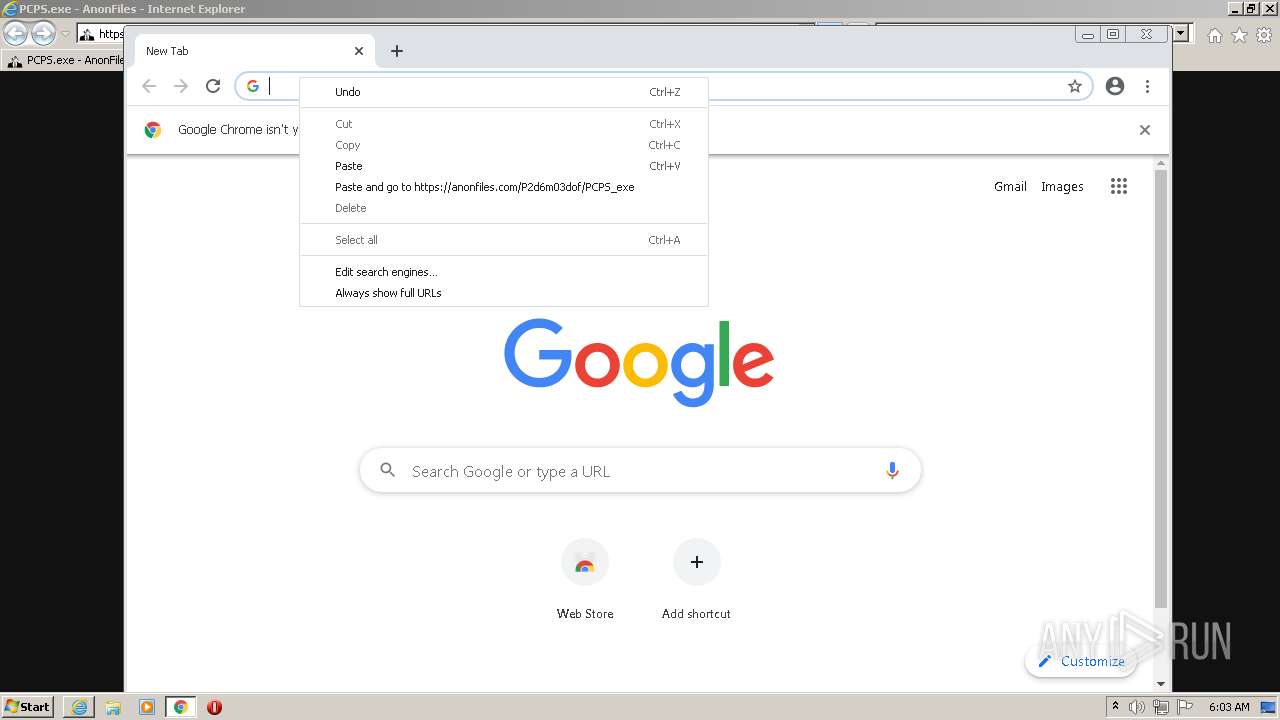
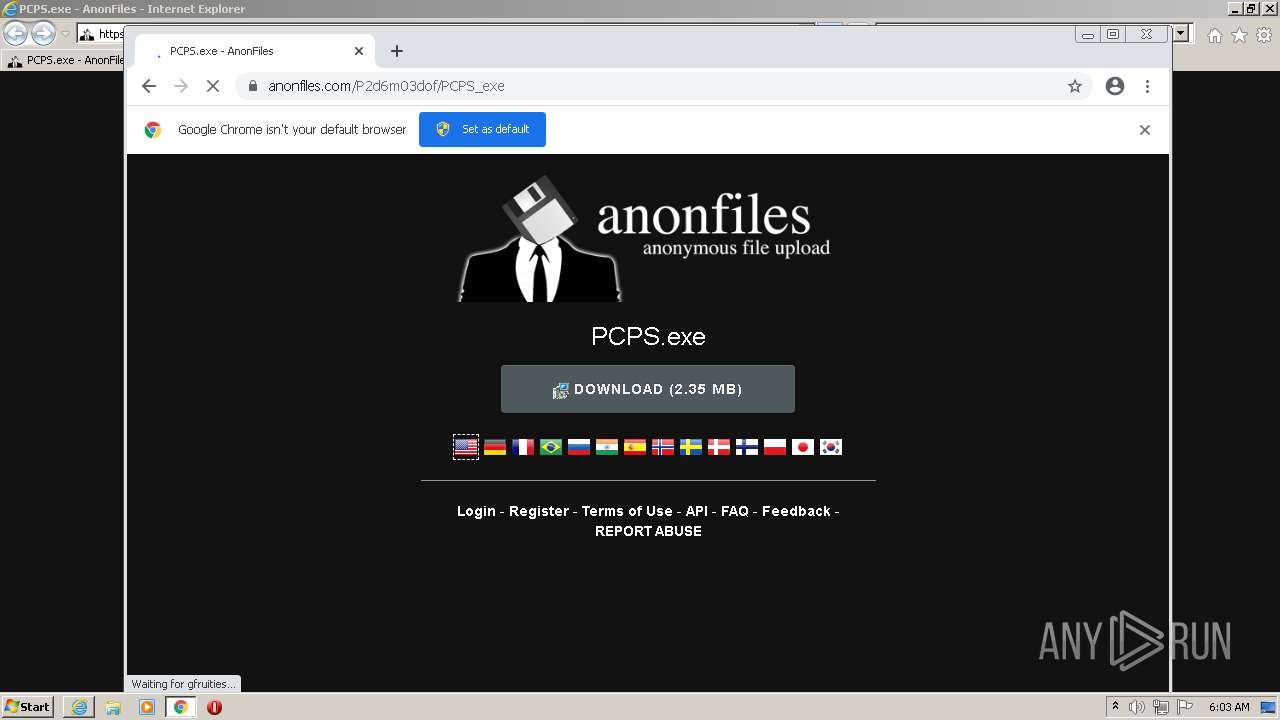
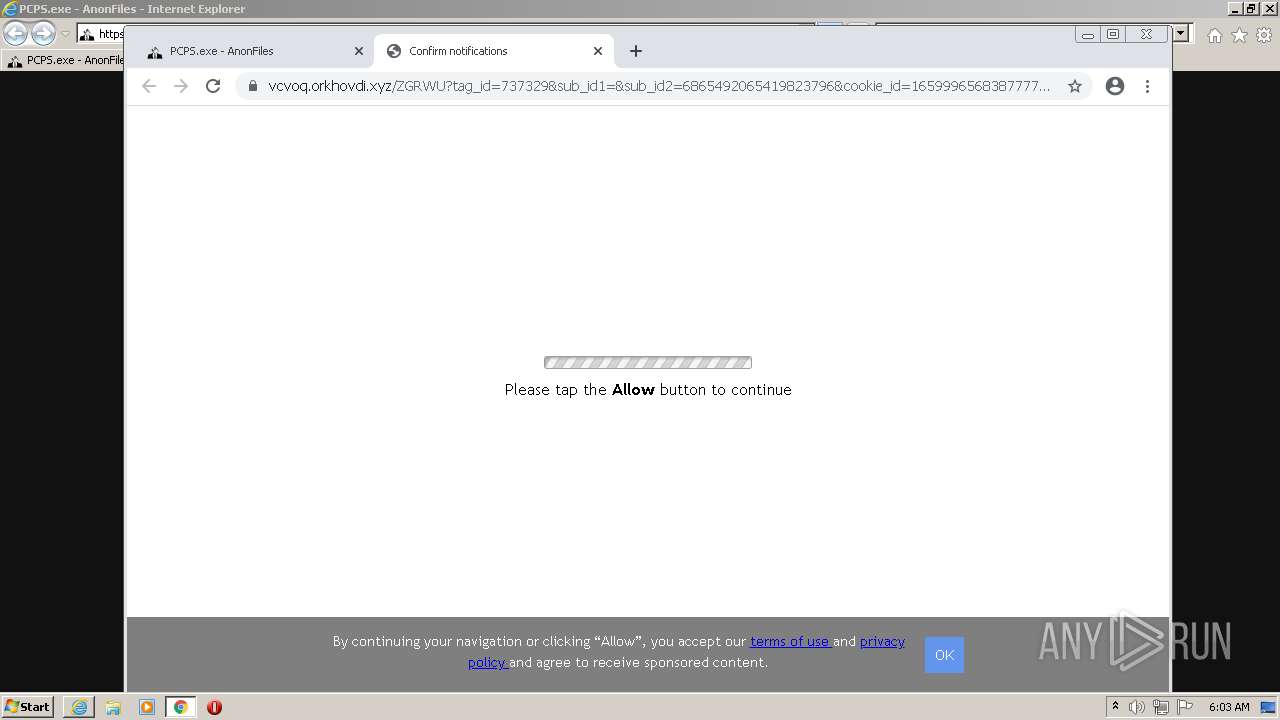
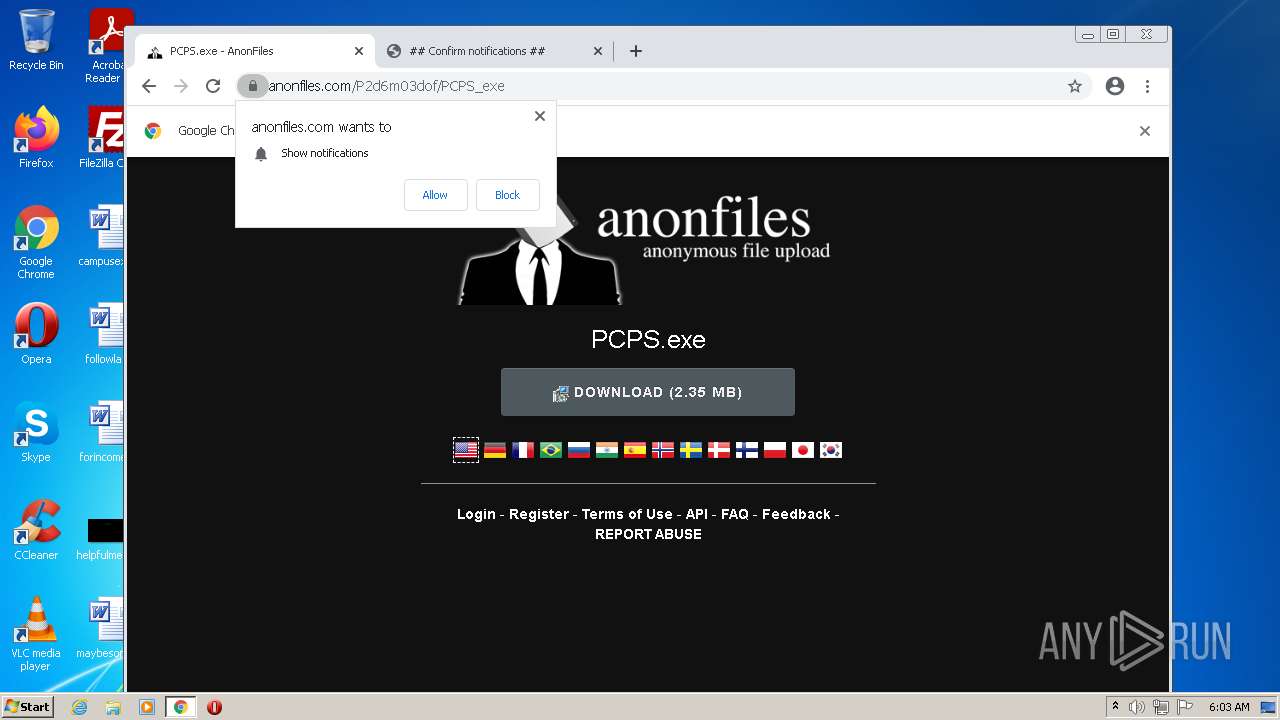
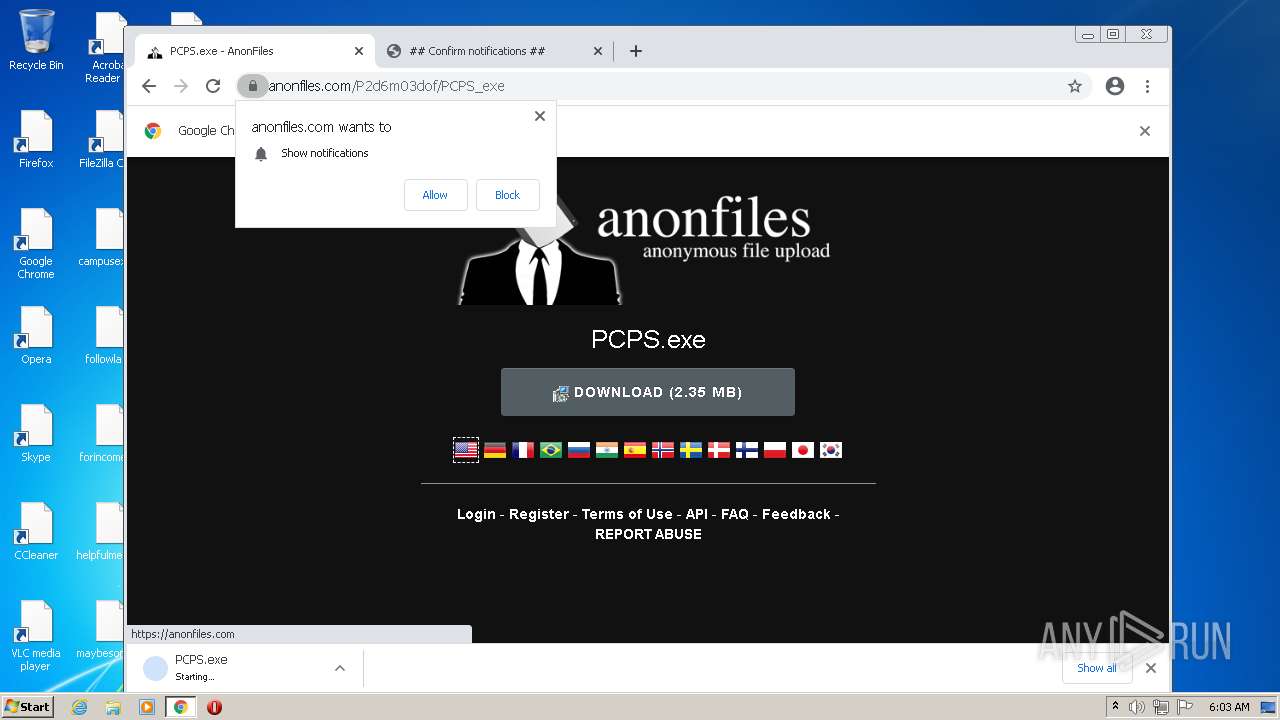
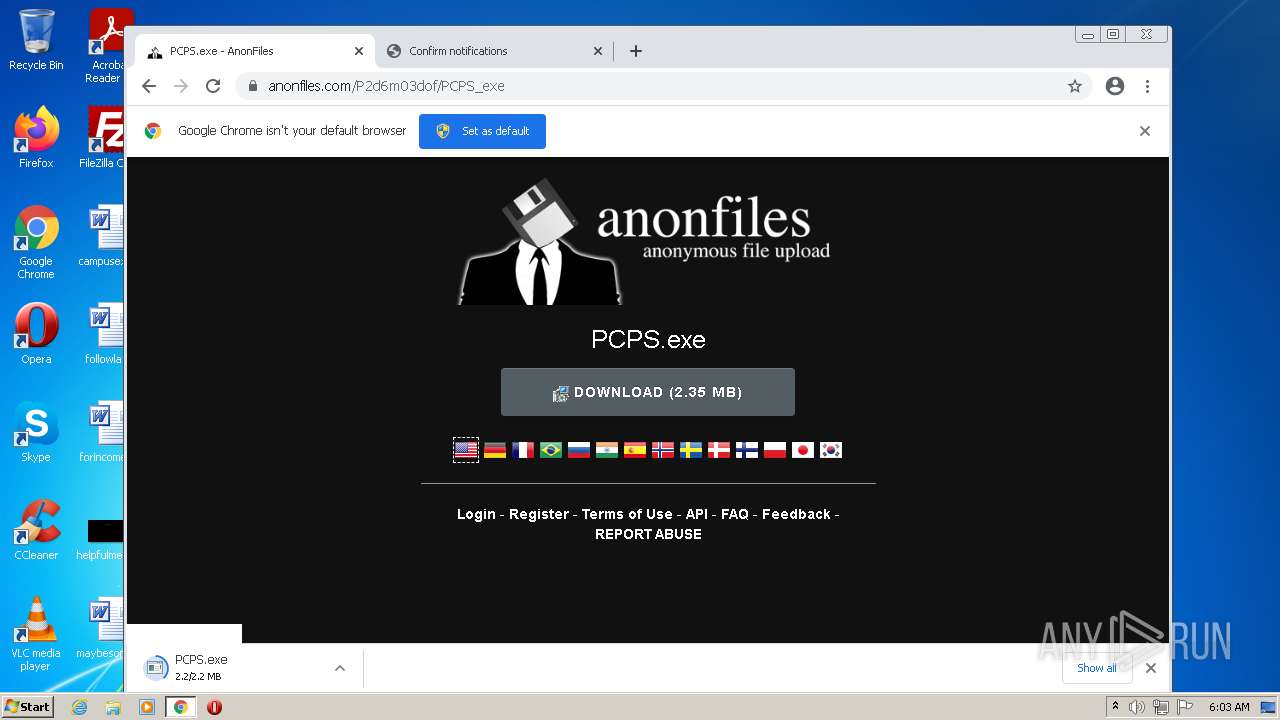
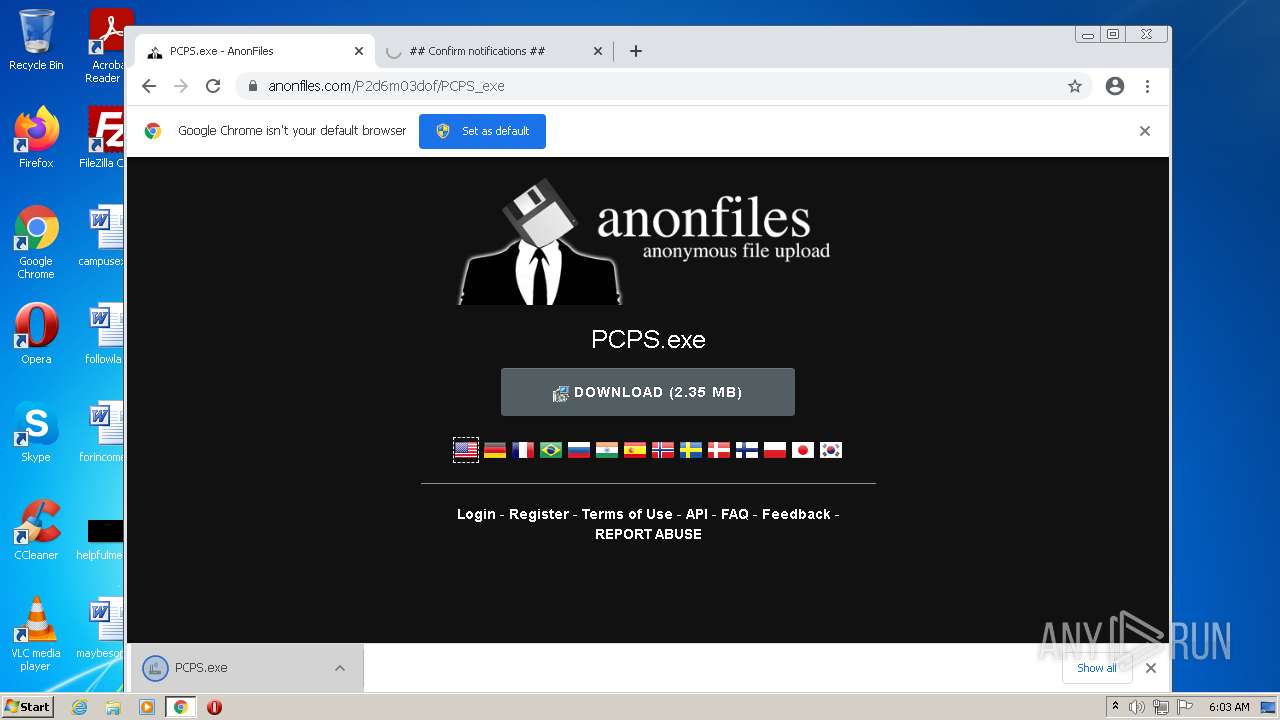
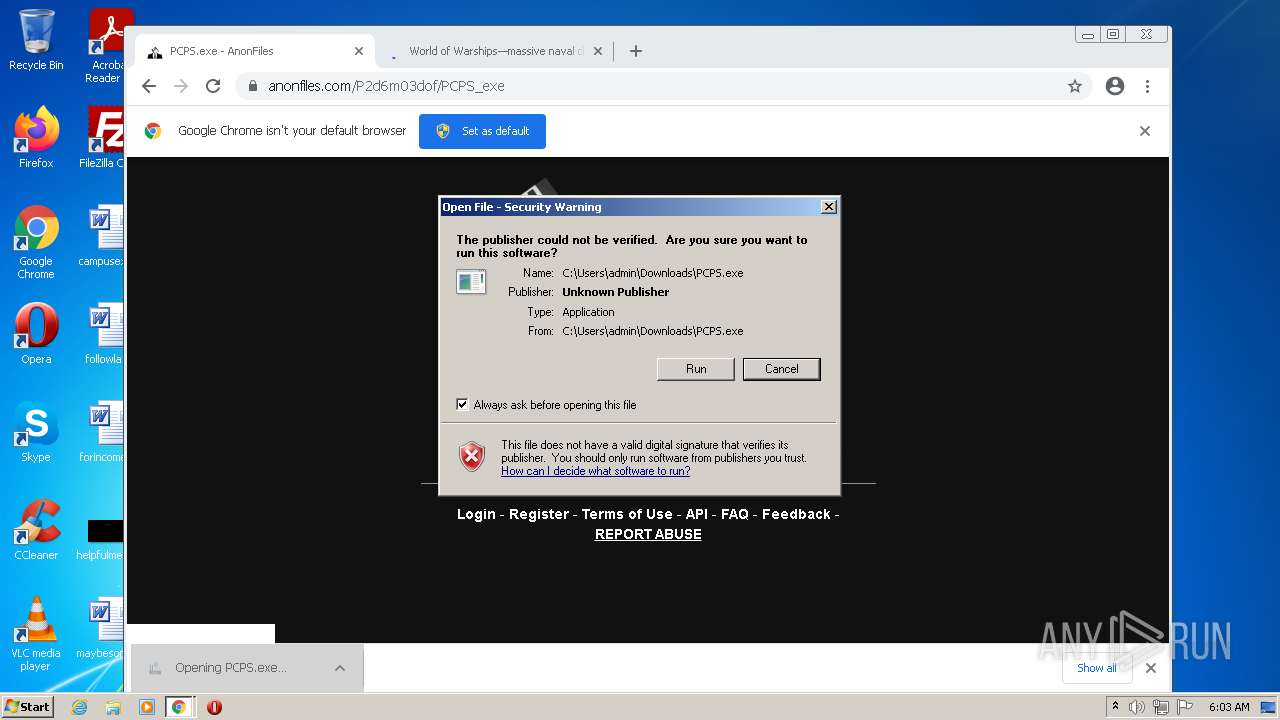
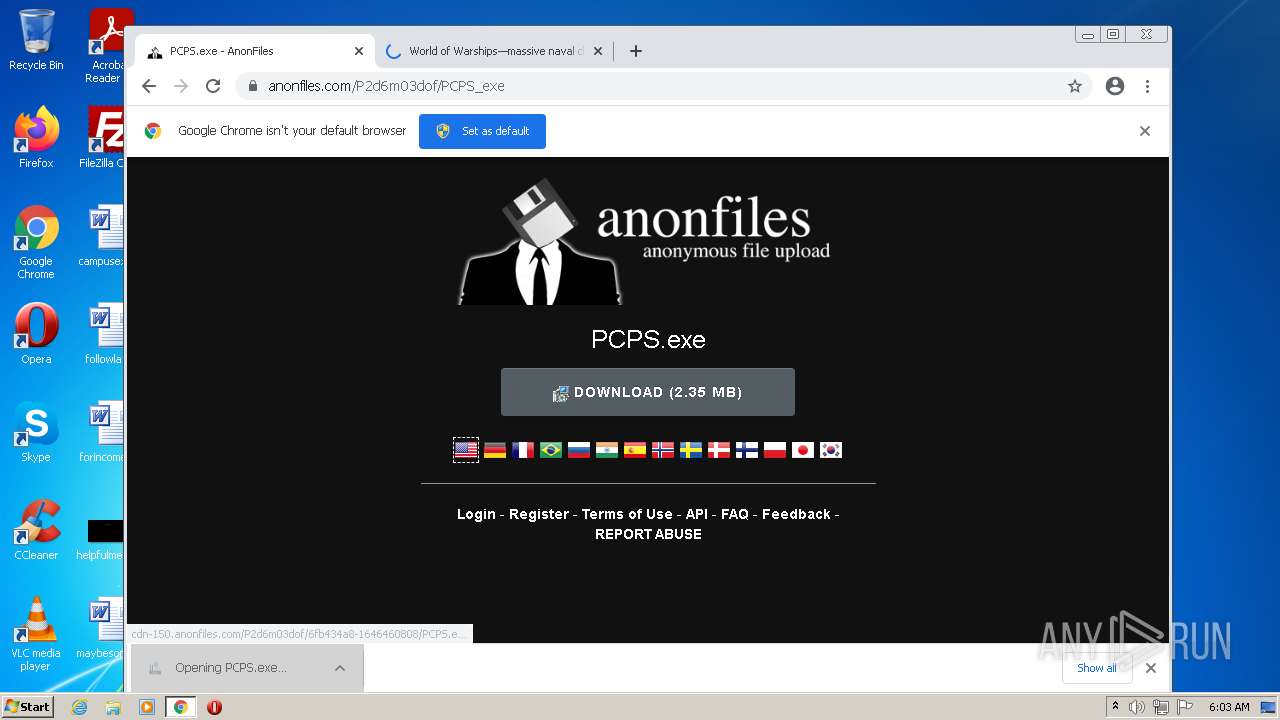
| URL: | https://anonfiles.com/P2d6m03dof/PCPS_exe |
| Full analysis: | https://app.any.run/tasks/f7273642-c53d-42fa-a0f8-1f19bc535cca |
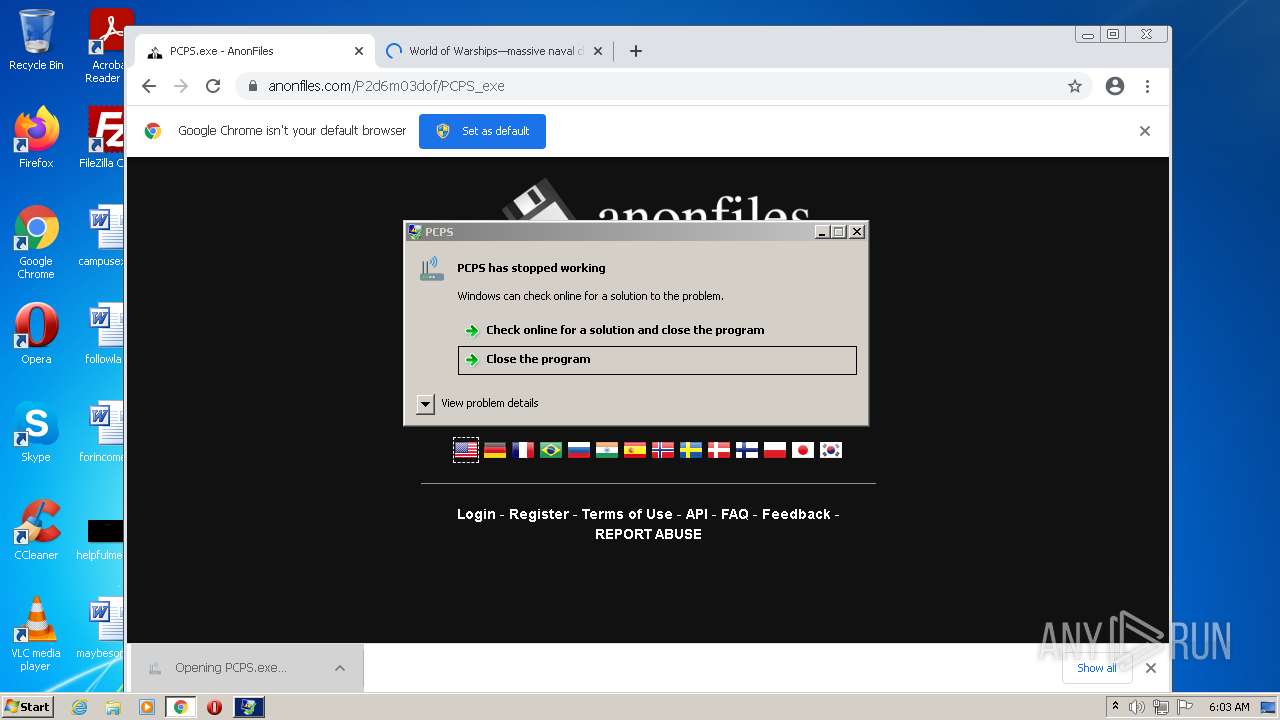
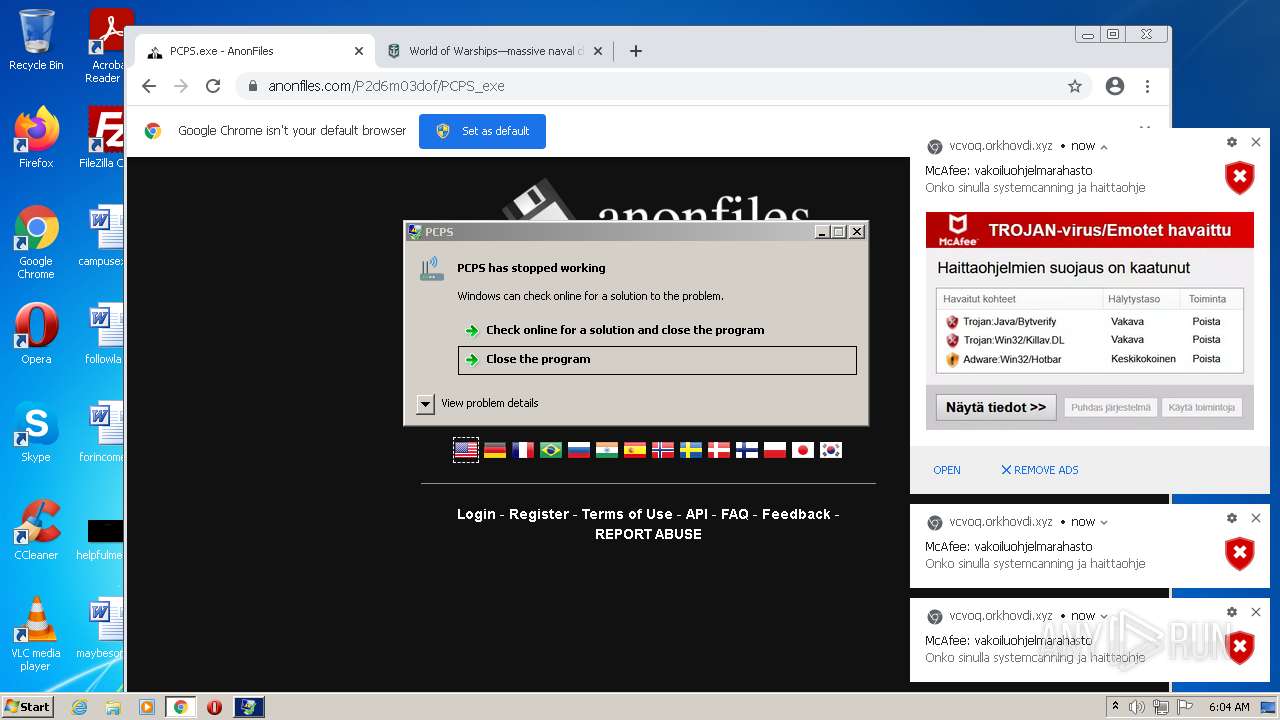
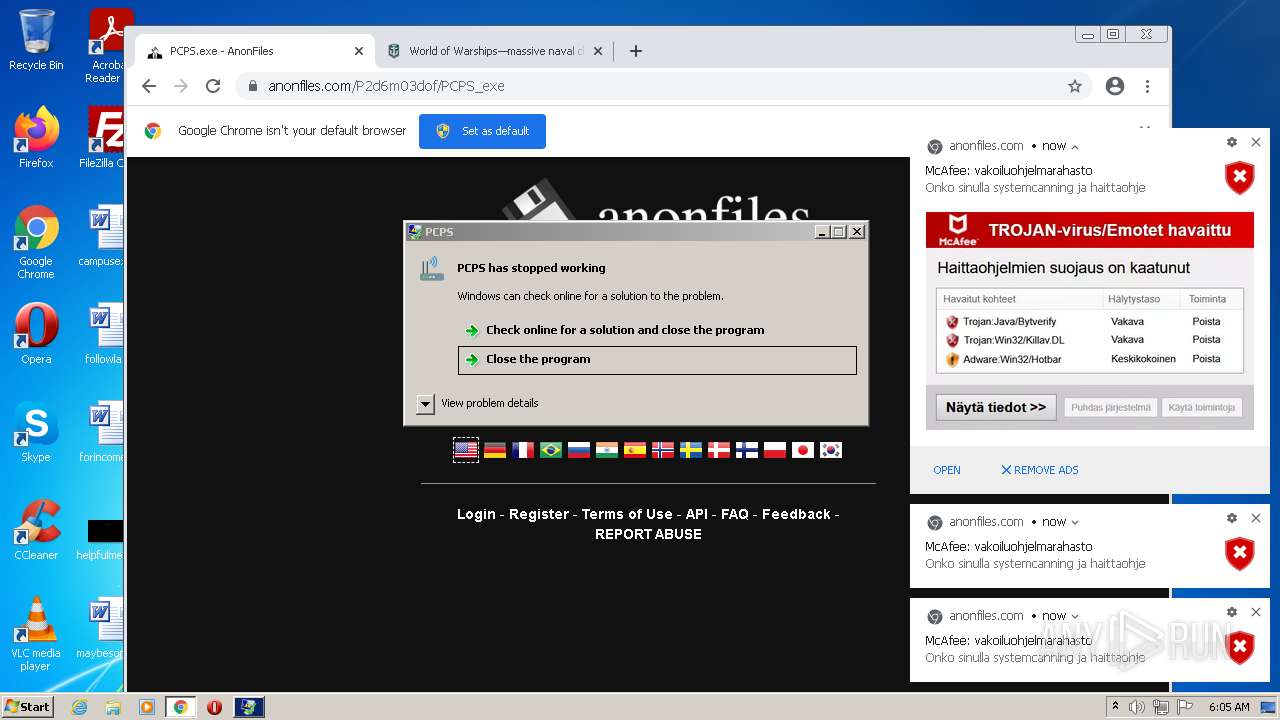
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2022, 06:03:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F0DCC37F3271A95506A578E6D5973F3A |
| SHA1: | 8609E72C41AA859B1841211207375DC8BDCC479A |
| SHA256: | 276707F71B5291CAA4C6EB88AB8B28969723974A4228F9CC83181F797BAFE240 |
| SSDEEP: | 3:N8M2Q5U2rC:2M2Q5U2O |
MALICIOUS
Application was dropped or rewritten from another process
- PCPS.exe (PID: 3552)
Loads dropped or rewritten executable
- PCPS.exe (PID: 3552)
Drops executable file immediately after starts
- PCPS.exe (PID: 3552)
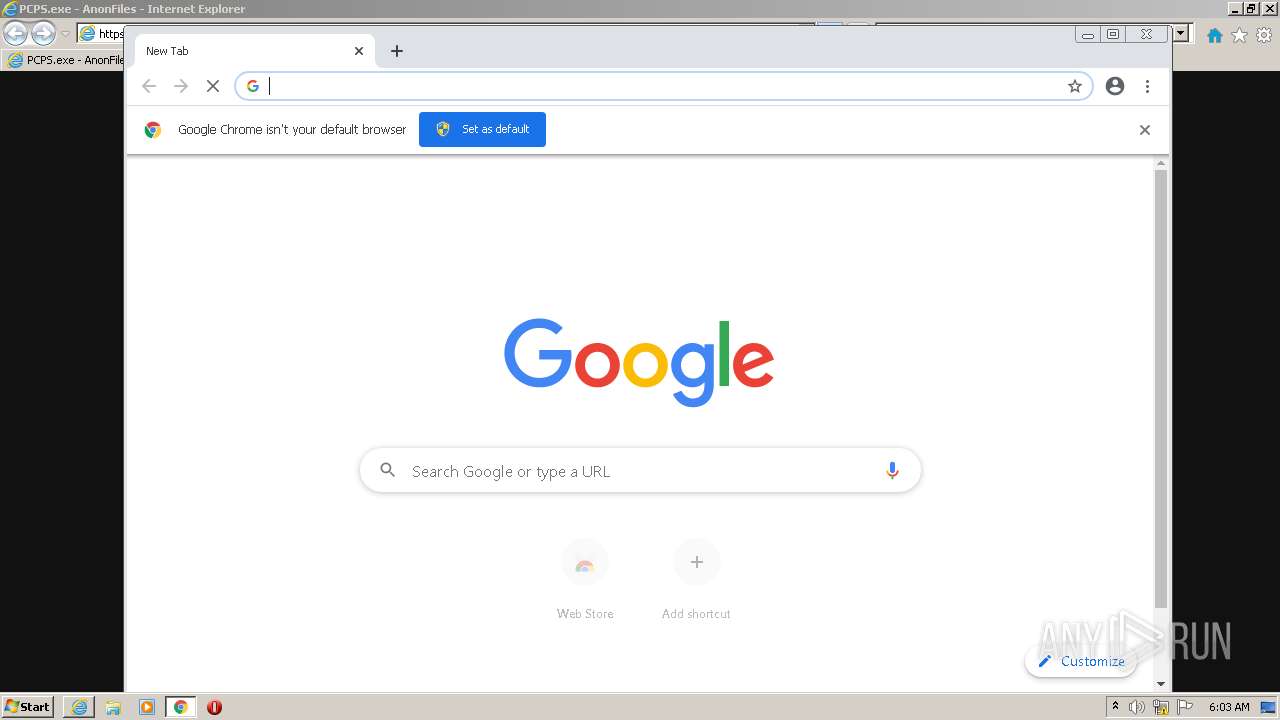
- chrome.exe (PID: 3076)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 532)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3496)
- PCPS.exe (PID: 3552)
- chrome.exe (PID: 3076)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3496)
Executable content was dropped or overwritten
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2560)
- PCPS.exe (PID: 3552)
- chrome.exe (PID: 3076)
Checks supported languages
- PCPS.exe (PID: 3552)
Reads the computer name
- PCPS.exe (PID: 3552)
INFO
Checks supported languages
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 532)
- chrome.exe (PID: 760)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 580)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3076)
Reads the computer name
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 532)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 2376)
Changes internet zones settings
- iexplore.exe (PID: 2824)
Checks Windows Trust Settings
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 2824)
- chrome.exe (PID: 3496)
Application launched itself
- iexplore.exe (PID: 2824)
- chrome.exe (PID: 3496)
Reads internet explorer settings
- iexplore.exe (PID: 532)
Reads settings of System Certificates
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 2824)
- chrome.exe (PID: 2560)
Manual execution by user
- chrome.exe (PID: 3496)
Reads the hosts file
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2560)
Changes settings of System certificates
- iexplore.exe (PID: 2824)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2824)
Reads the date of Windows installation
- iexplore.exe (PID: 2824)
- chrome.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
39
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2824 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x717fd988,0x717fd998,0x717fd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1080 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4008 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3280 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2848 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3428 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8315735377851544647,8082070924963325116,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 772
Read events
23 466
Write events
295
Delete events
11
Modification events
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30945366 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30945366 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
196
Text files
193
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\85E355EF8BE58AD6F5F064D1F33C152F | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE812.tmp | cat | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\85E355EF8BE58AD6F5F064D1F33C152F | der | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE811.tmp | compressed | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\app[1].js | text | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
129
DNS requests
85
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=8_&mip=196.244.192.14&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1646460018&mv=m&mvi=5&pl=25&rmhost=r2---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 74.125.104.230:80 | http://r1---sn-ixh7yn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=196.244.192.14&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1646460018&mv=m&mvi=1&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
2824 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
532 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
2560 | chrome.exe | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 557 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | html | 558 b | whitelisted |
924 | svchost.exe | HEAD | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 558 b | whitelisted |
924 | svchost.exe | GET | 200 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTVkQUFYWTN2V0pFMl9rR2VLalMxS0pyZw/1.0.0.12_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=8_&mip=196.244.192.14&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1646460018&mv=m&mvi=5&pl=25&rmhost=r2---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | crx | 2.84 Kb | whitelisted |
2824 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | iexplore.exe | 45.154.253.150:443 | anonfiles.com | — | — | suspicious |
532 | iexplore.exe | 92.123.195.28:80 | r3.o.lencr.org | Akamai International B.V. | — | suspicious |
532 | iexplore.exe | 104.90.178.254:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
532 | iexplore.exe | 67.26.73.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
532 | iexplore.exe | 151.101.194.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
532 | iexplore.exe | 52.84.107.180:443 | djv99sxoqpv11.cloudfront.net | Amazon.com, Inc. | US | unknown |
532 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2824 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
532 | iexplore.exe | 18.66.242.81:80 | o.ss2.us | Massachusetts Institute of Technology | US | suspicious |
2824 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r3.o.lencr.org |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
ocsp2.globalsign.com |
| whitelisted |
o.ss2.us |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
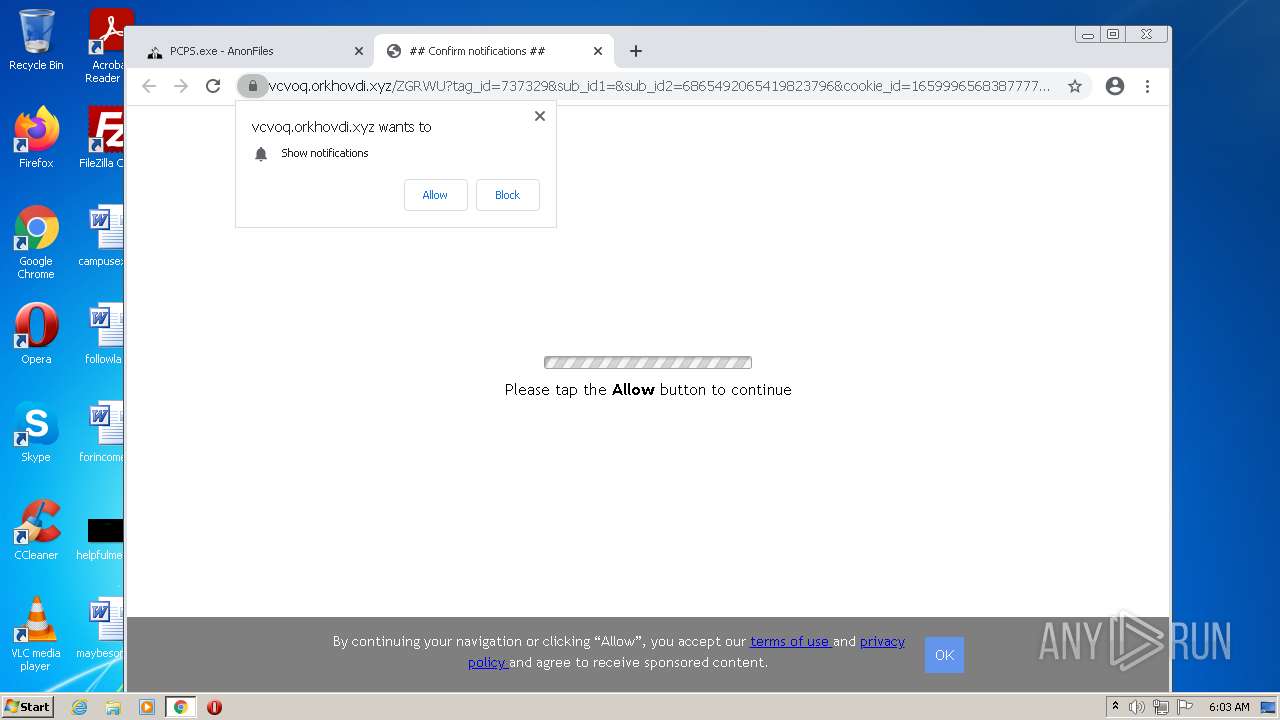
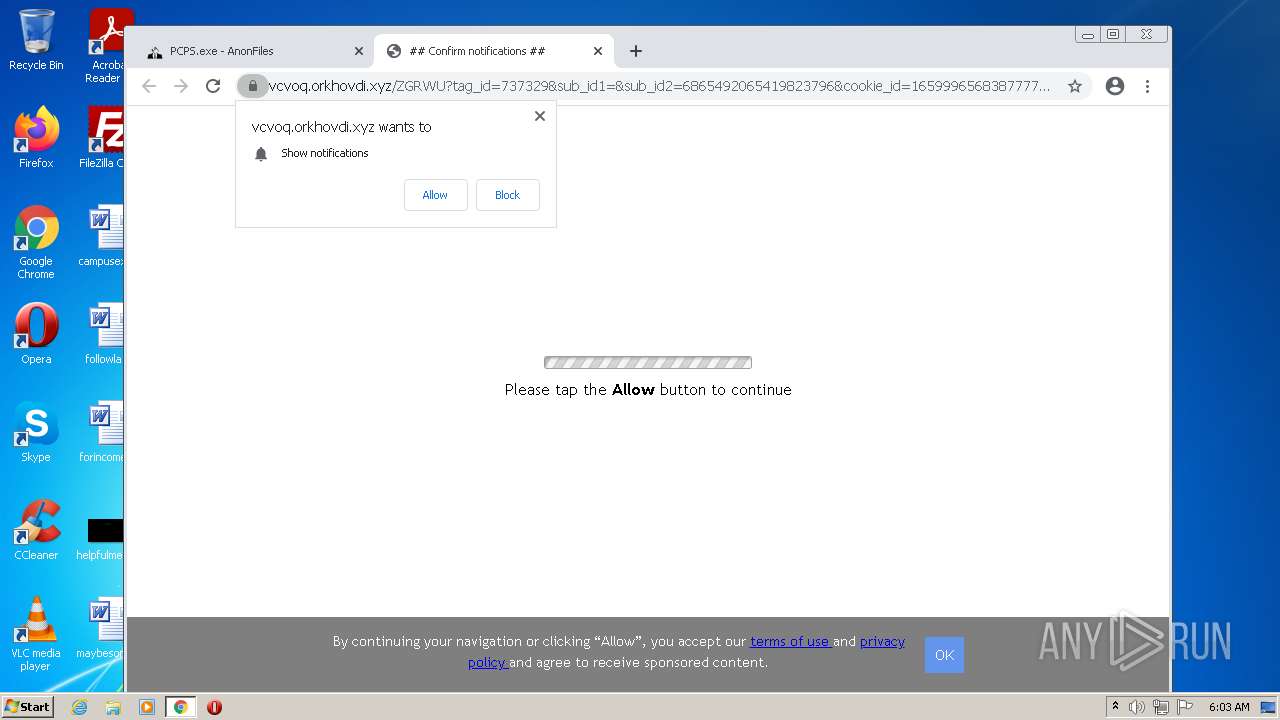
2560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2560 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |