| File name: | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin |
| Full analysis: | https://app.any.run/tasks/c7646456-cead-49b8-b318-ccb8fabfd1ce |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2026, 14:38:57 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 3779B1981EC400046F8A7F8C9973F75B |
| SHA1: | 619FD9BF9B091DBCD011998C498F8AA1CE8C9D59 |
| SHA256: | 26EF05EFAE0D0D6F04302AACD9CCB8104A51BD87E61E9485375A0DCACAFC135D |
| SSDEEP: | 98304:bL9T2gNT5OqfI65M0ixGIxC1WDMC8+eQIFGbMzXJTv7a6iCB3YdtTvV:Uus |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1872)
SUSPICIOUS
ADVANCEDINSTALLER mutex has been found
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
Reads settings of System Certificates
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
Reads the Internet Settings
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- powershell.exe (PID: 6800)
Reads the Windows owner or organization settings
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
Executable content was dropped or overwritten
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1872)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1872)
The process executes Powershell scripts
- powershell.exe (PID: 6800)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1872)
Bypass execution policy to execute commands
- powershell.exe (PID: 6800)
Detects AdvancedInstaller (YARA)
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6800)
INFO
Reads the computer name
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 3148)
- msiexec.exe (PID: 1872)
Checks supported languages
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 3148)
- msiexec.exe (PID: 1872)
The sample compiled with english language support
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
Reads Environment values
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 1872)
Reads security settings of Internet Explorer
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 4872)
- powershell.exe (PID: 6800)
Reads the machine GUID from the registry
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 3796)
Creates files or folders in the user directory
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
Create files in a temporary directory
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
- msiexec.exe (PID: 1872)
- powershell.exe (PID: 6800)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3796)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6800)
Disables trace logs
- powershell.exe (PID: 6800)
Reads settings of System Certificates
- powershell.exe (PID: 6800)
There is functionality for taking screenshot (YARA)
- 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe (PID: 2760)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 6800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:17 09:40:36+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.26 |
| CodeSize: | 1535488 |
| InitializedDataSize: | 588288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x121f67 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.6.5 |
| ProductVersionNumber: | 2.3.6.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
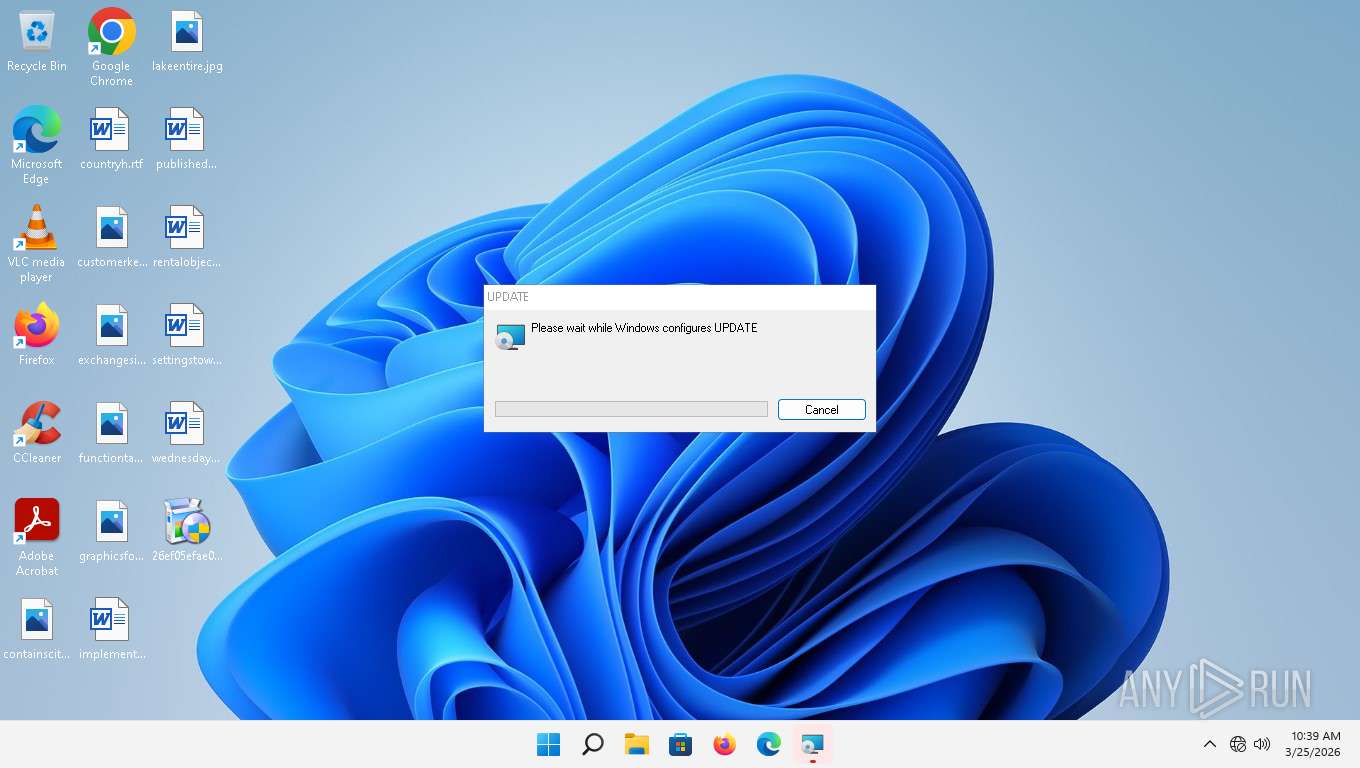
| CompanyName: | UPDATE |
| FileDescription: | UPDATE Installer |
| FileVersion: | 2.3.6.5 |
| InternalName: | Updateeee3 |
| LegalCopyright: | Copyright (C) 2026 UPDATE |
| OriginalFileName: | Updateeee3.exe |
| ProductName: | UPDATE |
| ProductVersion: | 2.3.6.5 |
Total processes
140
Monitored processes
10
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1872 | C:\Windows\syswow64\MsiExec.exe -Embedding 0DC841E5BEB015614EE7945B7364A71C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 135.0.7023.0 Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=135.0.7023.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x294,0x298,0x29c,0x270,0x2a0,0xb24850,0xb2485c,0xb24868 | C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 135.0.7023.0 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\Desktop\26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe" | C:\Users\admin\Desktop\26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | explorer.exe | ||||||||||||
User: admin Company: UPDATE Integrity Level: HIGH Description: UPDATE Installer Exit code: 0 Version: 2.3.6.5 Modules
| |||||||||||||||
| 3148 | C:\Windows\syswow64\MsiExec.exe -Embedding 5F5A085A47219A8C34DC3FC0BF7CD5E3 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3796 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4872 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\UPDATE\UPDATE 2.3.6.5\install\Updateeee3.msi" AI_SETUPEXEPATH=C:\Users\admin\Desktop\26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe SETUPEXEDIR=C:\Users\admin\Desktop\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1774448195 " AI_EUIMSI="" | C:\Windows\SysWOW64\msiexec.exe | — | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6732 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6800 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss9B86.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi9B64.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr9B65.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr9B66.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 574 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7156 | "C:\Users\admin\Desktop\26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe" | C:\Users\admin\Desktop\26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | — | explorer.exe | |||||||||||
User: admin Company: UPDATE Integrity Level: MEDIUM Description: UPDATE Installer Exit code: 3221226540 Version: 2.3.6.5 Modules
| |||||||||||||||
Total events
15 990
Read events
15 954
Write events
23
Delete events
13
Modification events
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-166304369-59083888-3082702900-1001\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D40E0000E9CB222165BCDC01 | |||
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-166304369-59083888-3082702900-1001\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B01B0EB62626358B4C0DB135CEE49DDCFB4E3D47AFDEA4DE4917F335BC21E6C2 | |||
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-166304369-59083888-3082702900-1001\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\41244B54069744A4A82540428A4F1667 |
| Operation: | write | Name: | 01AA80214A312D3429827697AAD8D986 |
Value: 02:\Software\Caphyon\Advanced Installer\LZMA\{1208AA10-13A4-43D2-9228-6779AA8D9D68}\2.3.6.5\AI_ExePath | |||
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Program Files (x86)\UPDATE\UPDATE\ |
Value: 1 | |||
| (PID) Process: | (3796) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Program Files (x86)\UPDATE\ |
Value: 1 | |||
| (PID) Process: | (6800) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4e\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6800) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4e |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6800) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4f\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ci.dll,-100 |
Value: Isolated User Mode (IUM) | |||
| (PID) Process: | (6800) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4f\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ci.dll,-101 |
Value: Enclave | |||
Executable files
11
Suspicious files
25
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:E0D41FCBB9608398F79D371629F36E67 | SHA256:D46F4CABD187B305B303B9B4315759B6C343C687AD5BC187470EAA5C66E26A2F | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\Roaming\UPDATE\UPDATE 2.3.6.5\install\Updateeee3.msi | executable | |
MD5:791E4B3CE512CAA68E8001CB7DEE8D12 | SHA256:5E9378F72E5F96E0215390C8F44E4B2E0445A09EBE8781C6E5D9CB512129CDA3 | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\Local\Temp\shi97AA.tmp | executable | |
MD5:B40E4304F279119D9345BE970BABCE41 | SHA256:06285446D57089FE85B3B6127BBC92508773AF458AD5CF20ABF4570D41C0FEE7 | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:63728B5AEB426CCDBEEC753A5B260FFB | SHA256:65A3BBE100B46A7DB1A6ECDC5C80C875E5824185212565888C432259D1E857DE | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\Local\Temp\MSI97EA.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_E88B05DBFCDCEFB86087018E8B170177 | binary | |
MD5:A211B2CCB59E529D15D71B27EAA1ED44 | SHA256:0F3105073B3F7D45406B3000584FEABF371FC8BB48701402605A56C0D1707E01 | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:40219ED14177FC890C45A74840662F83 | SHA256:A5A8A1908C2097EA1212199ABFBF8A5F5927BE44A6FAB7E4AA0222F26693D7FA | |||
| 2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:FB64F997E3D157FE801ACD08DED67DDC | SHA256:96D6FE1C6B0A6ADBFB2CA46311FCD1FACF514AAF1C2A57ECDA1B0C1366D365E2 | |||
| 3796 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:C5EBE3D643BCC7C9A6EF7DC7646B0FC4 | SHA256:478C1925B1C578F155B26EF4FAB9963D562488BECC18582D3B213FCCFBE9363F | |||
| 1872 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi9B64.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
36
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6364 | svchost.exe | HEAD | 200 | 23.197.142.186:443 | https://fs.microsoft.com/fs/windows/config.json | US | — | — | whitelisted |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e05dbcf99649dadb | US | — | — | unknown |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | NL | binary | 471 b | whitelisted |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | NL | binary | 727 b | whitelisted |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAjwOlYyQbZNOnpcaqXPLY4%3D | NL | binary | 751 b | whitelisted |
3248 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?368fbc9349a1159a | US | compressed | 71.5 Kb | unknown |
3248 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d54a93af7d177287 | US | compressed | 71.5 Kb | unknown |
3248 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?13493b395631d4e5 | US | compressed | 7.61 Kb | unknown |
6856 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
6856 | svchost.exe | POST | 200 | 20.190.160.130:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1380 | svchost.exe | 23.55.161.164:80 | www.msftconnecttest.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 52.110.17.47:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2760 | 26ef05efae0d0d6f04302aacd9ccb8104a51bd87e61e9485375a0dcacafc135d.bin.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
3248 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
6800 | powershell.exe | 146.103.104.40:443 | hugomarmdarm.com | VDSINA | AE | malicious |
6856 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6856 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
1380 | svchost.exe | 23.55.161.150:80 | www.msftconnecttest.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.msftconnecttest.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
hugomarmdarm.com |
| unknown |
login.live.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1380 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
4164 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |