| File name: | updater.exe |
| Full analysis: | https://app.any.run/tasks/cf534aa8-45cc-4450-b2b8-93c73db3b7a2 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2020, 08:41:02 |
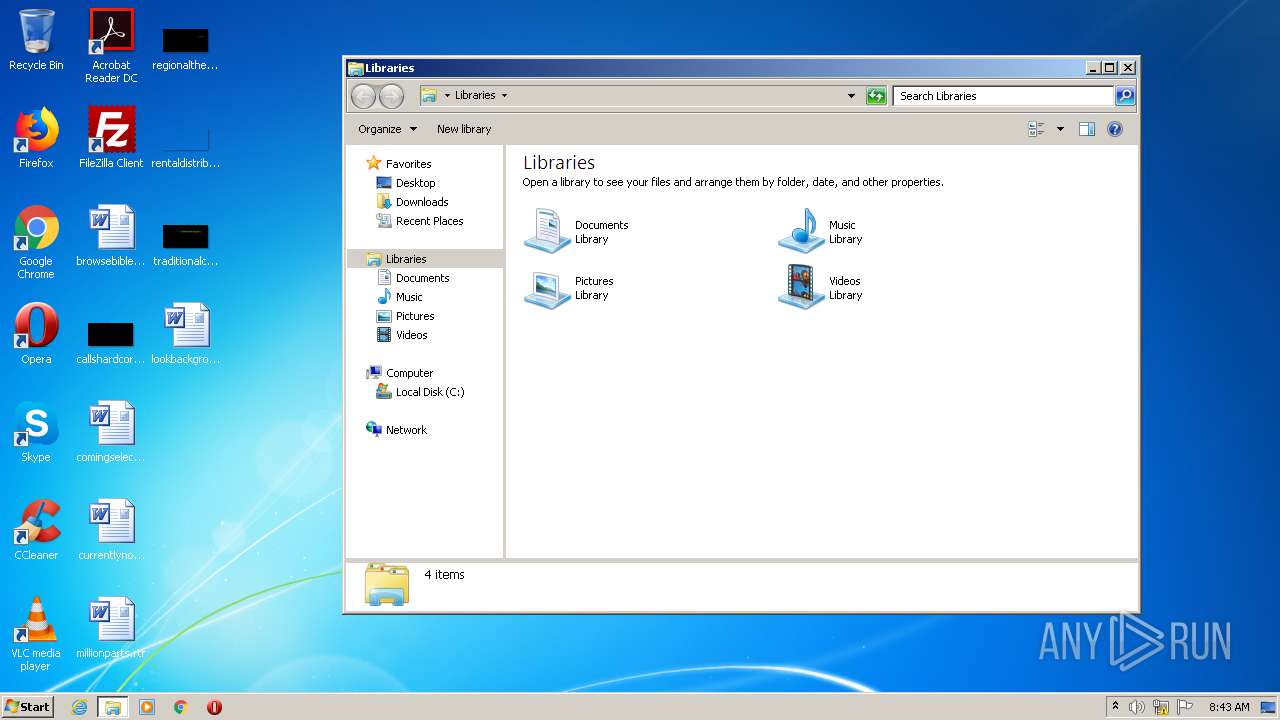
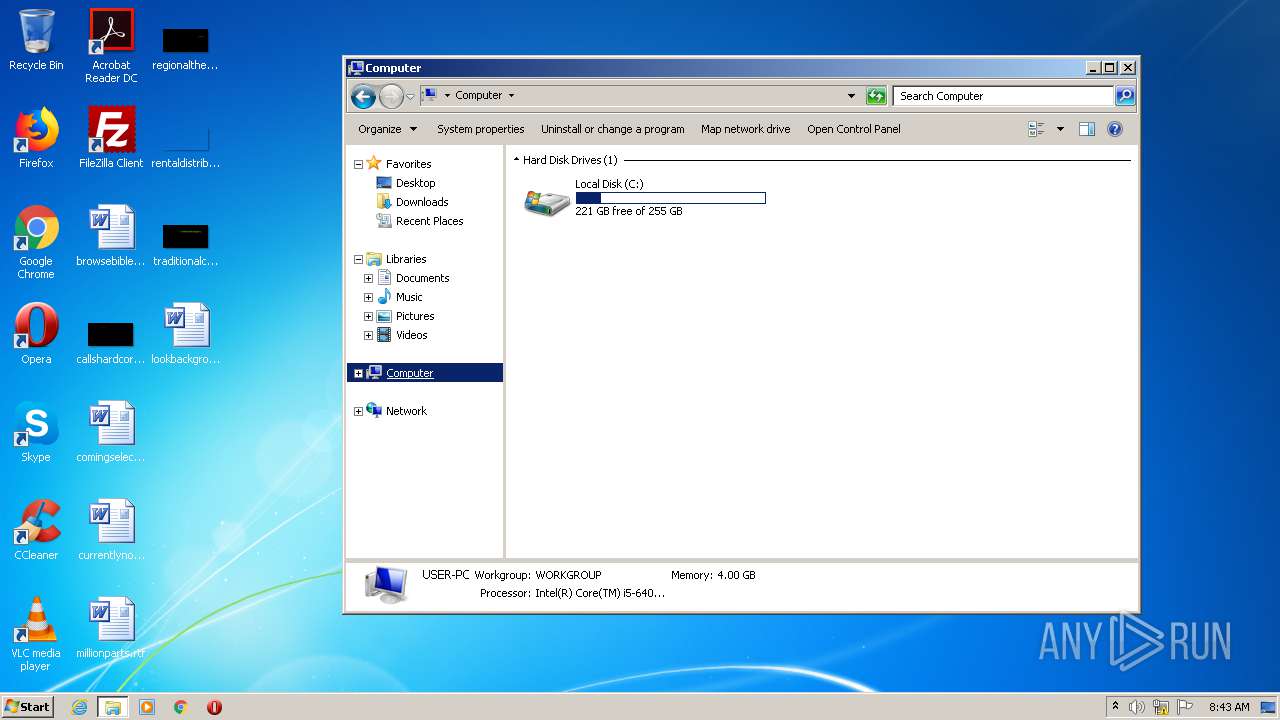
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 245234988E32E7E437F93FFD8DB15FA3 |
| SHA1: | 4CB4D13F4B7EC6D346808C265AF305685B4547F5 |
| SHA256: | 2703E453EAEBDCB801F81E3FE54CB23D7FB475B7687B1E9FCACC737D5460DCA3 |
| SSDEEP: | 3072:R4f7aZzu/qSut6rgvLZNiOQtk8eeuHZrAs8qxmIxZe+Xq:R4WY/qxLXiCeix3Xq |
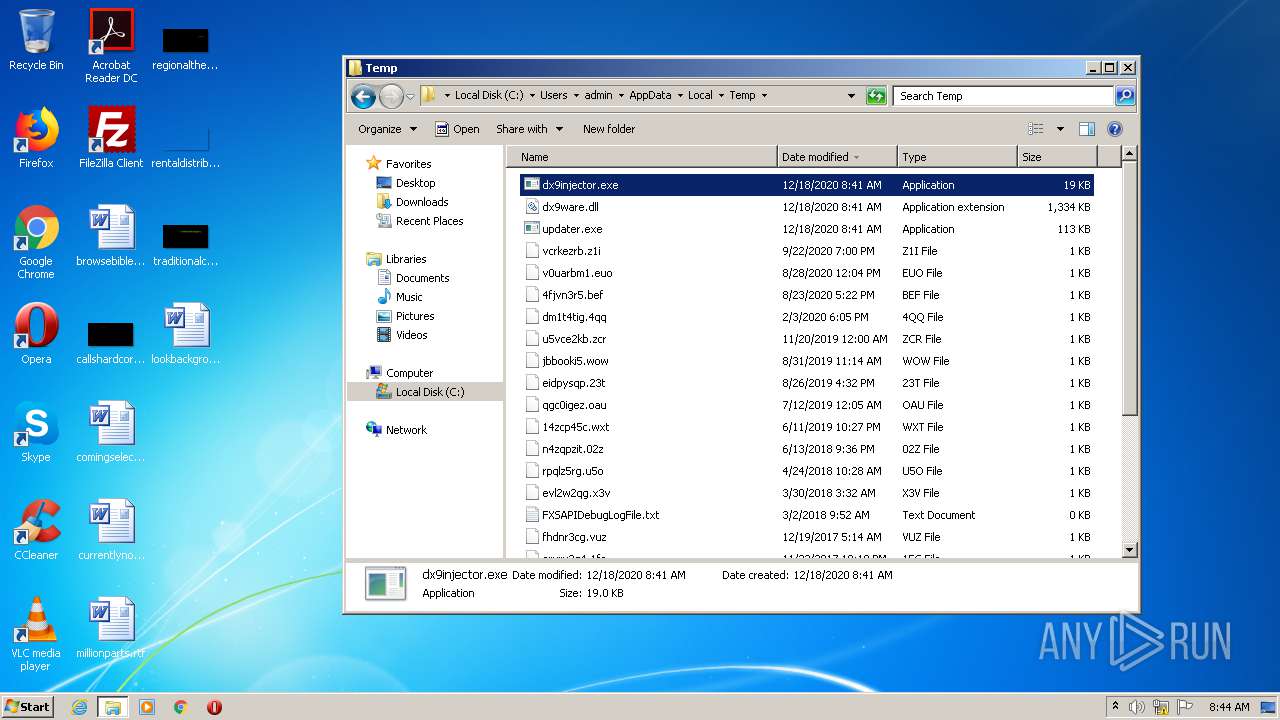
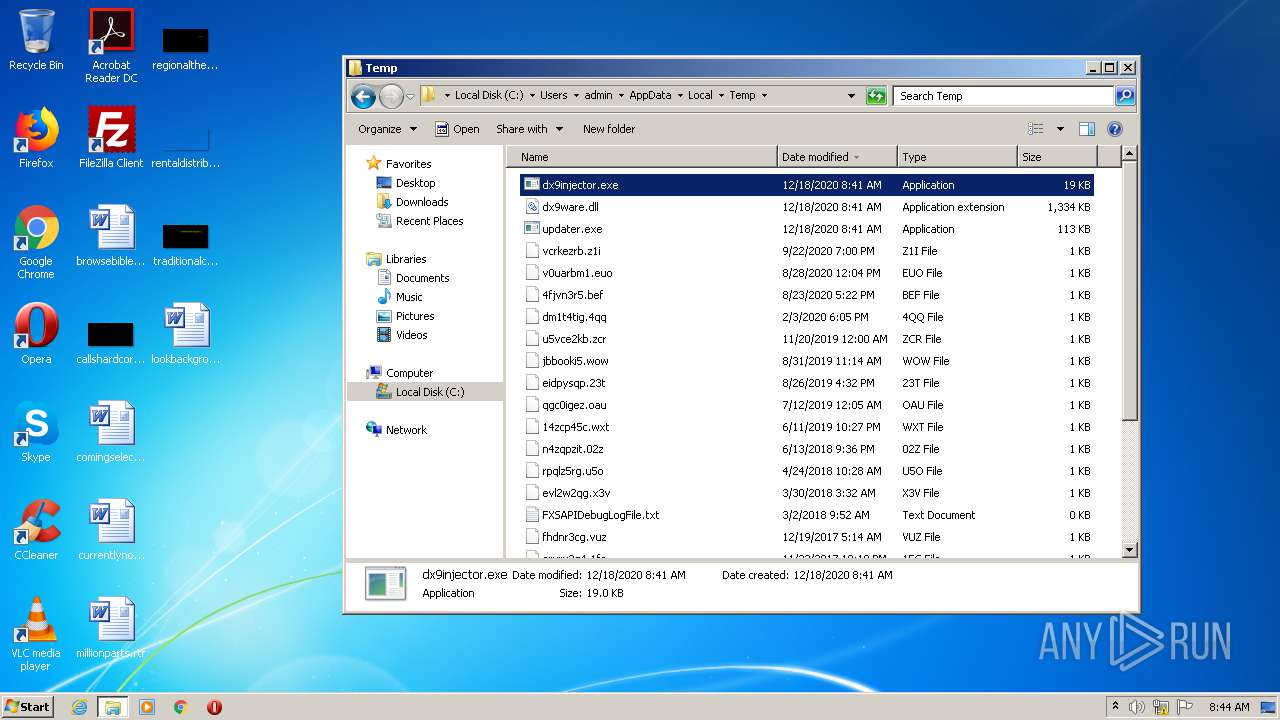
MALICIOUS
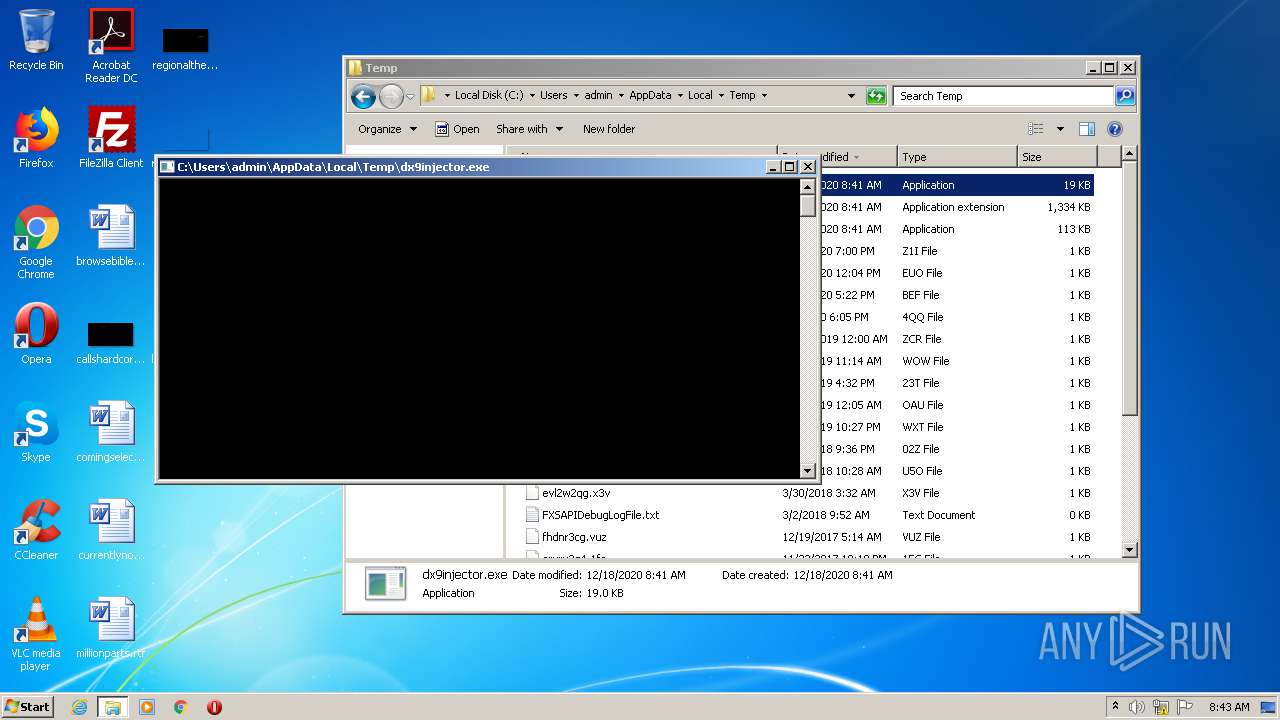
Application was dropped or rewritten from another process
- dx9injector.exe (PID: 2416)
SUSPICIOUS
Creates files in the user directory
- updater.exe (PID: 1796)
Drops a file with a compile date too recent
- updater.exe (PID: 1796)
Drops a file that was compiled in debug mode
- updater.exe (PID: 1796)
Executable content was dropped or overwritten
- updater.exe (PID: 1796)
INFO
Manual execution by user
- explorer.exe (PID: 3616)
- dx9injector.exe (PID: 2416)
- explorer.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:31 13:23:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 77824 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x273f |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 31-Jul-2020 11:23:15 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Jul-2020 11:23:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012E8E | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62307 |
.rdata | 0x00014000 | 0x00006E10 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16044 |
.data | 0x0001B000 | 0x000013A4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.4311 |
.rsrc | 0x0001D000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71006 |
.reloc | 0x0001E000 | 0x000010E4 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.35143 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
USER32.dll |
WININET.dll |
urlmon.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
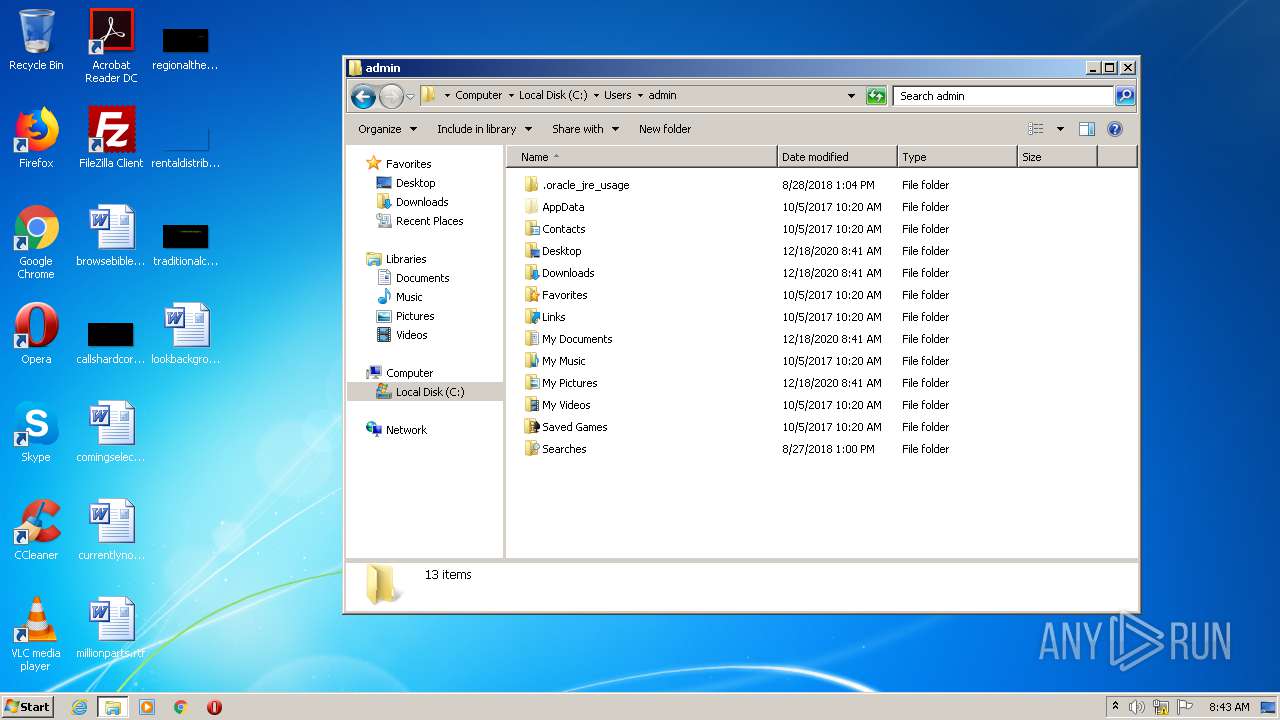
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
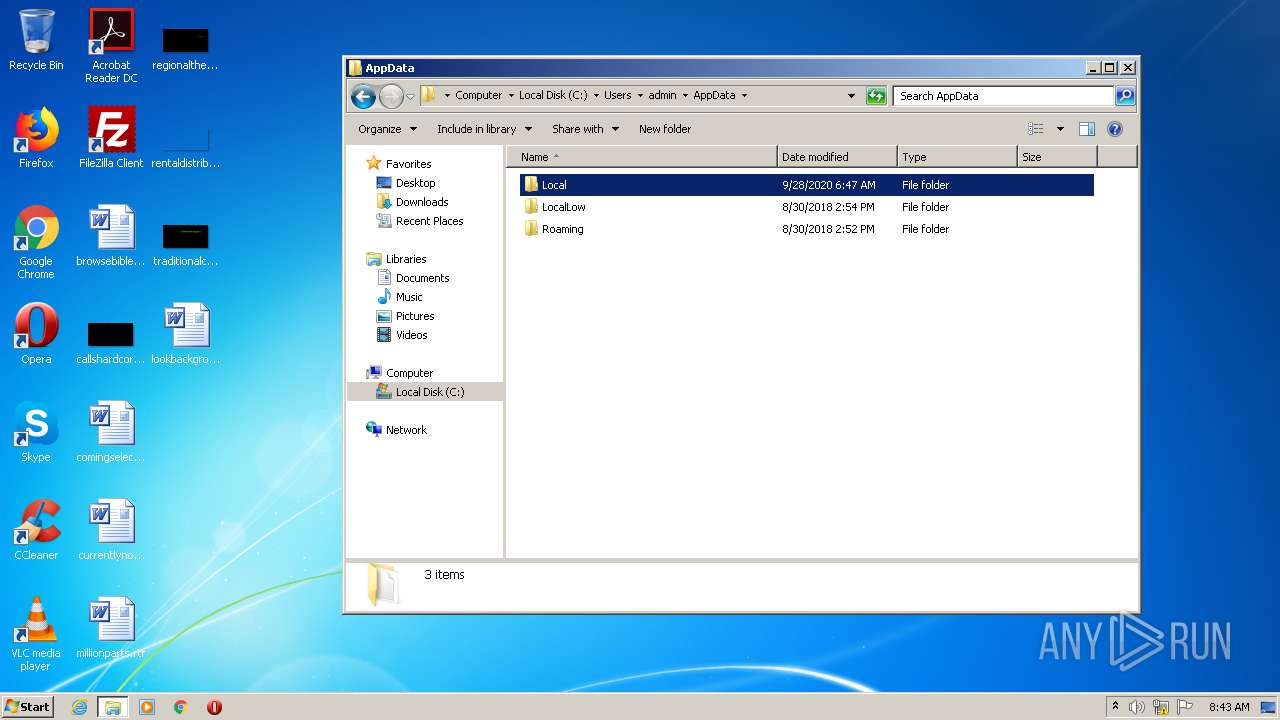
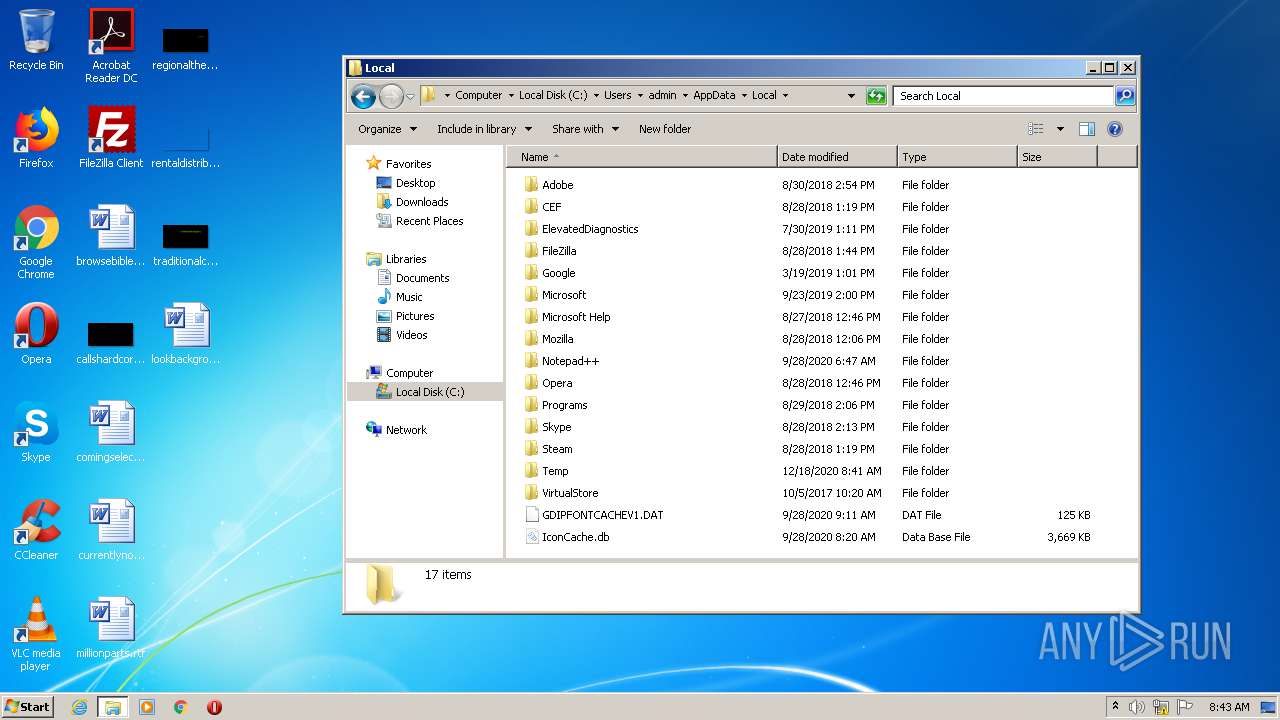
| 1796 | "C:\Users\admin\AppData\Local\Temp\updater.exe" | C:\Users\admin\AppData\Local\Temp\updater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\dx9injector.exe" | C:\Users\admin\AppData\Local\Temp\dx9injector.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3616 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
129
Read events
101
Write events
28
Delete events
0
Modification events
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1796) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2416) dx9injector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2416) dx9injector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
4
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
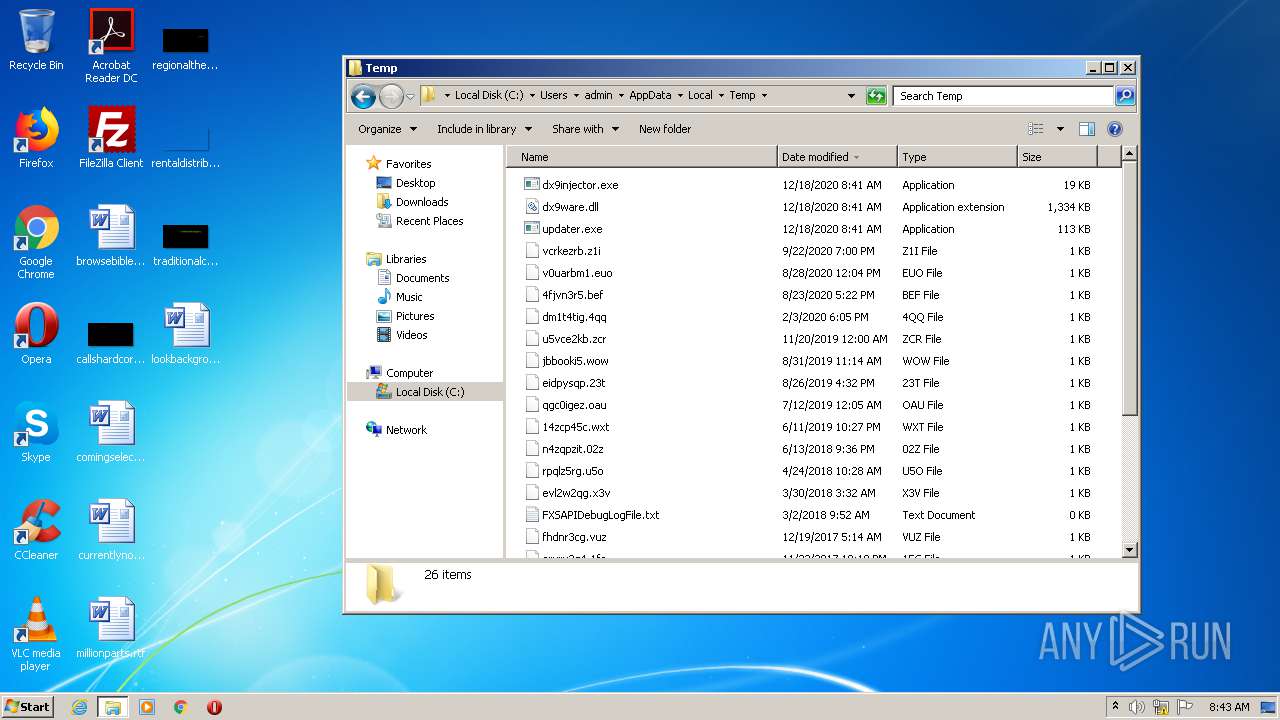
| 1796 | updater.exe | C:\Users\admin\AppData\Local\Temp\Cab4F33.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | updater.exe | C:\Users\admin\AppData\Local\Temp\Tar4F34.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | updater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:BA3600DA9CEF1BD31E4E808374B8CB17 | SHA256:8F30A3F974EF0D3EEAE4739C0AAFA7EDB5050C54D86CD0B547EAF2803C7F0910 | |||
| 1796 | updater.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\test[1].png | image | |
MD5:9BC3FD972CA4B7E34A3E191C6F0DB5AF | SHA256:CA1C42C67EEA8A89C9BA3C4F5AA08937B6BC8BBBC9FB703F49E631D6BC949D99 | |||
| 1796 | updater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:BFCA3A681EAD83ADB57AD49FA63D58CB | SHA256:432DCD03CA50FF53AEAD9193783330BB92DB3A59A26D12B9FB510B935C889AA2 | |||
| 1796 | updater.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\UHEGW1AF.txt | text | |
MD5:35986BE750859829F47985738770E4A5 | SHA256:CD8395498987EF1B6651385608A2418CE8221C4D5694AD22F6B2642AC52545EB | |||
| 1796 | updater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_BDDB570BA71C5B8B010B63EEA41AFD4C | der | |
MD5:4818F697B90D43997762CA03CB43EF83 | SHA256:6D4686A064CC958B49D132AD3C17AEFE6ECA252C0B8CA6A513DF58280506E69F | |||
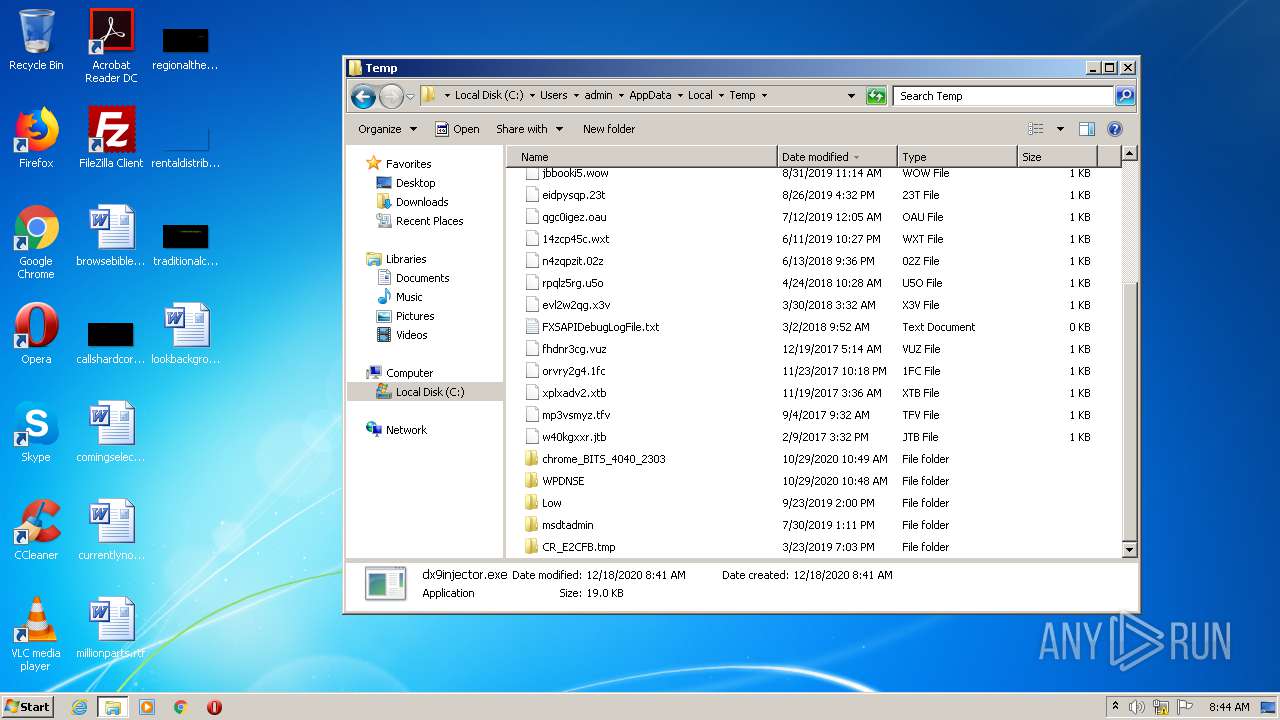
| 1796 | updater.exe | C:\Users\admin\AppData\Local\Temp\dx9injector.exe | executable | |
MD5:CC4CFF565FCF4169350E18EA2EAB4A5F | SHA256:880A4F16713ABF9577E285DCA0F242DB2DE8E62477B5C8867A5A67BDEB09BD2E | |||
| 1796 | updater.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\version[1] | text | |
MD5:5B048EF4782AFE2BE400E756C8C87F3E | SHA256:97598D3EF2FCDB14F8F06ED09EBDD05EB9117796507B2DFF089983B68710F052 | |||
| 1796 | updater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_BDDB570BA71C5B8B010B63EEA41AFD4C | binary | |
MD5:8DCE5D01D3C504B95FB603DB1BB96180 | SHA256:0AB519E3A4F98B9C85805E2113B1E383D7B5EEF743880554A1BA19AC45F4B869 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | updater.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2416 | dx9injector.exe | GET | 304 | 52.216.132.93:80 | http://setup.roblox.com/version | US | — | — | shared |
1796 | updater.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA9e8IhLKa5LWF8EvLXEFaU%3D | US | der | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | updater.exe | 104.28.4.92:443 | cultofintellect.com | Cloudflare Inc | US | shared |
1796 | updater.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1796 | updater.exe | 52.217.14.46:80 | setup.roblox.com | Amazon.com, Inc. | US | suspicious |
2416 | dx9injector.exe | 52.216.132.93:80 | setup.roblox.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cultofintellect.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
setup.roblox.com |
| shared |
Threats
2 ETPRO signatures available at the full report