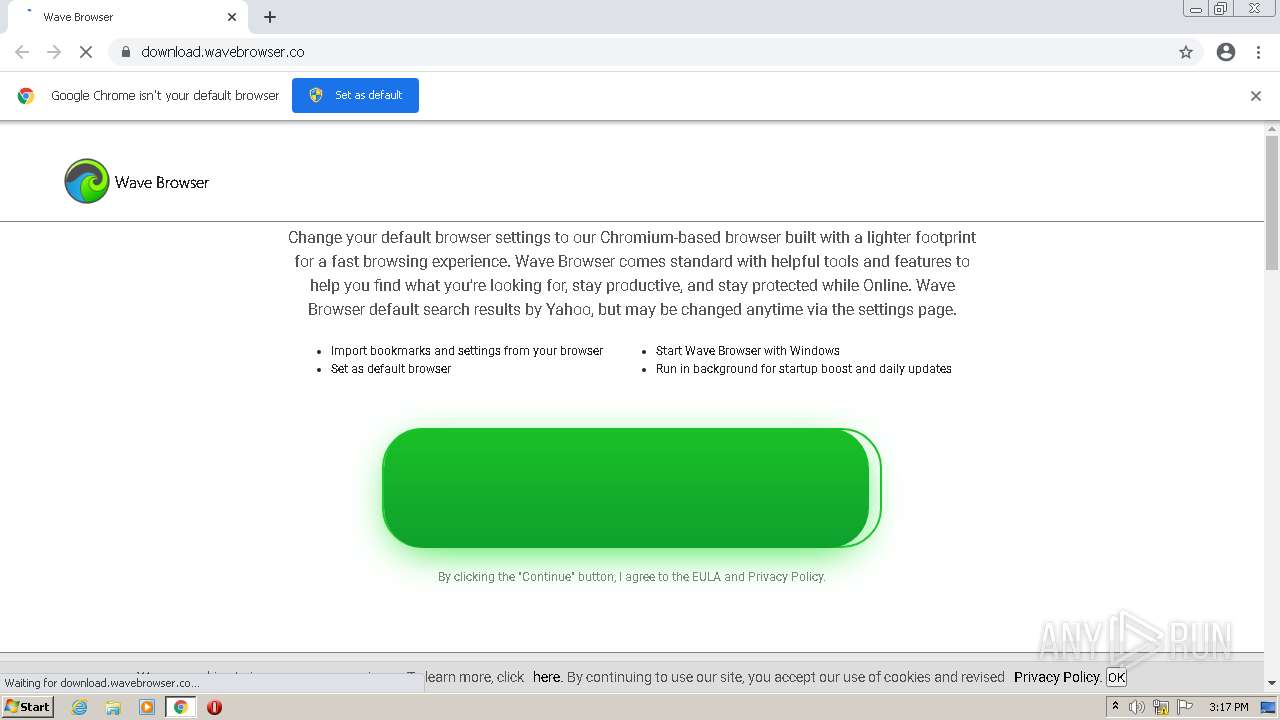
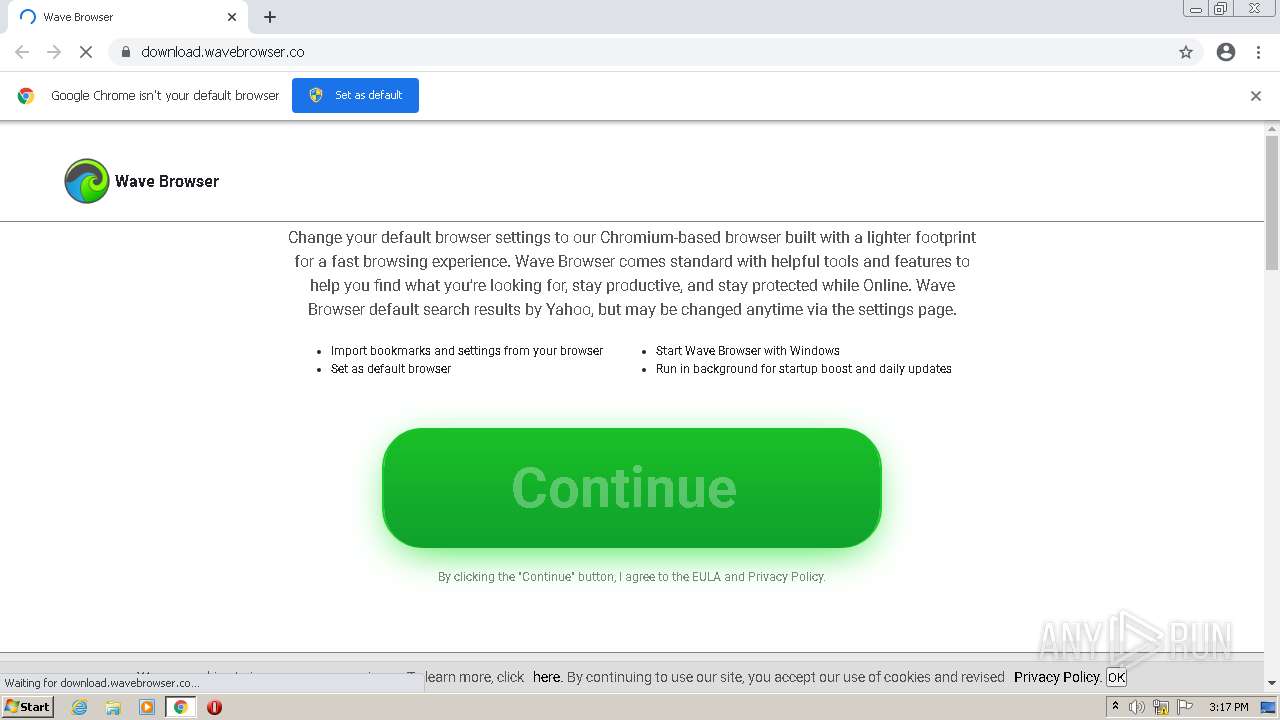
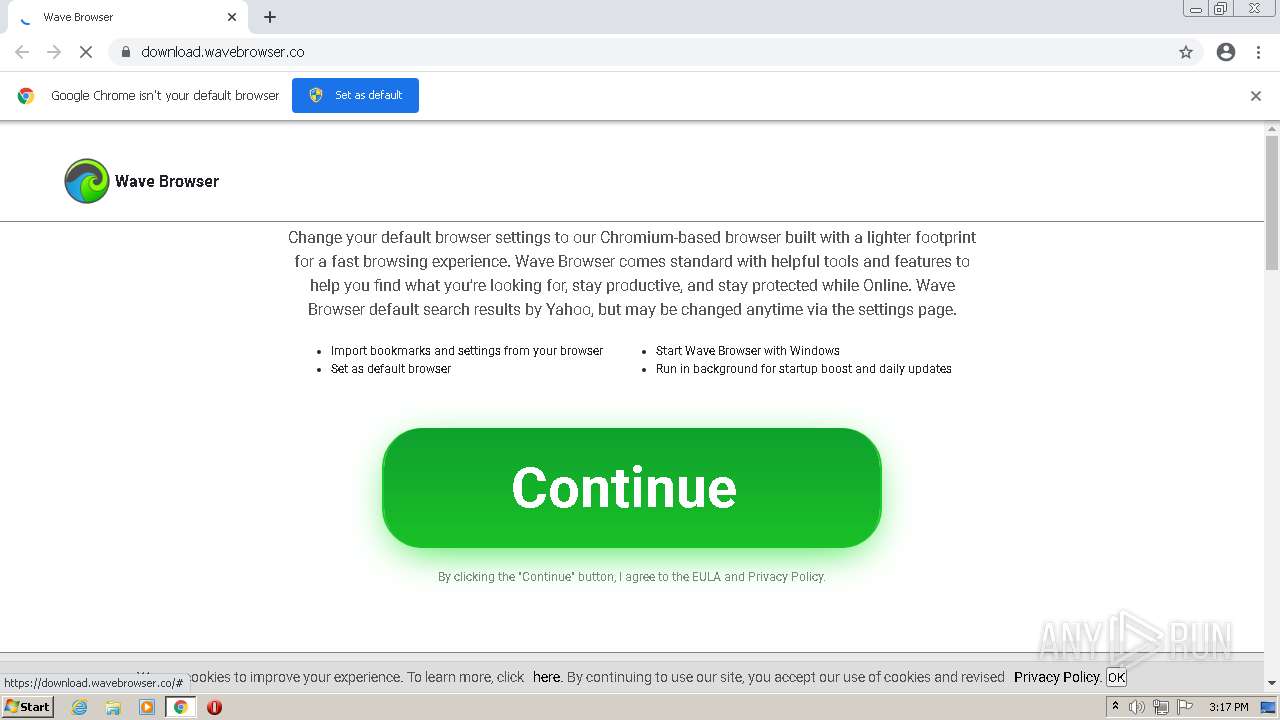
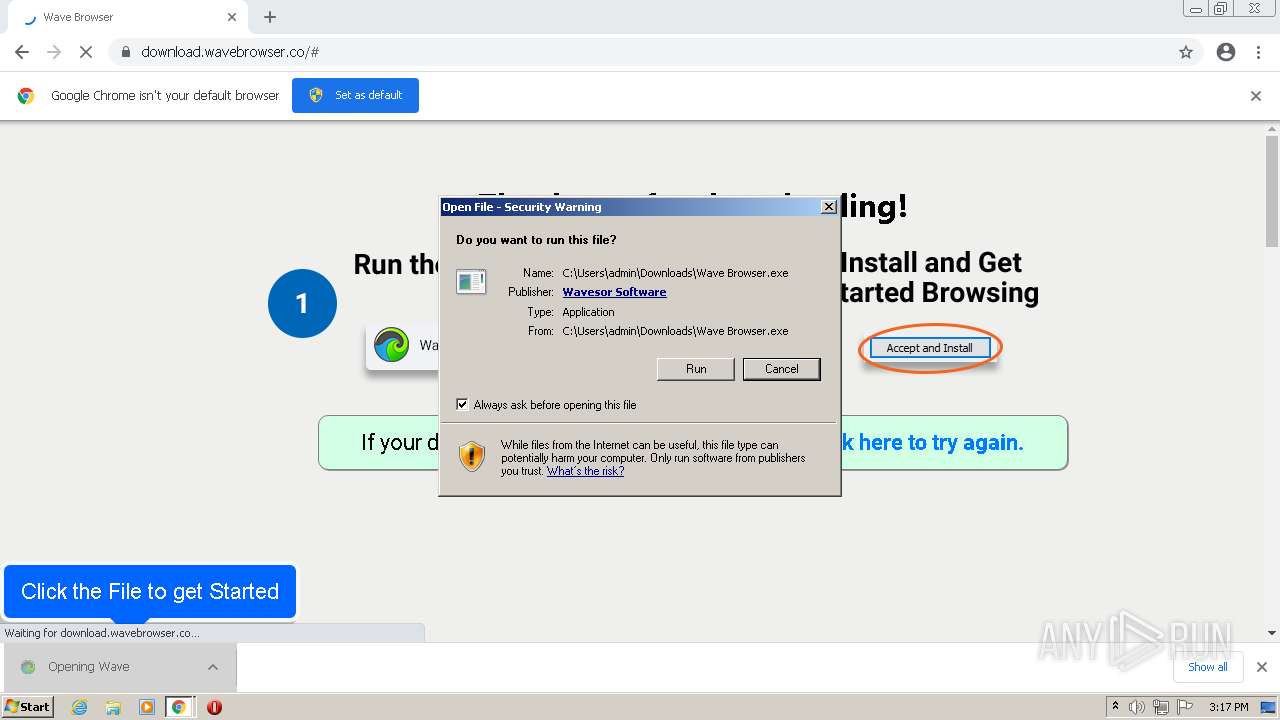
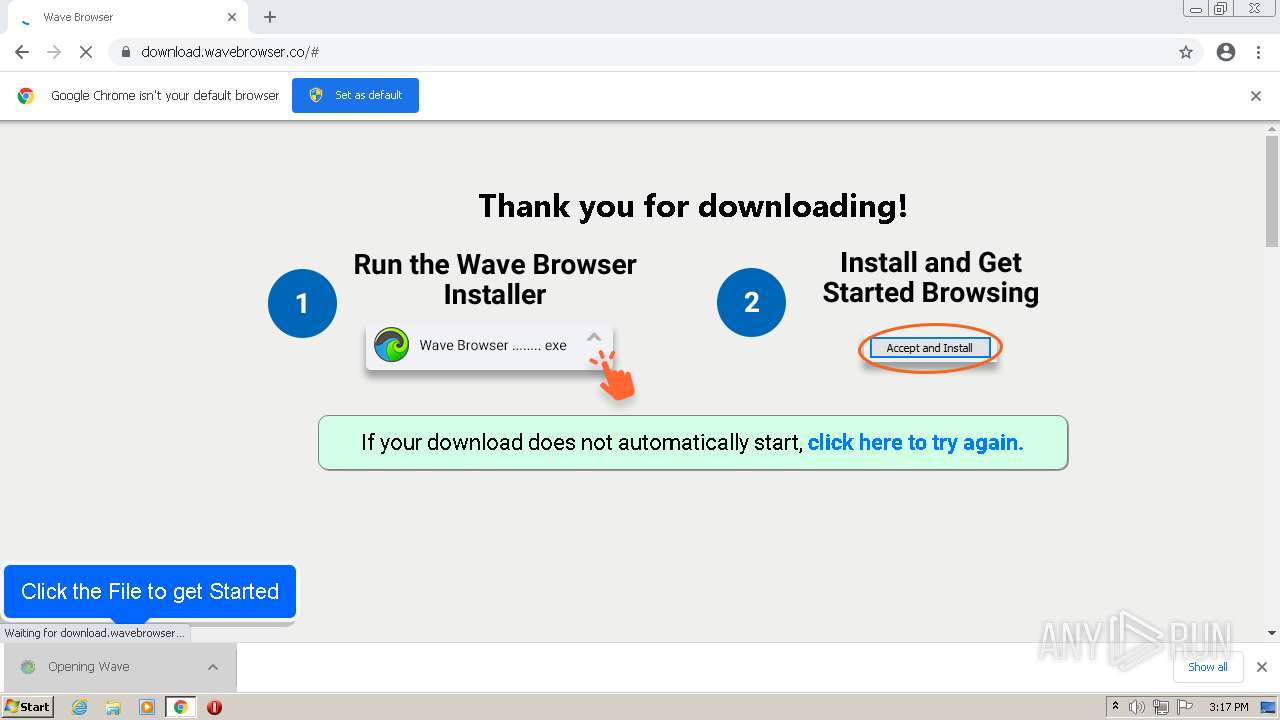
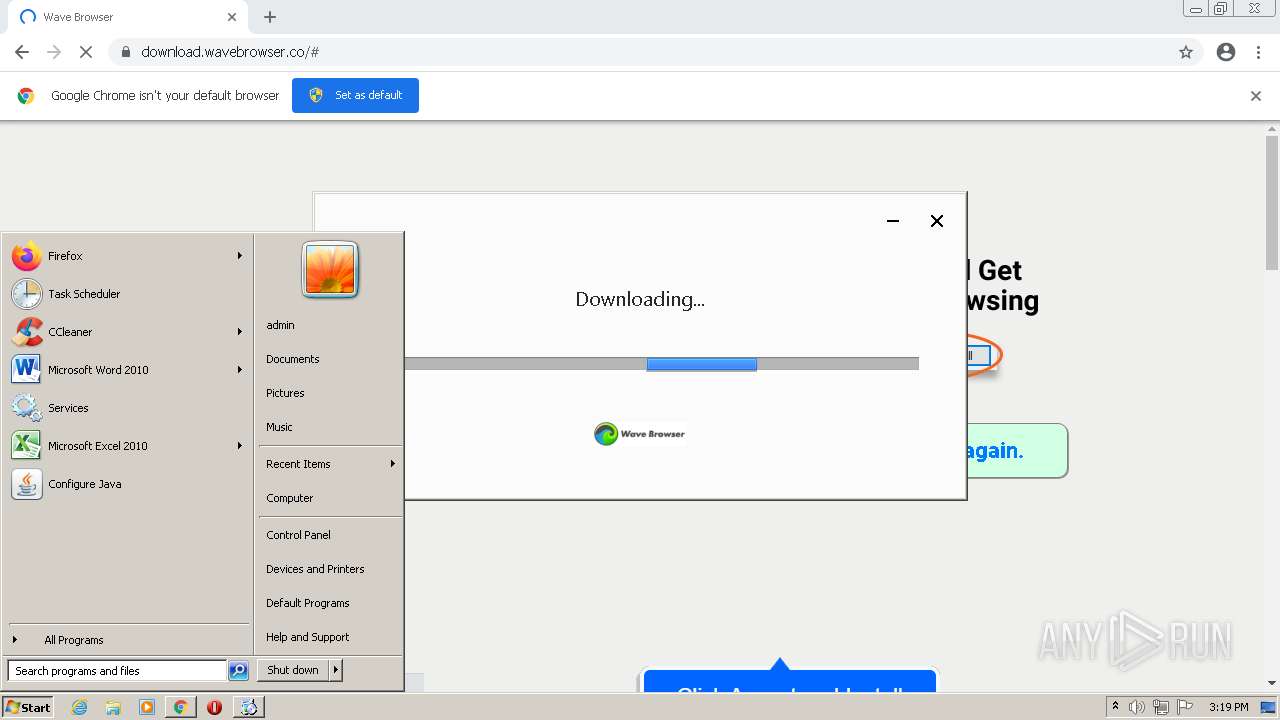
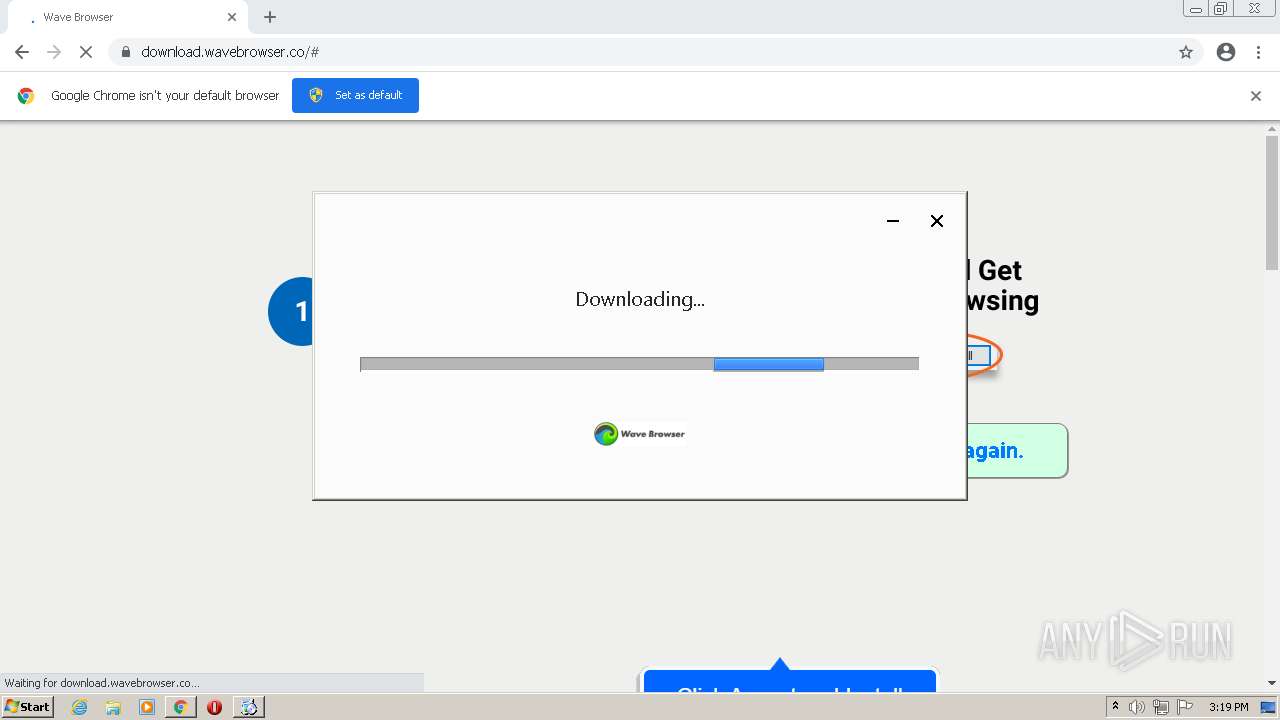
| URL: | https://download.wavebrowser.co |
| Full analysis: | https://app.any.run/tasks/bc6e0679-4645-4857-bc1c-cf4b23d453c3 |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2022, 15:16:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 61E192522F1D34A9C2A5E0368C30D0FA |
| SHA1: | AC7AE00D003D0AF992241D53A37E62DC8D379344 |
| SHA256: | 2687668269E855AD3C3BD27505DAD317BE4B6392D0C4575ACBA07A07D060F2D9 |
| SSDEEP: | 3:N8SElWZ3yKn:2SKVKn |
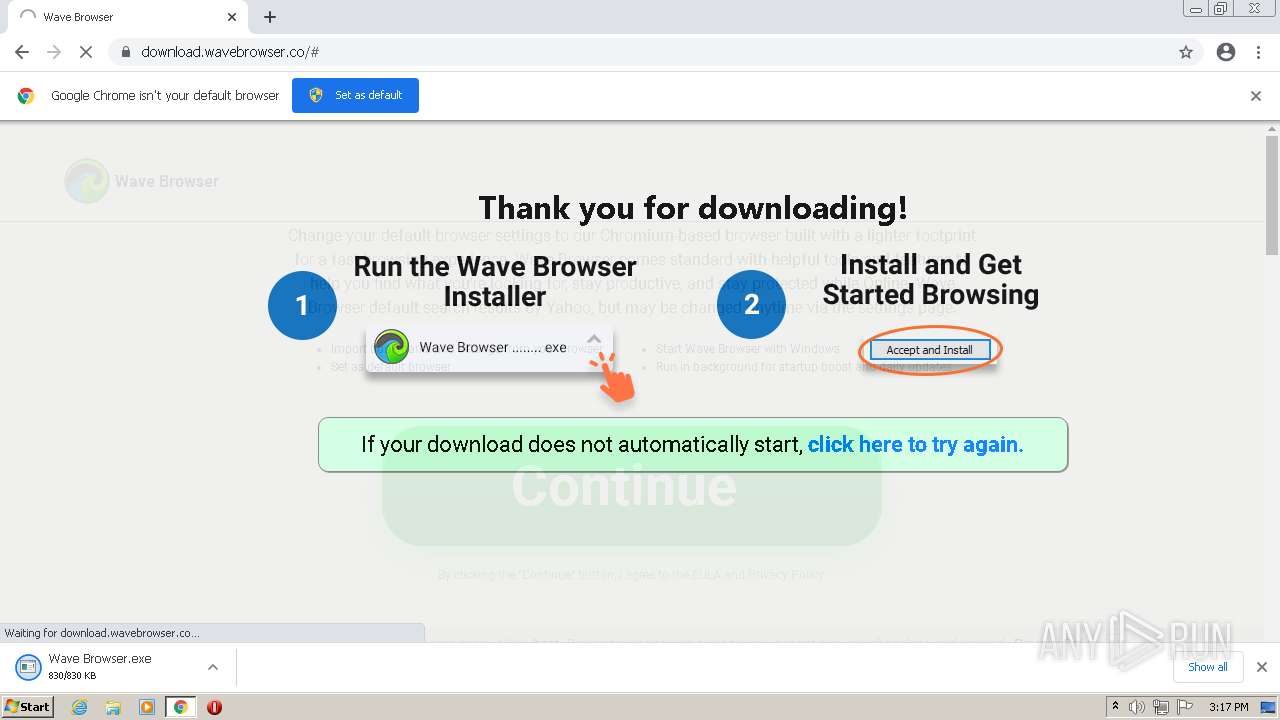
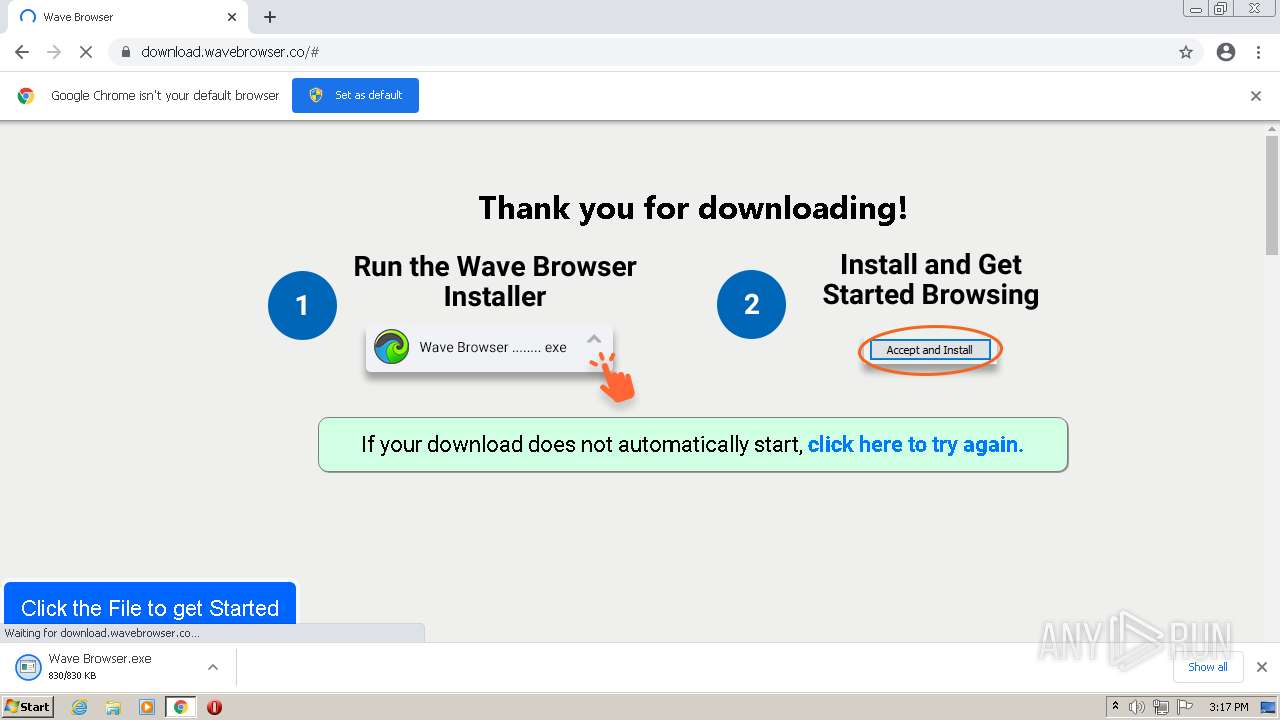
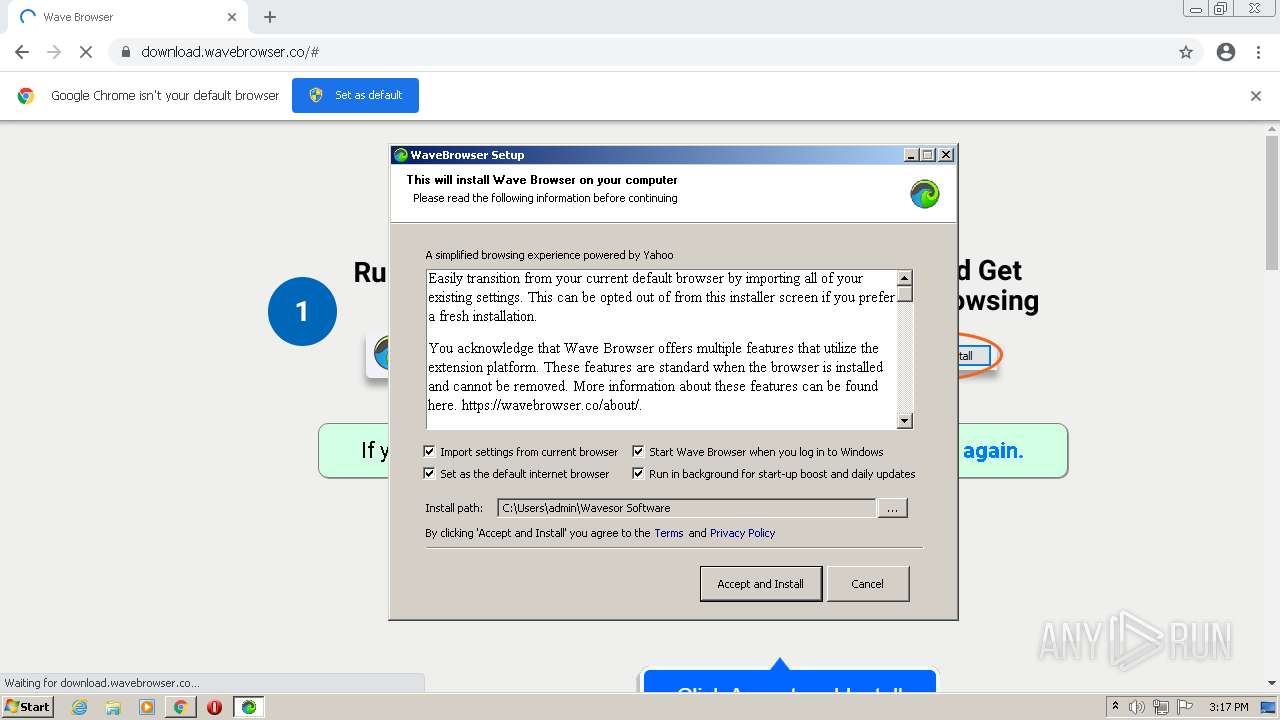
MALICIOUS
Drops executable file immediately after starts
- Wave Browser.exe (PID: 3540)
- SWUpdaterSetup.exe (PID: 2984)
- SWUpdater.exe (PID: 2116)
Changes the autorun value in the registry
- SWUpdater.exe (PID: 2116)
Loads the Task Scheduler COM API
- SWUpdater.exe (PID: 2116)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2928)
- Wave Browser.exe (PID: 3540)
- SWUpdaterSetup.exe (PID: 2984)
- SWUpdater.exe (PID: 2116)
Drops a file with a compile date too recent
- chrome.exe (PID: 2928)
- Wave Browser.exe (PID: 3540)
- SWUpdaterSetup.exe (PID: 2984)
- SWUpdater.exe (PID: 2116)
Reads the computer name
- Wave Browser.exe (PID: 3540)
- SWUpdater.exe (PID: 2116)
- SWUpdater.exe (PID: 2908)
- SWUpdater.exe (PID: 2604)
- SWUpdater.exe (PID: 3968)
- SWUpdater.exe (PID: 3204)
Checks supported languages
- Wave Browser.exe (PID: 3540)
- SWUpdaterSetup.exe (PID: 2984)
- SWUpdater.exe (PID: 2116)
- SWUpdater.exe (PID: 2456)
- SWUpdater.exe (PID: 2908)
- SWUpdater.exe (PID: 2604)
- SWUpdater.exe (PID: 3968)
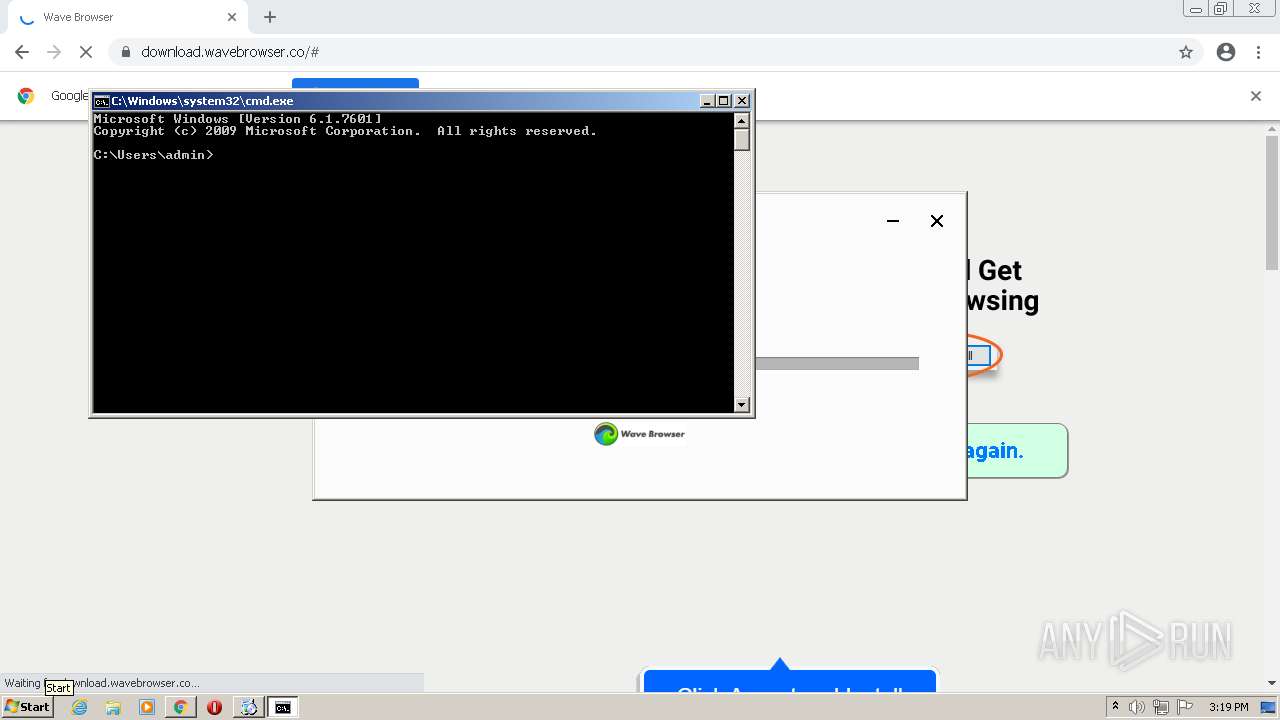
- cmd.exe (PID: 3704)
- SWUpdater.exe (PID: 3204)
Drops a file that was compiled in debug mode
- Wave Browser.exe (PID: 3540)
- SWUpdaterSetup.exe (PID: 2984)
- SWUpdater.exe (PID: 2116)
Starts itself from another location
- SWUpdater.exe (PID: 2116)
Creates/Modifies COM task schedule object
- SWUpdater.exe (PID: 2456)
Executed via COM
- SWUpdater.exe (PID: 3968)
Application launched itself
- SWUpdater.exe (PID: 3968)
INFO
Application launched itself
- chrome.exe (PID: 2928)
Checks supported languages
- chrome.exe (PID: 2928)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 692)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 836)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 1228)
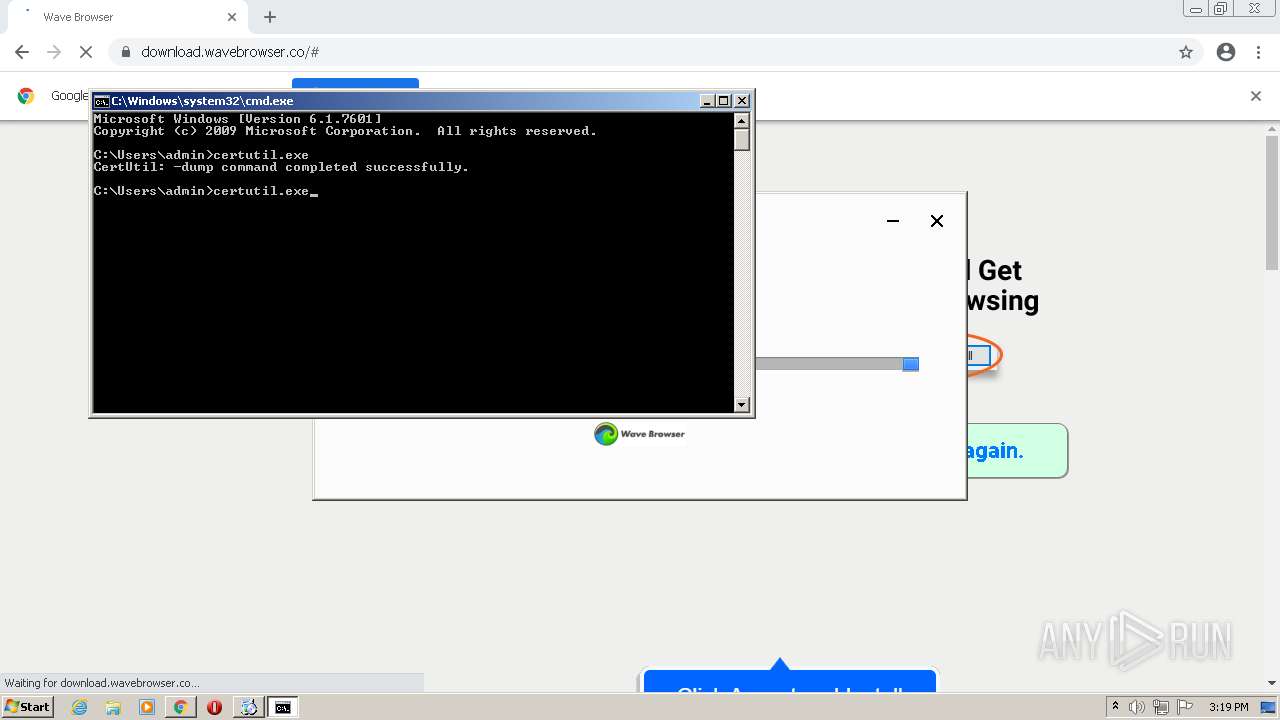
- certutil.exe (PID: 3664)
- certutil.exe (PID: 1772)
- certutil.exe (PID: 124)
- certutil.exe (PID: 2320)
- certutil.exe (PID: 1060)
- certutil.exe (PID: 2644)
Reads the hosts file
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3072)
