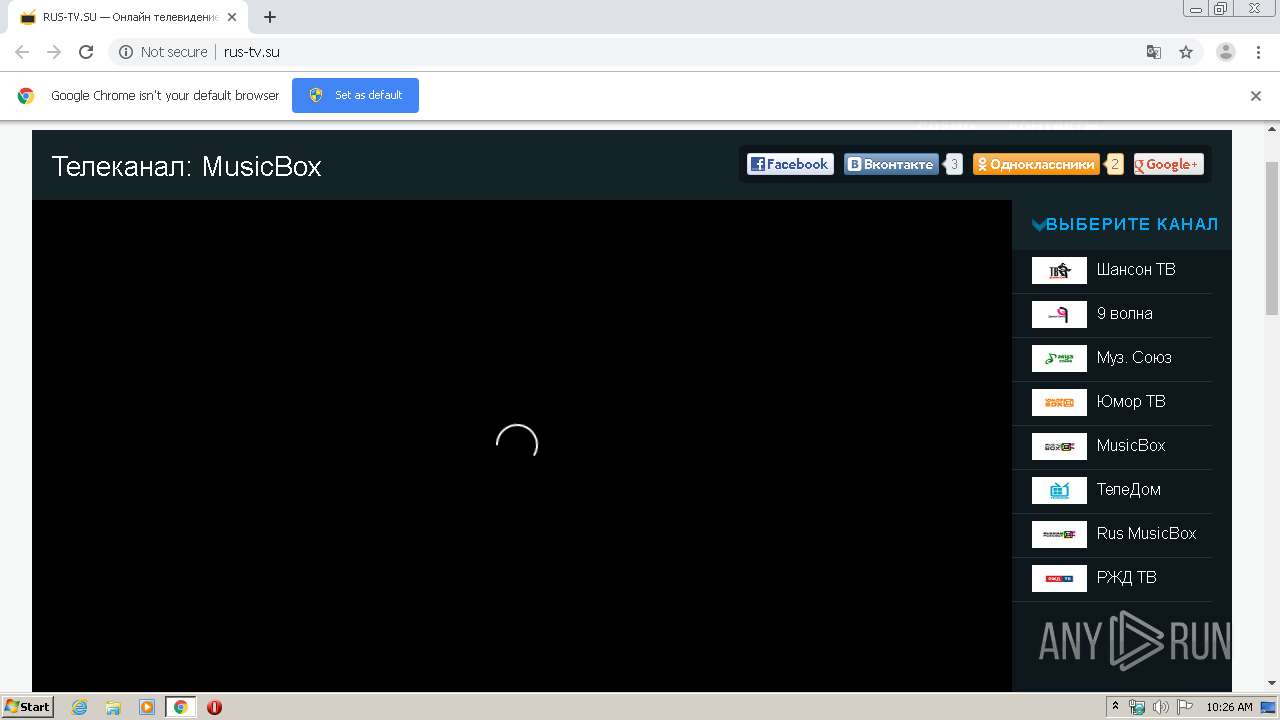
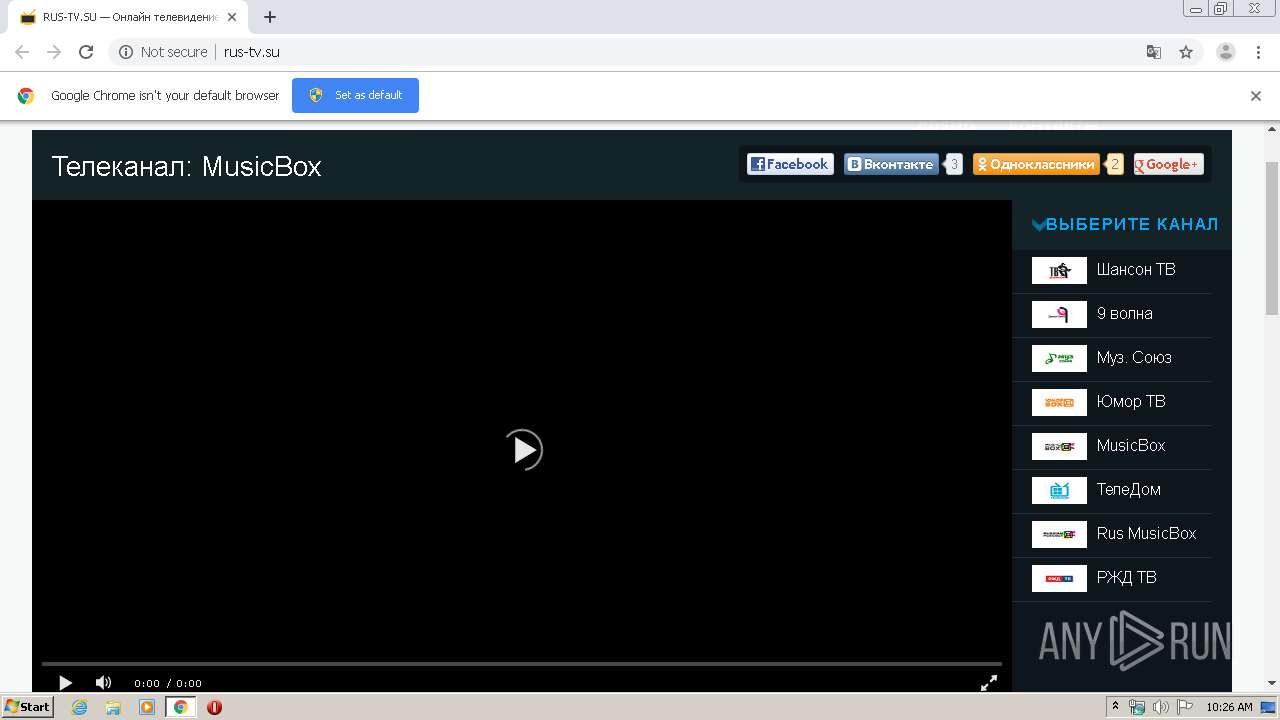
| URL: | http://rus-tv.su |
| Full analysis: | https://app.any.run/tasks/6c1de155-7757-47e0-a151-20d6361ffd4f |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2020, 10:25:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EF3D3B147DF5D7C812612647930E86B4 |
| SHA1: | DE1A4EDCC151E0CCB32A749130355AC22FE473F5 |
| SHA256: | 26DA6FB806D82231C94AD6D5B41BA6A6B25CFDCB2DC2AA720701F79C2E64577E |
| SSDEEP: | 3:N1KMI2Q:CMI3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1748)
INFO
Reads the hosts file
- chrome.exe (PID: 1748)
- chrome.exe (PID: 3164)
Changes settings of System certificates
- chrome.exe (PID: 3164)
Reads settings of System Certificates
- chrome.exe (PID: 3164)
Application launched itself
- chrome.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
59
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6984273001550093489 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18422276201486893456 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11976251341730628596 --mojo-platform-channel-handle=4720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15628628850694721282 --mojo-platform-channel-handle=1964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12057426224810751622 --mojo-platform-channel-handle=4320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3884340464659442010 --mojo-platform-channel-handle=4680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5071407568761679721 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6371708580412404003 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17650825741850491027 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5893645292308084539 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
699
Read events
570
Write events
124
Delete events
5
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1748-13229691974058750 |
Value: 259 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
163
Text files
268
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7C8346-6D4.pma | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3c5e1631-1f3a-4b67-89d5-fb7280e626b1.tmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c4f.TMP | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c4f.TMP | text | |
MD5:— | SHA256:— | |||
| 1696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66db6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
180
DNS requests
110
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/style.css?ver=2013-07-18 | US | text | 15.4 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/plugins/meteor-slides/css/meteor-slides.css?ver=1.0 | US | text | 1.24 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/logo4.png | US | image | 1.62 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/plugins/lightbox/css/frontend/colorbox-2.css?ver=4.0.29 | US | text | 1.03 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/shanson-logo.jpg | US | image | 1.99 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/humor-tv-logo.jpg | US | image | 3.04 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/musicbox-logo.jpg | US | image | 2.09 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/muzsoyuz-logo.jpg | US | image | 2.24 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.64.100.13:80 | http://rus-tv.su/wp-content/themes/rustv/images/9volna-logo.jpg | US | image | 1.80 Kb | suspicious |
3164 | chrome.exe | GET | 200 | 172.217.22.74:80 | http://fonts.googleapis.com/css?family=Source+Sans+Pro%3A300%2C400%2C700%2C300italic%2C400italic%2C700italic%7CBitter%3A400%2C700&subset=latin%2Clatin-ext | US | text | 1.04 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | chrome.exe | 178.154.131.216:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
3164 | chrome.exe | 172.64.100.13:80 | rus-tv.su | Cloudflare Inc | US | shared |
3164 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3164 | chrome.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3164 | chrome.exe | 172.217.22.74:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3164 | chrome.exe | 172.217.16.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3164 | chrome.exe | 212.109.217.75:443 | tivizor.ru | JSC ISPsystem | RU | unknown |
3164 | chrome.exe | 77.88.21.179:443 | ads.adfox.ru | YANDEX LLC | RU | whitelisted |
3164 | chrome.exe | 172.217.22.35:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3164 | chrome.exe | 213.180.193.90:443 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rus-tv.su |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
yastatic.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
tivizor.ru |
| unknown |
ajax.googleapis.com |
| whitelisted |
ads.adfox.ru |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
an.yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3164 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |