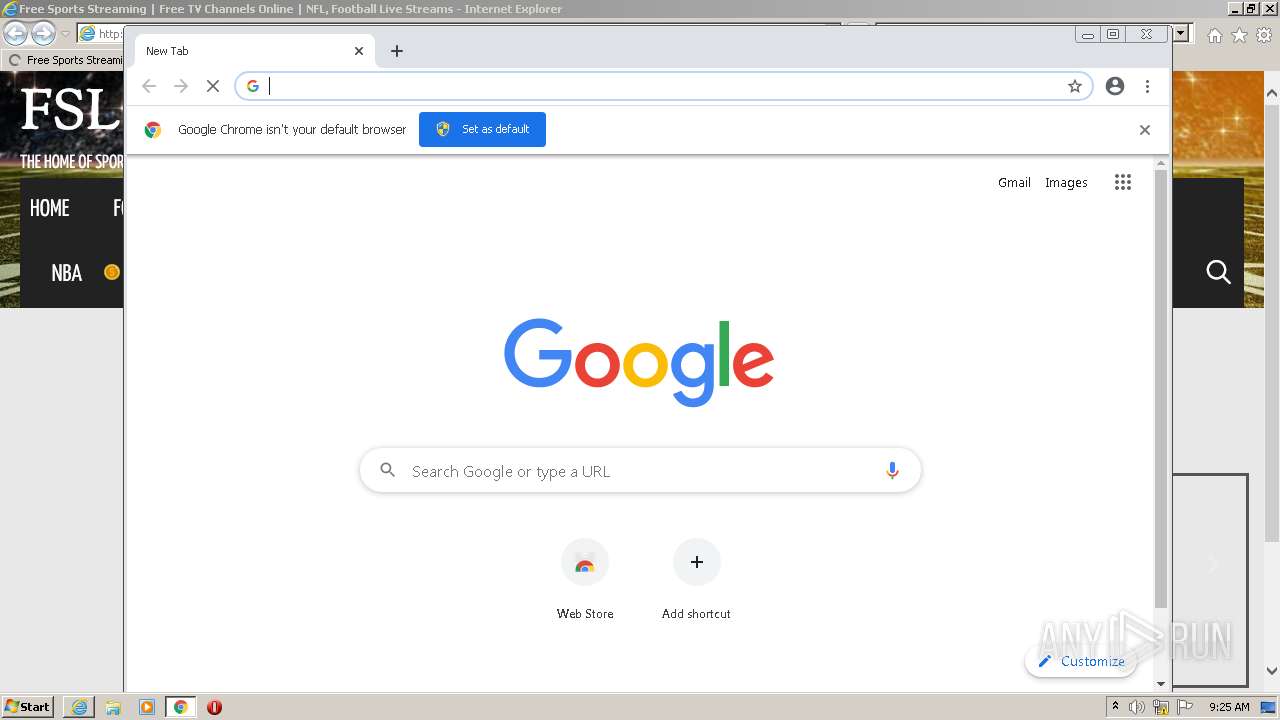
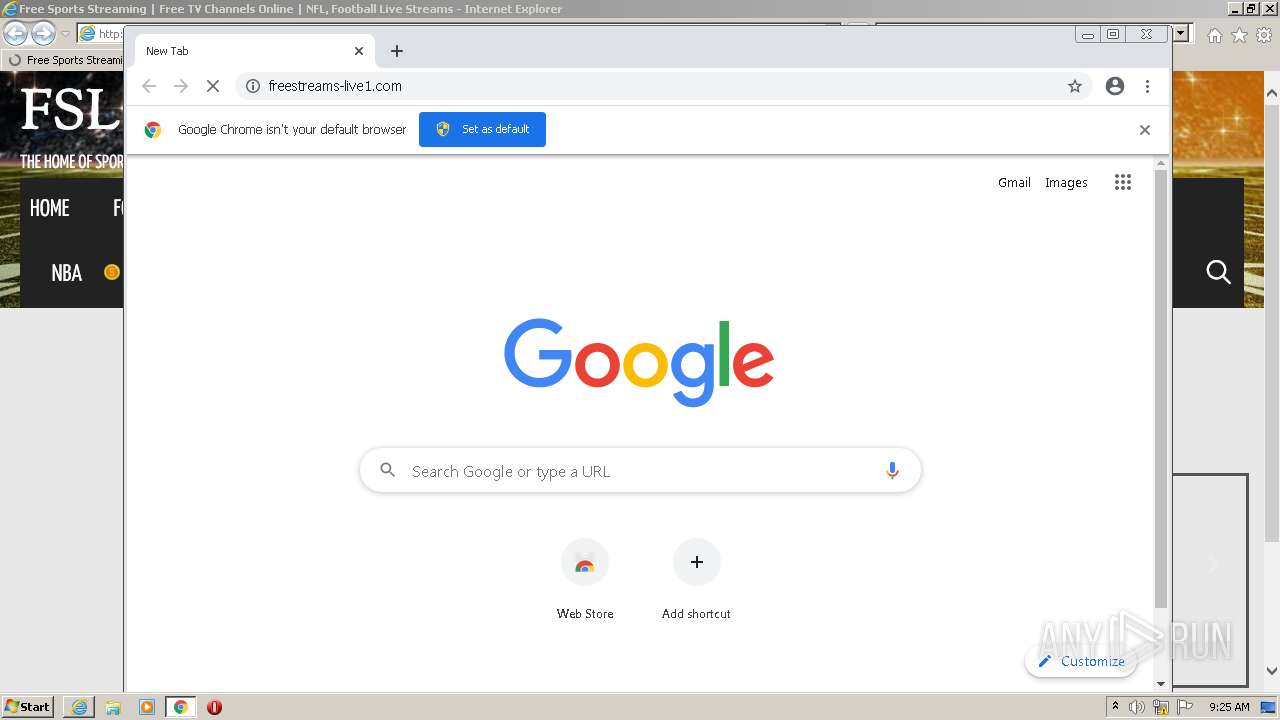
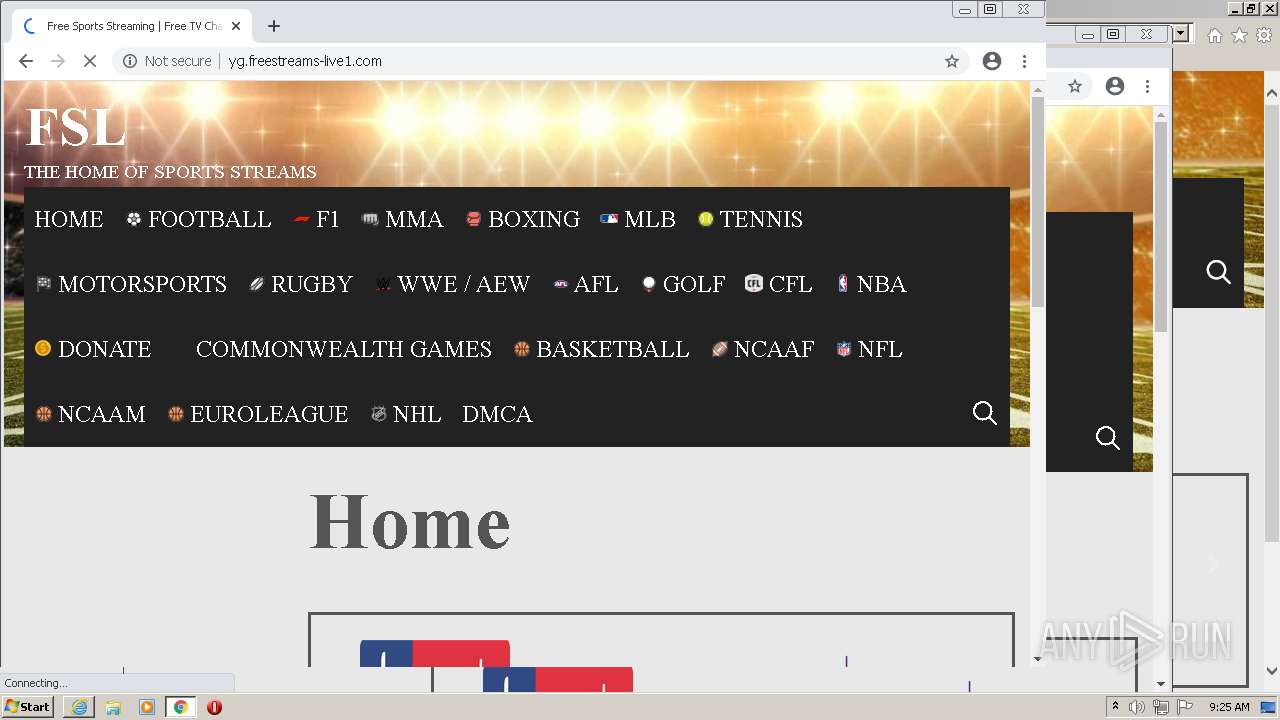
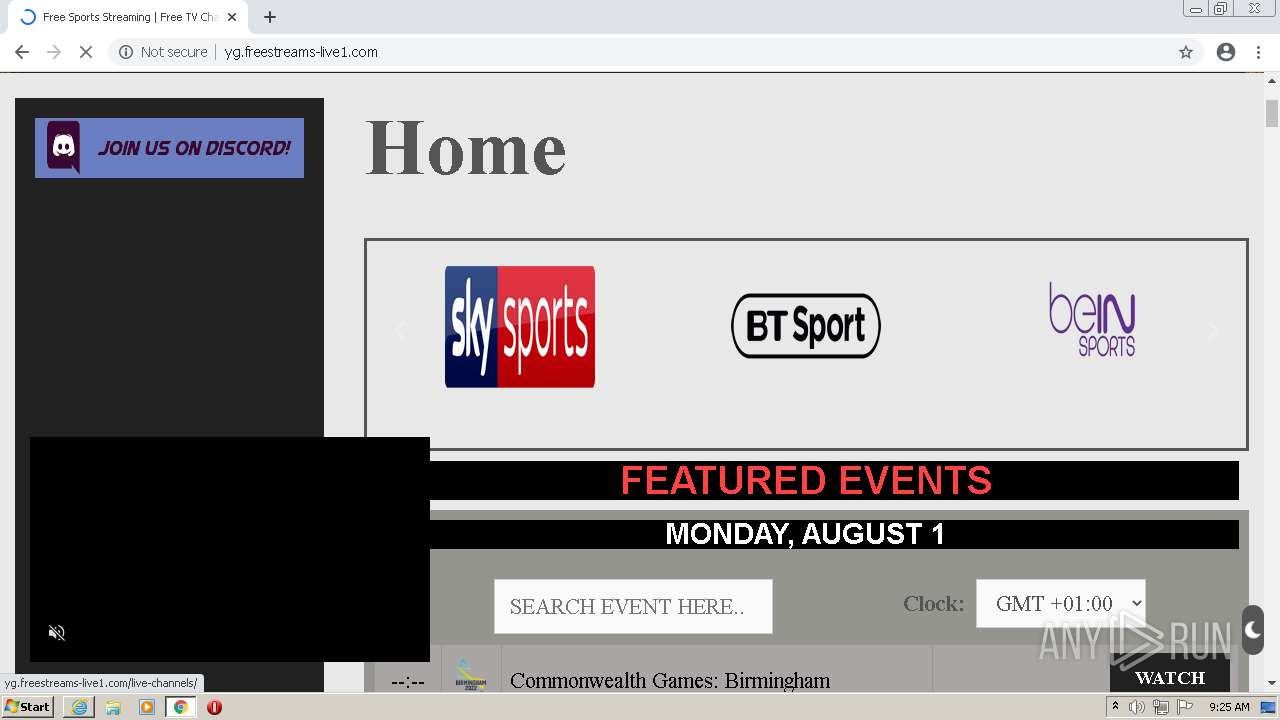
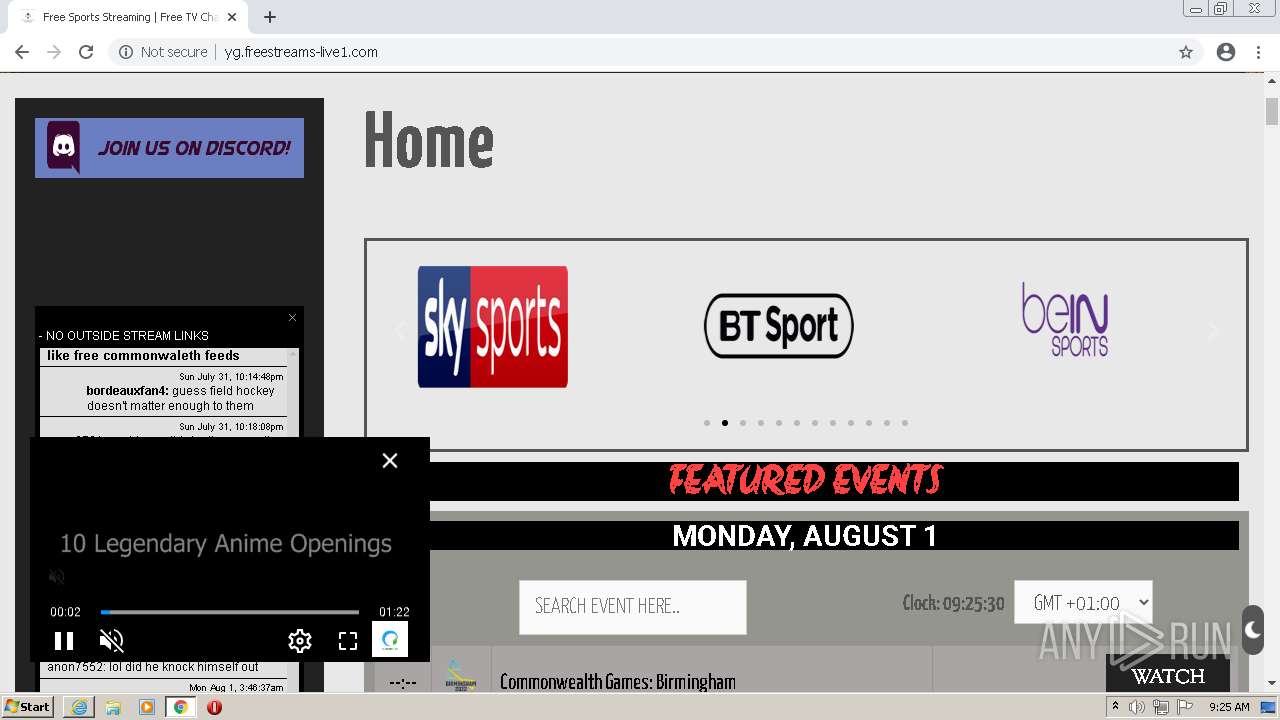
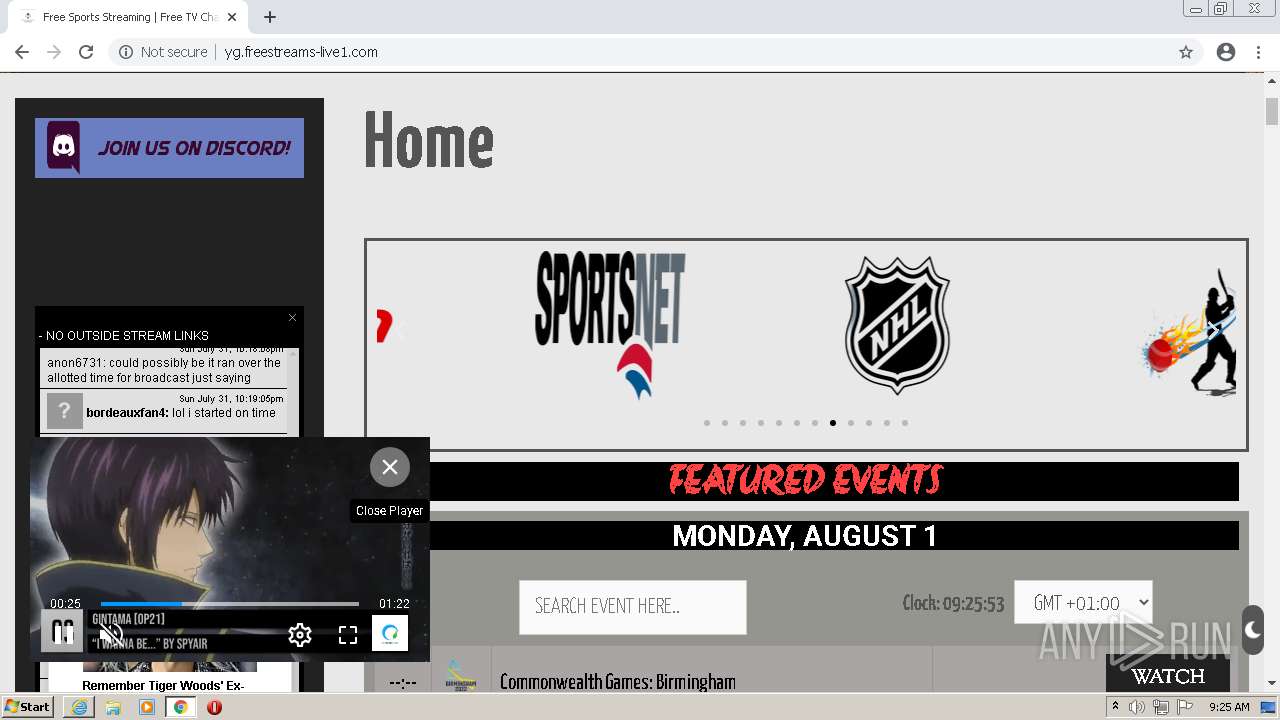
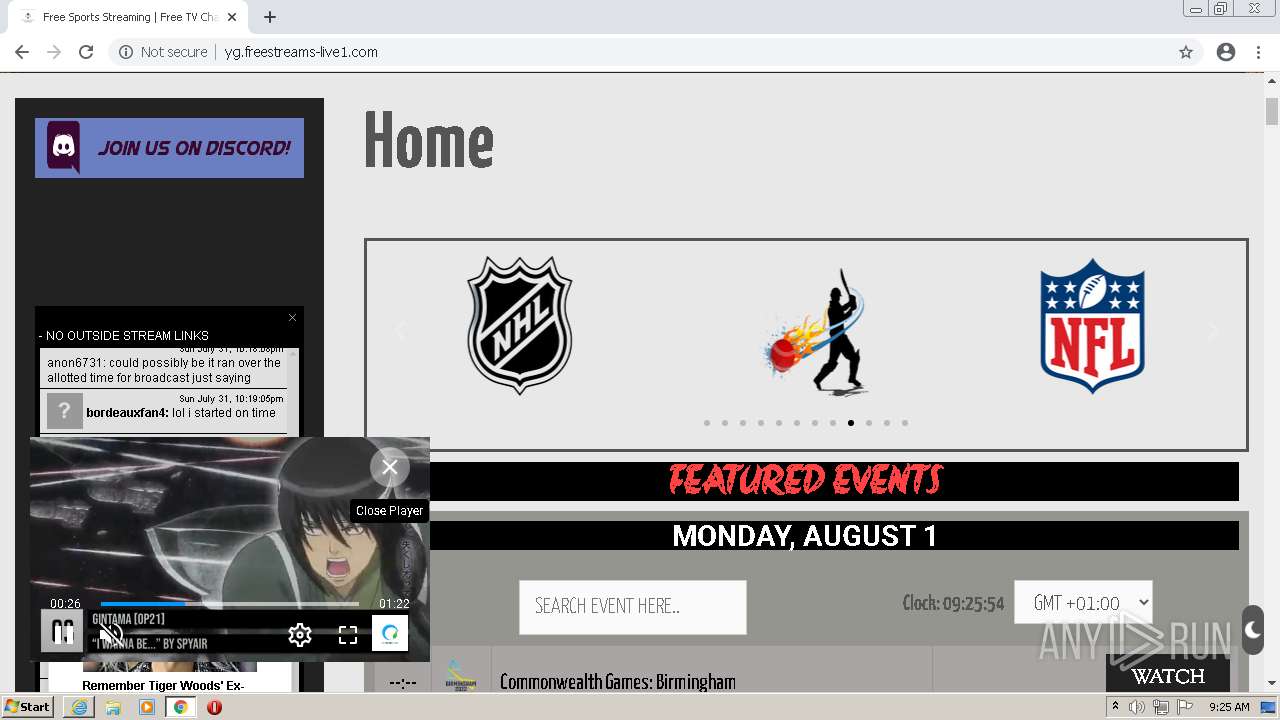
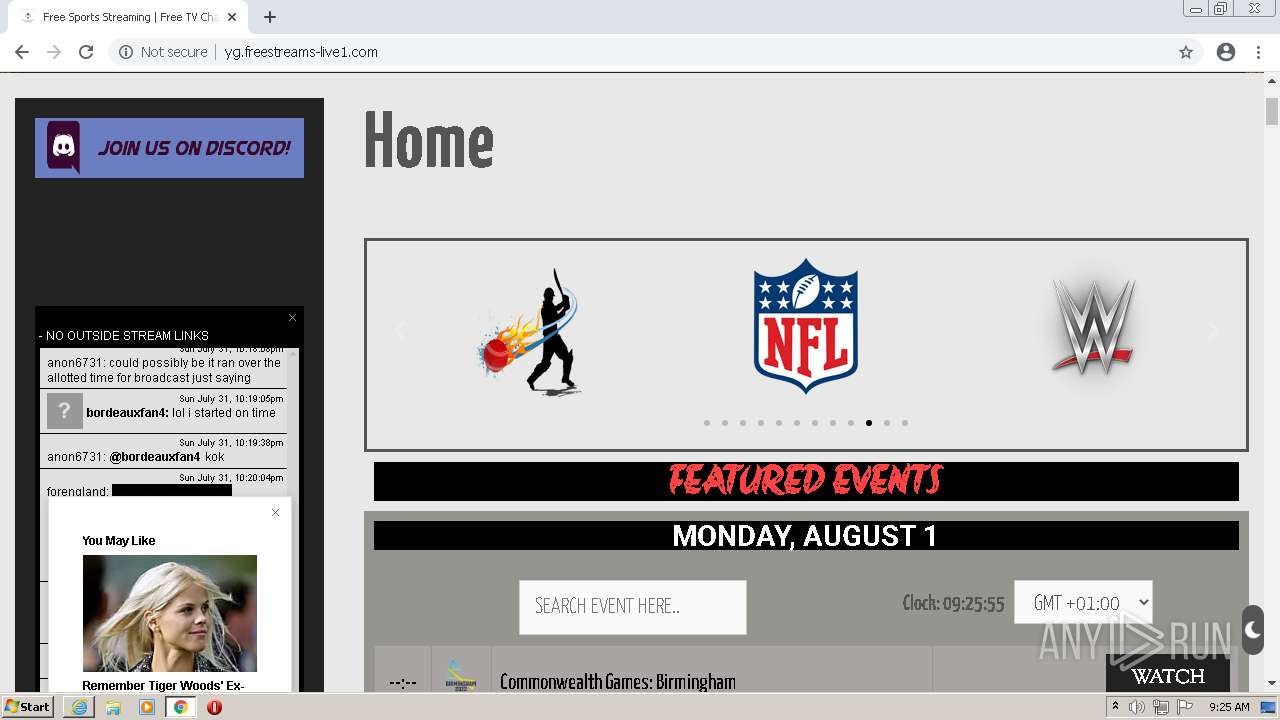
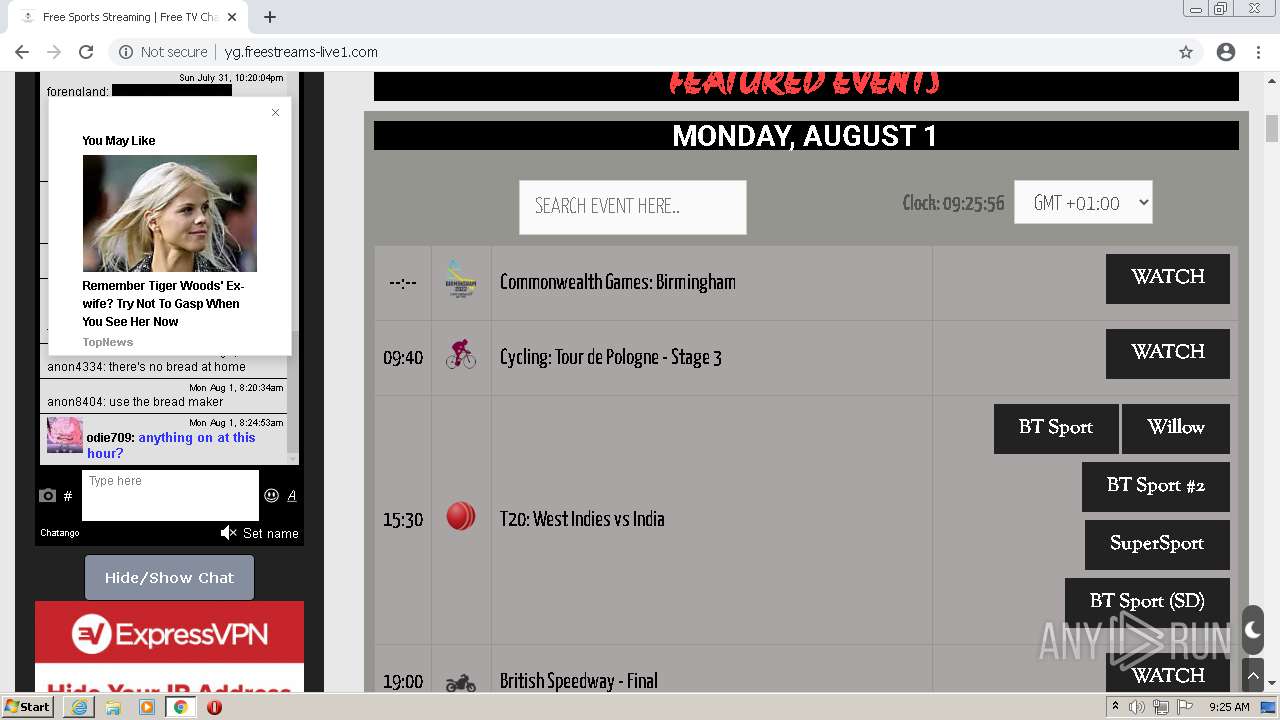
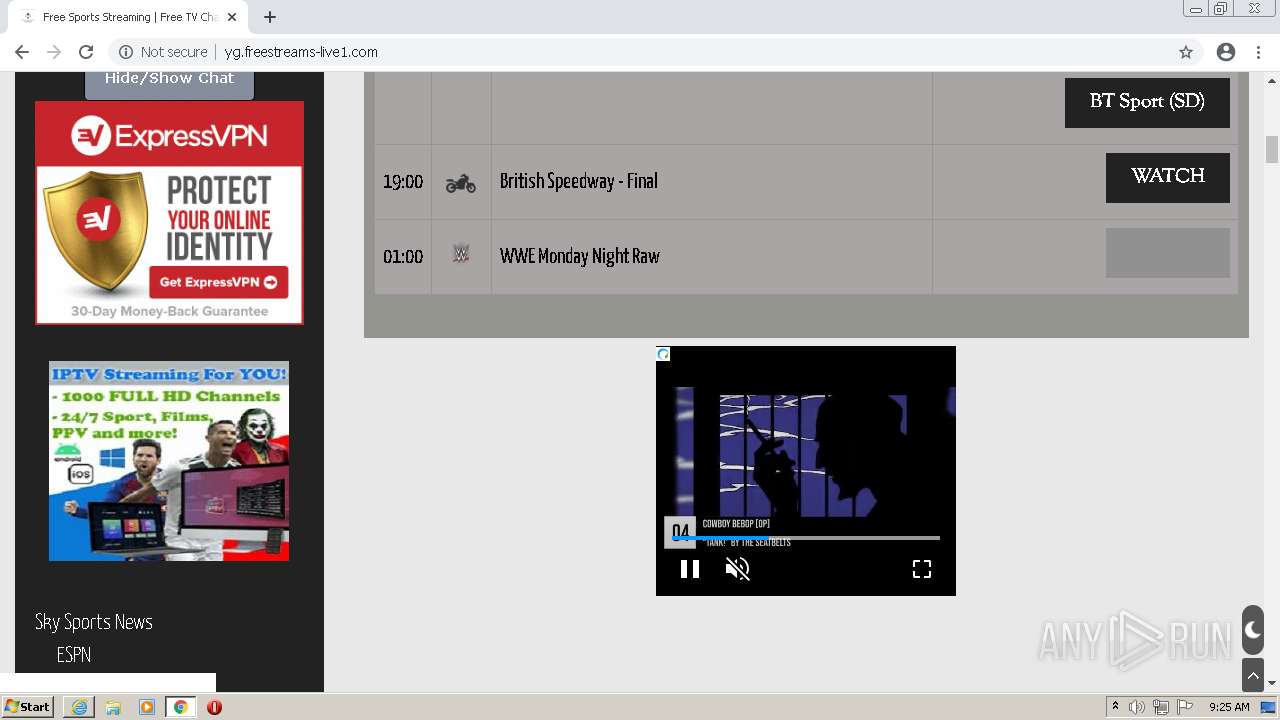
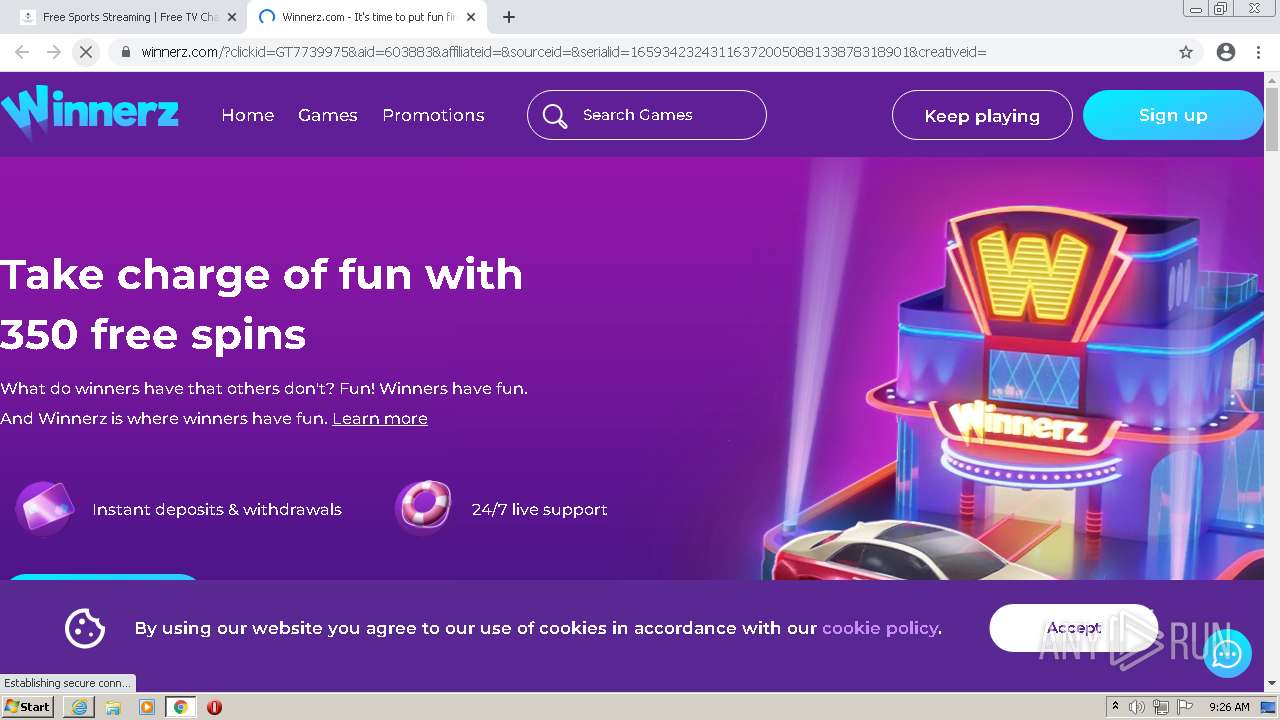
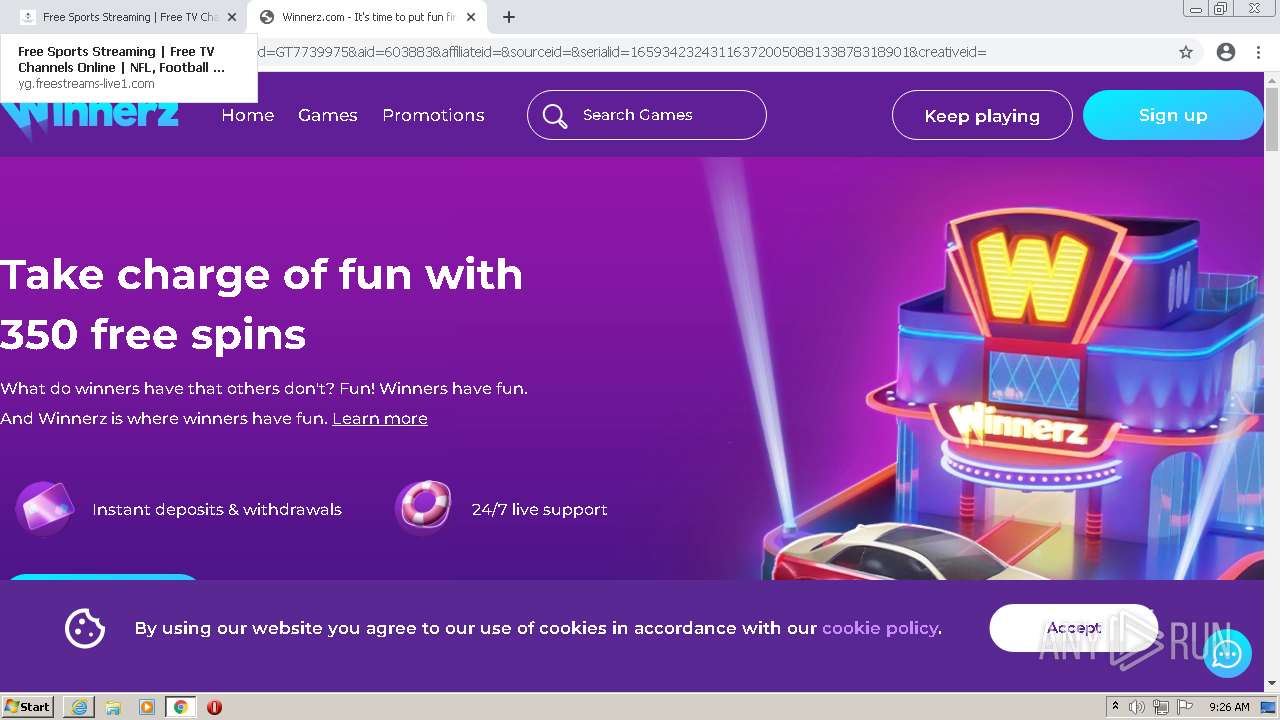
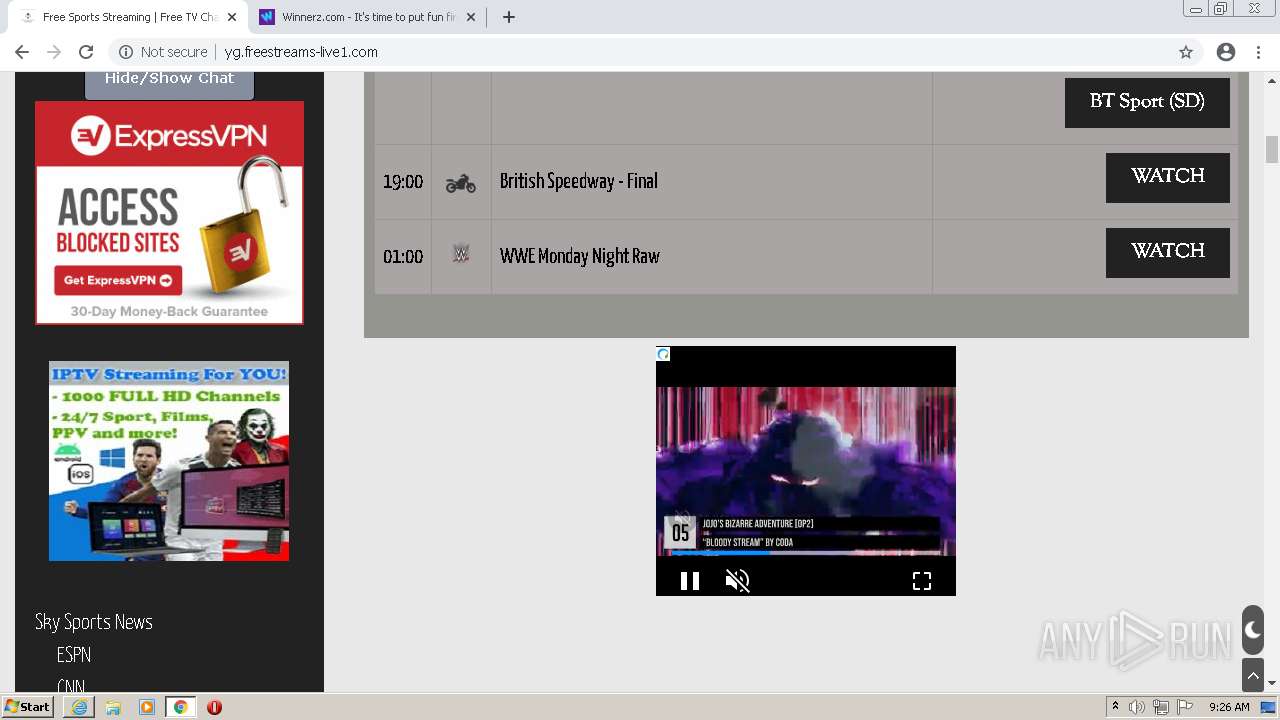
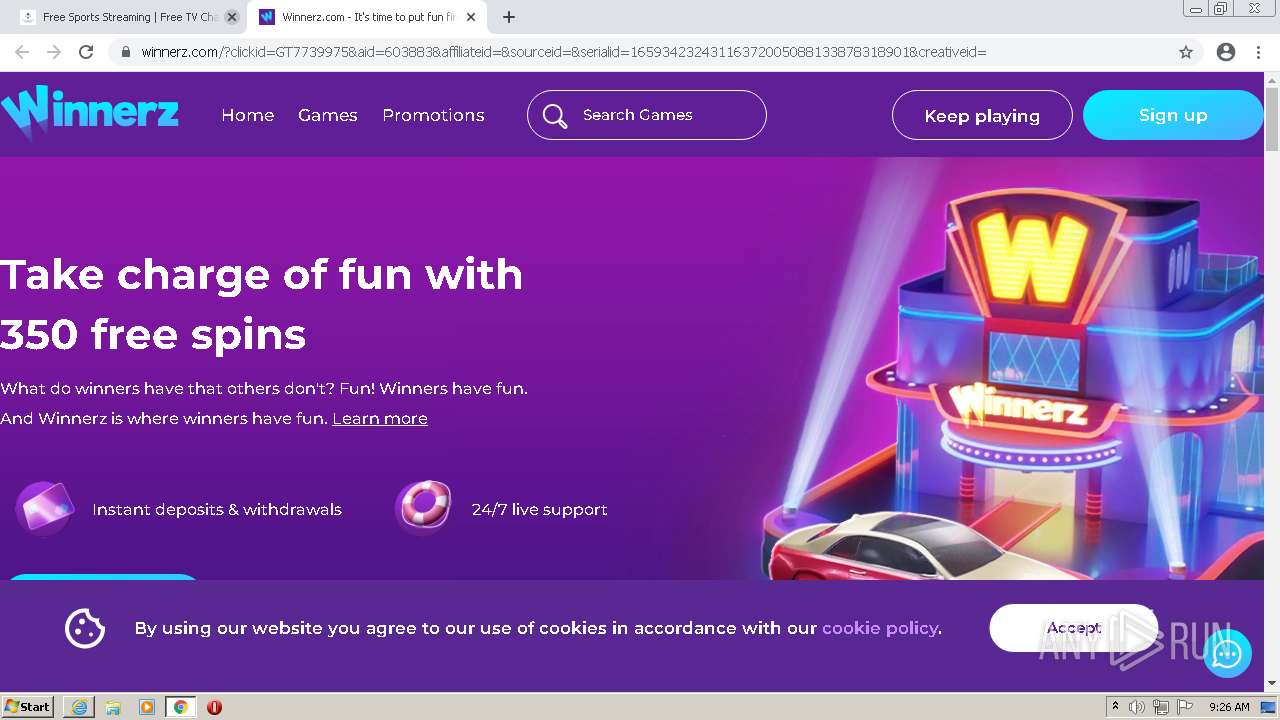
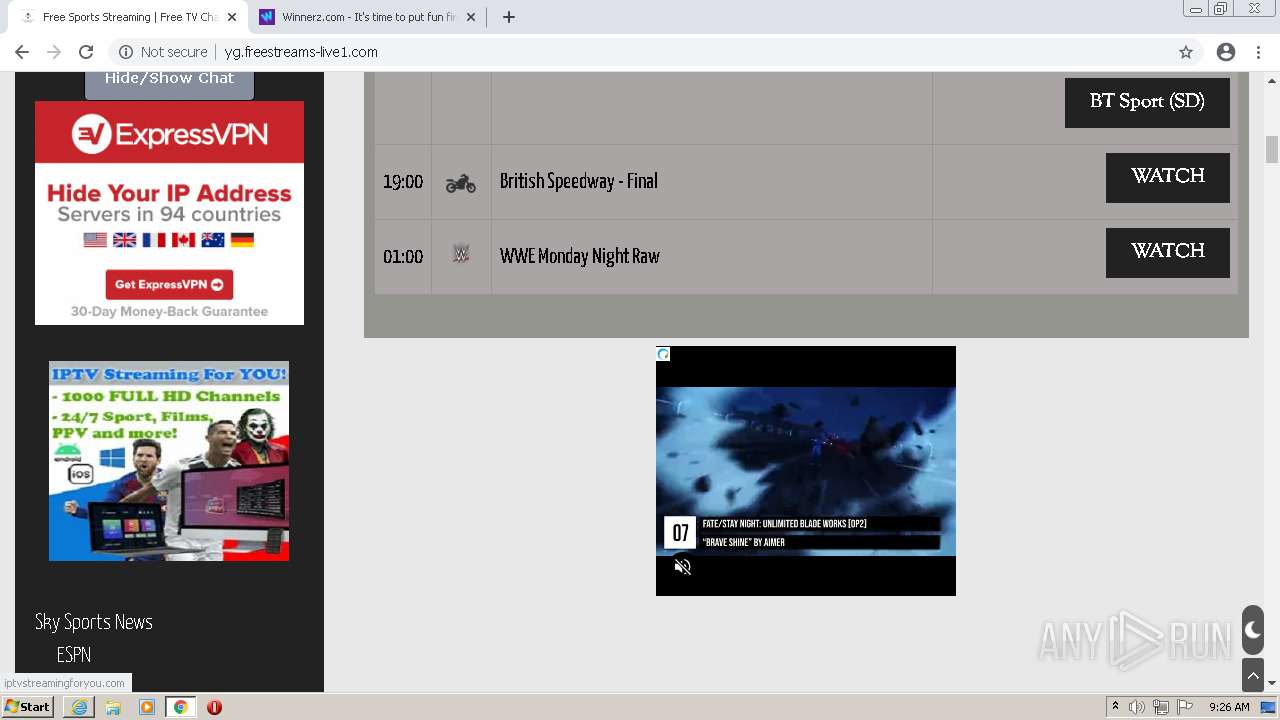
| URL: | https://freestreams-live1.com |
| Full analysis: | https://app.any.run/tasks/edff49cb-e8c8-4d77-bb95-5ada7d85d943 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2022, 08:24:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 398FD1D5B1C1C90FF30D4F091C58320D |
| SHA1: | 908886482BF3499C58C608B330671DEAF71534AE |
| SHA256: | 26854DE34936EA5B24A36A27F48FEA5A7009A2D1052B487FC414FF1A91E5AA38 |
| SSDEEP: | 3:N8iRRcJMMtn:2iTcJMgn |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3112)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2876)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3112)
Drops a file with a compile date too recent
- chrome.exe (PID: 3112)
INFO
Checks supported languages
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2872)
- iexplore.exe (PID: 2876)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 564)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2720)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 276)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 932)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3688)
Reads the computer name
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 3936)
- iexplore.exe (PID: 2876)
- chrome.exe (PID: 276)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 932)
- chrome.exe (PID: 3252)
Changes internet zones settings
- iexplore.exe (PID: 2920)
Application launched itself
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 3112)
Reads settings of System Certificates
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 3936)
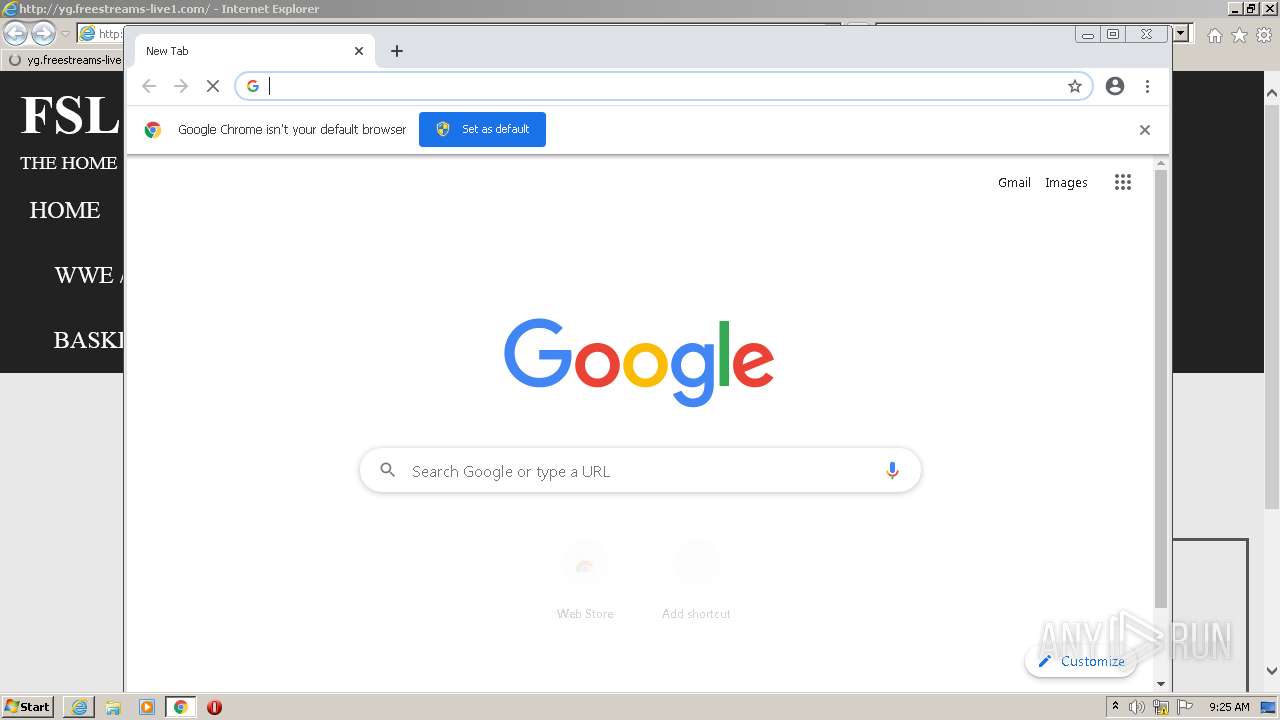
Manual execution by user
- chrome.exe (PID: 3112)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
Checks Windows Trust Settings
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 2876)
Reads the date of Windows installation
- chrome.exe (PID: 3452)
Changes settings of System certificates
- iexplore.exe (PID: 2920)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
31
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bb3d988,0x6bb3d998,0x6bb3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3236 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,18321301334954963142,5207080609469447575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 167
Read events
29 912
Write events
245
Delete events
10
Modification events
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 801643440 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30975360 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30975360 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
252
Text files
278
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\1NSN2JPS.htm | html | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cflsch[1].htm | html | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\style.min[1].css | text | |
MD5:B7915926FE42D76E9C802353AB01DAE4 | SHA256:D7705700D24D5919255576642AD2C28BFC790390B7183A369038FF5C1E814D51 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\frontend[1].css | text | |
MD5:898C9CC8AB3CE86EC26C2431550DE21A | SHA256:5E880C8DE639677C2EC0A2759D646FC8A6FF41245D648994176A8F1F22C0DCAF | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
237
TCP/UDP connections
411
DNS requests
173
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
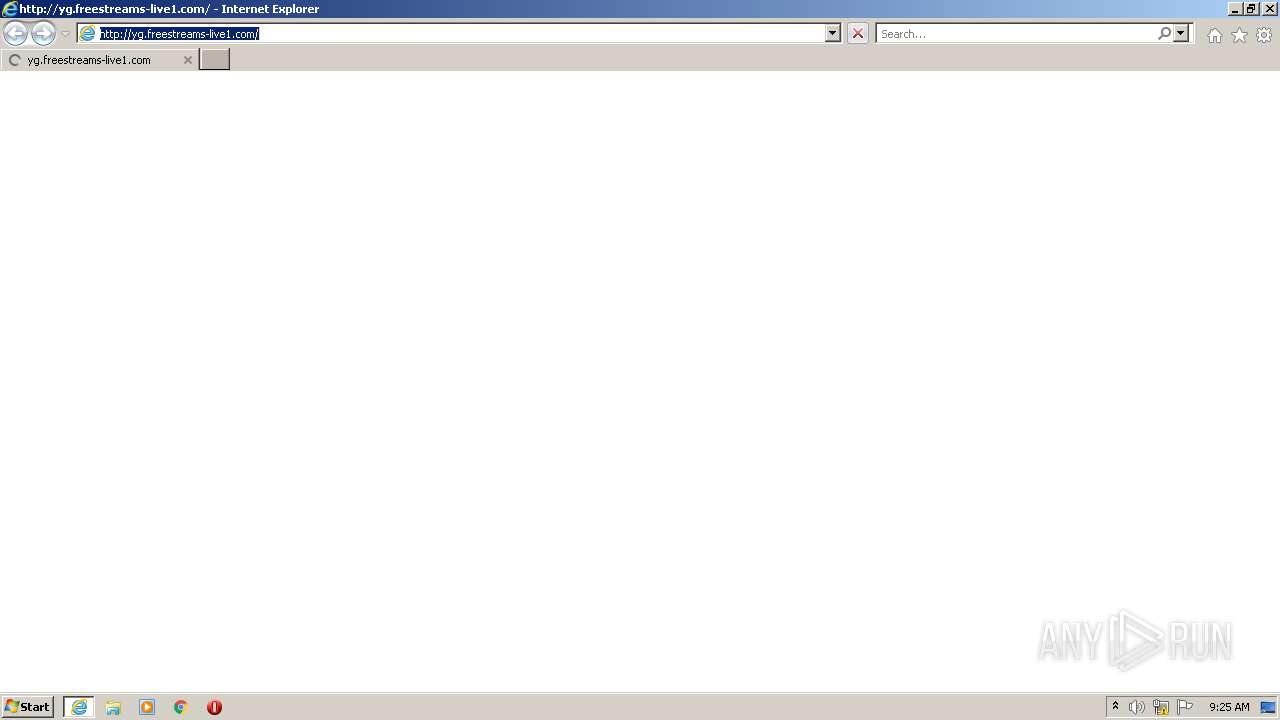
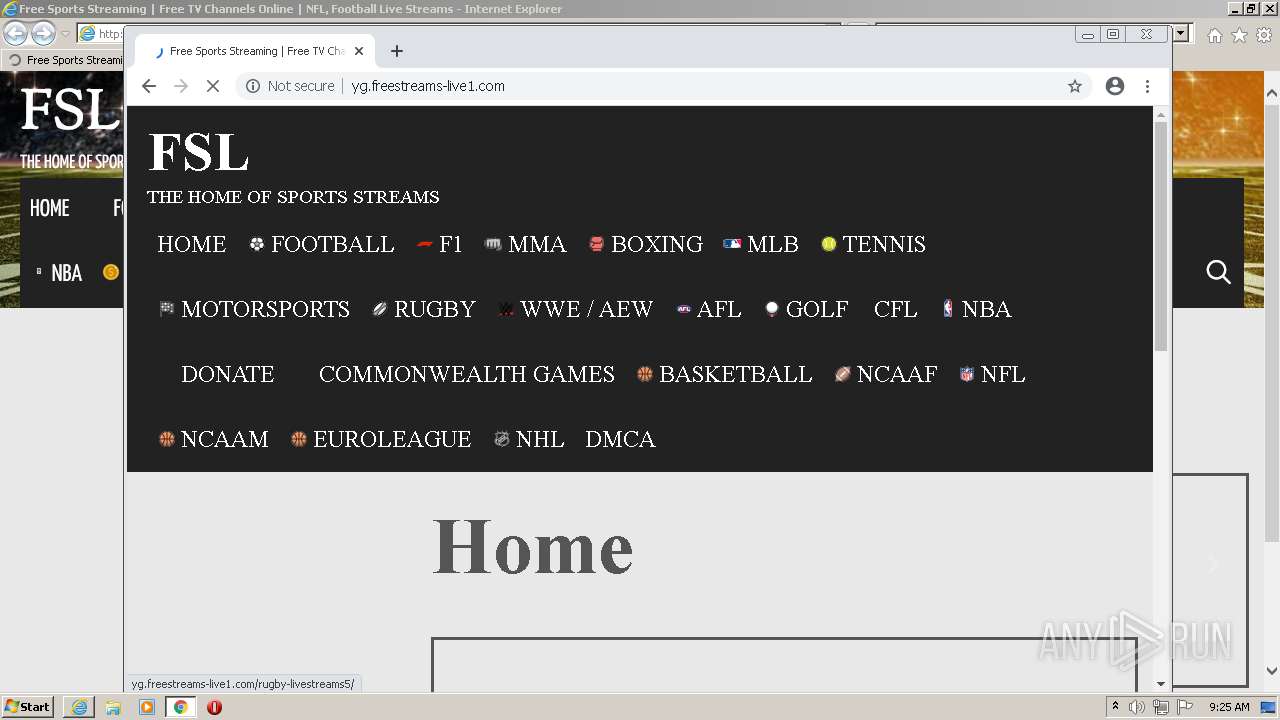
2876 | iexplore.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/ | US | html | 23.4 Kb | suspicious |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/plugins/litespeed-cache/assets/js/webfontloader.min.js | US | compressed | 854 b | suspicious |
2876 | iexplore.exe | GET | 301 | 172.67.196.251:80 | http://fs.freestreams-live1.com/wp-content/uploads/2018/12/cflsch.png | US | html | 1.05 Kb | suspicious |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/plugins/wp-dark-mode/assets/css/frontend.css?ver=2.3.5 | US | text | 354 b | suspicious |
2920 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/uploads/elementor/css/post-156.css?ver=1659315232 | US | text | 433 b | suspicious |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?84e65fa95d72fa7a | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2876 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
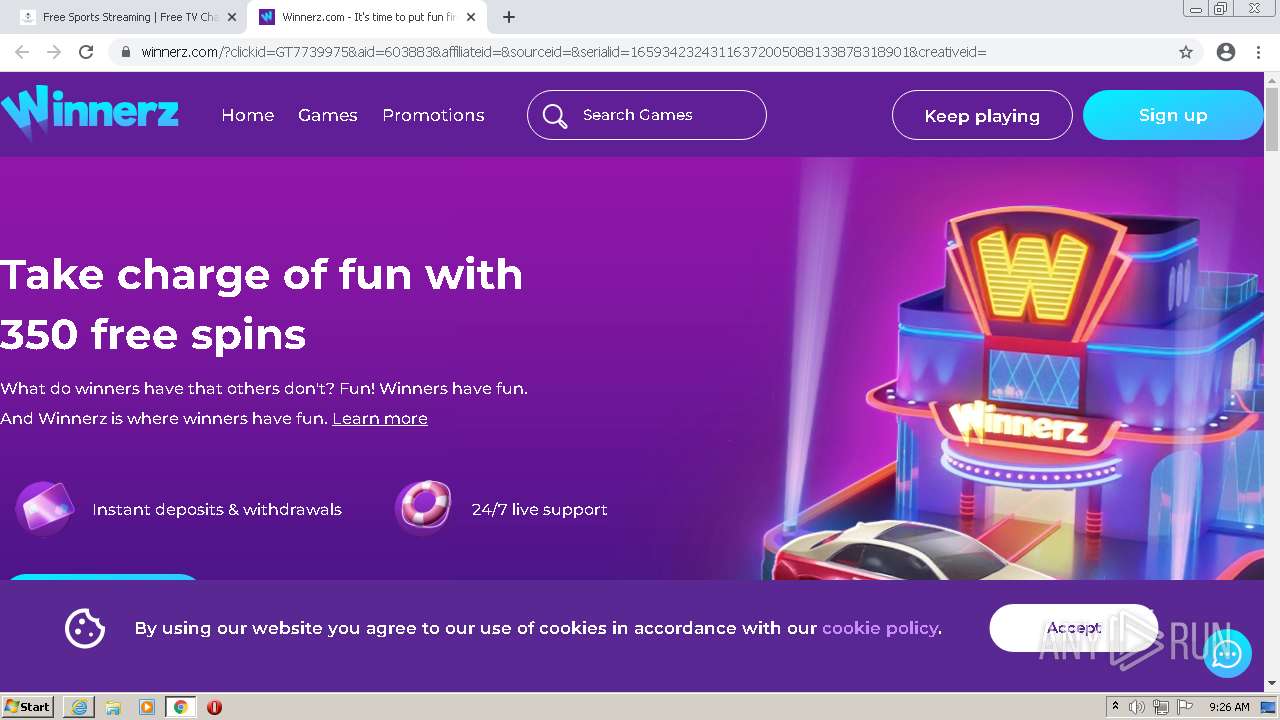
2876 | iexplore.exe | 142.250.184.194:443 | securepubads.g.doubleclick.net | Google Inc. | US | suspicious |
2920 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2876 | iexplore.exe | 104.21.36.163:80 | freestreams-live1.com | Cloudflare Inc | US | suspicious |
2876 | iexplore.exe | 172.67.196.251:80 | freestreams-live1.com | — | US | suspicious |
2876 | iexplore.exe | 142.250.184.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2876 | iexplore.exe | 142.250.185.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2876 | iexplore.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
2876 | iexplore.exe | 208.93.230.18:80 | st.chatango.com | Chatango LLC | US | suspicious |
2876 | iexplore.exe | 142.250.185.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
freestreams-live1.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
yg.freestreams-live1.com |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
a.espncdn.com |
| whitelisted |
fs.freestreams-live1.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
2876 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |