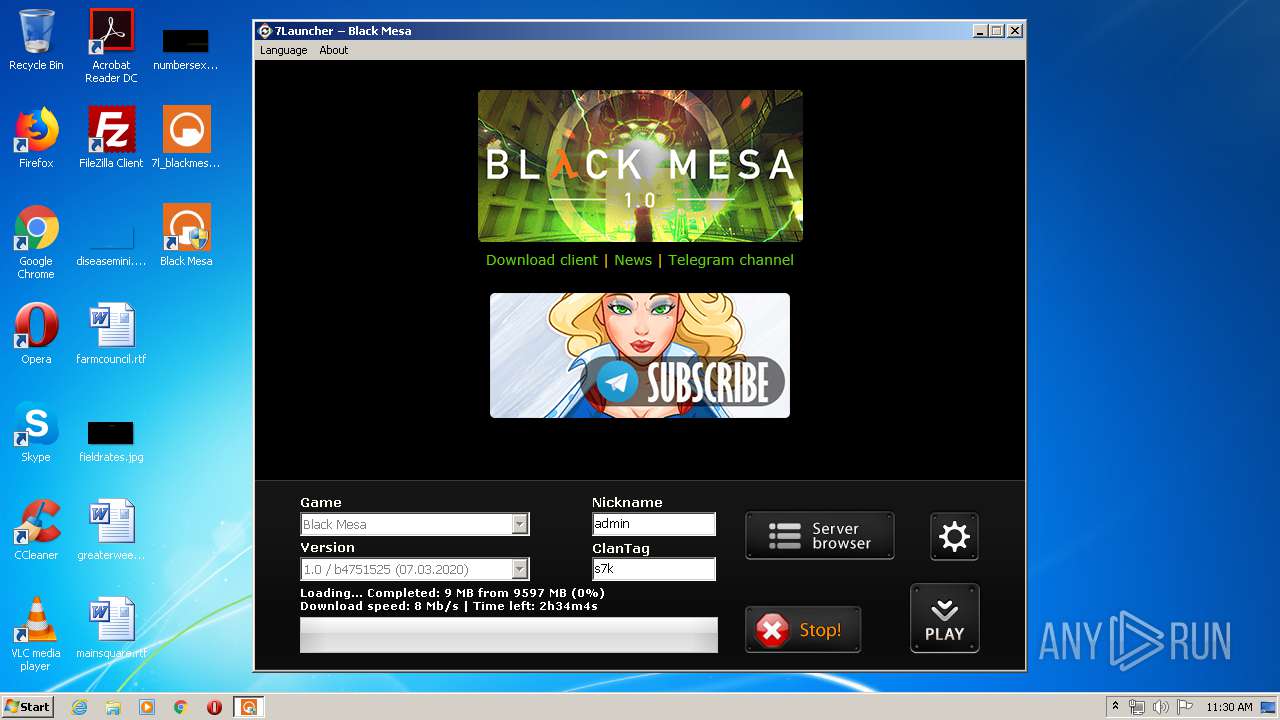
| File name: | 7l_blackmesa_setup.exe |
| Full analysis: | https://app.any.run/tasks/5087f1f6-36b1-49d7-b04b-bb76c3b04277 |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2020, 11:29:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9F62B8FBB942583C1448F96869C5486F |
| SHA1: | CCE4BF87ED89721C81ED748F449973A08225F7B3 |
| SHA256: | 279956C3866691EBB84E929DAD4B67181C490F1EAA366BEC5B915D600925F05B |
| SSDEEP: | 49152:CVR8ejzgoFu4nOdqMwD6HeE/O7xR8Iy0y4z:8s6nOdYEKRk0Pz |
MALICIOUS
Adds new firewall rule via NETSH.EXE
- 7l_blackmesa_setup.tmp (PID: 580)
Application was dropped or rewritten from another process
- Run_BMS.exe (PID: 3512)
- aria2c.exe (PID: 2380)
Changes settings of System certificates
- Run_BMS.exe (PID: 3512)
SUSPICIOUS
Executable content was dropped or overwritten
- 7l_blackmesa_setup.exe (PID: 3836)
- 7l_blackmesa_setup.exe (PID: 3040)
- 7l_blackmesa_setup.tmp (PID: 580)
- Run_BMS.exe (PID: 3512)
Reads Windows owner or organization settings
- 7l_blackmesa_setup.tmp (PID: 580)
Uses TASKKILL.EXE to kill process
- 7l_blackmesa_setup.tmp (PID: 580)
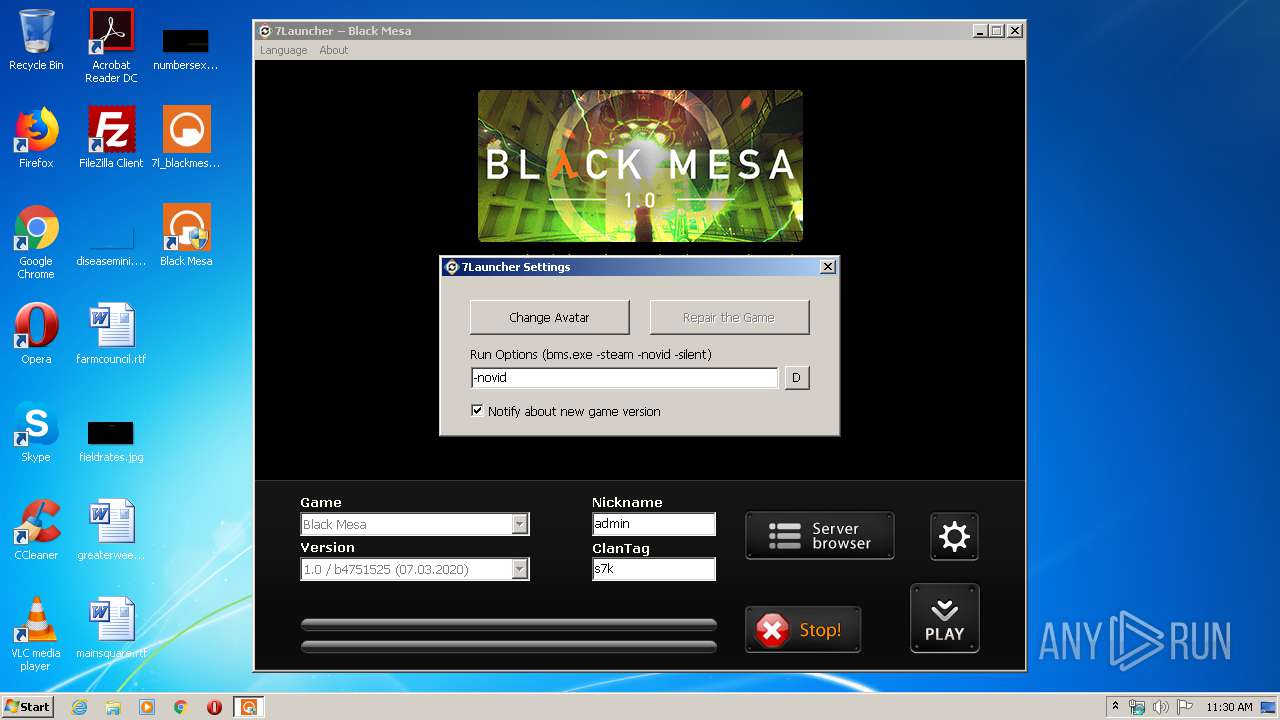
Changes IE settings (feature browser emulation)
- Run_BMS.exe (PID: 3512)
Reads Internet Cache Settings
- Run_BMS.exe (PID: 3512)
Uses NETSH.EXE for network configuration
- 7l_blackmesa_setup.tmp (PID: 580)
Reads the Windows organization settings
- 7l_blackmesa_setup.tmp (PID: 580)
Creates files in the user directory
- Run_BMS.exe (PID: 3512)
Creates files in the program directory
- Run_BMS.exe (PID: 3512)
- aria2c.exe (PID: 2380)
Modifies the open verb of a shell class
- Run_BMS.exe (PID: 3512)
Reads internet explorer settings
- Run_BMS.exe (PID: 3512)
Adds / modifies Windows certificates
- Run_BMS.exe (PID: 3512)
INFO
Application was dropped or rewritten from another process
- 7l_blackmesa_setup.tmp (PID: 580)
- 7l_blackmesa_setup.tmp (PID: 3592)
Creates files in the program directory
- 7l_blackmesa_setup.tmp (PID: 580)
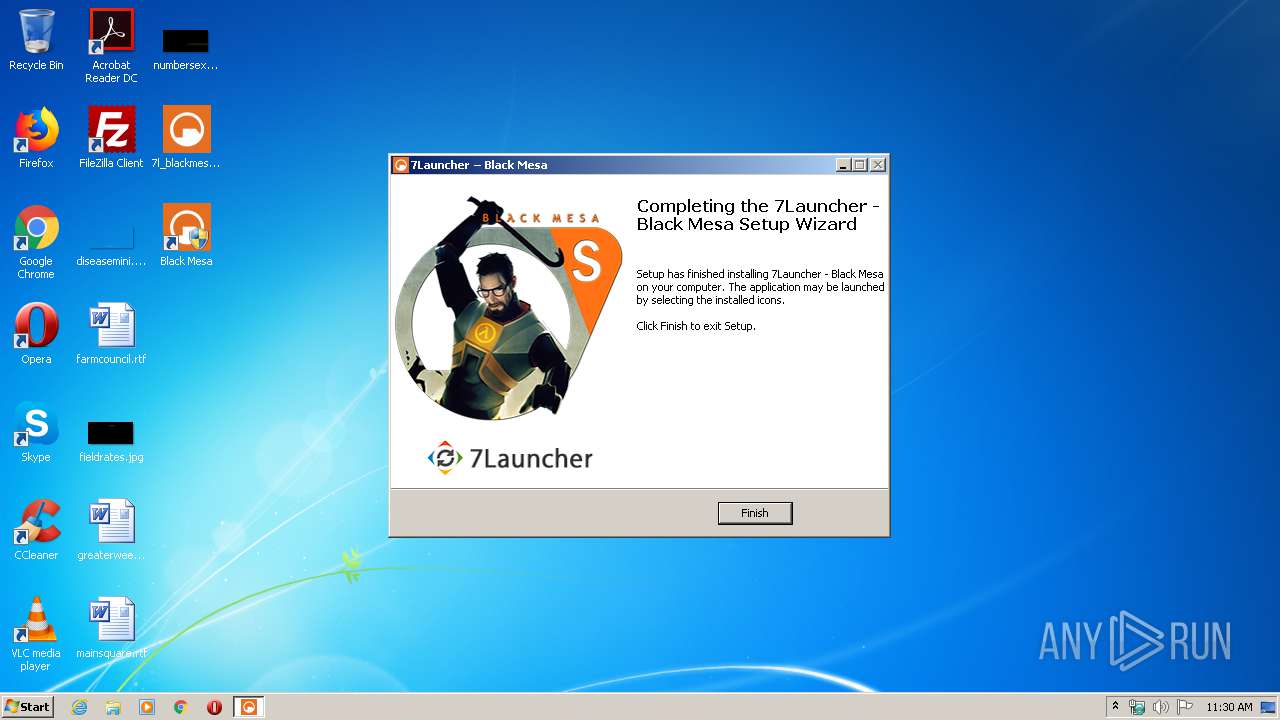
Creates a software uninstall entry
- 7l_blackmesa_setup.tmp (PID: 580)
Reads settings of System Certificates
- Run_BMS.exe (PID: 3512)
Reads the hosts file
- aria2c.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 419328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.11.0 |
| ProductVersionNumber: | 1.3.11.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | SE7EN Solutions |
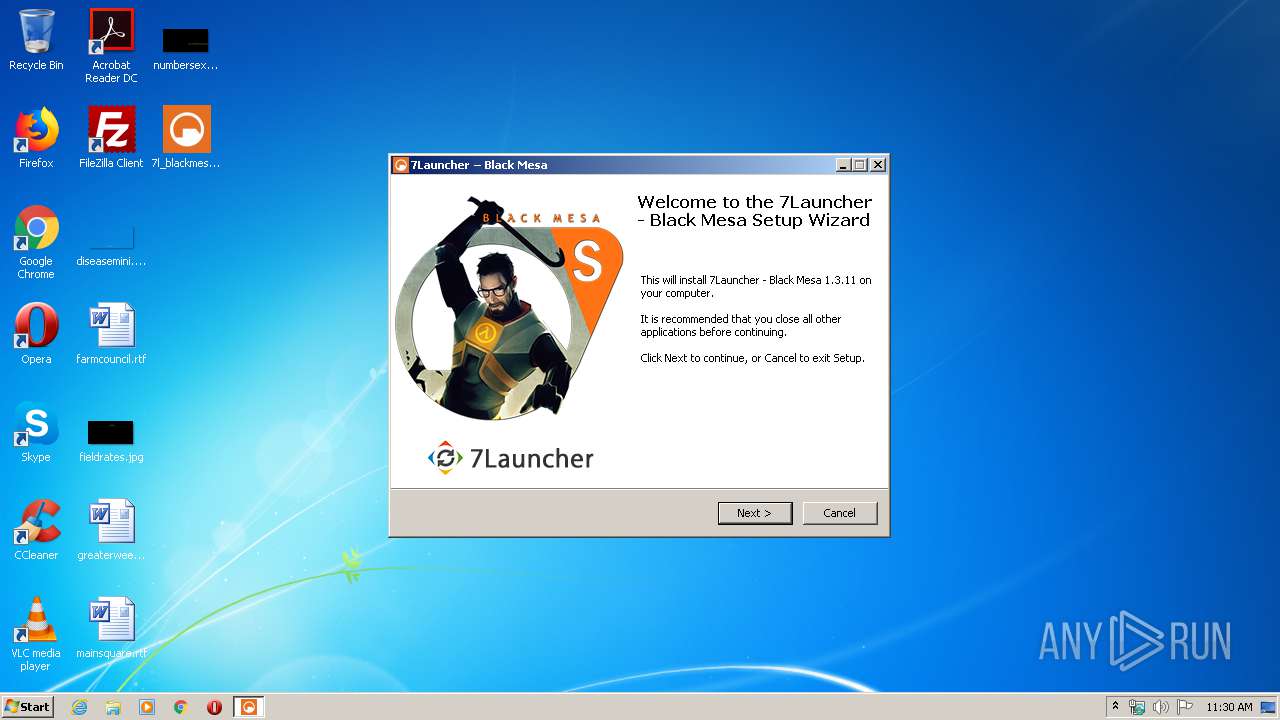
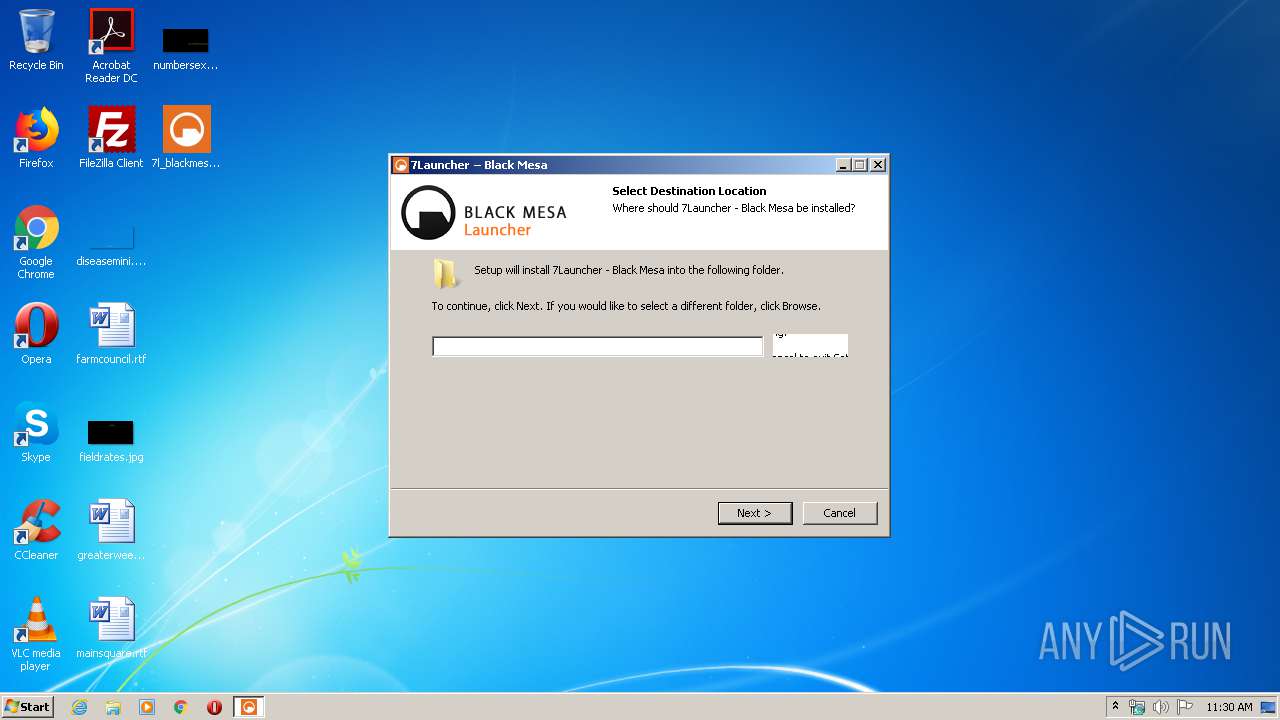
| FileDescription: | 7Launcher - Black Mesa Setup |
| FileVersion: | 1.3.11 |
| LegalCopyright: | SE7EN Solutions |
| ProductName: | 7Launcher - Black Mesa 1.3.11 |
| ProductVersion: | 1.3.11 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | SE7EN Solutions |
| FileDescription: | 7Launcher - Black Mesa Setup |
| FileVersion: | 1.3.11 |
| LegalCopyright: | SE7EN Solutions |
| ProductName: | 7Launcher - Black Mesa 1.3.11 |
| ProductVersion: | 1.3.11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00064408 | 0x00064600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.86356 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.08728 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.43656 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.60629 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.31737 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.1564 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
61
Monitored processes
13
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
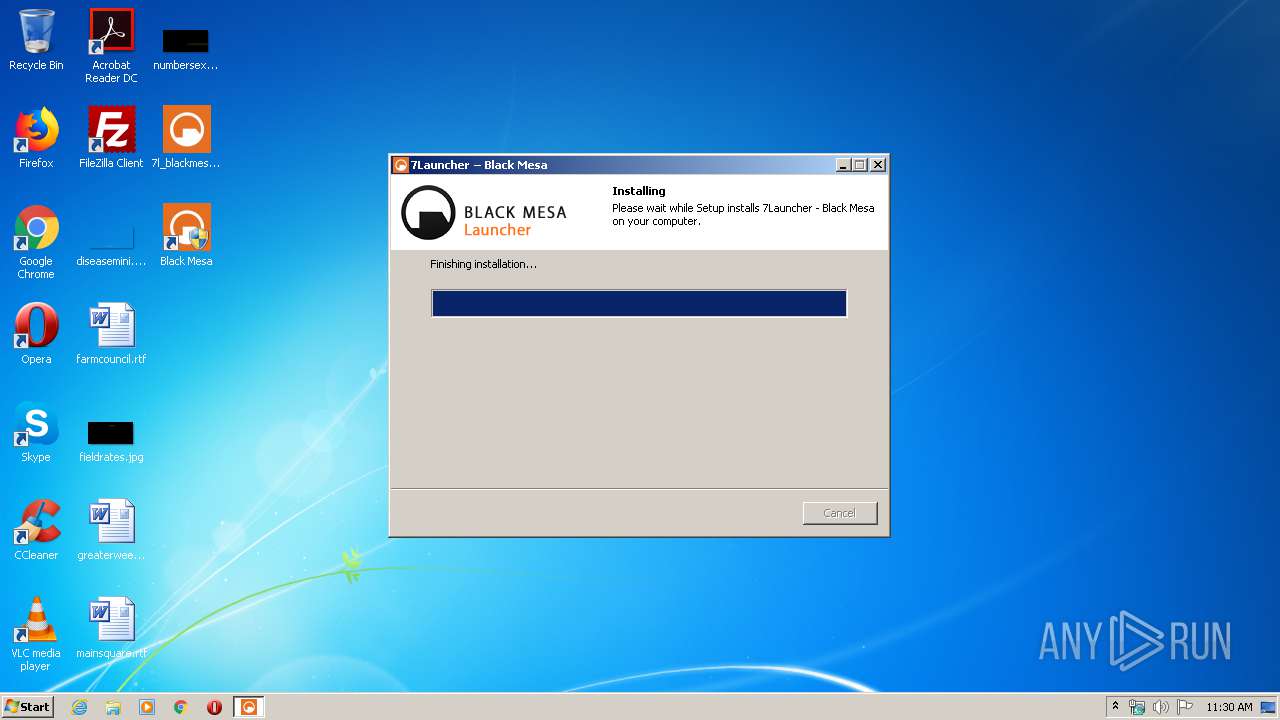
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Users\admin\AppData\Local\Temp\is-D81VM.tmp\7l_blackmesa_setup.tmp" /SL5="$80150,1668858,486912,C:\Users\admin\Desktop\7l_blackmesa_setup.exe" /SPAWNWND=$90140 /NOTIFYWND=$130224 | C:\Users\admin\AppData\Local\Temp\is-D81VM.tmp\7l_blackmesa_setup.tmp | 7l_blackmesa_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1524 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="7Launcher - Black Mesa Out" program="C:\Program Files\Black Mesa\Run_BMS.exe" dir=out action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1872 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="7Launcher - Black Mesa In" program="C:\Program Files\Black Mesa\Run_BMS.exe" dir=in action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Black Mesa\7launcher\tools\aria2\aria2c.exe" "https://se7en.ws/torrents/blackmesa_latest.torrent" --follow-torrent=mem --file-allocation=none --seed-time=0 --bt-enable-lpd=true --summary-interval=0 --truncate-console-readout=false --enable-color=false --human-readable=false --check-integrity=true --bt-max-peers=256 --bt-request-peer-speed-limit=200K --bt-max-open-files=300 --disk-cache=32M --dir="C:\Program Files\Black Mesa\!Setup" | C:\Program Files\Black Mesa\7launcher\tools\aria2\aria2c.exe | Run_BMS.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="Black Mesa Out" program="C:\Program Files\Black Mesa\bms.exe" dir=out action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | "taskkill.exe" /f /im "Run_BMS.exe" | C:\Windows\system32\taskkill.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="P2P In" program="C:\Program Files\Black Mesa\7launcher\tools\aria2\aria2c.exe" dir=in action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\Desktop\7l_blackmesa_setup.exe" /SPAWNWND=$90140 /NOTIFYWND=$130224 | C:\Users\admin\Desktop\7l_blackmesa_setup.exe | 7l_blackmesa_setup.tmp | ||||||||||||
User: admin Company: SE7EN Solutions Integrity Level: HIGH Description: 7Launcher - Black Mesa Setup Exit code: 0 Version: 1.3.11 Modules
| |||||||||||||||
| 3072 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="P2P Out" program="C:\Program Files\Black Mesa\7launcher\tools\aria2\aria2c.exe" dir=out action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_blackmesa_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | "C:\Program Files\Black Mesa\Run_BMS.exe" - forceupdate installp2p | C:\Program Files\Black Mesa\Run_BMS.exe | 7l_blackmesa_setup.tmp | ||||||||||||
User: admin Company: SE7EN Solutions Integrity Level: HIGH Description: 7Launcher - Black Mesa Exit code: 0 Version: 1.3.11.0 Modules
| |||||||||||||||
Total events
1 843
Read events
331
Write events
1 506
Delete events
6
Modification events
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 44020000488298E26103D601 | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7EC9EC82B3A2D80343F0A50BA350927C8EAAD97F4CD3EAE90A297D868DA5A8DA | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: \\?\C:\Program Files\Black Mesa\Run_BMS.exe | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 61AFF3056A1A98DA906467D4A84230AB434EB9FDE9935D4A363038213D9E8633 | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - Black Mesa |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\Black Mesa | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - Black Mesa |
| Operation: | write | Name: | GameEXE |
Value: C:\Program Files\Black Mesa\bms.exe | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - Black Mesa |
| Operation: | write | Name: | LauncherEXE |
Value: C:\Program Files\Black Mesa\Run_BMS.exe | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7l_blackmesa_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (580) 7l_blackmesa_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7l_blackmesa_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Black Mesa | |||
Executable files
5
Suspicious files
7
Text files
16
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 580 | 7l_blackmesa_setup.tmp | C:\Program Files\Black Mesa\is-QT6P3.tmp | — | |
MD5:— | SHA256:— | |||
| 580 | 7l_blackmesa_setup.tmp | C:\Program Files\Black Mesa\7launcher\is-DK9QT.tmp | — | |
MD5:— | SHA256:— | |||
| 580 | 7l_blackmesa_setup.tmp | C:\Program Files\Black Mesa\is-5UD25.tmp | — | |
MD5:— | SHA256:— | |||
| 3512 | Run_BMS.exe | C:\Users\admin\AppData\Local\Temp\CabB86B.tmp | — | |
MD5:— | SHA256:— | |||
| 3512 | Run_BMS.exe | C:\Users\admin\AppData\Local\Temp\TarB86C.tmp | — | |
MD5:— | SHA256:— | |||
| 580 | 7l_blackmesa_setup.tmp | C:\Program Files\Black Mesa\Run_BMS.exe | executable | |
MD5:— | SHA256:— | |||
| 580 | 7l_blackmesa_setup.tmp | C:\Users\admin\Desktop\Black Mesa.lnk | lnk | |
MD5:— | SHA256:— | |||
| 580 | 7l_blackmesa_setup.tmp | C:\Program Files\Black Mesa\7lcfg_BMS.ini | text | |
MD5:— | SHA256:— | |||
| 3512 | Run_BMS.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 3512 | Run_BMS.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
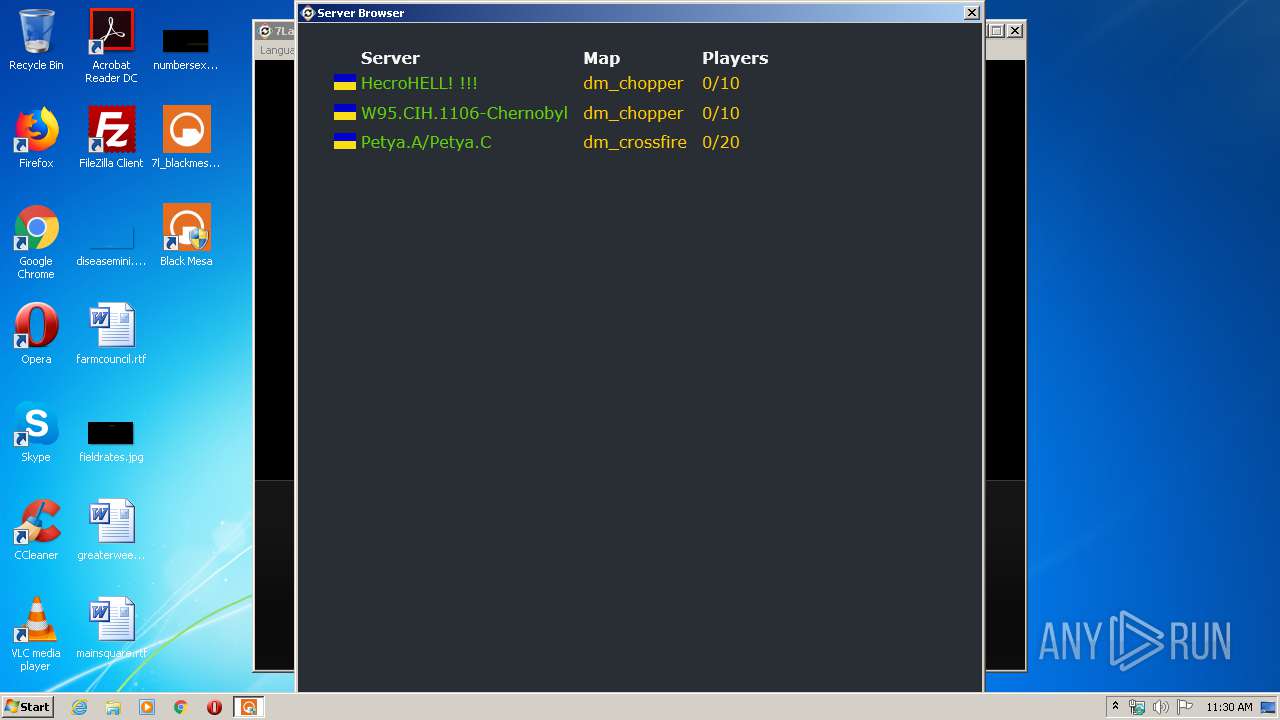
TCP/UDP connections
369
DNS requests
8
Threats
13
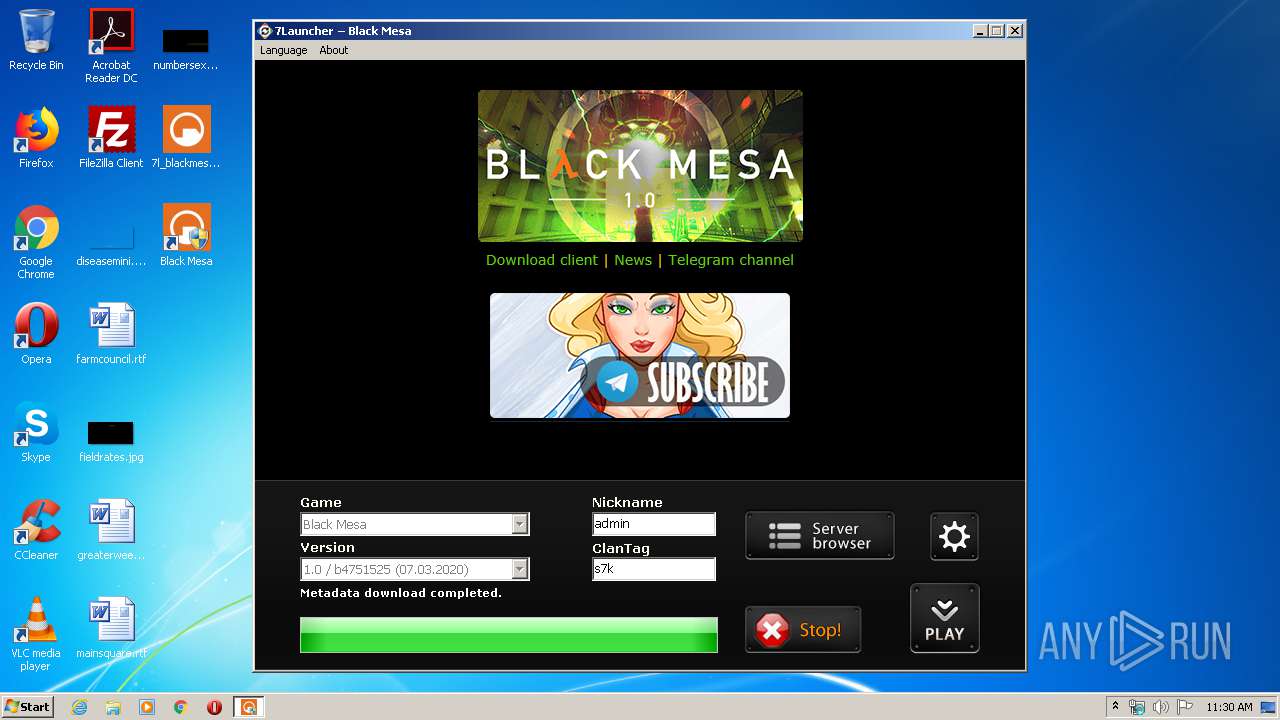
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/images/telega-banner.png | US | image | 20.6 Kb | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/images/black-mesa-header-v4.png | US | image | 32.4 Kb | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/bms/en/ | US | html | 1.01 Kb | whitelisted |
2380 | aria2c.exe | GET | 200 | 104.18.1.1:8080 | http://tracker1.itzmx.com:8080/announce?info_hash=%C3%DF%AE%28%F3%C2%0B%D6%F1%F2g%40%5C%AA%86%93YX%3D%AD&peer_id=A2-1-34-0-0%15%22%C3%26%D8%AA%F22%BD&uploaded=0&downloaded=0&left=10063375907&compact=1&key=%22%C3%26%D8%AA%F22%BD&numwant=50&no_peer_id=1&port=6997&event=started&supportcrypto=1 | US | binary | 1.83 Kb | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/images/black-mesa-header-v4.png | US | image | 32.4 Kb | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/bms/monitoring/country/ua.png | US | image | 111 b | whitelisted |
3512 | Run_BMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/bms/monitoring/ | US | html | 798 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3512 | Run_BMS.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.26.2.87:443 | up.se7en.ws | Cloudflare Inc | US | suspicious |
3512 | Run_BMS.exe | 172.217.22.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3512 | Run_BMS.exe | 216.58.207.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2380 | aria2c.exe | 37.188.246.5:6953 | — | O2 Czech Republic, a.s. | CZ | unknown |
2380 | aria2c.exe | 37.188.160.253:6927 | — | O2 Czech Republic, a.s. | CZ | unknown |
2380 | aria2c.exe | 79.134.37.141:15586 | — | JSC Alma Telecommunications | KZ | unknown |
2380 | aria2c.exe | 104.26.2.87:443 | up.se7en.ws | Cloudflare Inc | US | suspicious |
2380 | aria2c.exe | 77.239.88.105:44108 | — | Telrad doo | BA | unknown |
2380 | aria2c.exe | 78.81.166.209:62360 | — | PJSC Rostelecom | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
up.se7en.ws |
| suspicious |
ocsp.digicert.com |
| whitelisted |
updater.se7enkills.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
se7en.ws |
| whitelisted |
tracker1.itzmx.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3512 | Run_BMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3512 | Run_BMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3512 | Run_BMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3512 | Run_BMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2380 | aria2c.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
2380 | aria2c.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
2380 | aria2c.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
2380 | aria2c.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
2380 | aria2c.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT nodes reply |