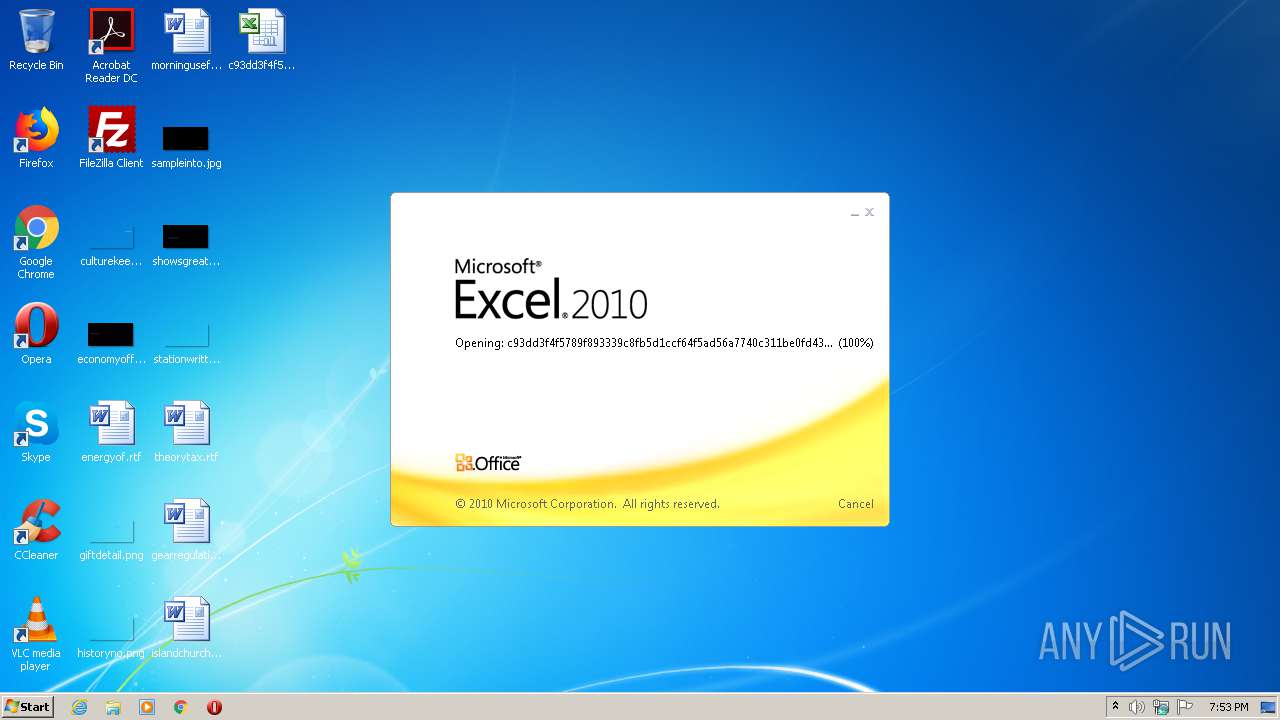
| File name: | c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.zip |
| Full analysis: | https://app.any.run/tasks/c618e5b4-fc99-46ce-aed2-a1bb12d546de |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:52:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B07155656119C1038FBAA8EAA822D0B7 |
| SHA1: | EE6D4B1FE947376EF7E63E4AAE216B0A1BBA1173 |
| SHA256: | 270FDF2CA8B5467A2E953B3FA2EE9BEE8B1A9F564854ABD76E1A229B21F2F93E |
| SSDEEP: | 12288:KzBpRN7osE49nIWHpjtDaeQaxbJtTi8DwU+1yQKUYuAQDyMffjBfWLSEgrMvE:SBd7xnppjB/QaxbJBi8p+MQGudDyyxWU |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 4024)
SUSPICIOUS
Executes application which crashes
- EXCEL.EXE (PID: 4024)
INFO
Manual execution by user
- EXCEL.EXE (PID: 4024)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 4024)
Creates files in the user directory
- EXCEL.EXE (PID: 4024)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
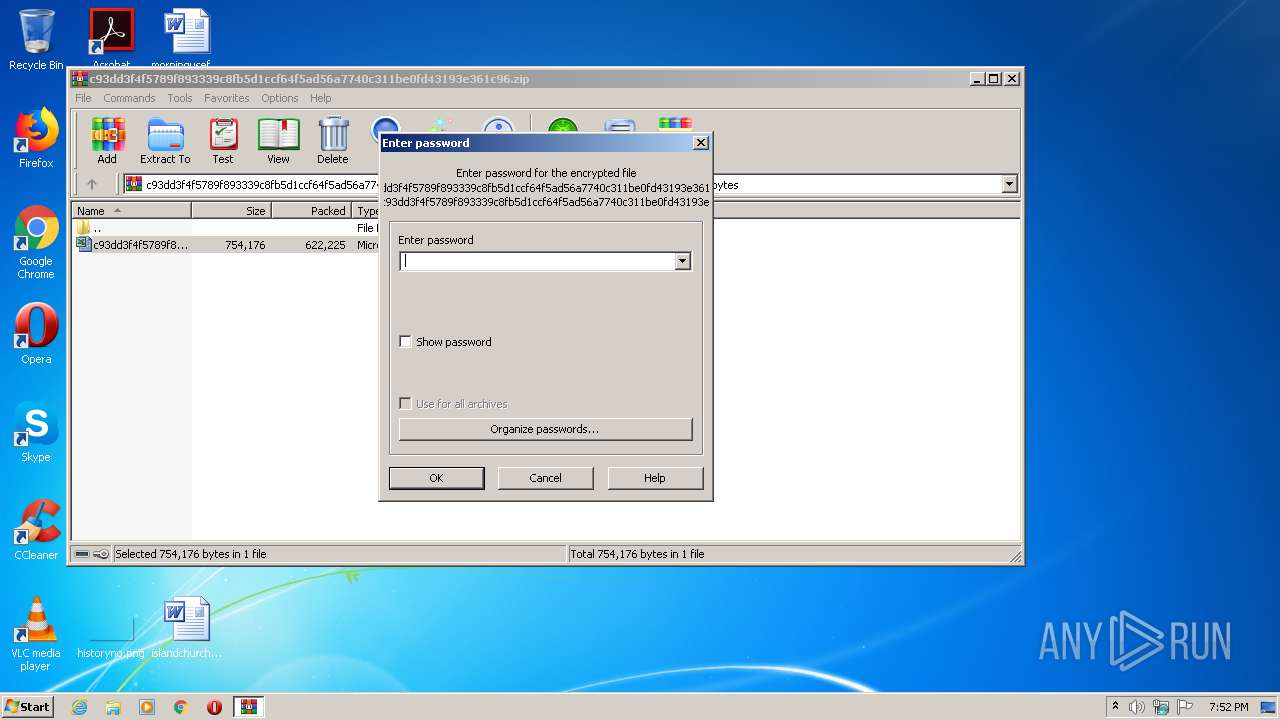
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:07:12 18:51:29 |
| ZipCRC: | 0xf4b4060e |
| ZipCompressedSize: | 622225 |
| ZipUncompressedSize: | 754176 |
| ZipFileName: | c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.xls |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
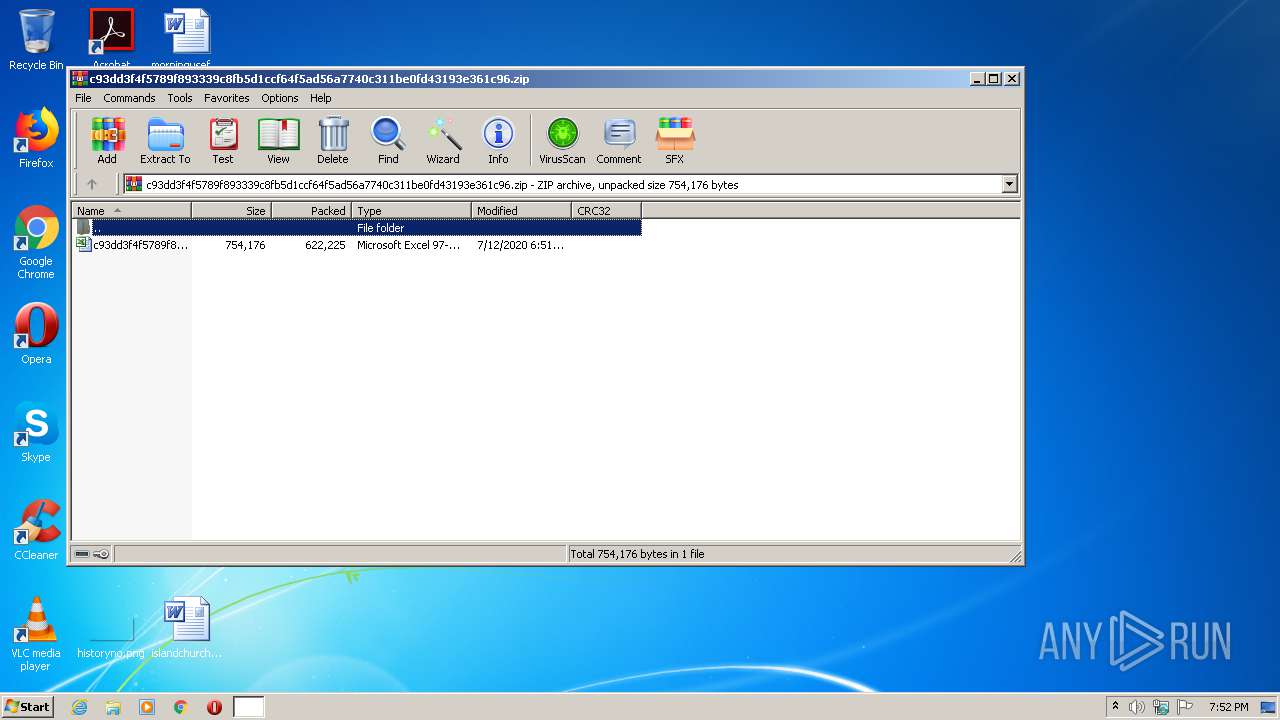
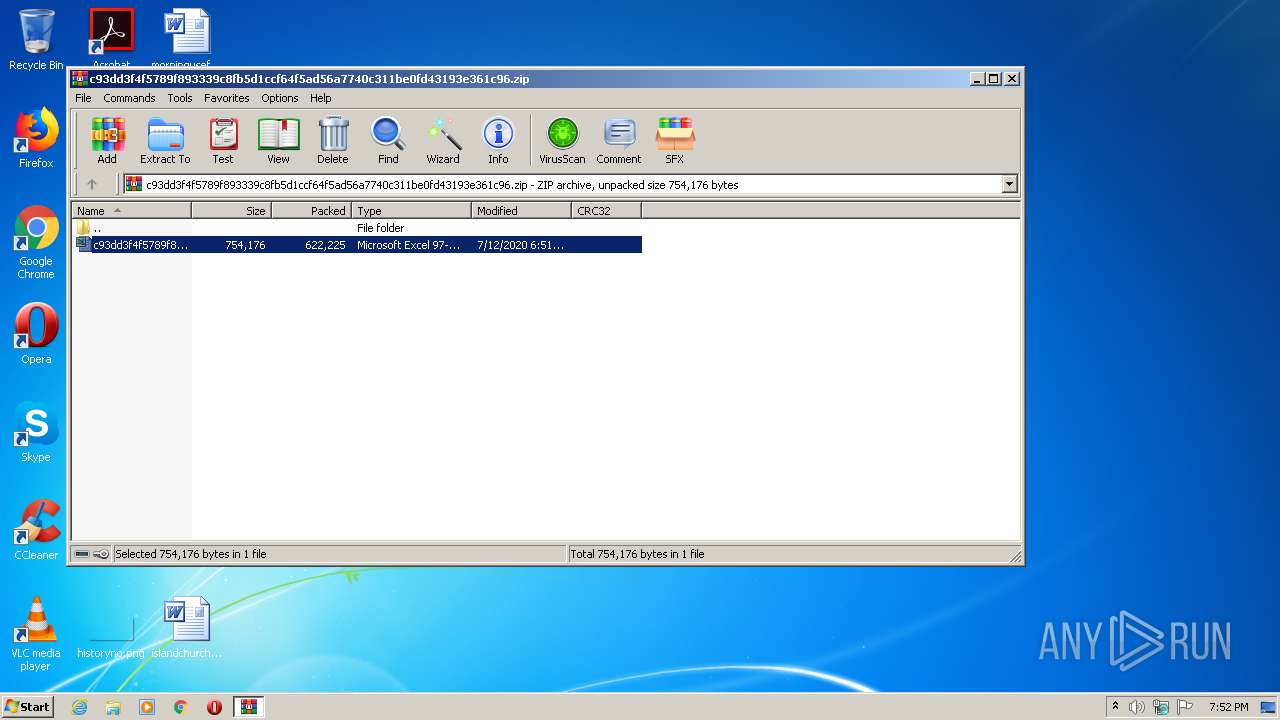
| 600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1196 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 206
Read events
1 125
Write events
70
Delete events
11
Modification events
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.zip | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
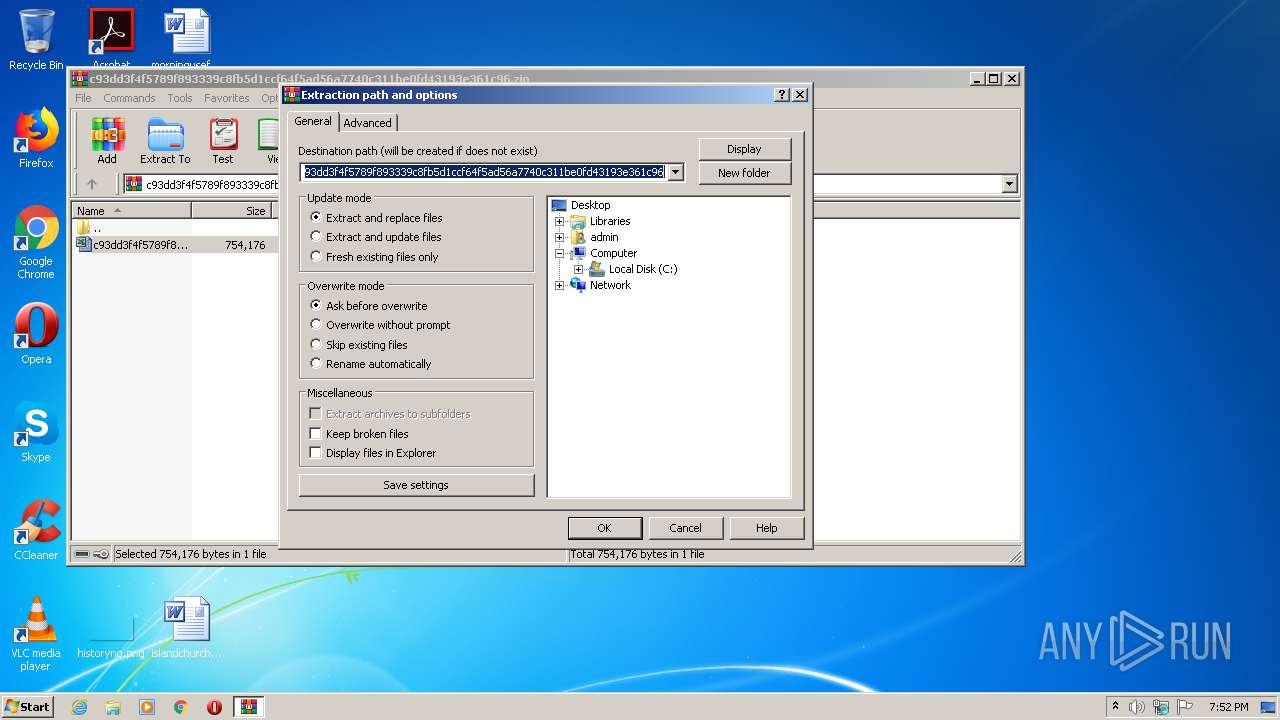
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1196 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs1634.tmp | — | |
MD5:— | SHA256:— | |||
| 1196 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs1645.tmp | — | |
MD5:— | SHA256:— | |||
| 4024 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 4024 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\antarktida[1].htm | html | |
MD5:— | SHA256:— | |||
| 4024 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 4024 | EXCEL.EXE | C:\Users\admin\Documents\QLzULCP.exe | html | |
MD5:— | SHA256:— | |||
| 600 | WinRAR.exe | C:\Users\admin\Desktop\c93dd3f4f5789f893339c8fb5d1ccf64f5ad56a7740c311be0fd43193e361c96.xls | document | |
MD5:8074AC3927DFB130C1FB20D7B248A339 | SHA256:C93DD3F4F5789F893339C8FB5D1CCF64F5AD56A7740C311BE0FD43193E361C96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | EXCEL.EXE | GET | 200 | 43.255.154.107:80 | http://solfacts.com/smjw6q7/antarktida.php | SG | html | 10.8 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | EXCEL.EXE | 43.255.154.107:80 | solfacts.com | GoDaddy.com, LLC | SG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
solfacts.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4024 | EXCEL.EXE | A Network Trojan was detected | MALWARE [PTsecurity] VBS.Loader.Gen |