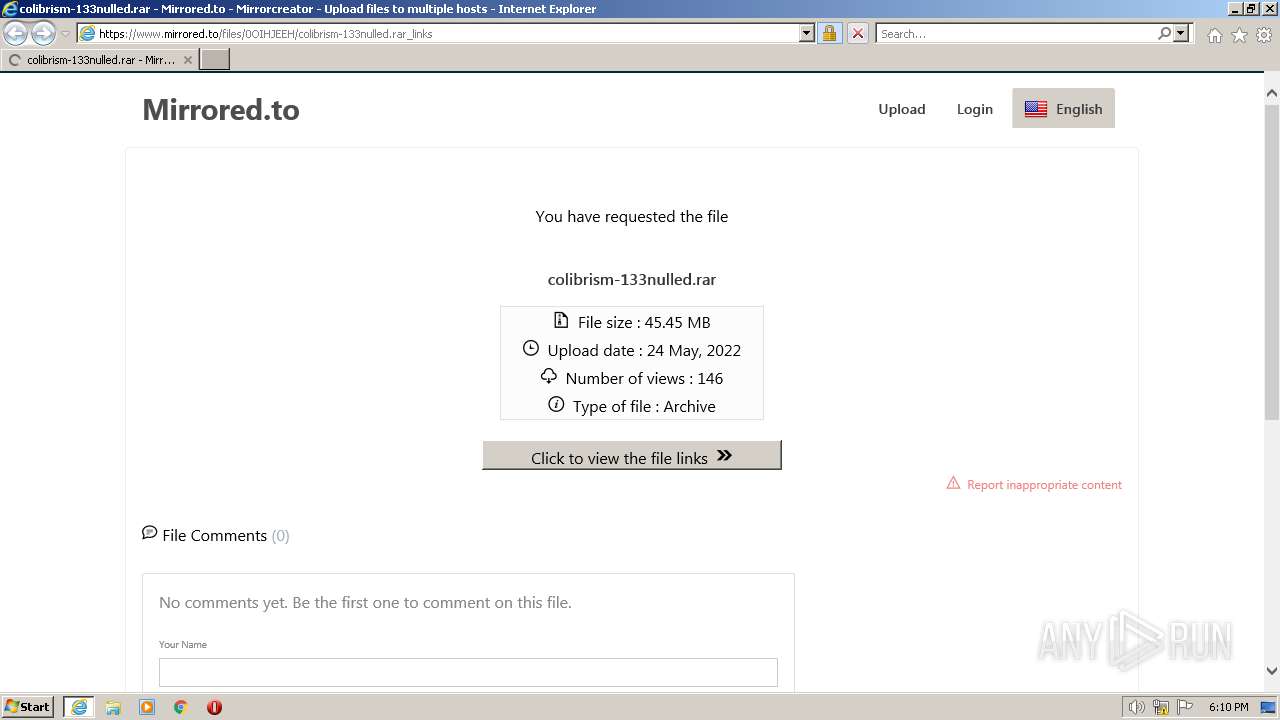
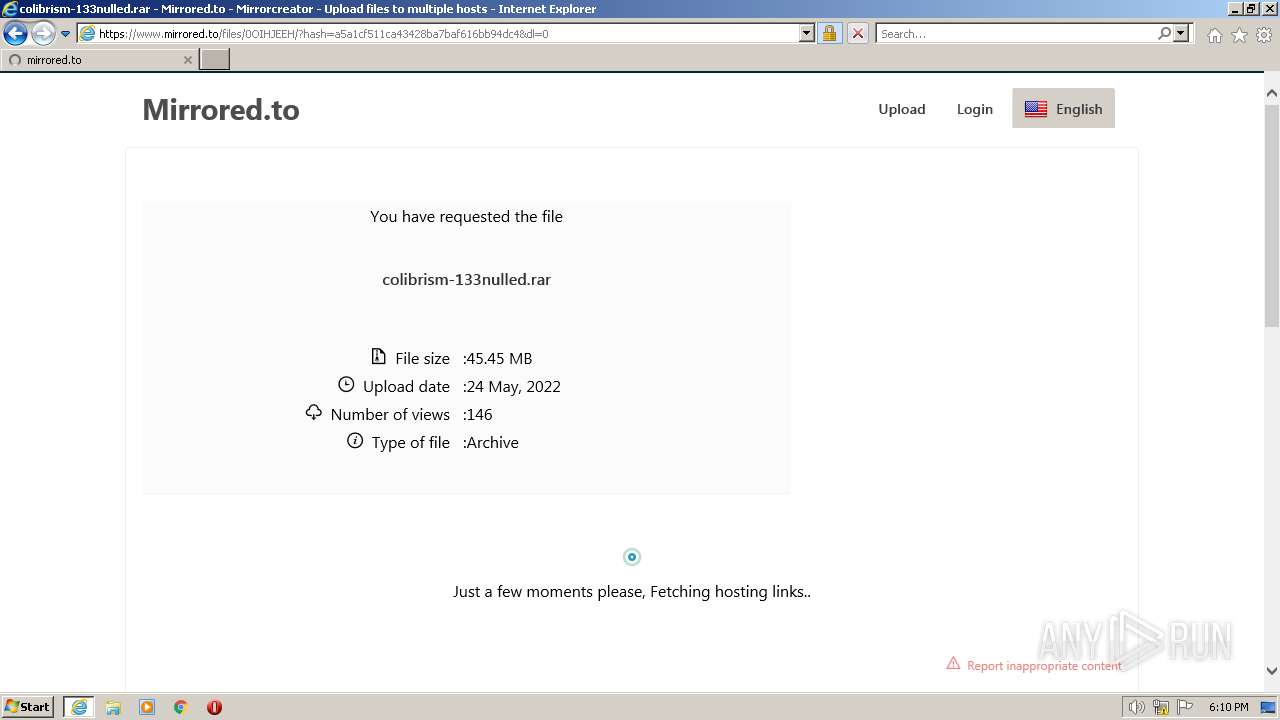
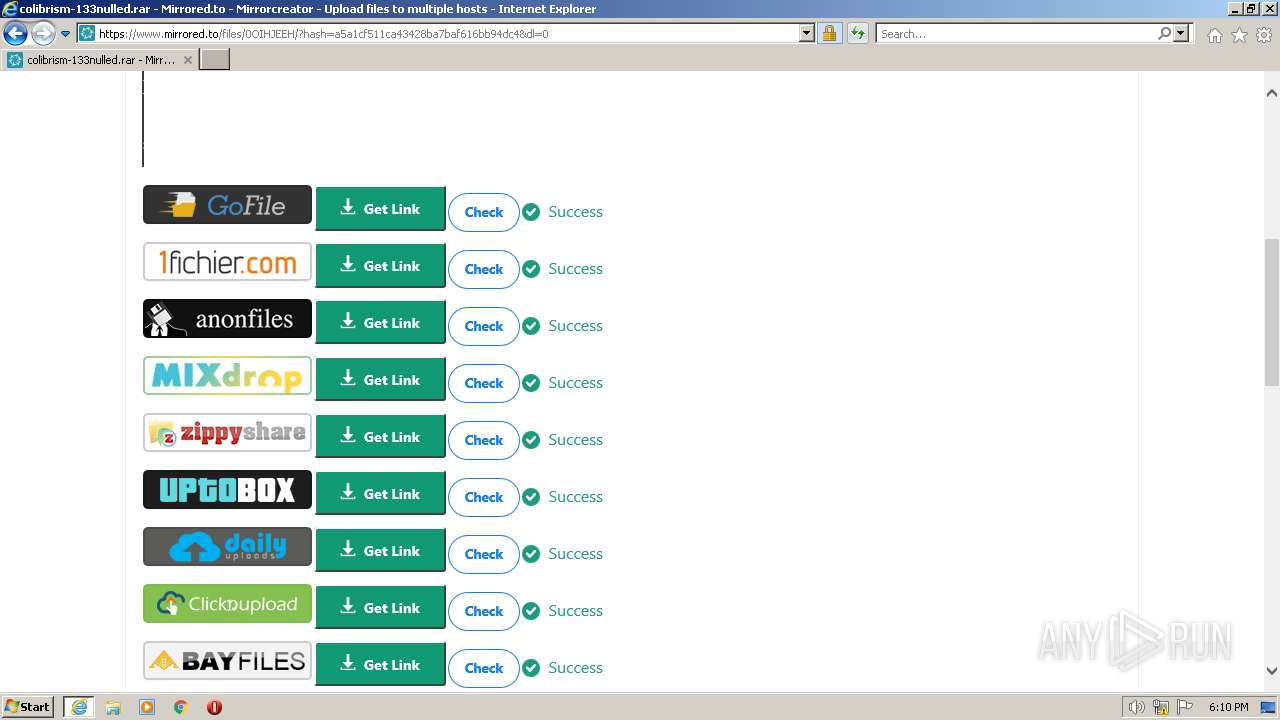
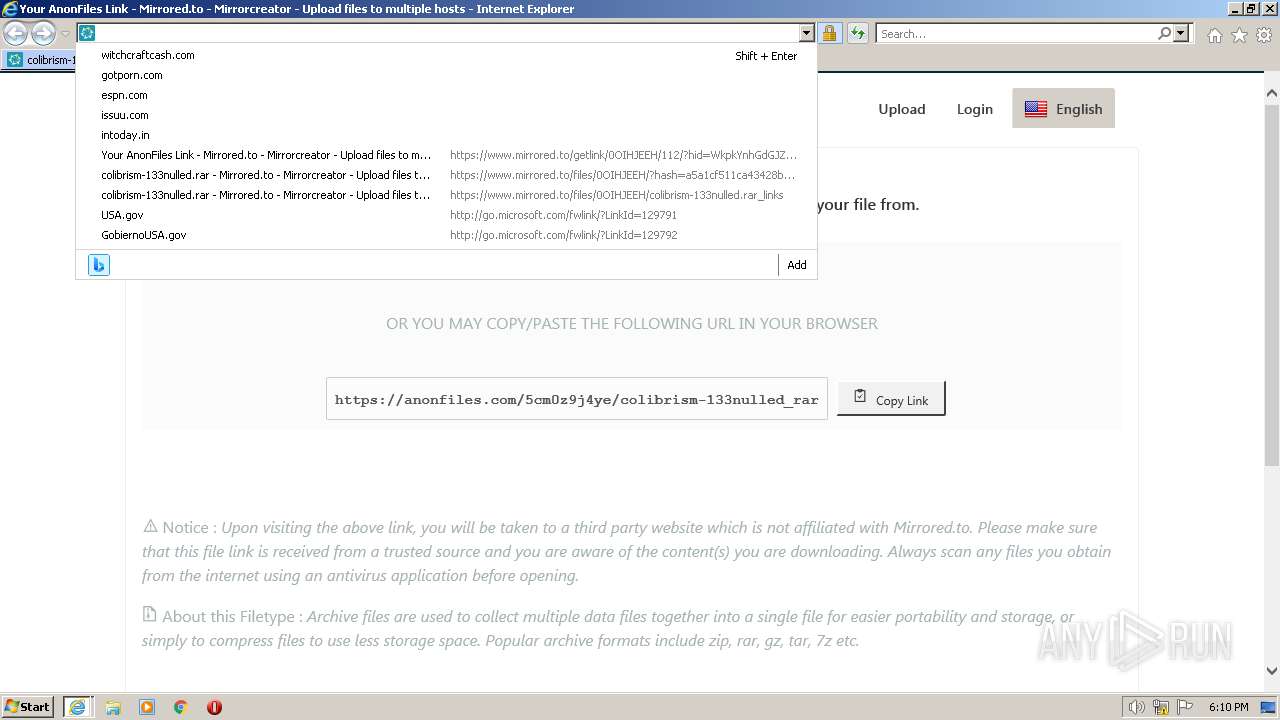
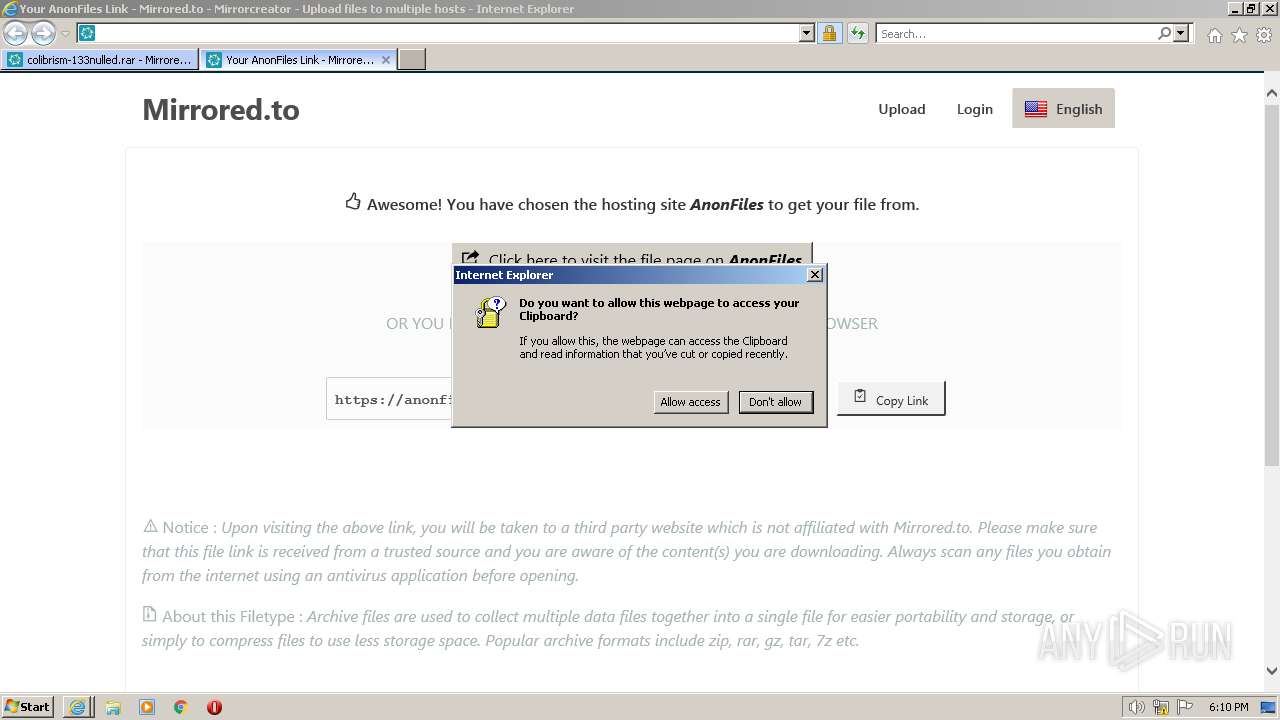
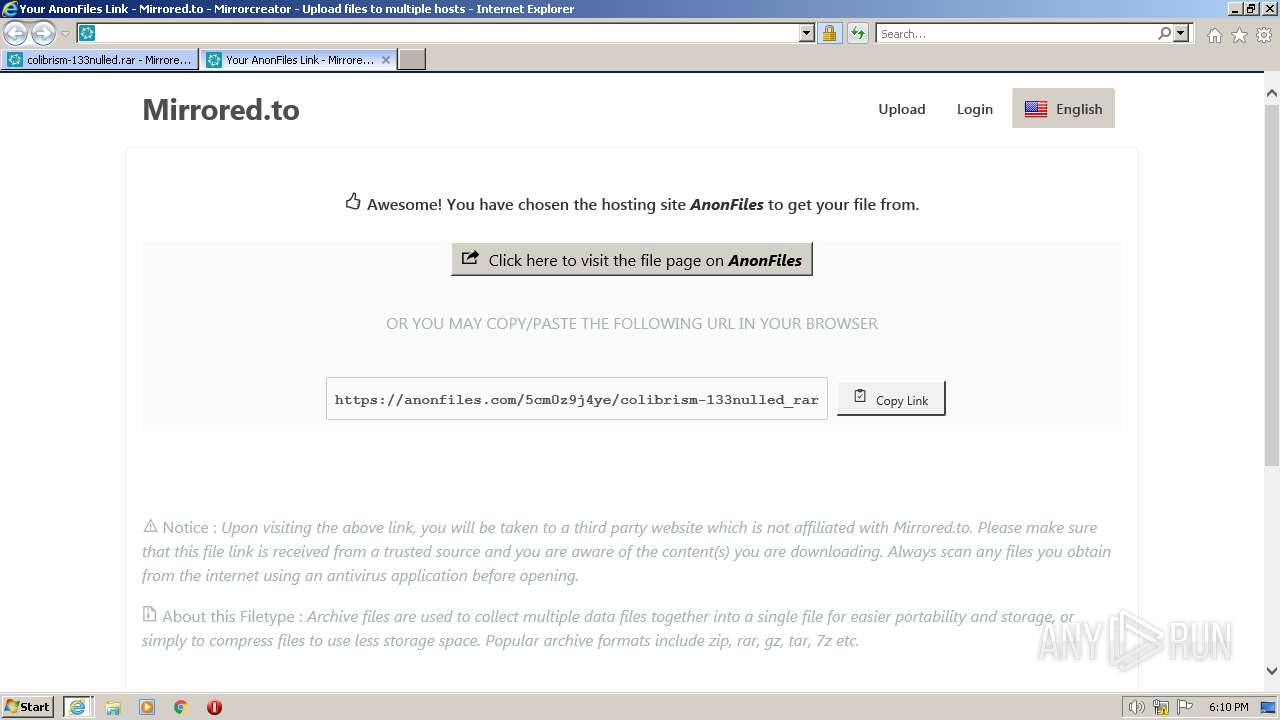
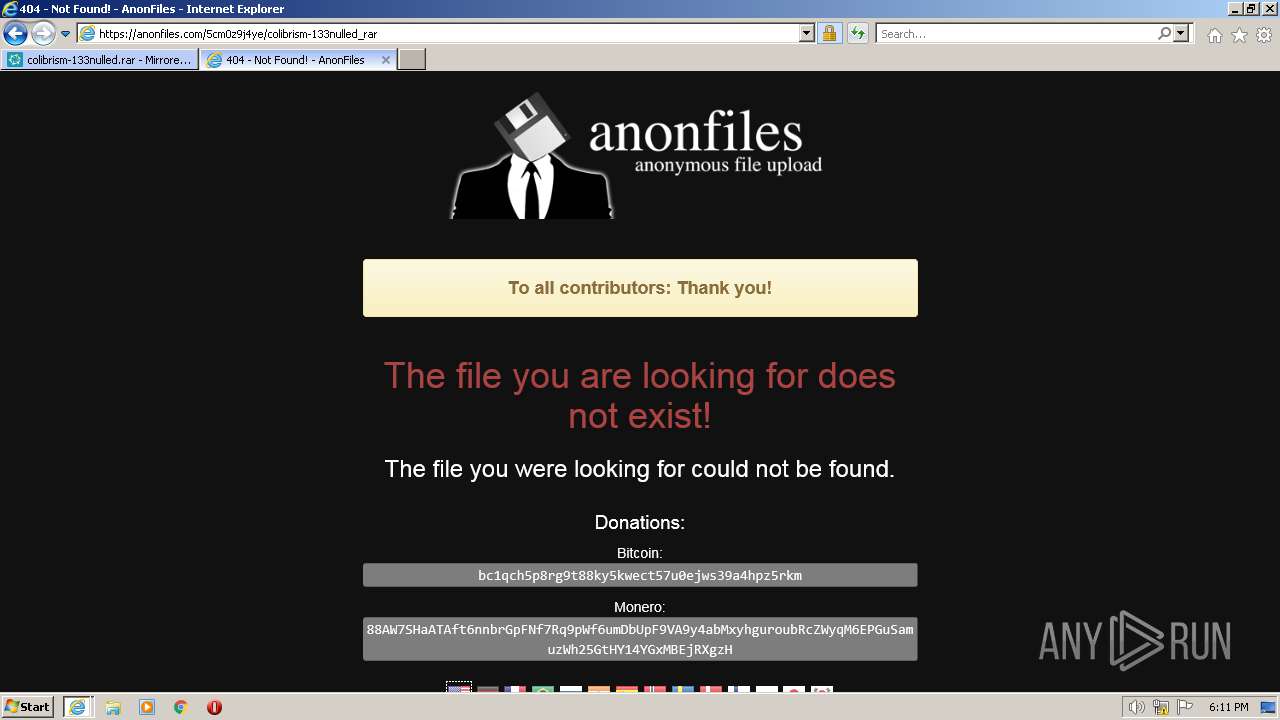
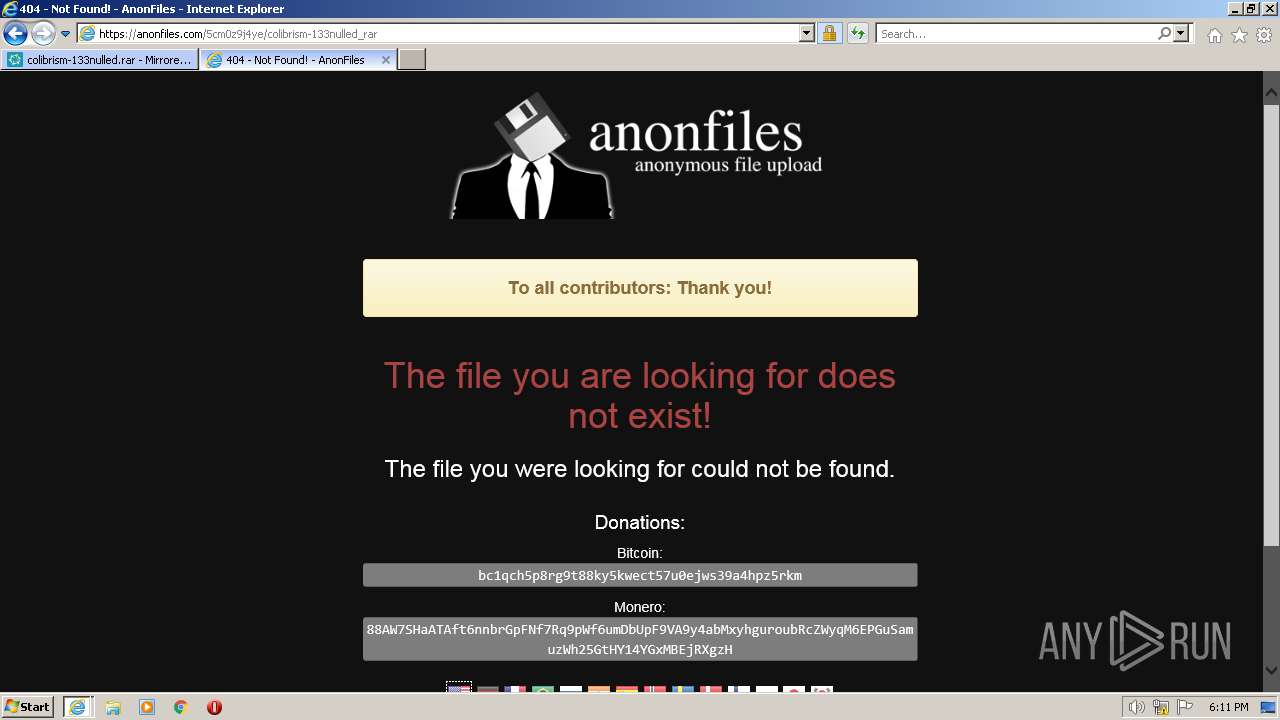
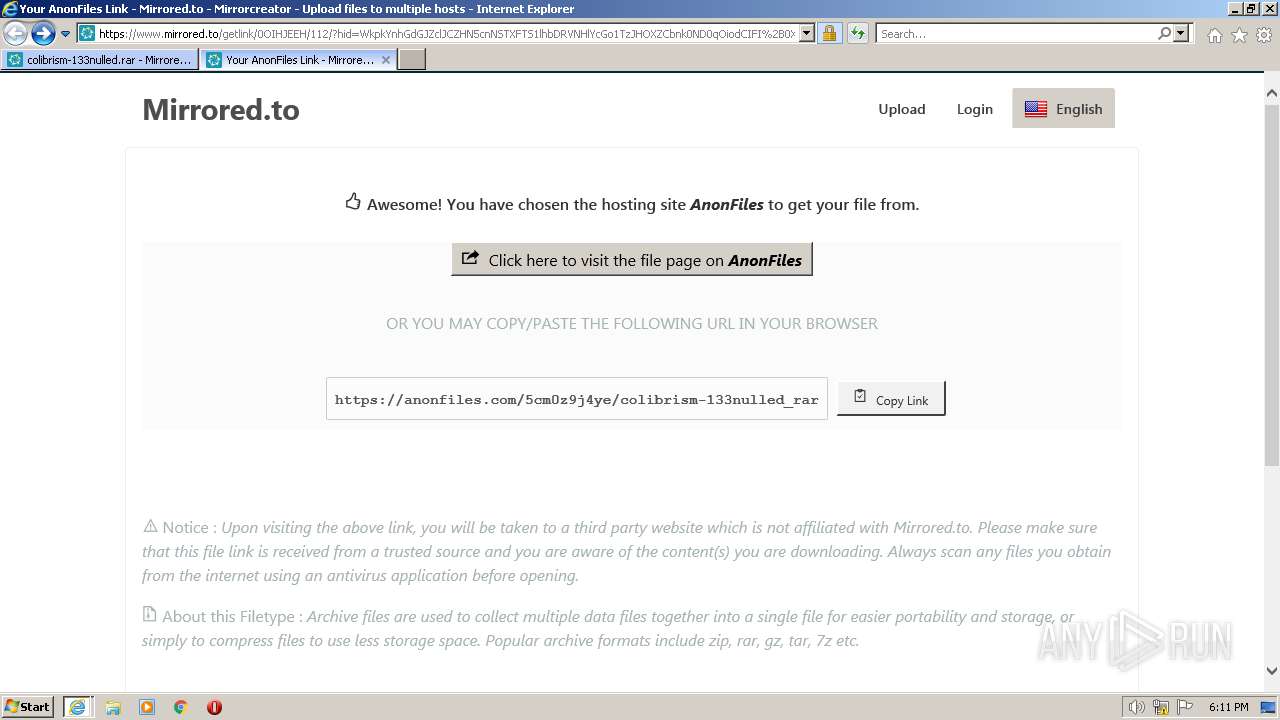
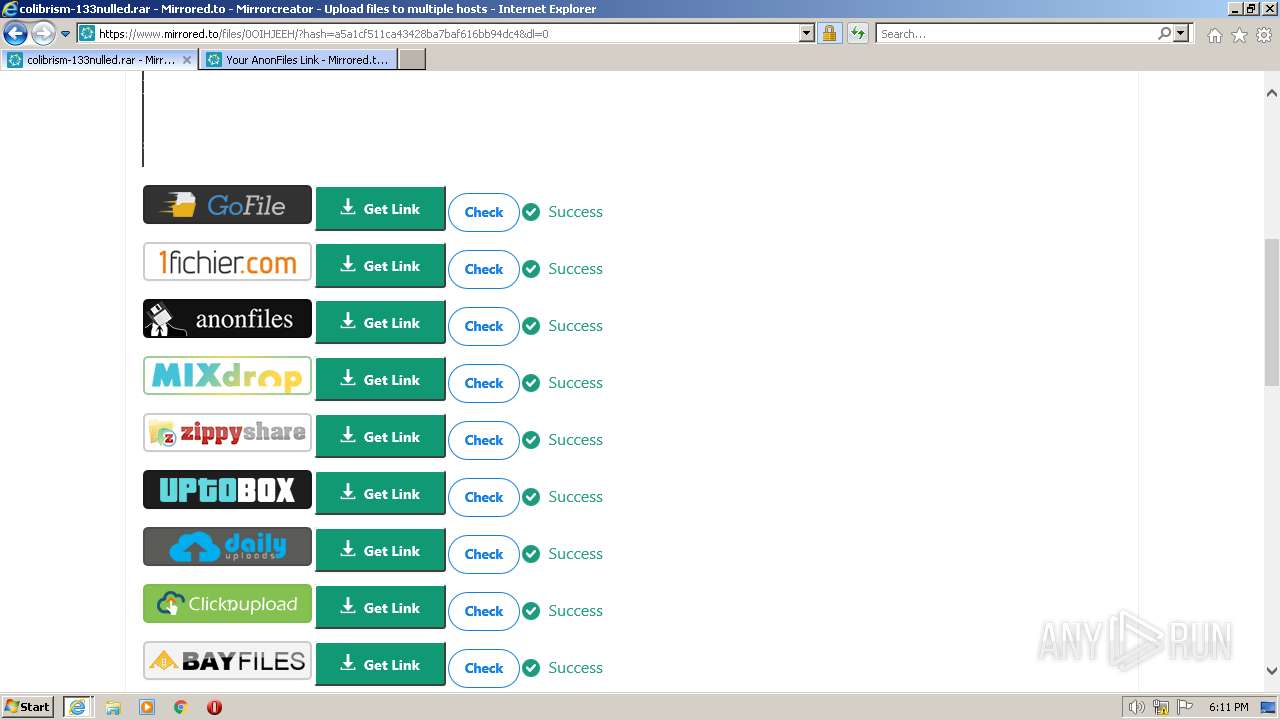
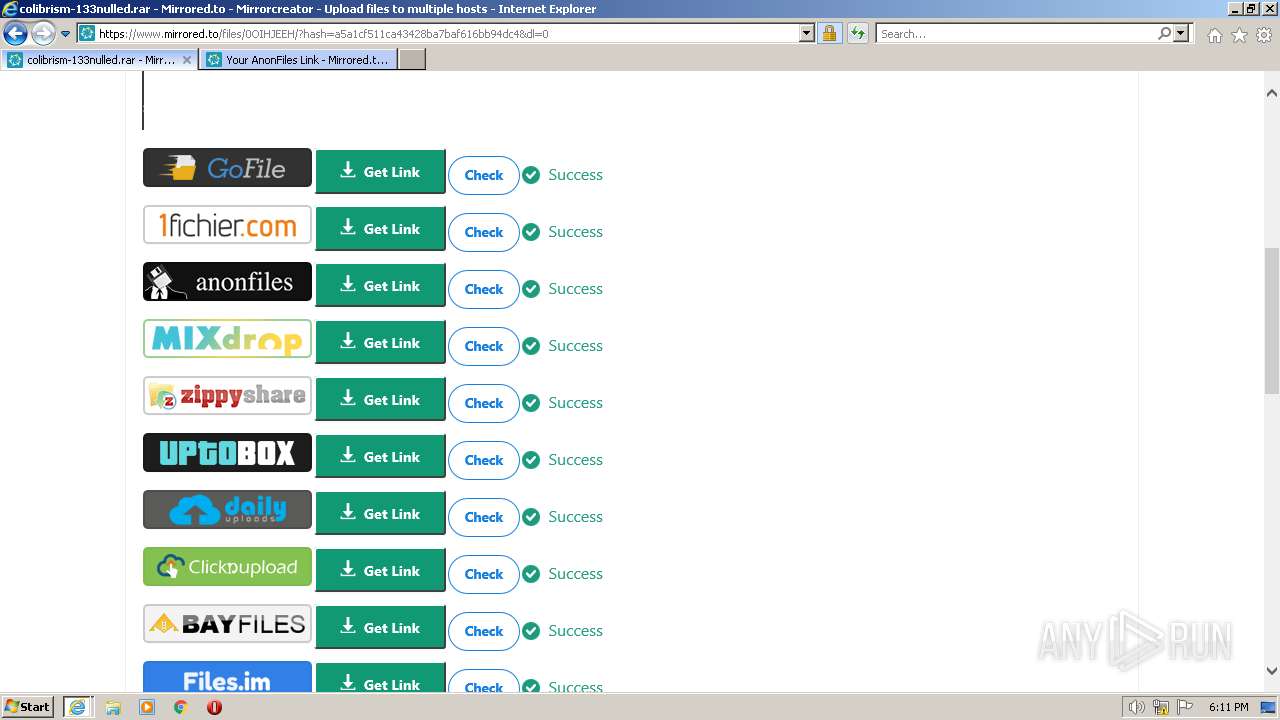
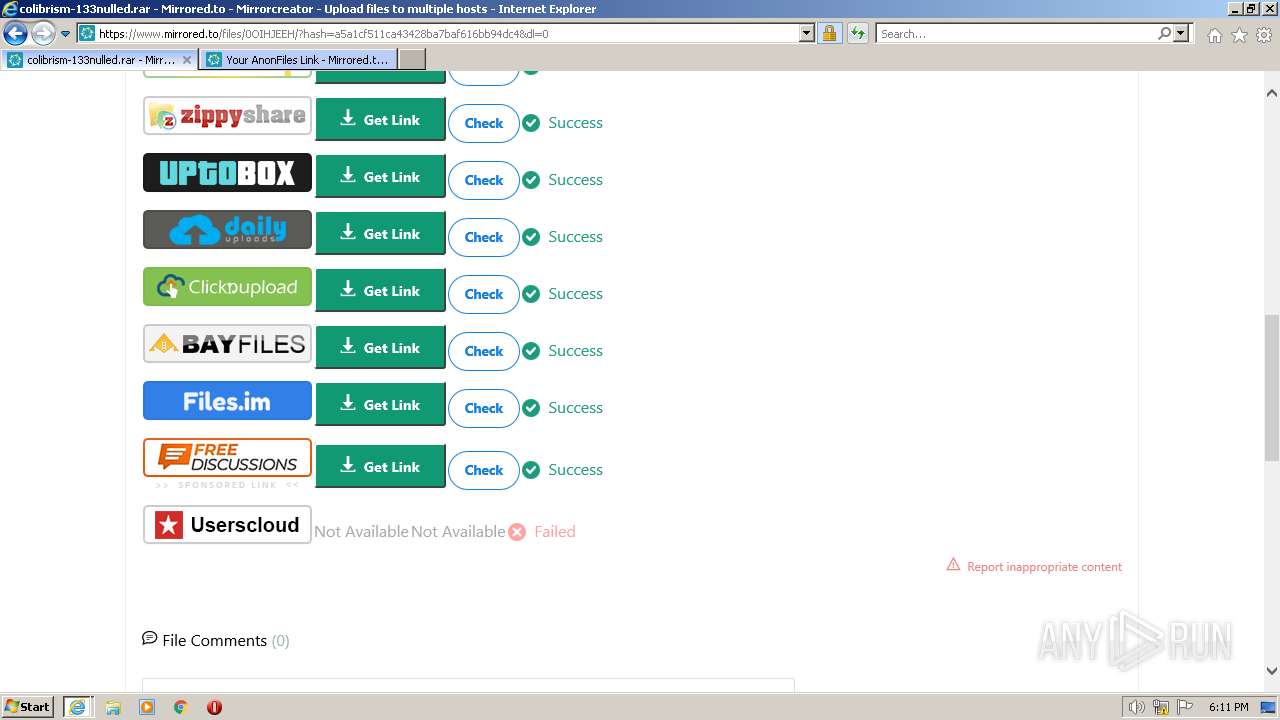
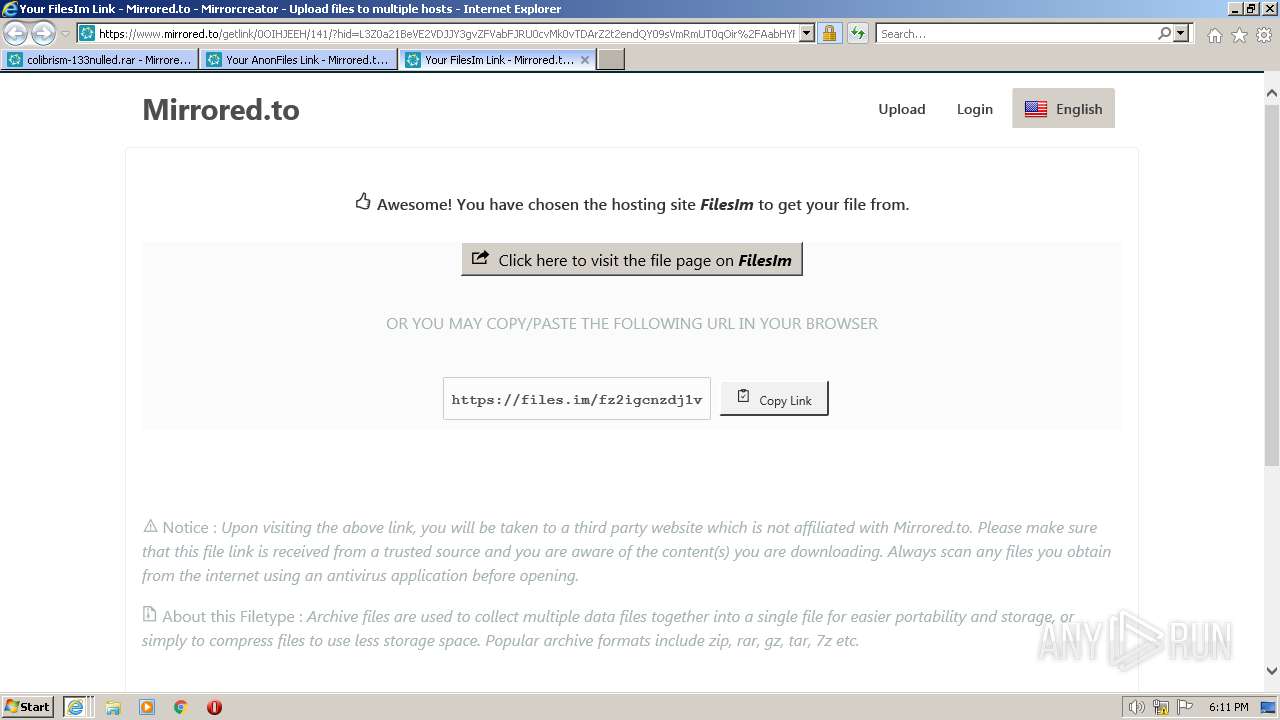
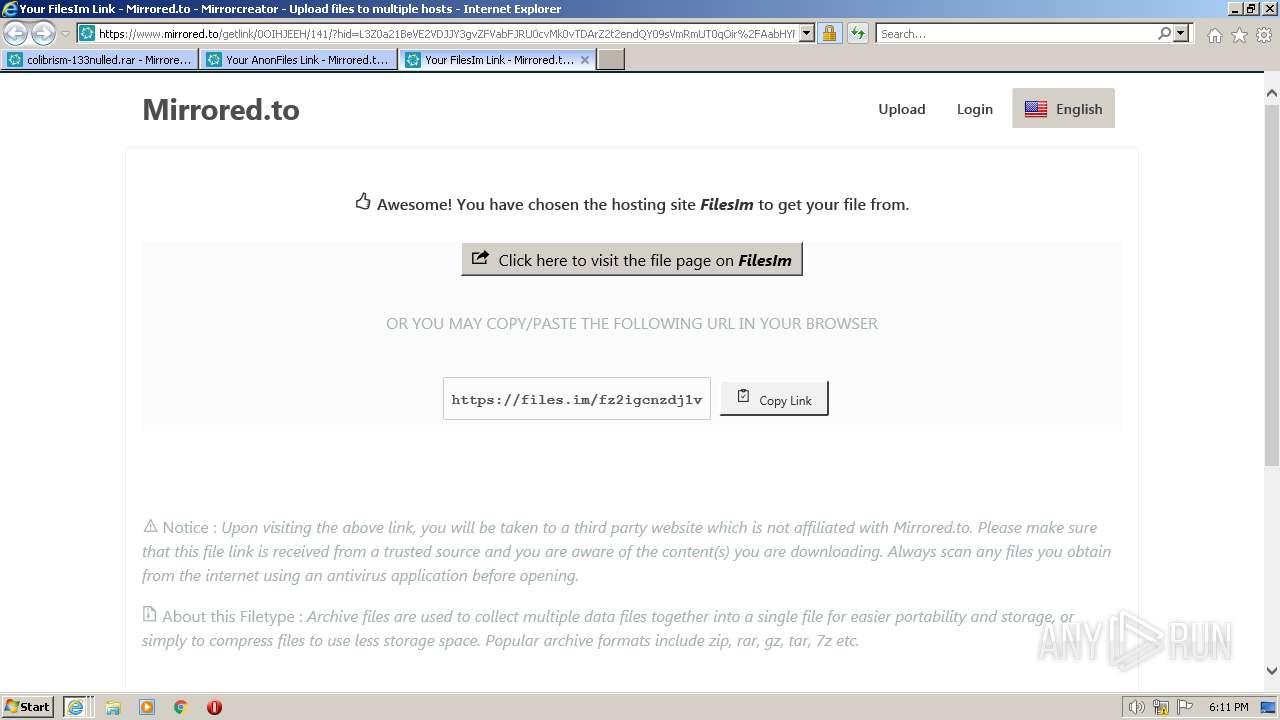
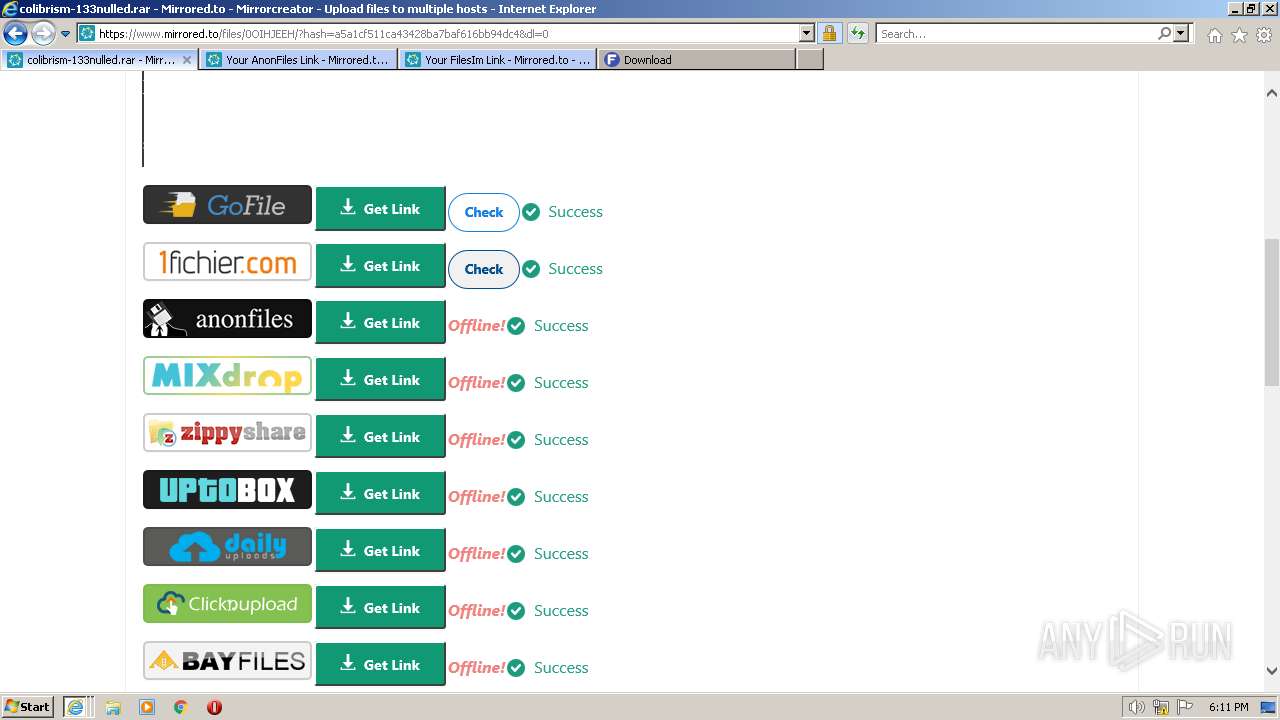
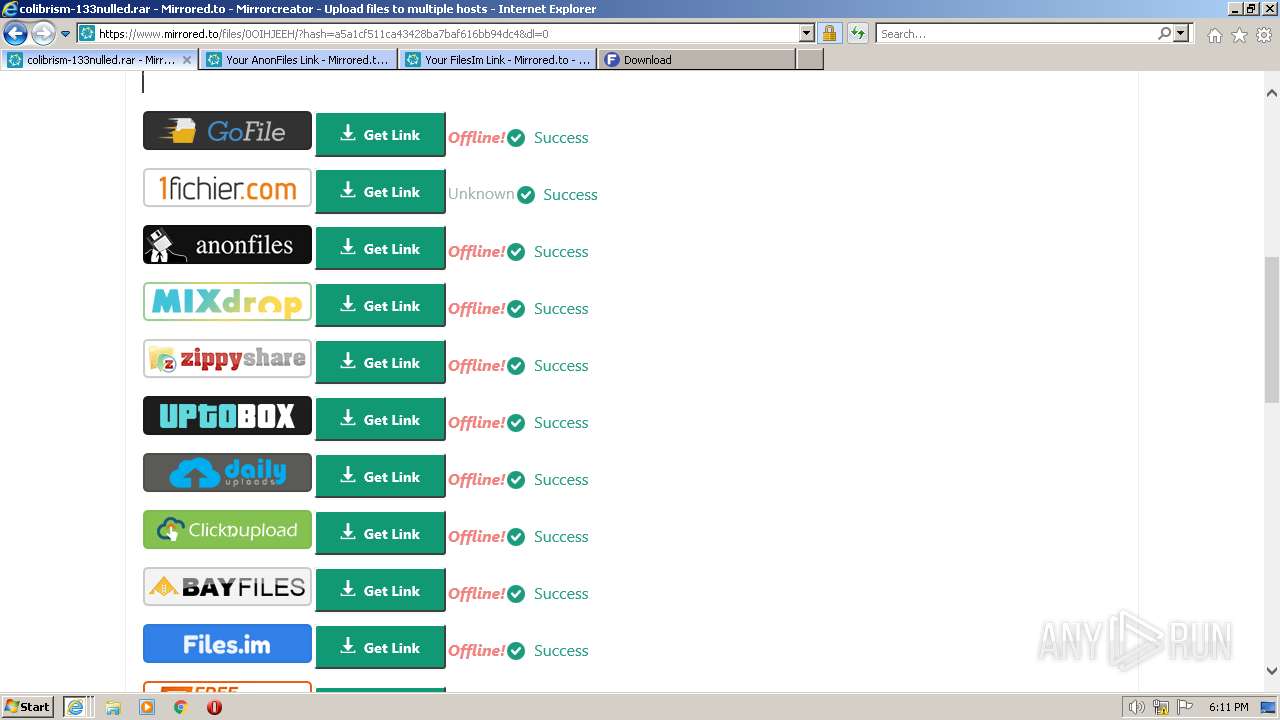
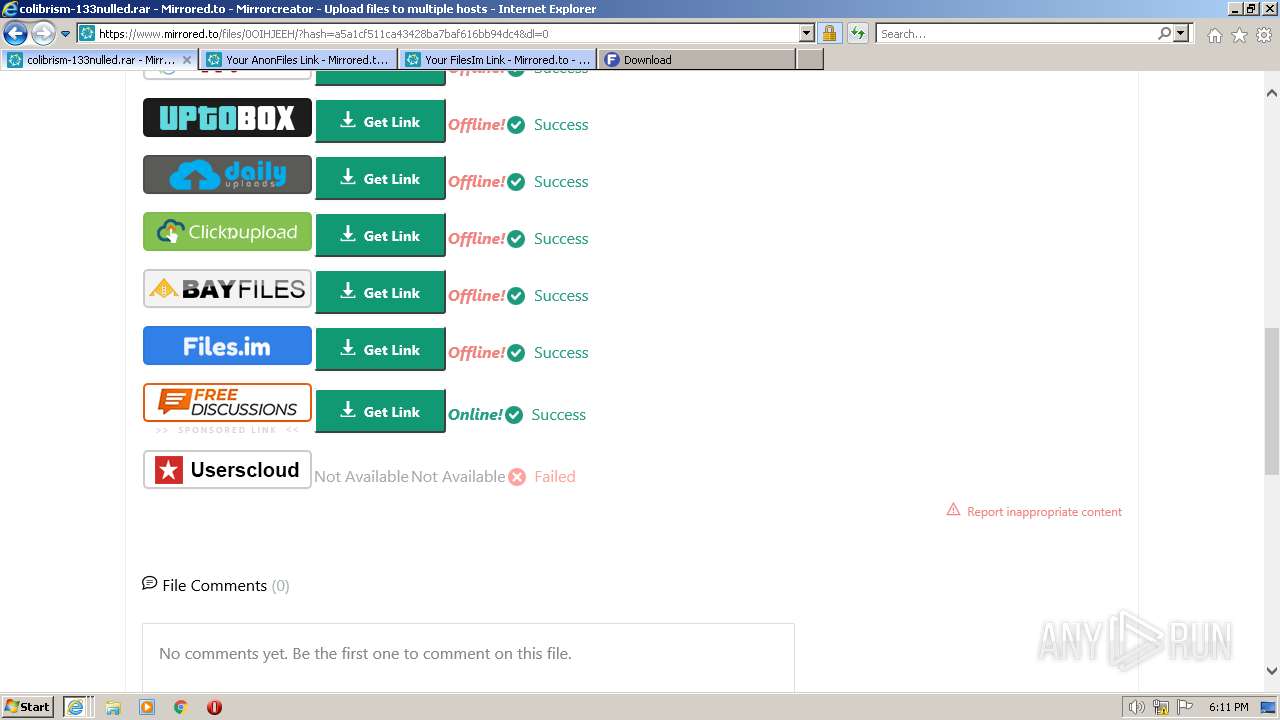
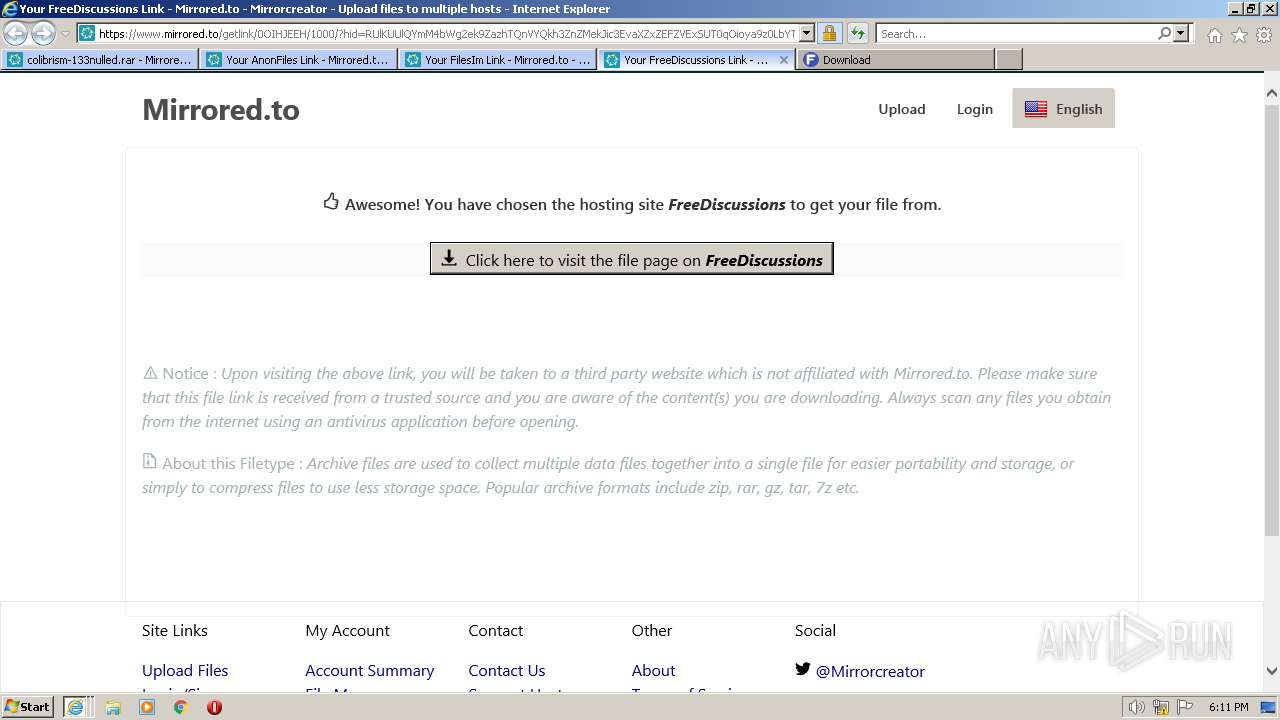
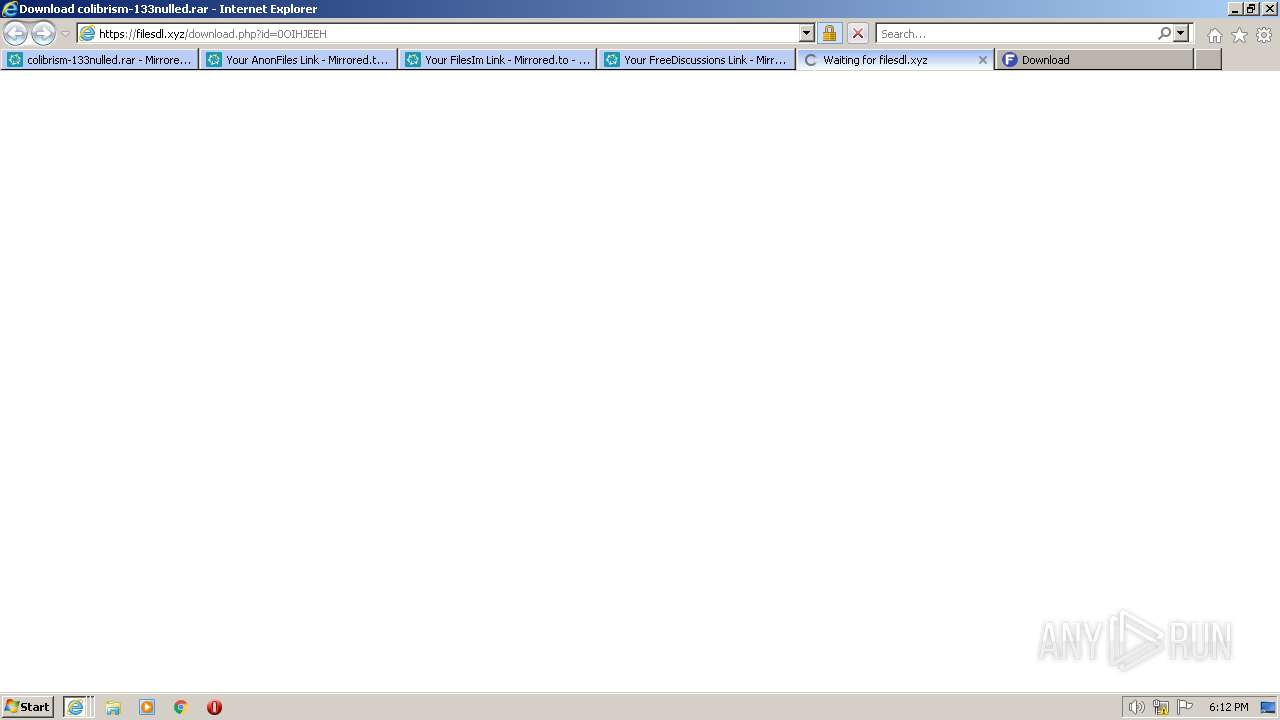
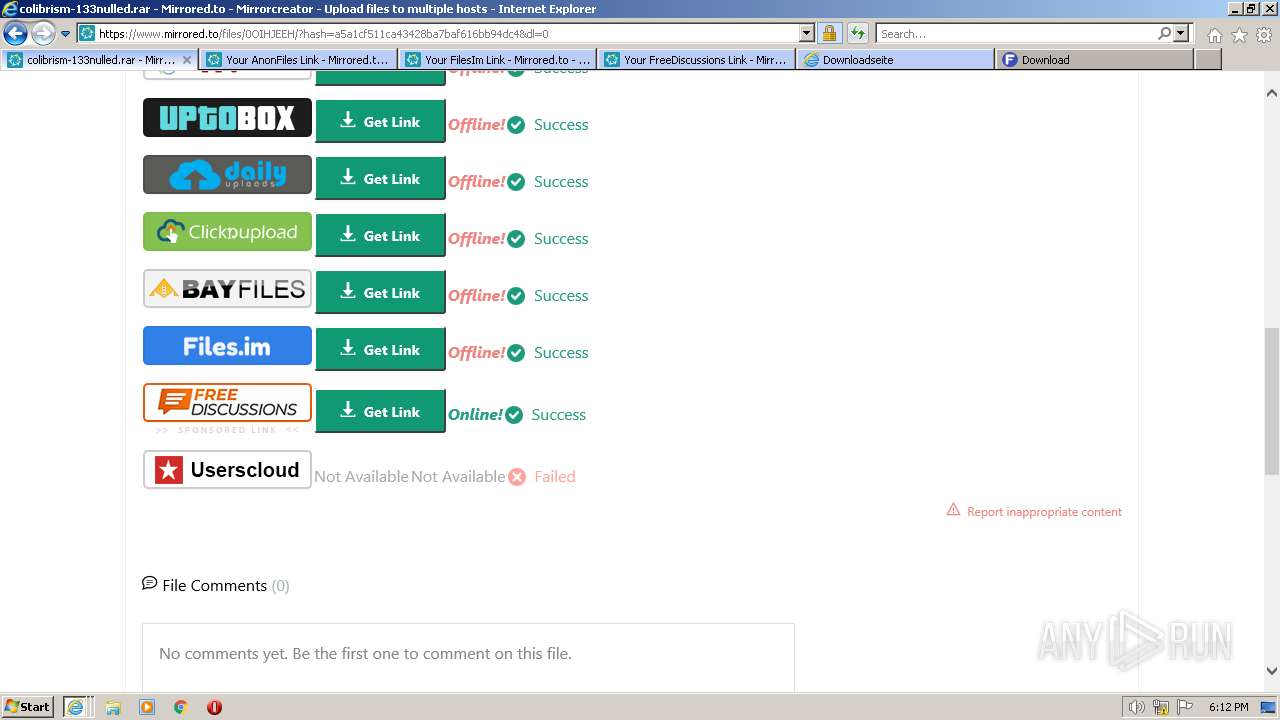
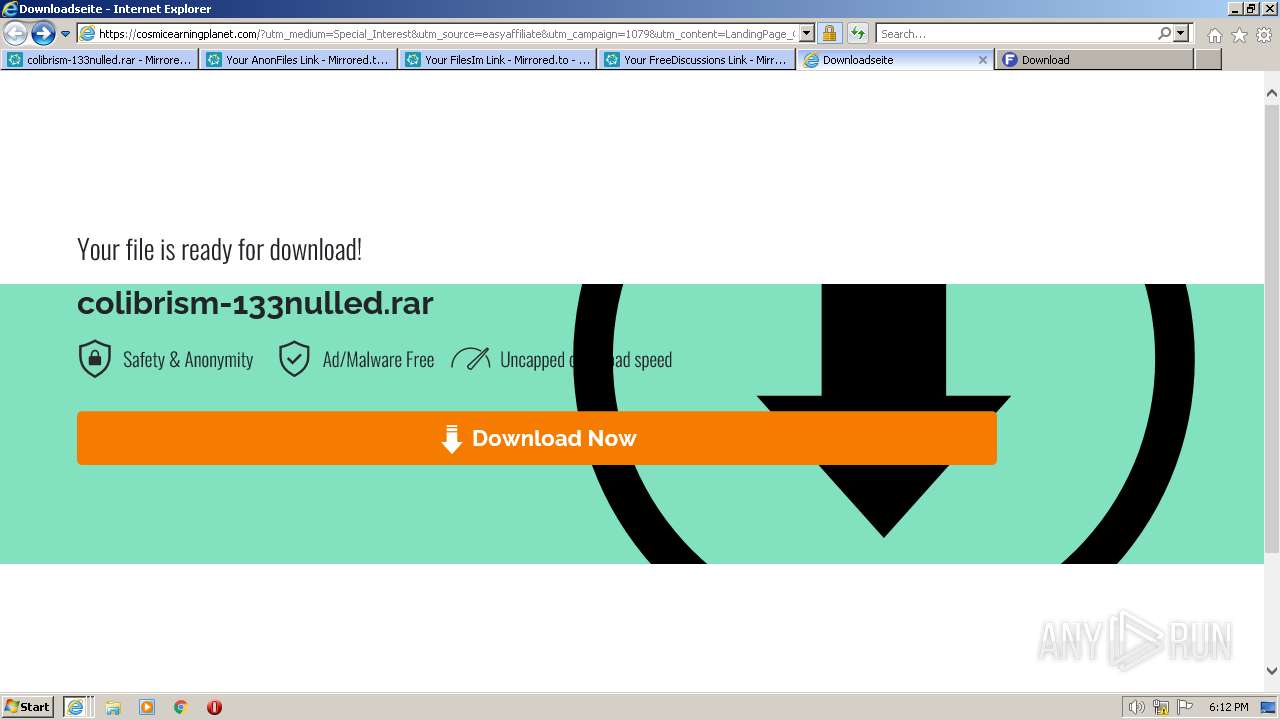
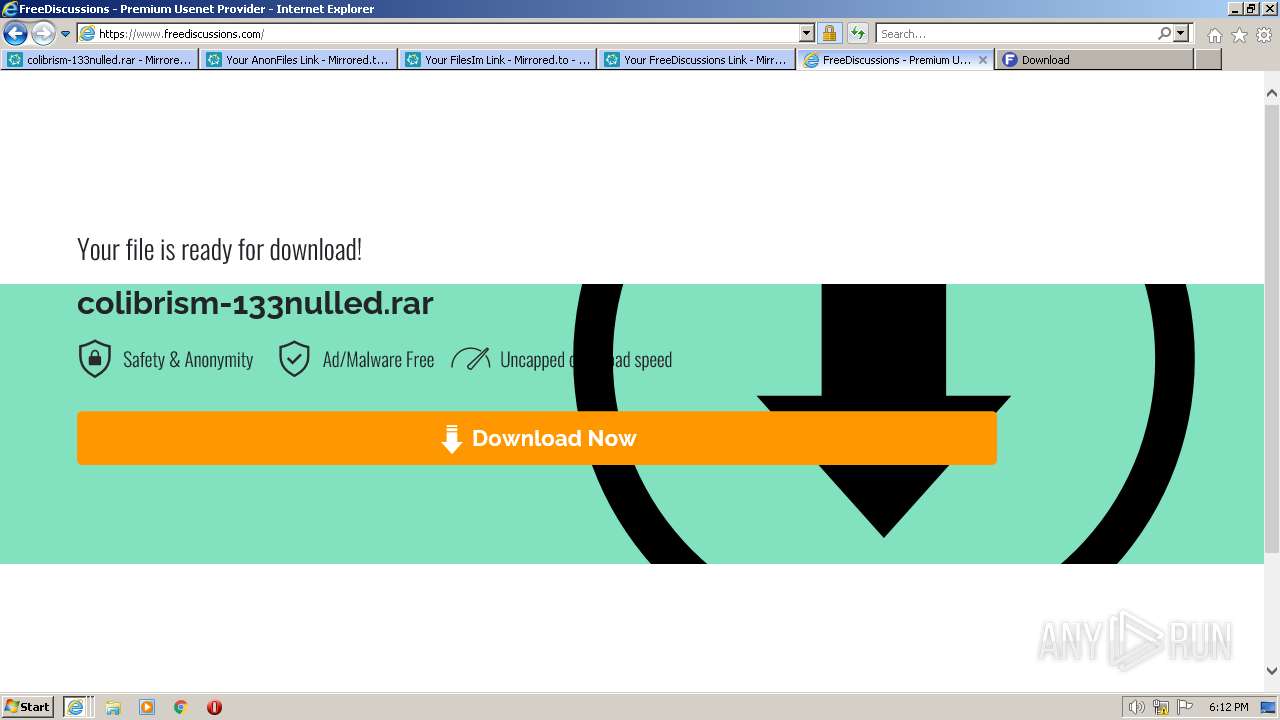
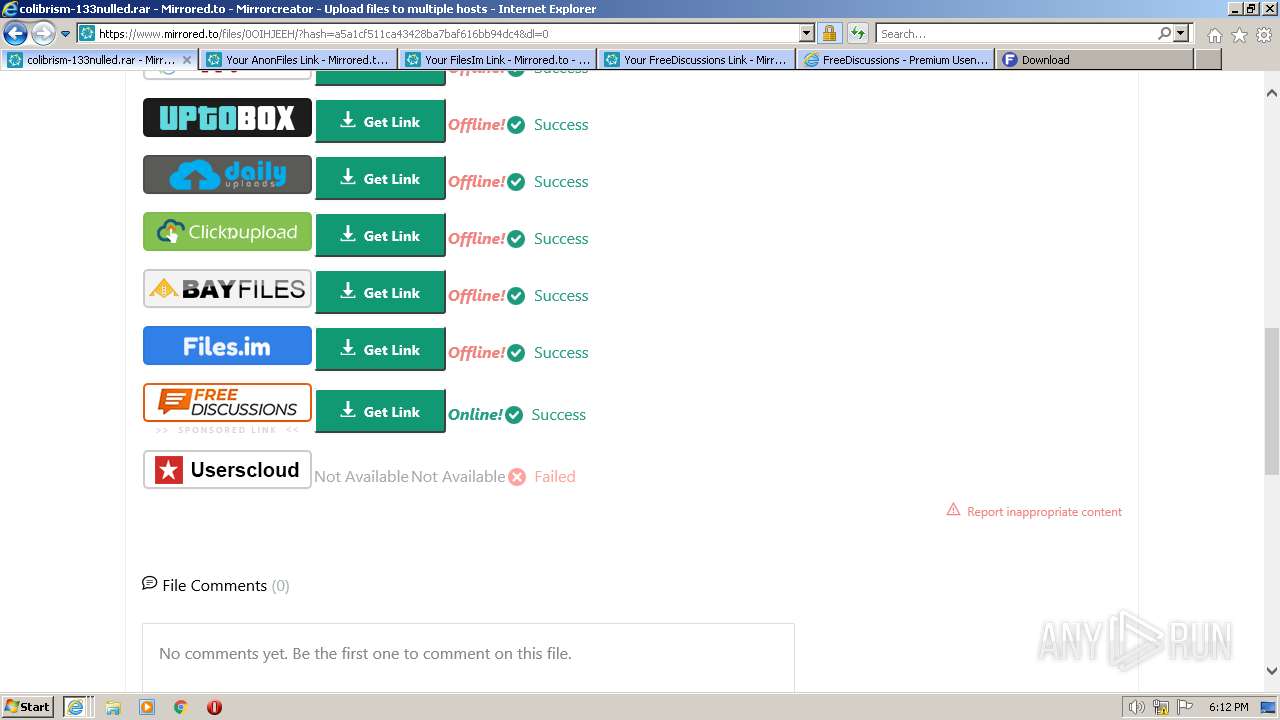
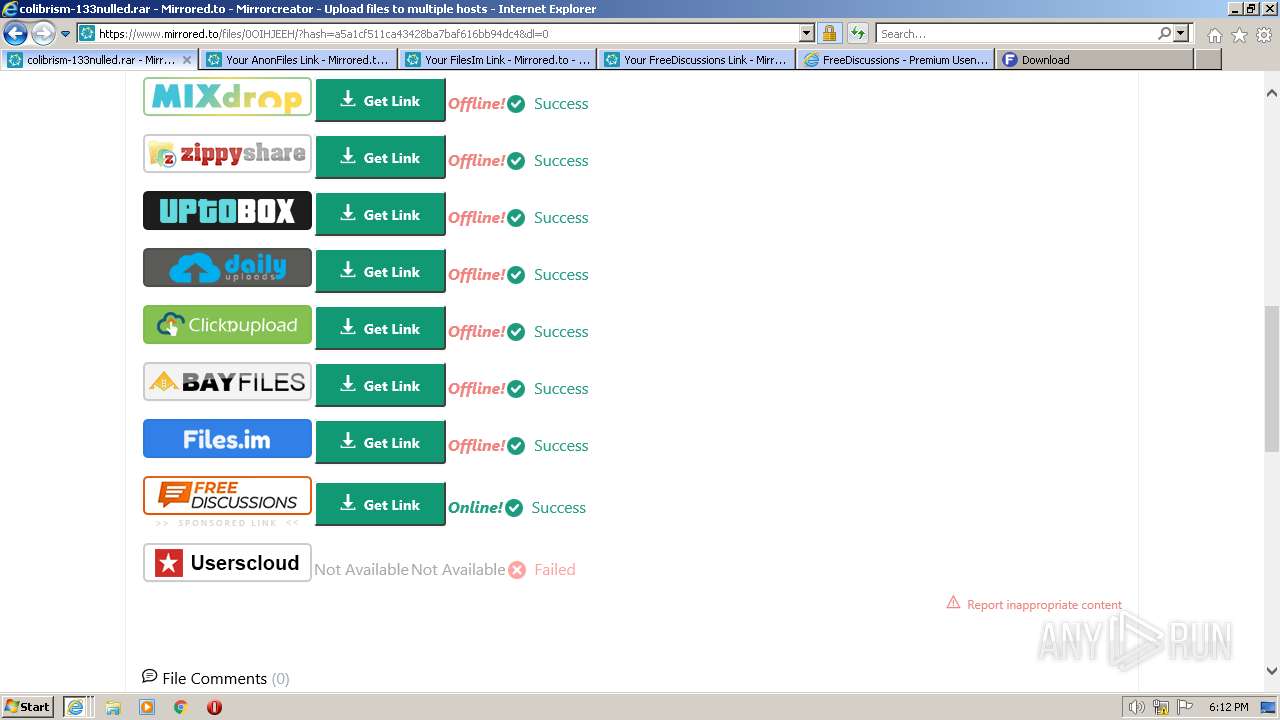
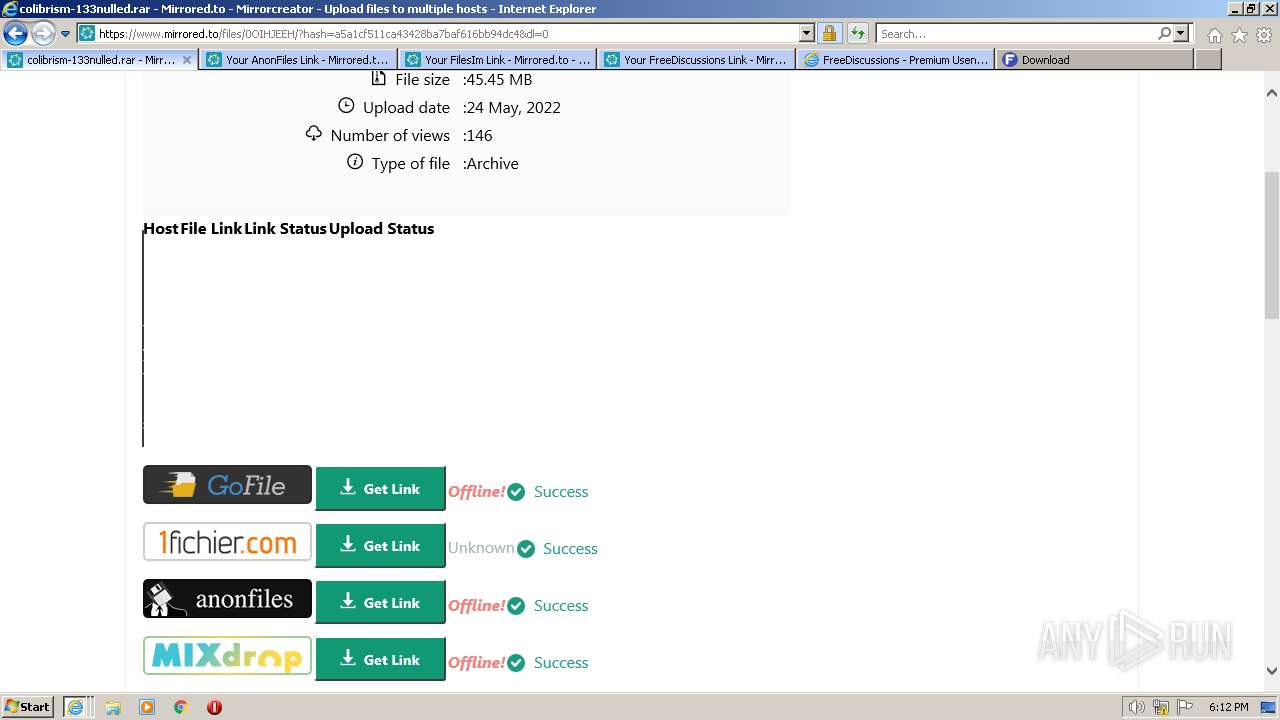
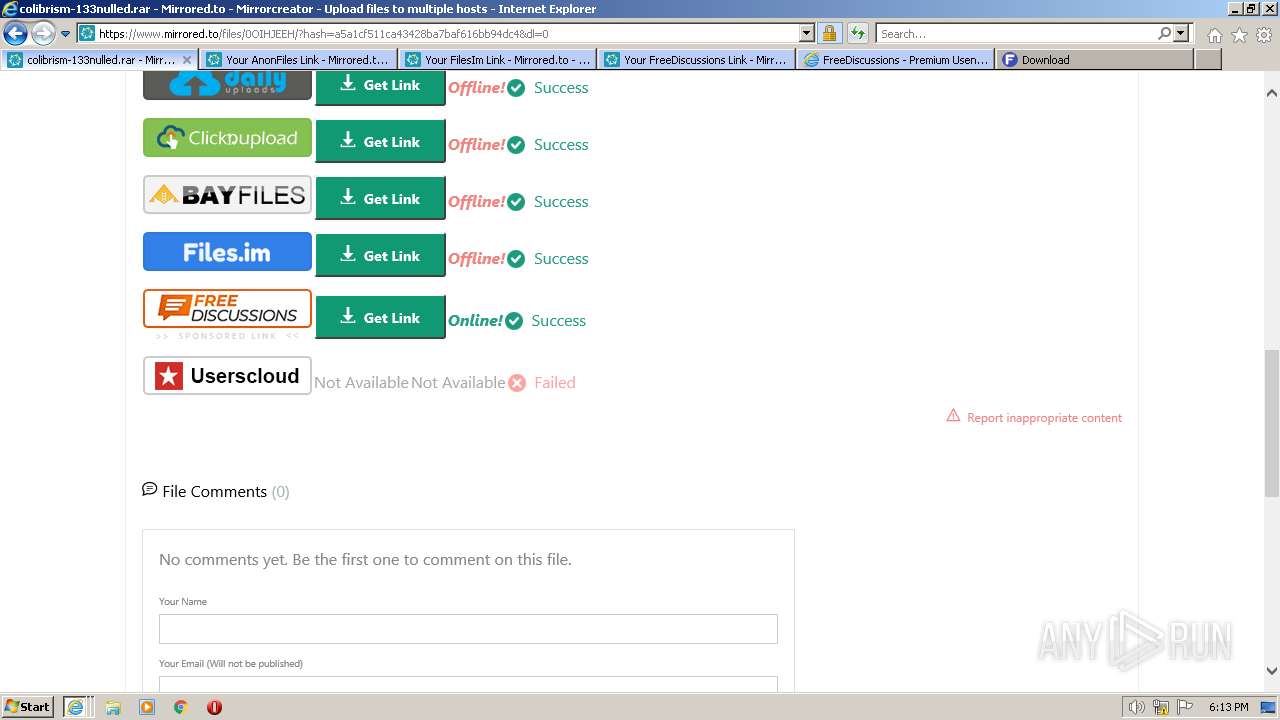
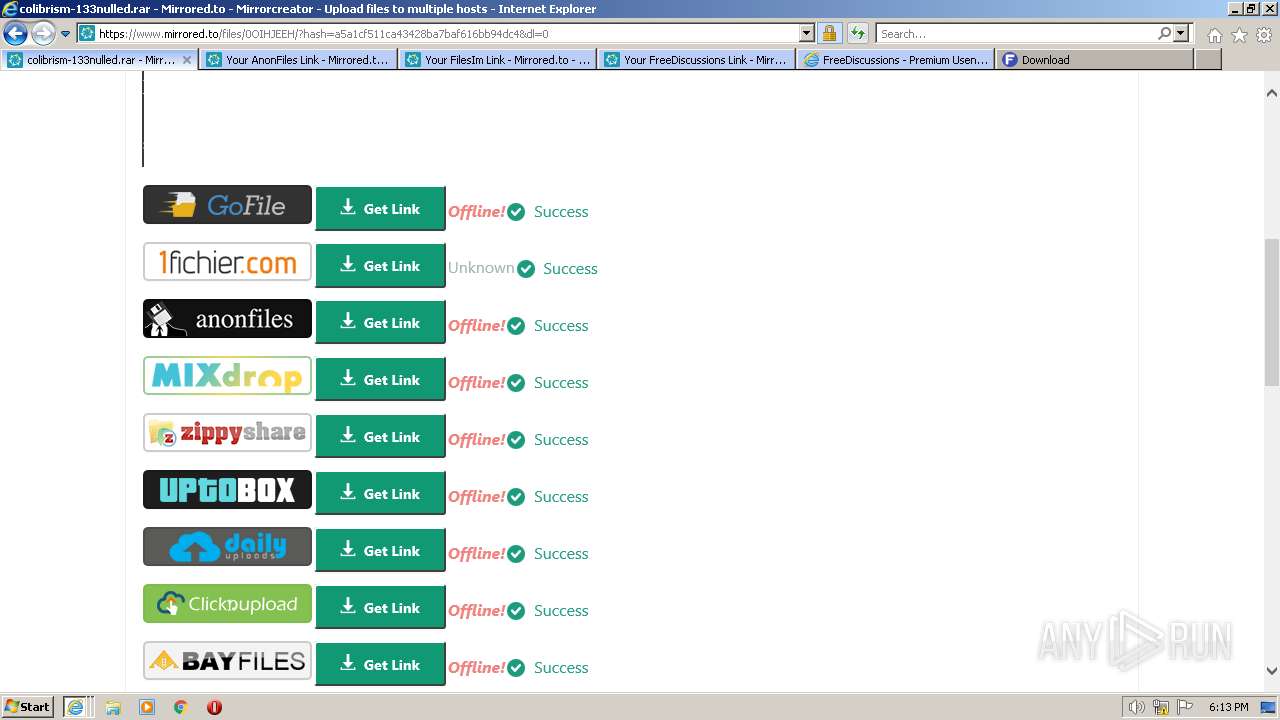
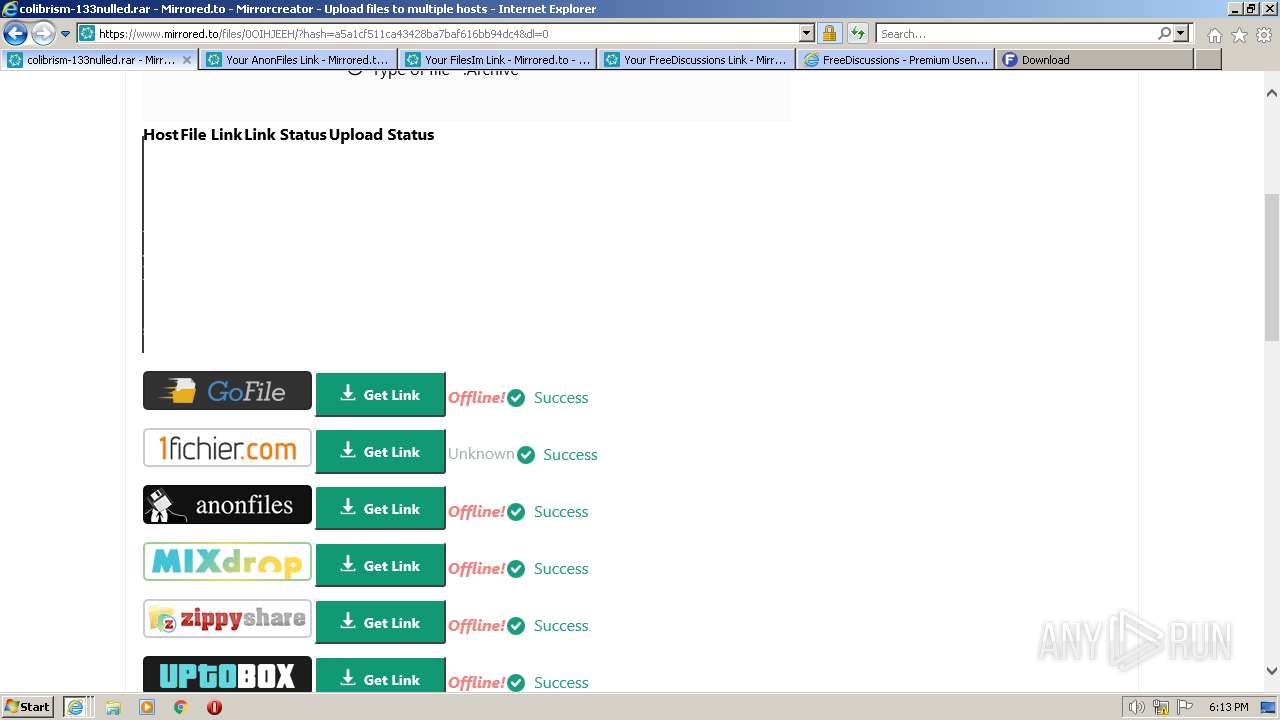
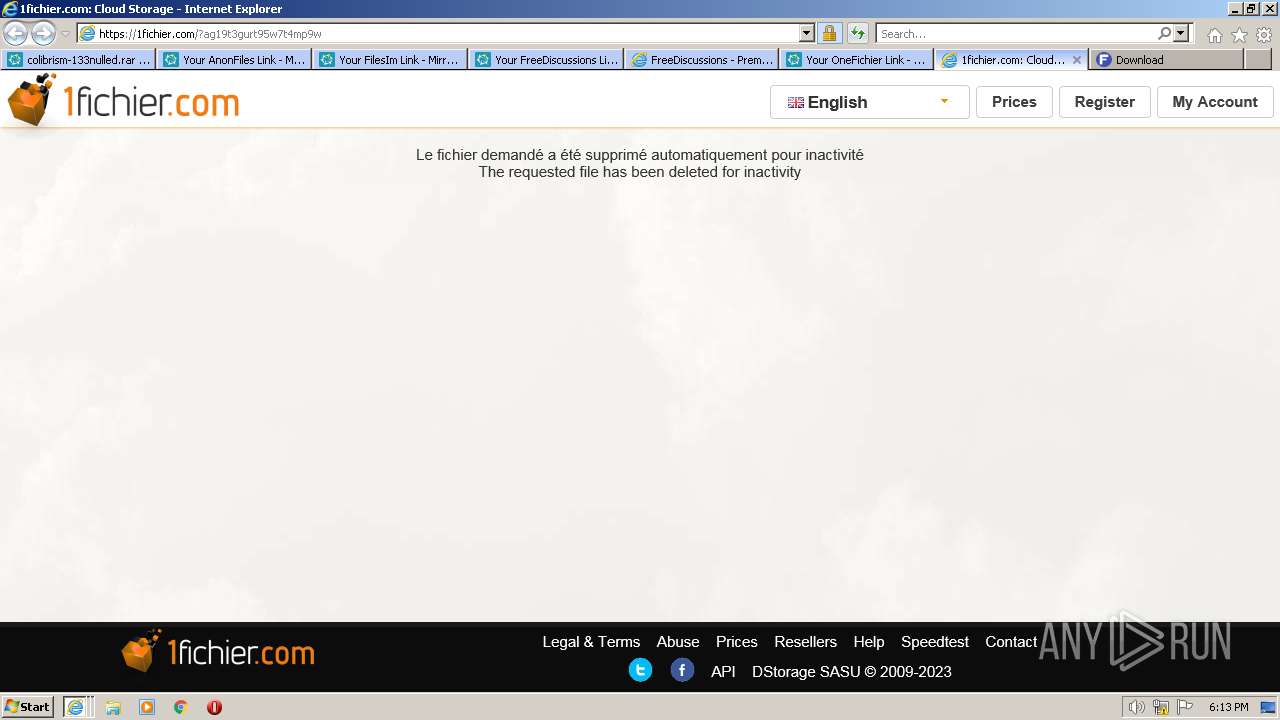
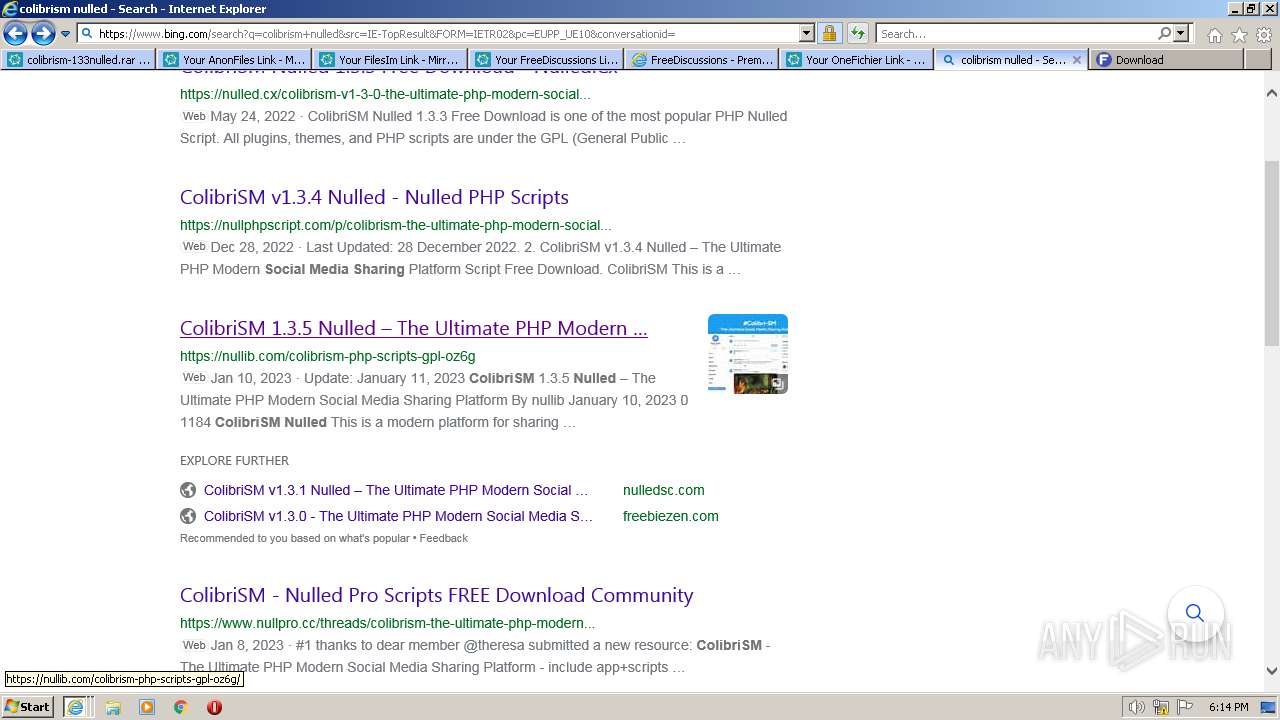
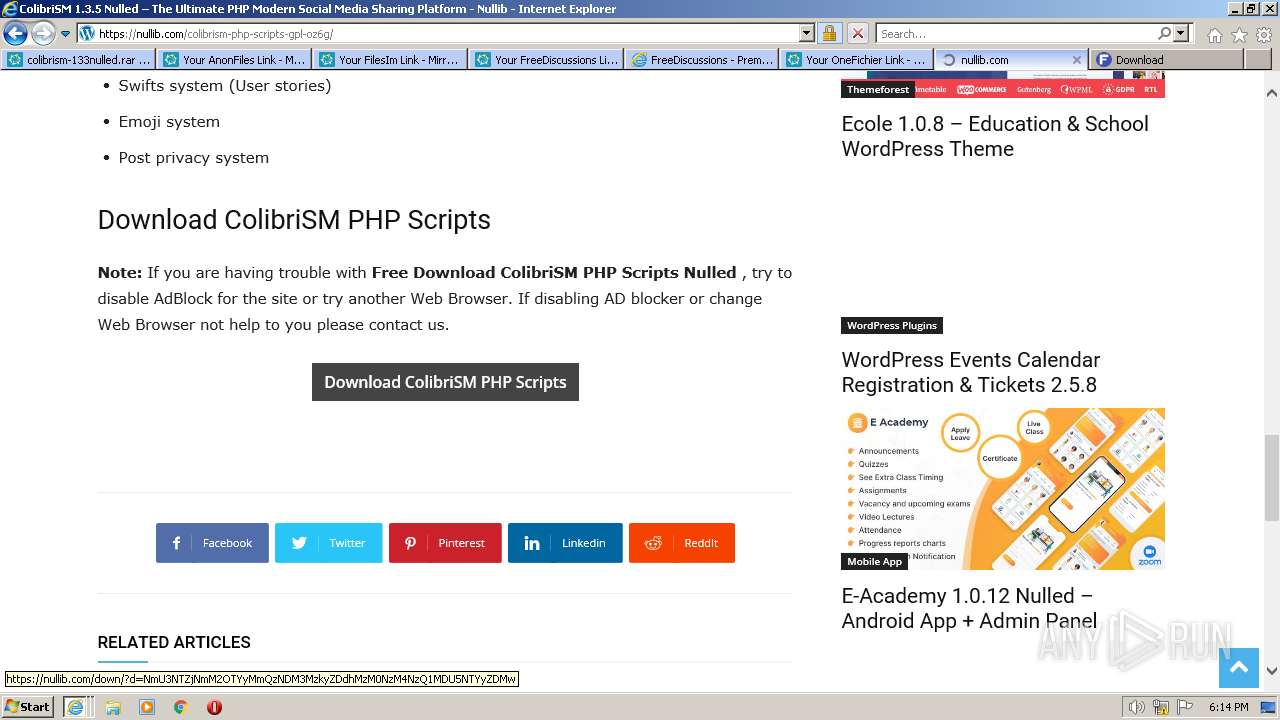
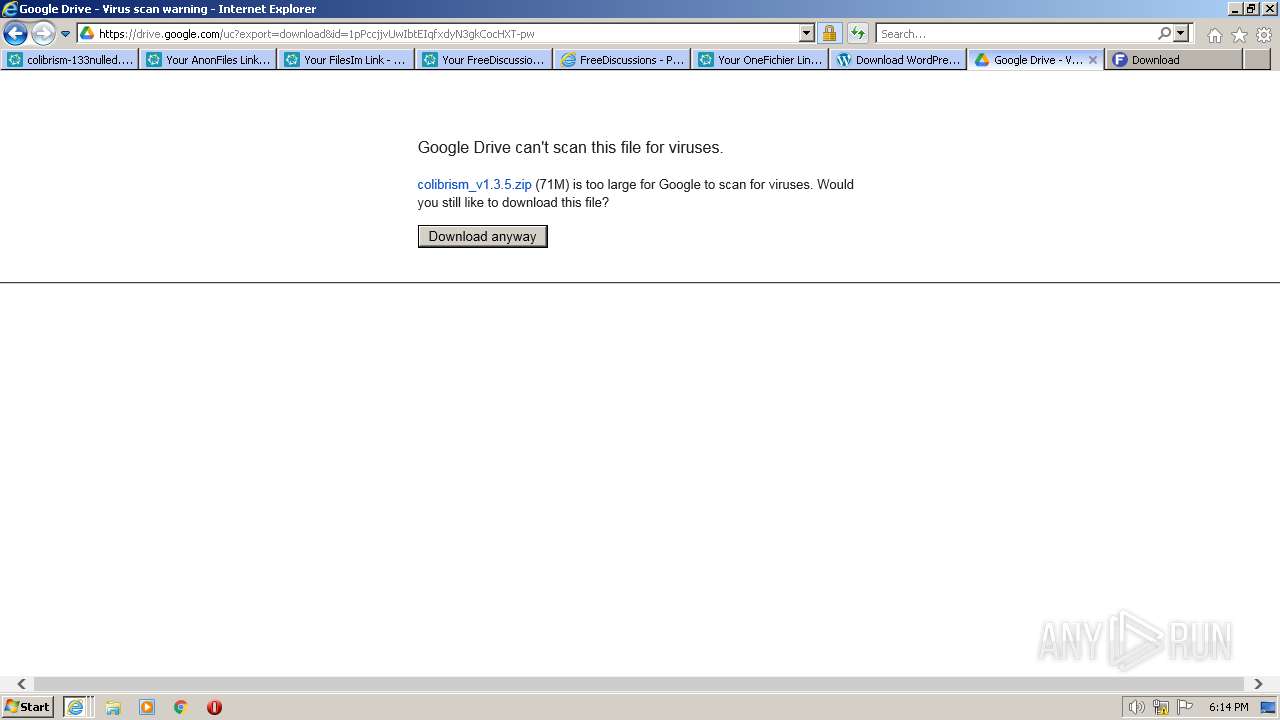
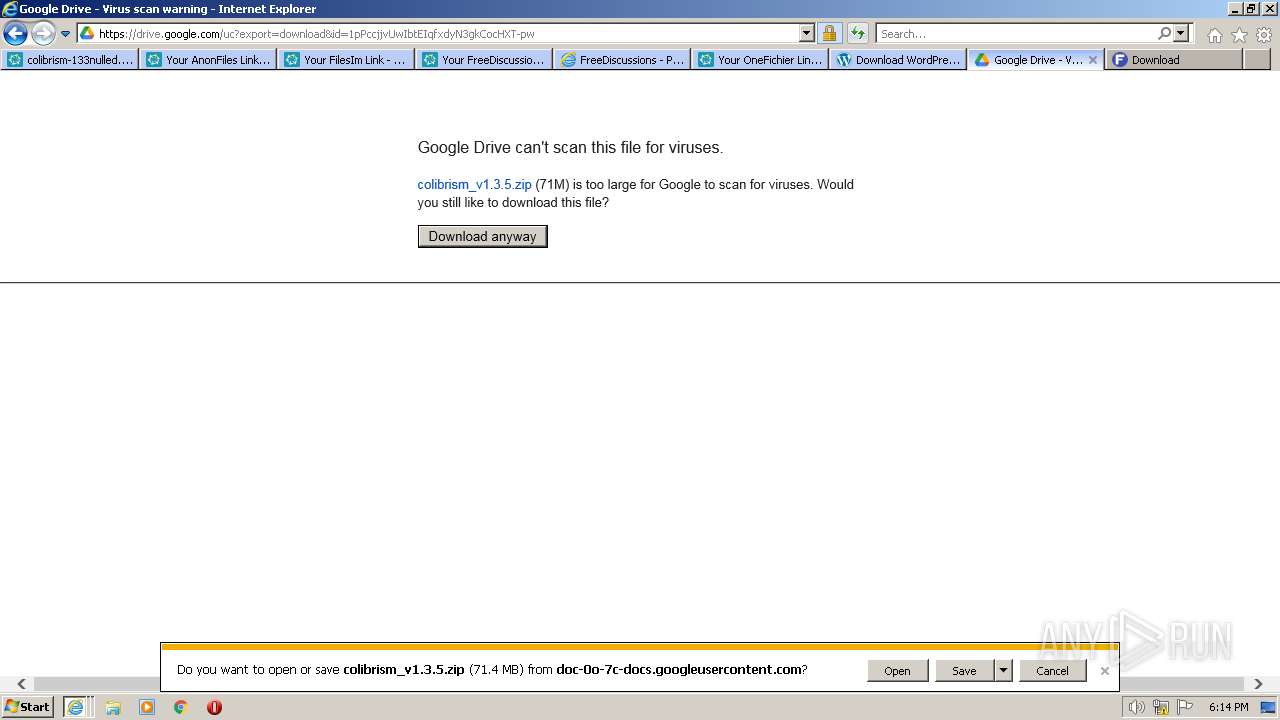
| URL: | https://www.mirrored.to/files/0OIHJEEH/colibrism-133nulled.rar_links |
| Full analysis: | https://app.any.run/tasks/e9653422-c72f-43d2-a54a-4adaa755371f |
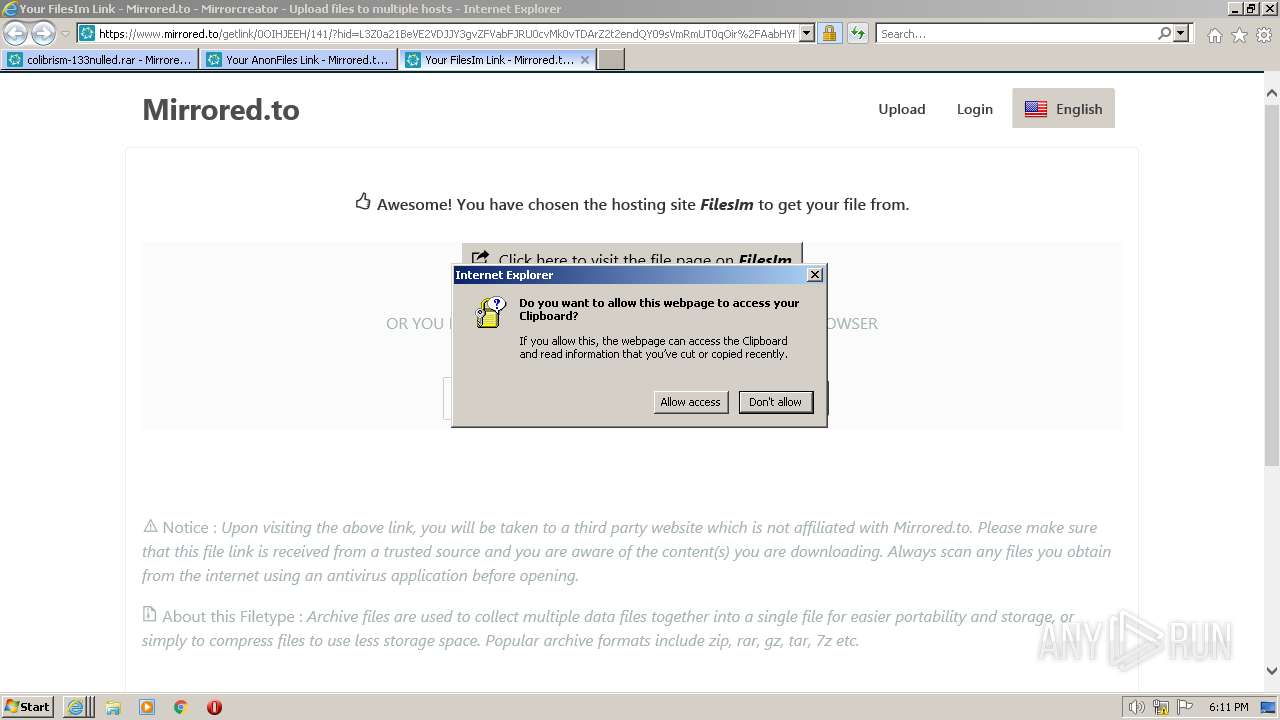
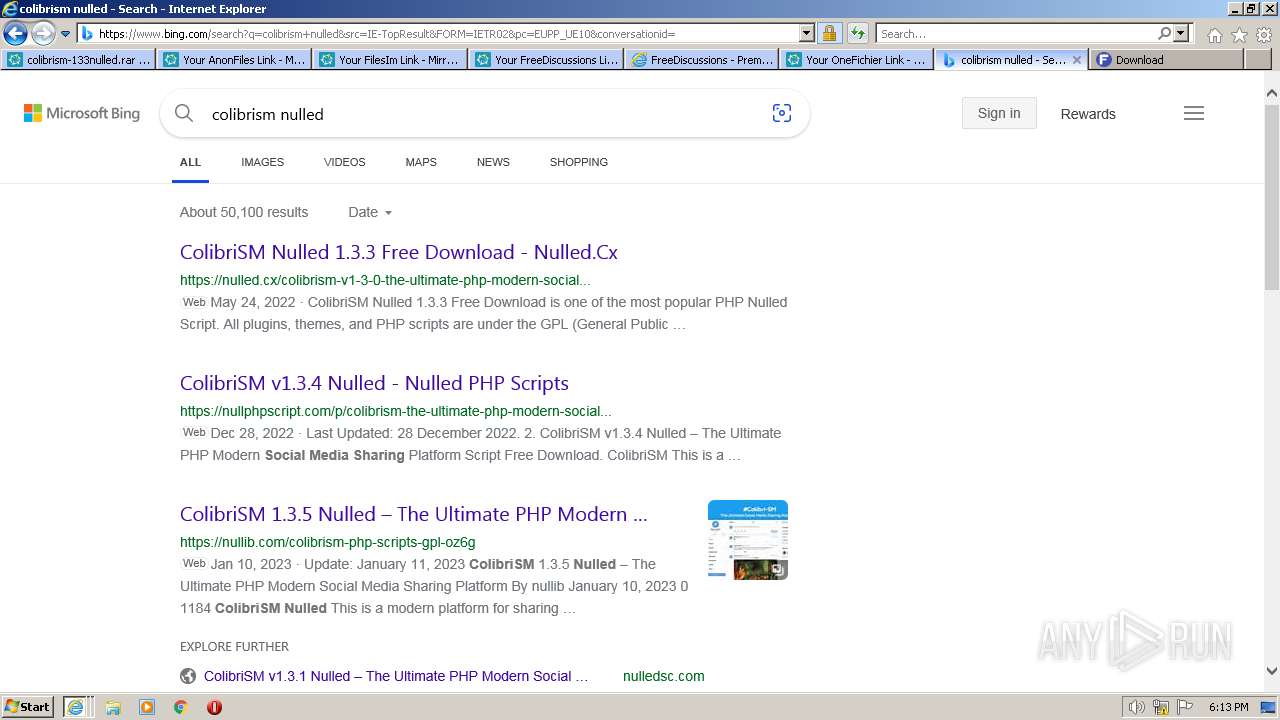
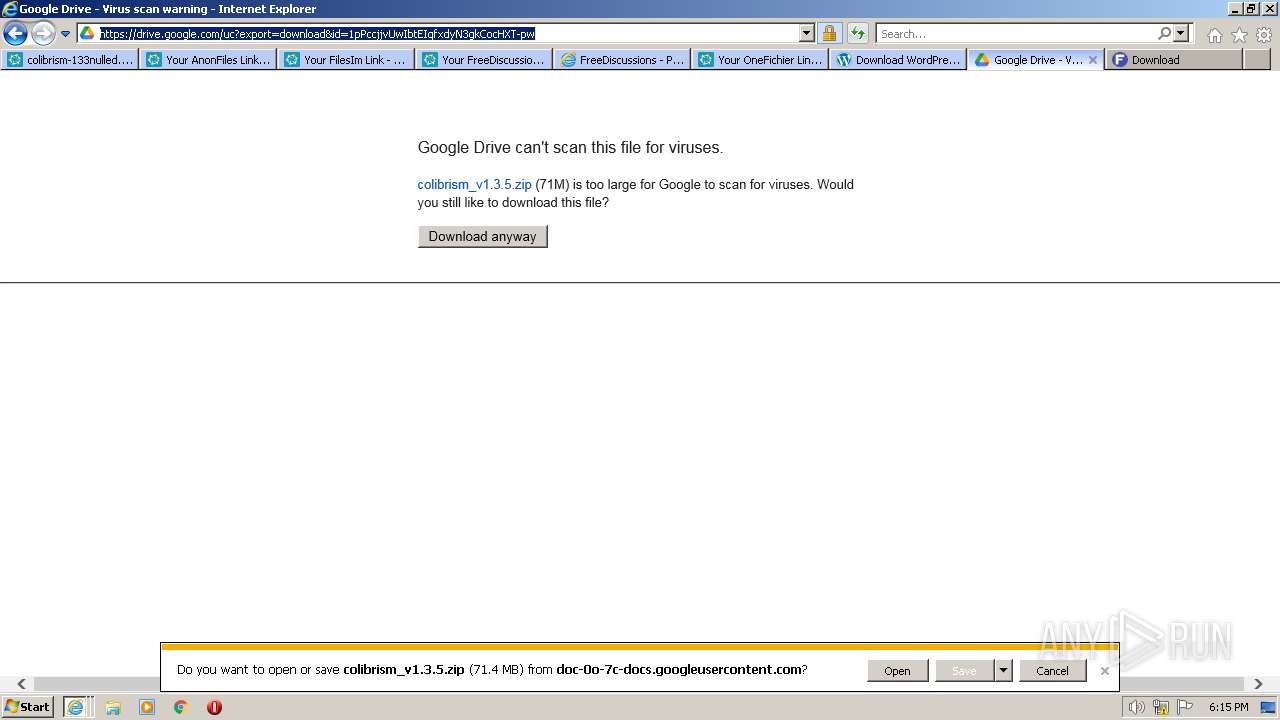
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2023, 17:10:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 498840DA6B36BDC4996ABA09F45696FB |
| SHA1: | 9E9DD6F5C68B9E0FFBBCF39E8CA7D29CD6EDC111 |
| SHA256: | 272A1F8BEF2D2A556D1442CC4082472D42B813A7DD0B506F91FC7D19FABB8D0F |
| SSDEEP: | 3:N8DSLWHJzKVXiW/H1PMTj+TOWn:2OLTX9ETjOOW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
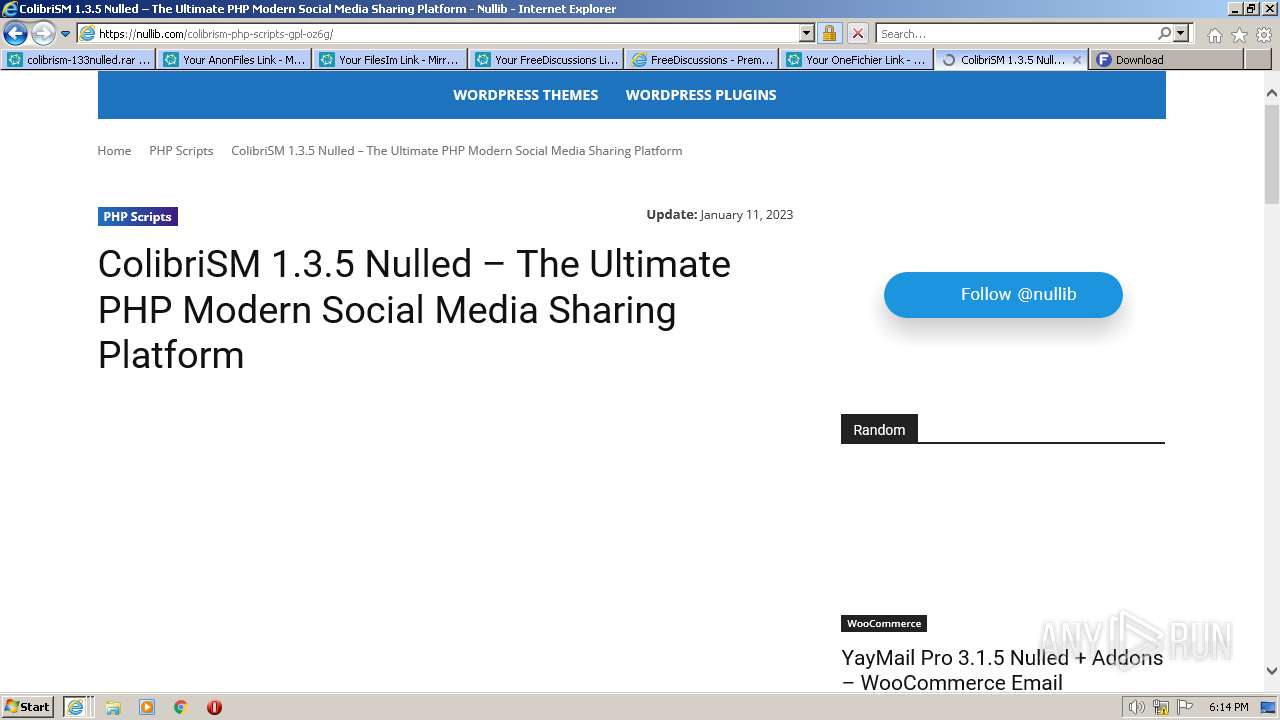
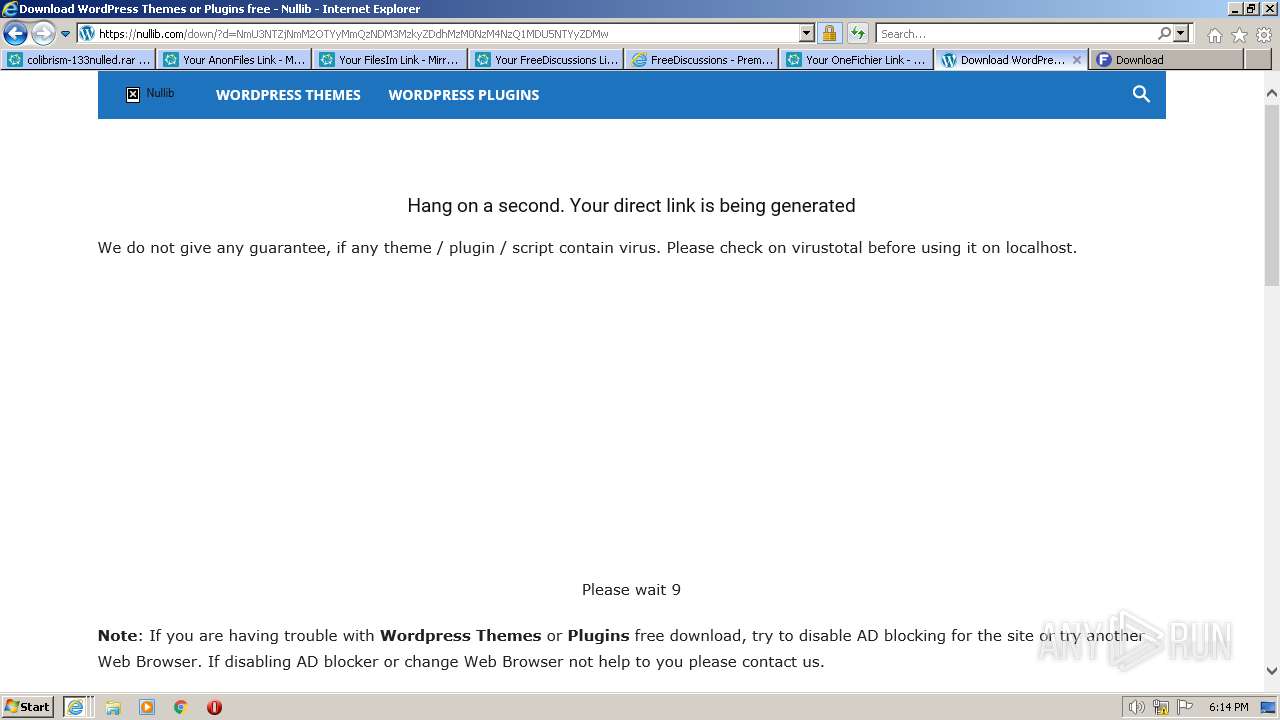
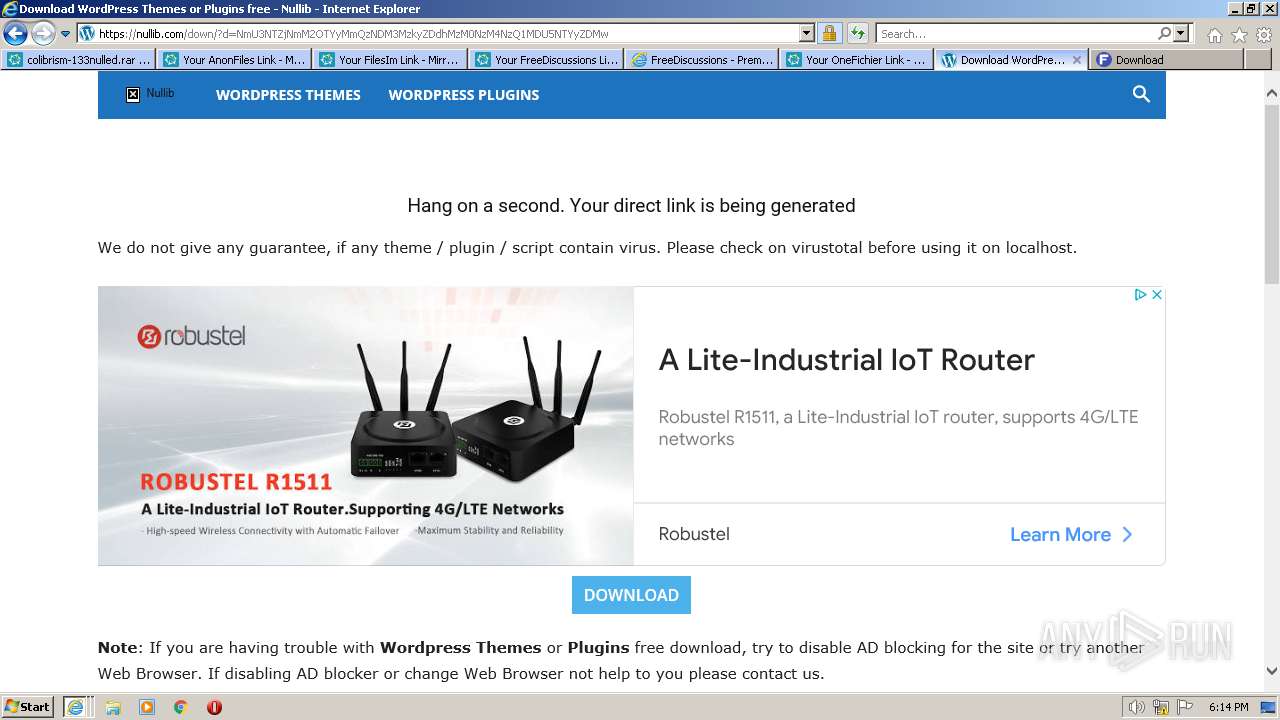
Application launched itself
- iexplore.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:726331 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:4134193 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:2561286 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:791845 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2720 CREDAT:922928 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.mirrored.to/files/0OIHJEEH/colibrism-133nulled.rar_links" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
68 029
Read events
67 476
Write events
541
Delete events
12
Modification events
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2720) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
180
Text files
630
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:E76273BCD83D9127AE1B46053B8C4E92 | SHA256:0EDDBDCC07AA95F6829860489B7367913108EAE9F87E8A0078842FBCCB70AE3D | |||
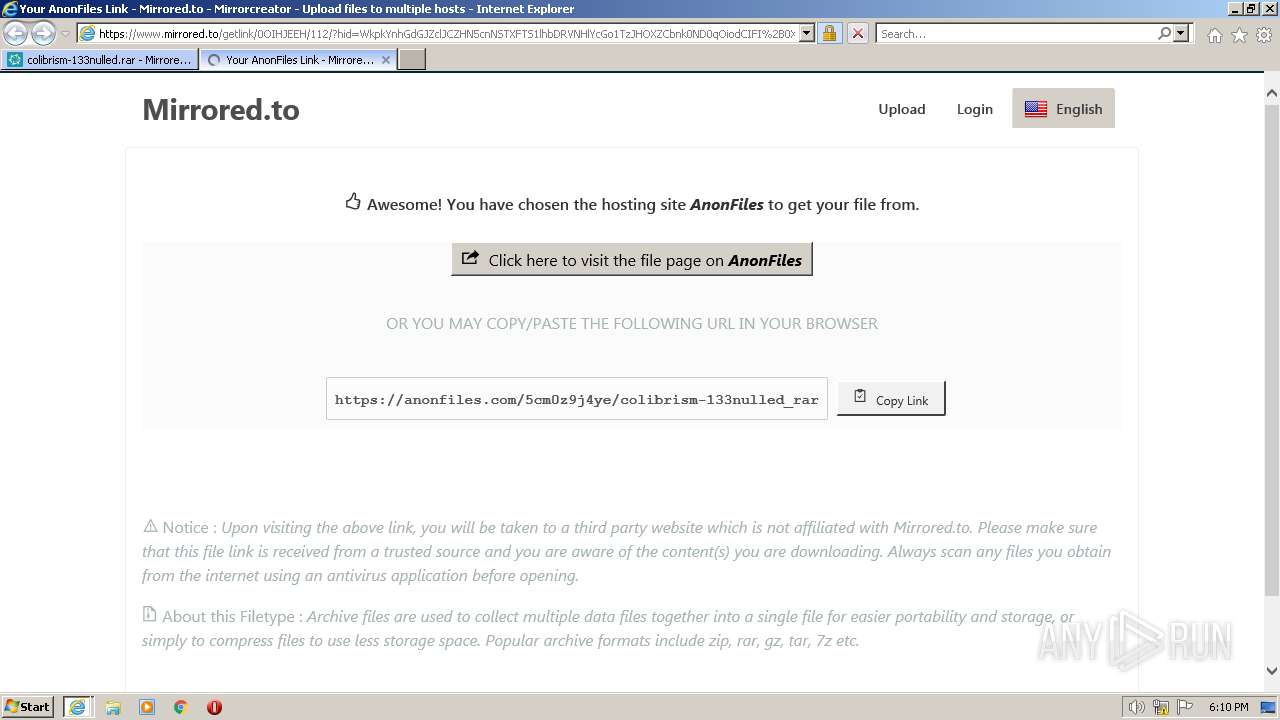
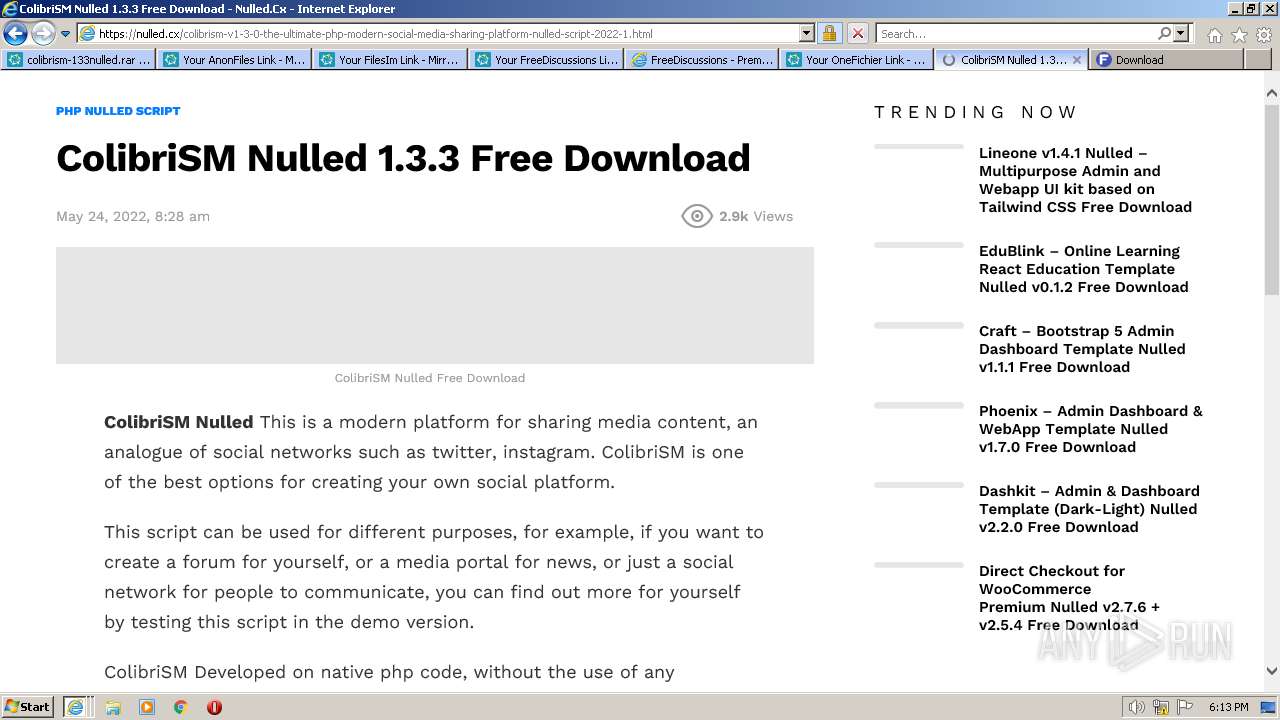
| 2520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\colibrism-133nulled[1].htm | html | |
MD5:FD7B311A4766A6423B36045681BDDAAA | SHA256:8BD981D8A8C1B3869C67AD0553847F777D507EDFAEBCB2FFA3064C0CD3A550FA | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0255CEC2C51D081EFF40366512890989_221475F22EAD39FD178000E1E2909356 | binary | |
MD5:B6A7CAD194E263BBB135A659D0B872A2 | SHA256:1F3CF2224B01167D8140949ACFF0673029CECF9DB6DC6CD142C9127F84D8047A | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:735D405C0967A88F2209C4A6FA61F113 | SHA256:80C04108E6523F73BA8E9A135AEBF4E0C5569DD3AB825373C3393F250E5457A1 | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\normalize[1].css | text | |
MD5:D63641064D467219FD9C00D23DA1272B | SHA256:D5963ECBF1DB726386F0557788A4E8EDCF4FC3B25E75E55898C1CE0FD9953230 | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | binary | |
MD5:500E0D20DFB15E72AEE4DF1703237391 | SHA256:D3B69BE9262624114339652E31A643B40A13098E4C332706BC964D9818DC9A78 | |||
| 2520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0255CEC2C51D081EFF40366512890989_221475F22EAD39FD178000E1E2909356 | binary | |
MD5:E3258F41B8C36D2FBE5A41DEE6E6EAF4 | SHA256:9AC1AEC942E6BA416201588F7EFE66D3C350E07591D706335BC56ECC8ADB4D00 | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
369
DNS requests
117
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | iexplore.exe | GET | 200 | 143.204.214.29:80 | http://s.ss2.us/r.crl | US | binary | 486 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 8.253.95.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbfc03f98bc5ce51 | US | compressed | 4.70 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 104.18.15.101:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | unknown | binary | 1.42 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA8YZzspoxtbCTc%2Bbw9oYFQ%3D | US | binary | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA8YZzspoxtbCTc%2Bbw9oYFQ%3D | US | binary | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 8.253.95.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4eea6f841946d09e | US | compressed | 4.70 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG2%2Fl3nJNGq9Ck3gvVLB41Y%3D | US | binary | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 104.18.15.101:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSTufqHinruS%2FP9Wi1XSjRRzoTLfAQUfgNaZUFrp34K4bidCOodjh1qx2UCEQChq22gOXYFan1LMAQybgcg | unknown | der | 472 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEE%2Fke5Q8HG0aENG6mJCKPmQ%3D | US | binary | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGiKnXCJIkKUErtB3cBGUhA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2520 | iexplore.exe | 8.253.95.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2520 | iexplore.exe | 18.66.121.82:443 | d1ux93ber9vlwt.cloudfront.net | AMAZON-02 | US | unknown |
2520 | iexplore.exe | 142.250.186.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
2520 | iexplore.exe | 104.18.15.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
2520 | iexplore.exe | 142.250.185.136:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
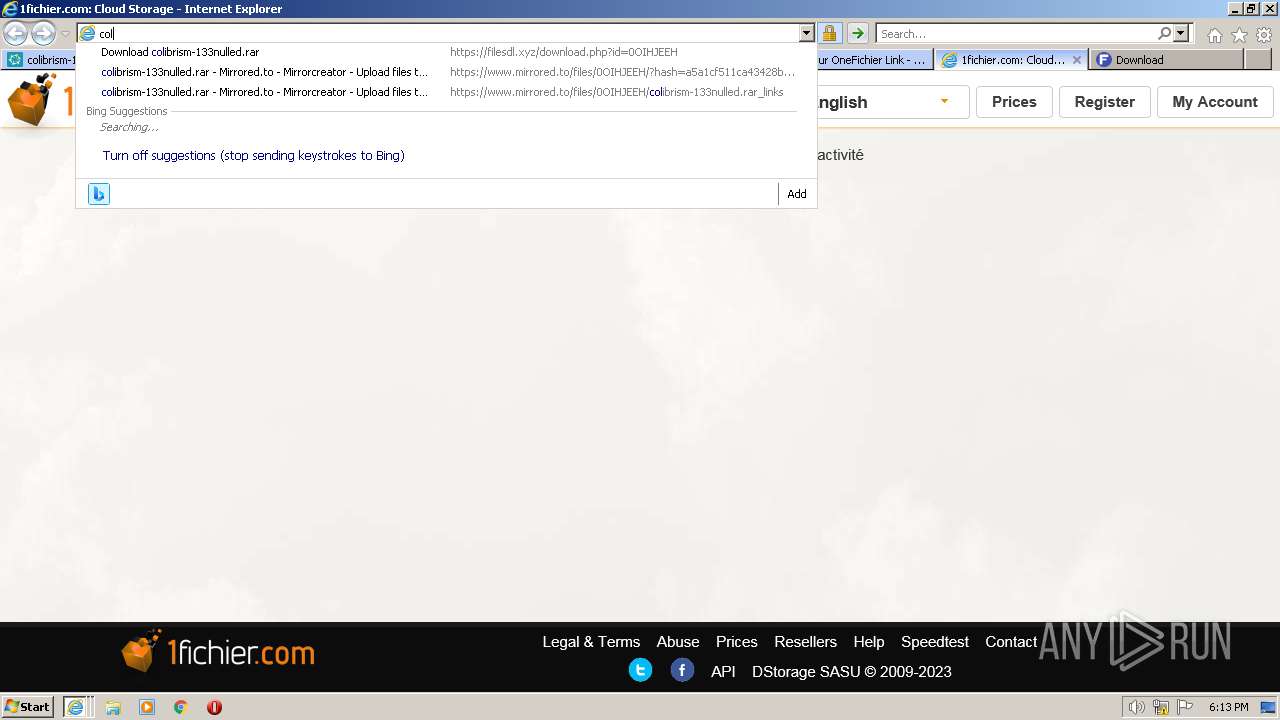
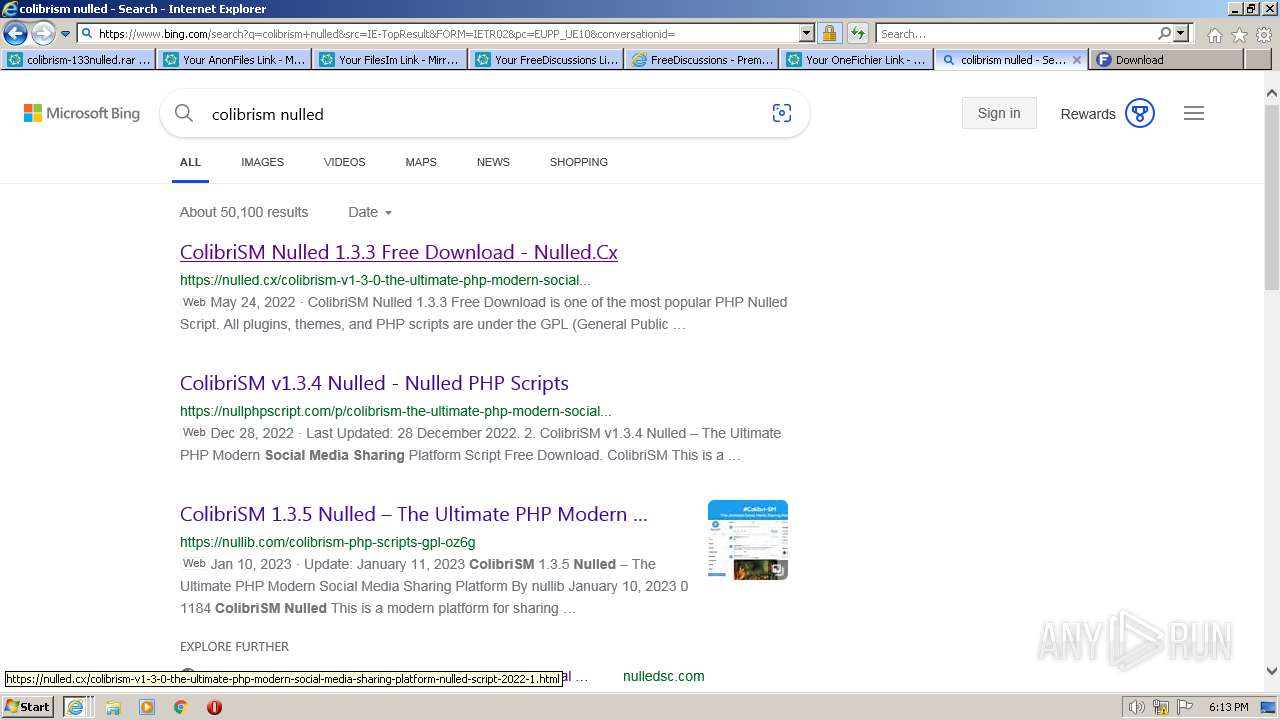
2720 | iexplore.exe | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2520 | iexplore.exe | 143.204.214.29:80 | s.ss2.us | AMAZON-02 | US | unknown |
2720 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
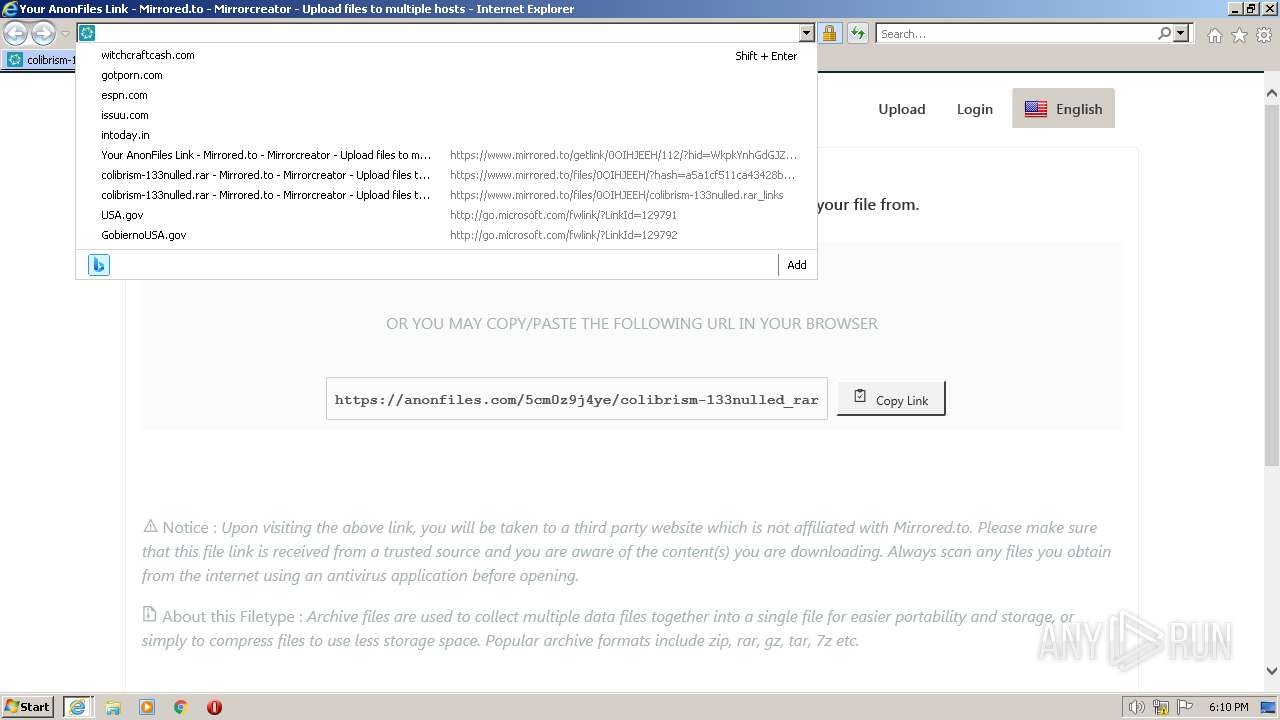
www.mirrored.to |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
d1ux93ber9vlwt.cloudfront.net |
| suspicious |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
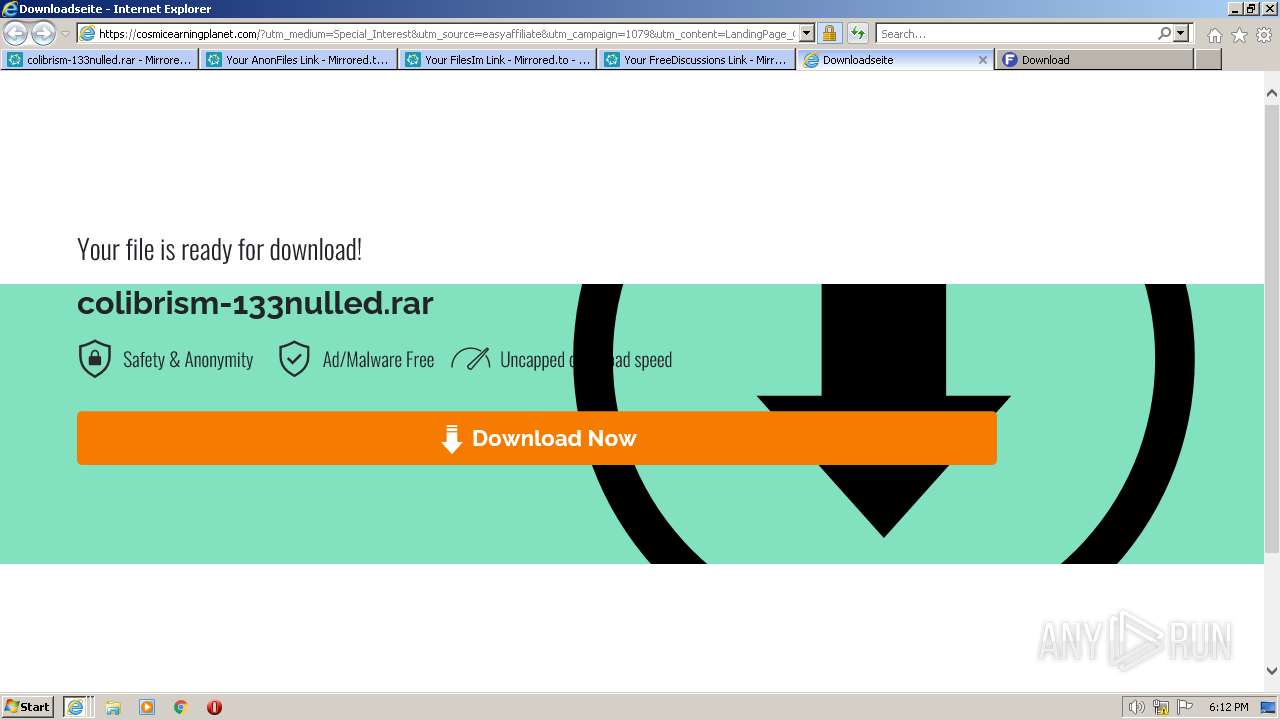
Threats
PID | Process | Class | Message |
|---|---|---|---|
2644 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
2644 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
2644 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
2644 | iexplore.exe | Generic Protocol Command Decode | SURICATA TLS certificate invalid der |
1076 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |