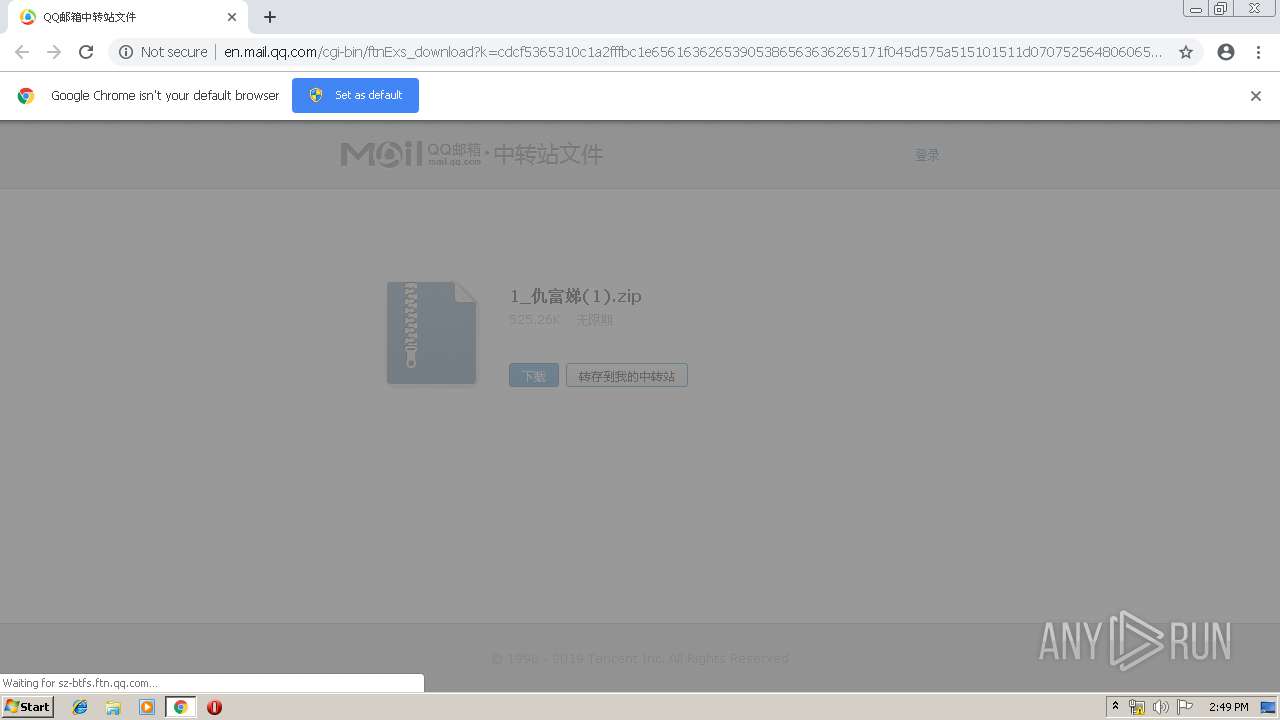
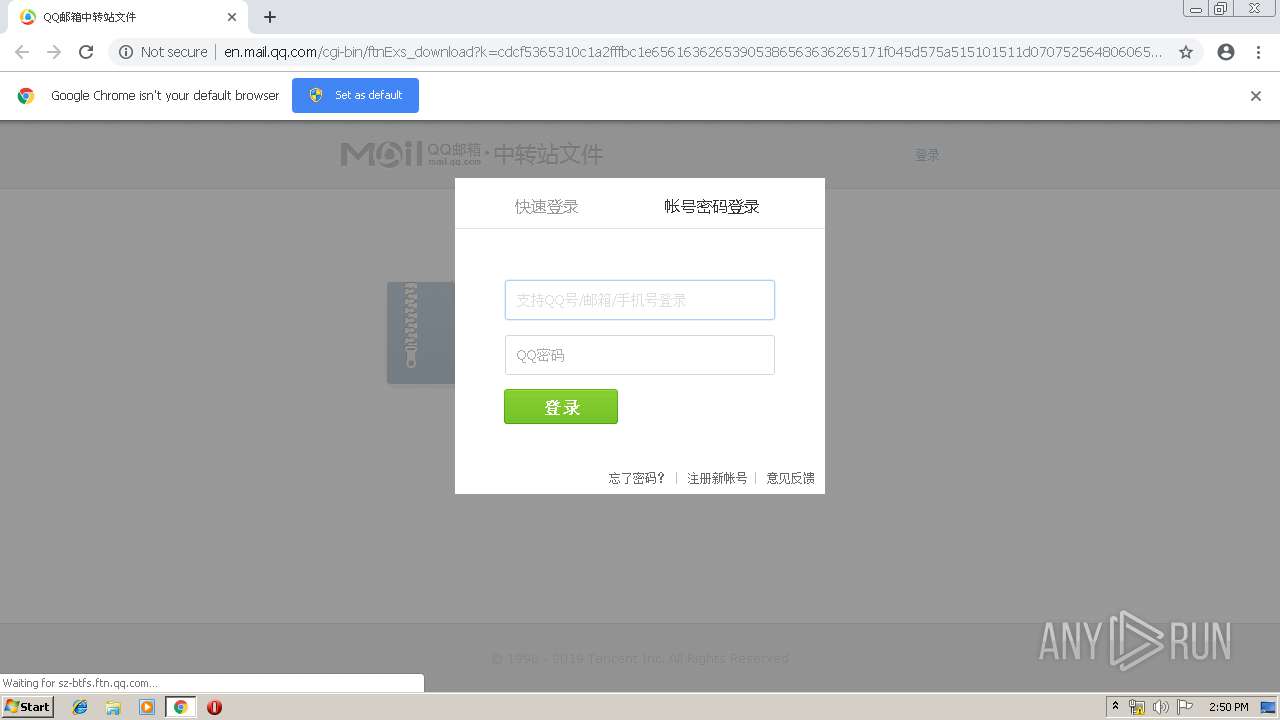
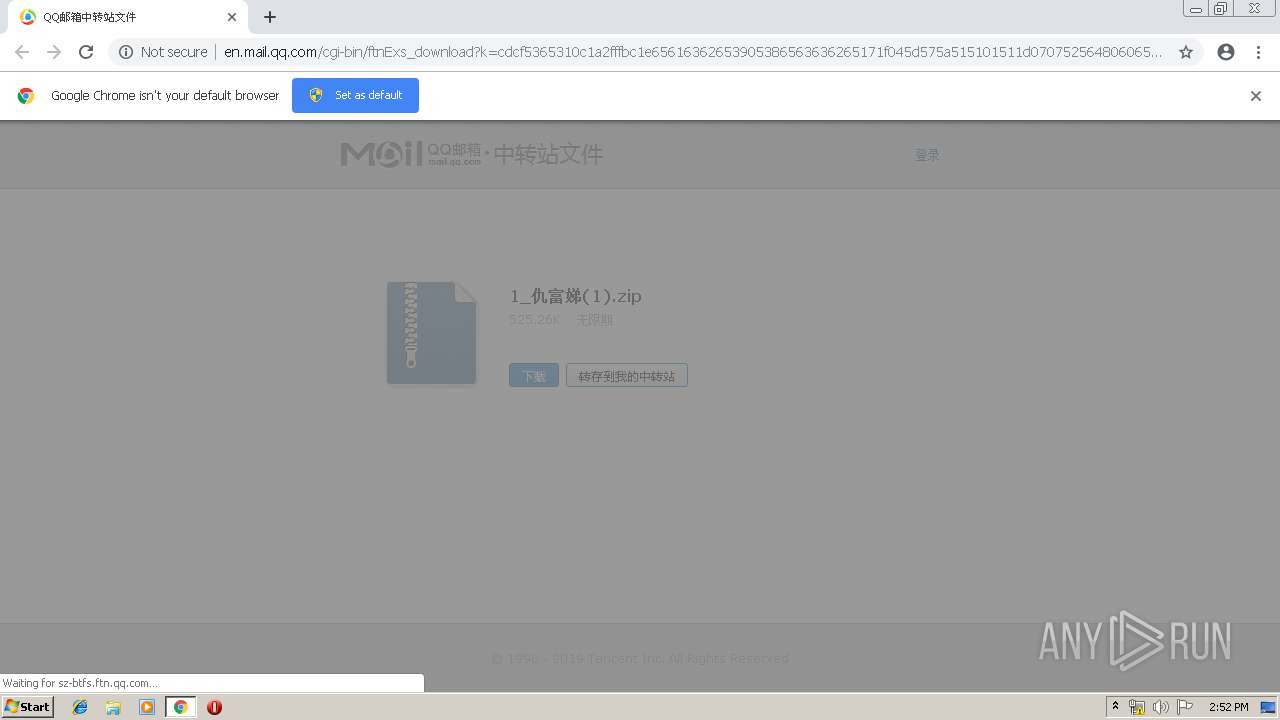
| URL: | http://mail.qq.com/cgi-bin/ftnExs_download?k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&t=exs_ftn_download&code=200eccbe&from=mobile&expiretime=-1&fsize=525.26K&suffix=zip&from=mobile&expiretime=0&fsize=525.26K&suffix=zip |
| Full analysis: | https://app.any.run/tasks/c0735183-4744-4ed8-8f4c-35cc7d47deca |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 13:48:47 |
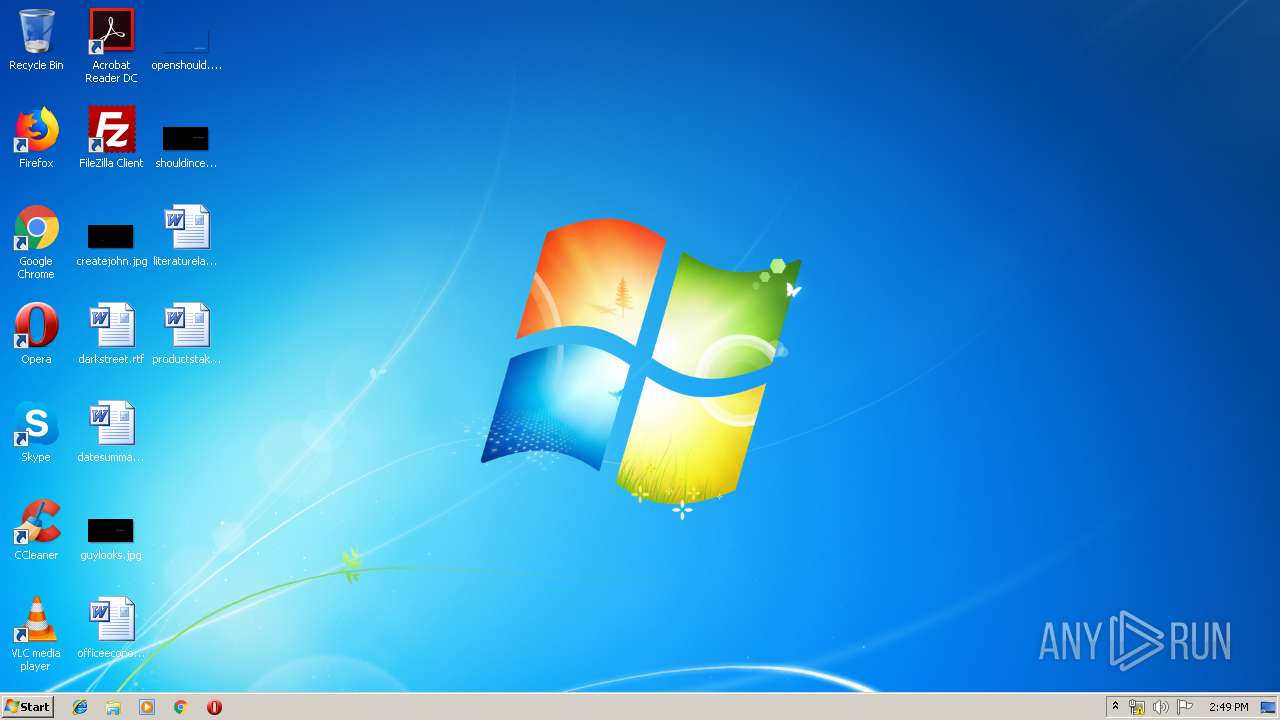
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9939023BD4C1EE8B2487680E9DE9DD38 |
| SHA1: | A90CA90DBCC44A270437E8390AE6191CE92D9A3D |
| SHA256: | 26FA905B08778EFD5130A3A75E233EFE20DCB8C7FAE6A7810245E34A33B1E432 |
| SSDEEP: | 12:8jrvnRSval2vJK38BS9spBXxSLvf/JtGaJtxcy:8jrRSyl283H9sptytftJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3376)
INFO
Application launched itself
- chrome.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6356088624882300803 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6356088624882300803 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --service-pipe-token=16422241629782155459 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16422241629782155459 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --service-pipe-token=1054983337464922648 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1054983337464922648 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15145457068731222638 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15145457068731222638 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6482690560804747269 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=789629784475373438 --mojo-platform-channel-handle=4488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --service-pipe-token=17596412431970965992 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17596412431970965992 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13113196947758092781 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c680f18,0x6c680f28,0x6c680f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,1202593172576514276,2785419405118137926,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9414453336610807231 --mojo-platform-channel-handle=3816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
564
Read events
470
Write events
89
Delete events
5
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3376-13205425748080125 |
Value: 259 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
42
Text files
188
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5418db45-e6de-4e19-abda-56aaa8a172dc.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
78
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | chrome.exe | GET | — | 183.61.38.200:80 | http://sz-btfs.ftn.qq.com/ftn_handler/ad07ac212ab35c8874b8e45279eb4a1a7255066ecc68cc5687bda93b1e0c08d59fa4549b683f25777c67add0202bc5df8961b30888dca34e73520707275ac447/?fname=1_%B3%F0%B8%BB%E6%B7(1).zip&k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&fr=00&&txf_fid=f681e5236a69d643b34dfec10fab011f58893ad3 | CN | — | — | unknown |
3376 | chrome.exe | GET | — | 183.61.38.200:80 | http://sz-btfs.ftn.qq.com/ftn_handler/ad07ac212ab35c8874b8e45279eb4a1a7255066ecc68cc5687bda93b1e0c08d59fa4549b683f25777c67add0202bc5df8961b30888dca34e73520707275ac447/?fname=1_%B3%F0%B8%BB%E6%B7(1).zip&k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&fr=00&&txf_fid=f681e5236a69d643b34dfec10fab011f58893ad3 | CN | — | — | unknown |
3376 | chrome.exe | GET | — | 183.61.38.200:80 | http://sz-btfs.ftn.qq.com/ftn_handler/ad07ac212ab35c8874b8e45279eb4a1a7255066ecc68cc5687bda93b1e0c08d59fa4549b683f25777c67add0202bc5df8961b30888dca34e73520707275ac447/?fname=1_%B3%F0%B8%BB%E6%B7(1).zip&k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&fr=00&&txf_fid=f681e5236a69d643b34dfec10fab011f58893ad3 | CN | — | — | unknown |
3376 | chrome.exe | GET | — | 183.61.38.200:80 | http://sz-btfs.ftn.qq.com/ftn_handler/ad07ac212ab35c8874b8e45279eb4a1a7255066ecc68cc5687bda93b1e0c08d59fa4549b683f25777c67add0202bc5df8961b30888dca34e73520707275ac447/?fname=1_%B3%F0%B8%BB%E6%B7(1).zip&k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&fr=00&&txf_fid=f681e5236a69d643b34dfec10fab011f58893ad3 | CN | — | — | unknown |
3376 | chrome.exe | GET | 302 | 103.7.30.100:80 | http://mail.qq.com/cgi-bin/ftnExs_download?k=cdcf5365310c1a2fffbc1e65616362653905386563636265171f045d575a515101511d0707525648060656044e025a07041d5553050150010a09085d02057065036fd4dee486cde9d798934d524a4c1f5b402493e286410f5be673d62e9da36a99312f3dea59b1&t=exs_ftn_download&code=200eccbe&from=mobile&expiretime=-1&fsize=525.26K&suffix=zip&from=mobile&expiretime=0&fsize=525.26K&suffix=zip | CN | — | — | shared |
3376 | chrome.exe | GET | 200 | 2.16.186.25:80 | http://r99.res.qqmail.com/zh_CN/htmledition/style/ft_download327bfb.css | unknown | text | 3.42 Kb | whitelisted |
3376 | chrome.exe | GET | 200 | 2.16.186.25:80 | http://r99.res.qqmail.com/zh_CN/htmledition/js/all4699d6.js | unknown | text | 108 Kb | whitelisted |
3376 | chrome.exe | GET | 200 | 2.16.186.25:80 | http://r99.res.qqmail.com/zh_CN/htmledition/js/qmptlogin2ff953.js | unknown | text | 1.94 Kb | whitelisted |
3376 | chrome.exe | GET | 200 | 103.7.30.100:80 | http://en.mail.qq.com/zh_CN/htmledition/images/xdisk/ftn_icon/ftn_compress_8.png | CN | image | 9.11 Kb | malicious |
3376 | chrome.exe | GET | 200 | 2.16.186.25:80 | http://r99.res.qqmail.com/zh_CN/htmledition/images/ftn/ftn_download_bg1e9c5d.png | unknown | image | 3.93 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 103.7.30.100:80 | mail.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
3376 | chrome.exe | 2.16.186.25:80 | r99.res.qqmail.com | Akamai International B.V. | — | whitelisted |
3376 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 203.205.138.79:80 | imgcache.qq.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
3376 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 183.61.38.200:80 | sz-btfs.ftn.qq.com | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mail.qq.com |
| shared |
accounts.google.com |
| shared |
en.mail.qq.com |
| malicious |
r99.res.qqmail.com |
| whitelisted |
imgcache.qq.com |
| whitelisted |
sz-btfs.ftn.qq.com |
| unknown |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |