| File name: | mailpv.exe |
| Full analysis: | https://app.any.run/tasks/85fdad7a-1cd9-495d-a4e6-34822fa55e3d |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2019, 09:55:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 782DD6152AB52361EBA2BAFD67771FA0 |
| SHA1: | 5C5FF30A24A3858A8E9BD531DFEF885D0B2A00C7 |
| SHA256: | 26A3395A4115355E897A7DAF04551EBA5E62DA661D8DBAE7C99205A2E74D24BA |
| SSDEEP: | 3072:1WSVGdlouHiwfXjObBBDTn991ix689w2KQik:1Wrdl9fzOzTna689V |
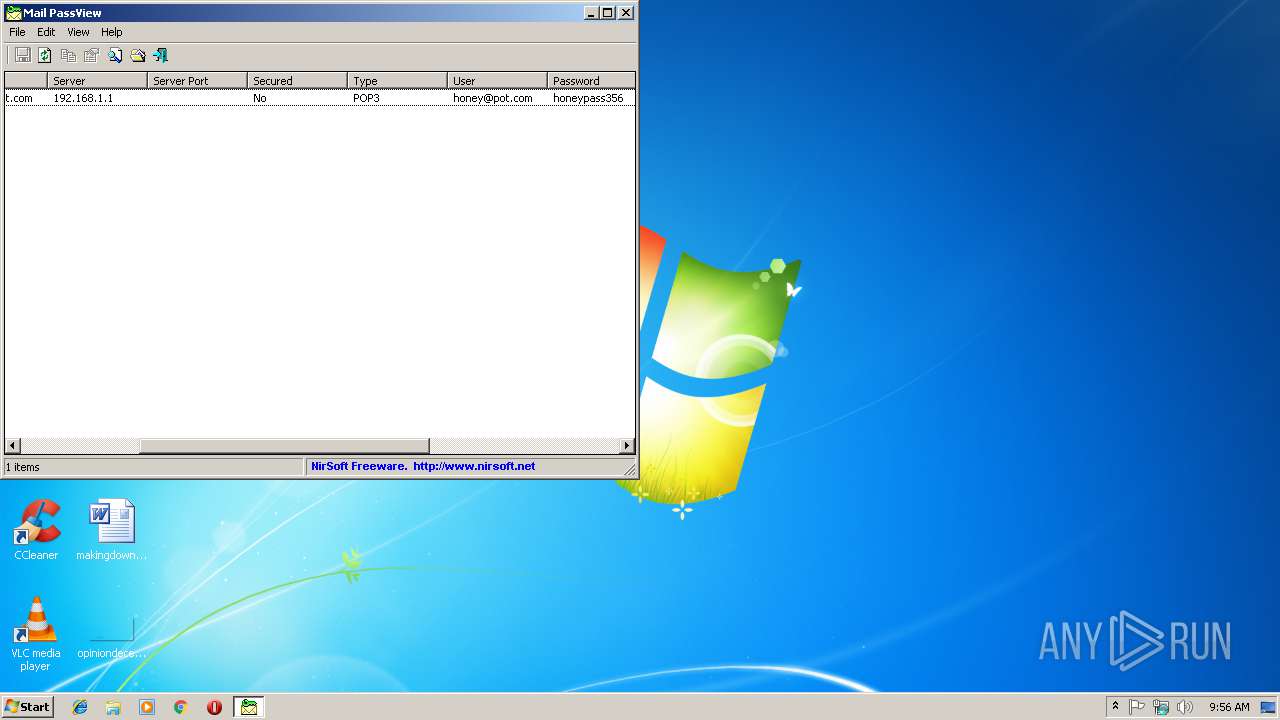
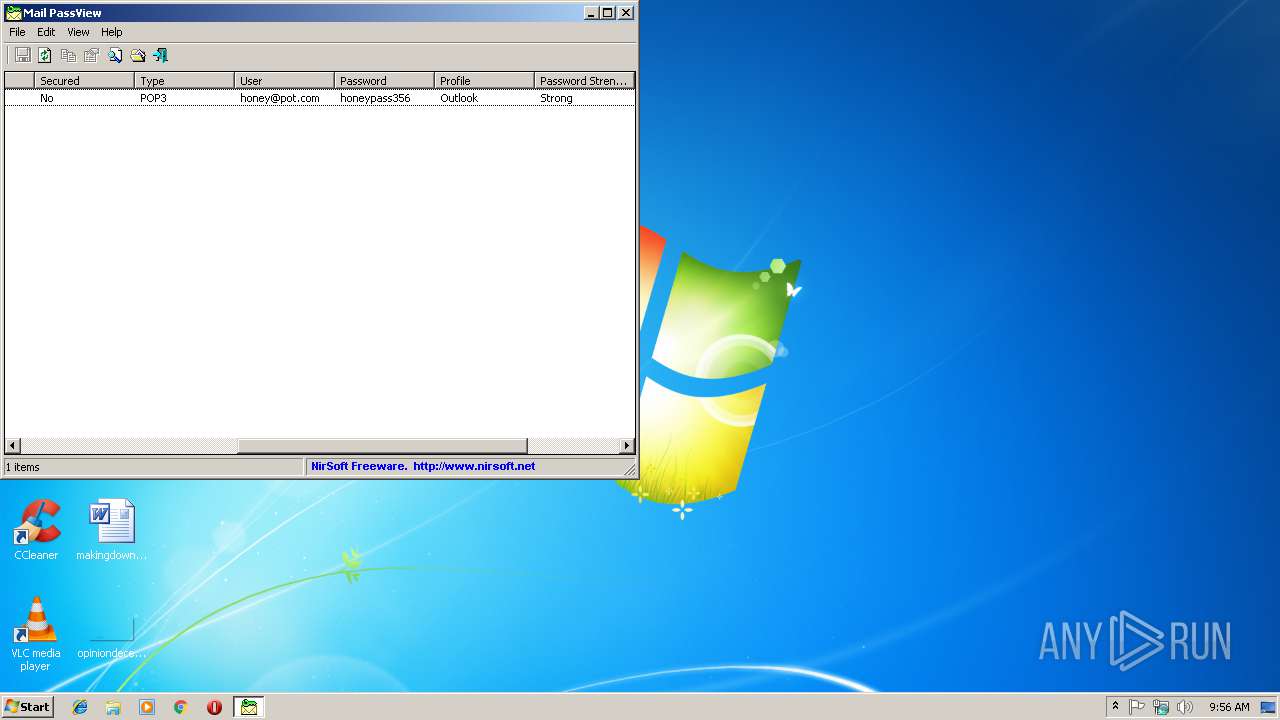
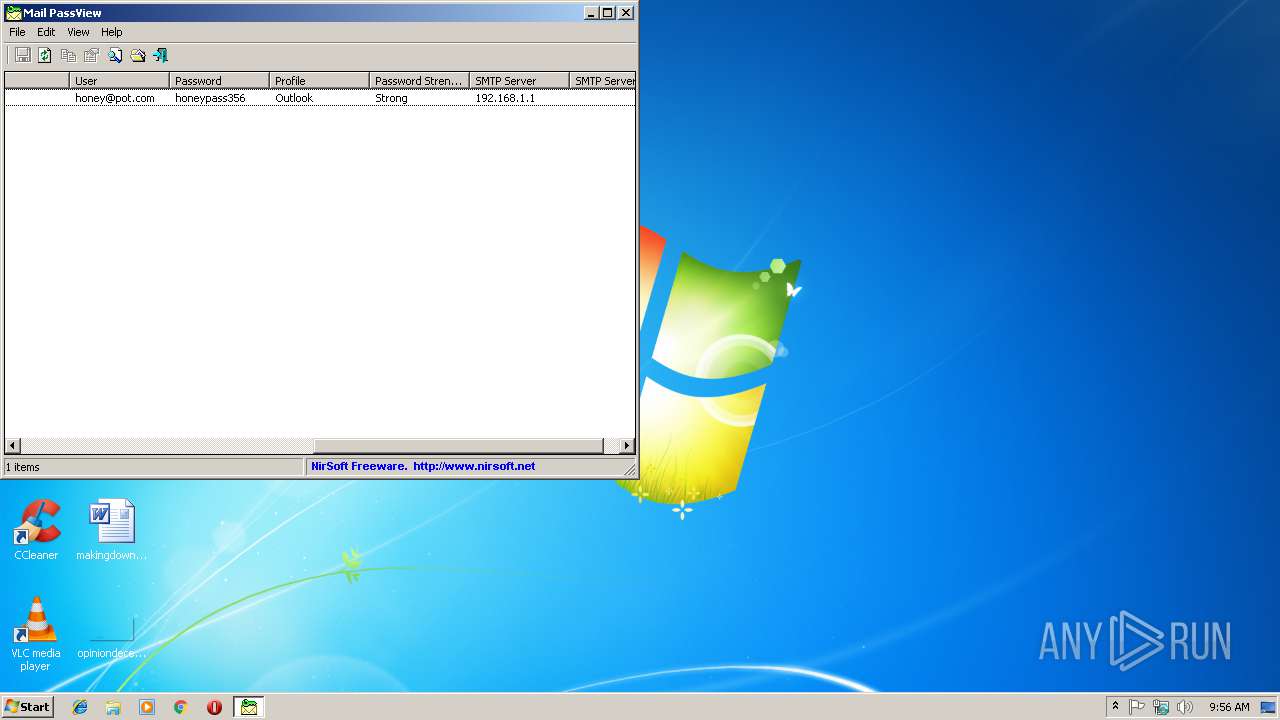
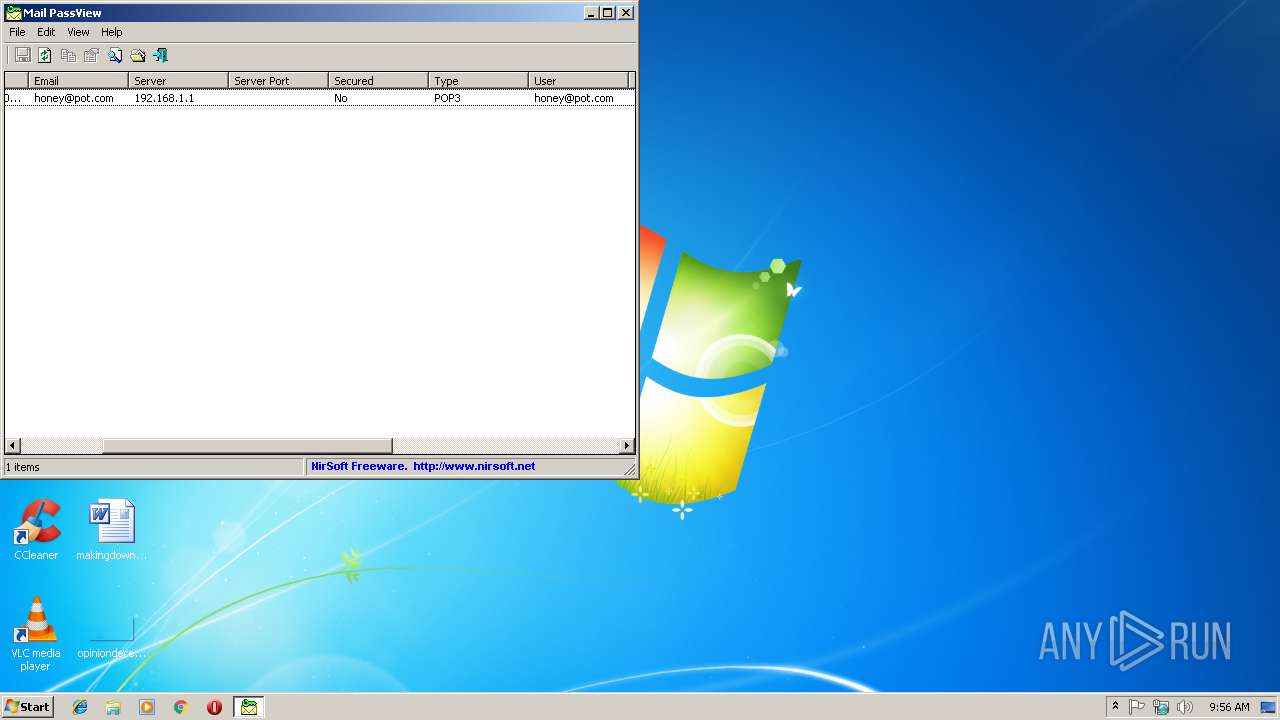
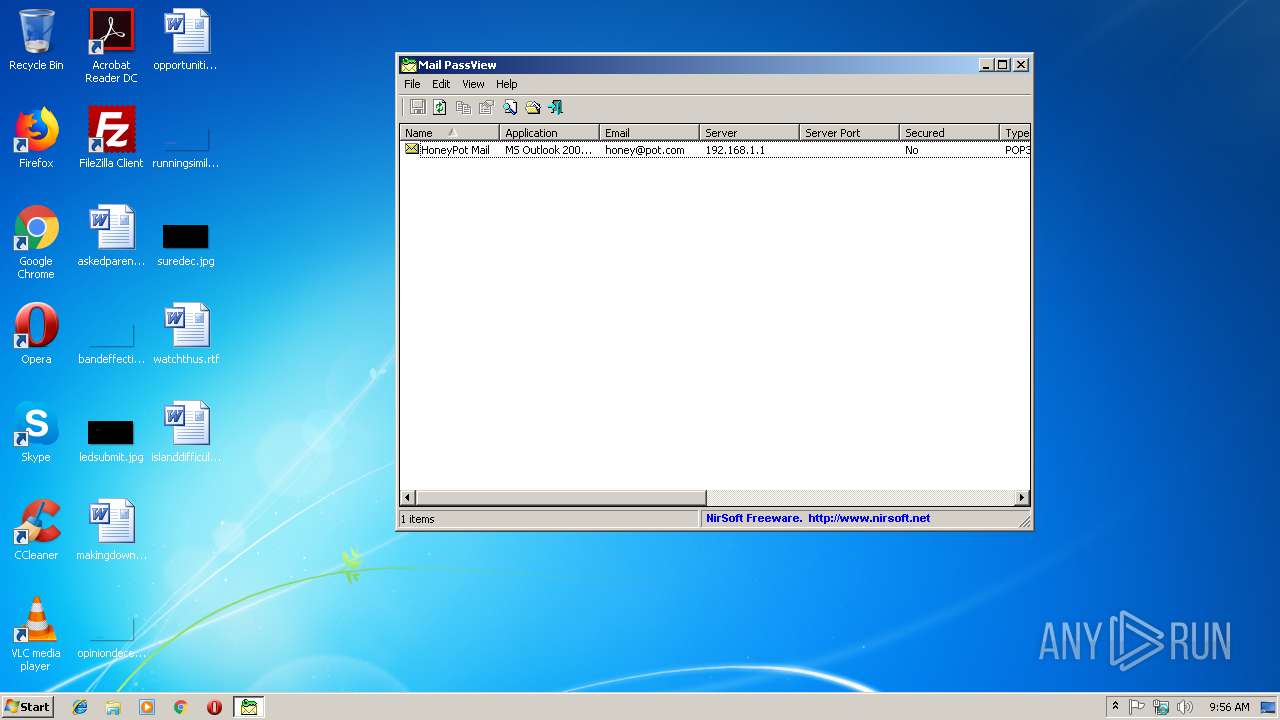
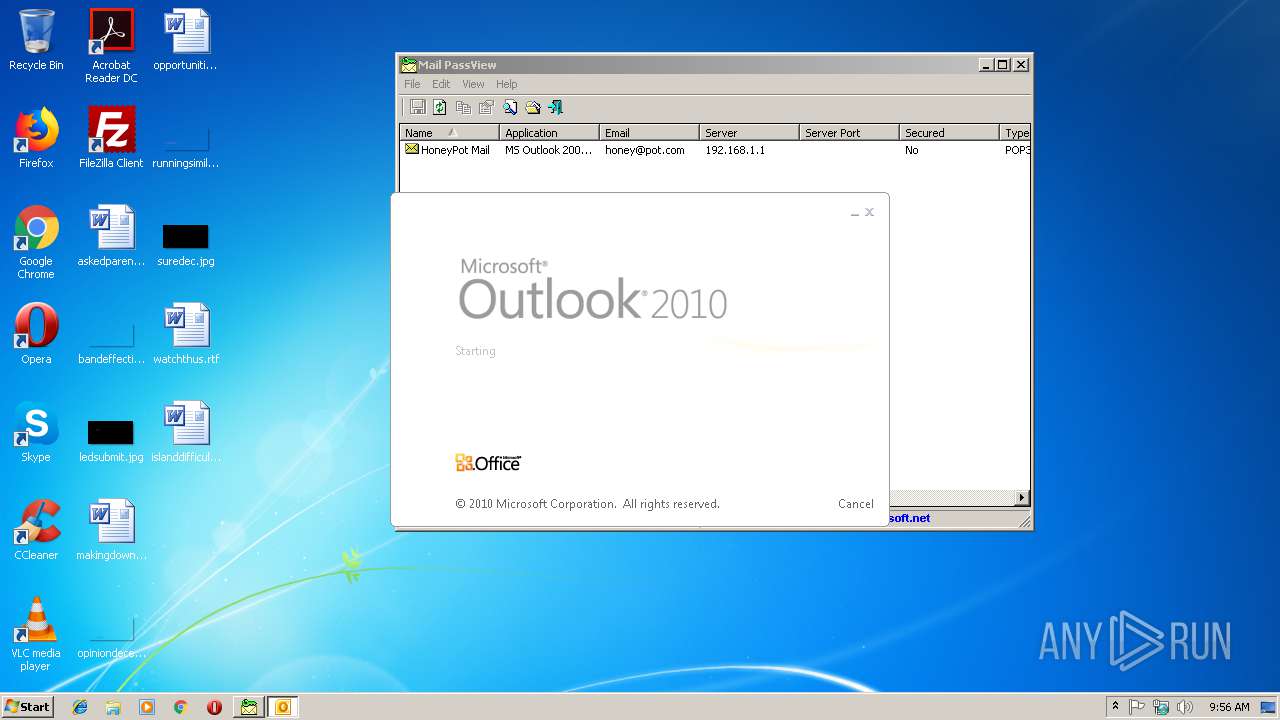
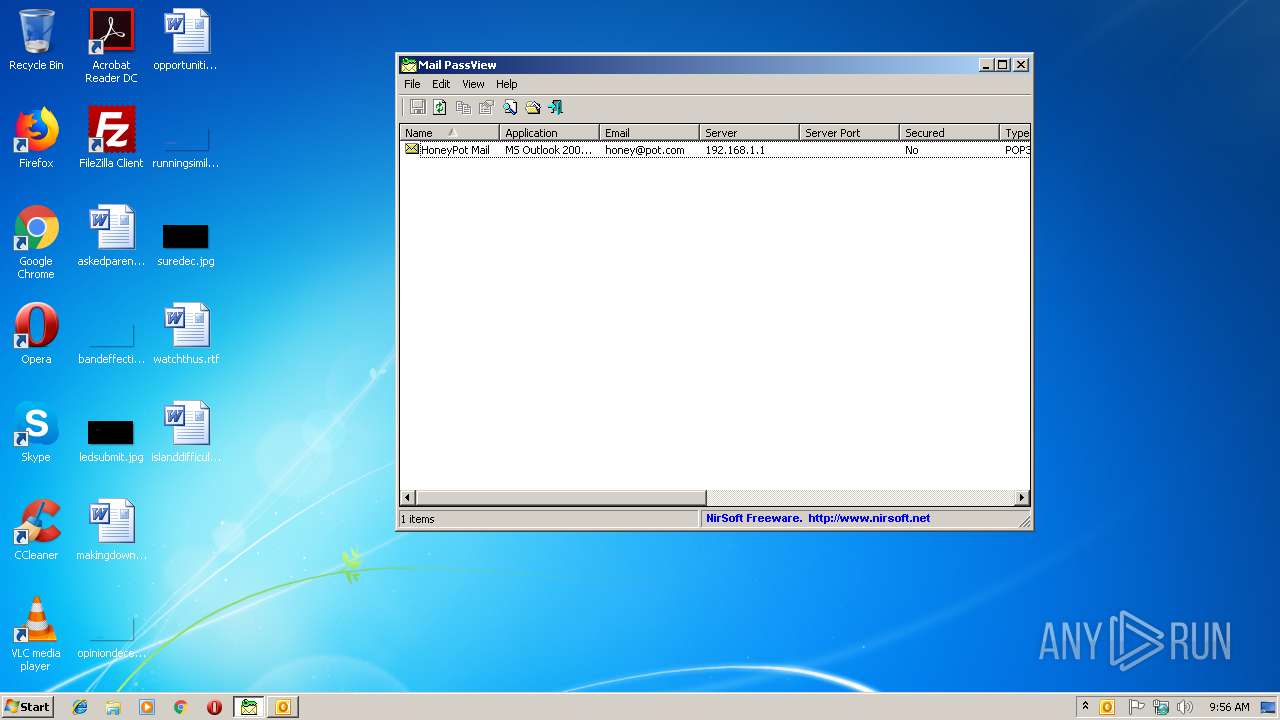
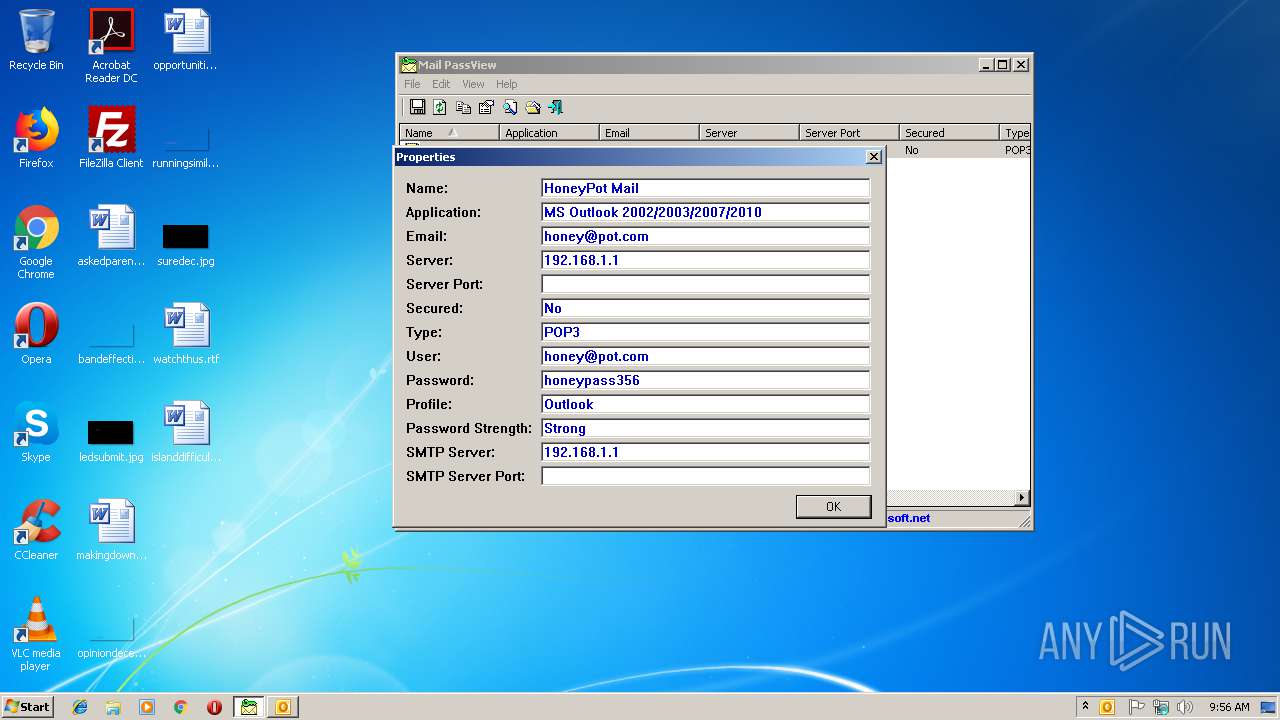
MALICIOUS
Actions looks like stealing of personal data
- mailpv.exe (PID: 3072)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2840)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 2840)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2840)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:26 11:48:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 69632 |
| InitializedDataSize: | 30208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11b34 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.8.6.183 |
| ProductVersionNumber: | 1.8.6.183 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | NirSoft |
| FileDescription: | Email Password-Recovery |
| FileVersion: | 1.86 |
| LegalCopyright: | Copyright © 2003 - 2016 Nir Sofer |
| ProductName: | Mail PassView |
| ProductVersion: | 1.86 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jun-2016 09:48:08 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | NirSoft |
| FileDescription: | Email Password-Recovery |
| FileVersion: | 1.86 |
| LegalCopyright: | Copyright © 2003 - 2016 Nir Sofer |
| ProductName: | Mail PassView |
| ProductVersion: | 1.86 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Jun-2016 09:48:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010E64 | 0x00011000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43384 |
.rdata | 0x00012000 | 0x00003822 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.5332 |
.data | 0x00016000 | 0x00001B74 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.69061 |
.rsrc | 0x00018000 | 0x00002EC4 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21334 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07251 | 362 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 0.545897 | 36 | Latin 1 / Western European | English - United States | RT_STRING |
3 | 3.0851 | 296 | Latin 1 / Western European | Hebrew - Israel | RT_ICON |
4 | 2.65212 | 296 | Latin 1 / Western European | Hebrew - Israel | RT_ICON |
32 | 3.13812 | 314 | Latin 1 / Western European | English - United States | RT_STRING |
33 | 1.77938 | 62 | Latin 1 / Western European | English - United States | RT_STRING |
51 | 2.00069 | 72 | Latin 1 / Western European | English - United States | RT_STRING |
57 | 3.42484 | 308 | Latin 1 / Western European | English - United States | RT_STRING |
58 | 2.98248 | 166 | Latin 1 / Western European | English - United States | RT_STRING |
63 | 2.90059 | 116 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
comdlg32.dll |
msvcrt.dll |
ole32.dll |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
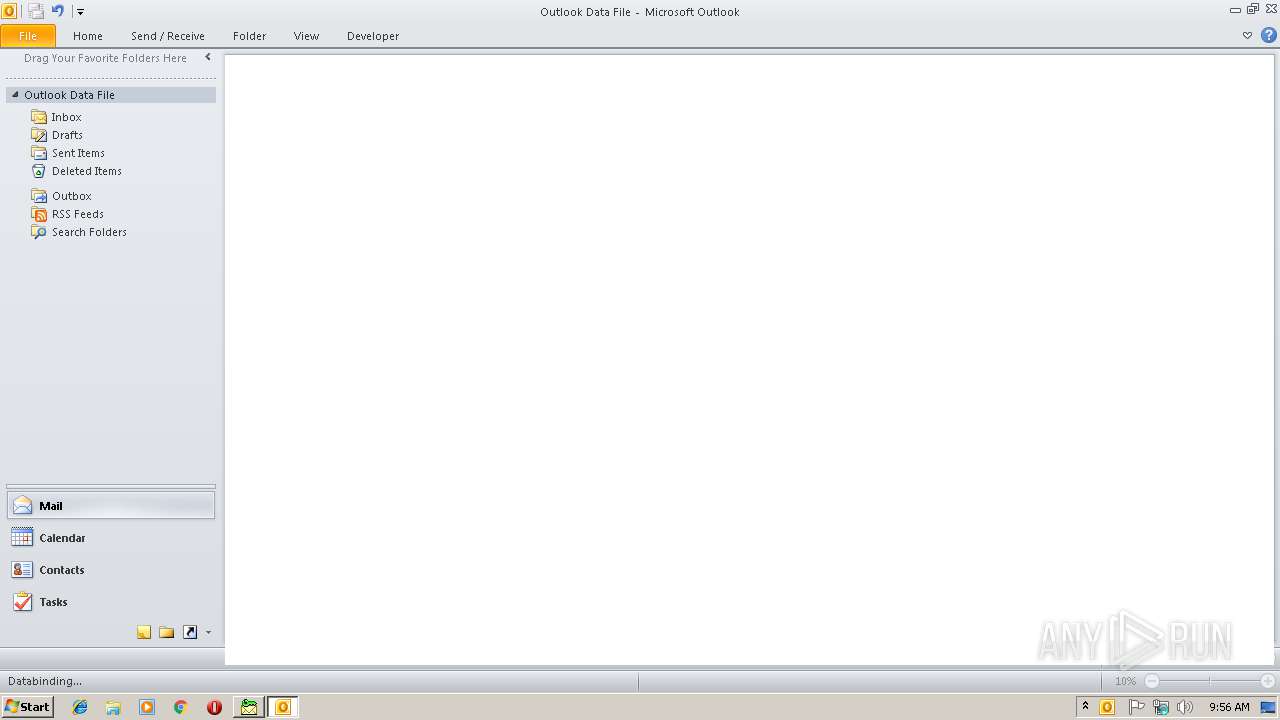
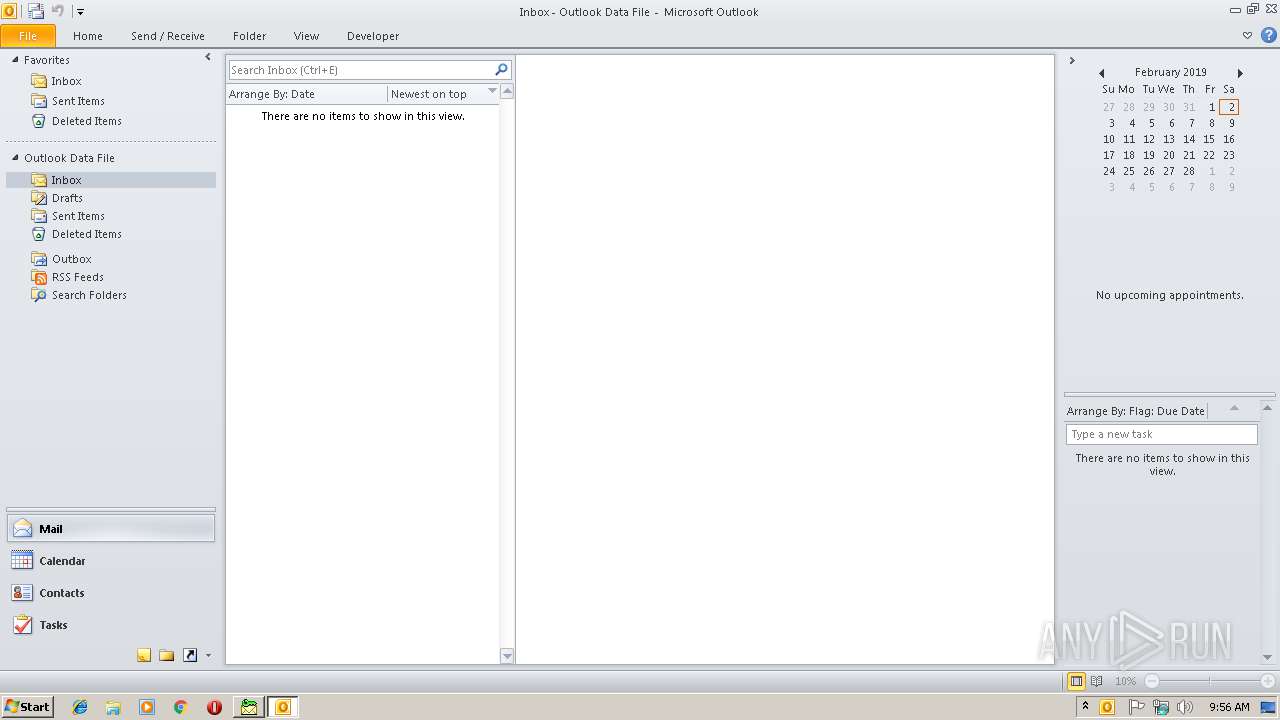
| 2840 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\mailpv.exe" | C:\Users\admin\AppData\Local\Temp\mailpv.exe | explorer.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Email Password-Recovery Exit code: 0 Version: 1.86 Modules
| |||||||||||||||
Total events
830
Read events
696
Write events
108
Delete events
26
Modification events
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | i$0 |
Value: 69243000180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 180B0000A4984992DDBAD40100000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219892320 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1312948245 | |||
Executable files
0
Suspicious files
0
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE8DA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\msoFEB6.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso59C.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019020220190203\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_ED6BC9F0CDF9694BAC42C418D3A2B72E.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_DD2357182470B94597EA8AC7A0F6E5EF.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\gap[1] | image | |
MD5:96C4C871750D7CA05DFA18CE6A85D369 | SHA256:74441313BB1FB62500484443C4937E90D4E335351A4FCD12A9AC48448500E33E | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{A070978F-6658-4B6A-9E10-F53E2377FD86}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\msoECA4.tmp | html | |
MD5:A8934077843220A8E31367C7BBE15E6C | SHA256:A2DB0201D36F07F3F99D1ADF8B8EAFB9CF9BB803D024FCC9327B77AF56346861 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |