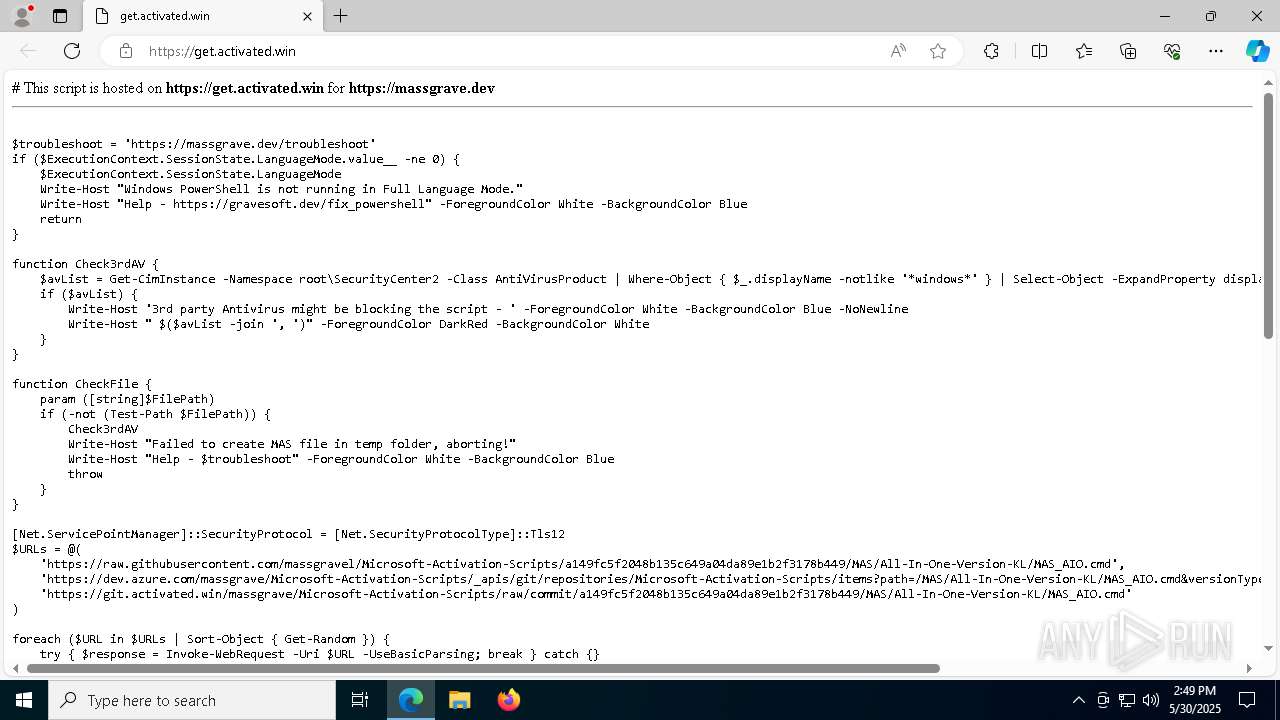
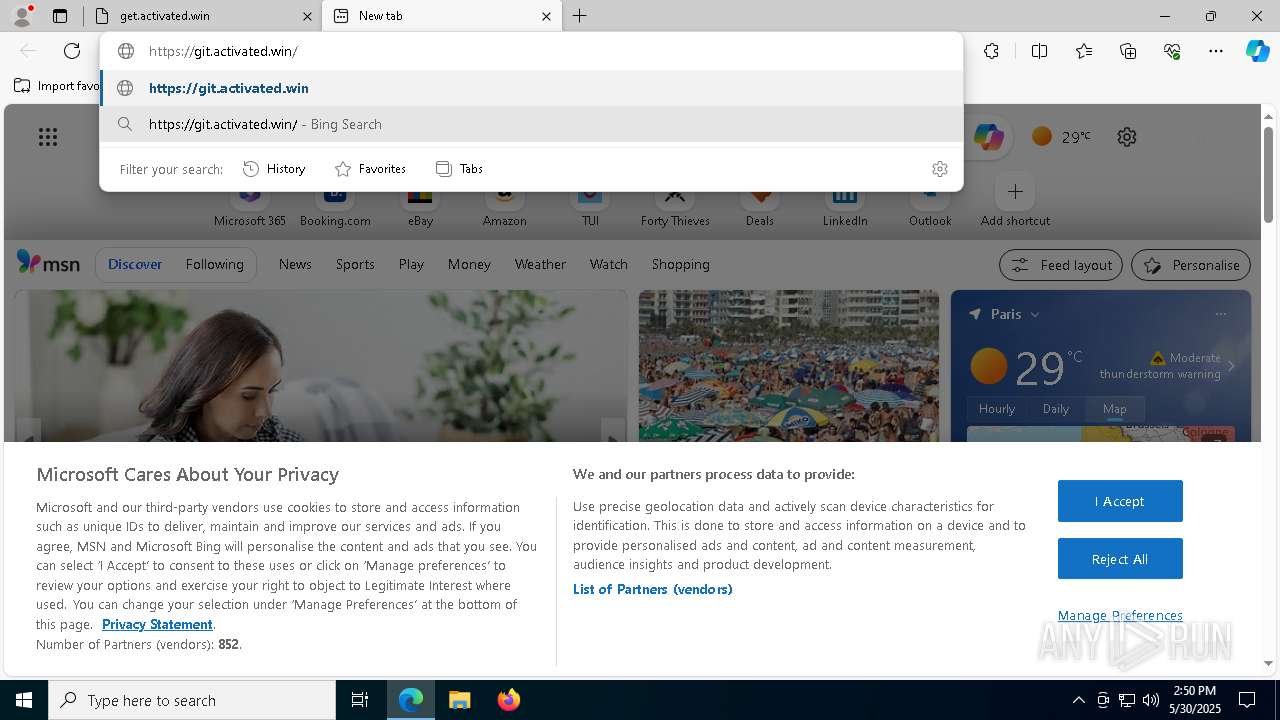
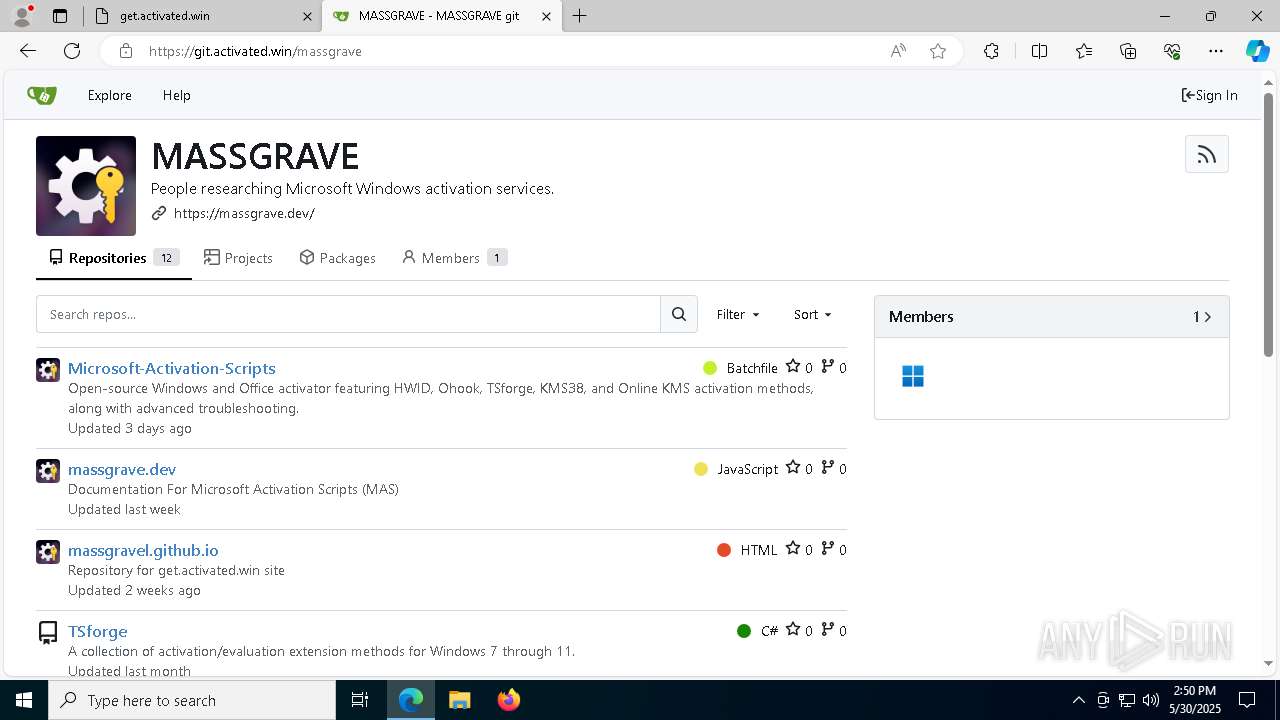
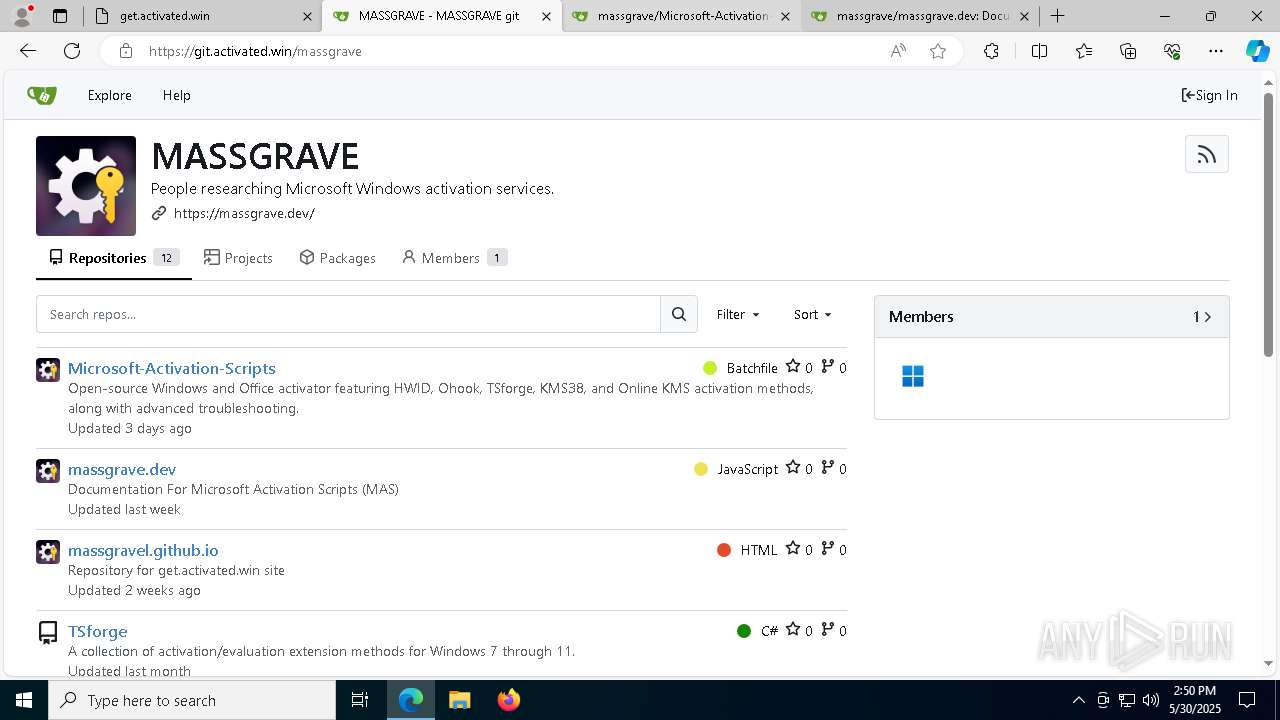
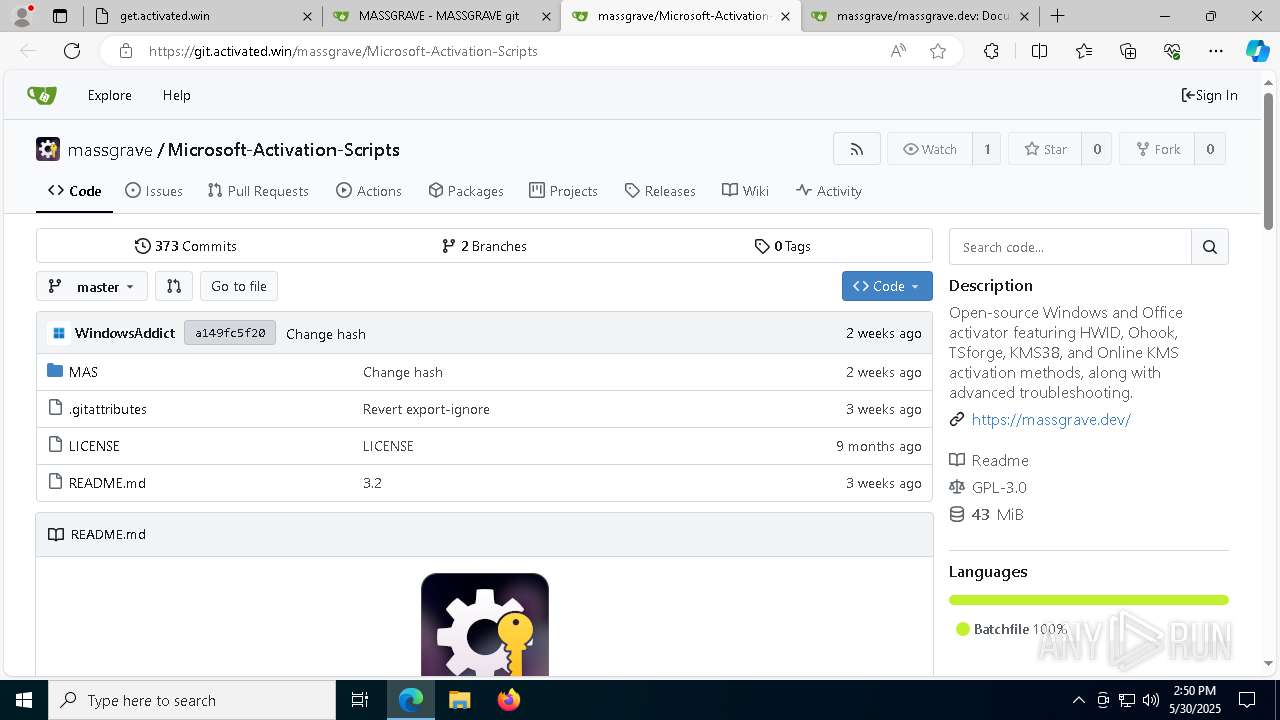
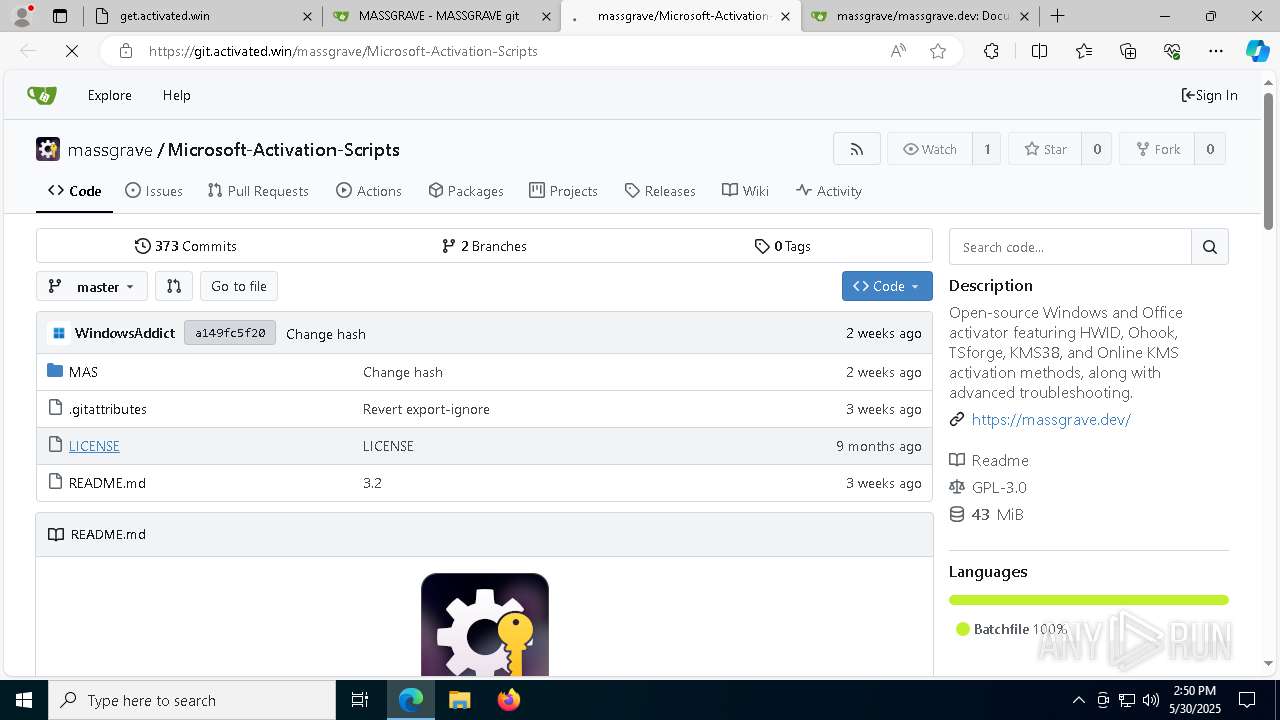
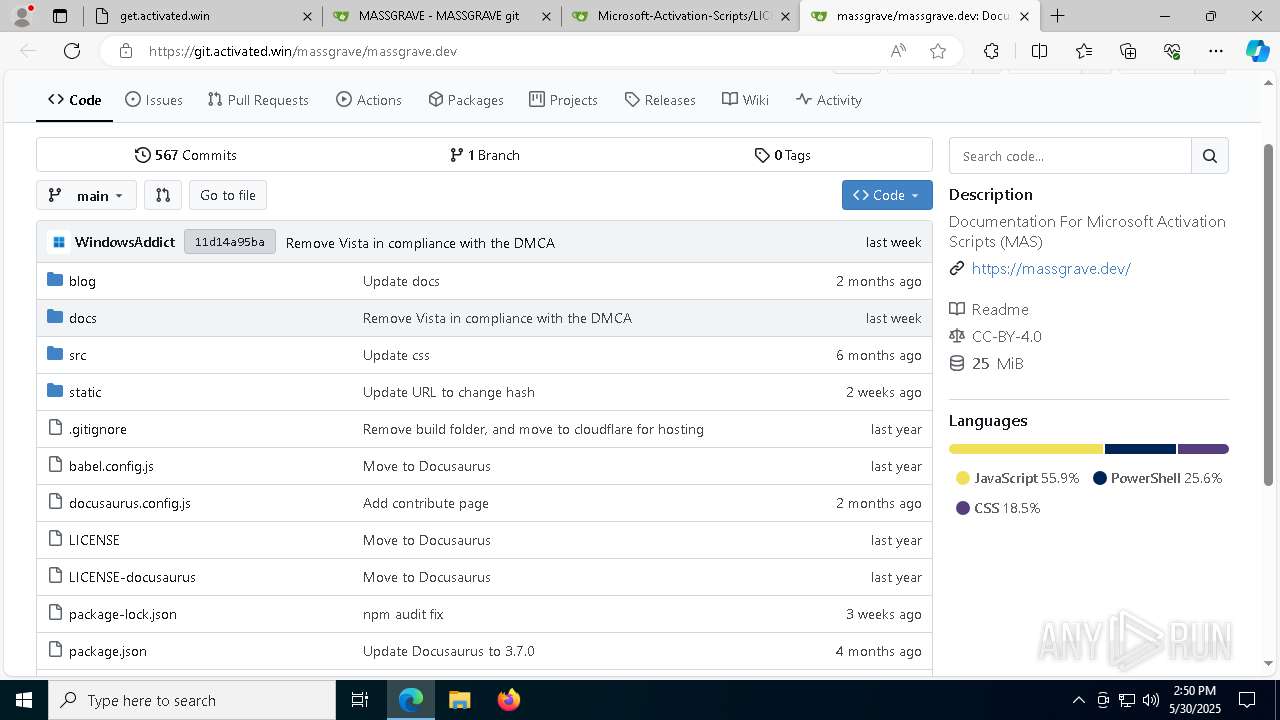
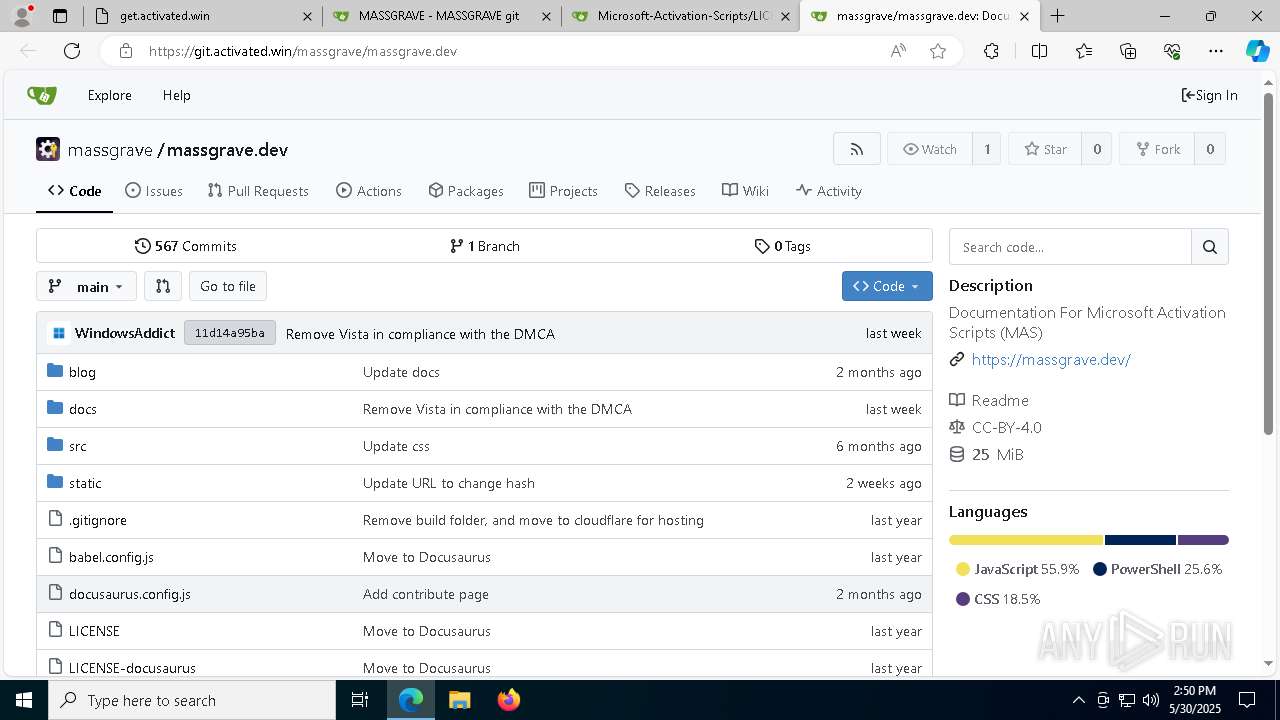
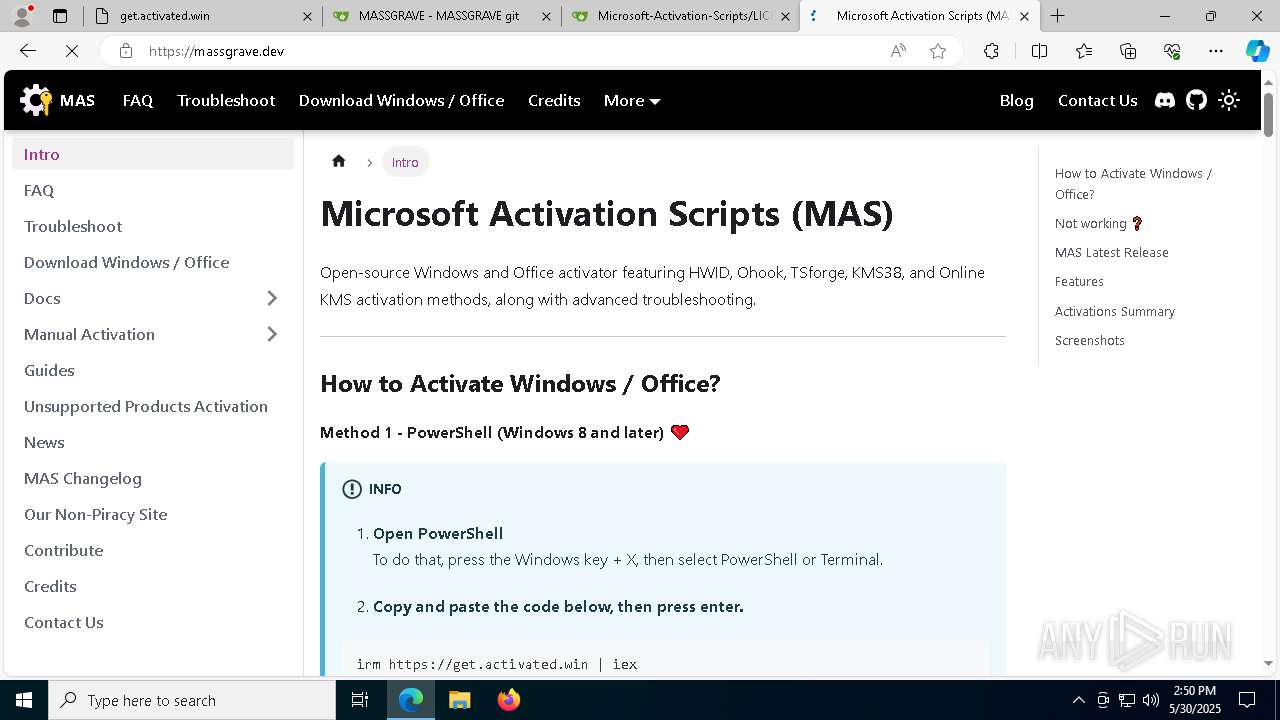
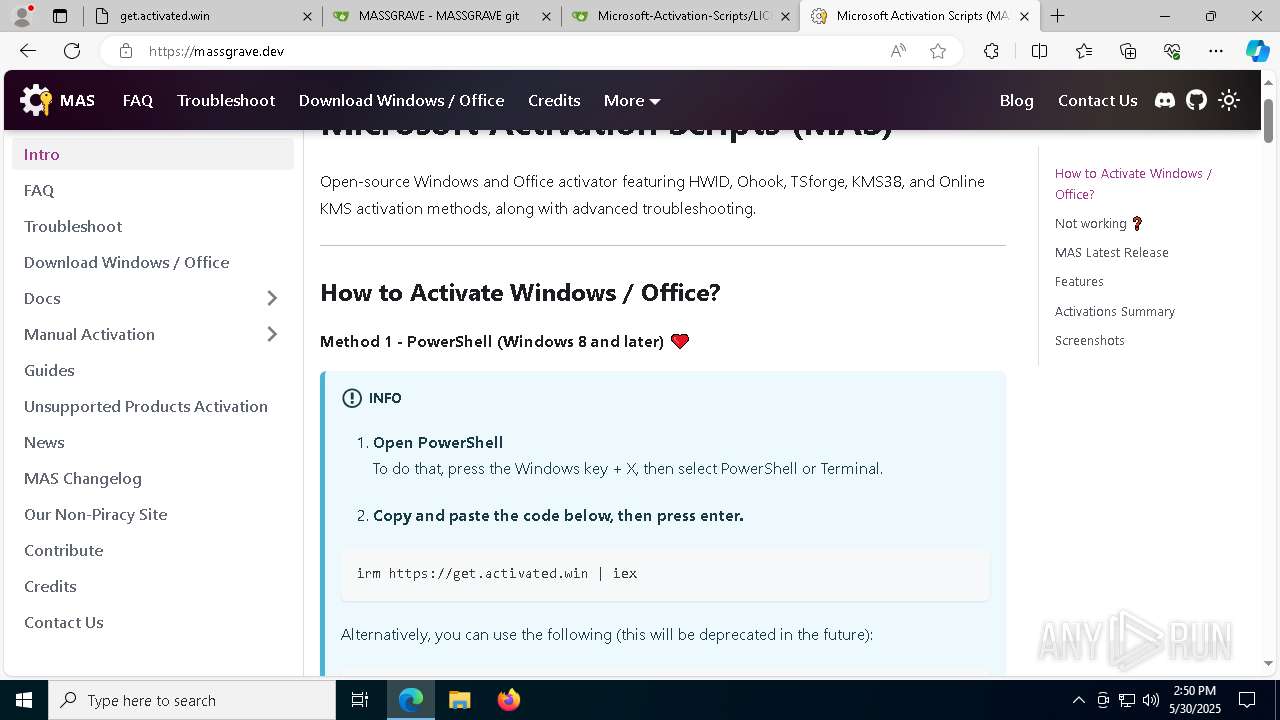
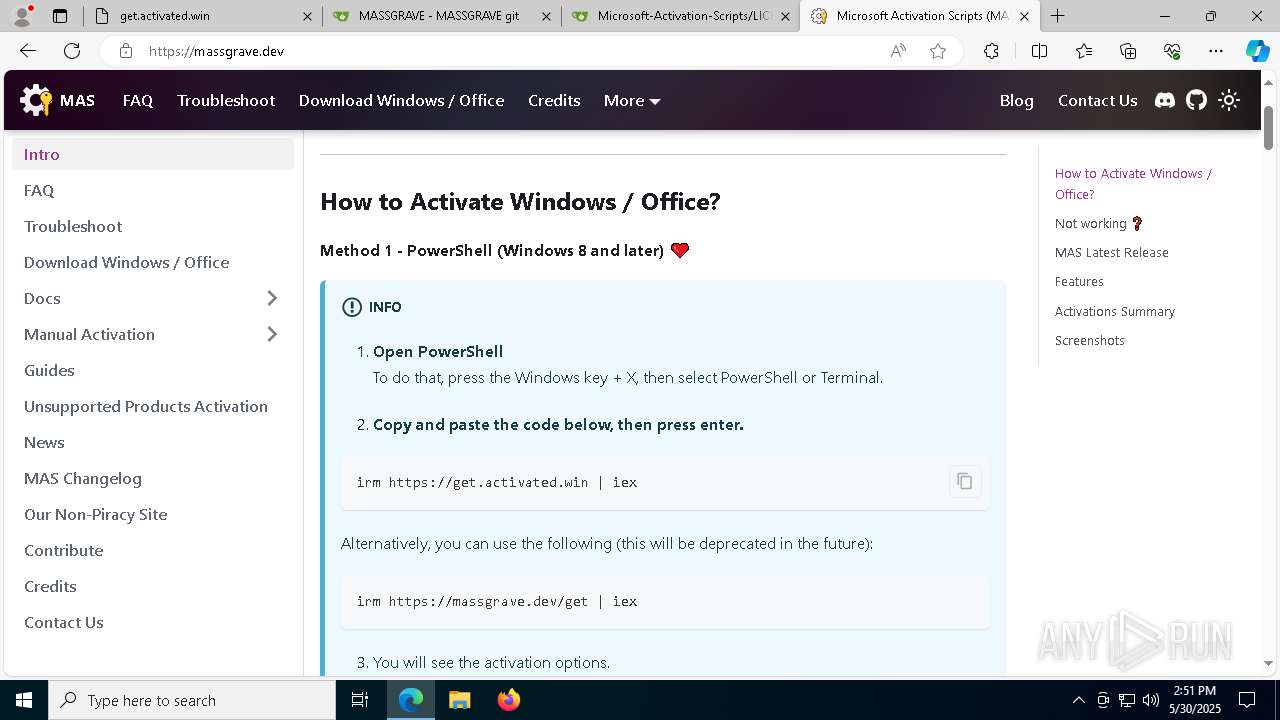
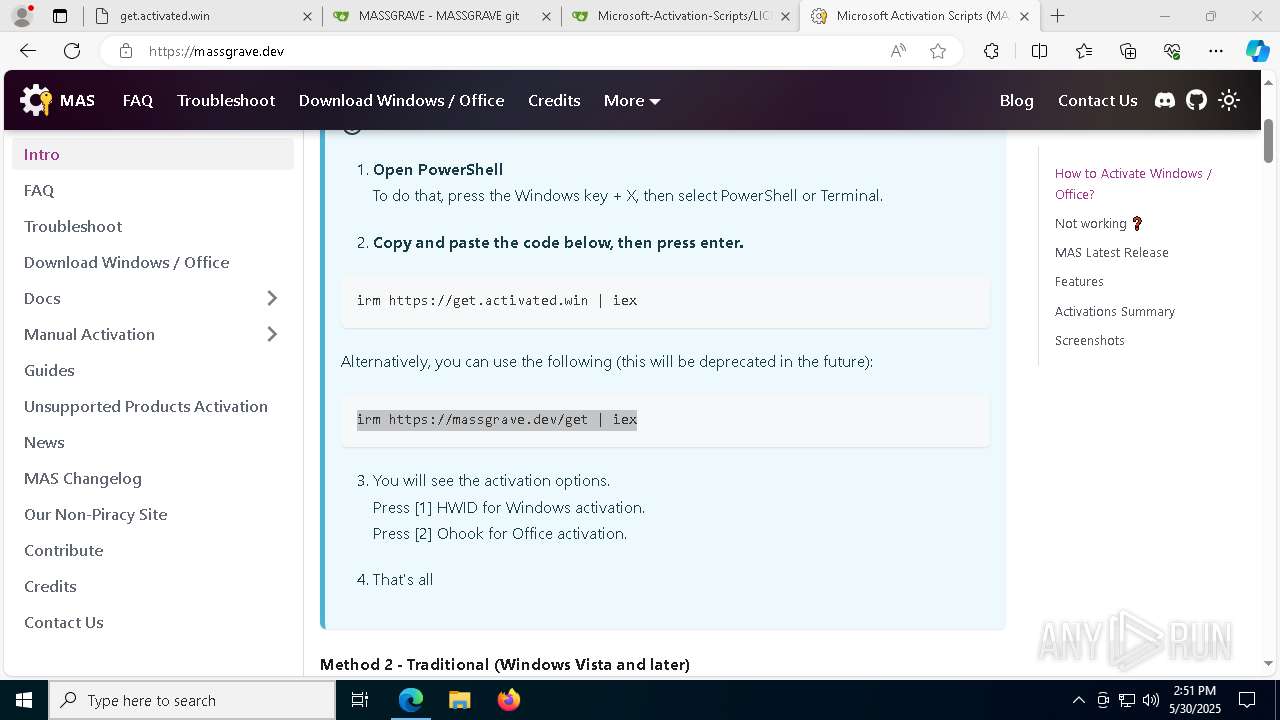
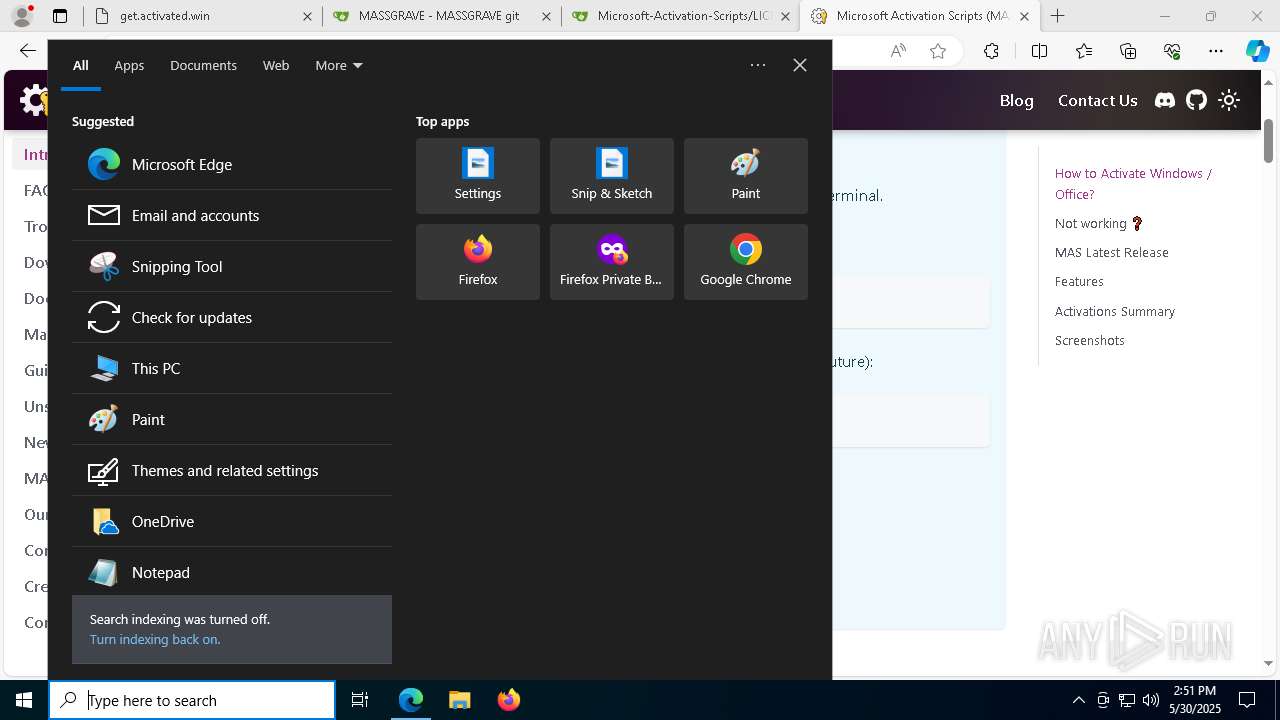
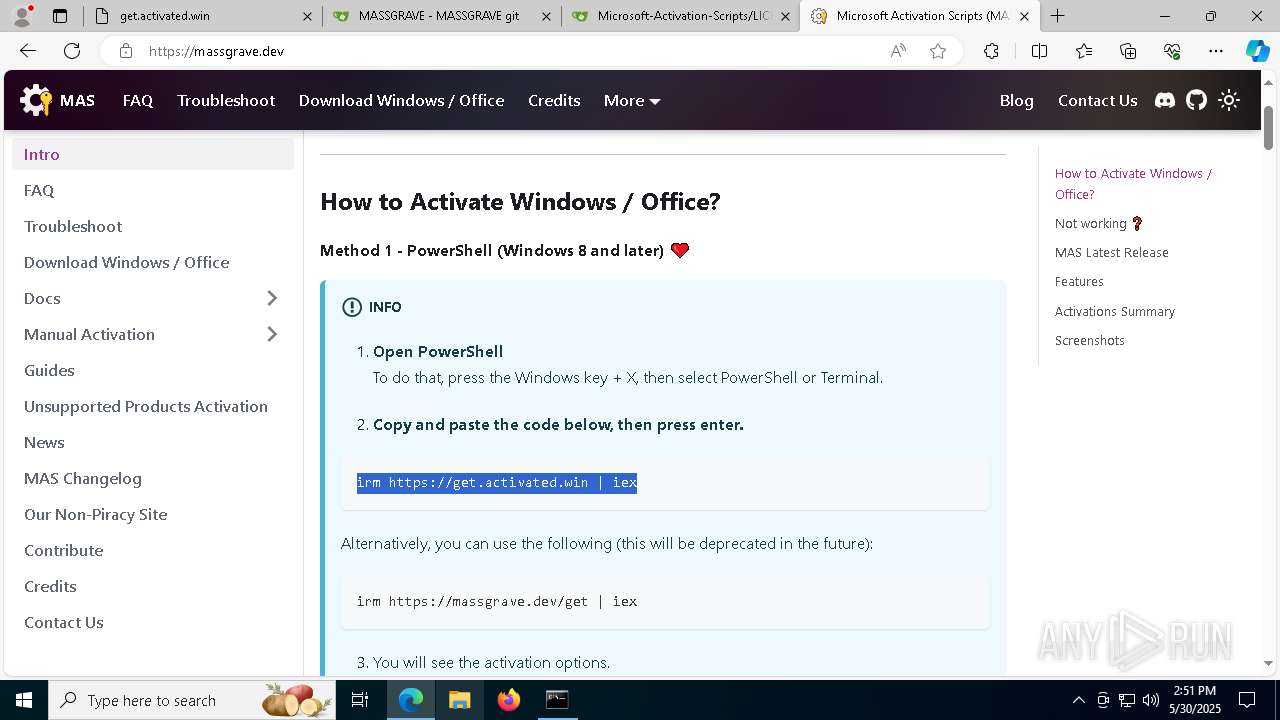
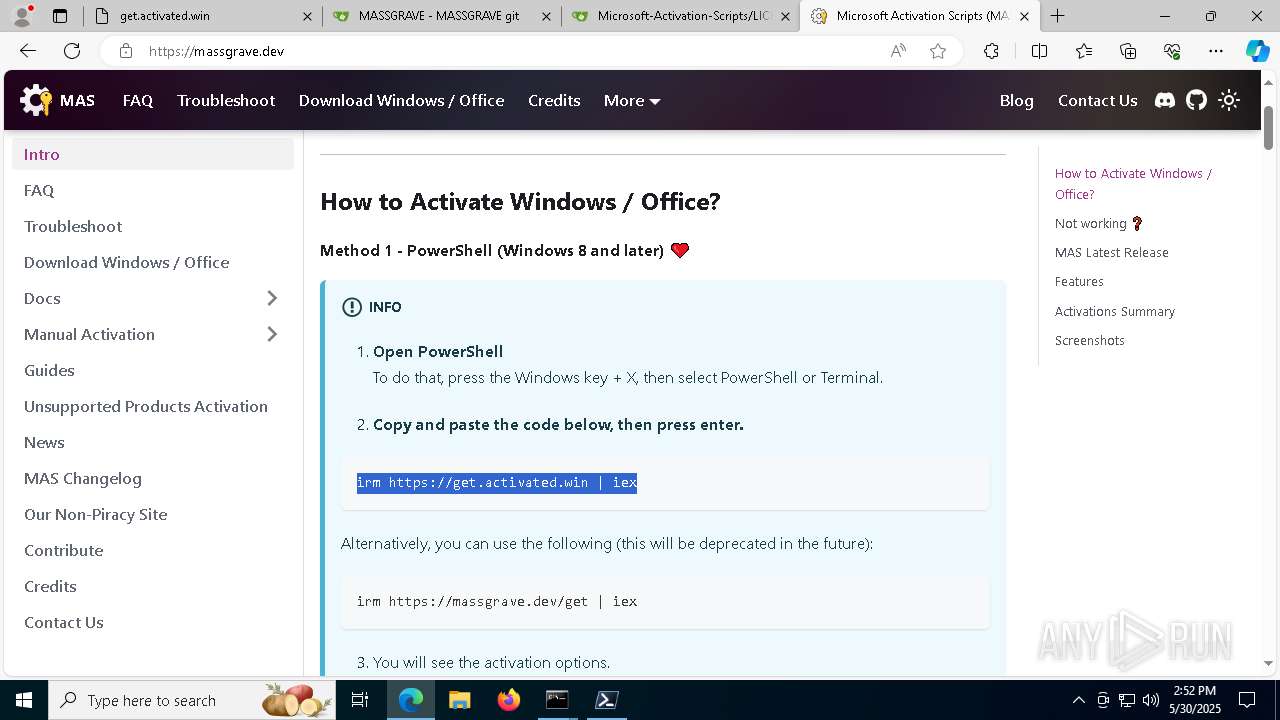
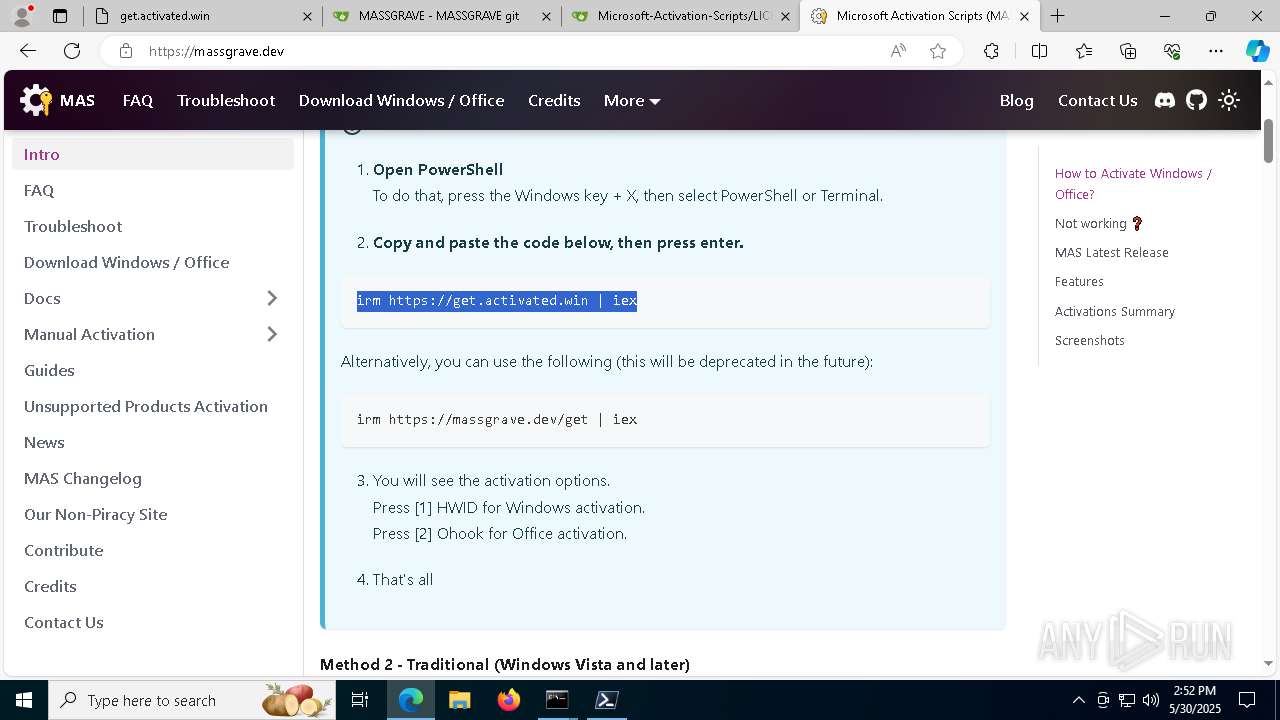
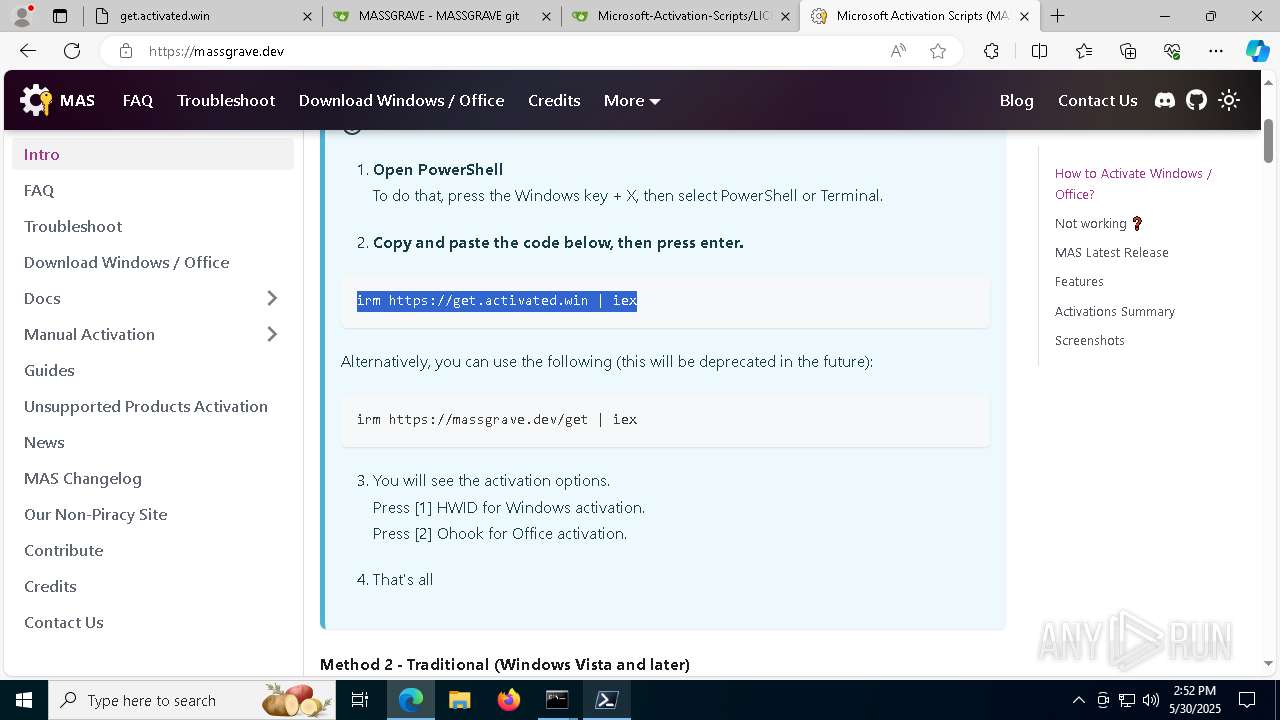
| URL: | http://get.activated.win/ |
| Full analysis: | https://app.any.run/tasks/ebe840ae-7e65-4ea1-b333-f4d6bf737625 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 14:49:41 |
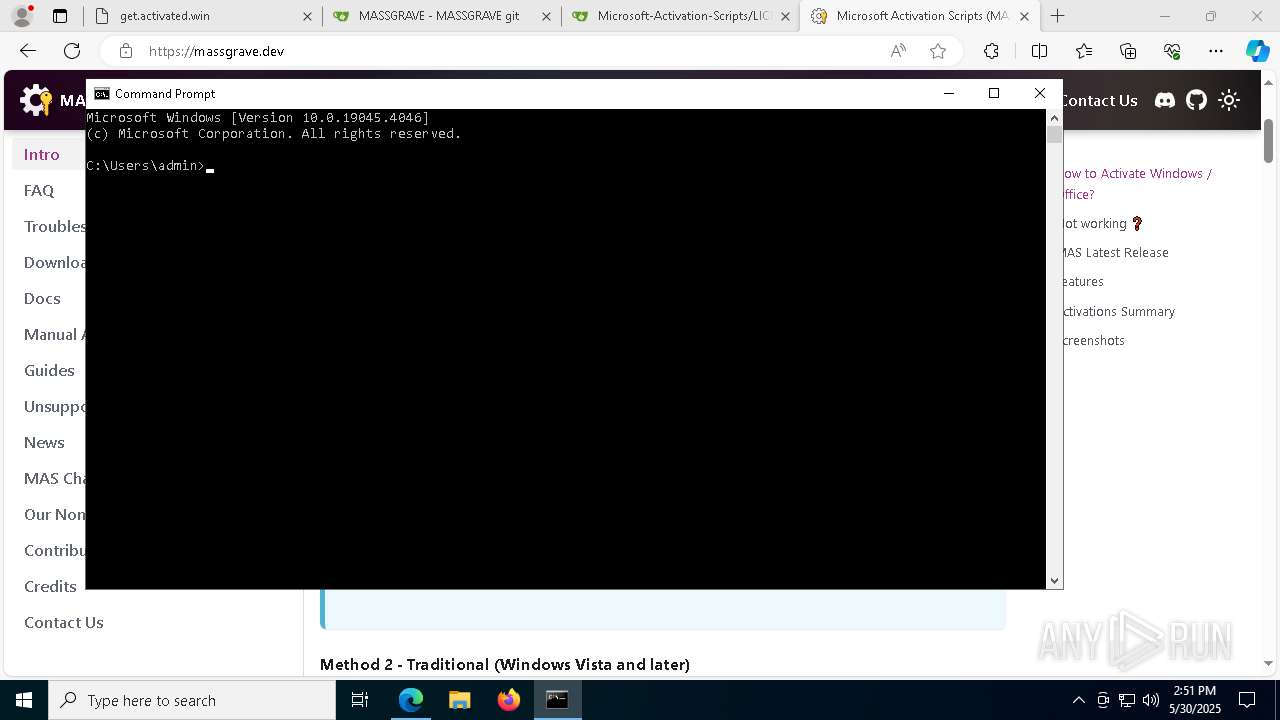
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | C70F7CAFDB4696F338EC24ADEADD3F23 |
| SHA1: | 961764E161E0B35EFEA1BD3A86A3948C9FAB20C2 |
| SHA256: | 26FB60891C1791DC50133B24E35ED8C815E877B859603A24161086EBCF4D299F |
| SSDEEP: | 3:N1KZARuTE2mM+:C+mmR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 2780)
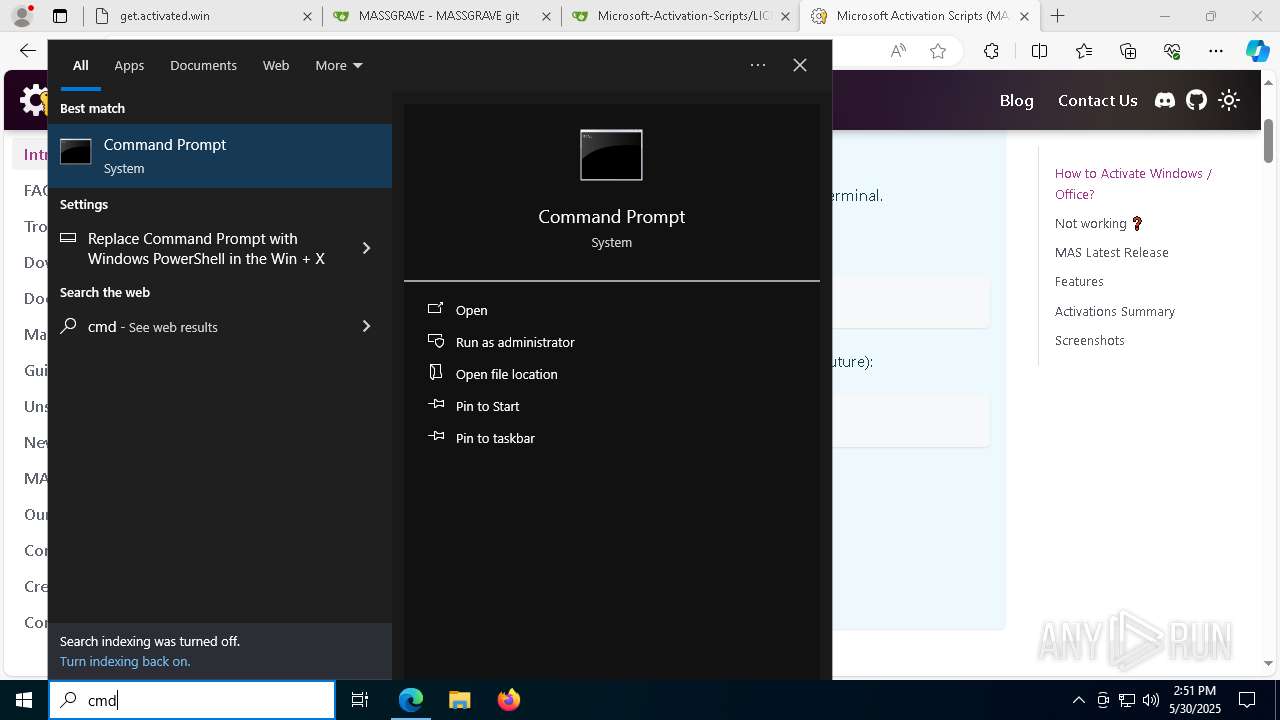
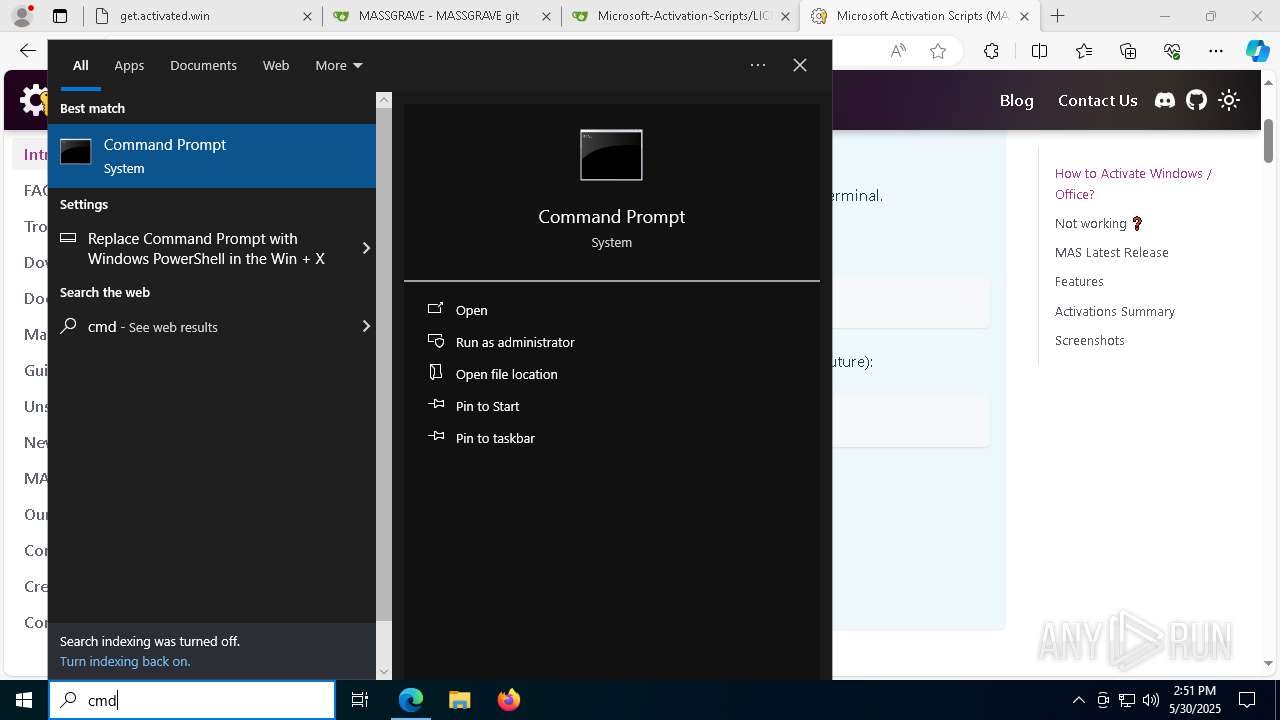
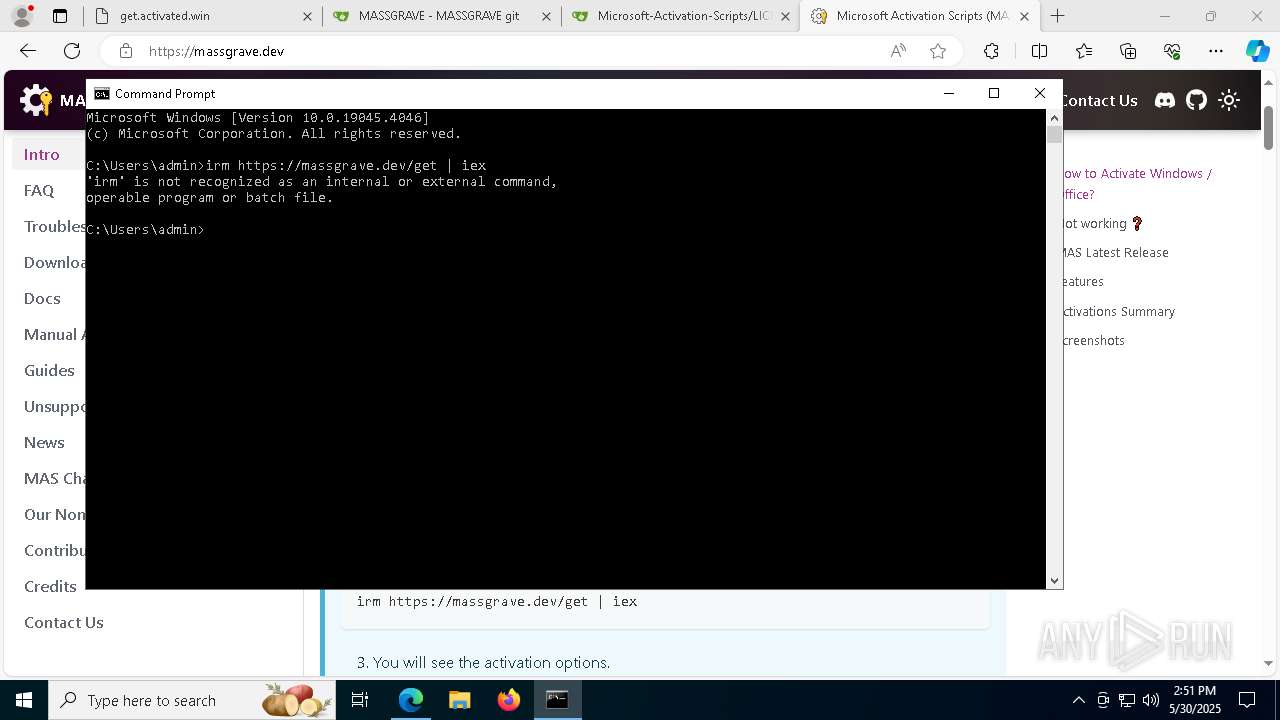
Starts CMD.EXE for commands execution
- pwsh.exe (PID: 2780)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 4784)
- powershell.exe (PID: 5344)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 5676)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 7812)
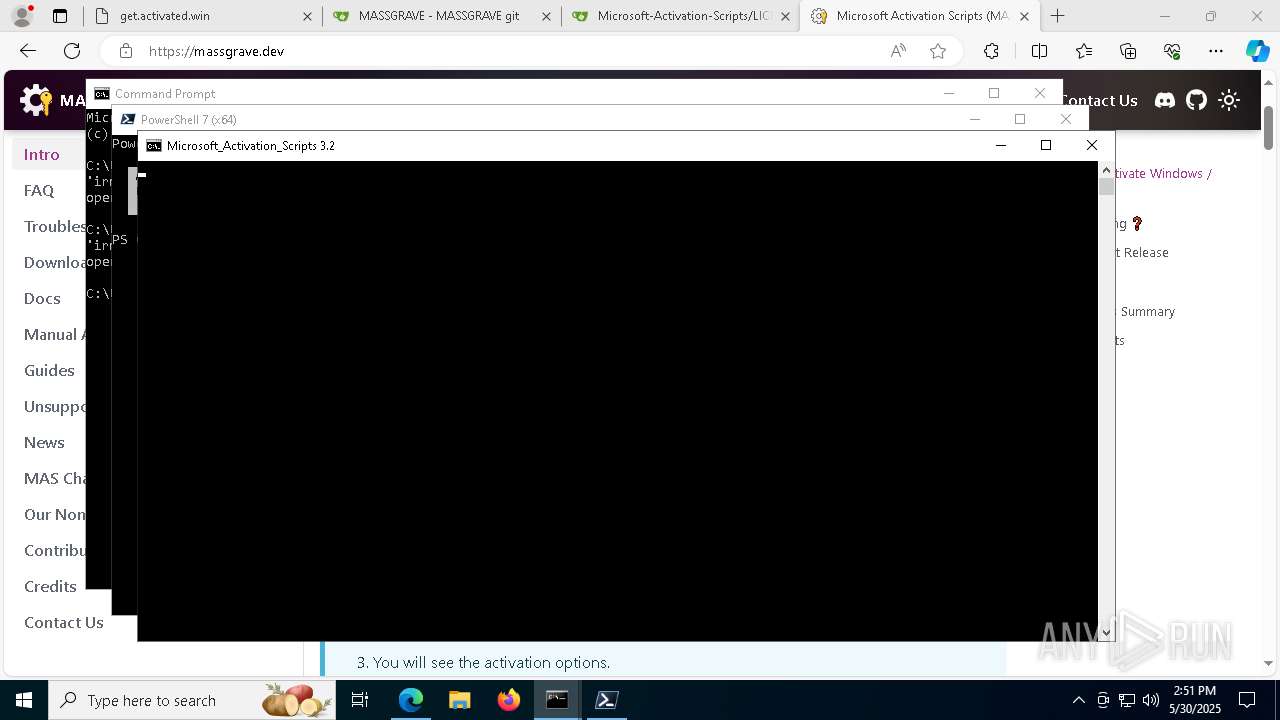
Executing commands from ".cmd" file
- pwsh.exe (PID: 2780)
- powershell.exe (PID: 5344)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4272)
Windows service management via SC.EXE
- sc.exe (PID: 2596)
- sc.exe (PID: 5400)
- sc.exe (PID: 8188)
- sc.exe (PID: 4164)
- sc.exe (PID: 2392)
- sc.exe (PID: 6816)
- sc.exe (PID: 6072)
- sc.exe (PID: 2392)
- sc.exe (PID: 4880)
- sc.exe (PID: 208)
- sc.exe (PID: 7000)
- sc.exe (PID: 5260)
- sc.exe (PID: 4572)
- sc.exe (PID: 6592)
- sc.exe (PID: 5188)
- sc.exe (PID: 1240)
- sc.exe (PID: 2148)
- sc.exe (PID: 8044)
- sc.exe (PID: 924)
Starts SC.EXE for service management
- cmd.exe (PID: 4688)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4272)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4688)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2392)
Application launched itself
- cmd.exe (PID: 4688)
- cmd.exe (PID: 5676)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 7812)
- powershell.exe (PID: 5400)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4688)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 7476)
- powershell.exe (PID: 5400)
- cmd.exe (PID: 236)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 3768)
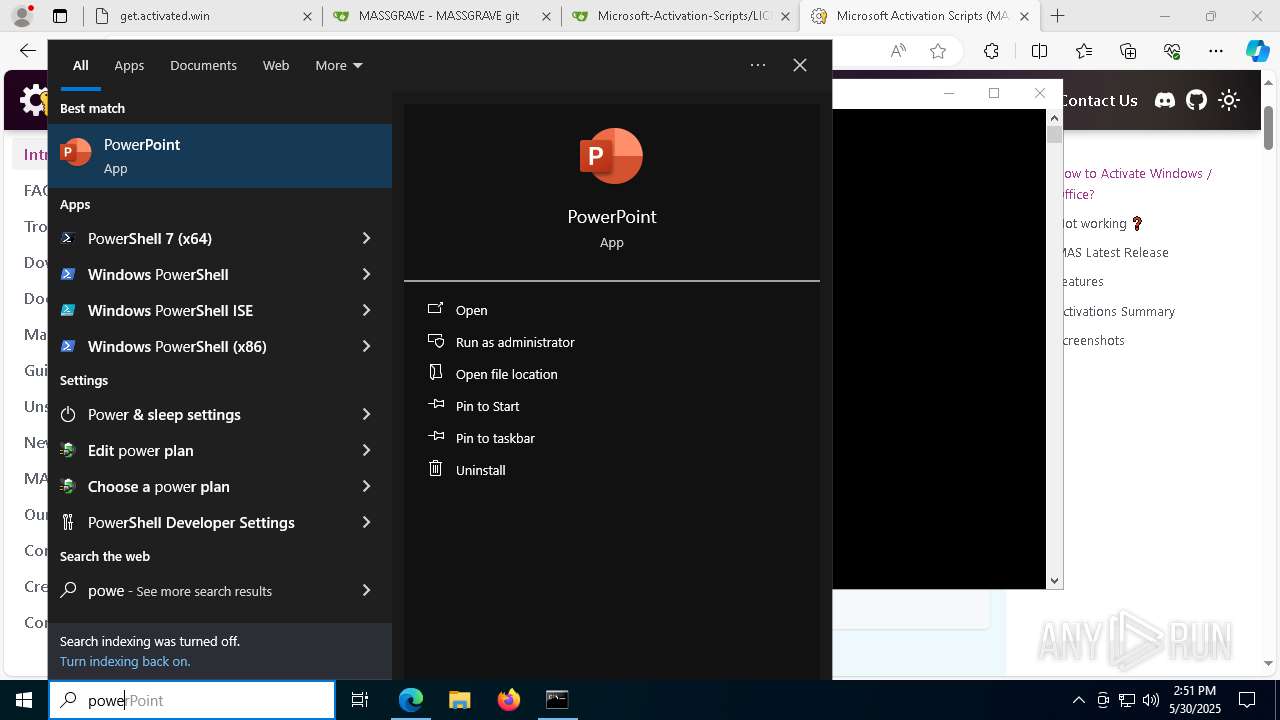
Executes script without checking the security policy
- powershell.exe (PID: 5344)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 4452)
- powershell.exe (PID: 1748)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 6476)
- powershell.exe (PID: 5728)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 8188)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6424)
- powershell.exe (PID: 2840)
- powershell.exe (PID: 1040)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4688)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 7476)
- powershell.exe (PID: 5400)
- cmd.exe (PID: 236)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 3768)
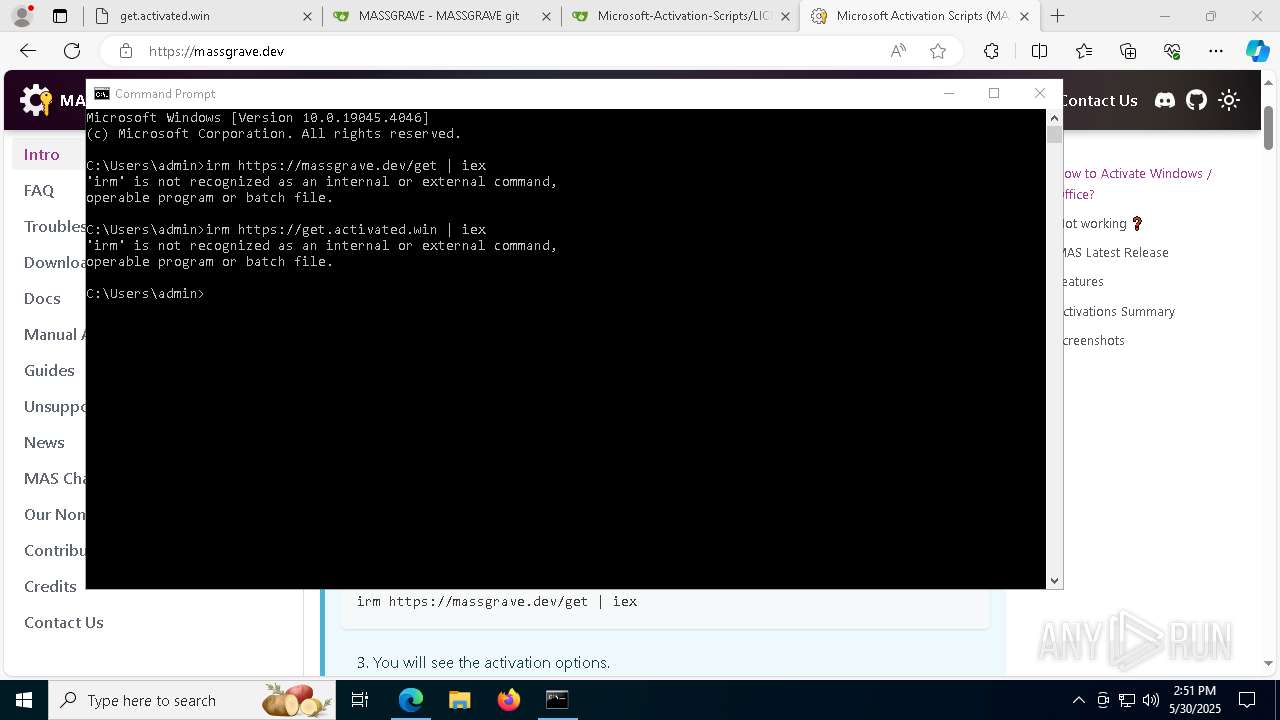
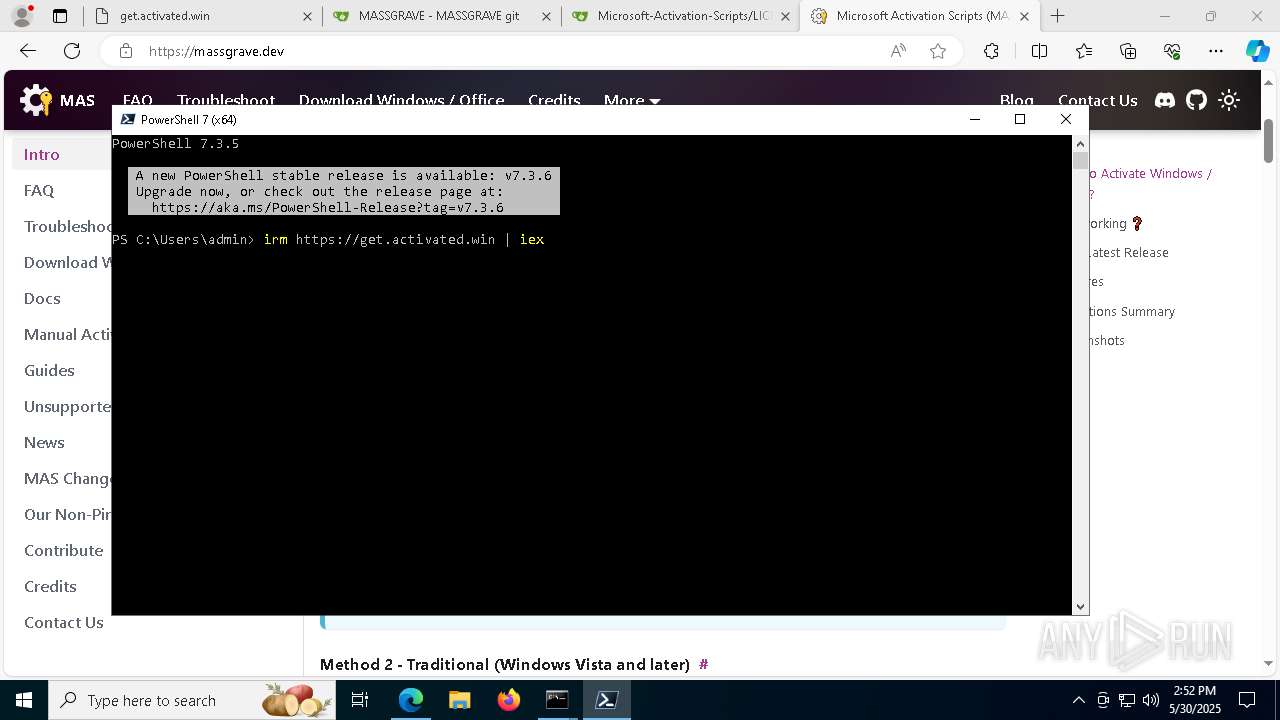
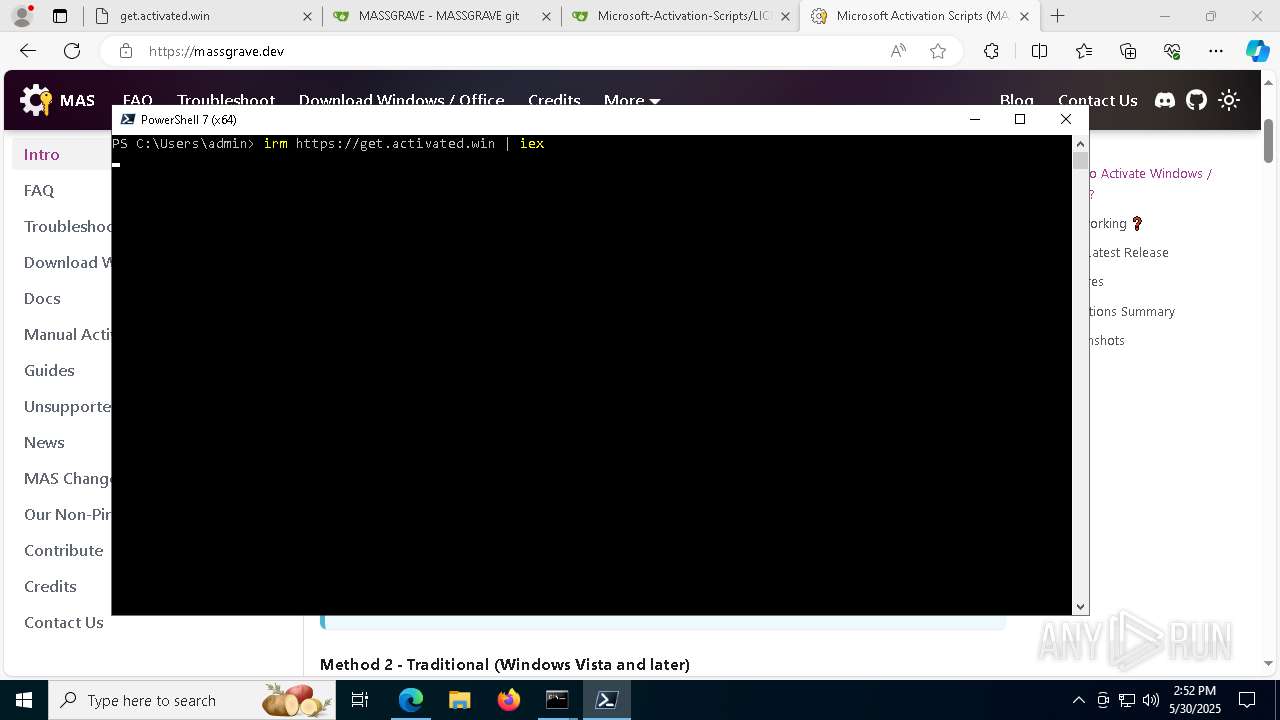
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 236)
- cmd.exe (PID: 4272)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 2960)
Hides command output
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 236)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 924)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 7476)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 236)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 4272)
Get information on the list of running processes
- cmd.exe (PID: 6344)
- cmd.exe (PID: 4272)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8184)
- cmd.exe (PID: 4272)
Probably file/command deobfuscation
- cmd.exe (PID: 7476)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 5400)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7020)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 1128)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 4272)
Executable content was dropped or overwritten
- powershell.exe (PID: 2840)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 1040)
INFO
Checks supported languages
- identity_helper.exe (PID: 1324)
- pwsh.exe (PID: 2780)
Reads Environment values
- identity_helper.exe (PID: 1324)
Reads the computer name
- identity_helper.exe (PID: 1324)
- pwsh.exe (PID: 2780)
Application launched itself
- msedge.exe (PID: 5408)
Reads the software policy settings
- slui.exe (PID: 8132)
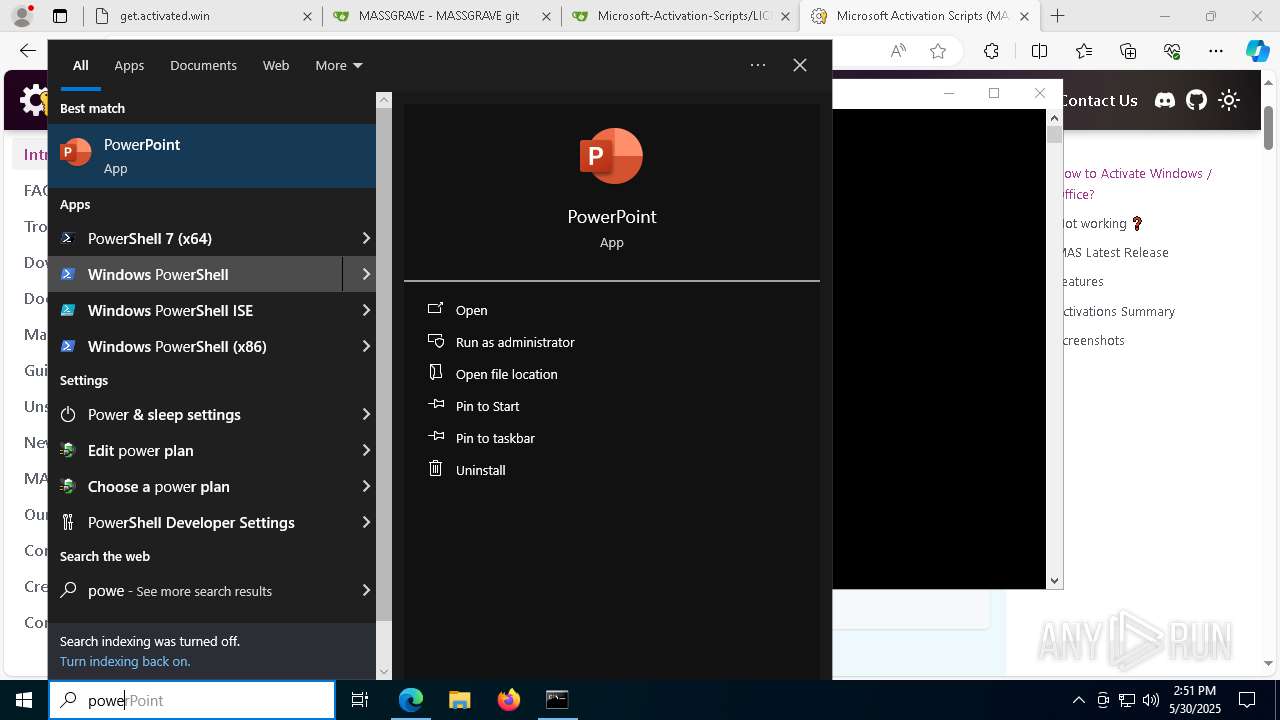
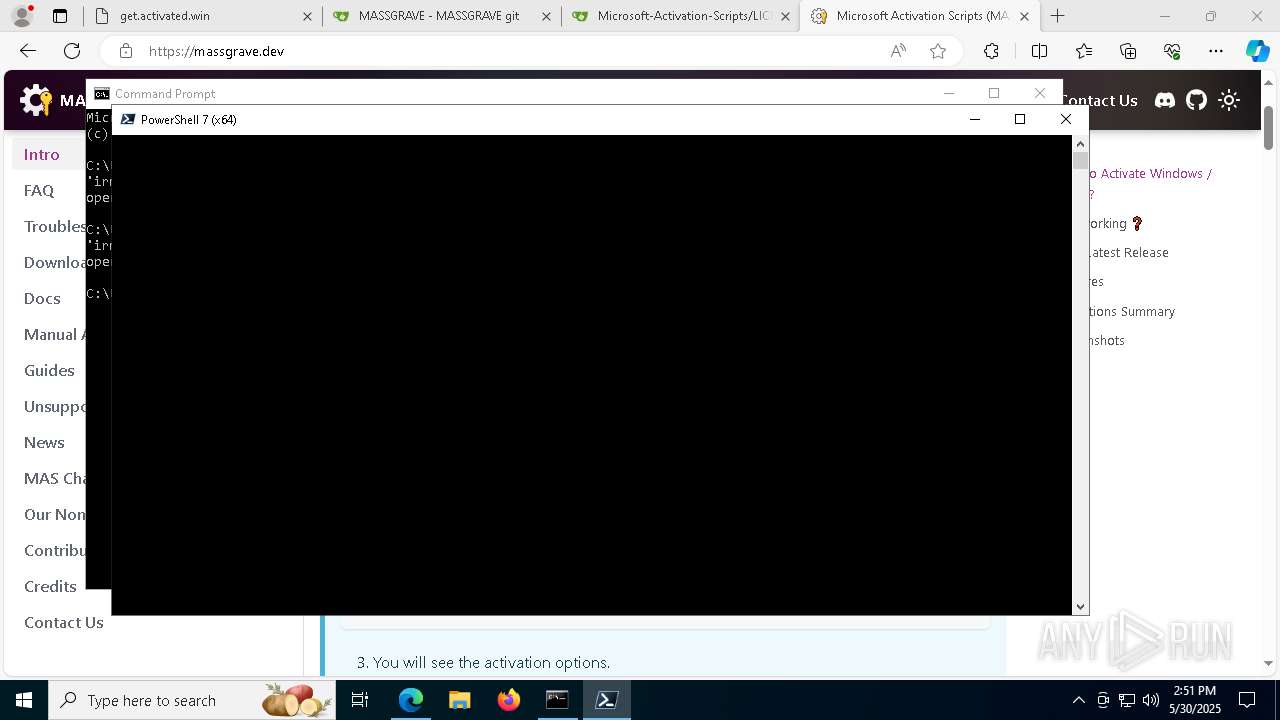
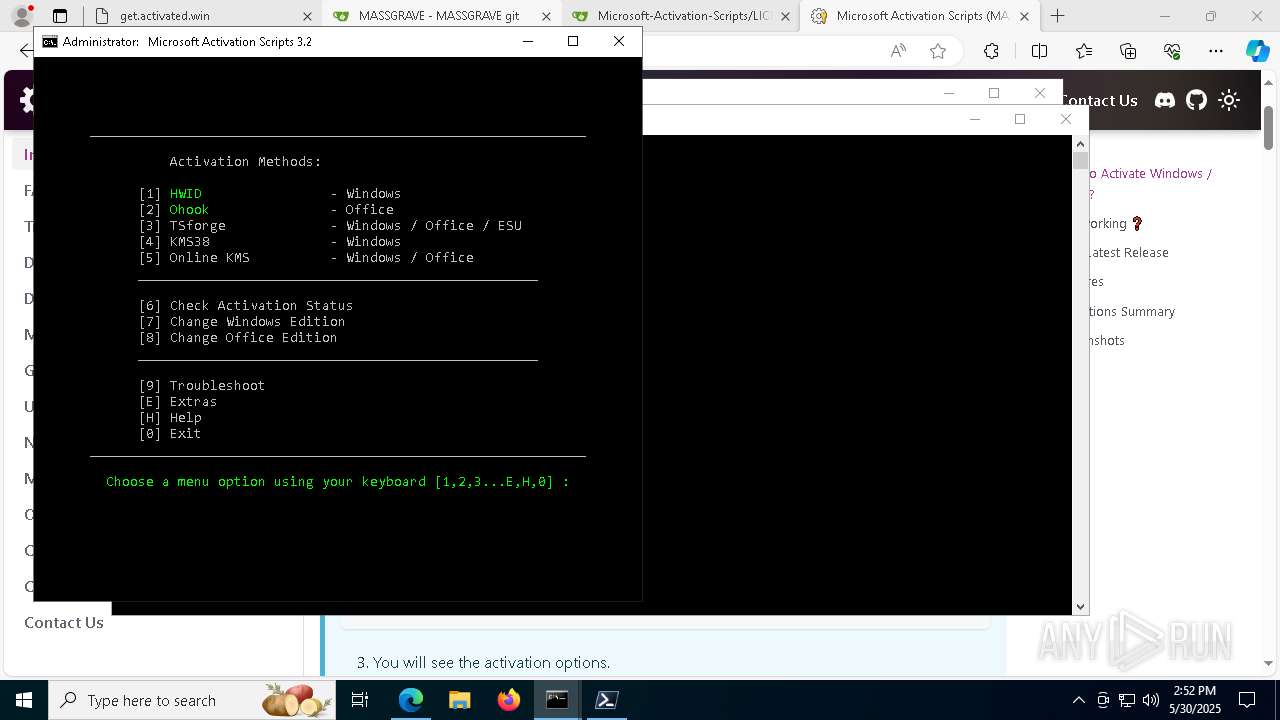
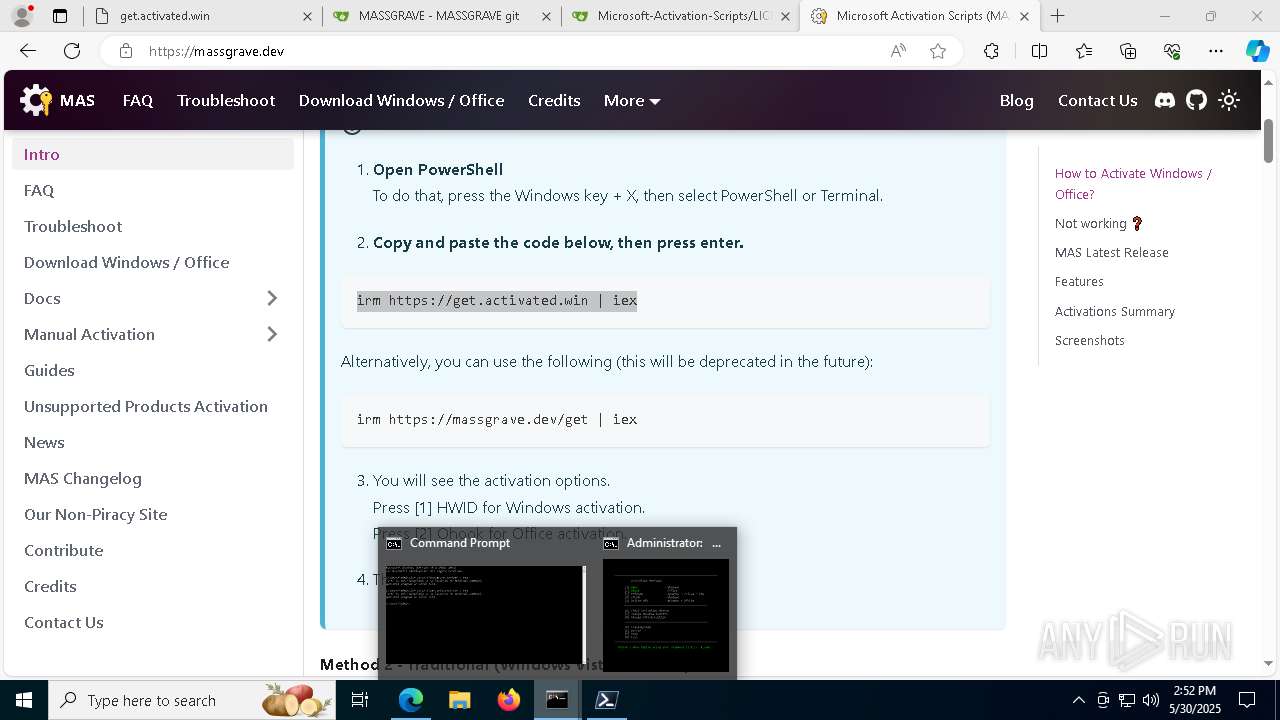
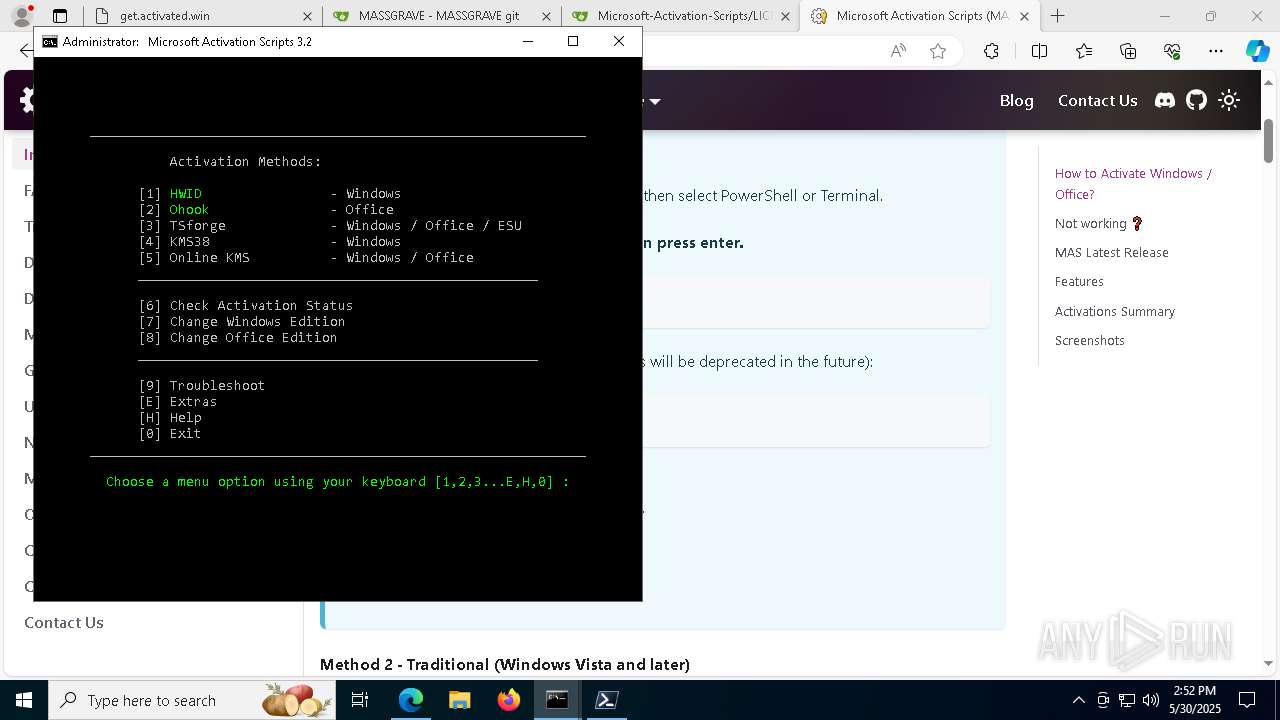
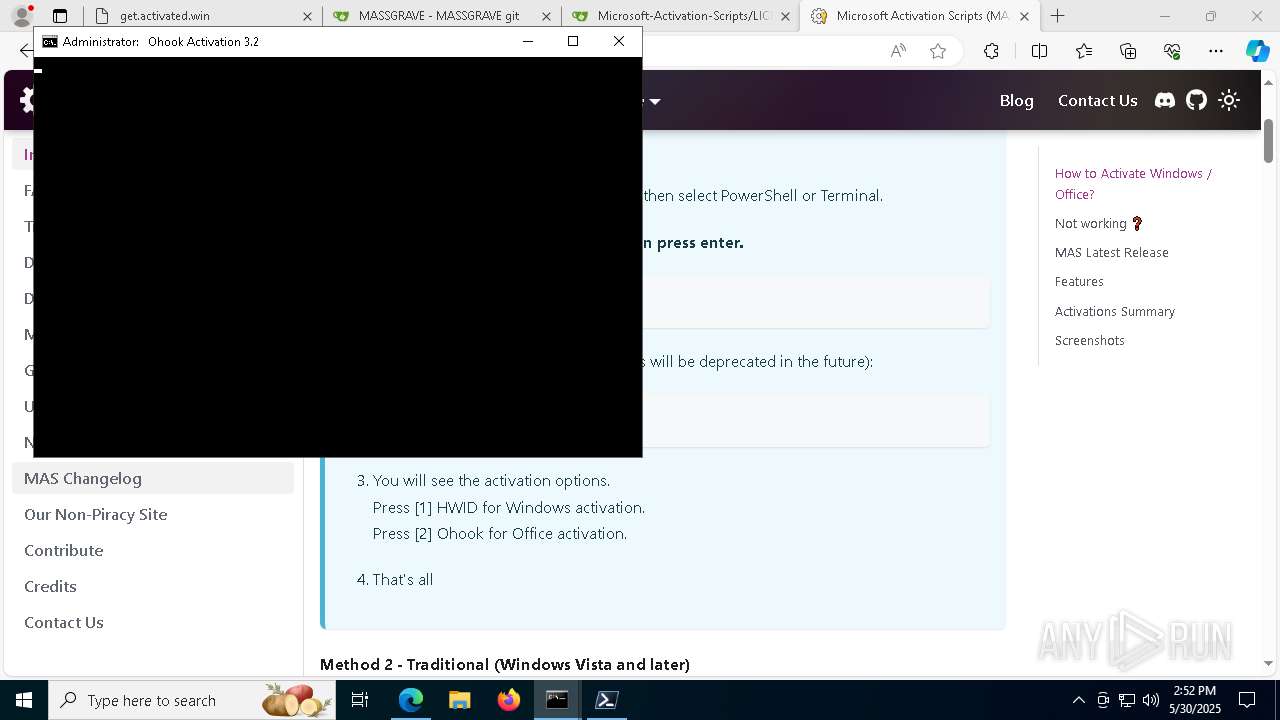
Manual execution by a user
- cmd.exe (PID: 3016)
- pwsh.exe (PID: 2780)
Checks proxy server information
- slui.exe (PID: 7524)
Process checks computer location settings
- pwsh.exe (PID: 2780)
Checks operating system version
- cmd.exe (PID: 2980)
- cmd.exe (PID: 4272)
- cmd.exe (PID: 4688)
Starts MODE.COM to configure console settings
- mode.com (PID: 3828)
- mode.com (PID: 924)
- mode.com (PID: 236)
- mode.com (PID: 7952)
- mode.com (PID: 7476)
- mode.com (PID: 4884)
The sample compiled with english language support
- powershell.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
565
Monitored processes
425
Malicious processes
5
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\WINDOWS\system32\cmd.exe" /c "echo CMD is working" | C:\Windows\System32\cmd.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
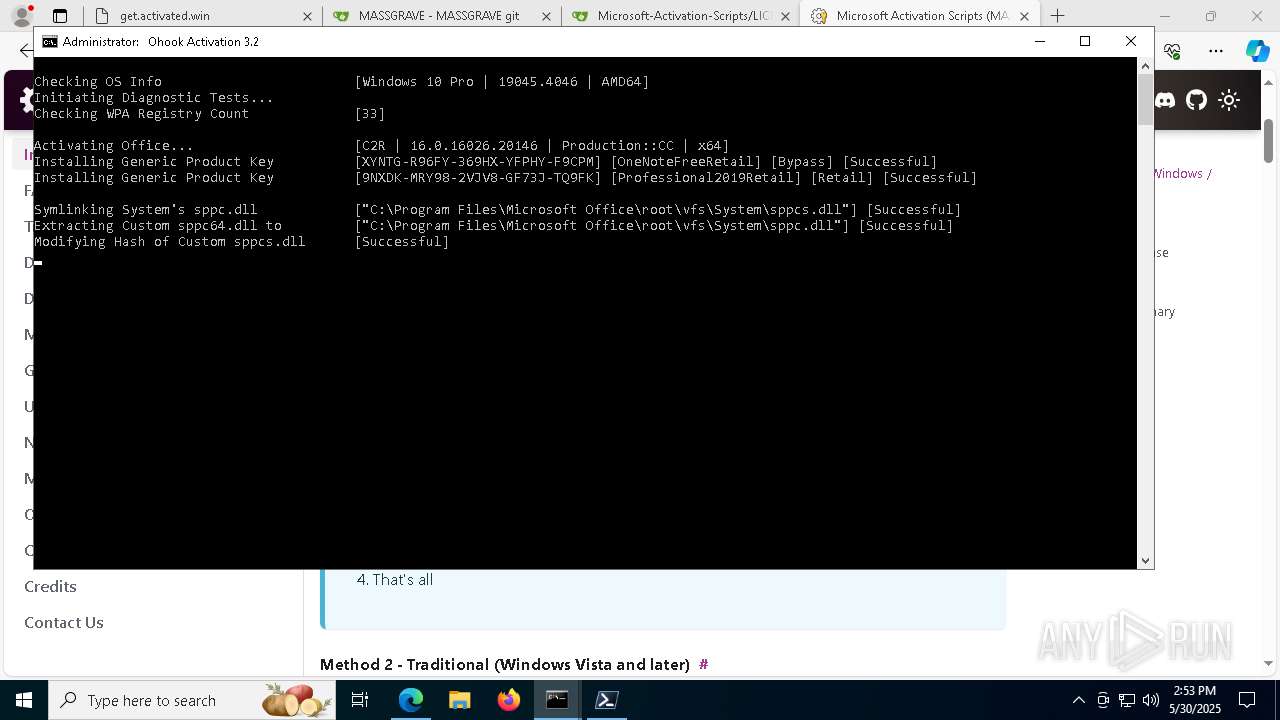
| 132 | wmic path SoftwareLicensingService where __CLASS='SoftwareLicensingService' call InstallProductKey ProductKey="XYNTG-R96FY-369HX-YFPHY-F9CPM" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3464 --field-trial-handle=2188,i,7172254500791753865,9168448725535602971,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\16.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | wmic path SoftwareLicensingProduct where (ApplicationID='0ff1ce15-a989-479d-af46-f275c6370663' and PartialProductKey is not null) get ID /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | mode 76, 34 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | find /i "-onenote.exe-" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
105 461
Read events
105 405
Write events
47
Delete events
9
Modification events
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3A4FF8CEF1942F00 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 164541CFF1942F00 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262994 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B4C6FE6E-0279-436F-8031-99CE1758B8C5} | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (5408) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 462373CFF1942F00 | |||
Executable files
2
Suspicious files
798
Text files
234
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ae14.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ae14.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ae14.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ae33.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ae14.TMP | — | |
MD5:— | SHA256:— | |||
| 5408 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
130
DNS requests
138
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2040 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748972816&P2=404&P3=2&P4=TjGisan9gx%2fw3XqUQYalCd5BGz9z9KVm6M9YOtURMqx22Er%2fSvnC6MNzLnj9WRO0%2biNDzNqN36qDTKR3NLrPQg%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748972816&P2=404&P3=2&P4=i0gq2%2bb1T%2b3Ng7HNFgTrII8jWZywvoyseF6wiS60n5TF4deOzsmyI%2bi5%2bI2hNlAo4obAXZDX7wBi3rA5FbHodQ%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748972816&P2=404&P3=2&P4=TjGisan9gx%2fw3XqUQYalCd5BGz9z9KVm6M9YOtURMqx22Er%2fSvnC6MNzLnj9WRO0%2biNDzNqN36qDTKR3NLrPQg%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748972816&P2=404&P3=2&P4=TjGisan9gx%2fw3XqUQYalCd5BGz9z9KVm6M9YOtURMqx22Er%2fSvnC6MNzLnj9WRO0%2biNDzNqN36qDTKR3NLrPQg%3d%3d | unknown | — | — | whitelisted |
2040 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748972816&P2=404&P3=2&P4=i0gq2%2bb1T%2b3Ng7HNFgTrII8jWZywvoyseF6wiS60n5TF4deOzsmyI%2bi5%2bI2hNlAo4obAXZDX7wBi3rA5FbHodQ%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7356 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5408 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
get.activated.win |
| malicious |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7356 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7356 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2780 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |