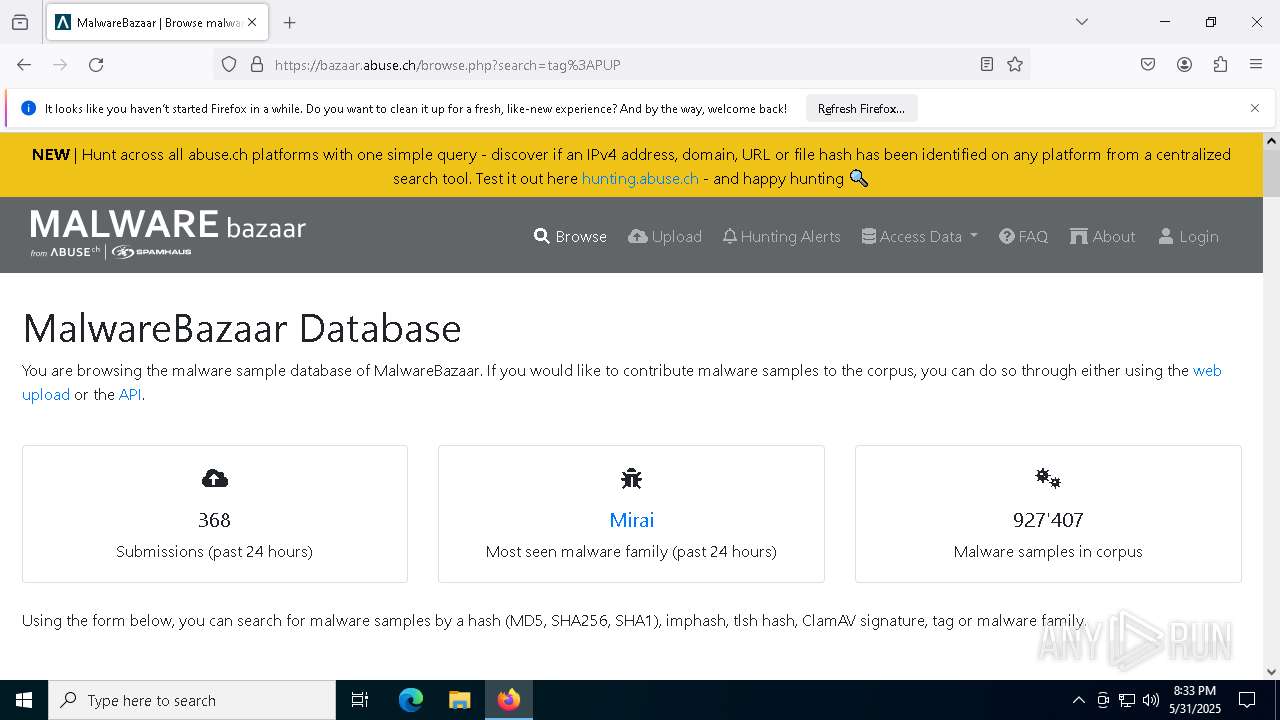
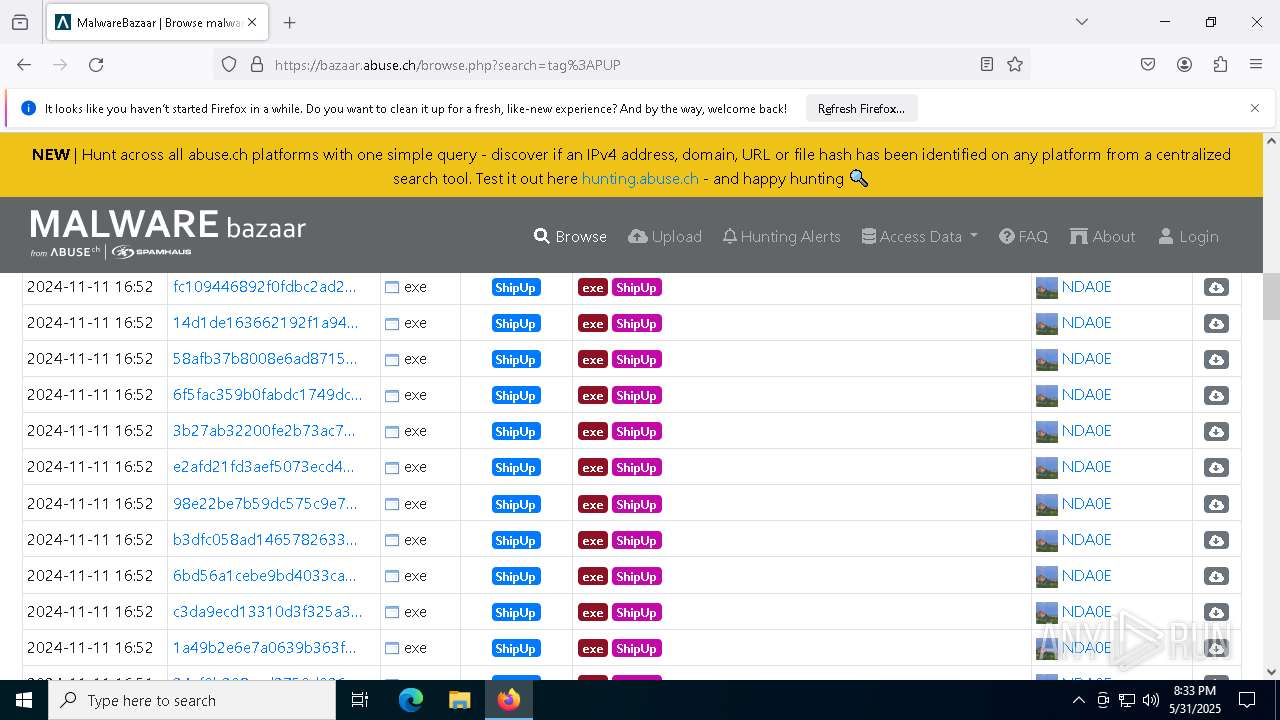
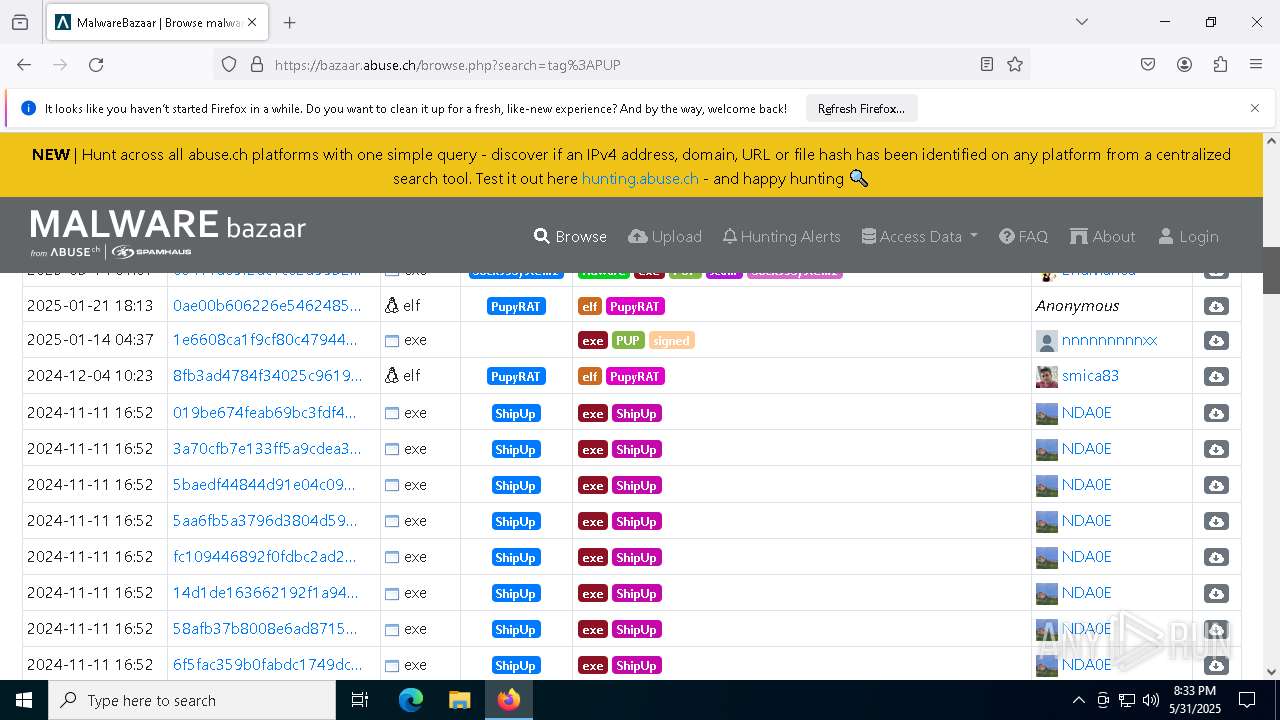
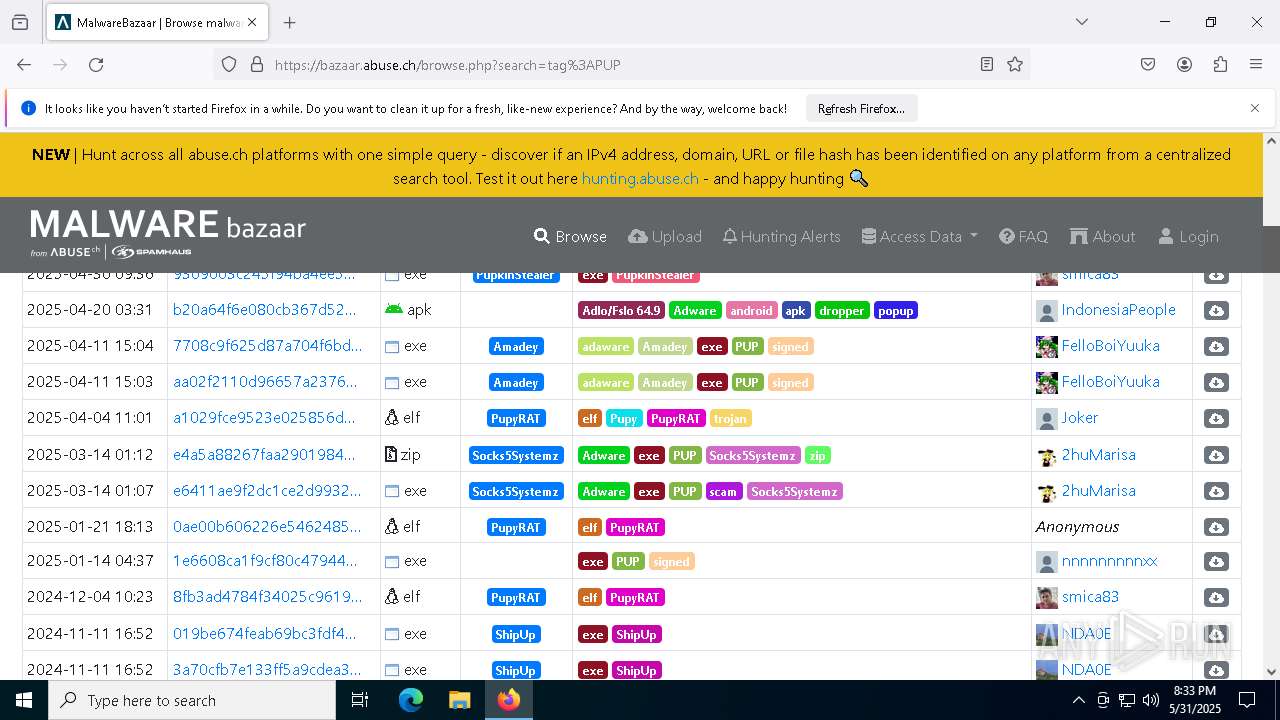
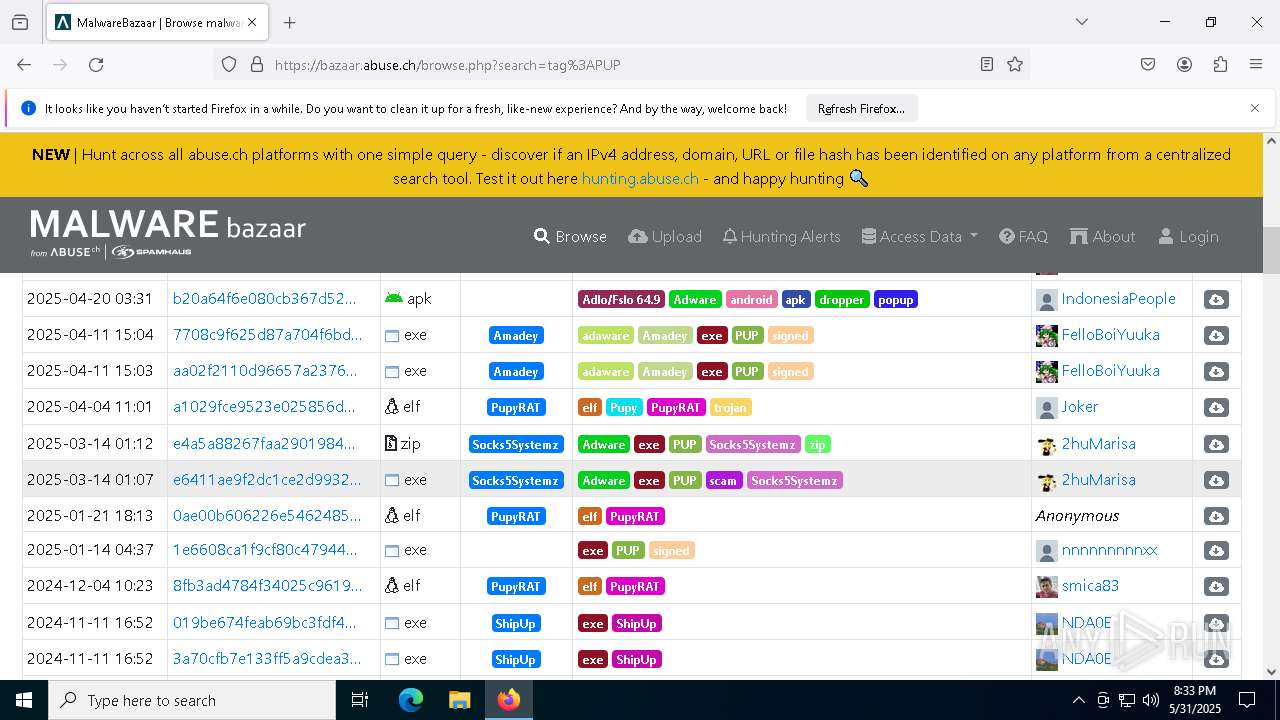
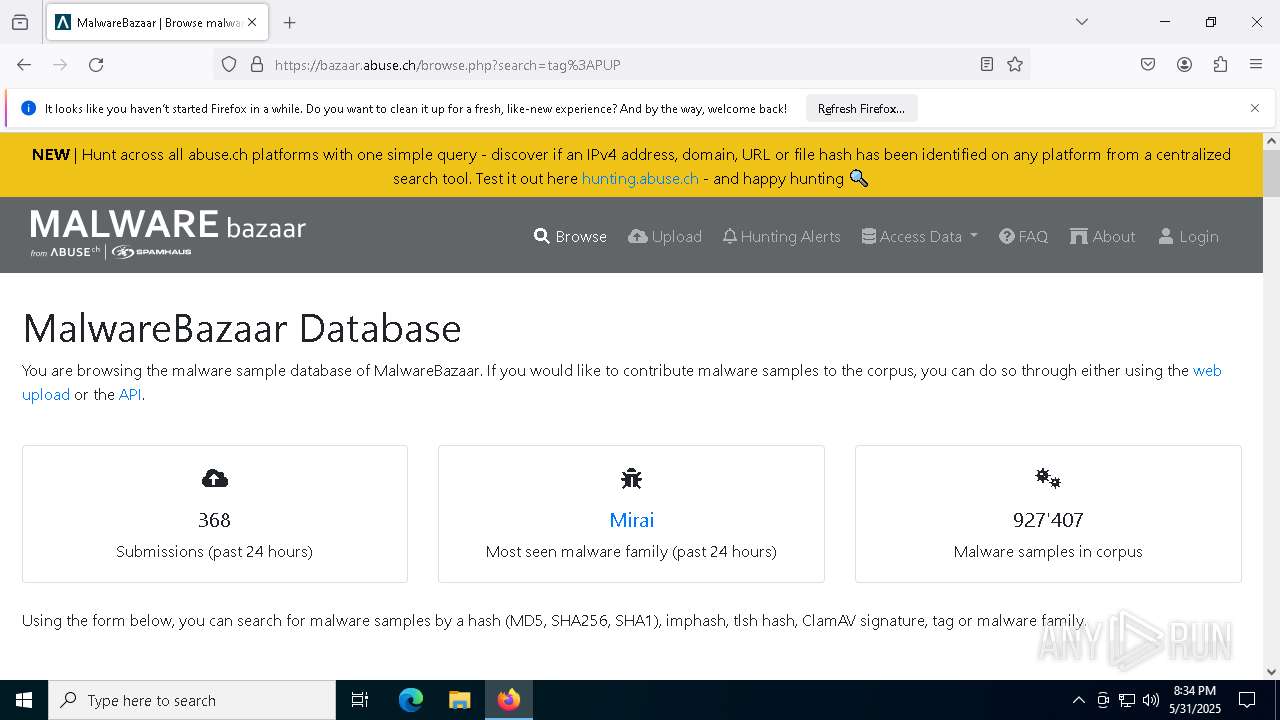
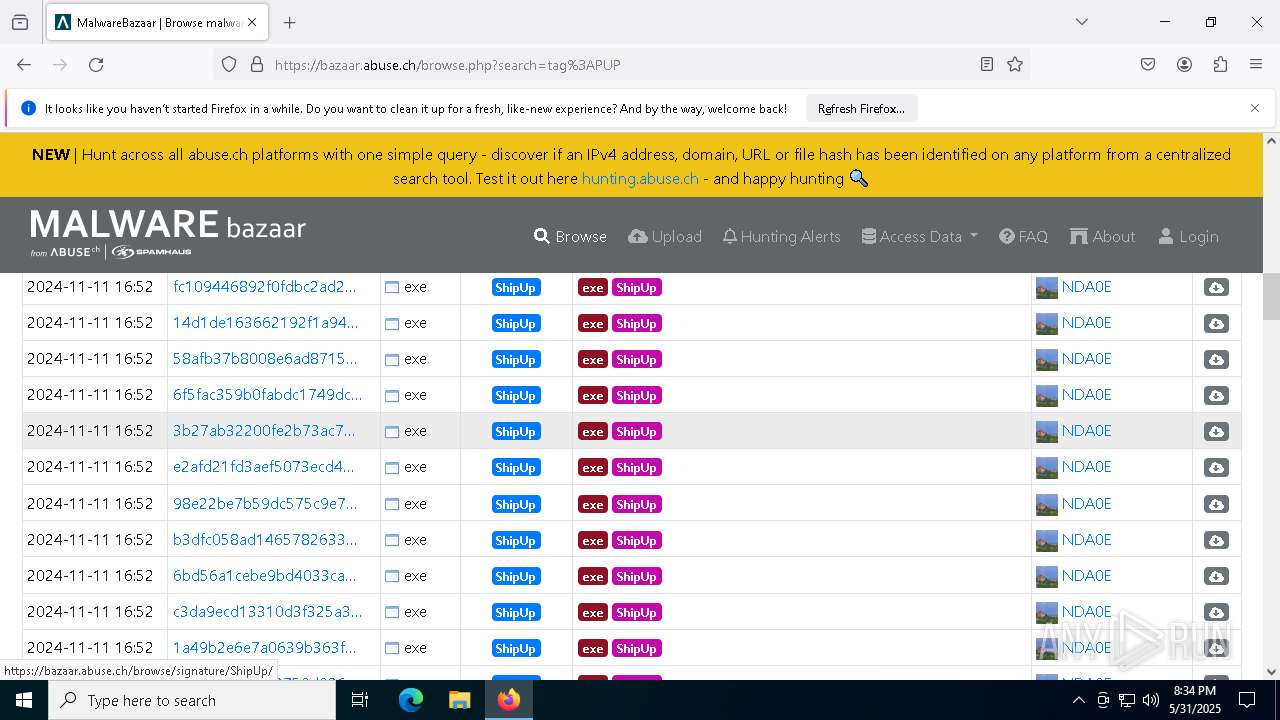
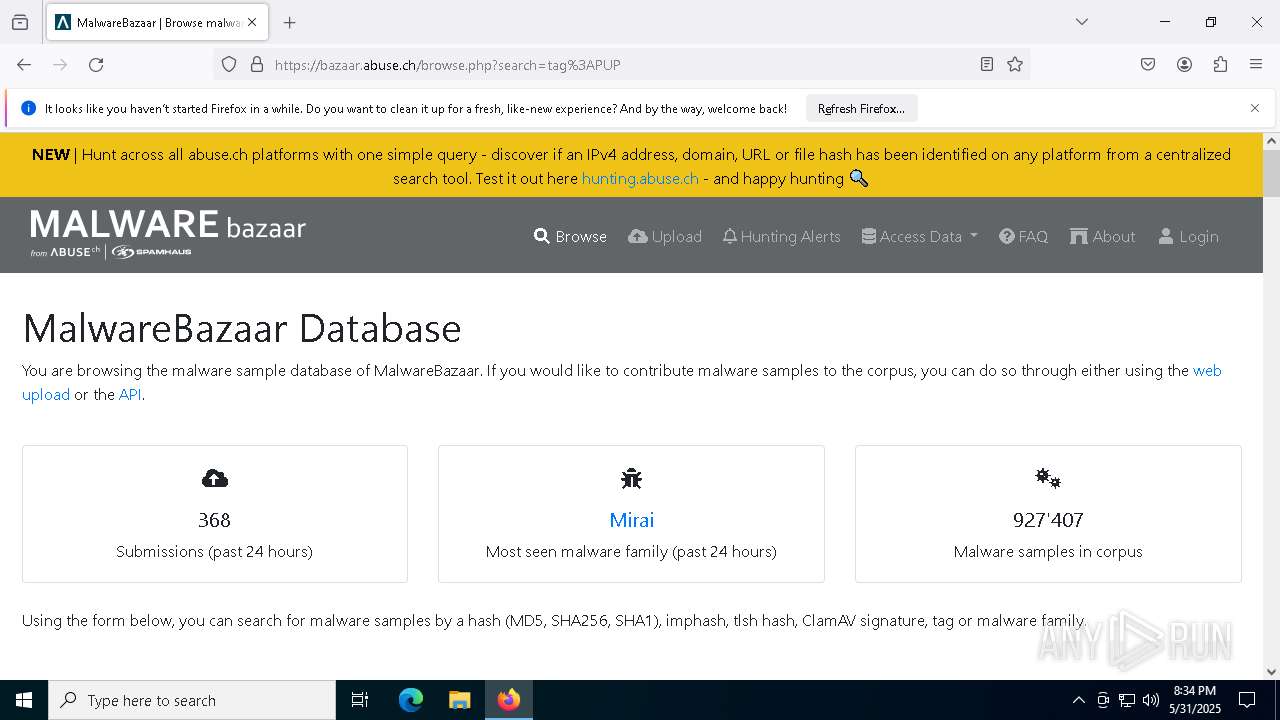
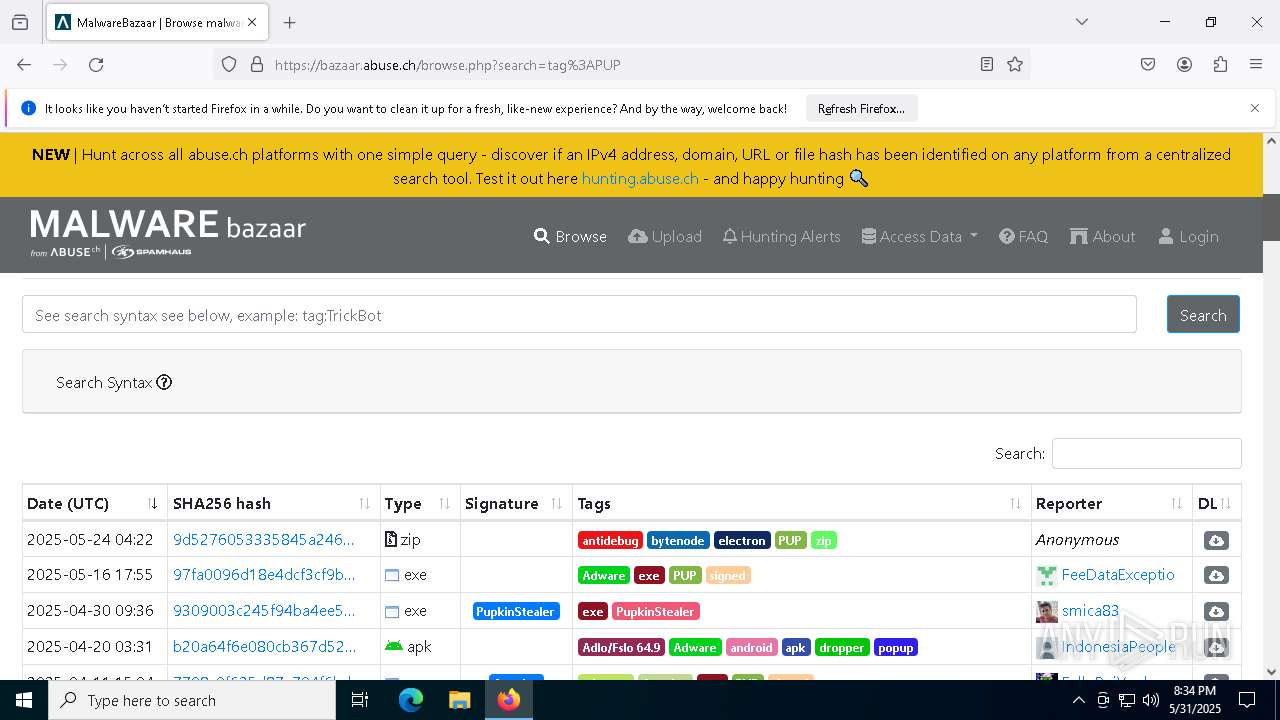
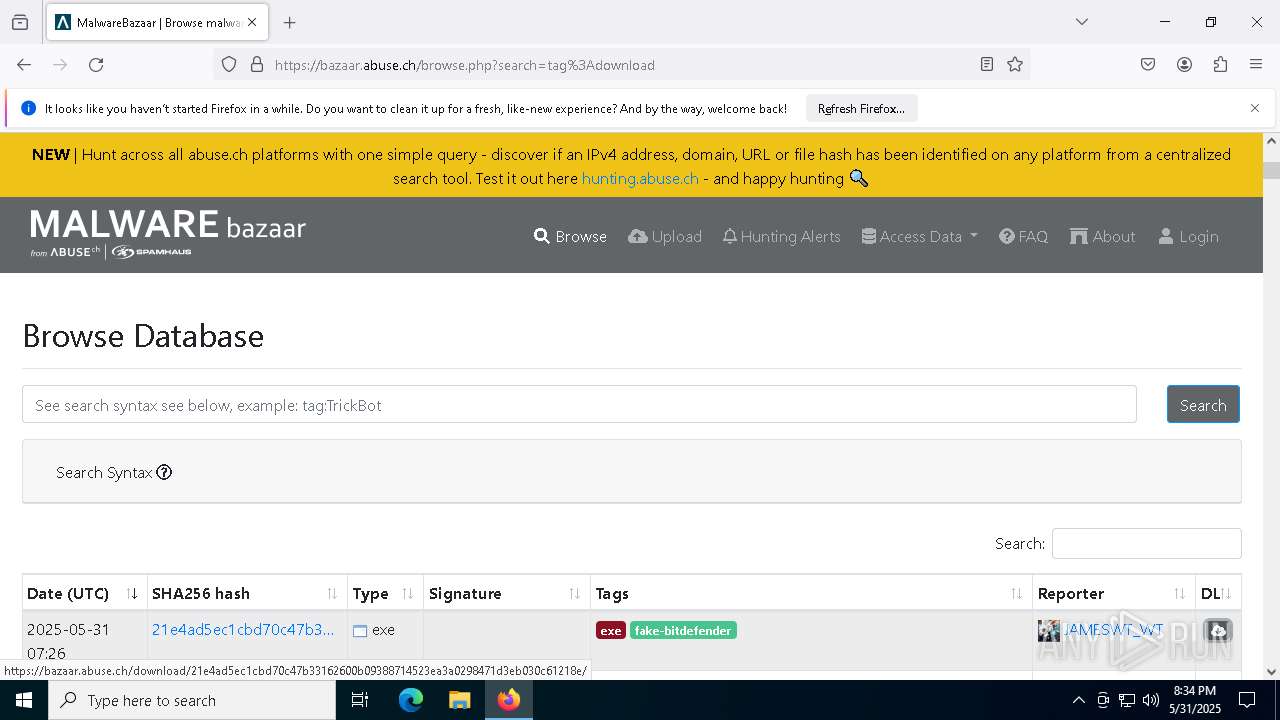
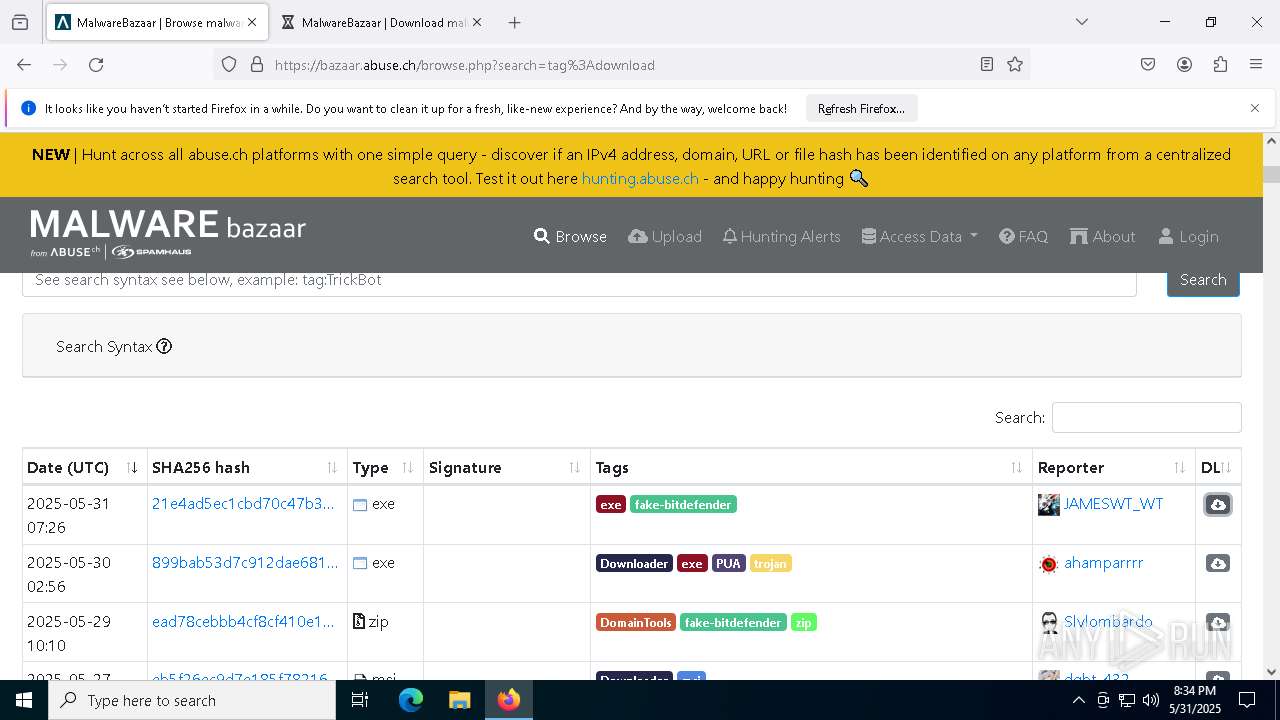
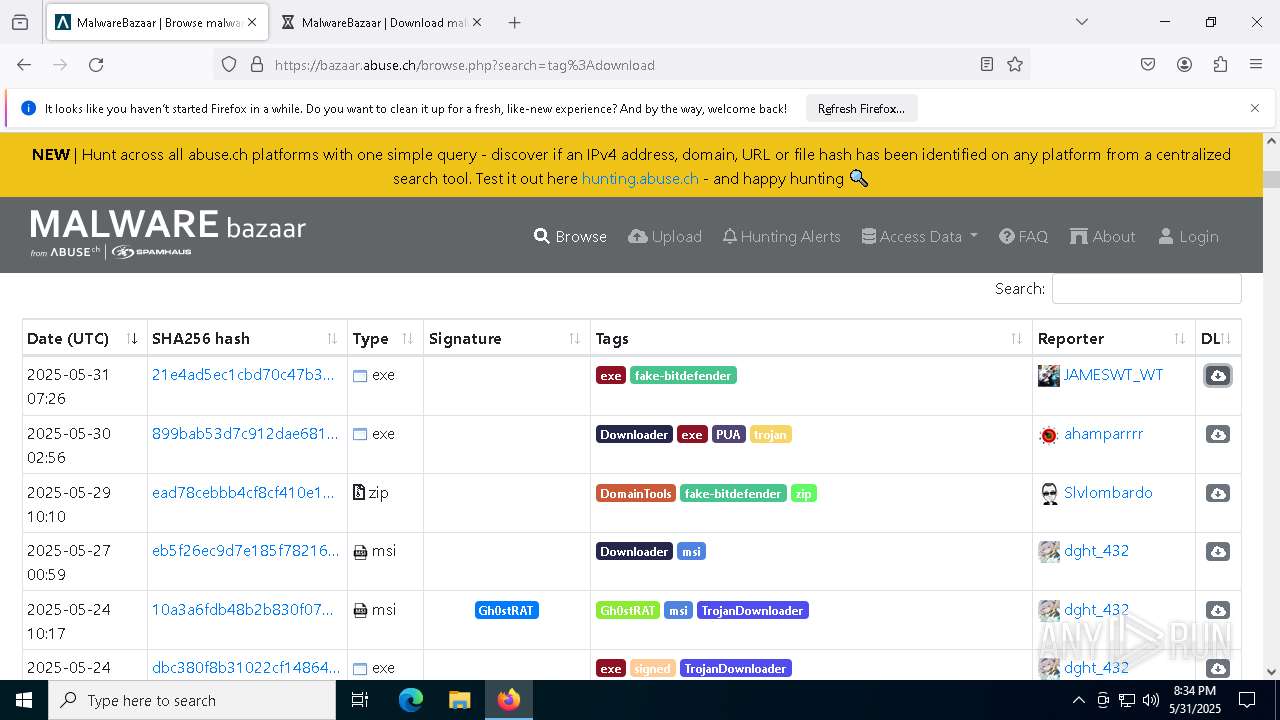
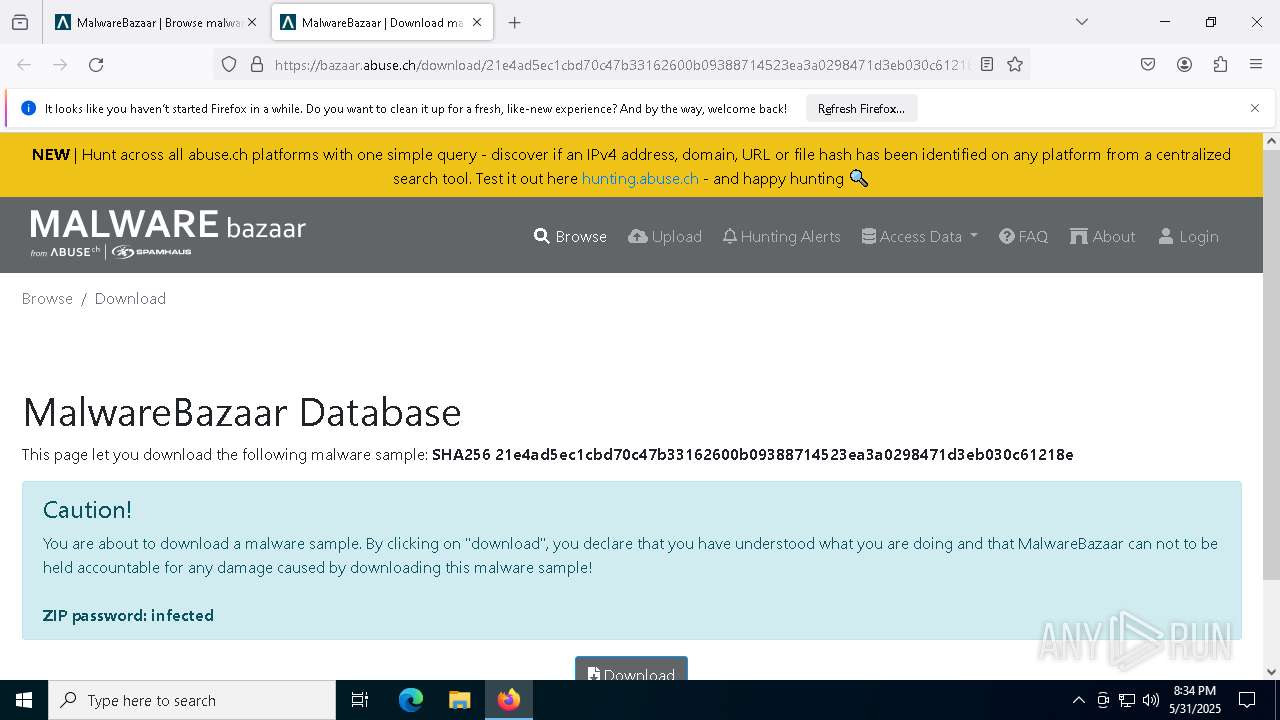
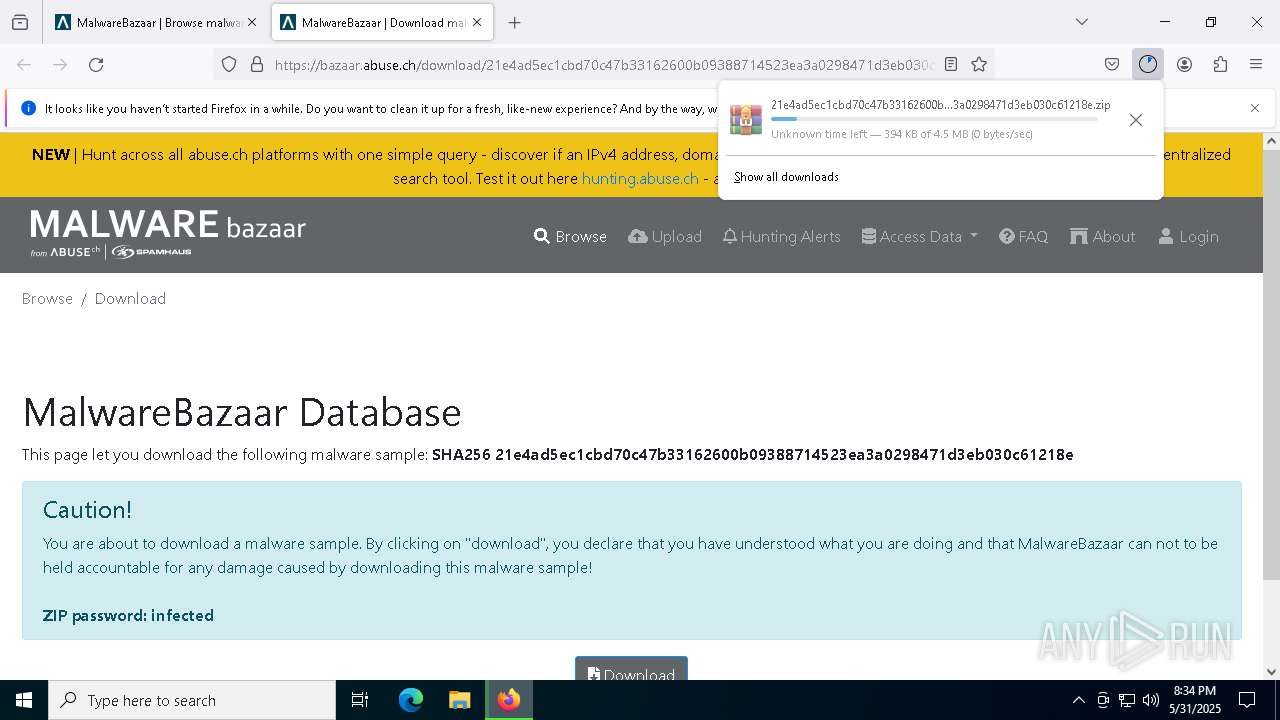
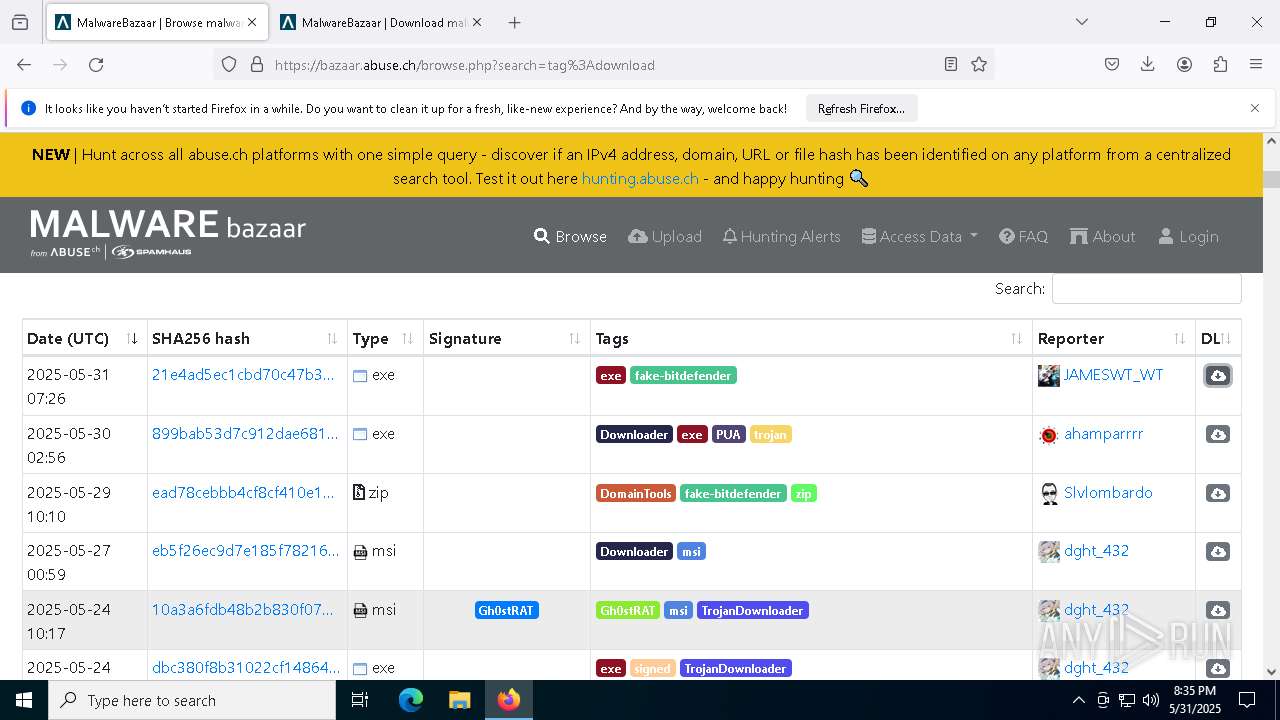
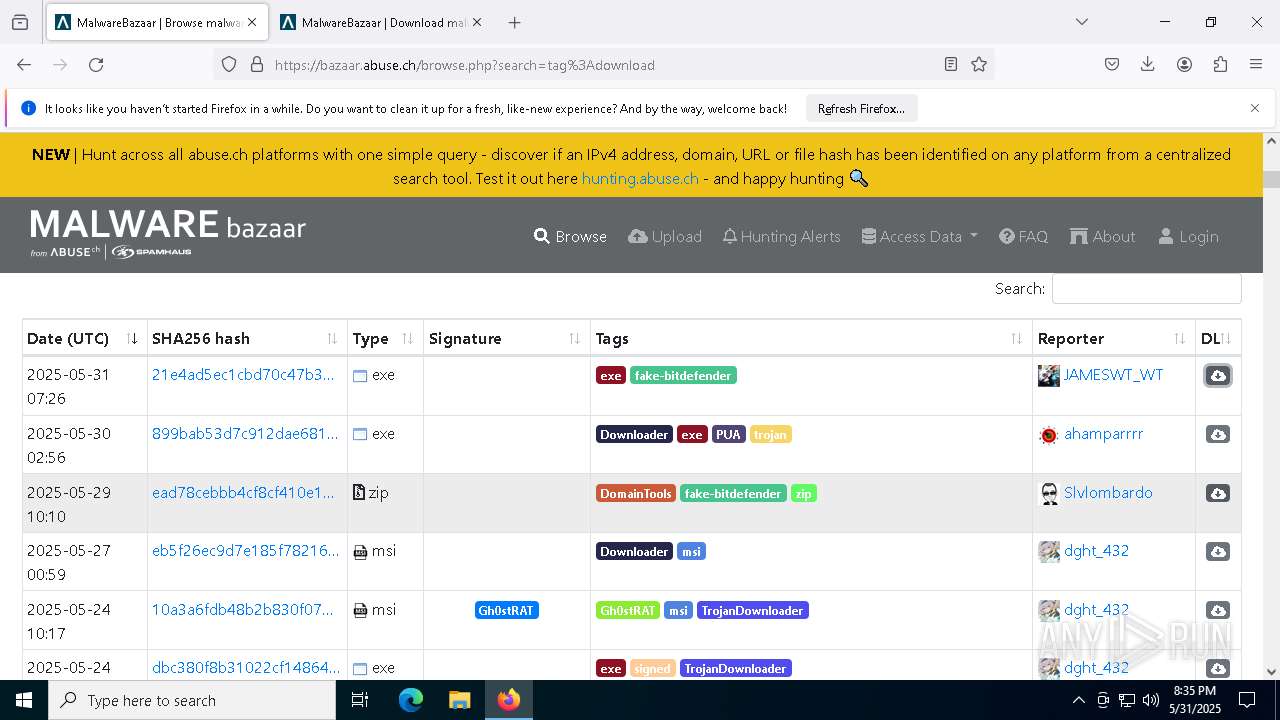
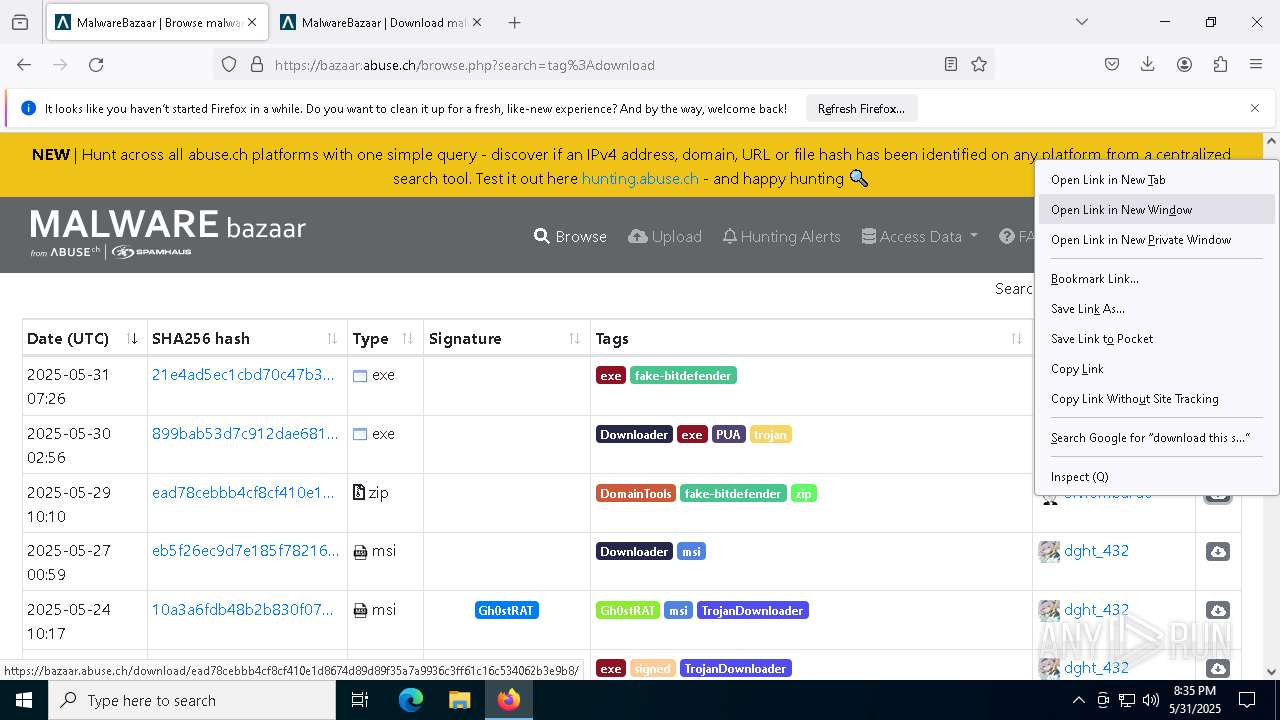
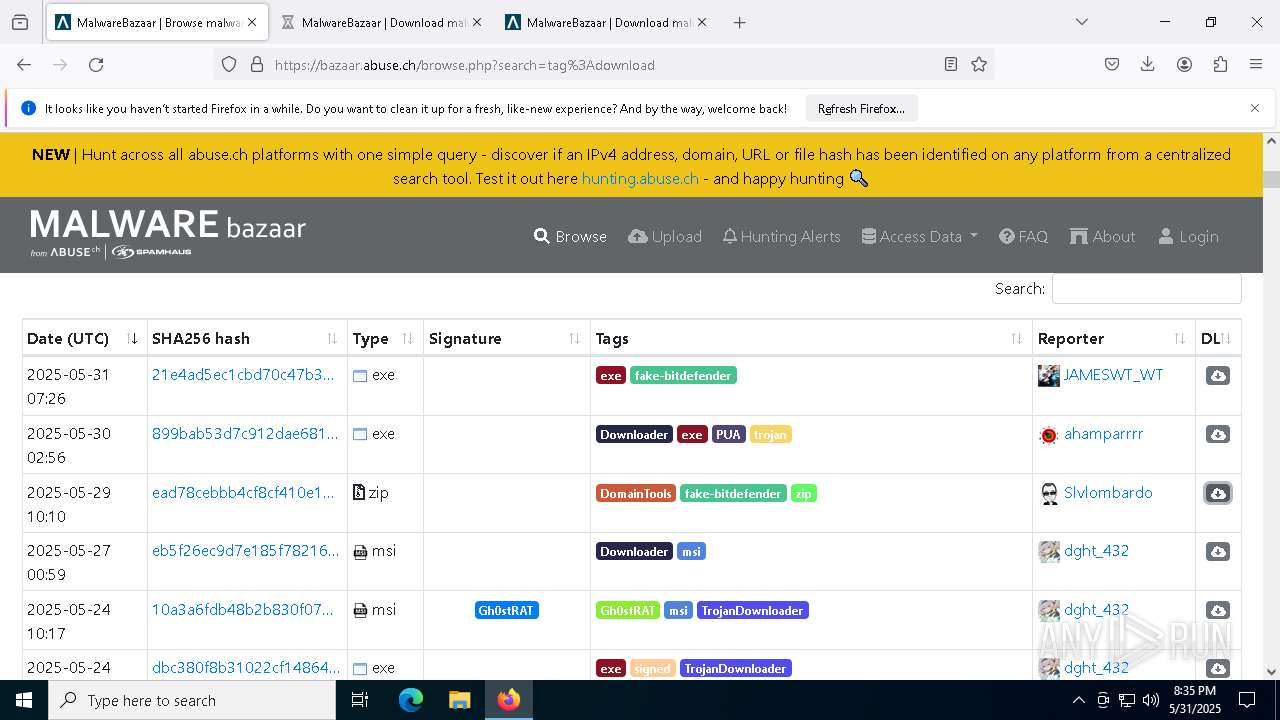
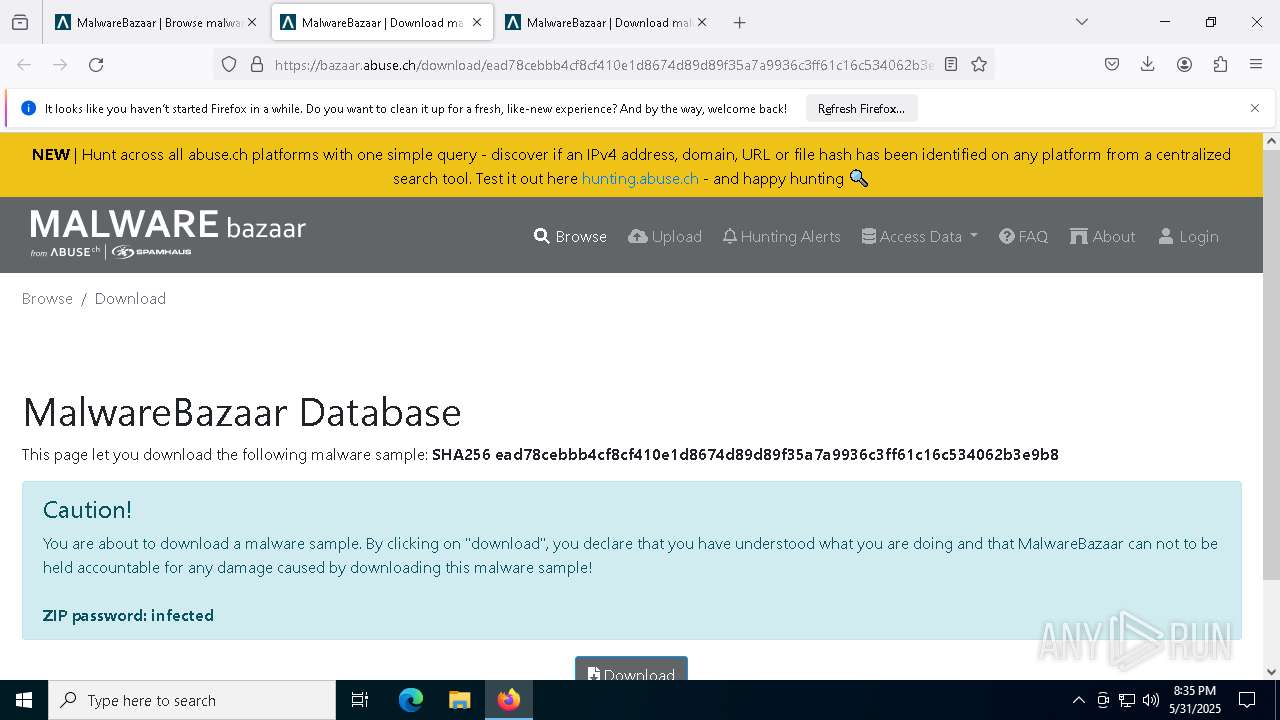
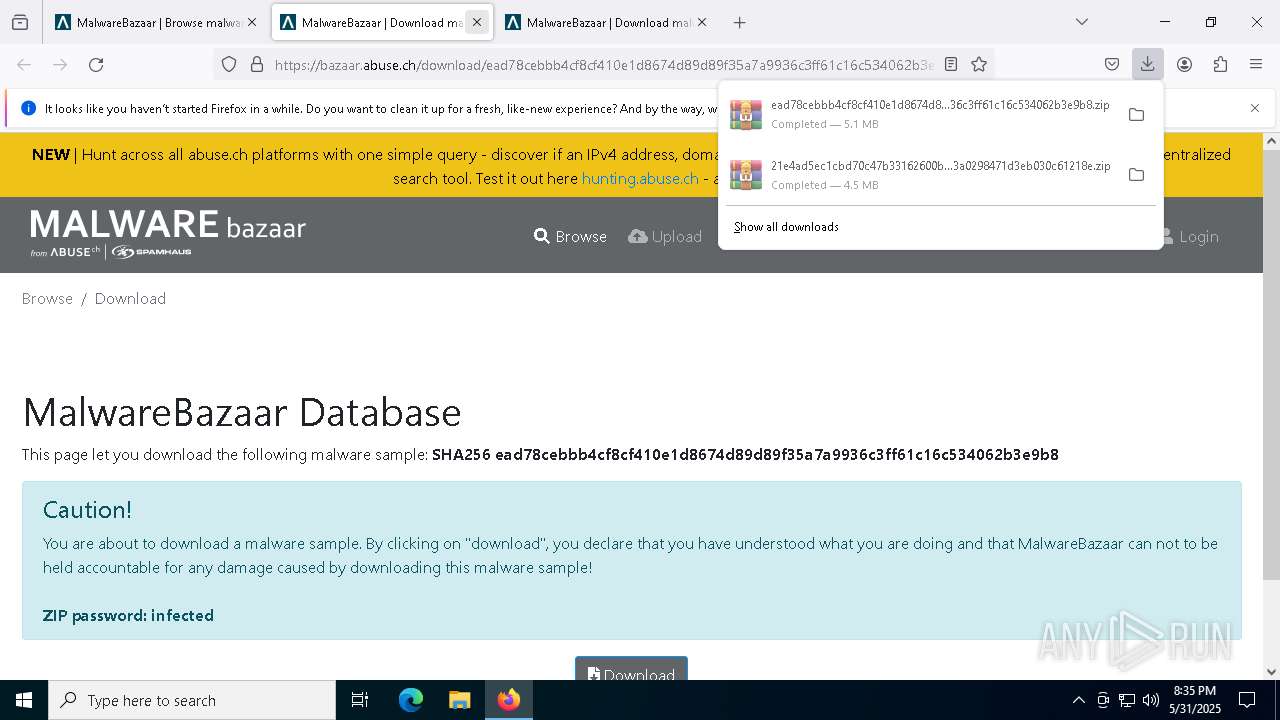
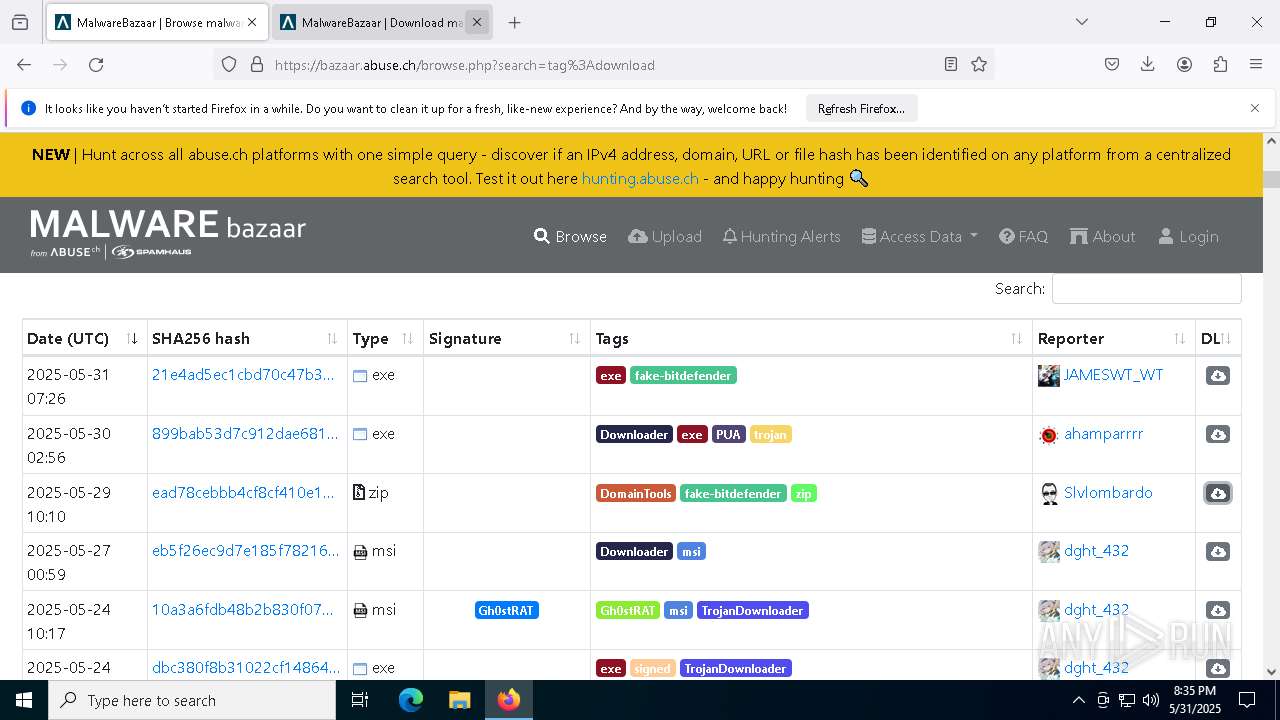
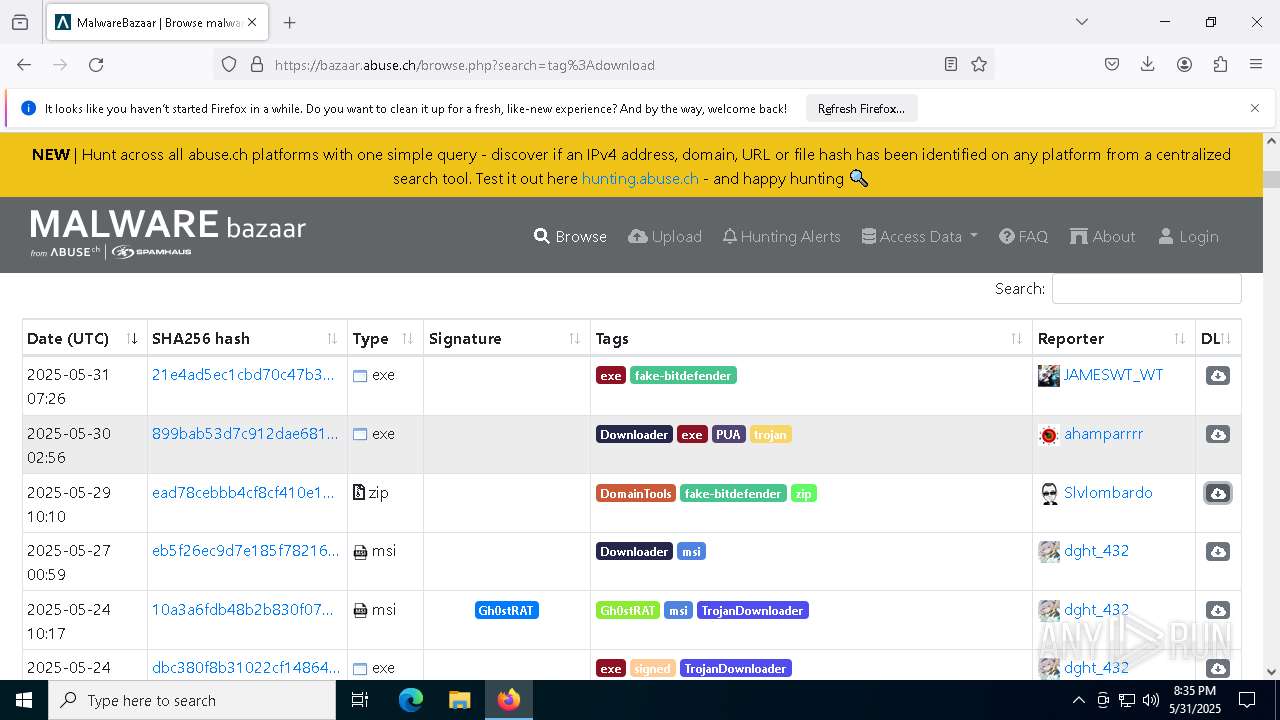
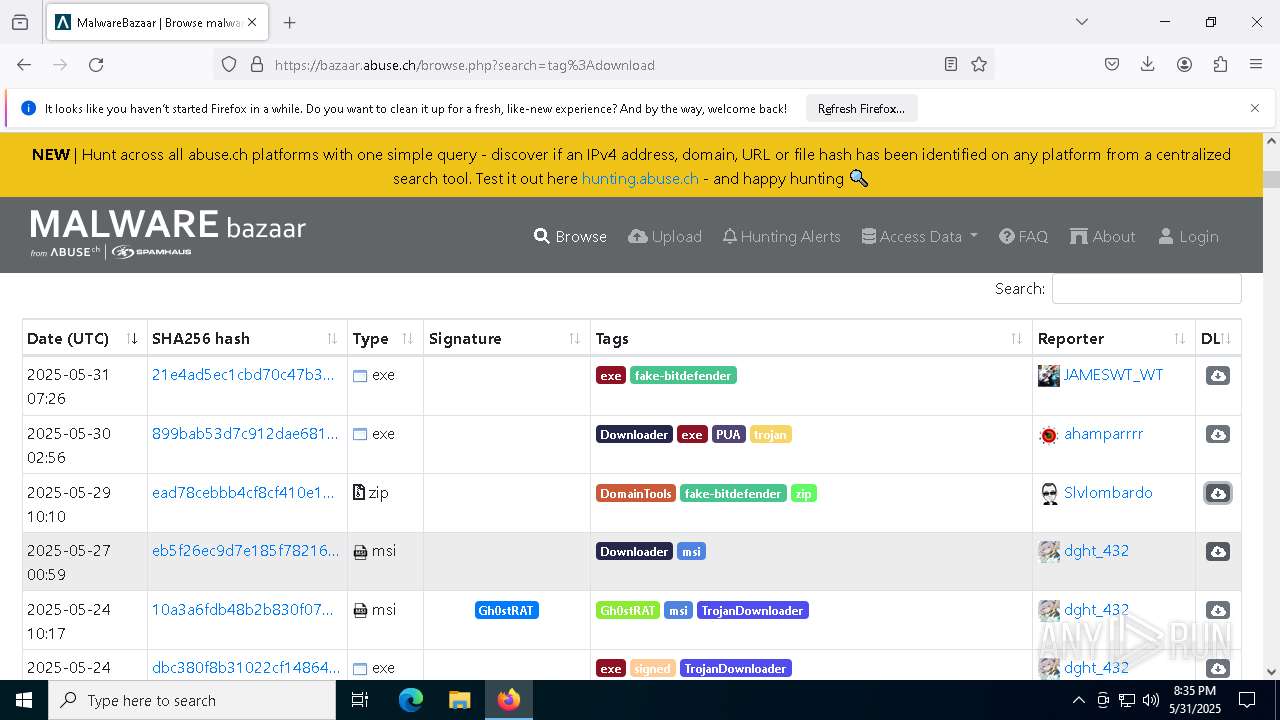
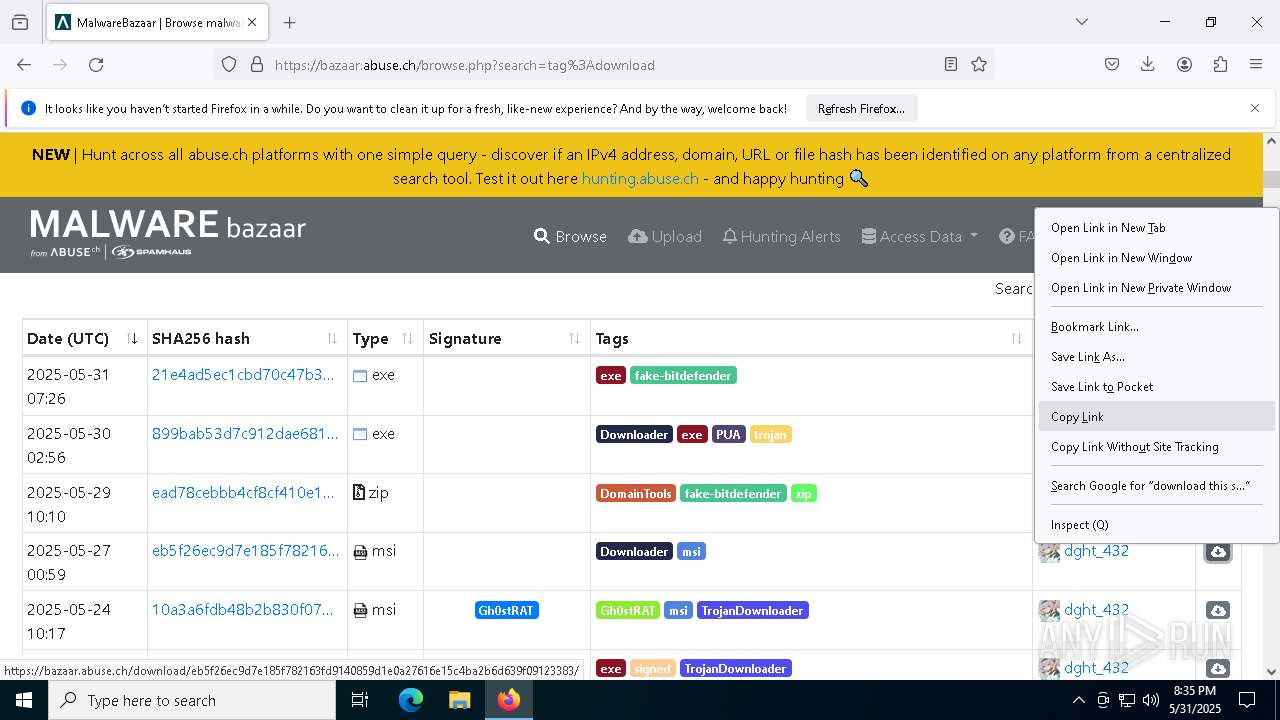
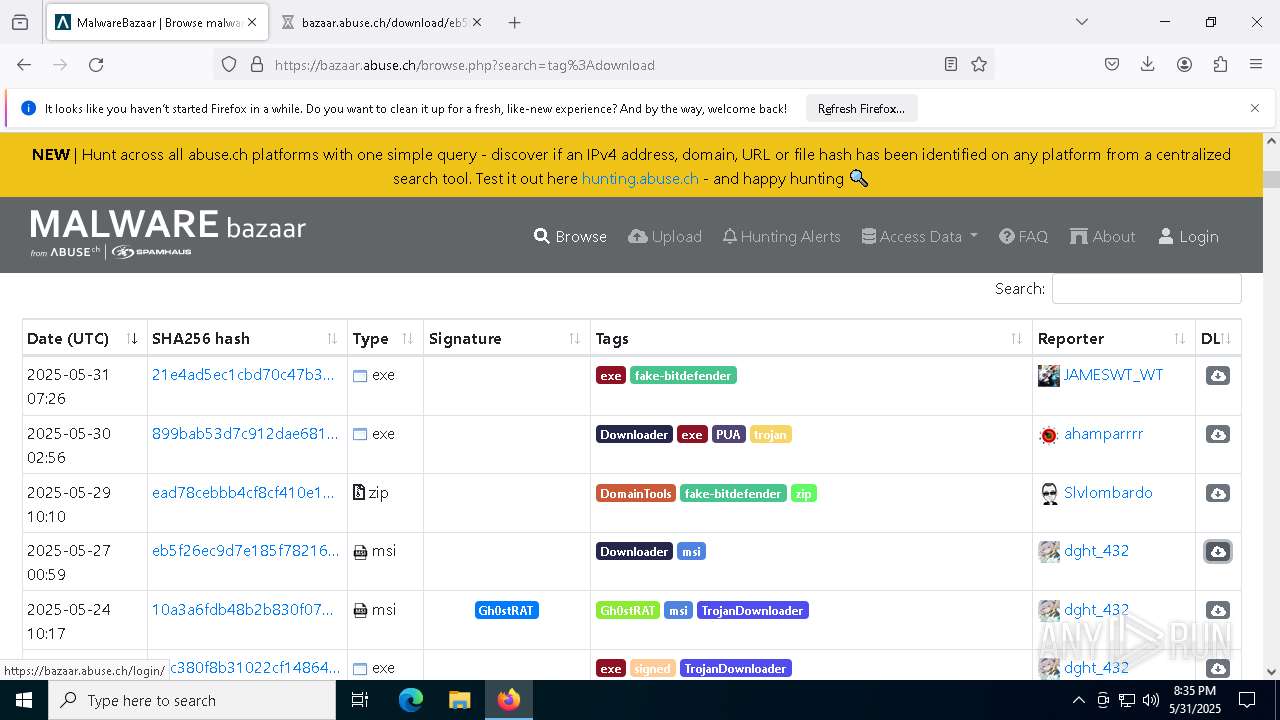
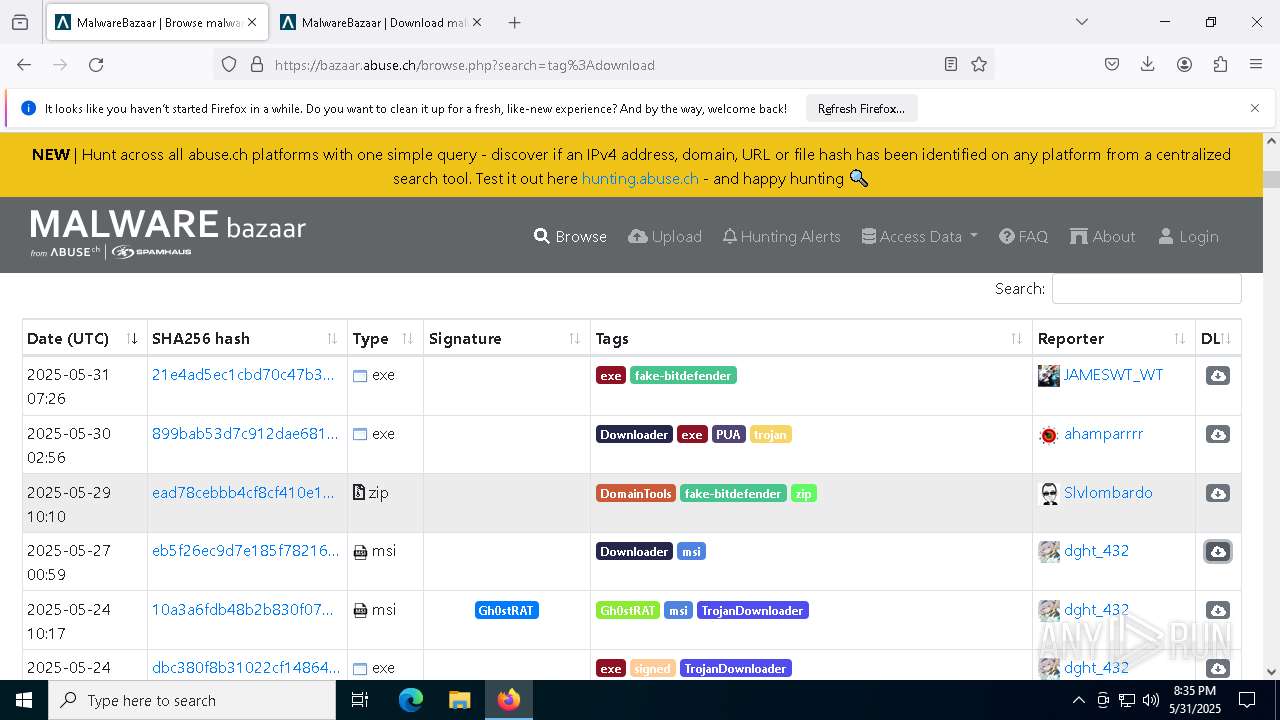
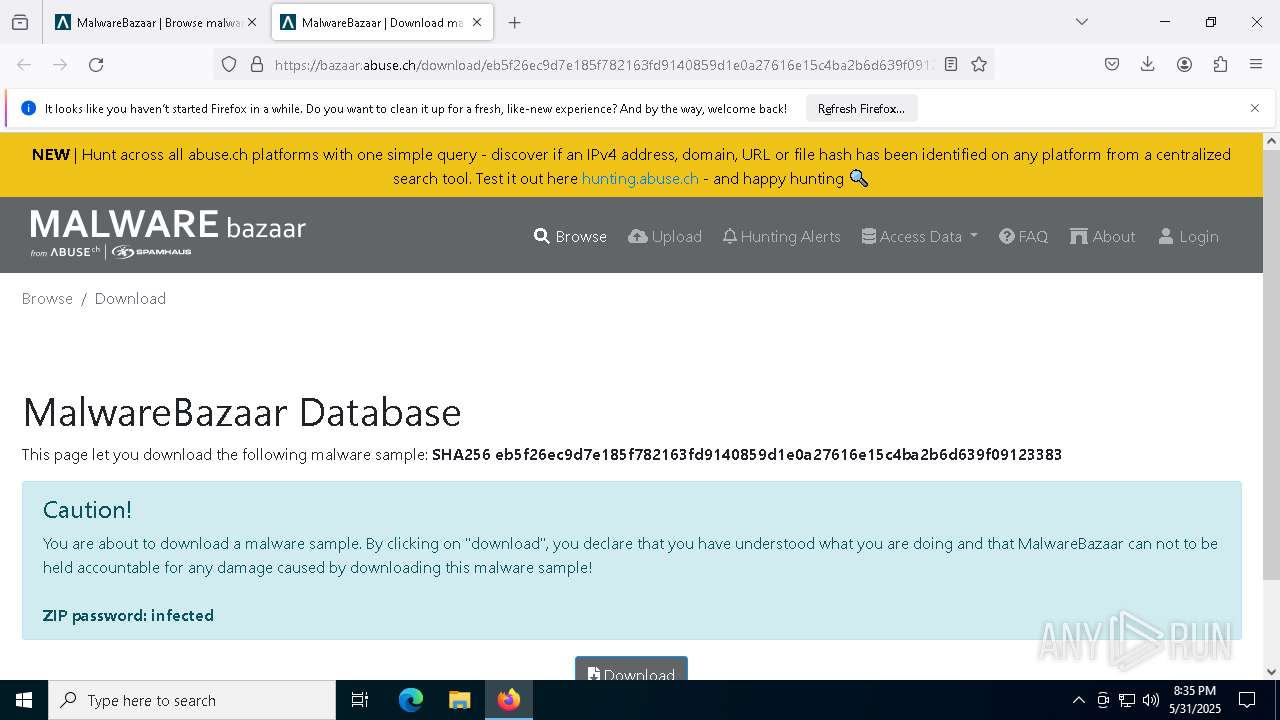
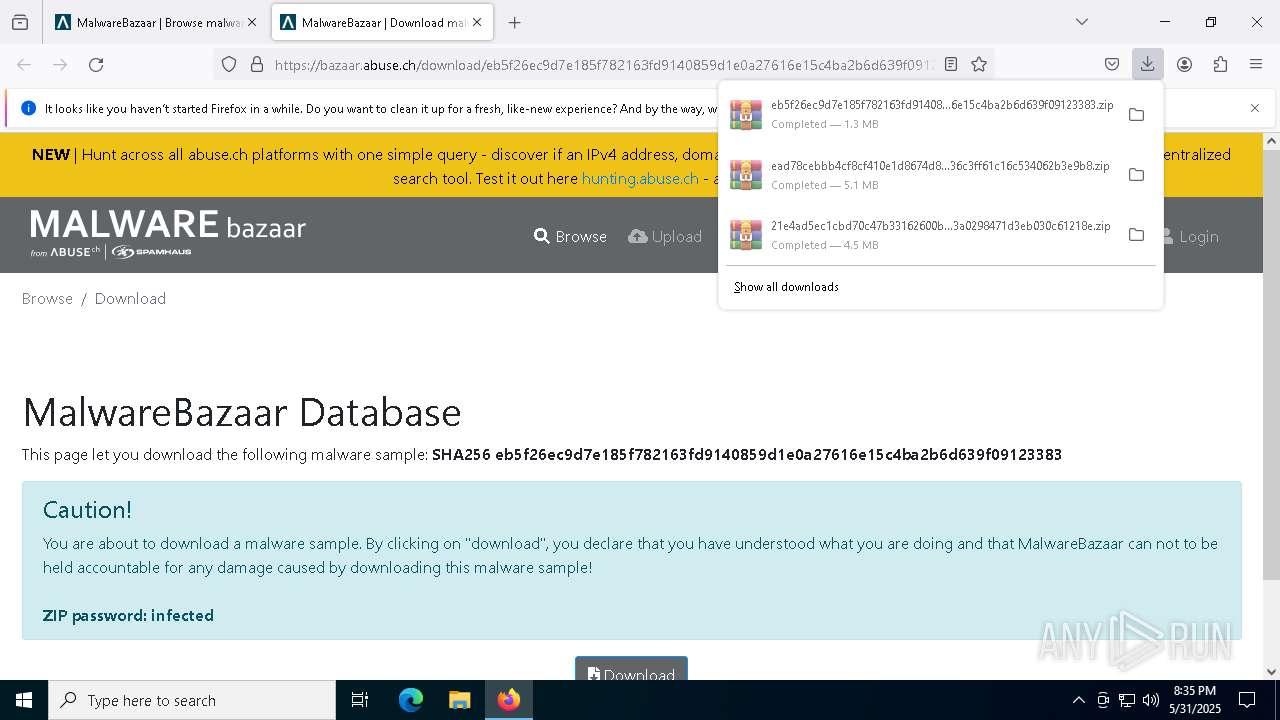
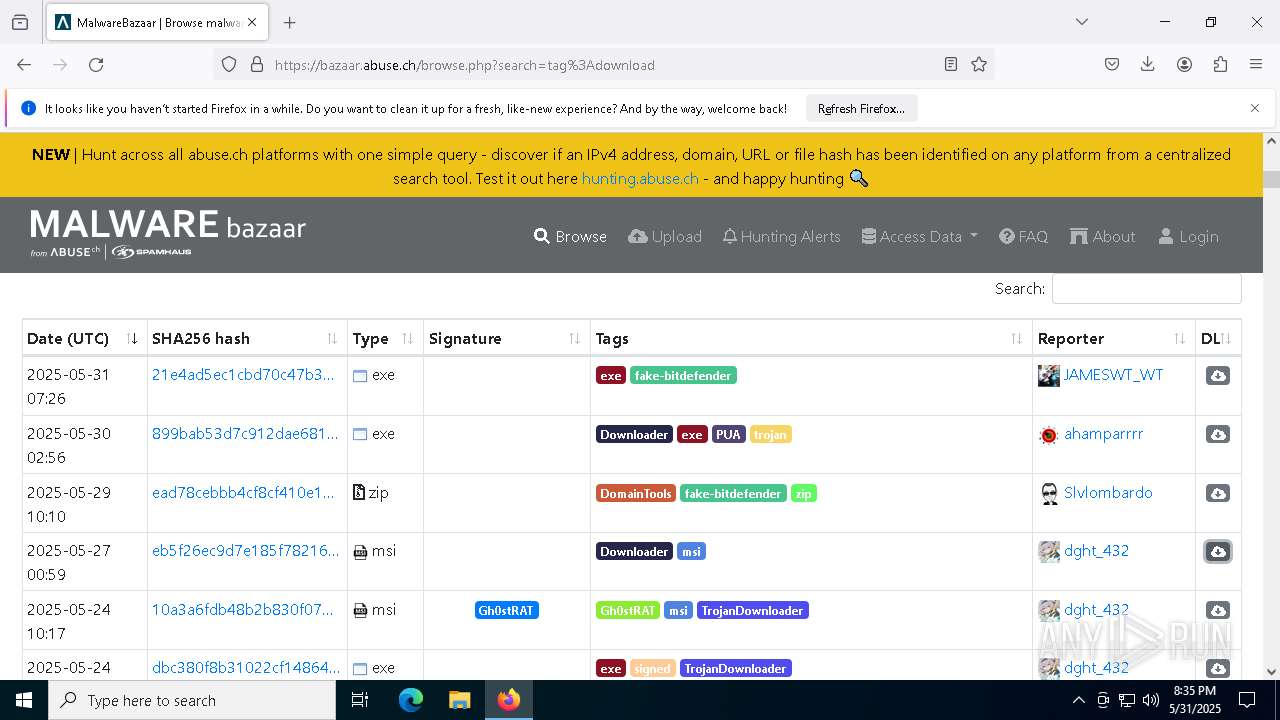
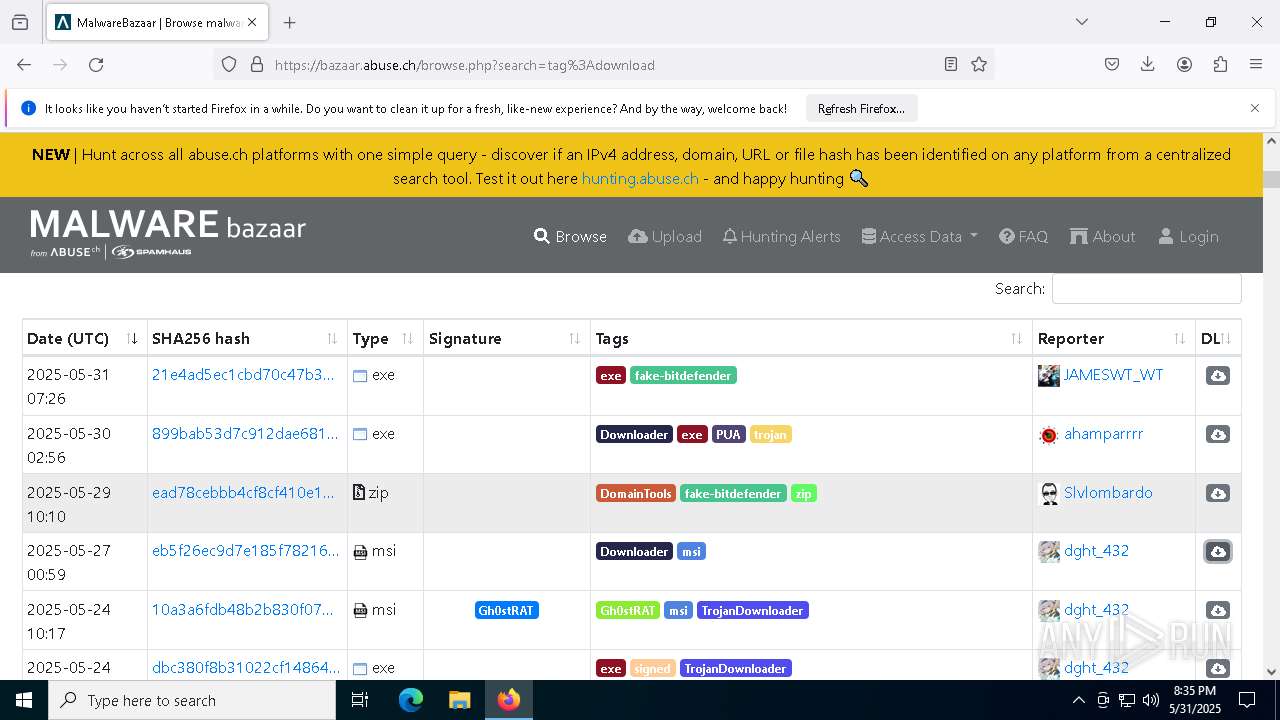
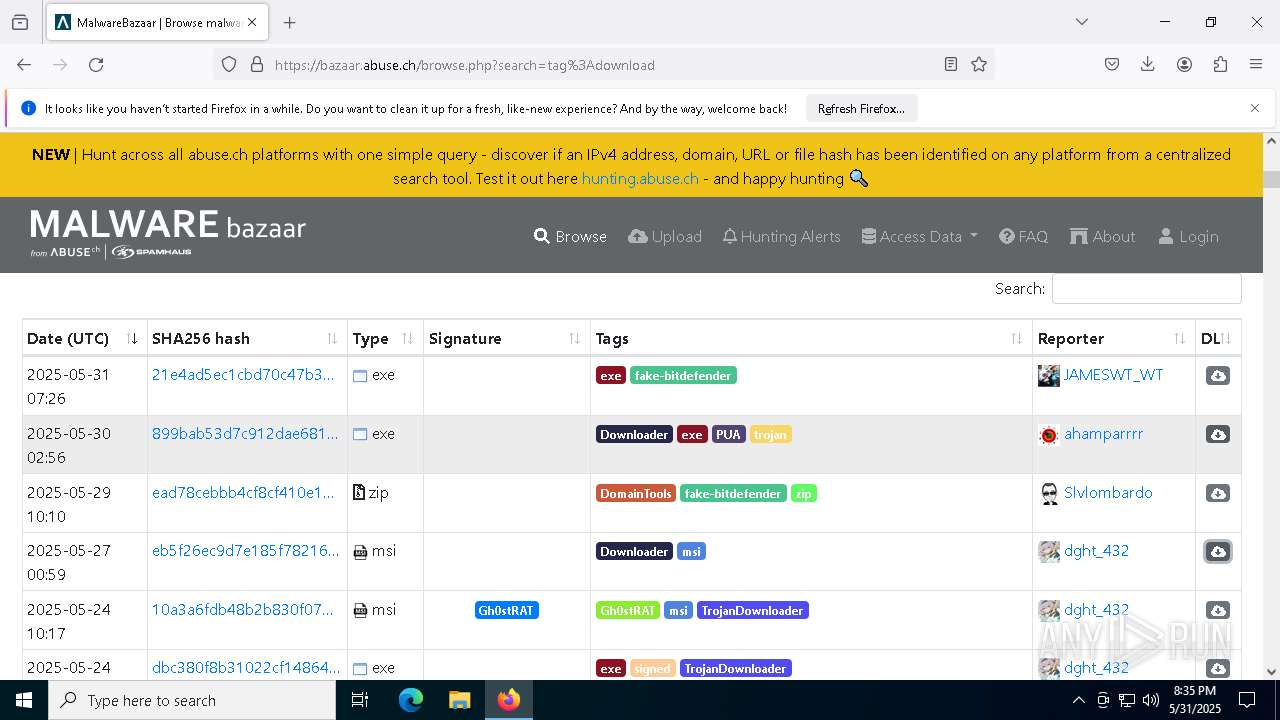
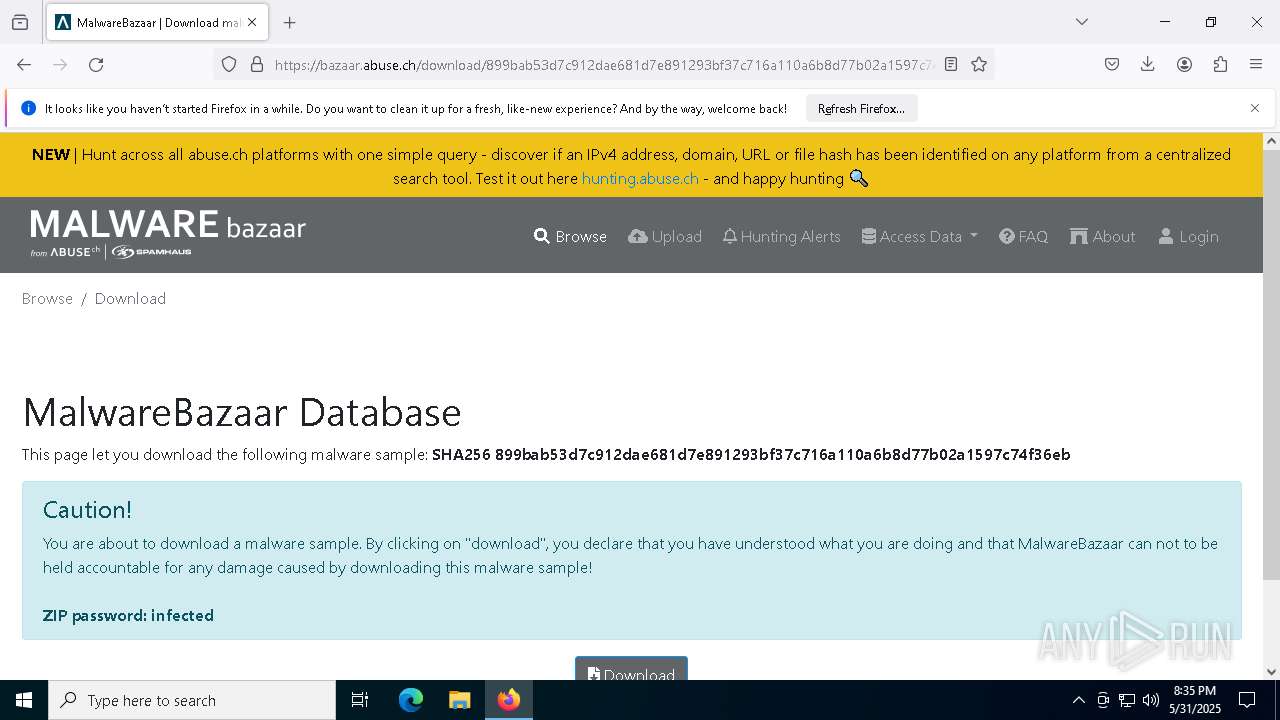
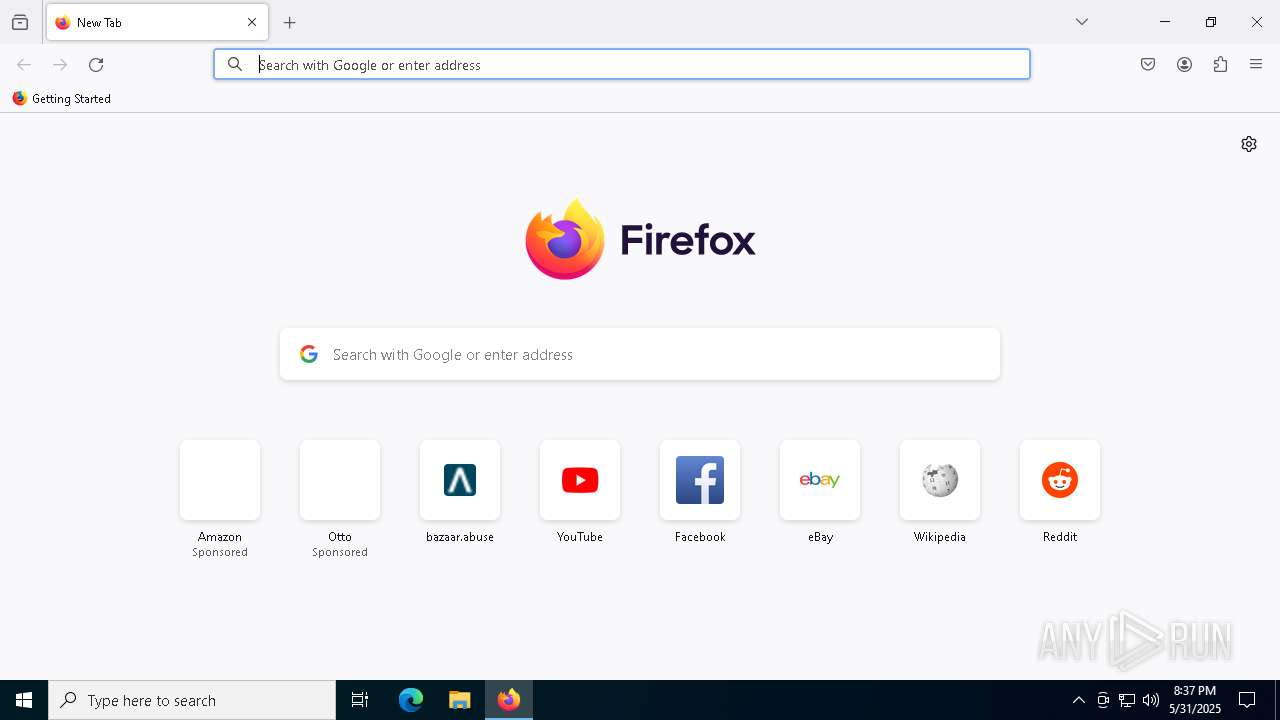
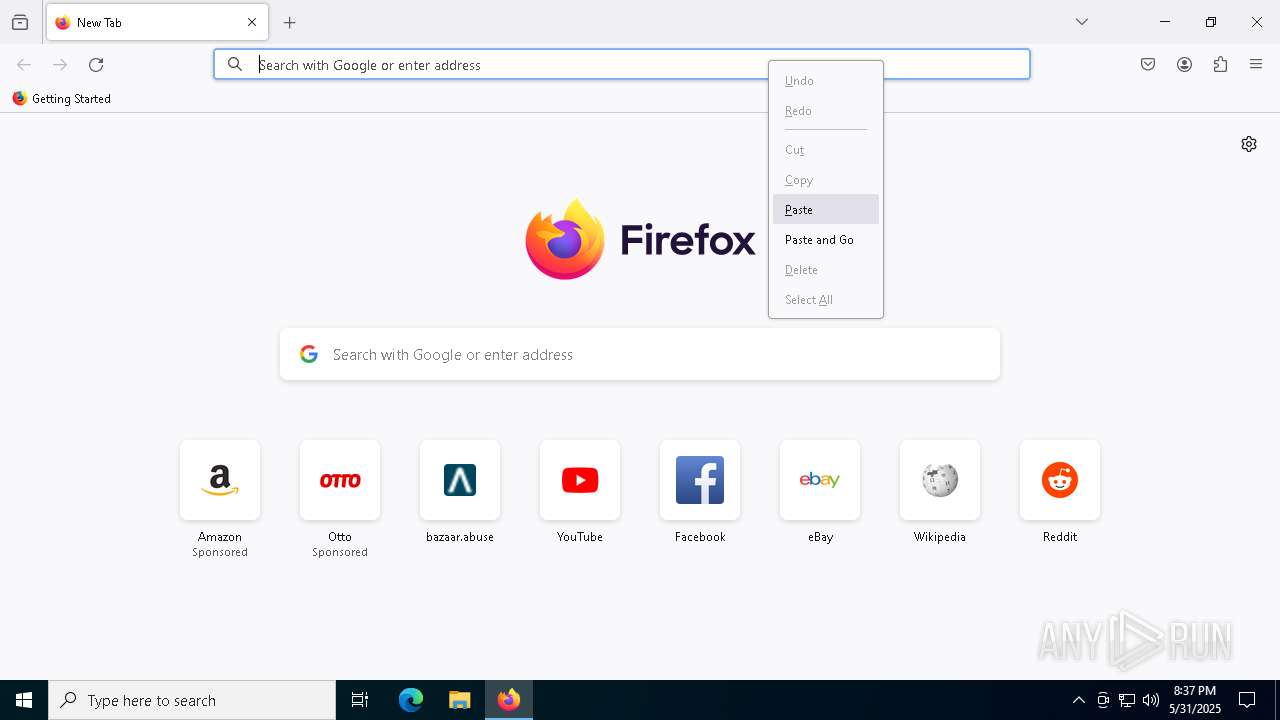
| URL: | https://bazaar.abuse.ch/browse.php?search=tag%3APUP |
| Full analysis: | https://app.any.run/tasks/e8d65da3-31a6-424a-bf6b-760e9fb3e99f |
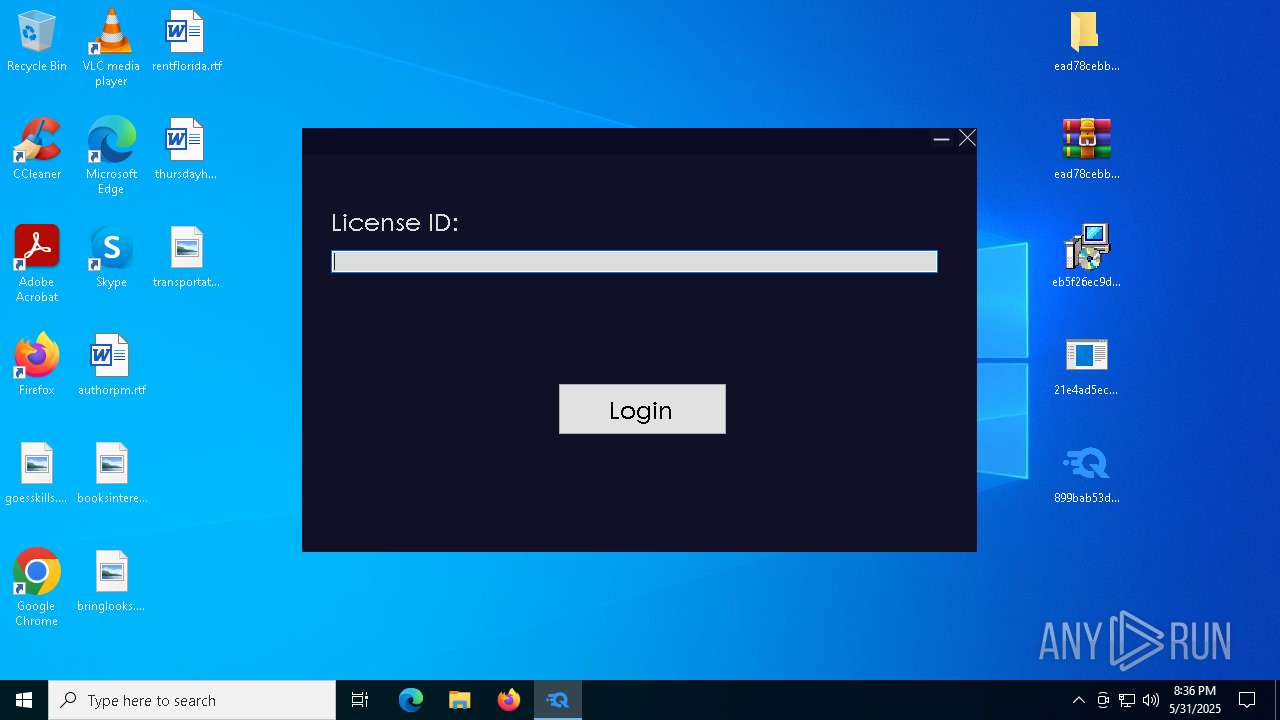
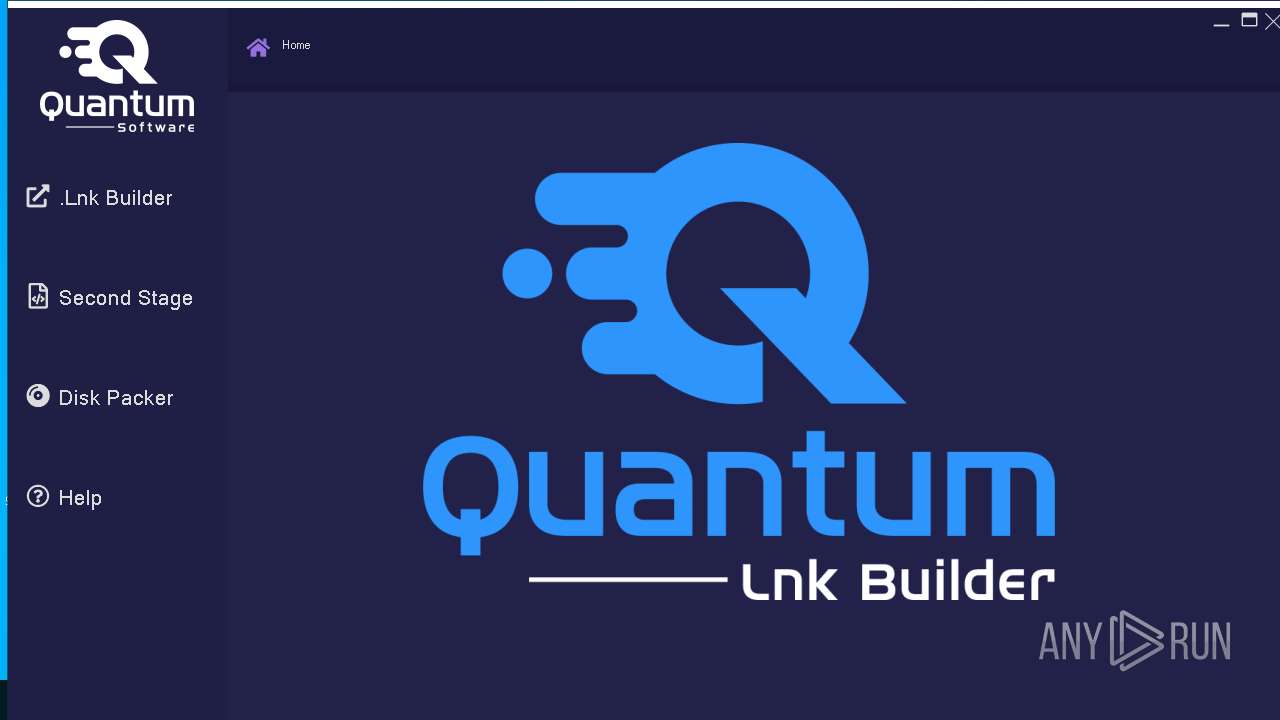
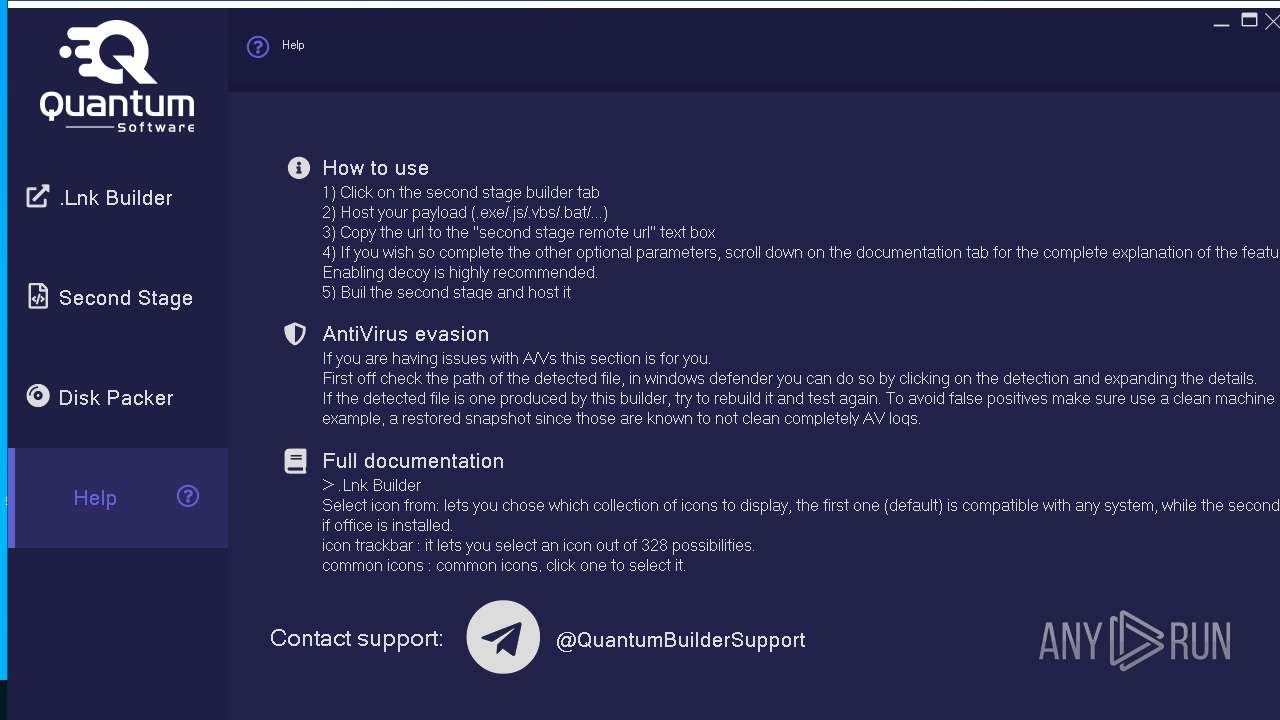
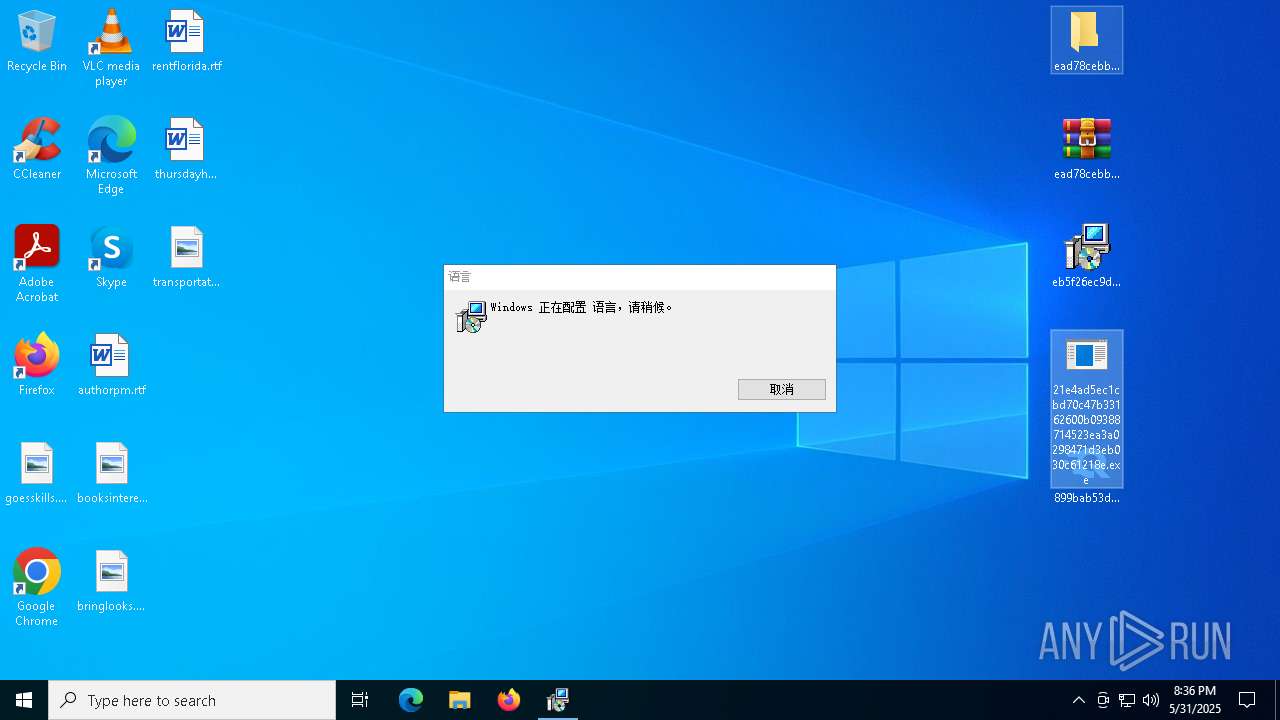
| Verdict: | Malicious activity |
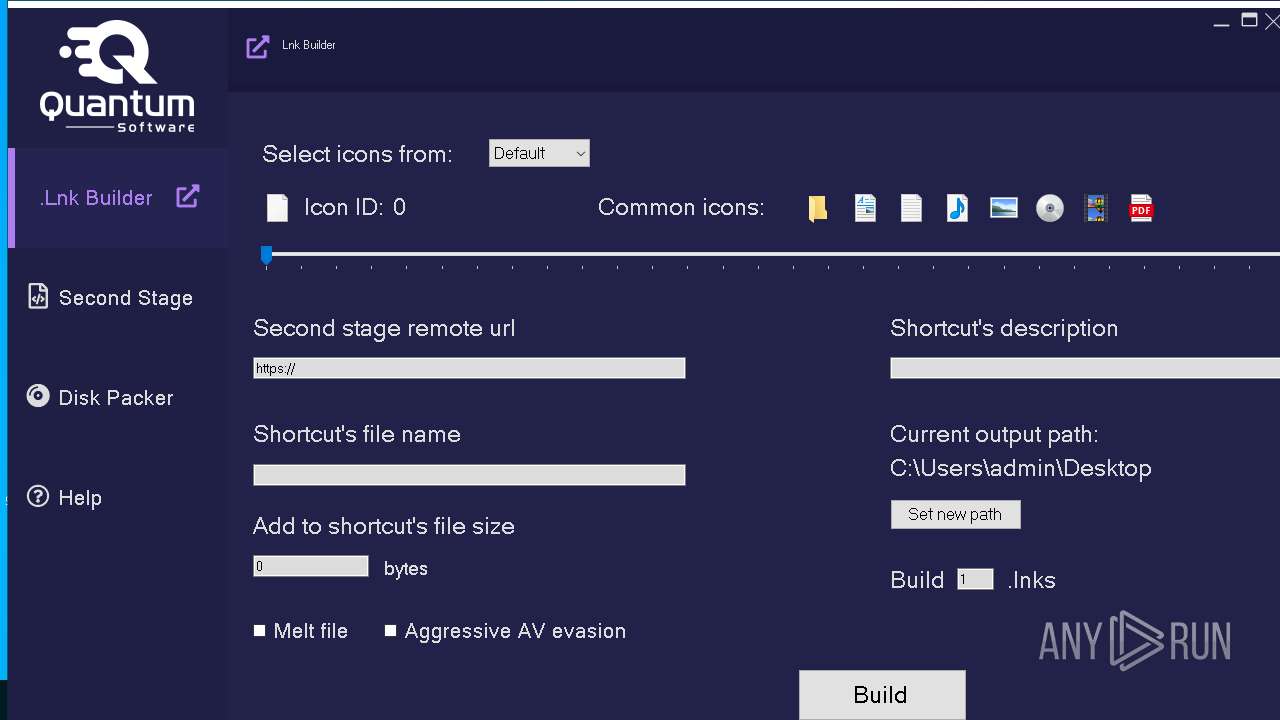
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 31, 2025, 20:33:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DA7C0ABFB89AE8B146D06BF17AA881FA |
| SHA1: | CE899A23B1DC25CE687CFA184FDBE1B14C5E2437 |
| SHA256: | 2779D6C8C78A57145EF7CB73FD18BE66B075C9C8E40CE05D03FFABB76CDA57ED |
| SSDEEP: | 3:N8N0uDWHXKAVdhWX61:23AaYHWX61 |
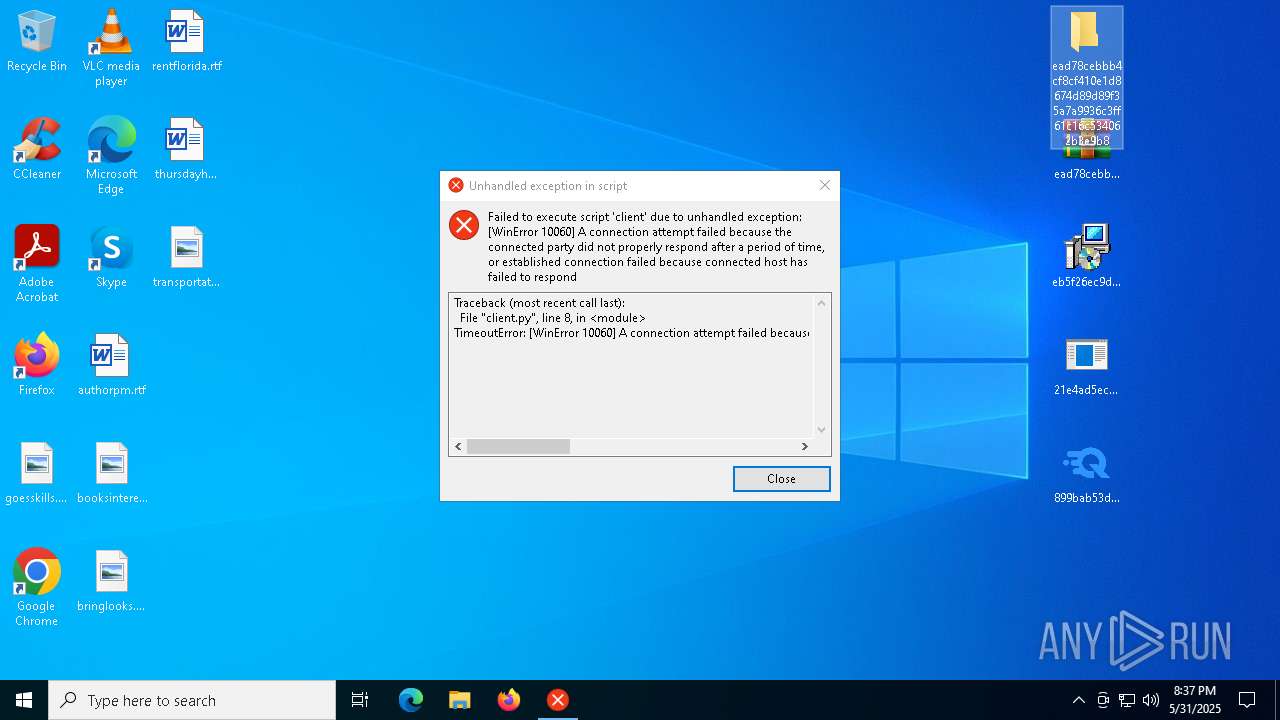
MALICIOUS
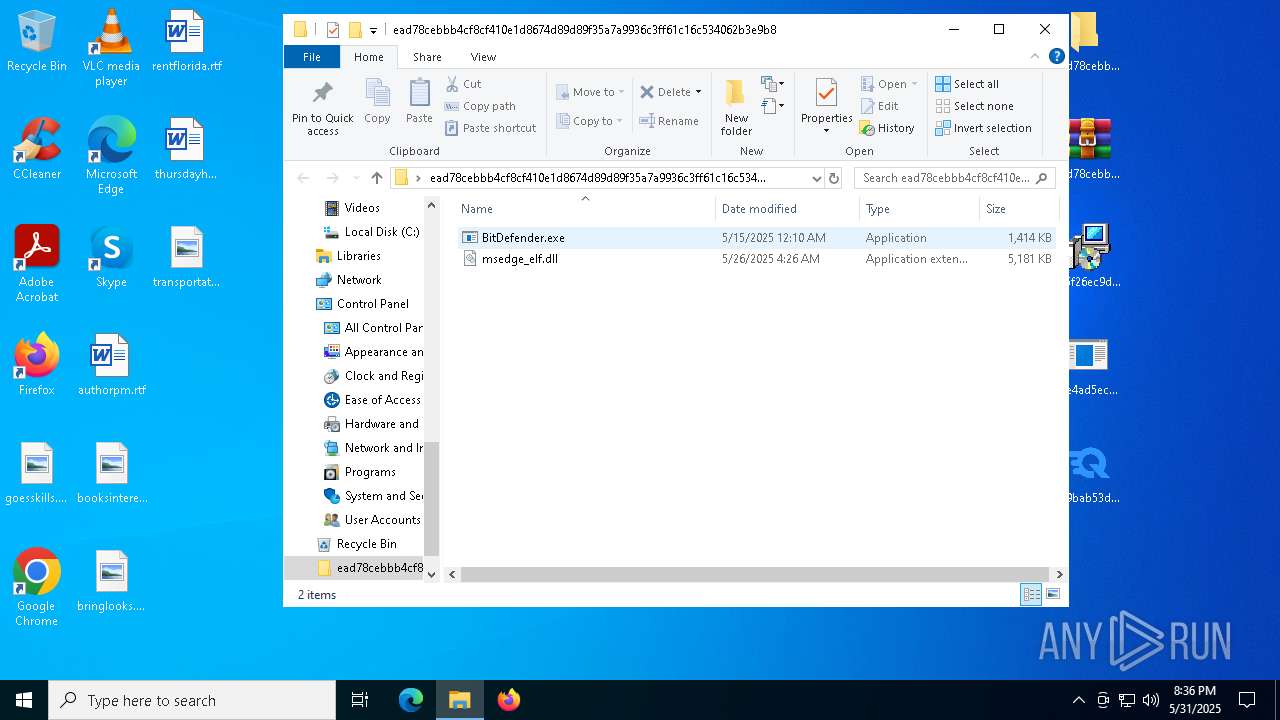
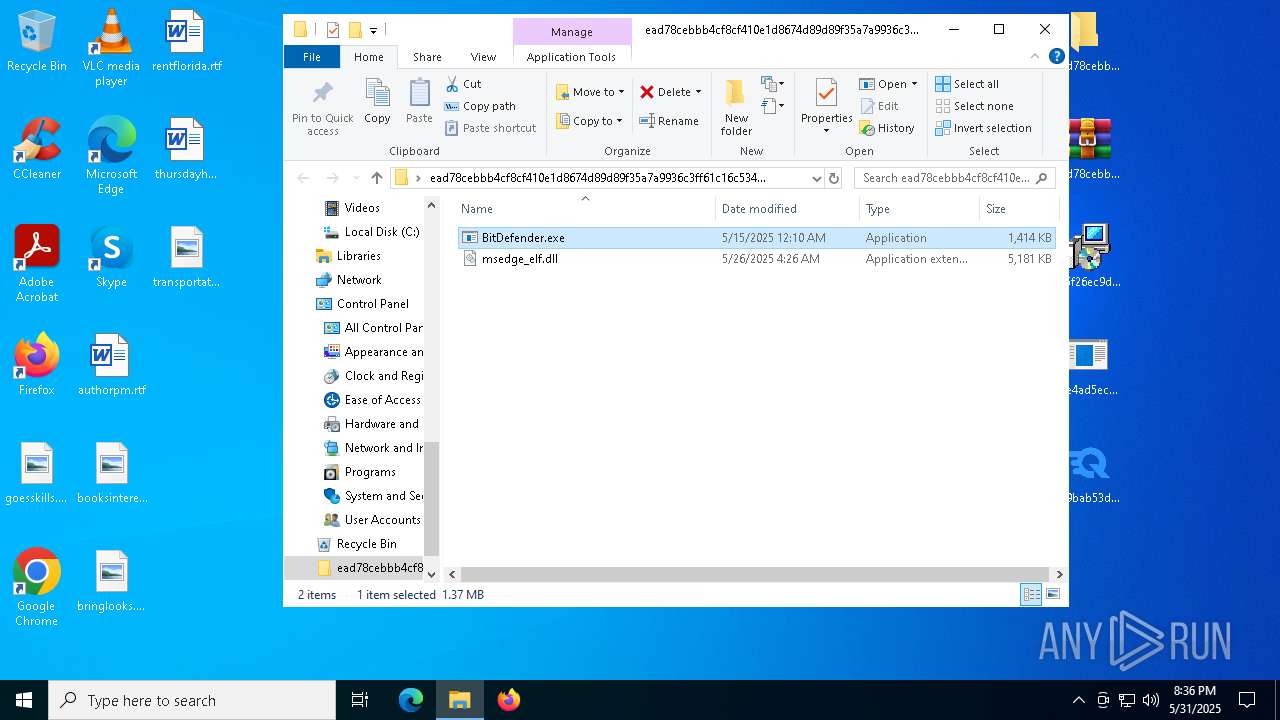
Antivirus name has been found in the command line (generic signature)
- BitDefender.exe (PID: 8724)
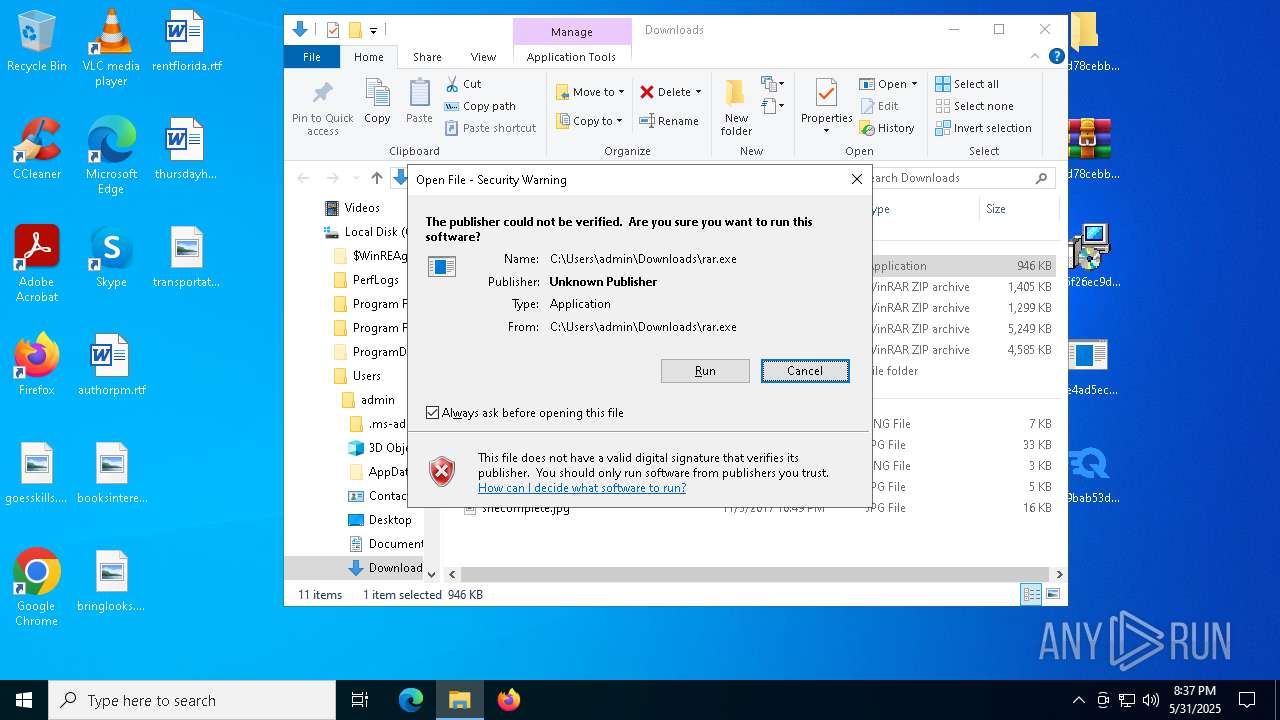
Executing a file with an untrusted certificate
- side.exe (PID: 6880)
- side.exe (PID: 8908)
GENERIC has been found (auto)
- BitDefender.exe (PID: 8724)
- side.exe (PID: 6880)
AHK has been detected (YARA)
- url.exe (PID: 9008)
SUSPICIOUS
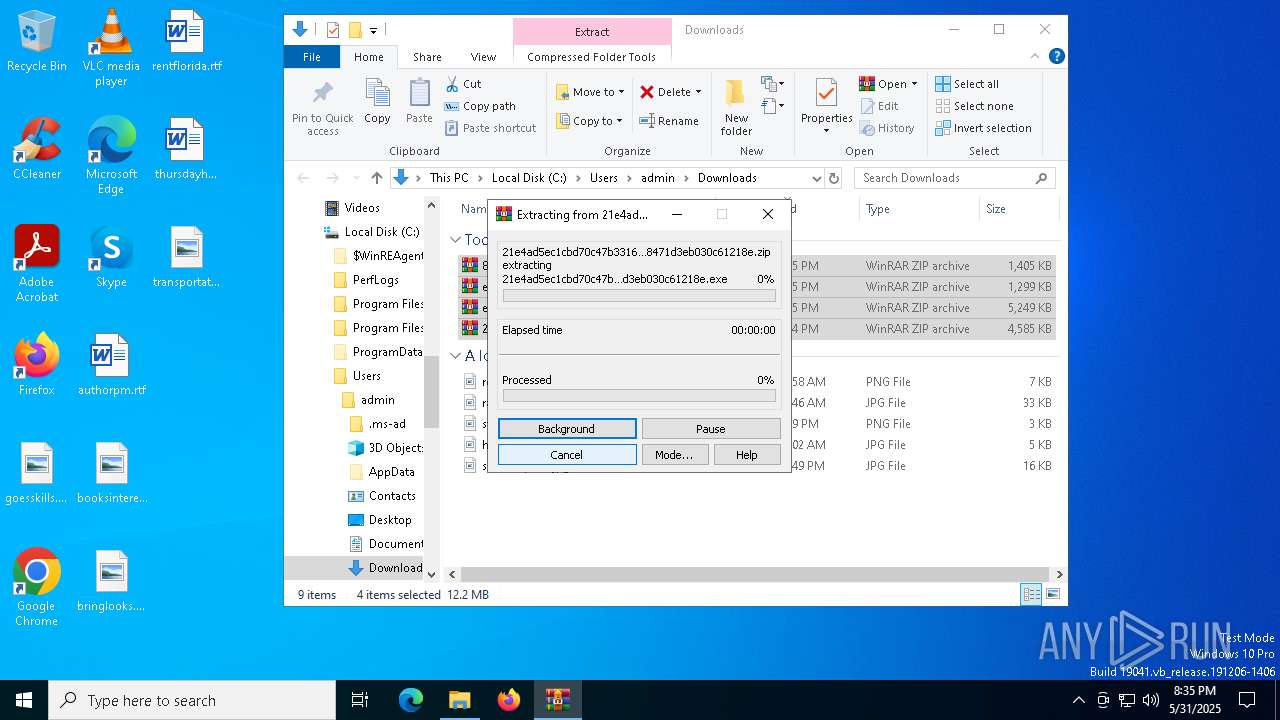
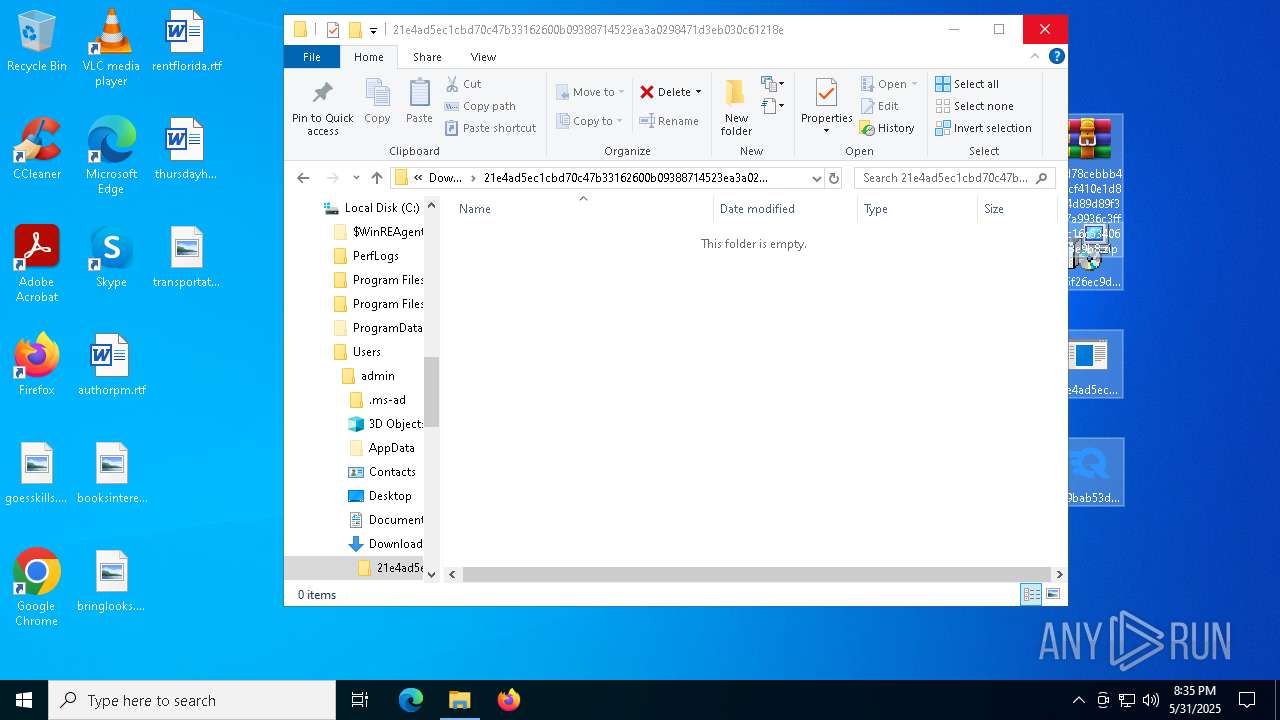
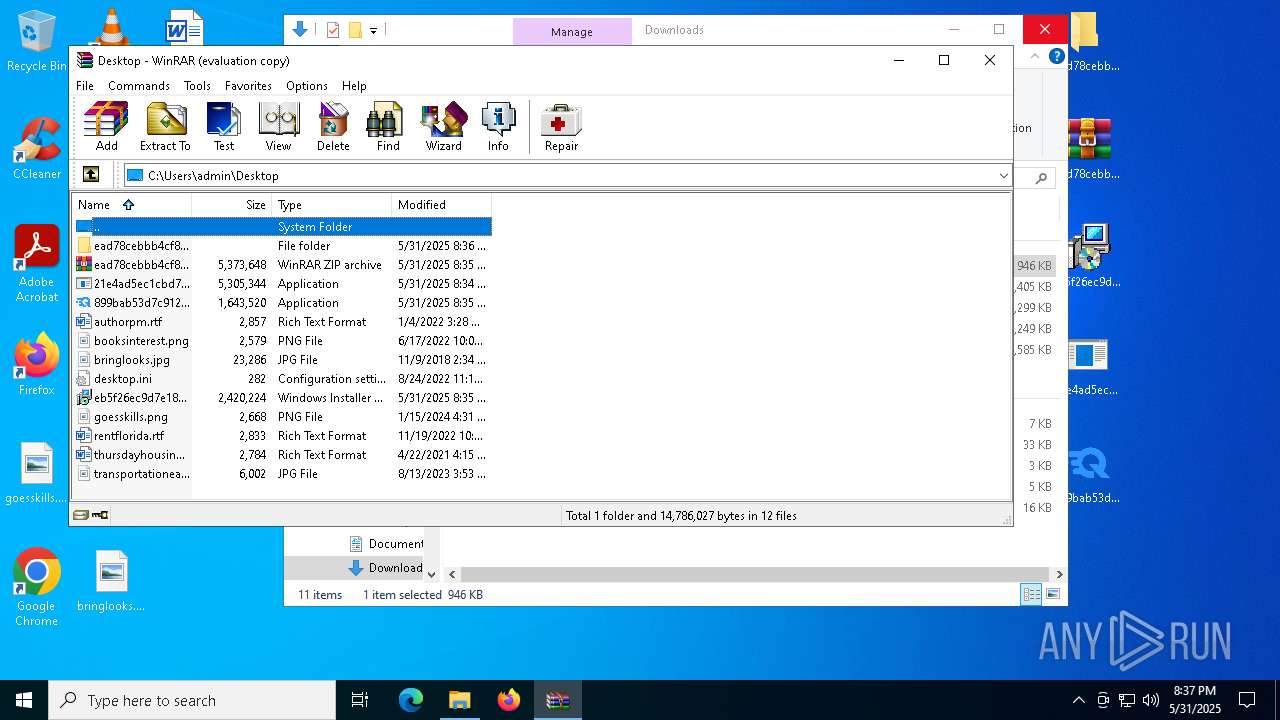
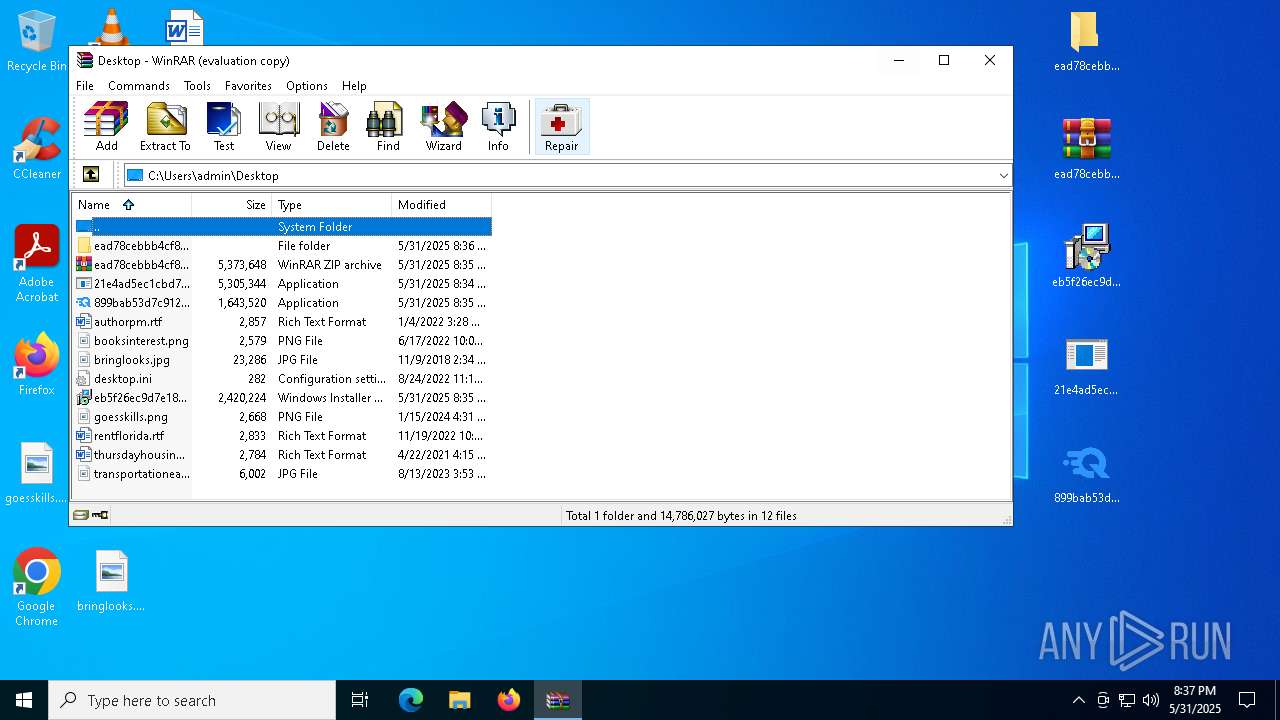
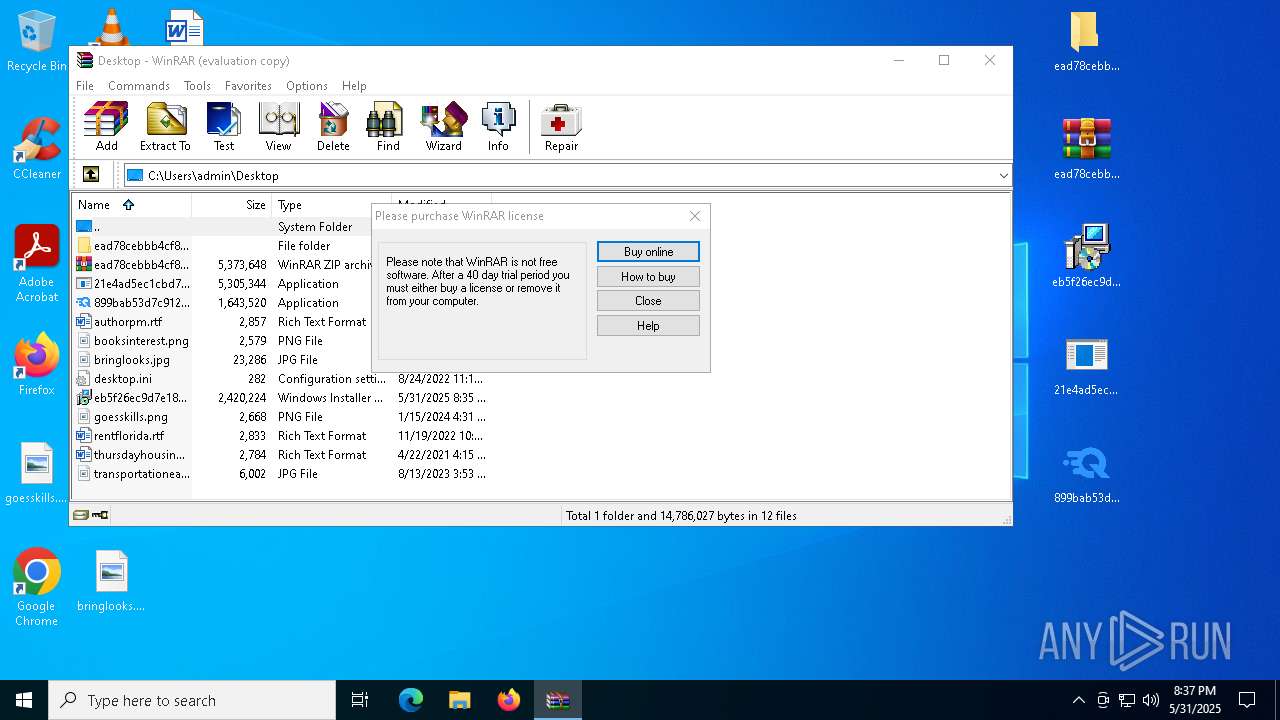
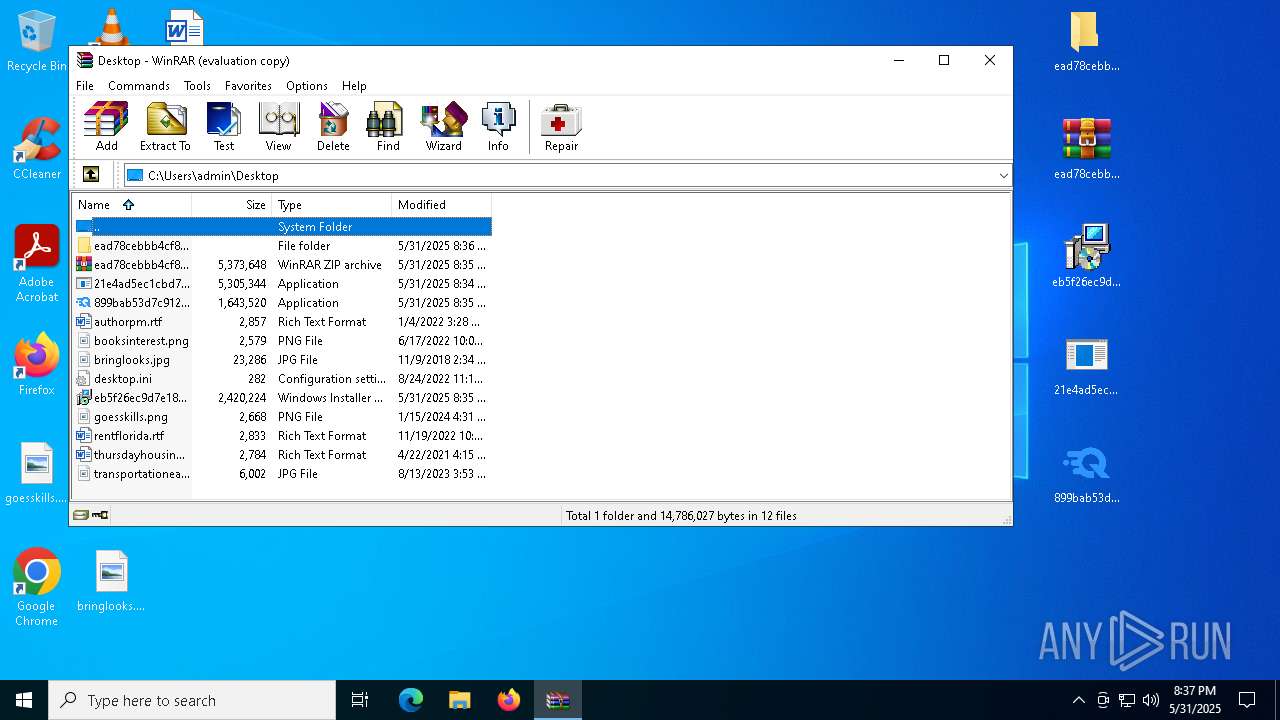
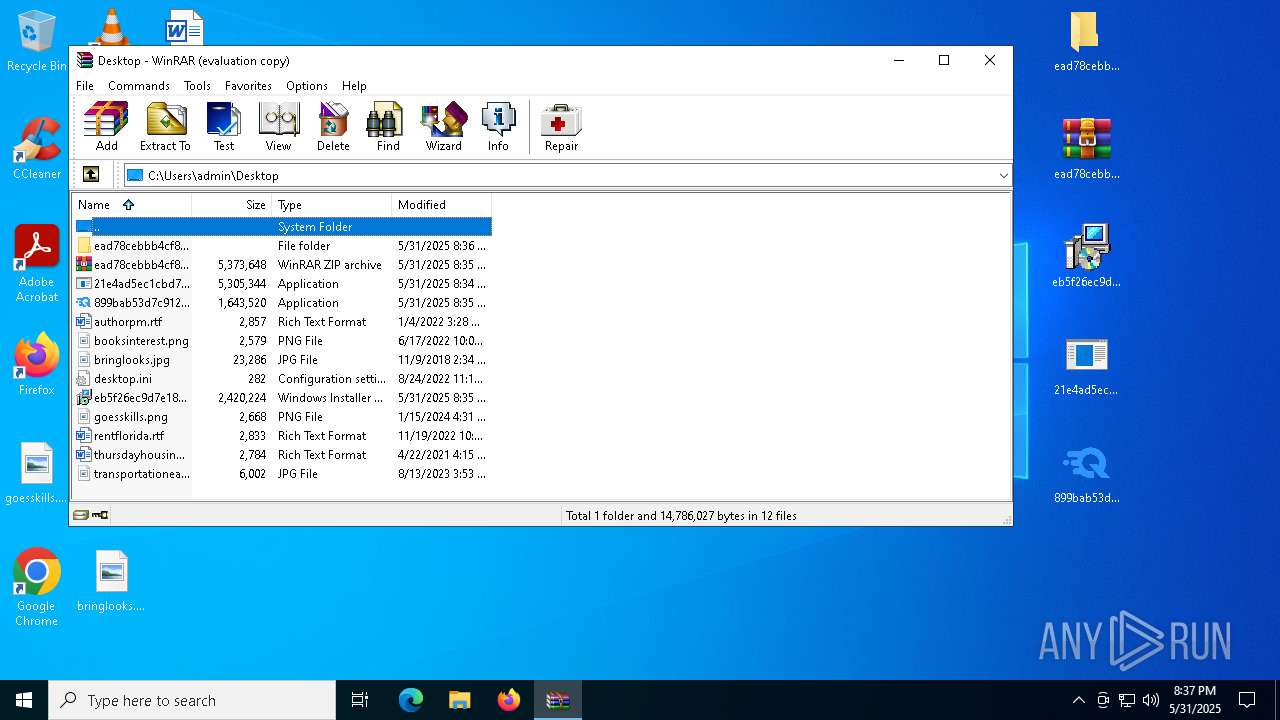
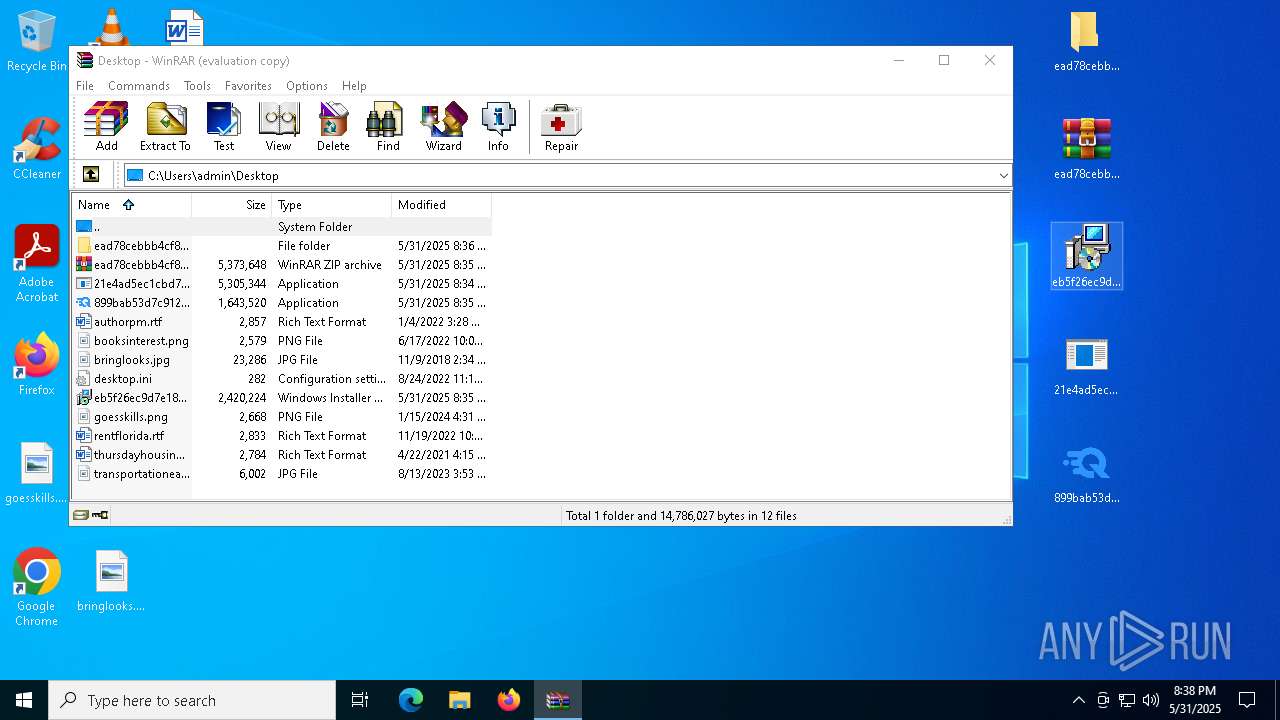
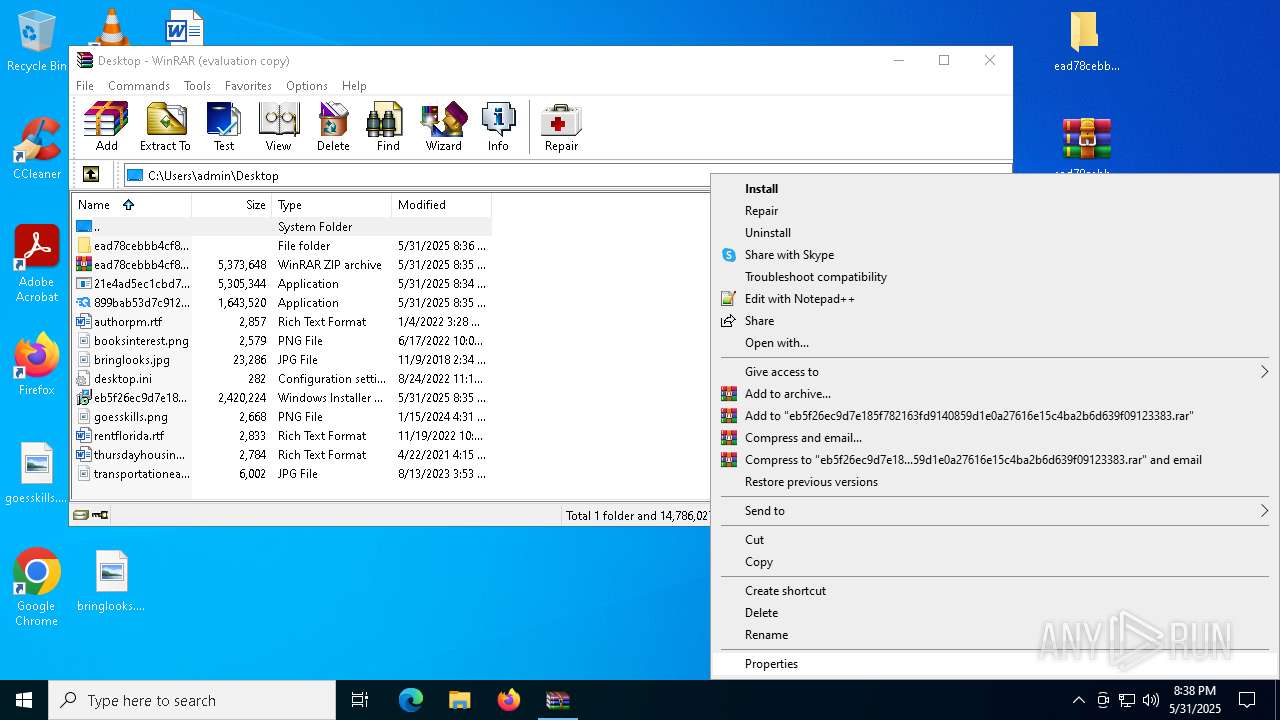
Process drops legitimate windows executable
- firefox.exe (PID: 7816)
- WinRAR.exe (PID: 7636)
- WinRAR.exe (PID: 2384)
- side.exe (PID: 6880)
- url.exe (PID: 9008)
There is functionality for taking screenshot (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
- url.exe (PID: 9008)
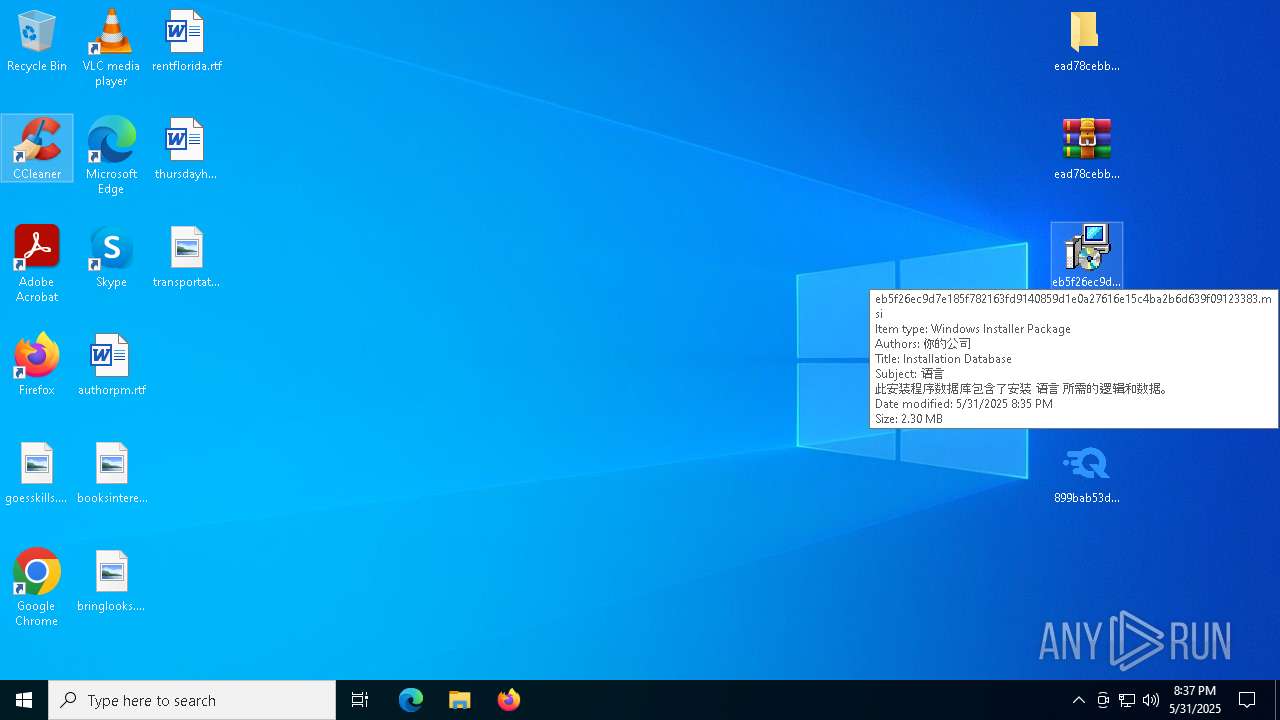
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 8476)
Executes as Windows Service
- VSSVC.exe (PID: 5984)
Likely accesses (executes) a file from the Public directory
- url.exe (PID: 9008)
- MSID873.tmp (PID: 8936)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 5344)
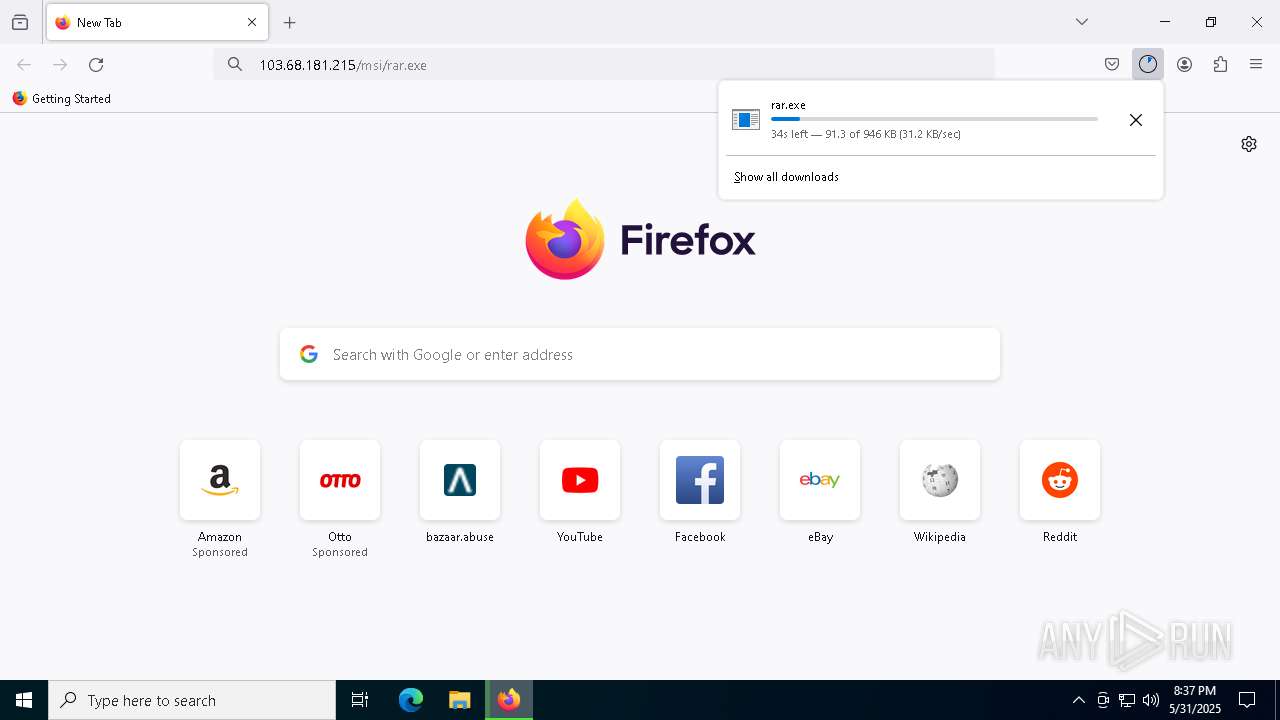
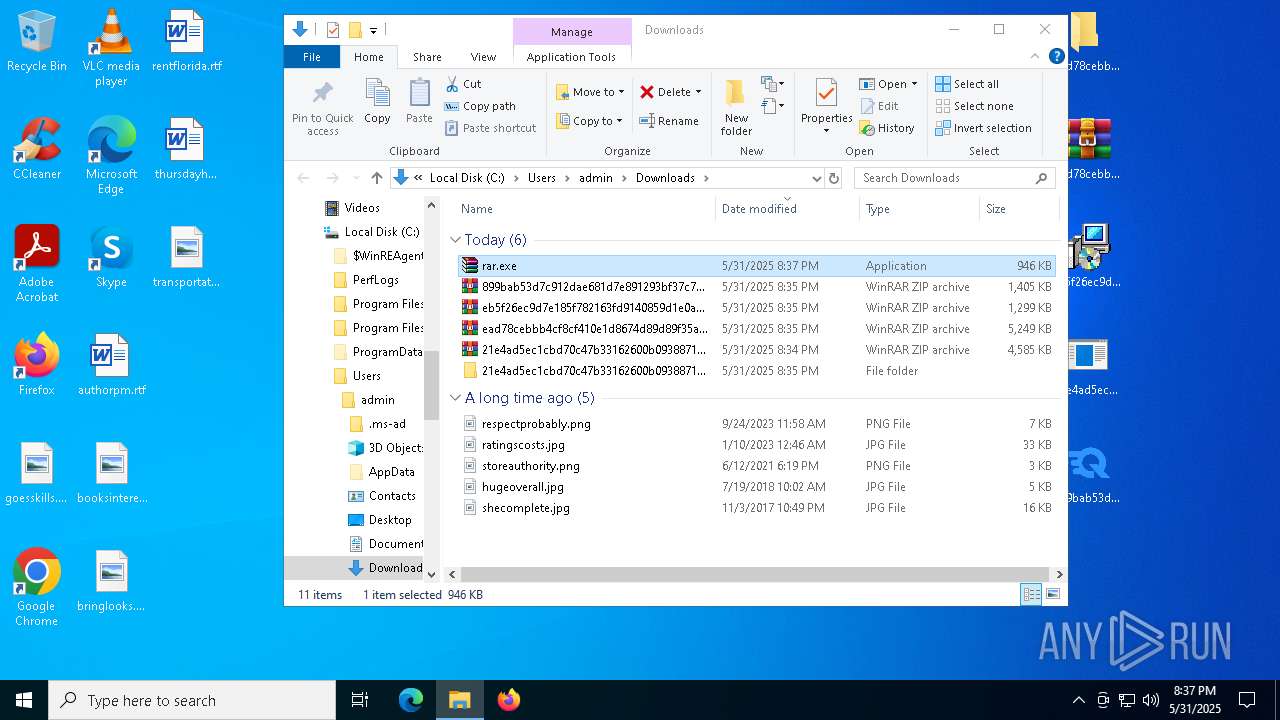
- rar.exe (PID: 4452)
- cc.exe (PID: 7676)
Starts CMD.EXE for commands execution
- MSID873.tmp (PID: 8936)
- url.exe (PID: 9008)
Executable content was dropped or overwritten
- BitDefender.exe (PID: 8724)
- side.exe (PID: 6880)
- url.exe (PID: 9008)
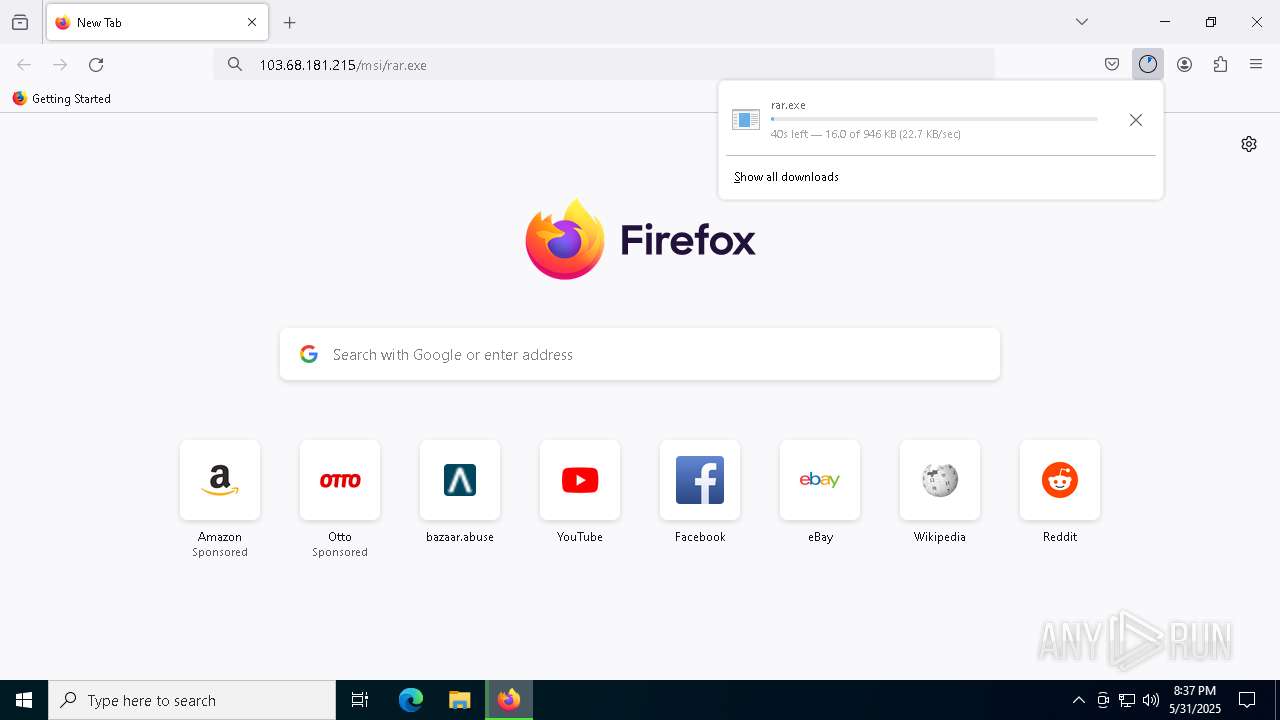
- rar.exe (PID: 4452)
Starts a Microsoft application from unusual location
- BitDefender.exe (PID: 8724)
- cc.exe (PID: 7676)
The process drops C-runtime libraries
- side.exe (PID: 6880)
Process drops python dynamic module
- side.exe (PID: 6880)
- rar.exe (PID: 4452)
Application launched itself
- side.exe (PID: 6880)
Connects to unusual port
- side.exe (PID: 8908)
Potential Corporate Privacy Violation
- url.exe (PID: 9008)
- firefox.exe (PID: 5380)
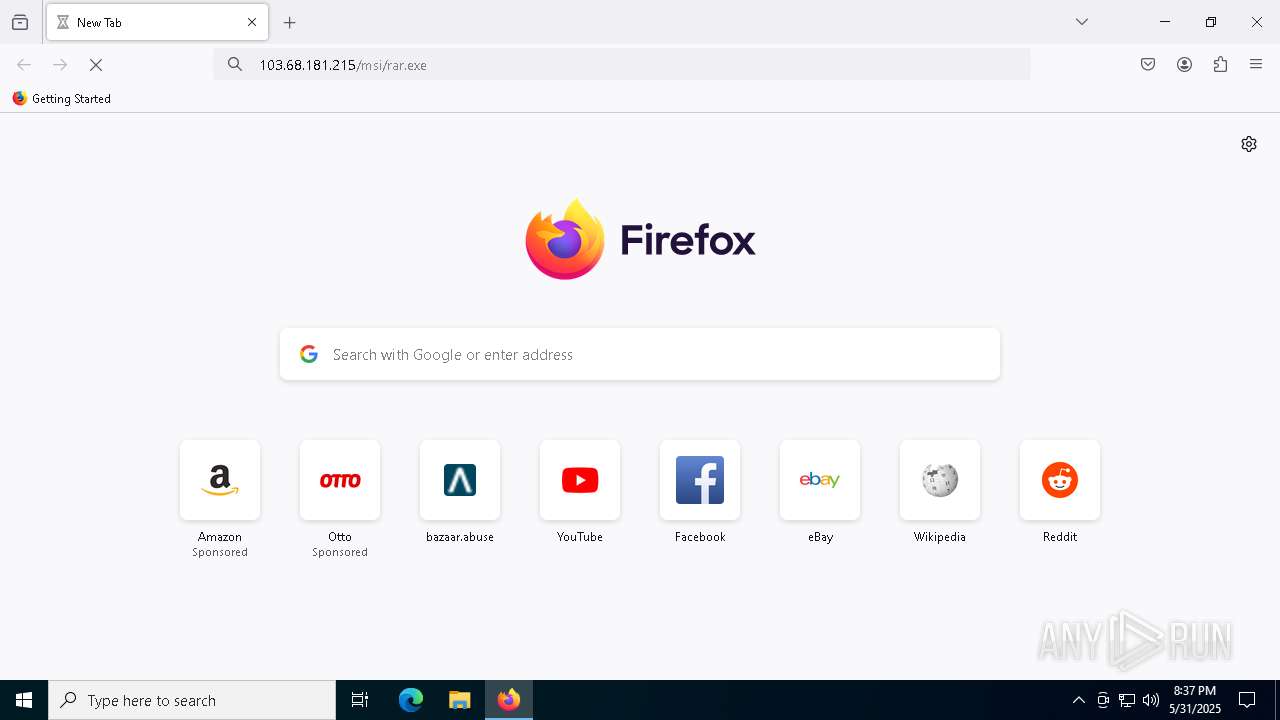
Process requests binary or script from the Internet
- url.exe (PID: 9008)
Connects to the server without a host name
- url.exe (PID: 9008)
INFO
Application launched itself
- firefox.exe (PID: 7360)
- firefox.exe (PID: 7816)
- firefox.exe (PID: 5380)
- firefox.exe (PID: 7208)
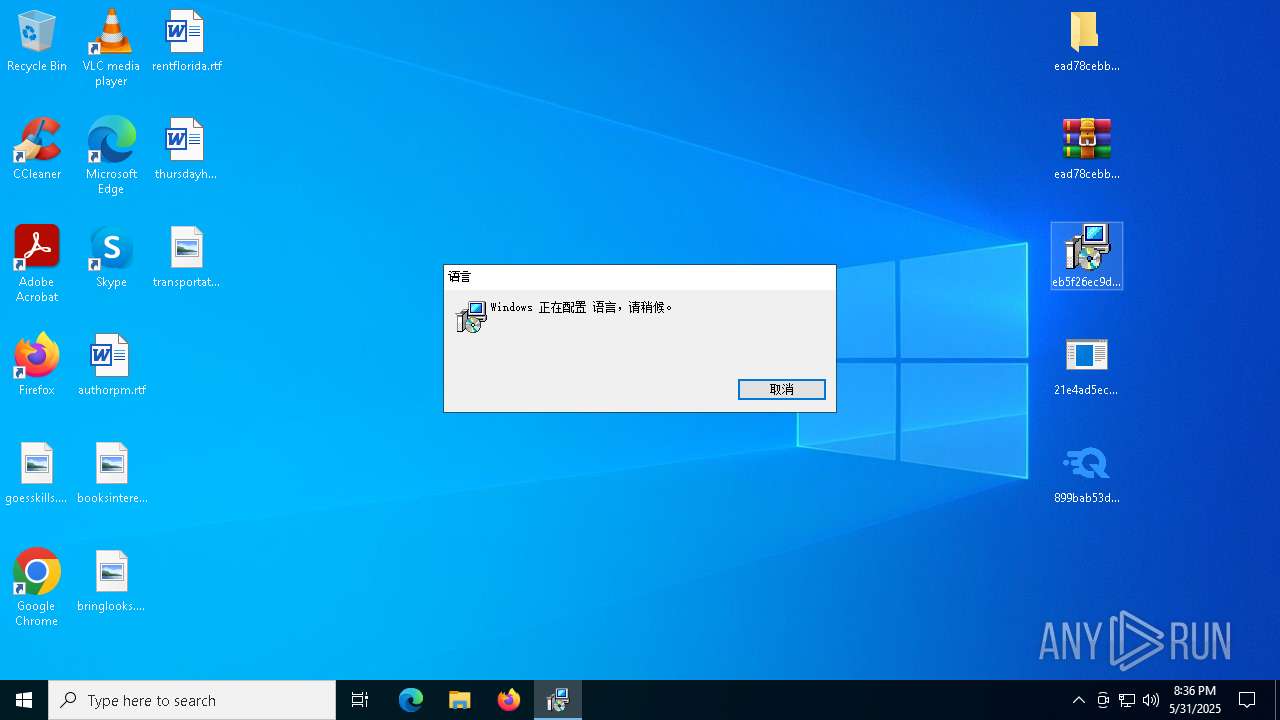
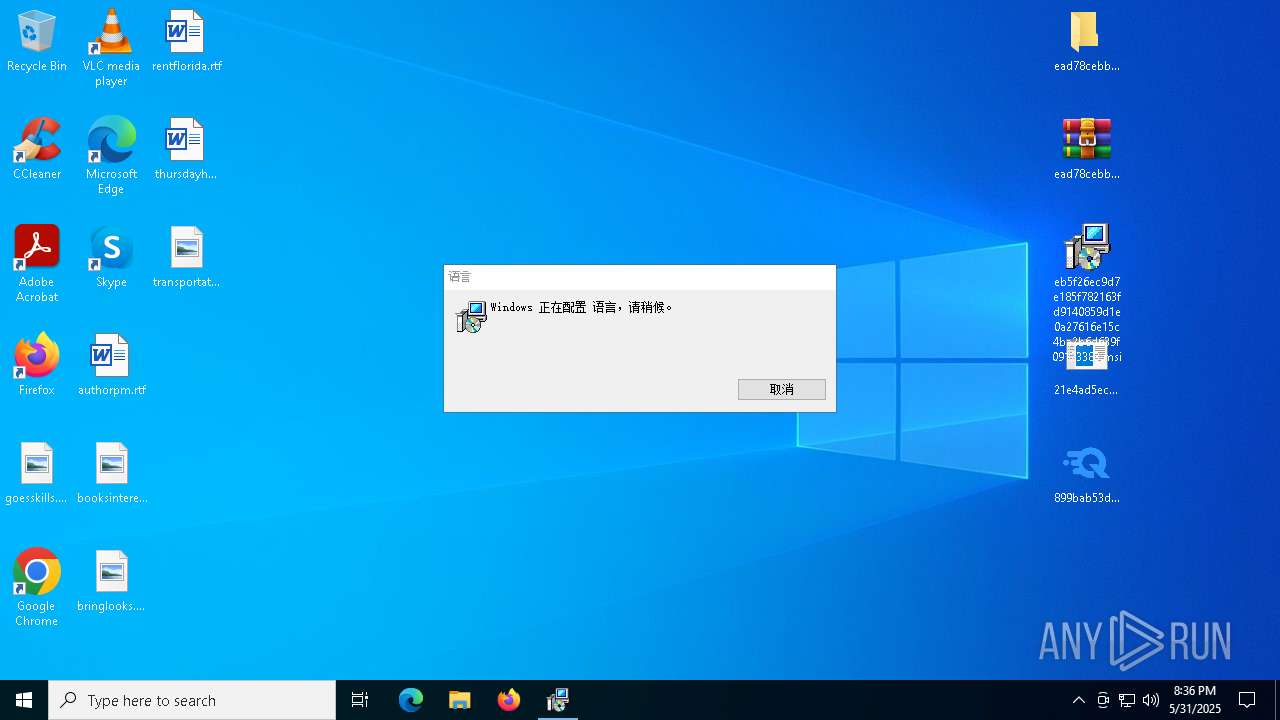
Reads the software policy settings
- slui.exe (PID: 2516)
The sample compiled with english language support
- firefox.exe (PID: 7816)
- WinRAR.exe (PID: 7636)
- WinRAR.exe (PID: 2384)
- msiexec.exe (PID: 6192)
- side.exe (PID: 6880)
- url.exe (PID: 9008)
- firefox.exe (PID: 5380)
- rar.exe (PID: 4452)
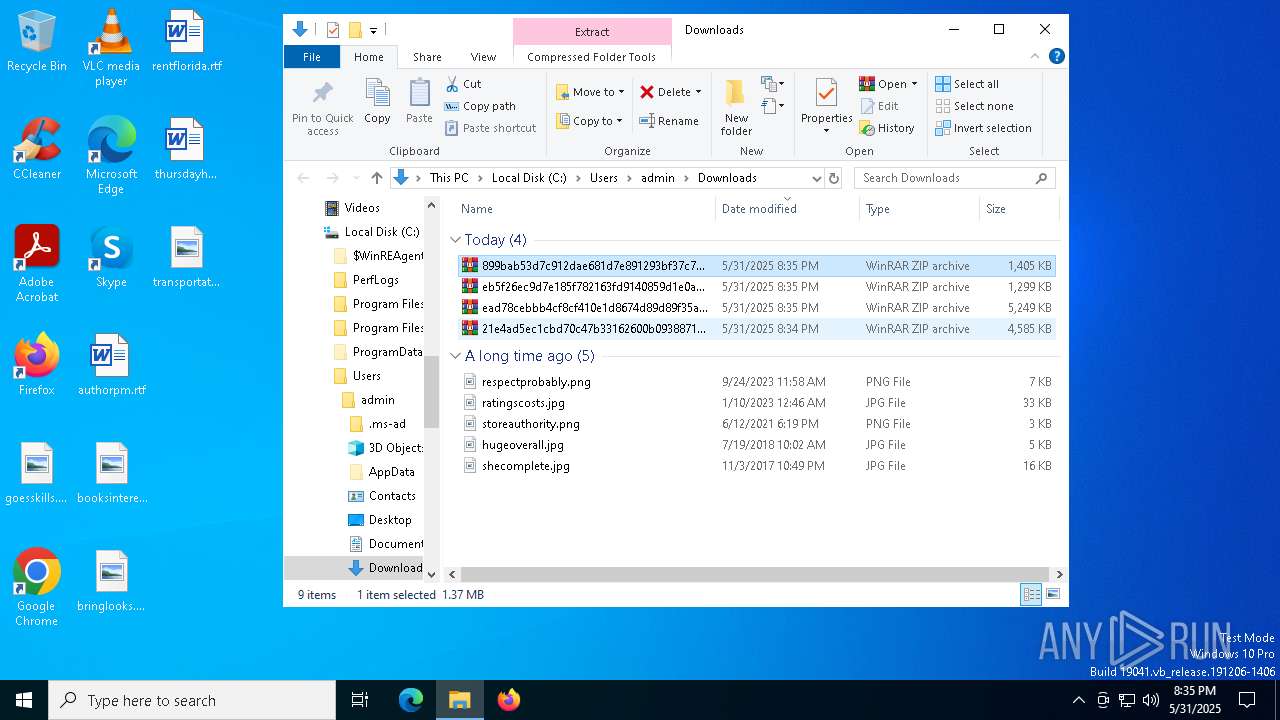
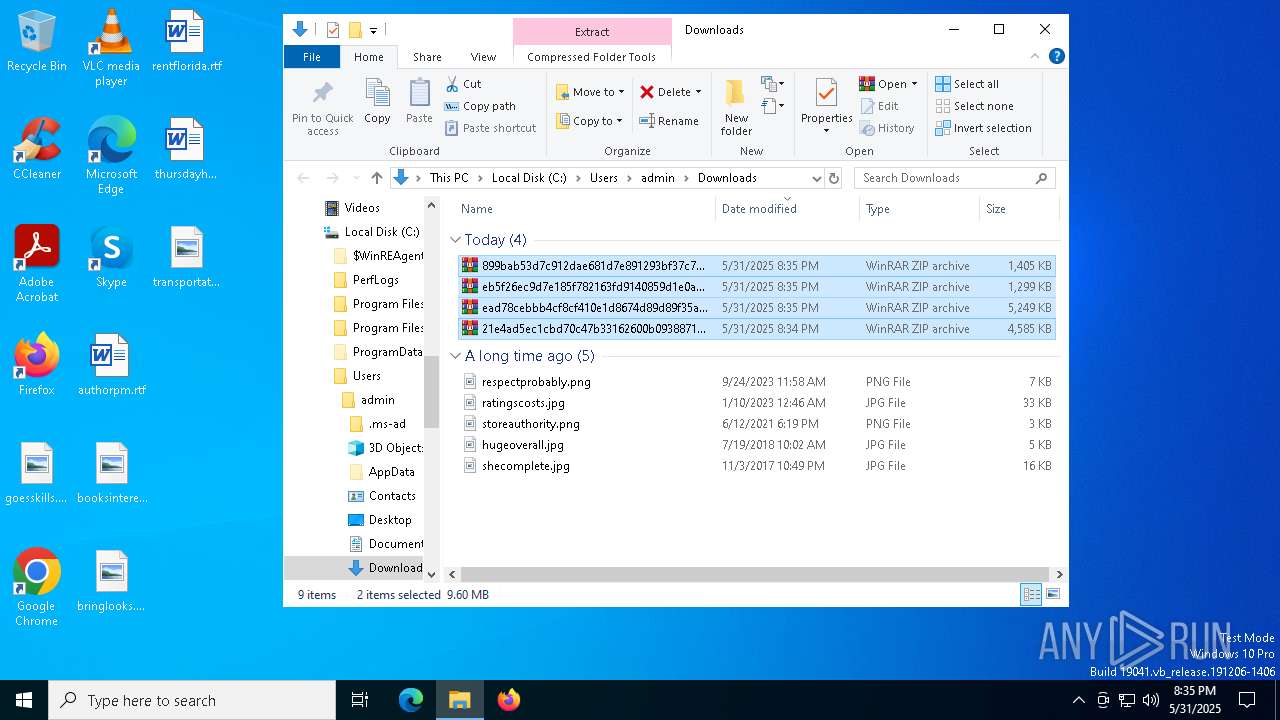
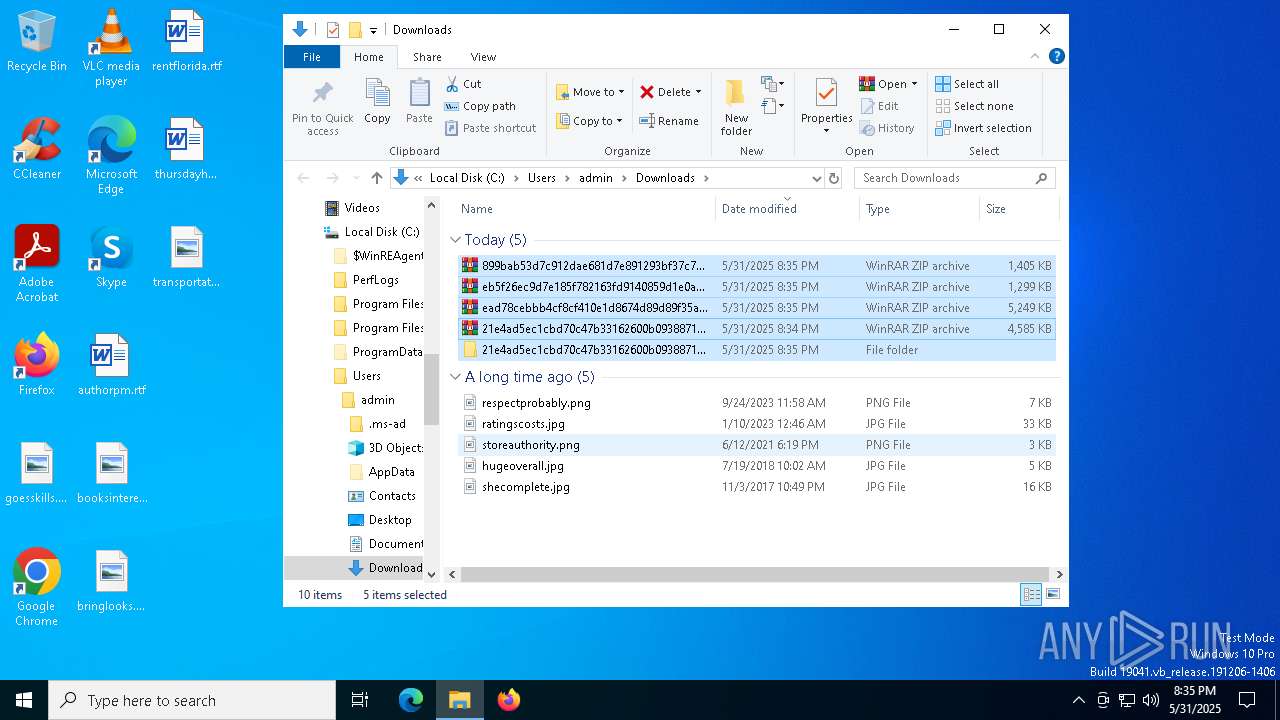
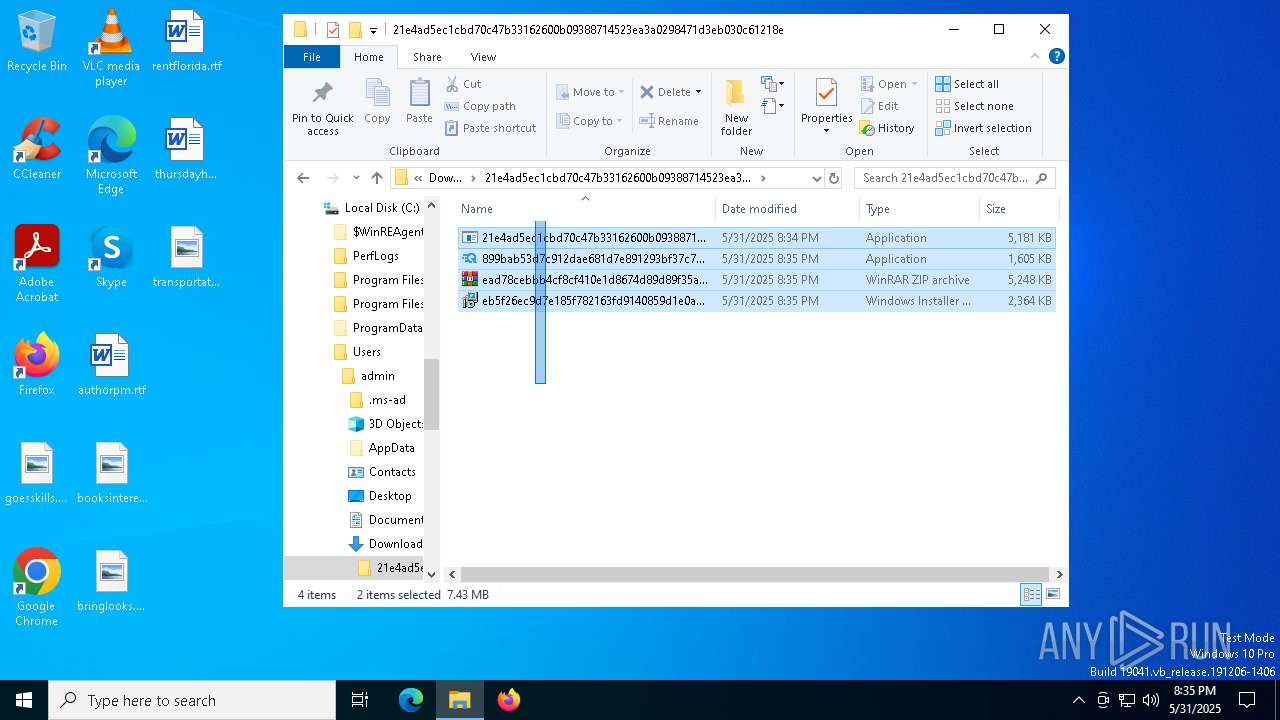
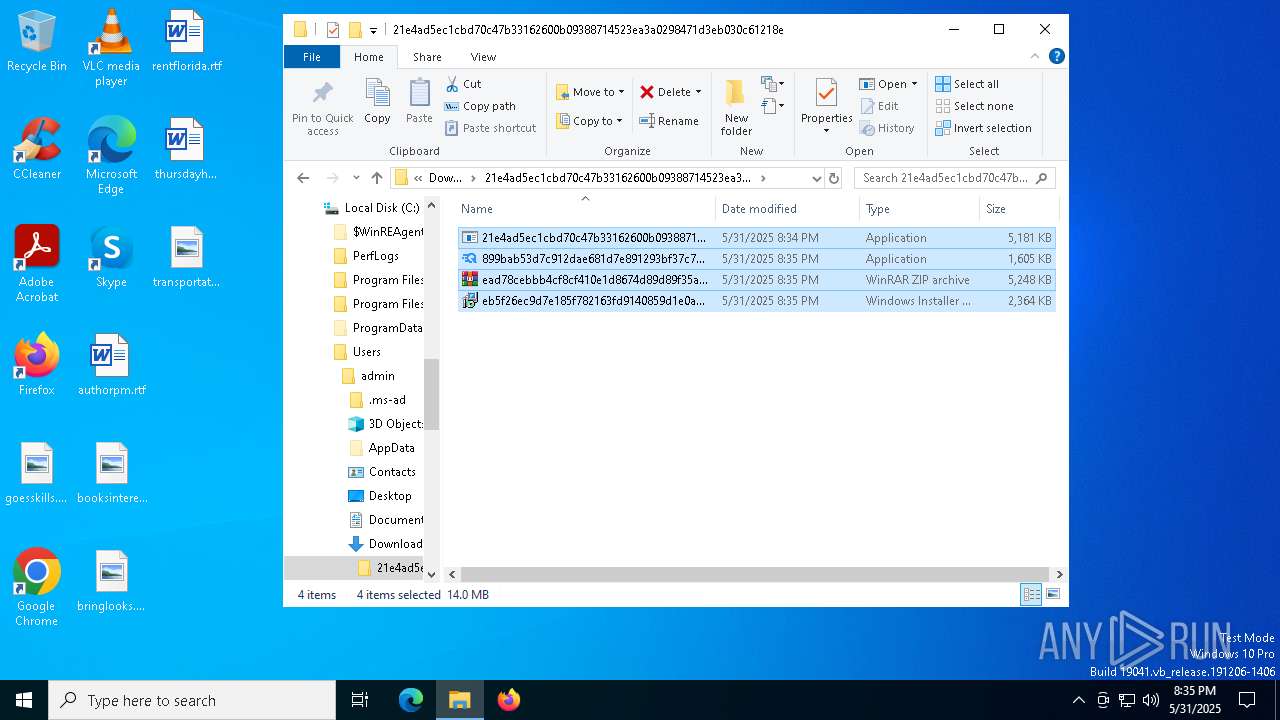
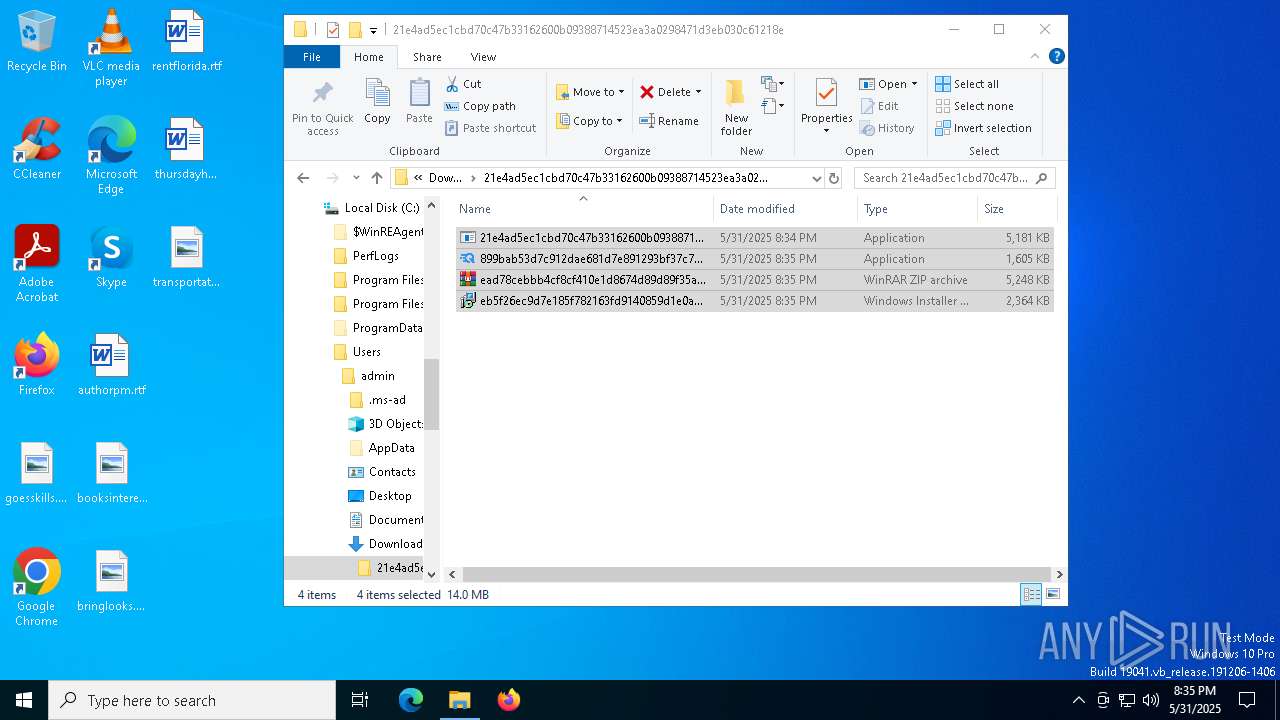
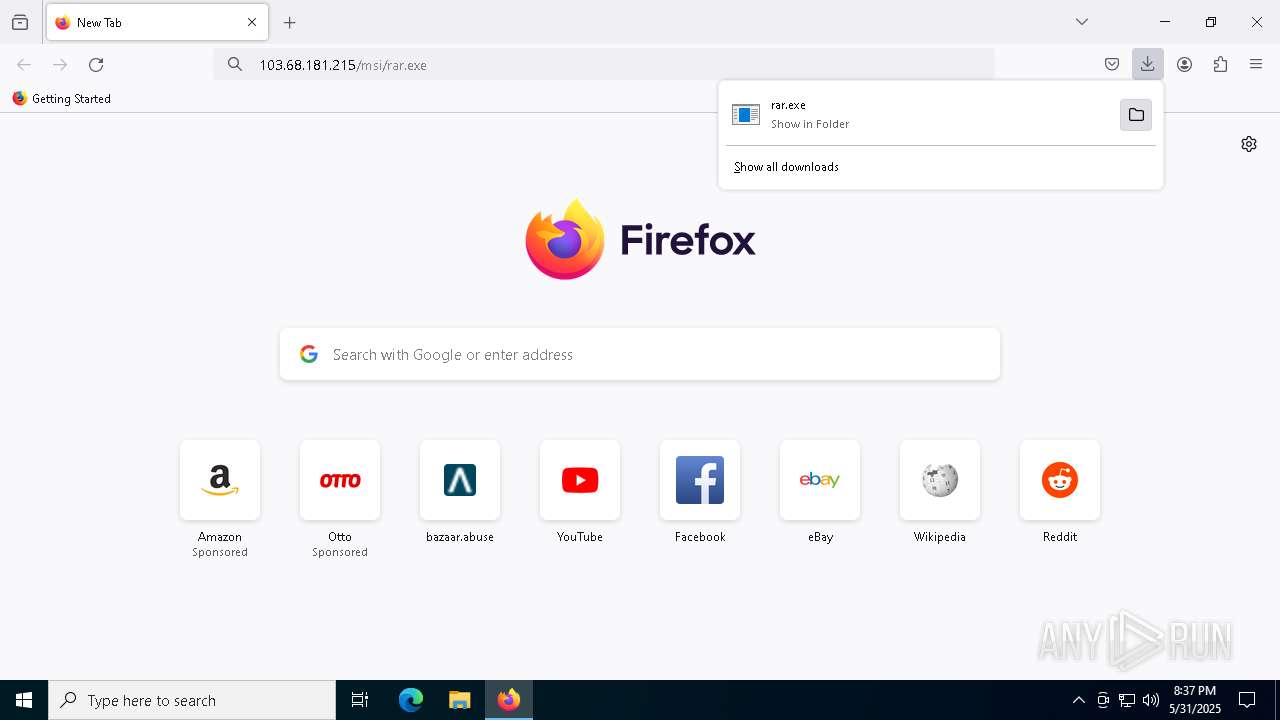
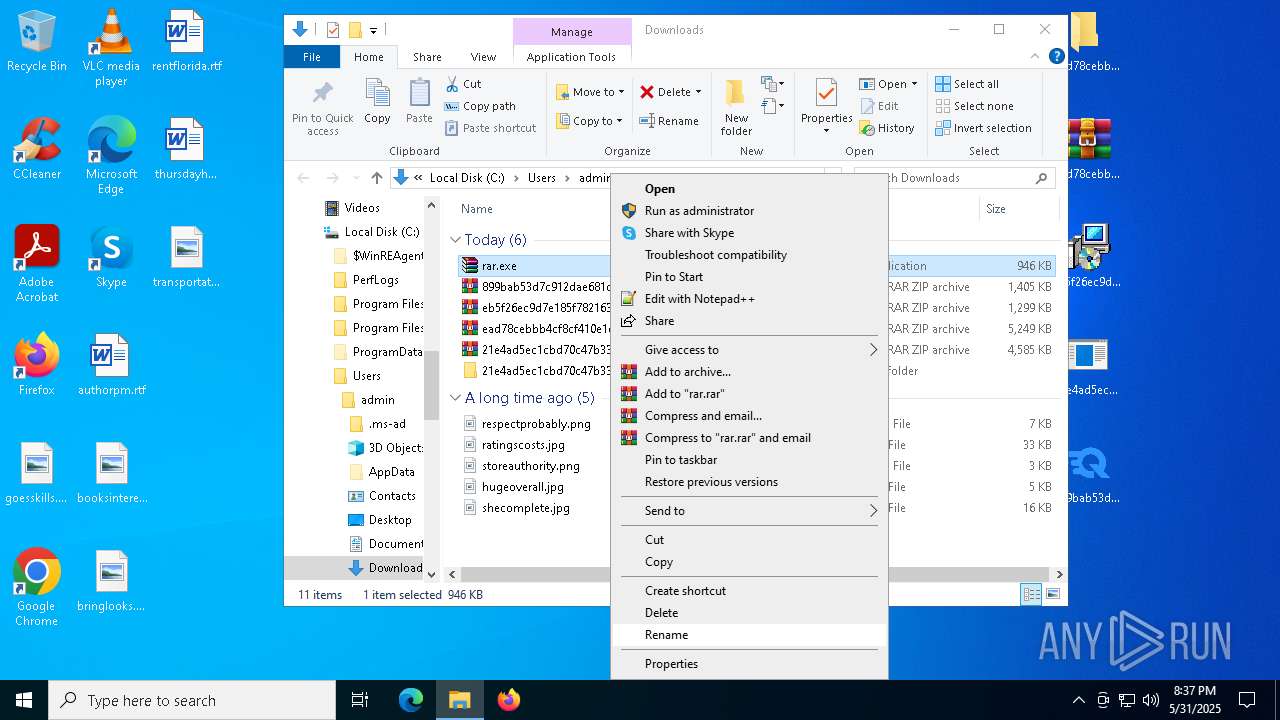
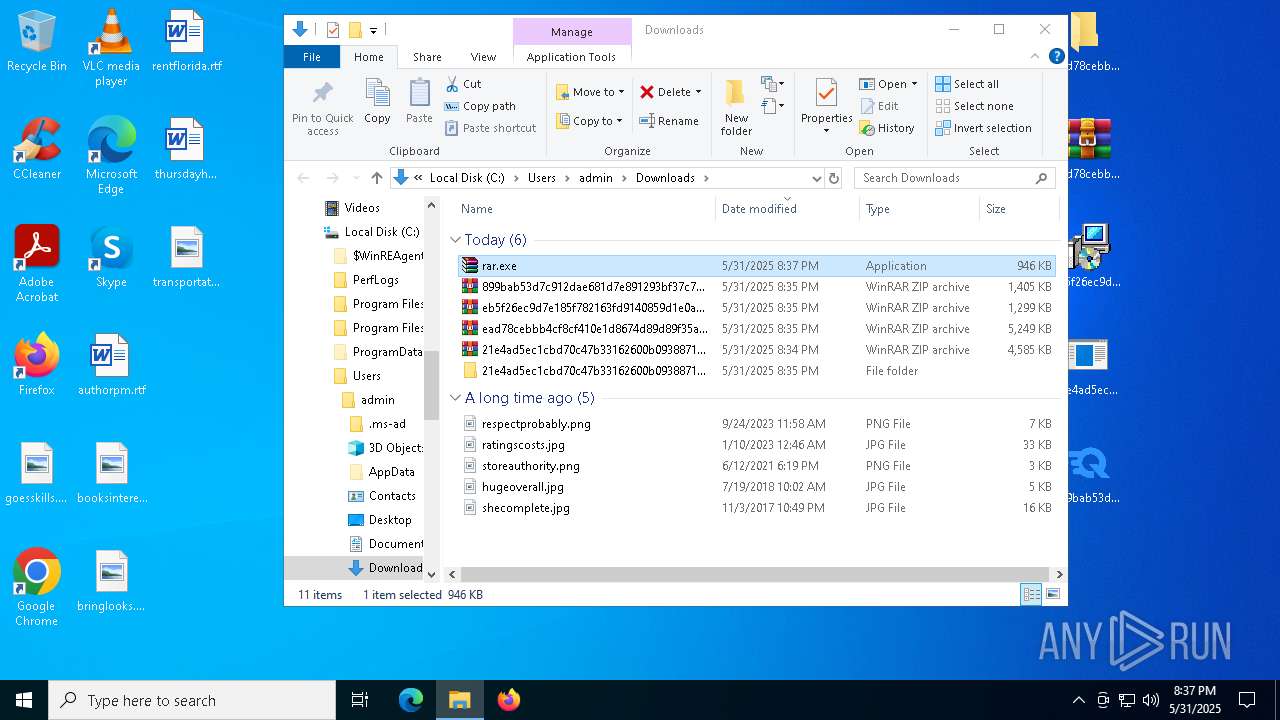
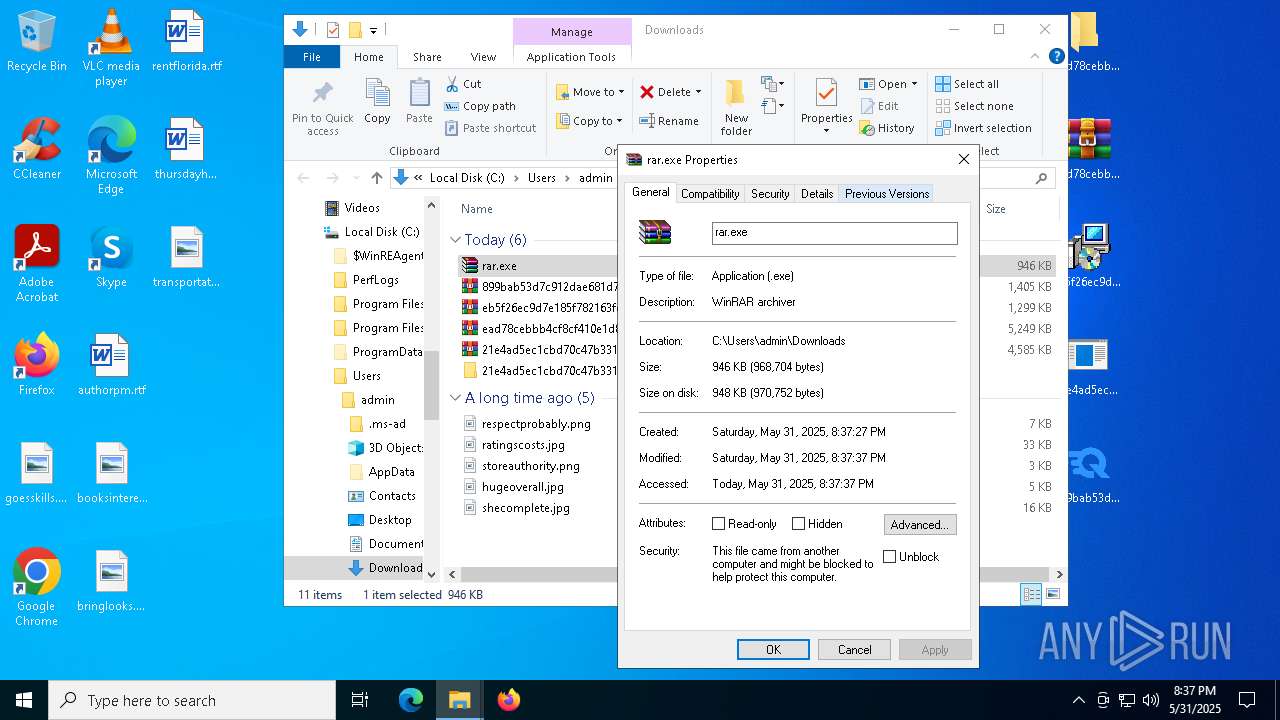
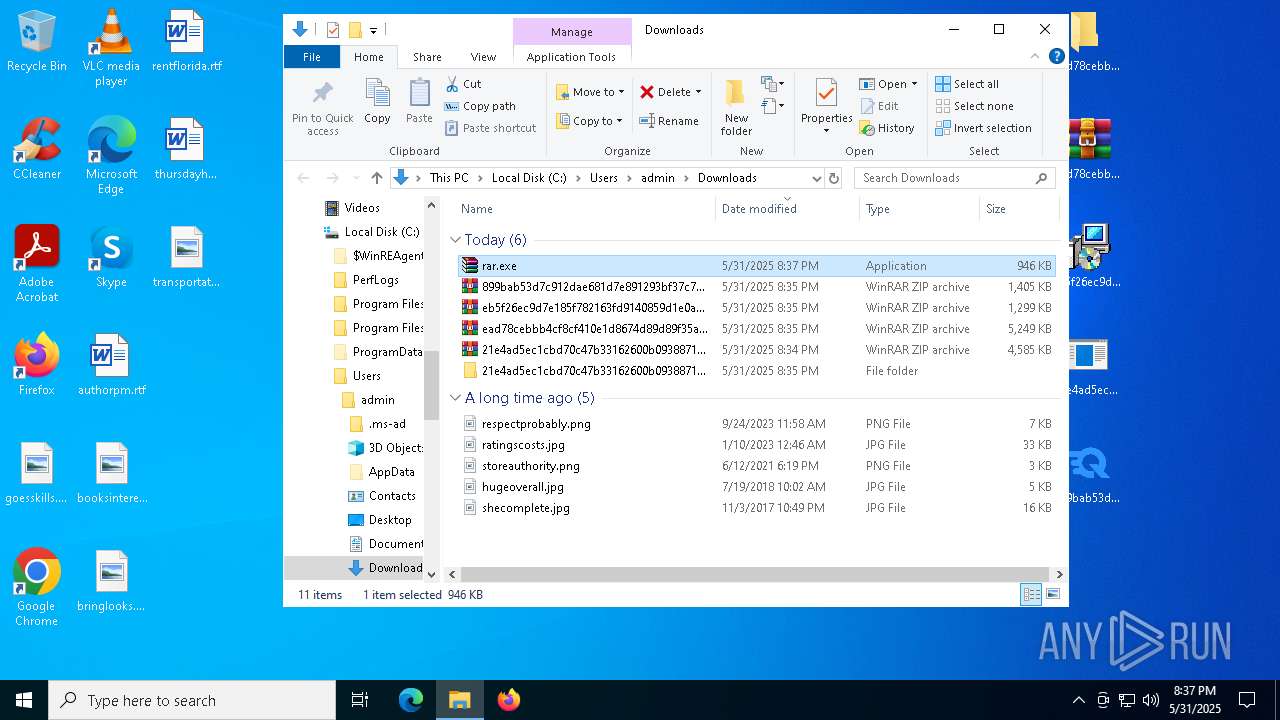
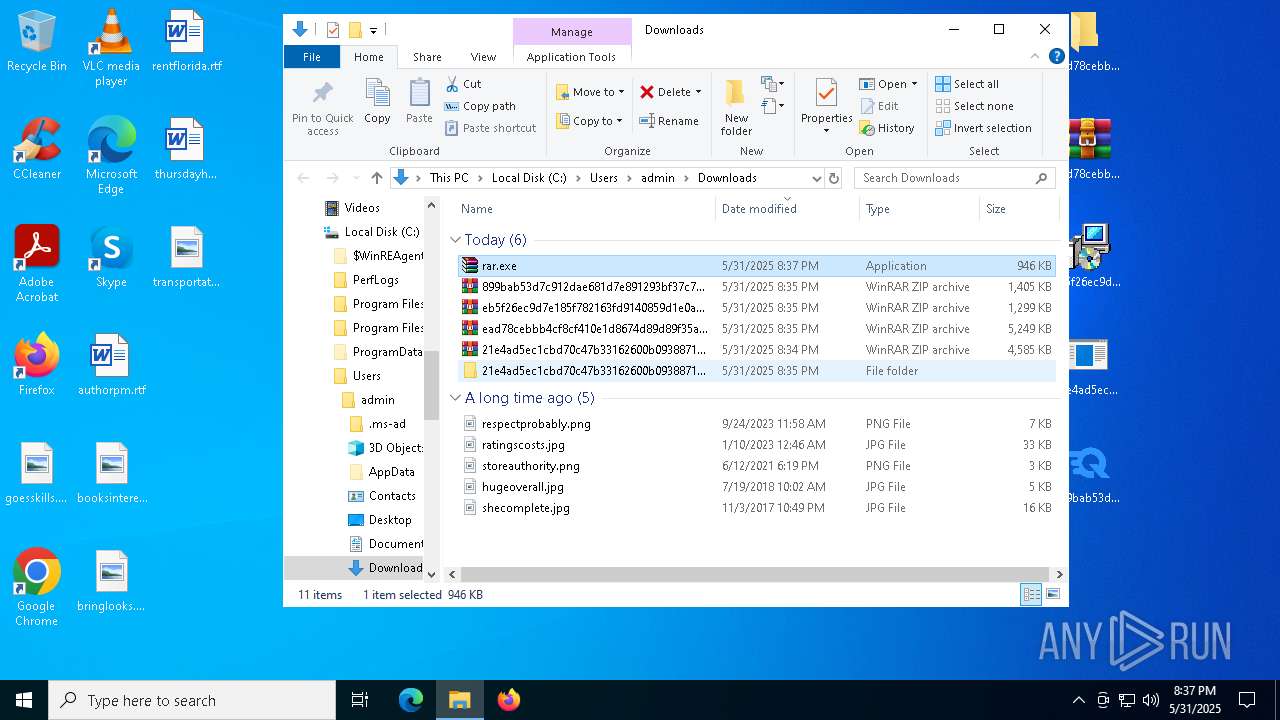
Launch of the file from Downloads directory
- firefox.exe (PID: 7816)
- firefox.exe (PID: 5380)
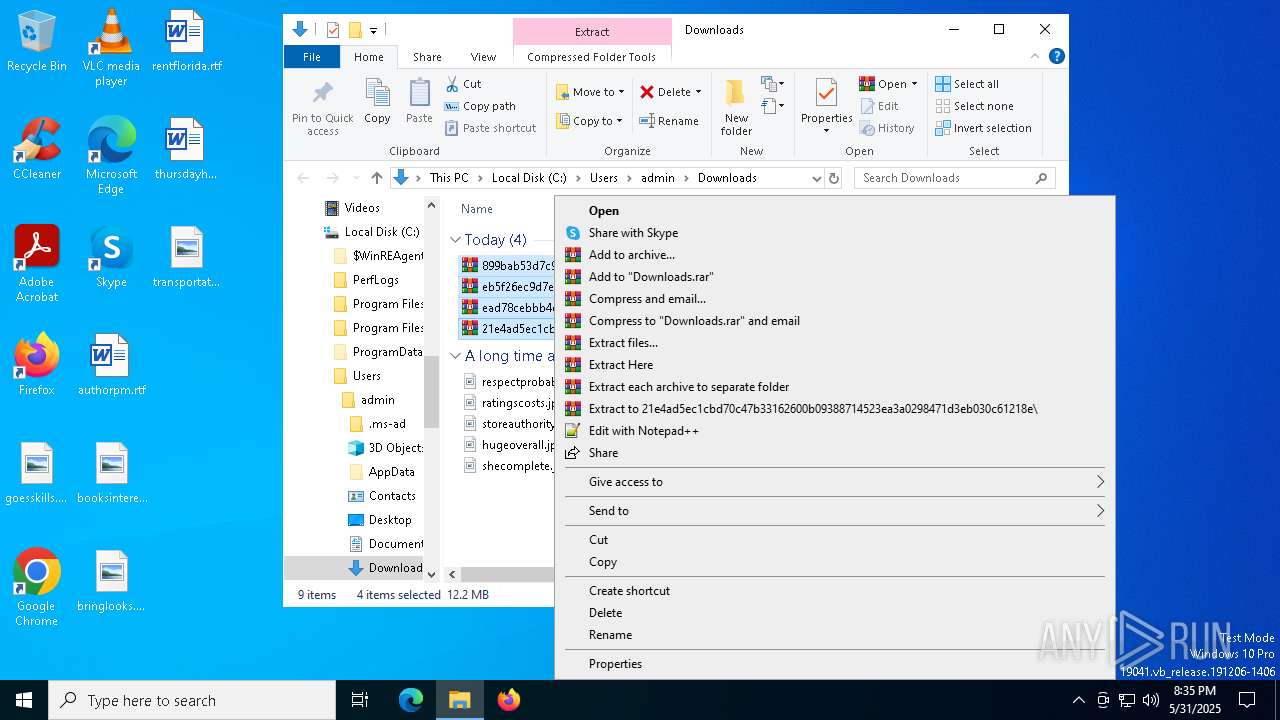
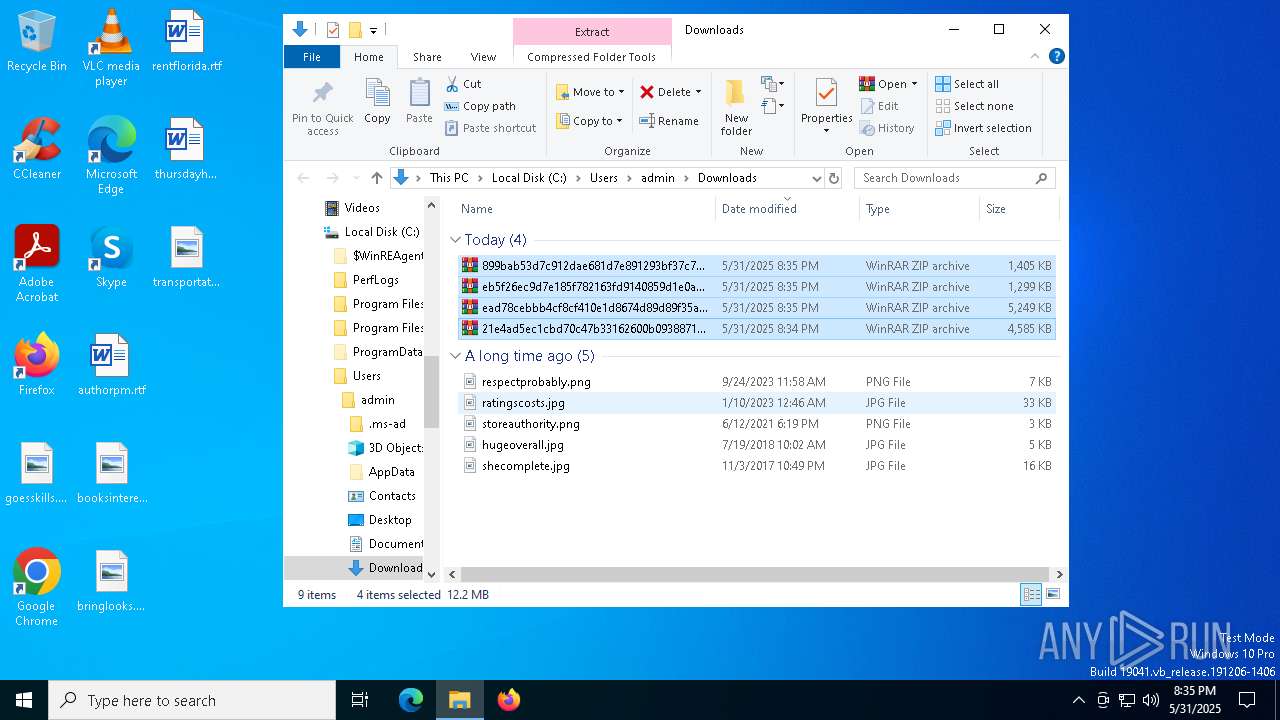
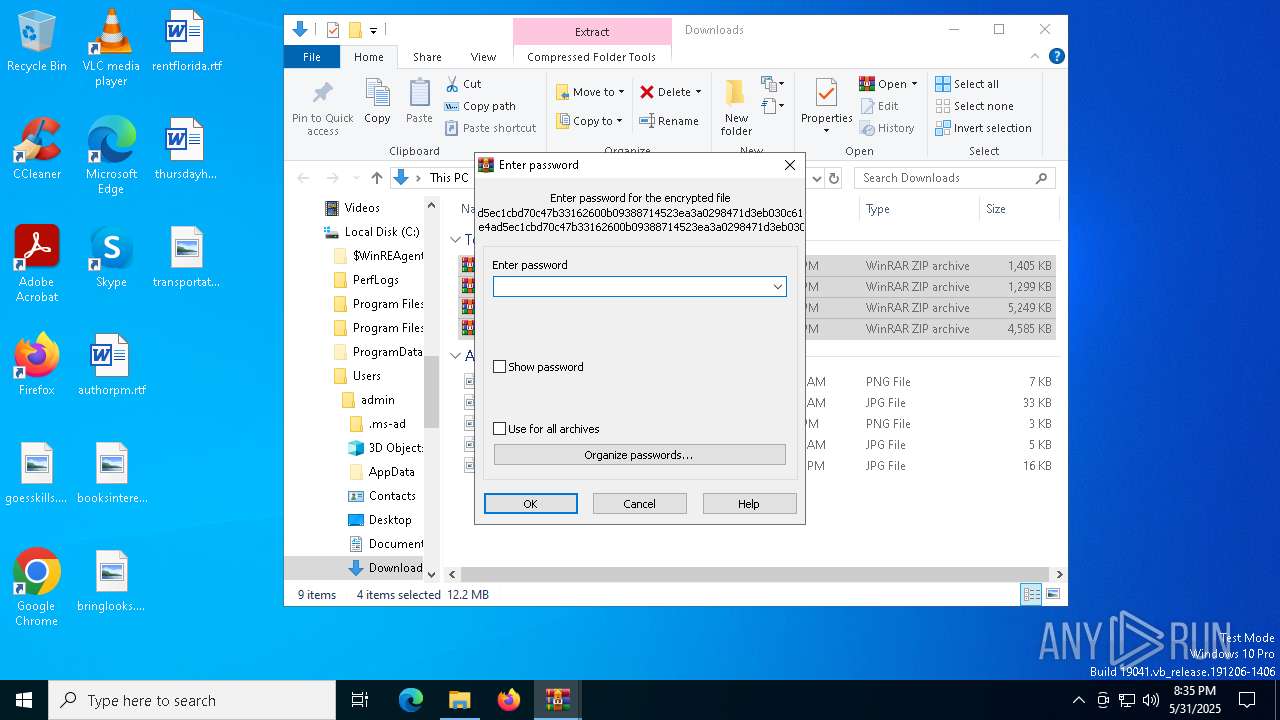
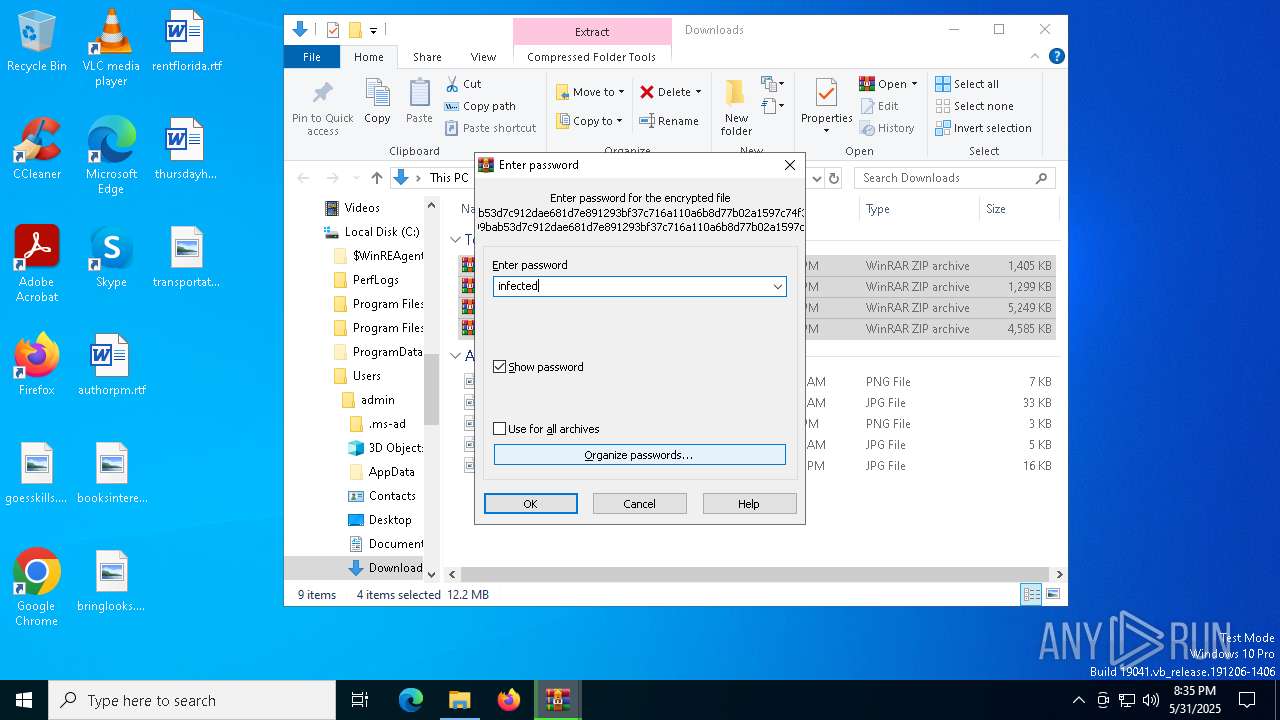
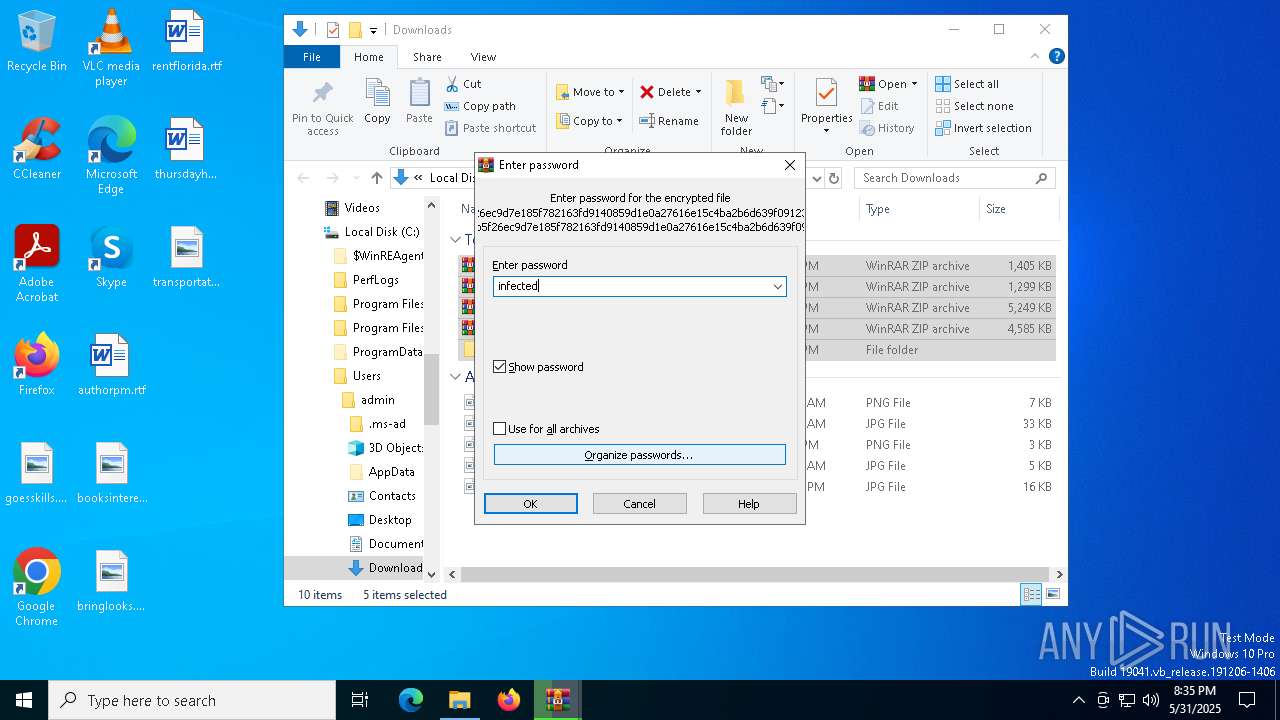
Manual execution by a user
- WinRAR.exe (PID: 7636)
- WinRAR.exe (PID: 2384)
- WinRAR.exe (PID: 7652)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
- msiexec.exe (PID: 8476)
