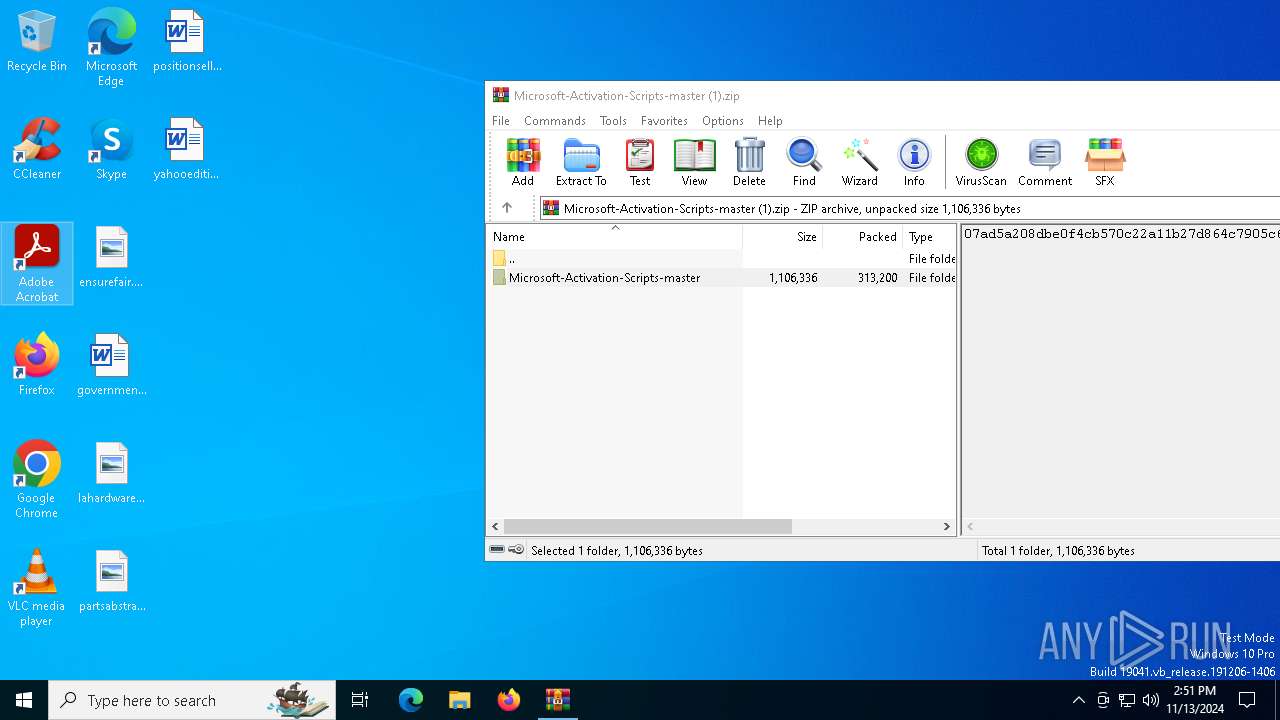
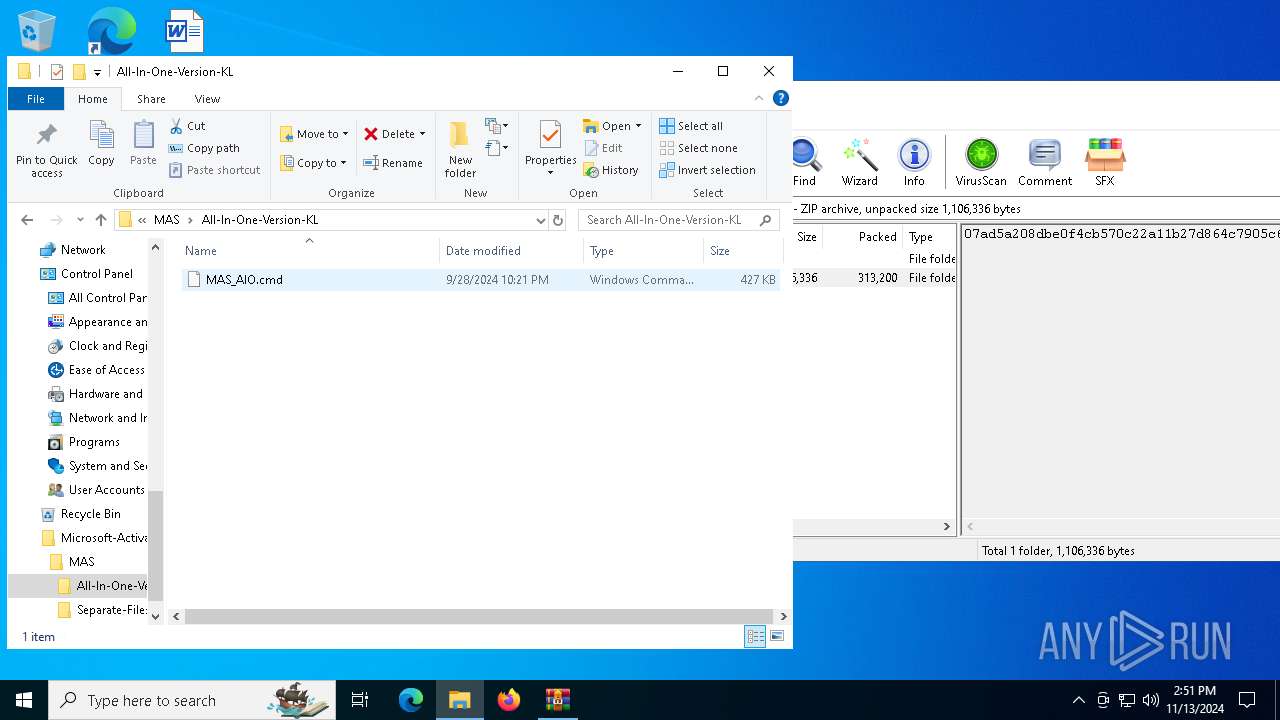
| File name: | Microsoft-Activation-Scripts-master (1).zip |
| Full analysis: | https://app.any.run/tasks/34b2ce33-69f9-4ec4-aea8-287cc3d697c9 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2024, 14:50:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 3973CB0DA65FC881008031AC388046B2 |
| SHA1: | 24DD6E62125508A6DB5D53E087BDDD37451ED4B8 |
| SHA256: | 26AB9DF0D662009AAA45693D94057F0B5EBCD83859772A4C082914D1D5B7AE68 |
| SSDEEP: | 6144:ZaTxEkBXOVyuq6ttBkKRFLqG3rwwCKmxx+z2x1HHDn/61NUFb0WatjlRi5WYW6pZ:Za+eMq659BbrwnljgkatBRy3fj7 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7052)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 632)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4448)
Application launched itself
- cmd.exe (PID: 7128)
- cmd.exe (PID: 632)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 1048)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 6332)
Starts SC.EXE for service management
- cmd.exe (PID: 632)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4448)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 632)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6044)
- powershell.exe (PID: 5612)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6588)
- powershell.exe (PID: 4836)
- powershell.exe (PID: 6412)
- cmd.exe (PID: 1048)
- powershell.exe (PID: 2784)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 6332)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 632)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 4700)
- cmd.exe (PID: 4448)
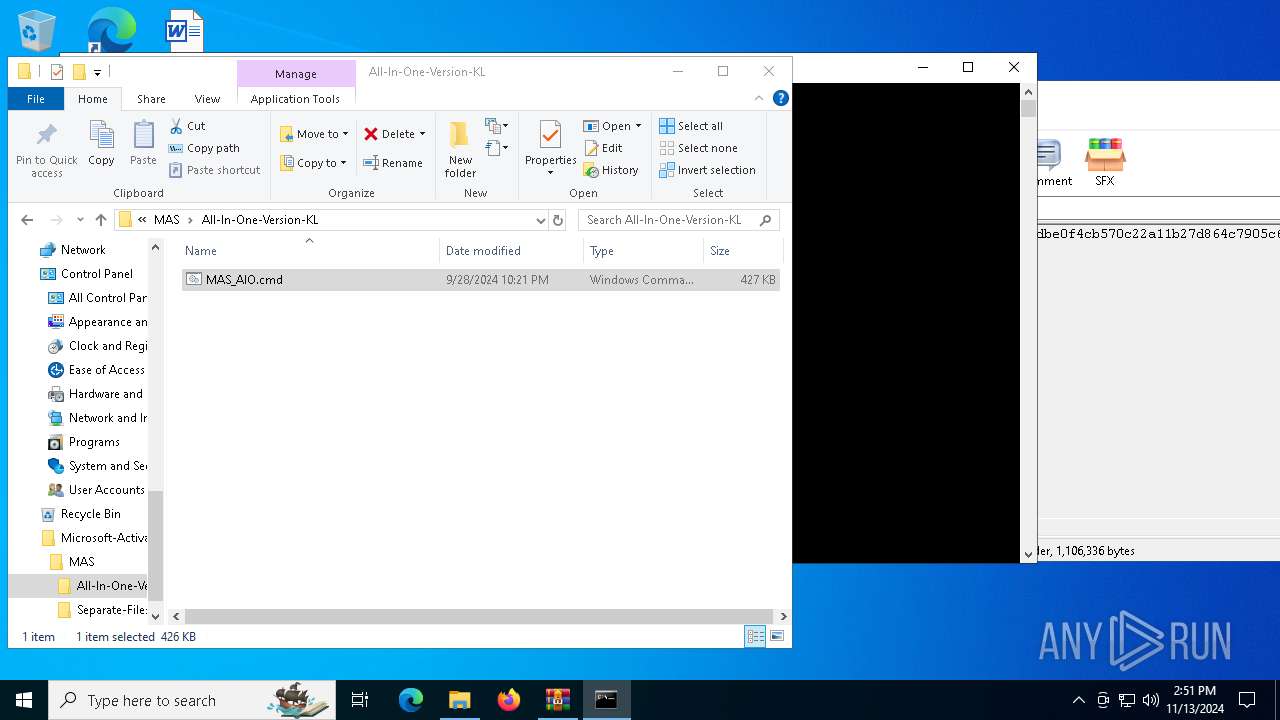
Executing commands from ".cmd" file
- cmd.exe (PID: 632)
- cmd.exe (PID: 1804)
- powershell.exe (PID: 4836)
- cmd.exe (PID: 6028)
- powershell.exe (PID: 6412)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4548)
- powershell.exe (PID: 2784)
- powershell.exe (PID: 5612)
- cmd.exe (PID: 4448)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1572)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 4700)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1572)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 4700)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 6224)
- powershell.exe (PID: 7148)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 6224)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 7148)
INFO
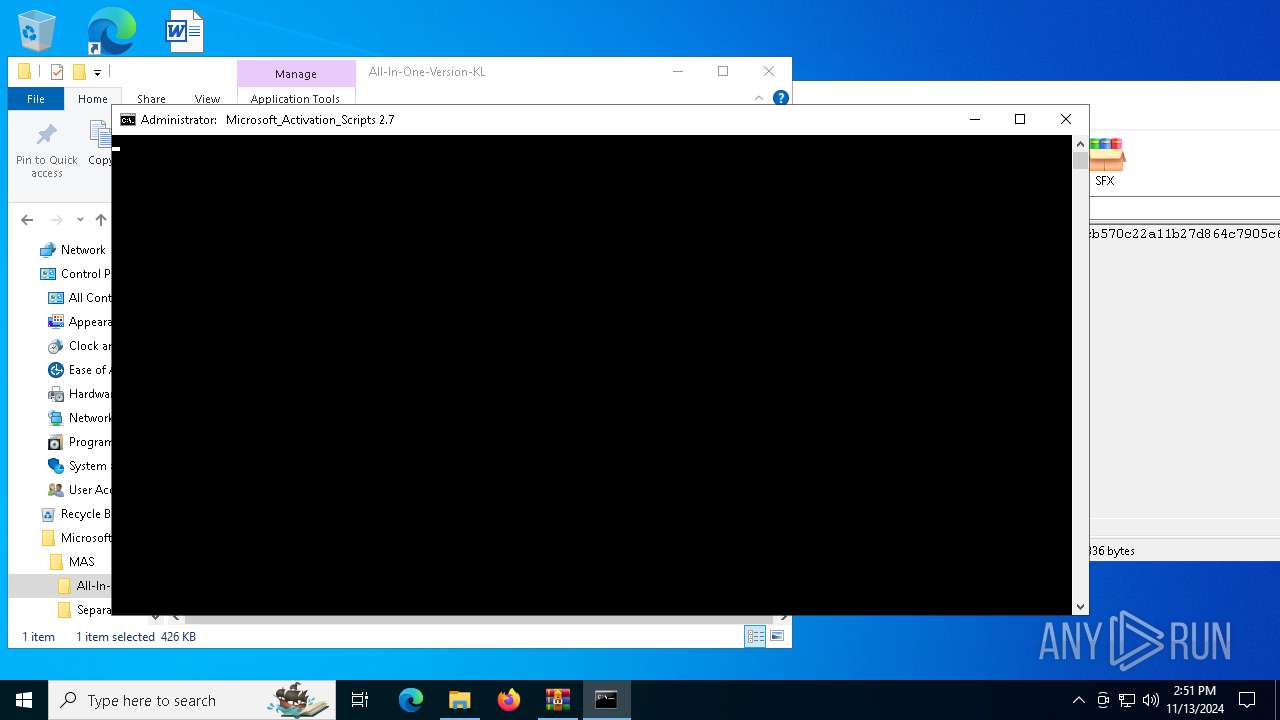
Manual execution by a user
- cmd.exe (PID: 632)
- cmd.exe (PID: 6028)
- msedge.exe (PID: 780)
Checks operating system version
- cmd.exe (PID: 632)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6028)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4448)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 6224)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 7148)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 6224)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 7148)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6964)
- powershell.exe (PID: 1572)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 5892)
- powershell.exe (PID: 6224)
- powershell.exe (PID: 7148)
Application launched itself
- msedge.exe (PID: 1584)
- msedge.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:09:28 15:21:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
302
Monitored processes
172
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | find "127.69" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 612 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_AIO.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
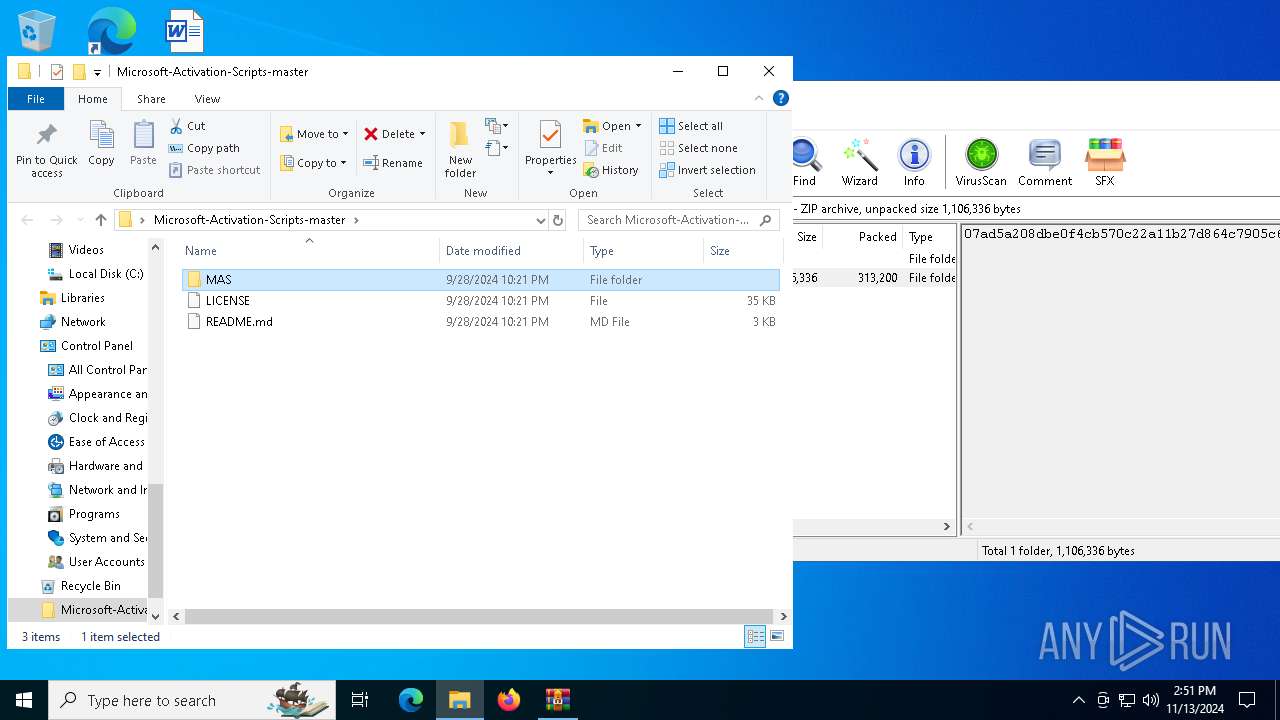
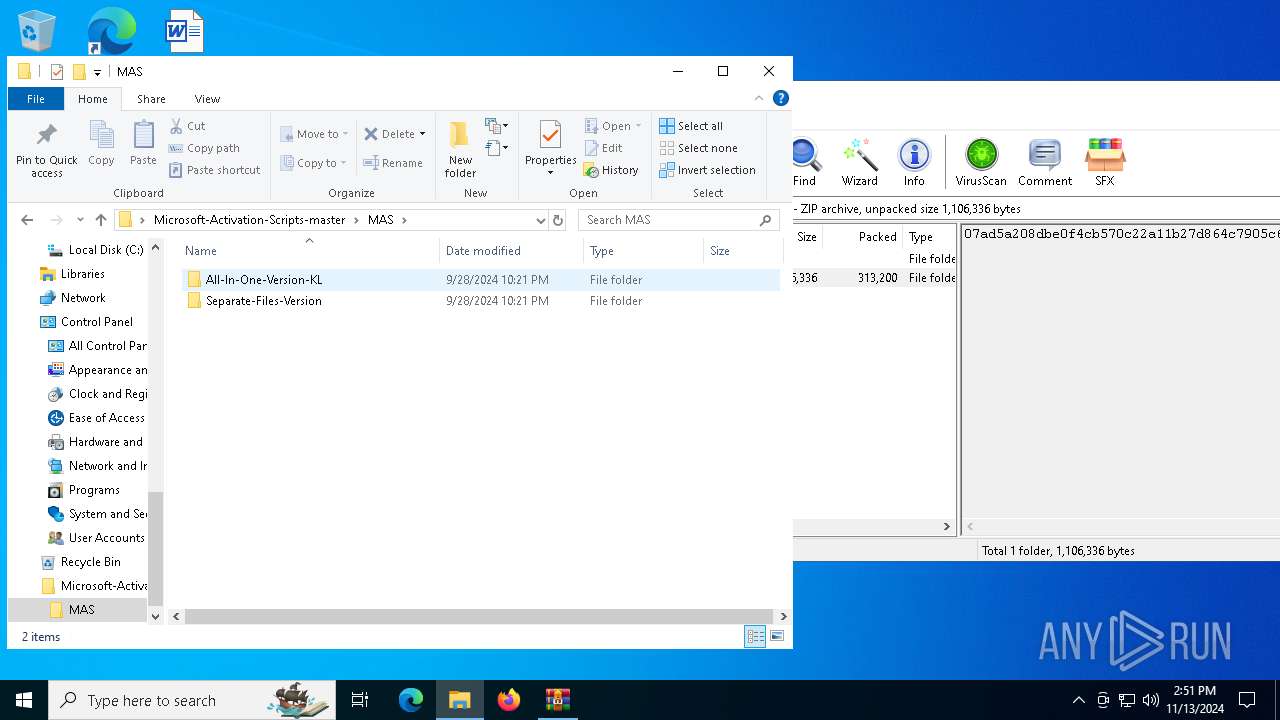
| 632 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\All-In-One-Version-KL\MAS_AIO.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
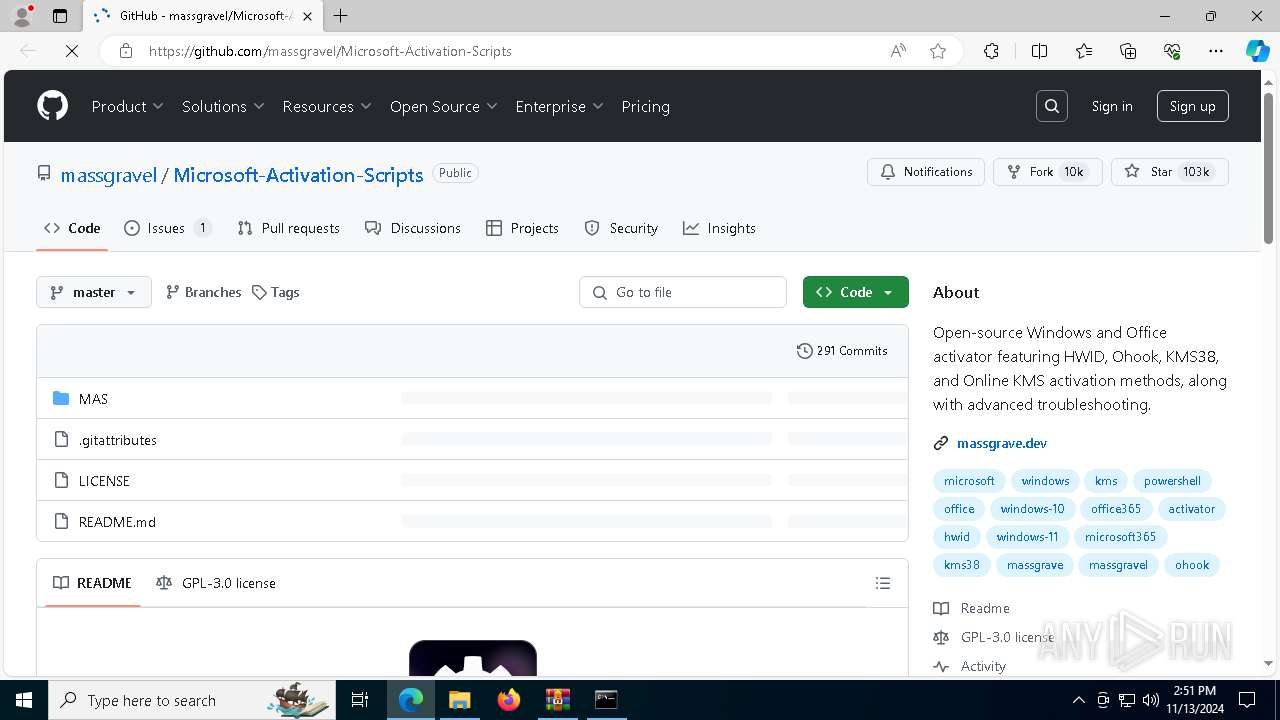
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate --single-argument https://github.com/massgravel/Microsoft-Activation-Scripts | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2776 --field-trial-handle=2500,i,9228527435514444770,16550795254007923093,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1048 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 170
Read events
66 135
Write events
35
Delete events
0
Modification events
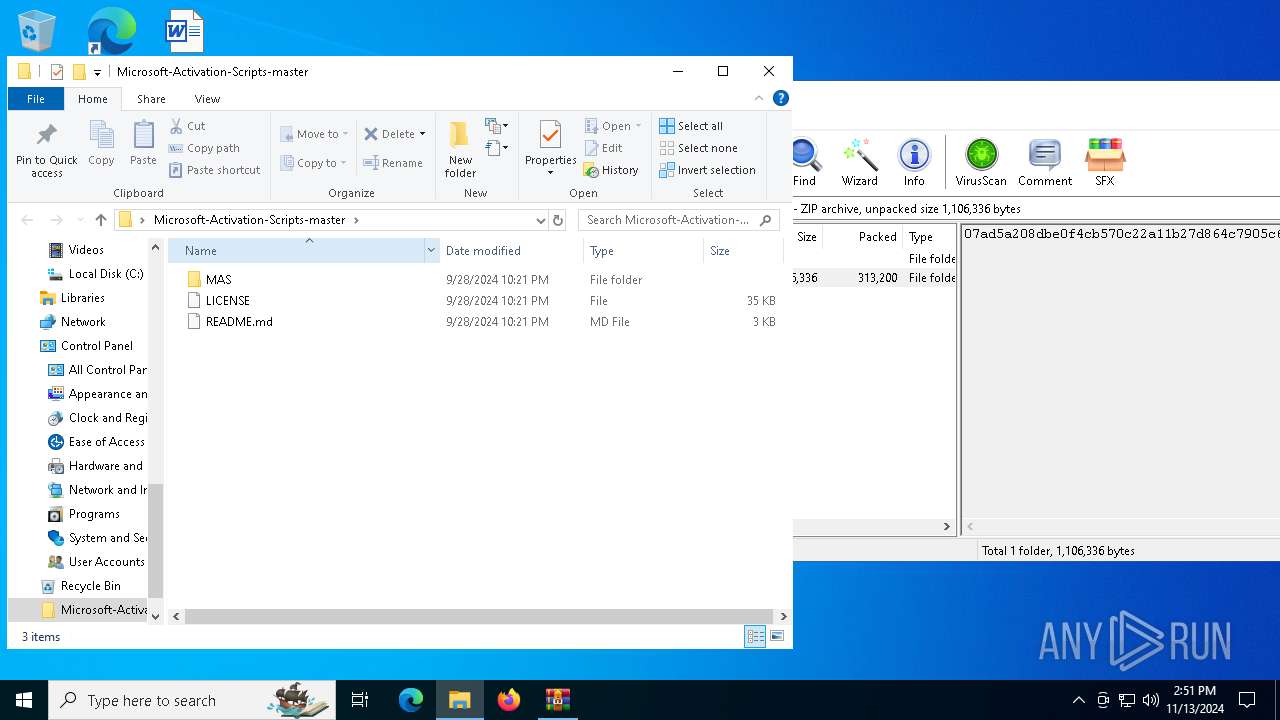
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft-Activation-Scripts-master (1).zip | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4548) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4548) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4548) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4548) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
296
Text files
77
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\LICENSE | text | |
MD5:1EBBD3E34237AF26DA5DC08A4E440464 | SHA256:3972DC9744F6499F0F9B2DBF76696F2AE7AD8AF9B23DDE66D6AF86C9DFB36986 | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Troubleshoot.cmd | text | |
MD5:59CAE5412898B564652AF61C3EA68BB4 | SHA256:D40BDF0D65FB8787088CABE8F46670E73F27C78AB760A8D5977ECCBAF0DD41C4 | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Check_Activation_Status.cmd | text | |
MD5:1EBF95A85EEC40BAB2045BD26658A345 | SHA256:997C19C8AC529E7F2B20E094897CF4FE1A4E03C26AC9E0E5724AA4011A7BB262 | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\Ohook_Activation_AIO.cmd | text | |
MD5:8D32C6AA965D15876377646233BB877A | SHA256:0D45FF95EC377BF8820DBD3581A0D5135C9C74CB2E6840A4C196C1686EA5183C | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\_ReadMe.html | html | |
MD5:574E18C1F9B32A47F988AC91588901BA | SHA256:8932BACD828C0716B136AF6AA15011AED0015E7838006F2CFF7A64954A5696B0 | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\KMS38_Activation.cmd | text | |
MD5:9E088080EFA90FCF81EA485C54EF18FF | SHA256:6026FF44F58D11A9FB178B3A8996978882719469CBB5F3C57D137E836A6A0BBB | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Change_Office_Edition.cmd | text | |
MD5:6D178A37EF202B616DF131F81D6FFAC3 | SHA256:0A44AD744F1ECBA45022C63A28ED22ACA64B98376738F75068F186A6D9D2806E | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Extract_OEM_Folder.cmd | text | |
MD5:7A7A1E02B59C63494C15487744D0781D | SHA256:830CF24042BF8A0C843AE1DDD36607A5F2374C531381AFF2909E331BE7F2A9FF | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\ReadMe.txt | text | |
MD5:B7FA33165116723BC2F83676FD62CC69 | SHA256:B0218B2723A32157A094EE3B852159B339EC3E01CE25AA05E19B28F55A0E9528 | |||
| 7052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7052.28067\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Change_Windows_Edition.cmd | text | |
MD5:38035CDB3A139188007EE389EA86F450 | SHA256:F1E5C6F797C71DA6BBE6BA019B685D40FE3E8AE21725071464DC61DF858B93F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
87
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.166:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
624 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
780 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |