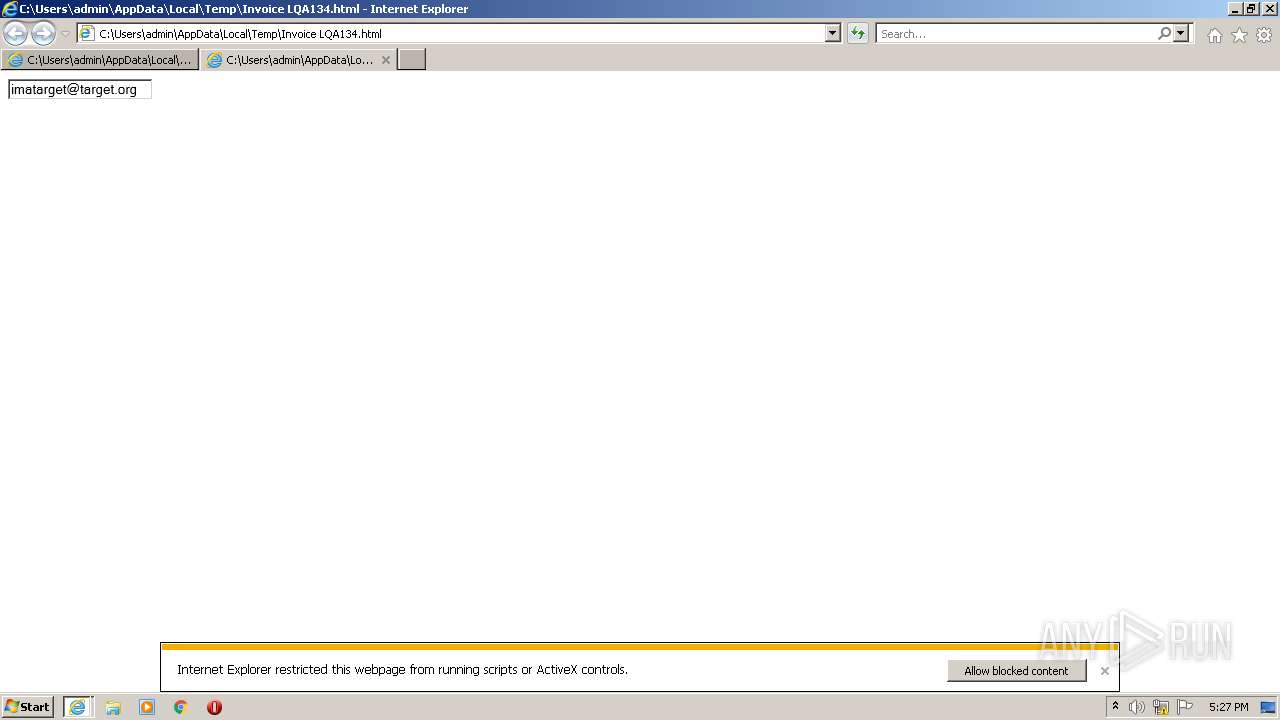
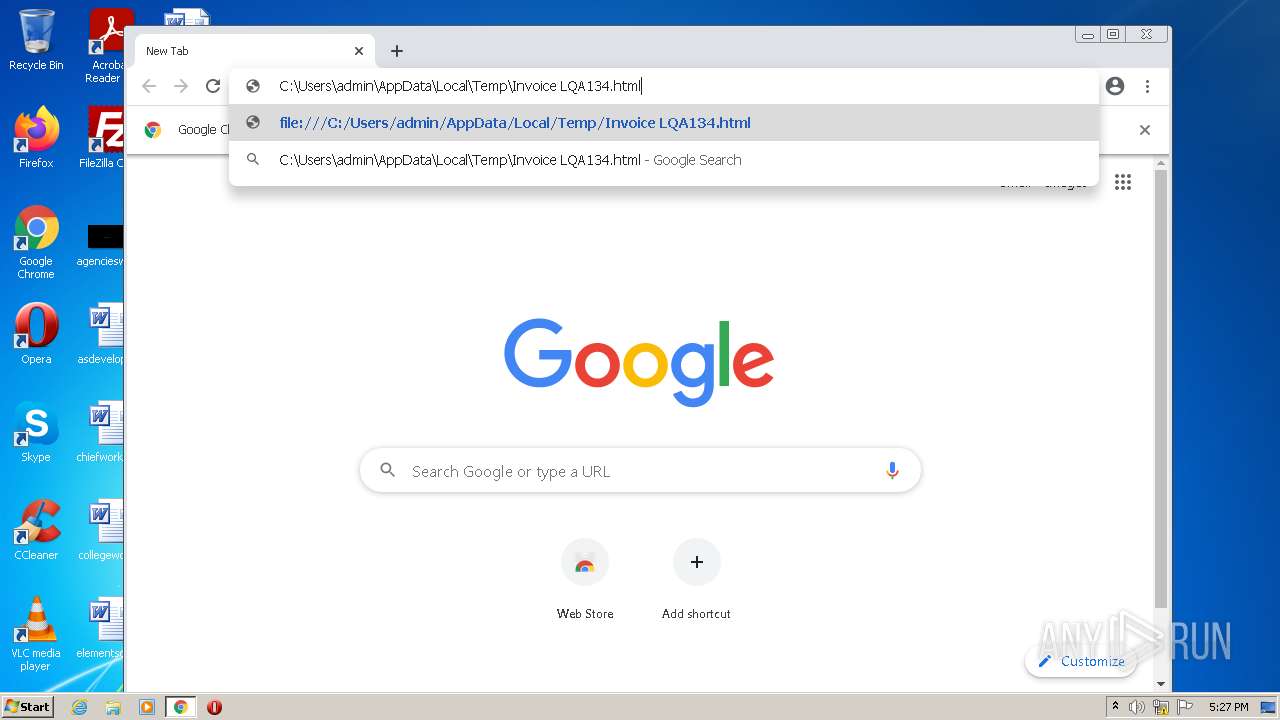
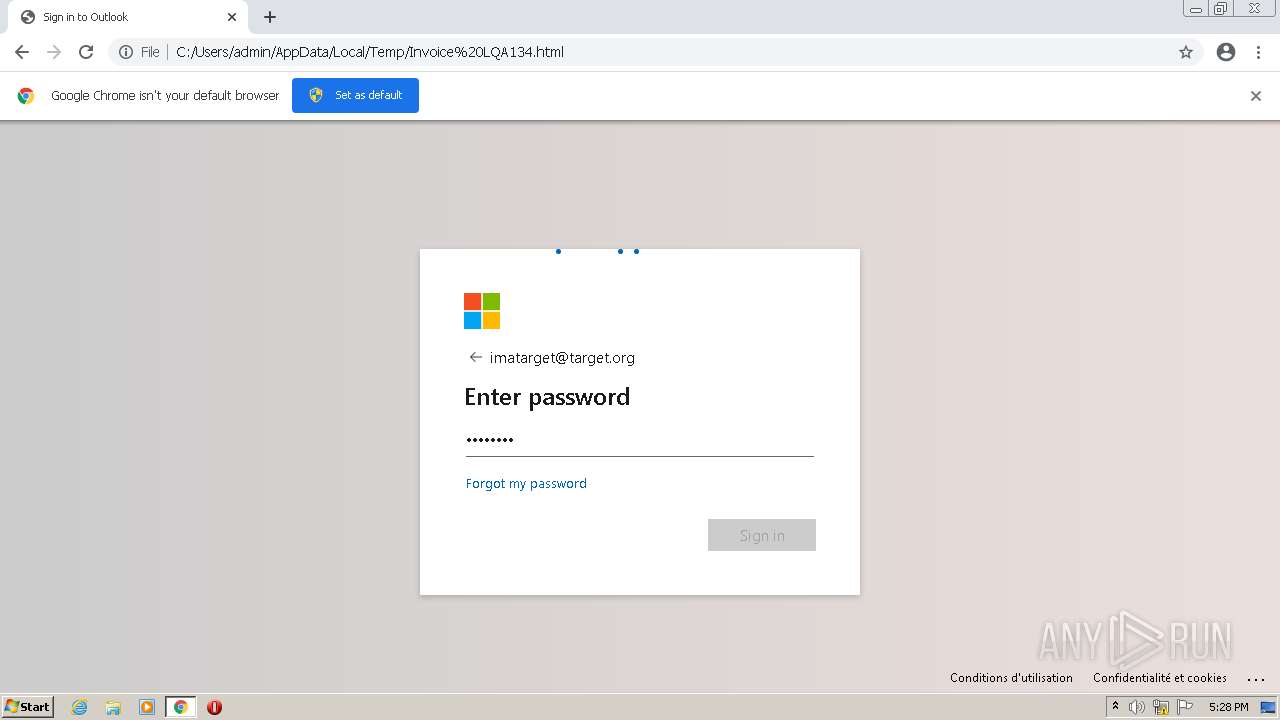
| File name: | Invoice LQA134.html |
| Full analysis: | https://app.any.run/tasks/78255e5f-d258-4c3f-9461-82eeb0cd99e2 |
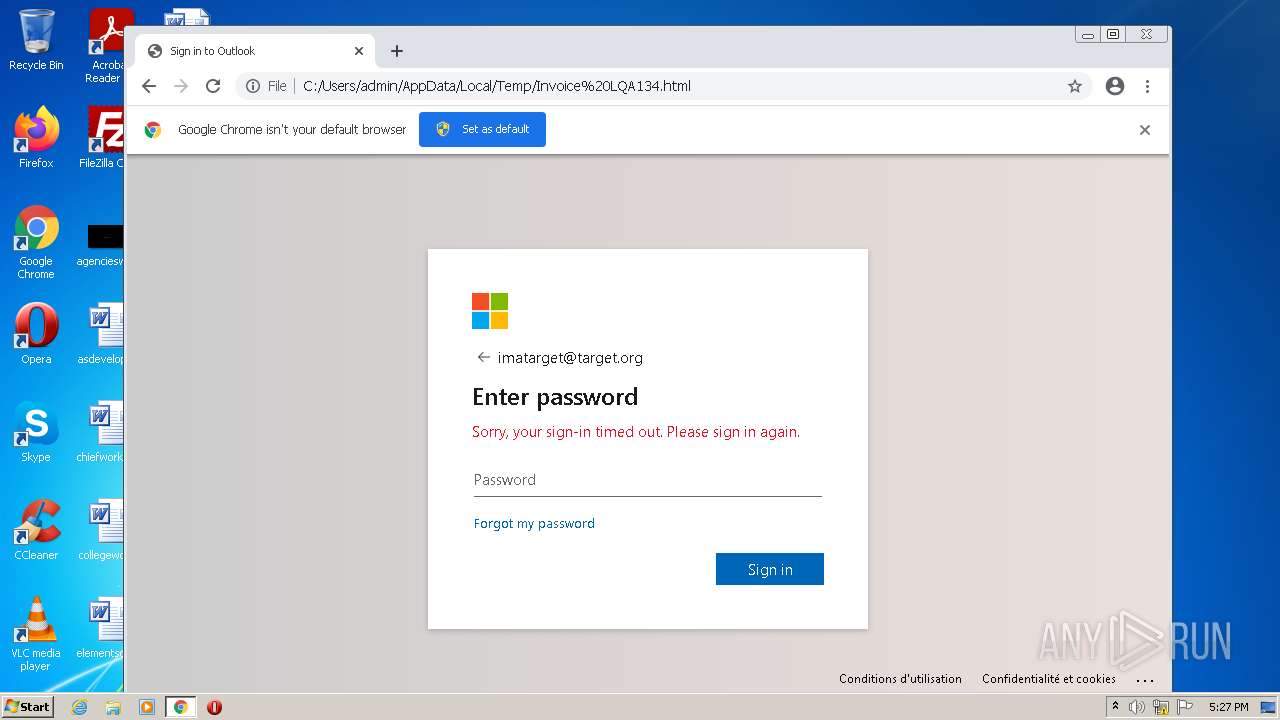
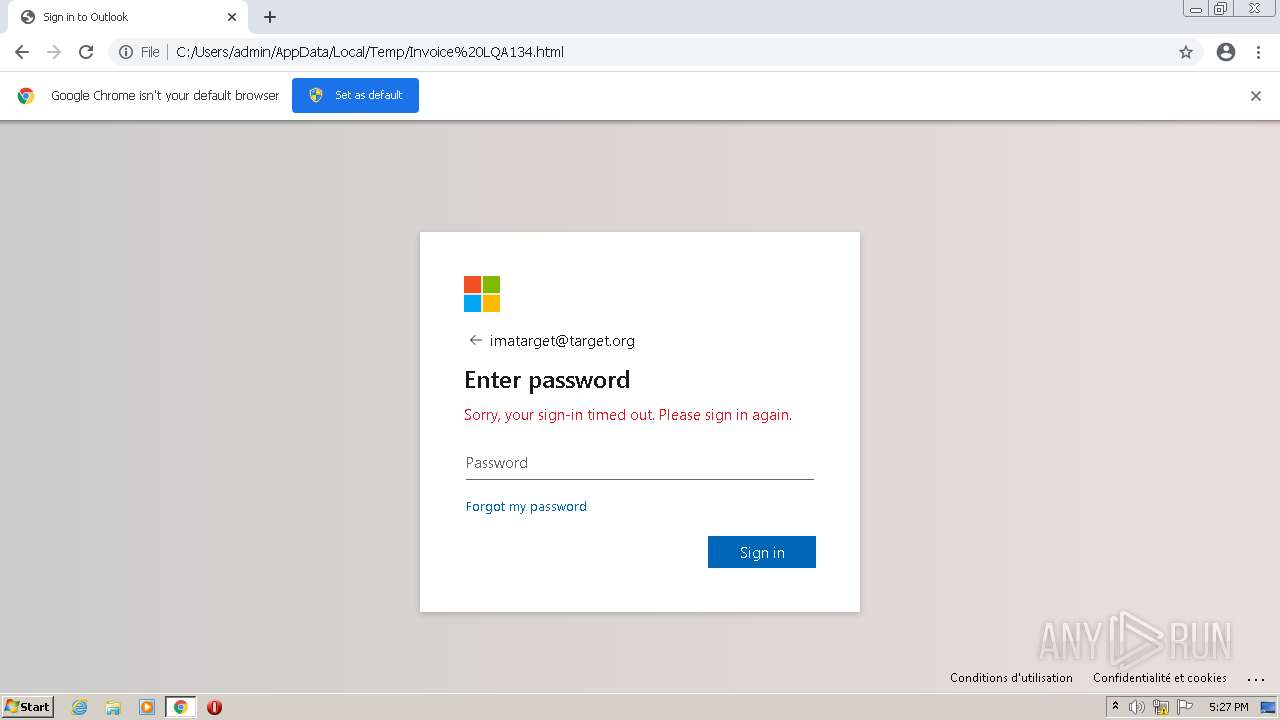
| Verdict: | Suspicious activity |
| Analysis date: | March 26, 2022, 17:27:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | EDF767D60614C42D39A4FA586C01B6B8 |
| SHA1: | 530FDBFC5B32D2ECDACFA7FA42A339172CF24B3D |
| SHA256: | 26FA008FB38CA01EDB3952C23943AA5AE791ECB286F81B5D908217B25F18D8D5 |
| SSDEEP: | 3072:f8gJ+cbBONCmQhrNkozJqvQEwXXa3LwCjJWTVQwYVKEQ:v+cONCmQ+QZnKLpjJyQR/Q |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1924)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2556)
INFO
Checks supported languages
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 860)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 484)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 188)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 404)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 1876)
Reads the computer name
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 1924)
- iexplore.exe (PID: 860)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 1876)
Changes internet zones settings
- iexplore.exe (PID: 2728)
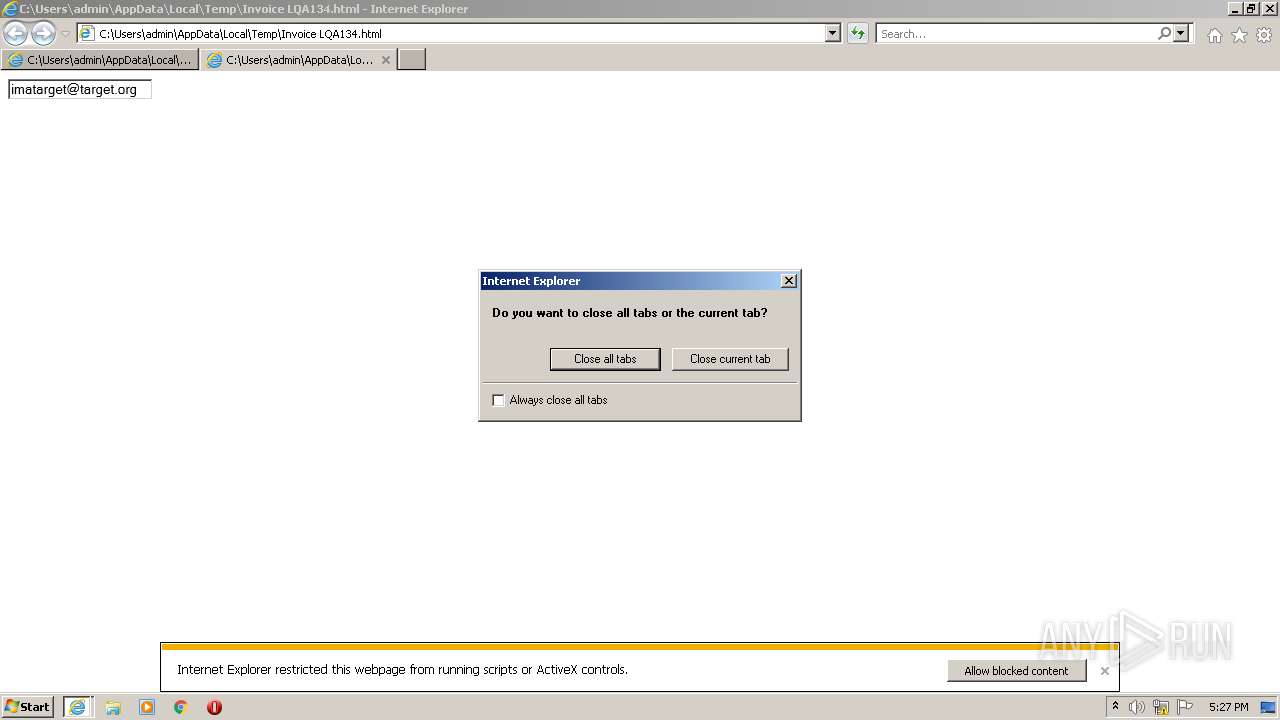
Application launched itself
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 1924)
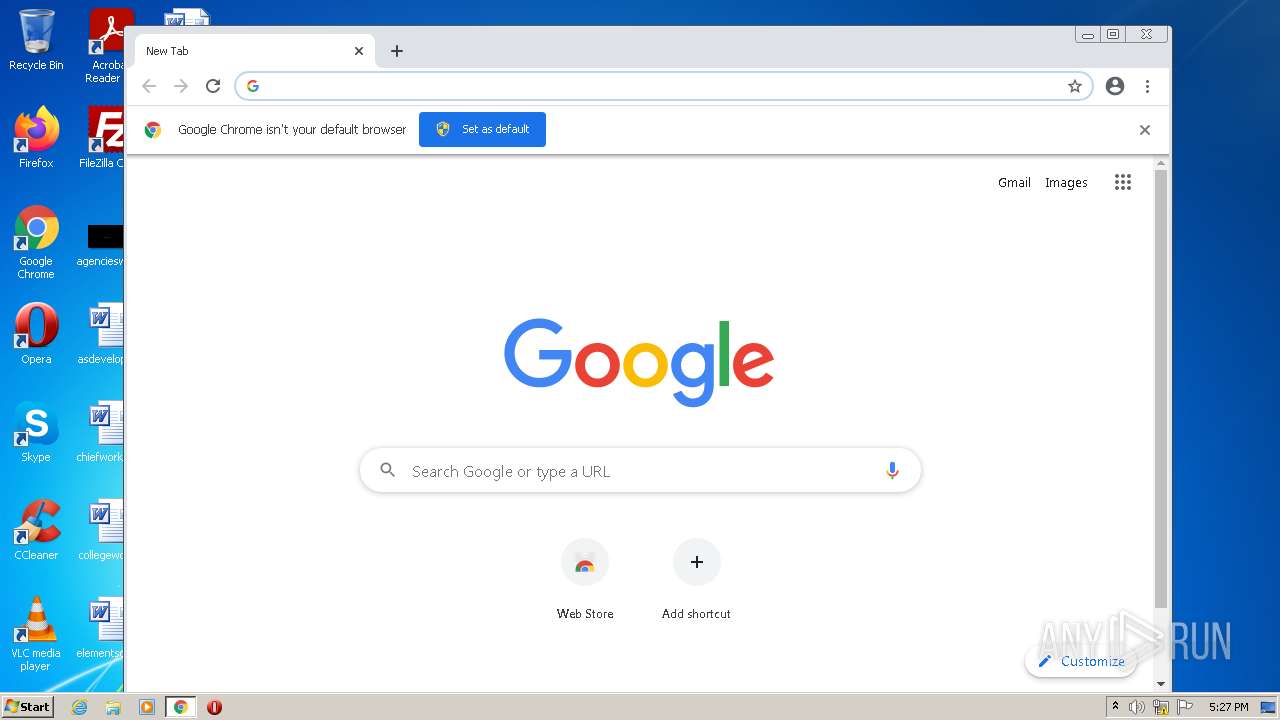
- chrome.exe (PID: 2556)
Reads internet explorer settings
- iexplore.exe (PID: 1924)
Reads settings of System Certificates
- iexplore.exe (PID: 2728)
- chrome.exe (PID: 3356)
Reads the date of Windows installation
- iexplore.exe (PID: 2728)
- chrome.exe (PID: 1876)
Checks Windows Trust Settings
- iexplore.exe (PID: 2728)
Manual execution by user
- chrome.exe (PID: 2556)
Reads the hosts file
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
56
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2728 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,9019701801308215191,5060584571780811672,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2728 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\Invoice LQA134.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 397
Read events
21 149
Write events
245
Delete events
3
Modification events
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30949686 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30949686 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
129
Text files
90
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EA6AA0FD78EA3DA6ECB56ACD1A156E9A | SHA256:5A05B5DDB1DA846741481592CB8C5339A2A6C55A9FD114E1EC930EA7B4BD6752 | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{0B07F65A-AD2A-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:5A8280C3706FADC5CBBFBB06A9A39B89 | SHA256:C3555A6832386AF85D4A8E397D27F47B46E9A25D810AFD7690B2C5C332A4CC81 | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-623F4D11-9FC.pma | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1EADEFDD937872ED.TMP | gmc | |
MD5:BE654443BB7894F28CAAADFE9757927B | SHA256:4799E2246A38C76F7621D99B022D1CB0A257D0A1F928666C064C4E77ED5AD1EE | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF570CEB2284A11240.TMP | gmc | |
MD5:807BA873EBA7A8A29AB54CC7E3DABDAE | SHA256:95DCD7F214A2AF40D0FC8BA51FE2D59230886123C3089BC35DF63B58218F8C7B | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:A2B4E909C9C1DCB6802265789C25E476 | SHA256:7BD0E22D2371C1C0C58C48EE20E6C975D45AD95FE7BAA27B340CAEC551B3BEDD | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:7A32C9BBA6C40A9ED86AD2D6B8DAB729 | SHA256:388CBFB1256AEC82D028C8D632F00B462AA909C7FF3501E04ED8186738E55B9A | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{0B07F659-AD2A-11EC-BE1B-12A9866C77DE}.dat | binary | |
MD5:4AB0F89FB505564FFAE1652464401243 | SHA256:26781CD3177651CBE862EF5DB08F7269232EBB272EEFDAE168C4ECEFC3C0F091 | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF491757ED01292DD.TMP | gmc | |
MD5:123BCA4601D070DF2B009EDAF2629446 | SHA256:DB4A2AD12F41D2063A388954AF7AA2107868D920A1E5E4624A3FBA4EB330CFF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3356 | chrome.exe | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
3356 | chrome.exe | GET | 200 | 188.120.127.142:80 | http://r3---sn-nvm-cxbz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.86.200.90&mm=28&mn=sn-nvm-cxbz&ms=nvh&mt=1648315223&mv=m&mvi=3&pl=25&rmhost=r1---sn-nvm-cxbz.gvt1.com&shardbypass=sd&smhost=r1---sn-nvm-cxbs.gvt1.com | RS | crx | 242 Kb | whitelisted |
2728 | iexplore.exe | GET | 200 | 23.32.238.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?62ebceabaa1fbbef | US | compressed | 4.70 Kb | whitelisted |
2728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3356 | chrome.exe | POST | — | 159.223.143.85:80 | http://159.223.143.85/fdkjghdfjkgvutereryecfc/kdfjhgskdjgheterererwfkcbswcfe/dsfkjdgsttrrererwbdk776653ncfkbvge.php | US | — | — | suspicious |
2728 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c4d1992dc9b80147 | US | compressed | 4.70 Kb | whitelisted |
2728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3356 | chrome.exe | HEAD | — | 159.223.143.85:80 | http://159.223.143.85/fdkjghdfjkgvutereryecfc/kdfjhgskdjgheterererwfkcbswcfe/dsfkjdgsttrrererwbdk776653ncfkbvge.php | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2728 | iexplore.exe | 23.32.238.208:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
2728 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2728 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3356 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
3356 | chrome.exe | 142.250.185.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3356 | chrome.exe | 188.120.127.142:80 | r3---sn-nvm-cxbz.gvt1.com | Serbian Open Exchange DOO | RS | whitelisted |
3356 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report