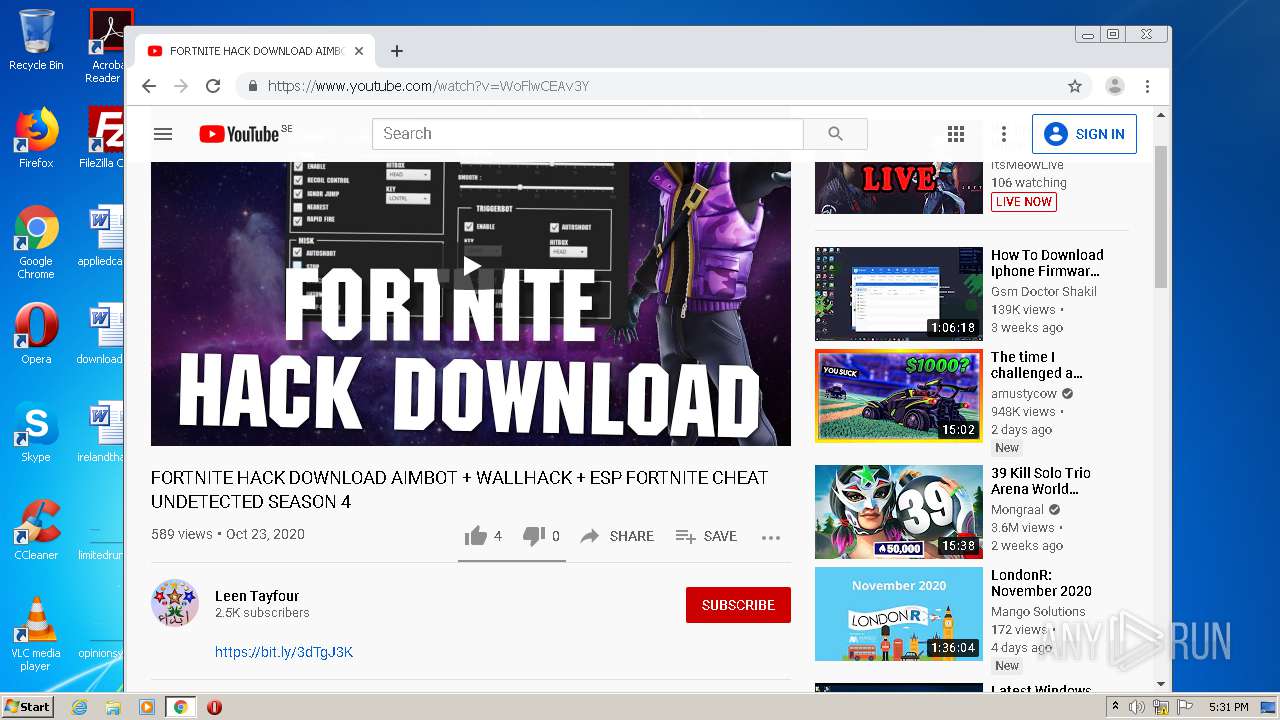
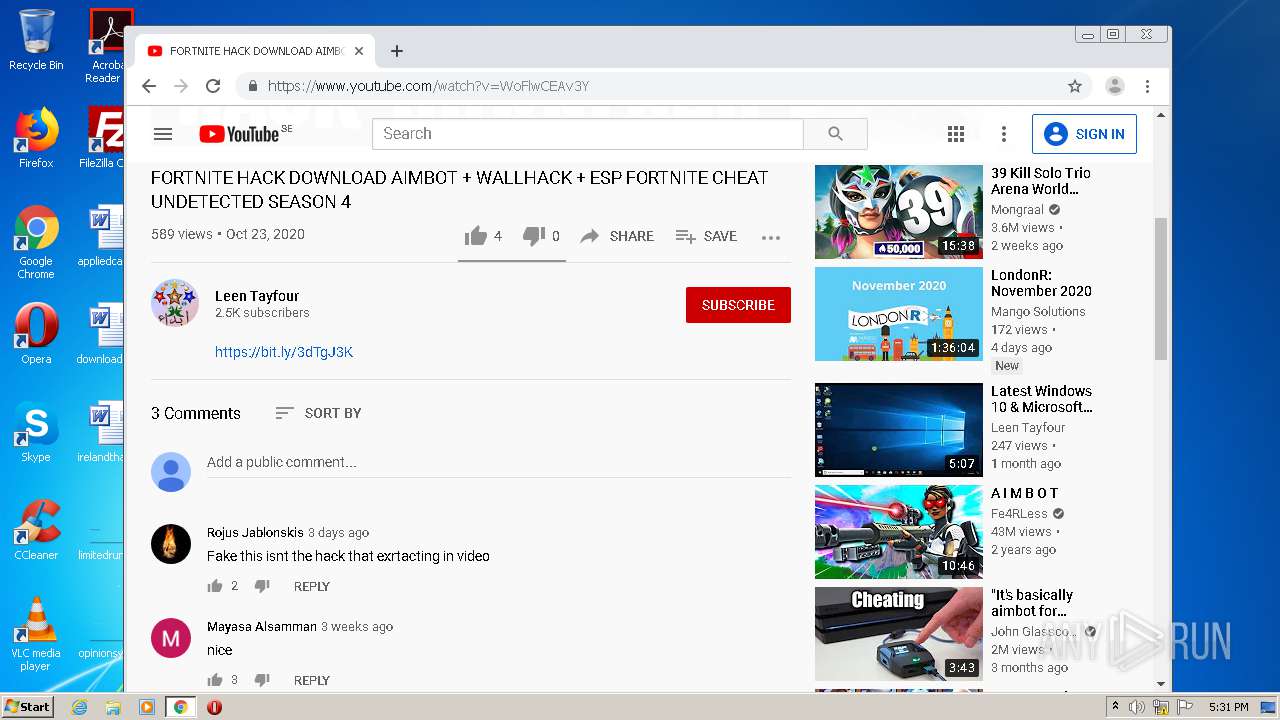
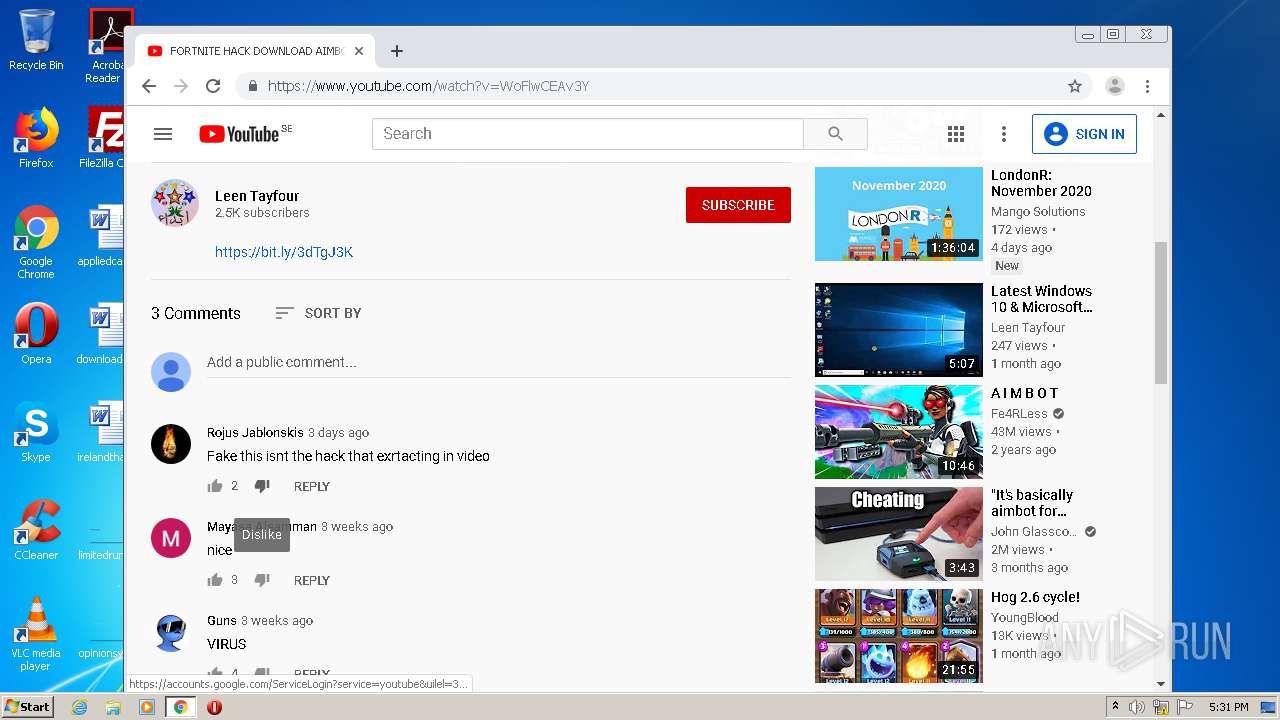
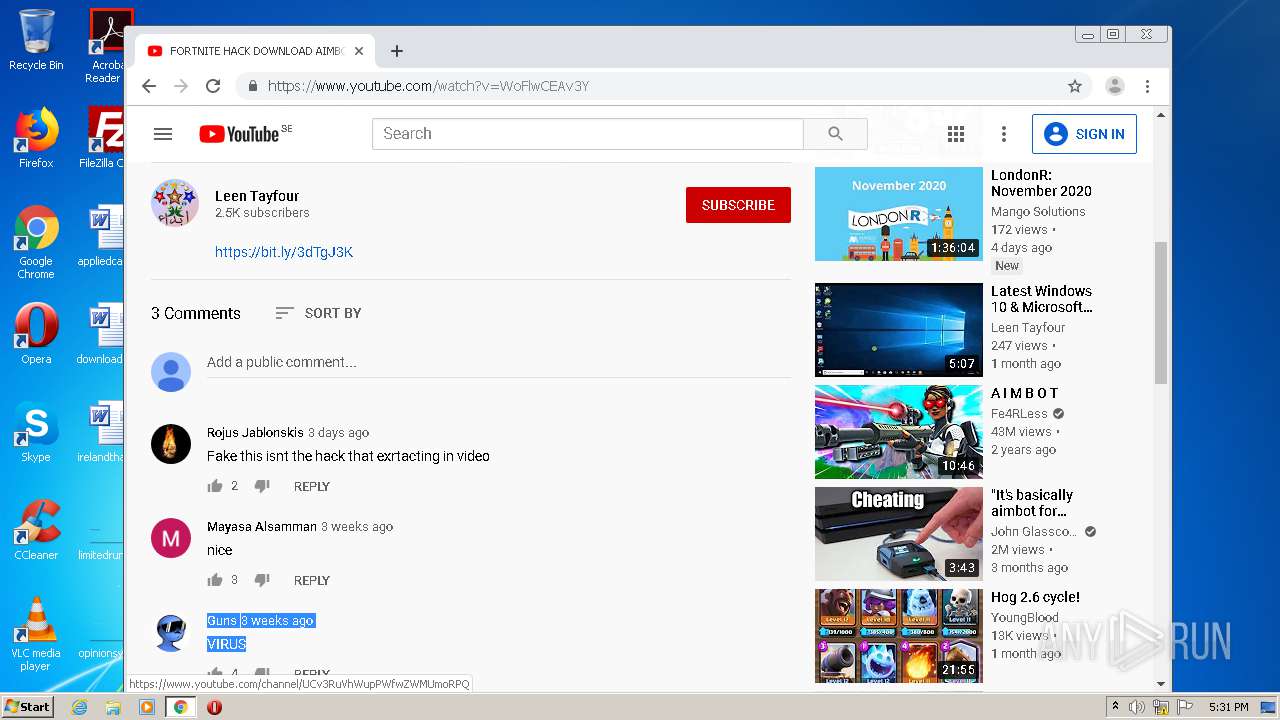
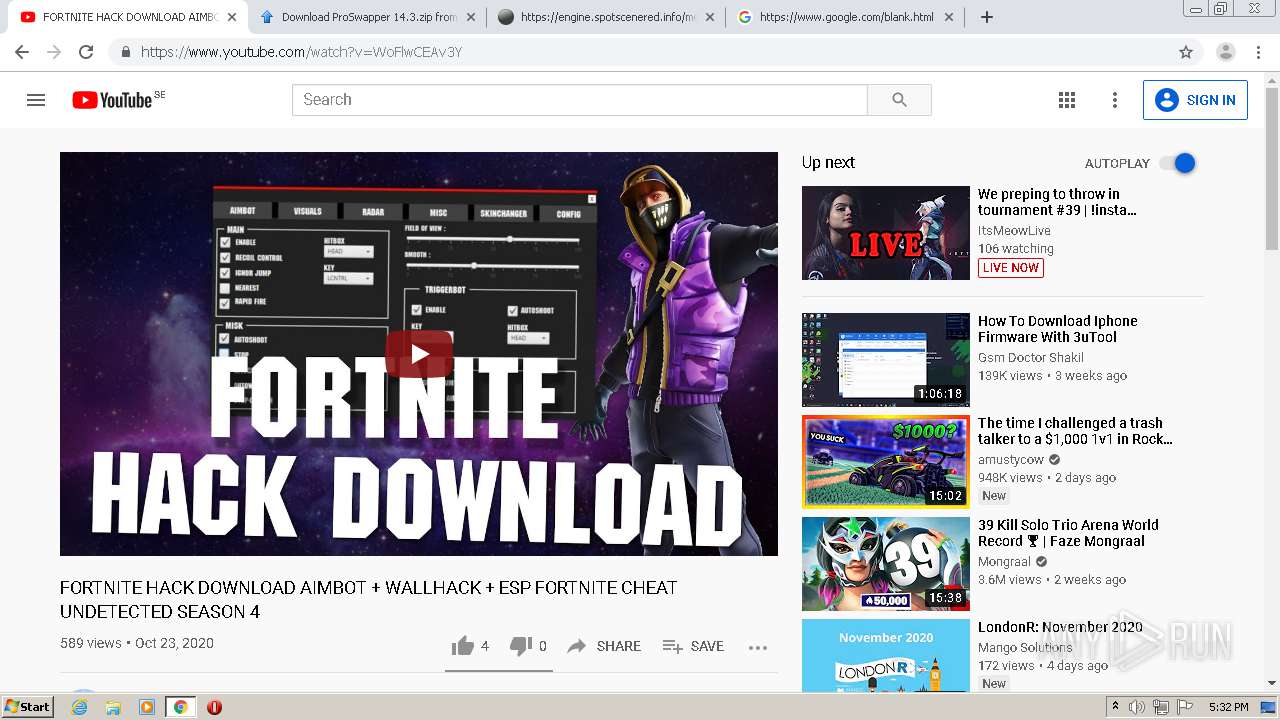
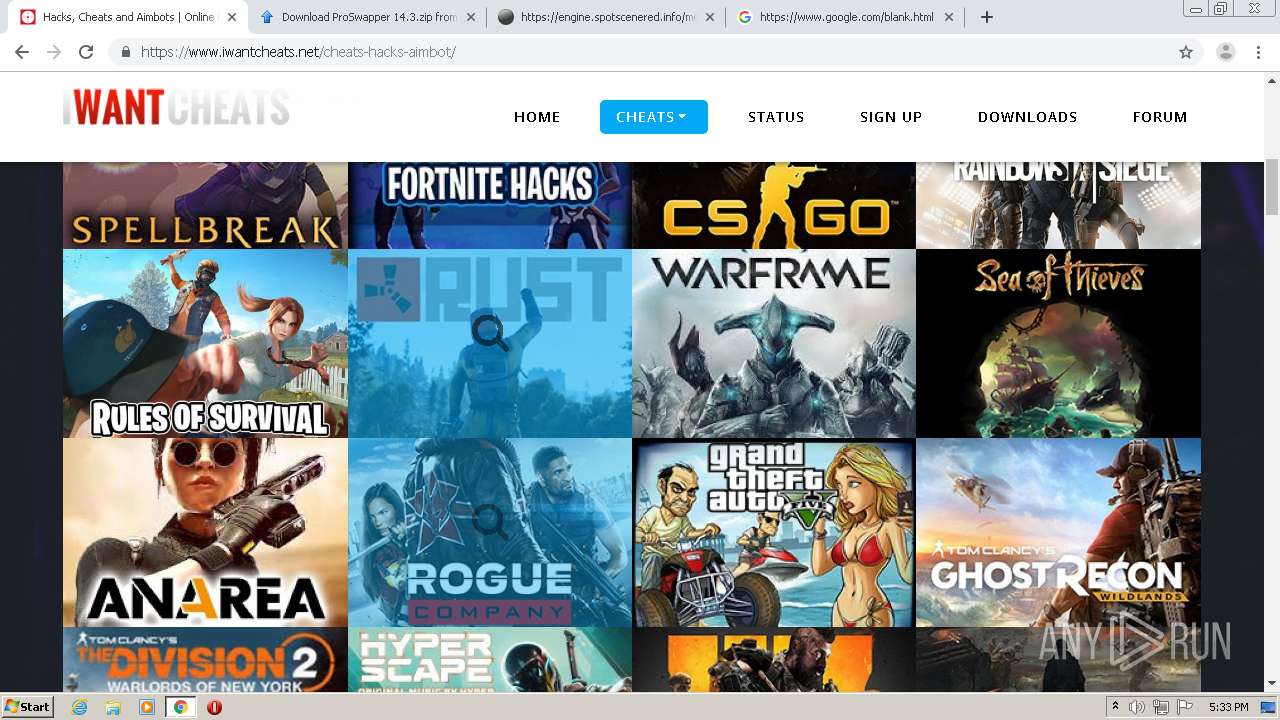
| File name: | apple2.png |
| Full analysis: | https://app.any.run/tasks/e24b0852-3390-43b0-8385-177167c7713f |
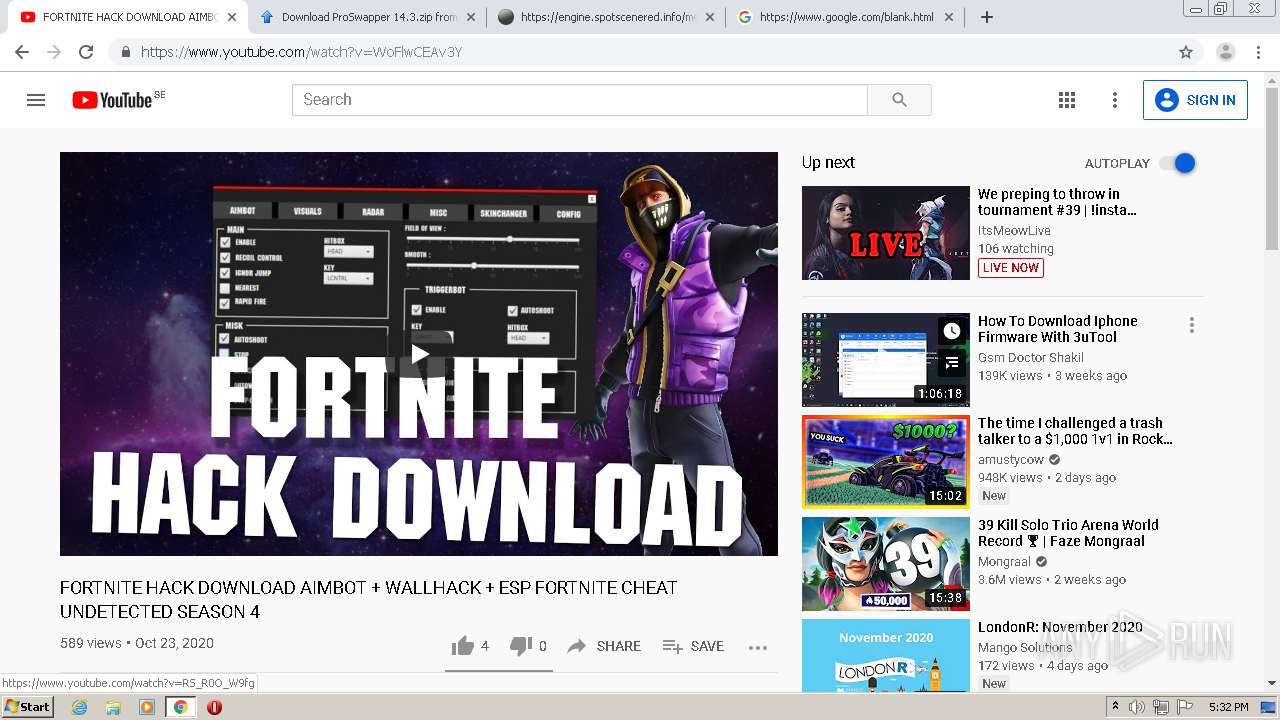
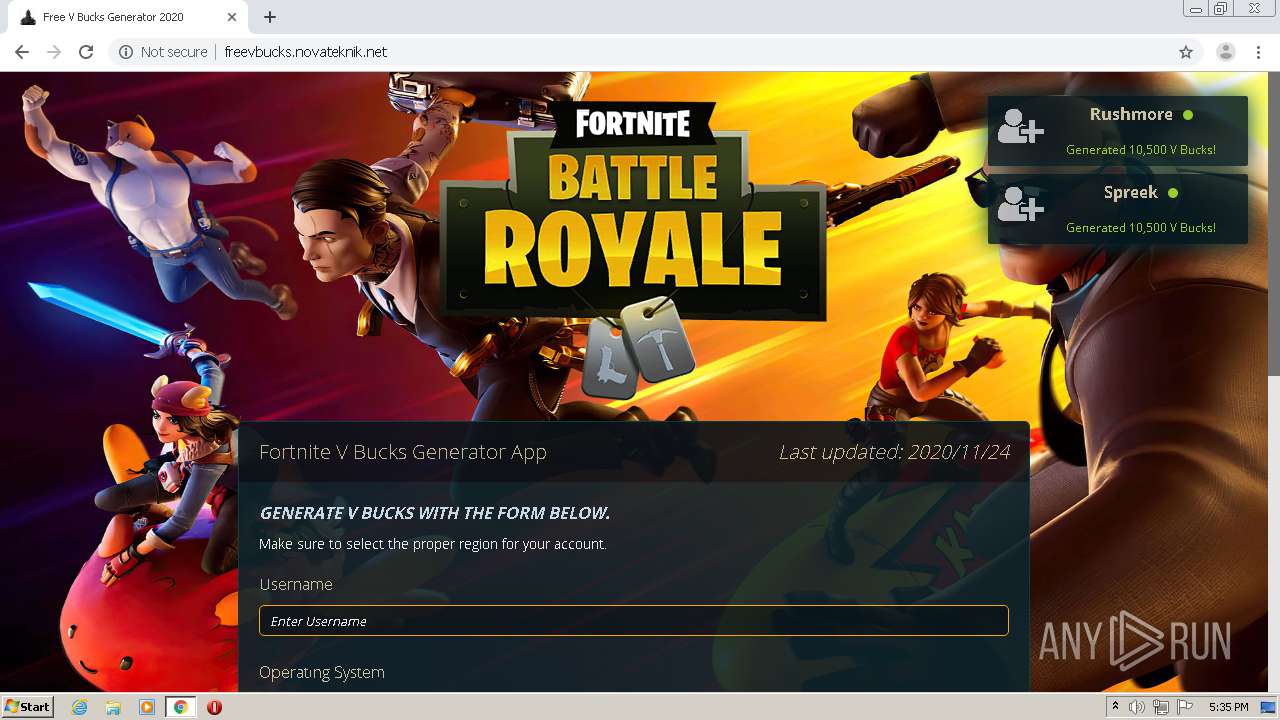
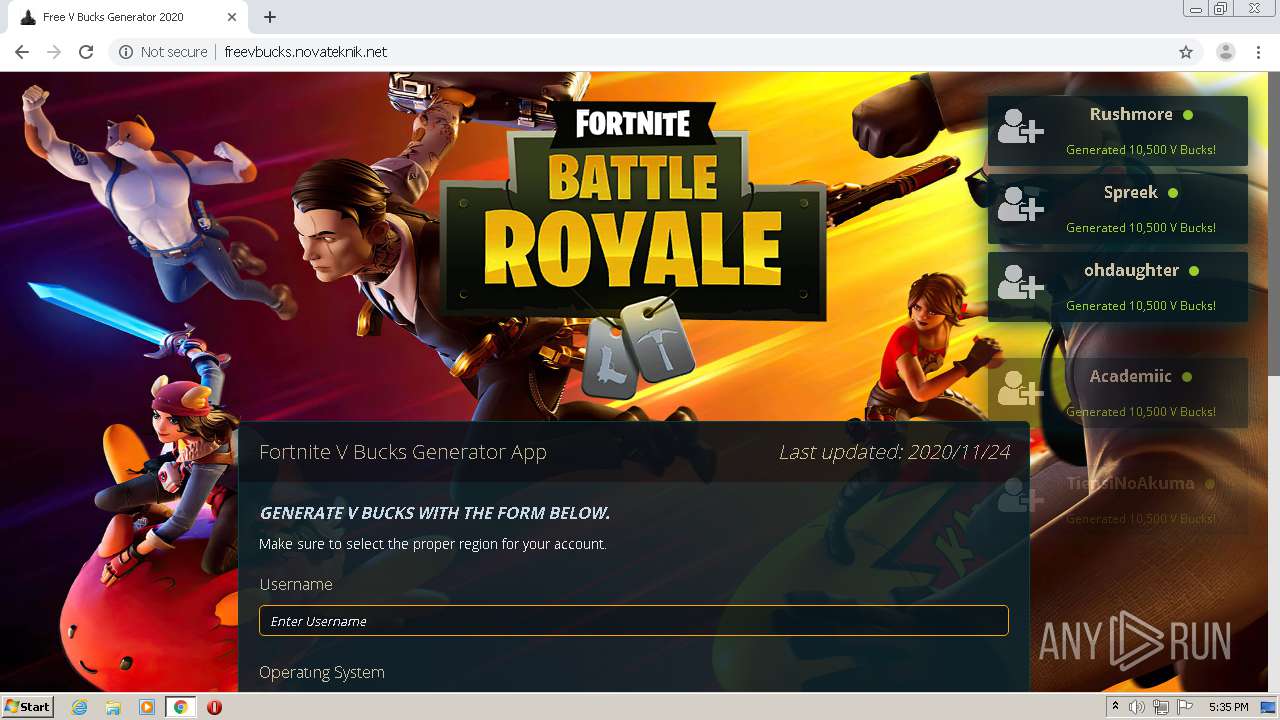
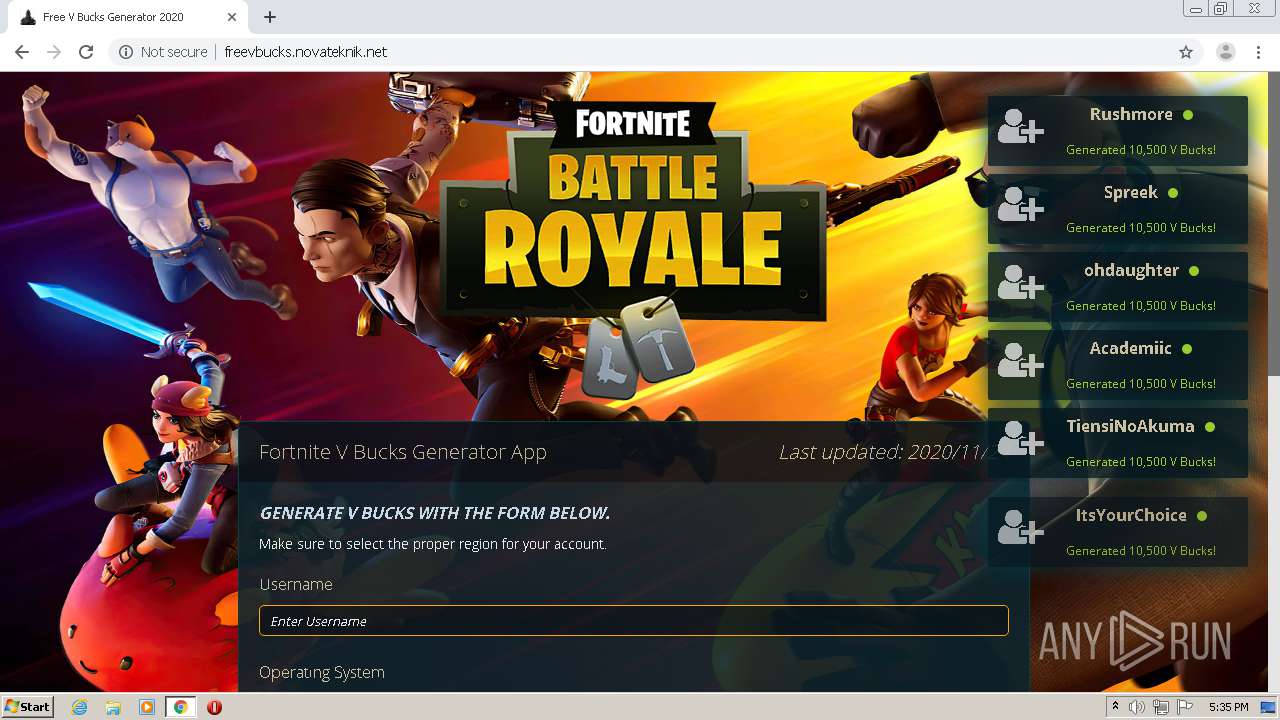
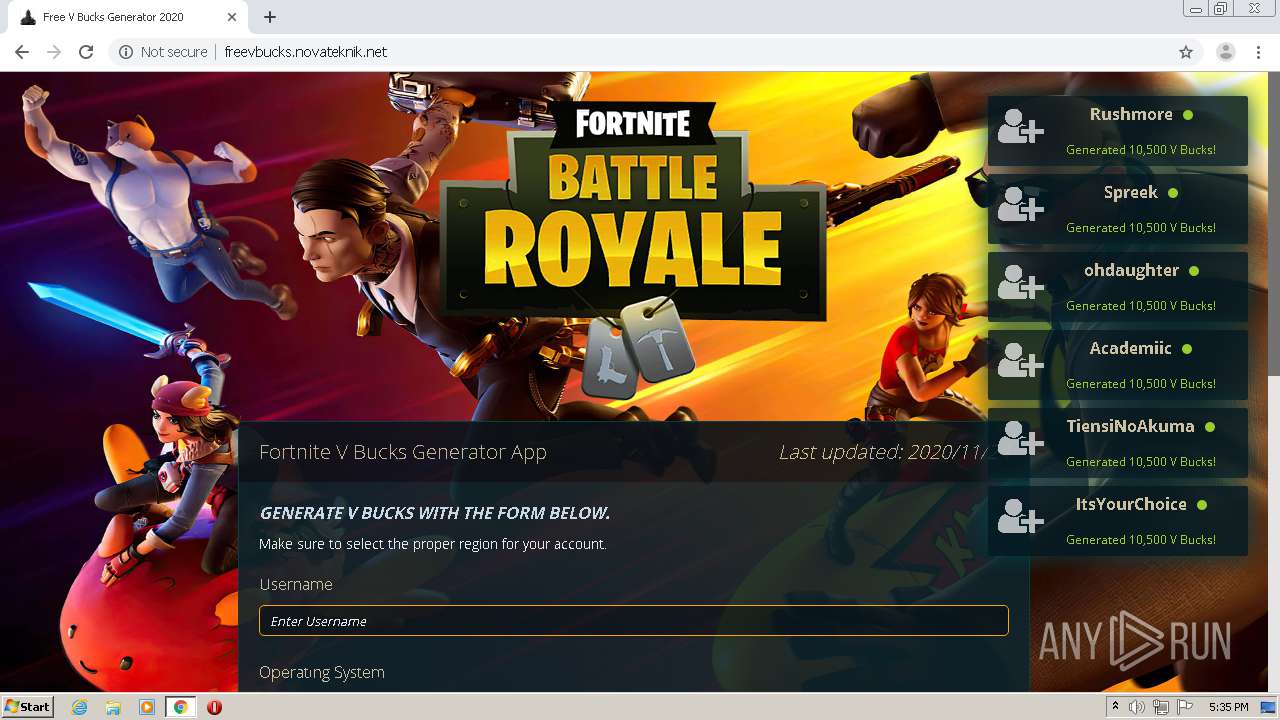
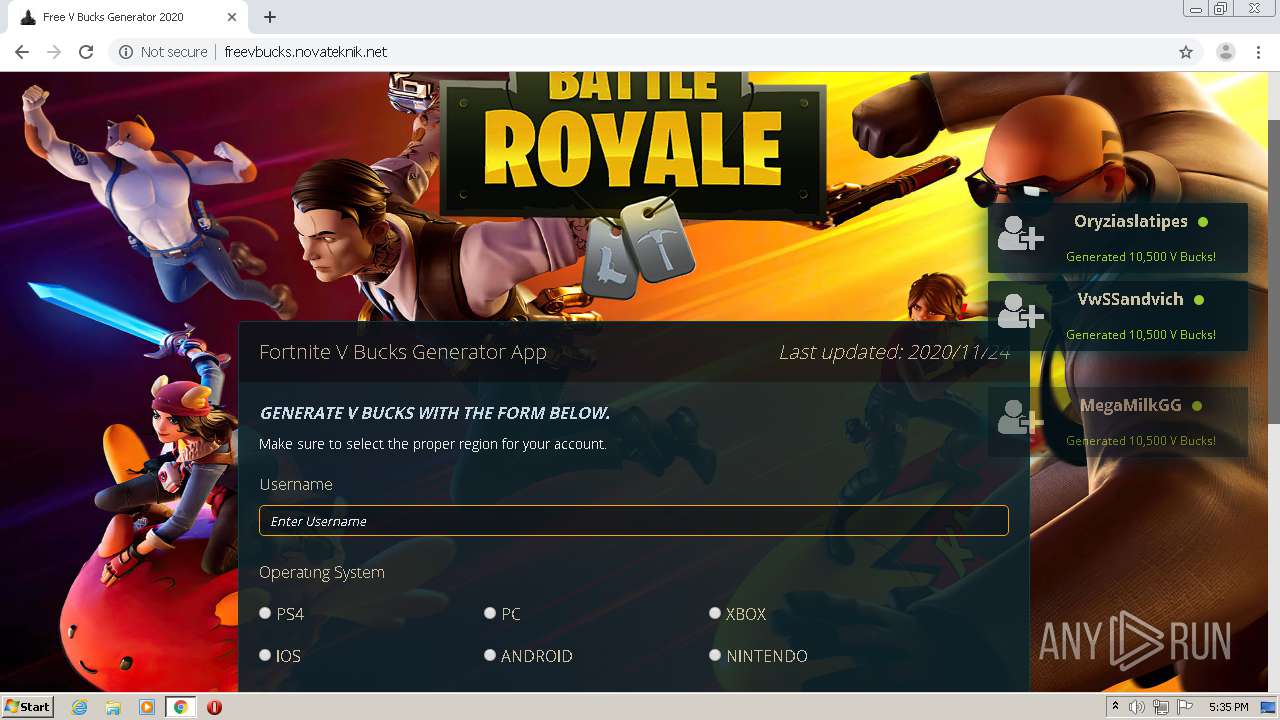
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 17:30:28 |
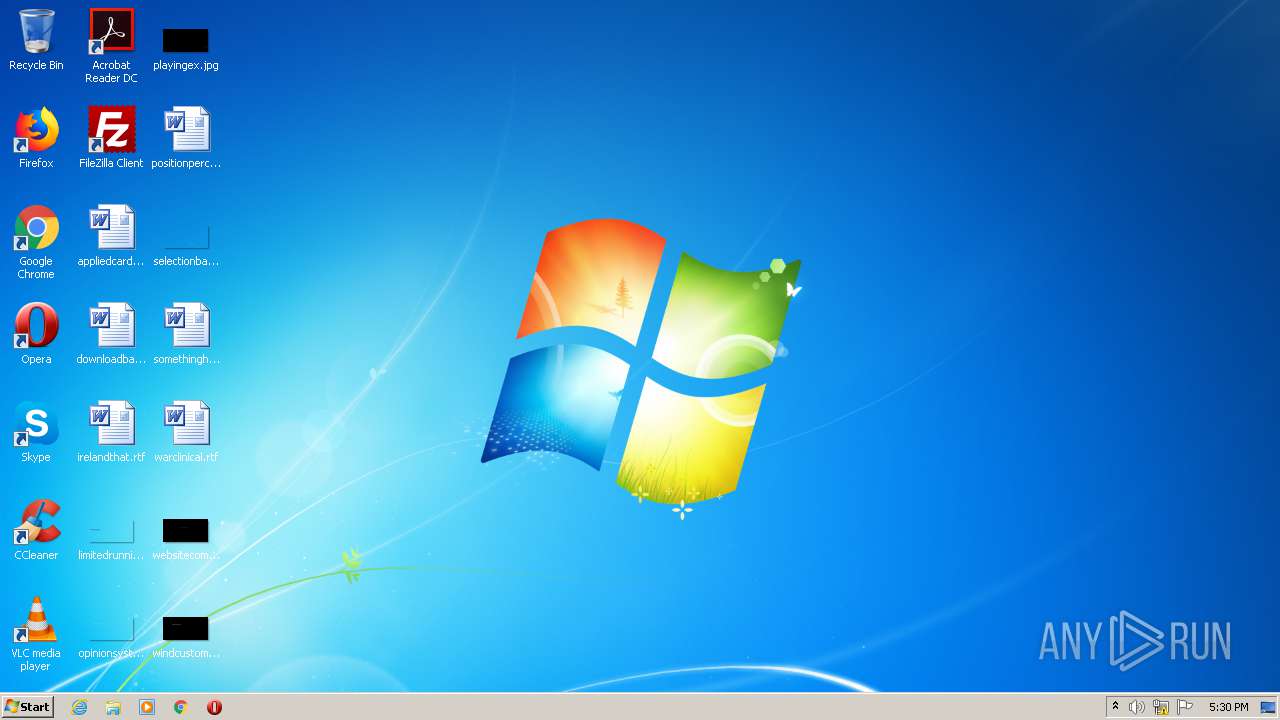
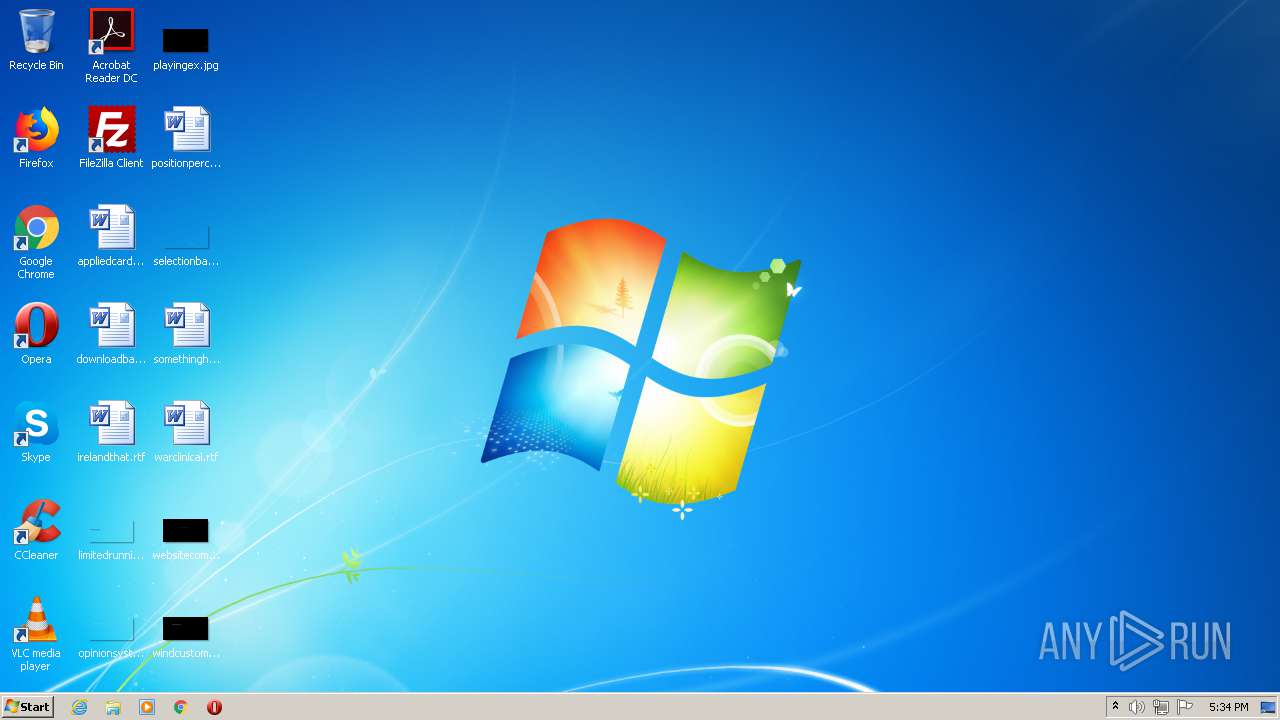
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/png |
| File info: | PNG image data, 768 x 432, 8-bit/color RGBA, non-interlaced |
| MD5: | CB2F9F801DA0FE7E1D2A64EBC5B7859F |
| SHA1: | F9BA7035A29BB3B88B97E98B5EE0E62E1CFABA22 |
| SHA256: | 26FB2BC614296744C511B9180F5C0D919FD87162947D9C28243125E76068D056 |
| SSDEEP: | 12288:SfvP1Ut4kemV9YdAnPDMSf24oW8WN7imUVBrhacxJ0lUsexYNE:SnP1UikemXbMStDYVZhclyYNE |
MALICIOUS
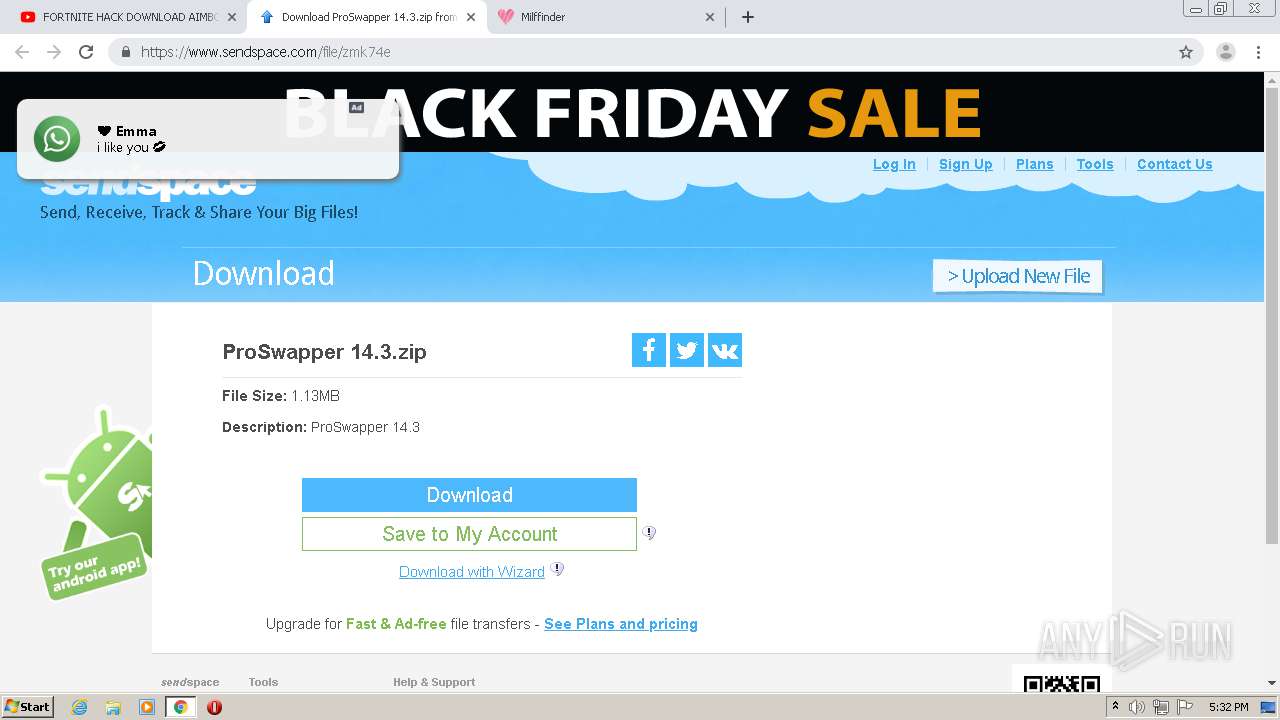
No malicious indicators.SUSPICIOUS
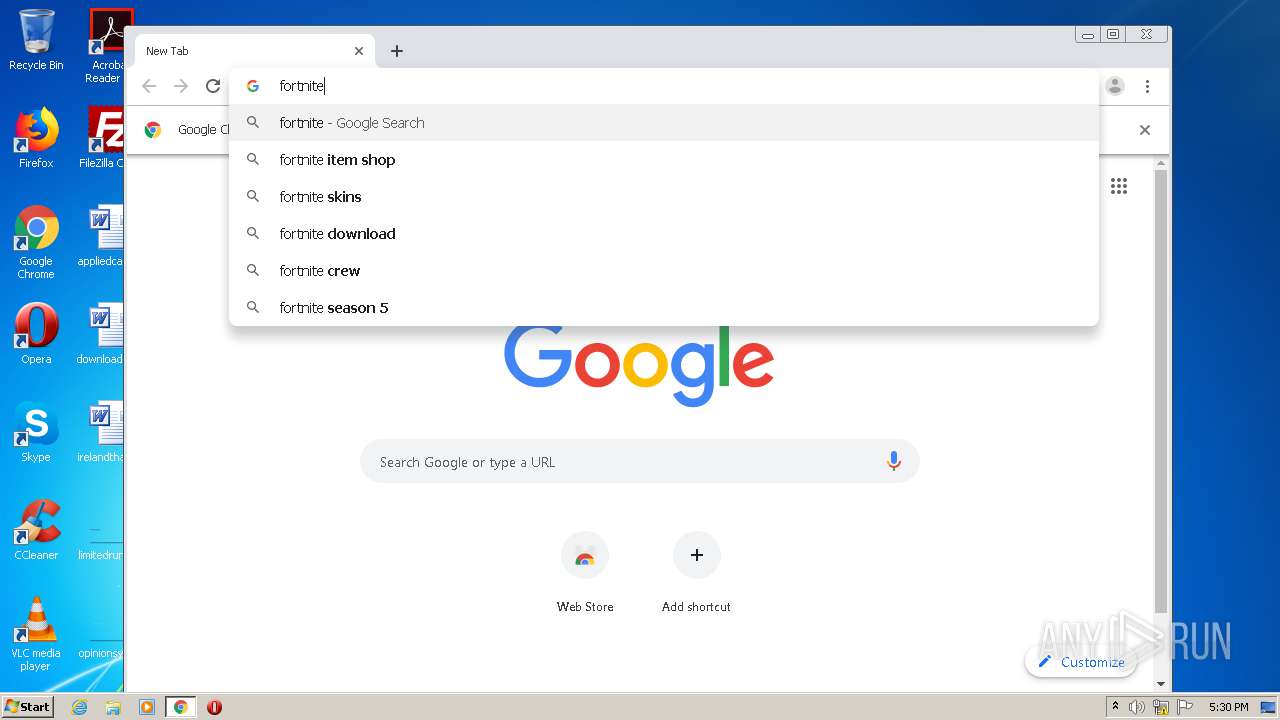
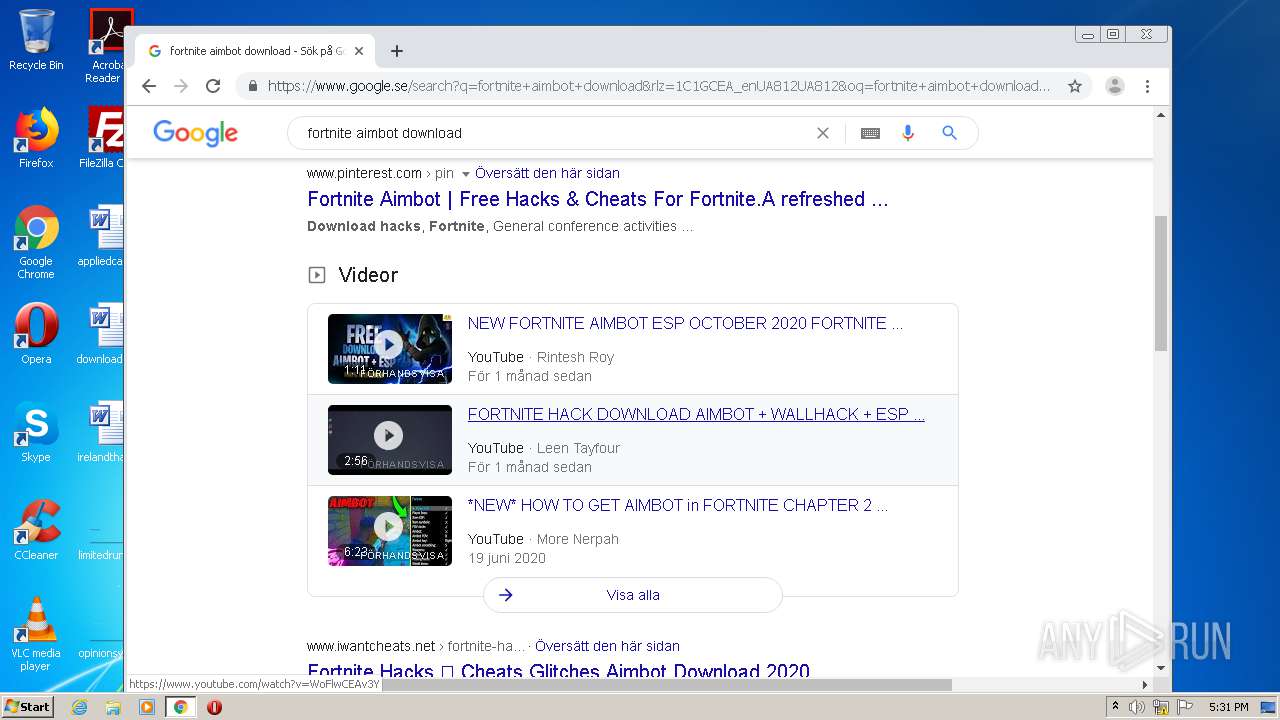
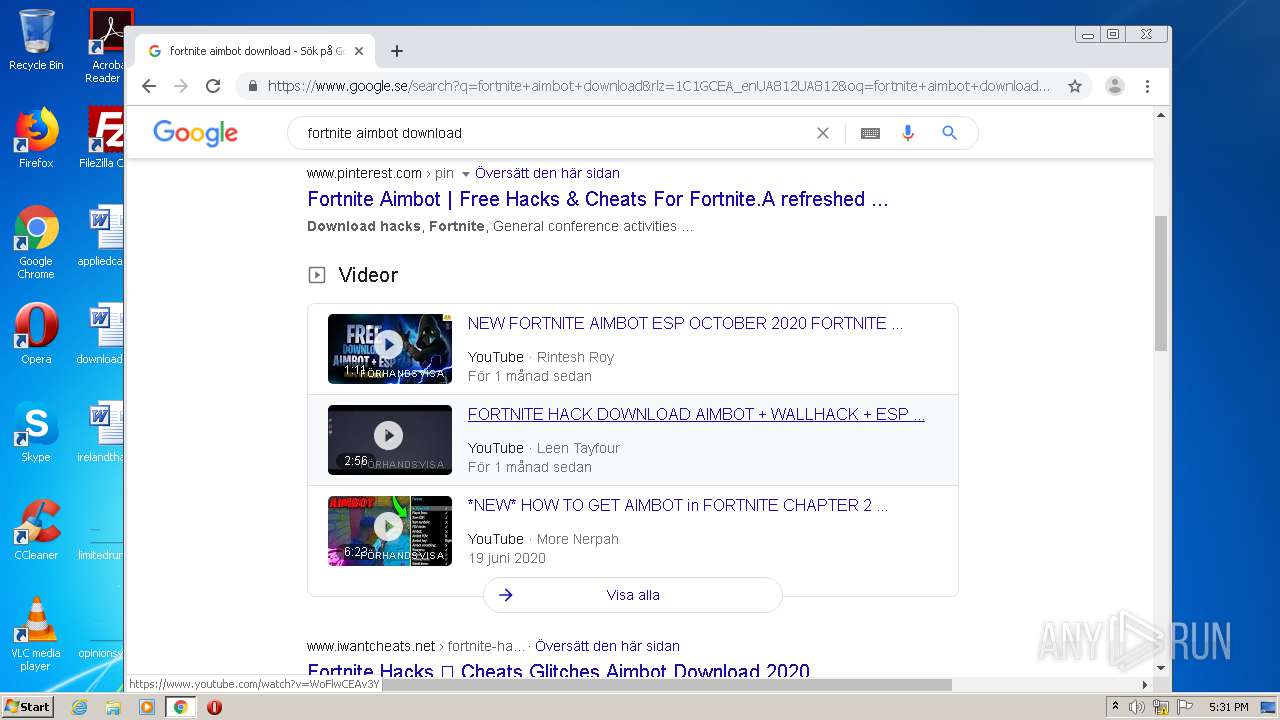
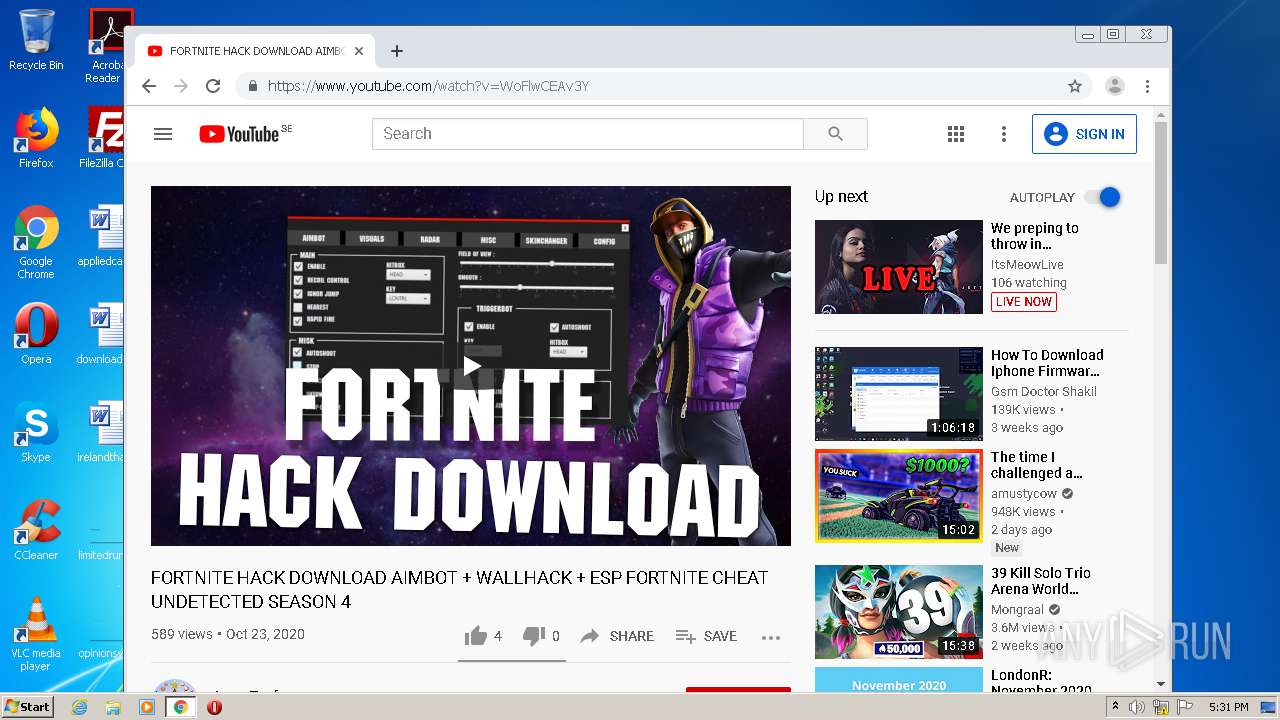
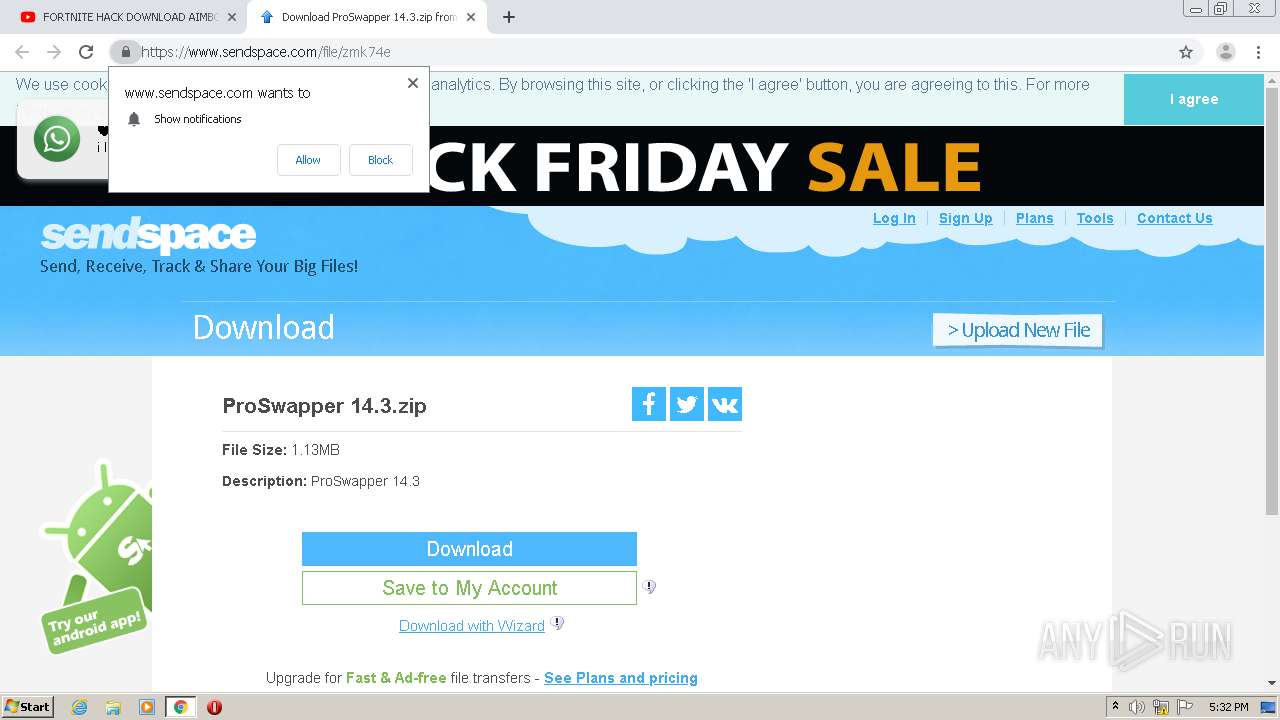
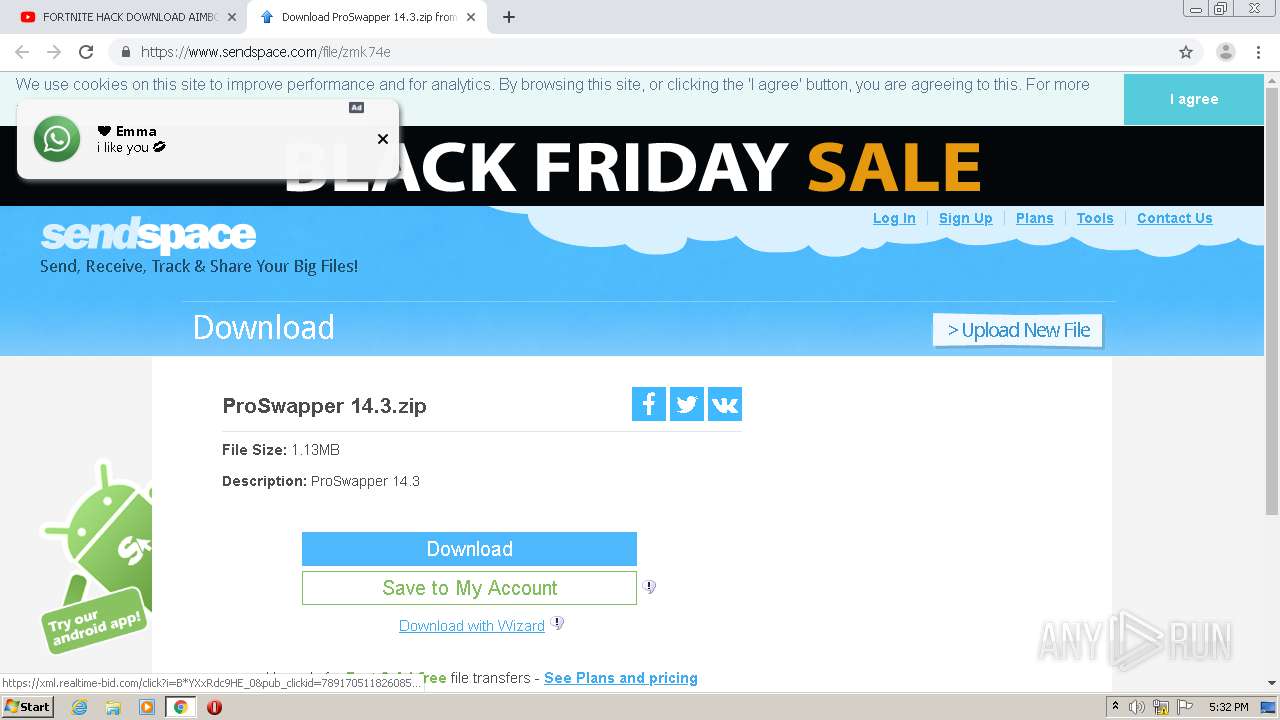
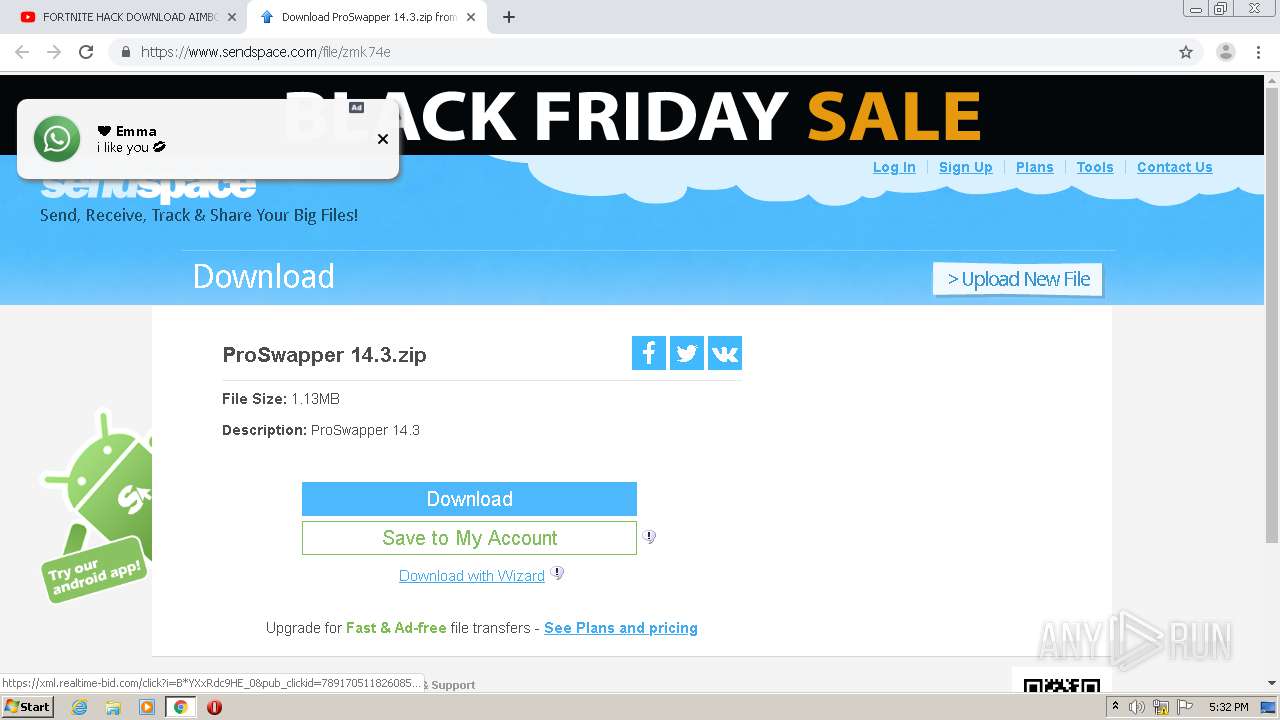
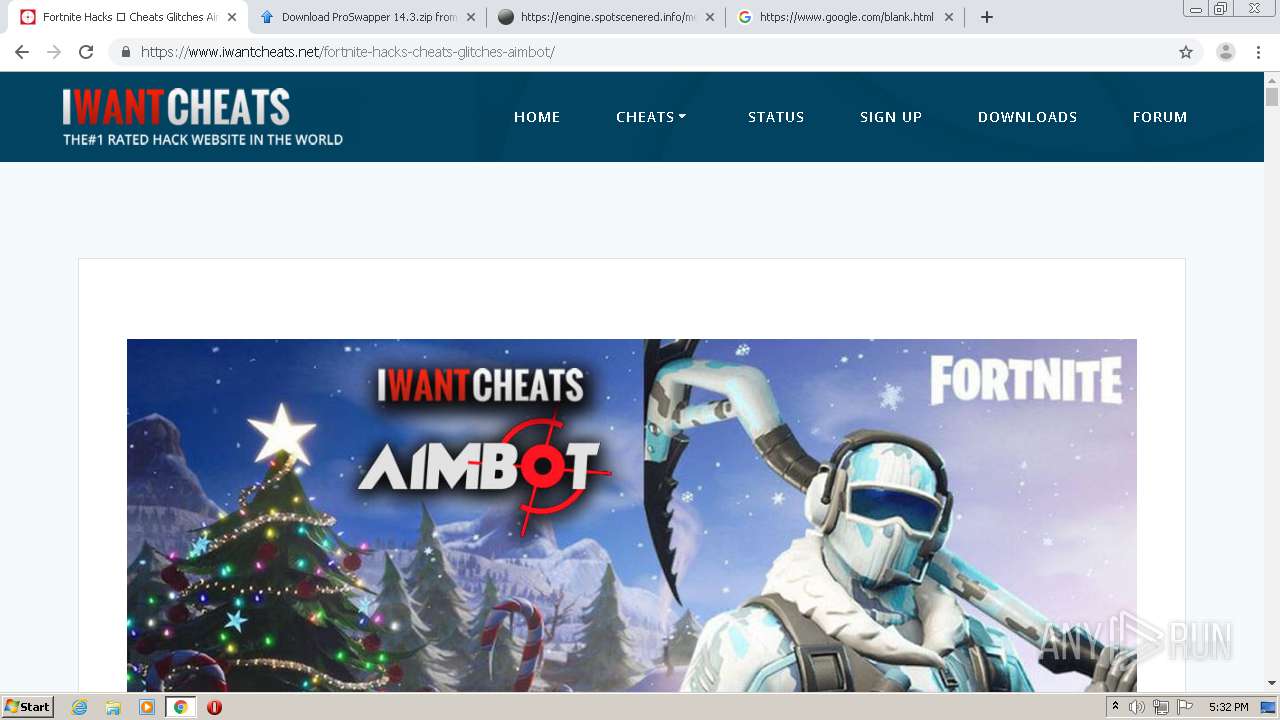
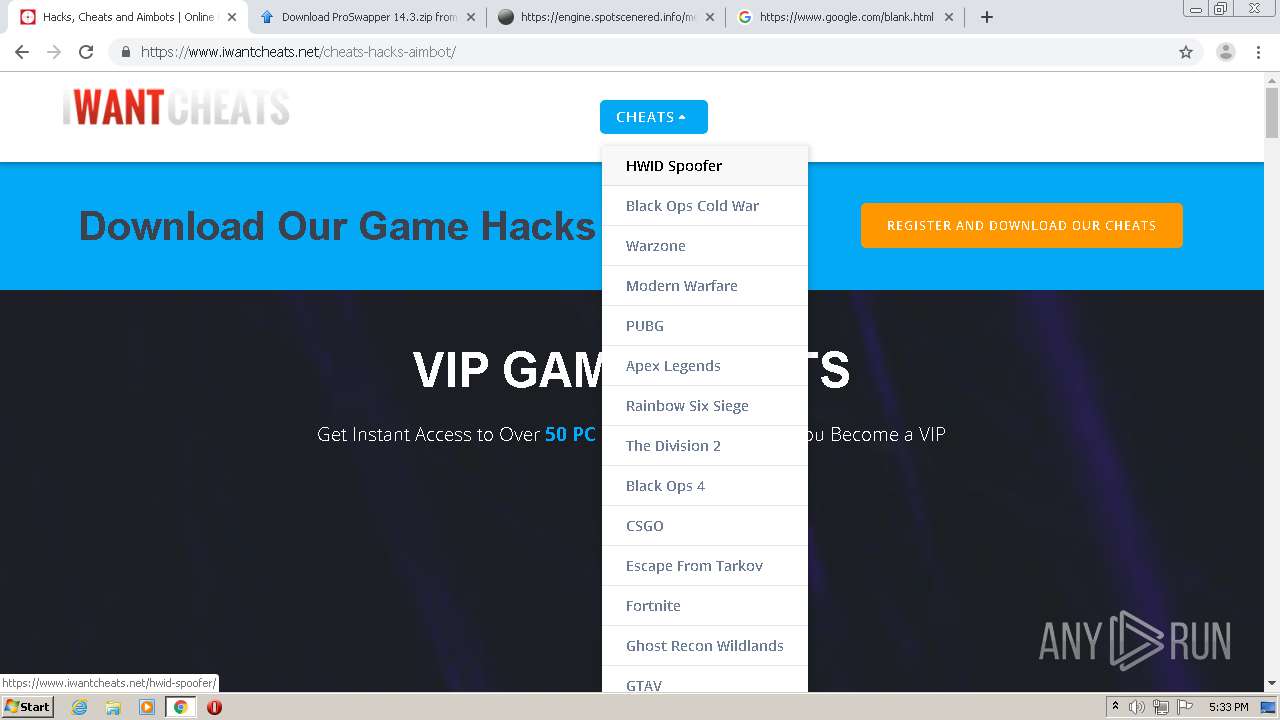
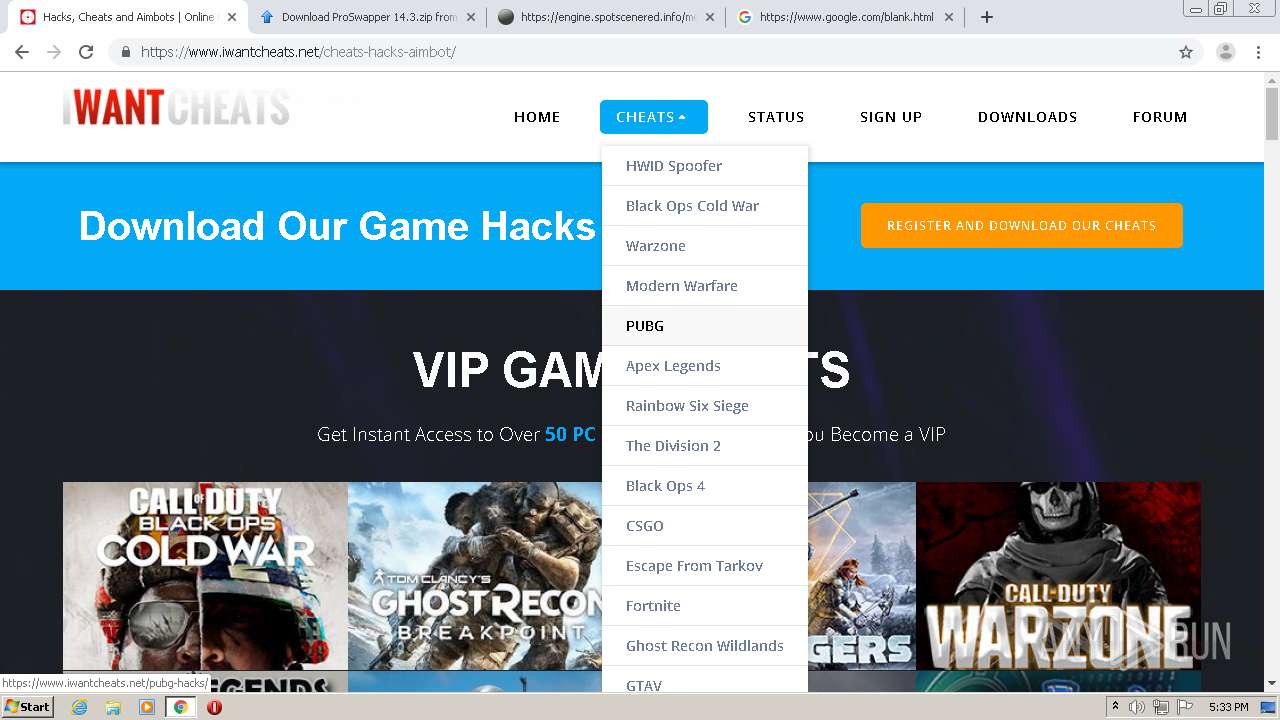
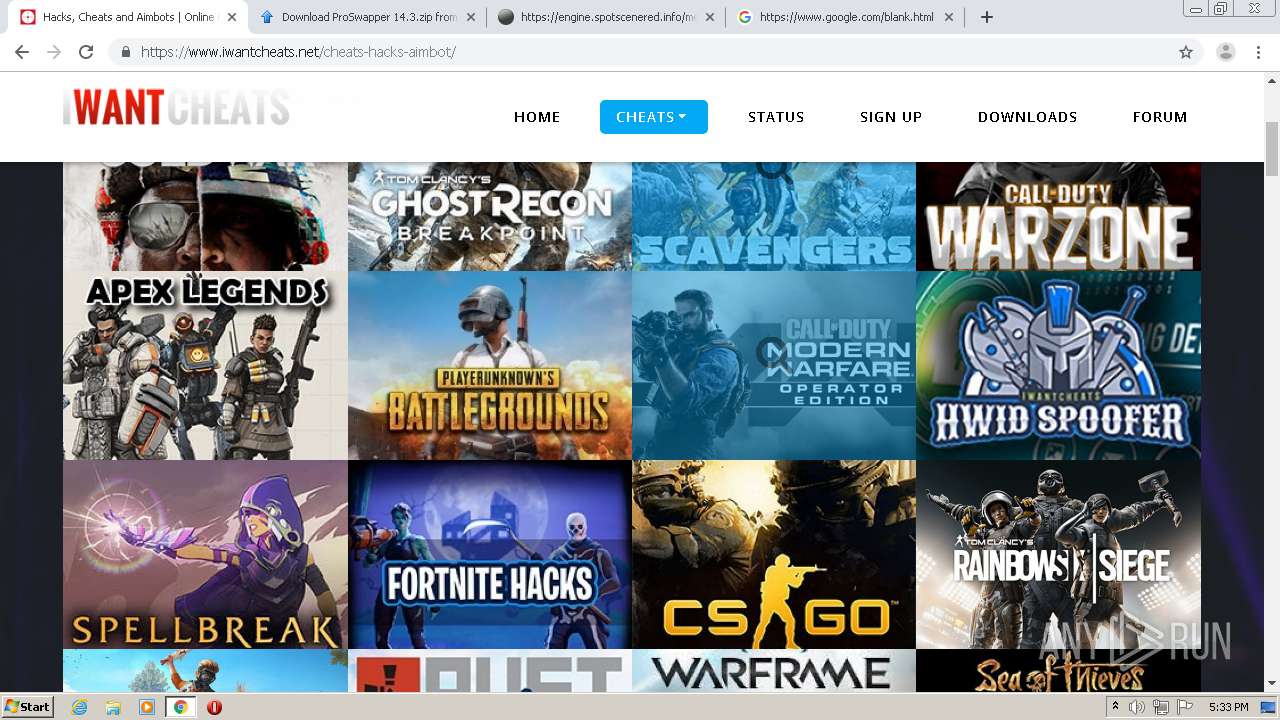
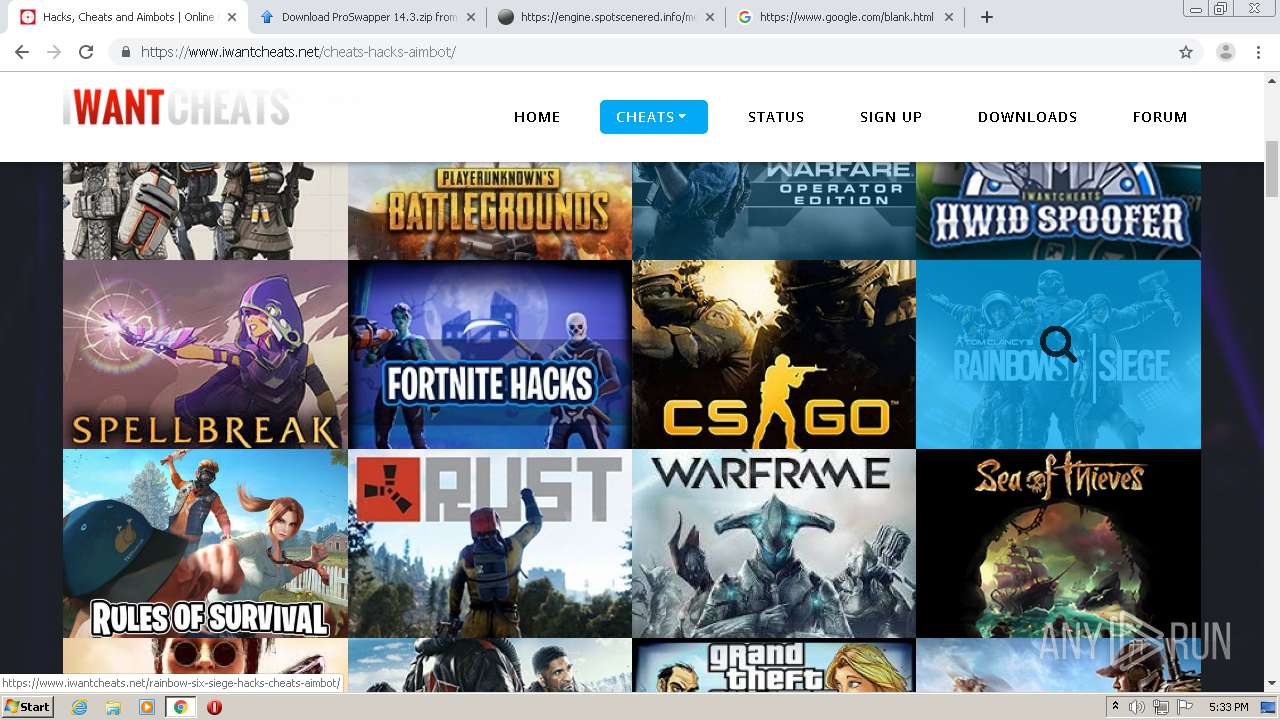
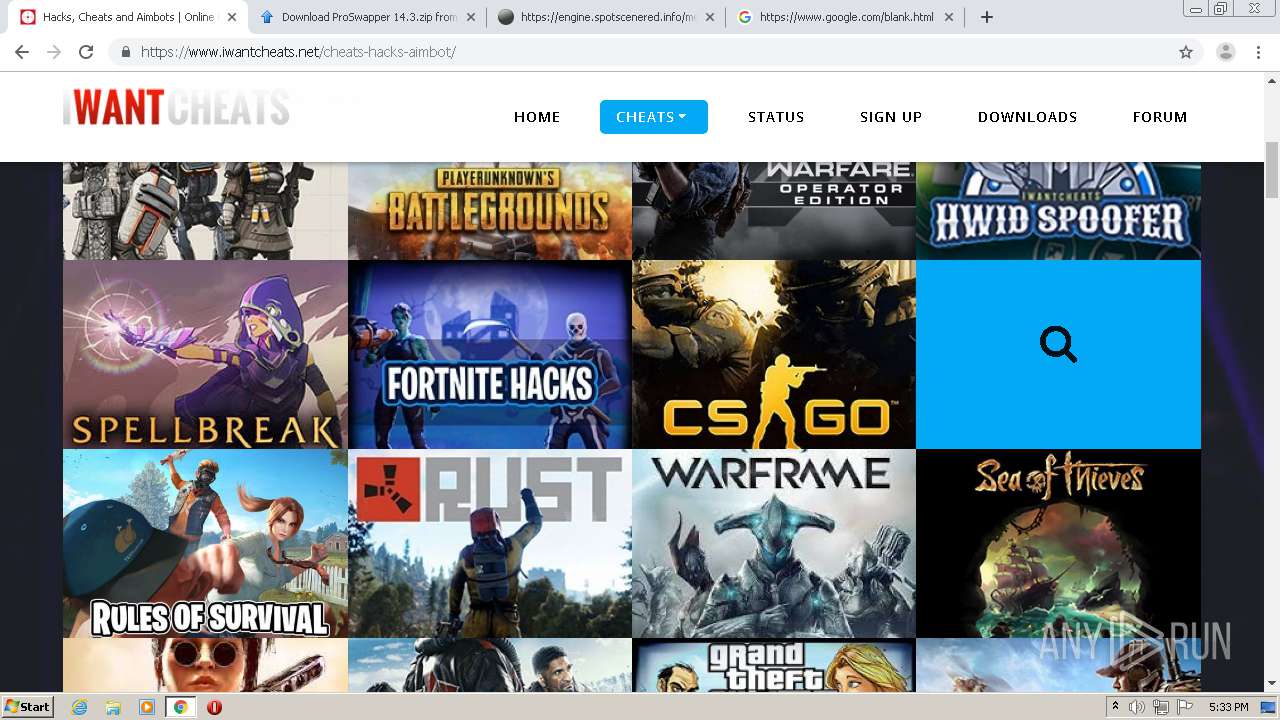
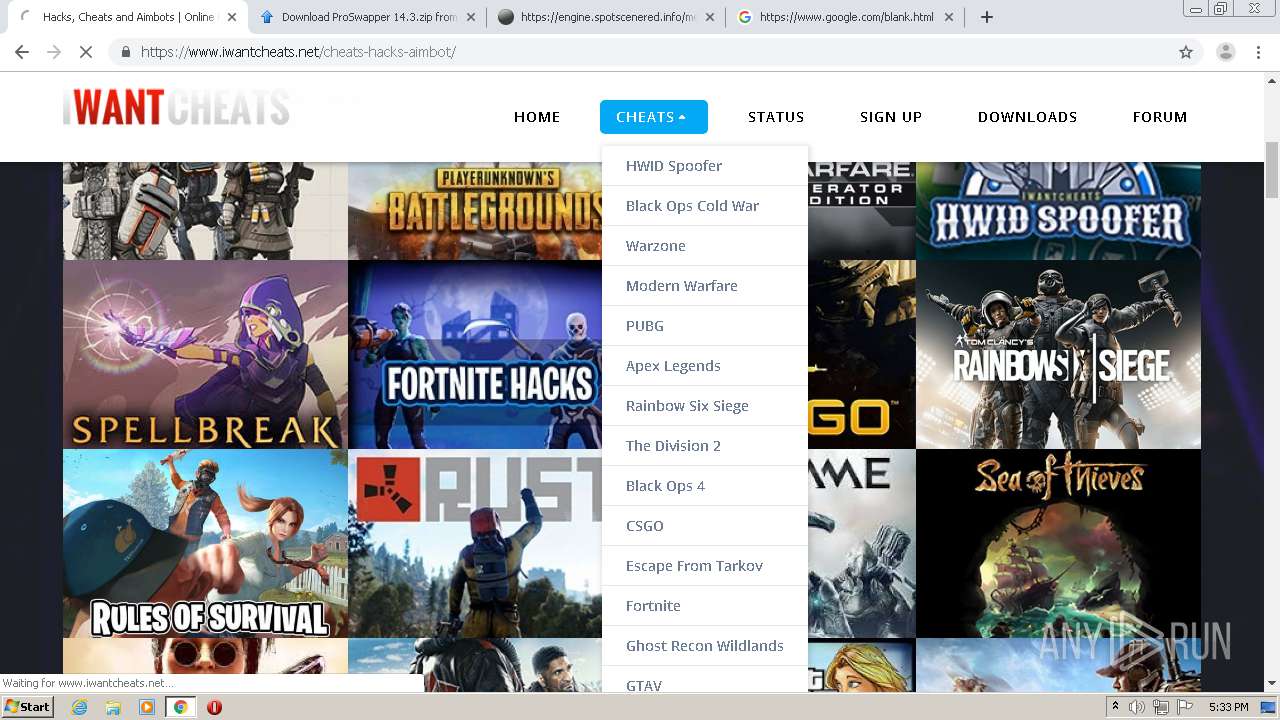
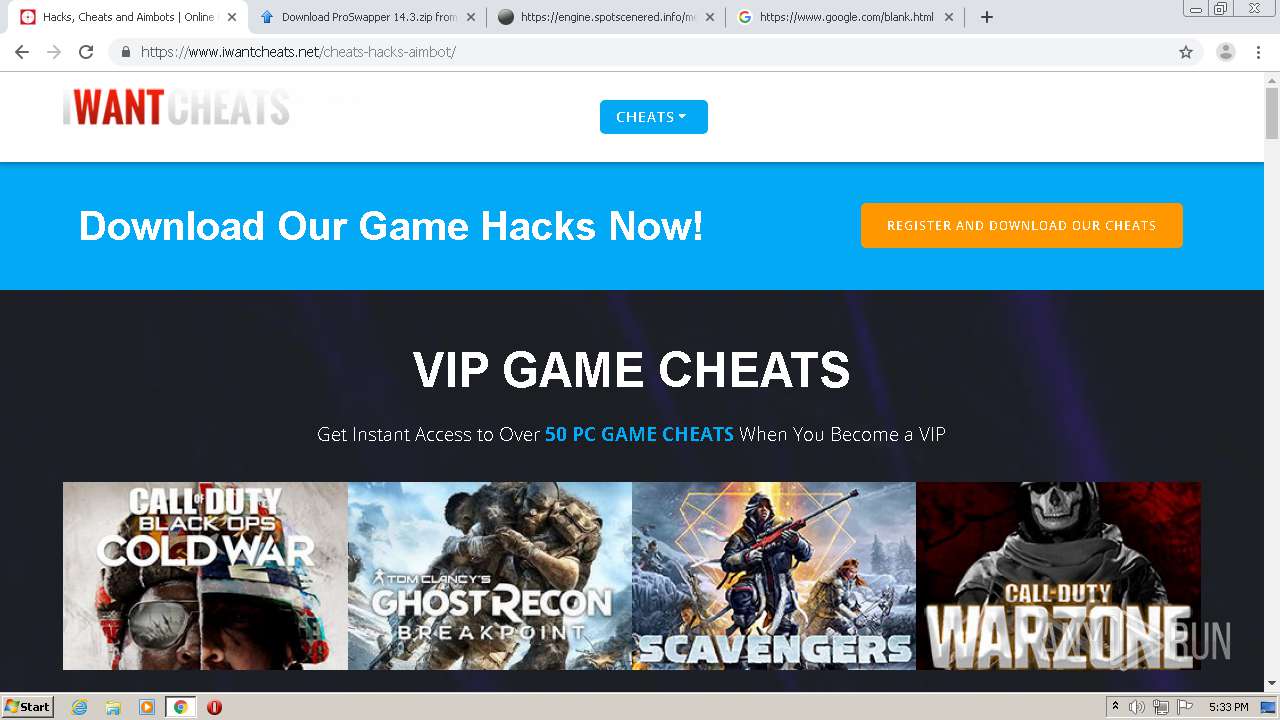
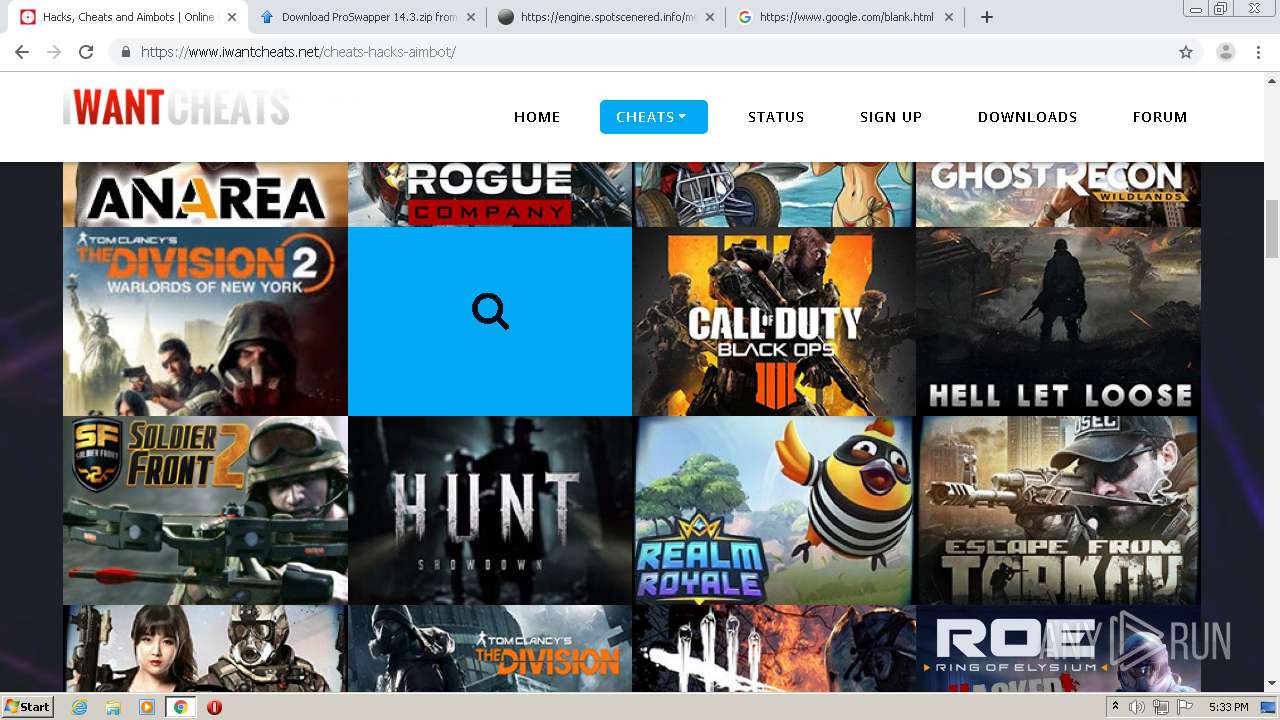
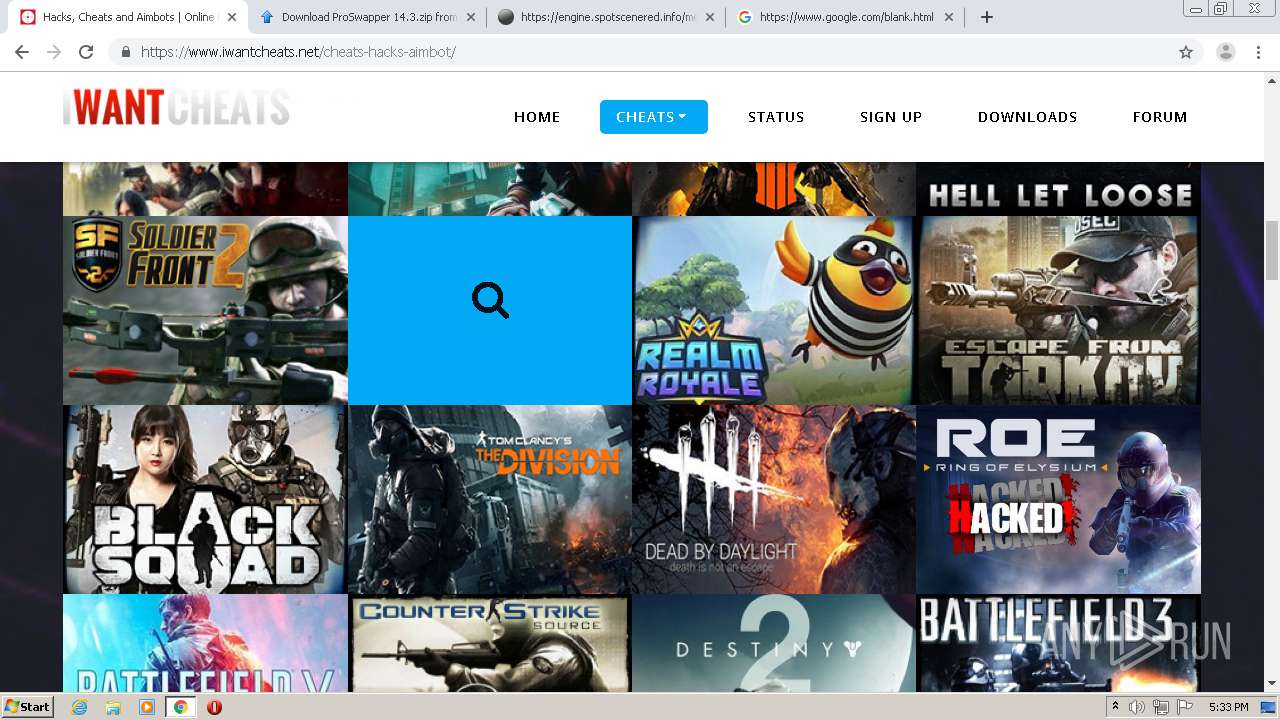
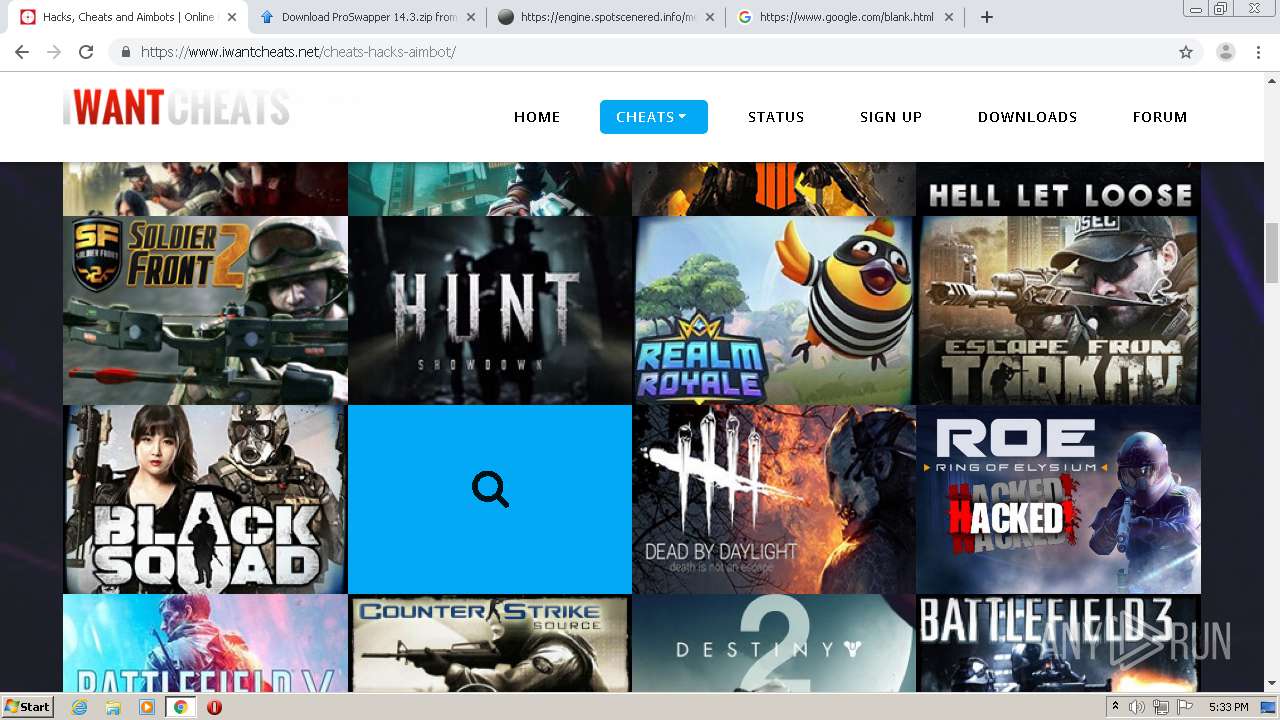
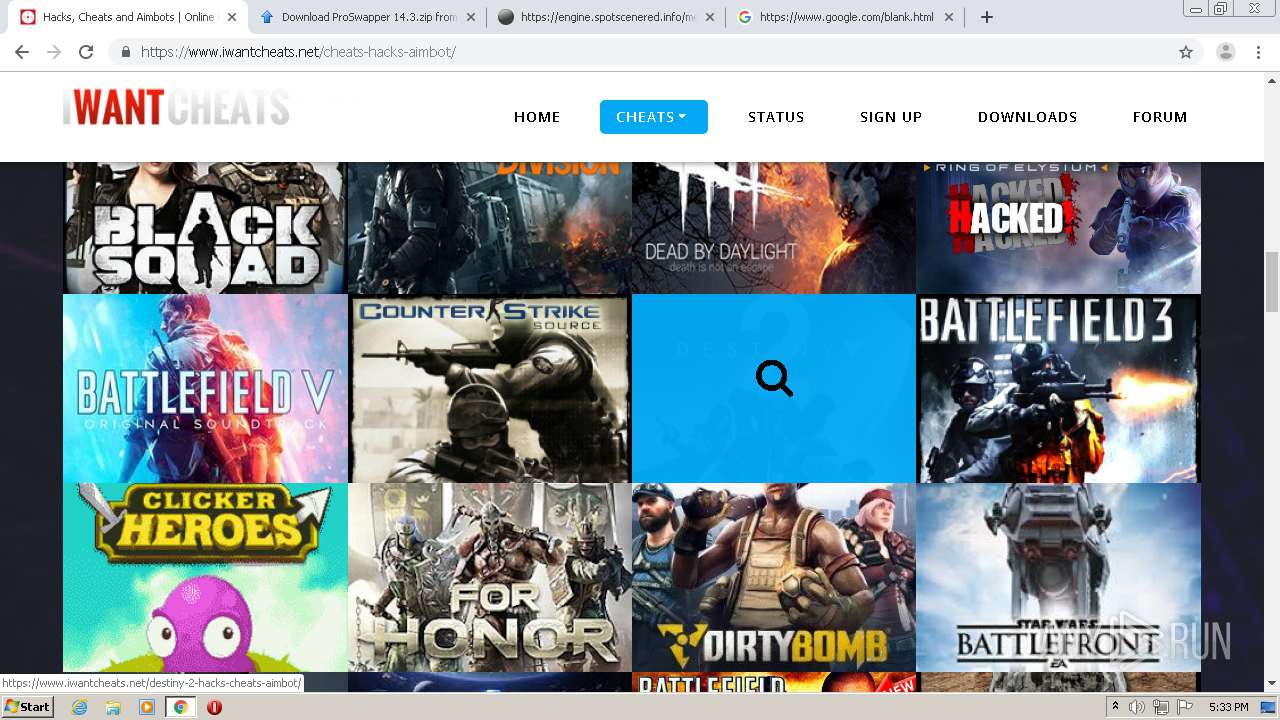
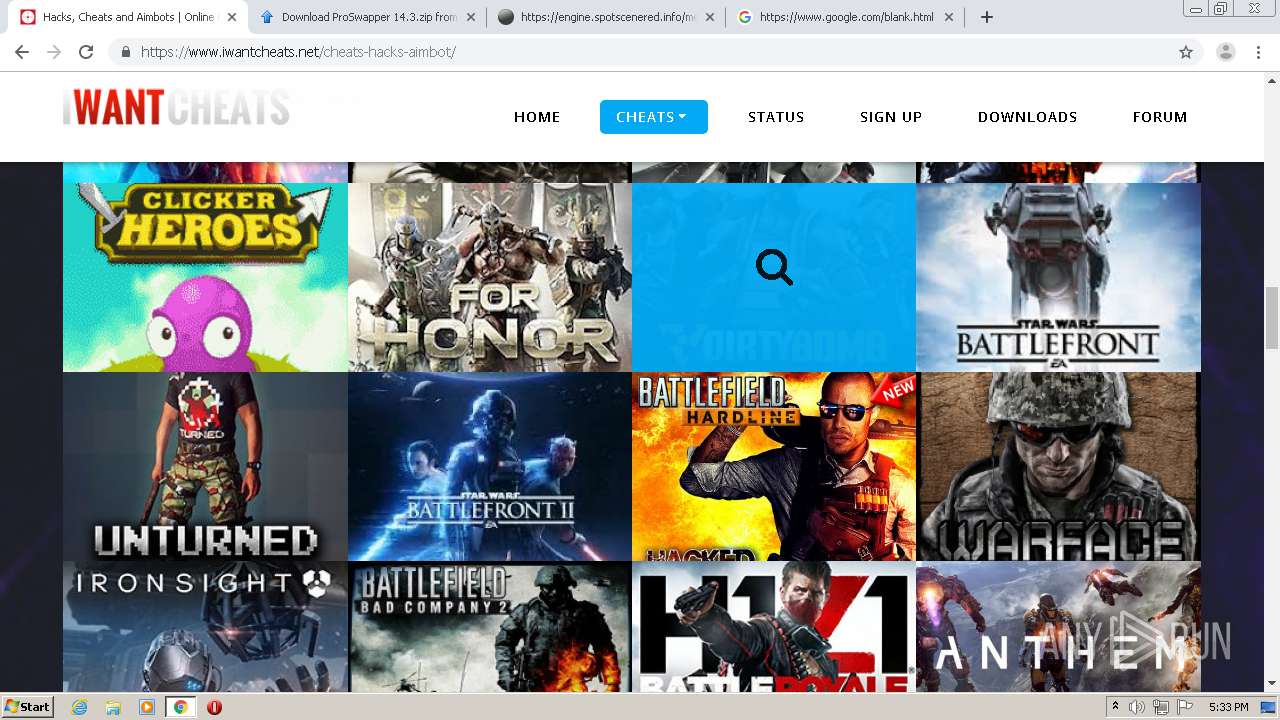
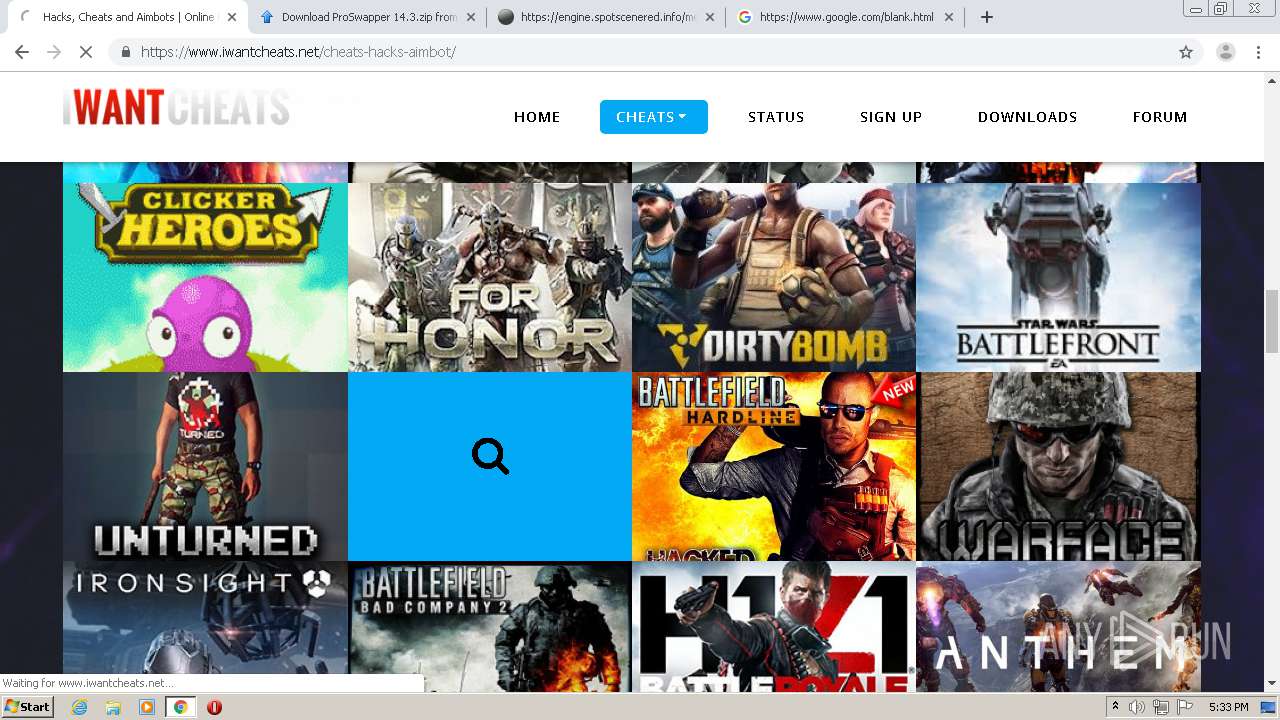
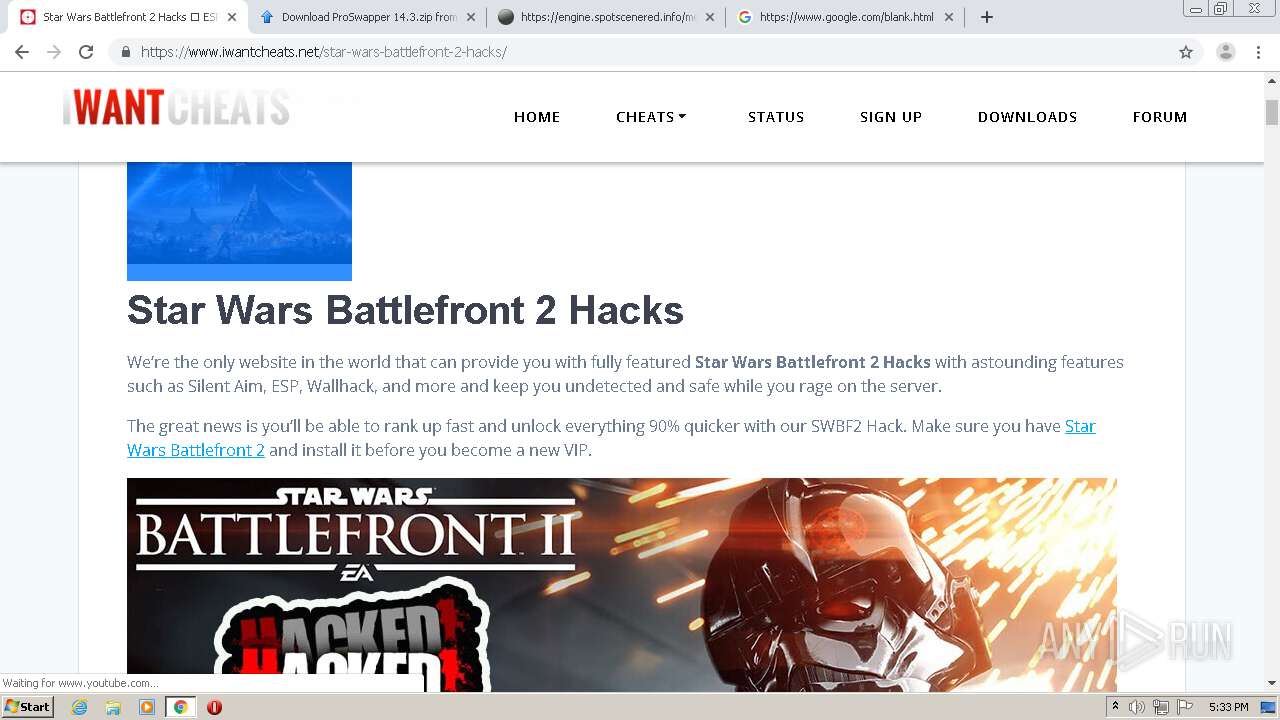
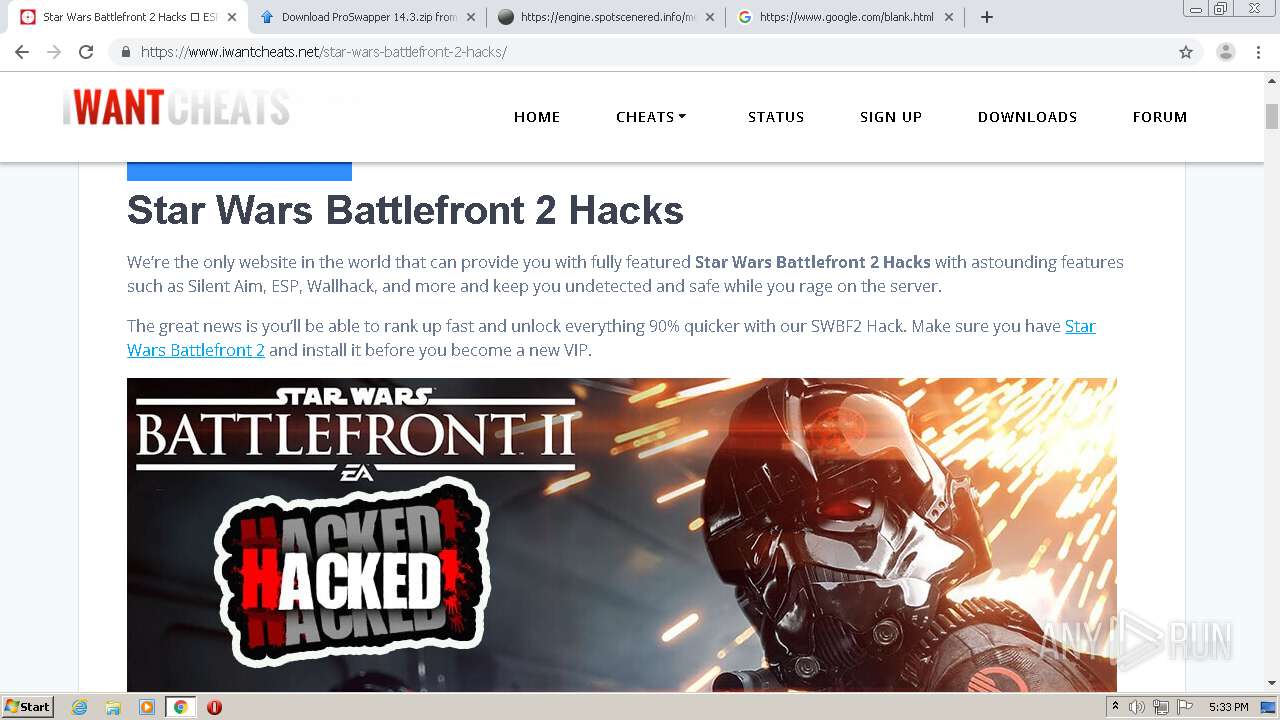
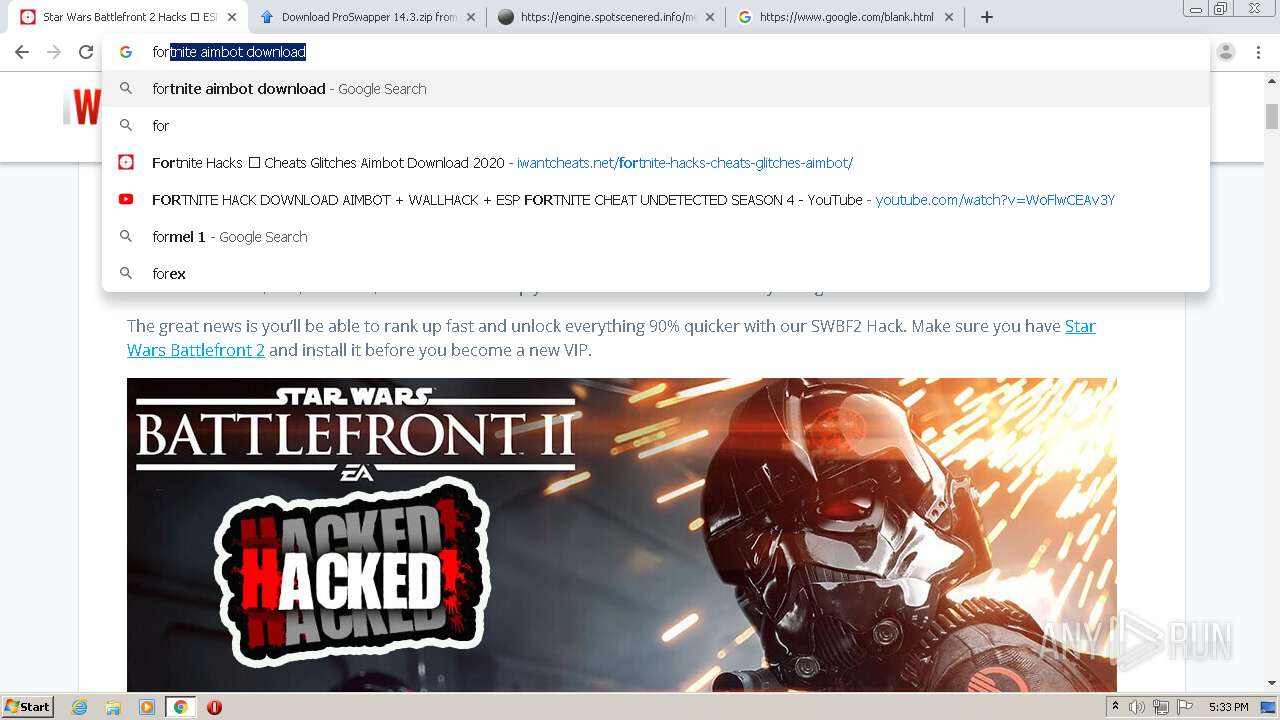
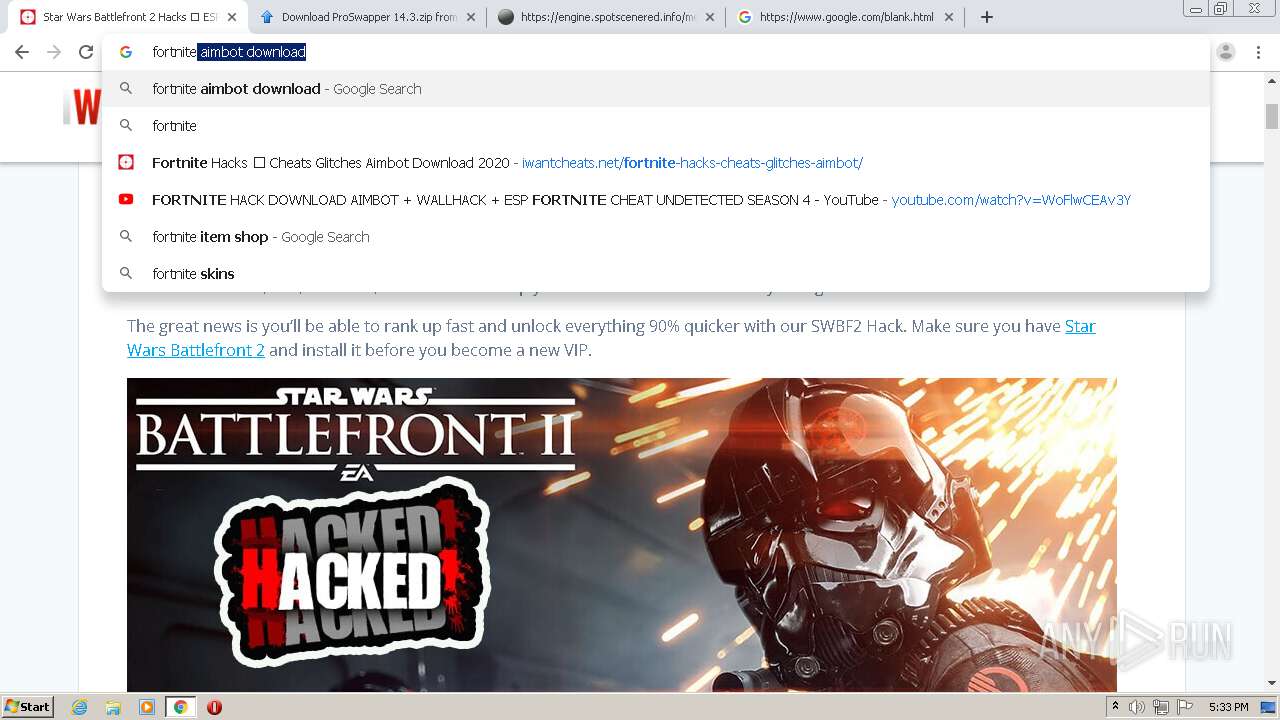
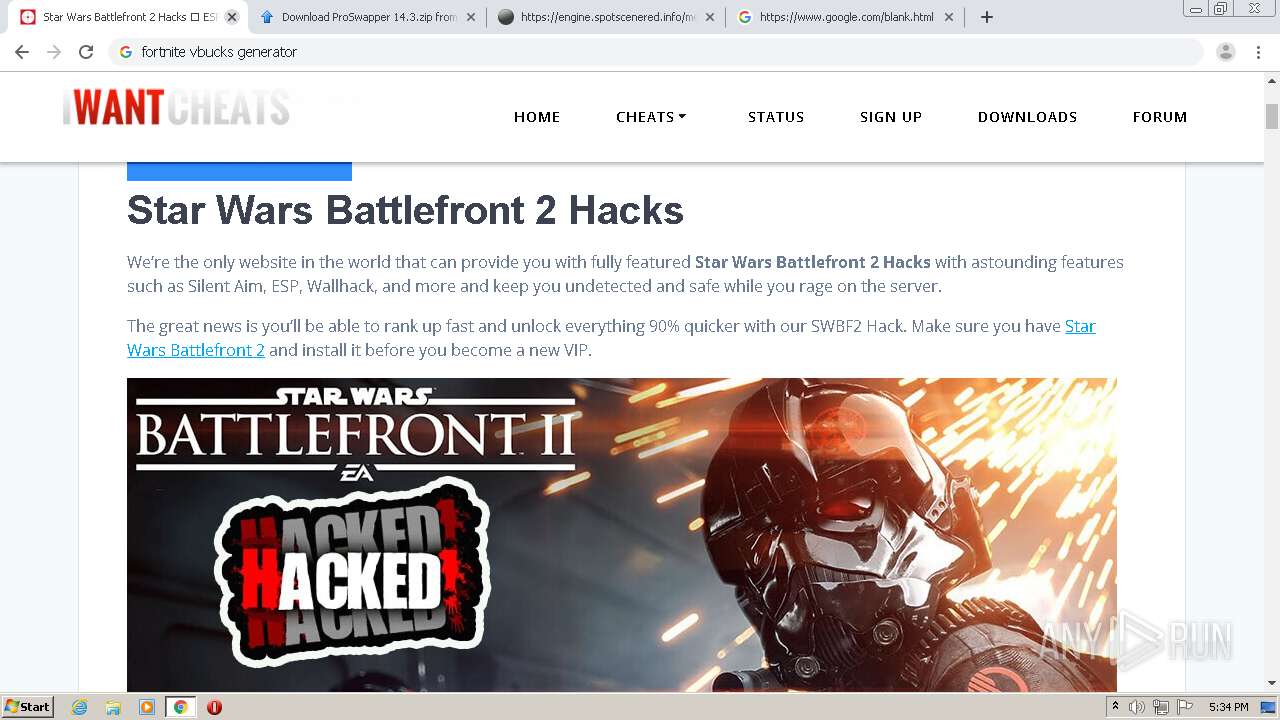
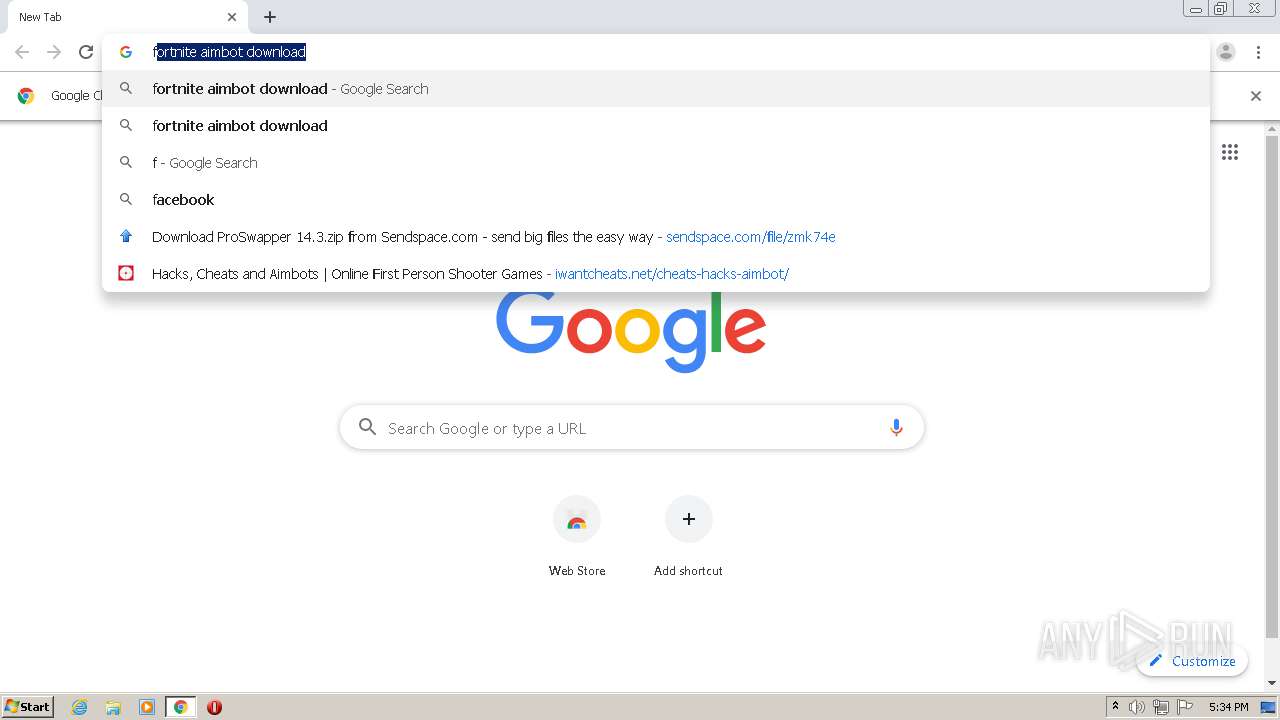
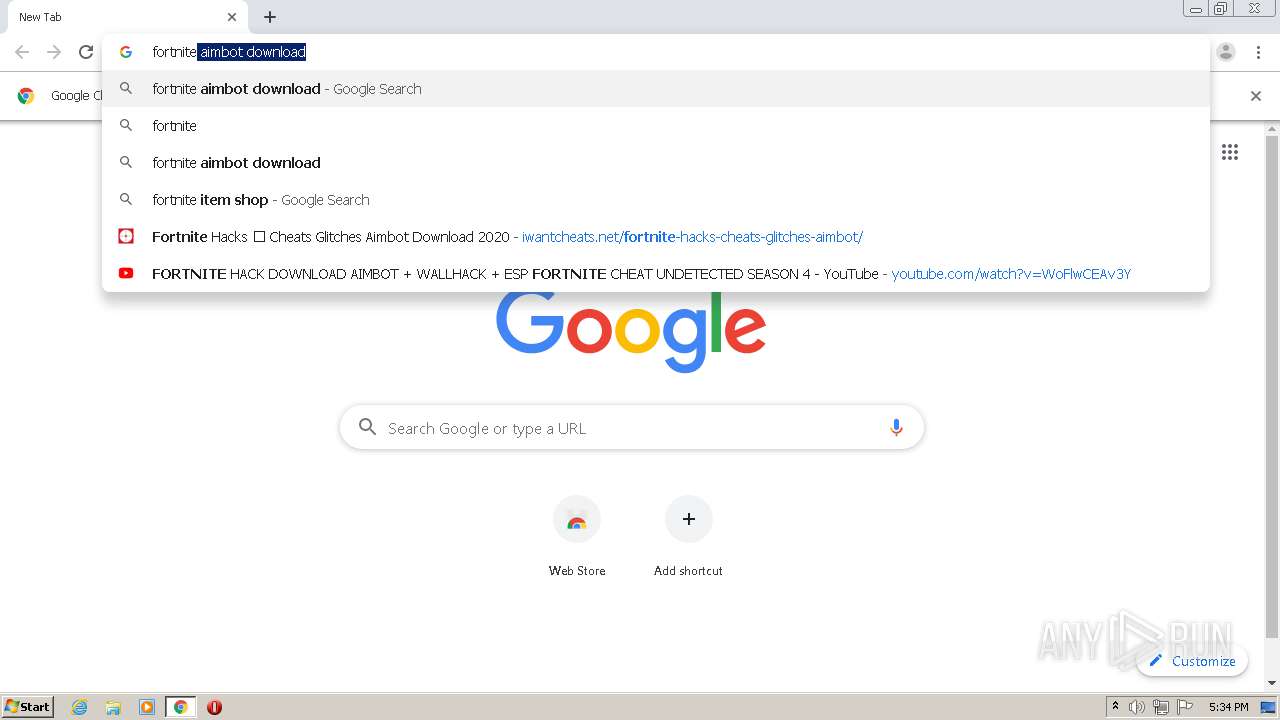
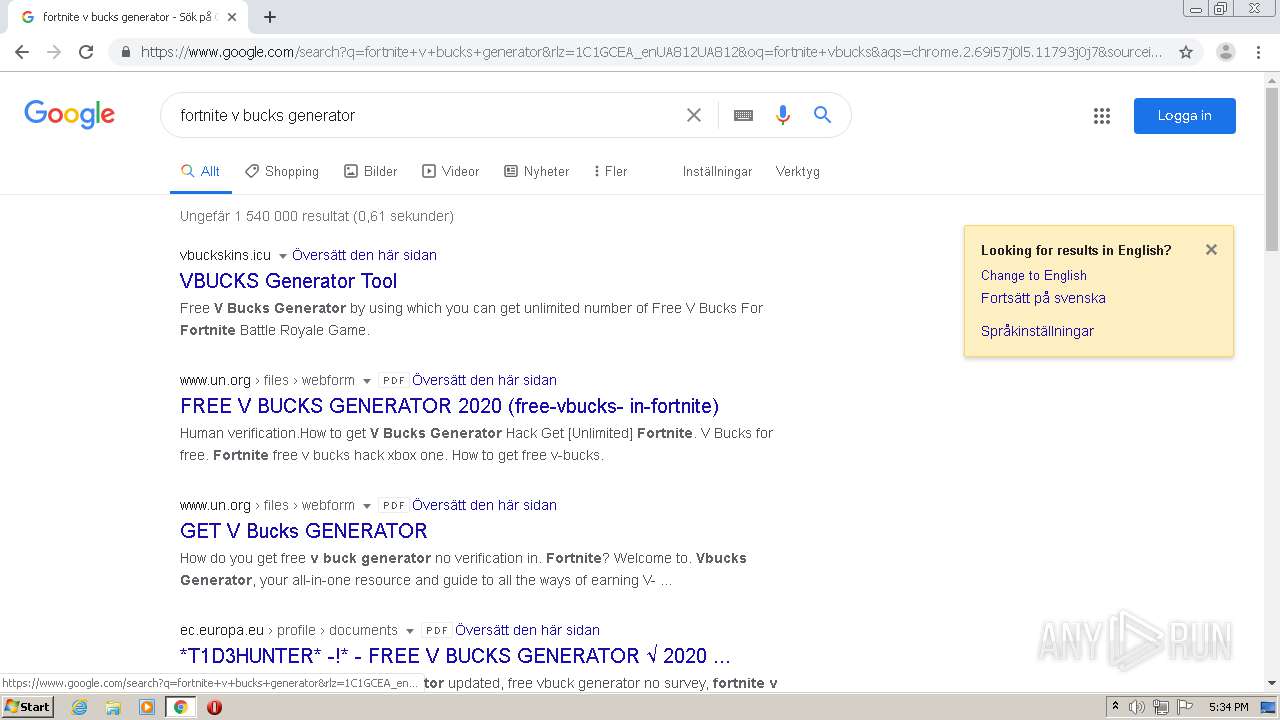
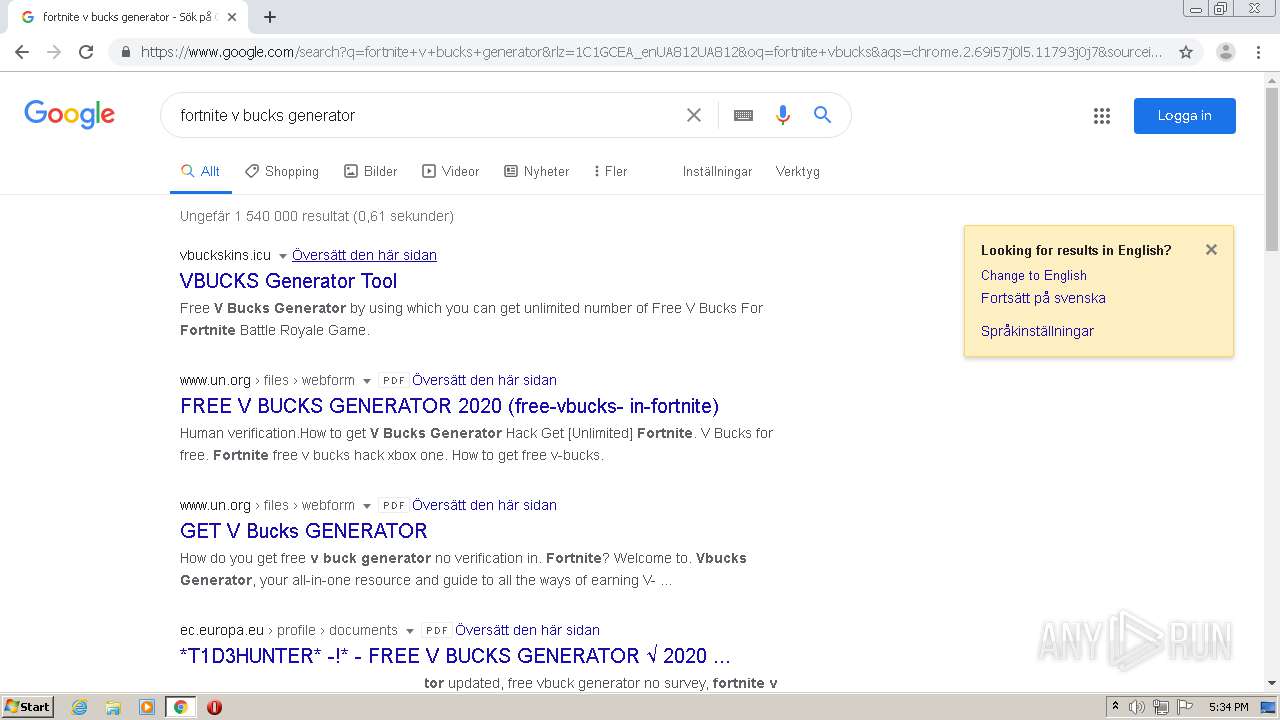
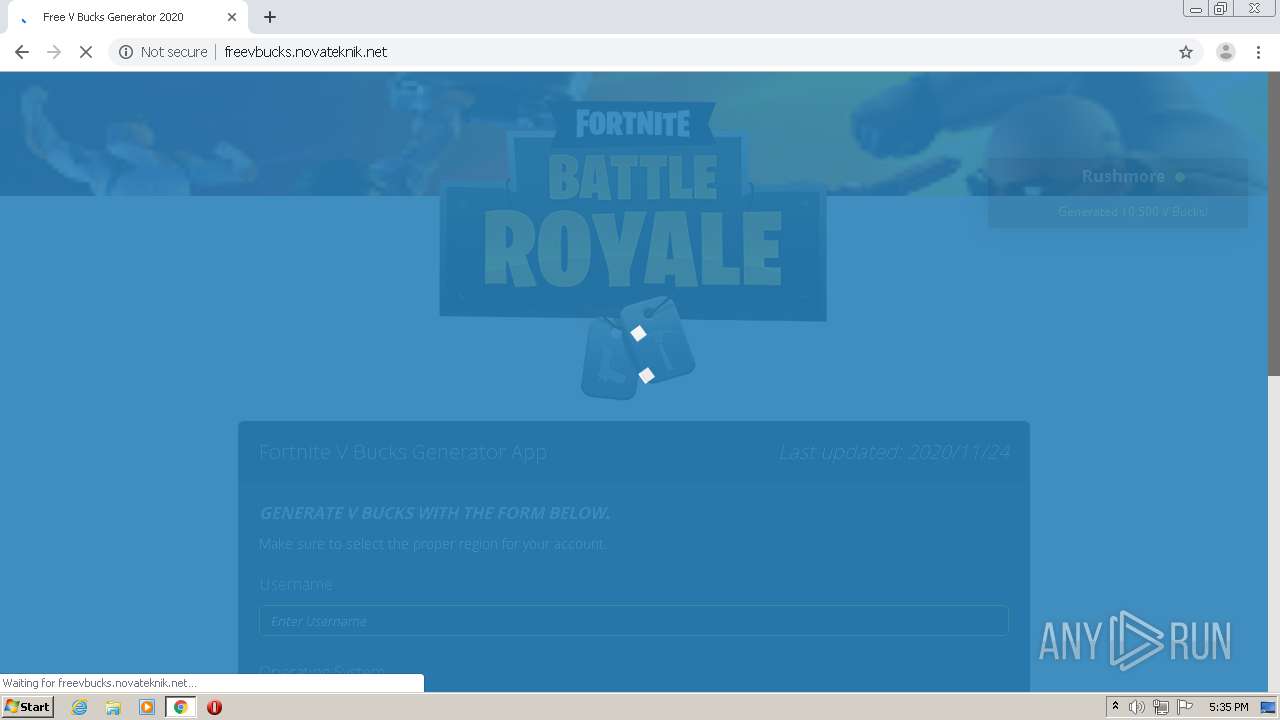
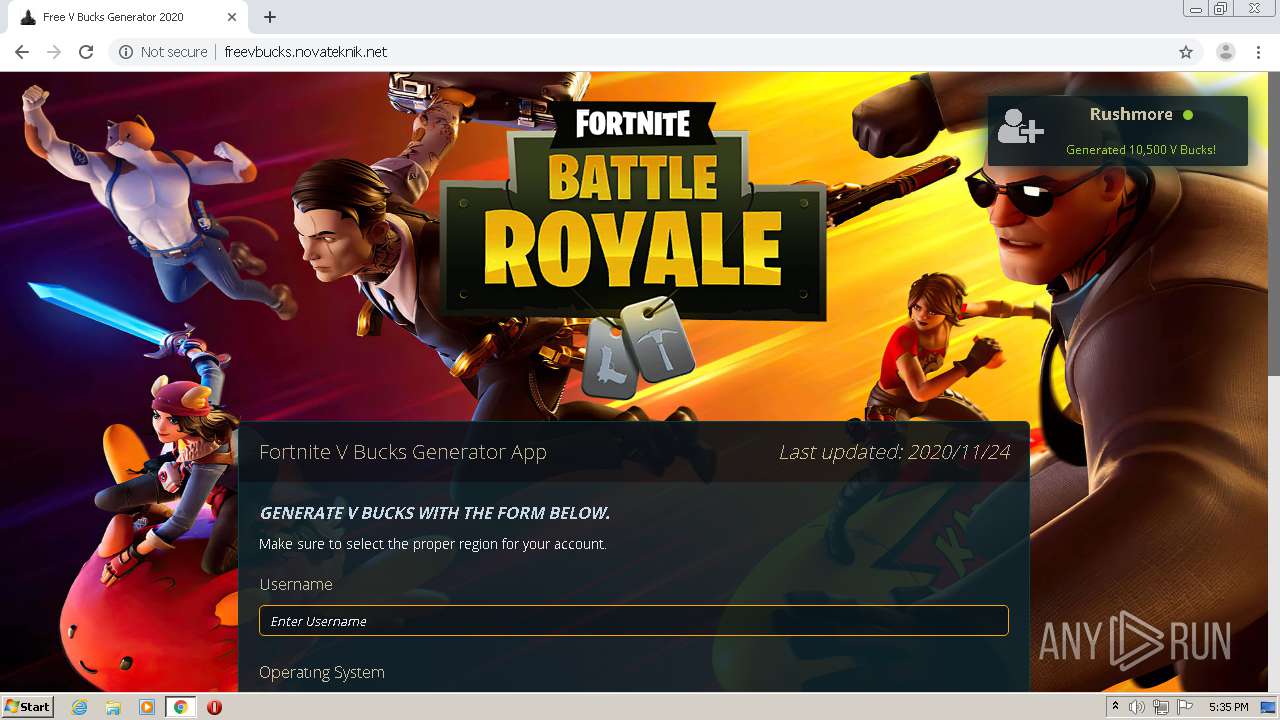
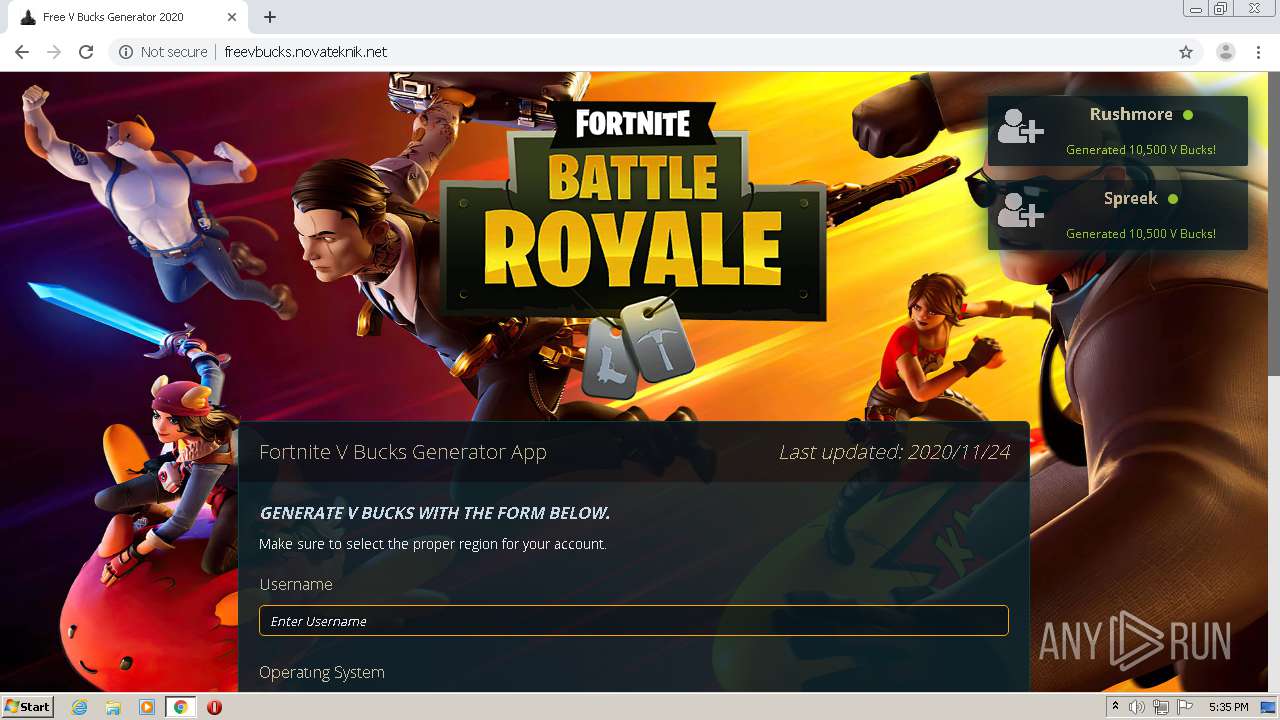
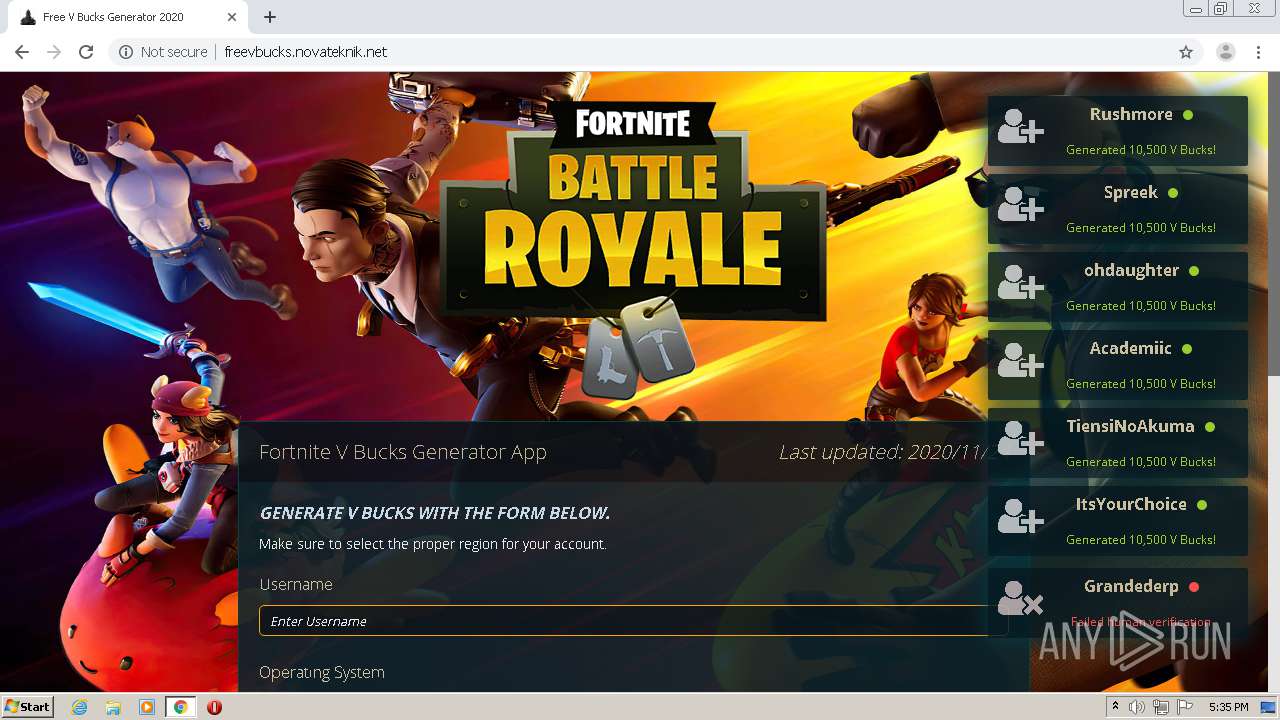
Modifies files in Chrome extension folder
- chrome.exe (PID: 3880)
INFO
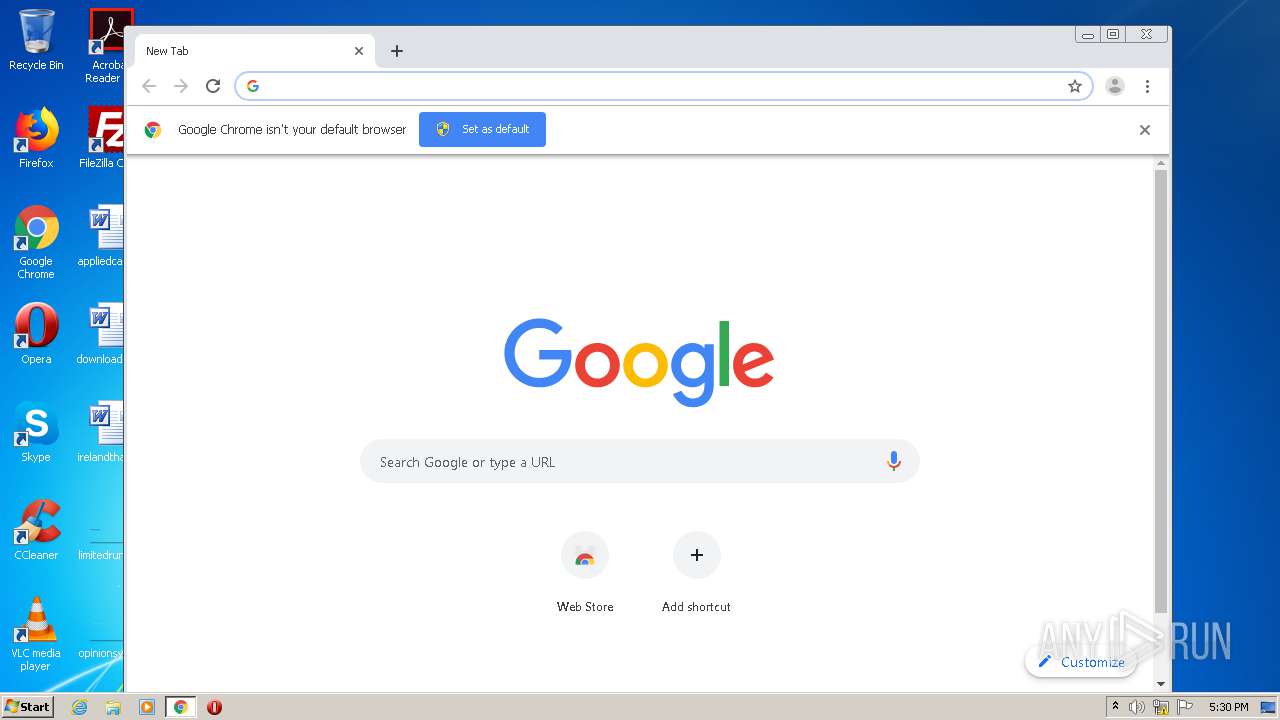
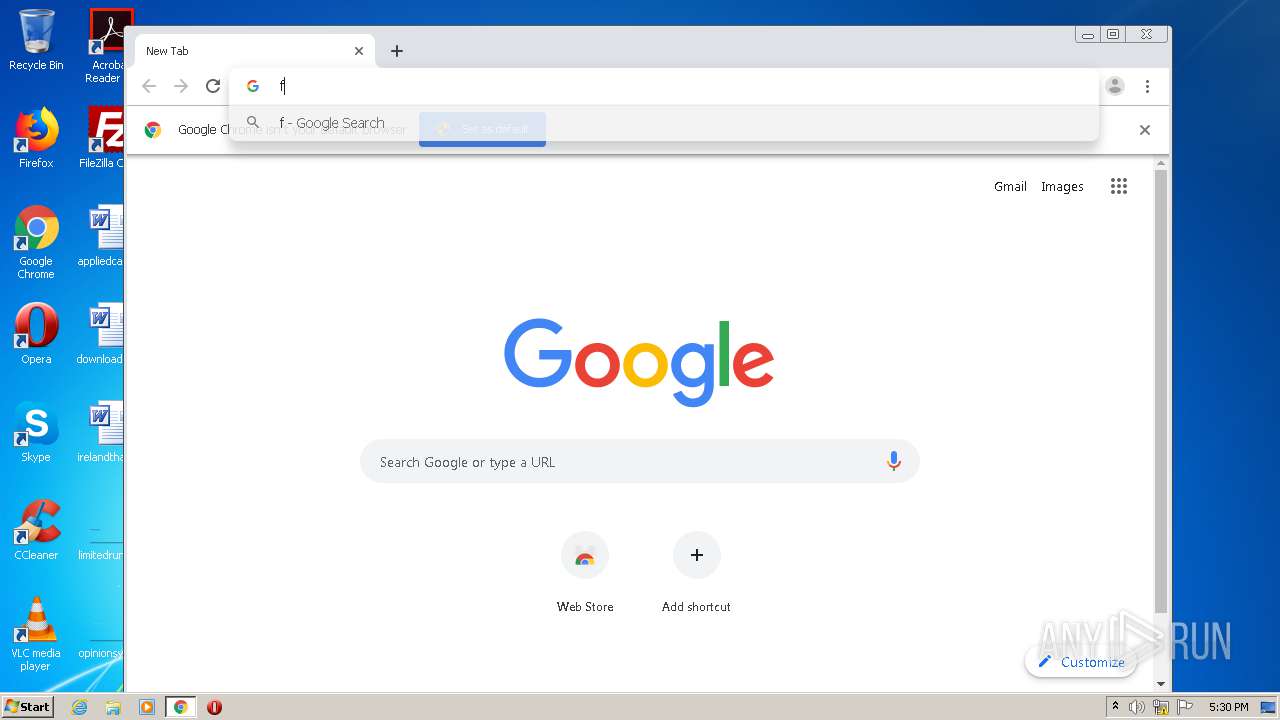
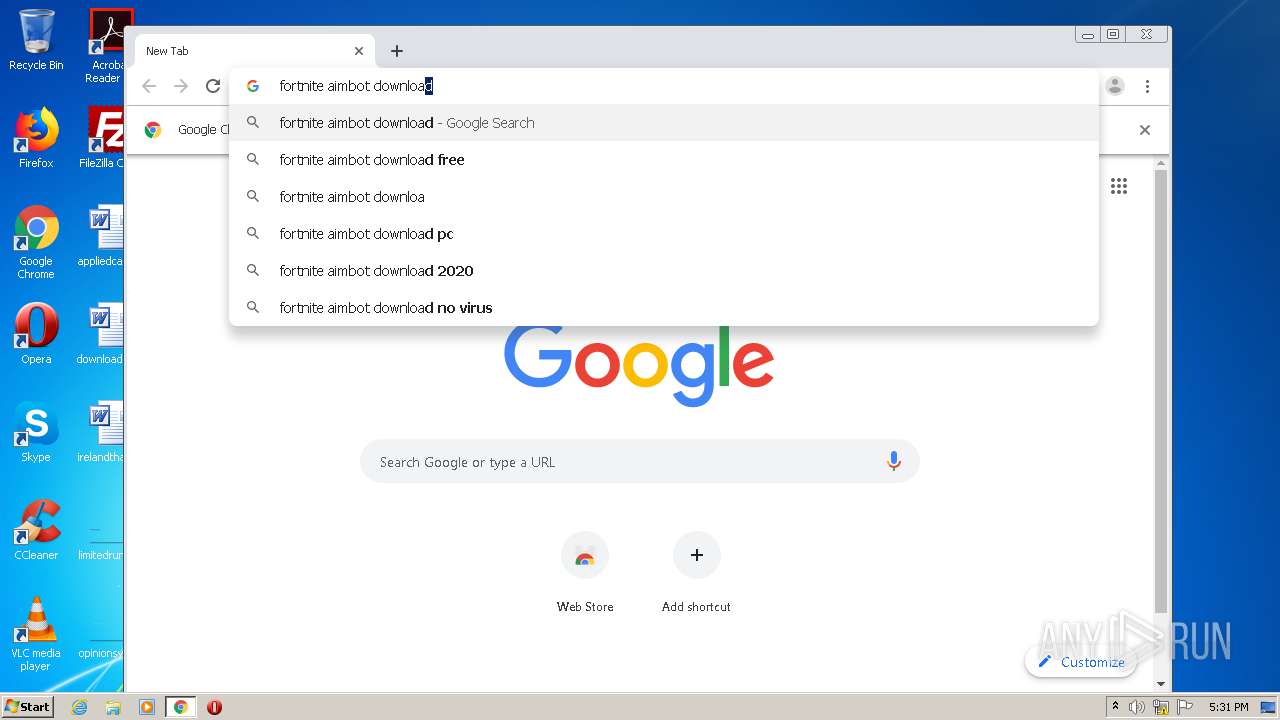
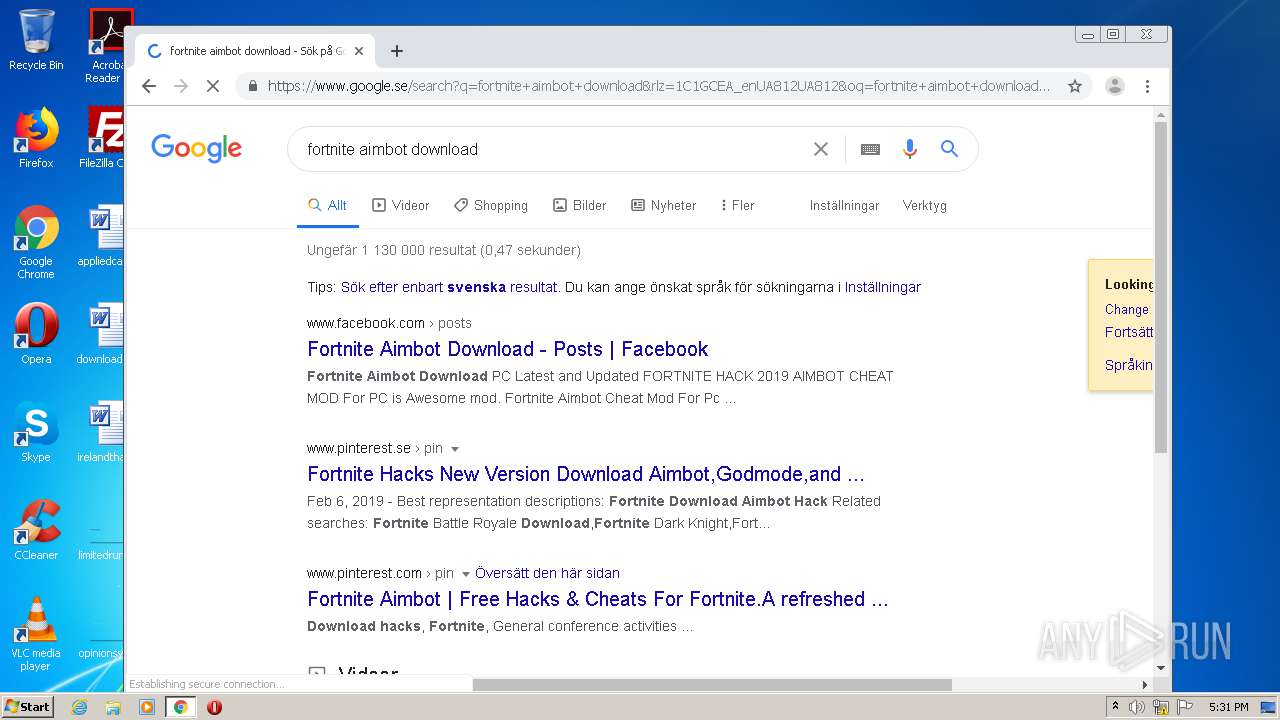
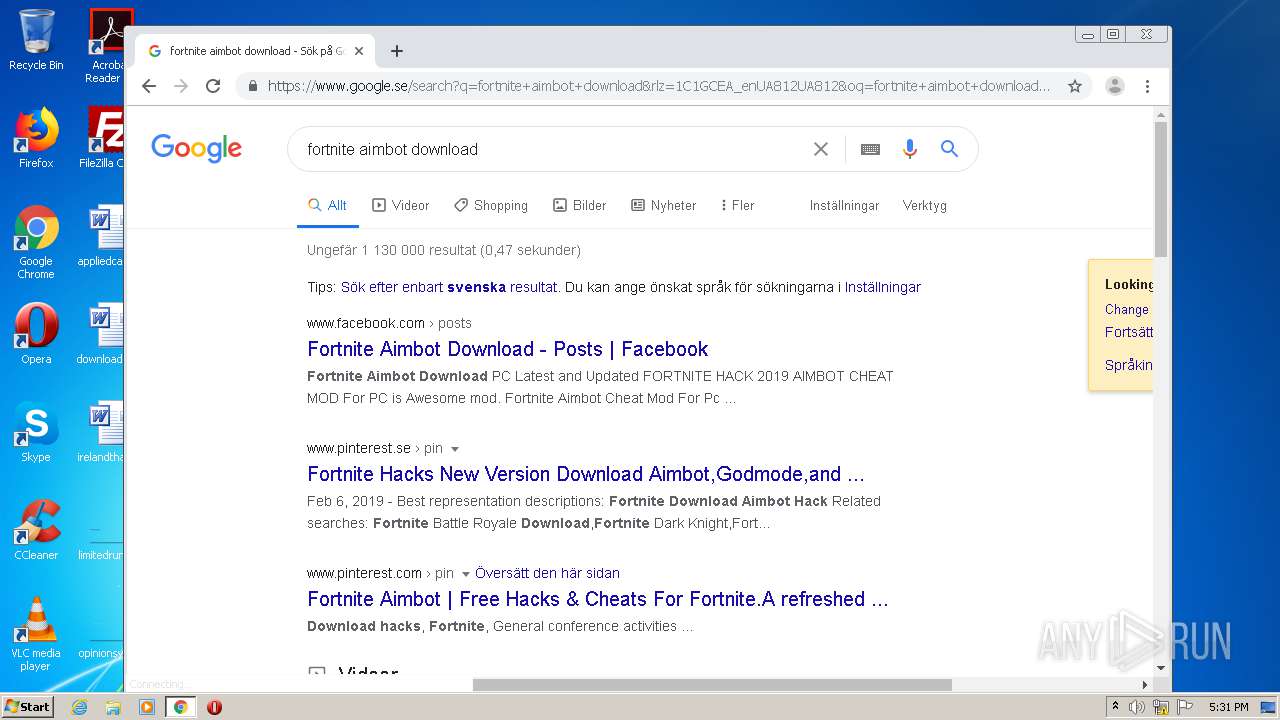
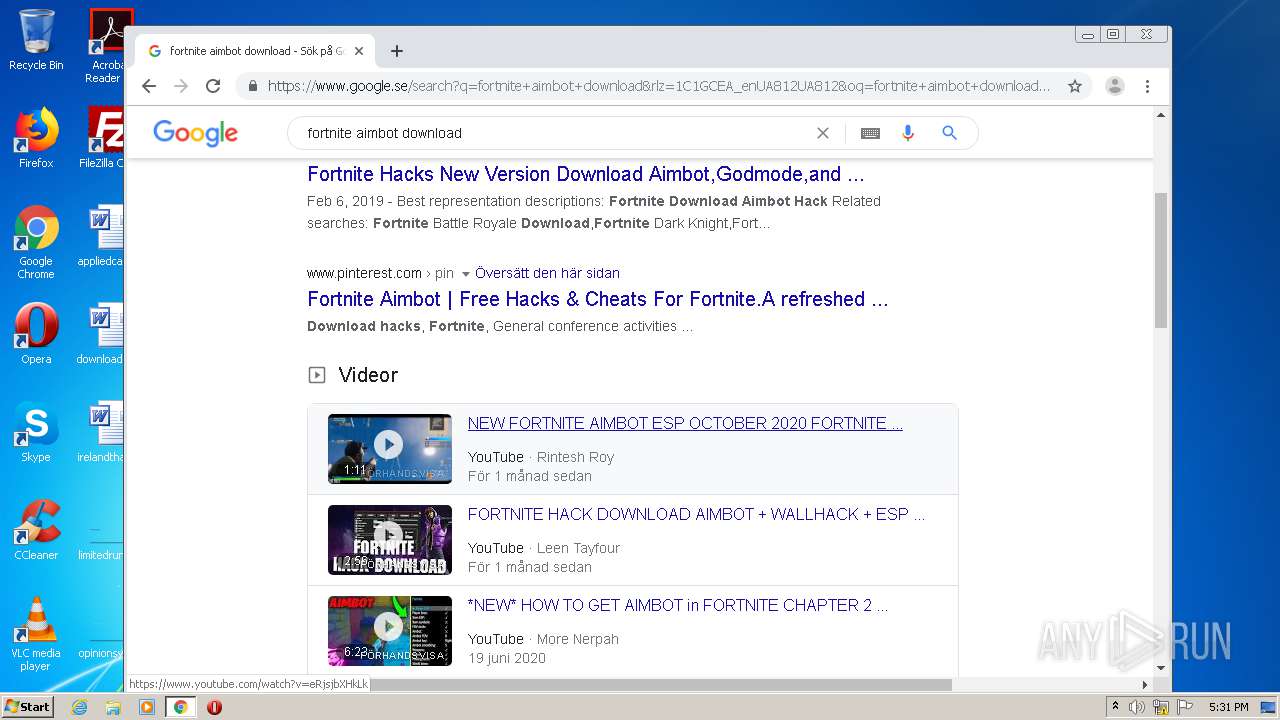
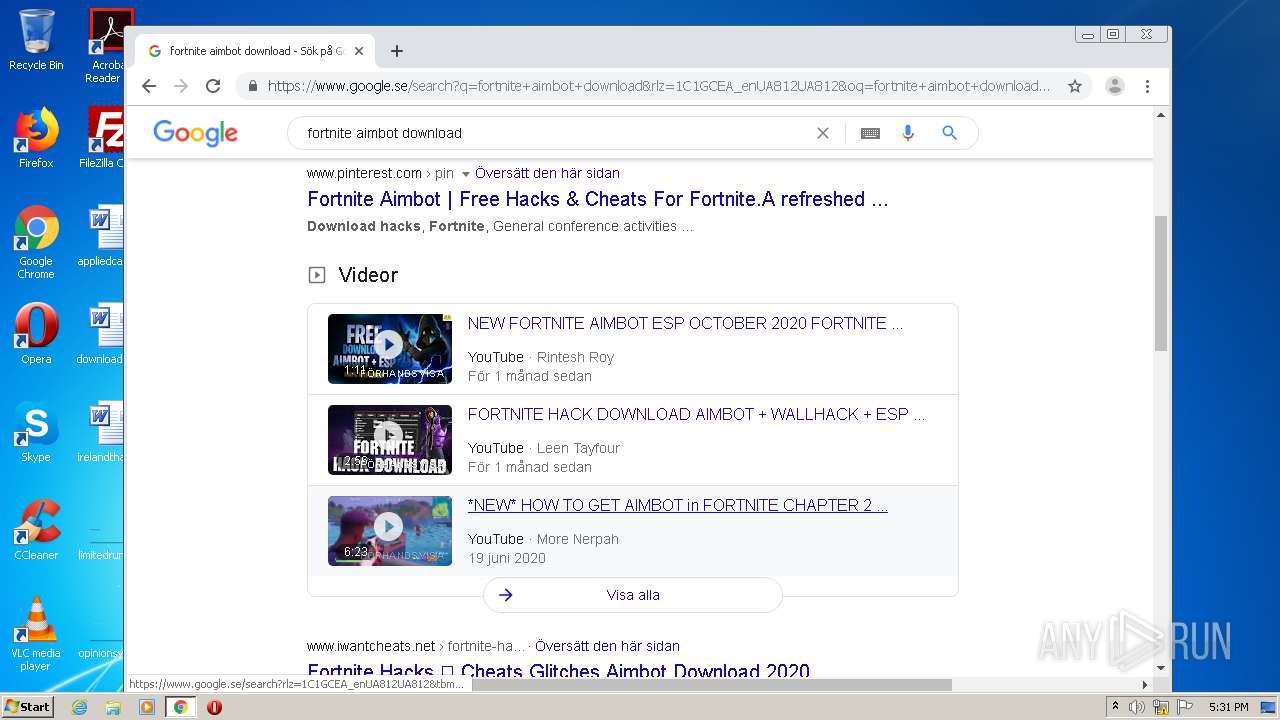
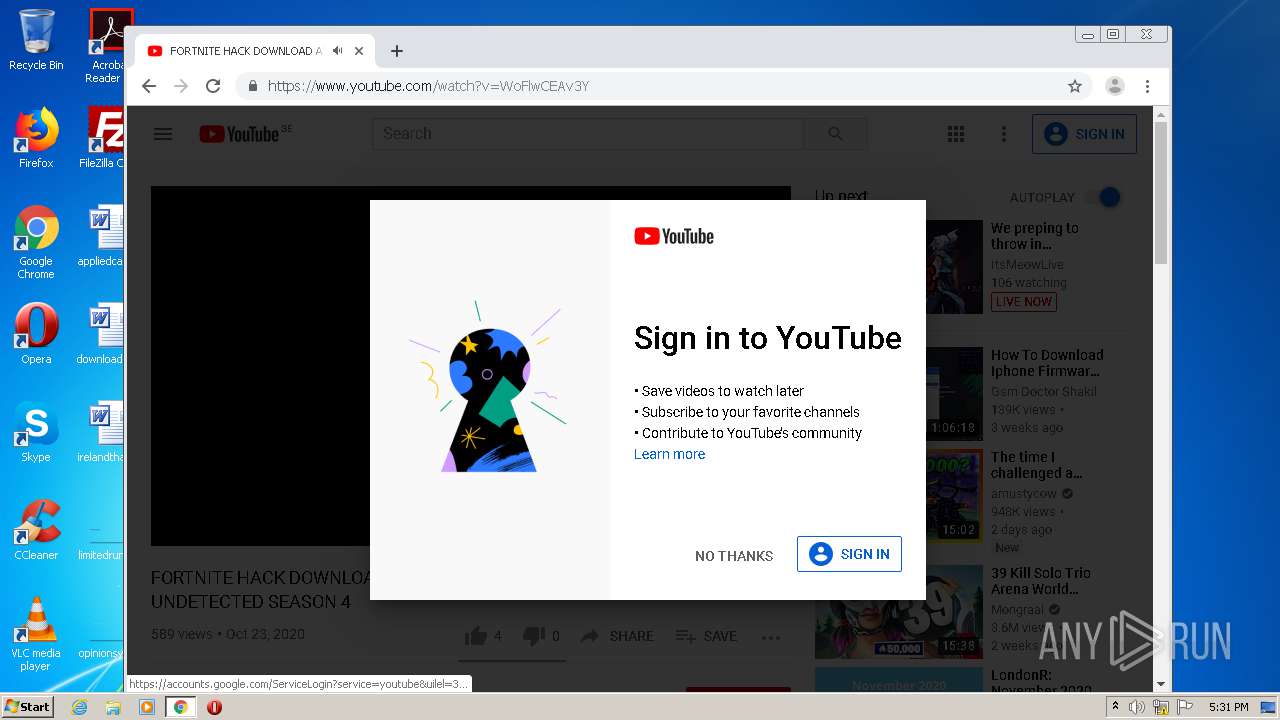
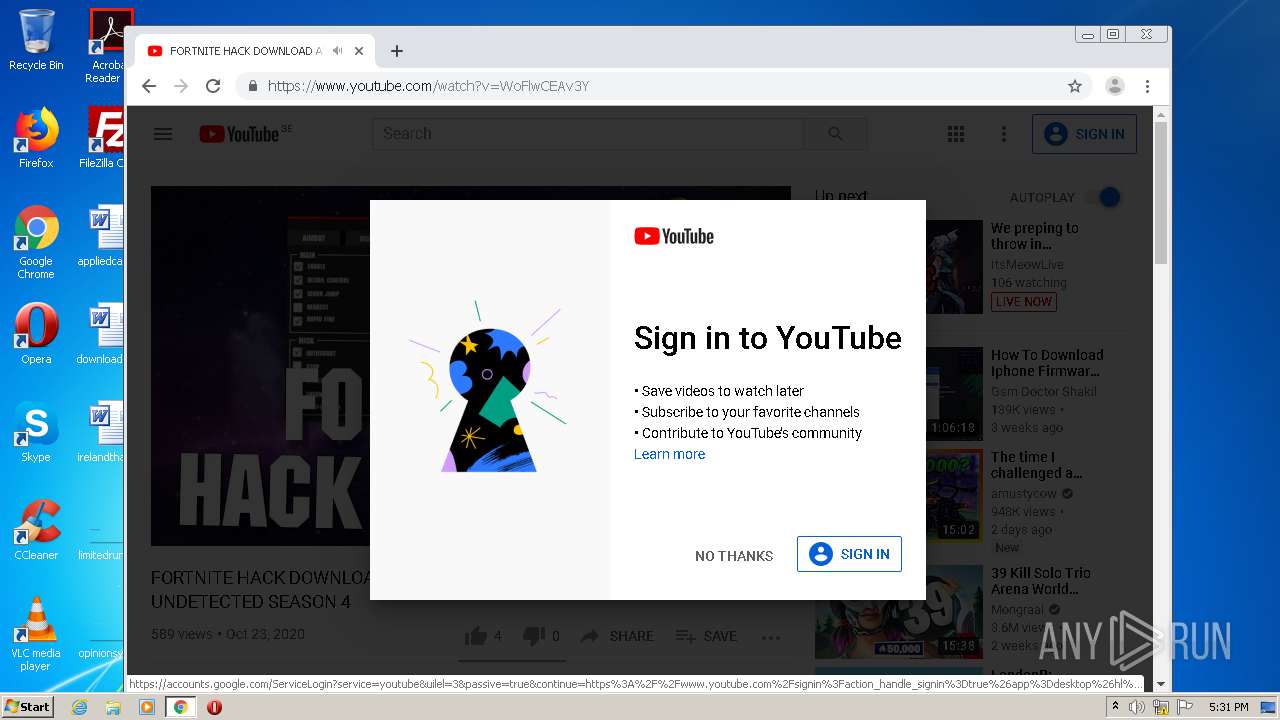
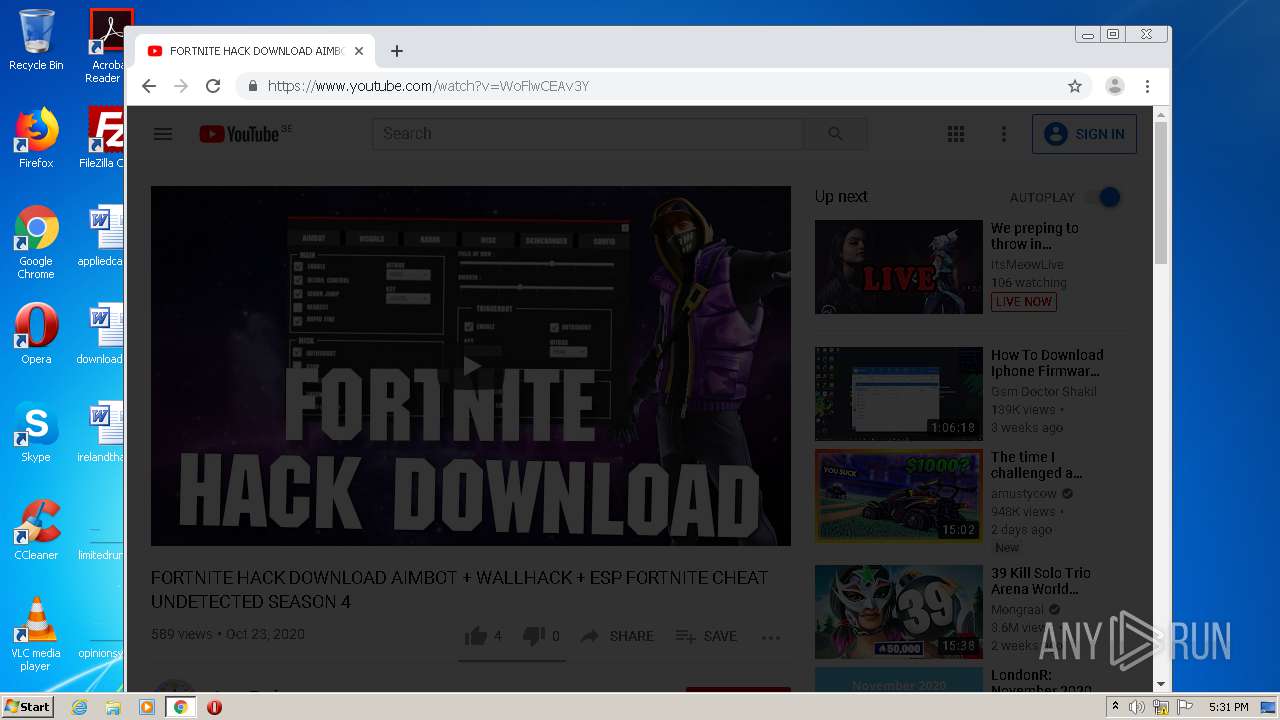
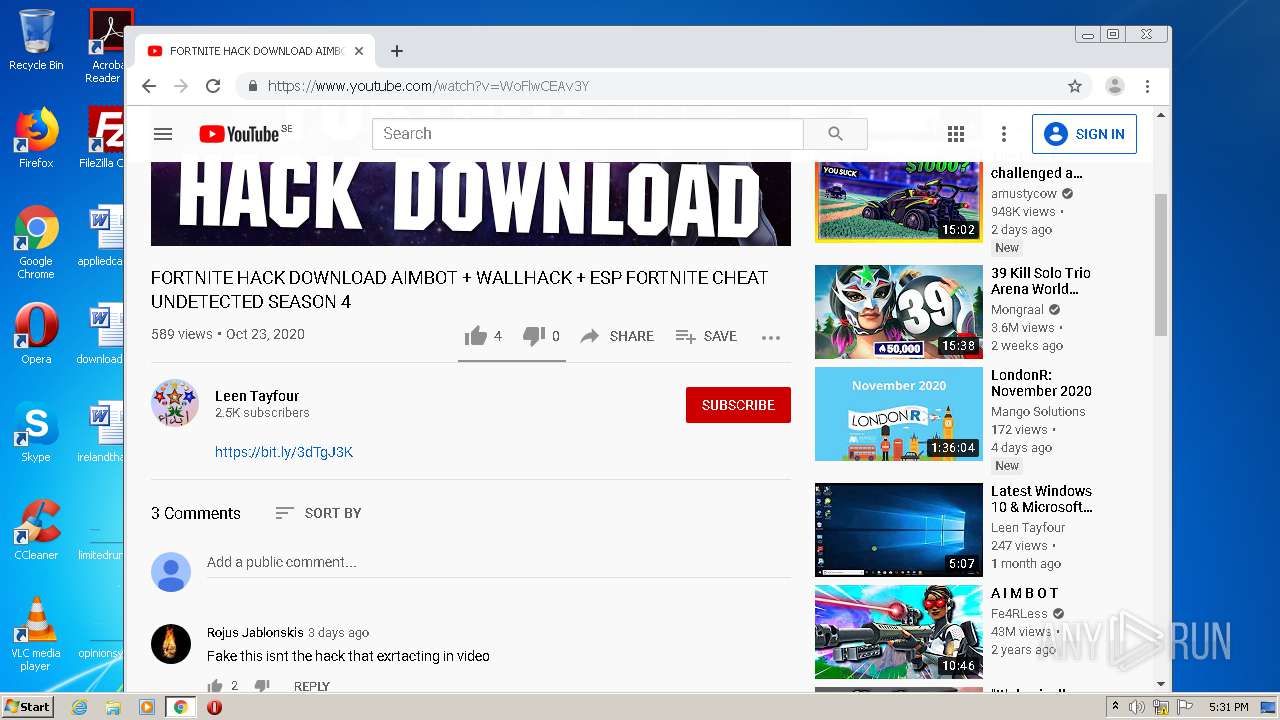
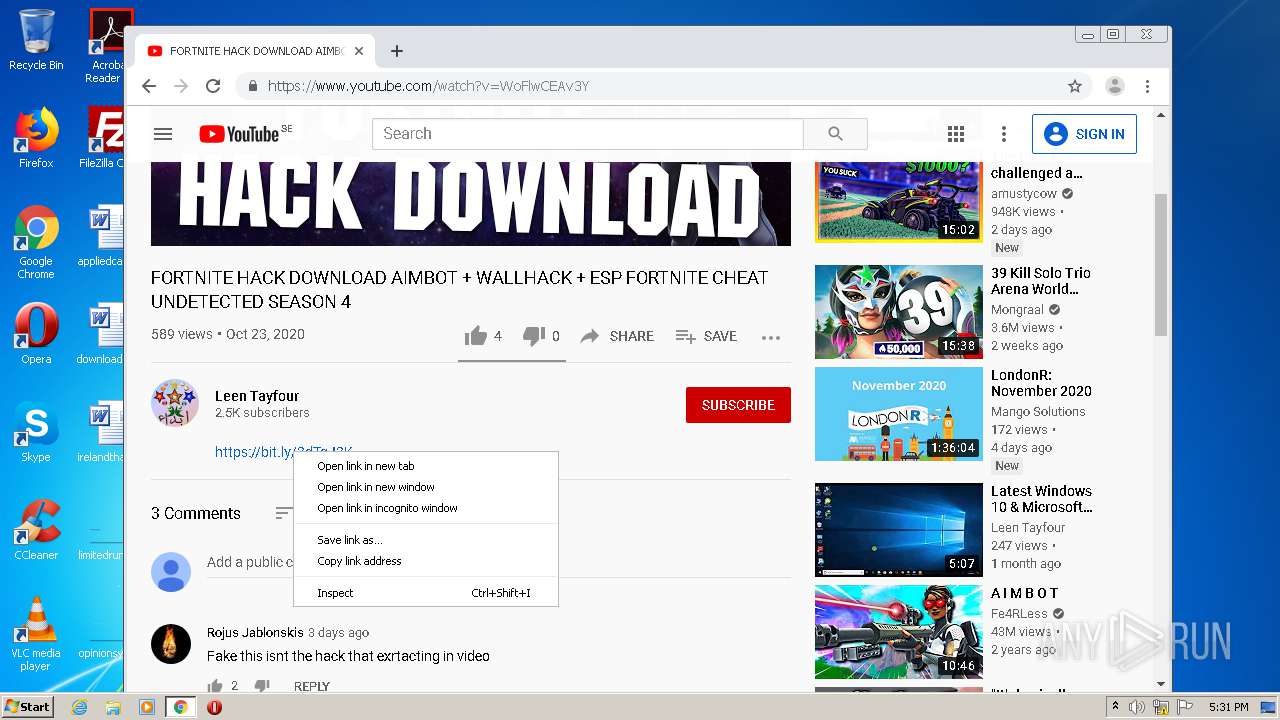
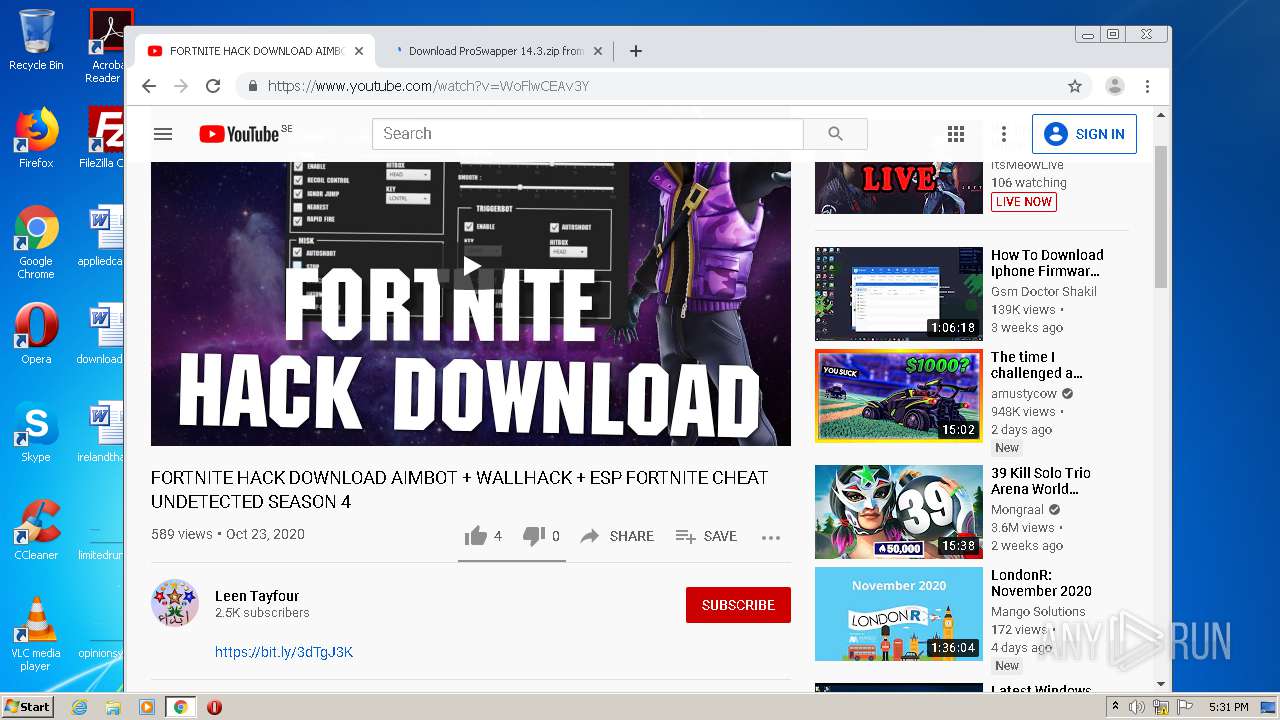
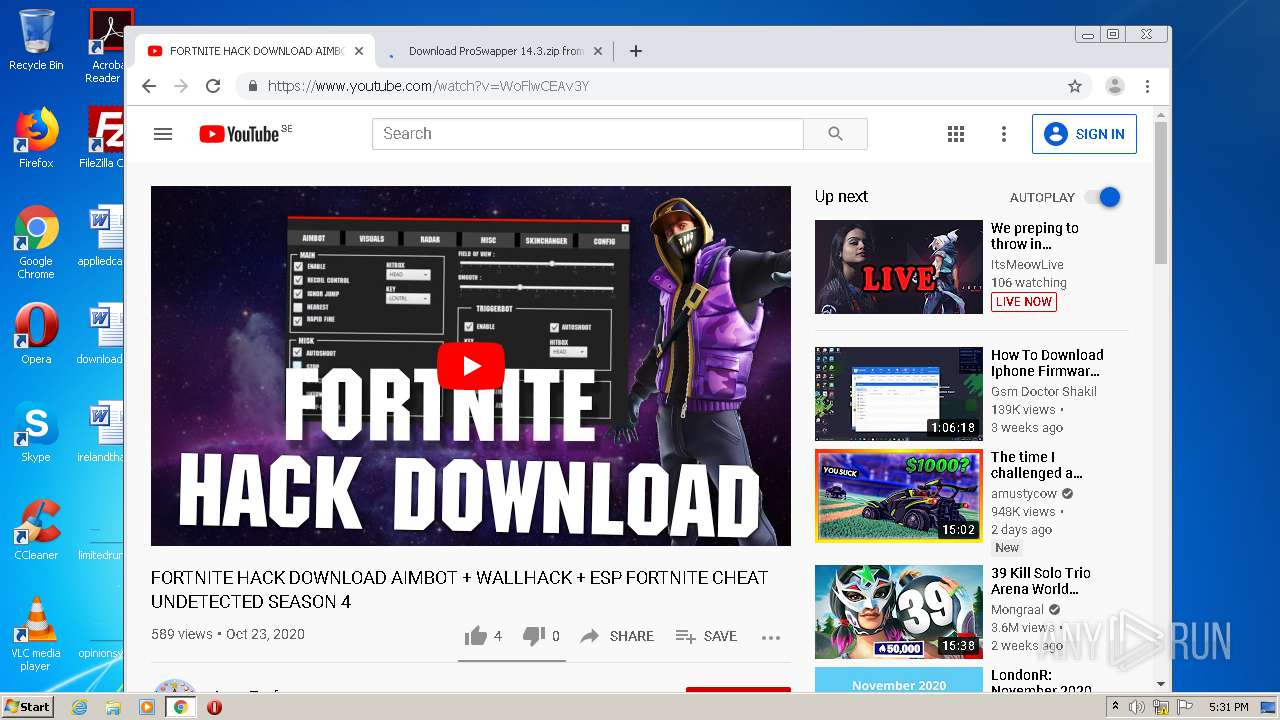
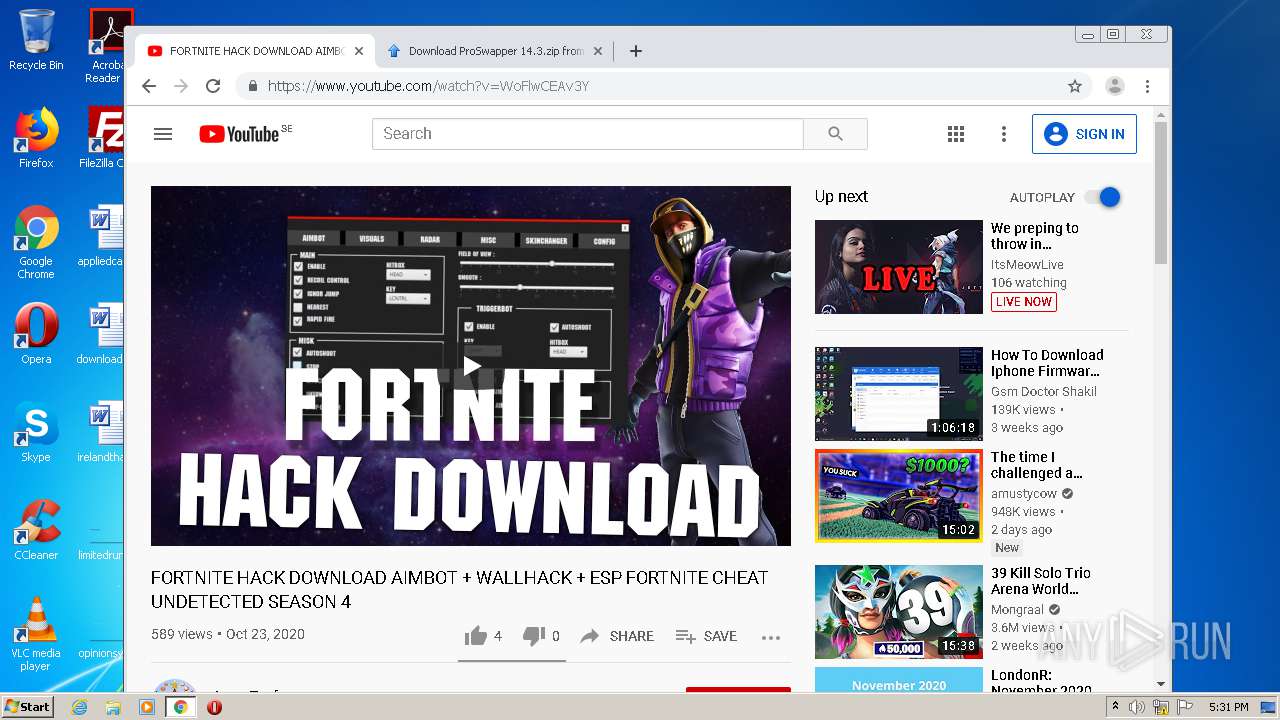
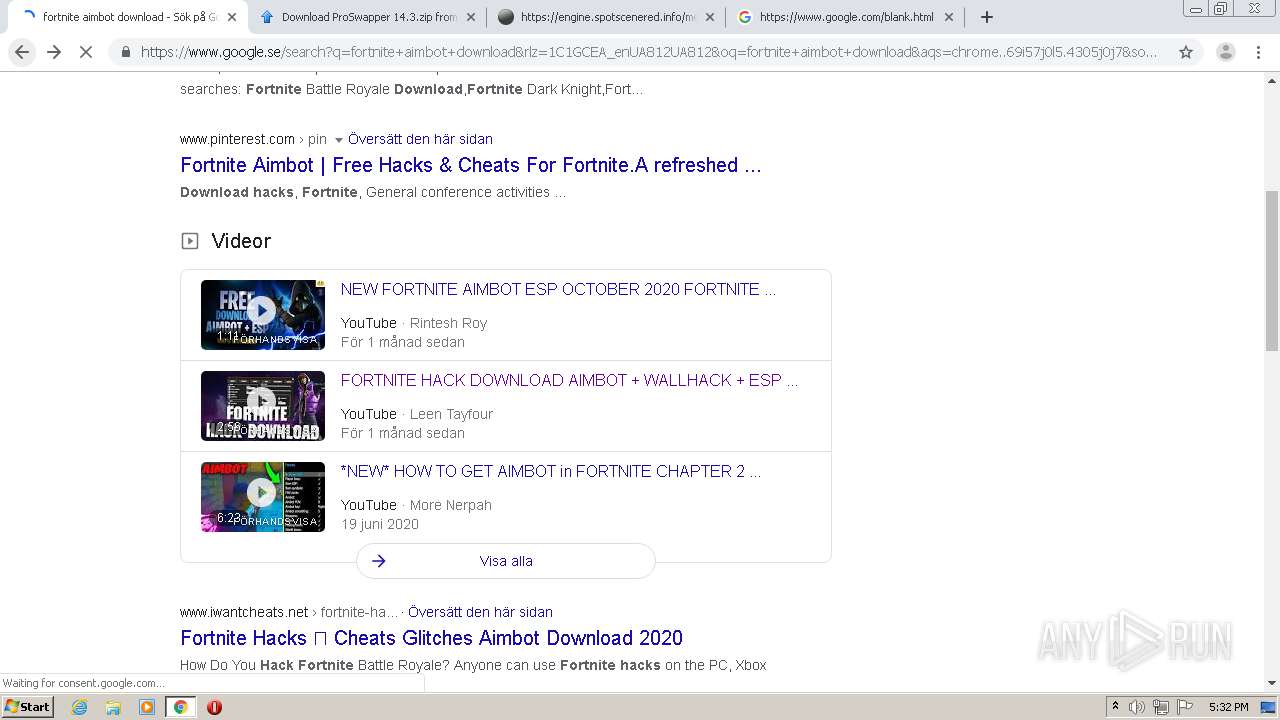
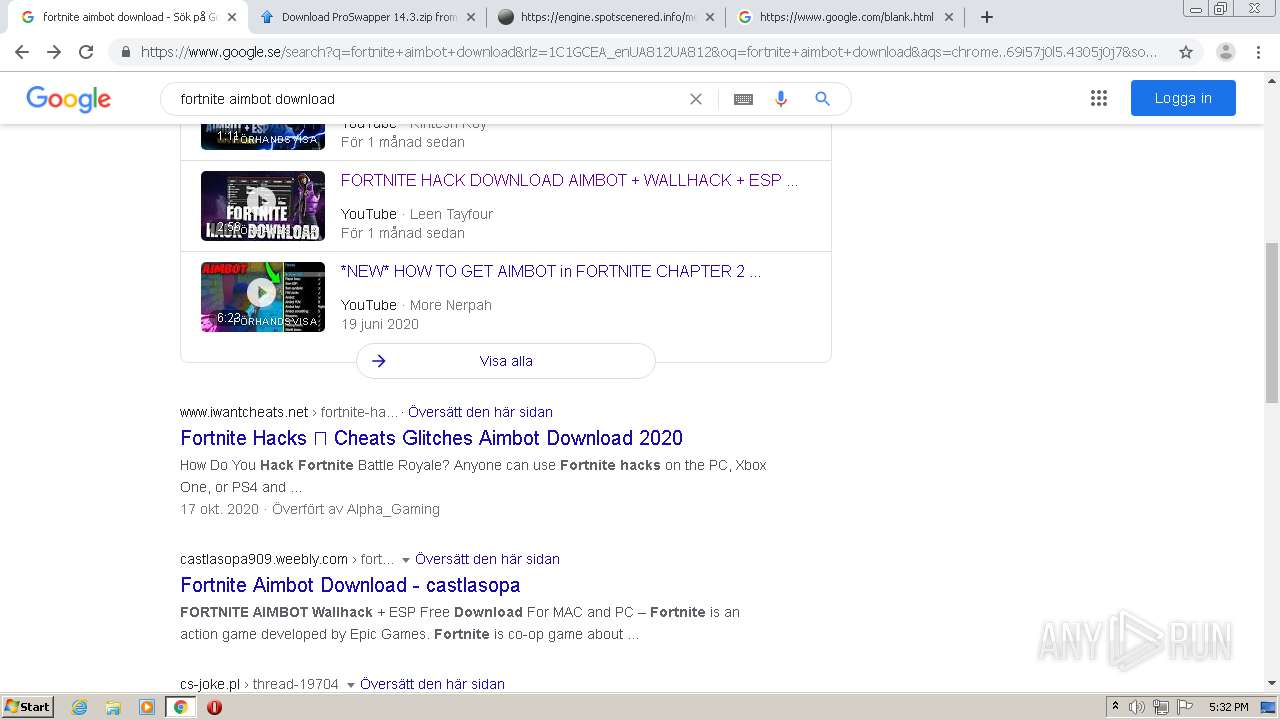
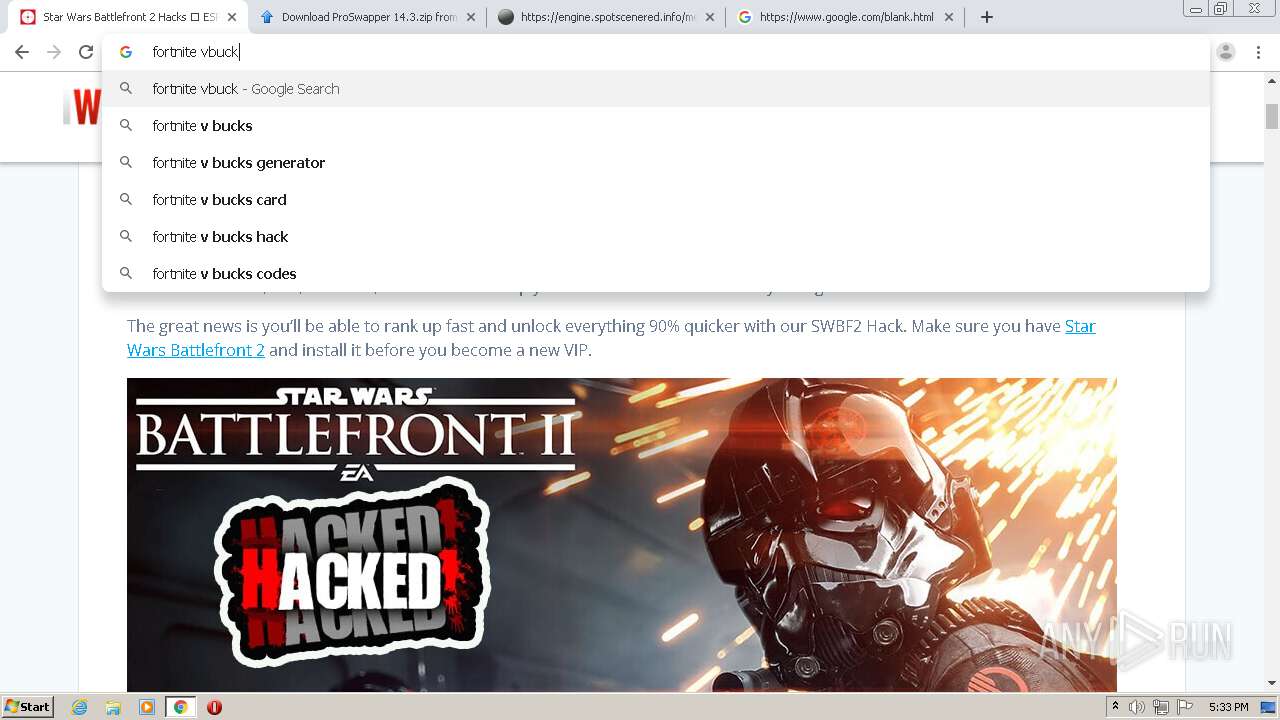
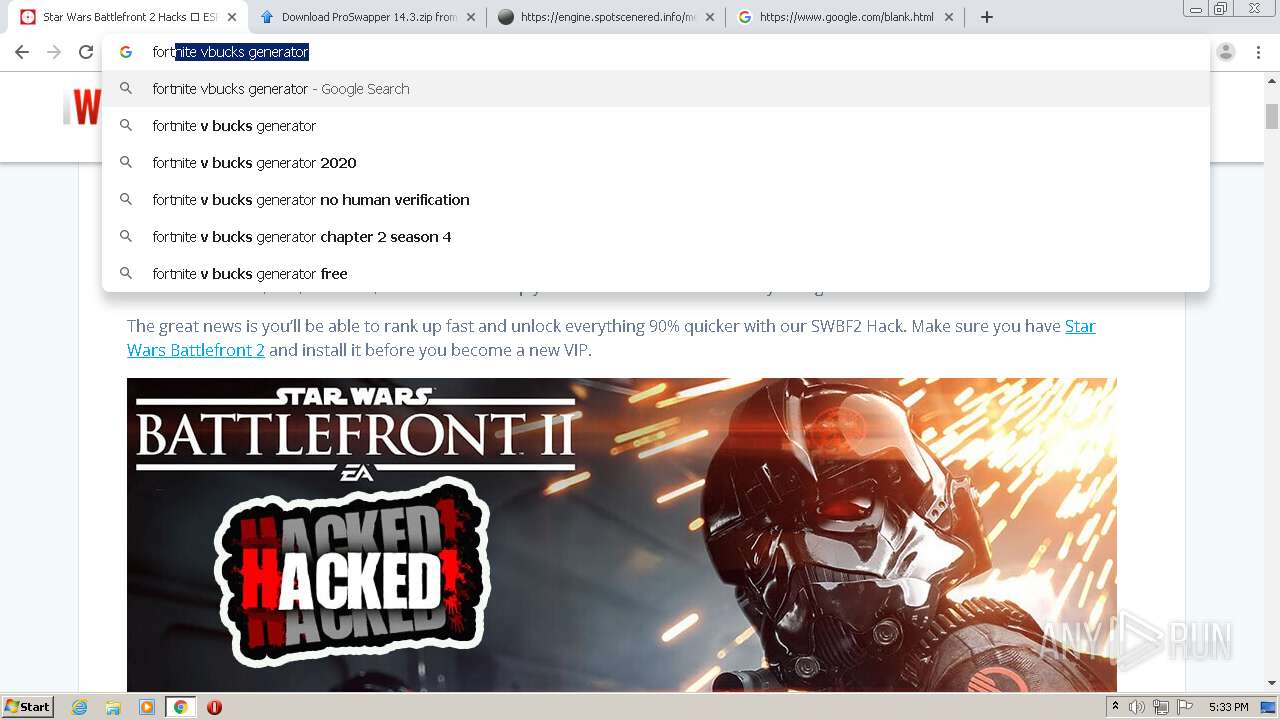
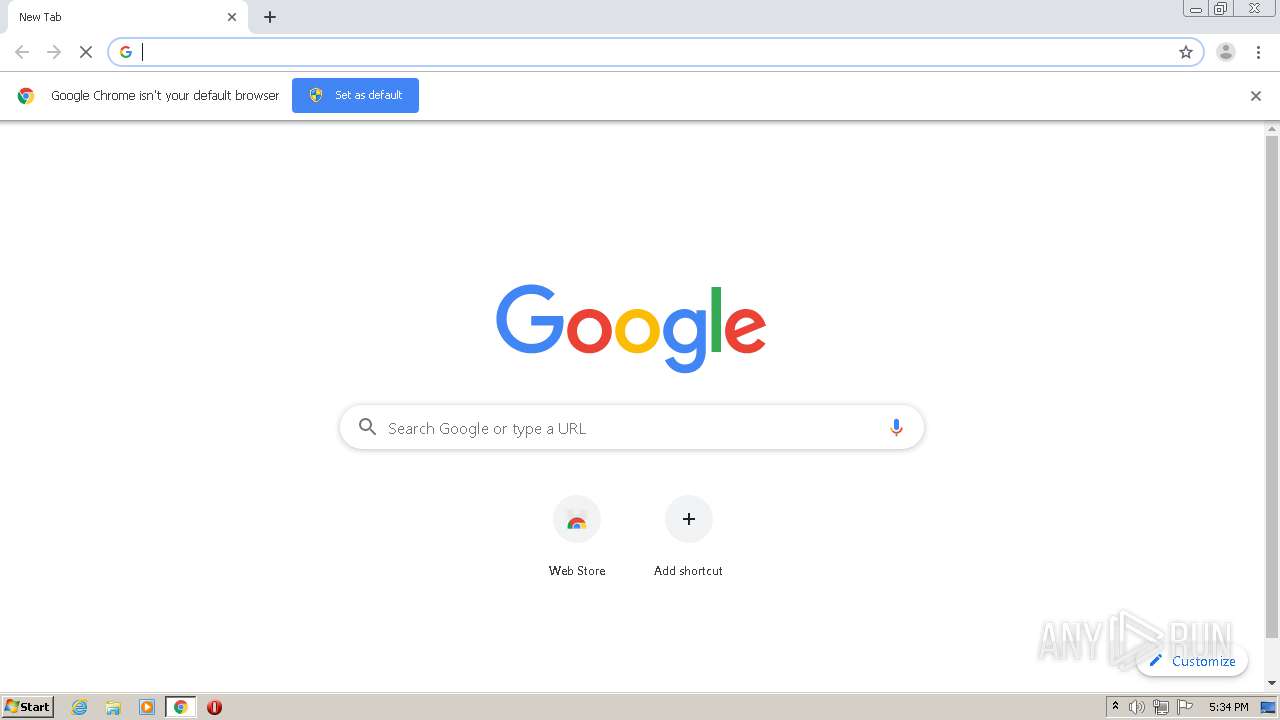
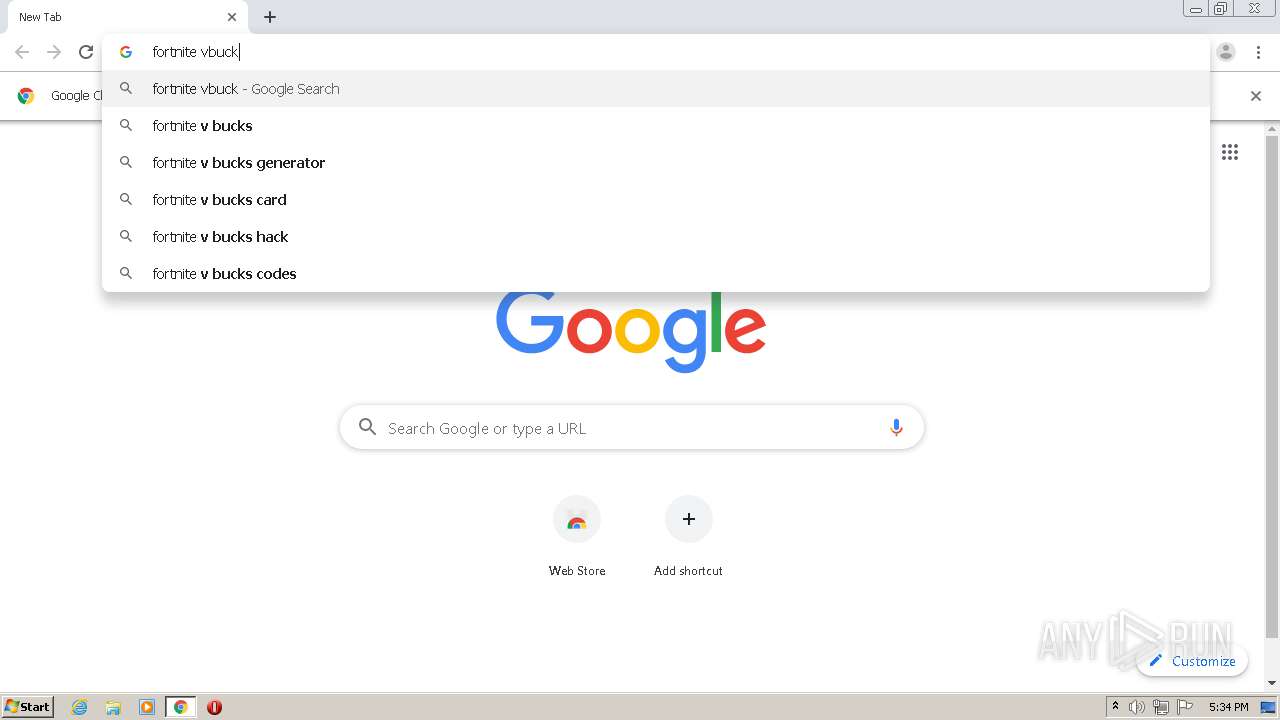
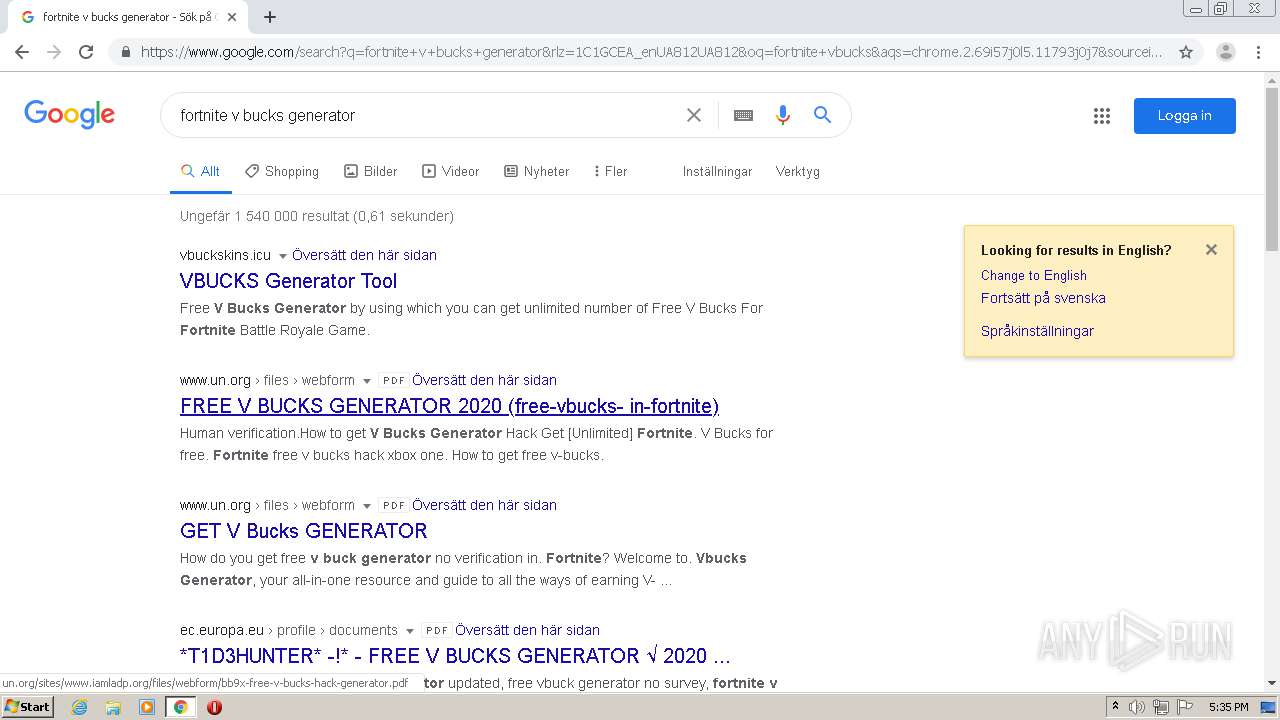
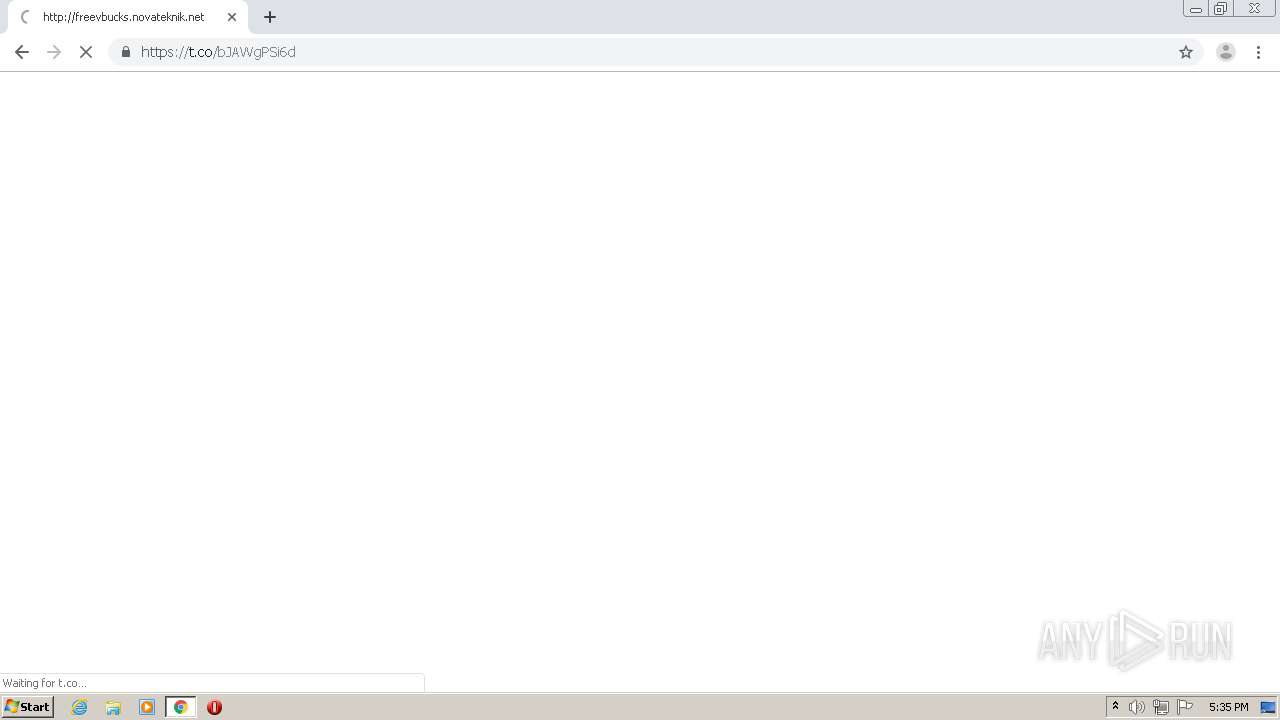
Manual execution by user
- chrome.exe (PID: 3880)
- chrome.exe (PID: 1652)
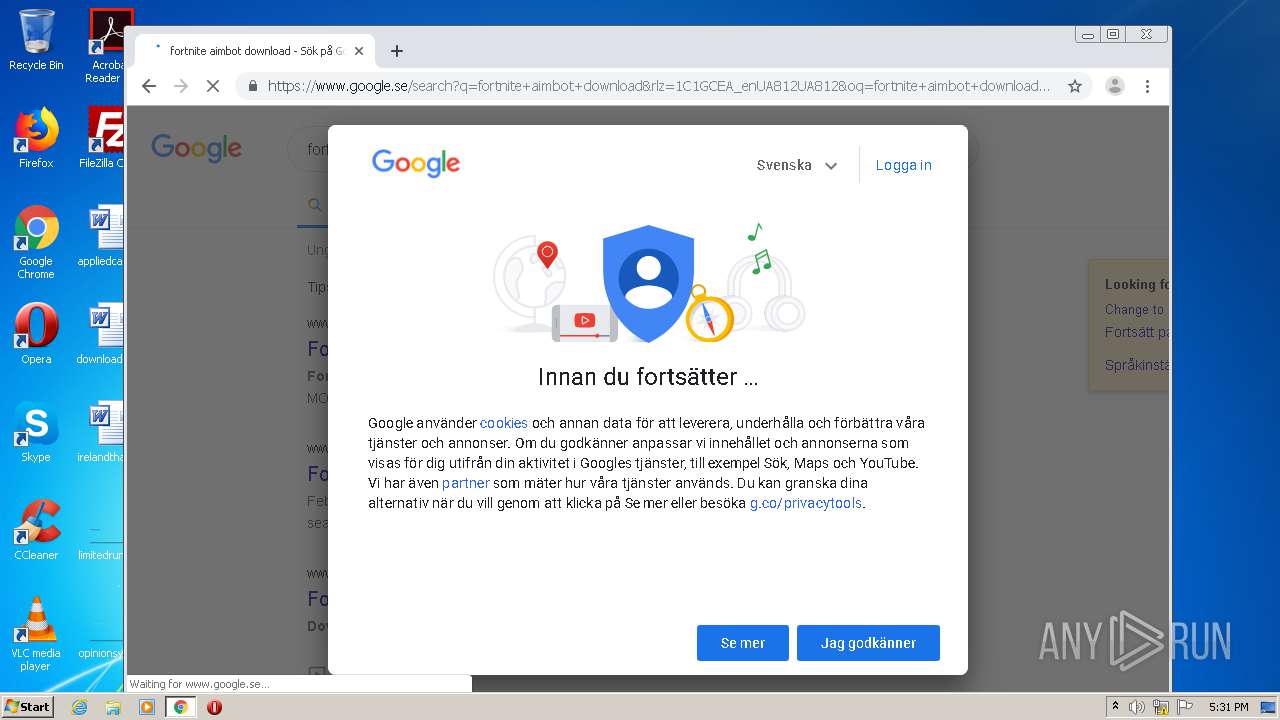
Reads the hosts file
- chrome.exe (PID: 3248)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2904)
Application launched itself
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .png | | | Portable Network Graphics (100) |
|---|
EXIF
PNG
| ImageWidth: | 768 |
|---|---|
| ImageHeight: | 432 |
| BitDepth: | 8 |
| ColorType: | RGB with Alpha |
| Compression: | Deflate/Inflate |
| Filter: | Adaptive |
| Interlace: | Noninterlaced |
| PixelsPerUnitX: | 1 |
| PixelsPerUnitY: | 1 |
| PixelUnits: | Unknown |
| Creator: | Premiere Pro |
XMP
| XMPToolkit: | Adobe XMP Core 6.0-c002 79.164360, 2020/02/13-01:07:22 |
|---|---|
| InstanceID: | xmp.iid:69541ef9-9d56-6d48-83ab-c2254b51dc97 |
| DocumentID: | bed2f23e-a996-cac6-9966-b0da0000003f |
| OriginalDocumentID: | xmp.did:8517dfdc-0edd-8141-92c3-94c7e31540b1 |
| MetadataDate: | 2020:11:26 16:49:22Z |
| ModifyDate: | 2020:11:26 16:49:22Z |
| CreateDate: | 2020:11:26 16:48:51 |
| VideoFrameRate: | 25 |
| VideoFieldOrder: | Progressive |
| VideoPixelAspectRatio: | 1 |
| StartTimeScale: | 25 |
| StartTimeSampleSize: | 1 |
| Format: | PNG |
| HistoryAction: |
|
| HistoryInstanceID: |
|
| HistoryWhen: |
|
| HistorySoftwareAgent: |
|
| HistoryChanged: |
|
| VideoFrameSizeW: | 768 |
| VideoFrameSizeH: | 432 |
| VideoFrameSizeUnit: | pixel |
| DurationValue: | 248 |
| DurationScale: | 0.04 |
| StartTimecodeTimeFormat: | 25 fps |
| StartTimecodeTimeValue: | 00:04:53:03 |
| AltTimecodeTimeValue: | 00:04:53:03 |
| AltTimecodeTimeFormat: | 25 fps |
Composite
| ImageSize: | 768x432 |
|---|---|
| Megapixels: | 0.332 |
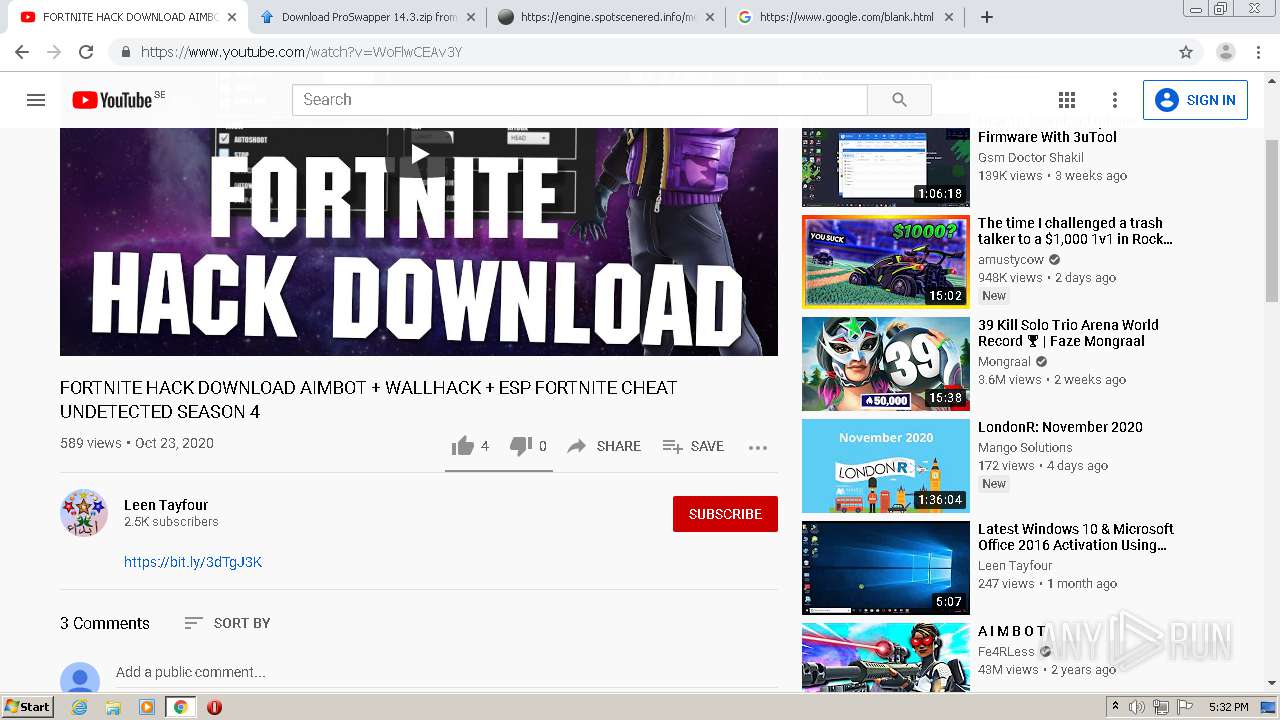
Total processes
106
Monitored processes
69
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6646111067168111926,16787393904325451847,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16008648517236593849 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5350725570364173055,14095141721391263925,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13745034728136530082 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,5350725570364173055,14095141721391263925,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5596268488118735116 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=1028,6646111067168111926,16787393904325451847,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=8134669758754581853 --mojo-platform-channel-handle=2924 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6646111067168111926,16787393904325451847,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12419165008701992844 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,5350725570364173055,14095141721391263925,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15568763199504208422 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6646111067168111926,16787393904325451847,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4898606547960116750 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5350725570364173055,14095141721391263925,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4684991625229041452 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5350725570364173055,14095141721391263925,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16906745683715648094 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 700
Read events
1 533
Write events
159
Delete events
8
Modification events
| (PID) Process: | (2728) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2728) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
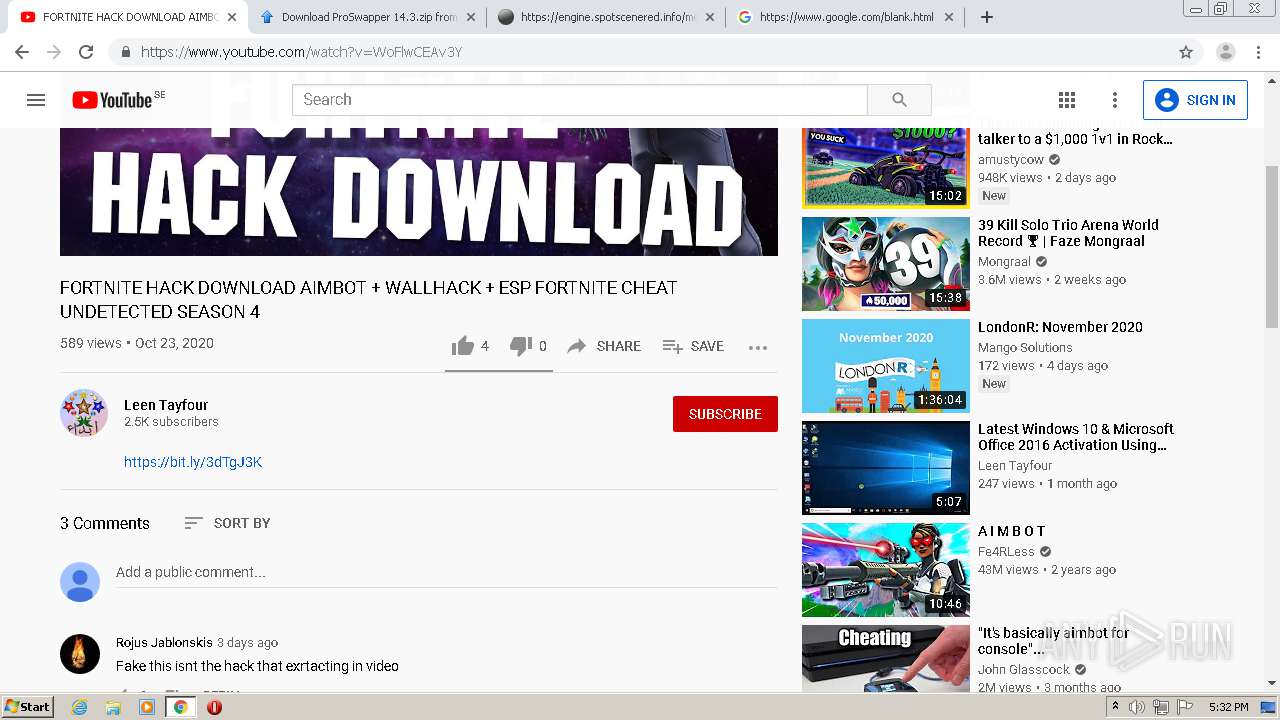
Executable files
0
Suspicious files
197
Text files
482
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3DACD-F28.pma | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\001c27ac-cee5-4836-9ecc-46436aac2bb2.tmp | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18f96e.TMP | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF18f96e.TMP | text | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18fb05.TMP | — | |
MD5:— | SHA256:— | |||
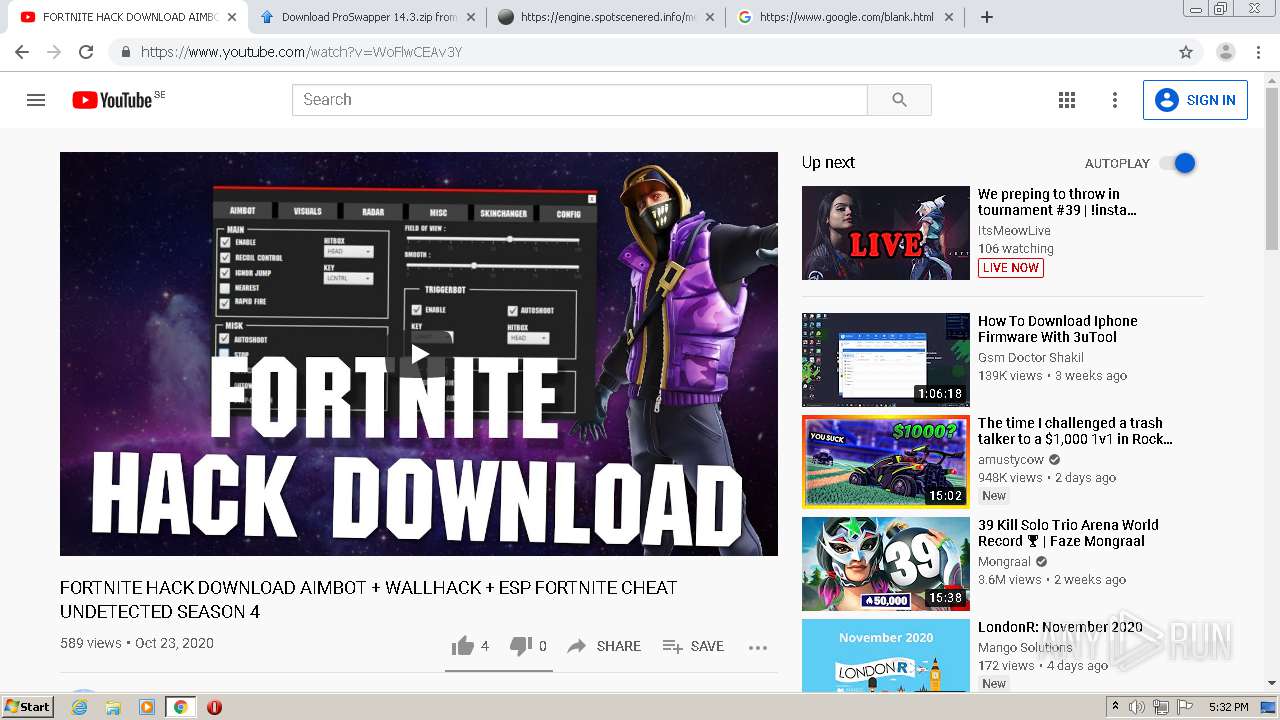
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
117
DNS requests
85
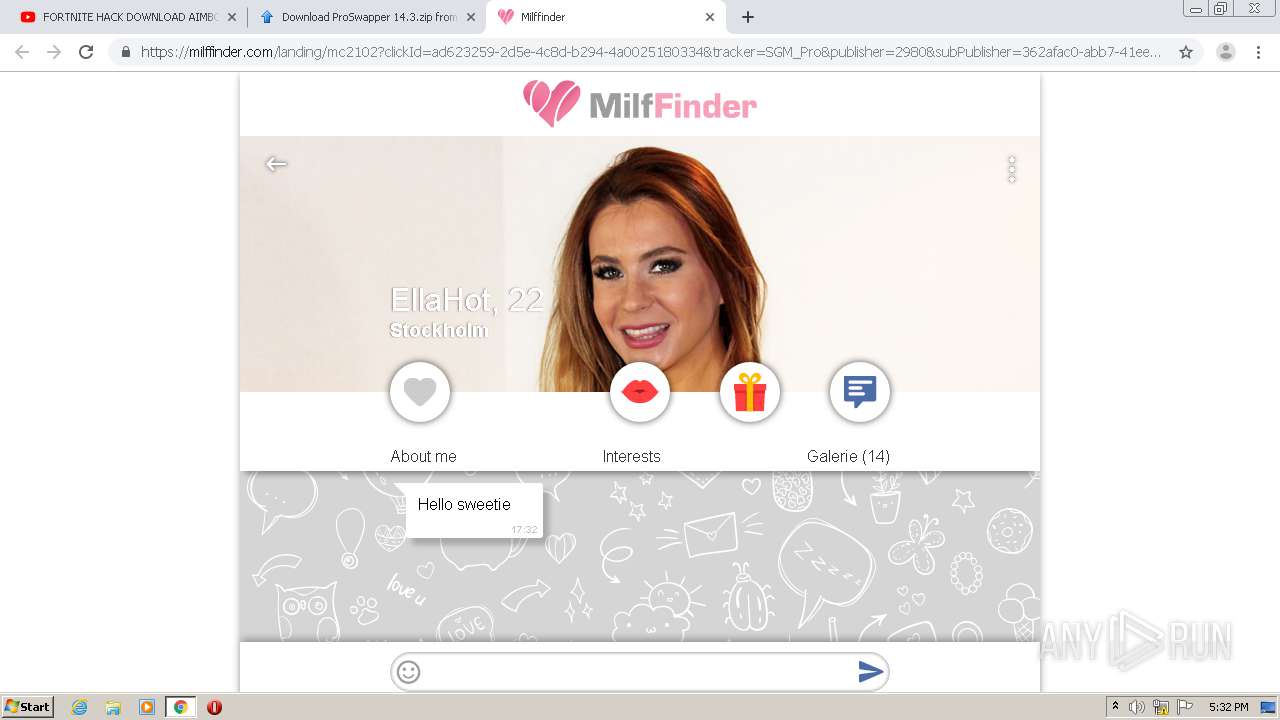
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3248 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAqN7HPiQ2%2F4c3rdXE3uHG8%3D | US | der | 471 b | whitelisted |
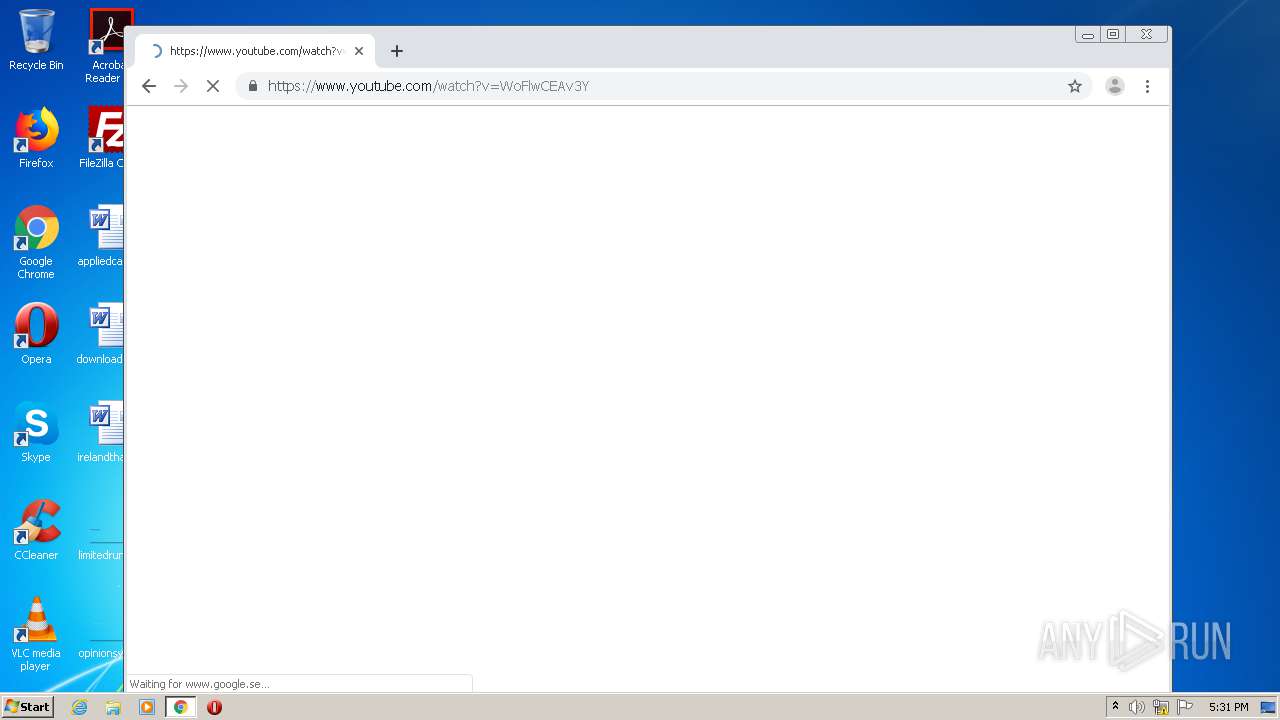
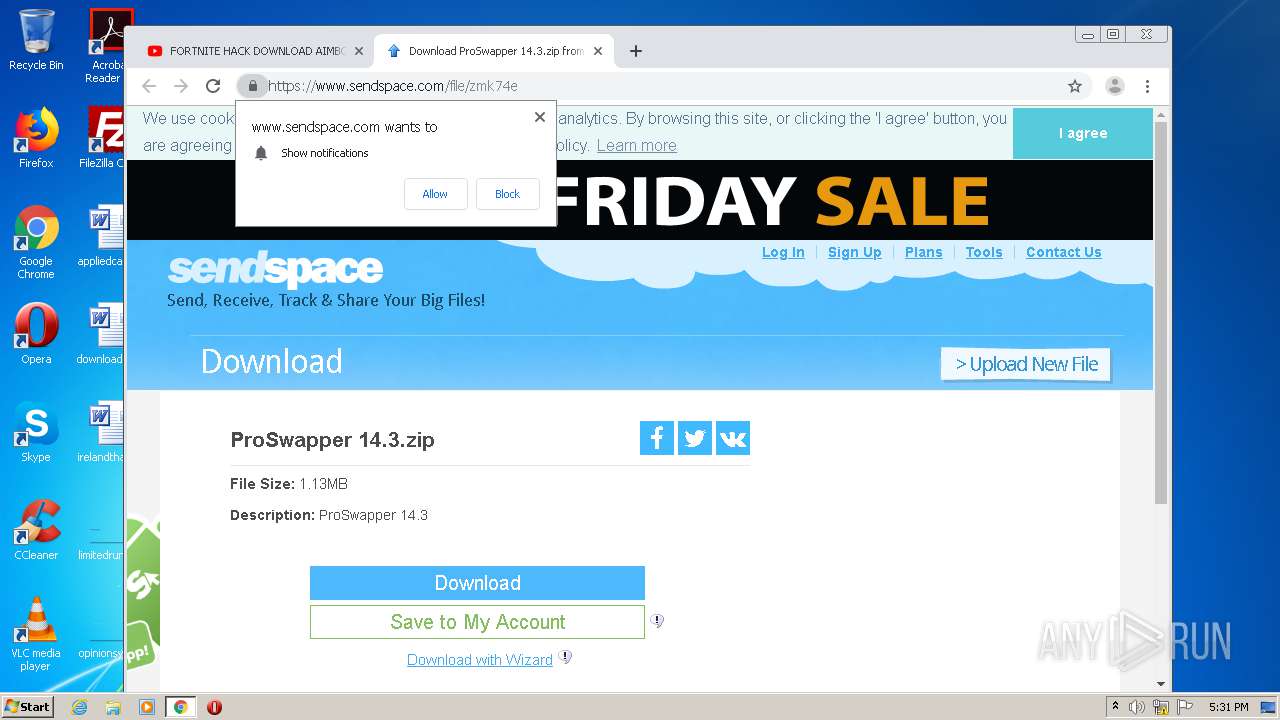
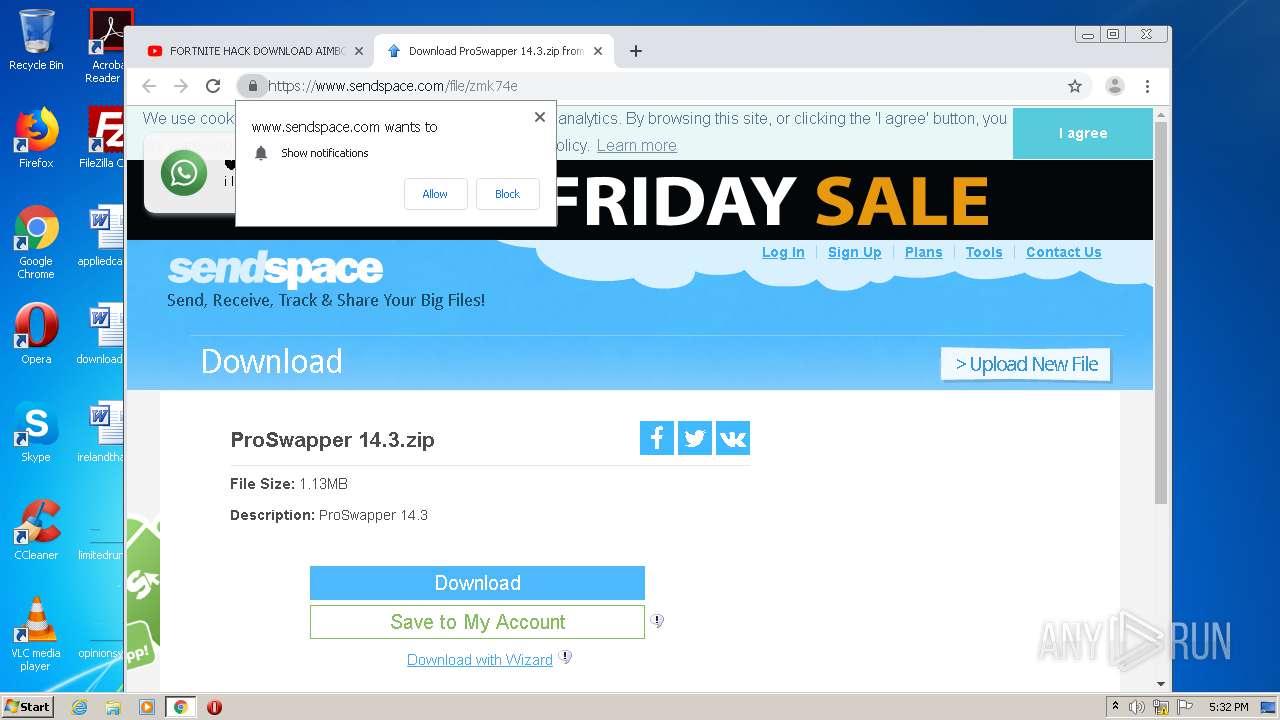
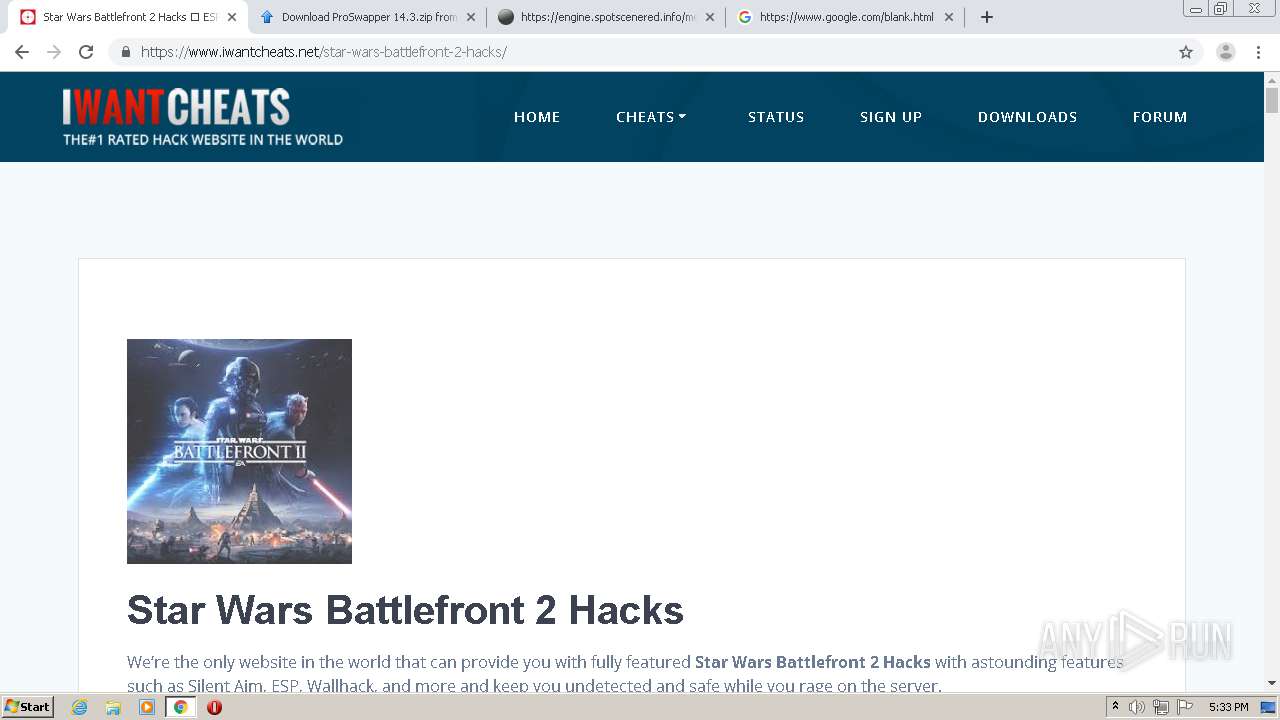
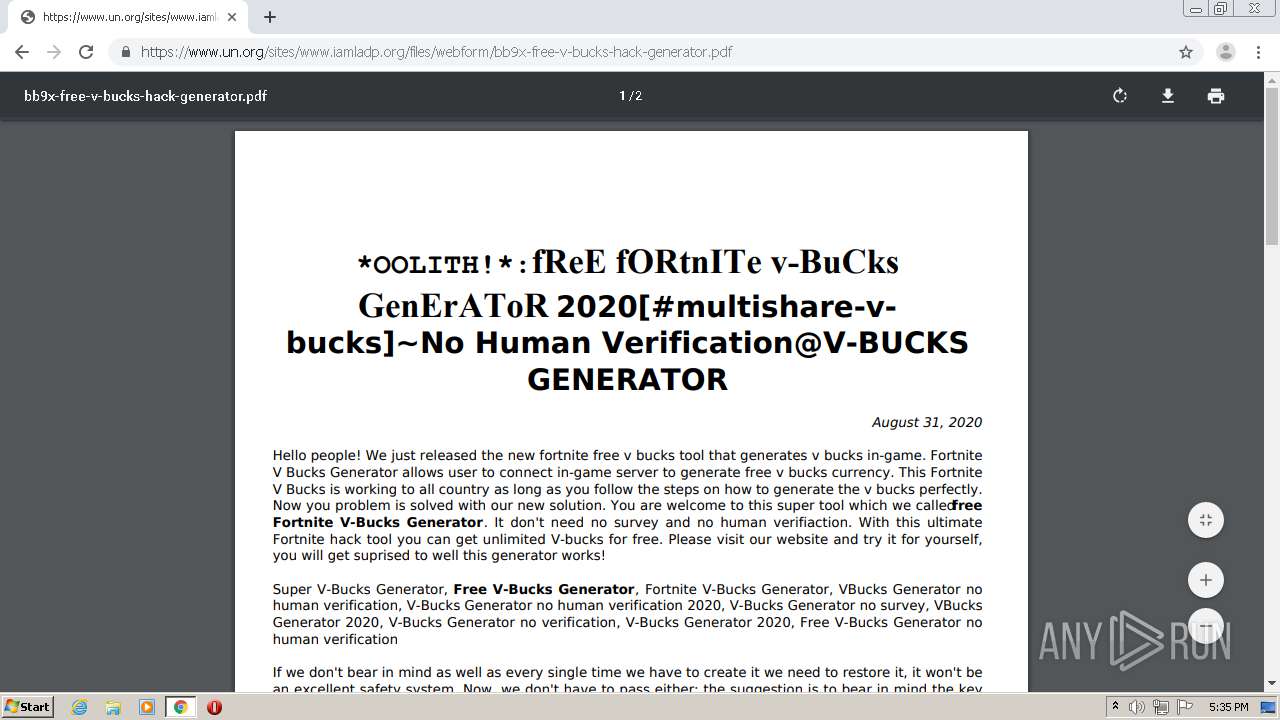
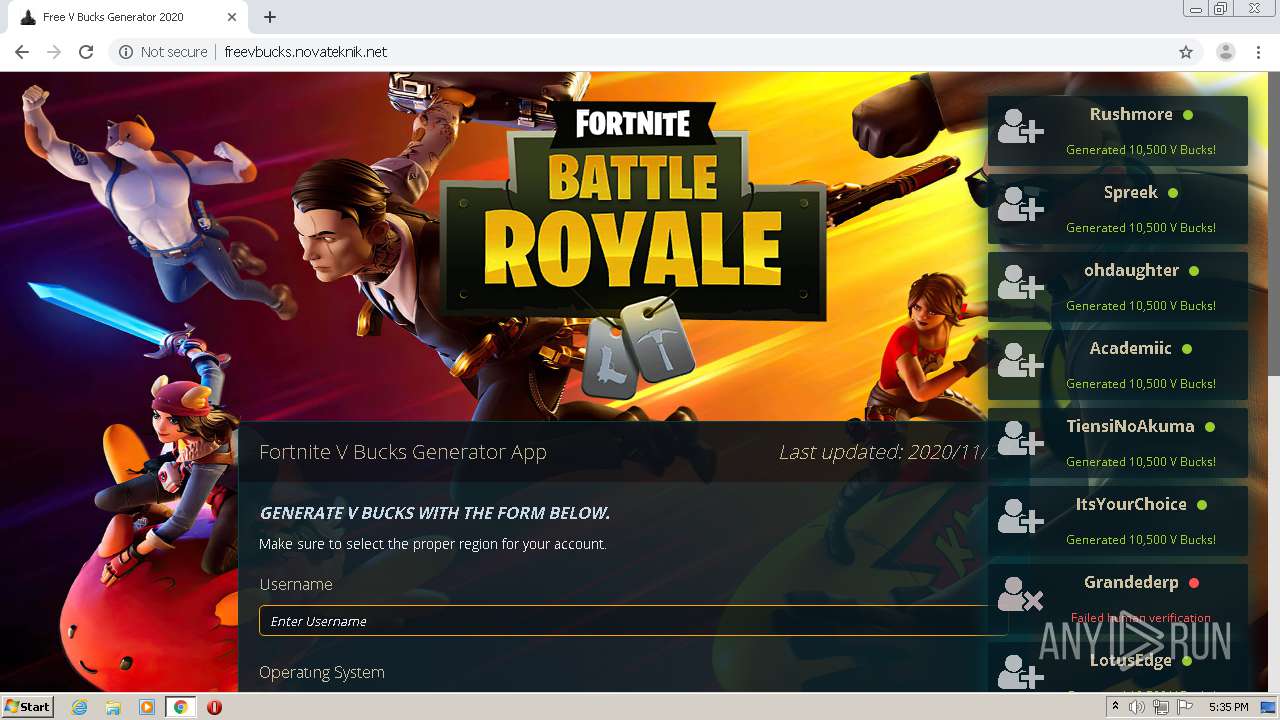
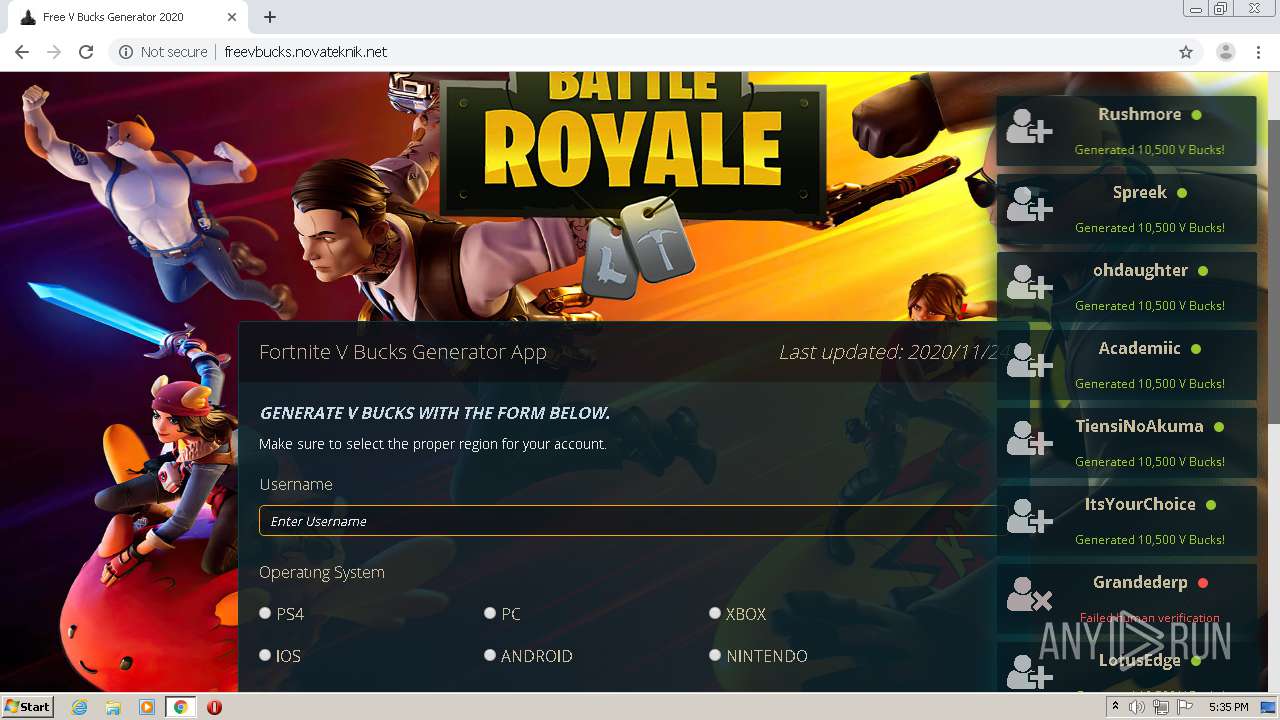
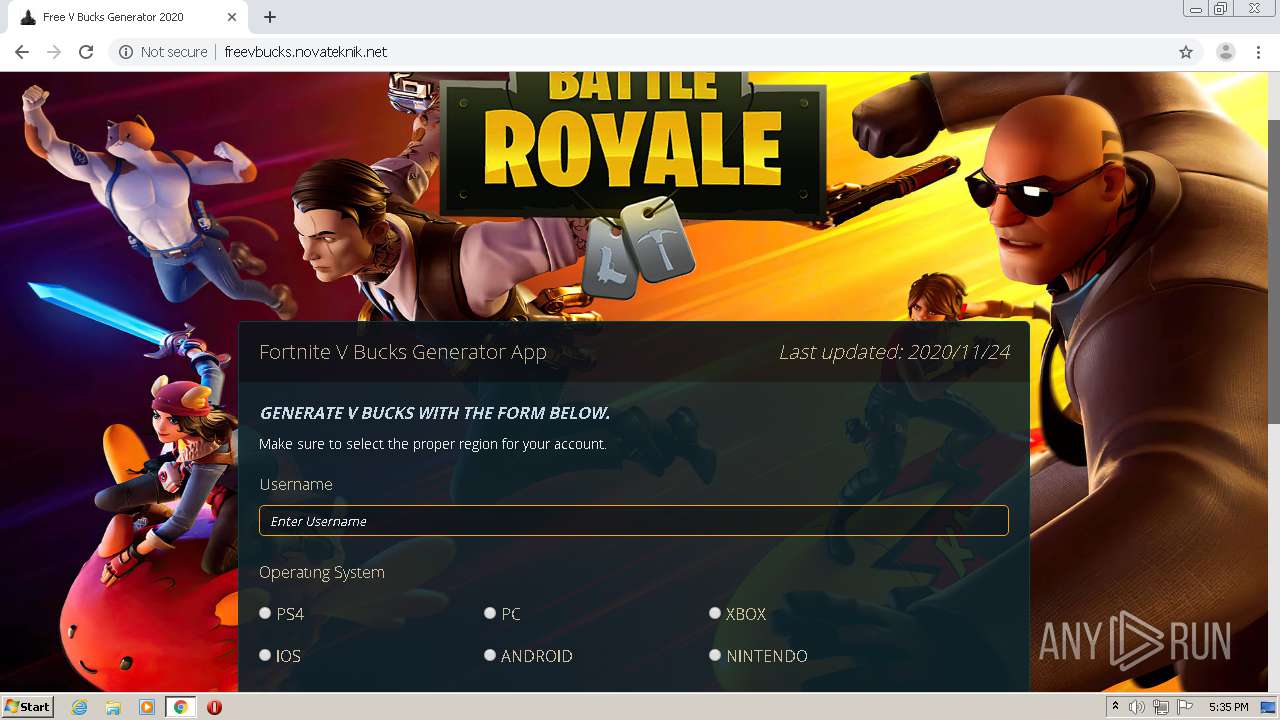
2904 | chrome.exe | GET | 200 | 192.64.118.108:80 | http://vbuckskins.icu/1.png | US | image | 46.8 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 67.225.152.21:80 | http://freevbucks.novateknik.net/media/font-awesome.min.css | US | text | 6.54 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 67.225.152.21:80 | http://freevbucks.novateknik.net/og.php?tool=cl&toolarg=s&id=2b68bec0c2256e31ee1641030cf66d99 | US | text | 1.28 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 192.64.118.108:80 | http://vbuckskins.icu/ | US | html | 652 b | suspicious |
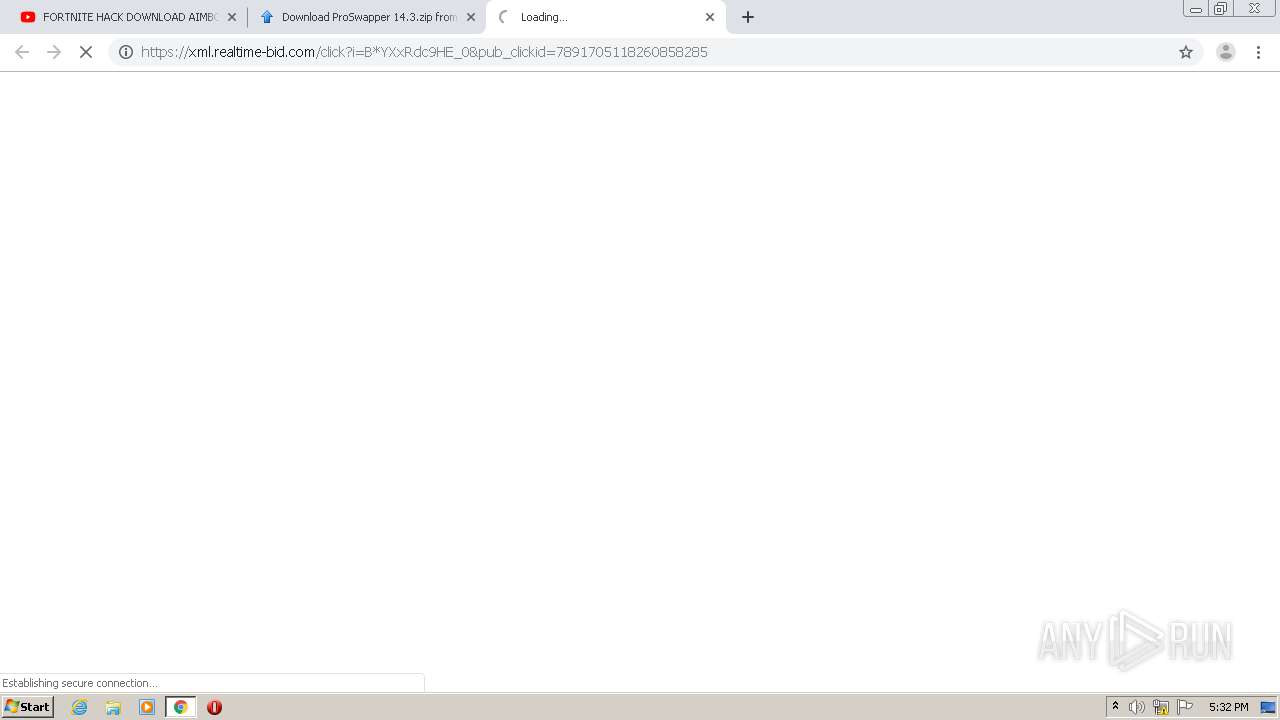
3248 | chrome.exe | GET | 302 | 18.200.170.55:80 | http://performance.affiliaxe.com/aff_c?offer_id=28127&aff_id=12958&aff_sub=12038&aff_sub2=f59c1db6-a94d-47f3-a193-7a730b1385cd | US | html | 300 b | suspicious |
2904 | chrome.exe | GET | 200 | 67.225.152.21:80 | http://freevbucks.novateknik.net/media/15860938316492ea693e076818b711015ec01b6461.jpg | US | image | 254 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 67.225.152.21:80 | http://freevbucks.novateknik.net/media/1527779044eb29bf06b89f3209ae1c61773c32e4b8.png | US | image | 124 Kb | suspicious |
2904 | chrome.exe | GET | 200 | 67.225.152.21:80 | http://freevbucks.novateknik.net/media/jquery-ui.min.css | US | text | 7.58 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.16.174:443 | consent.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.213.14:443 | consent.google.se | Google Inc. | US | whitelisted |
3248 | chrome.exe | 216.58.207.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.se |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3248 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |