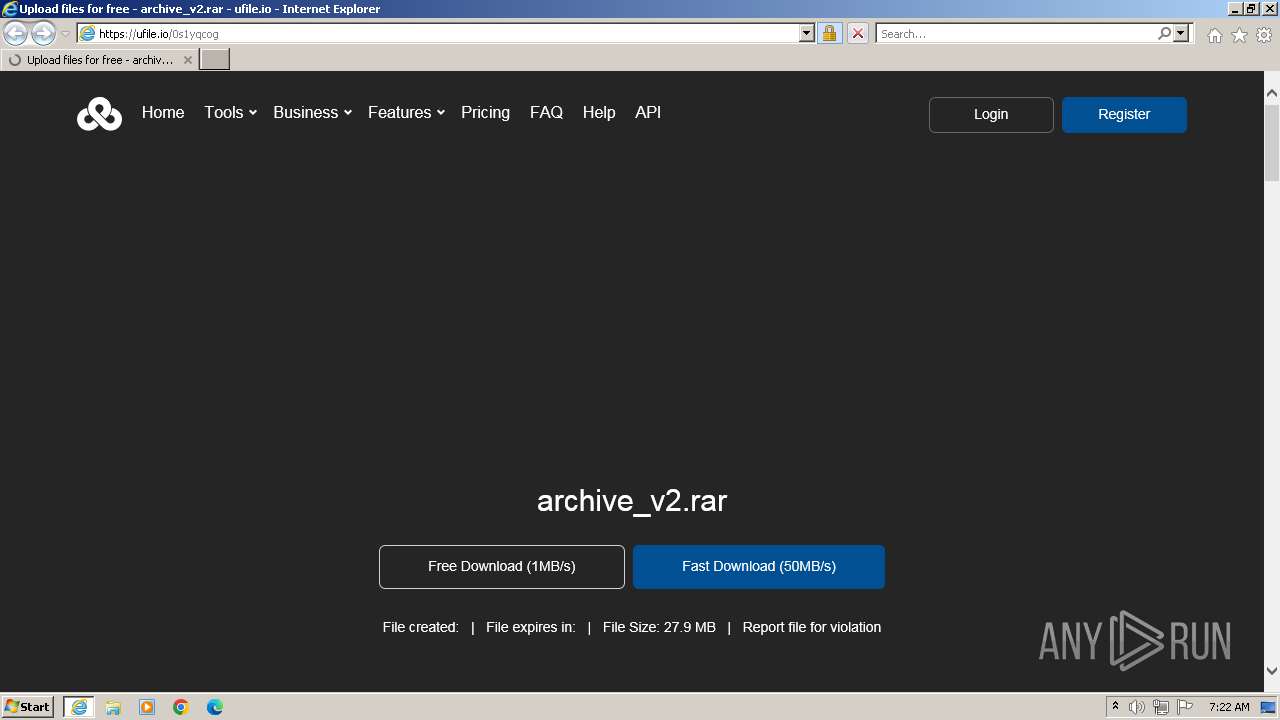
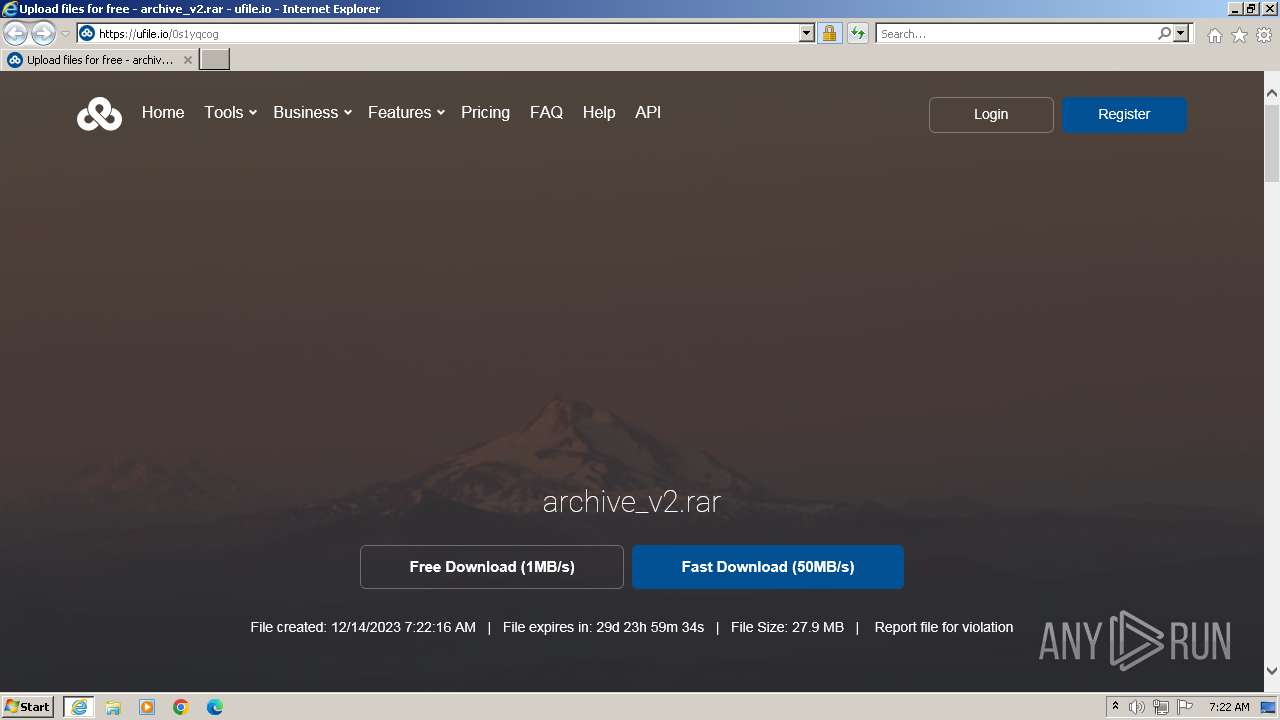
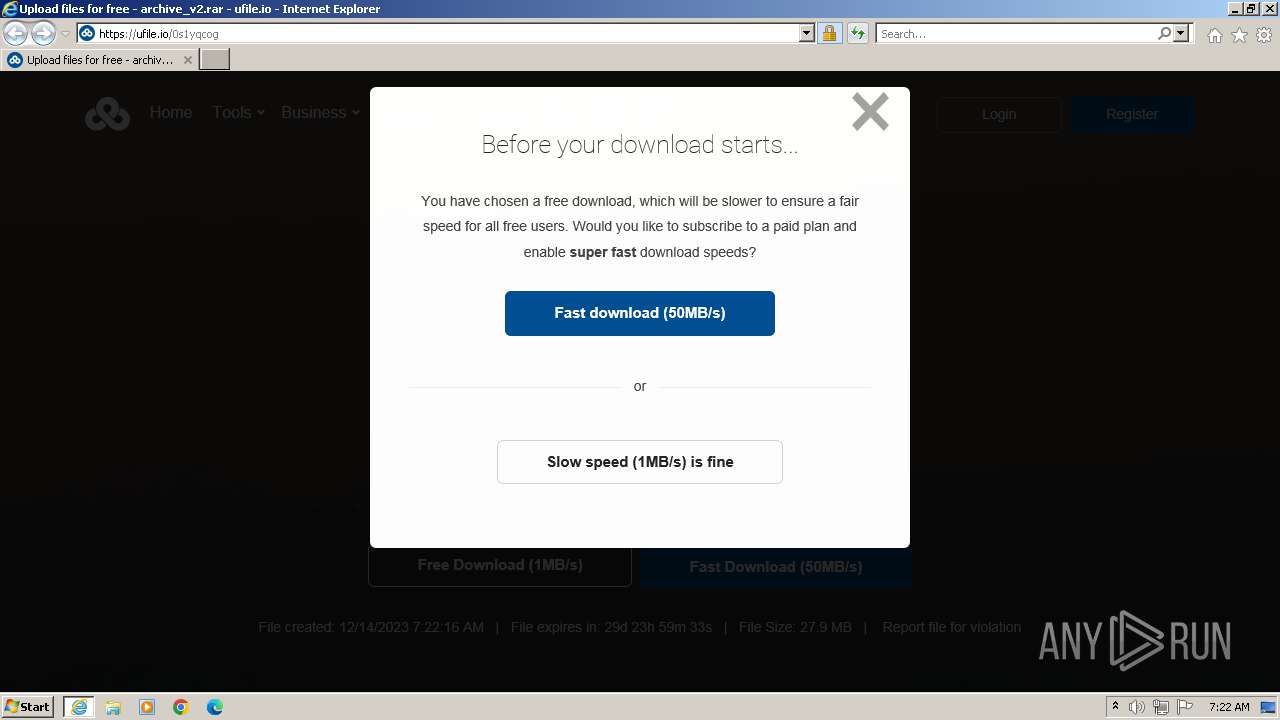
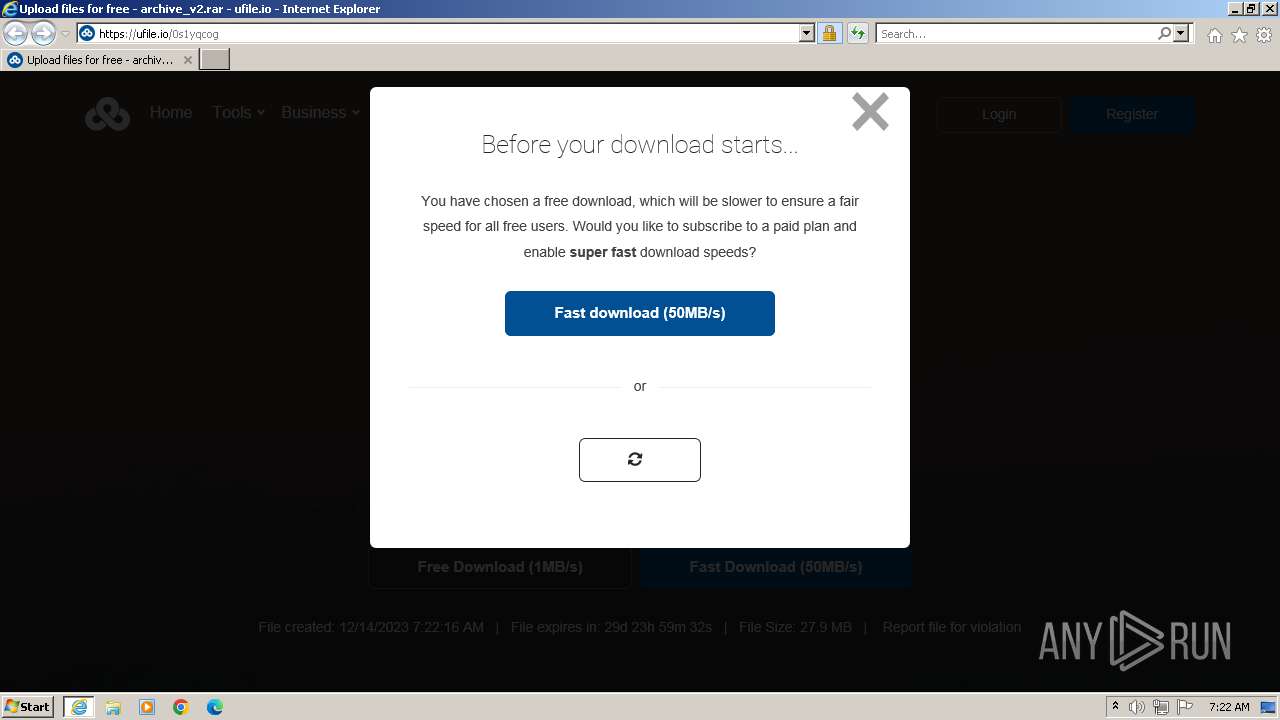
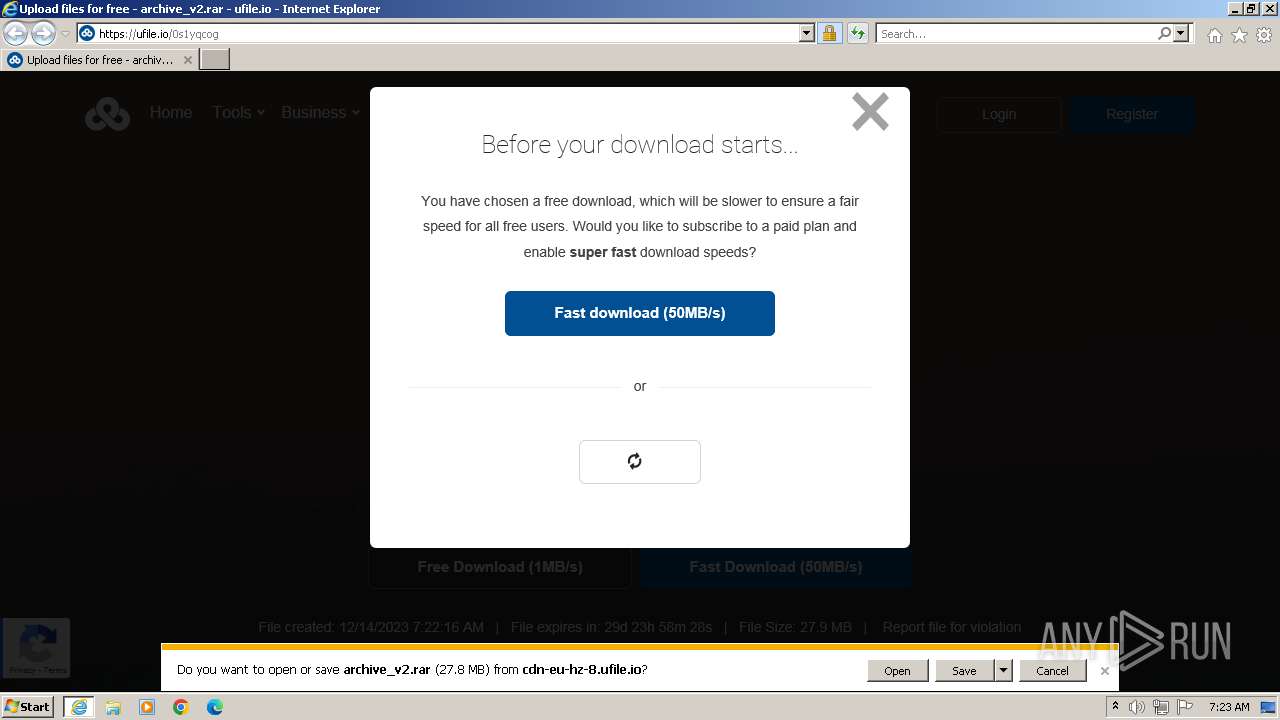
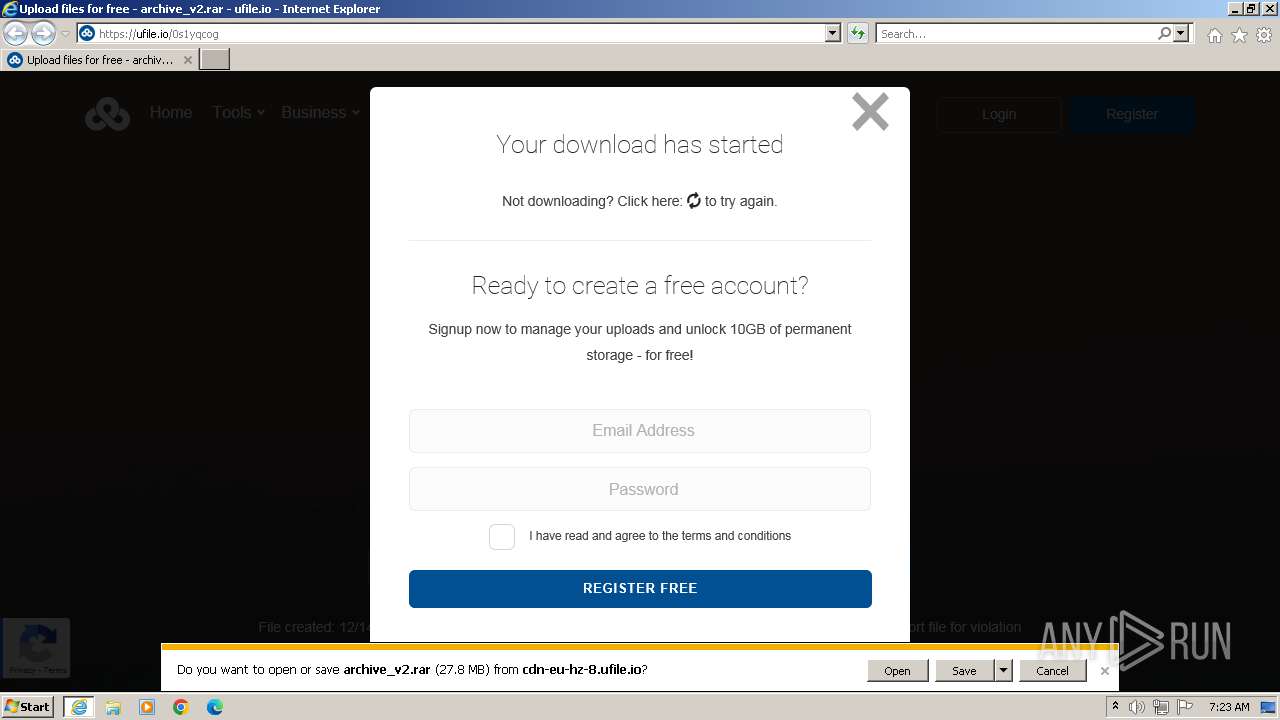
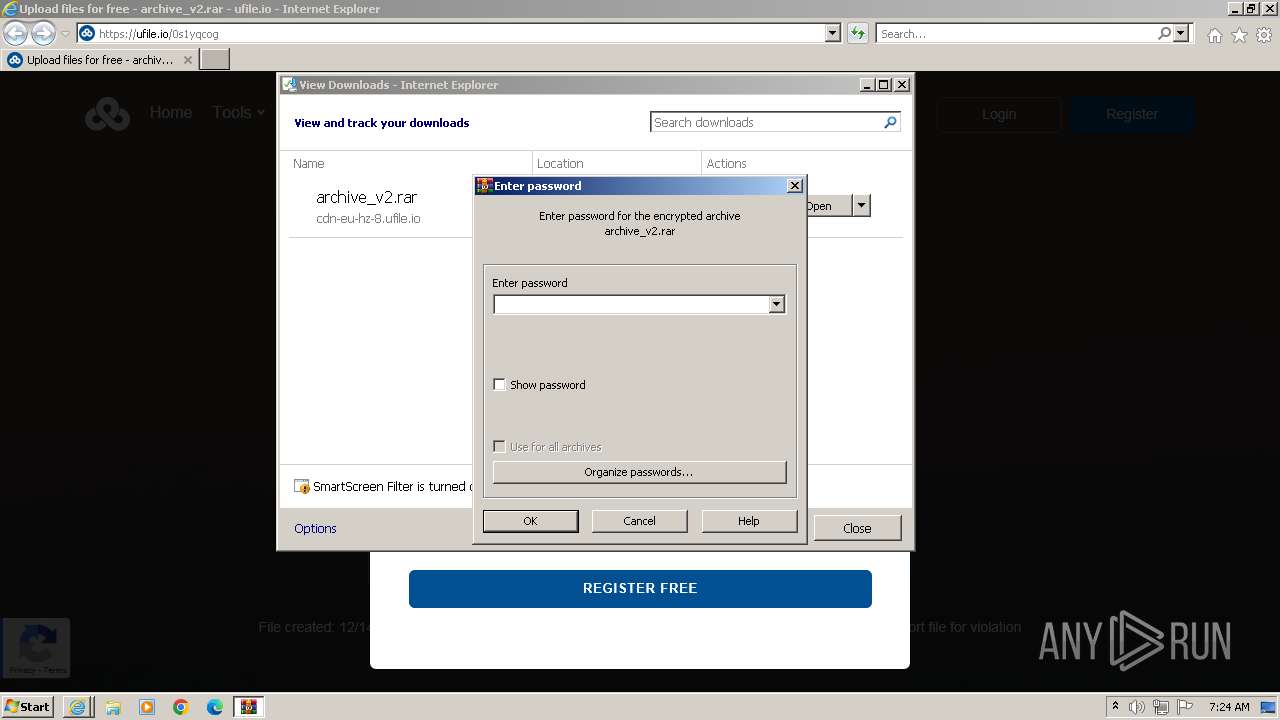
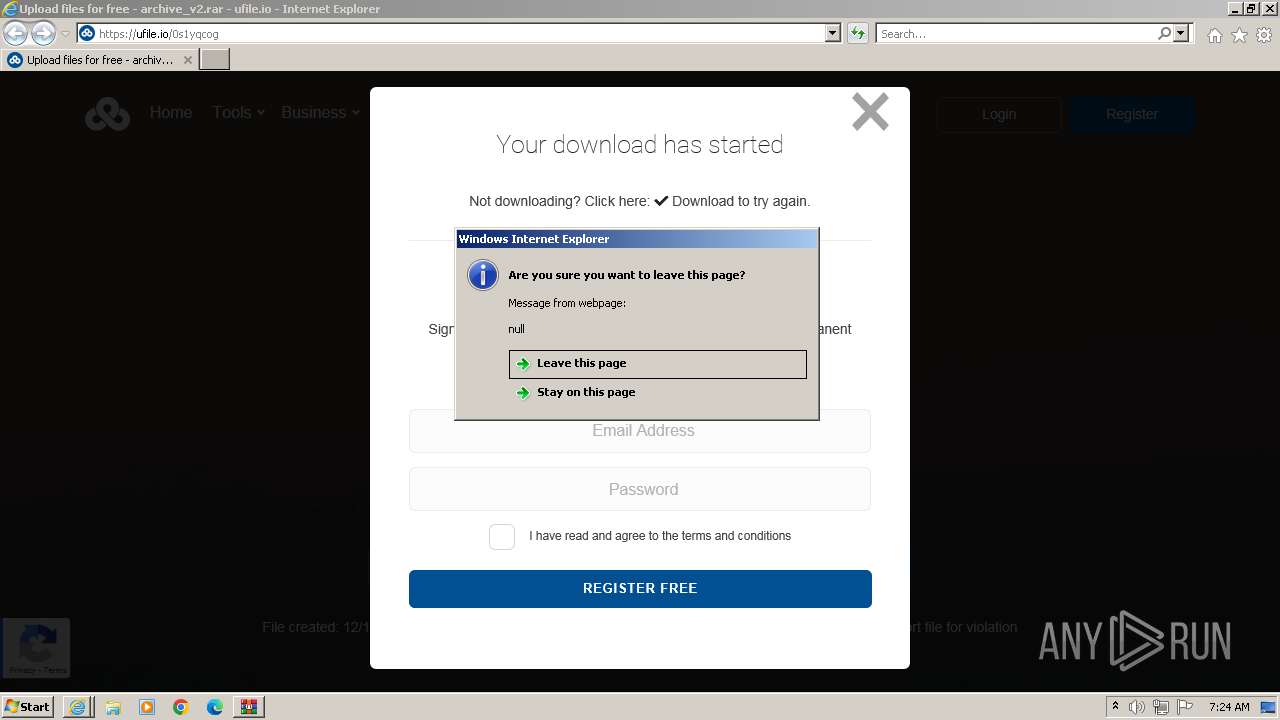
| URL: | https://ufile.io/0s1yqcog |
| Full analysis: | https://app.any.run/tasks/70d7380b-357c-4edb-a771-7894a153c693 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2023, 07:22:29 |
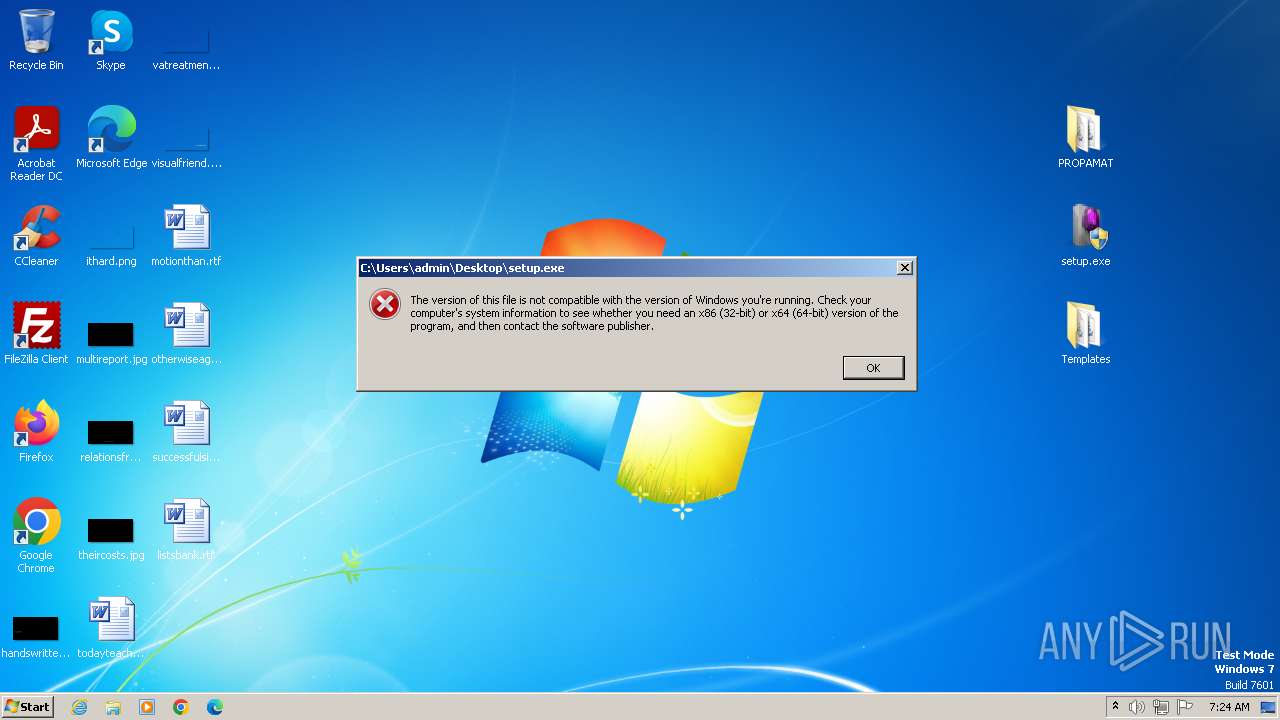
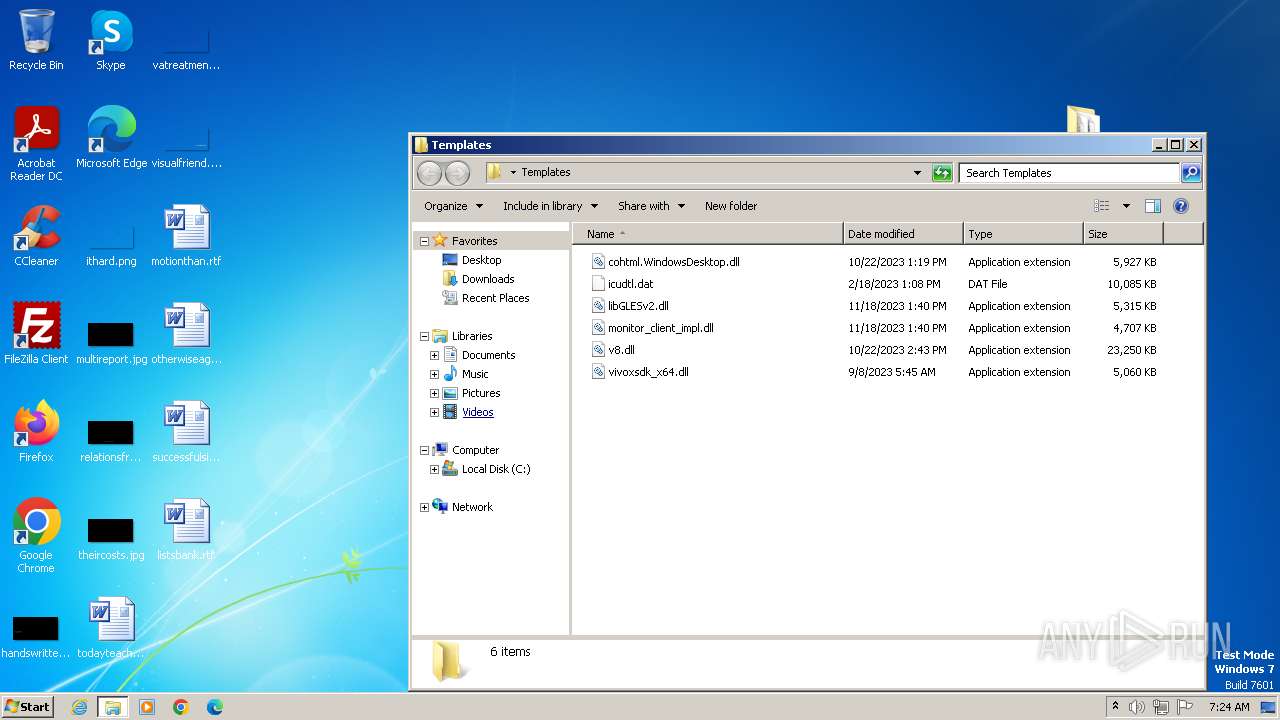
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2E5D3ED0AE497675B47D483D7BC8E0A2 |
| SHA1: | C5BCC03AC02883E2864EAC8835BCA653937EE95C |
| SHA256: | 270D9F4EC7262519241BC6B5BE3EE4D98A99248ABE79640EC4FD0DE184561C13 |
| SSDEEP: | 3:N8dJDNAn:2LDO |
MALICIOUS
No malicious indicators.SUSPICIOUS
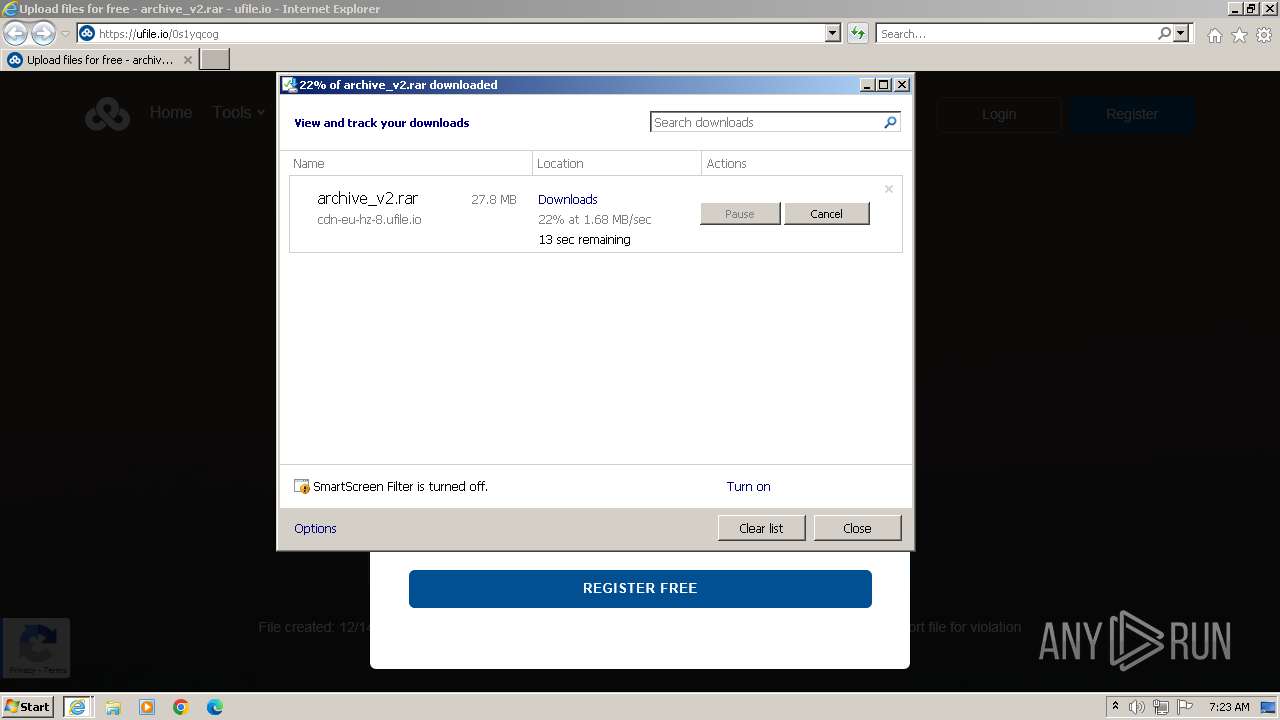
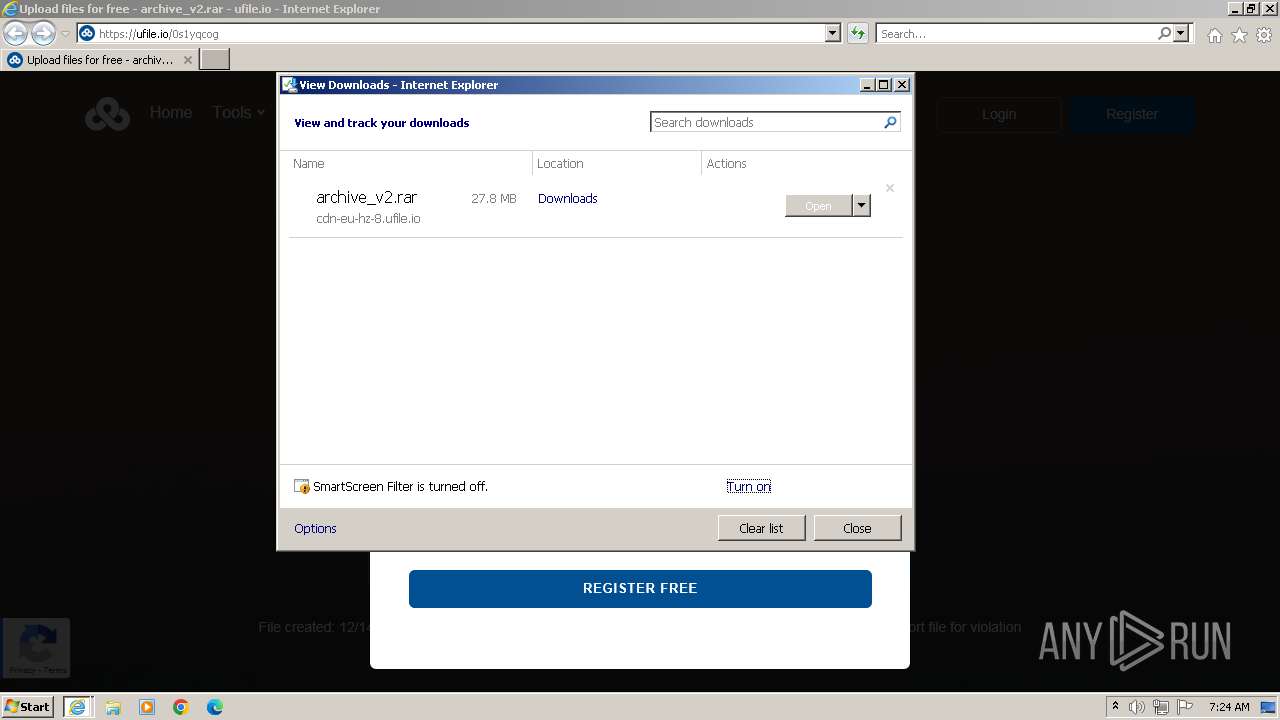
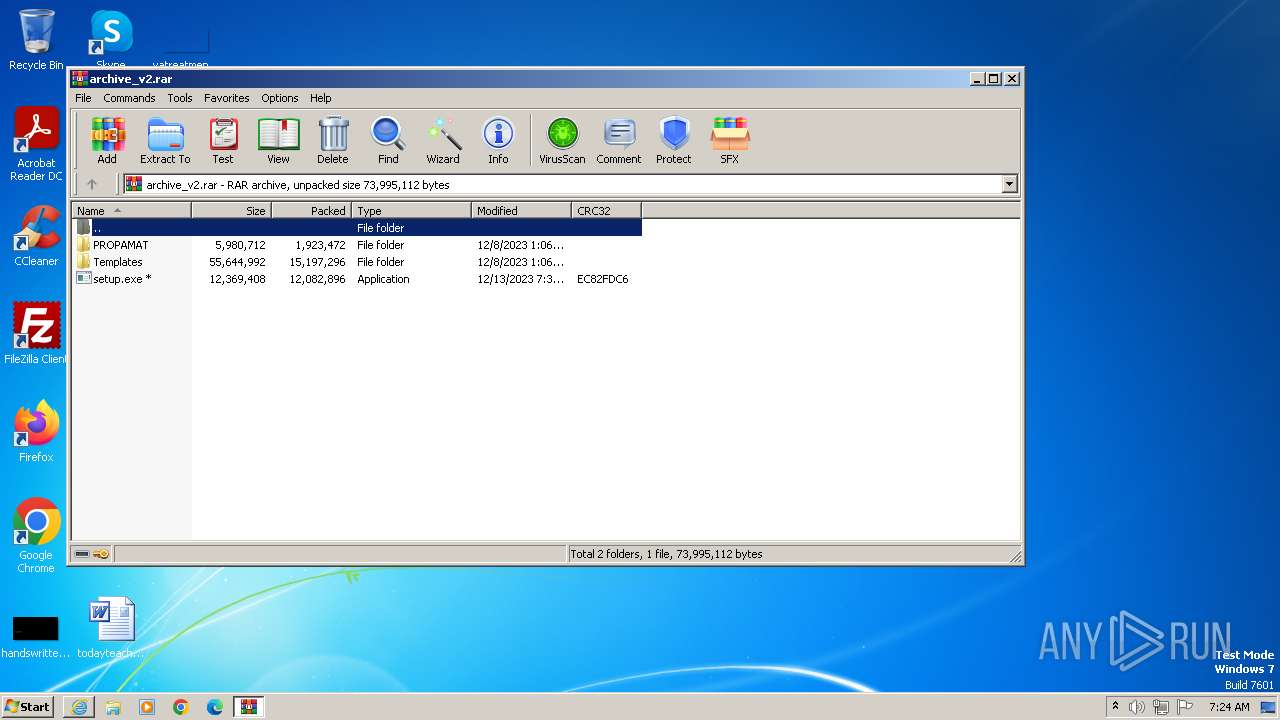
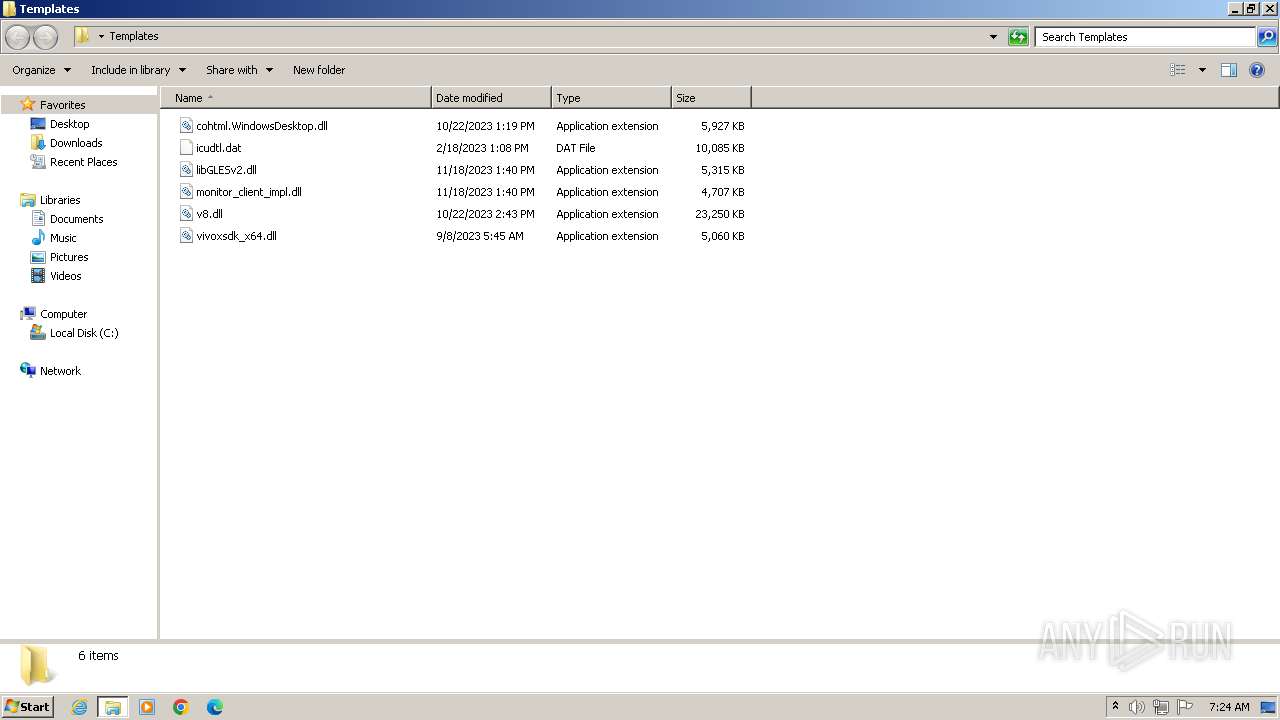
Process drops legitimate windows executable
- WinRAR.exe (PID: 3972)
INFO
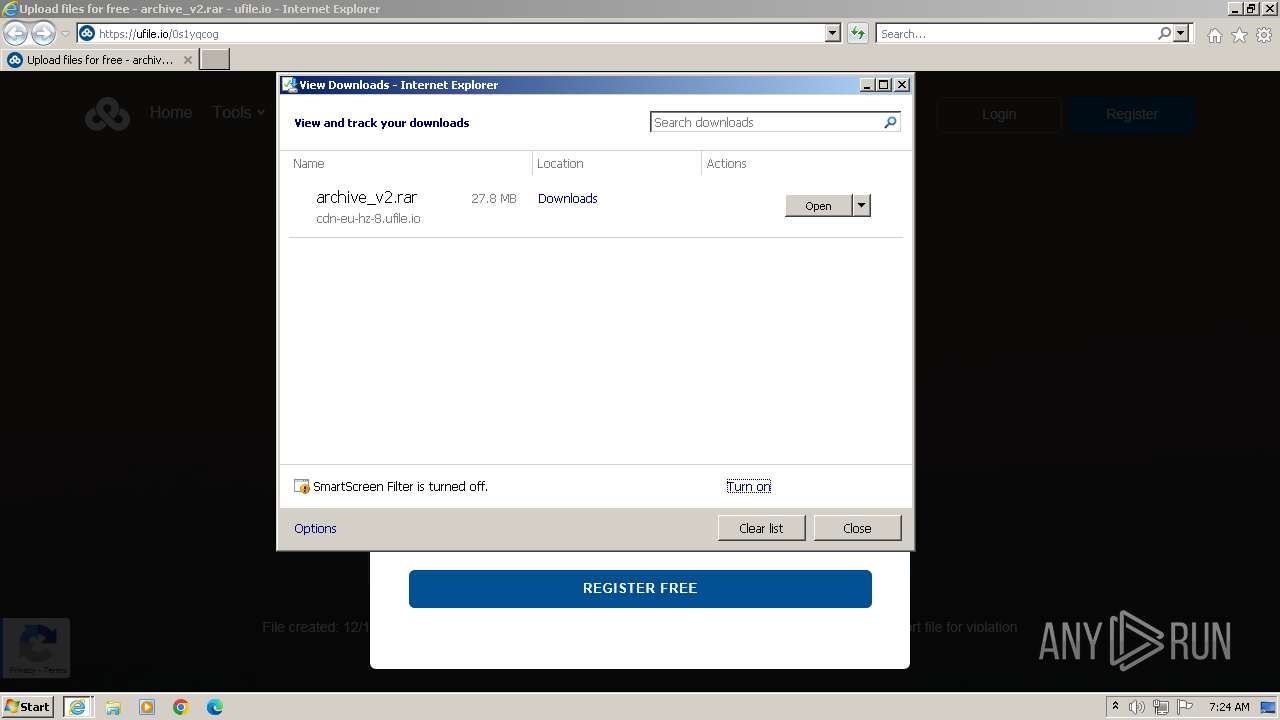
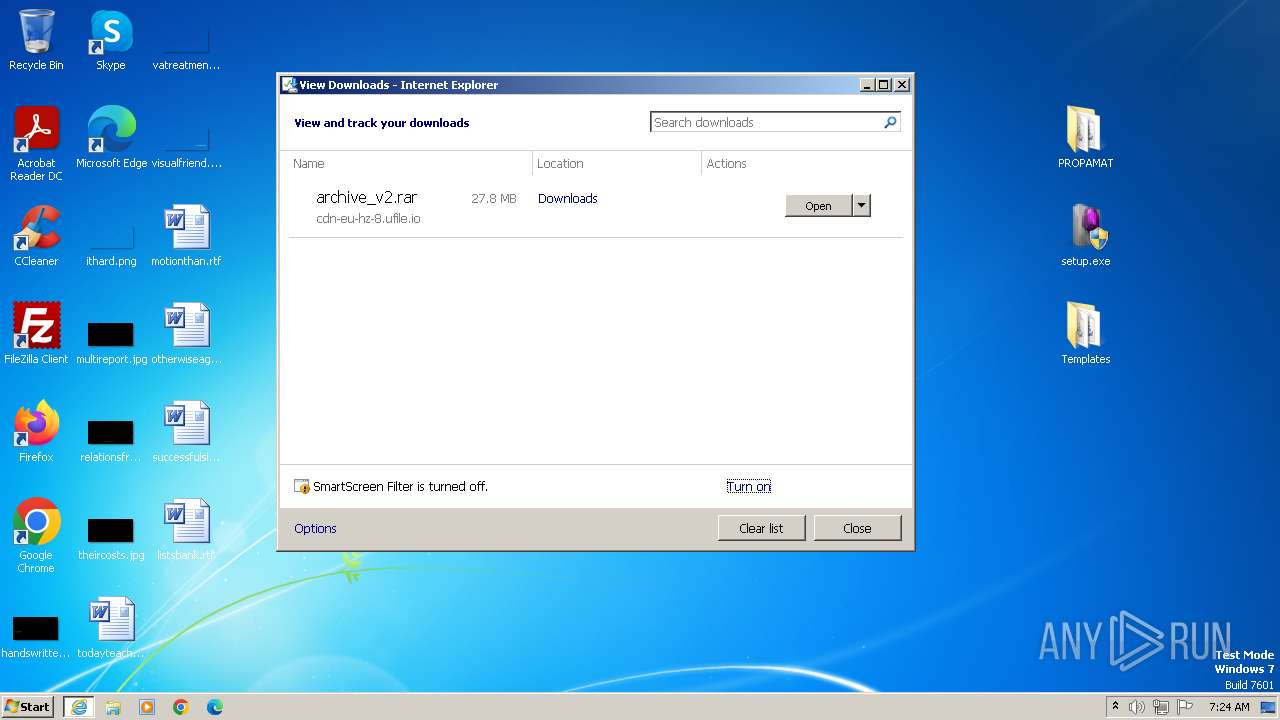
The process uses the downloaded file
- WinRAR.exe (PID: 3972)
- iexplore.exe (PID: 1864)
Manual execution by a user
- wmpnscfg.exe (PID: 3924)
Application launched itself
- iexplore.exe (PID: 1864)
Reads the computer name
- wmpnscfg.exe (PID: 3924)
Checks supported languages
- wmpnscfg.exe (PID: 3924)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ufile.io/0s1yqcog" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3924 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
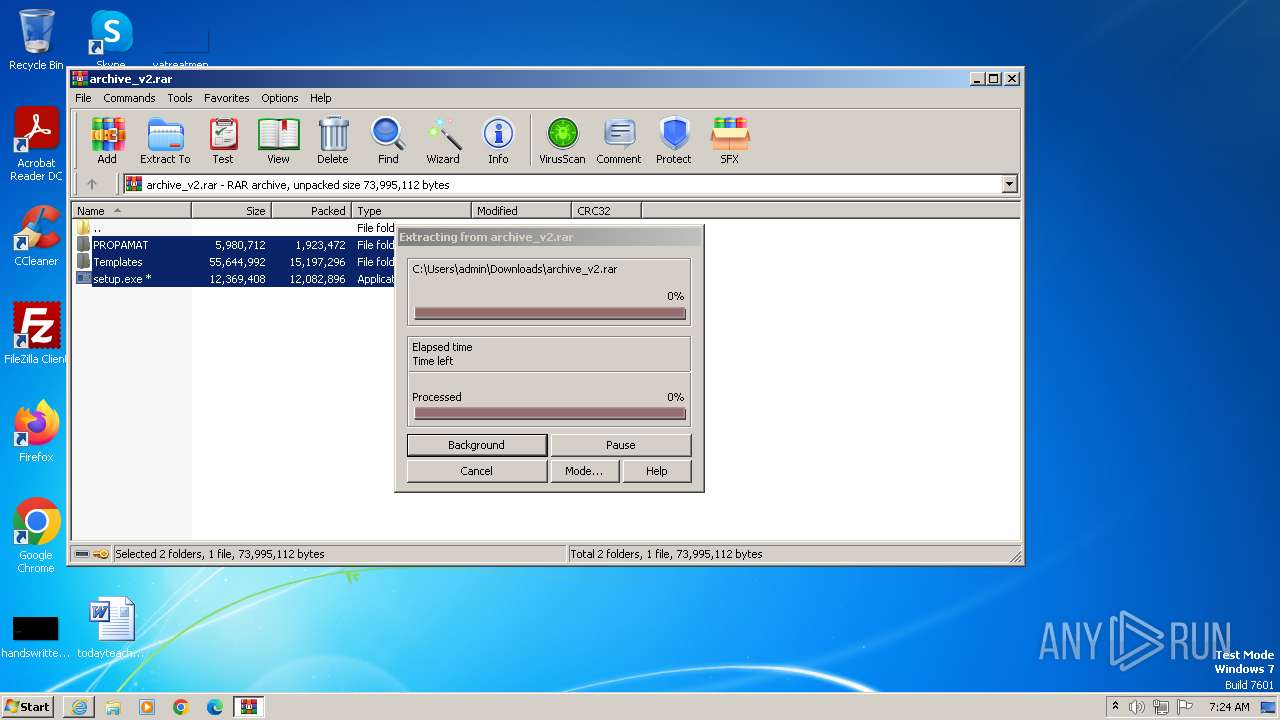
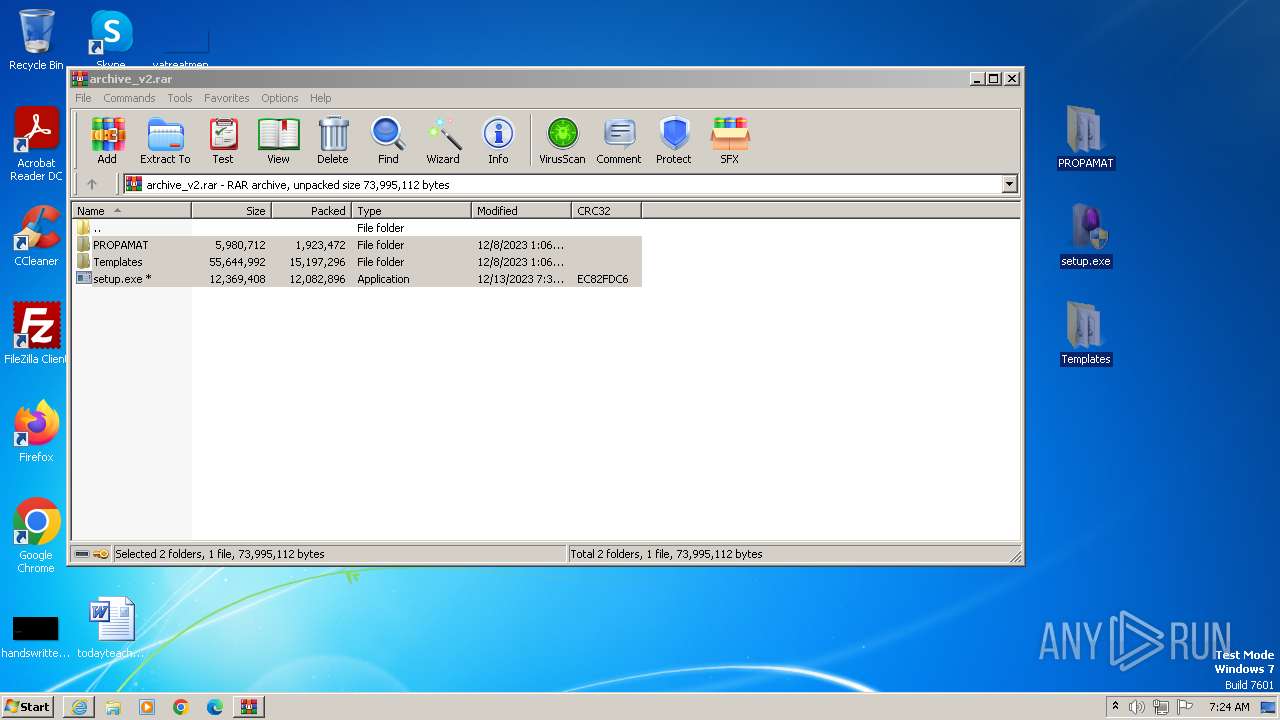
| 3972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\archive_v2.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
16 823
Read events
16 721
Write events
99
Delete events
3
Modification events
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
10
Suspicious files
56
Text files
81
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\beacon.min[1].js | text | |
MD5:DD1D068FDB5FE90B6C05A5B3940E088C | SHA256:6153D13804862B0FC1C016CF1129F34CB7C6185F2CF4BF1A3A862EECDAB50101 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:9FF1136D83FE45BC0A0134DB9D72BF06 | SHA256:BFABE6E132CB2EDF1793B27CED0AB7C0CA17525FEEAC8C1B7313534B918300A6 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\0s1yqcog[1].htm | html | |
MD5:7211A60BEA74CFD760EE373FC90042EE | SHA256:7758655D1298E0CE0821C3DF9DF983E78FB5A4A766293493877A3E9C705F8689 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:5F33C54D1567CFE59CC1789385DCFEB4 | SHA256:0A4E2DD8C0B21223834C0AAA9AFEF563AED7C7BE71D506DE1BA23CFDCCA2569D | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Z7Q8EBDT.txt | text | |
MD5:0FC97F34D7A8108B1C3D2440409AB282 | SHA256:271F09EAD8DFE6CAD95DEFC5FC042BEB68D4398B321D6483E05D18EFC3E1829D | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\v84a3a4012de94ce1a686ba8c167c359c1696973893317[1].js | text | |
MD5:DD1D068FDB5FE90B6C05A5B3940E088C | SHA256:6153D13804862B0FC1C016CF1129F34CB7C6185F2CF4BF1A3A862EECDAB50101 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EDSIN43B.txt | text | |
MD5:9A416728E5A9B1C6B9C15E20287C85D6 | SHA256:7F533EB4C13BEBF7E55803EE1FB5FC2205C63263B7EFB24C08ACAD6ABA21E18D | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:03CF09D113D869E2502A875B0B184E1C | SHA256:195B510551AF28098DEADDF20DAF43EADFE5D61D00F8656AED4AF3AFCC87C7E8 | |||
| 2136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\spacer[1].png | image | |
MD5:C791E19FDE8325467FA82B06B1BED80B | SHA256:89E344FDB98002D91C819A31ABA52D61893604CB816EBEA0C3426B5001B9D0F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
58
DNS requests
35
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2136 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8b85bbd74f4fca7d | unknown | compressed | 4.66 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2136 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 108.138.2.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.51 Kb | unknown |
2136 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | unknown | binary | 472 b | unknown |
2136 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.39 Kb | unknown |
1864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 314 b | unknown |
2136 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDEixfO34qnbCeE6N8VMp00%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2136 | iexplore.exe | 104.21.66.22:443 | ufile.io | CLOUDFLARENET | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2136 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2136 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2136 | iexplore.exe | 216.58.206.40:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2136 | iexplore.exe | 143.204.102.164:443 | d3vw4uehoh23hx.cloudfront.net | AMAZON-02 | US | unknown |
2136 | iexplore.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ufile.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.google.com |
| whitelisted |
adservice.google.com |
| whitelisted |
client.crisp.chat |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
settings.crisp.chat |
| whitelisted |
ad.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO File Sharing Service Domain in DNS Lookup (ufile .io) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
2136 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
1864 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |
1864 | iexplore.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ufile .io in TLS SNI) |