| File name: | 2740bd2b7aa0eaa8de2135dd710eb669d4c4c91d29eefbf54f1b81165ad2da4d.exe |
| Full analysis: | https://app.any.run/tasks/cc04e696-af90-4cfe-ba16-963b50a84ae6 |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2020, 18:22:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 55CD380A63FAD7A750B7C03E3E57FED4 |
| SHA1: | 37CC9744468E97ED2DA503A4DCA8CEFD97E2D7A4 |
| SHA256: | 2740BD2B7AA0EAA8DE2135DD710EB669D4C4C91D29EEFBF54F1B81165AD2DA4D |
| SSDEEP: | 6144:YR5cI2McXLRvIV97X9GN/3EAOlqGrP0iFA:YfcIjcXLRvIV9q/3EHciFA |
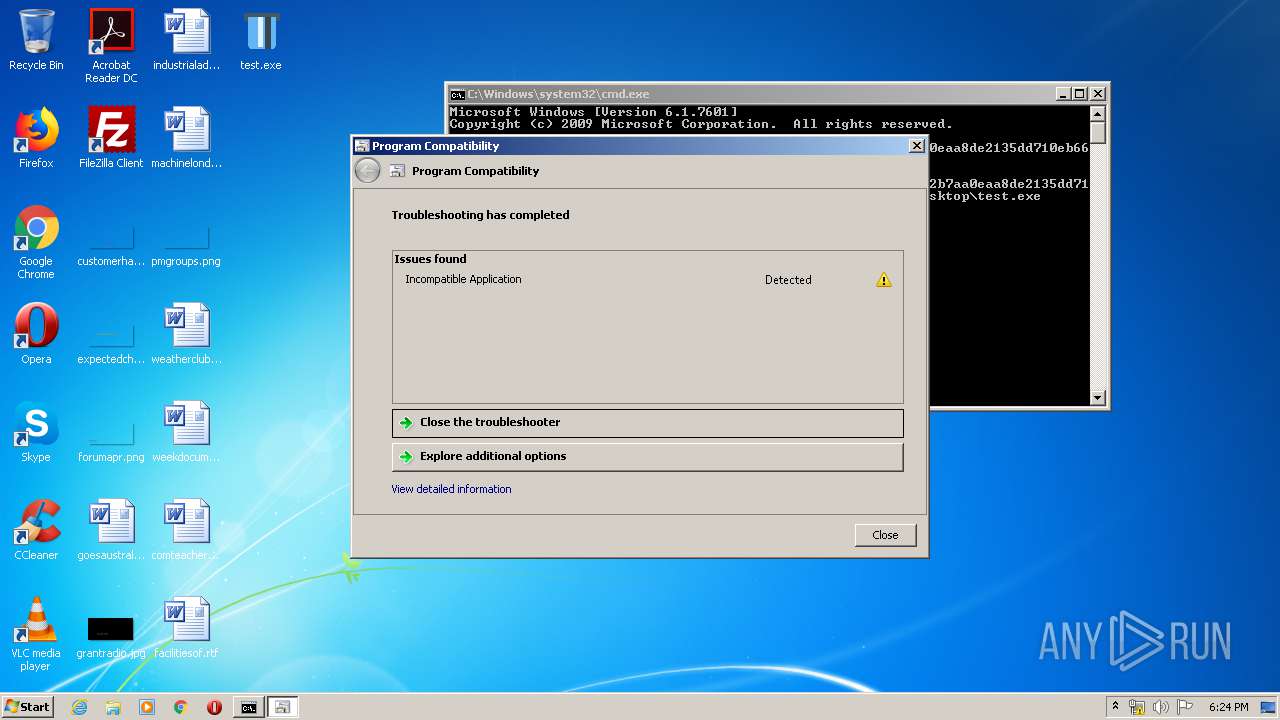
MALICIOUS
Starts Visual C# compiler
- sdiagnhost.exe (PID: 4008)
- sdiagnhost.exe (PID: 1860)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 3624)
SUSPICIOUS
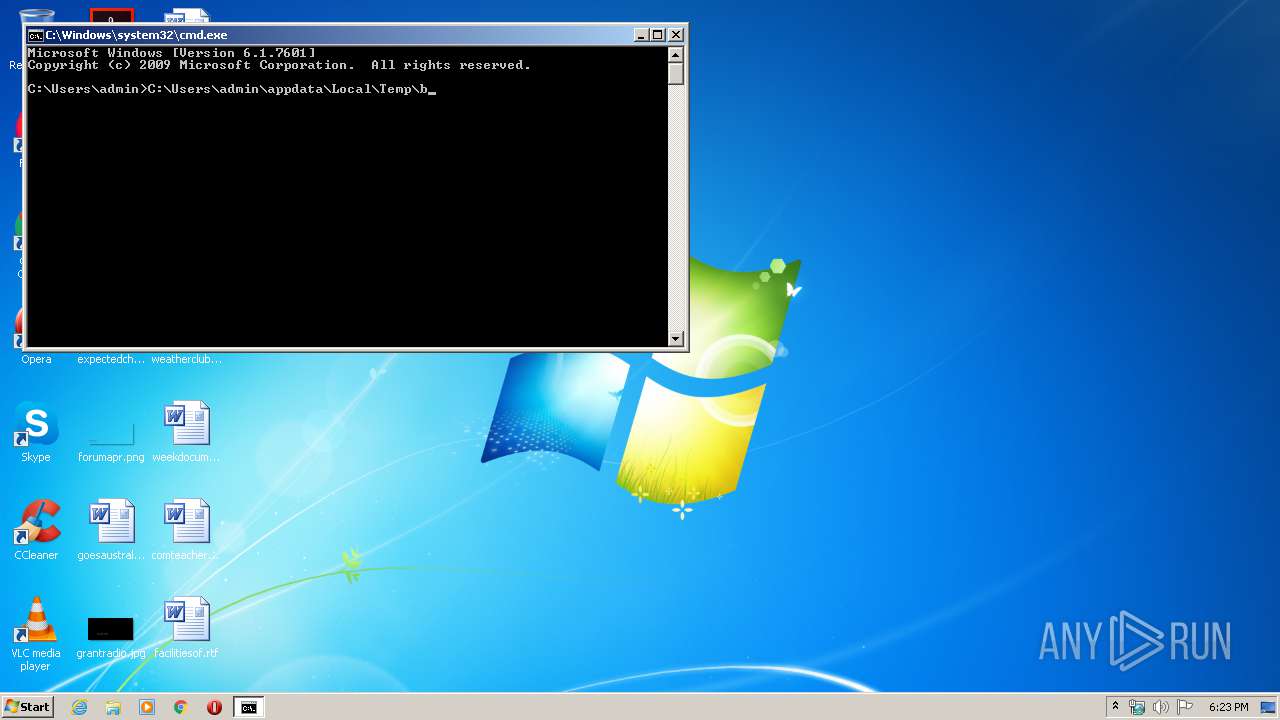
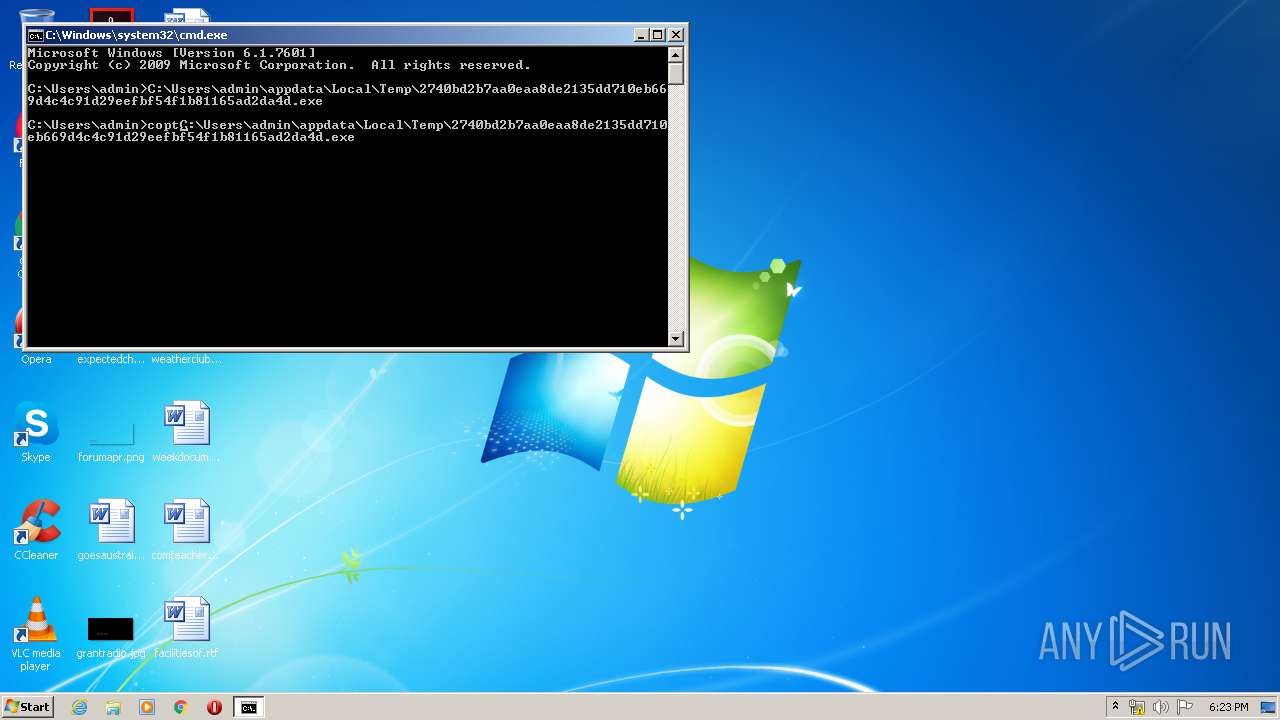
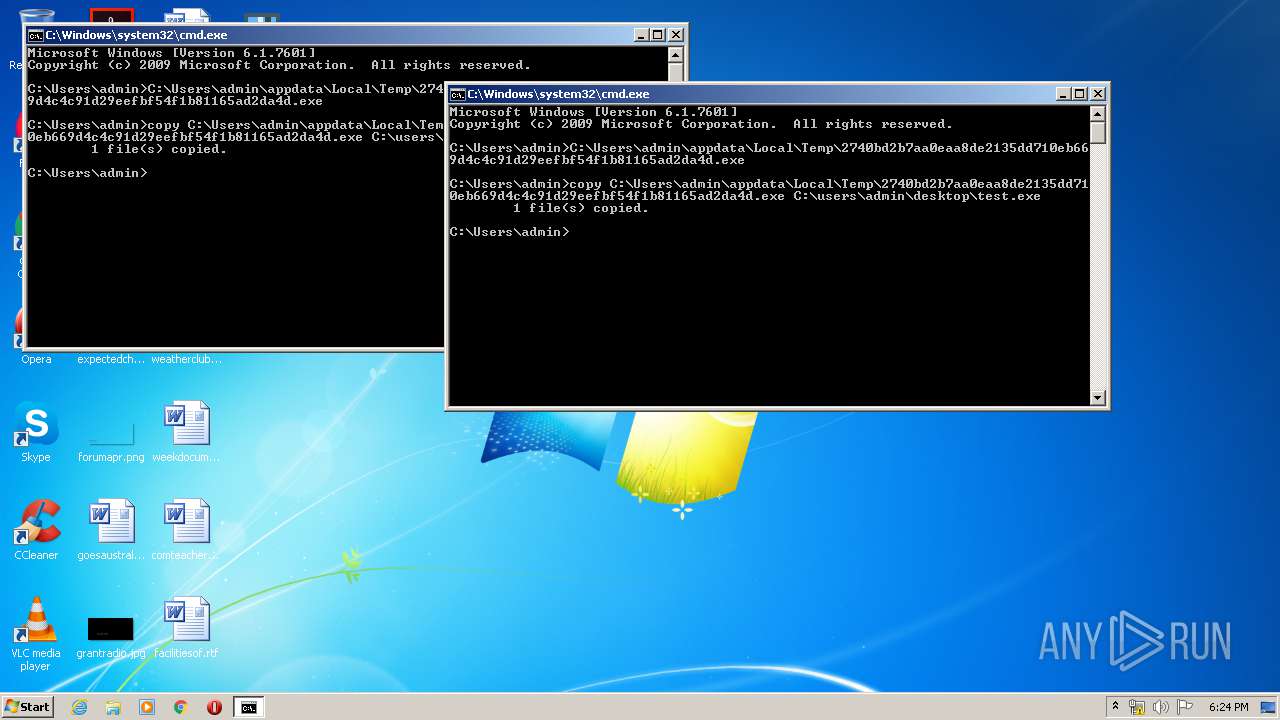
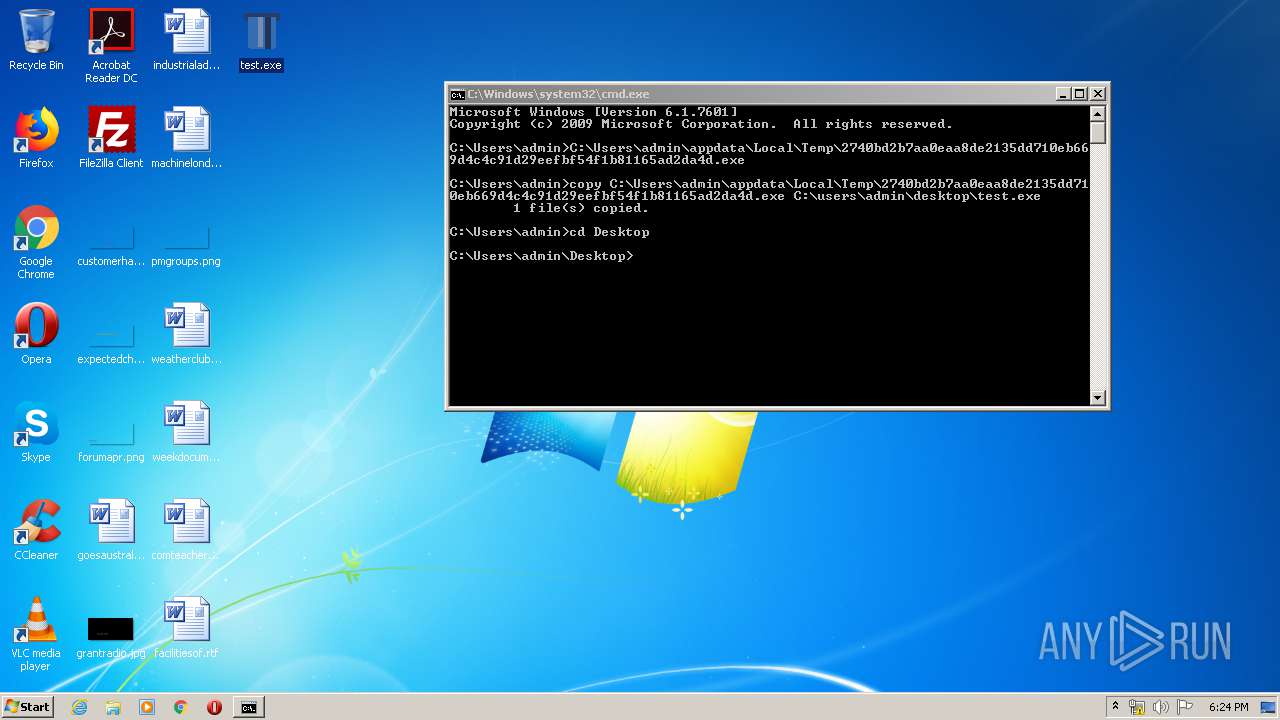
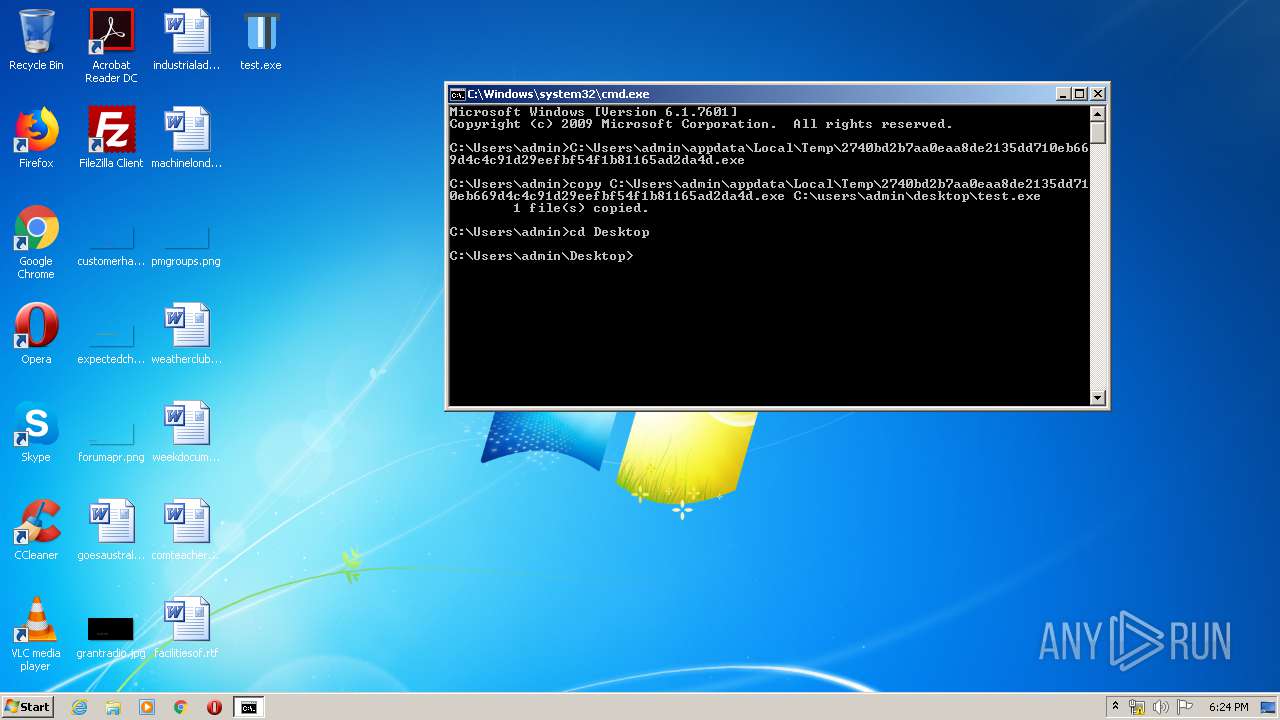
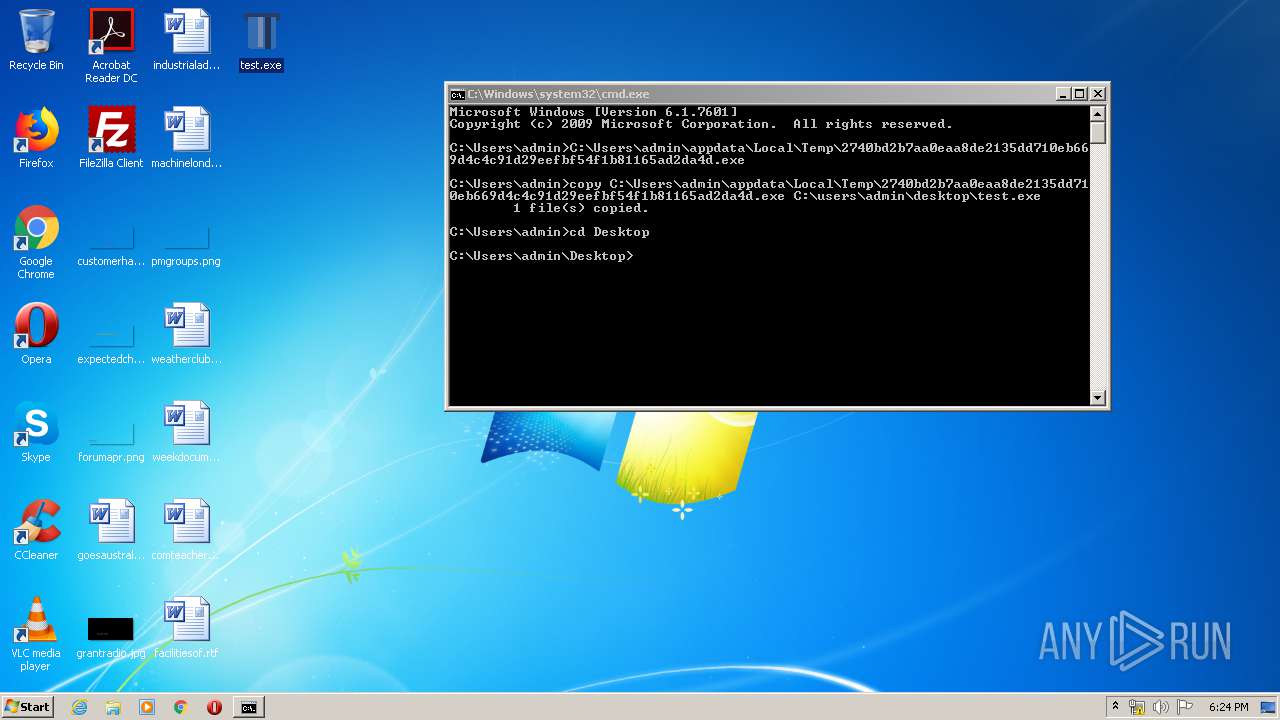
Executable content was dropped or overwritten
- cmd.exe (PID: 3732)
- msdt.exe (PID: 3924)
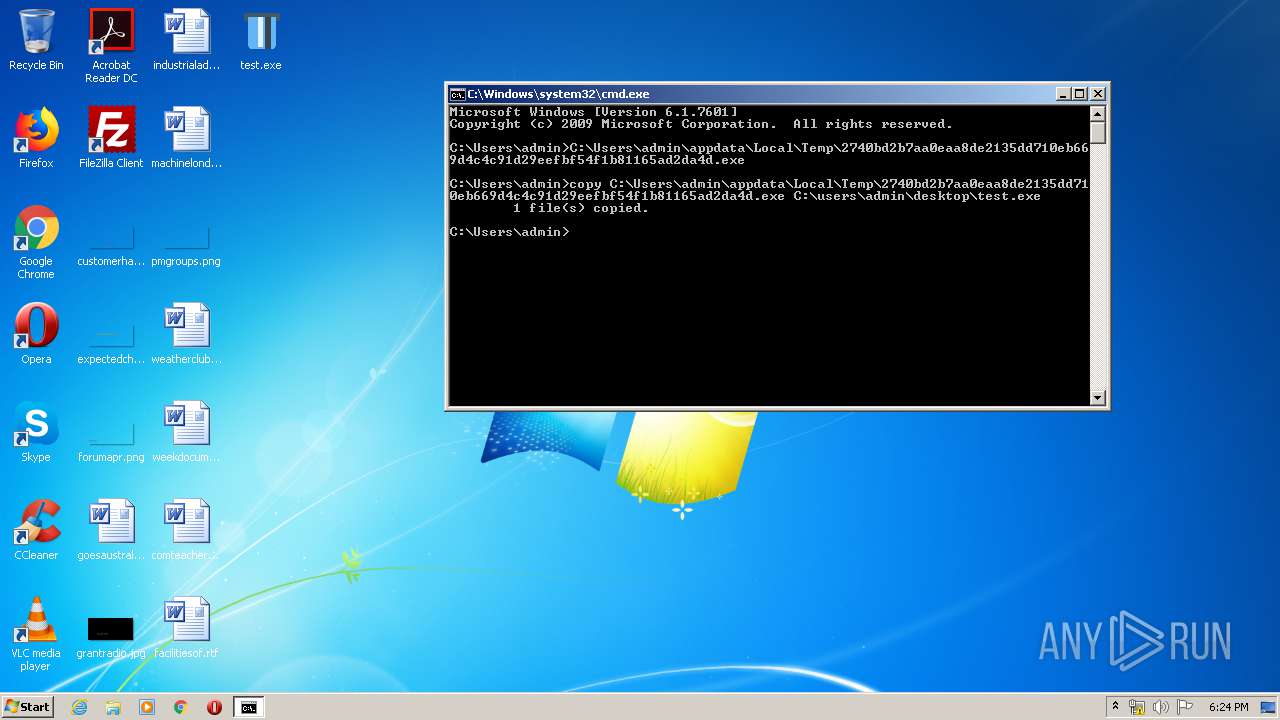
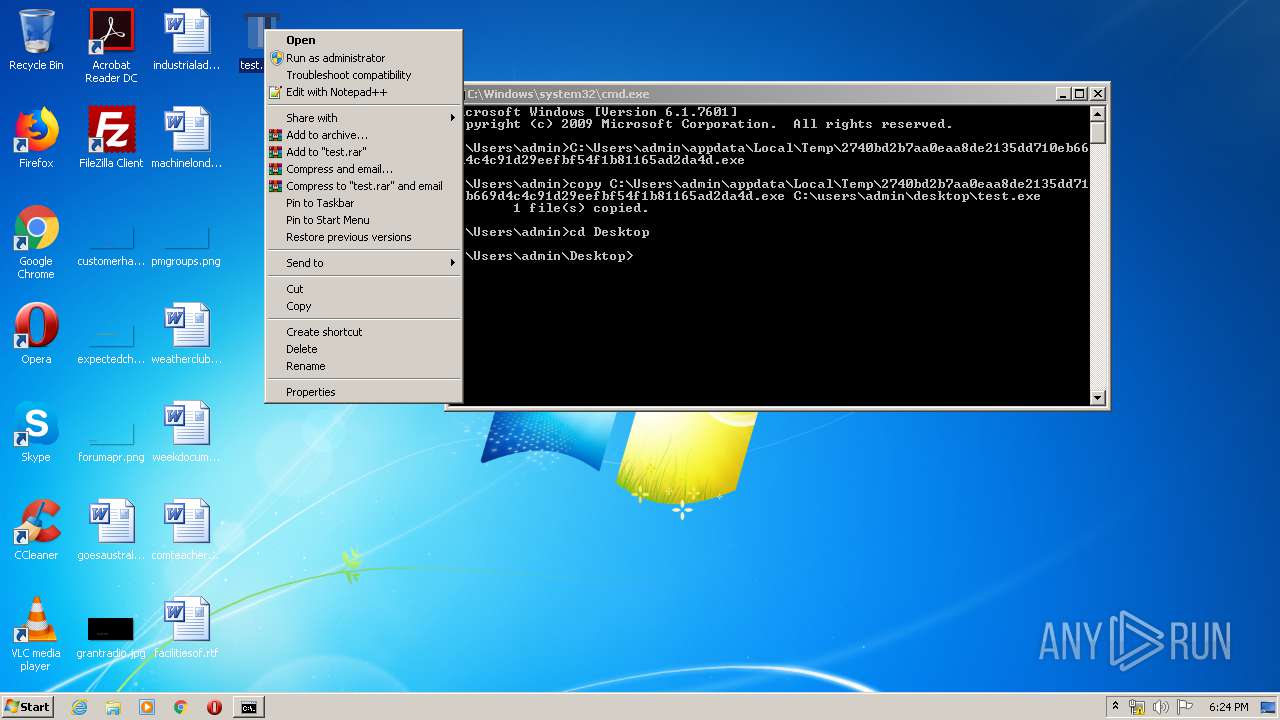
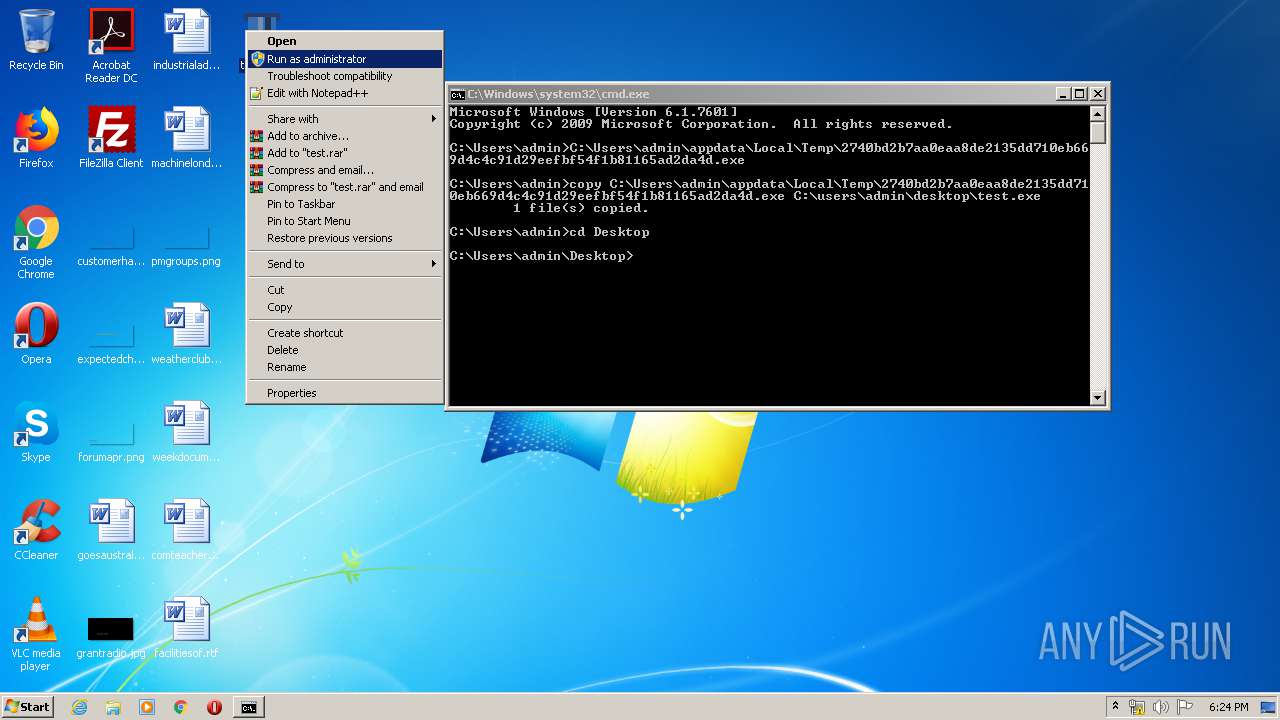
Executed via Task Scheduler
- test.exe (PID: 2580)
- test.exe (PID: 3320)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 3924)
Executed via COM
- sdiagnhost.exe (PID: 1860)
- sdiagnhost.exe (PID: 4008)
INFO
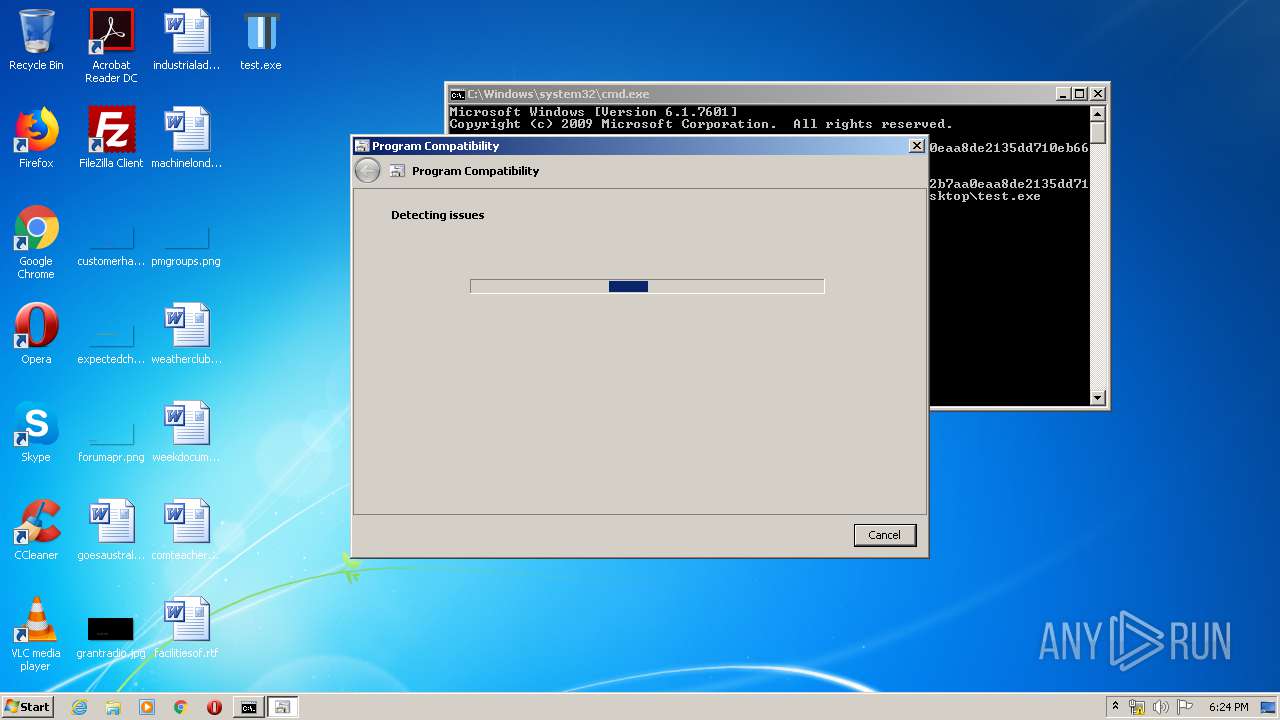
Manual execution by user
- cmd.exe (PID: 3732)
- pcwrun.exe (PID: 3880)
- test.exe (PID: 1928)
- test.exe (PID: 3932)
- test.exe (PID: 1296)
- test.exe (PID: 1780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:21 12:26:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.2 |
| CodeSize: | 113152 |
| InitializedDataSize: | 161792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7ff6 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jun-2019 10:26:43 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Jun-2019 10:26:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001B9EB | 0x0001BA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63441 |
.rdata | 0x0001D000 | 0x0000E868 | 0x0000EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.53822 |
.data | 0x0002C000 | 0x00001EFC | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.16762 |
.rsrc | 0x0002E000 | 0x00014B38 | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.88618 |
.reloc | 0x00043000 | 0x00002018 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.4399 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.82173 | 41640 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 1.04767 | 44 | UNKNOWN | Russian - Russia | RT_STRING |
103 | 3.37211 | 296 | UNKNOWN | Russian - Russia | RT_DIALOG |
107 | 1.91924 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
108 | 2.0815 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
109 | 1.79879 | 16 | UNKNOWN | Russian - Russia | RT_ACCELERATOR |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
70
Monitored processes
24
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4323.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4322.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Temp\2740bd2b7aa0eaa8de2135dd710eb669d4c4c91d29eefbf54f1b81165ad2da4d.exe" | C:\Users\admin\AppData\Local\Temp\2740bd2b7aa0eaa8de2135dd710eb669d4c4c91d29eefbf54f1b81165ad2da4d.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\Desktop\test.exe" | C:\Users\admin\Desktop\test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1688 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\fbcpd9py.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\Desktop\test.exe" | C:\Users\admin\Desktop\test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1860 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\9cjliwab.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\Desktop\test.exe" | C:\Users\admin\Desktop\test.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2252 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES44D8.tmp" "c:\Users\admin\AppData\Local\Temp\CSC44D7.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2360 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9097.tmp" "c:\Users\admin\AppData\Local\Temp\CSC9096.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
217
Read events
178
Write events
39
Delete events
0
Modification events
| (PID) Process: | (3924) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1860) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1860) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
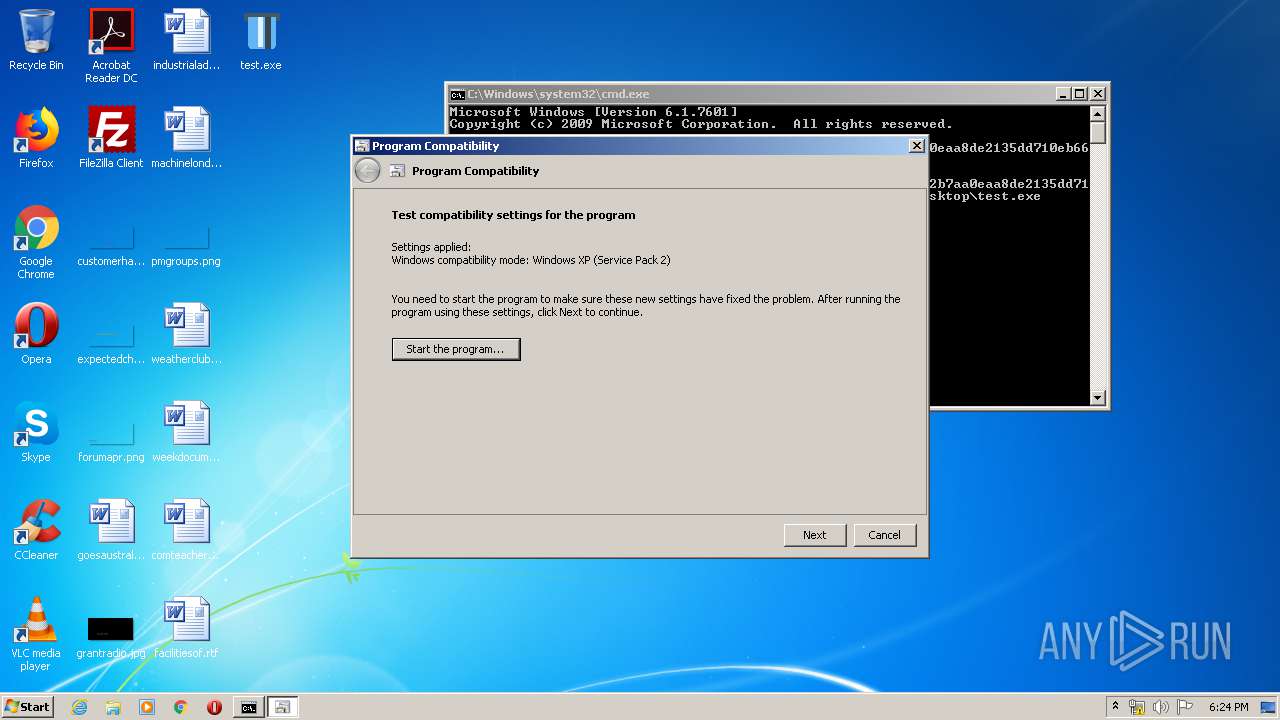
| (PID) Process: | (1860) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Users\admin\Desktop\test.exe |
Value: # WINXPSP2 | |||
| (PID) Process: | (3924) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3924) msdt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4008) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4008) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
3
Text files
30
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1900 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC4322.tmp | — | |
MD5:— | SHA256:— | |||
| 1900 | csc.exe | C:\Users\admin\AppData\Local\Temp\9cjliwab.pdb | — | |
MD5:— | SHA256:— | |||
| 1064 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES4323.tmp | — | |
MD5:— | SHA256:— | |||
| 1900 | csc.exe | C:\Users\admin\AppData\Local\Temp\9cjliwab.dll | — | |
MD5:— | SHA256:— | |||
| 1900 | csc.exe | C:\Users\admin\AppData\Local\Temp\9cjliwab.out | — | |
MD5:— | SHA256:— | |||
| 1860 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\fbcpd9py.0.cs | — | |
MD5:— | SHA256:— | |||
| 1860 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\fbcpd9py.cmdline | — | |
MD5:— | SHA256:— | |||
| 1688 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC43DD.tmp | — | |
MD5:— | SHA256:— | |||
| 1688 | csc.exe | C:\Users\admin\AppData\Local\Temp\fbcpd9py.pdb | — | |
MD5:— | SHA256:— | |||
| 2760 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES43DE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|