Reads the computer name
- chrome.exe (PID: 2928)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 1228)
- certutil.exe (PID: 3664)
- certutil.exe (PID: 2320)
- certutil.exe (PID: 124)
- certutil.exe (PID: 1060)
- certutil.exe (PID: 2644)
Reads settings of System Certificates
- chrome.exe (PID: 3072)
- chrome.exe (PID: 2928)
- Wave Browser.exe (PID: 3540)
- SWUpdater.exe (PID: 3968)
- SWUpdater.exe (PID: 2908)
- SWUpdater.exe (PID: 3204)
Checks Windows Trust Settings
- chrome.exe (PID: 2928)
- Wave Browser.exe (PID: 3540)
Reads the date of Windows installation
- chrome.exe (PID: 1228)
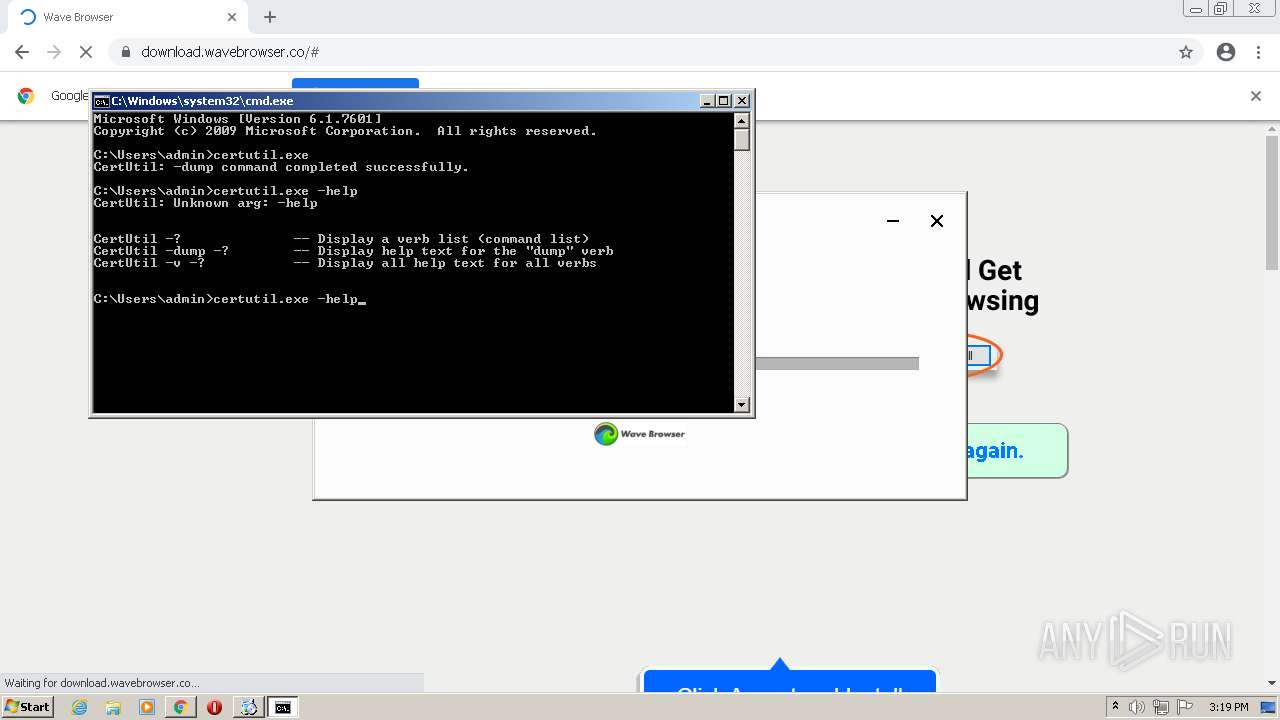
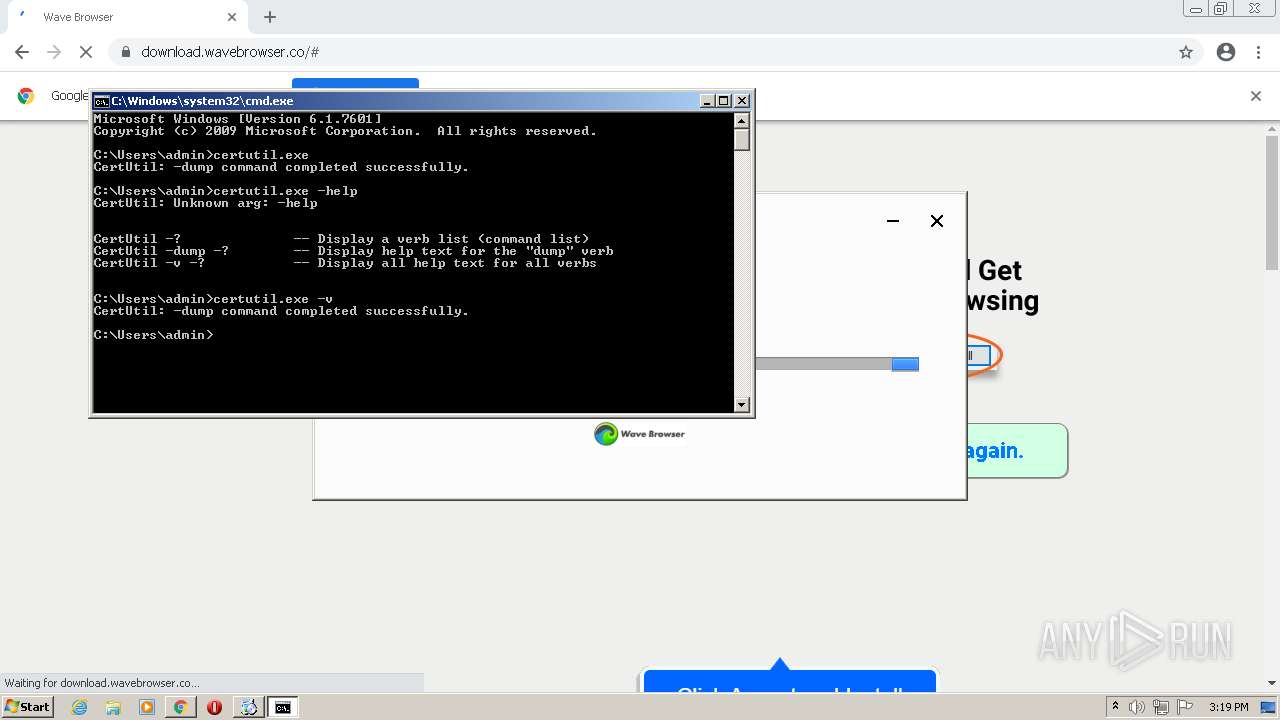
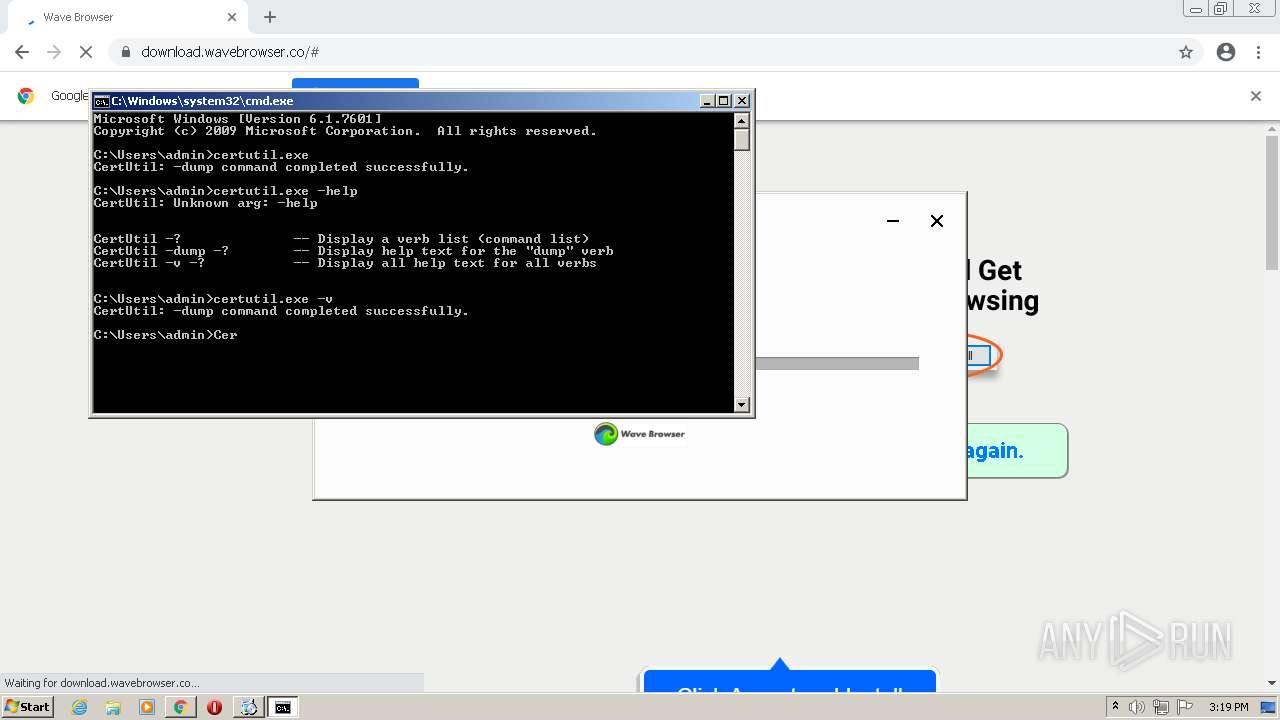
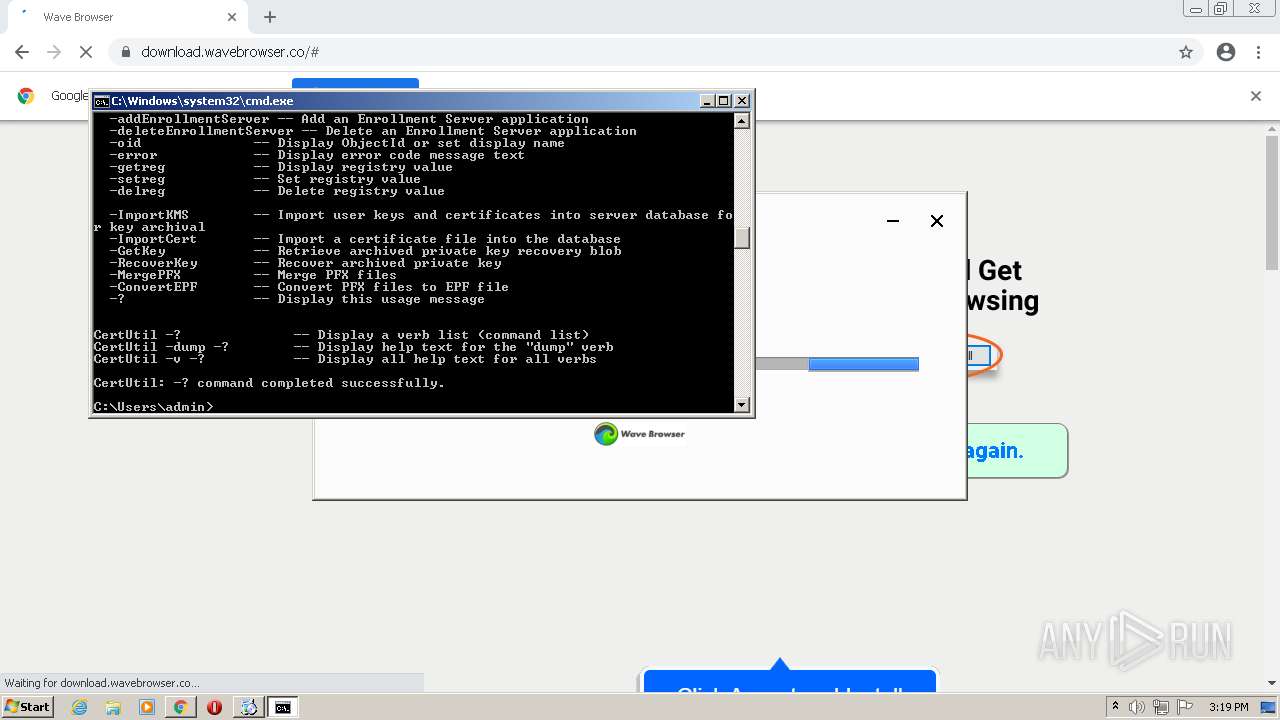
Manual execution by user
- cmd.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
32
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
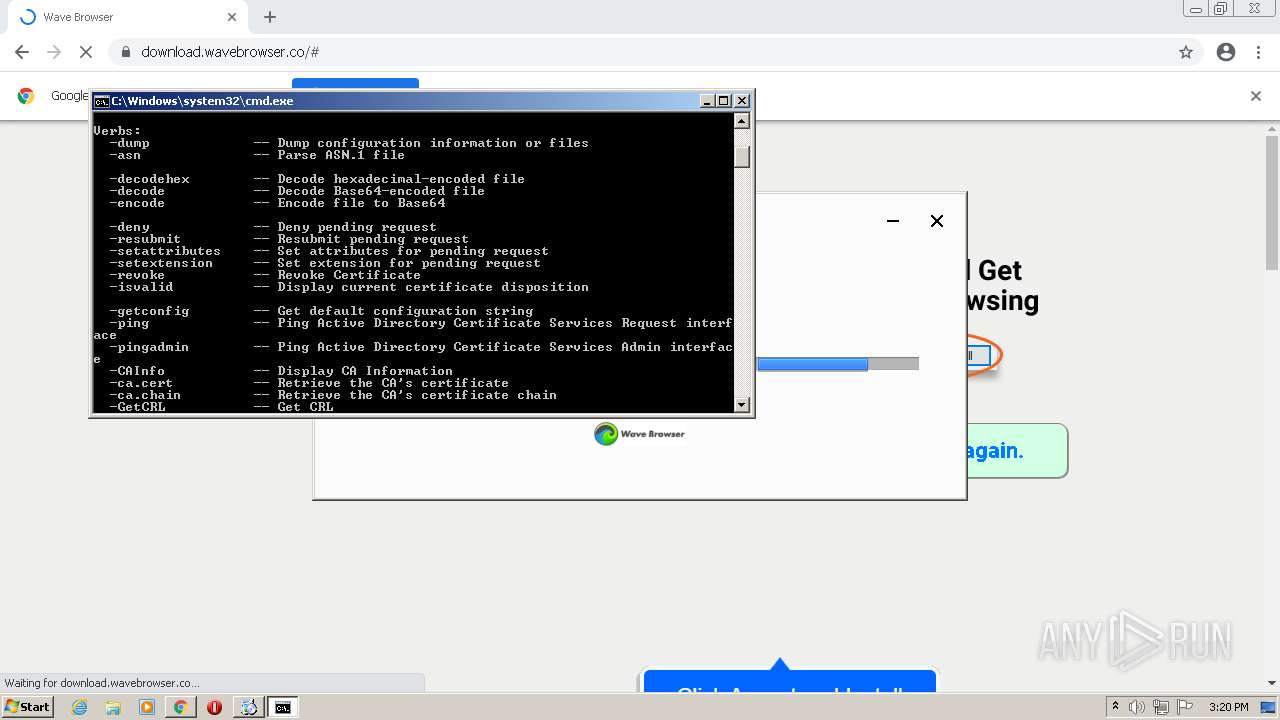
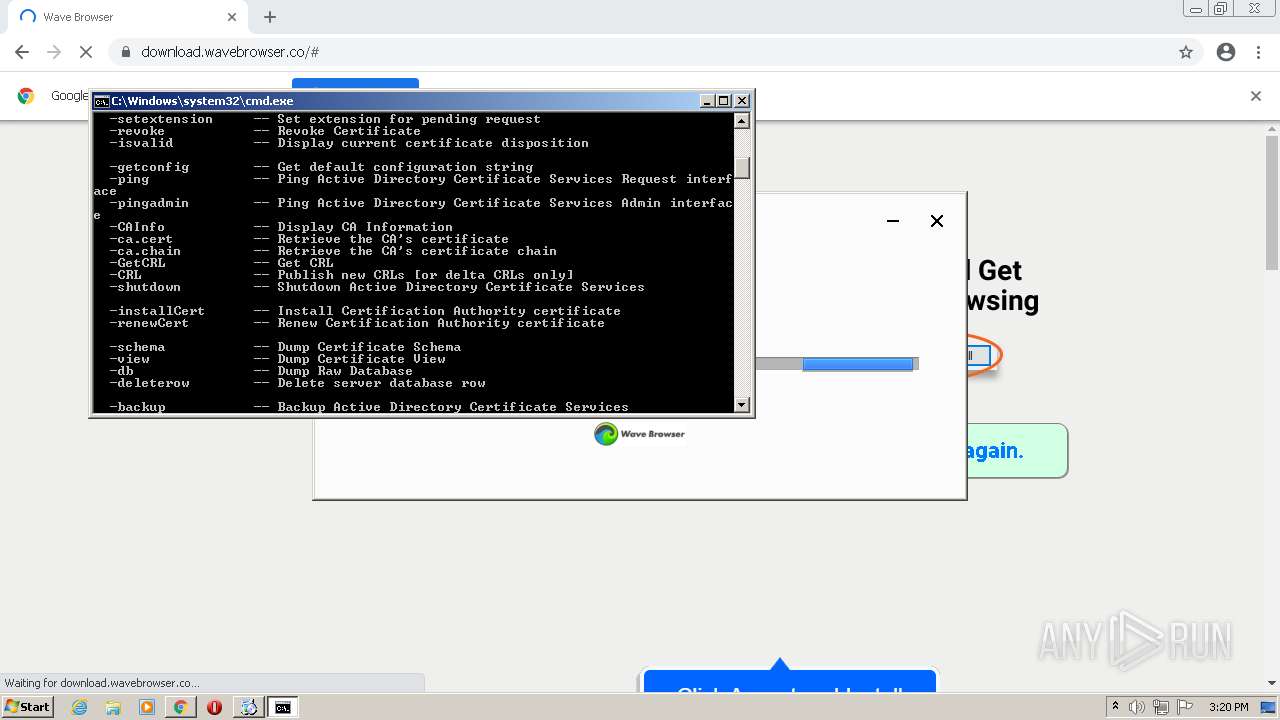
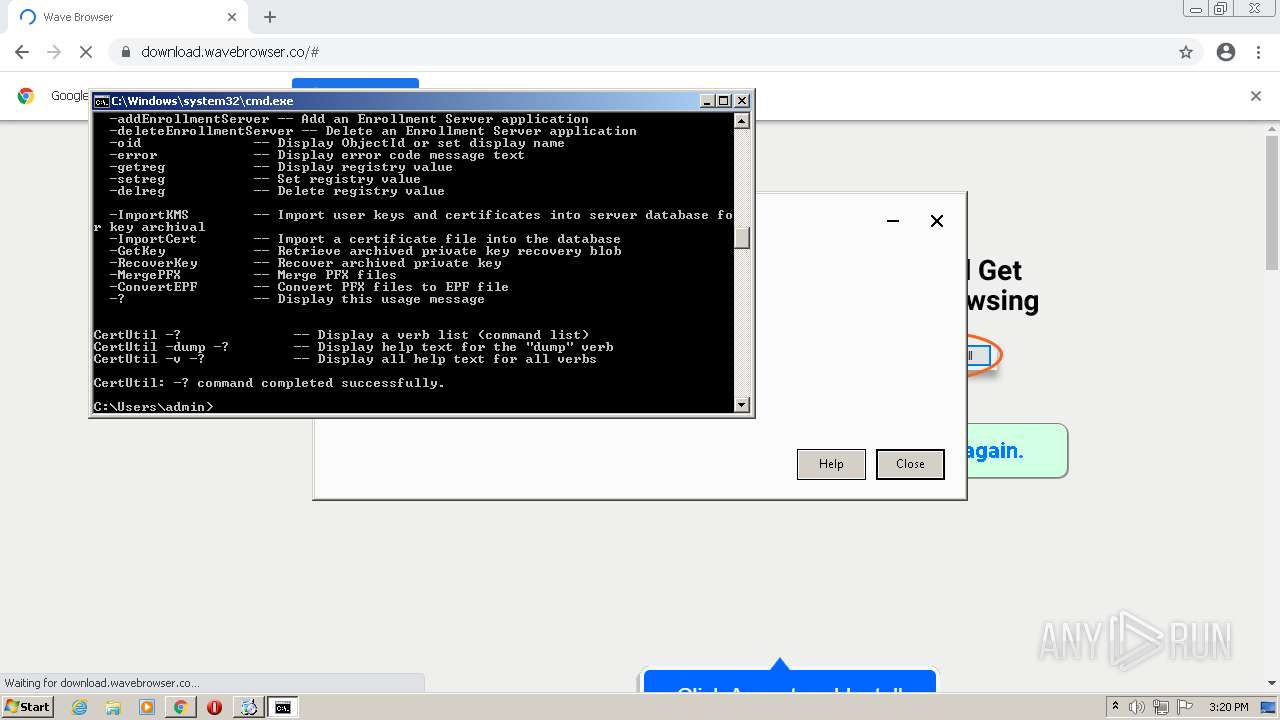
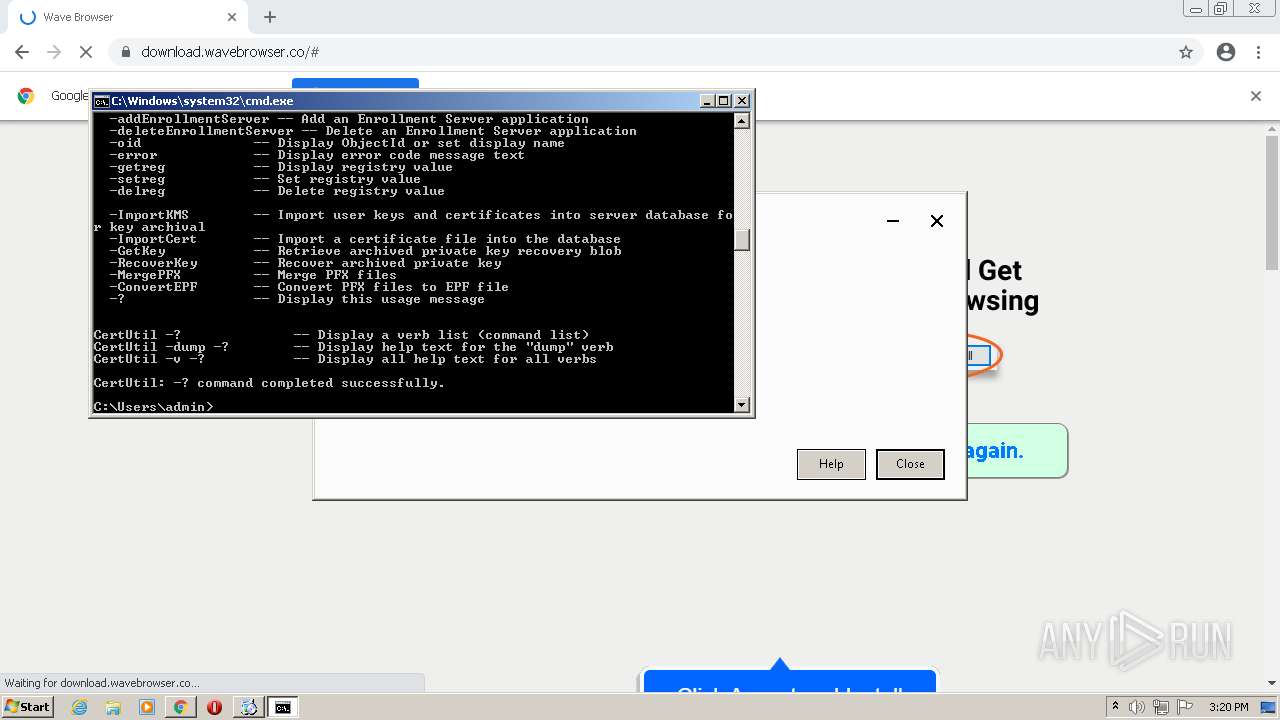
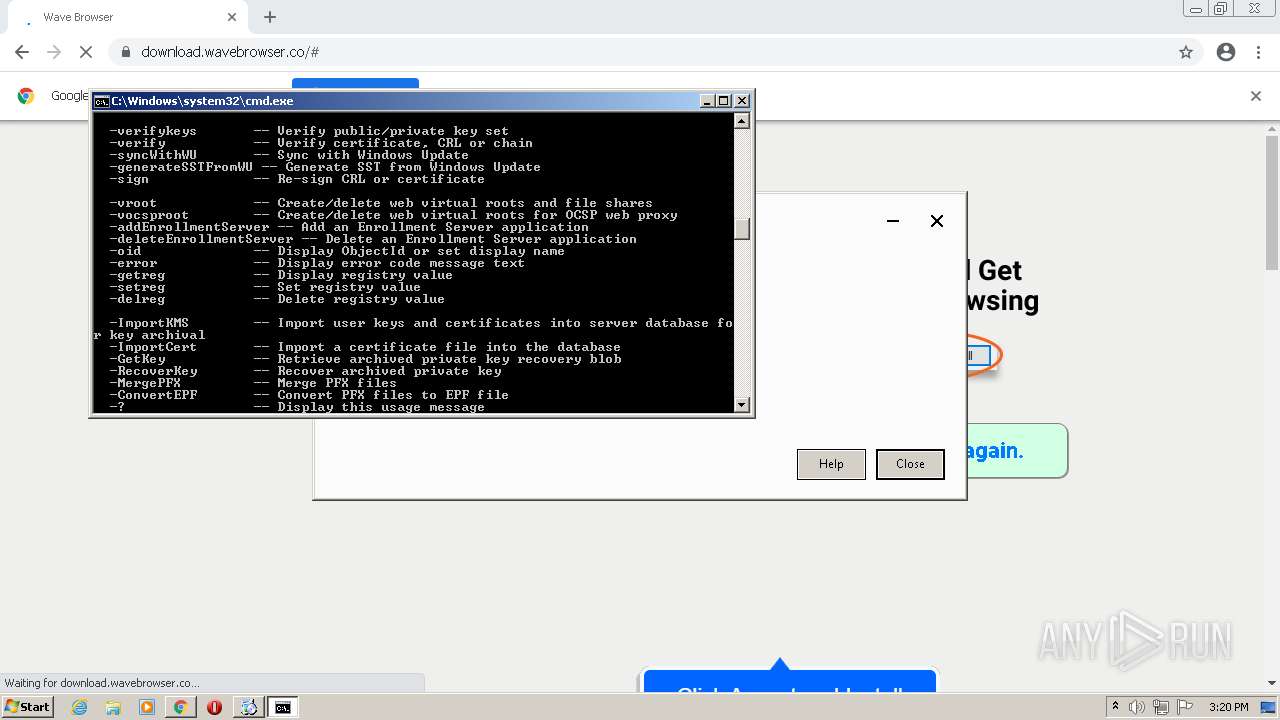
| 124 | CertUtil -? | C:\Windows\system32\certutil.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) | ||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3092 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1060 | CertUtil -hashfile "C:\Users\admin\Downloads\Wave Browser.exe" | C:\Windows\system32\certutil.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) | ||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1772 | certutil.exe -help | C:\Windows\system32\certutil.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 1 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) | ||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2116 | C:\Users\admin\AppData\Local\Temp\GUMEBFC.tmp\SWUpdater.exe /install "bundlename=WaveBrowser&appguid={EB149AD2-CE4E-4F51-B7FC-A149FAA4CCAF}&appname=WaveBrowser&needsadmin=False&lang=en&usagestats=0" | C:\Users\admin\AppData\Local\Temp\GUMEBFC.tmp\SWUpdater.exe | SWUpdaterSetup.exe | |
User: admin Company: Wavesor Software Integrity Level: MEDIUM Description: Wavesor SWUpdater Exit code: 0 Version: 1.3.115.0 | ||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1068,615892495701238281,3210660442540457938,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
34
Suspicious files
28
Text files
81
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6202896C-B70.pma | — | |
MD5:— | SHA256:— | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\50e68a6c-0a3f-4634-9bac-2ea7372aeffd.tmp | text | |
MD5:— | SHA256:— | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF19361a.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF193917.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF193704.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
84
DNS requests
35
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | Wave Browser.exe | GET | 200 | 13.225.84.49:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3540 | Wave Browser.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3540 | Wave Browser.exe | GET | 200 | 13.225.84.68:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3540 | Wave Browser.exe | GET | 200 | 13.225.84.107:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAwyf2o8ebkQnWEshzIXrEo%3D | US | der | 471 b | whitelisted |
3540 | Wave Browser.exe | GET | 200 | 8.241.122.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ca81c767b4eab402 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3072 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
3072 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 35.169.87.173:443 | download.wavebrowser.co | Amazon.com, Inc. | US | unknown |
3072 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 142.250.185.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3072 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3072 | chrome.exe | 35.169.68.112:443 | api.wavebrowser.co | Amazon.com, Inc. | US | unknown |
3072 | chrome.exe | 142.250.186.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.184.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
download.wavebrowser.co |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
api.wavebrowser.co |
| suspicious |
safebrowsing.googleapis.com |
| whitelisted |
api.wavebrowserbase.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
884 | svchost.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
884 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
884 | svchost.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
884 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
884 | svchost.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
884 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
884 | svchost.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |