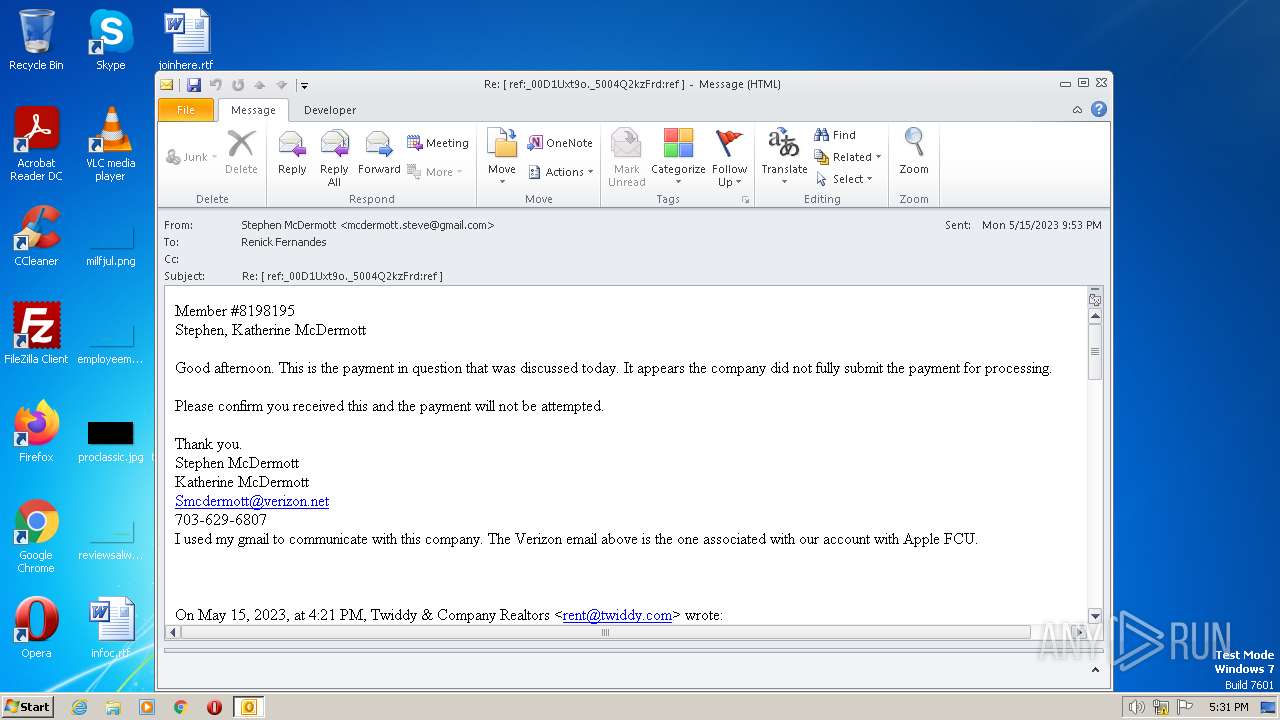
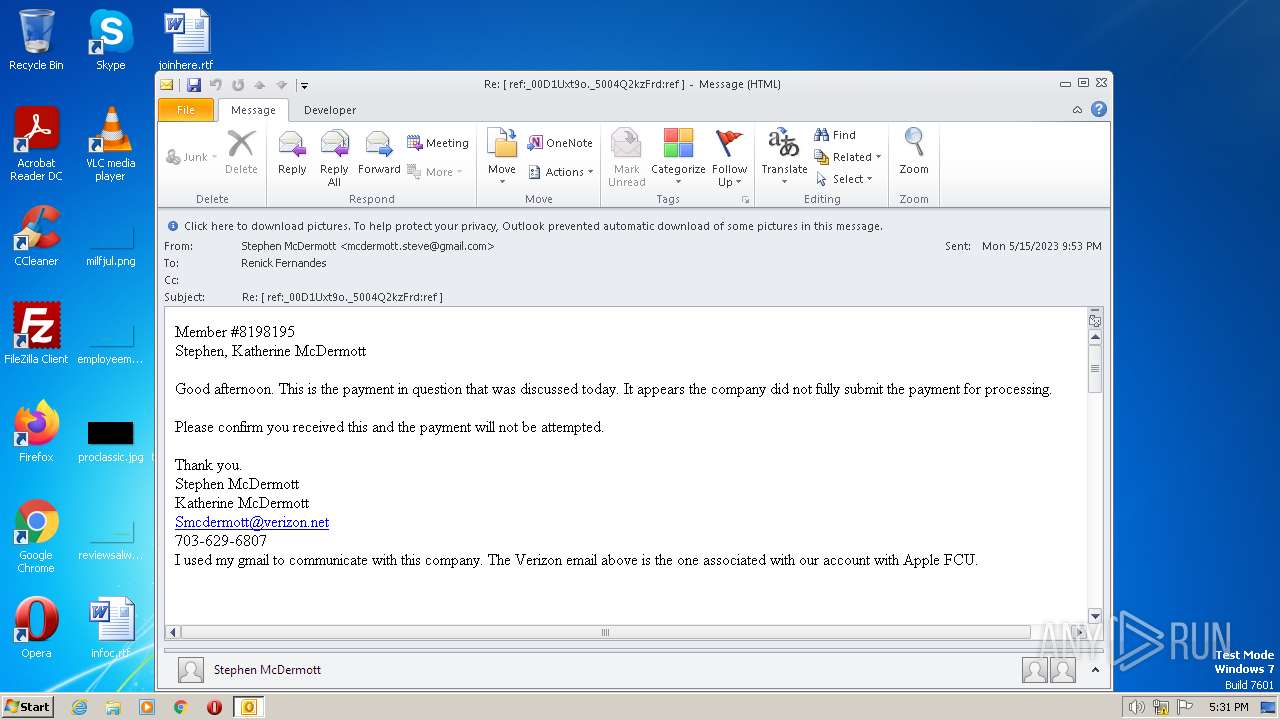
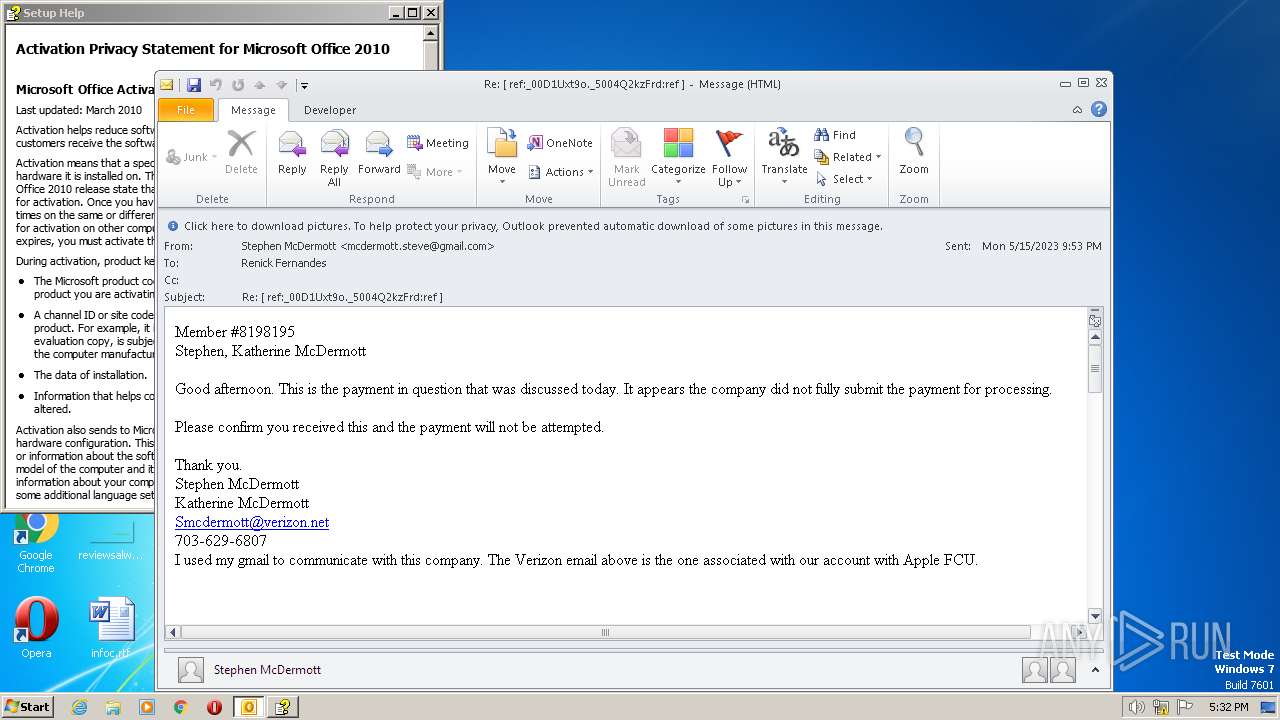
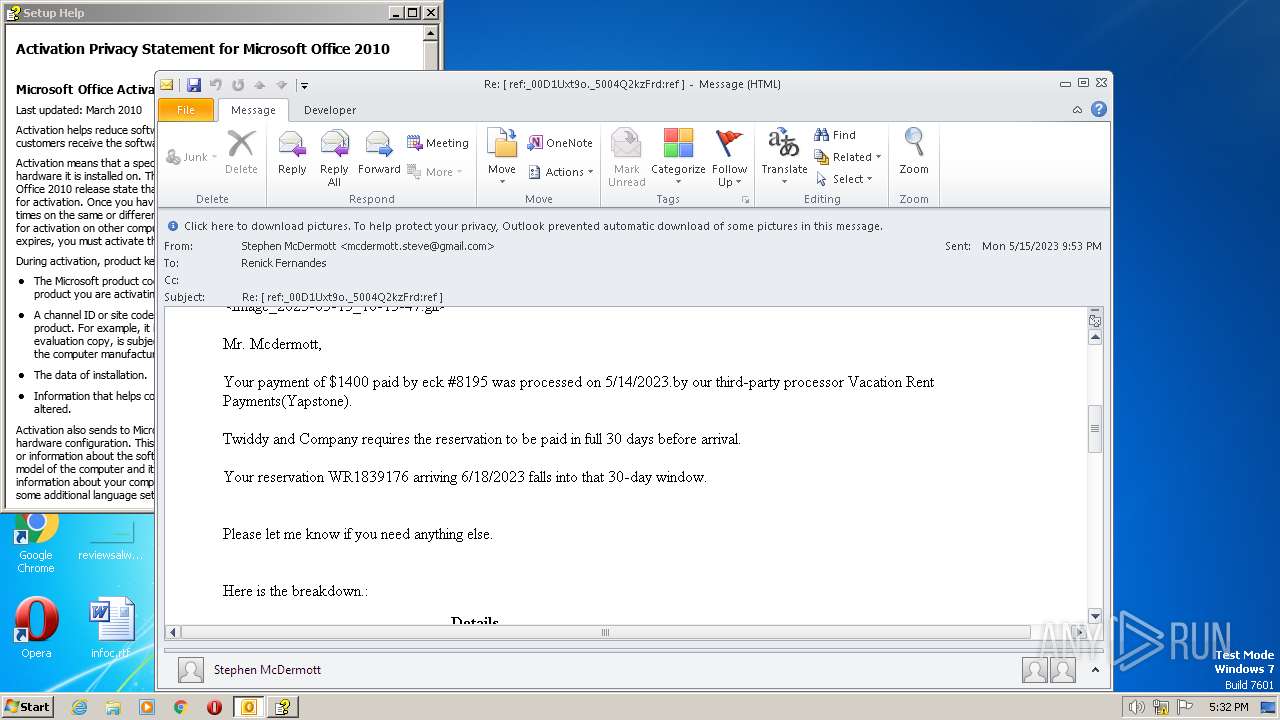
| File name: | Re ref_00D1Uxt9o._5004Q2kzFrdref .msg |
| Full analysis: | https://app.any.run/tasks/fc299ed8-a516-4d86-937e-f60c299b14ae |
| Verdict: | Malicious activity |
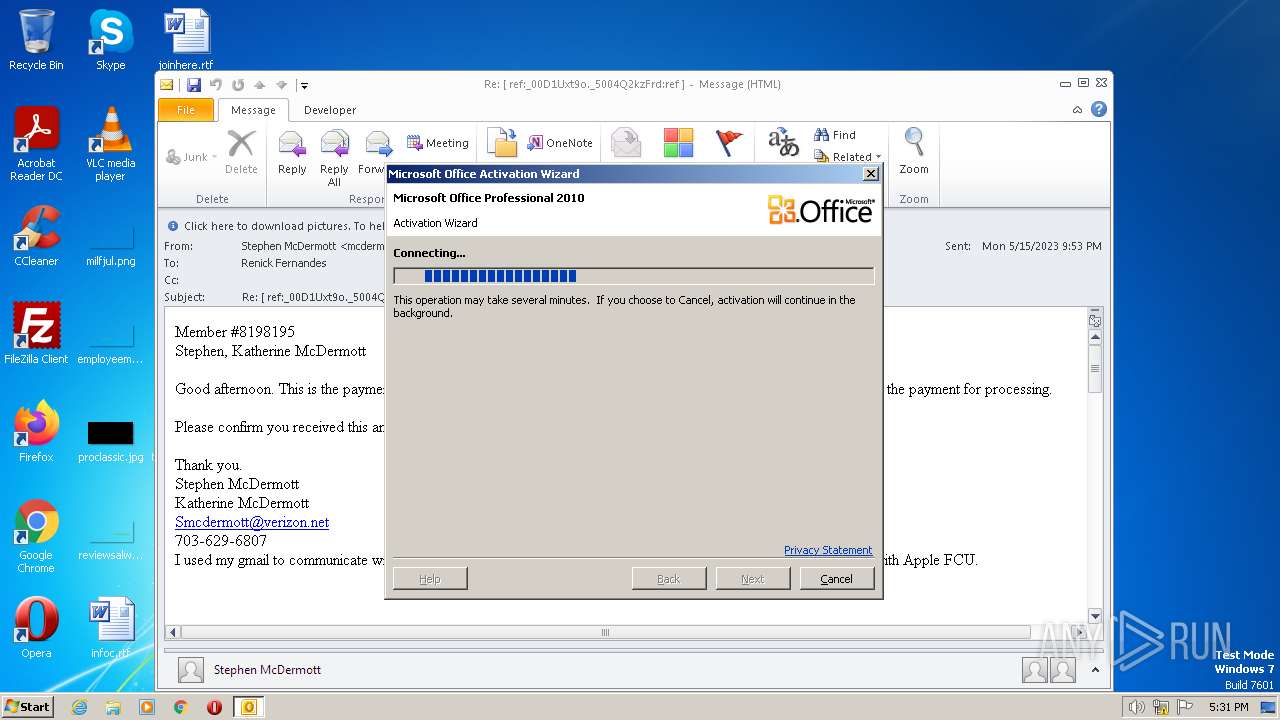
| Analysis date: | May 16, 2023, 16:30:53 |
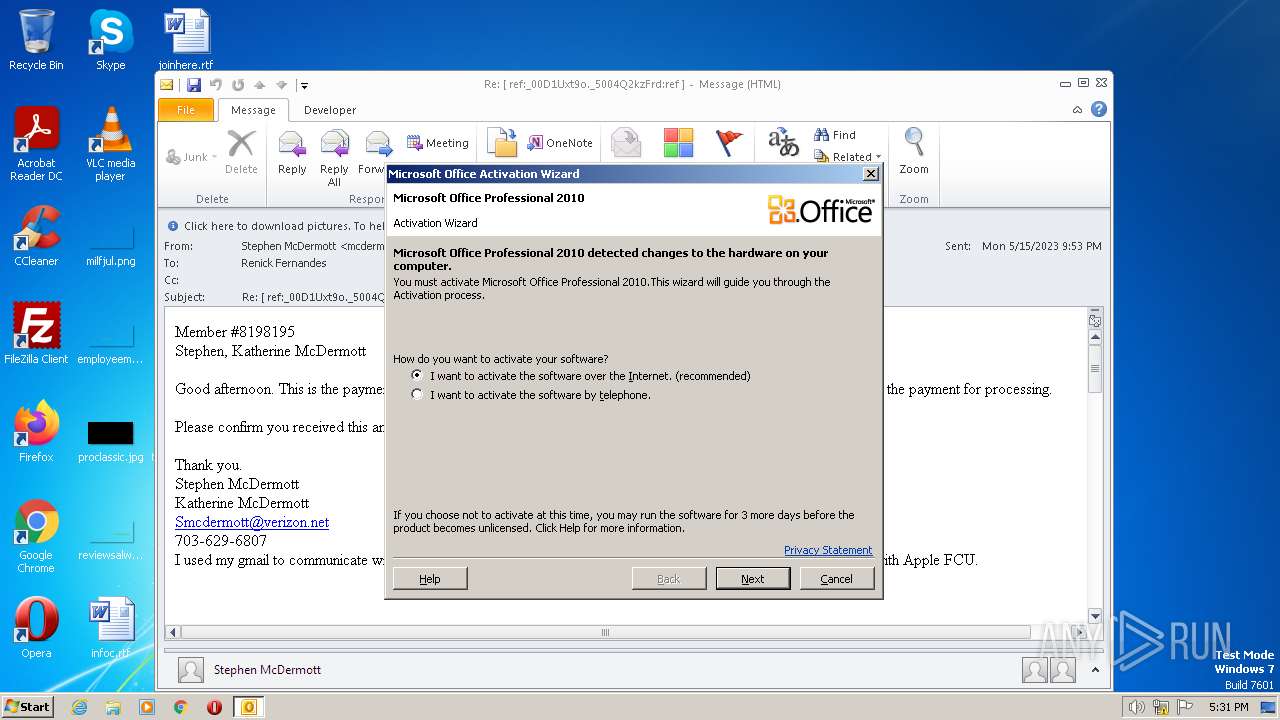
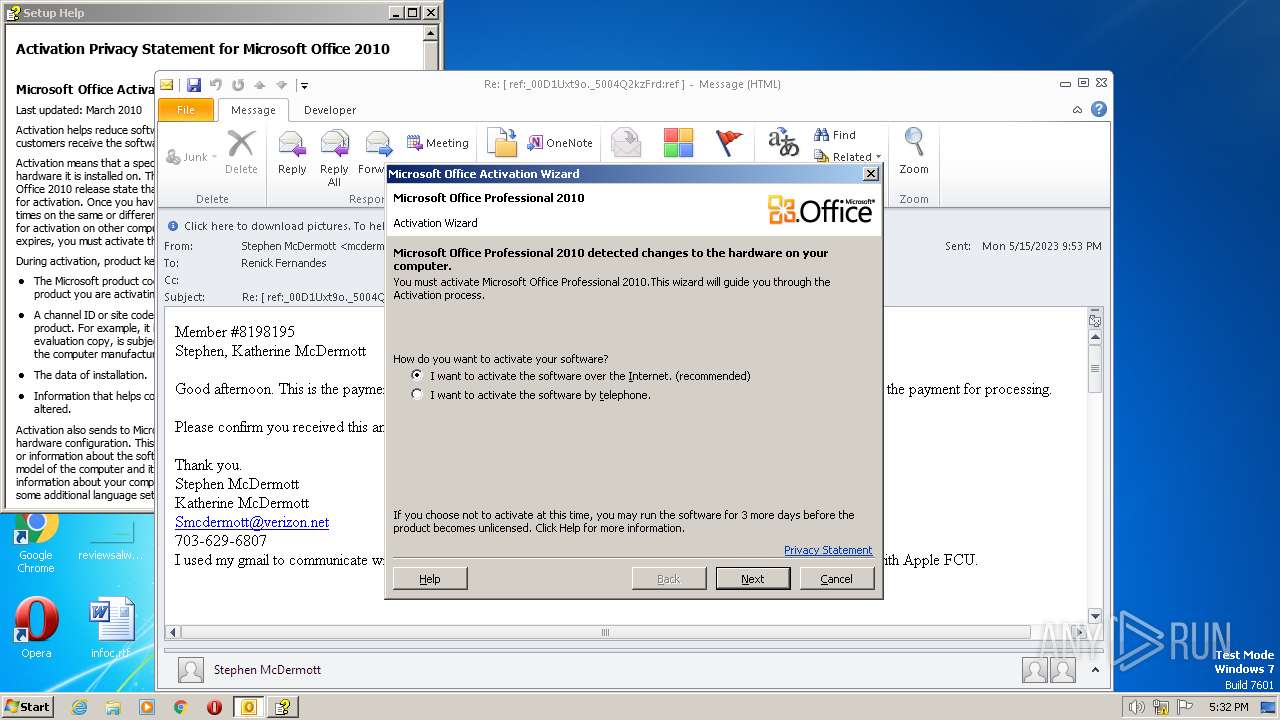
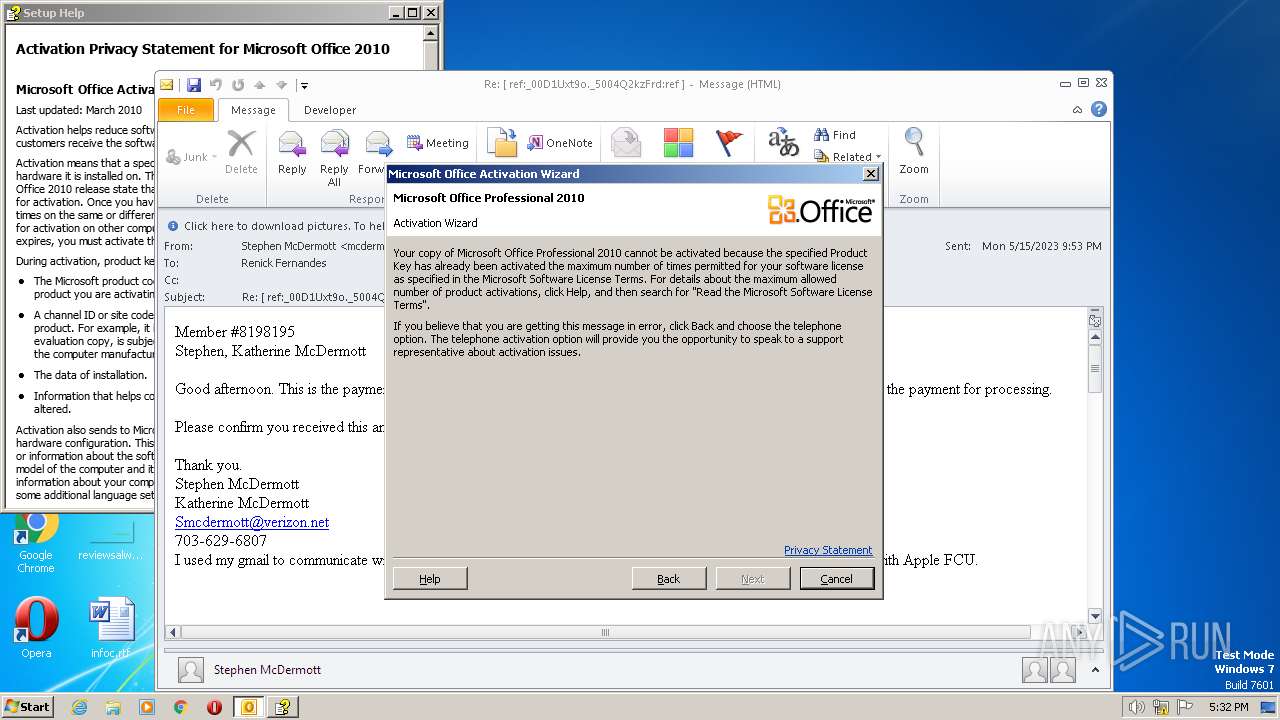
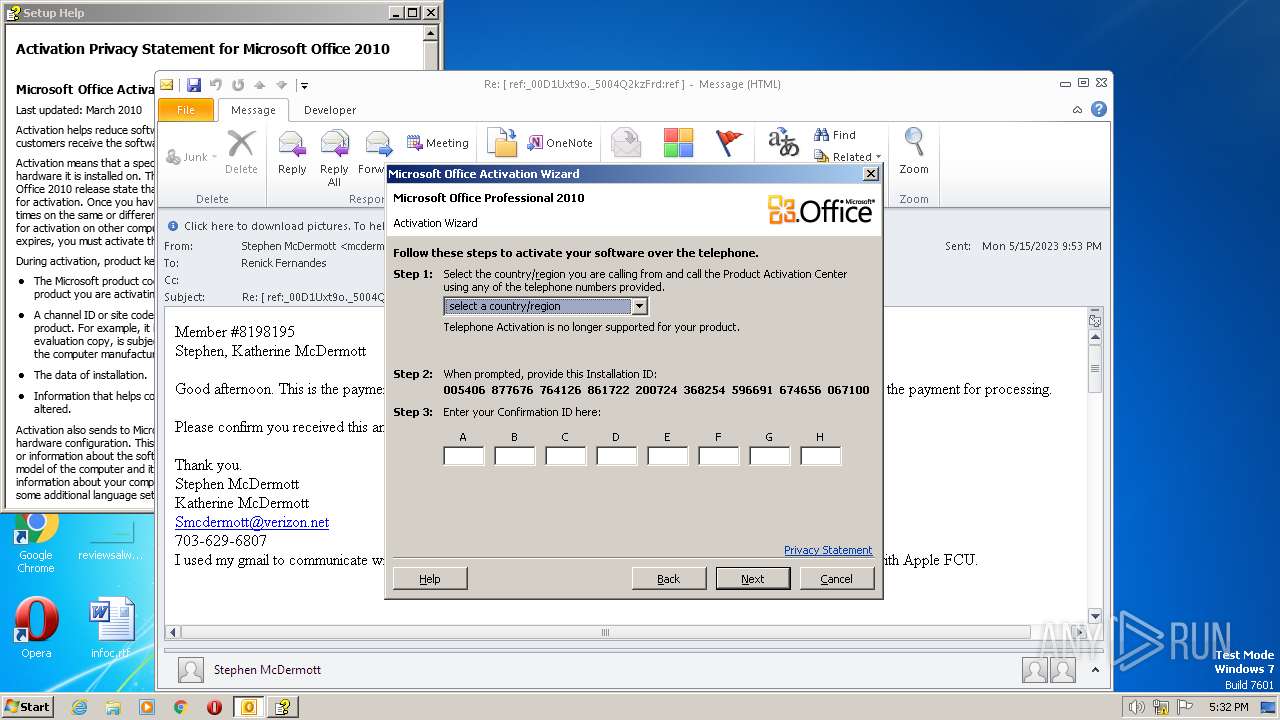
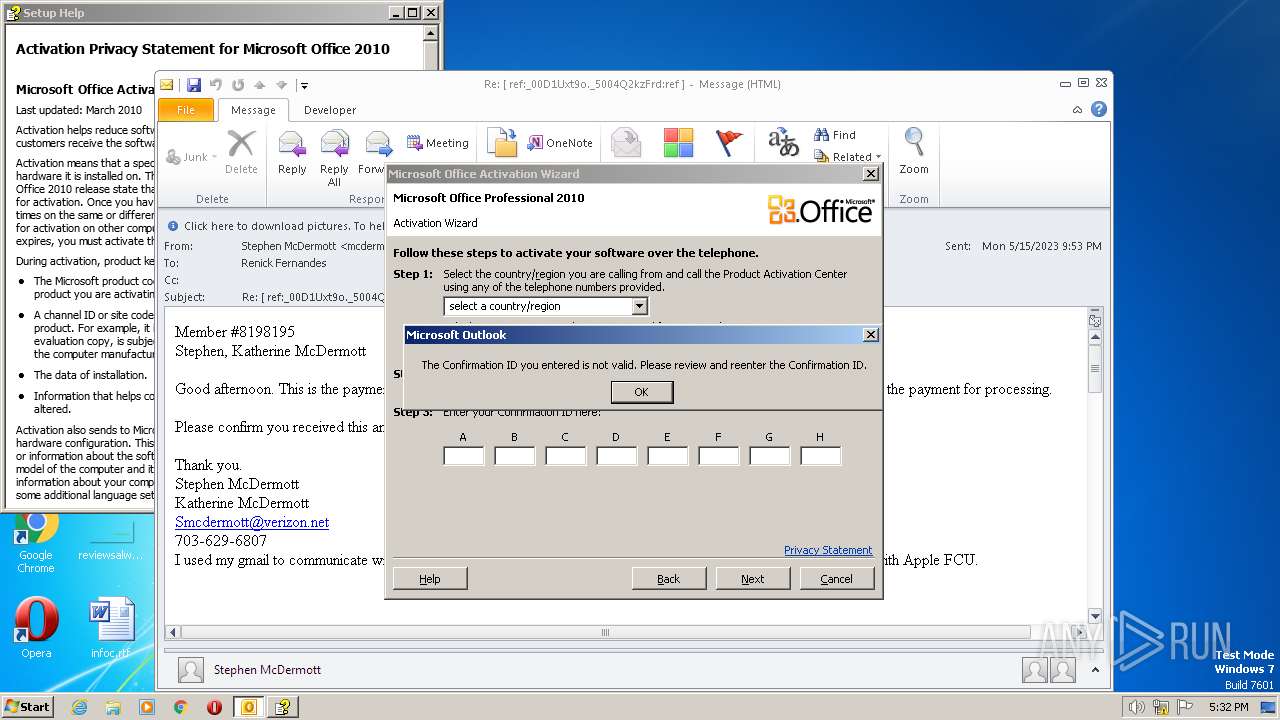
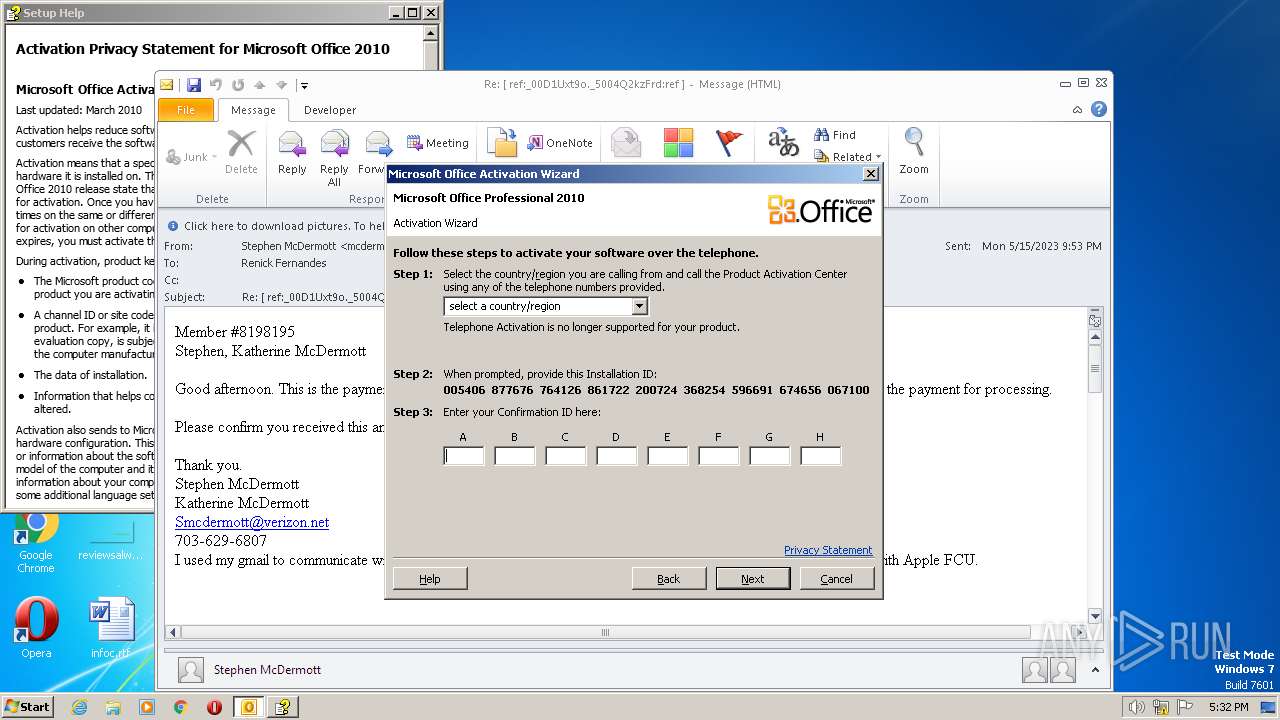
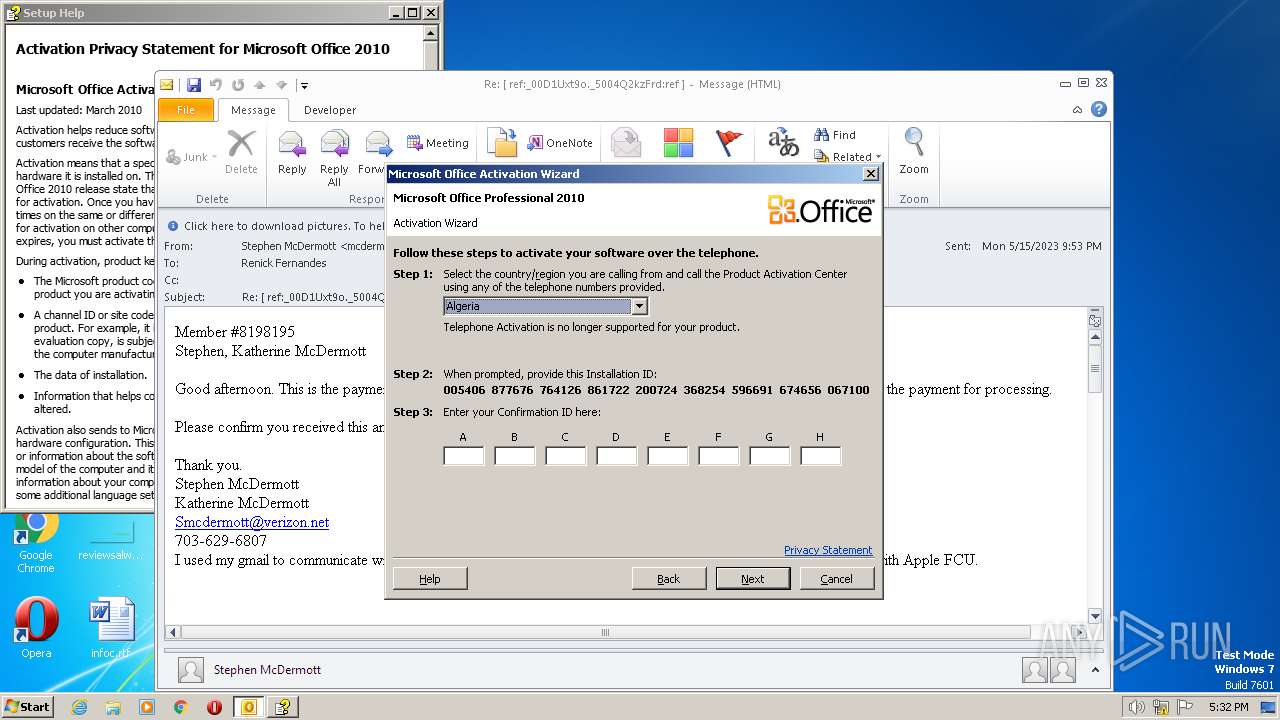
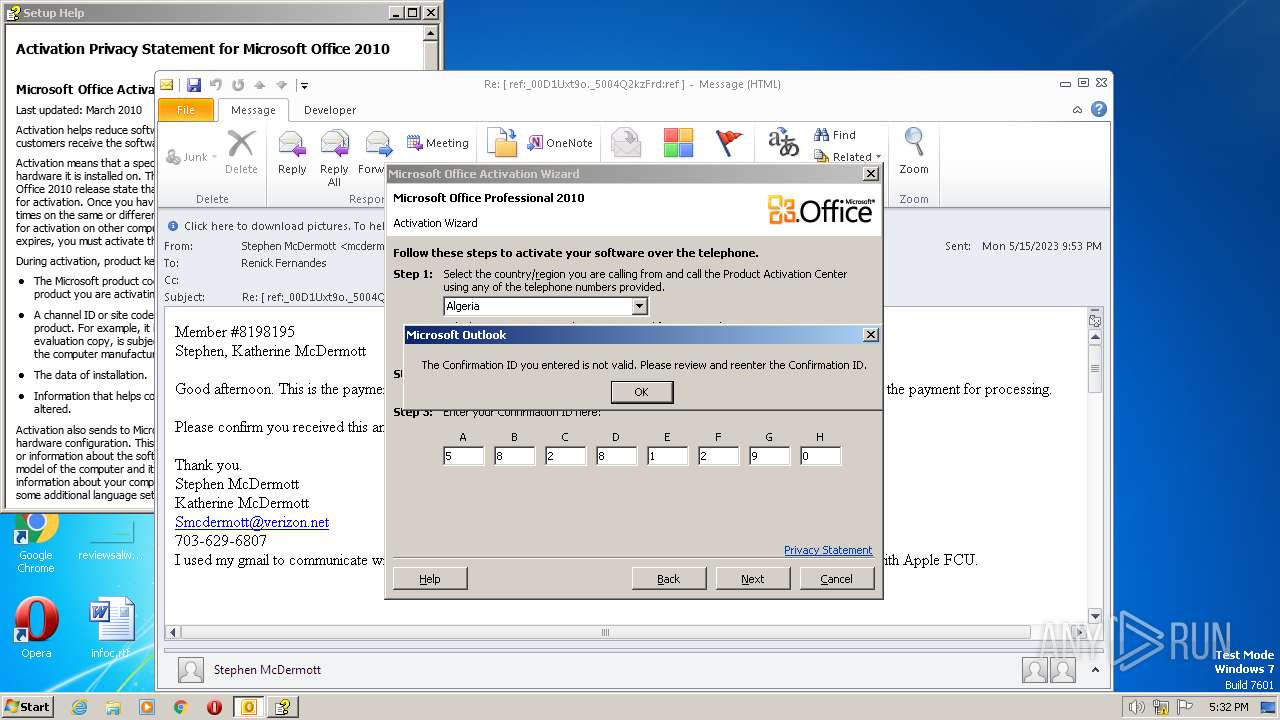
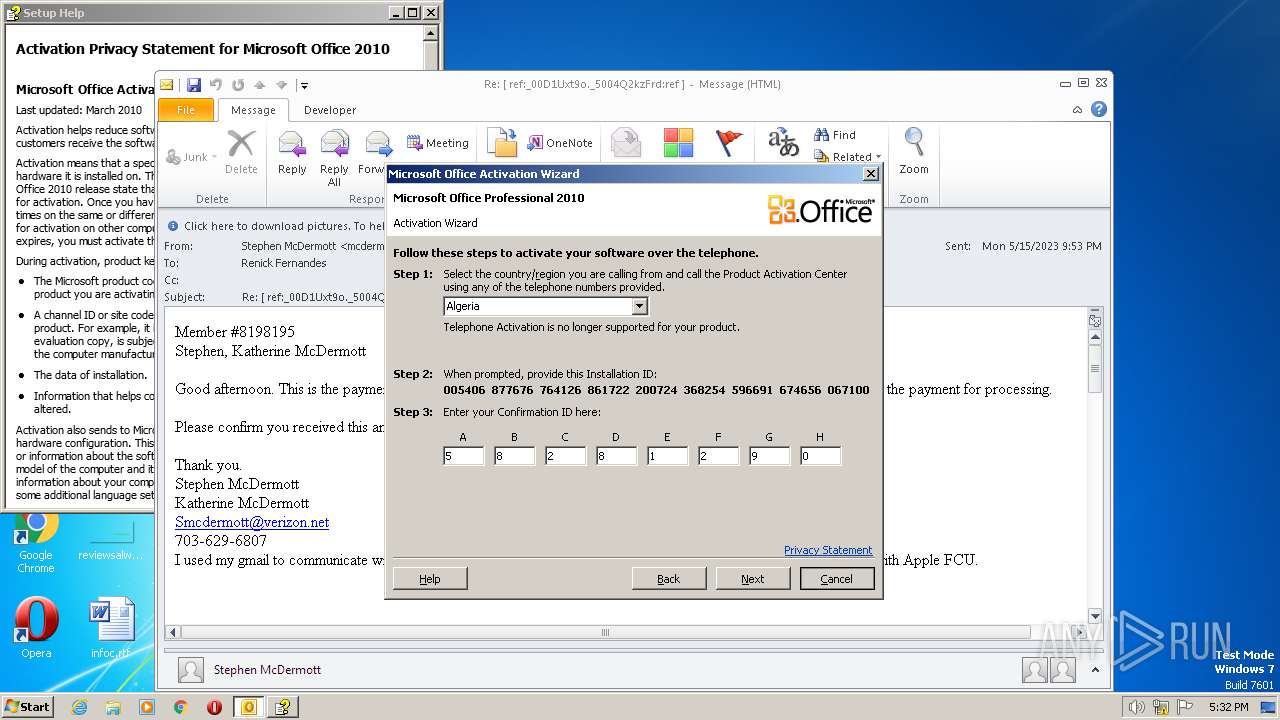
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 4C0298D231154D6BD9E0DA79A643F192 |
| SHA1: | 6F922E92EBB11997817A6F83A31D57C8C749806F |
| SHA256: | 26A6B7390EA86C963D280B40C4E520DB168A9D66A86A8209F673EA8EE5FCADB9 |
| SSDEEP: | 1536:64Cc6TcOul+VQlakY89fullTJqxQW3Wjb7YpdW9+uDU5BgZ/WNYB:64Cc6Tvulju89fulT3bcpg+uDdW |
MALICIOUS
No malicious indicators.SUSPICIOUS
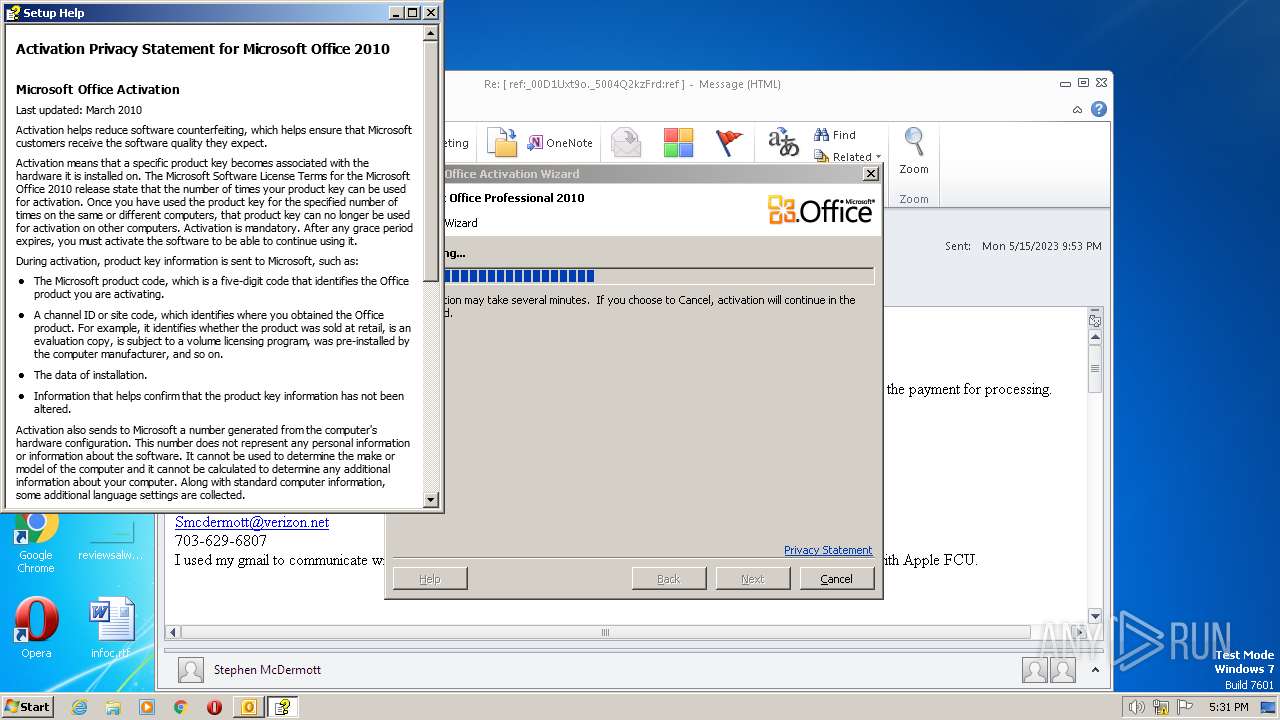
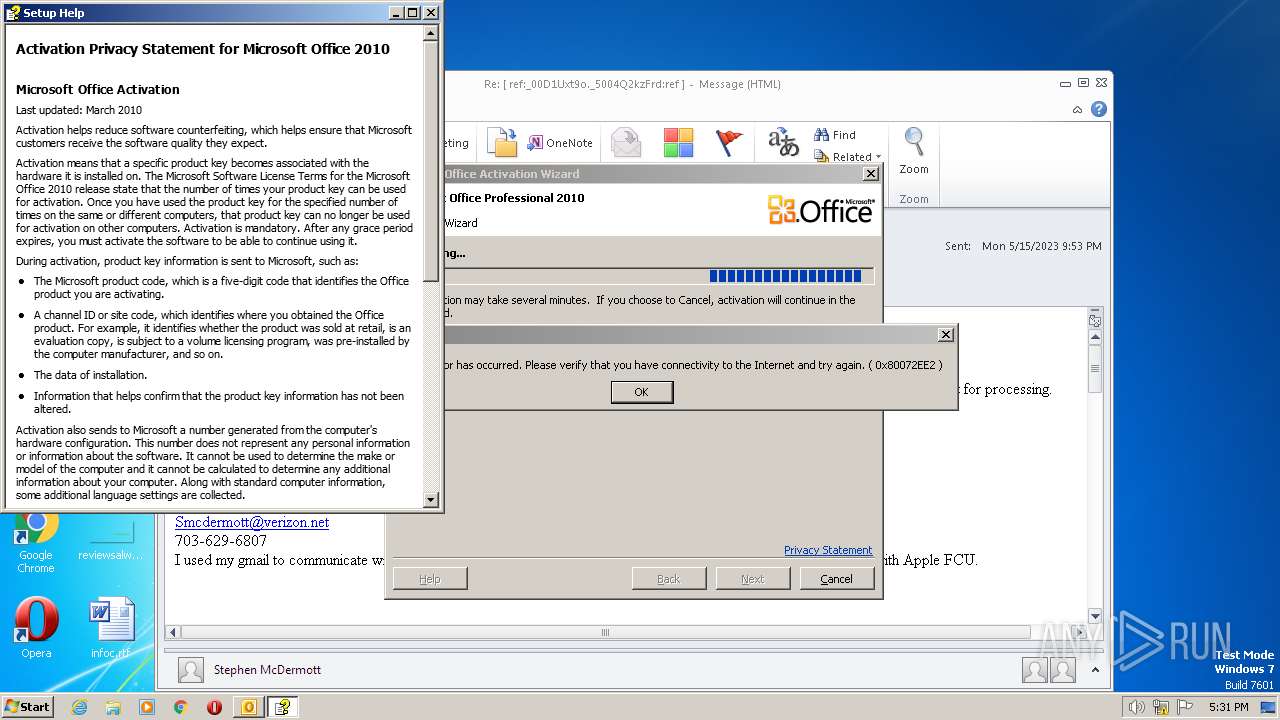
Reads Internet Explorer settings
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
Reads the Internet Settings
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
Reads Microsoft Outlook installation path
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
INFO
Create files in a temporary directory
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
- iexplore.exe (PID: 2484)
The process checks LSA protection
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
Reads Internet Explorer settings
- CLVIEW.EXE (PID: 3864)
Reads the machine GUID from the registry
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
Checks proxy server information
- hh.exe (PID: 372)
- hh.exe (PID: 4020)
- hh.exe (PID: 2476)
Creates files or folders in the user directory
- hh.exe (PID: 372)
Application launched itself
- iexplore.exe (PID: 2484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
46
Monitored processes
7
Malicious processes
4
Suspicious processes
0
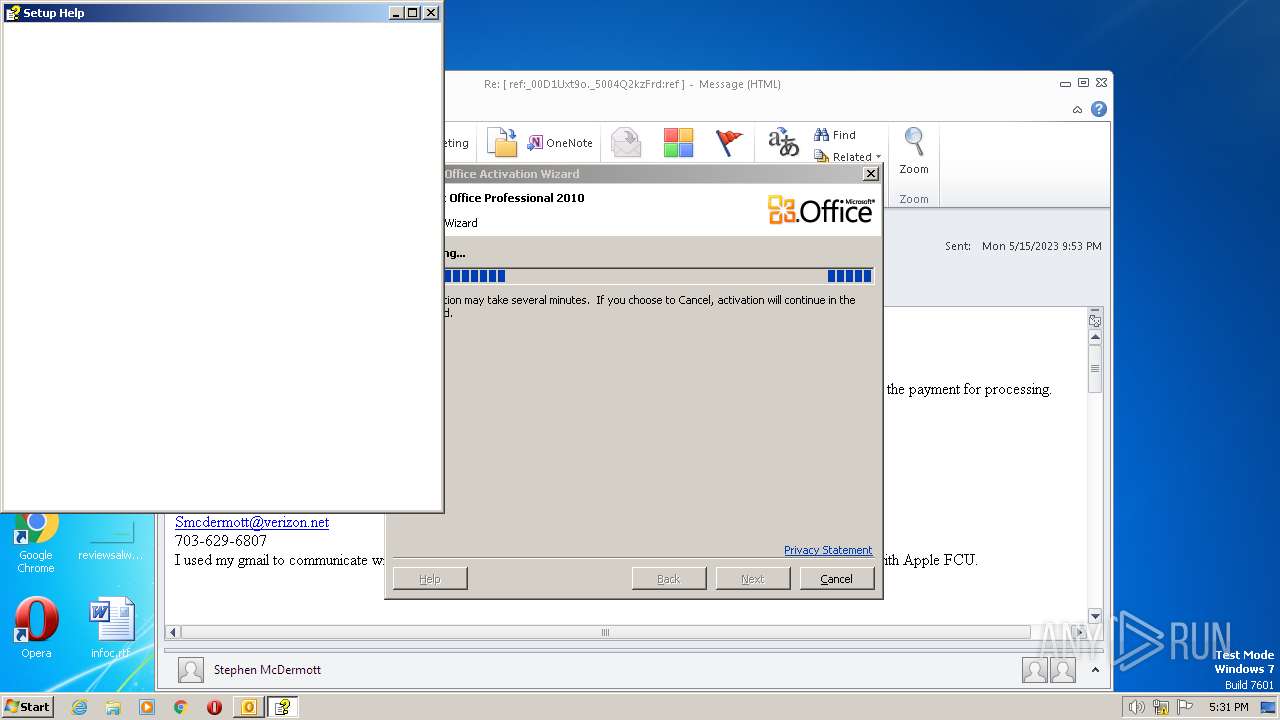
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
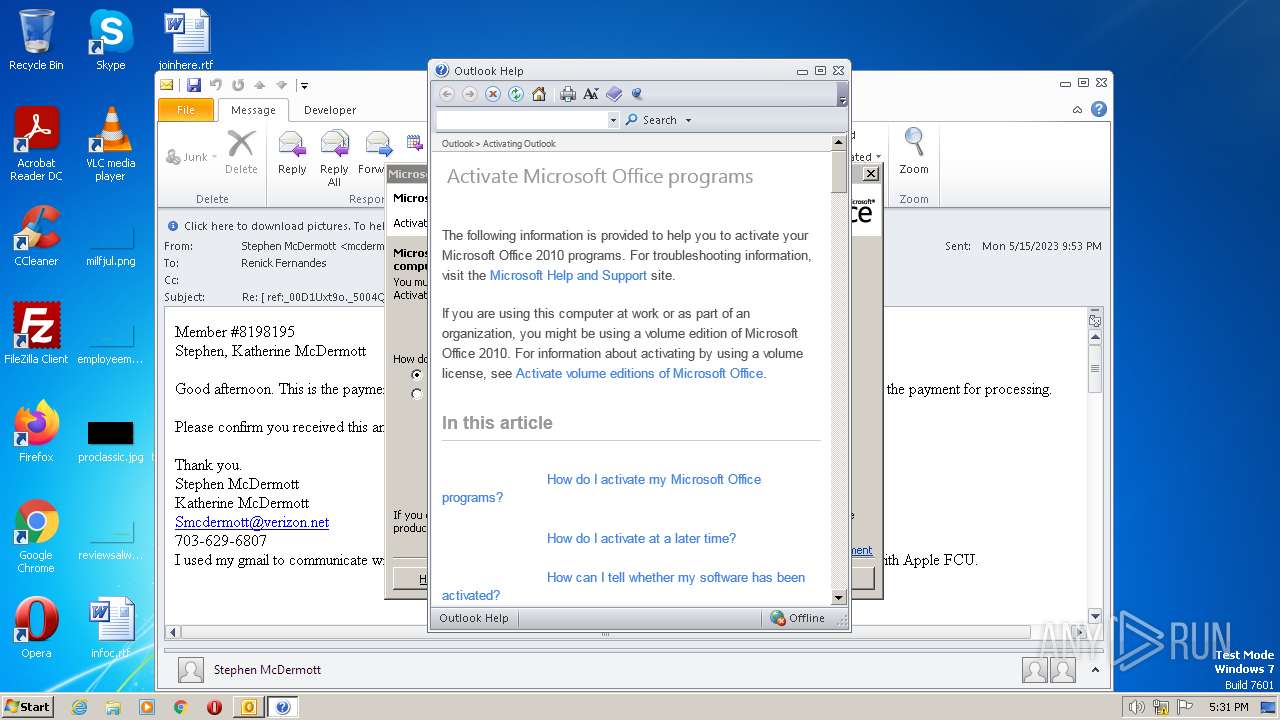
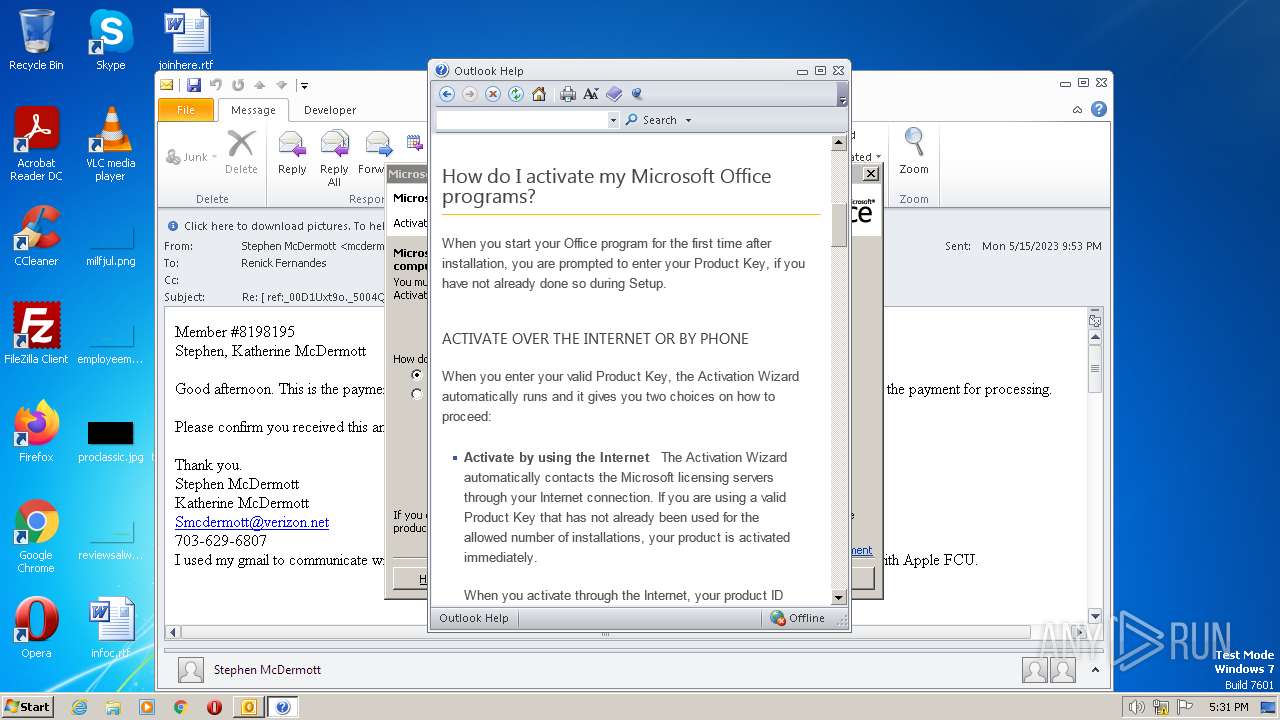
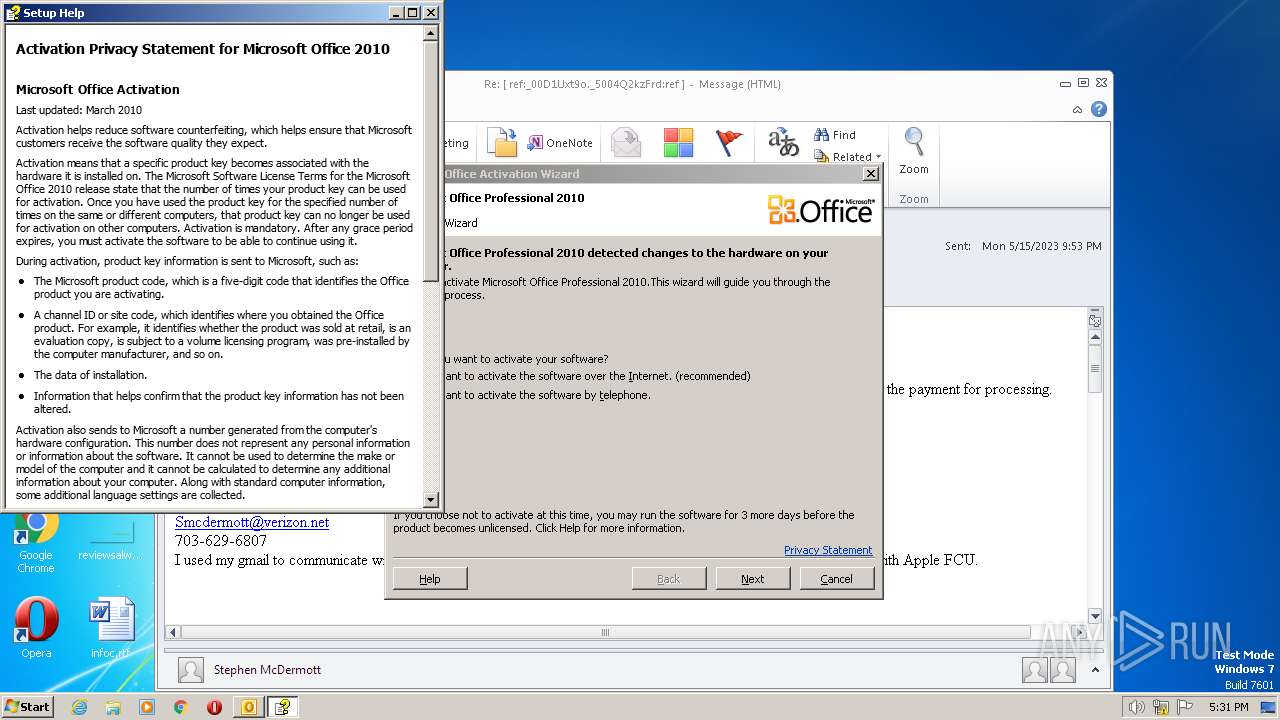
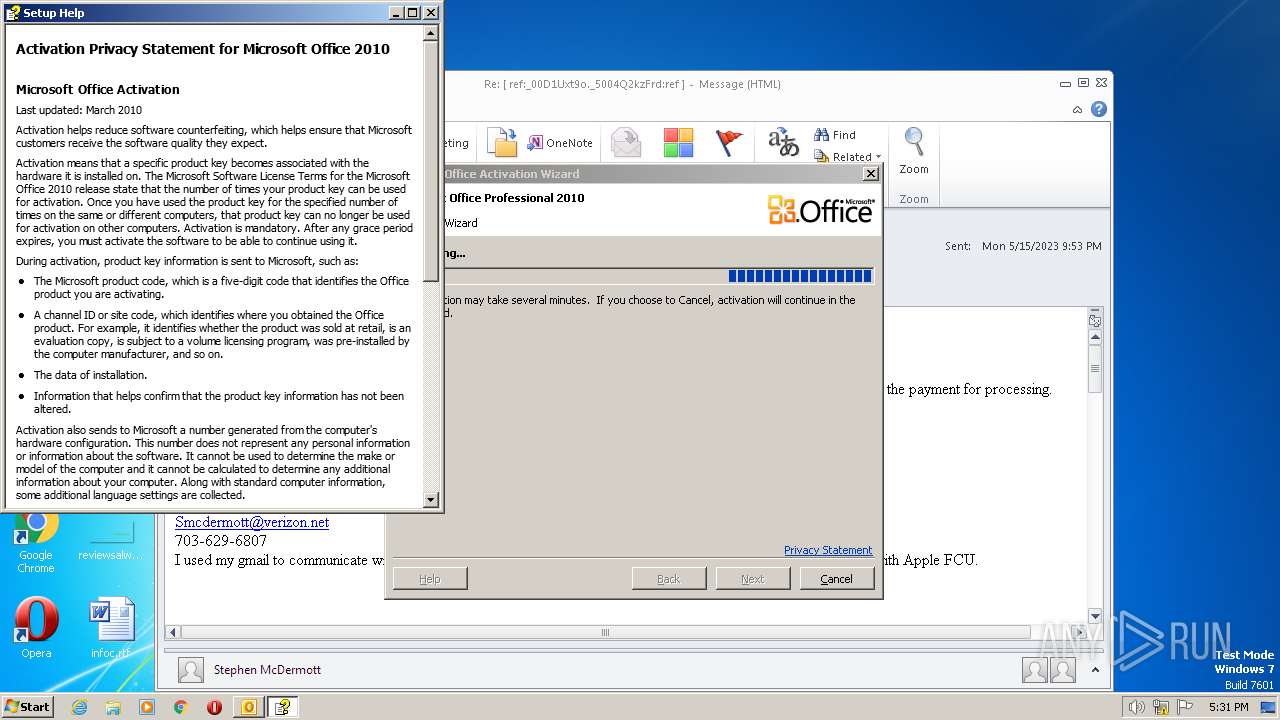
| 372 | "C:\Windows\hh.exe" -mapid 183675 "mk:@MSITStore:C:\Program Files\Common Files\Microsoft Shared\OFFICE14\Office Setup Controller\Office.en-us\SETUP.CHM" | C:\Windows\hh.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Windows\hh.exe" -mapid 183675 "mk:@MSITStore:C:\Program Files\Common Files\Microsoft Shared\OFFICE14\Office Setup Controller\Office.en-us\SETUP.CHM" | C:\Windows\hh.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
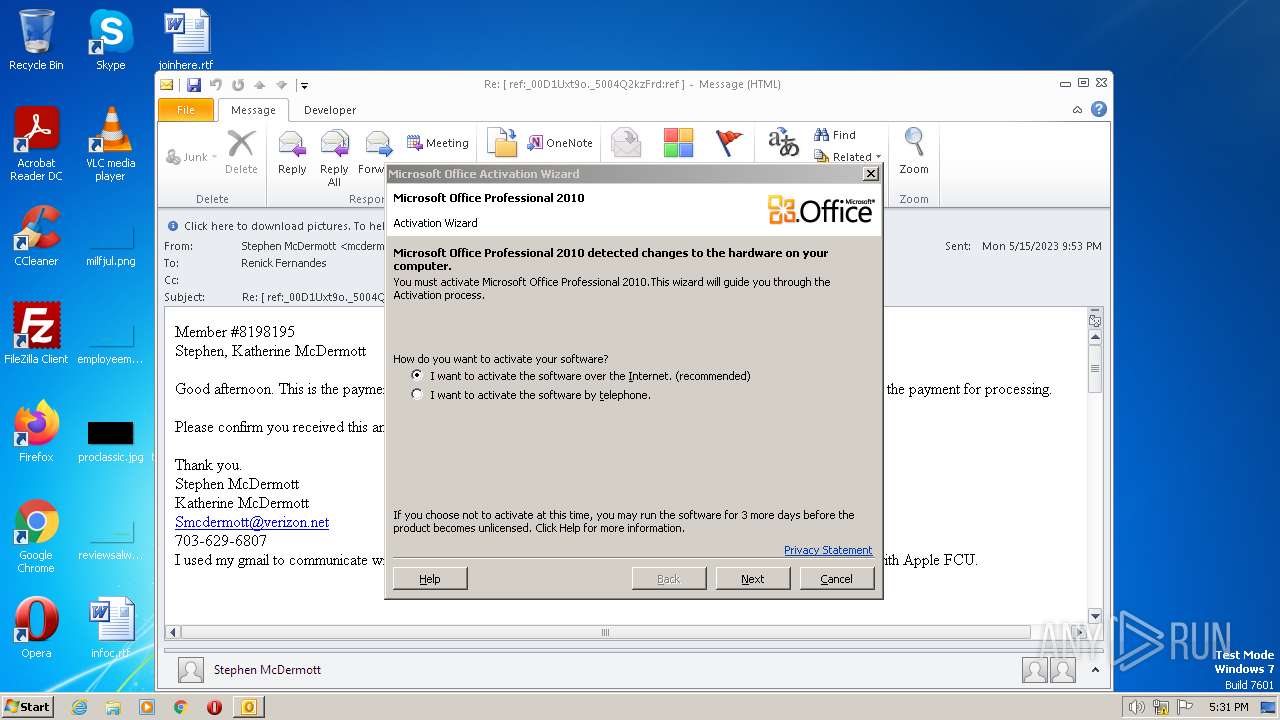
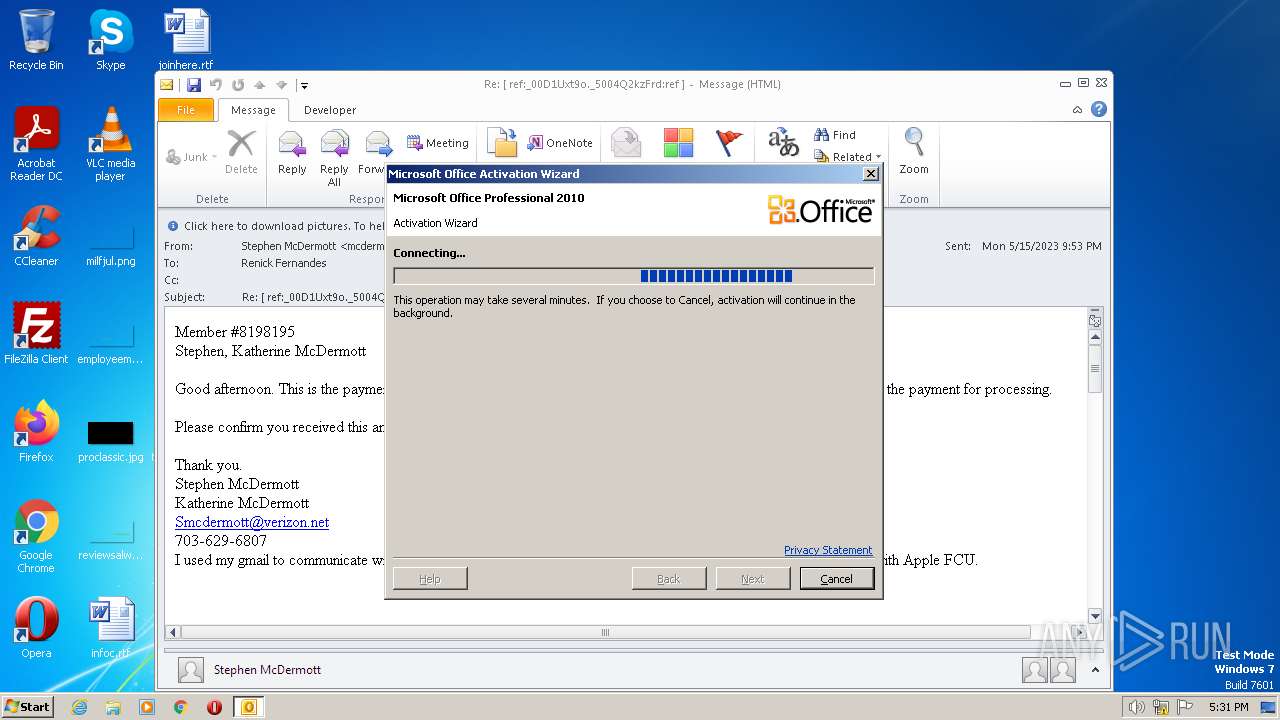
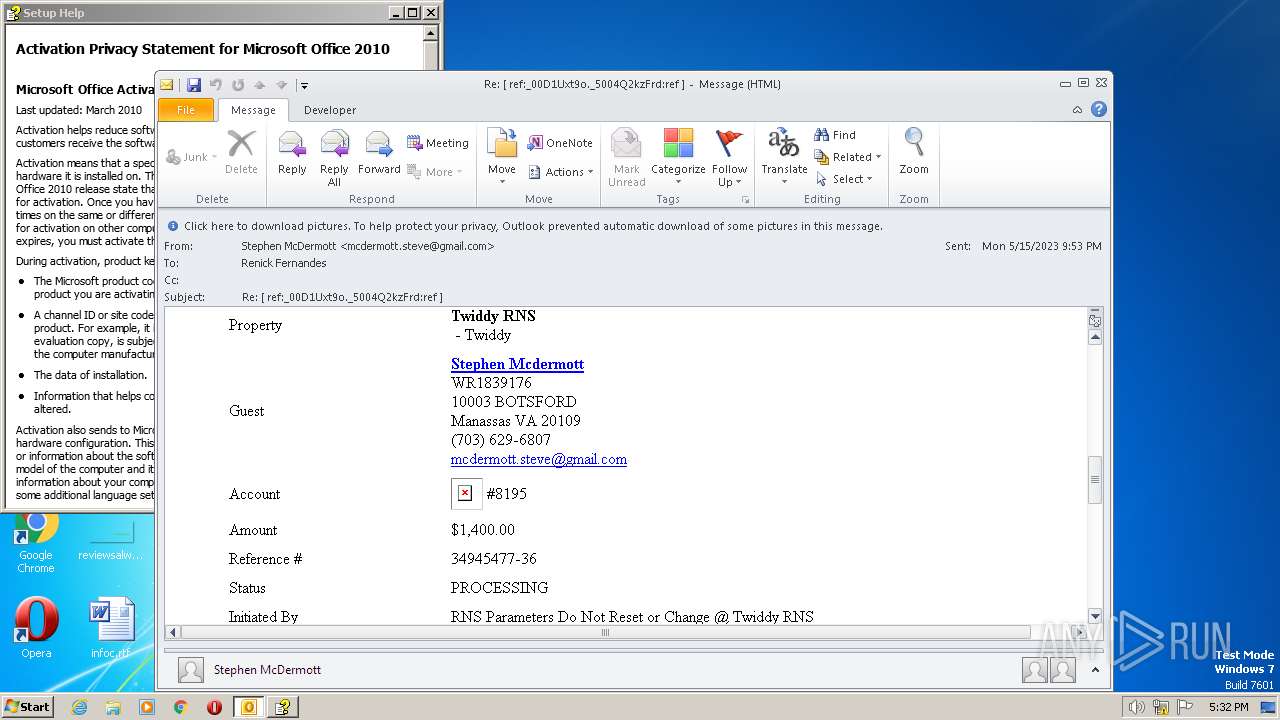
| 2484 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fwww.vacationrentpayment.com%2Fpay%2F0%2FupdatePerson.html%3Fcd%3D1826342453759565890&data=05%7C01%7Crfernandes%40applefcu.org%7C5b391a13b926453328b208db558657cf%7C0e0f75049315461590f1a59594a07e2a%7C0%7C0%7C638197807734018211%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&sdata=OhmDEotoOywjnX7XQnf%2F%2FnO0NhgiF86ntfsOWLtyqWk%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2484 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
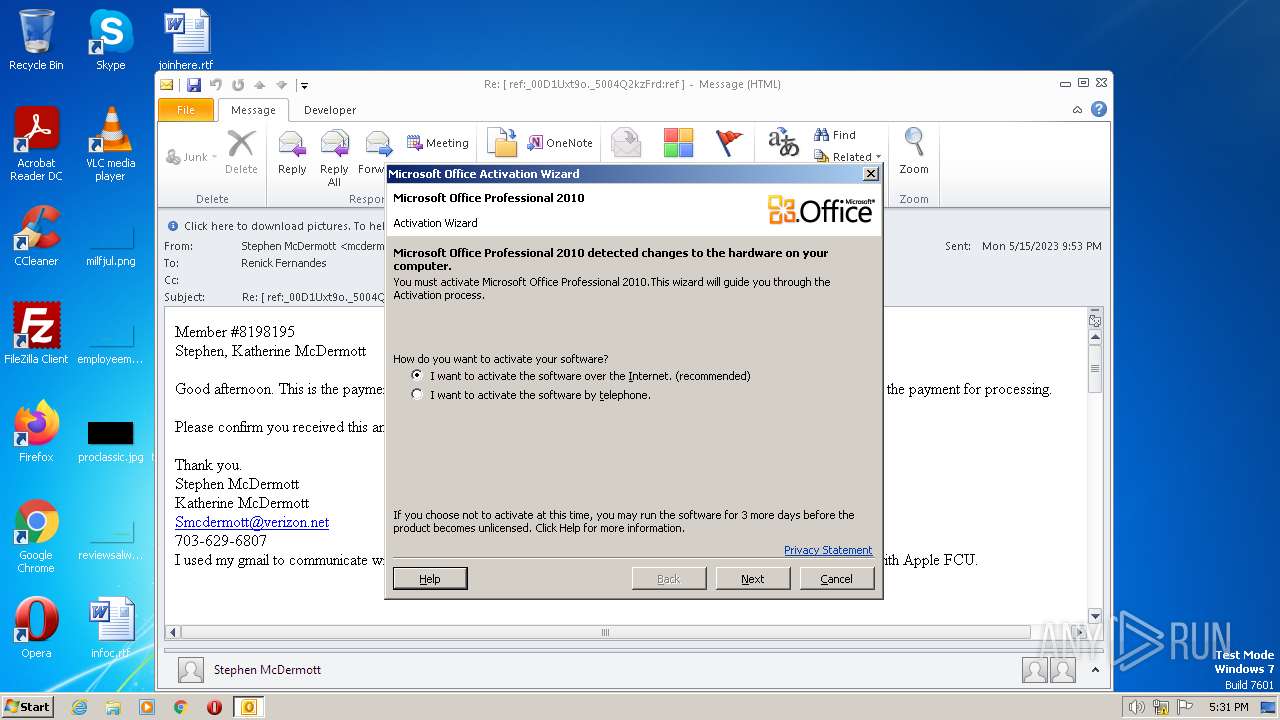
| 3864 | "C:\Program Files\Microsoft Office\Office14\CLVIEW.EXE" "OUTLOOK" "Microsoft Outlook" | C:\Program Files\Microsoft Office\Office14\CLVIEW.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Help Viewer Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Re ref_00D1Uxt9o._5004Q2kzFrdref .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 4020 | "C:\Windows\hh.exe" -mapid 183675 "mk:@MSITStore:C:\Program Files\Common Files\Microsoft Shared\OFFICE14\Office Setup Controller\Office.en-us\SETUP.CHM" | C:\Windows\hh.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
23 694
Read events
23 154
Write events
516
Delete events
24
Modification events
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (3964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
73
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD17B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_6D9054CA164165489EDEE296D545B0A9.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:6EDFF42E28D31B5C5A94D3B671A22485 | SHA256:6A7C681F07BE29313DEC500321279E9ACE558BCE2AE04FCA0FE20740A8901361 | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_8A0F489EF084C94689923E14B0A06821.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3864 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMTE4E5.tmp | binary | |
MD5:4BE2AEDDA24E0539C95564B48CA9D8BA | SHA256:E4D153F74AC21D4212A83FE030EE7A407B5FDFE2D3A8145F3E826532BD796893 | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_FF16D235F3AC944282C280A38ABFA9BD.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 3964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_481ED666FDB0D545B4A5B6265E12910D.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3864 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMTE4C5.tmp | binary | |
MD5:73E5F16AA352D7188E7266C6C20EAAF1 | SHA256:57408D0184C465A18379CAAF84030C6835B480BC644804F5670A02B985E84A0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
25
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | OUTLOOK.EXE | POST | 302 | 104.64.117.184:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | US | — | — | whitelisted |
3156 | iexplore.exe | GET | — | 52.222.206.35:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | — | — | shared |
3964 | OUTLOOK.EXE | POST | 302 | 104.64.117.184:80 | http://go.microsoft.com/fwlink/?LinkID=120750 | US | — | — | whitelisted |
3156 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b78f67769eba66de | US | compressed | 4.70 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?52950b3243174d97 | US | compressed | 4.70 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | binary | 471 b | whitelisted |
3964 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3156 | iexplore.exe | GET | 200 | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 1.70 Kb | whitelisted |
2484 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
3964 | OUTLOOK.EXE | POST | 302 | 104.64.117.184:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3380 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3964 | OUTLOOK.EXE | 104.102.40.139:80 | go.microsoft.com | AKAMAI-AS | DE | malicious |
3964 | OUTLOOK.EXE | 13.77.207.86:443 | activation.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
3964 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3156 | iexplore.exe | 104.47.74.28:443 | nam04.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
3156 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3156 | iexplore.exe | 8.238.30.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3156 | iexplore.exe | 52.24.63.44:443 | www.vacationrentpayment.com | AMAZON-02 | US | unknown |
3156 | iexplore.exe | 108.138.2.173:80 | o.ss2.us | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
activation.sls.microsoft.com |
| whitelisted |
nam04.safelinks.protection.outlook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.vacationrentpayment.com |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |