analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | C:\Users\admin\AppData\Roaming\nameX.exe |
| Full analysis: | https://app.any.run/tasks/e6d320a9-f140-4051-b82a-d8ba2f4b4f53 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 18, 2019, 15:46:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 93D602F0328CE1369929CECE8F05CCC1 |
| SHA1: | 63179791EABB25BA6BD6EF39CE1C804985D26E78 |
| SHA256: | 273B77DCA5D55FED454A74AC31E64FAD53F92136910192D08A8C40CAF3904469 |
| SSDEEP: | 12288:7p96pk6IQEwitkEMKOpRNnSoZy9NiV4LypL0wMKSSeaiTU:dgk6IQAtkEOjFS8y9UVscASea6U |
MALICIOUS
AGENTTESLA was detected
- nameX.exe (PID: 2692)
Actions looks like stealing of personal data
- nameX.exe (PID: 2692)
SUSPICIOUS
Reads Windows Product ID
- nameX.exe (PID: 2692)
Application launched itself
- nameX.exe (PID: 3536)
Reads Internet Cache Settings
- nameX.exe (PID: 2692)
Checks for external IP
- nameX.exe (PID: 2692)
Reads Environment values
- nameX.exe (PID: 2692)
INFO
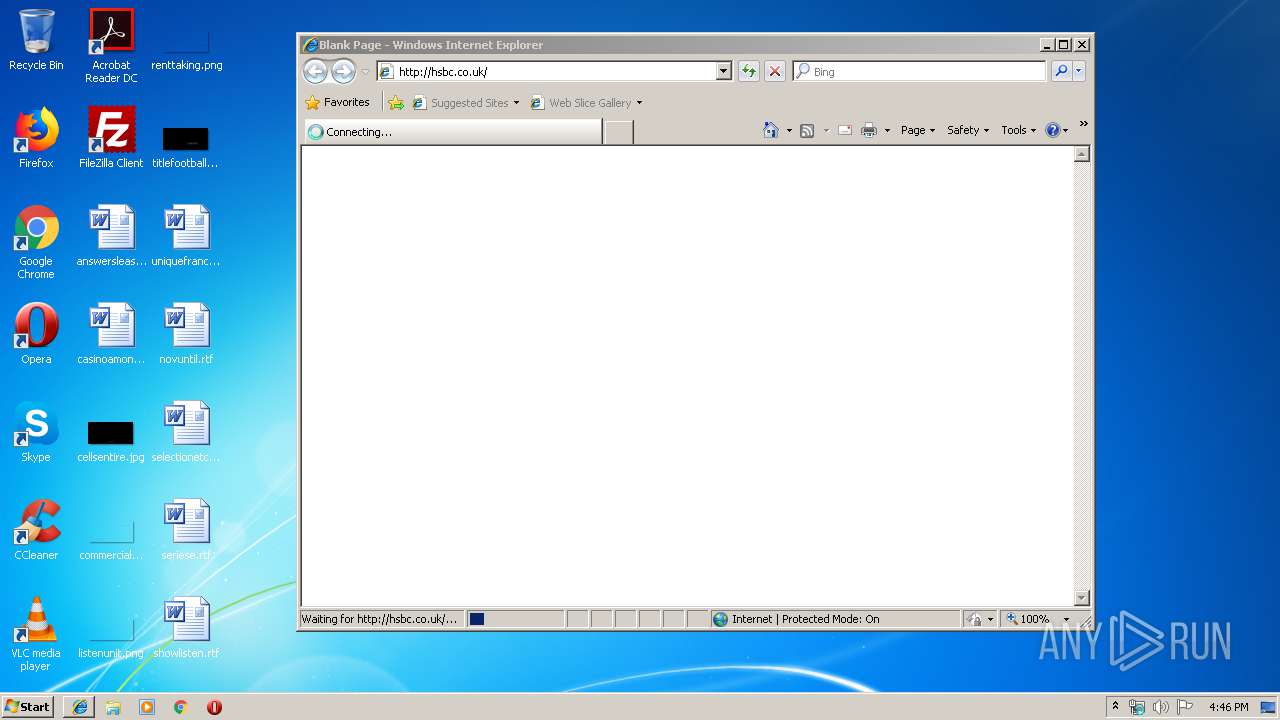
Manual execution by user
- iexplore.exe (PID: 2064)
- WINWORD.EXE (PID: 3956)
Changes internet zones settings
- iexplore.exe (PID: 2064)
Creates files in the user directory
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2084)
- WINWORD.EXE (PID: 3956)
Reads internet explorer settings
- iexplore.exe (PID: 2084)
Reads Internet Cache Settings
- iexplore.exe (PID: 2084)
Reads settings of System Certificates
- iexplore.exe (PID: 2064)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Tetris |
| OriginalFileName: | Tetris_Novi.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © Hewlett-Packard 2017 |
| InternalName: | Tetris_Novi.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Tetris |
| CompanyName: | Hewlett-Packard |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xc463e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2048 |
| CodeSize: | 796672 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2019:09:17 23:55:02+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2019 21:55:02 |
| Comments: | - |
| CompanyName: | Hewlett-Packard |
| FileDescription: | Tetris |
| FileVersion: | 1.0.0.0 |
| InternalName: | Tetris_Novi.exe |
| LegalCopyright: | Copyright © Hewlett-Packard 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | Tetris_Novi.exe |
| ProductName: | Tetris |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 17-Sep-2019 21:55:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000C2644 | 0x000C2800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.75168 |
.rsrc | 0x000C6000 | 0x00000600 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.19008 |
.reloc | 0x000C8000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0940979 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3536 | "C:\Users\admin\AppData\Local\Temp\nameX.exe" | C:\Users\admin\AppData\Local\Temp\nameX.exe | — | explorer.exe |
User: admin Company: Hewlett-Packard Integrity Level: MEDIUM Description: Tetris Exit code: 0 Version: 1.0.0.0 | ||||
| 2064 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 2084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2064 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
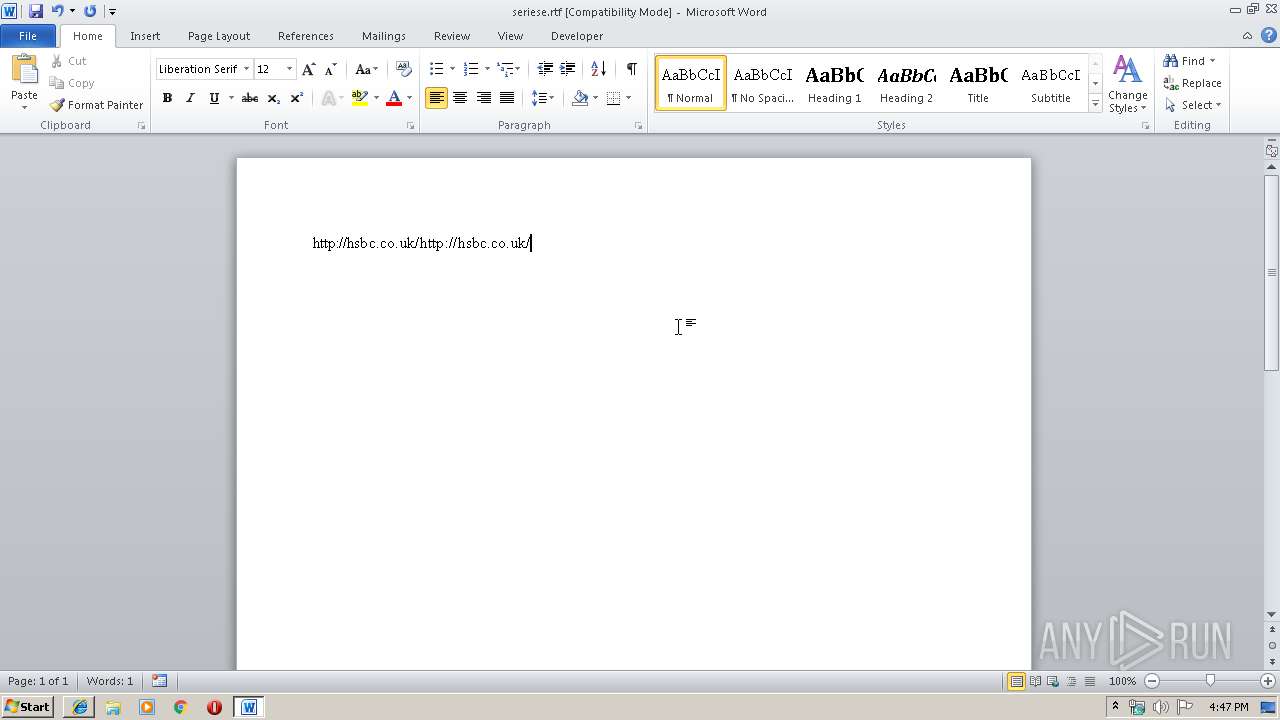
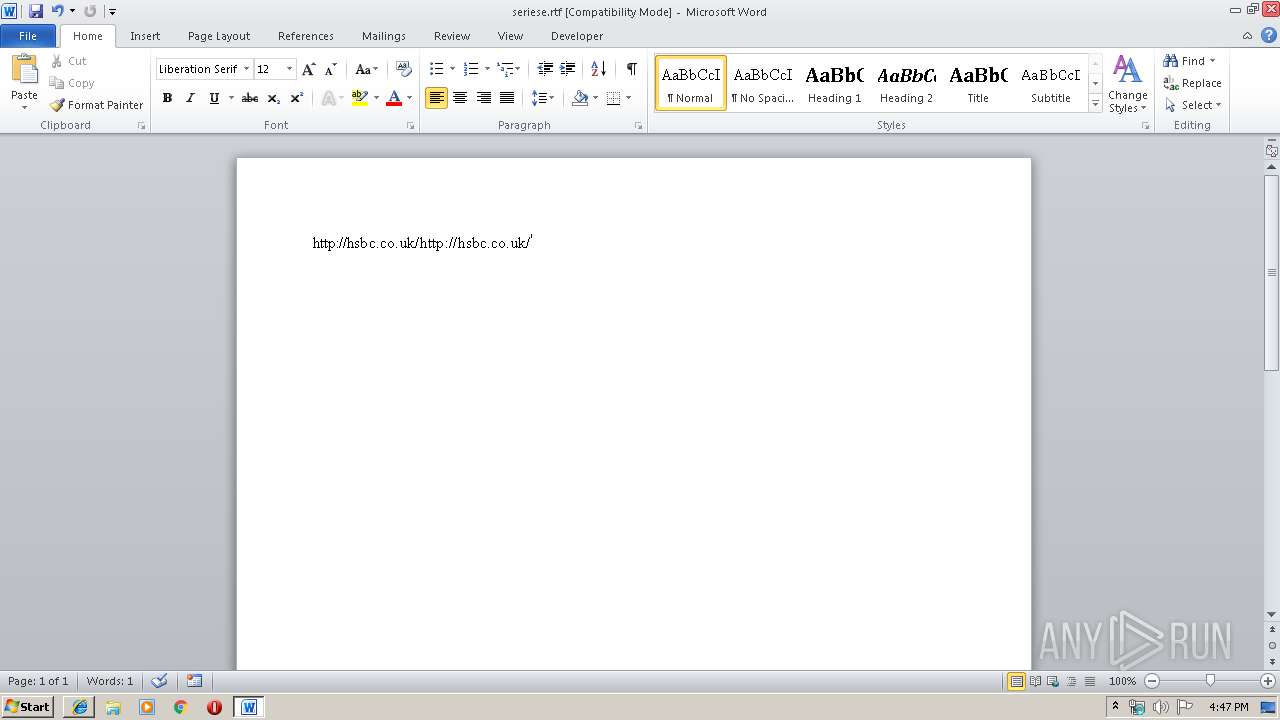
| 3956 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\seriese.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2692 | "C:\Users\admin\AppData\Local\Temp\nameX.exe" | C:\Users\admin\AppData\Local\Temp\nameX.exe | nameX.exe | |
User: admin Company: Hewlett-Packard Integrity Level: MEDIUM Description: Tetris Version: 1.0.0.0 | ||||
Total events
1 307
Read events
1 136
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
28
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1AAC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:3A0F0BF0D4CB55B9ADF19D1244A479E9 | SHA256:00D180C4F89489D52F16E1646D113CA3FB49D4A0936006367D8B6C3670ED25E1 | |||
| 3956 | WINWORD.EXE | C:\Users\admin\Desktop\~$eriese.rtf | pgc | |
MD5:B7AA9951B935B854A821EE2632723B4C | SHA256:12EB9605334A4396CC33D3CF69FFC838F5AF89800992B0A36A075436B10283E3 | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:A1FABA04D267E0583756D73C547BE1A1 | SHA256:30B2103A1BD39F27FCDBC9AC742AF7E5E4C46A2FC4A5D9F9394332385B6851E9 | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:236FB8932815684B4DF76B1F6536CFF0 | SHA256:FA0AFDF368C859359FCAF0D44566D6F1F5C62C5CA7079A842D6E85C7FCA9ECC6 | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RVU7ARXM\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3956 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:F7D9B50806DC38A54477DB5E76DE31C8 | SHA256:2226108D0AD18B79F6FEABB9C5223A8C50BD1CC6987B10C480785BF7224906D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
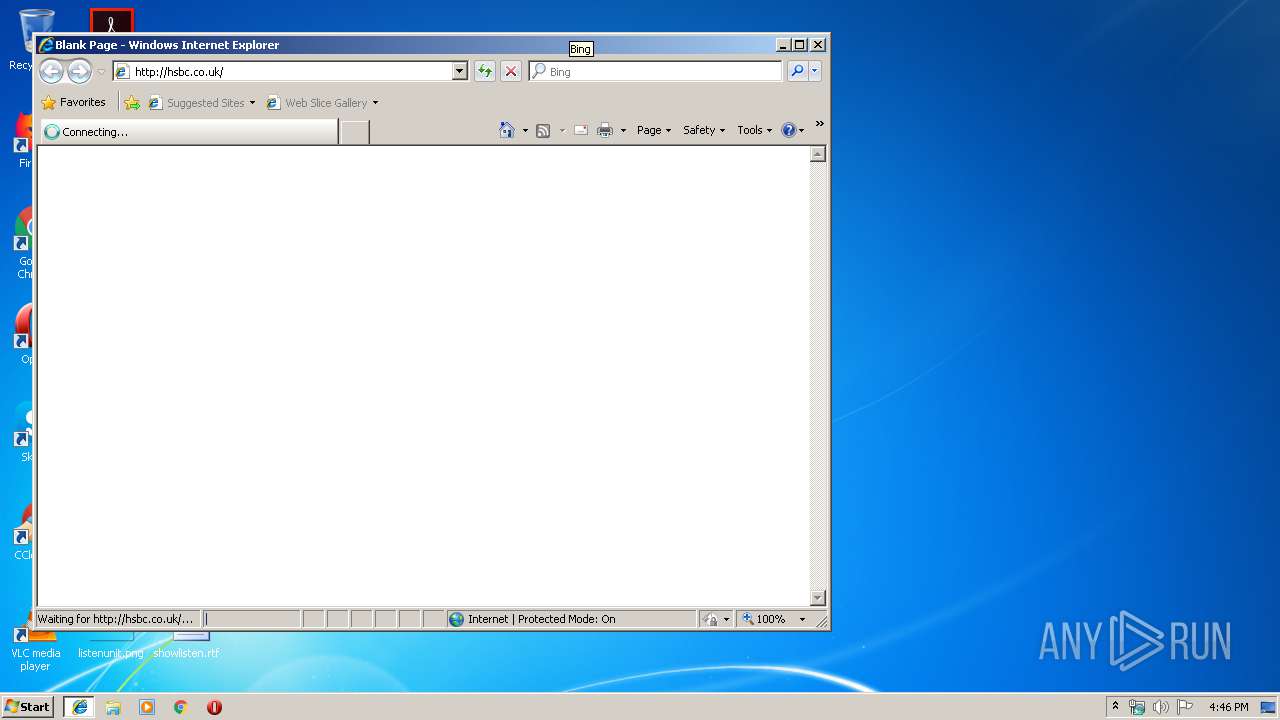
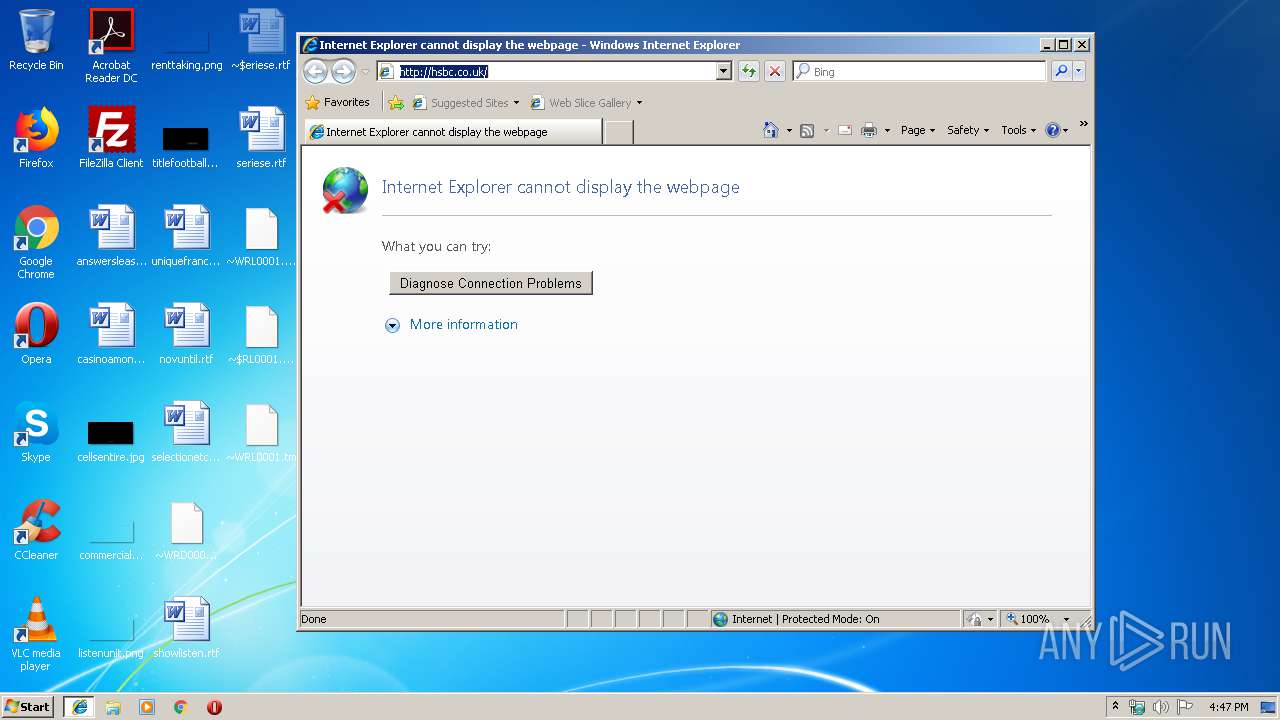
2084 | iexplore.exe | GET | 302 | 91.214.6.117:80 | http://hsbc.co.uk/ | GB | — | — | unknown |
2692 | nameX.exe | GET | 200 | 18.205.71.63:80 | http://checkip.amazonaws.com/ | US | text | 13 b | shared |
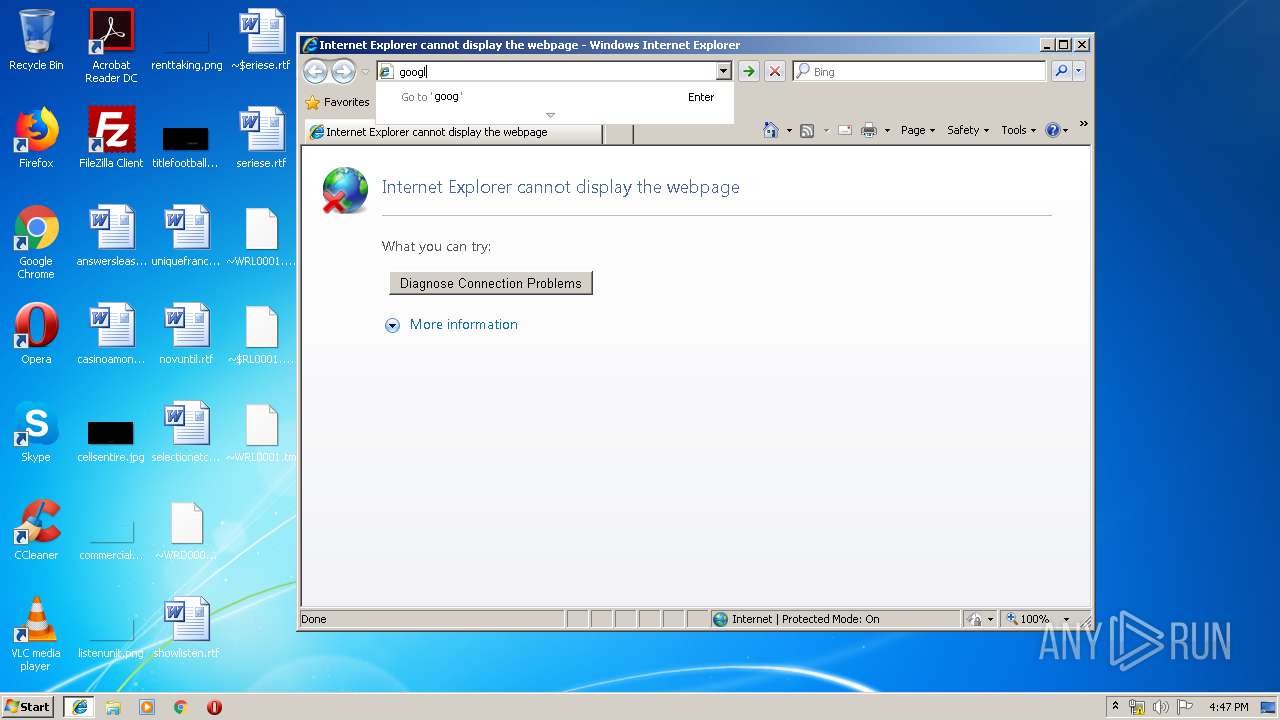
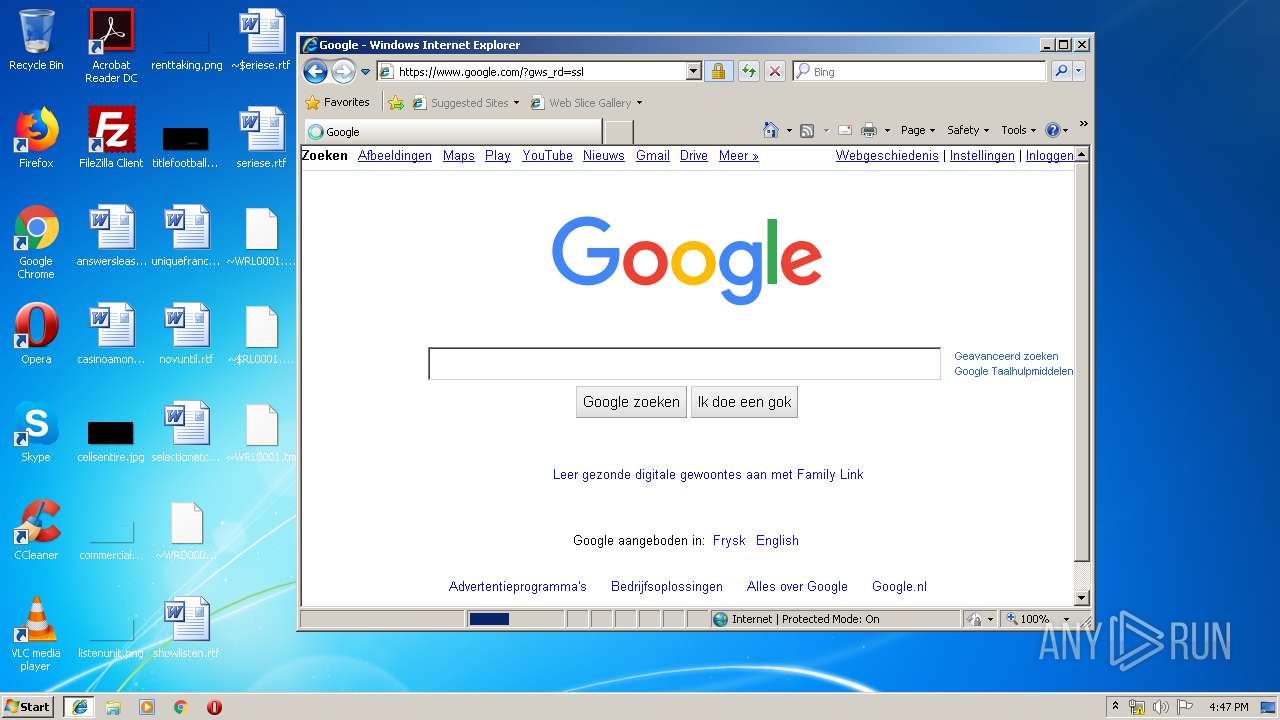
2084 | iexplore.exe | GET | 301 | 172.217.16.142:80 | http://google.com/ | US | html | 219 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2084 | iexplore.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 216.58.207.36:80 | www.google.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 193.108.75.22:443 | www.hsbc.co.uk | VeriSign Global Registry Services | GB | unknown |
2084 | iexplore.exe | 91.214.6.117:80 | hsbc.co.uk | VeriSign Global Registry Services | GB | unknown |
— | — | 172.217.16.142:80 | google.com | Google Inc. | US | whitelisted |
2064 | iexplore.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2692 | nameX.exe | 208.91.199.223:587 | smtp.microtexcomposite.com | PDR | US | shared |
— | — | 18.205.71.63:80 | checkip.amazonaws.com | — | US | shared |
2084 | iexplore.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
hsbc.co.uk |
| unknown |
www.hsbc.co.uk |
| whitelisted |
dns.msftncsi.com |
| shared |
google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
checkip.amazonaws.com |
| shared |
smtp.microtexcomposite.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2692 | nameX.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2692 | nameX.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report