- BitDefender.exe (PID: 8724)
- firefox.exe (PID: 7208)
- rar.exe (PID: 8340)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7636)
- WinRAR.exe (PID: 2384)
- msiexec.exe (PID: 6192)
- firefox.exe (PID: 5380)
Found Base64 encoded network access via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded access to environment variables via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded reference to AntiVirus WMI classes (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded encryption-related PowerShell classes (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded reflection usage via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded text manipulation via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded reference to WMI classes (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded compression PowerShell classes (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Found Base64 encoded file access via PowerShell (YARA)
- 899bab53d7c912dae681d7e891293bf37c716a110a6b8d77b02a1597c74f36eb.exe (PID: 3868)
Manages system restore points
- SrTasks.exe (PID: 2316)
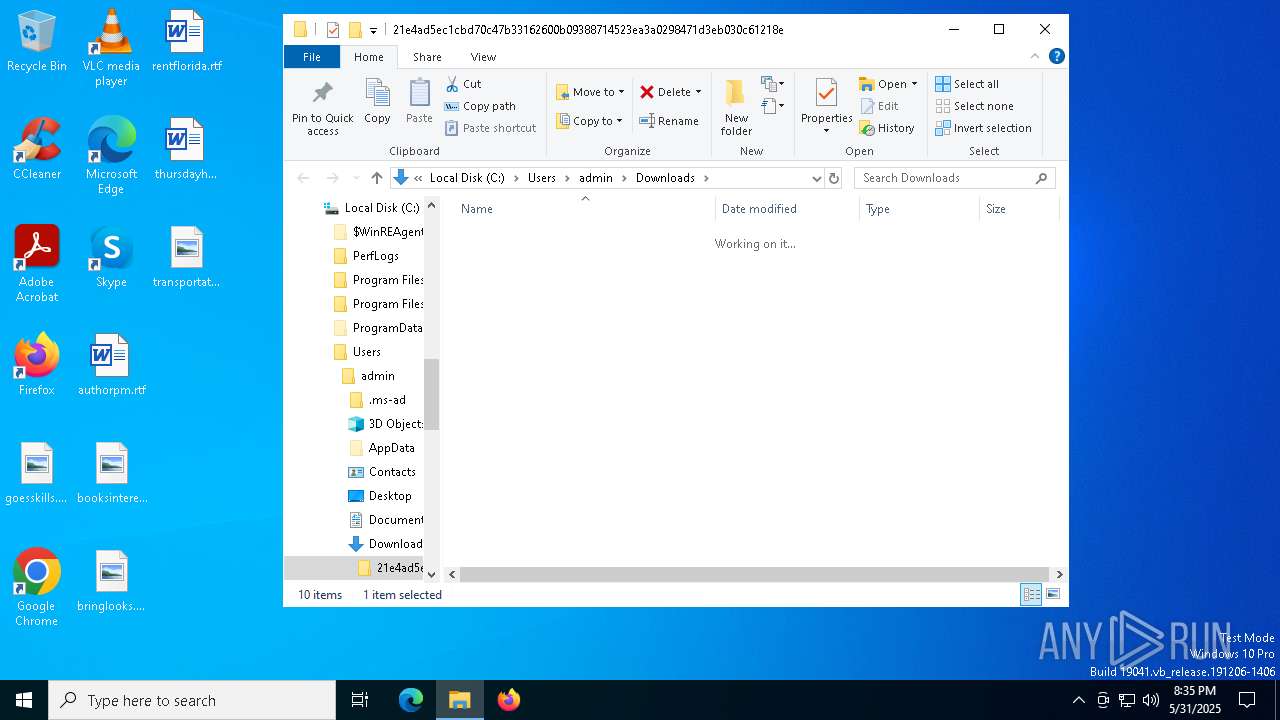
Creates a new folder
- cmd.exe (PID: 7480)
Starts application with an unusual extension
- msiexec.exe (PID: 6192)
AutoHotkey executable
- cmd.exe (PID: 7480)
Detects AutoHotkey samples (YARA)
- url.exe (PID: 9008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
57
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4564 -childID 3 -isForBrowser -prefsHandle 4568 -prefMapHandle 4528 -prefsLen 31222 -prefMapSize 244583 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {351e100f-434f-491e-a8fe-03dd46ffe322} 5380 "\\.\pipe\gecko-crash-server-pipe.5380" 2960b04a4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 512 | C:\Windows\syswow64\MsiExec.exe -Embedding 4D6ADF73E33C8088EAA66104F30FB561 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2772 -childID 1 -isForBrowser -prefsHandle 2764 -prefMapHandle 2760 -prefsLen 26911 -prefMapSize 244583 -jsInitHandle 1300 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9f9fcfd6-6c1b-40cf-9953-c8471613523a} 7816 "\\.\pipe\gecko-crash-server-pipe.7816" 246fcac4f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=3200 -childID 1 -isForBrowser -prefsHandle 3204 -prefMapHandle 3180 -prefsLen 32751 -prefMapSize 244583 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7b19ecfb-7b94-4947-99fa-898f4e51bd6b} 5380 "\\.\pipe\gecko-crash-server-pipe.5380" 296087d4d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4344 -childID 2 -isForBrowser -prefsHandle 4356 -prefMapHandle 4352 -prefsLen 38061 -prefMapSize 244583 -jsInitHandle 1468 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3bbe8756-2234-4953-aa9d-b2e63198a8ef} 5380 "\\.\pipe\gecko-crash-server-pipe.5380" 2960b04af50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2132 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {aac5c2c3-ef5c-489c-9941-91939346c9f8} 7816 "\\.\pipe\gecko-crash-server-pipe.7816" 246ead83710 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2316 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
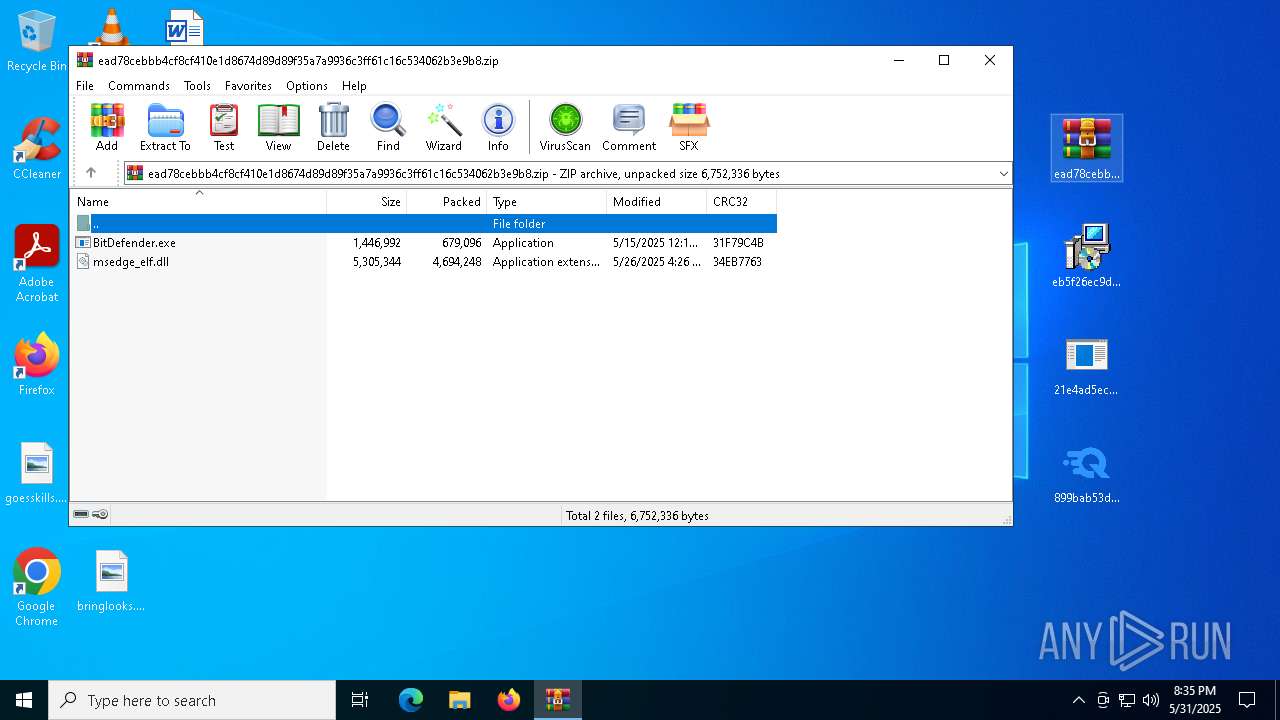
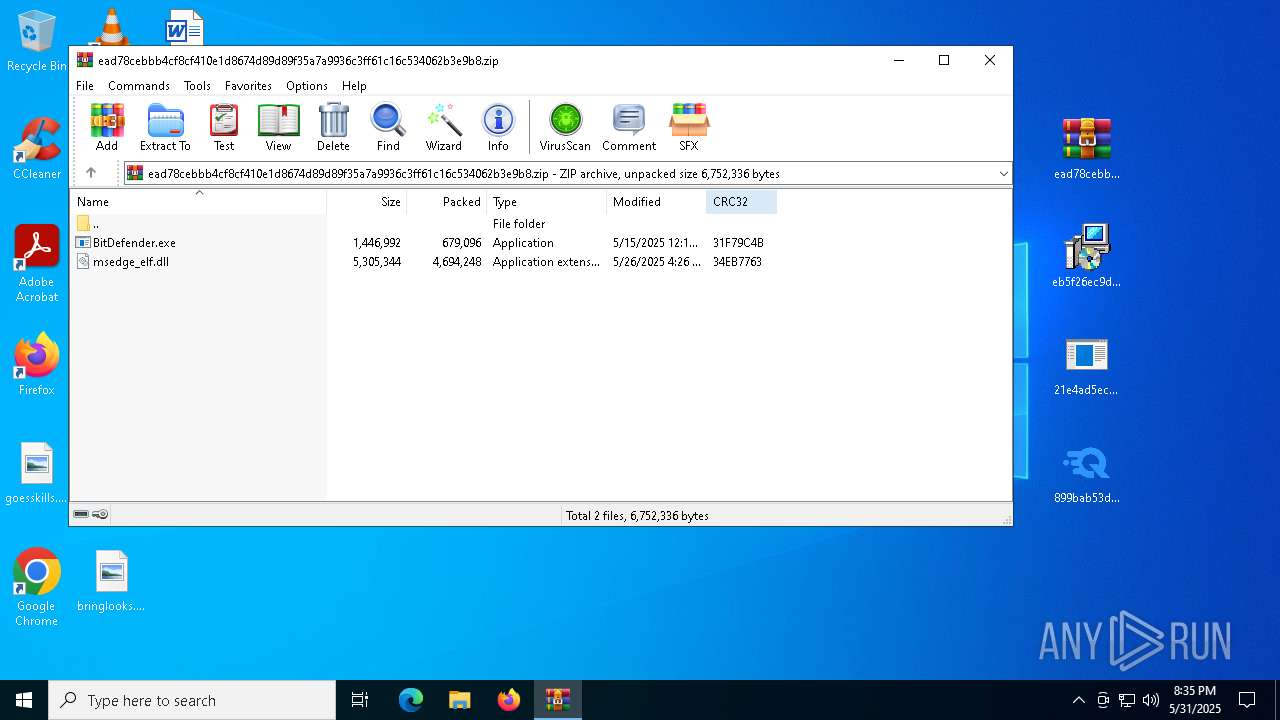
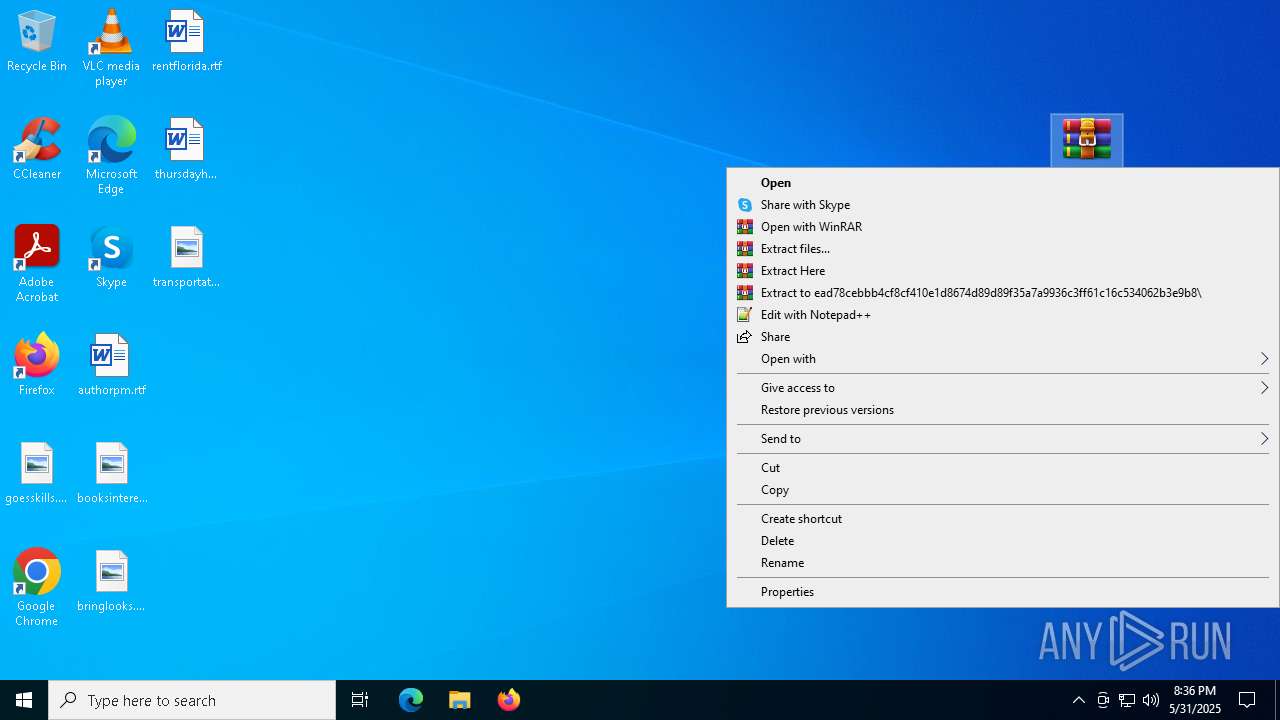
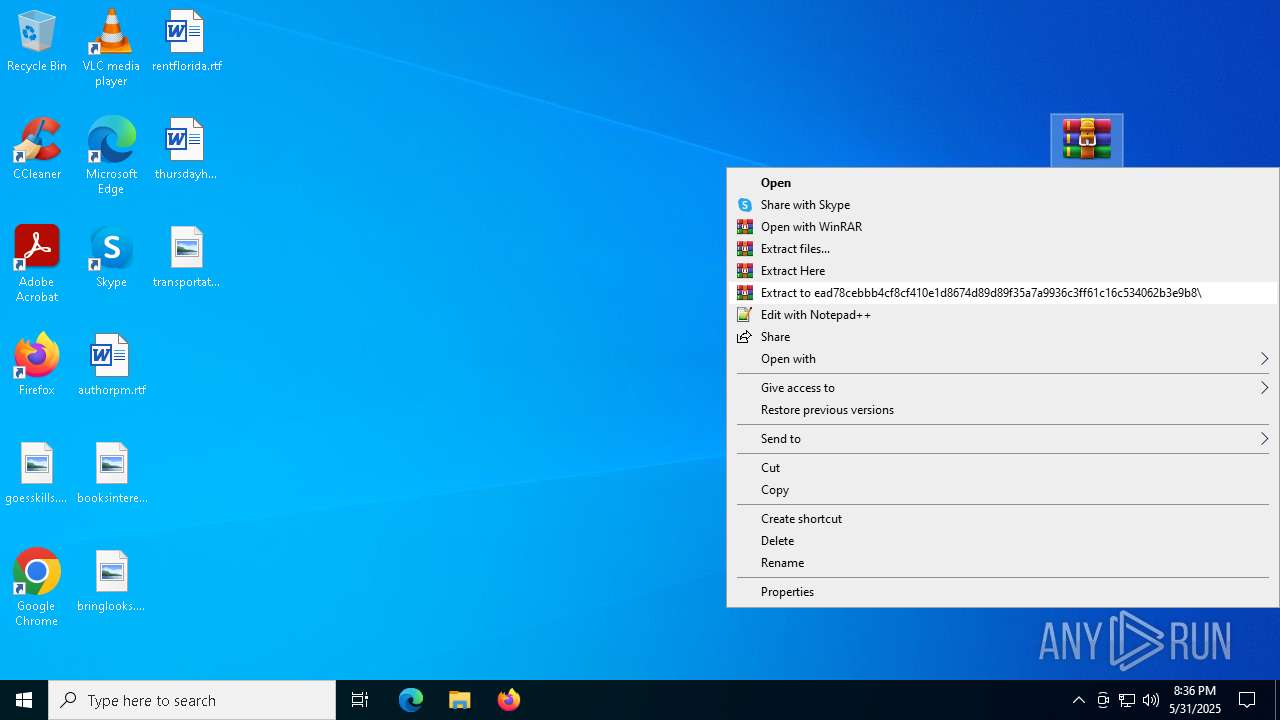
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\ead78cebbb4cf8cf410e1d8674d89d89f35a7a9936c3ff61c16c534062b3e9b8.zip" C:\Users\admin\Desktop\ead78cebbb4cf8cf410e1d8674d89d89f35a7a9936c3ff61c16c534062b3e9b8\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2516 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 447
Read events
41 210
Write events
219
Delete events
18
Modification events
| (PID) Process: | (7816) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
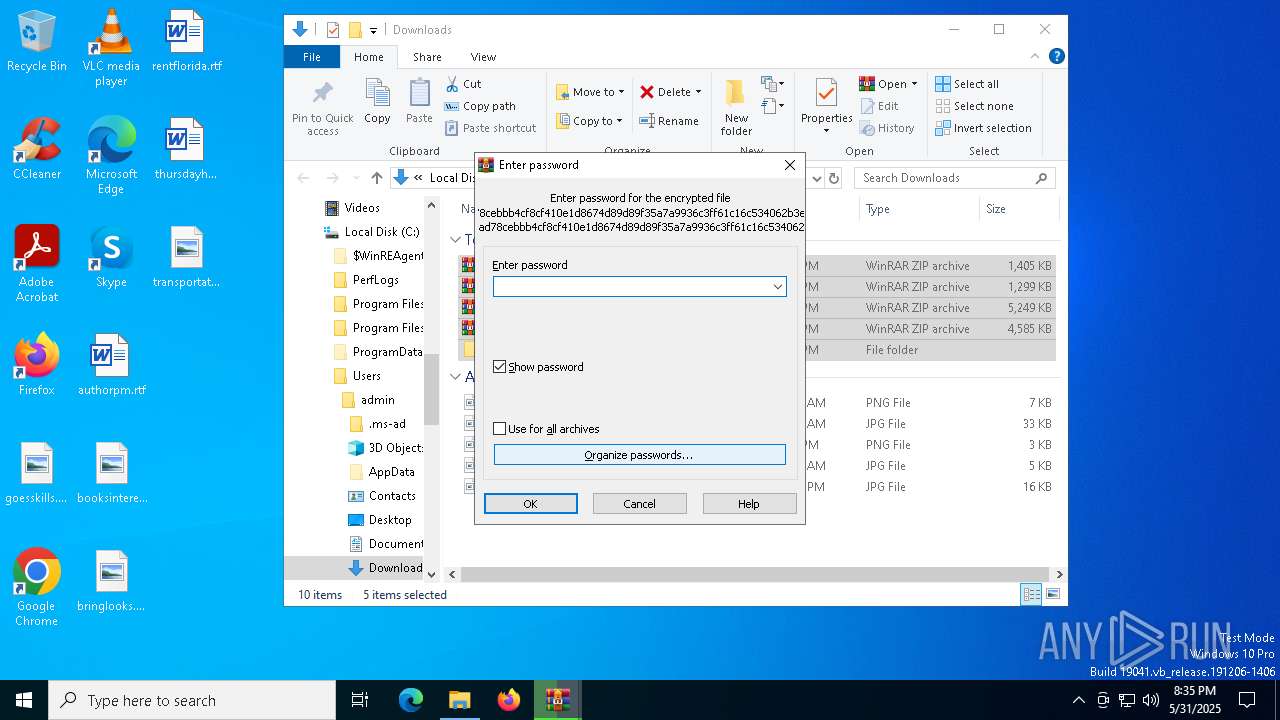
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | PswAllArchives |
Value: 0 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7636) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
64
Suspicious files
539
Text files
550
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7816 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:22DA36CA5BA1D055ADE237F52DC825A7 | SHA256:7438A5D5298BFA0ABAB51E6B35EAC0F26B830BCEFBDBEB5F07721DBA34F89E0D | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:1CF6EA1AB7E0D37600AD0551F2EC97C3 | SHA256:82586DE1D6338D1873D1983330CDB69D0922A3CB5D6A631861CB5886AD429F92 | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7816 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:4006DDC2918B16C7EF5516C58373842B | SHA256:269EA23B77EDE0874628BD8611BCC5A3E87E0C44CA8A821C0D028B929D4F468F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
102
DNS requests
183
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7816 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7816 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7816 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7816 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7816 | firefox.exe | POST | — | 142.250.186.35:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
7816 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7816 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
8076 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
864 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7816 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7816 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | whitelisted |
7816 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
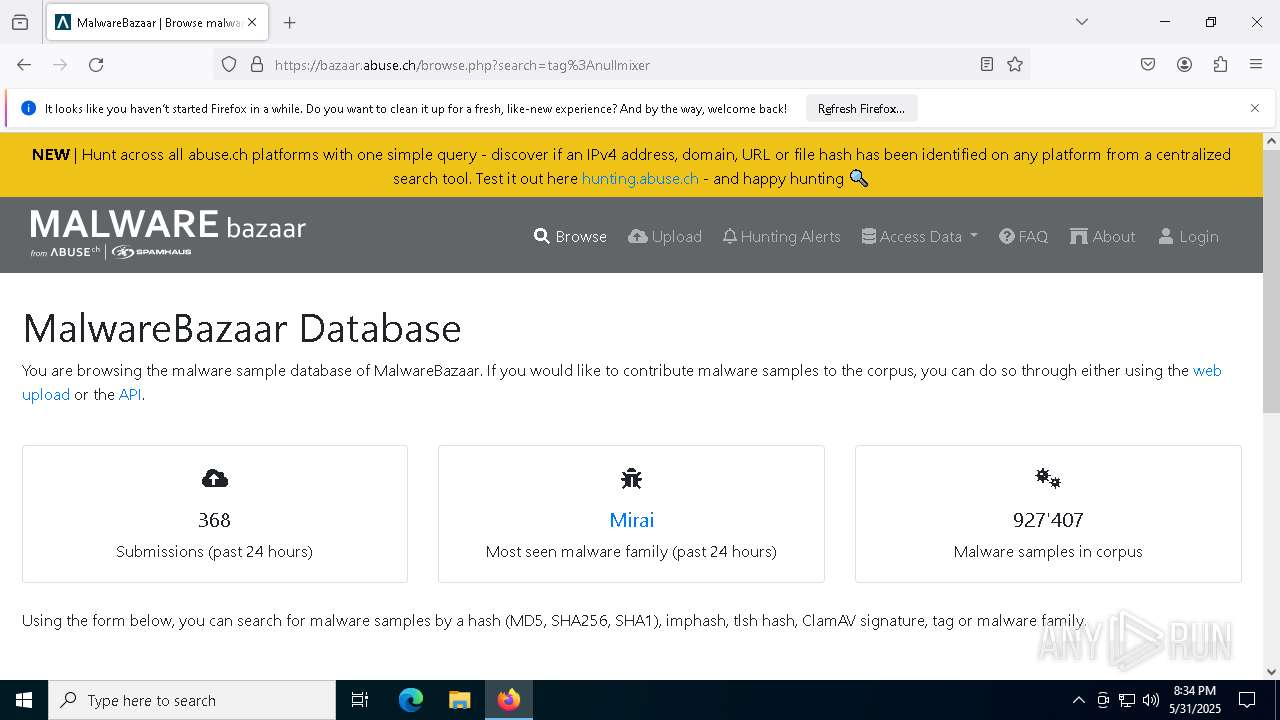
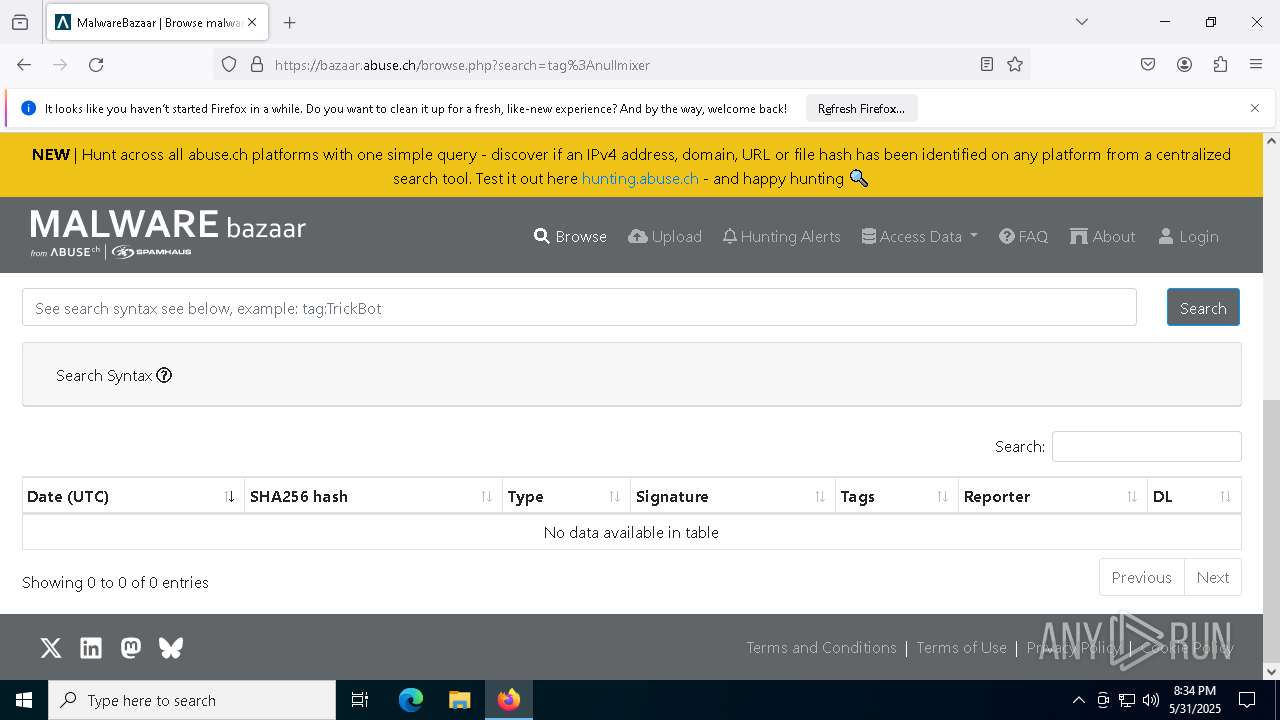
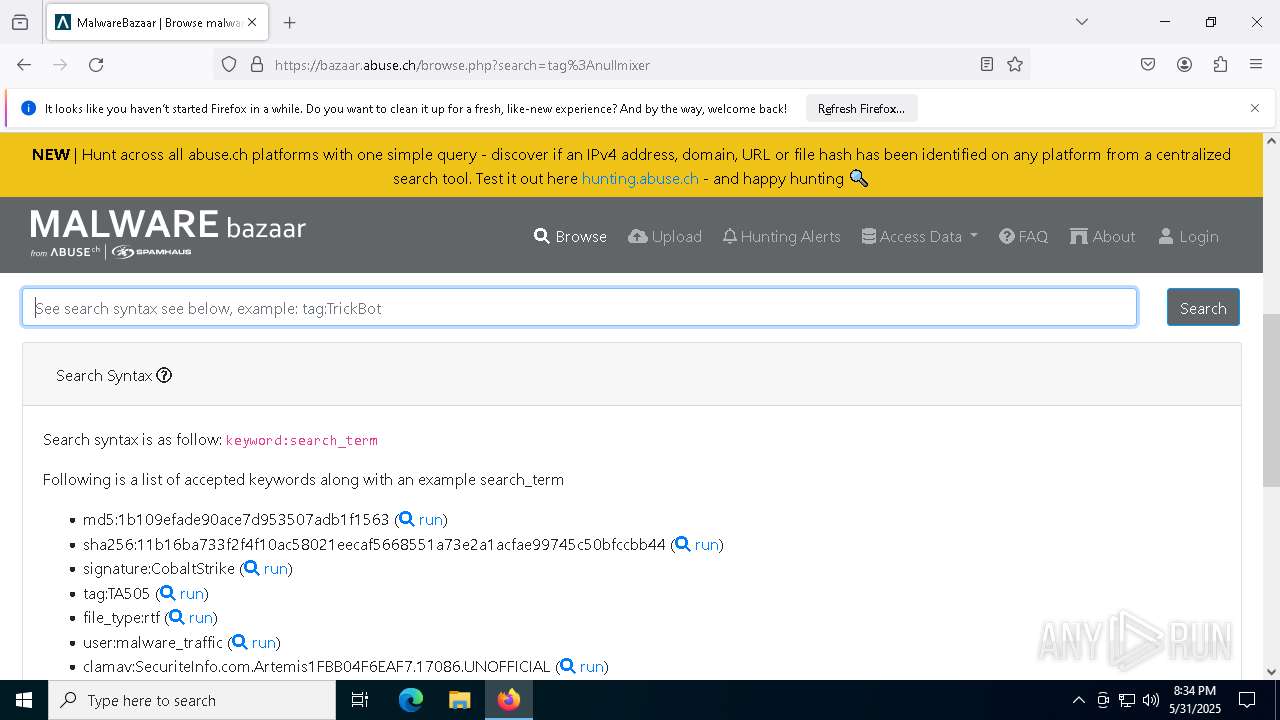
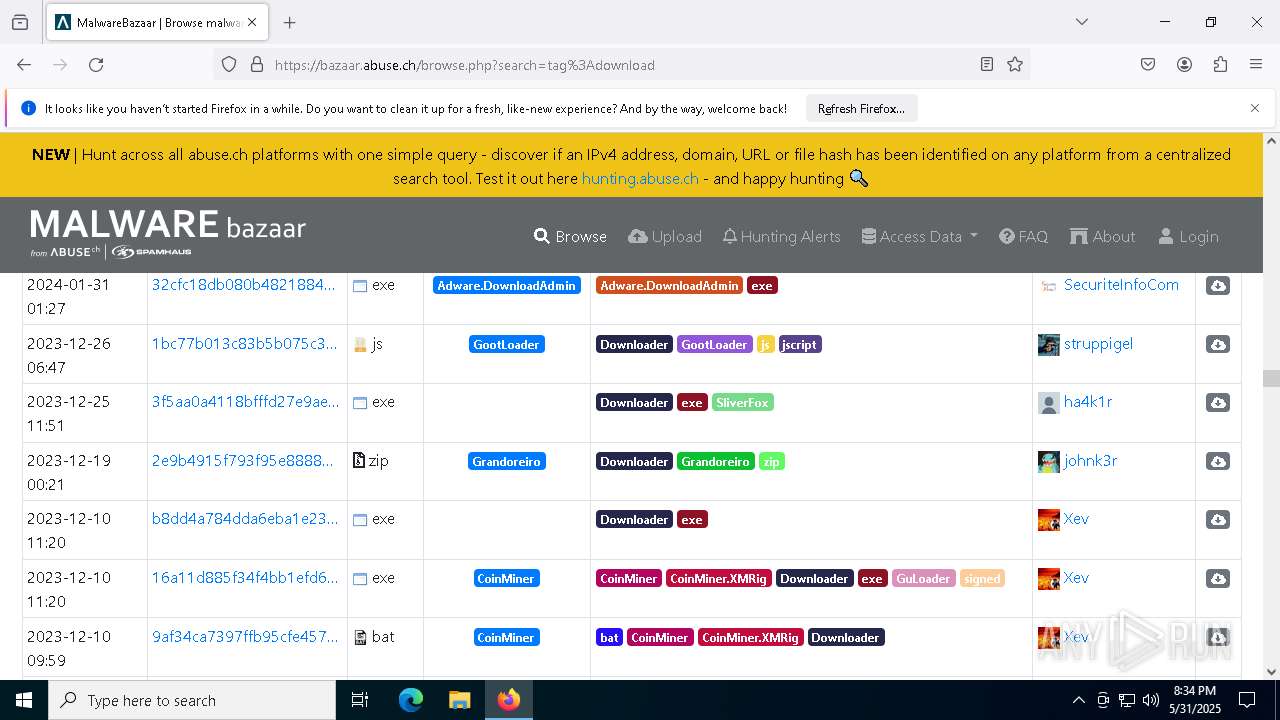
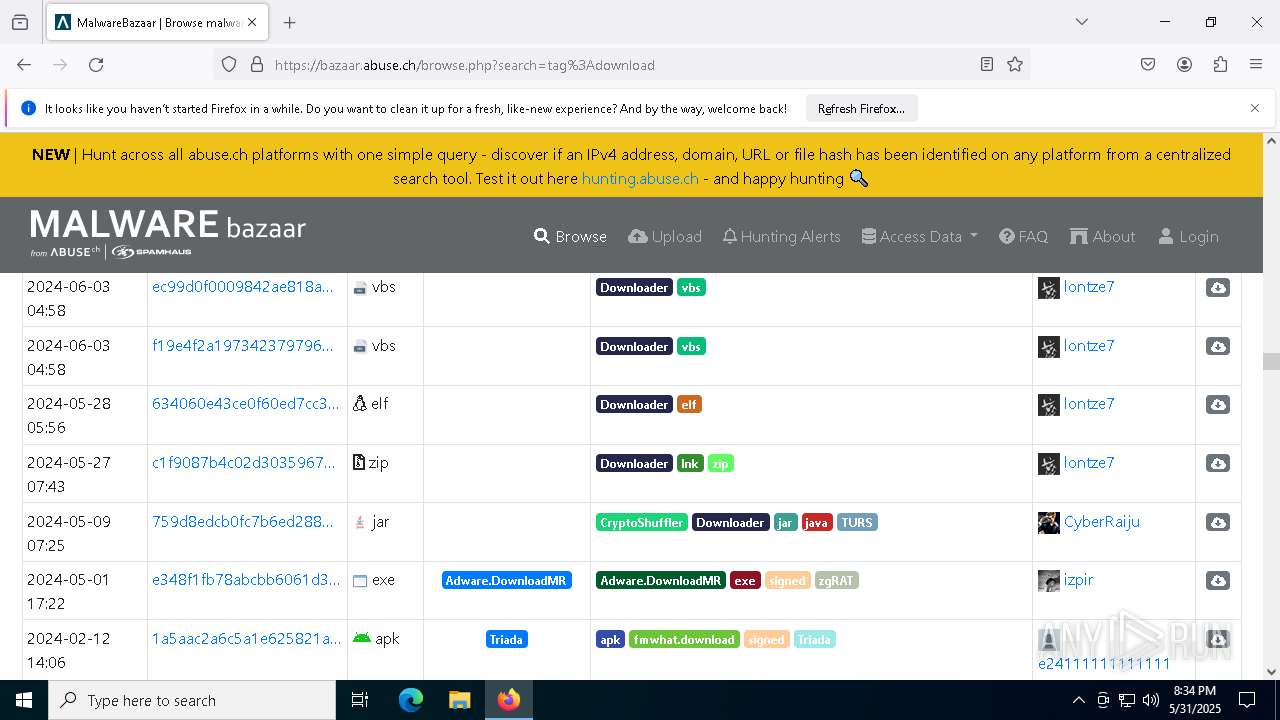
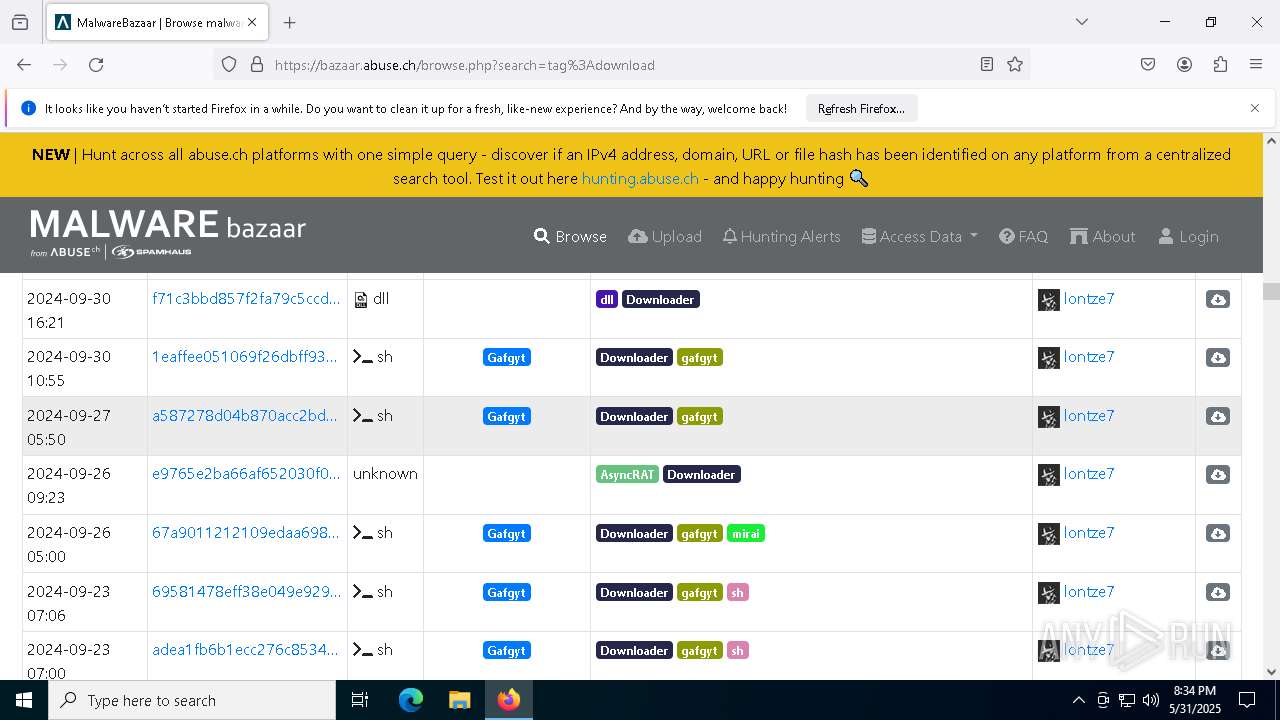
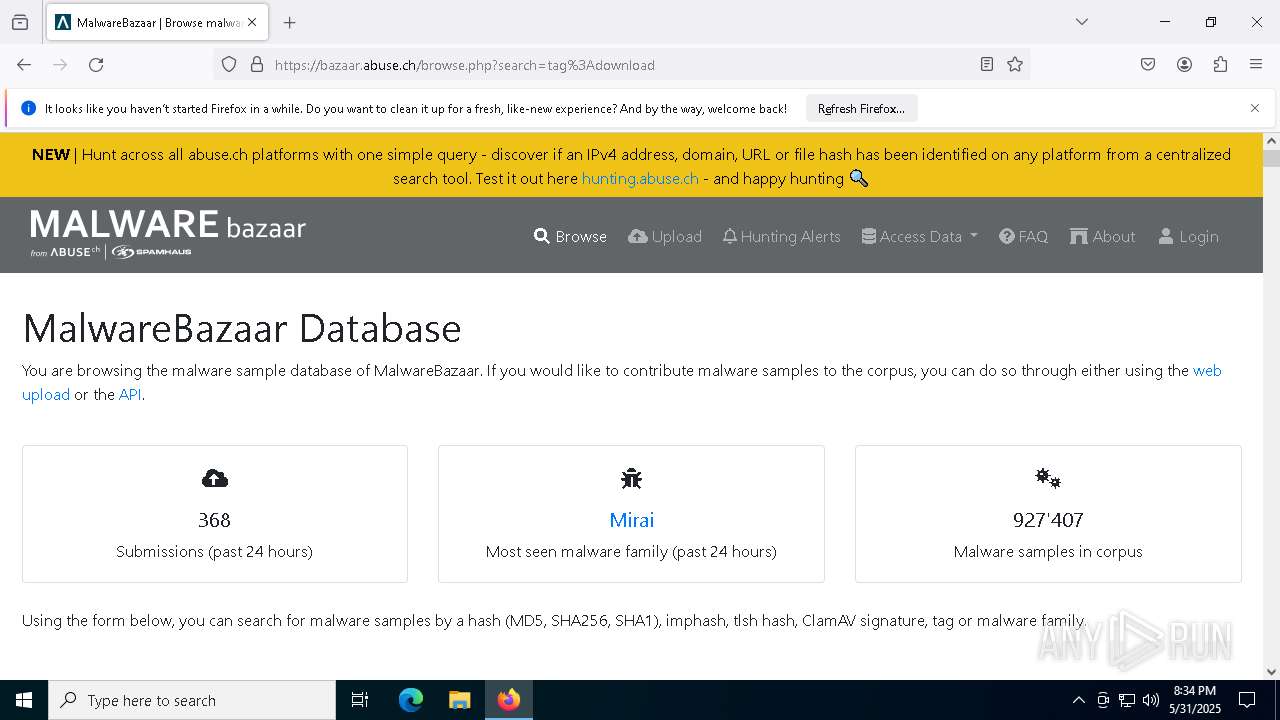
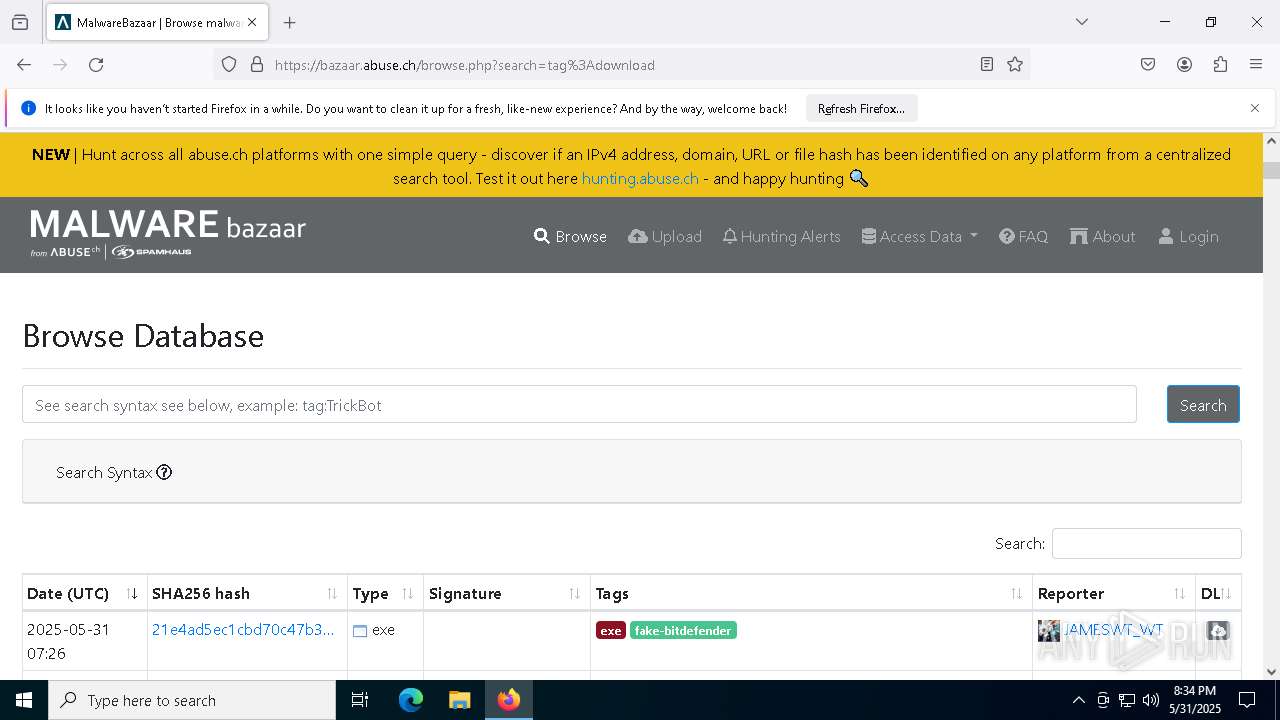
bazaar.abuse.ch |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
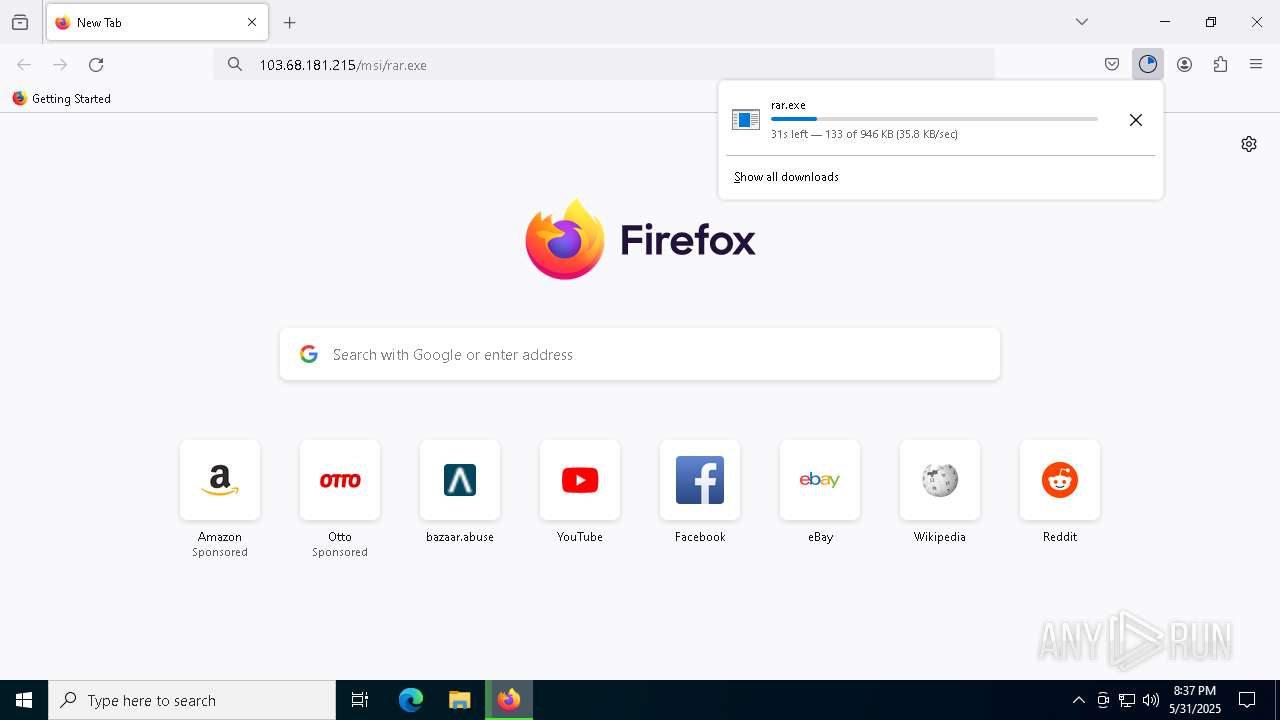
9008 | url.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
9008 | url.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |