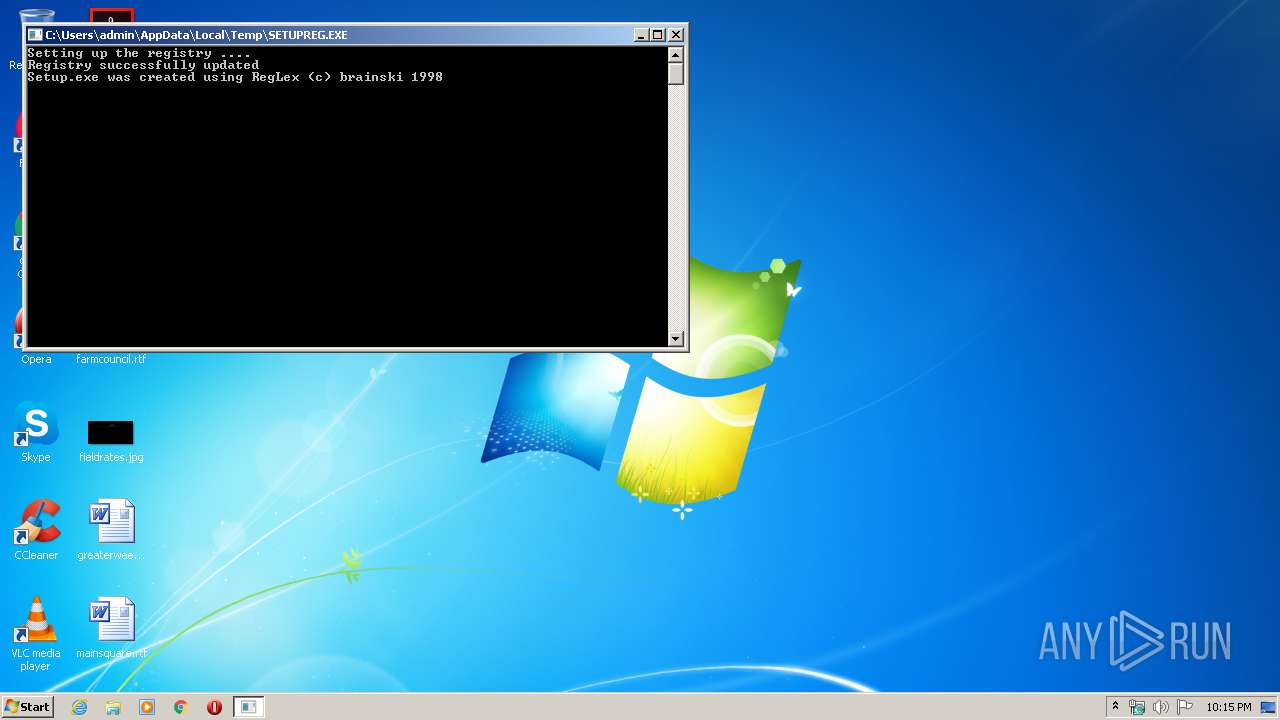
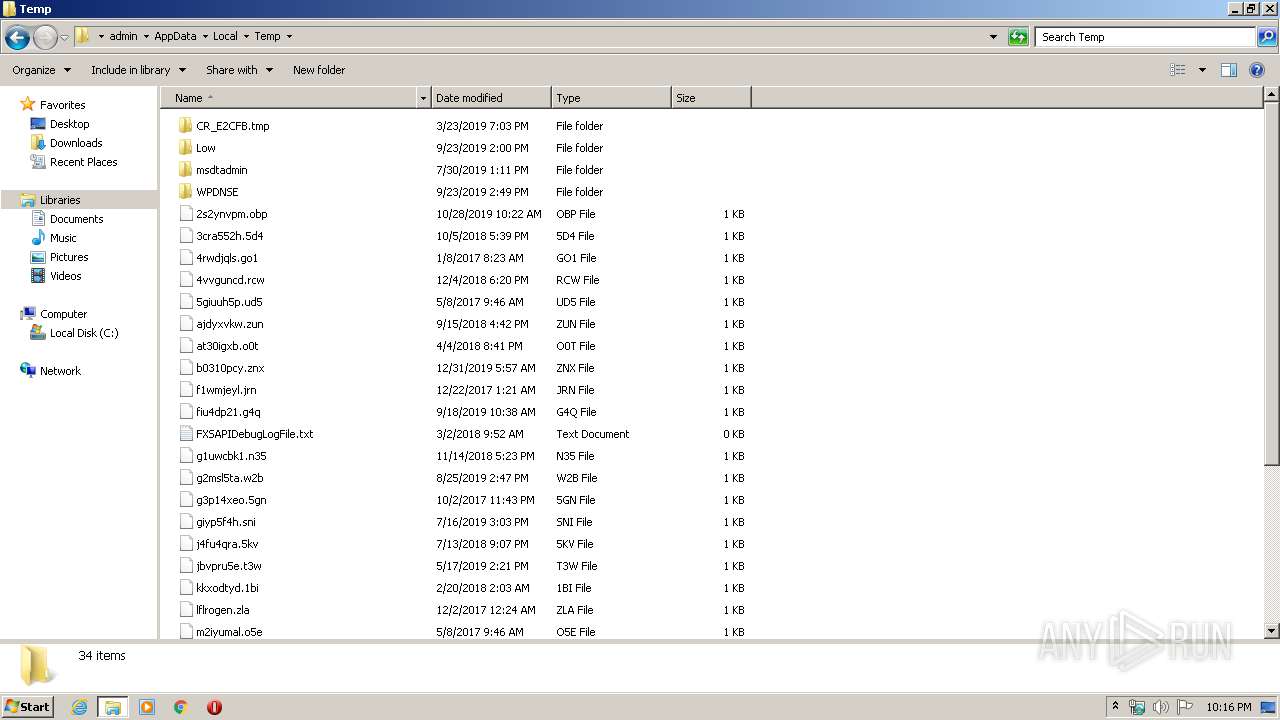
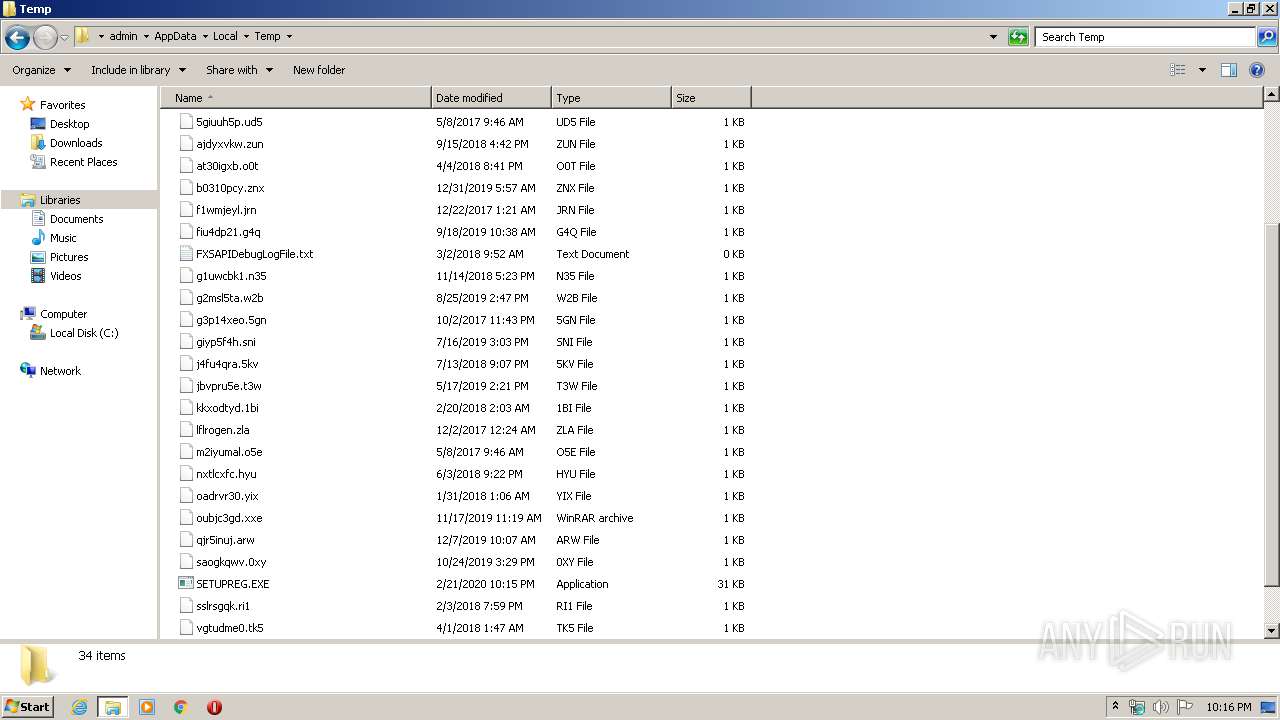
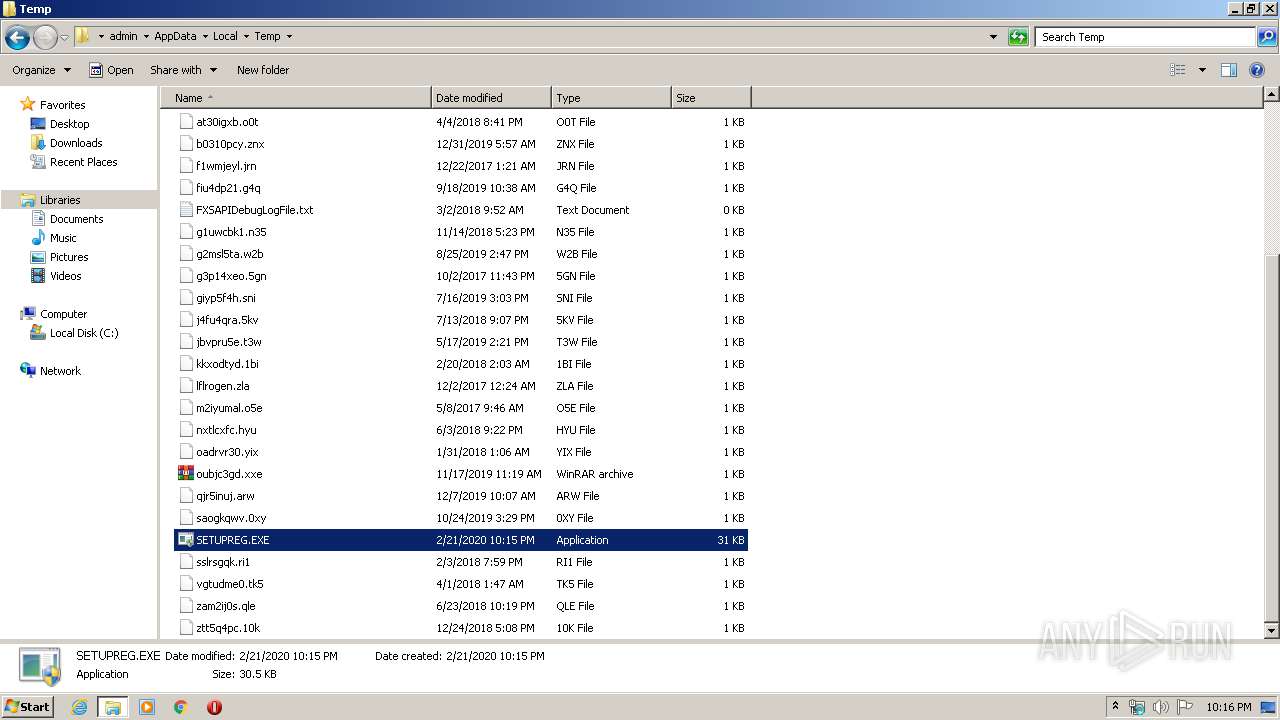
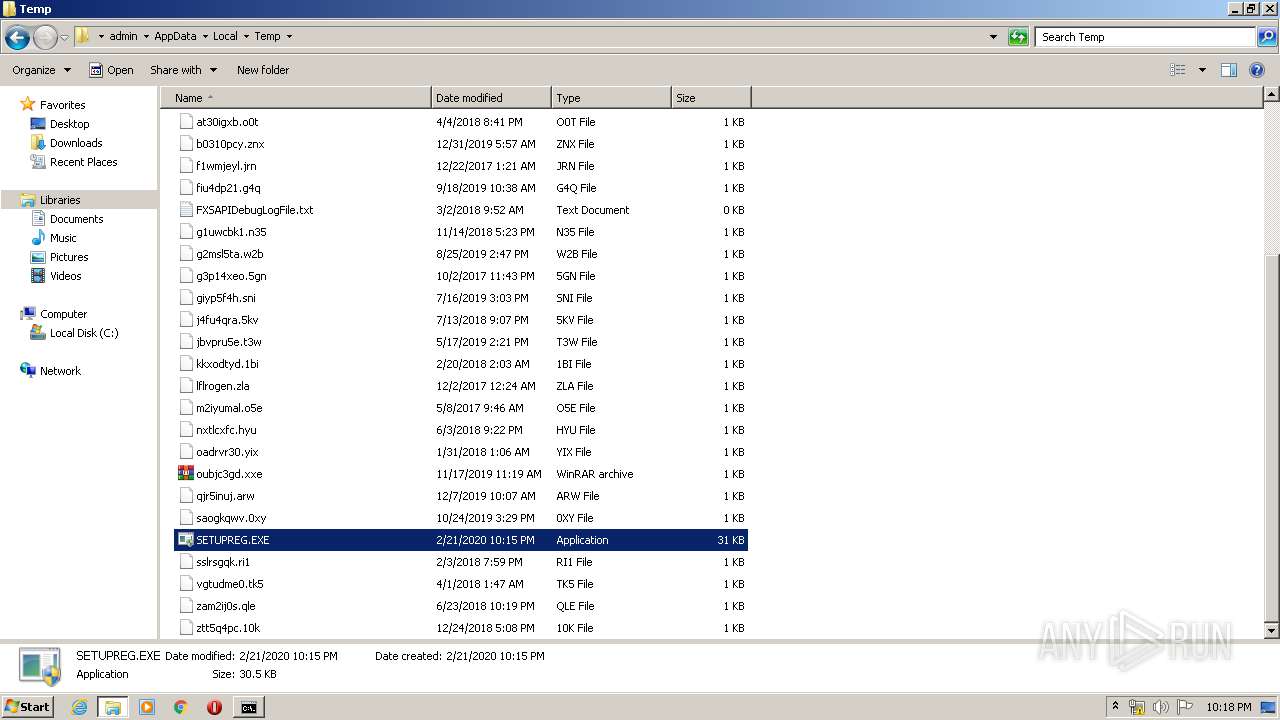
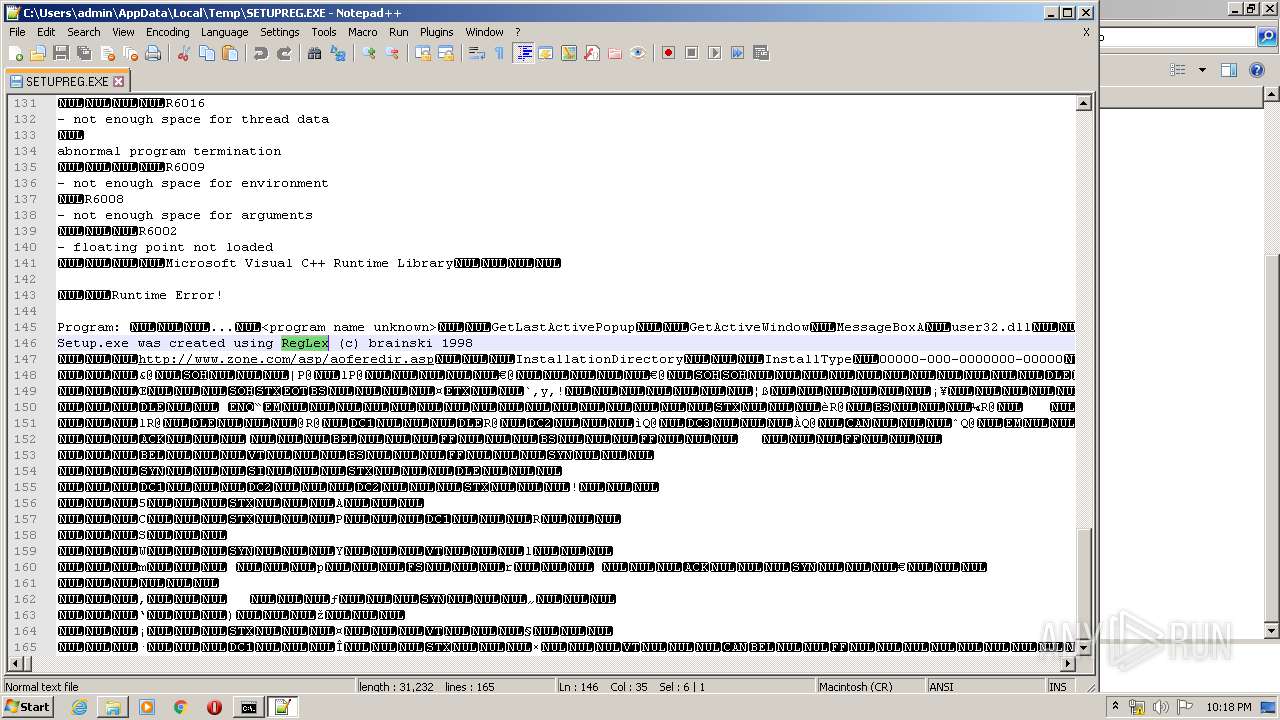
| File name: | SETUPREG.EXE |
| Full analysis: | https://app.any.run/tasks/bfece831-ded7-4761-98c0-4c1fc2467e7a |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 22:15:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 5138C8BECF9E02D4EEB59F3765DED178 |
| SHA1: | DC724770ECE8907FBB7E211B933B649AF73056E7 |
| SHA256: | 268FE404496426795E79748C755E481D33161906E1404A3C9BD3A5233688C1C3 |
| SSDEEP: | 384:67GRxdGLbl1fwzeV9TtHv5Z8kXILp+hZobru/agrtix:y2uoertHvHtXIYSrAZti |
MALICIOUS
No malicious indicators.SUSPICIOUS
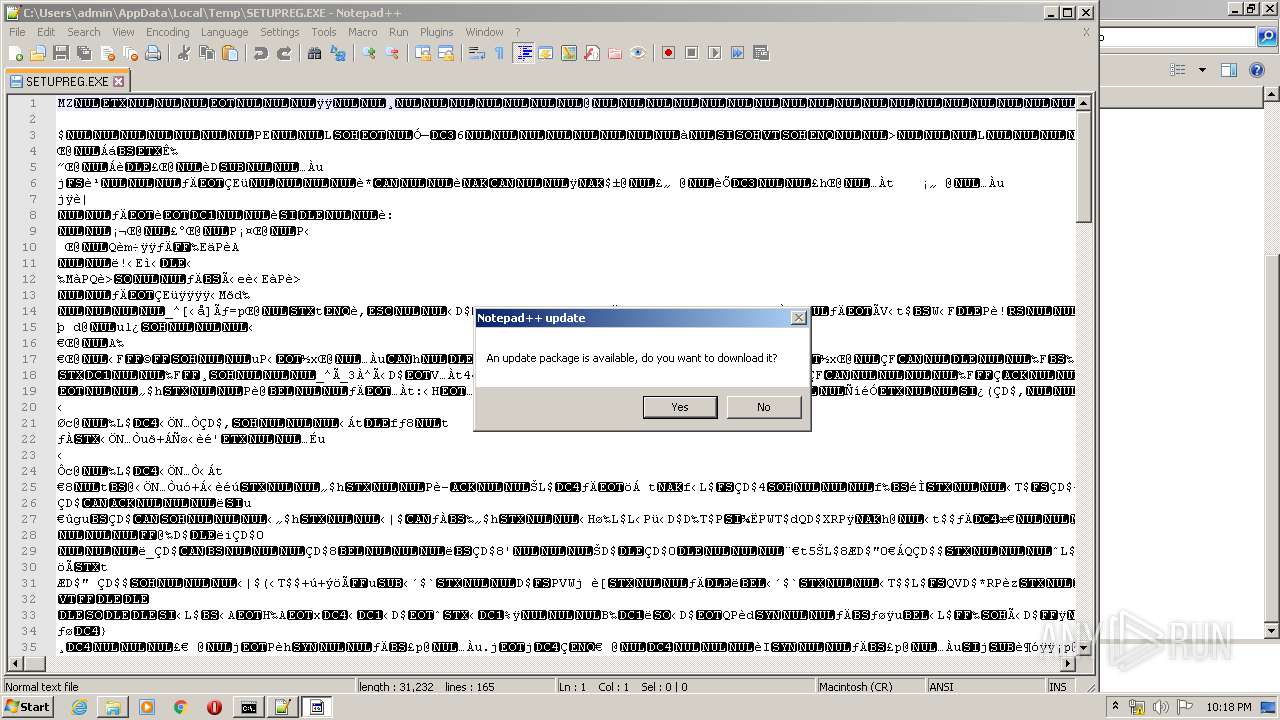
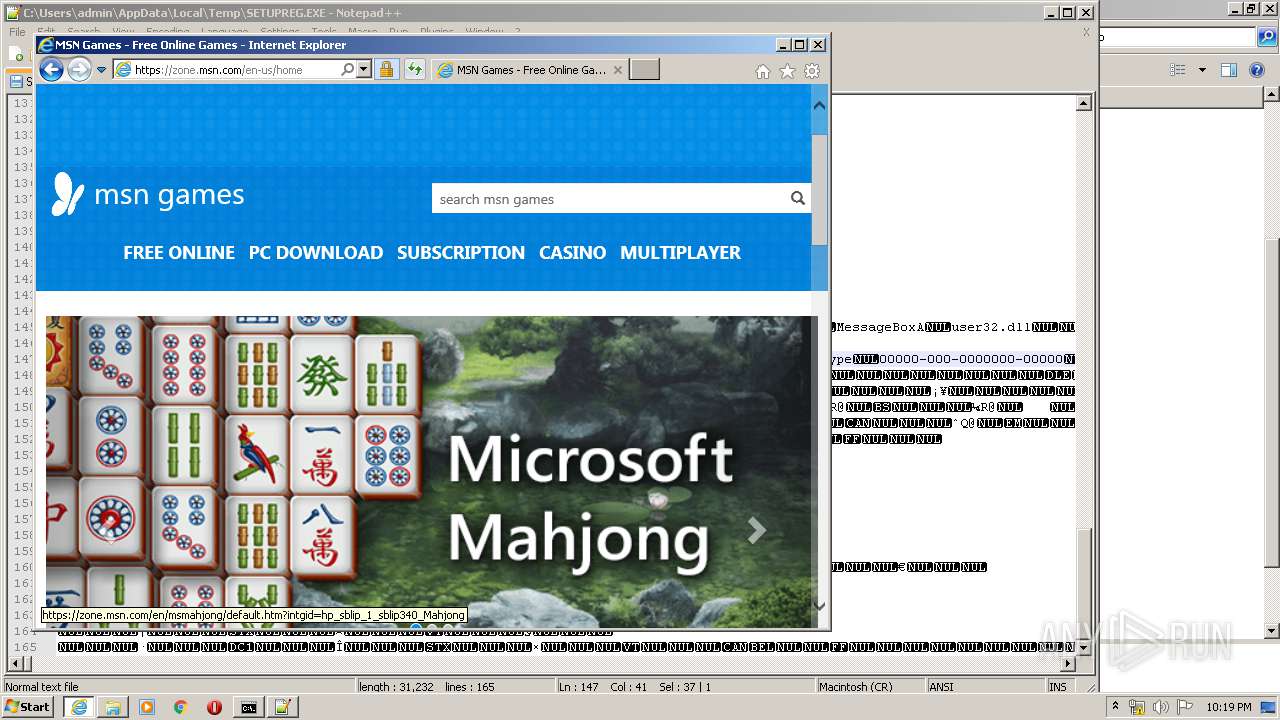
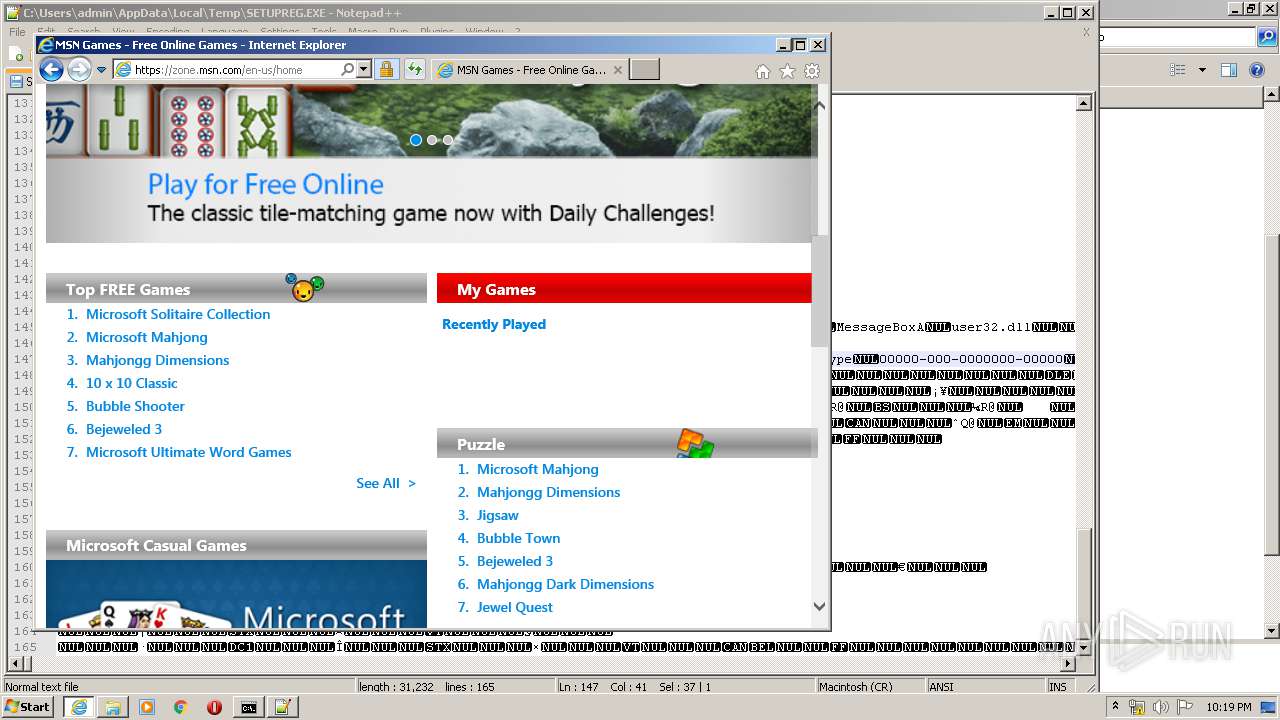
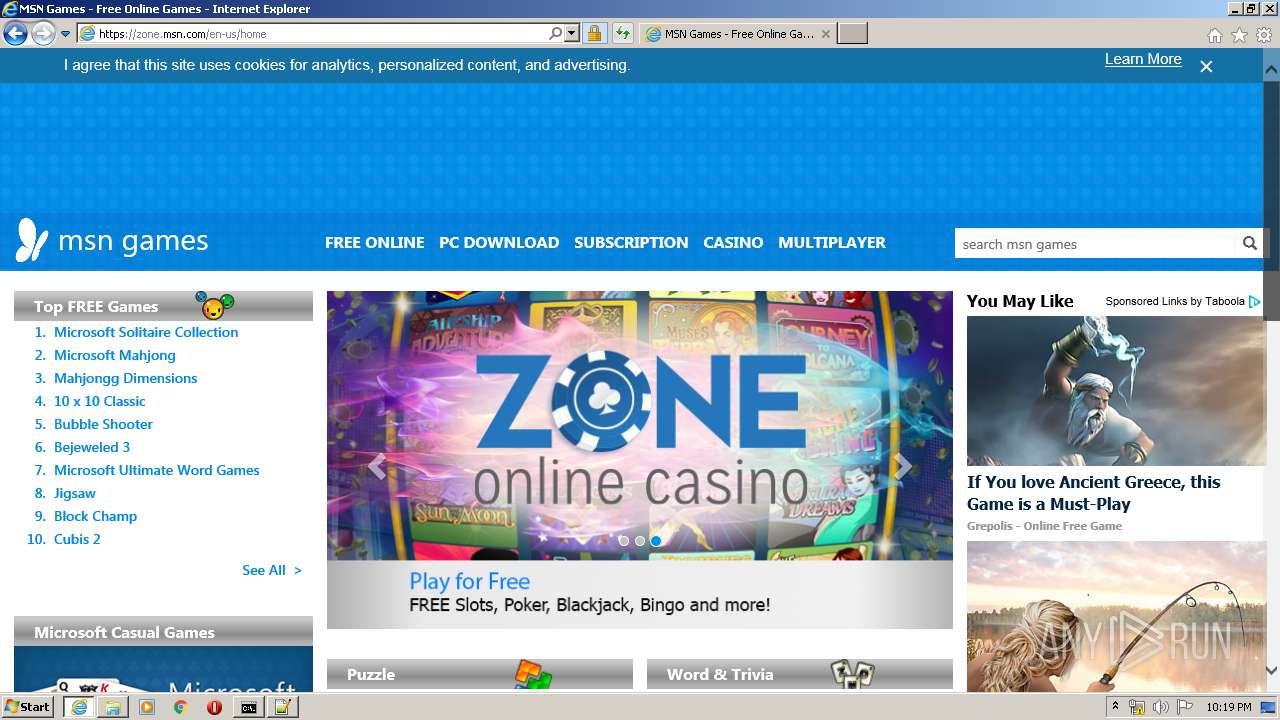
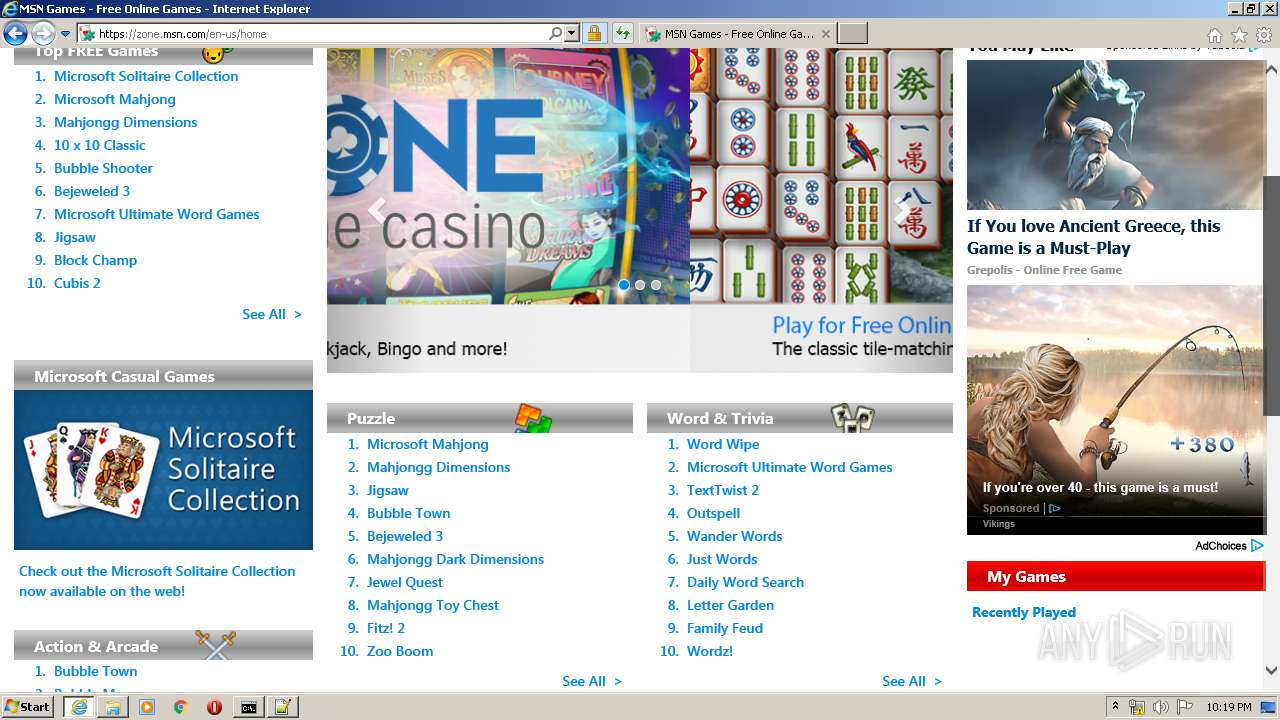
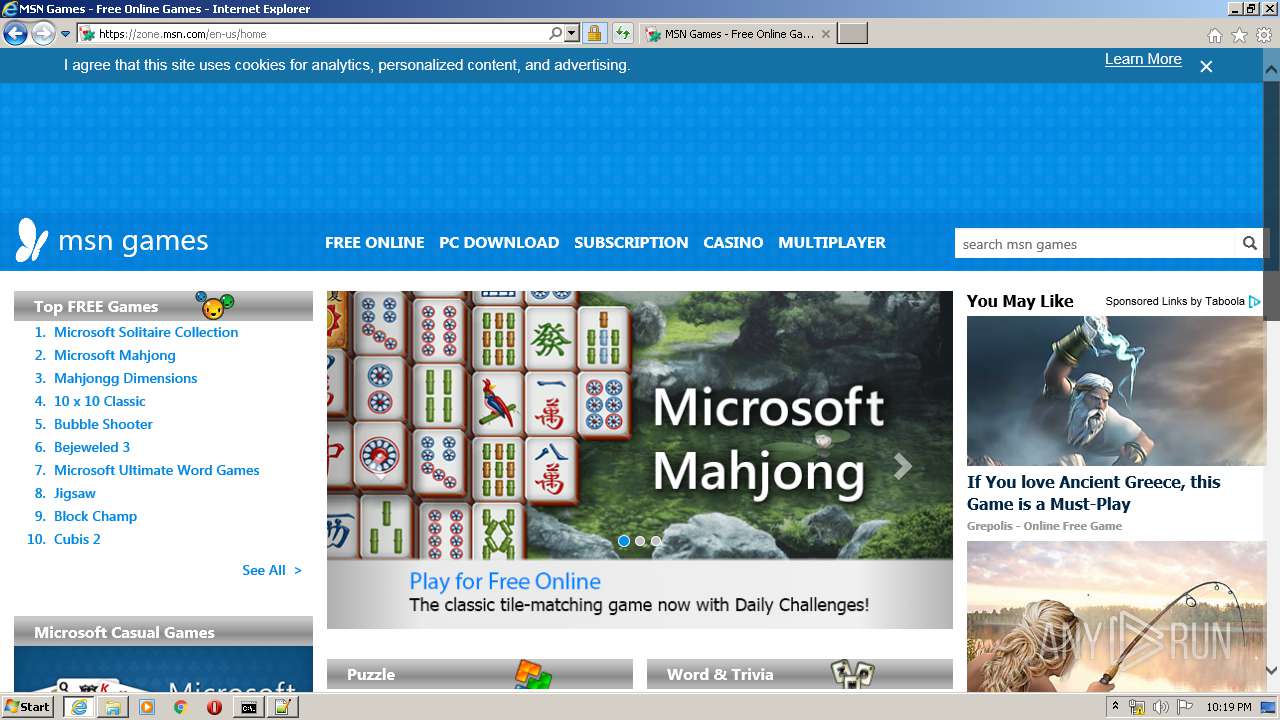
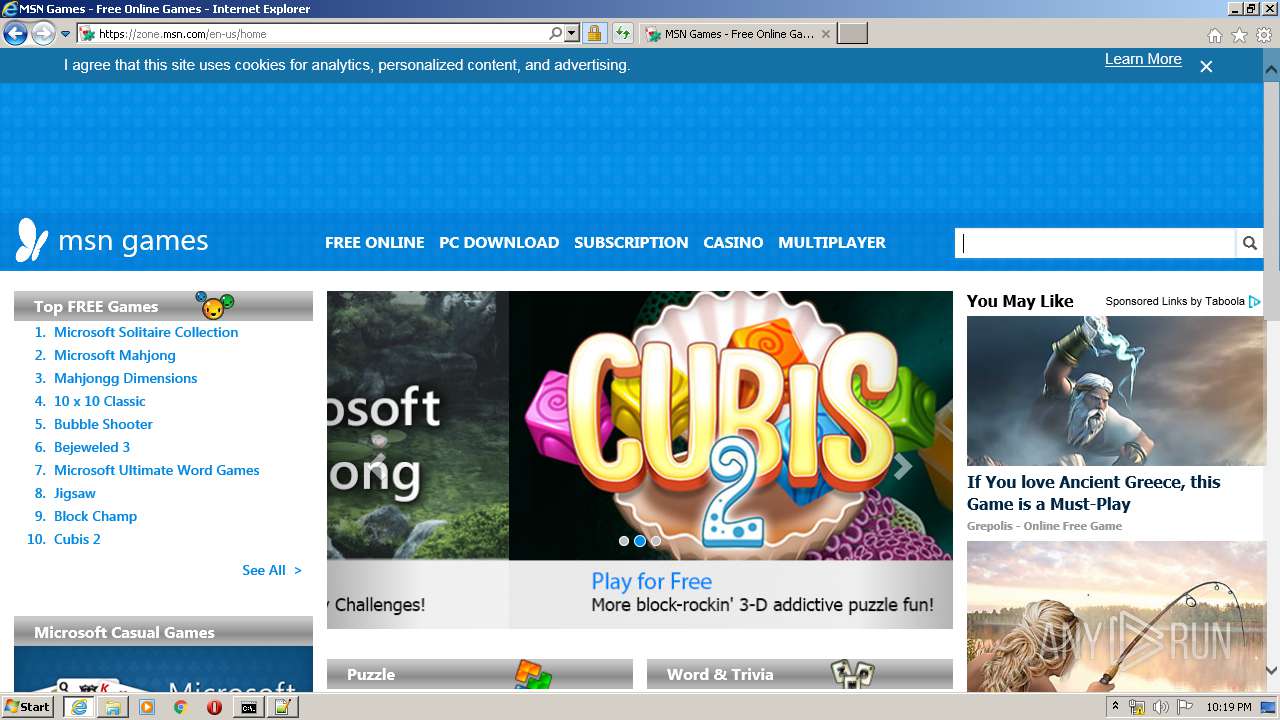
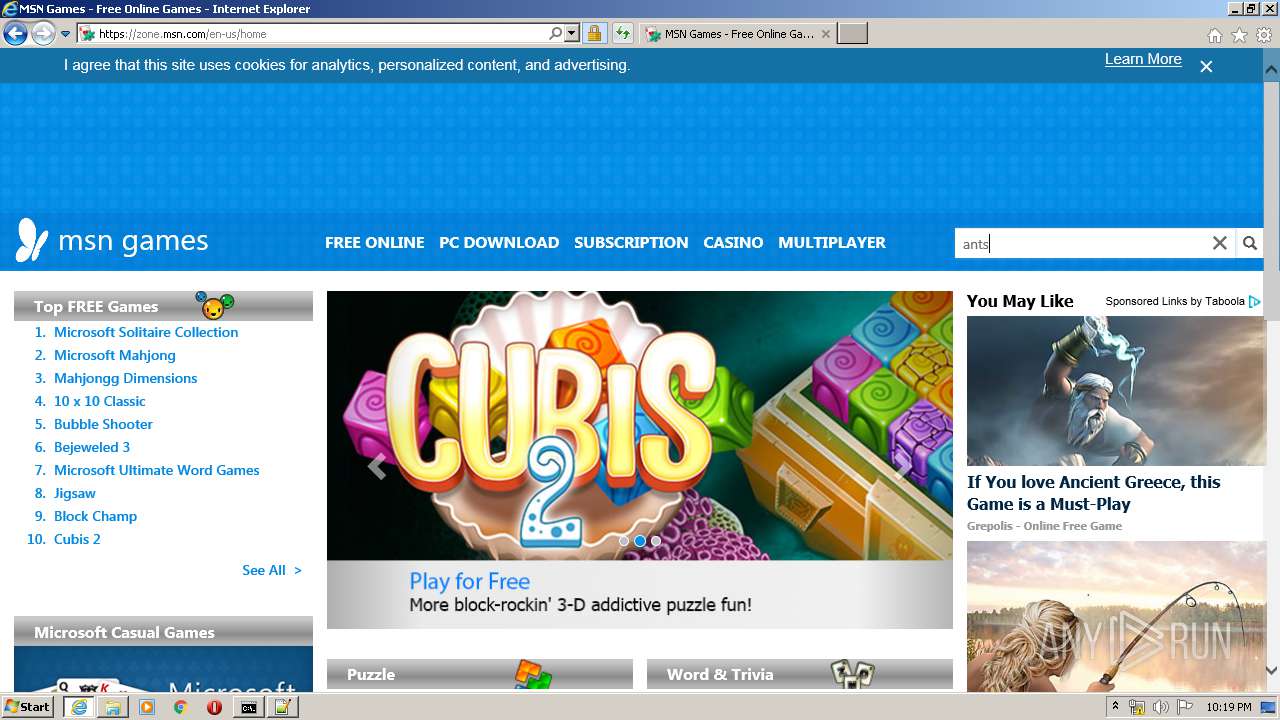
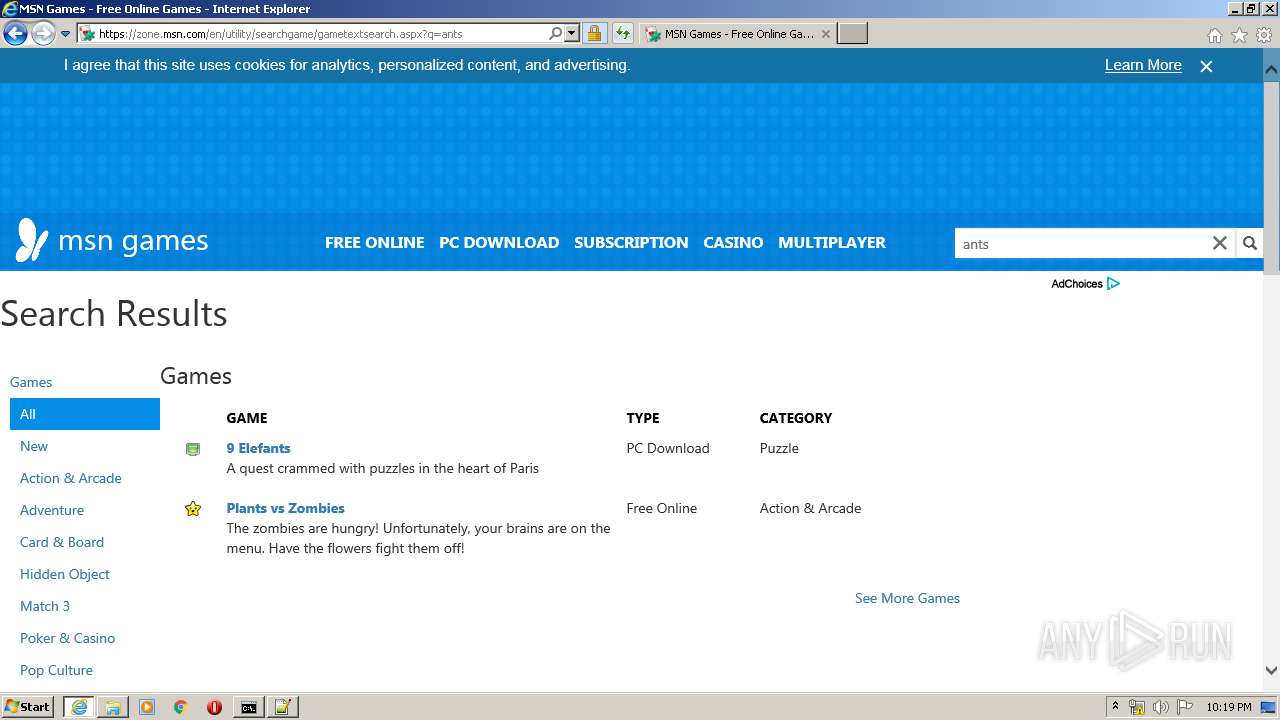
Starts Internet Explorer
- notepad++.exe (PID: 3892)
Creates files in the user directory
- notepad++.exe (PID: 3892)
INFO
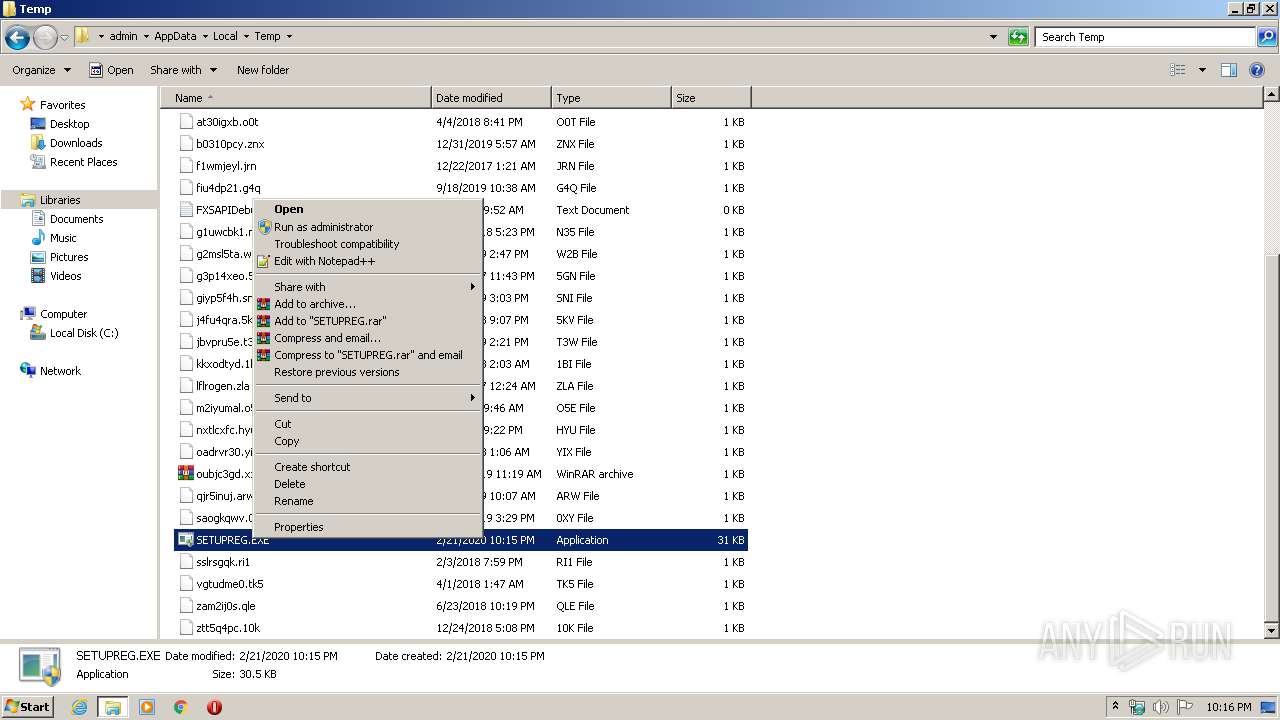
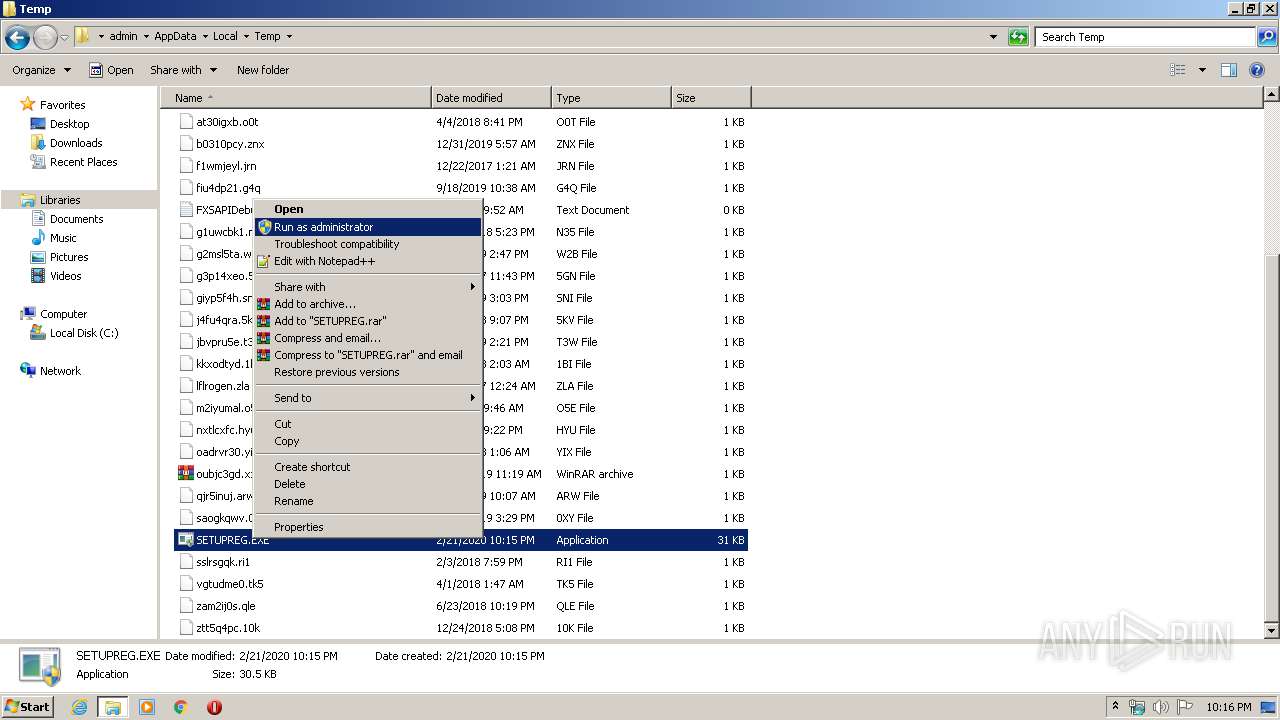
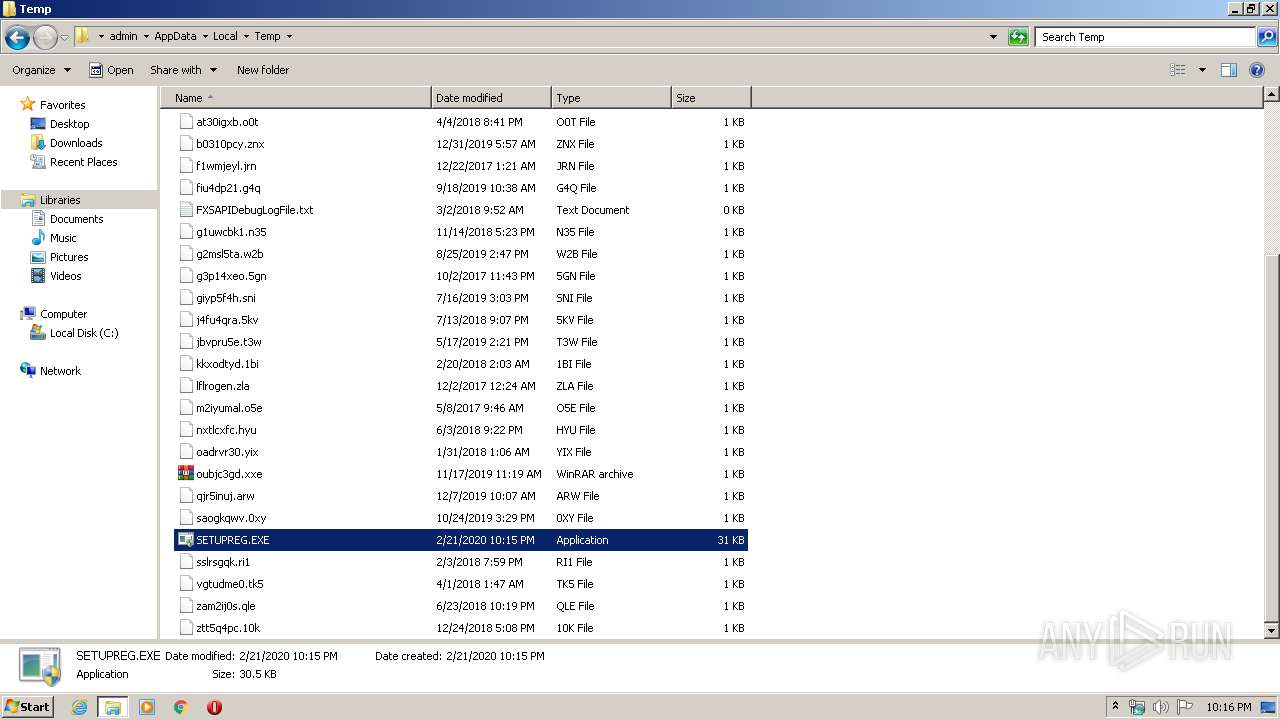
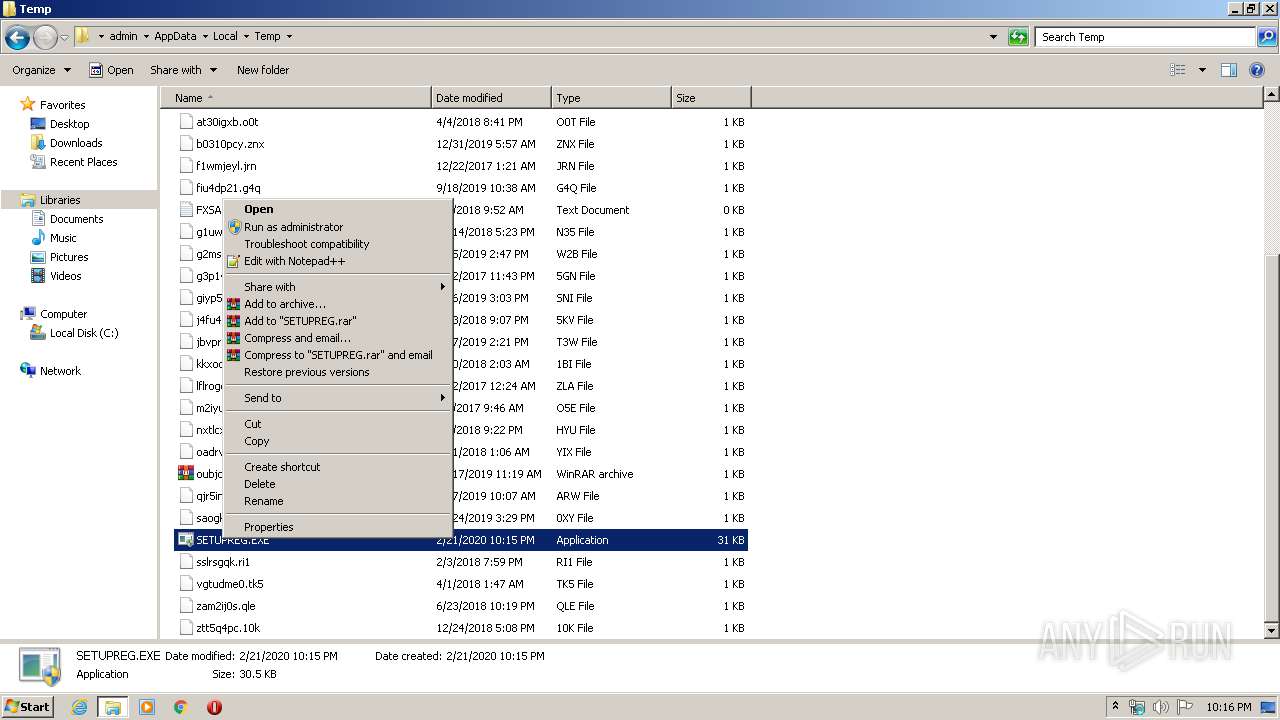
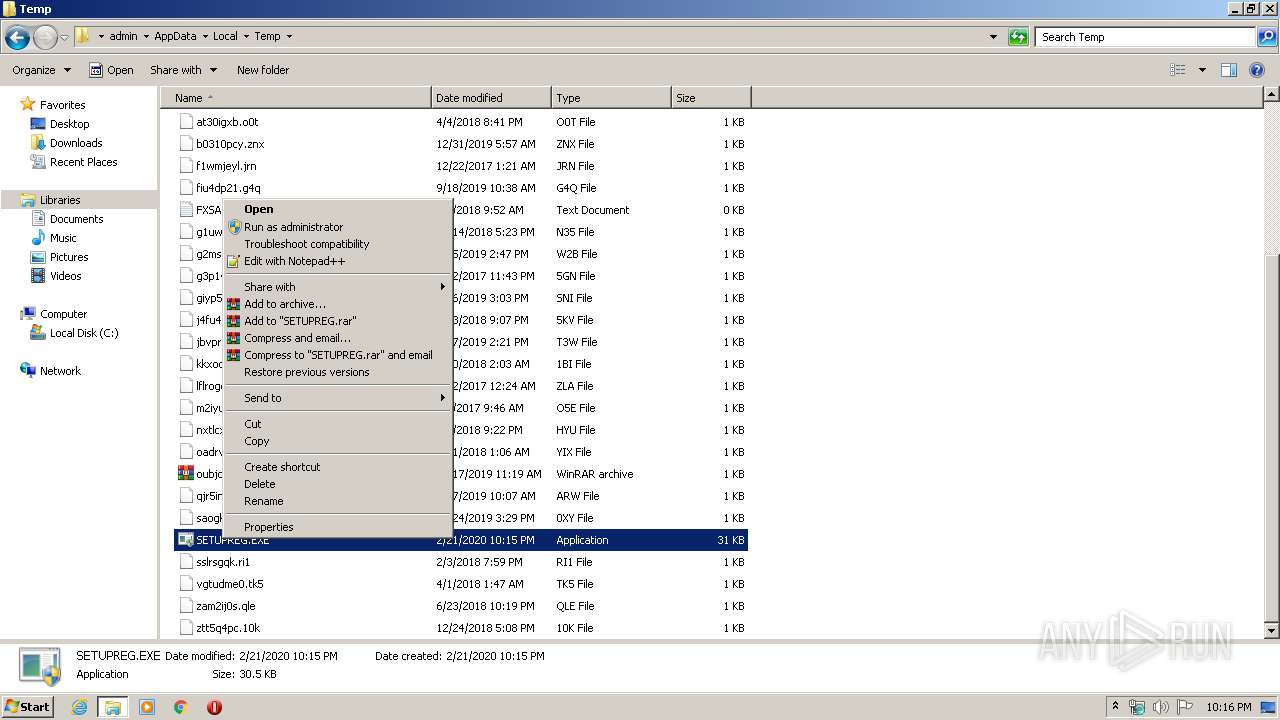
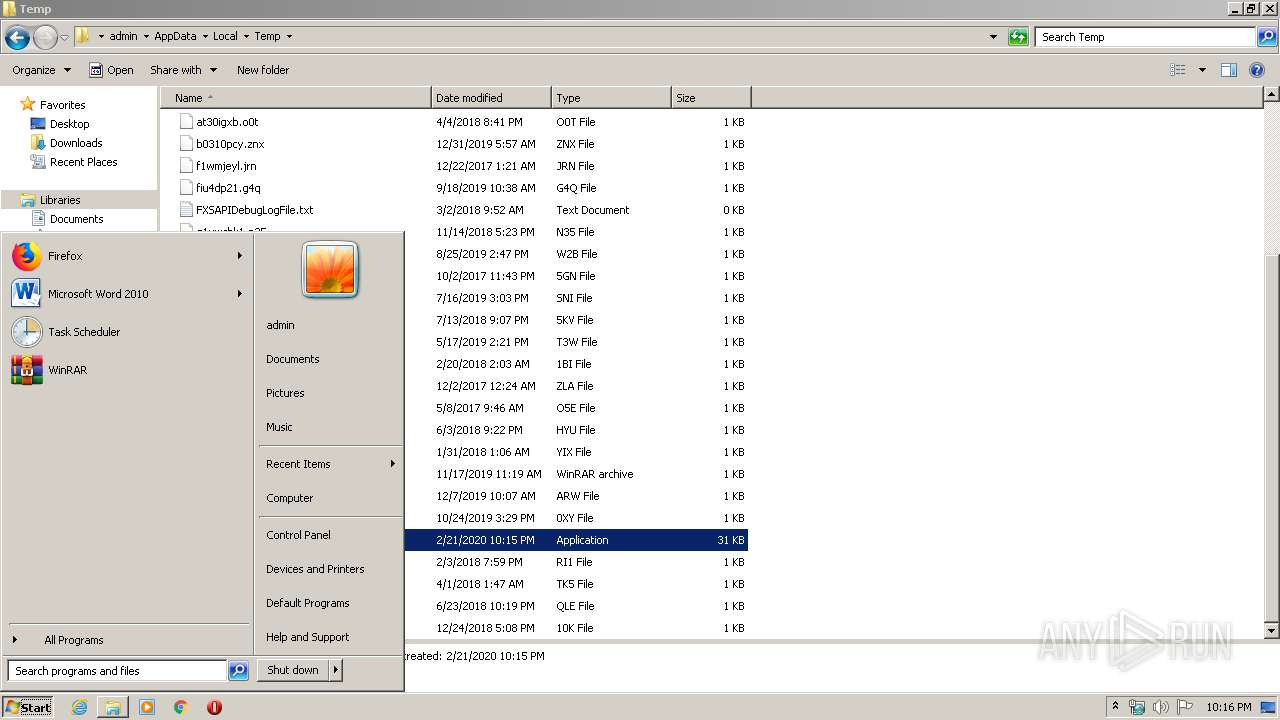
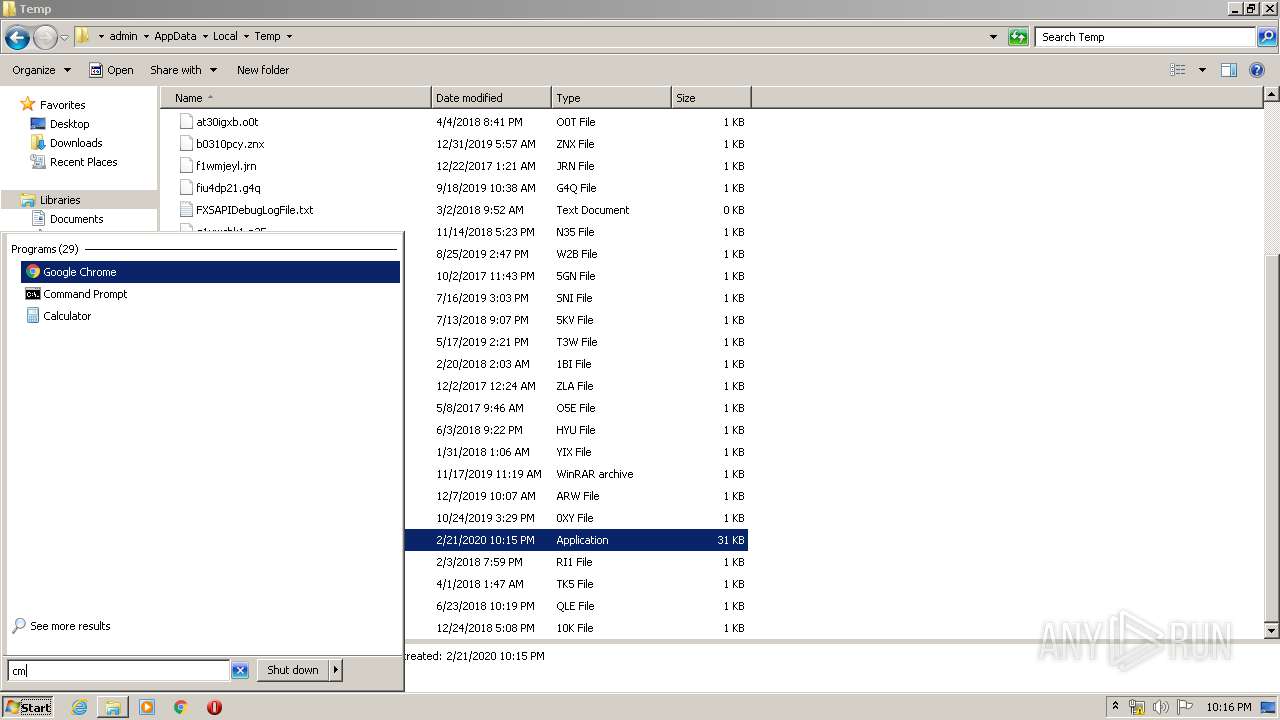
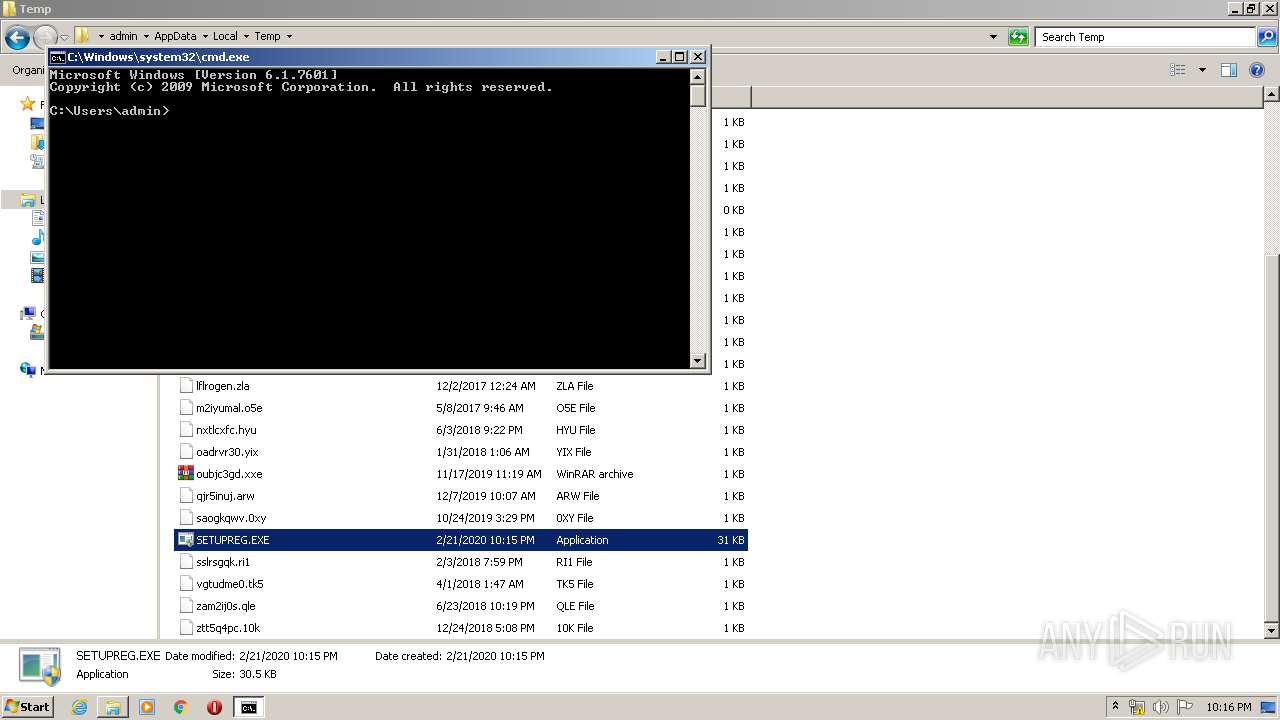
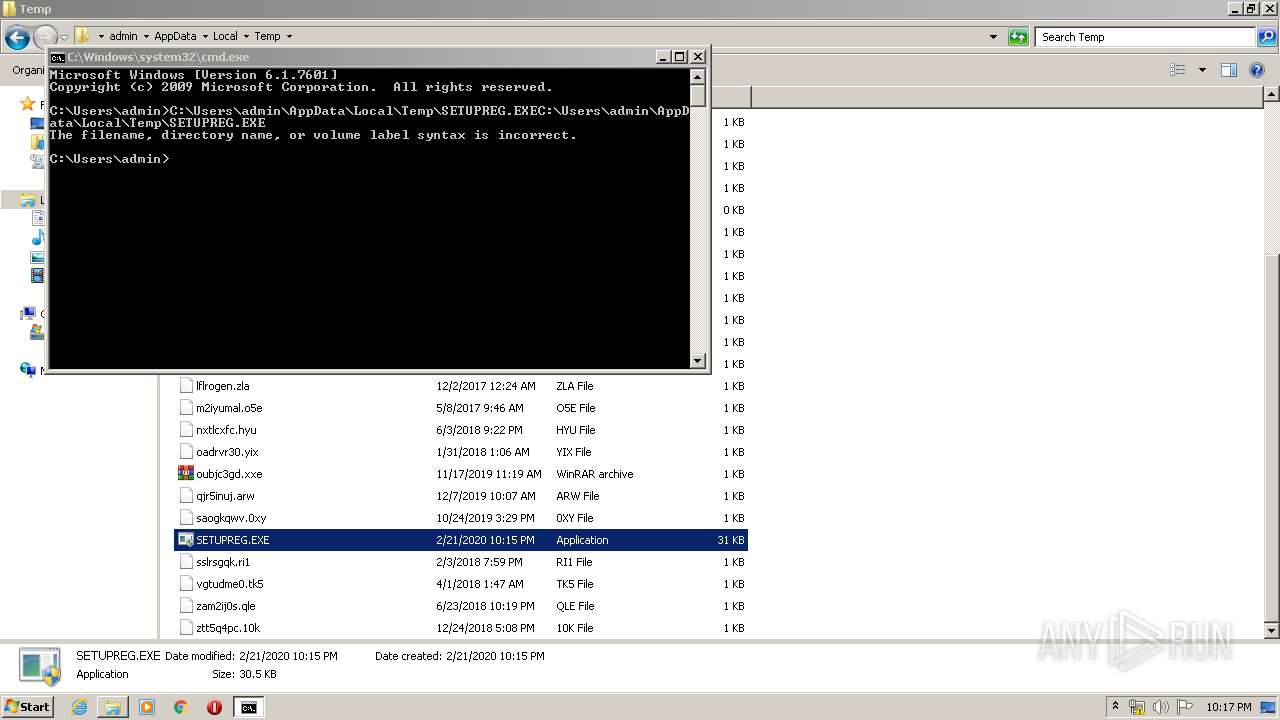
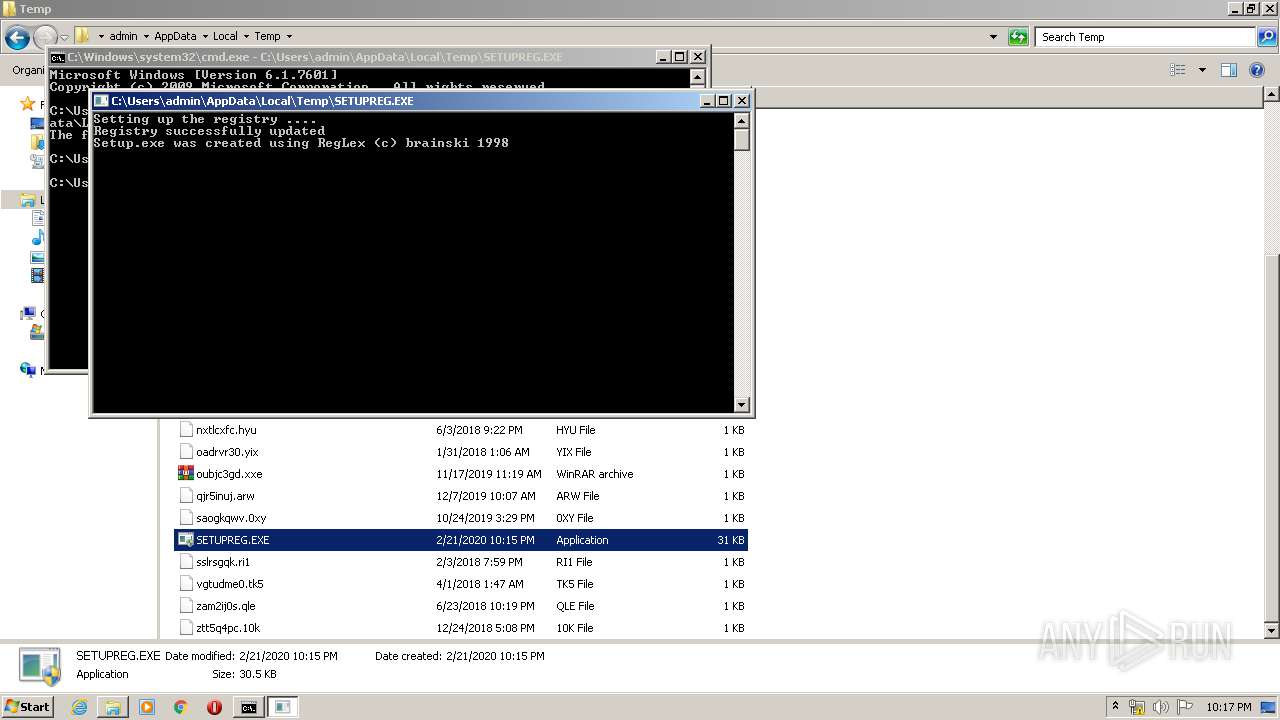
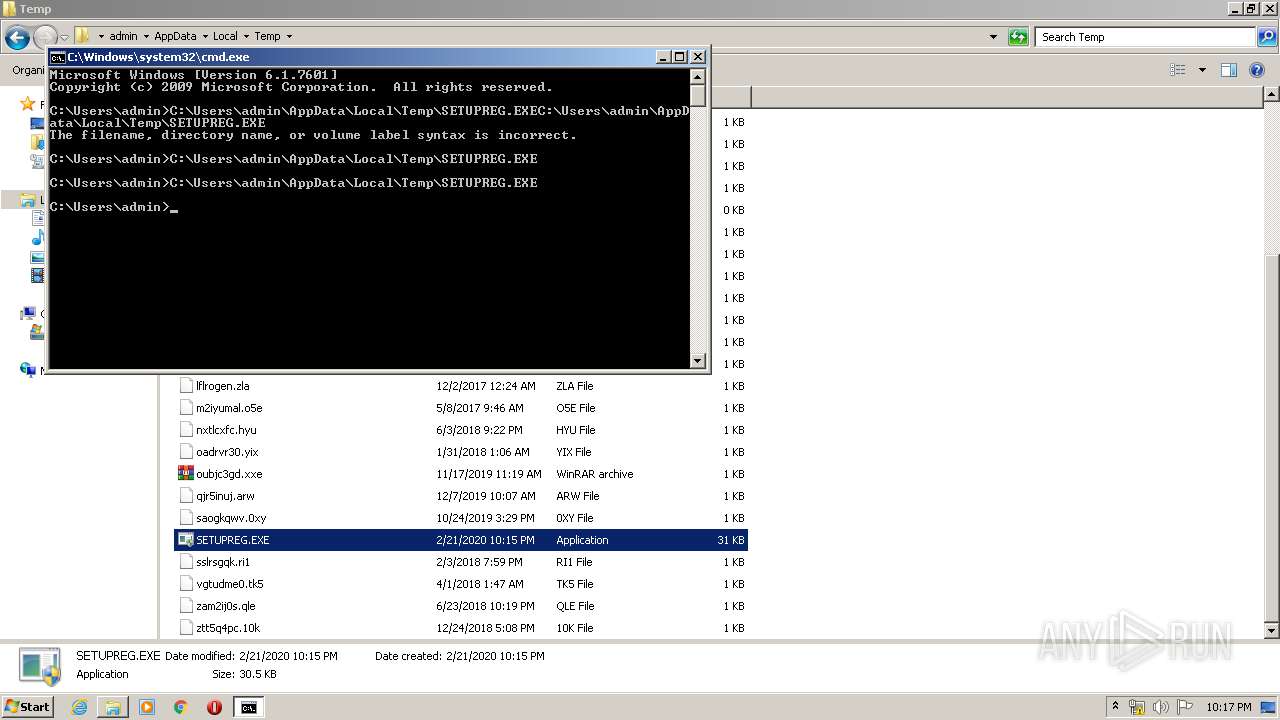
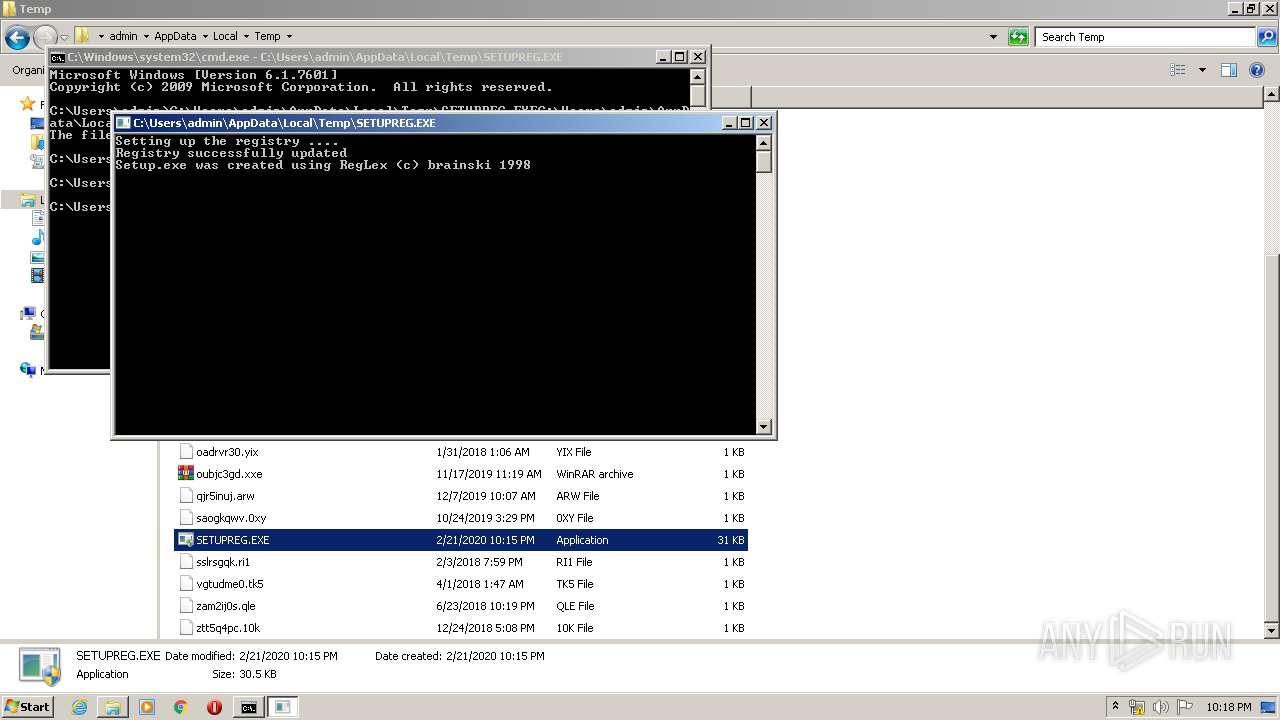
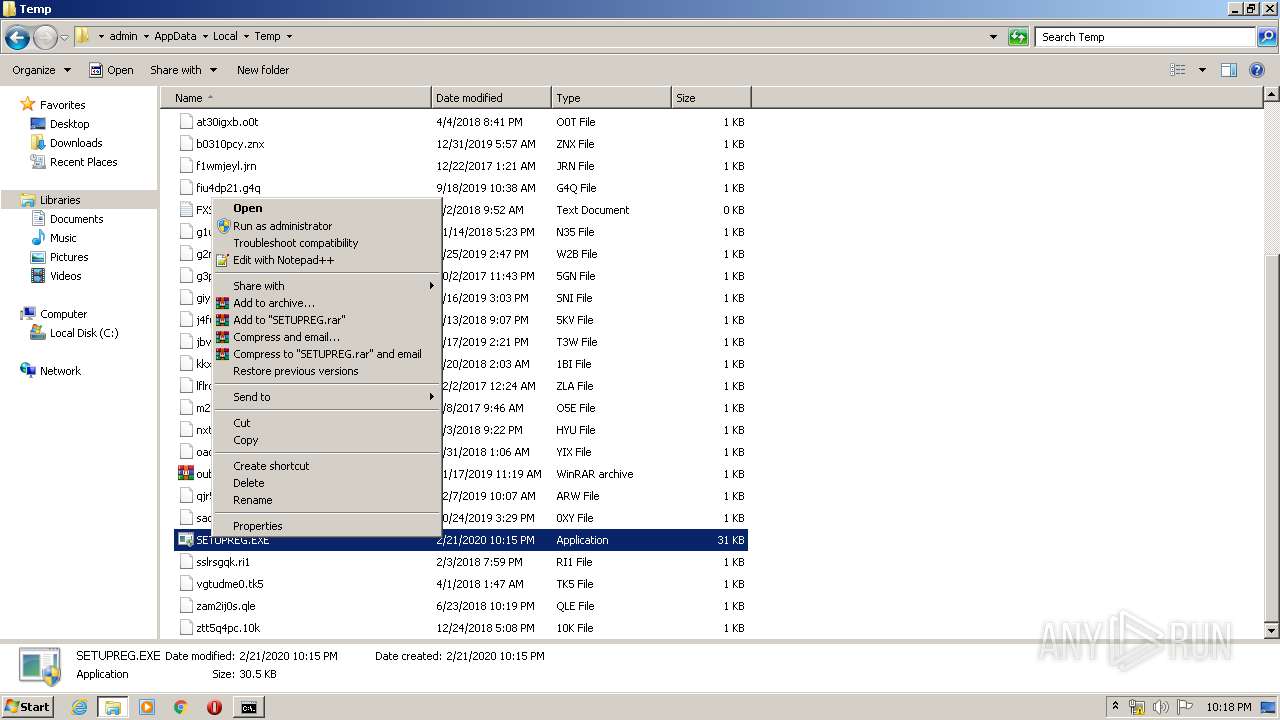
Manual execution by user
- cmd.exe (PID: 340)
- explorer.exe (PID: 3344)
- SETUPREG.EXE (PID: 3860)
- notepad++.exe (PID: 3892)
Reads Internet Cache Settings
- iexplore.exe (PID: 3828)
- iexplore.exe (PID: 2400)
Changes internet zones settings
- iexplore.exe (PID: 2400)
Creates files in the user directory
- iexplore.exe (PID: 2400)
- iexplore.exe (PID: 3828)
Reads settings of System Certificates
- iexplore.exe (PID: 3828)
- iexplore.exe (PID: 2400)
Reads internet explorer settings
- iexplore.exe (PID: 3828)
Changes settings of System certificates
- iexplore.exe (PID: 2400)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1998:10:01 16:55:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 15872 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17c0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Oct-1998 14:55:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Oct-1998 14:55:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00003C46 | 0x00003E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32792 |
.rdata | 0x00005000 | 0x000003AF | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91295 |
.data | 0x00006000 | 0x00004088 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.21721 |
.idata | 0x0000B000 | 0x00000476 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0337 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
76
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
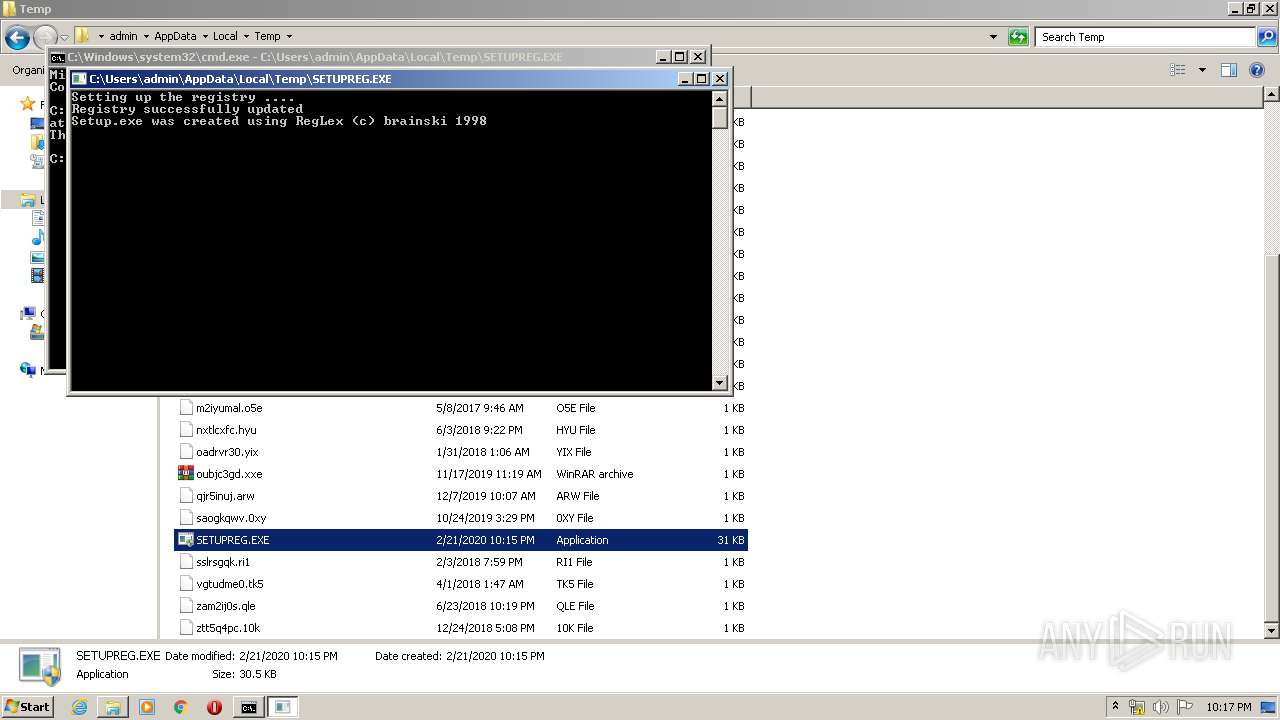
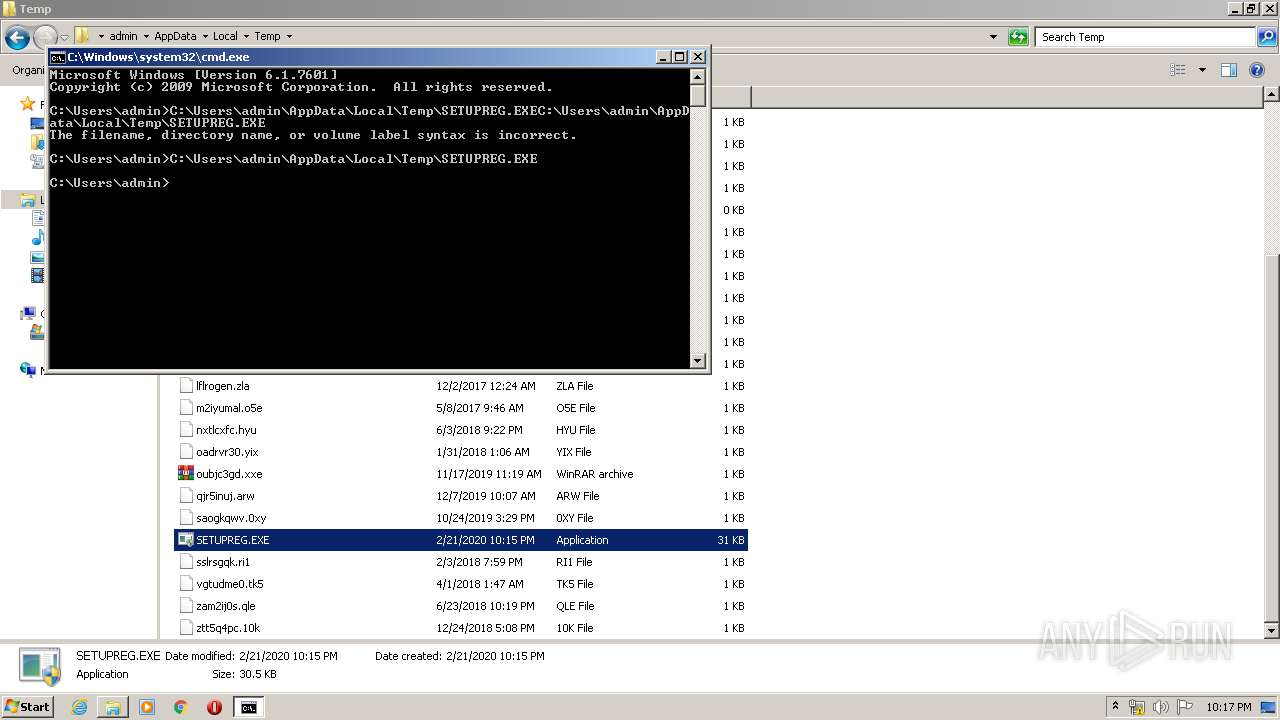
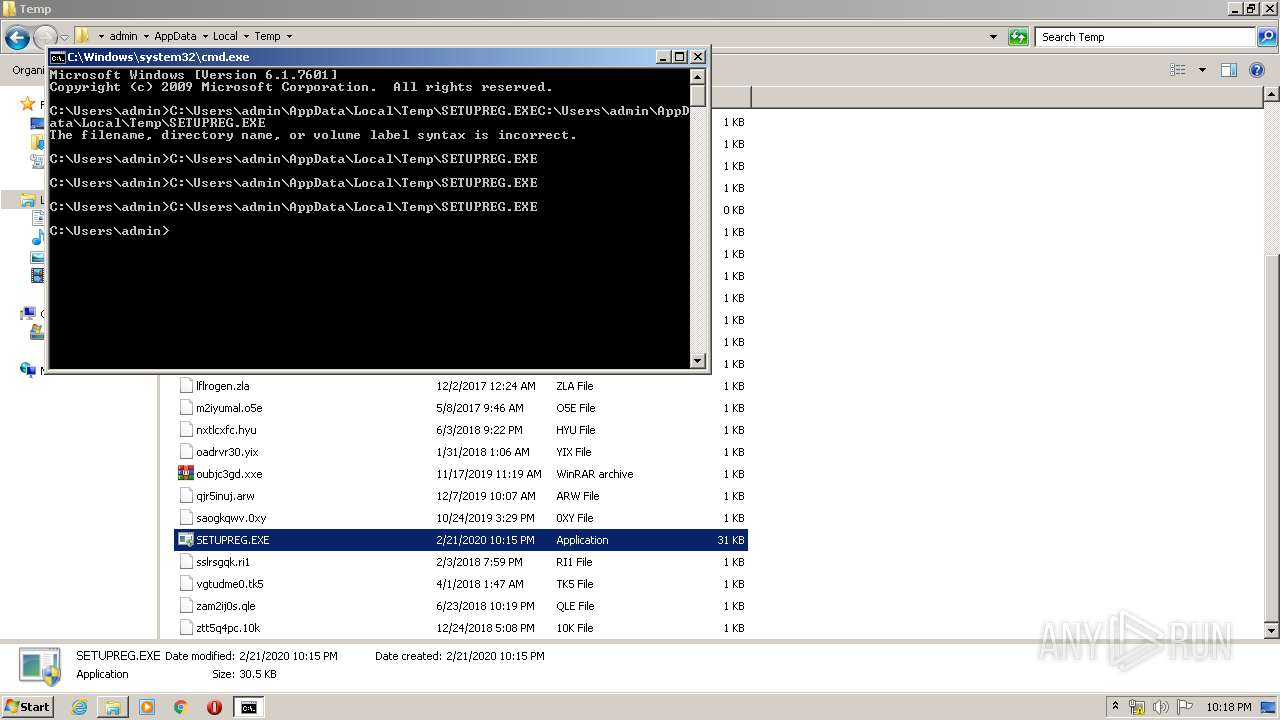
| 944 | "C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE" | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE" | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
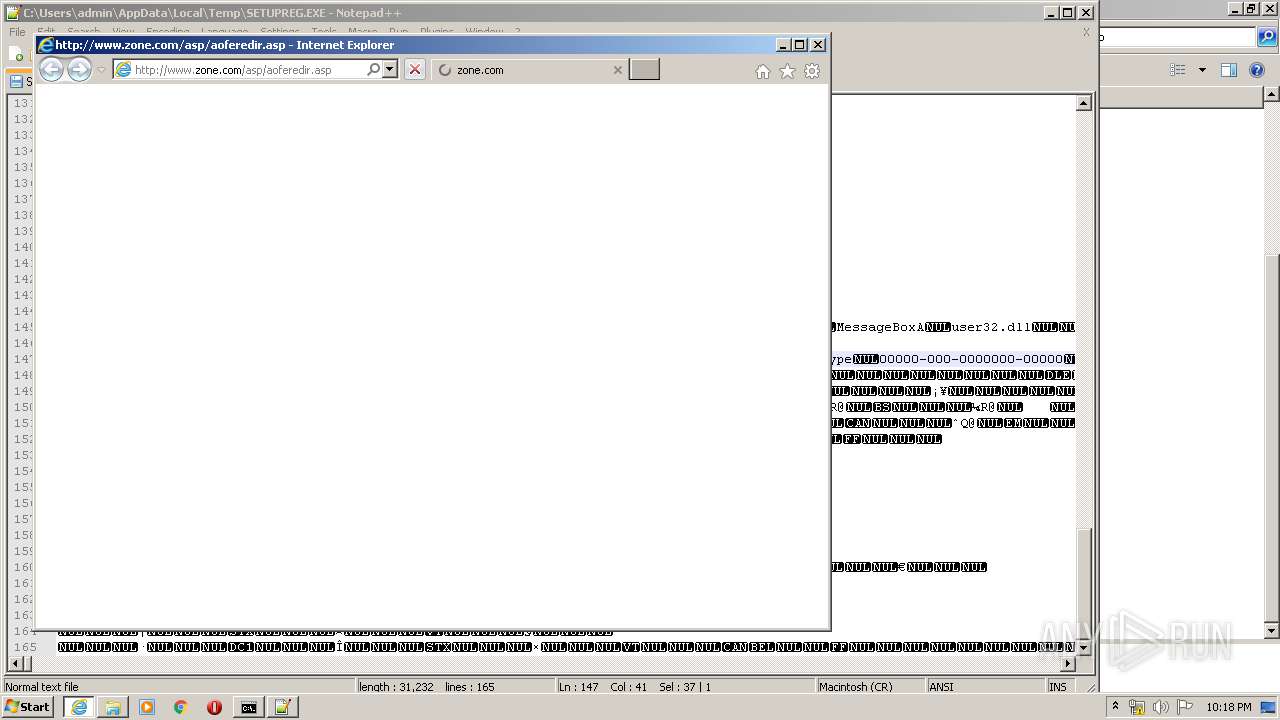
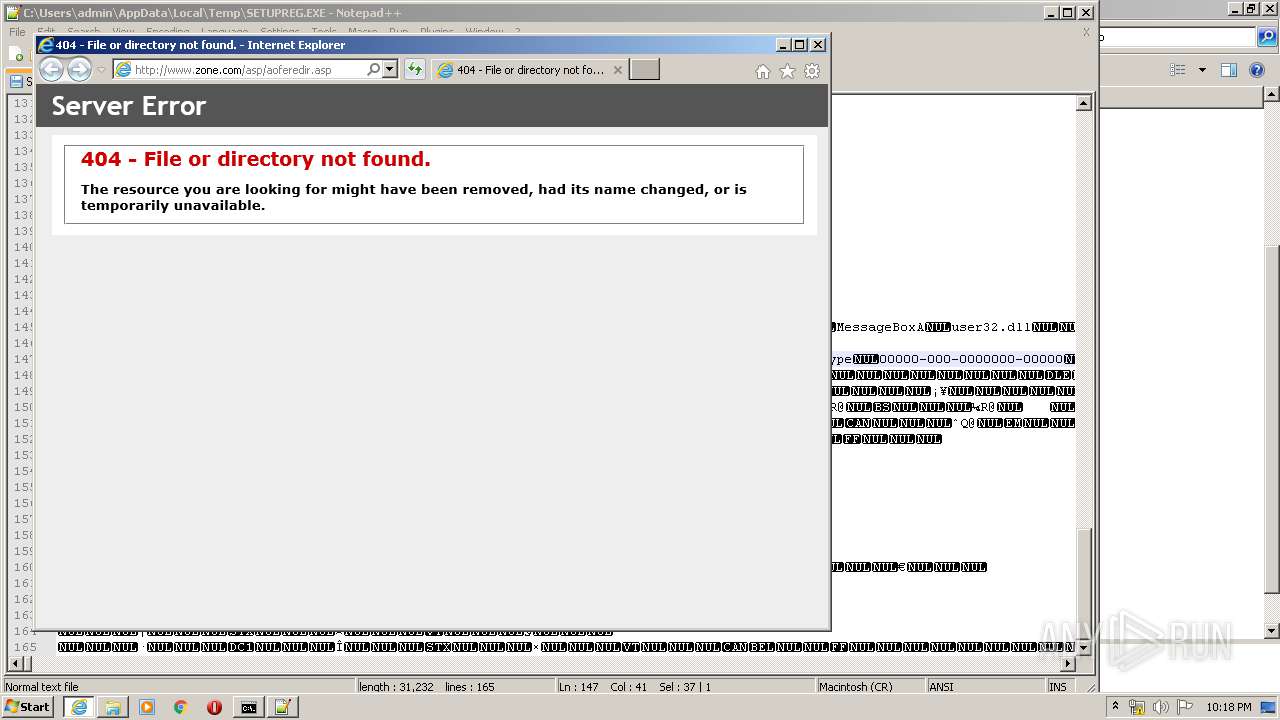
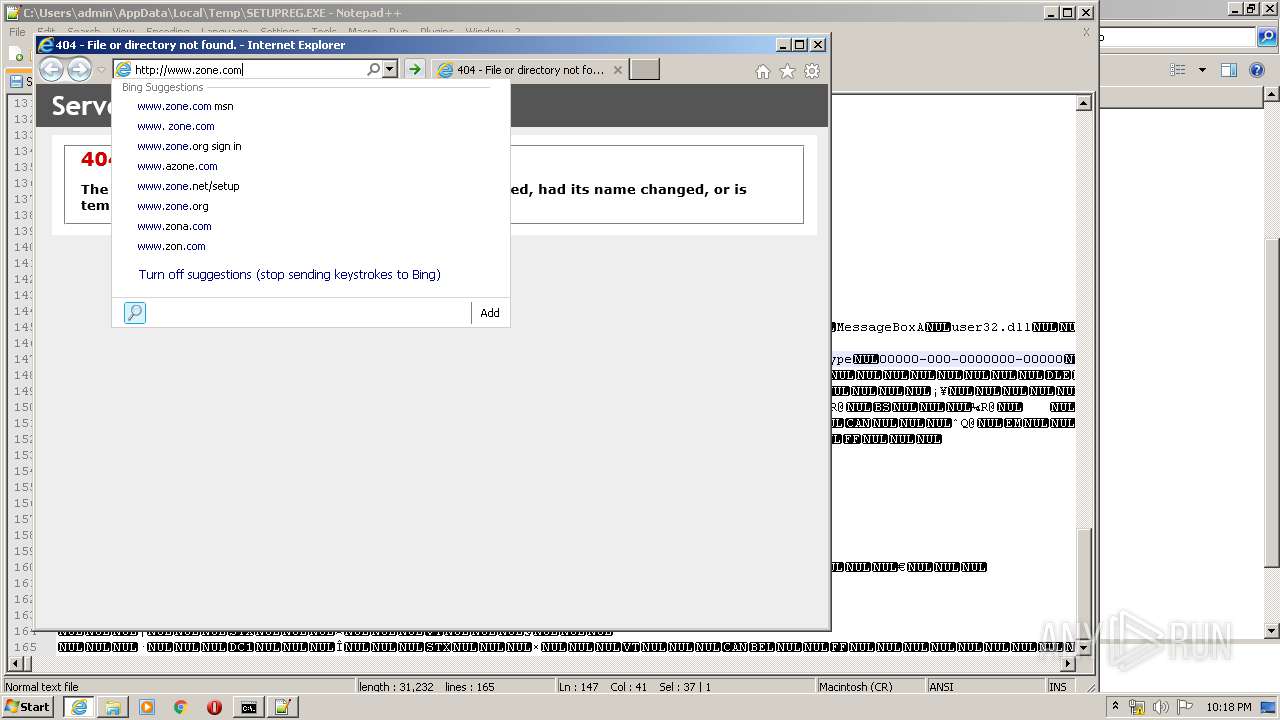
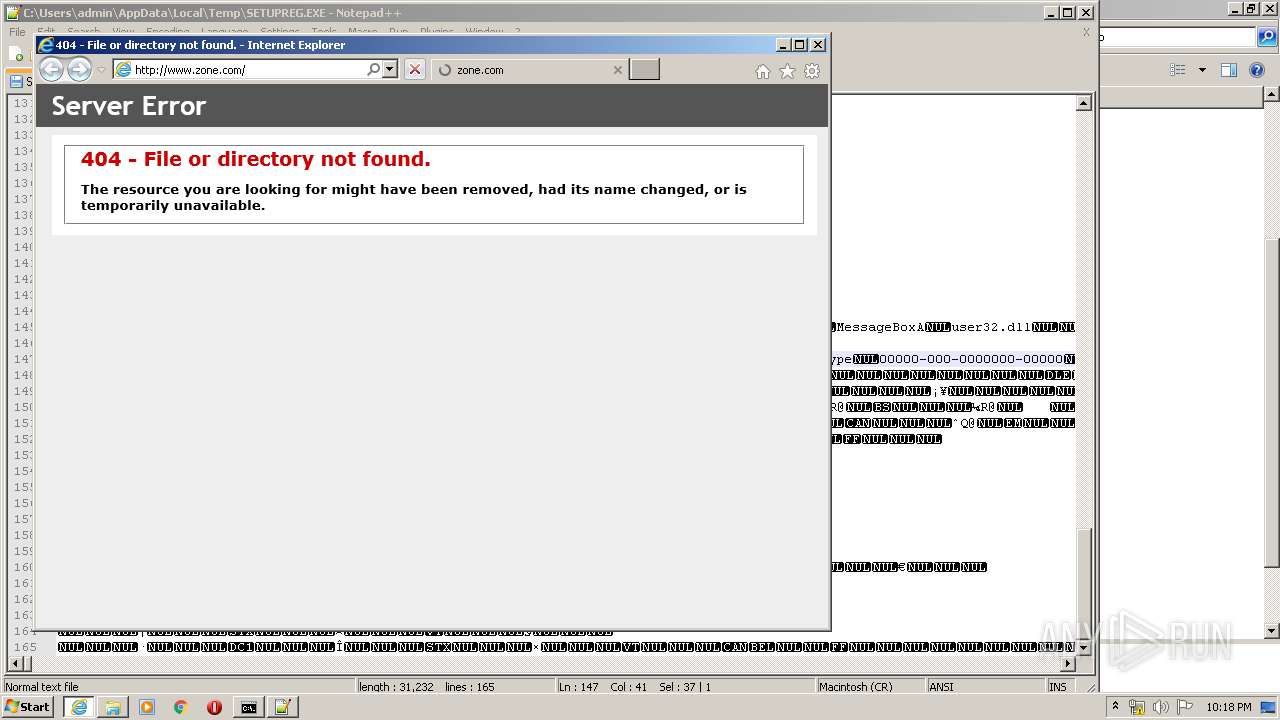
| 2400 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.zone.com/asp/aoferedir.asp | C:\Program Files\Internet Explorer\iexplore.exe | notepad++.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE" | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE" | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3184 | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | C:\Users\admin\AppData\Local\Temp\SETUPREG.EXE | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
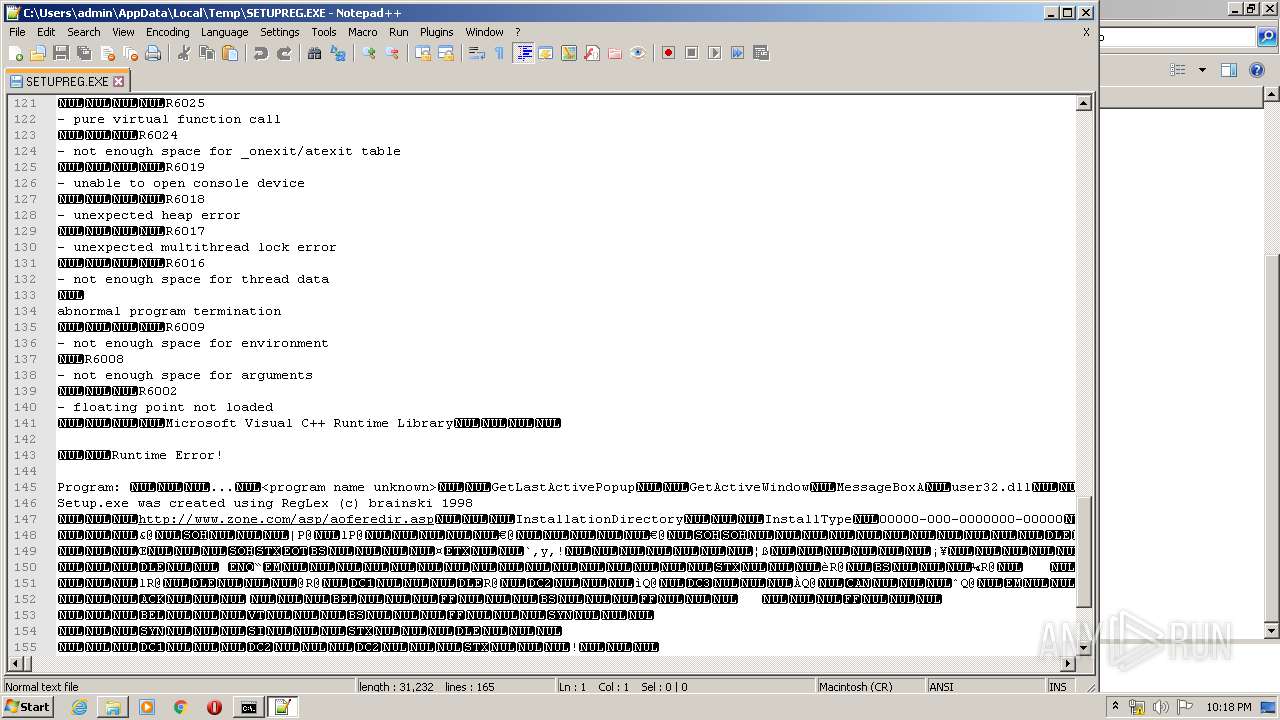
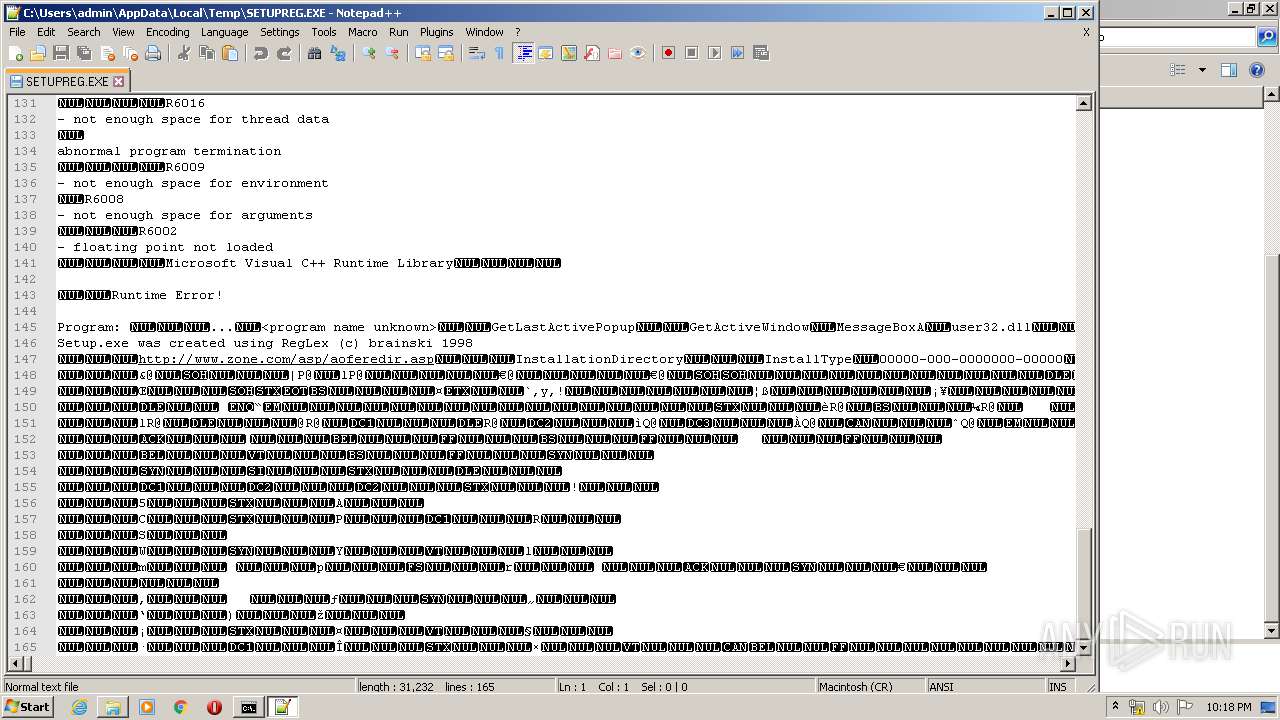
| 3344 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
Total events
6 731
Read events
1 212
Write events
3 803
Delete events
1 716
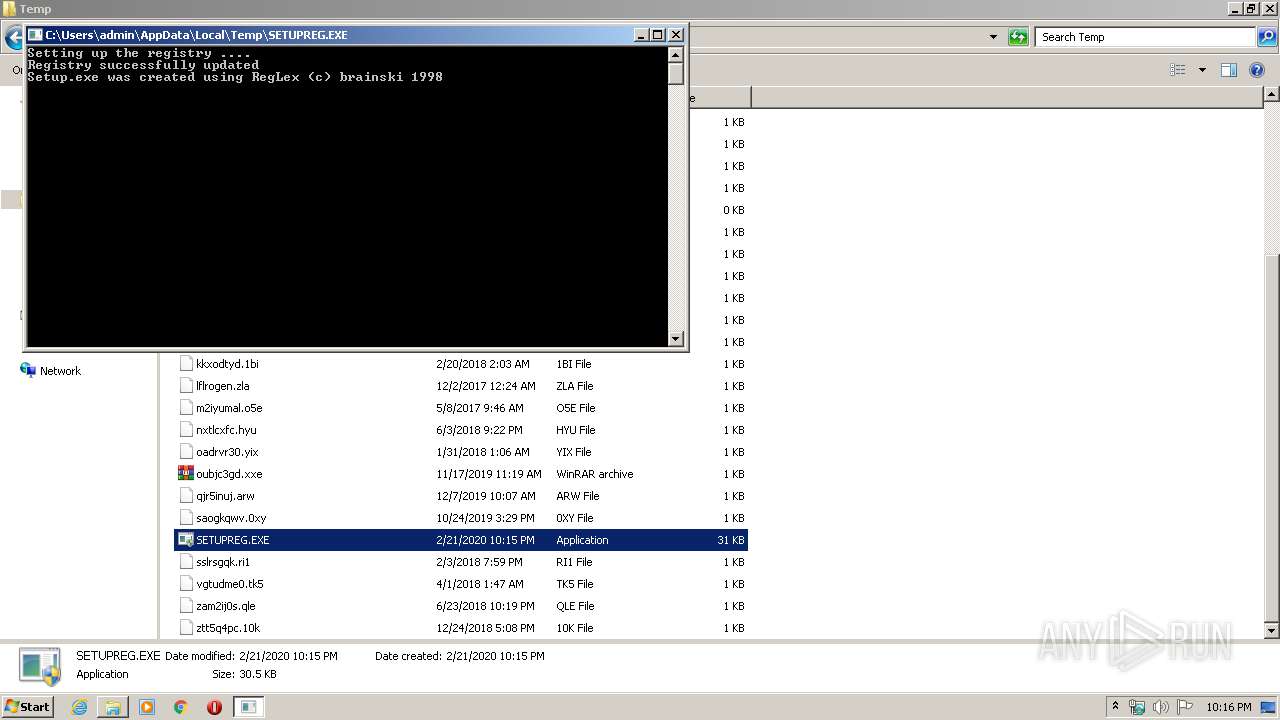
Modification events
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | Zone |
Value: http://www.zone.com/asp/aeepredir.asp | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | Launched |
Value: 1 | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | PID |
Value: 83622-442-7926675-57956 | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | EXE Path |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | VersionType |
Value: RetailVersion | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | InstalledGroup |
Value: 3 | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Games\Age of Empires Expansion\1.0 |
| Operation: | write | Name: | LangID |
Value: 9 | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectPlay\Applications\Age of Empires Expansion |
| Operation: | write | Name: | Guid |
Value: {8701C5C1-337B-11d2-839B-00609707F508} | |||
| (PID) Process: | (4020) SETUPREG.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectPlay\Applications\Age of Empires Expansion |
| Operation: | write | Name: | File |
Value: EmpiresX.Exe | |||
Executable files
0
Suspicious files
220
Text files
205
Unknown types
102
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\O0RFWST2.txt | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HYPF11M1.txt | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2787.tmp | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2788.tmp | — | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[3].xml | xml | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[2].xml | xml | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2KREP6BH.txt | text | |
MD5:— | SHA256:— | |||
| 3828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\A2C636GD.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
137
TCP/UDP connections
248
DNS requests
111
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp%2Faofer&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp%2Faofere&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp%2Faofe&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fas&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp%2Faoferedir.a&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 180 b | whitelisted |
3828 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fasp&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 172 b | whitelisted |
3828 | iexplore.exe | GET | 302 | 168.61.170.191:80 | http://zone.msn.com/ | US | html | 138 b | whitelisted |
3828 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 230 b | whitelisted |
3828 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fwww.zone.com%2Fa&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 200 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3828 | iexplore.exe | 104.215.95.187:80 | www.zone.com | Microsoft Corporation | US | whitelisted |
2400 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3828 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
3828 | iexplore.exe | 168.61.170.191:80 | zone.msn.com | Microsoft Corporation | US | whitelisted |
3828 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3828 | iexplore.exe | 168.61.170.191:443 | zone.msn.com | Microsoft Corporation | US | whitelisted |
3828 | iexplore.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3828 | iexplore.exe | 192.229.221.24:443 | s.aolcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.zone.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
zone.msn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
s.aolcdn.com |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|