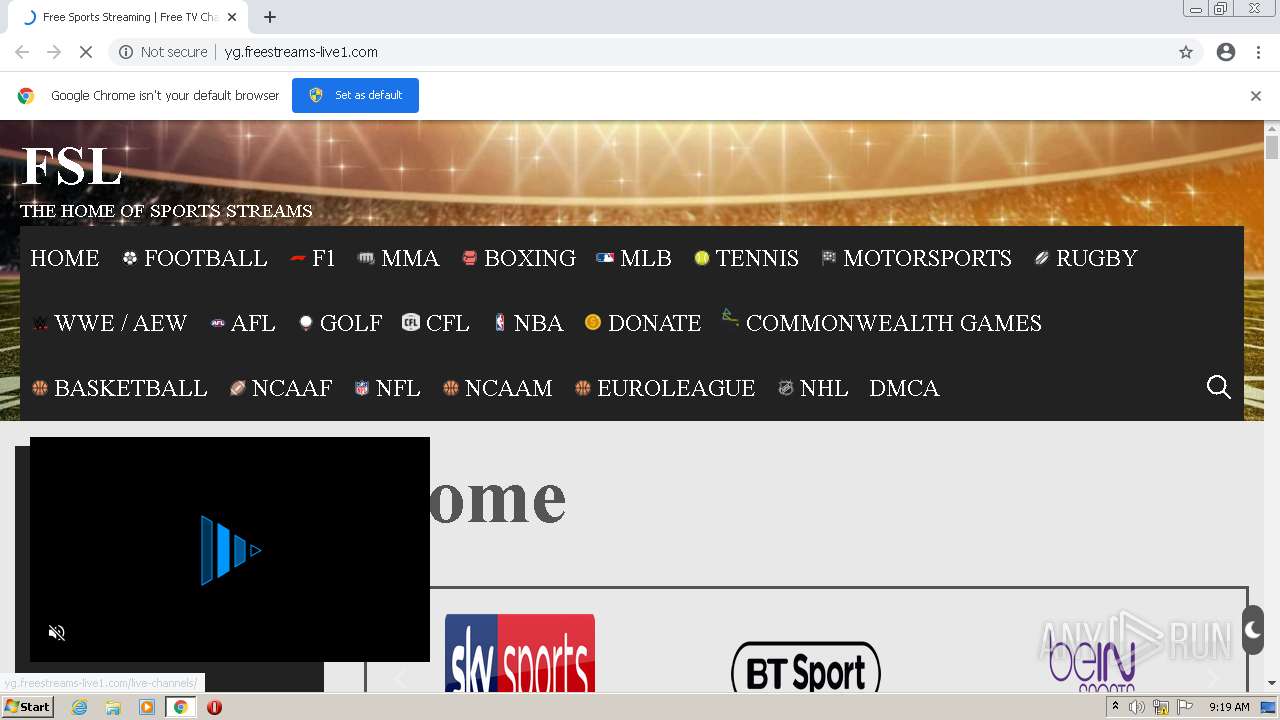
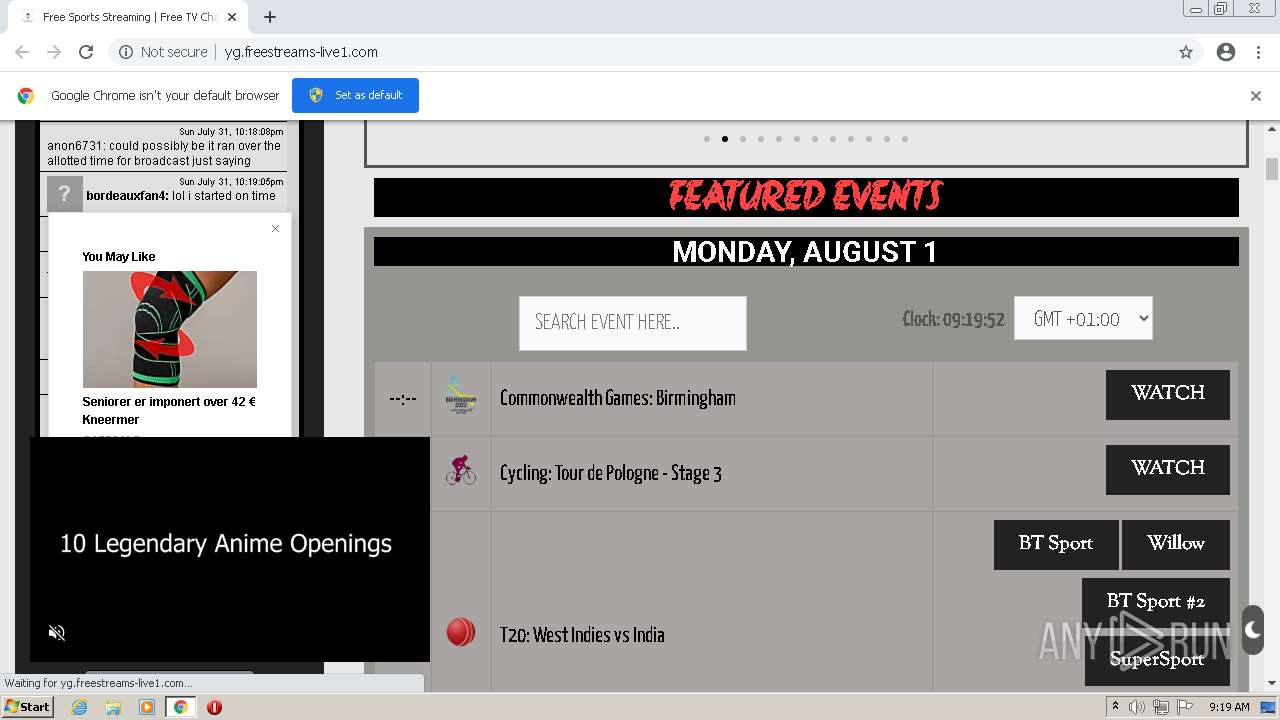
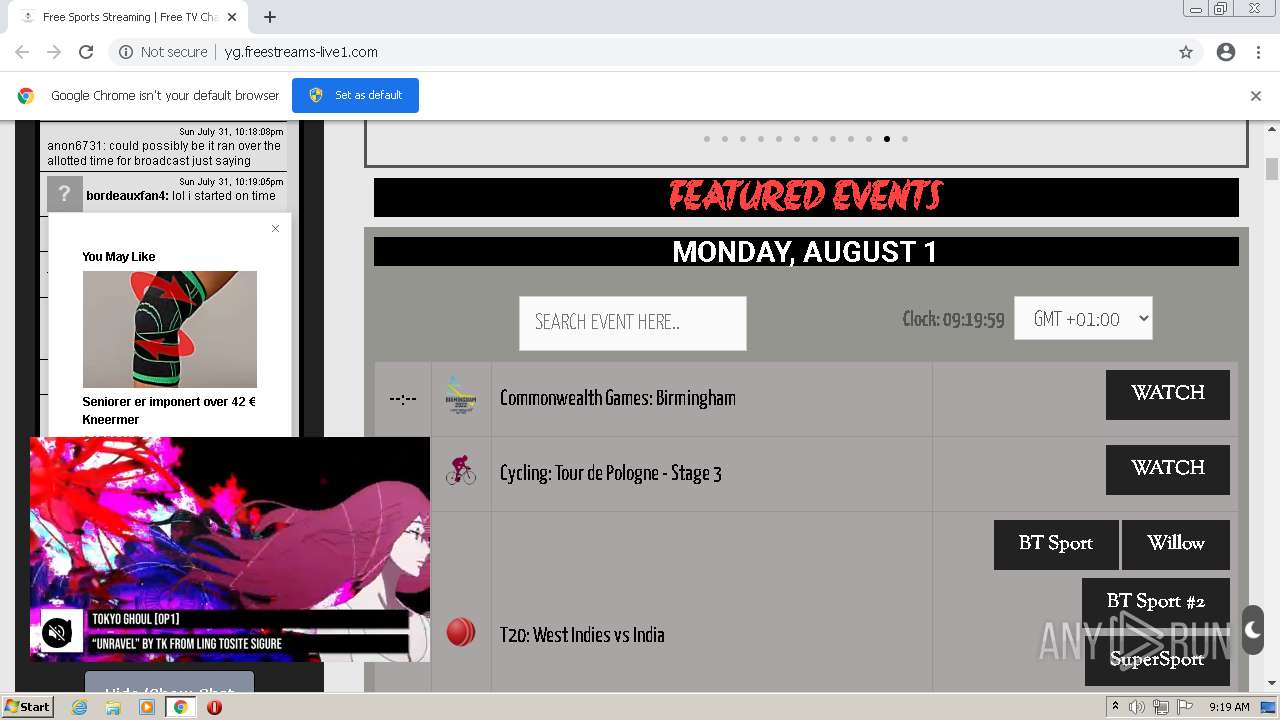
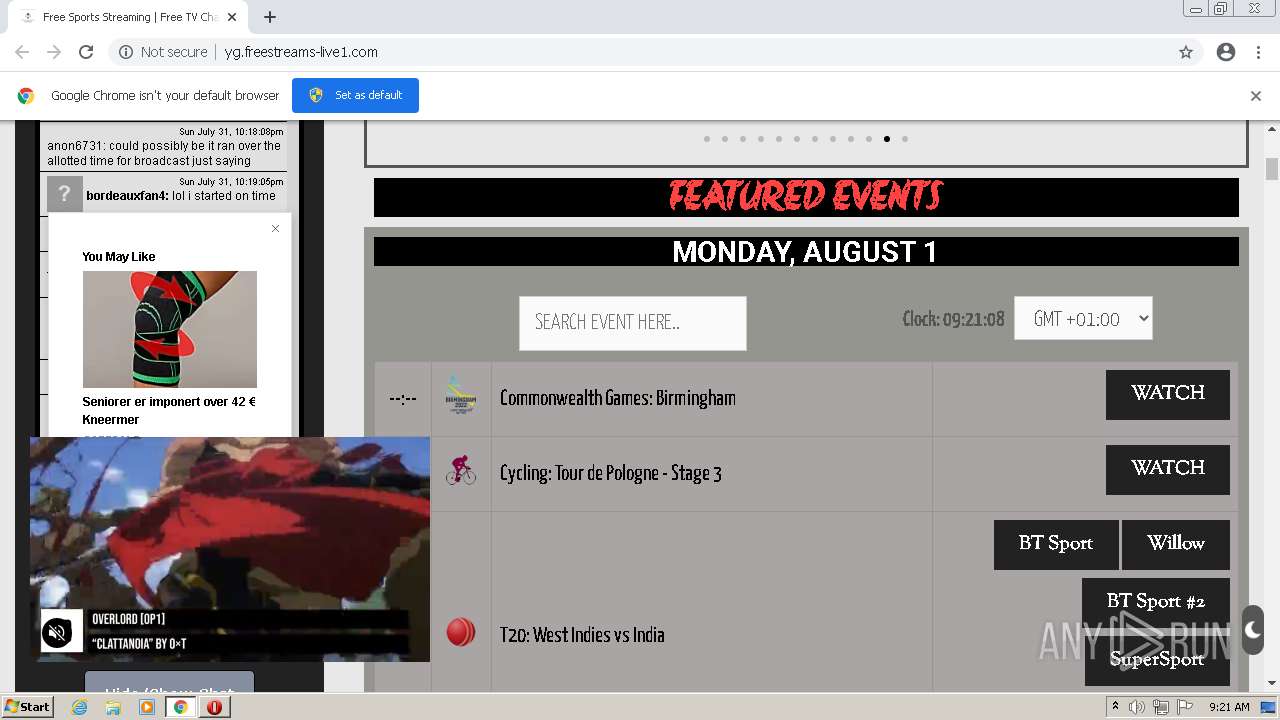
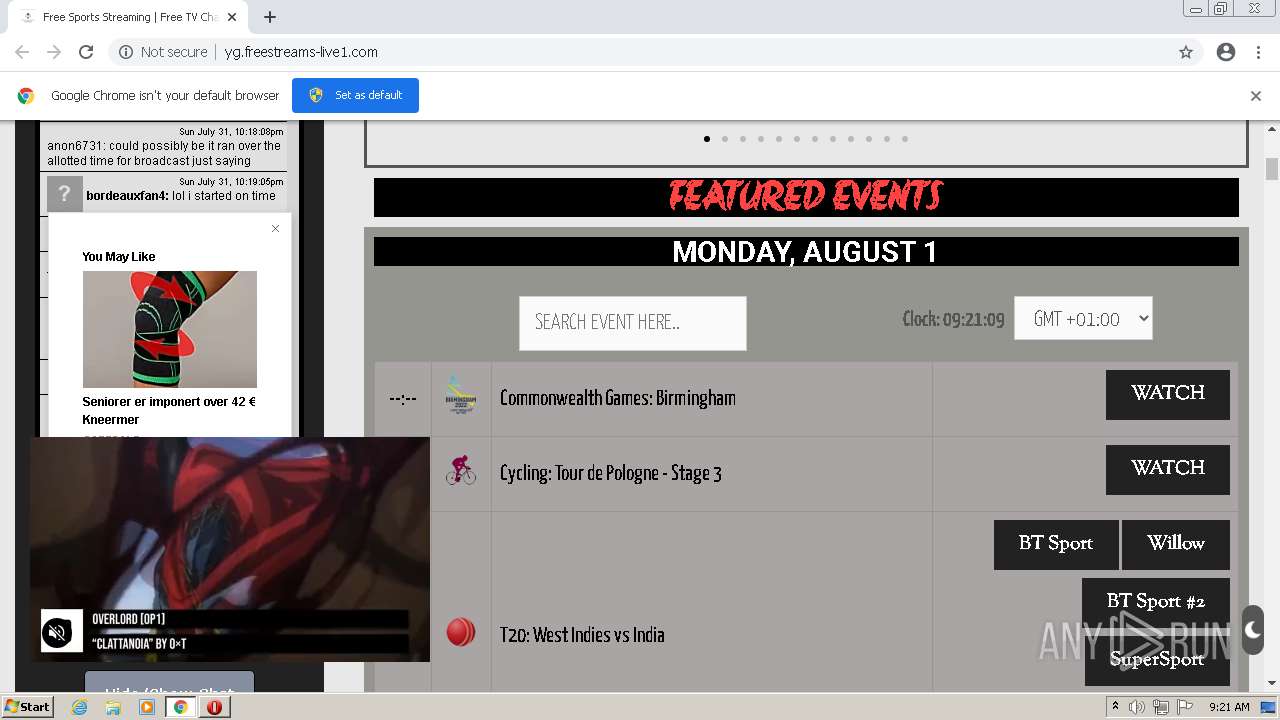
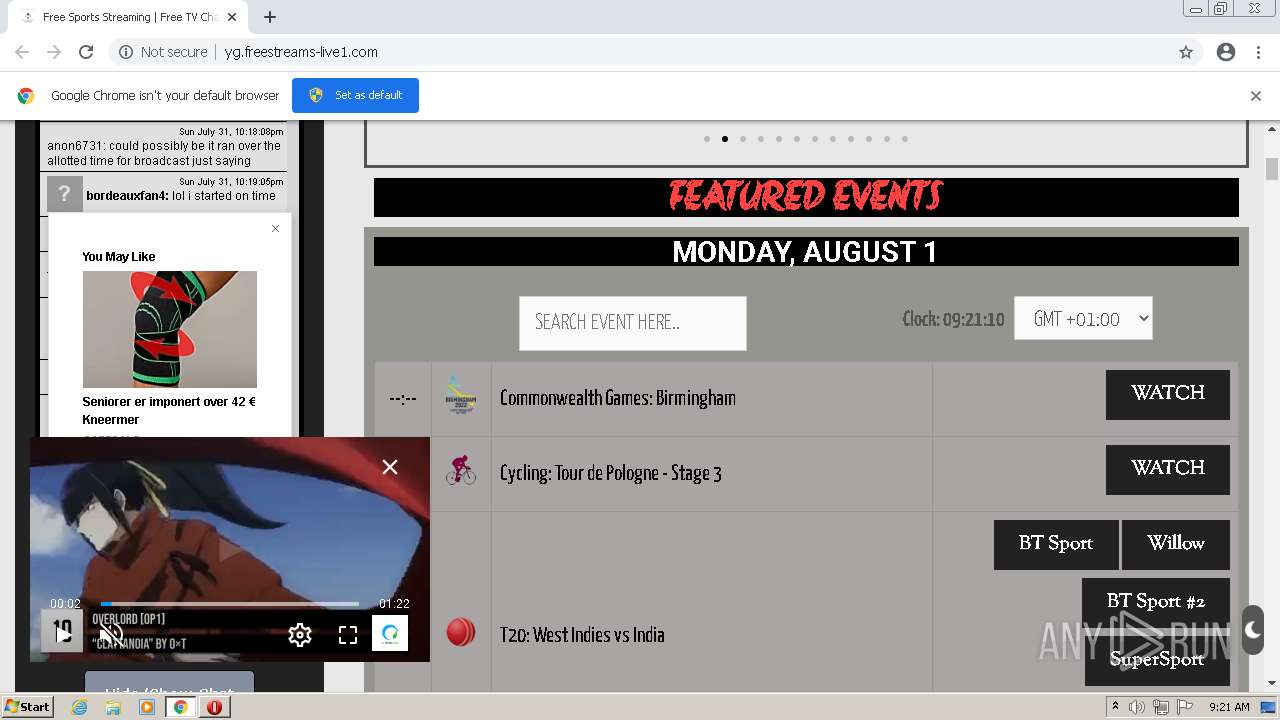
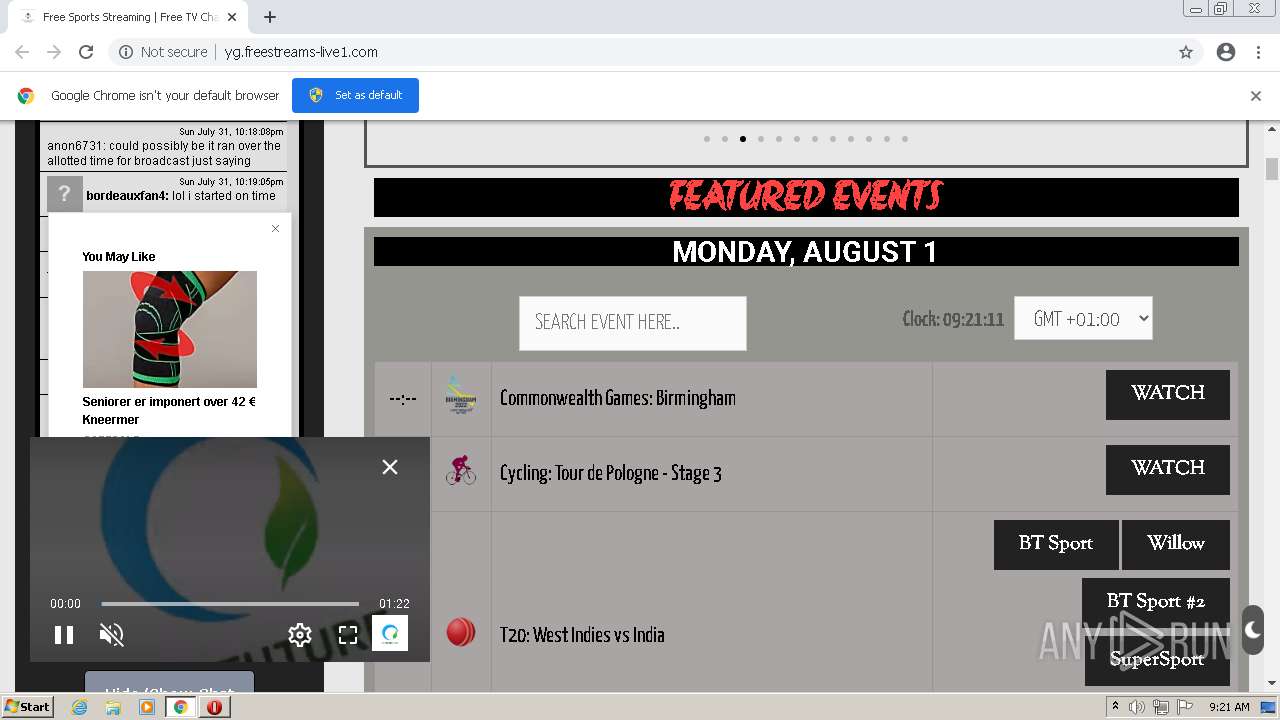
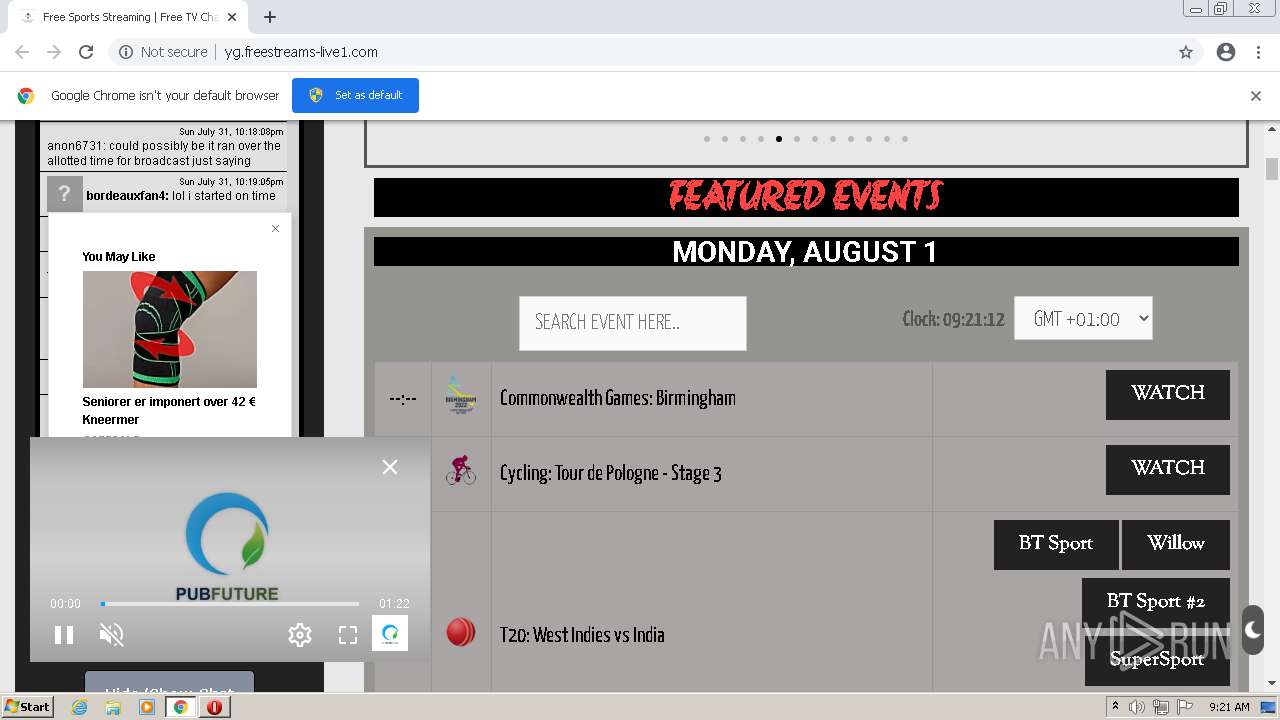
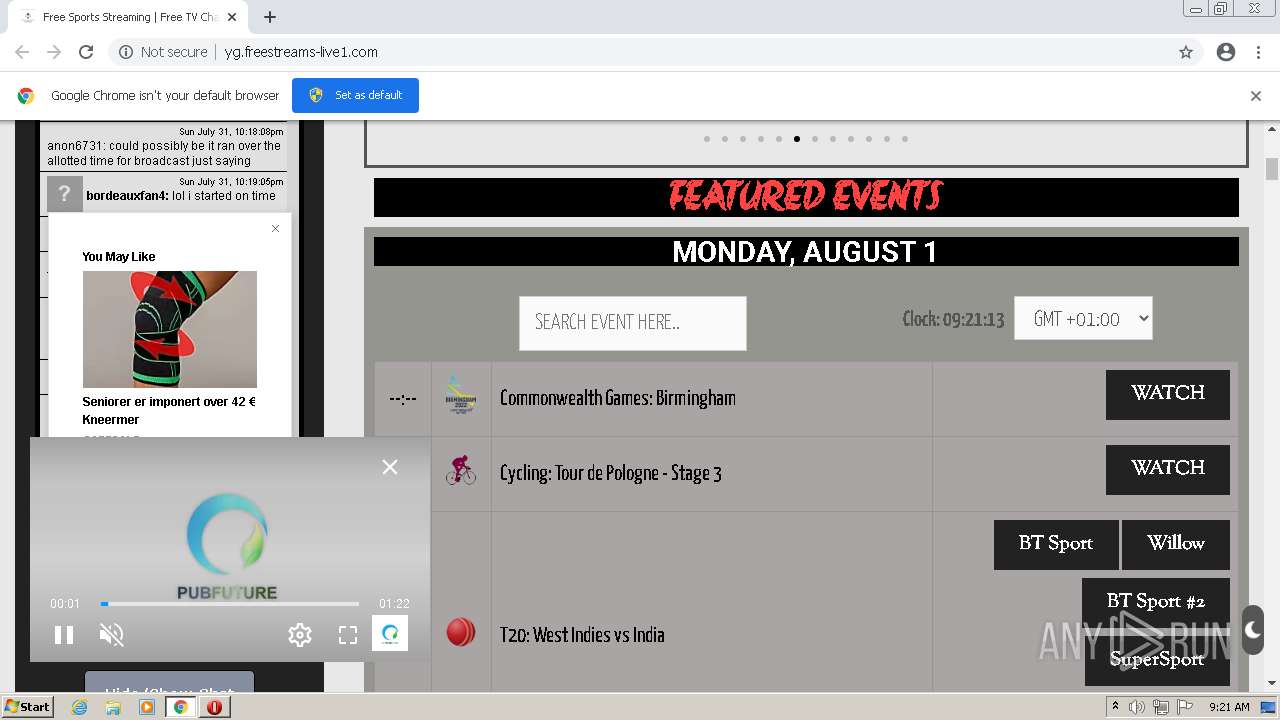
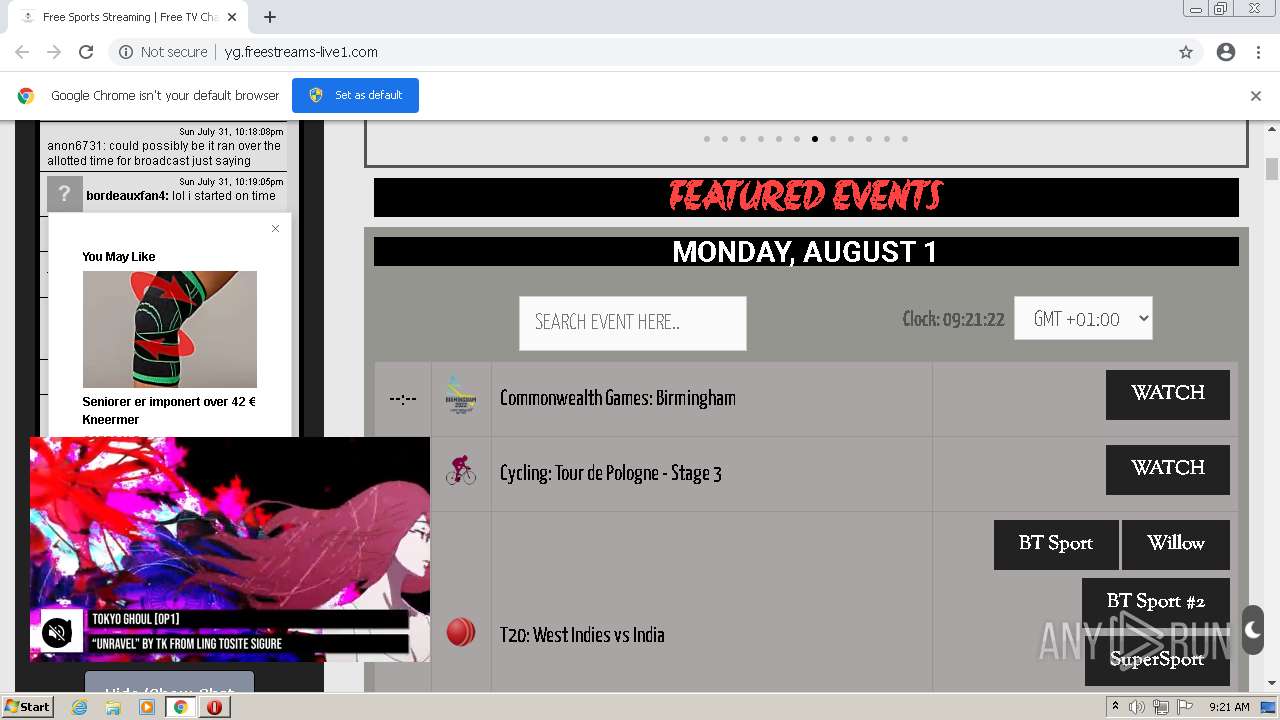
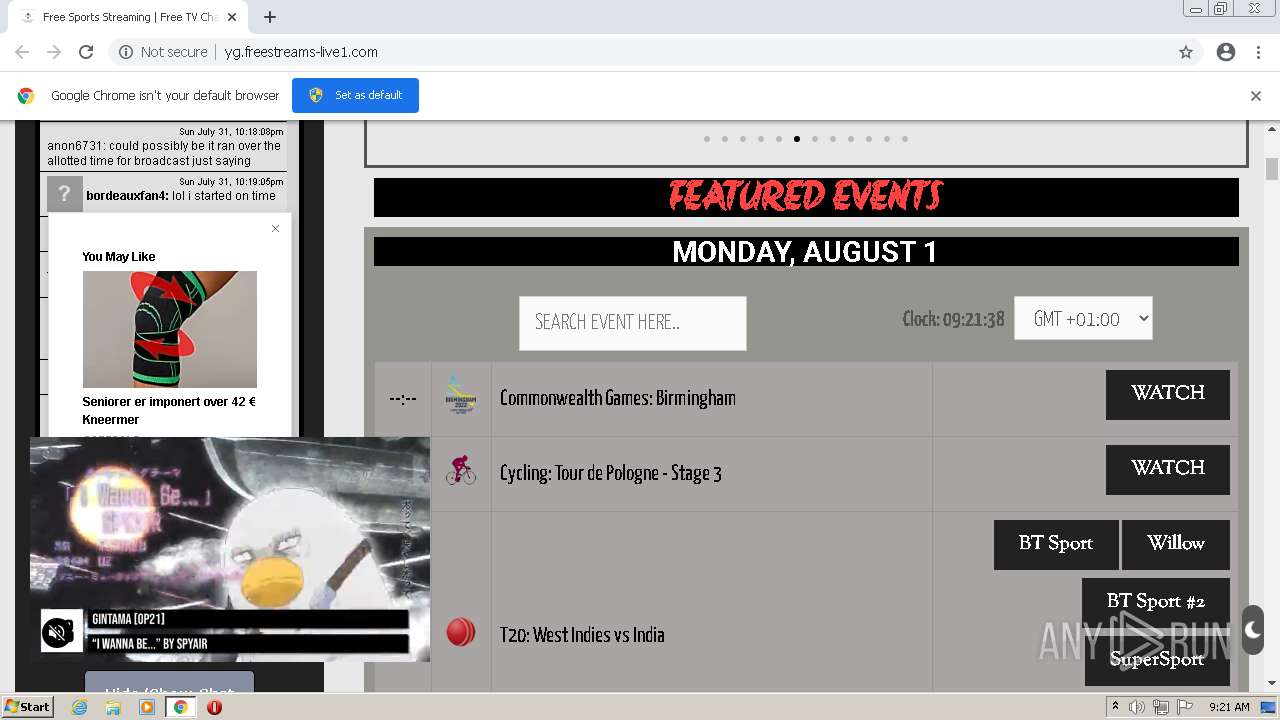
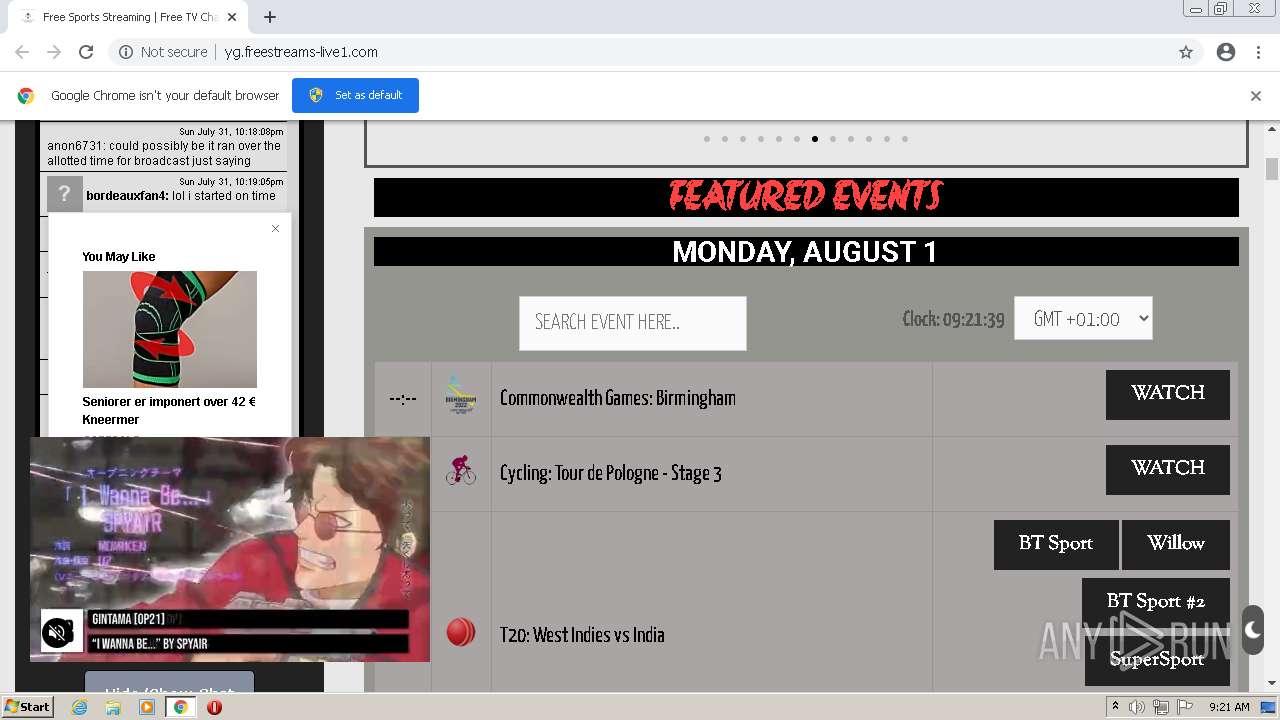
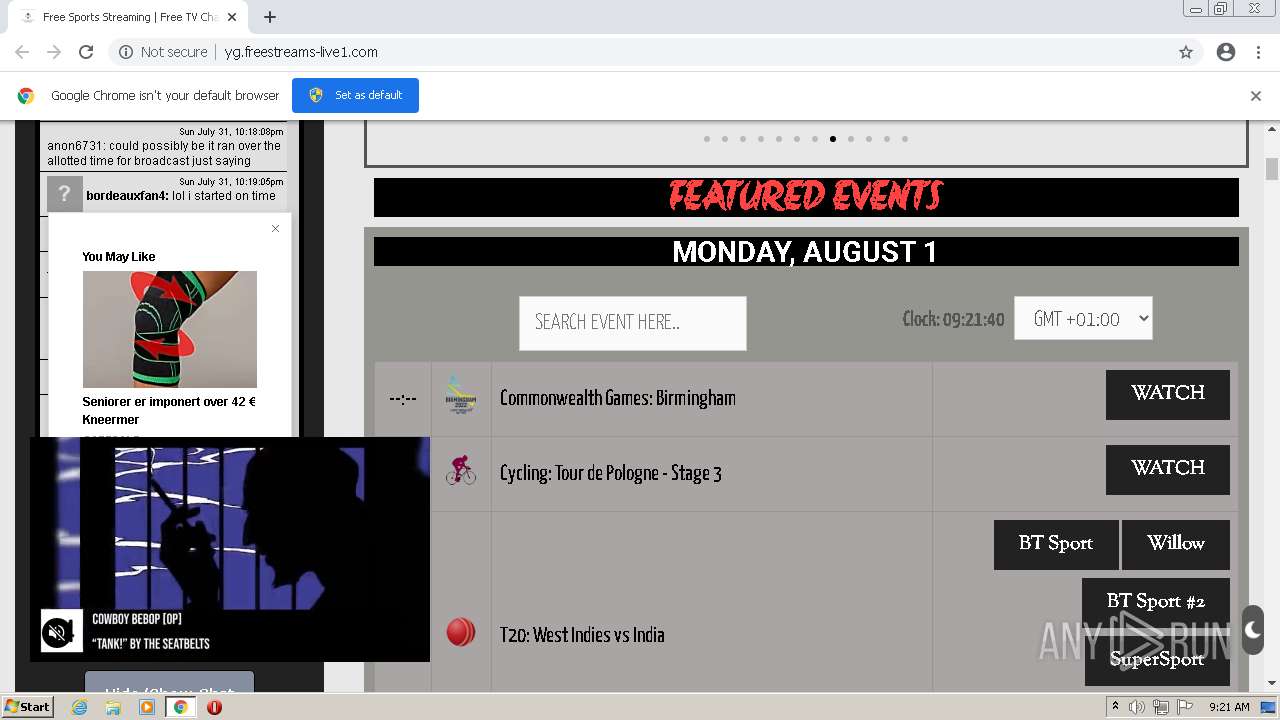
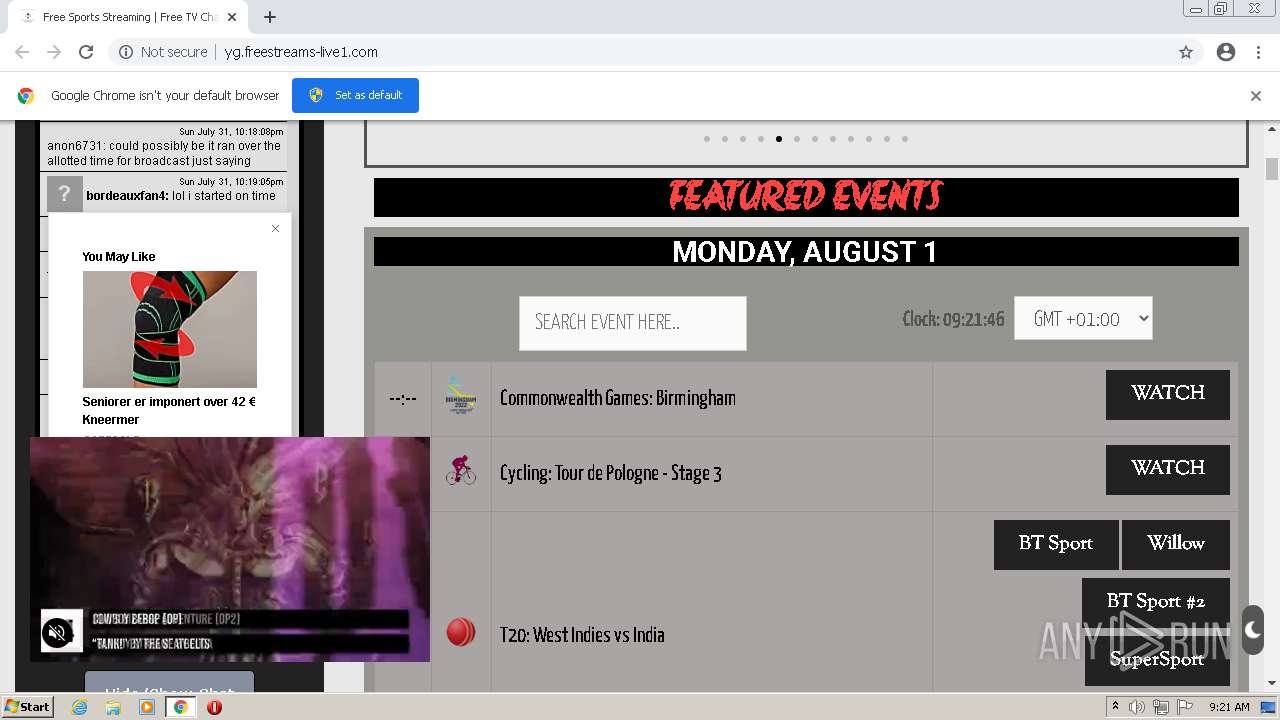
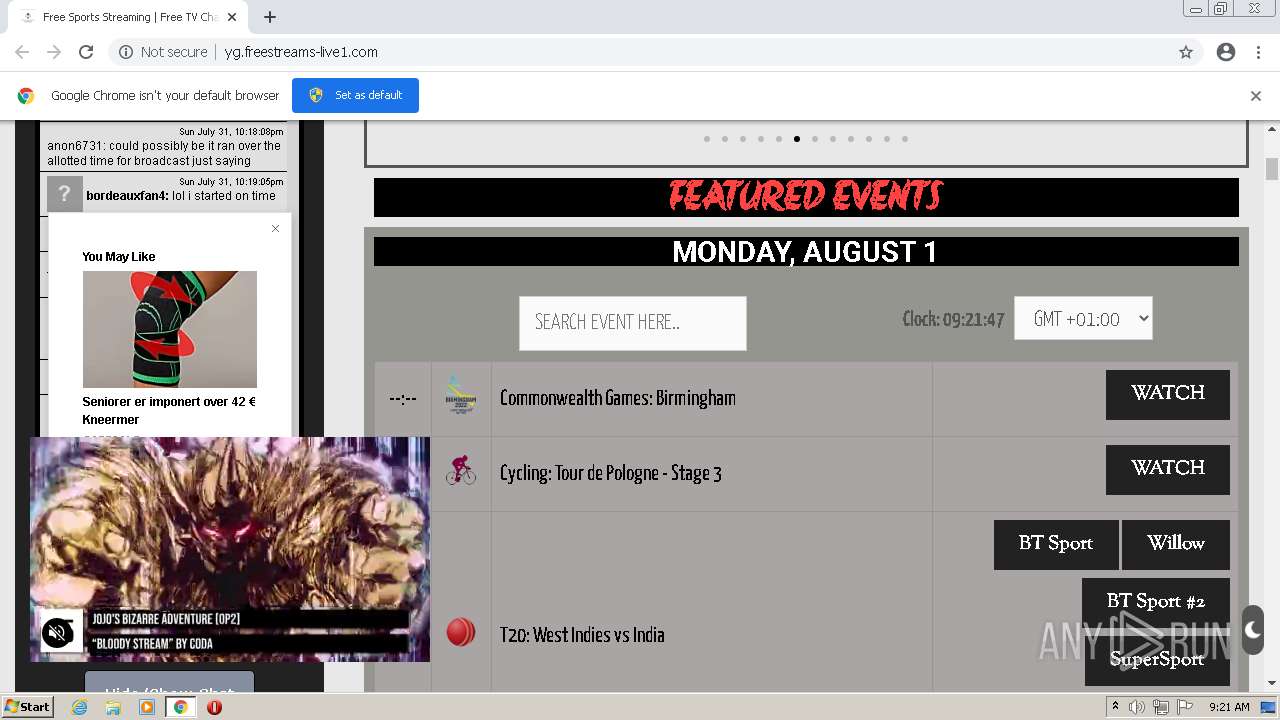
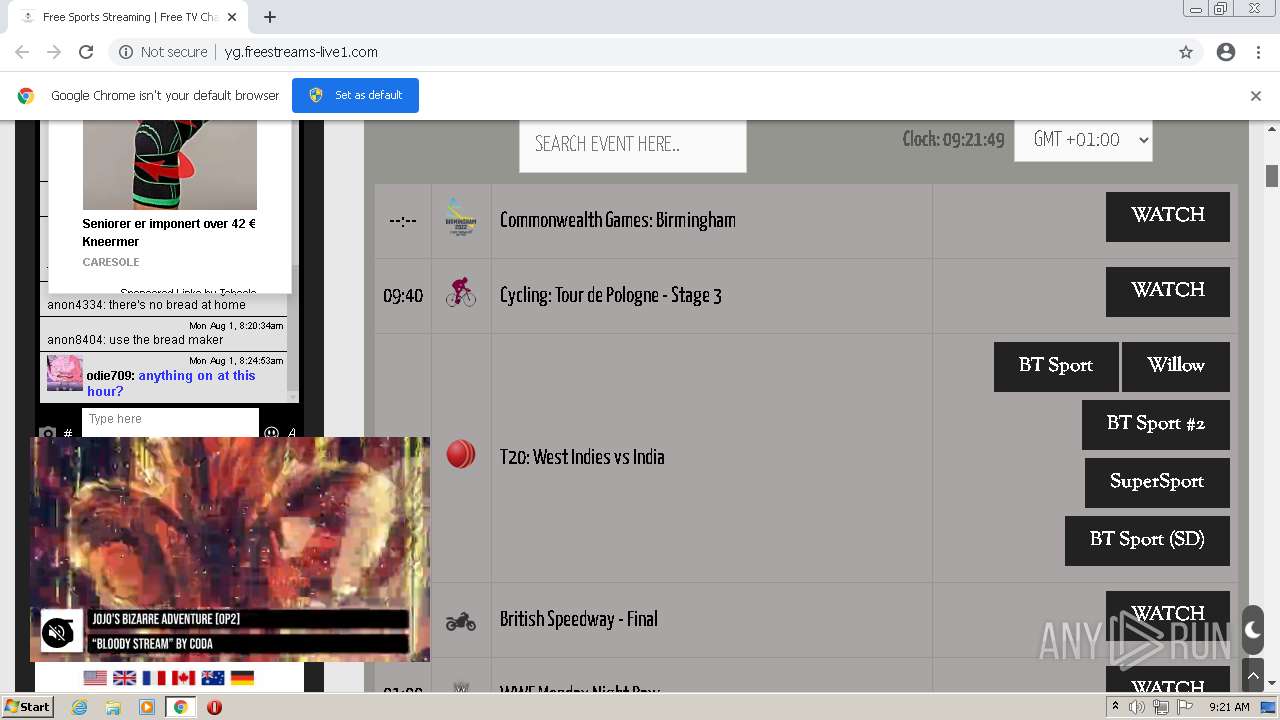
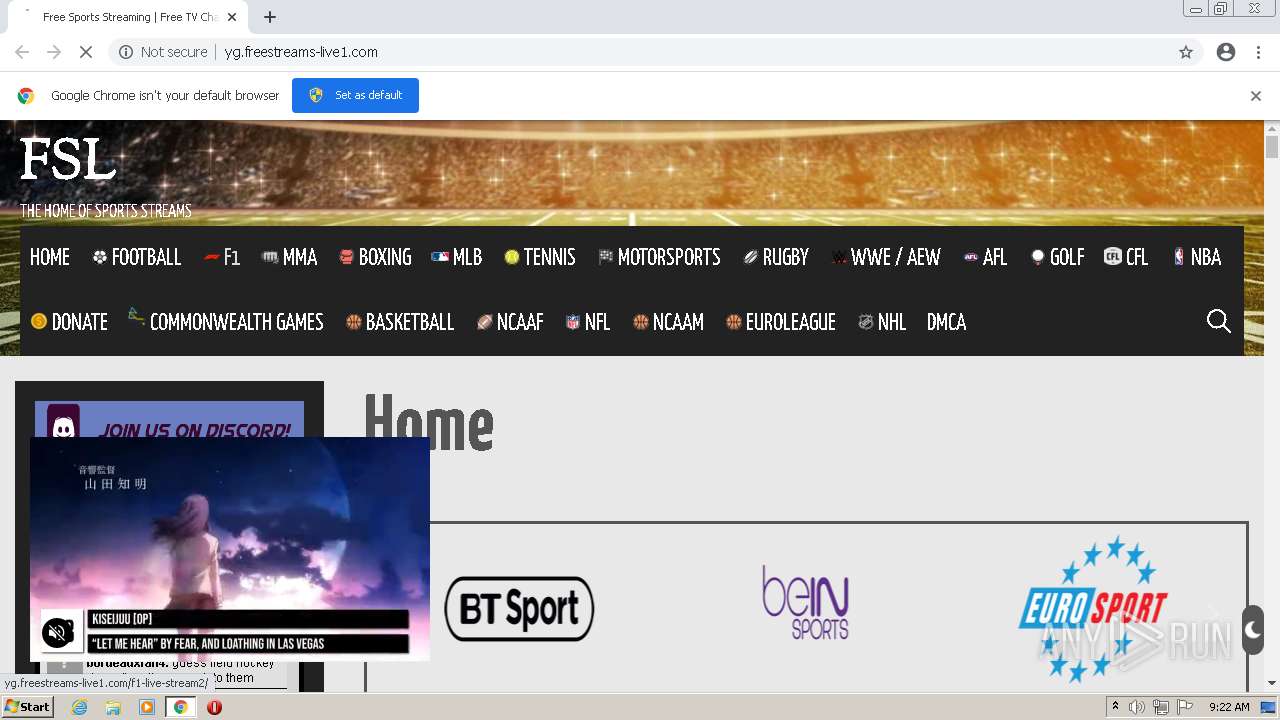
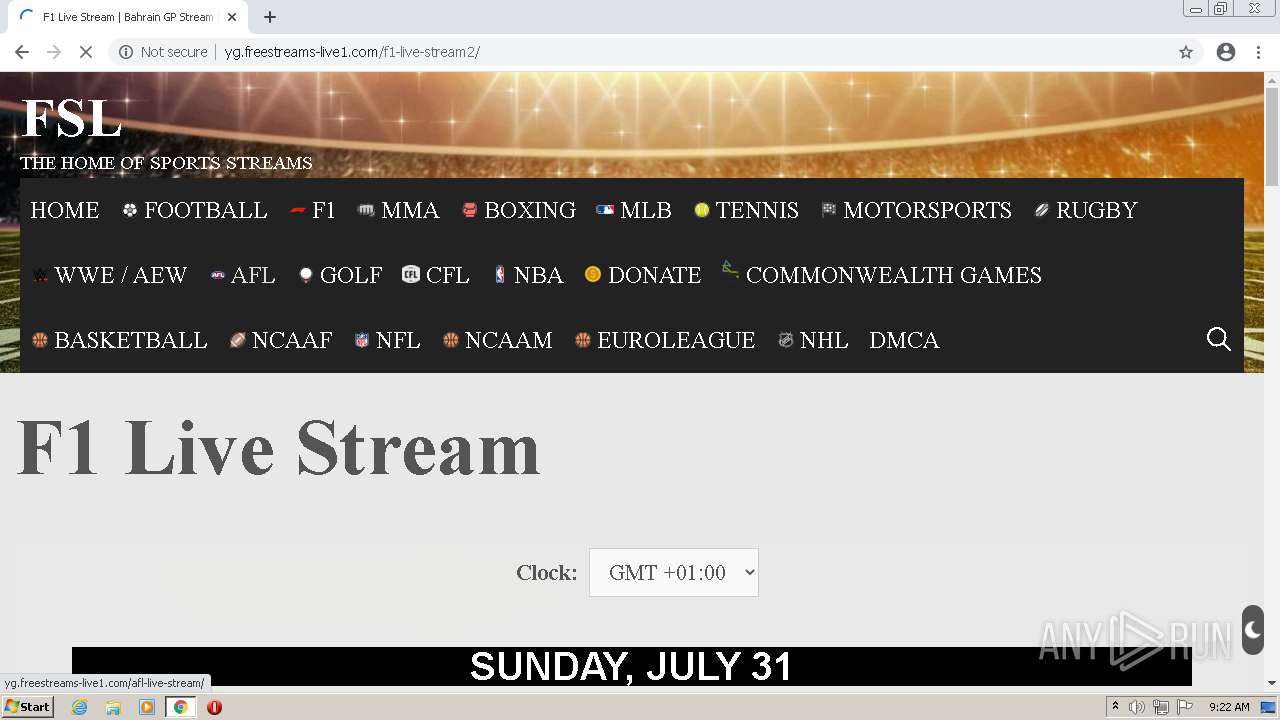
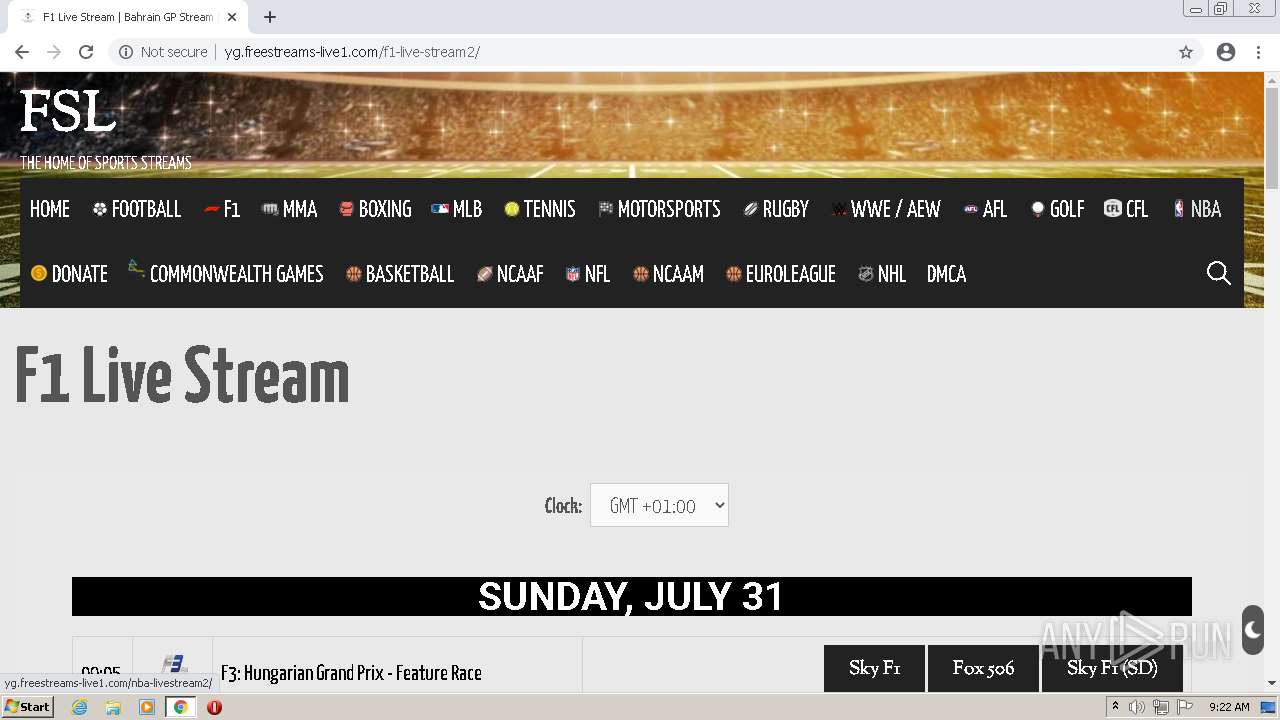
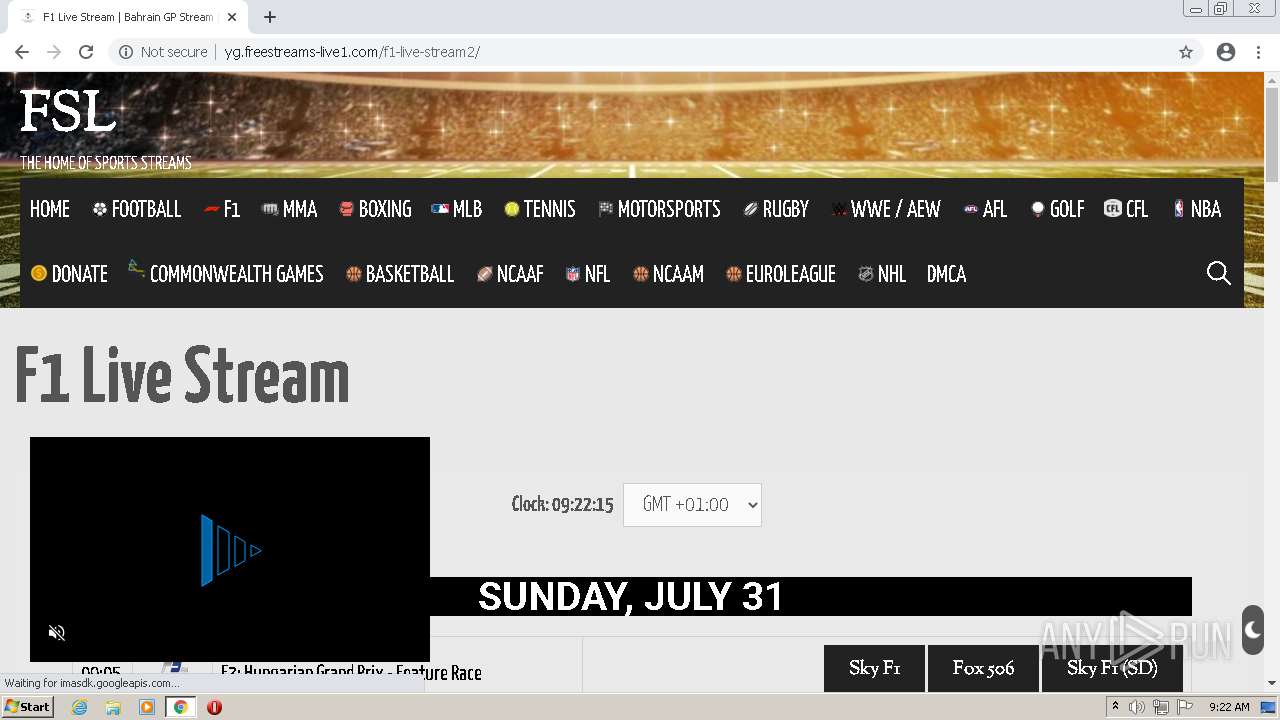
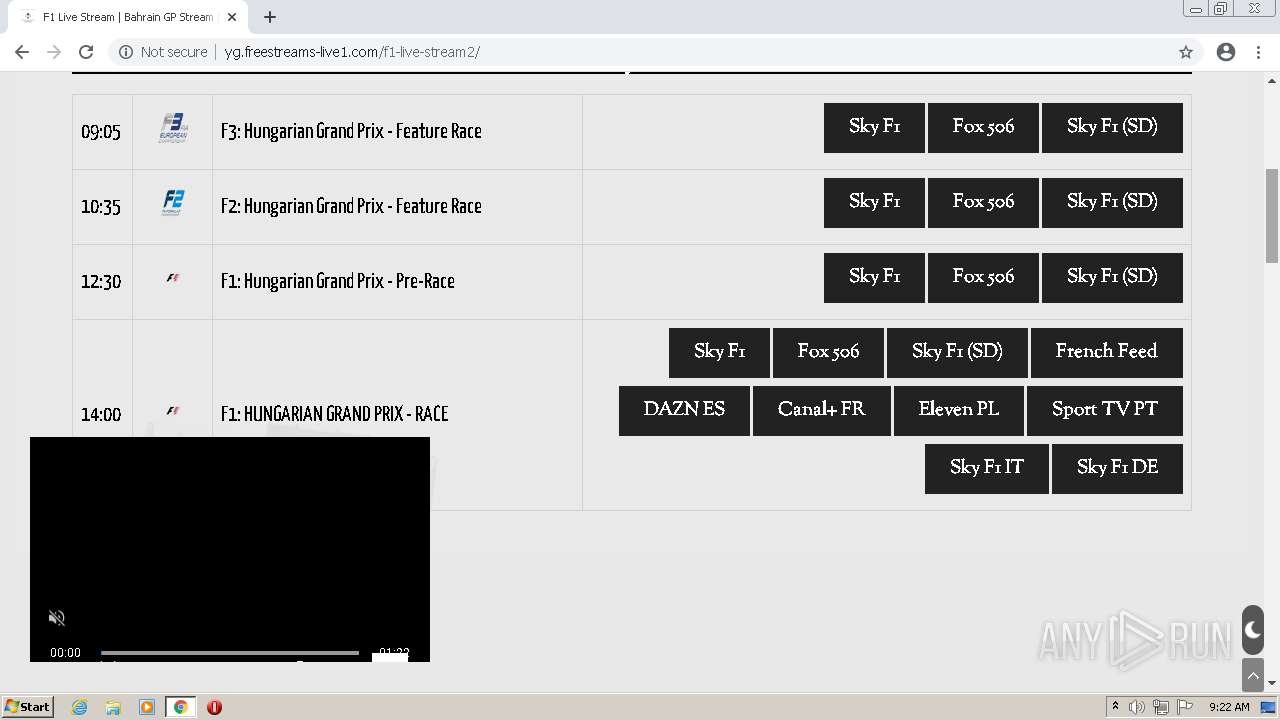
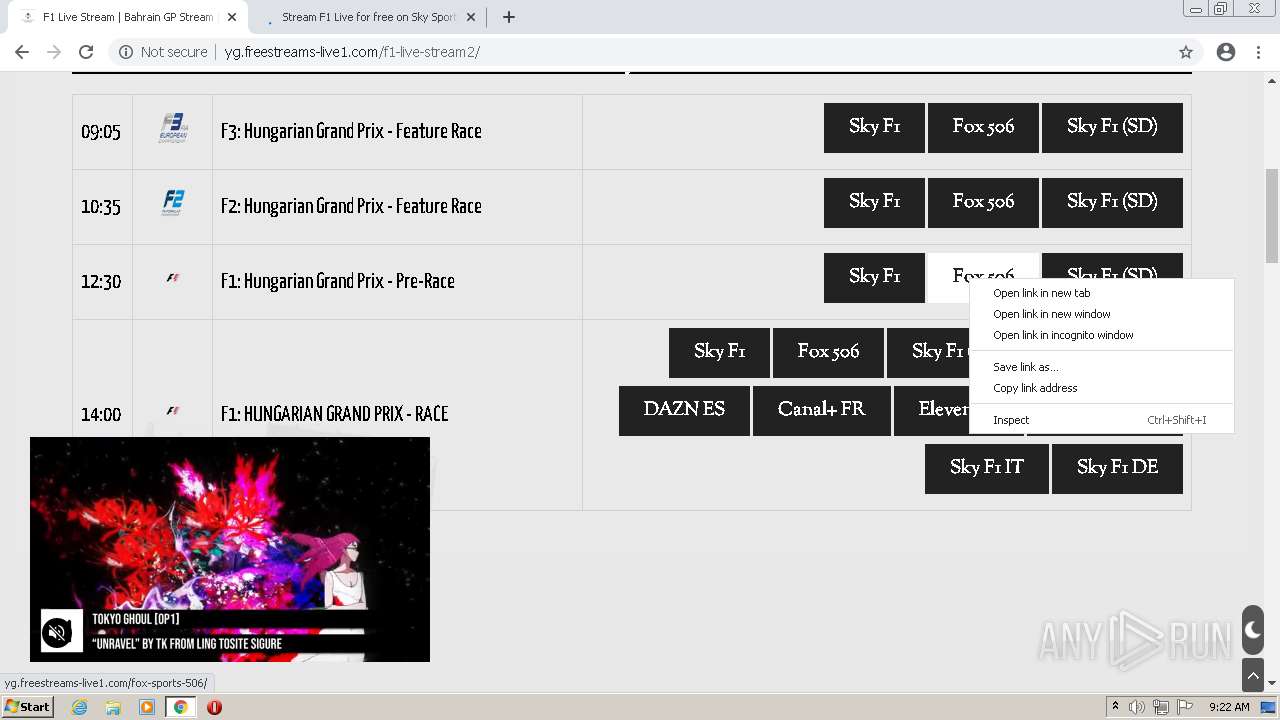
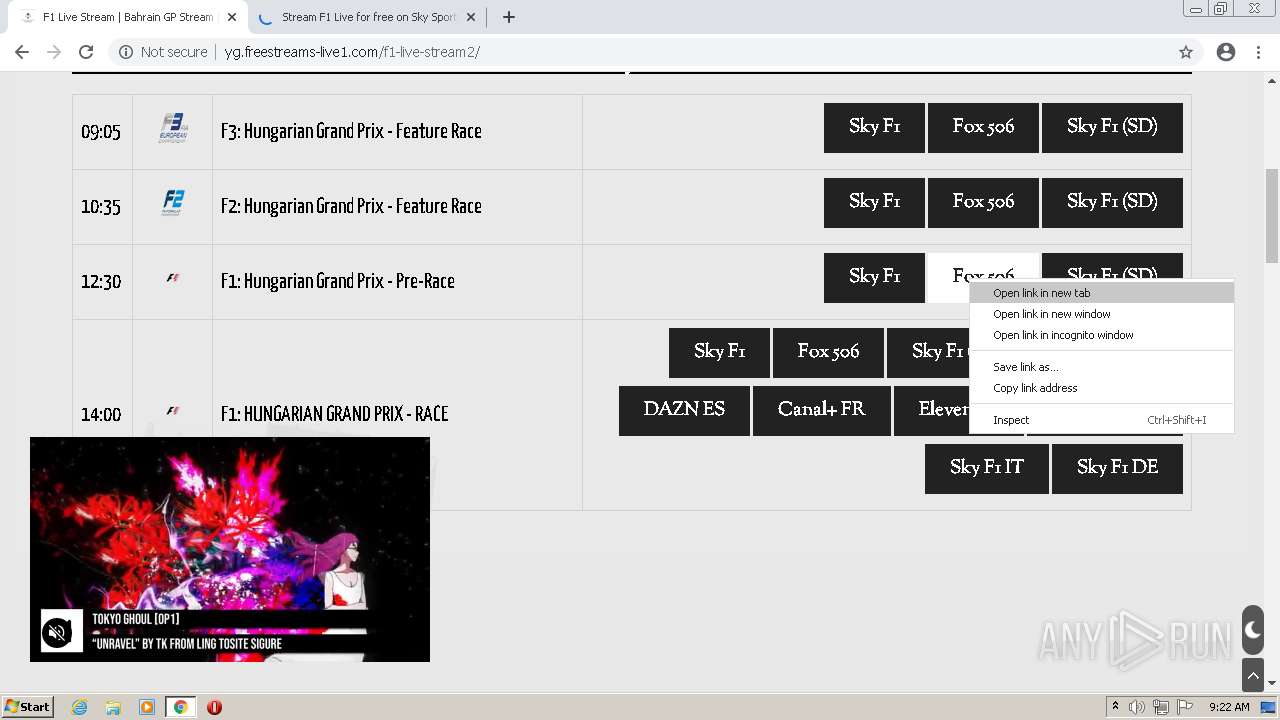
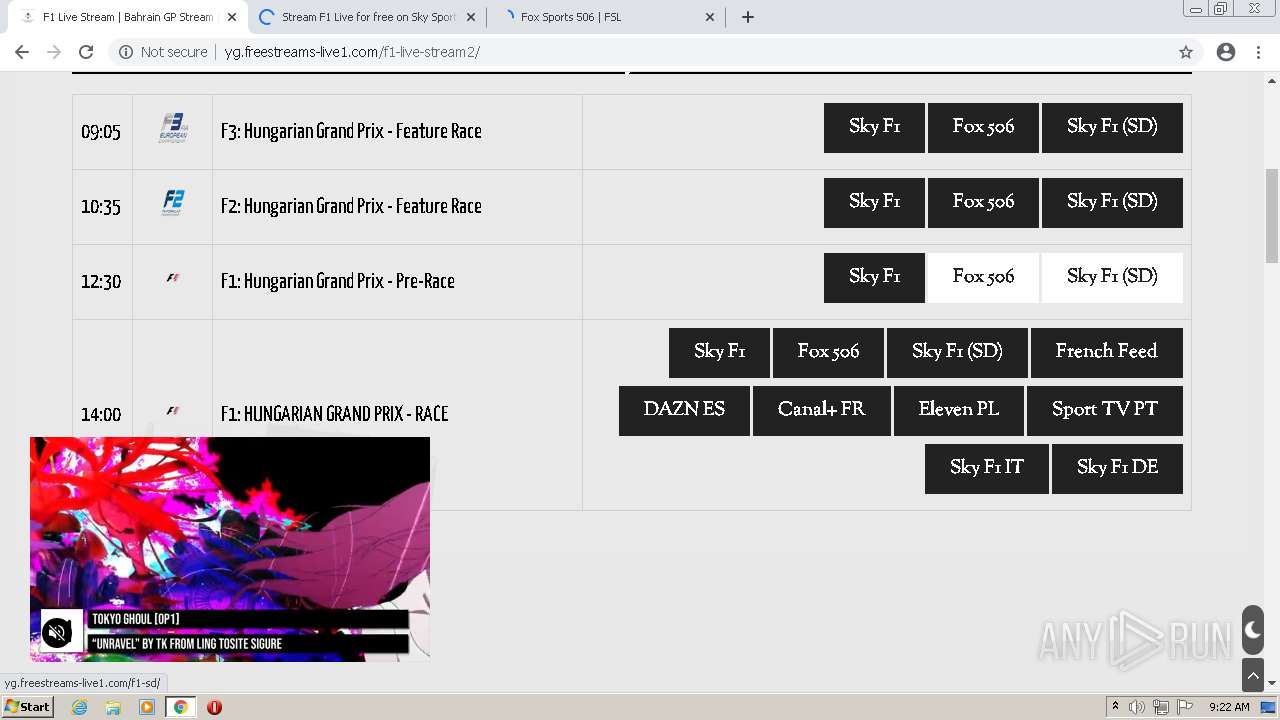
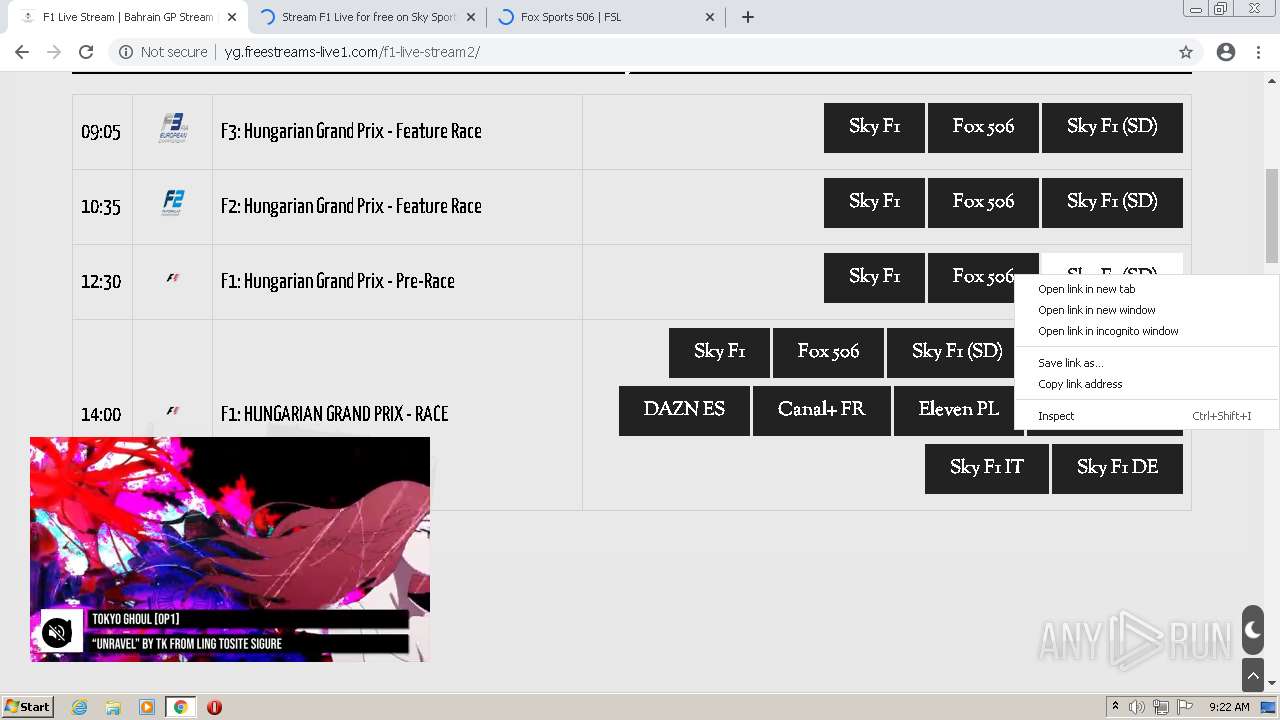
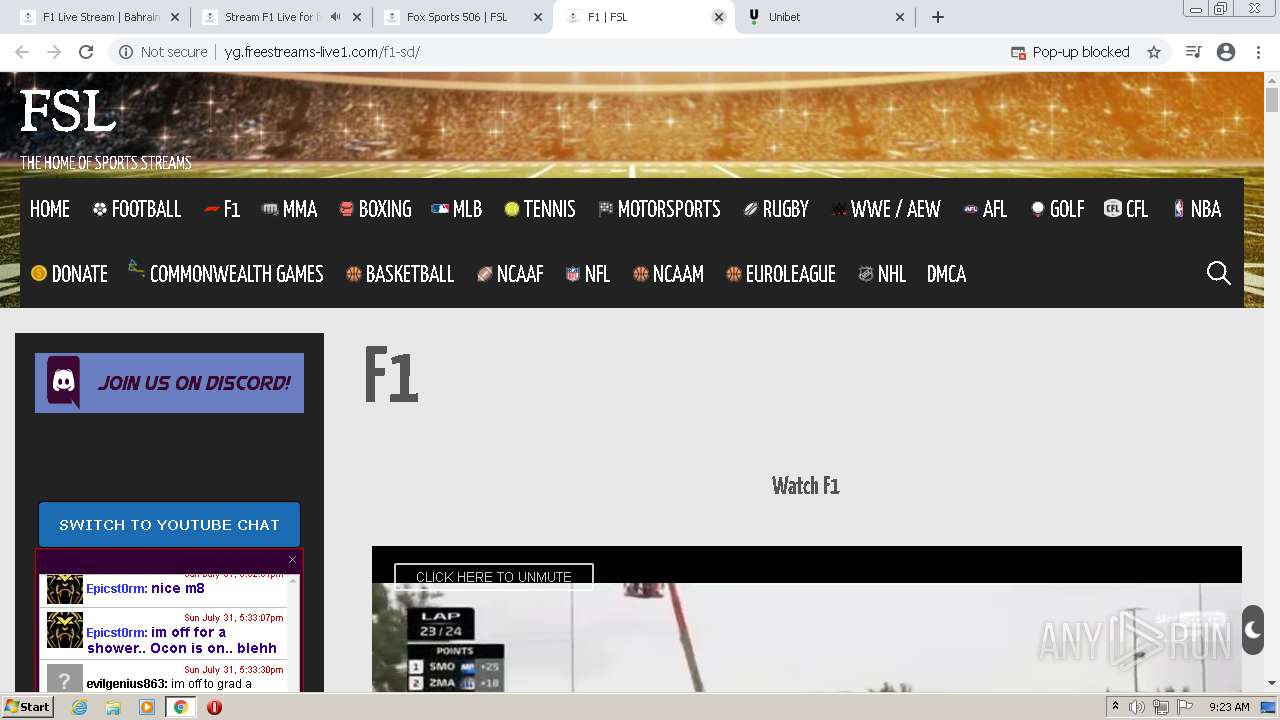
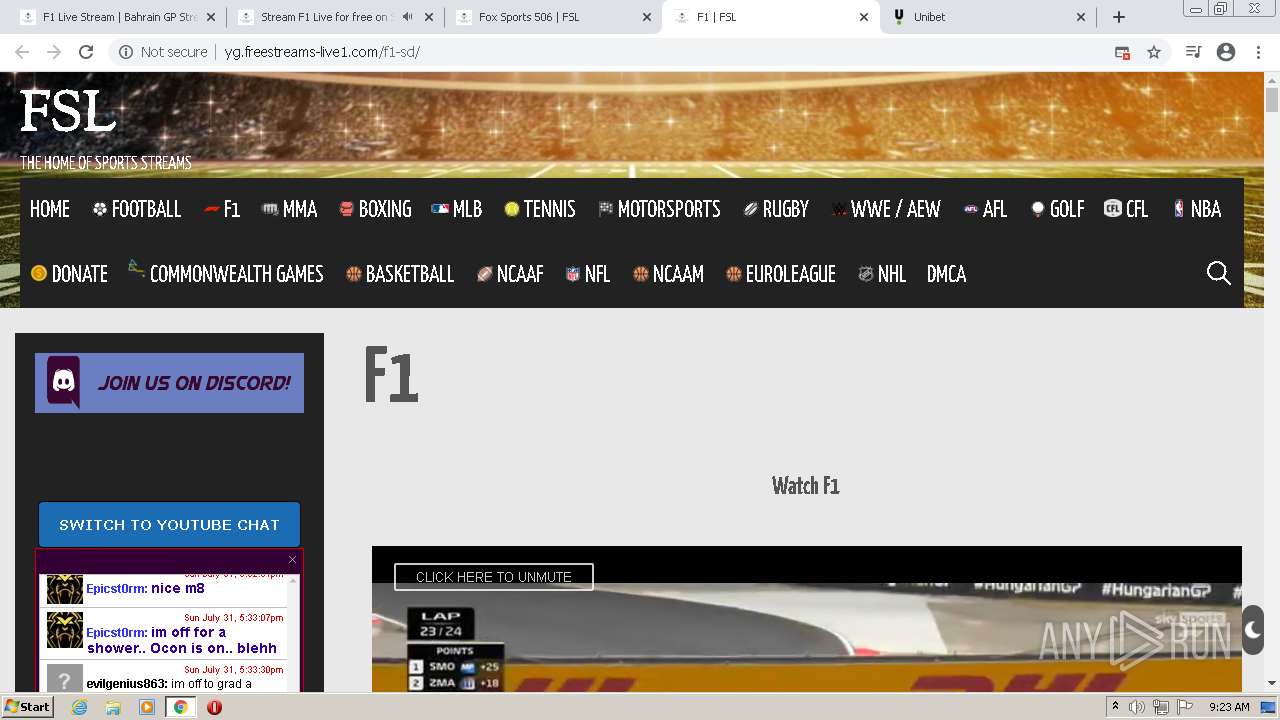
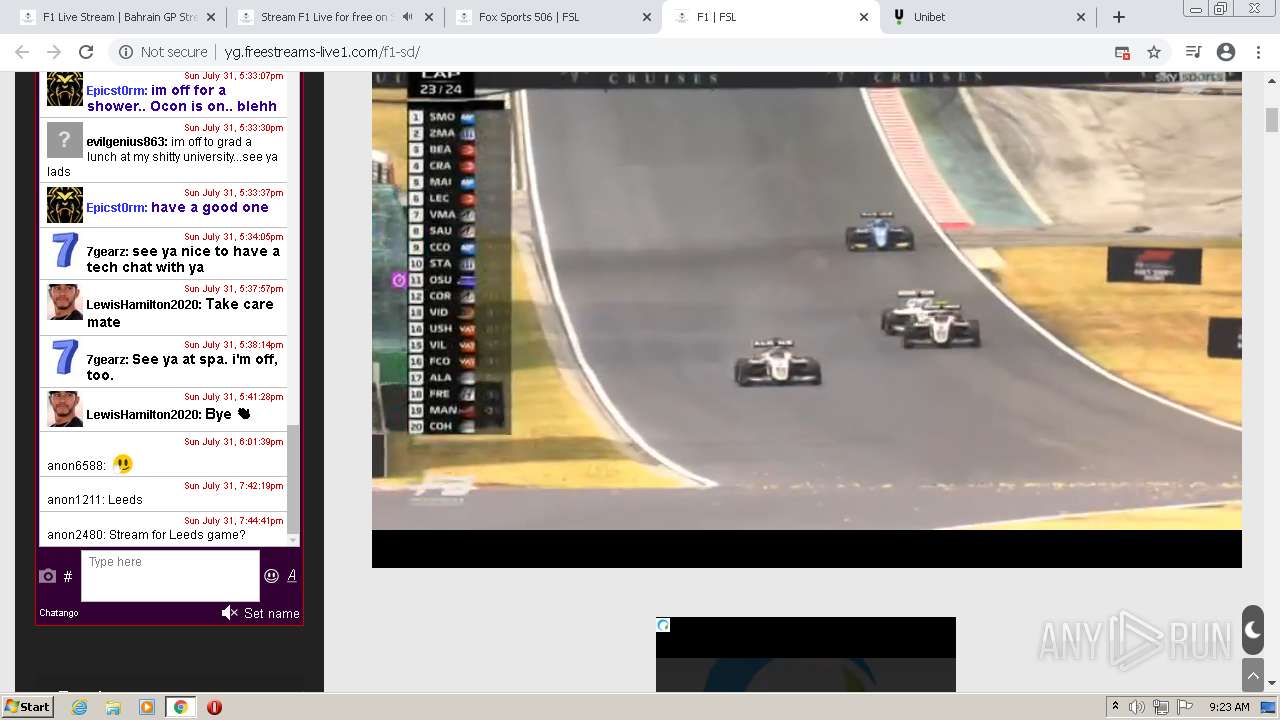
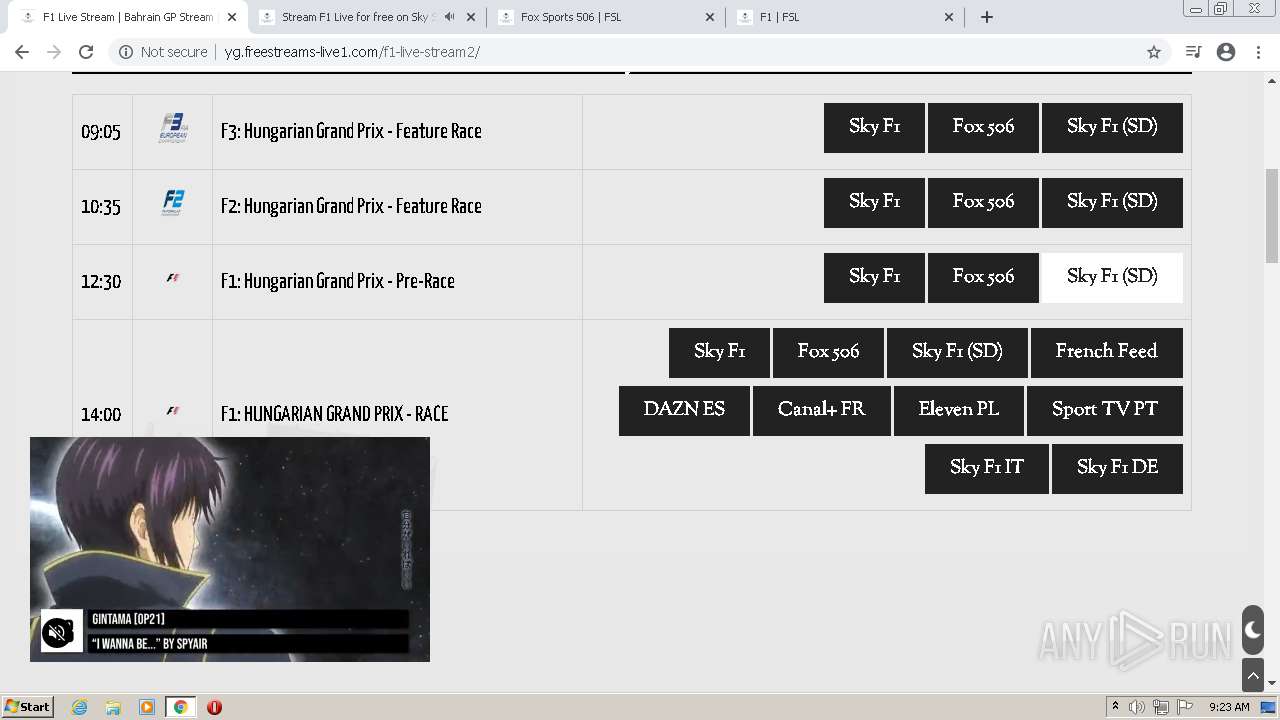
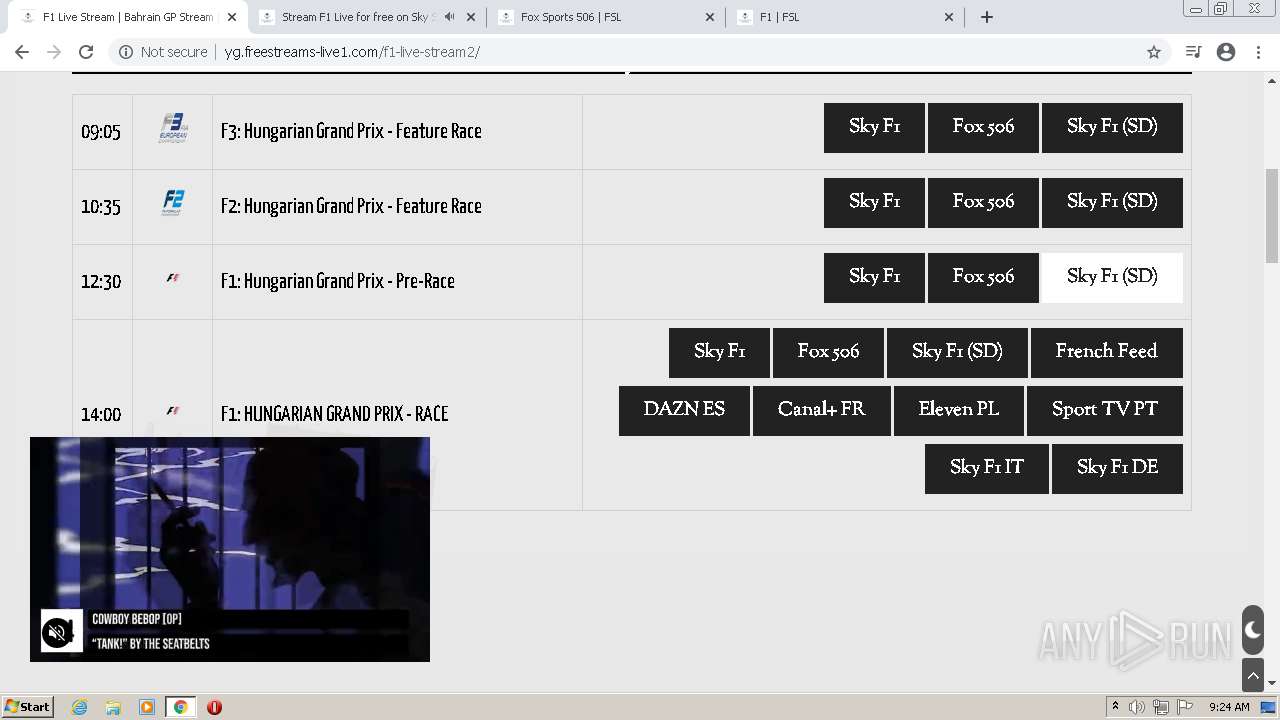
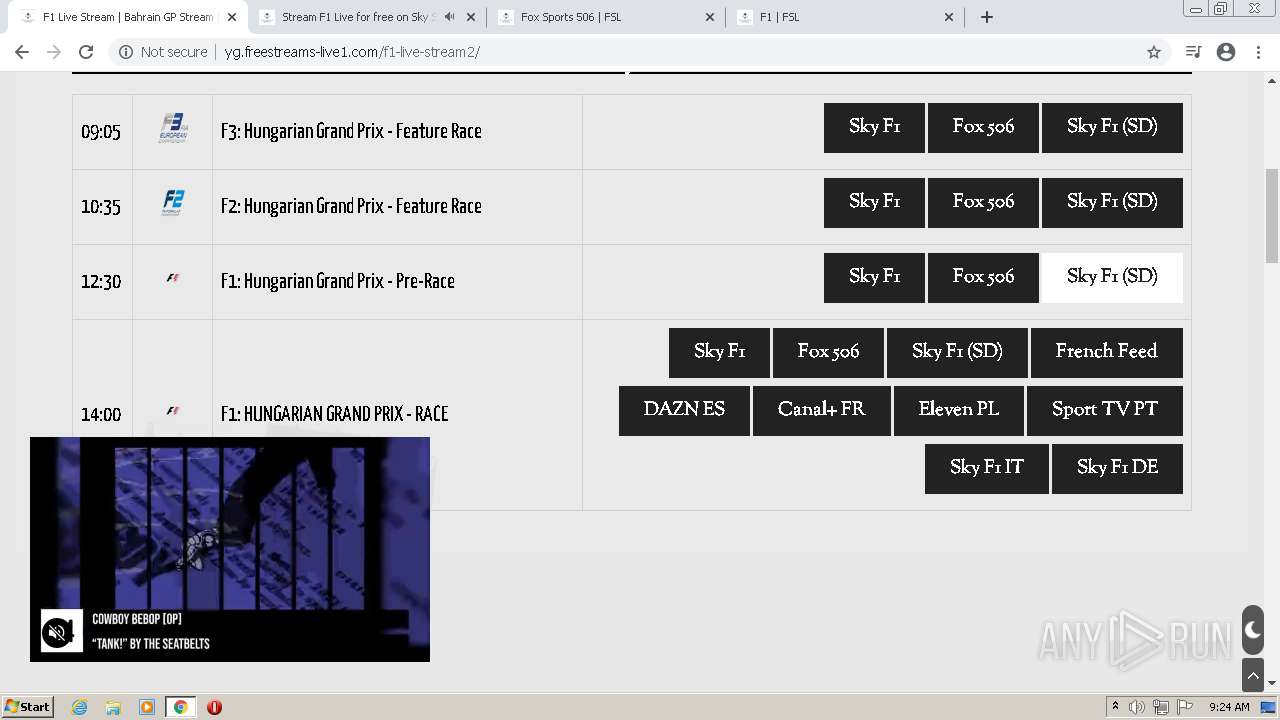
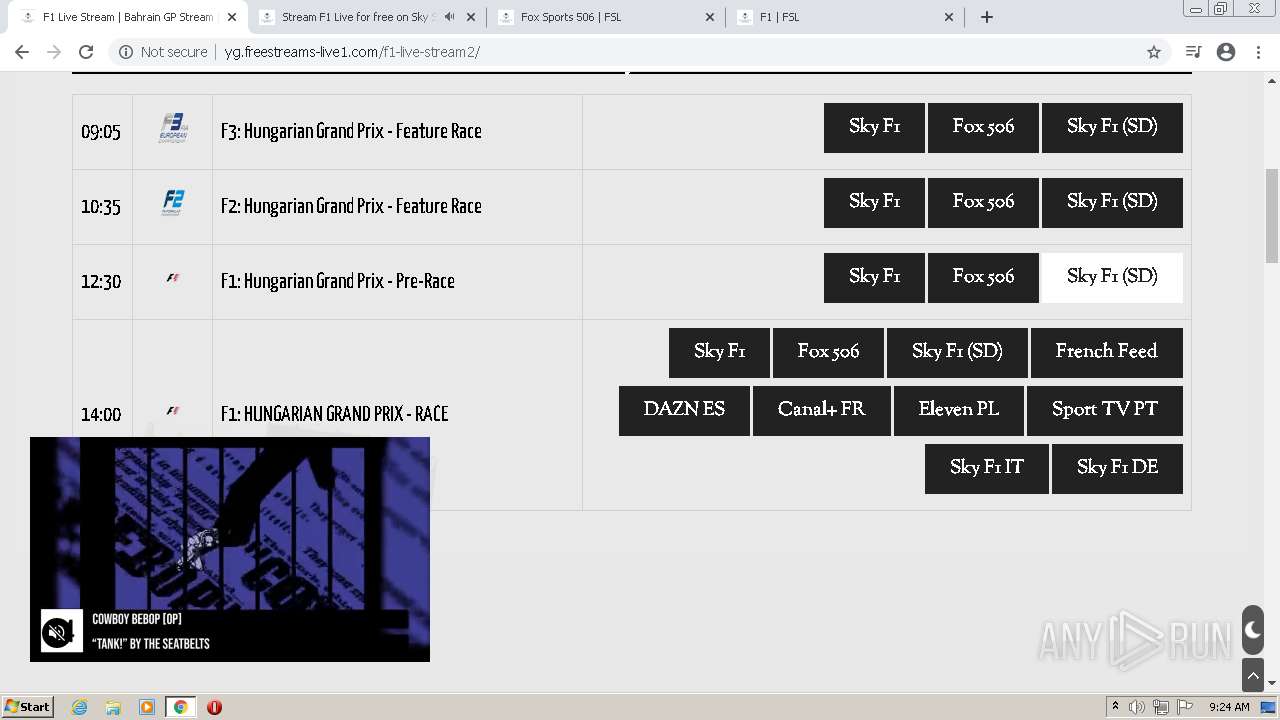
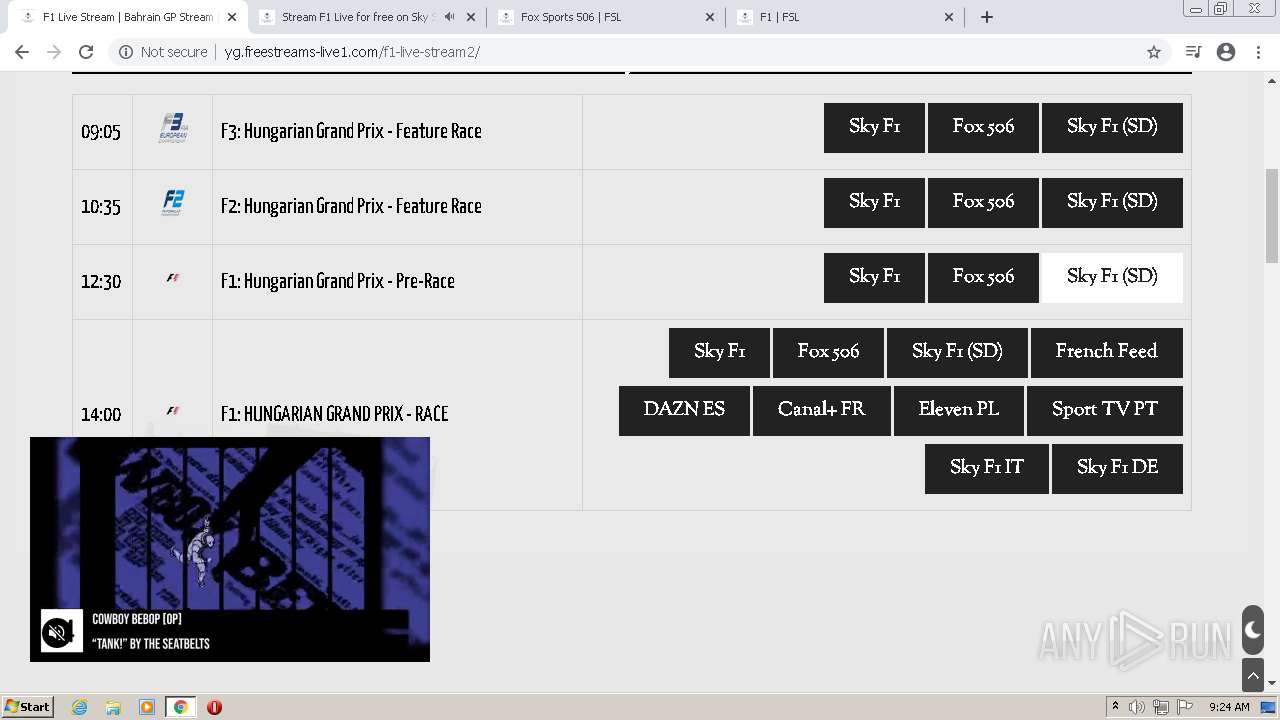
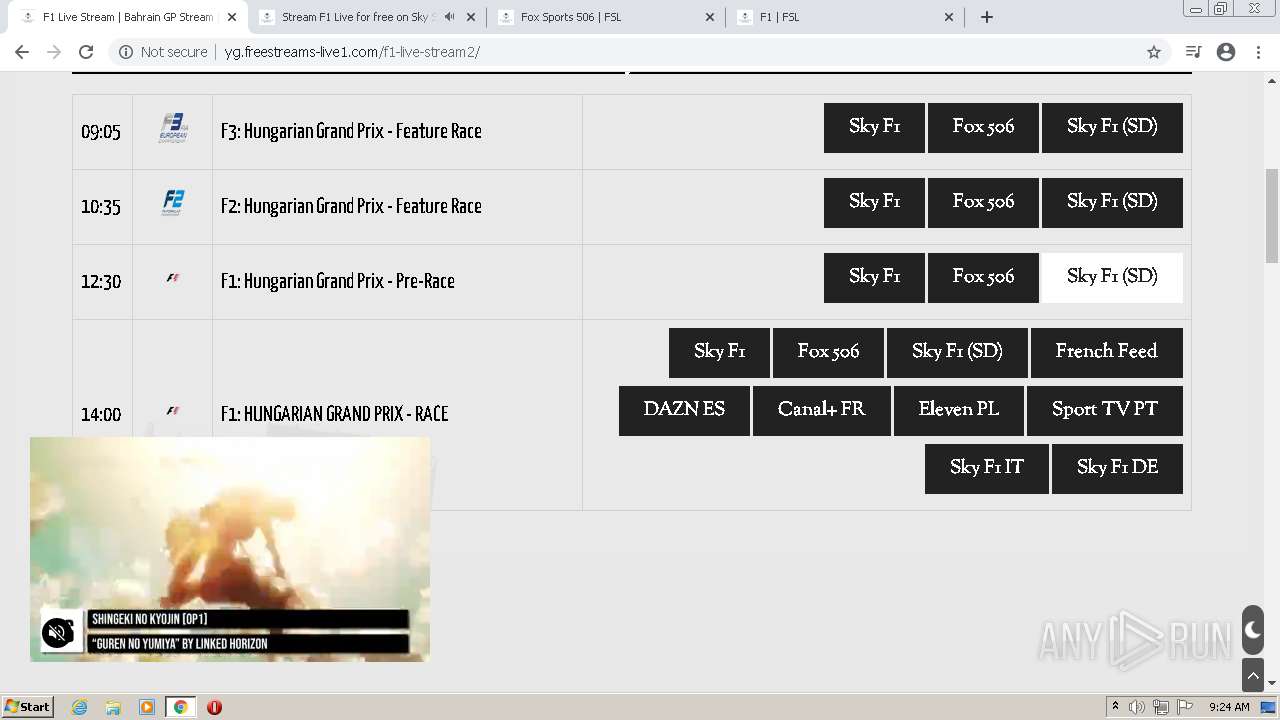
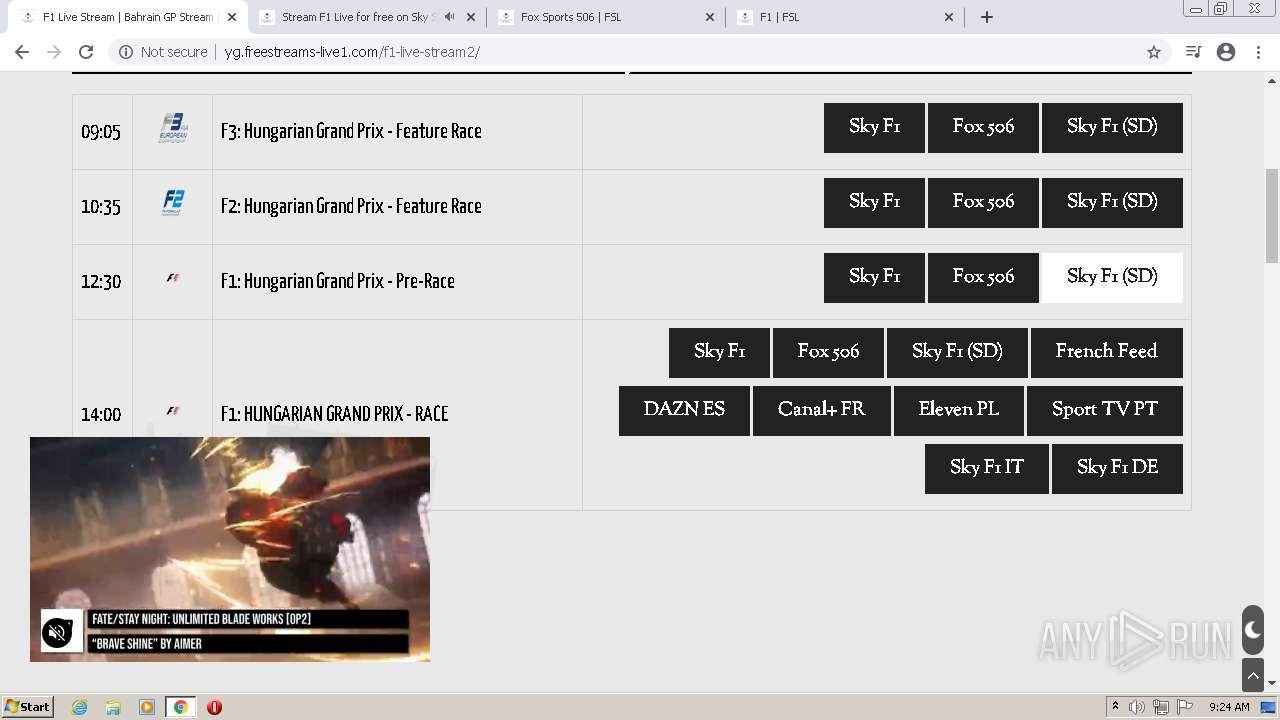
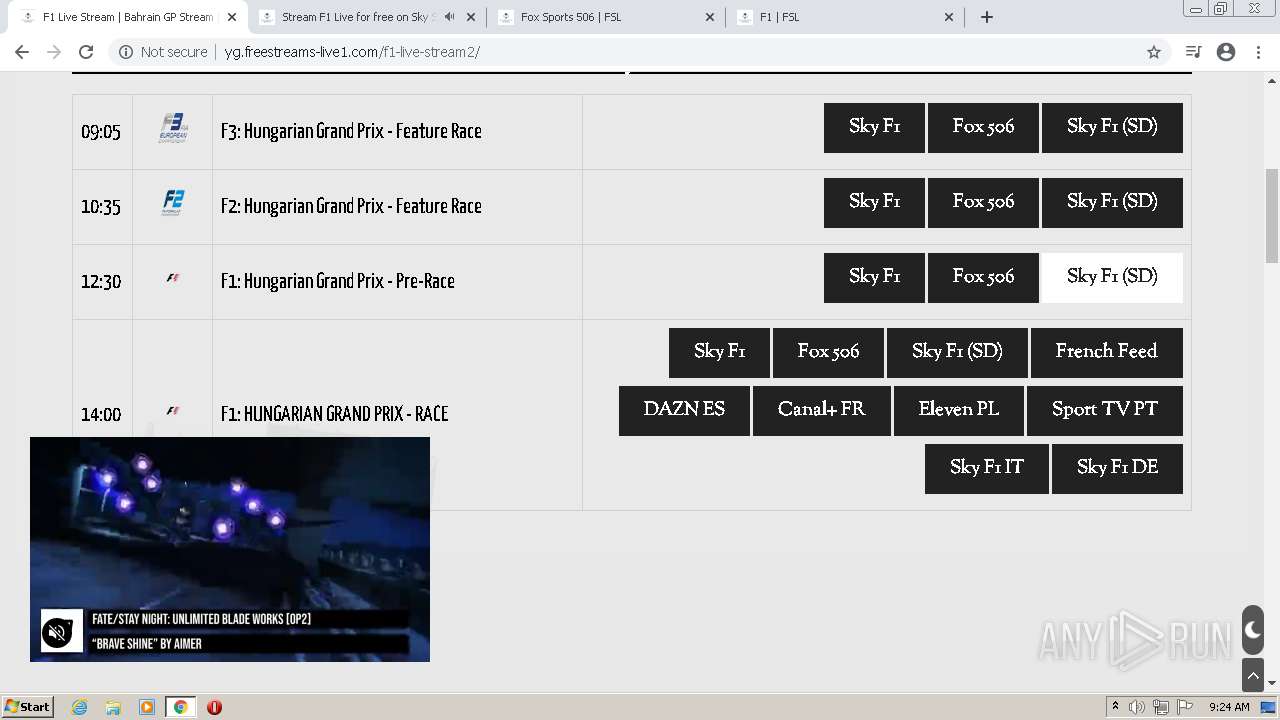
| URL: | https://freestreams-live1.com |
| Full analysis: | https://app.any.run/tasks/c9b98fa3-6145-48e0-b33e-6ed24ed92052 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2022, 08:19:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 398FD1D5B1C1C90FF30D4F091C58320D |
| SHA1: | 908886482BF3499C58C608B330671DEAF71534AE |
| SHA256: | 26854DE34936EA5B24A36A27F48FEA5A7009A2D1052B487FC414FF1A91E5AA38 |
| SSDEEP: | 3:N8iRRcJMMtn:2iTcJMgn |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1416)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3704)
Executable content was dropped or overwritten
- chrome.exe (PID: 1416)
Drops a file with a compile date too recent
- chrome.exe (PID: 1416)
Checks for external IP
- chrome.exe (PID: 3628)
INFO
Checks supported languages
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 780)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 116)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 1416)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1256)
- chrome.exe (PID: 1016)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2024)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 852)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 772)
- chrome.exe (PID: 1456)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3428)
Reads the computer name
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 780)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 116)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 2580)
Reads settings of System Certificates
- chrome.exe (PID: 3628)
Application launched itself
- chrome.exe (PID: 3704)
Reads the date of Windows installation
- chrome.exe (PID: 3812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
53
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4304 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3992185220629806008,13549850247360303811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 732
Read events
23 562
Write events
165
Delete events
5
Modification events
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
286
Text files
180
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62E78C96-E78.pma | — | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8ec4259e-e8a3-4d43-abb9-a7b0b3561da5.tmp | text | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF104ece.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF10518d.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\86832436-be7f-4df5-93e3-9034d4de5aba.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF104e51.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
497
TCP/UDP connections
335
DNS requests
174
Threats
743
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
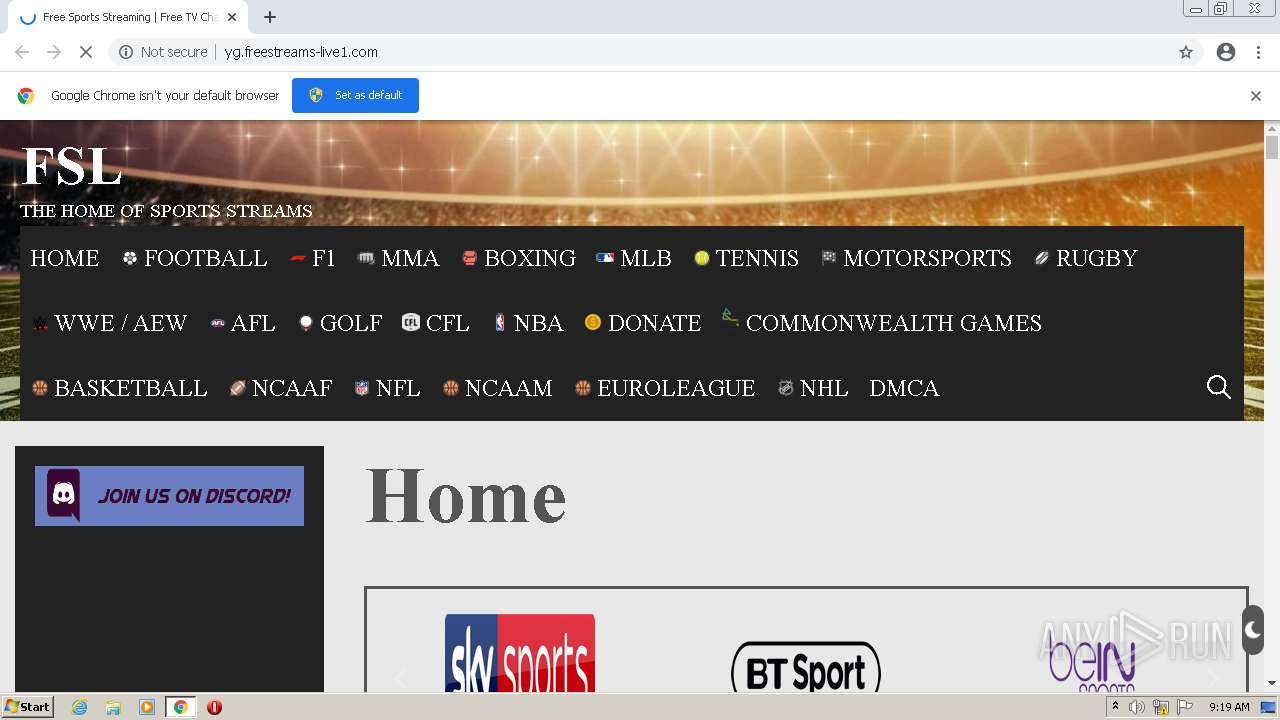
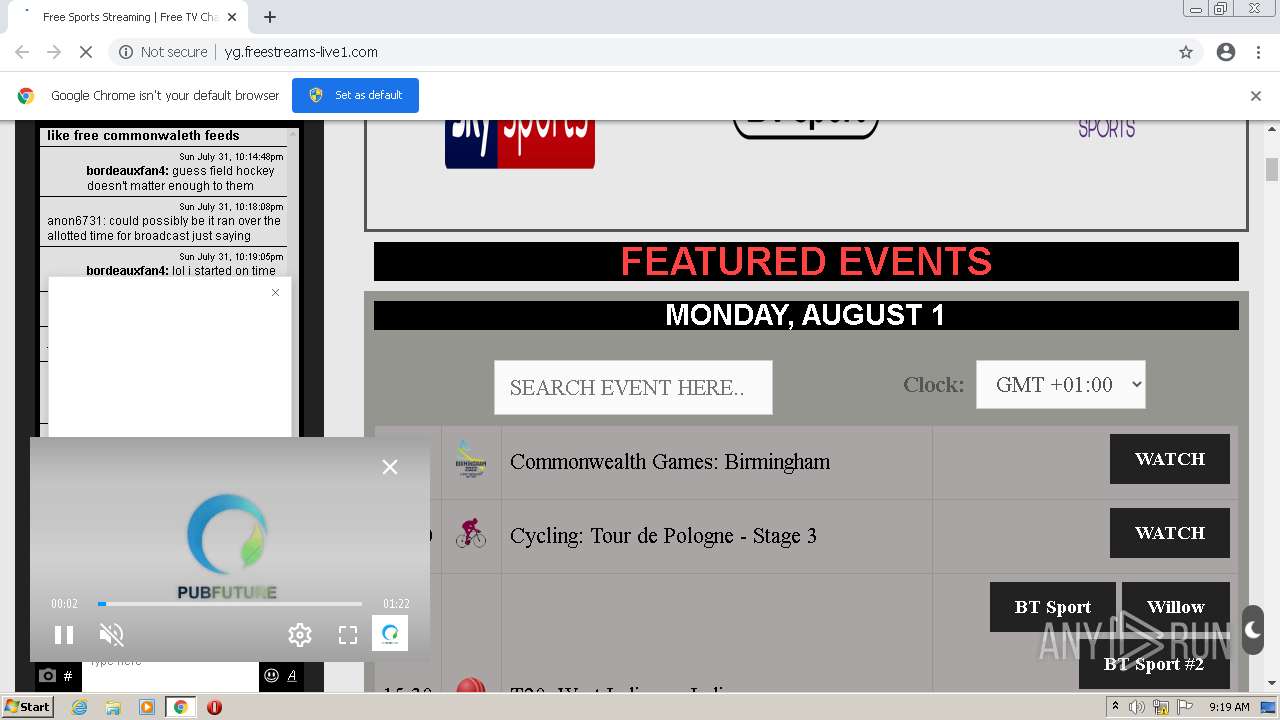
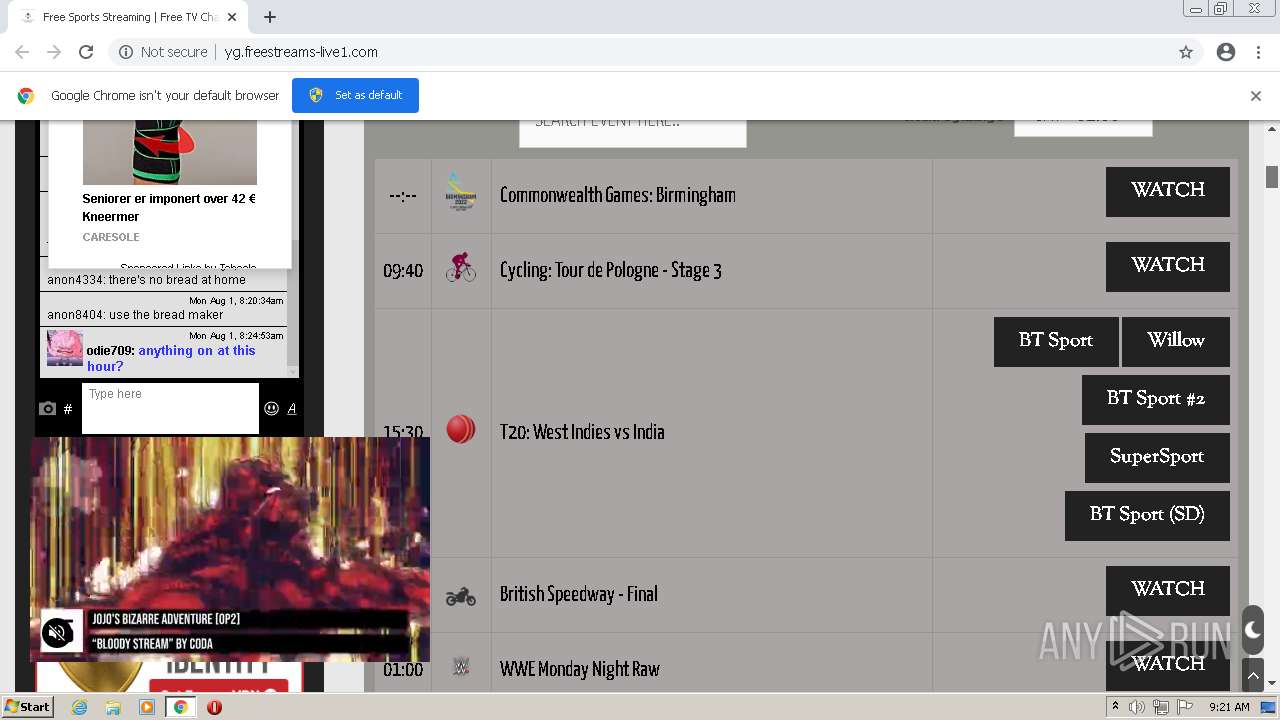
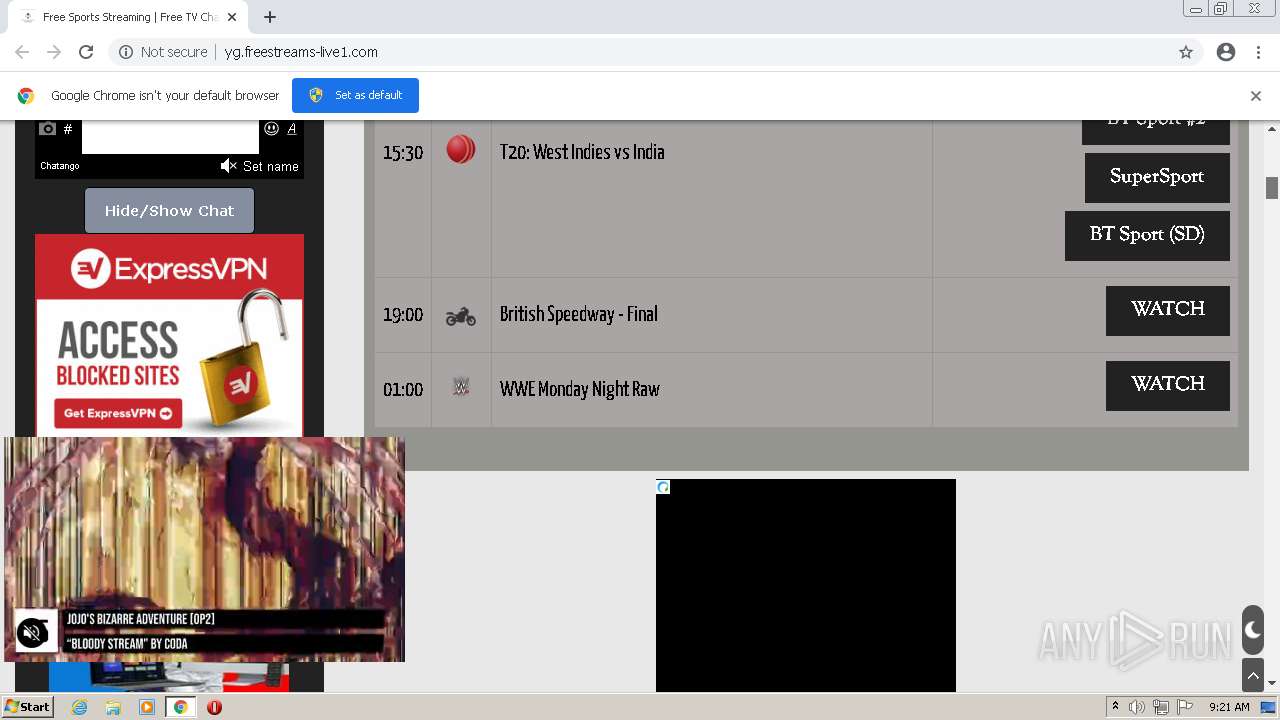
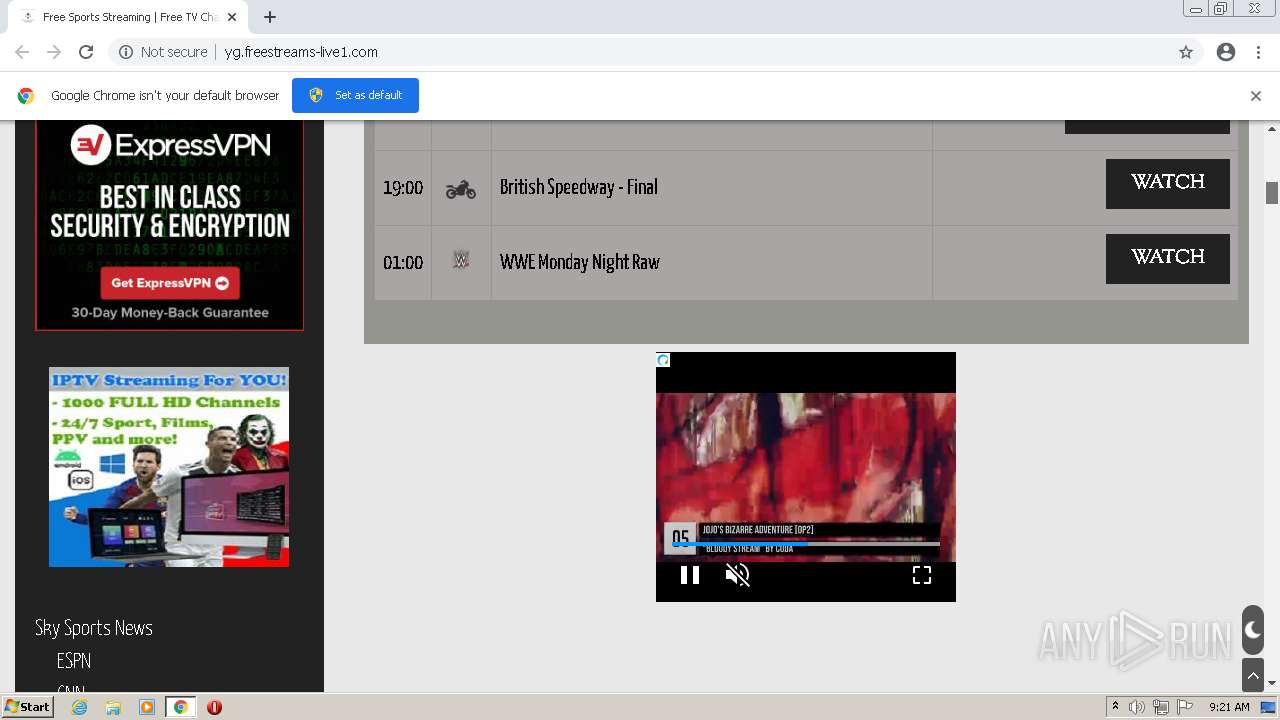
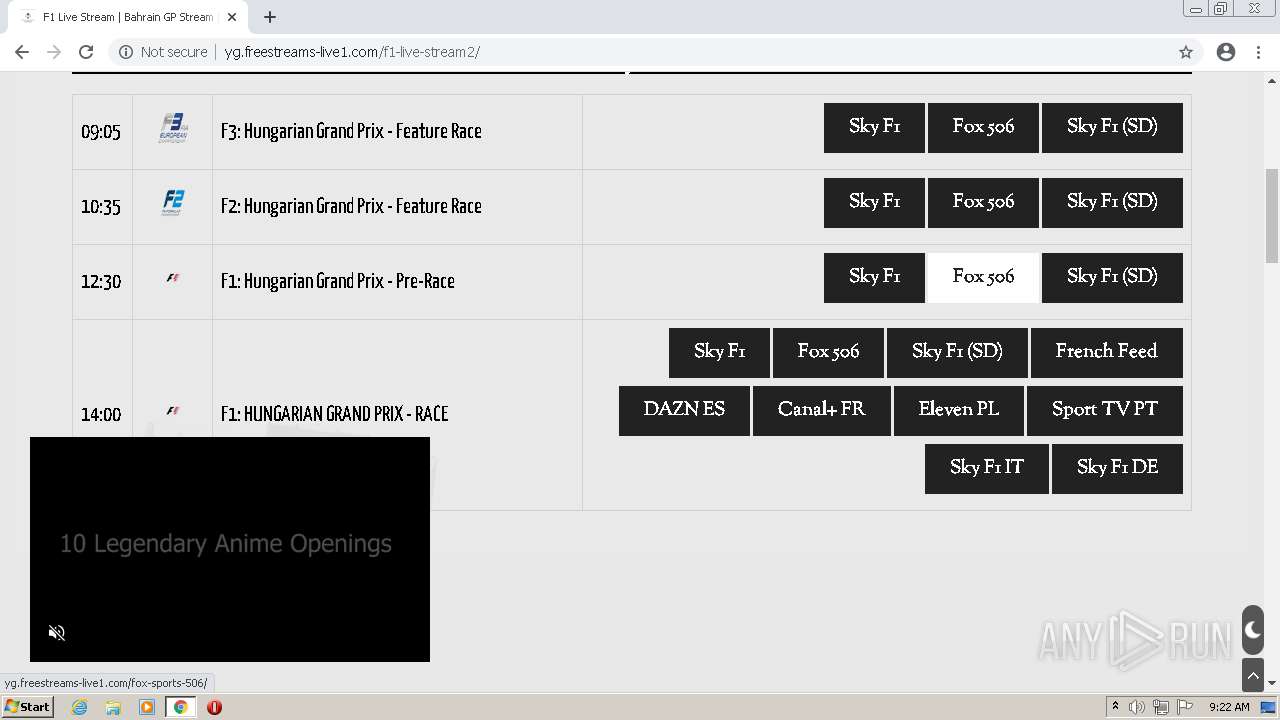
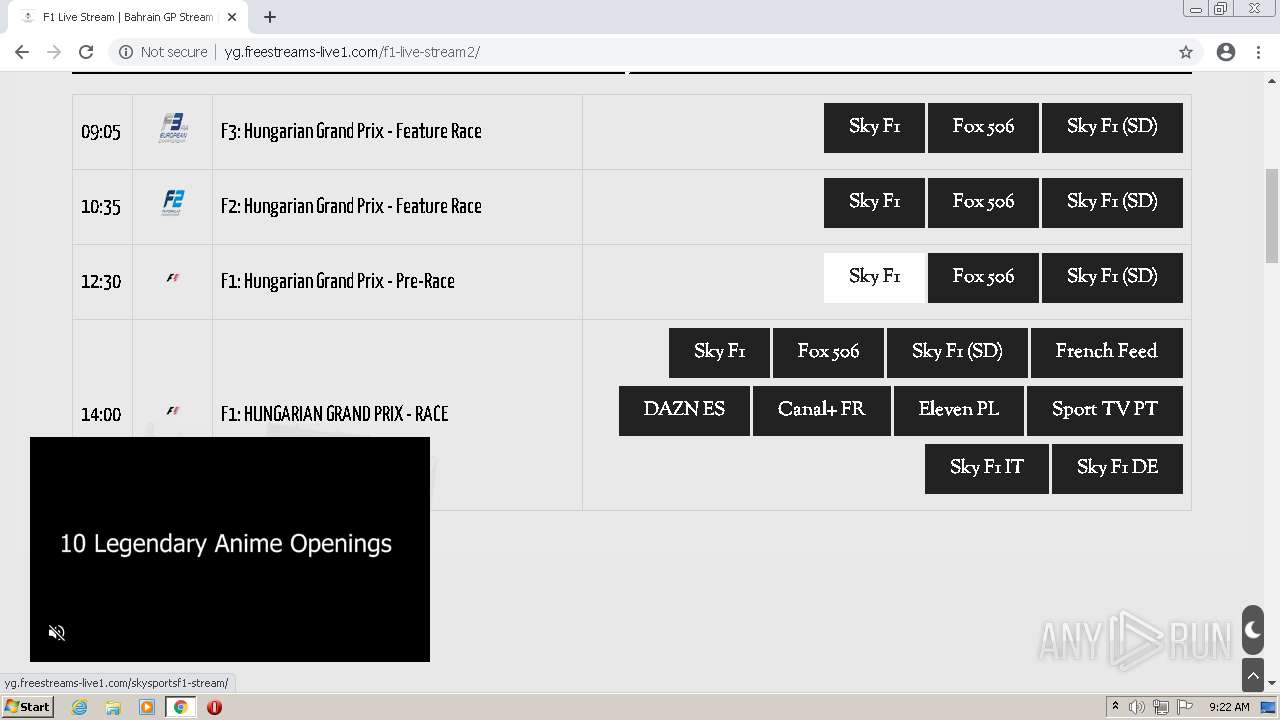
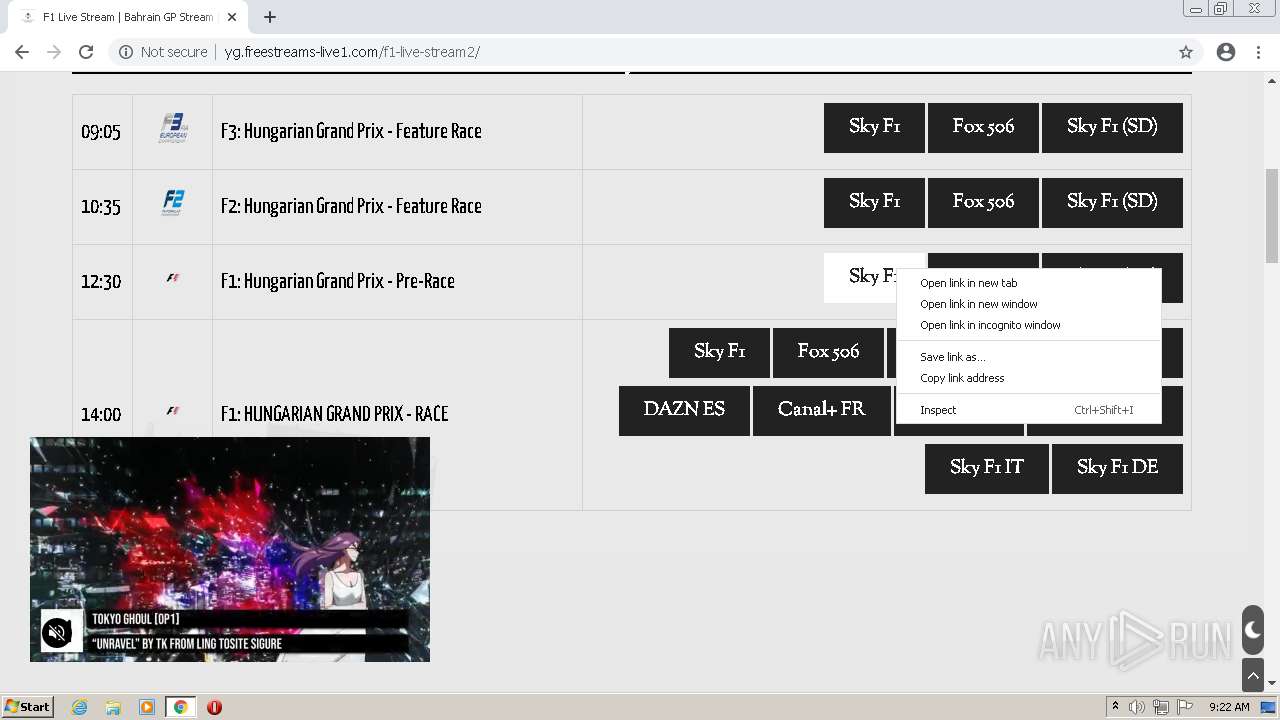
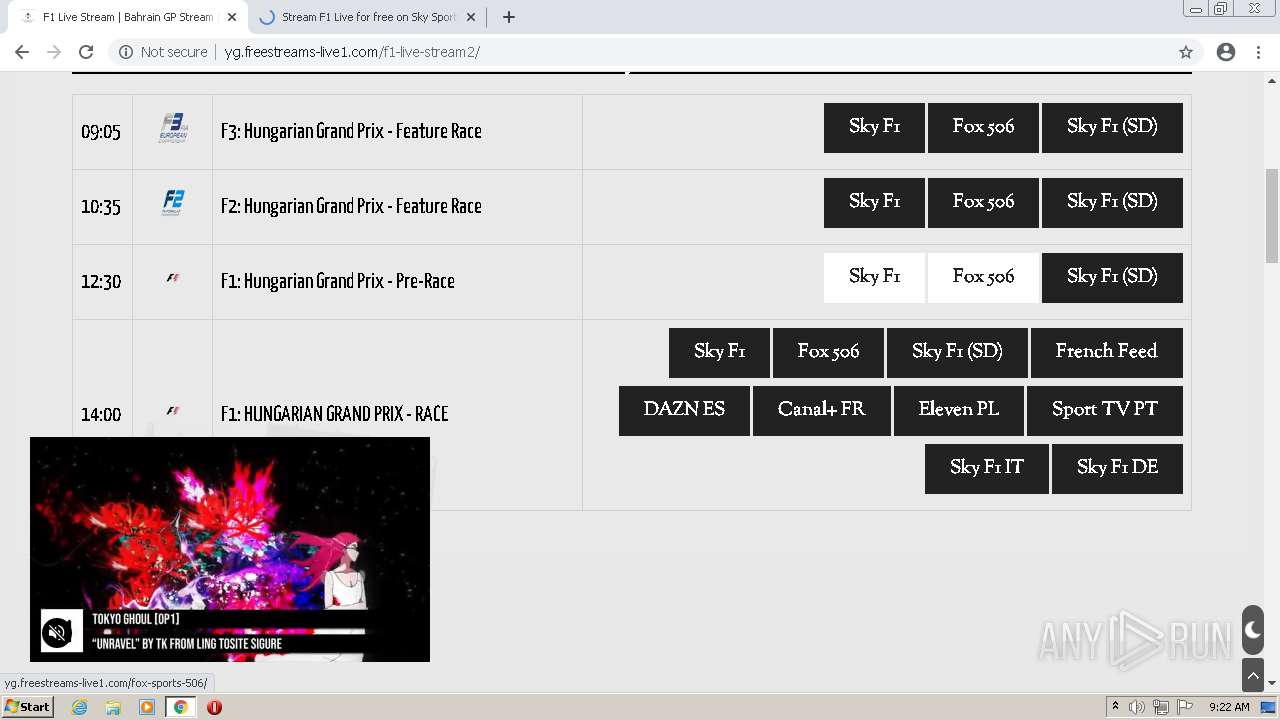
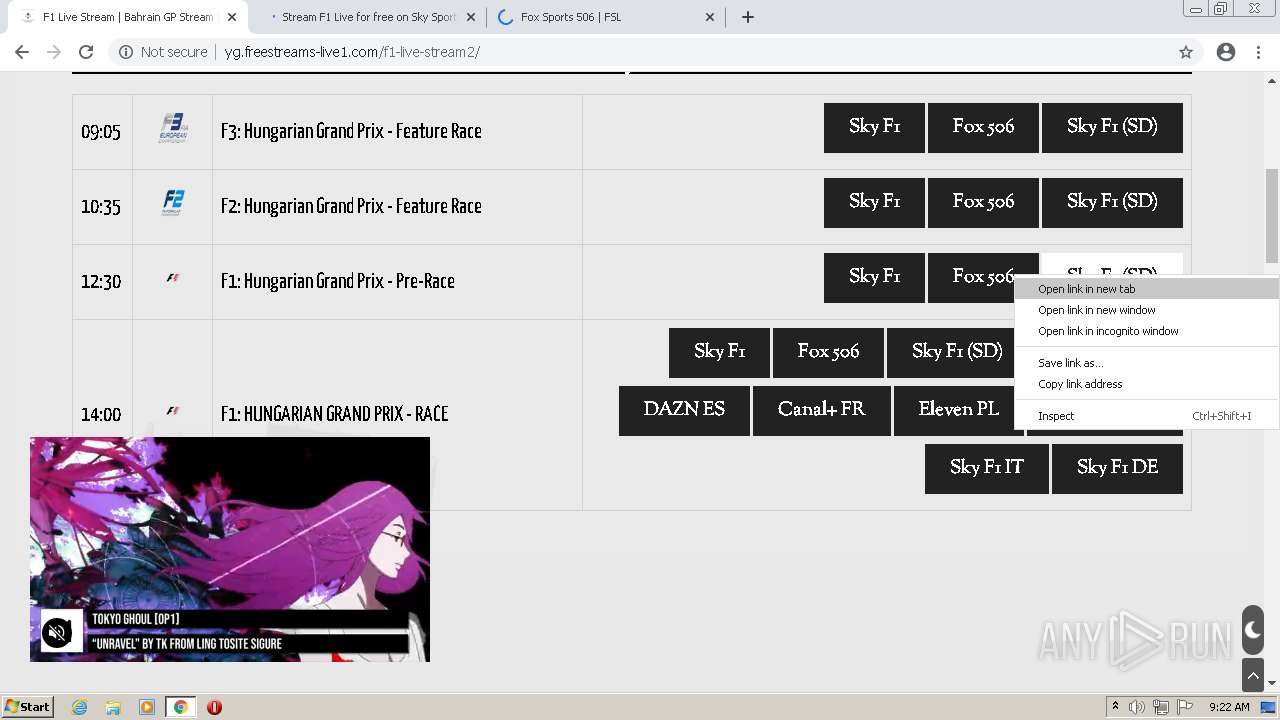
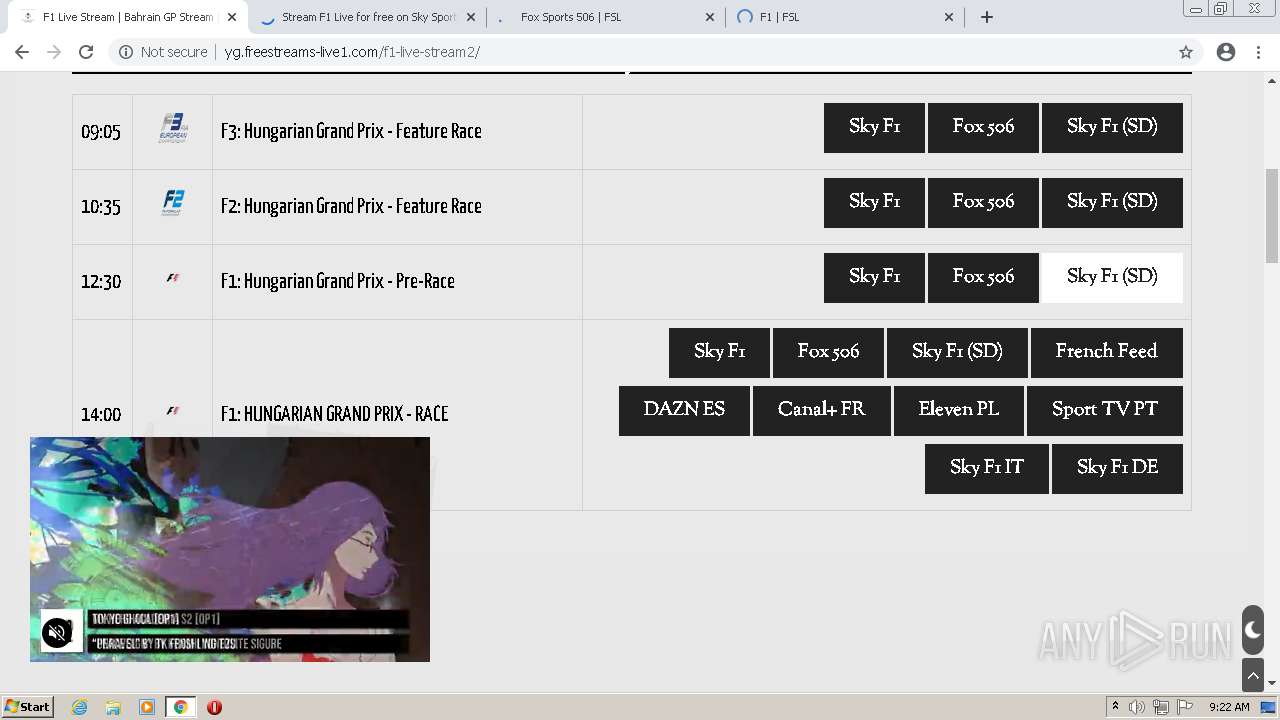
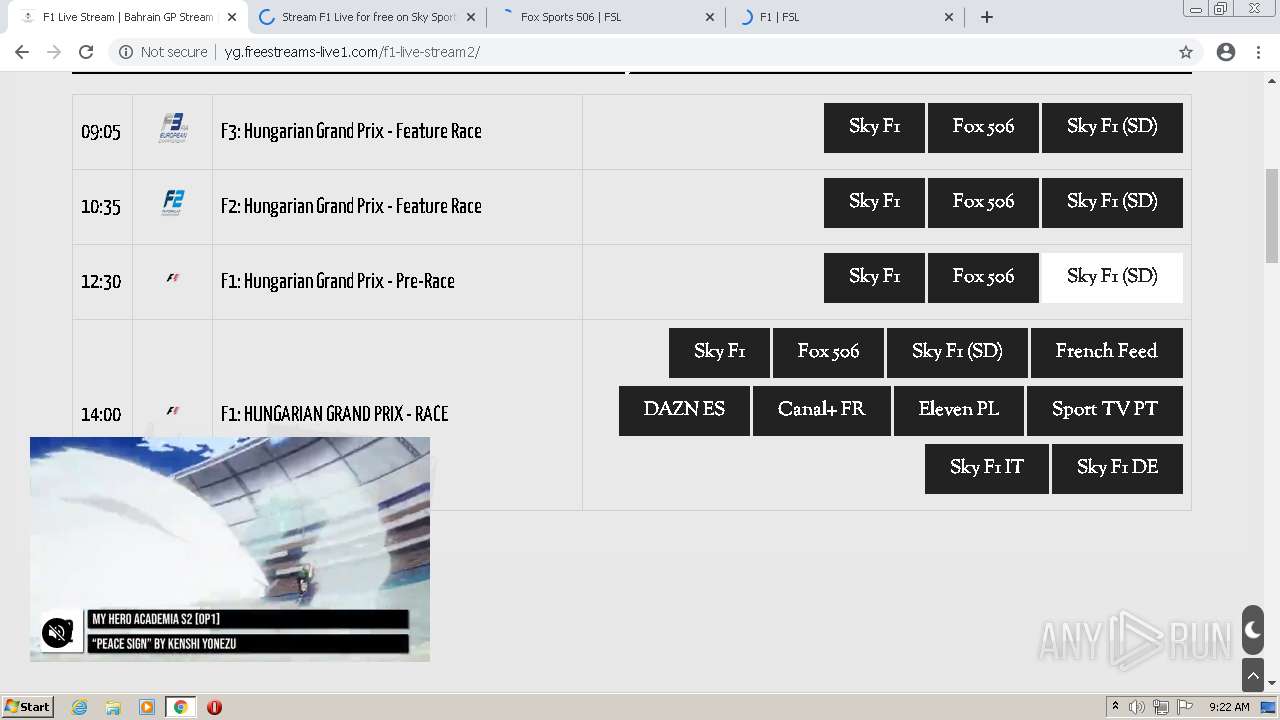
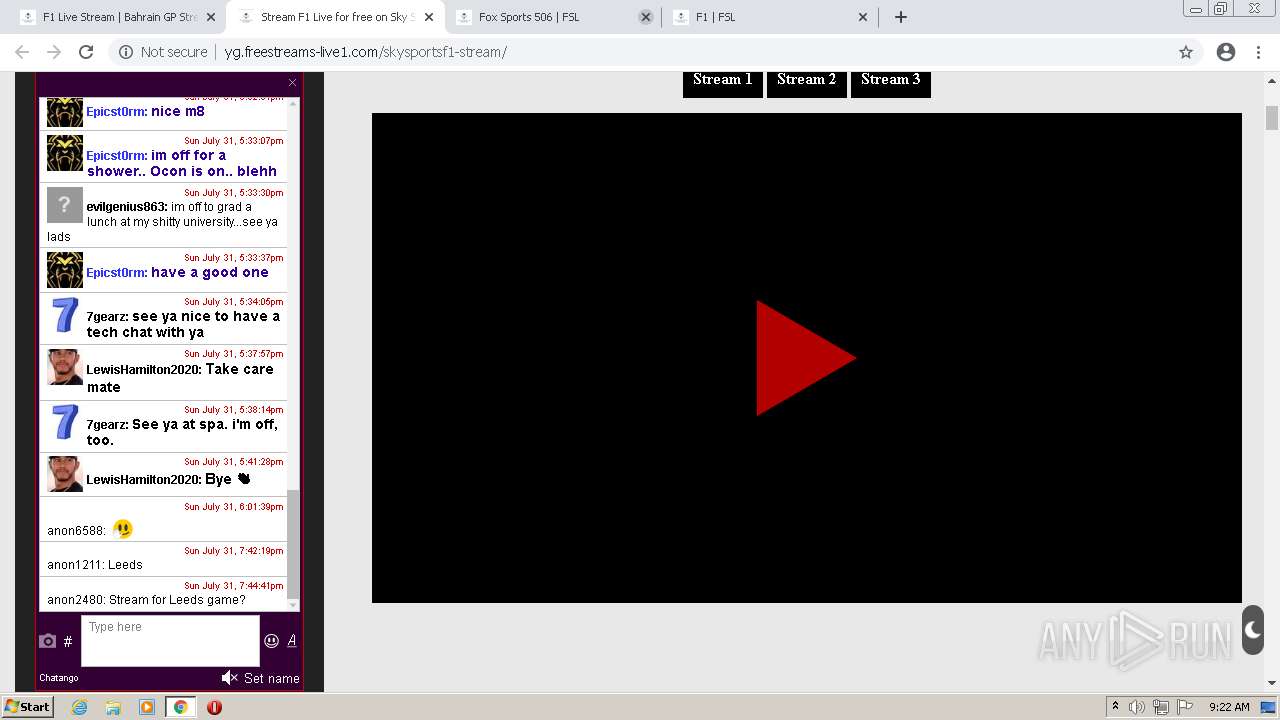
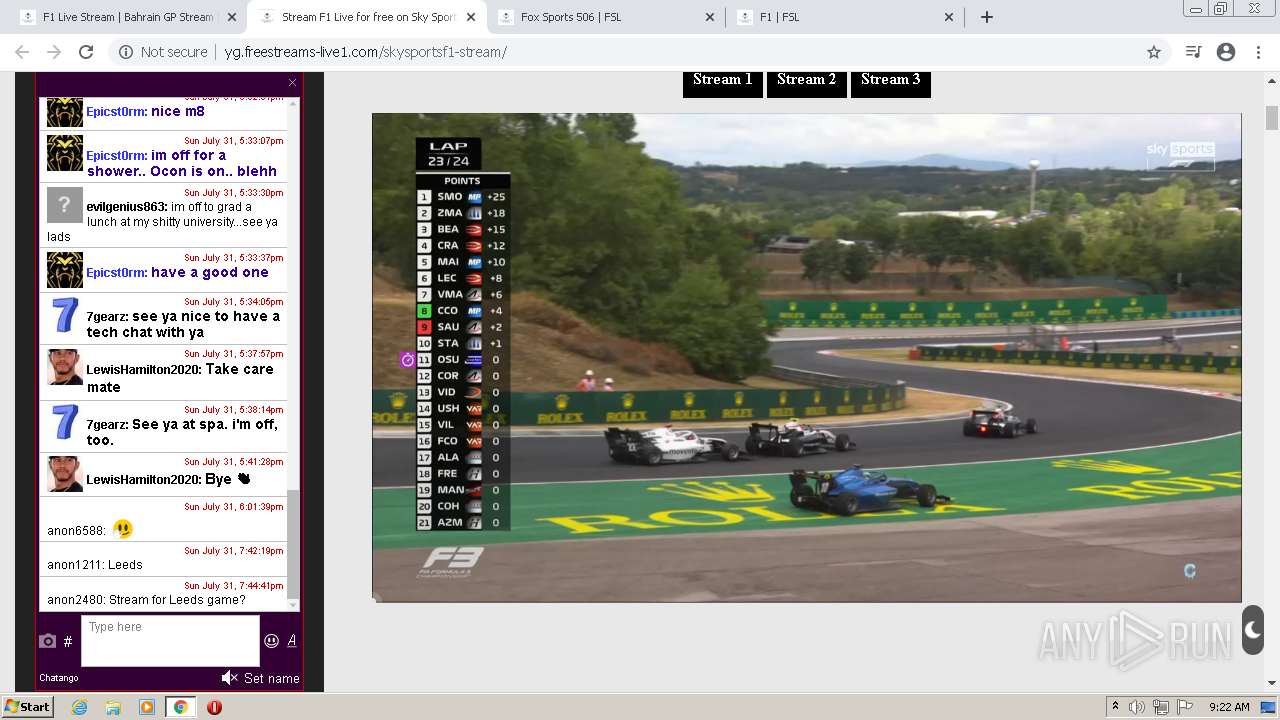
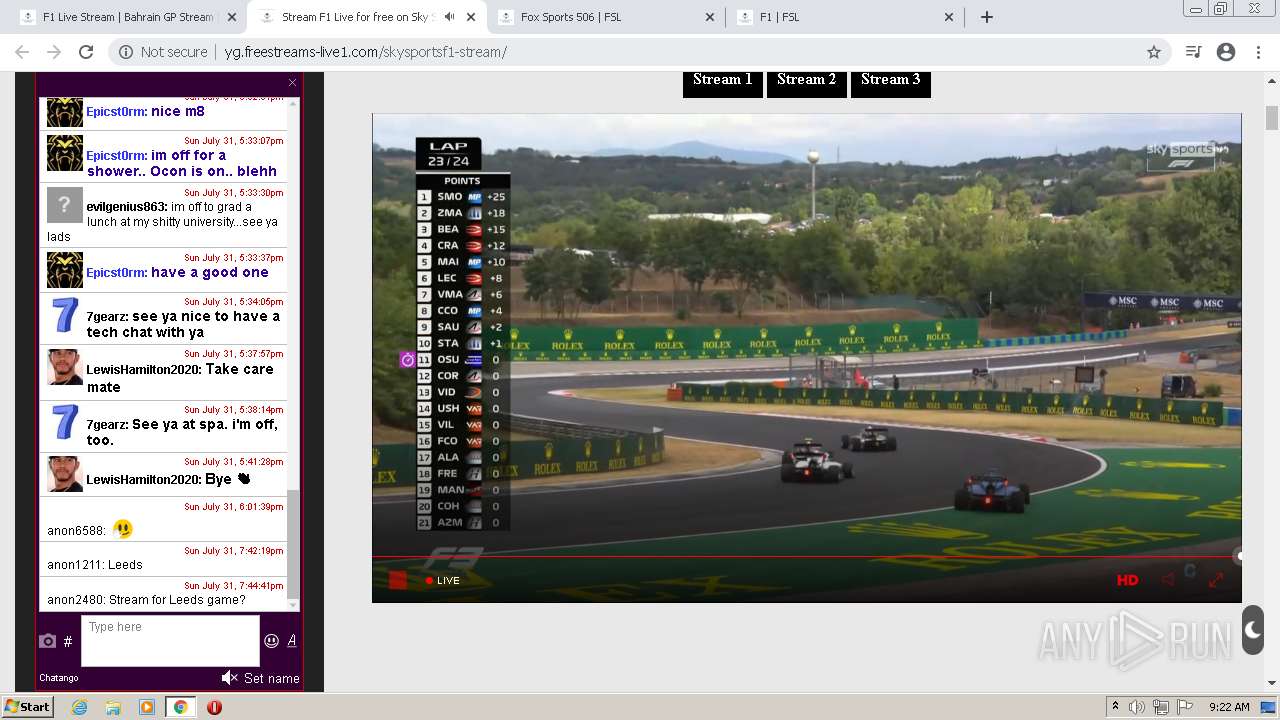
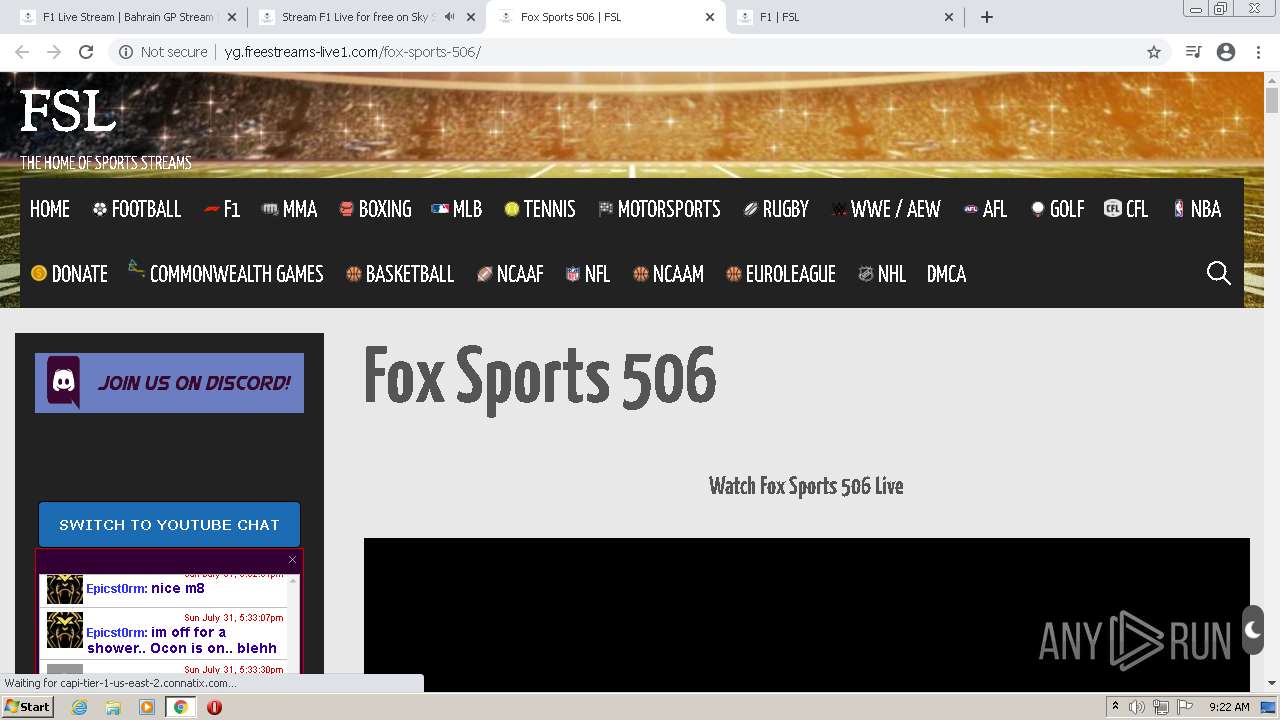
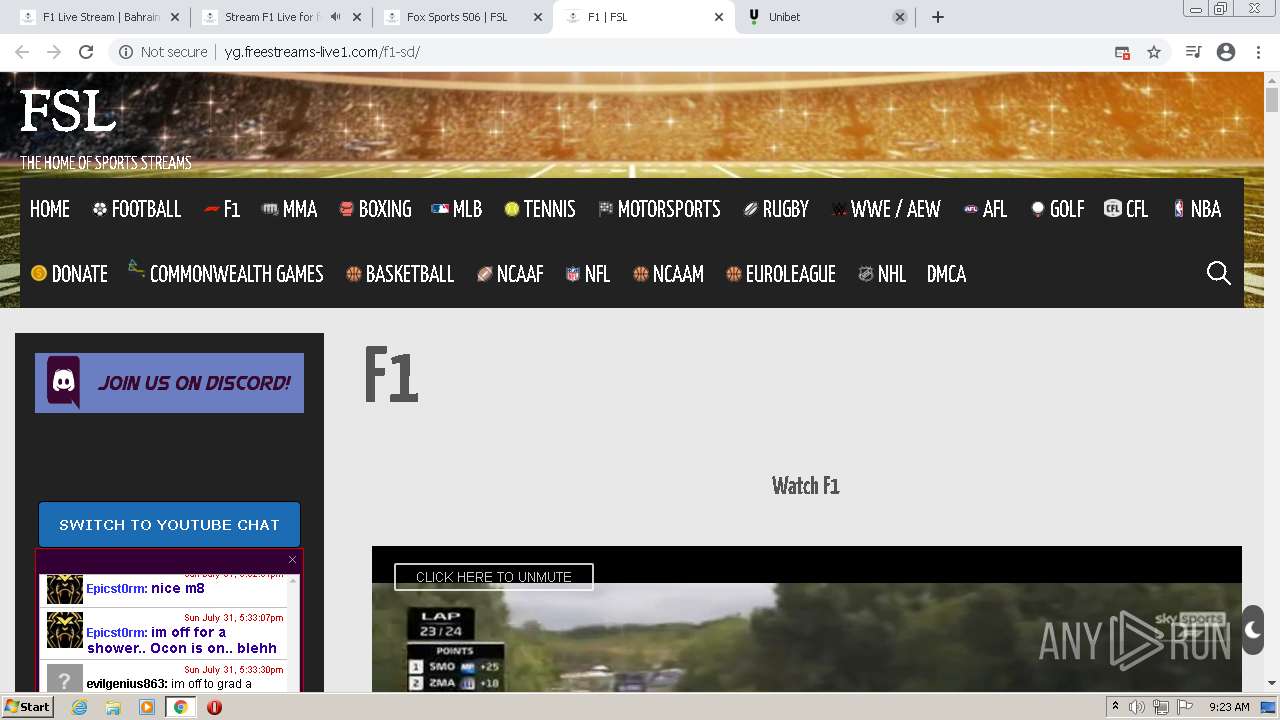
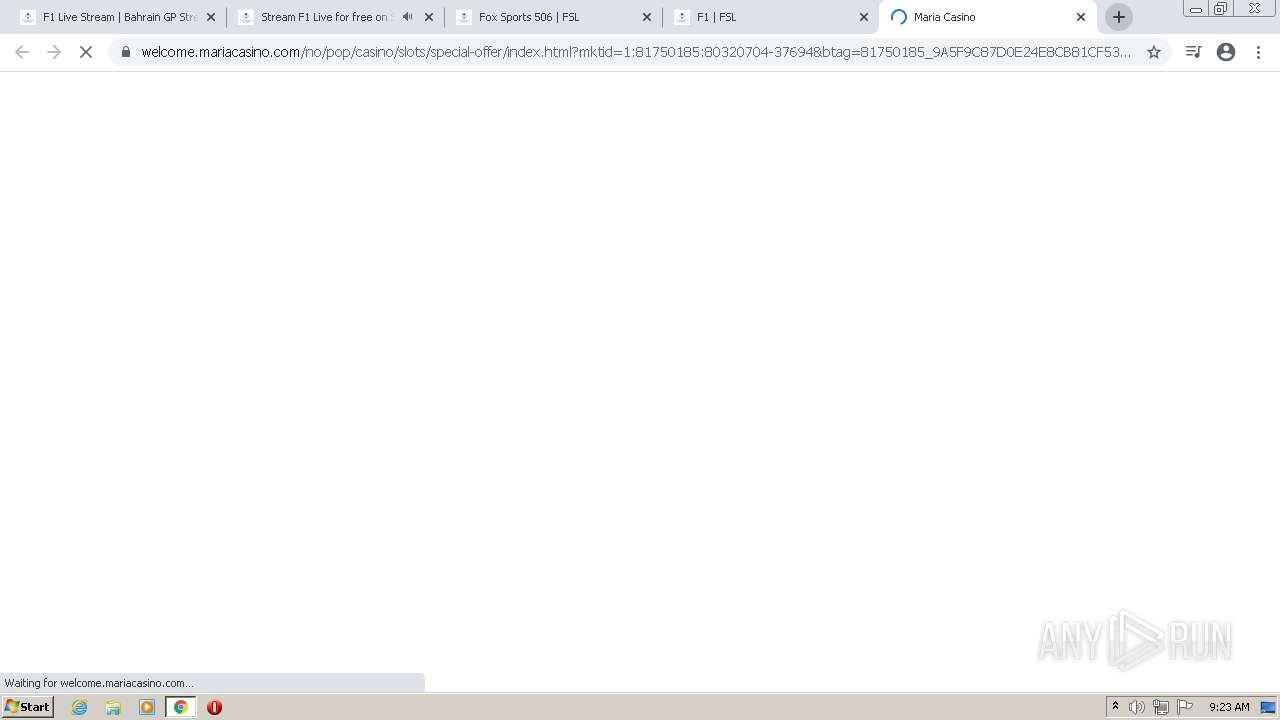
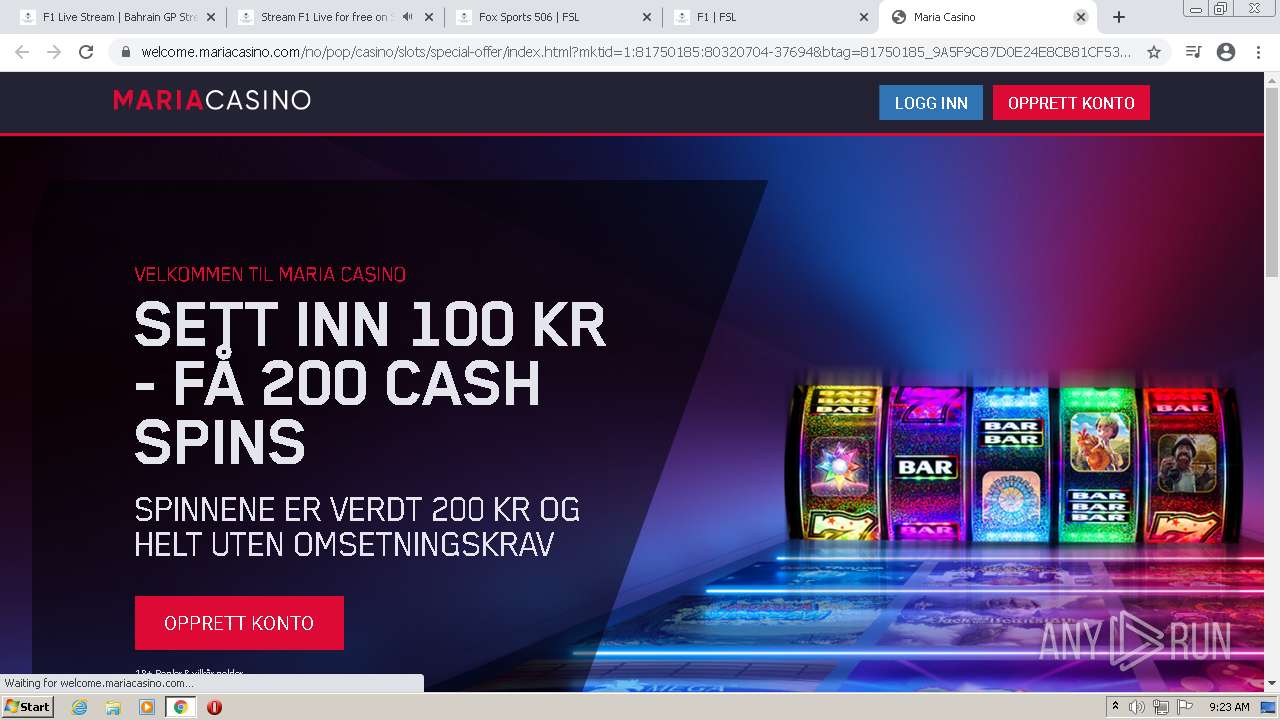
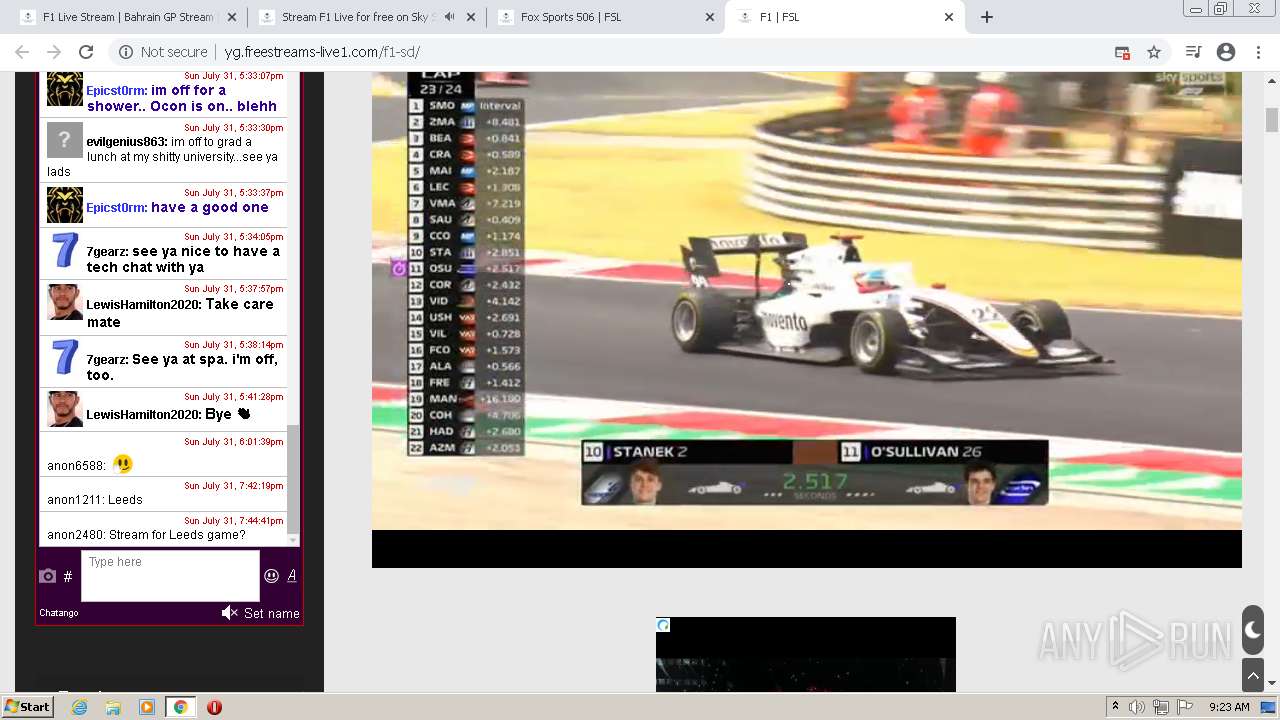
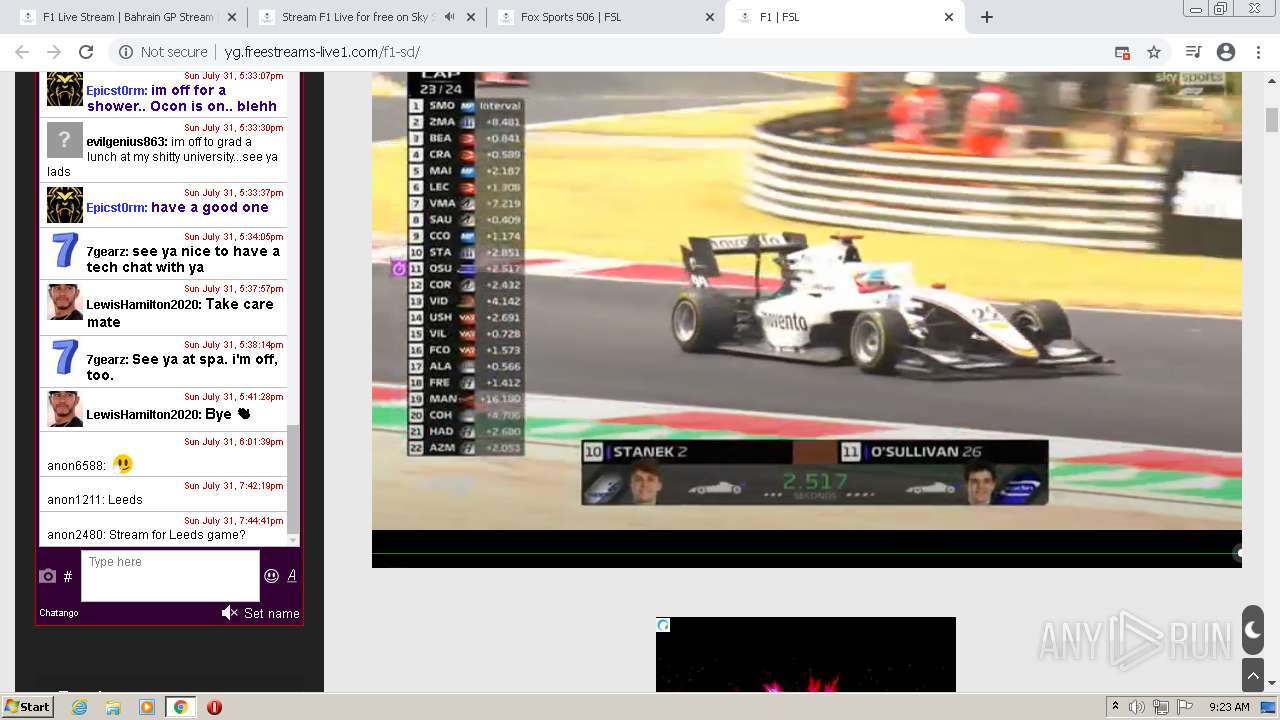
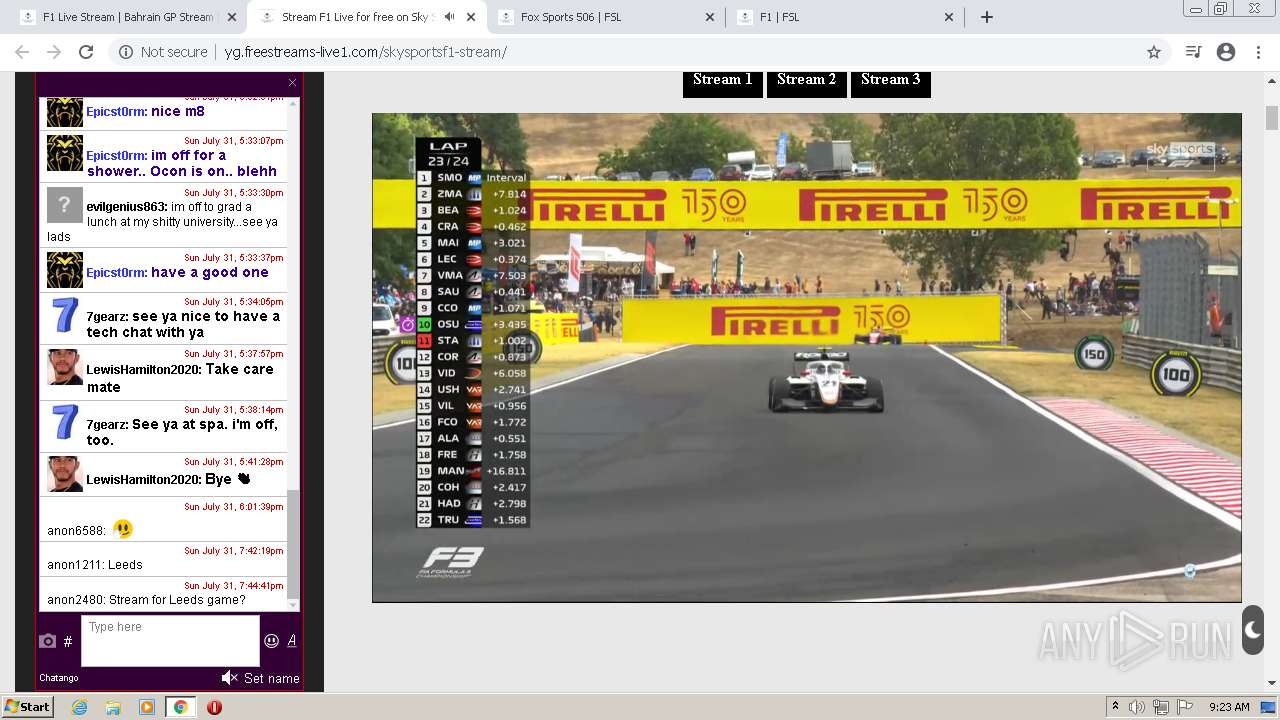
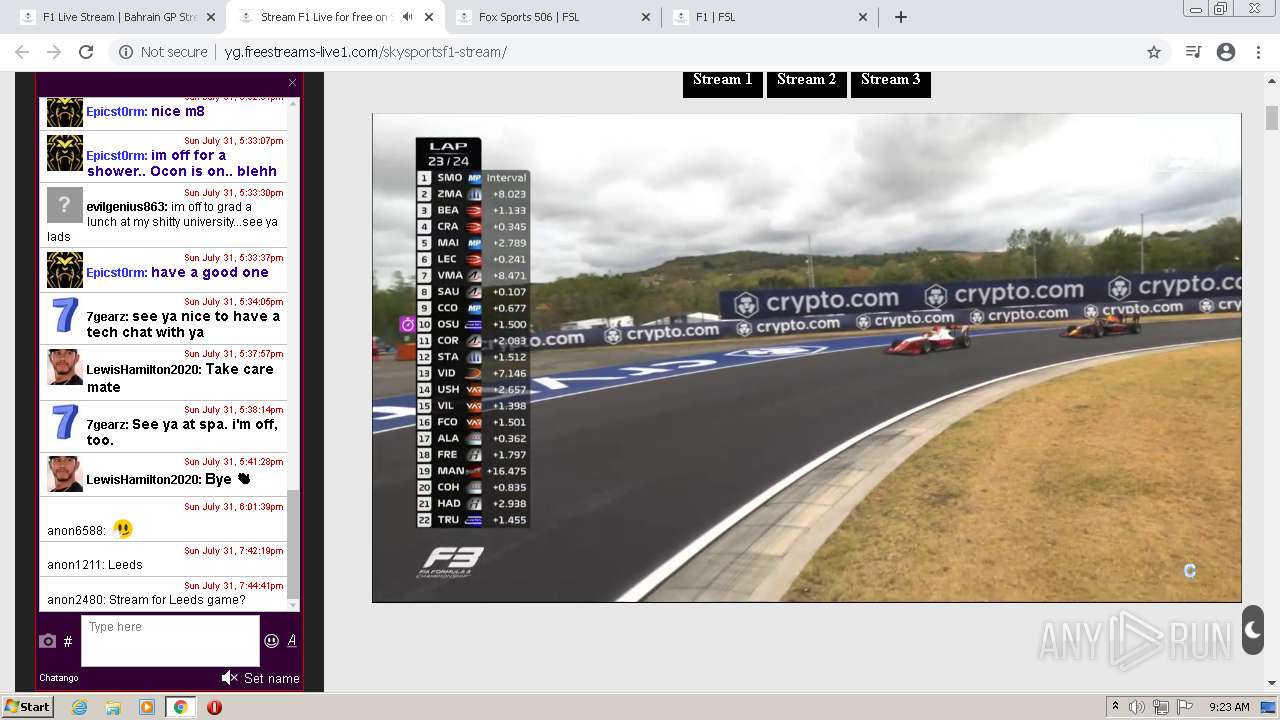
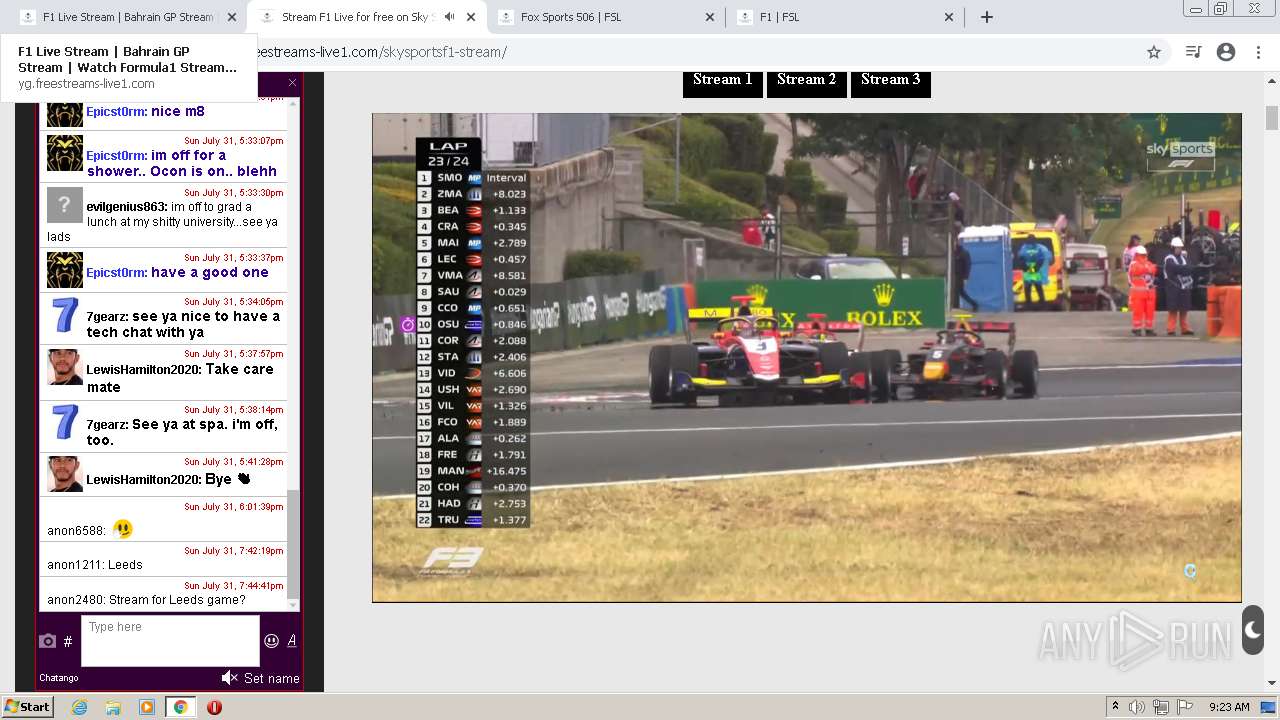
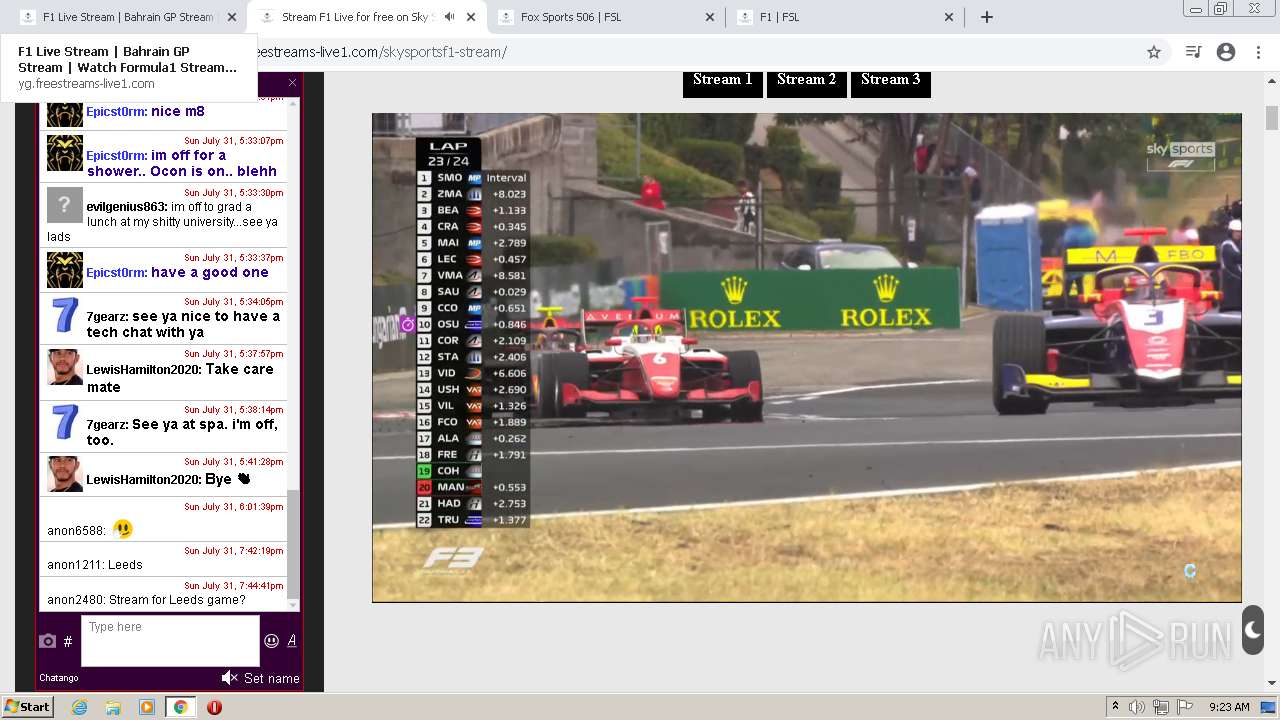
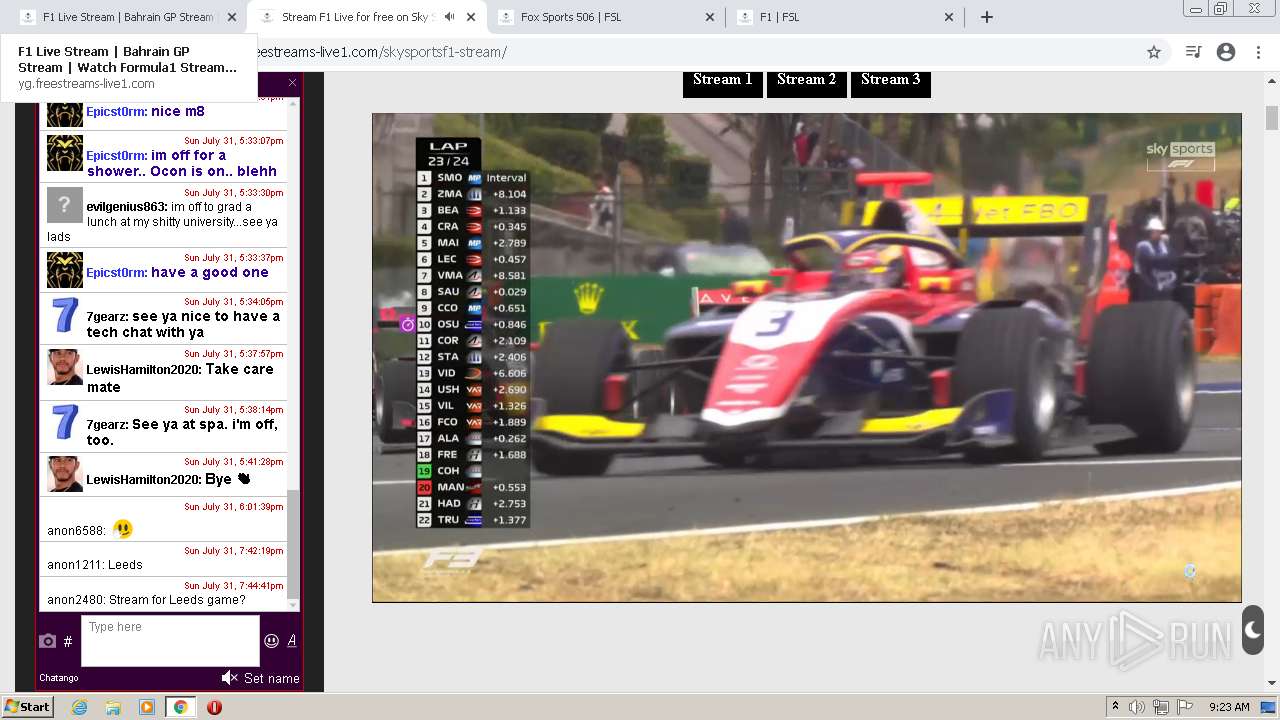
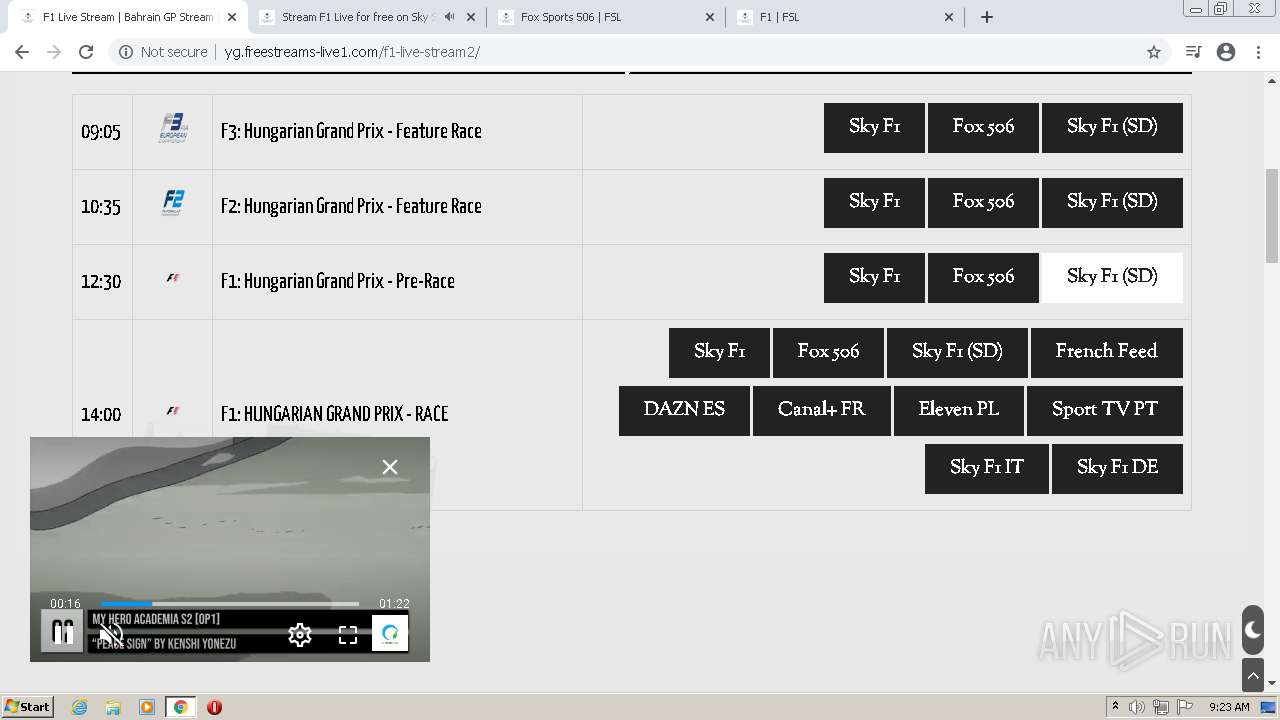
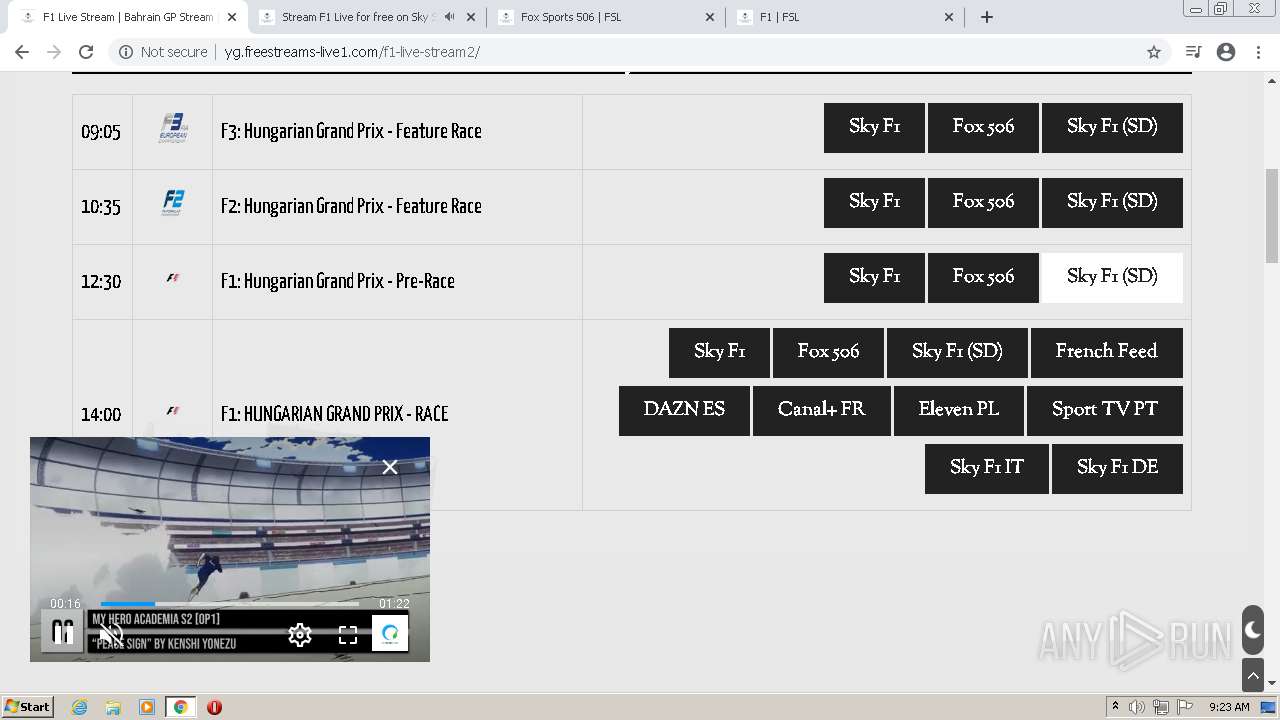
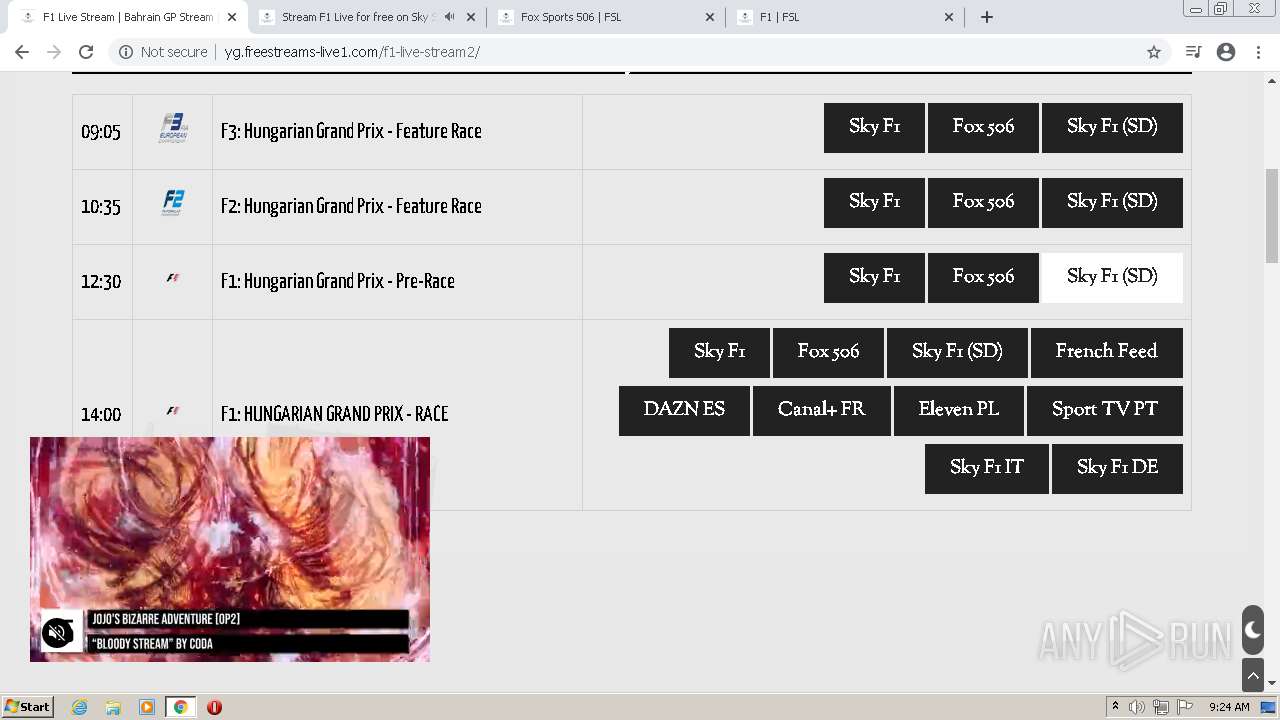
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/ | US | html | 23.6 Kb | suspicious |
3628 | chrome.exe | GET | 301 | 104.21.36.163:80 | http://fs.freestreams-live1.com/wp-content/uploads/2018/12/cflsch.png | US | html | 1.05 Kb | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/plugins/elementor/assets/css/frontend-legacy.min.css?ver=3.6.8 | US | compressed | 854 b | suspicious |
3628 | chrome.exe | GET | 301 | 104.21.36.163:80 | http://fs.freestreams-live1.com/wp-content/uploads/2018/12/donate.png | US | html | 1.05 Kb | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/themes/durga/style.min.css?ver=1.1.1 | US | compressed | 6.84 Kb | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/uploads/elementor/css/post-156.css?ver=1659315232 | US | text | 433 b | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/themes/durga/css/mobile.min.css?ver=1.1.1 | US | compressed | 1.44 Kb | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/uploads/elementor/css/post-58538.css?ver=1658972104 | US | text | 354 b | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/uploads/2019/02/sky-1.png | US | image | 7.83 Kb | suspicious |
3628 | chrome.exe | GET | 200 | 104.21.36.163:80 | http://yg.freestreams-live1.com/wp-content/plugins/elementor/assets/lib/font-awesome/css/font-awesome.min.css?ver=4.7.0 | US | compressed | 6.82 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3628 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3628 | chrome.exe | 104.21.36.163:443 | freestreams-live1.com | Cloudflare Inc | US | suspicious |
3628 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3628 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3628 | chrome.exe | 104.21.36.163:80 | freestreams-live1.com | Cloudflare Inc | US | suspicious |
3628 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
3628 | chrome.exe | 184.24.77.133:443 | a.espncdn.com | Time Warner Cable Internet LLC | US | suspicious |
3628 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3628 | chrome.exe | 3.229.90.217:443 | platform.pubfuture.com | — | US | unknown |
3628 | chrome.exe | 151.101.112.193:443 | i.imgur.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
freestreams-live1.com |
| malicious |
accounts.google.com |
| shared |
yg.freestreams-live1.com |
| unknown |
clients2.googleusercontent.com |
| whitelisted |
a.espncdn.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
fs.freestreams-live1.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3628 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3628 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3628 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3628 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3628 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3628 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3628 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3628 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |