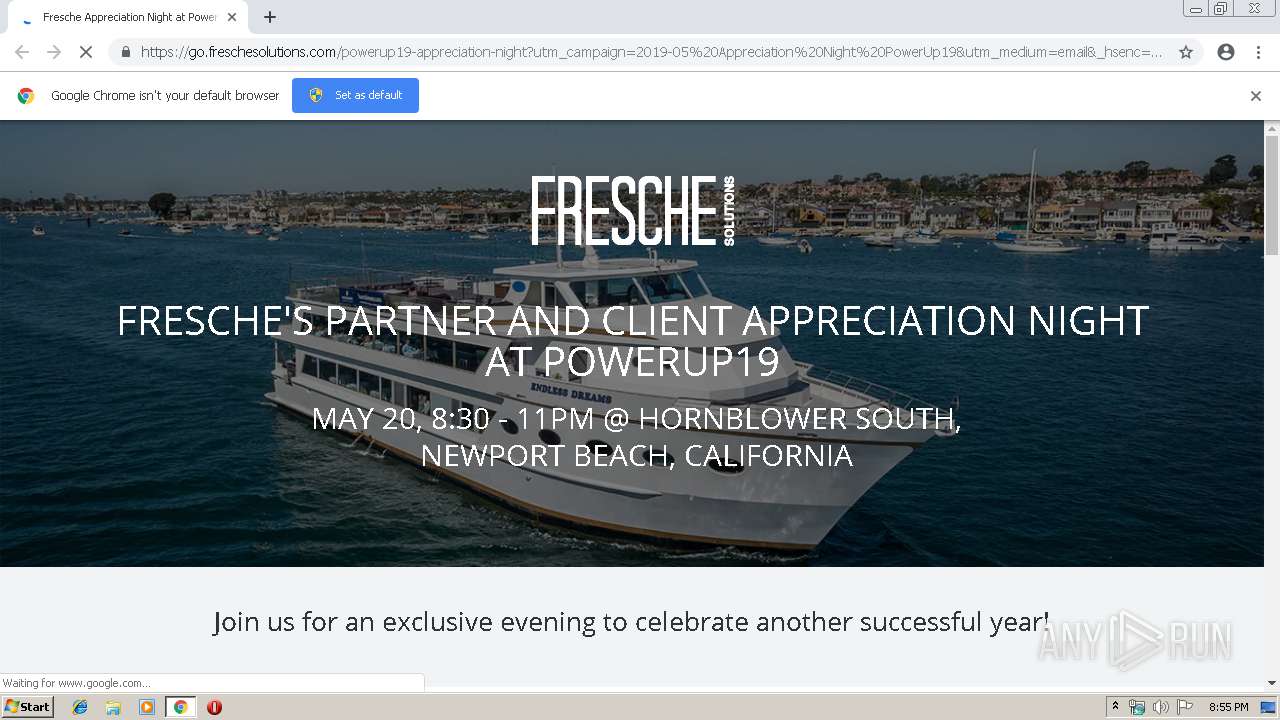
| URL: | https://go.freschesolutions.com/e2t/c/*W2SLMJQ2bD7F4W9690_P6mpR5Z0/*VBfY3P9b8p18V2hKK13jbZ5f0/5/f18dQhb0S1Wb7Bf-yvV1xZQ61MNfkJN1g-z5l6g0qjW2HNHwF3Grs7qW6TmHtp6zz8WSW1K_C_m2RGx3_W6KS3Jc8zbrrwW54jZGv2v2yVvW7mX29l16FTjWW5jbYKx7GbZzzVS_QL193d4sRW2kwsjk6VplCHN93bvH11zDQPW8pNDZP4jrRNgW64mrQP5BvCP-N8_MDfjMPXHLW1sd3h52y0-N_N6ZQ_JjgjK-GW1rbM8W6brRT4W5h3QzC6nVmH0V5GDVQ7rc9q-W4nYptM1LQlHpW1m46Zd6tNdtfV2Gq0n6vfNYzW4t3GkV2nJY2hW5w5-GZ8dbSrtW1qPgm81jktdHW3F5qPG1NXXRjW2RdWGG78PwnJW5WnZzw8qKWVhN7FFWjLHw0wYW5FWz475tYkp_W5n96N28QPR82W6Cx3dj6LsldDN5tKP8PX0nq9W2pCFMc6t7SgLW3wp0DT5hQLcJW1WS-zt3sDlsYW2_5SHp5QqTWdW2-vm4j8W82P2W2cW3cX5wCX98W61r_xS3fwlX_W4YPft85y0pY6W7l_Qyd6p0LHfW79C15l8TqpzxW6kbkH81WH-r4W2hxP9d8wzz5CN14DS4GPSxp7W578nhW7HVR1lW2tS16y6HVx-6W38v3Hf5bYK2NW6nZjdl6mlT0pW2tQFD-4v-6zSW4W6-WW1Rz5QjW59801f8KgCVTW3B8w9X915fxTW40S8917g0mXcW7yWVWg6scYKYW1j-53773KBDYW1kyryf888sZ9W21J9LK14JrTXW8ZlwRm7VQQDQW7zPW234FBndmW80mZ3K91fsBfW6L0YNj15v_RdW4lSSg24pKptM102 |
| Full analysis: | https://app.any.run/tasks/6e76c773-59ec-4f29-a2f8-9ca2dcee6697 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 19:55:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 65A1AB2E7E874BBCEE433F5554C06B76 |
| SHA1: | 8B0B738CC1625C32BB39A31E37EC23C9F3413C14 |
| SHA256: | 27131CB52F2054D4C1191838161E27868B19C580997AD5D21E28361167D92458 |
| SSDEEP: | 24:2n+4LB/1JYBOHaoc6vA9RxEFQrI8U8jAJ5:m+49gBAG9RxE688UaA3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2984)
INFO
Changes settings of System certificates
- chrome.exe (PID: 2984)
Application launched itself
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14399454790506768143 --mojo-platform-channel-handle=4680 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2169866614618884395 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2169866614618884395 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1436855853367201522 --mojo-platform-channel-handle=4436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10578475015779061293 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10578475015779061293 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=9224297308187589924 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9224297308187589924 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9370828880518939722 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2988 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://go.freschesolutions.com/e2t/c/*W2SLMJQ2bD7F4W9690_P6mpR5Z0/*VBfY3P9b8p18V2hKK13jbZ5f0/5/f18dQhb0S1Wb7Bf-yvV1xZQ61MNfkJN1g-z5l6g0qjW2HNHwF3Grs7qW6TmHtp6zz8WSW1K_C_m2RGx3_W6KS3Jc8zbrrwW54jZGv2v2yVvW7mX29l16FTjWW5jbYKx7GbZzzVS_QL193d4sRW2kwsjk6VplCHN93bvH11zDQPW8pNDZP4jrRNgW64mrQP5BvCP-N8_MDfjMPXHLW1sd3h52y0-N_N6ZQ_JjgjK-GW1rbM8W6brRT4W5h3QzC6nVmH0V5GDVQ7rc9q-W4nYptM1LQlHpW1m46Zd6tNdtfV2Gq0n6vfNYzW4t3GkV2nJY2hW5w5-GZ8dbSrtW1qPgm81jktdHW3F5qPG1NXXRjW2RdWGG78PwnJW5WnZzw8qKWVhN7FFWjLHw0wYW5FWz475tYkp_W5n96N28QPR82W6Cx3dj6LsldDN5tKP8PX0nq9W2pCFMc6t7SgLW3wp0DT5hQLcJW1WS-zt3sDlsYW2_5SHp5QqTWdW2-vm4j8W82P2W2cW3cX5wCX98W61r_xS3fwlX_W4YPft85y0pY6W7l_Qyd6p0LHfW79C15l8TqpzxW6kbkH81WH-r4W2hxP9d8wzz5CN14DS4GPSxp7W578nhW7HVR1lW2tS16y6HVx-6W38v3Hf5bYK2NW6nZjdl6mlT0pW2tQFD-4v-6zSW4W6-WW1Rz5QjW59801f8KgCVTW3B8w9X915fxTW40S8917g0mXcW7yWVWg6scYKYW1j-53773KBDYW1kyryf888sZ9W21J9LK14JrTXW8ZlwRm7VQQDQW7zPW234FBndmW80mZ3K91fsBfW6L0YNj15v_RdW4lSSg24pKptM102 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7044136533532908101 --mojo-platform-channel-handle=4512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=230685609012659923 --mojo-platform-channel-handle=4660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
563
Read events
475
Write events
83
Delete events
5
Modification events
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13202423733660875 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
48
Text files
133
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
41
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | chrome.exe | GET | 200 | 52.222.146.156:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2984 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
2984 | chrome.exe | GET | 200 | 74.125.173.166:80 | http://r1---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1557949947&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | chrome.exe | 104.16.252.5:443 | cta-image-cms2.hubspot.com | Cloudflare Inc | US | shared |
2984 | chrome.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.16.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 151.101.2.110:443 | fast.wistia.com | Fastly | US | suspicious |
2984 | chrome.exe | 104.17.243.204:443 | cdn2.hubspot.net | Cloudflare Inc | US | shared |
2984 | chrome.exe | 74.125.71.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
go.freschesolutions.com |
| suspicious |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
cta-image-cms2.hubspot.com |
| whitelisted |
cdn2.hubspot.net |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Too long restart command line passed |
chrome.exe | Too long restart command line passed |
chrome.exe |