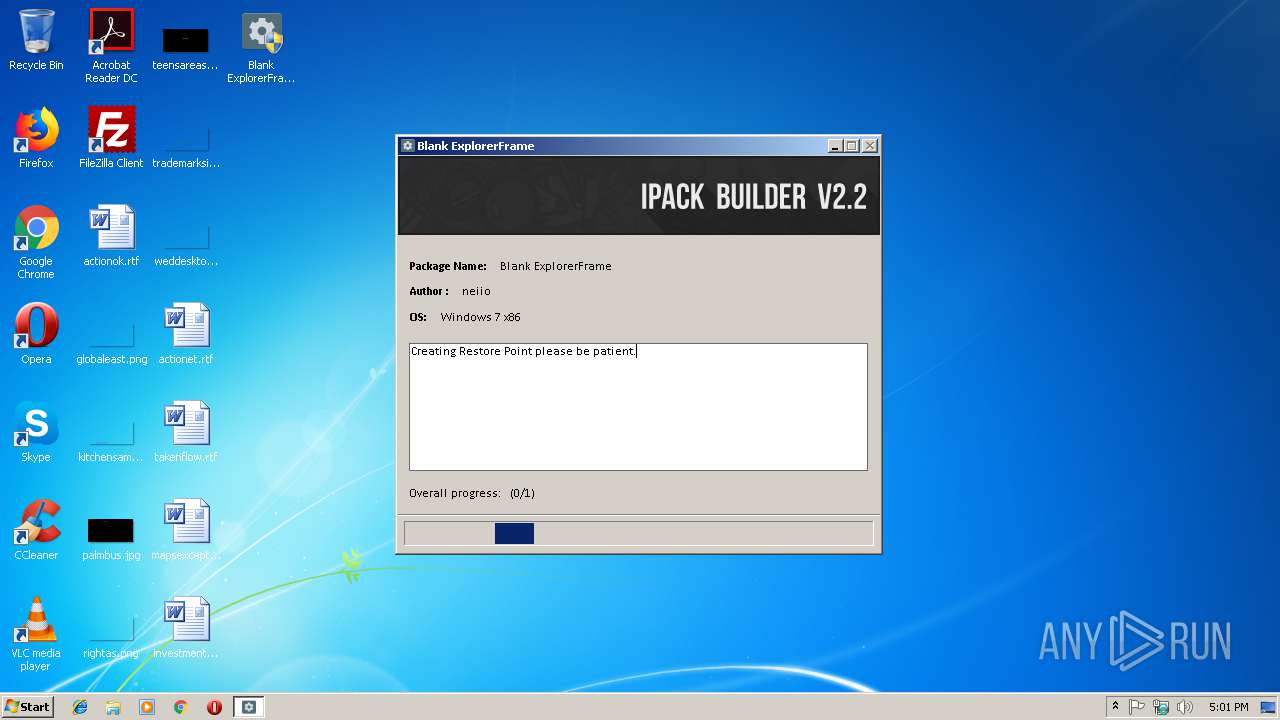
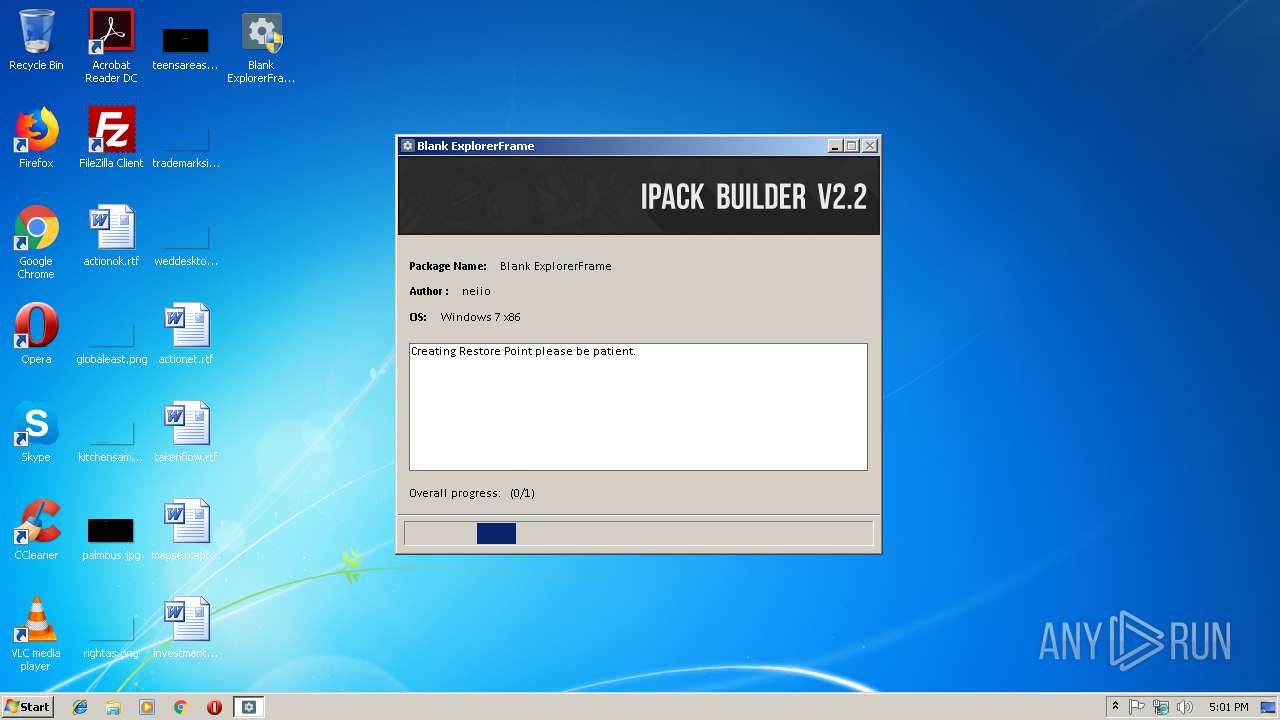
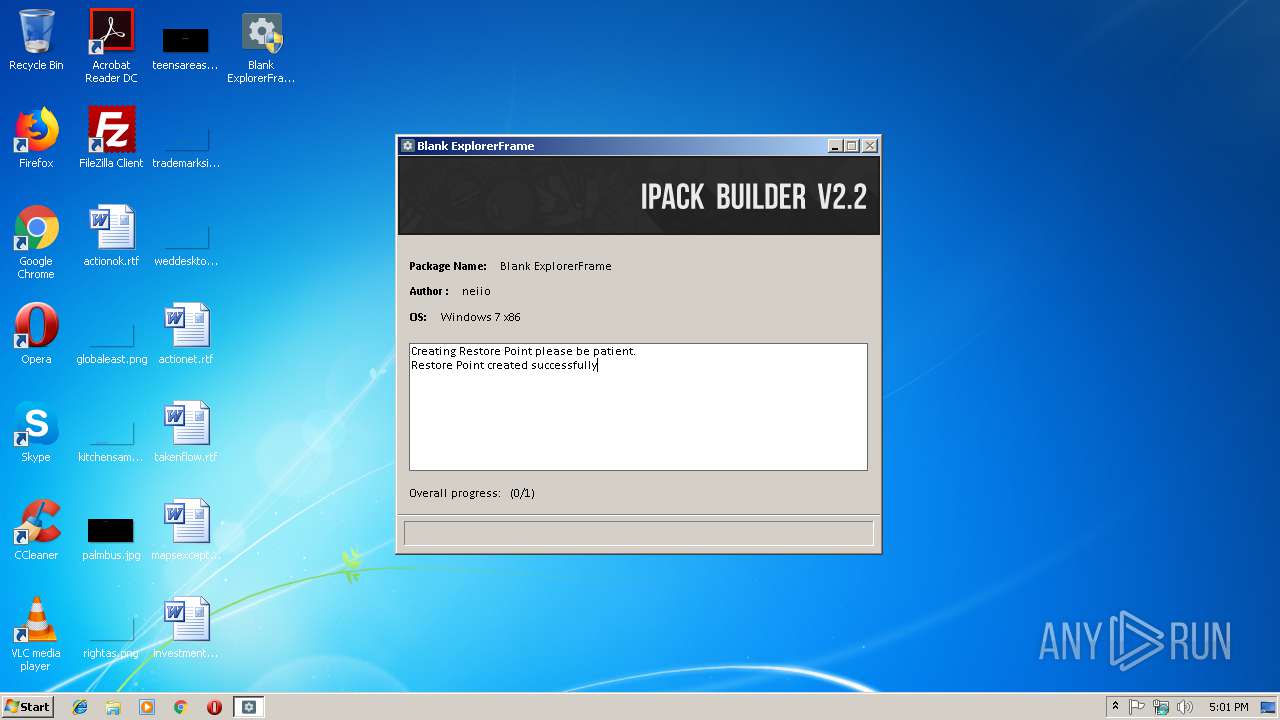
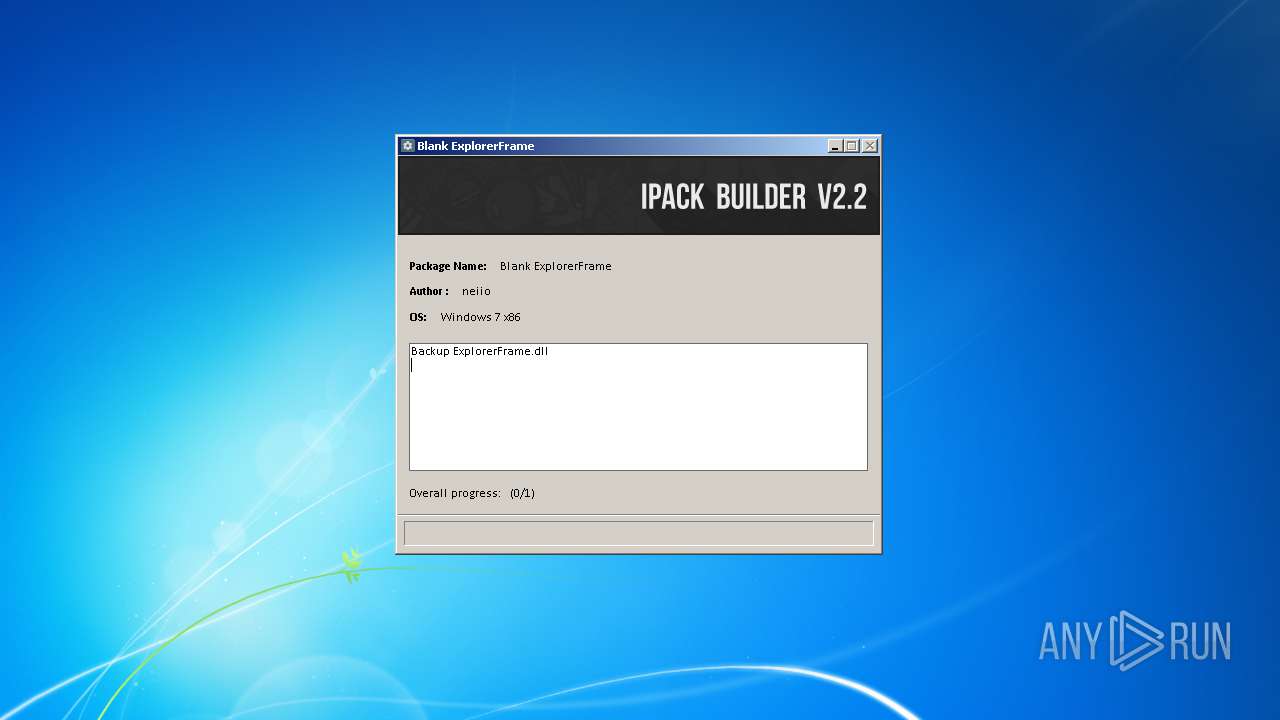
| File name: | Blank ExplorerFrame.exe |
| Full analysis: | https://app.any.run/tasks/88adbf24-e4a5-4c49-bc2e-2706e688de09 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2019, 17:00:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BFAB6EFB15287FEC4C8A1F5B1AC36453 |
| SHA1: | 46DD2F41256B86D6CB2574F900C6C9FB8E8C2366 |
| SHA256: | 275BDDCFC446C9467AAD09B7C154A48EC9B601576E17B623D12D65A2504BA432 |
| SSDEEP: | 24576:nmXLfcMQu4jBgAScXBp6iAJK1FUuiviHwfnm2FjYi:mAMQu4uXcDiQ1FUBvMwe2FjJ |
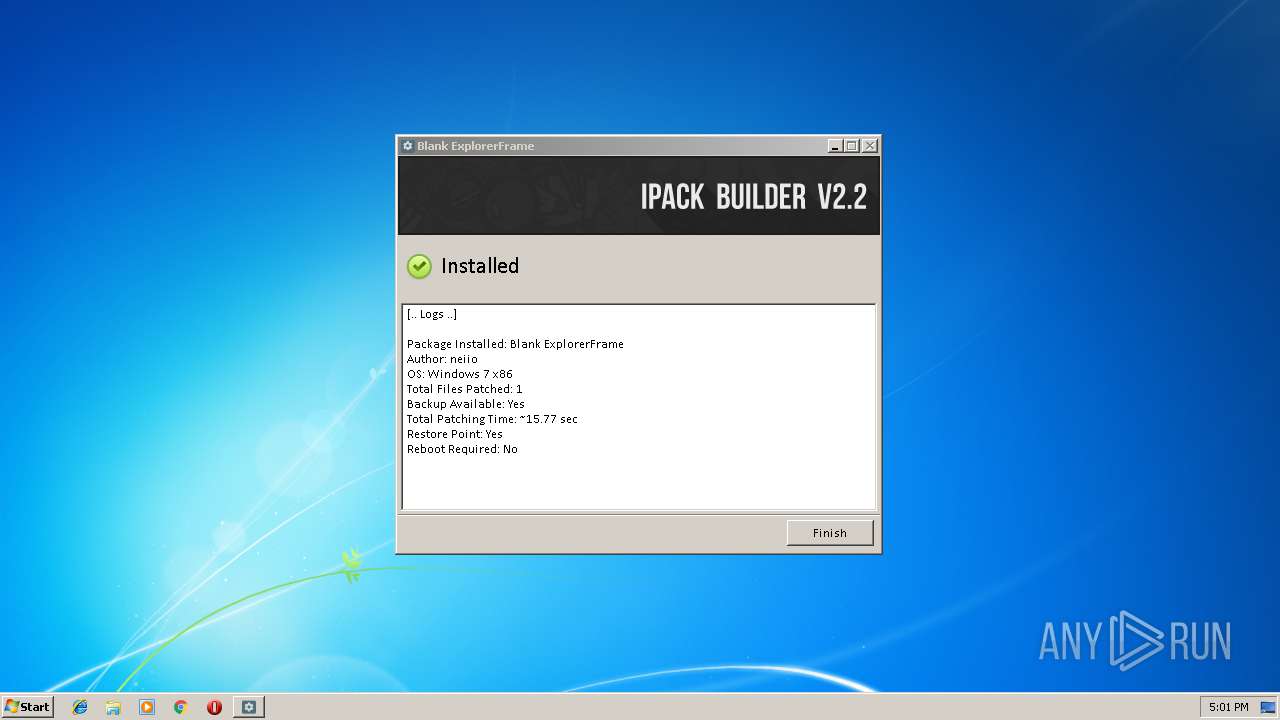
MALICIOUS
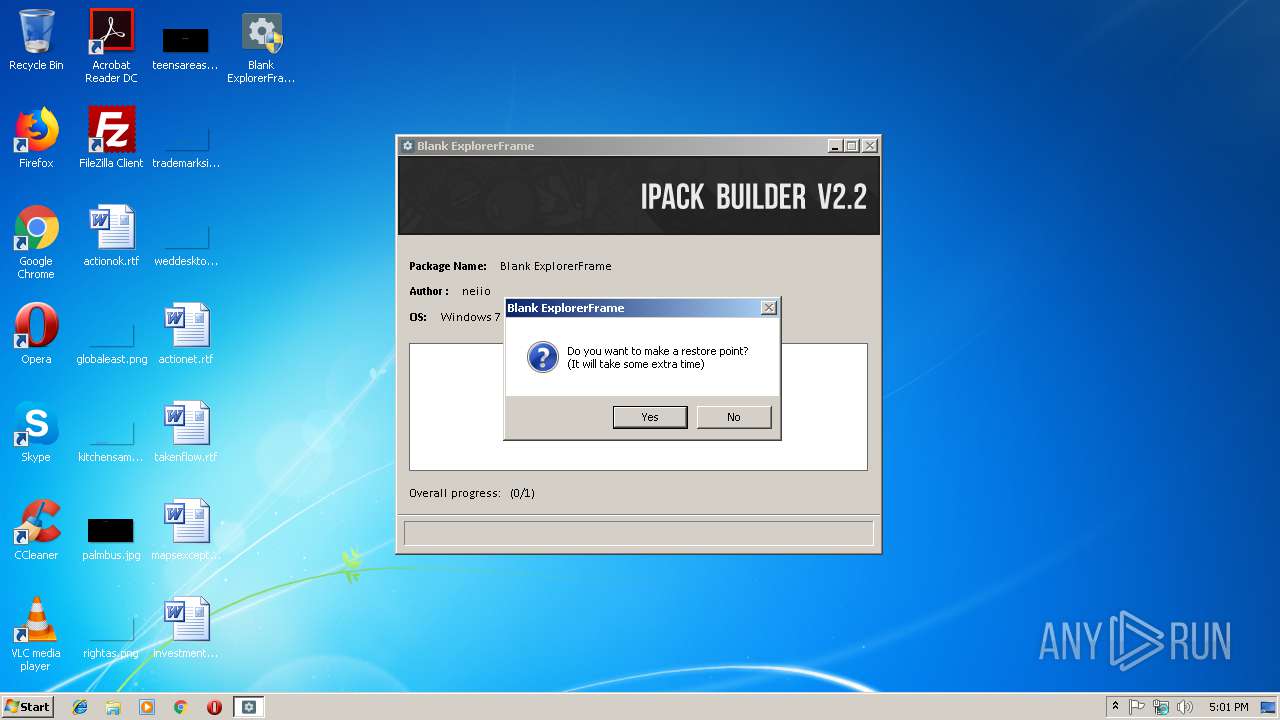
Application was dropped or rewritten from another process
- iPack_Installer.exe (PID: 3720)
- Patcher.exe (PID: 2356)
- 7z.exe (PID: 2348)
Loads the Task Scheduler COM API
- explorer.exe (PID: 2428)
Loads dropped or rewritten executable
- explorer.exe (PID: 2428)
- Blank ExplorerFrame.exe (PID: 2288)
SUSPICIOUS
Creates files in the program directory
- Blank ExplorerFrame.exe (PID: 2288)
- 7z.exe (PID: 2348)
- iPack_Installer.exe (PID: 3720)
- Patcher.exe (PID: 2356)
- icacls.exe (PID: 4048)
Reads internet explorer settings
- iPack_Installer.exe (PID: 3720)
Searches for installed software
- DllHost.exe (PID: 3132)
Uses ICACLS.EXE to modify access control list
- iPack_Installer.exe (PID: 3720)
- cmd.exe (PID: 3288)
- cmd.exe (PID: 3196)
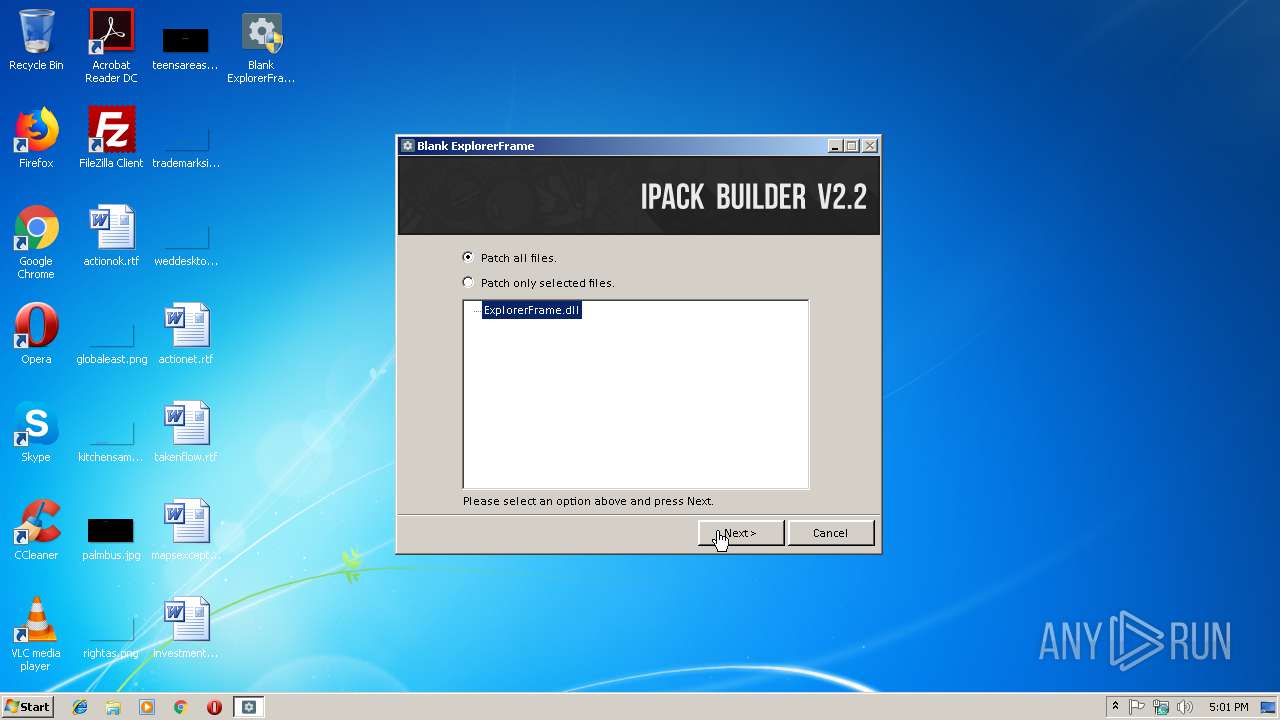
Executable content was dropped or overwritten
- Patcher.exe (PID: 2356)
- iPack_Installer.exe (PID: 3720)
- Blank ExplorerFrame.exe (PID: 2288)
Starts CMD.EXE for commands execution
- iPack_Installer.exe (PID: 3720)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3564)
Application launched itself
- explorer.exe (PID: 2428)
Creates a software uninstall entry
- iPack_Installer.exe (PID: 3720)
Uses TASKKILL.EXE to kill process
- iPack_Installer.exe (PID: 3720)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:27 09:06:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 61440 |
| InitializedDataSize: | 294912 |
| UninitializedDataSize: | 409600 |
| EntryPoint: | 0x73320 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
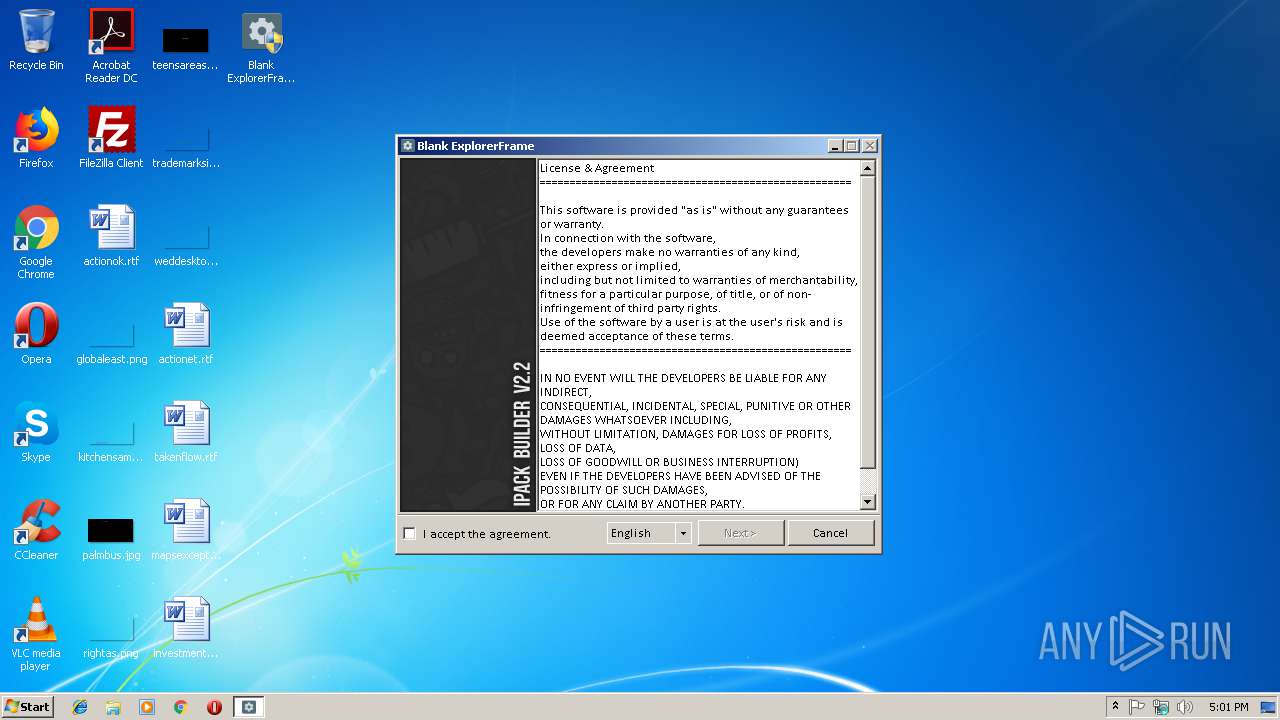
| CompanyName: | neiio |
| FileDescription: | iPack |
| FileVersion: | 1 |
| InternalName: | iPack |
| LegalCopyright: | gpl |
| OriginalFileName: | Blank ExplorerFrame.exe |
| ProductName: | Blank ExplorerFrame |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jun-2010 07:06:38 |
| Detected languages: |
|
| CompanyName: | neiio |
| FileDescription: | iPack |
| FileVersion: | 1 |
| InternalName: | iPack |
| LegalCopyright: | gpl |
| OriginalFilename: | Blank ExplorerFrame.exe |
| ProductName: | Blank ExplorerFrame |
| ProductVersion: | 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Jun-2010 07:06:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00064000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00065000 | 0x0000F000 | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9011 |
.rsrc | 0x00074000 | 0x00048000 | 0x00047200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.37398 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19958 | 1663 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.43394 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 3.61681 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.14867 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.39755 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 3.27245 | 270376 | UNKNOWN | English - United States | RT_ICON |
101 | 2.66848 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
68
Monitored processes
24
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1536 | ATTRIB +H "C:\Program Files\Blank ExplorerFrame\Uninstall iPack.exe.config" /S /D | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | ICACLS "C:\Users\admin\AppData\Local\IconCache.db" /grant:r "admin":F /T | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\Blank ExplorerFrame.exe" | C:\Users\admin\Desktop\Blank ExplorerFrame.exe | explorer.exe | ||||||||||||
User: admin Company: neiio Integrity Level: HIGH Description: iPack Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 2332 | TAKEOWN /f "C:\Users\admin\AppData\Local\IconCache.db" | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Blank ExplorerFrame\7z.exe" x -y -bd "C:\Program Files\Blank ExplorerFrame\Resource.7z" | C:\Program Files\Blank ExplorerFrame\7z.exe | — | iPack_Installer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Blank ExplorerFrame\Patcher.exe" -addoverwrite "Resource Files\Patch\System32\ExplorerFrame.dll", "Resource Files\Patch\System32\ExplorerFrame.dll", "Resource Files\ExplorerFrame.dll.res" ,,, | C:\Program Files\Blank ExplorerFrame\Patcher.exe | iPack_Installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Resource viewer, decompiler & recompiler. Exit code: 0 Version: 3.6.0.92 Modules
| |||||||||||||||
| 2372 | TAKEOWN /f "C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer" /r /d y | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000003F0" "000005C0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | icacls "C:\Windows\System32\ExplorerFrame.dll" /grant:r "admin":F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 373
Read events
2 062
Write events
309
Delete events
2
Modification events
| (PID) Process: | (2288) Blank ExplorerFrame.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2288) Blank ExplorerFrame.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3720) iPack_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3720) iPack_Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3132) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000946AD3CBBDC3D4013C0C0000B80D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3132) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3132) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000007A531DCCBDC3D4013C0C0000B80D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3132) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D4B51FCCBDC3D4013C0C0000A80C0000E8030000010000000000000000000000BDC730913E4E5145BF93E8D398F74FBF0000000000000000 | |||
| (PID) Process: | (3640) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000096A12BCCBDC3D401380E0000380D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3640) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000096A12BCCBDC3D401380E000084040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
12
Text files
79
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3132 | DllHost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3720 | iPack_Installer.exe | C:\Program Files\Blank ExplorerFrame\Resource.7z | compressed | |
MD5:— | SHA256:— | |||
| 2288 | Blank ExplorerFrame.exe | C:\Program Files\Blank ExplorerFrame\Resource.iPack | binary | |
MD5:— | SHA256:— | |||
| 2288 | Blank ExplorerFrame.exe | C:\Program Files\Blank ExplorerFrame\Setup files-iPack\Configuration.config | text | |
MD5:— | SHA256:— | |||
| 2288 | Blank ExplorerFrame.exe | C:\Program Files\Blank ExplorerFrame\iPack_Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 2348 | 7z.exe | C:\Program Files\Blank ExplorerFrame\Resource Files\ExplorerFrame.dll.res | res | |
MD5:— | SHA256:— | |||
| 2828 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 2828 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 3640 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2828 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report